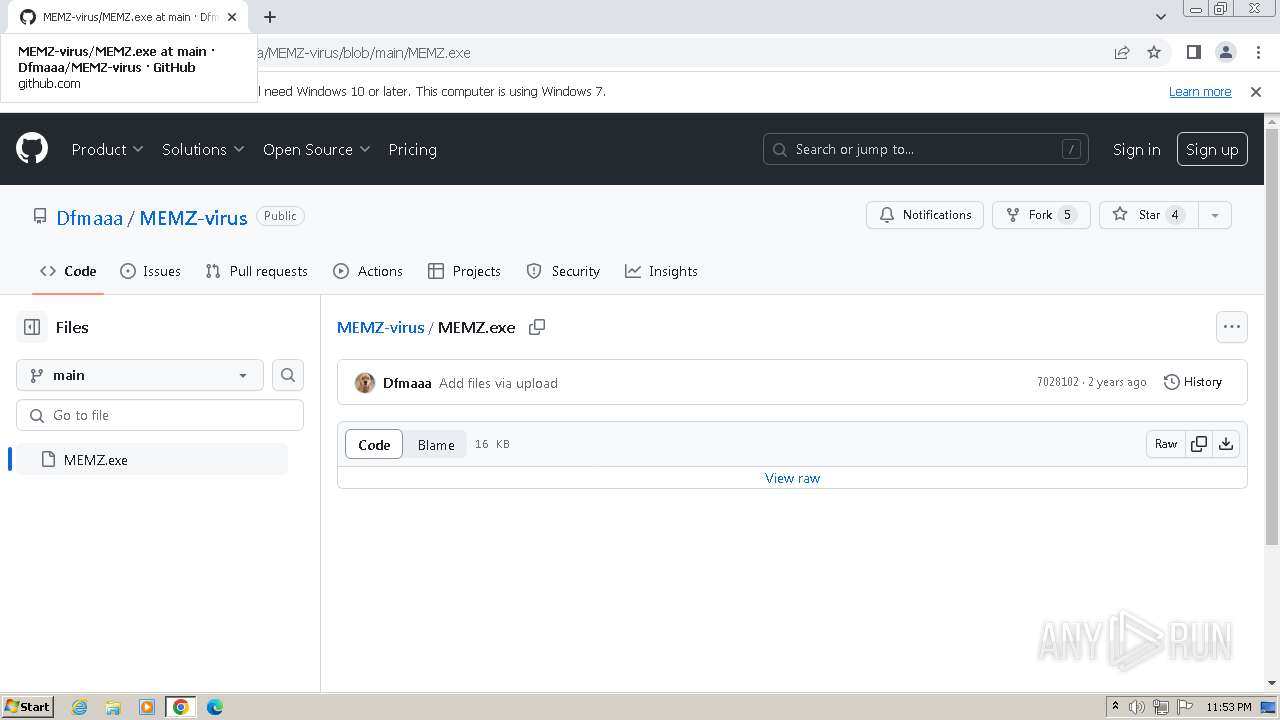
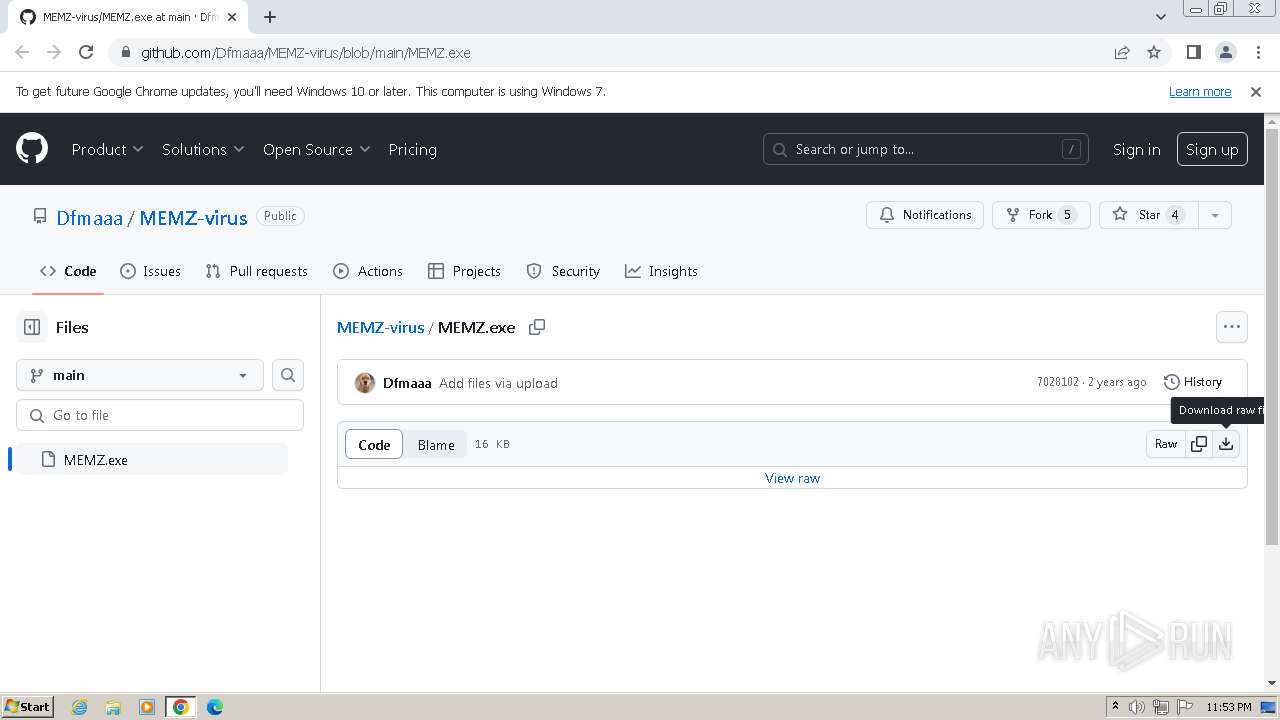
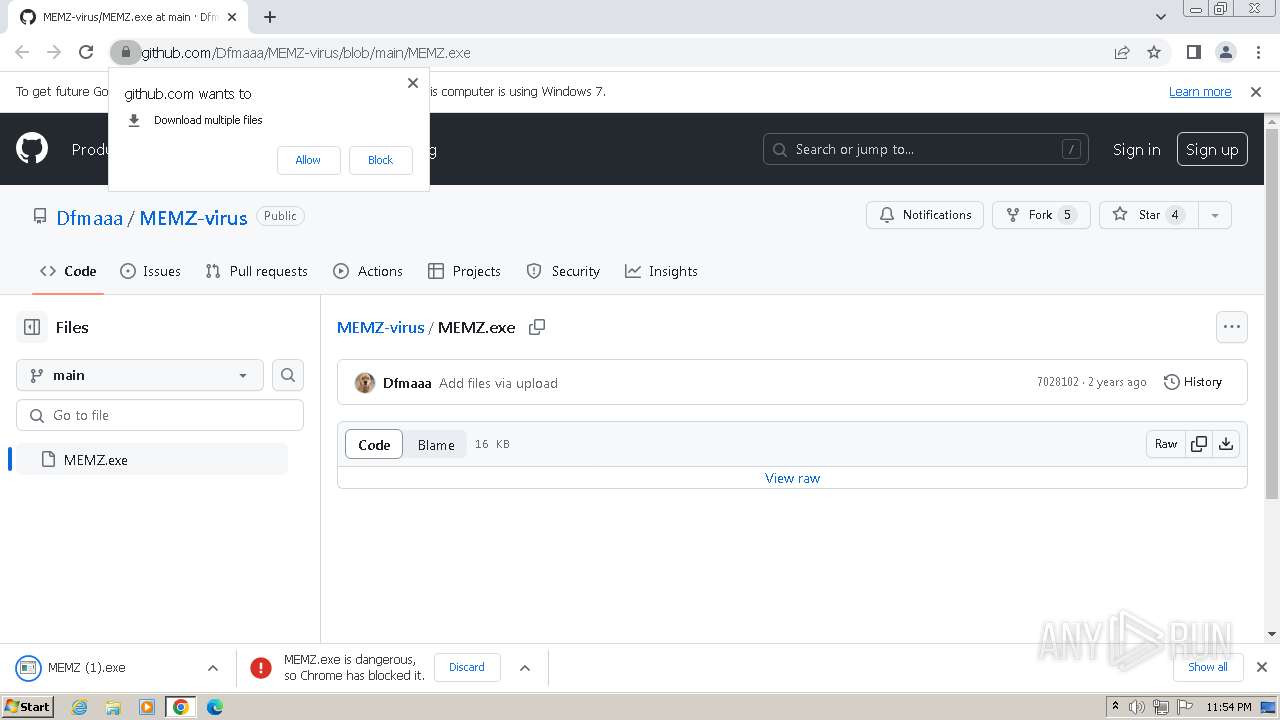
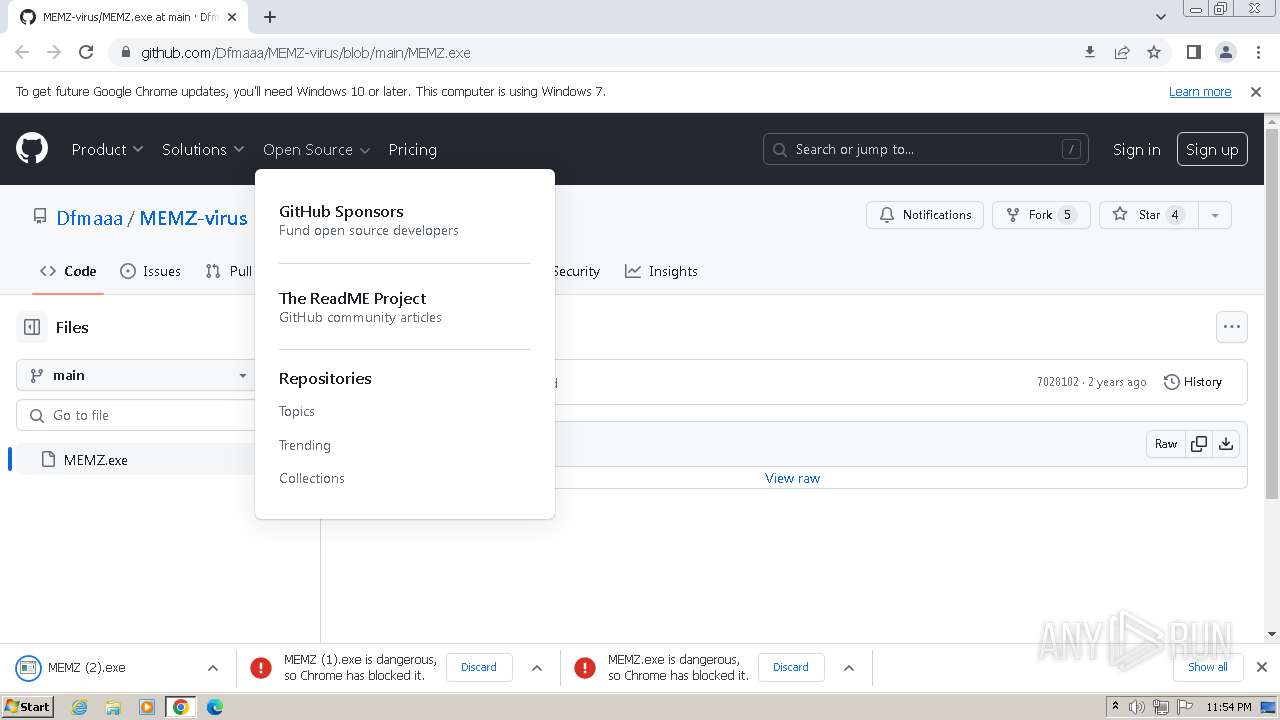
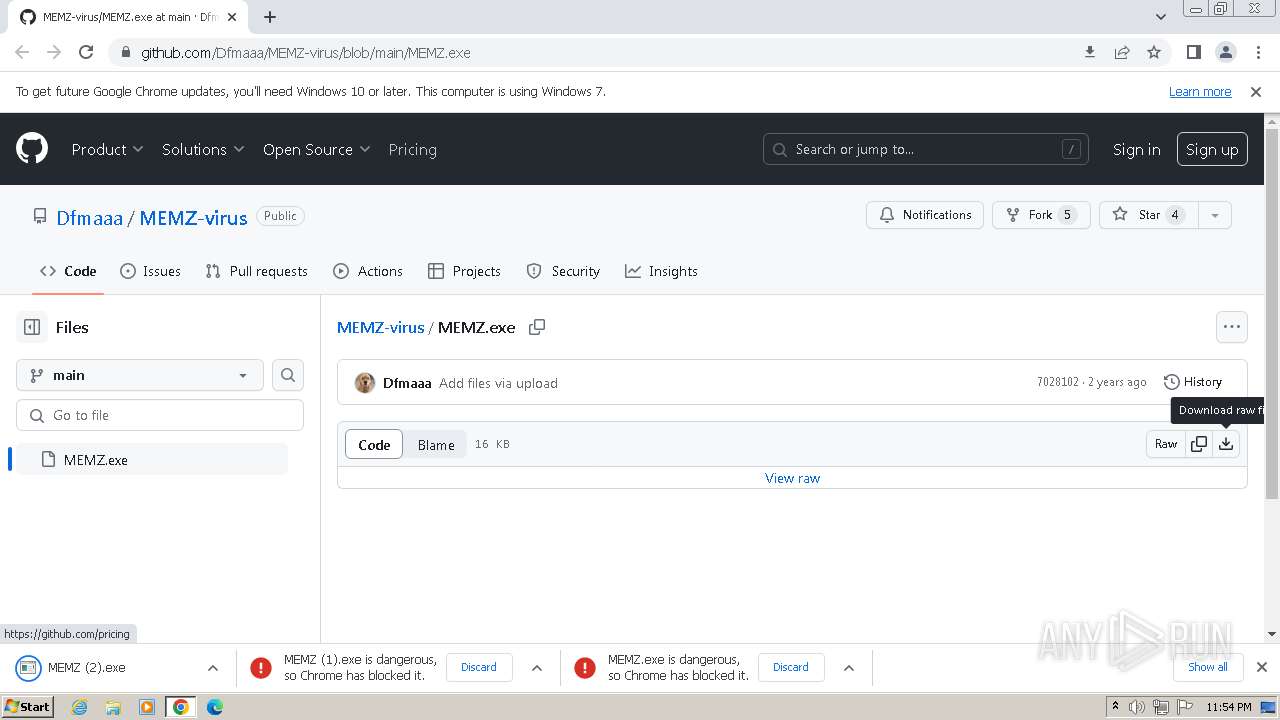
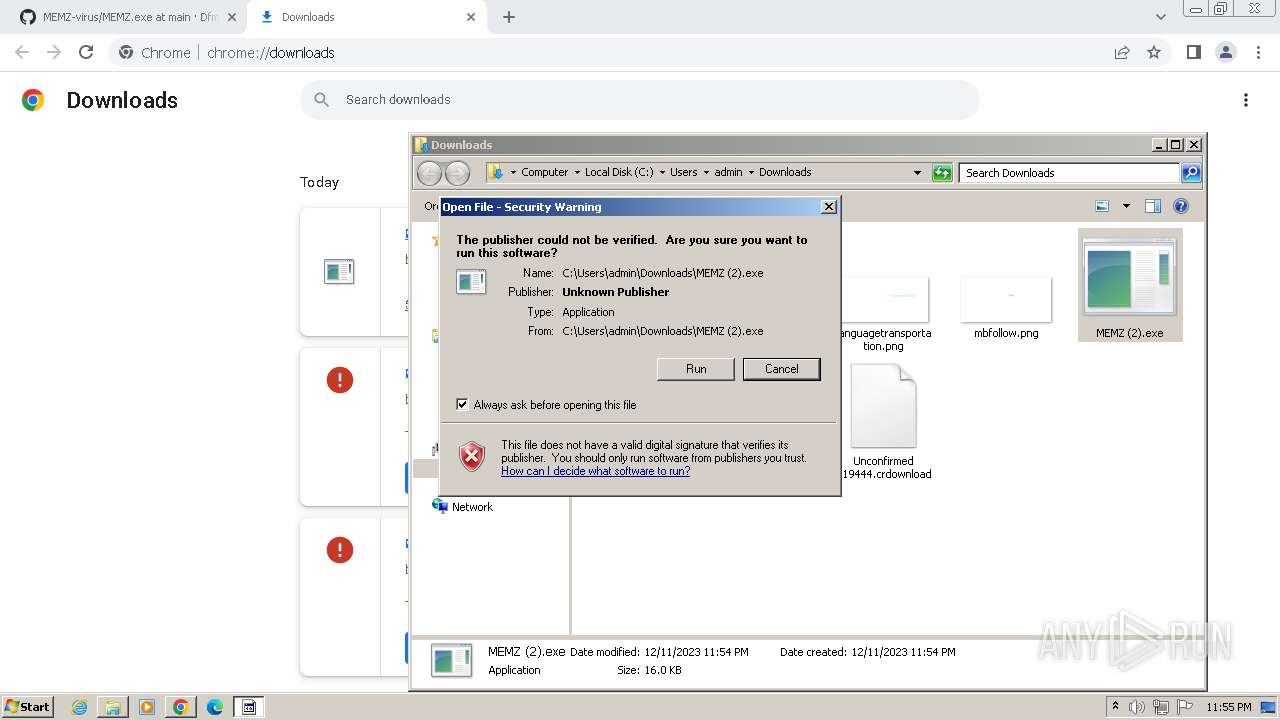
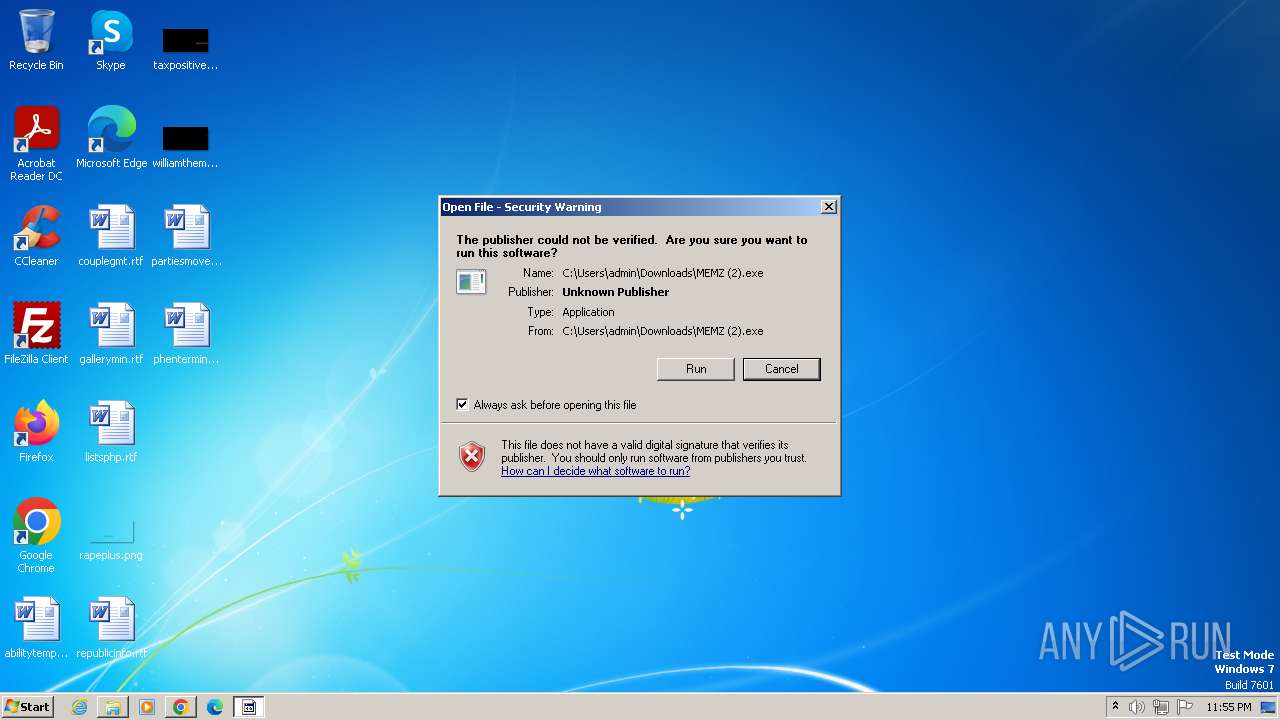
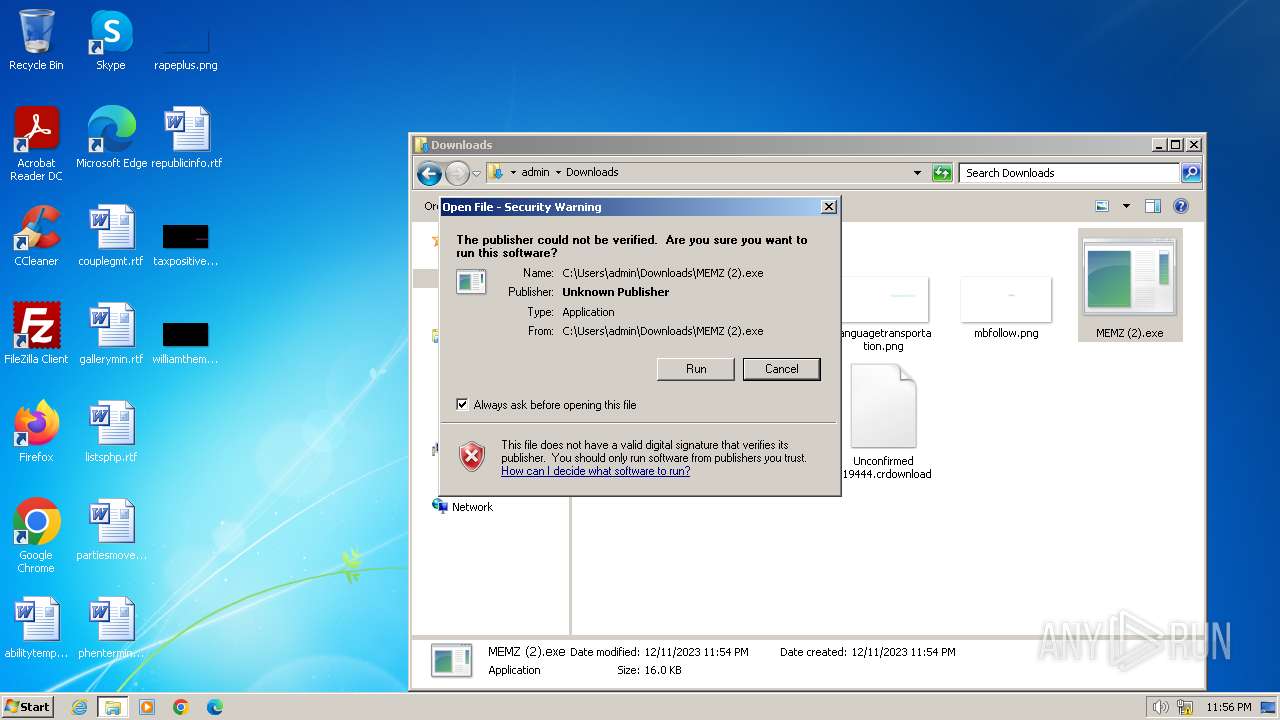
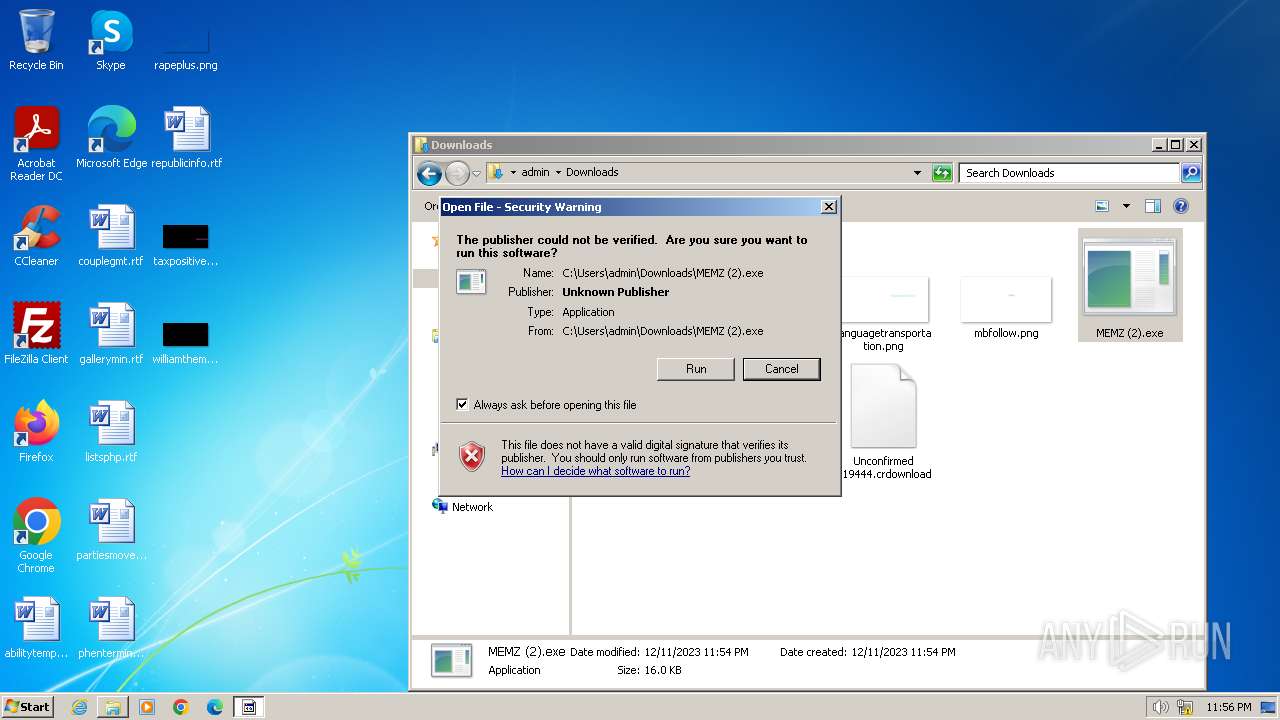
| URL: | https://github.com/Dfmaaa/MEMZ-virus/blob/main/MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/29706bd5-a34f-4433-80a8-f51f1faea9a0 |
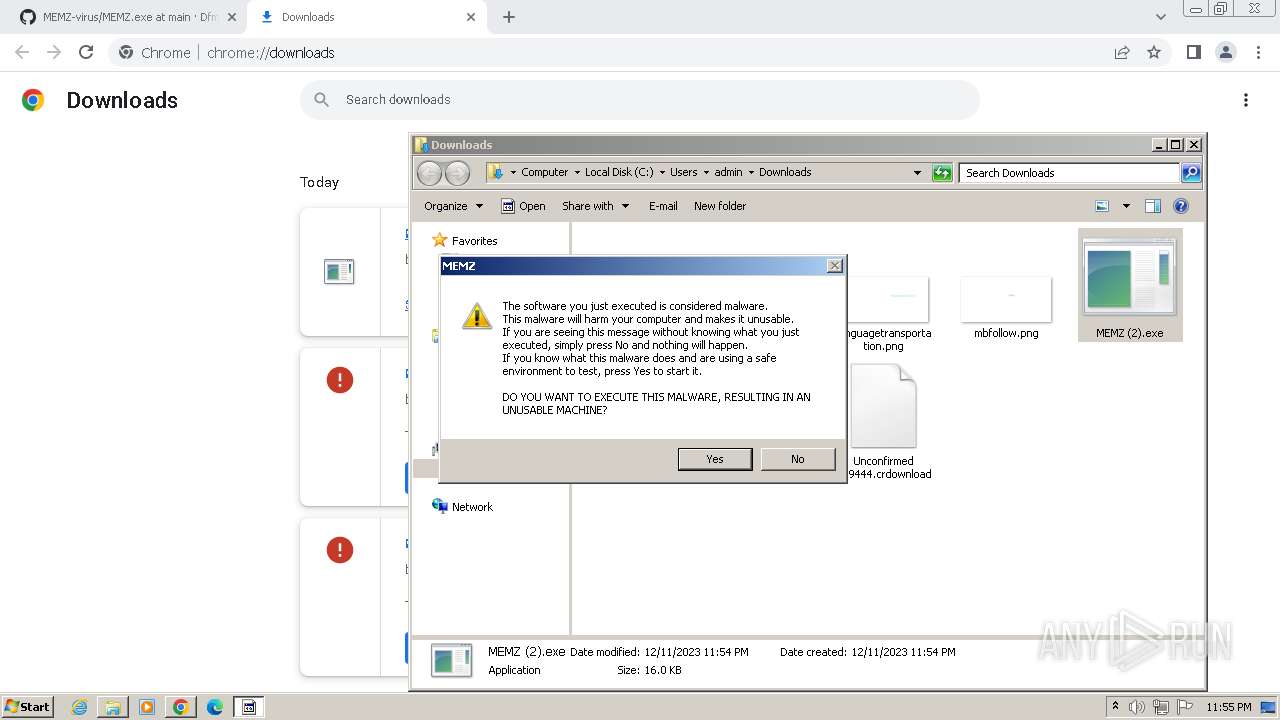
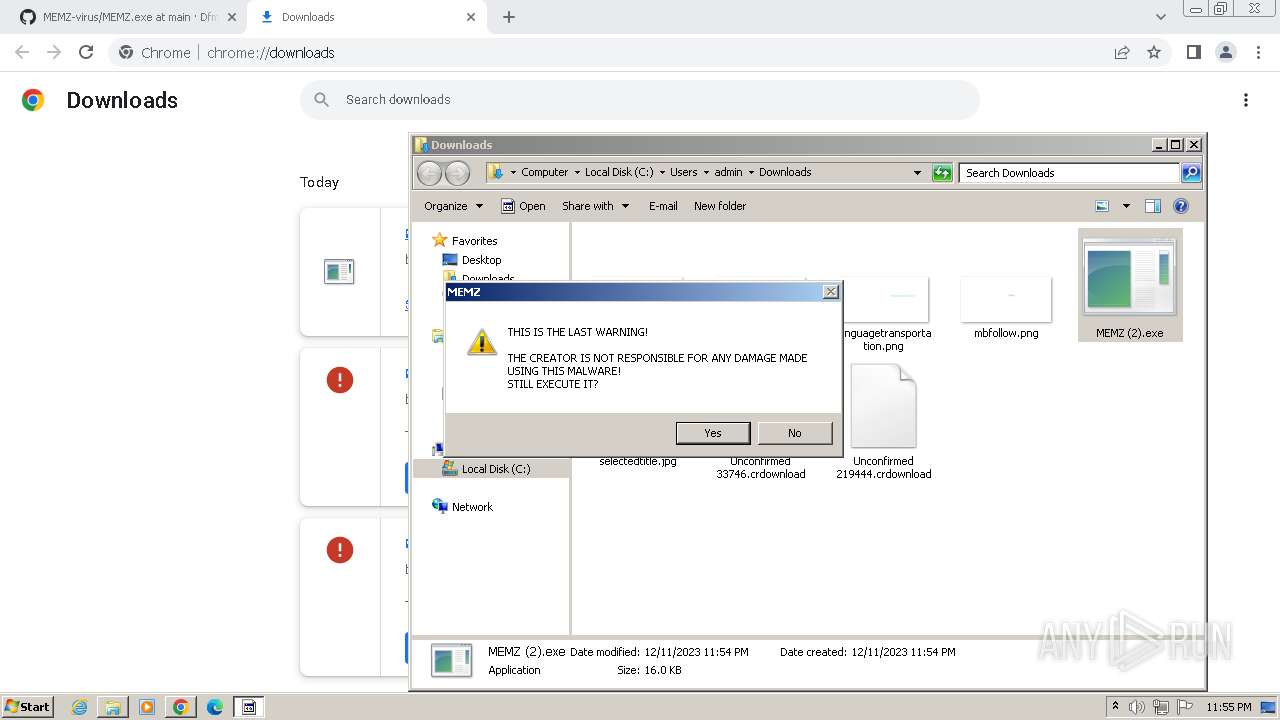
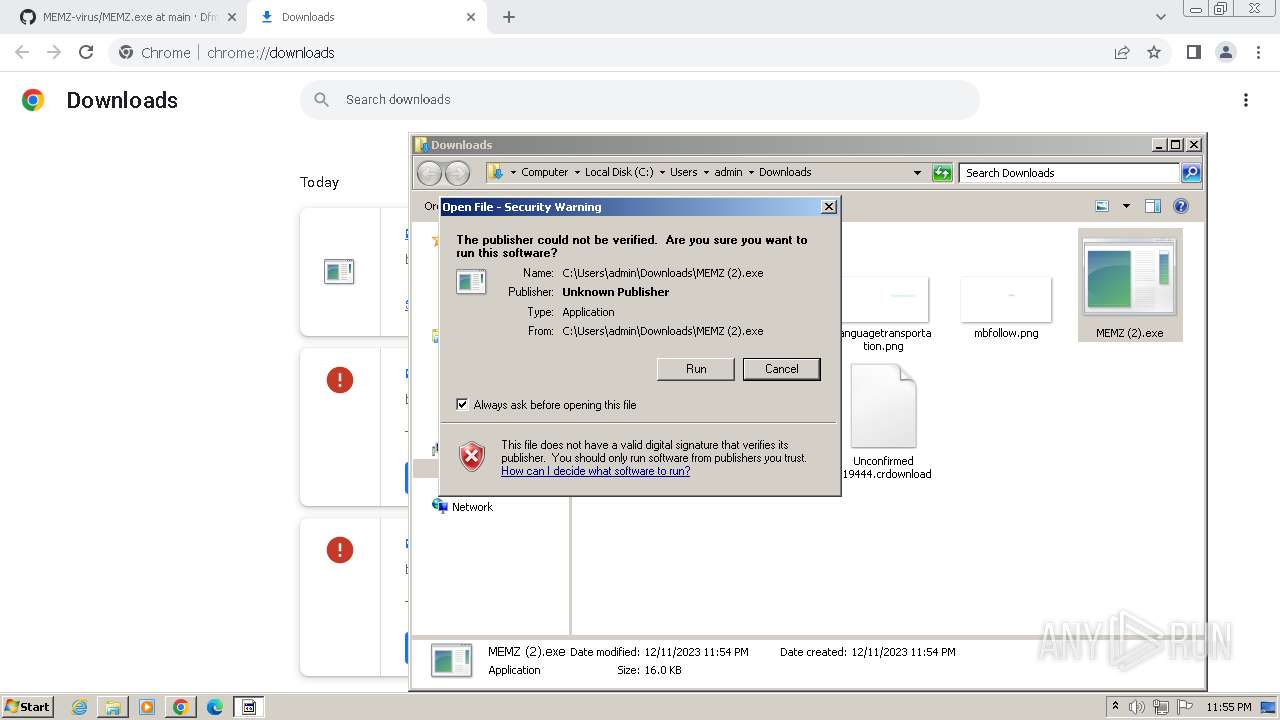
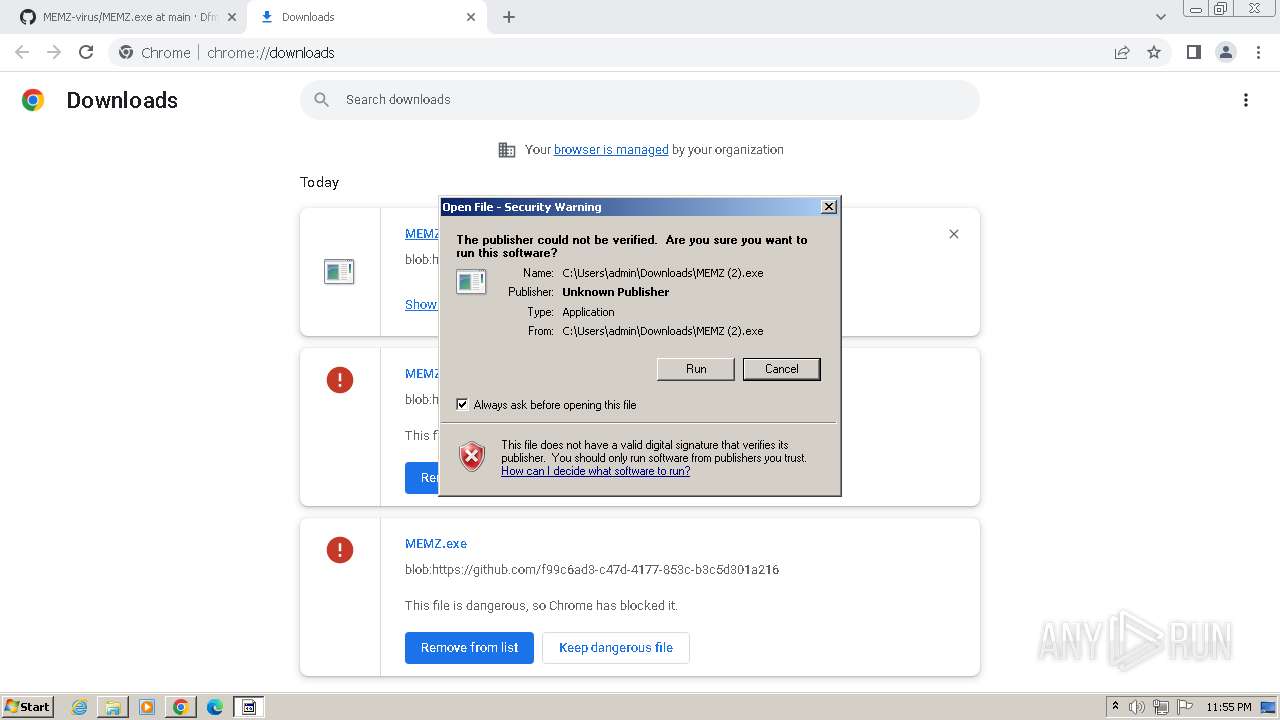
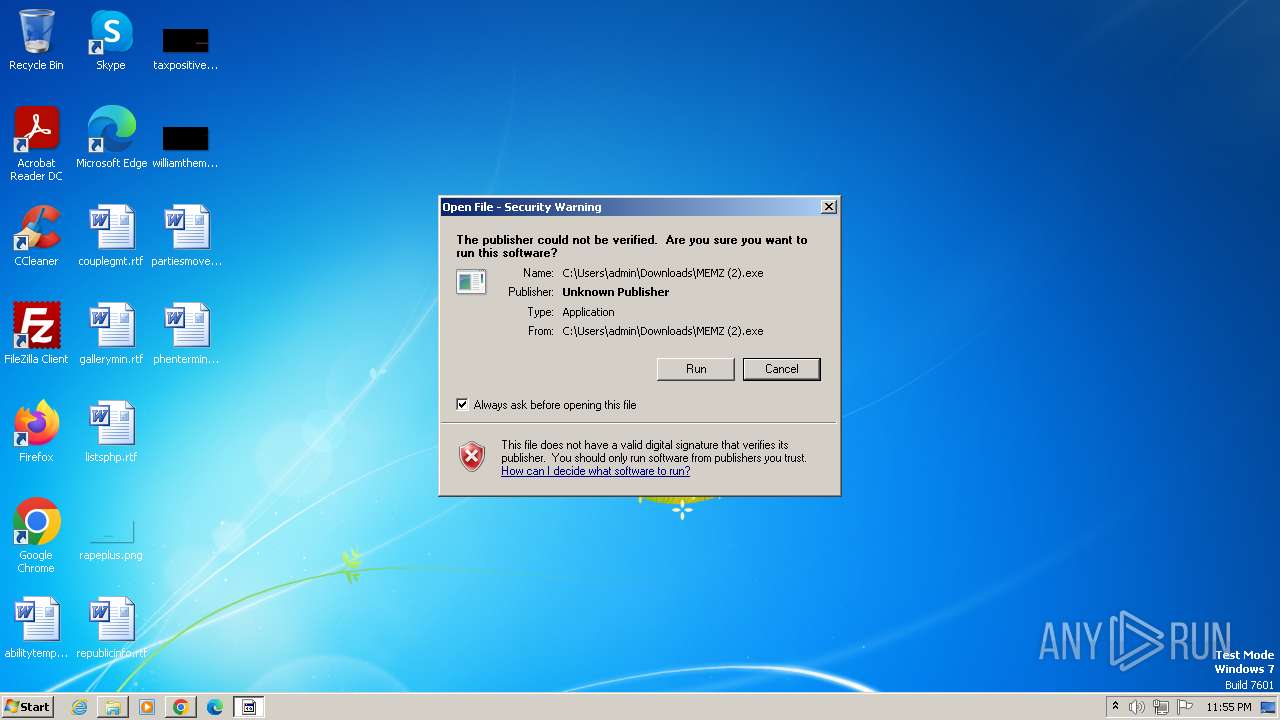
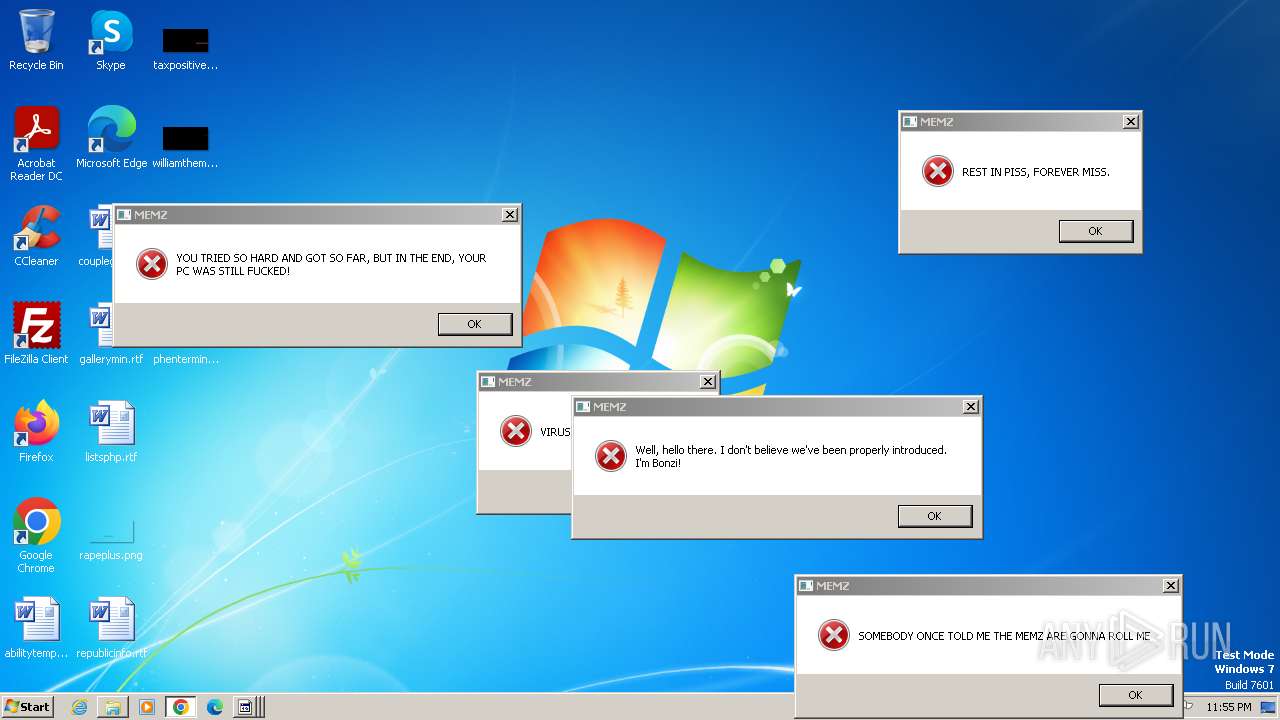
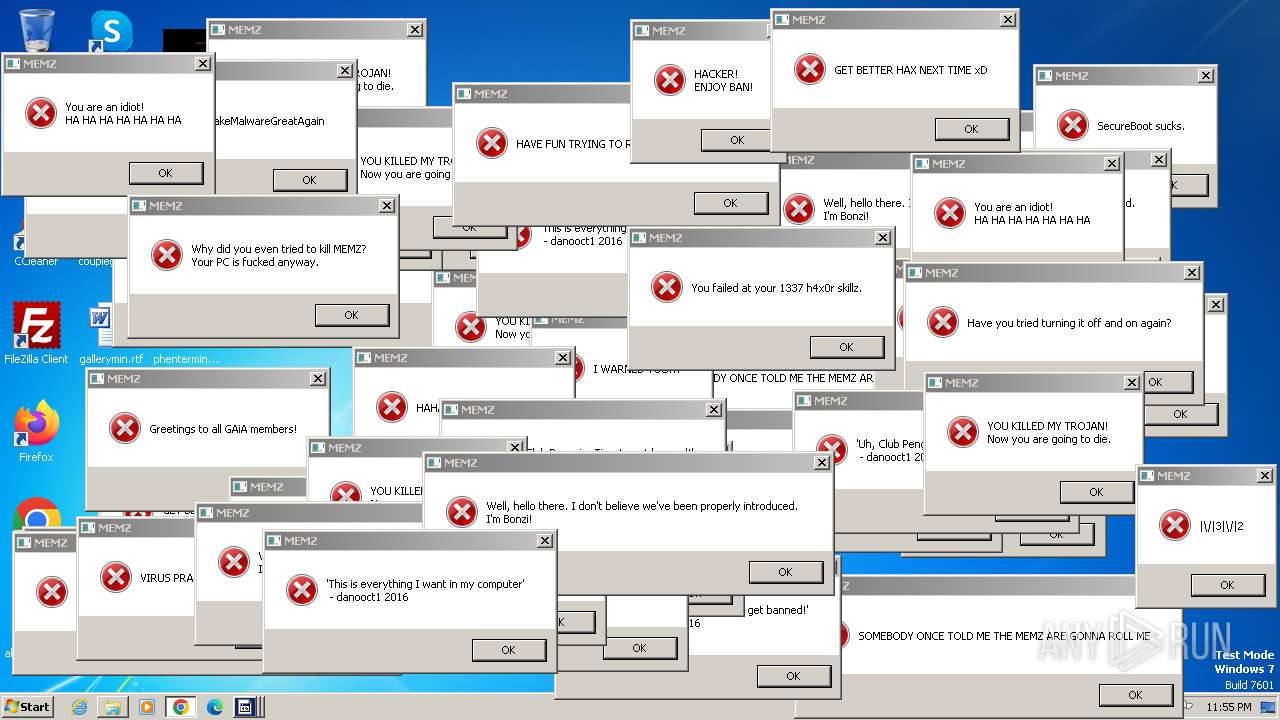
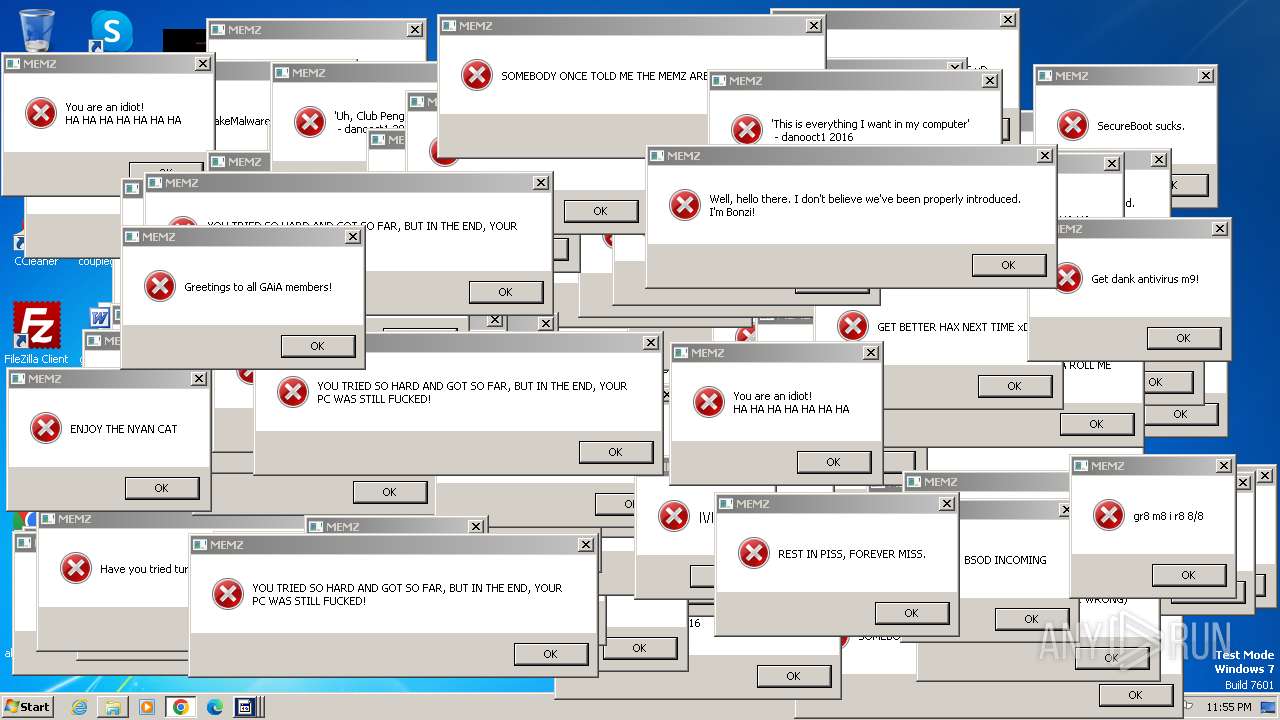
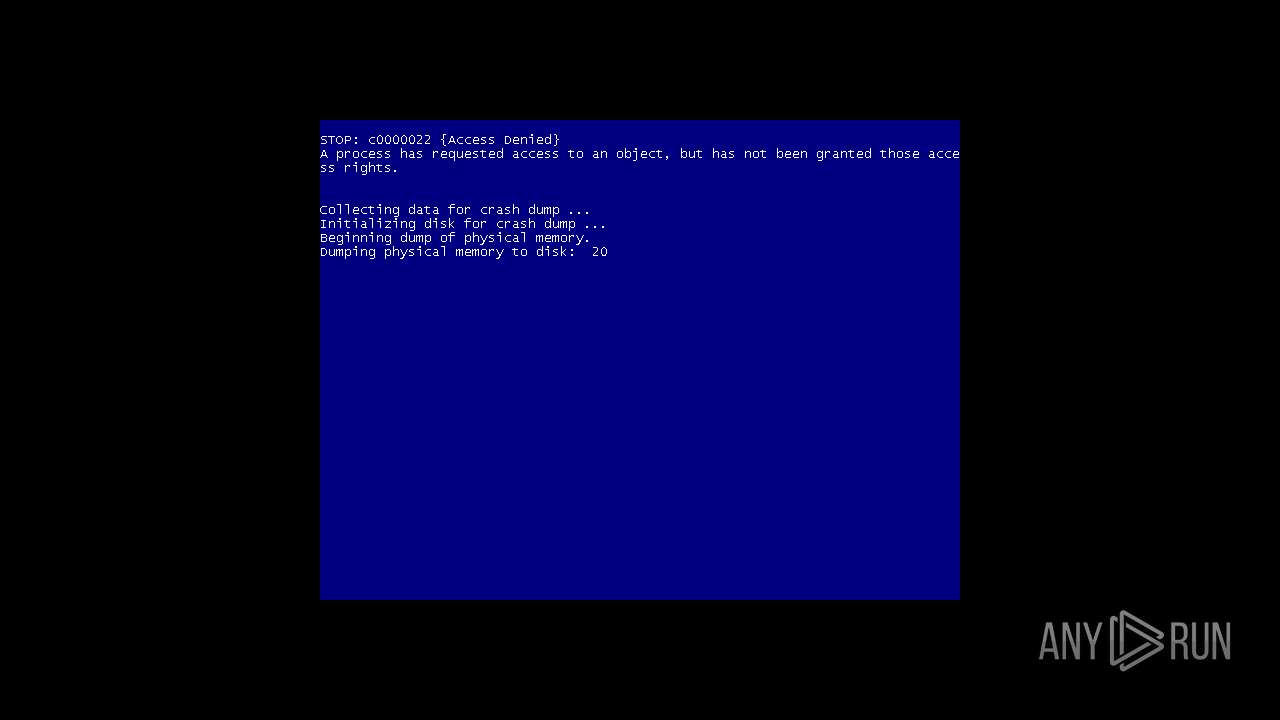
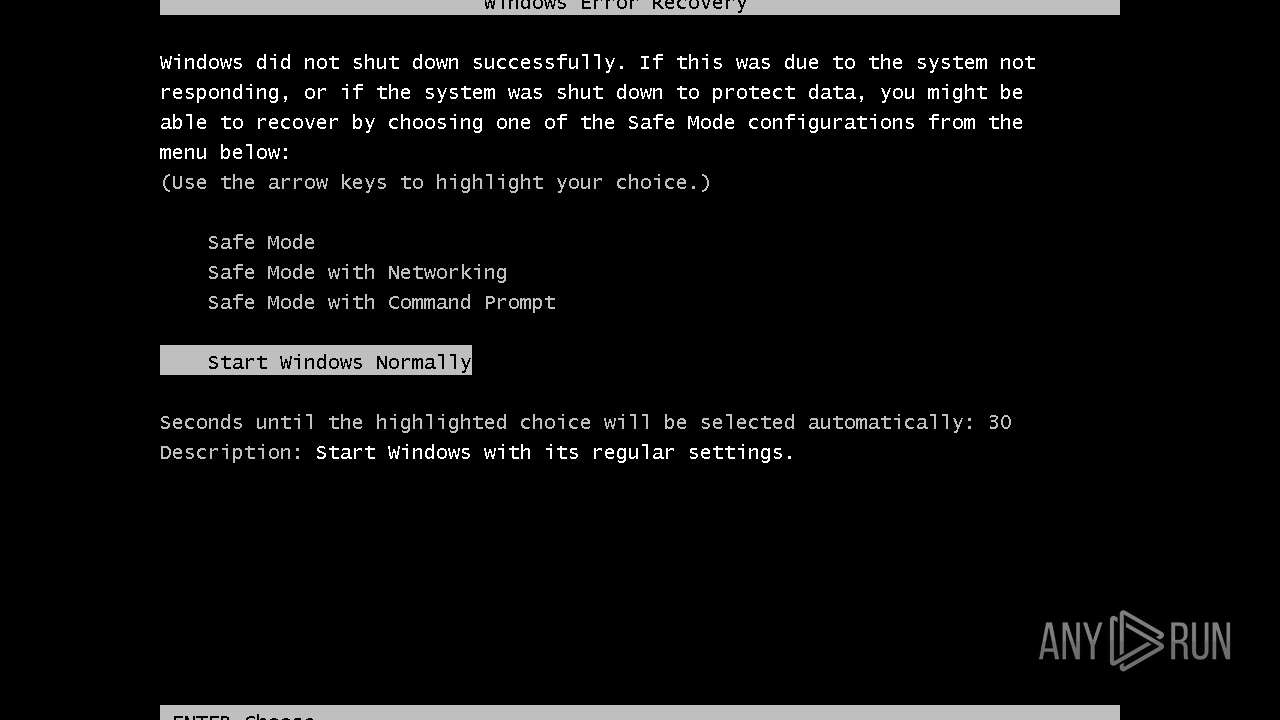
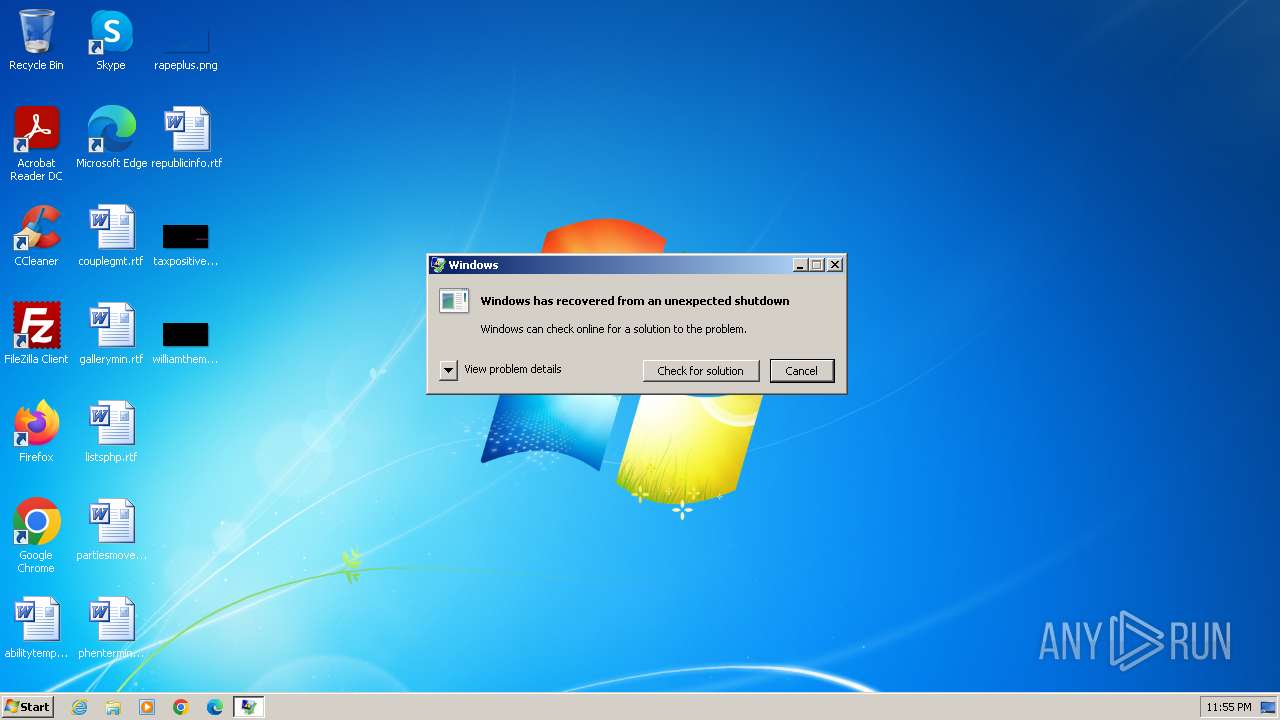
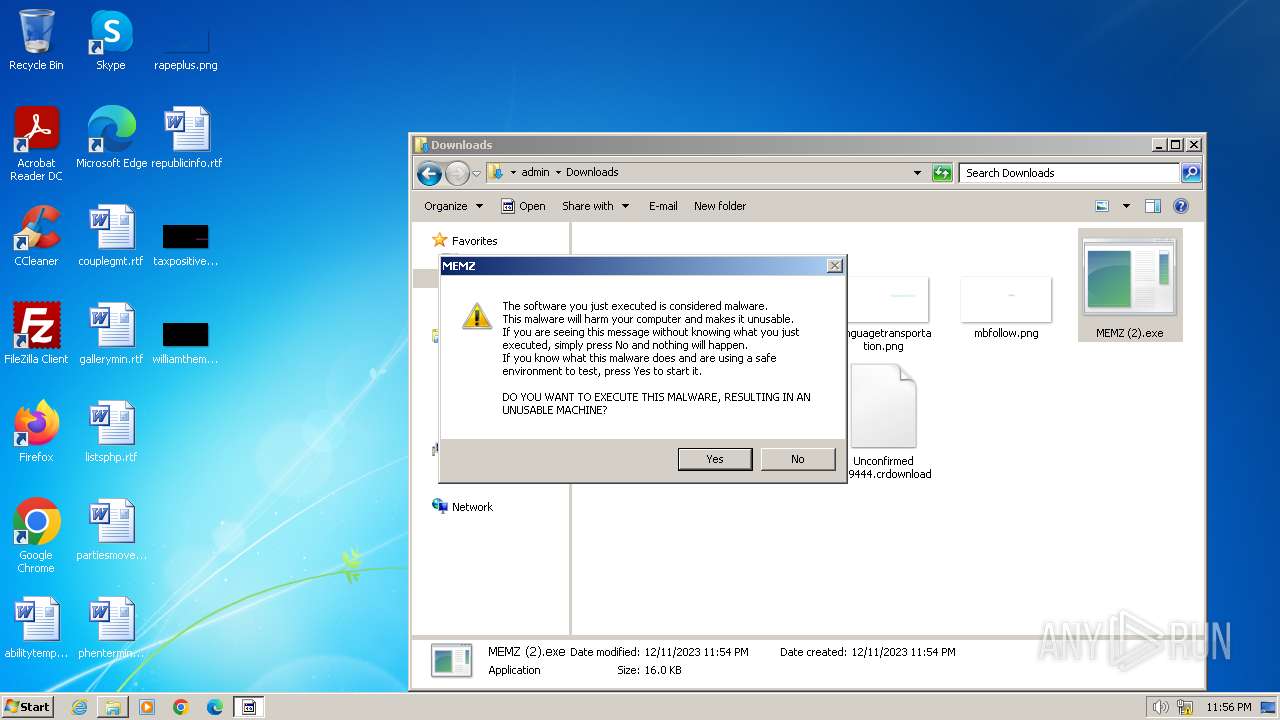
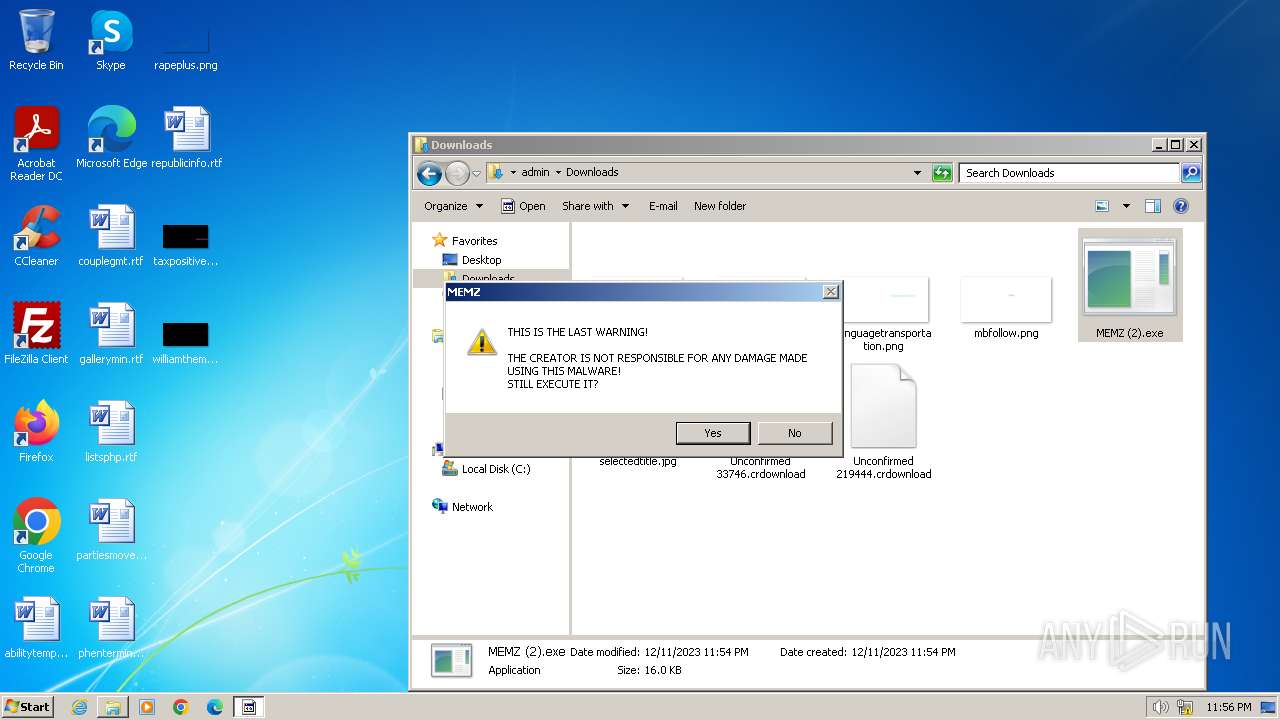
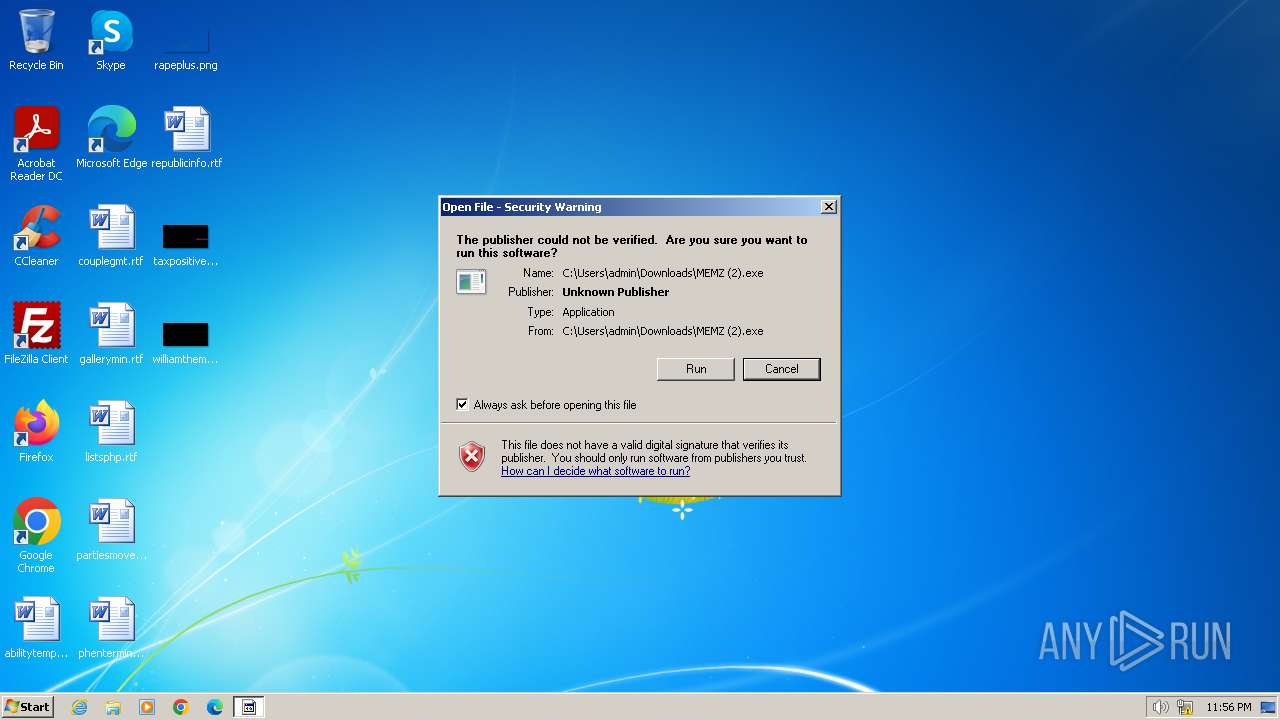
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2023, 23:53:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2088B21DABC0ACDA7736C3179B24AACA |
| SHA1: | 0DBD22894FEBDC39040D5DC7B93E1B045F5436C9 |
| SHA256: | DBEC3D4DDEC21F785D006F842C0F83FA31B8E08444A2A3A034352FB63F117A7D |
| SSDEEP: | 3:N8tEd1YMzcyERkL4A:2uwFys2 |
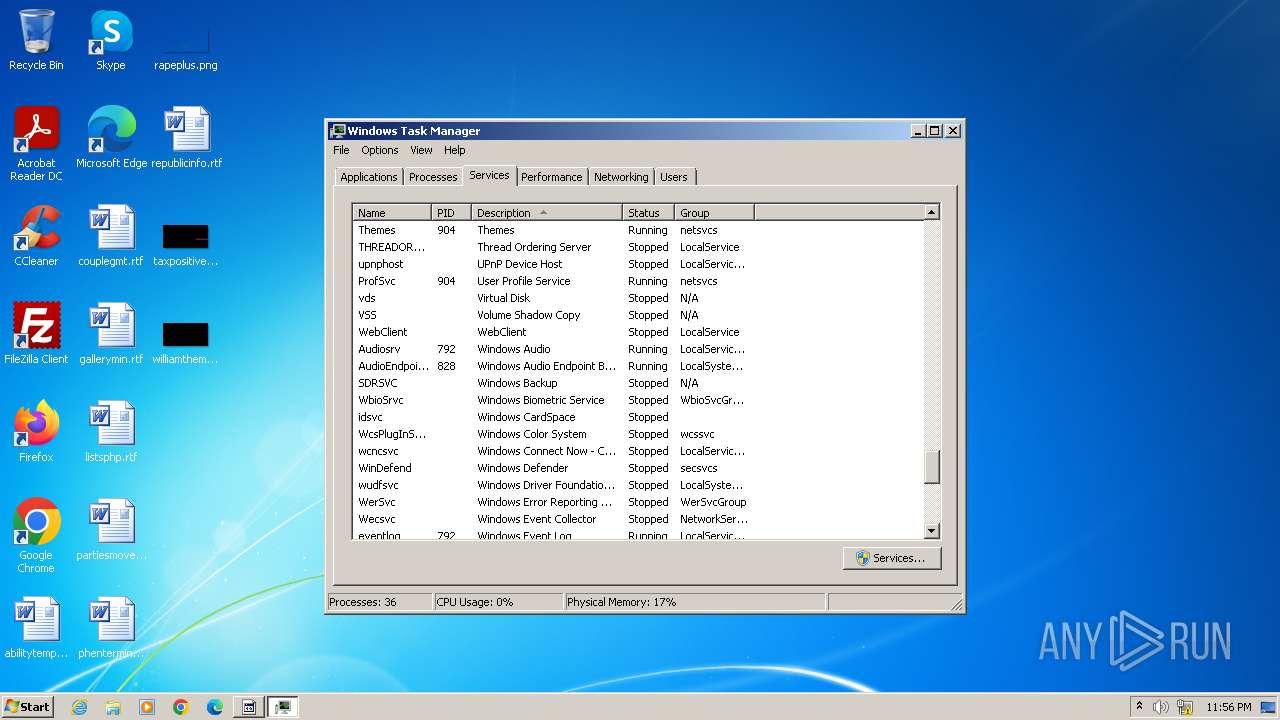
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- MEMZ (2).exe (PID: 2968)
- runonce.exe (PID: 352)
- sipnotify.exe (PID: 1656)
- MEMZ (2).exe (PID: 2960)
Reads security settings of Internet Explorer
- MEMZ (2).exe (PID: 2968)
- MEMZ (2).exe (PID: 2960)
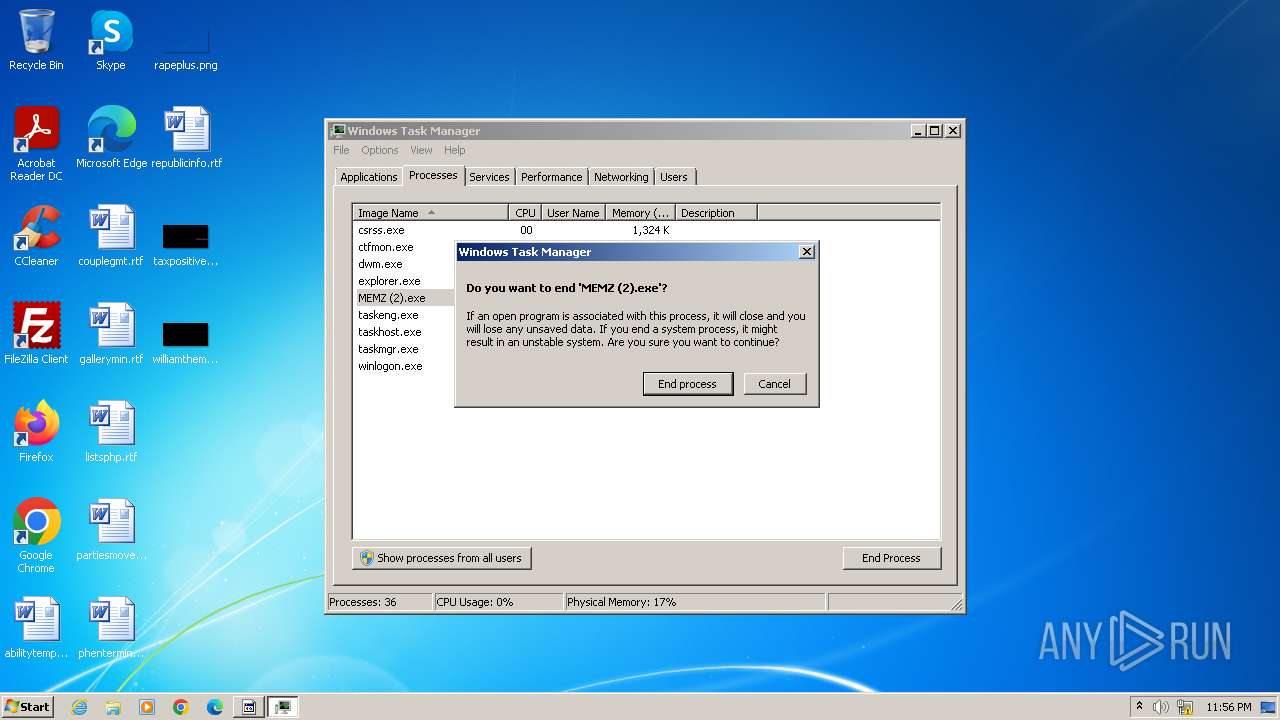
Application launched itself
- MEMZ (2).exe (PID: 2968)
- WerFault.exe (PID: 148)
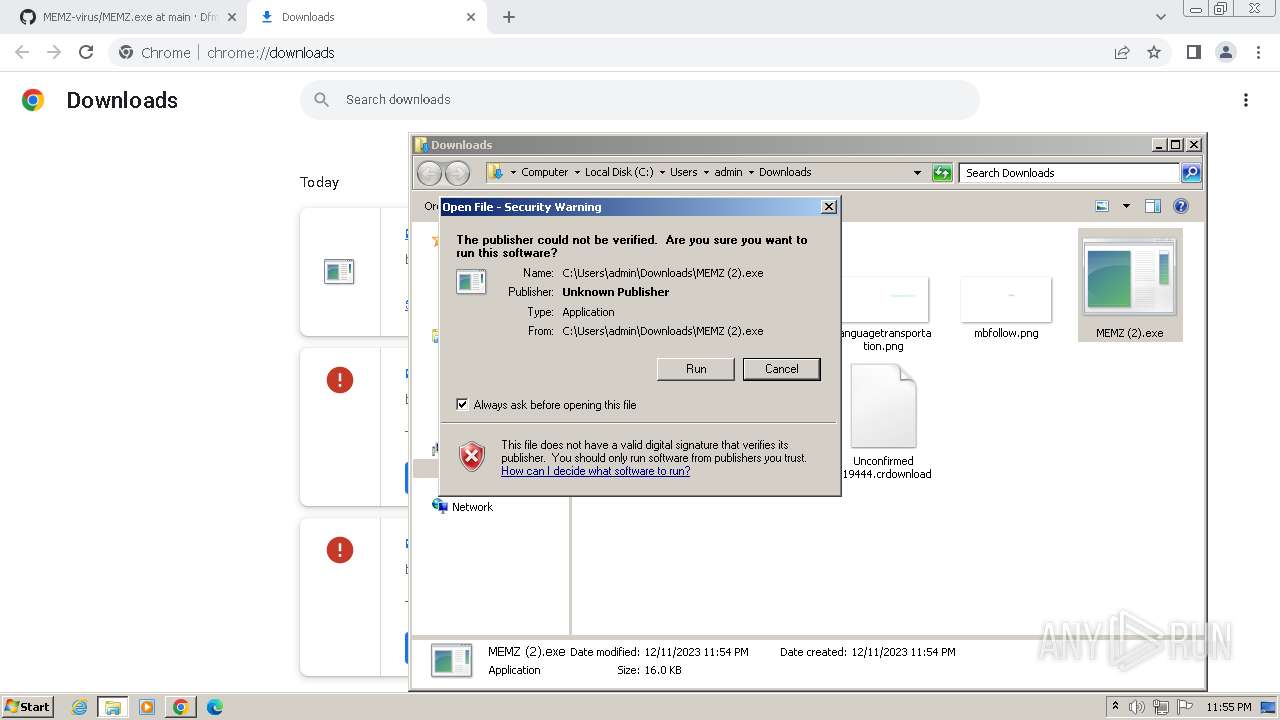
Checks Windows Trust Settings
- MEMZ (2).exe (PID: 2968)
- MEMZ (2).exe (PID: 2960)
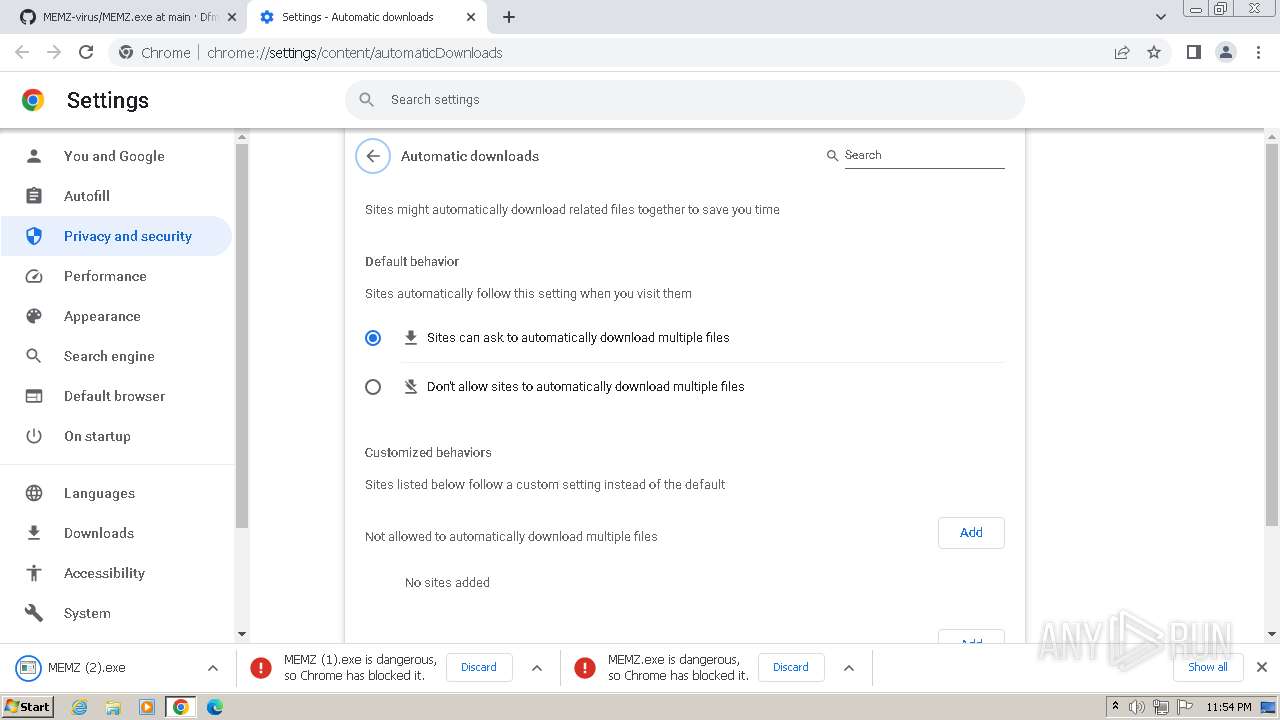
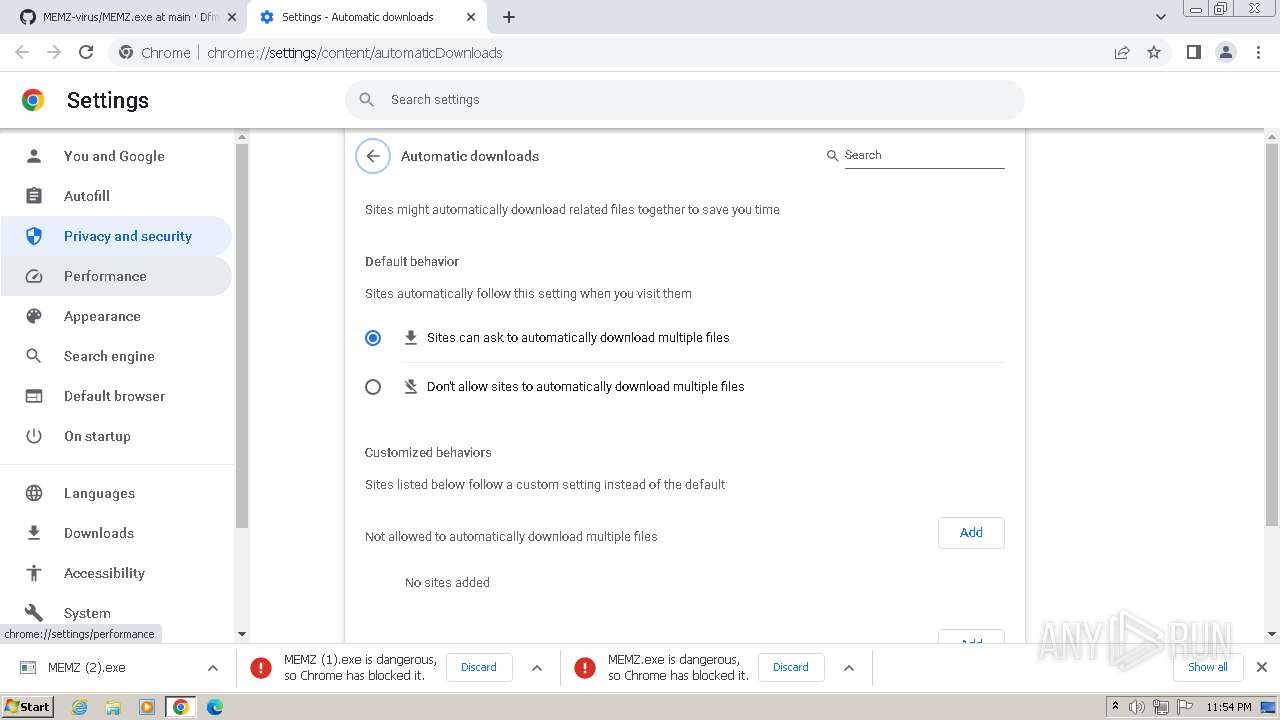
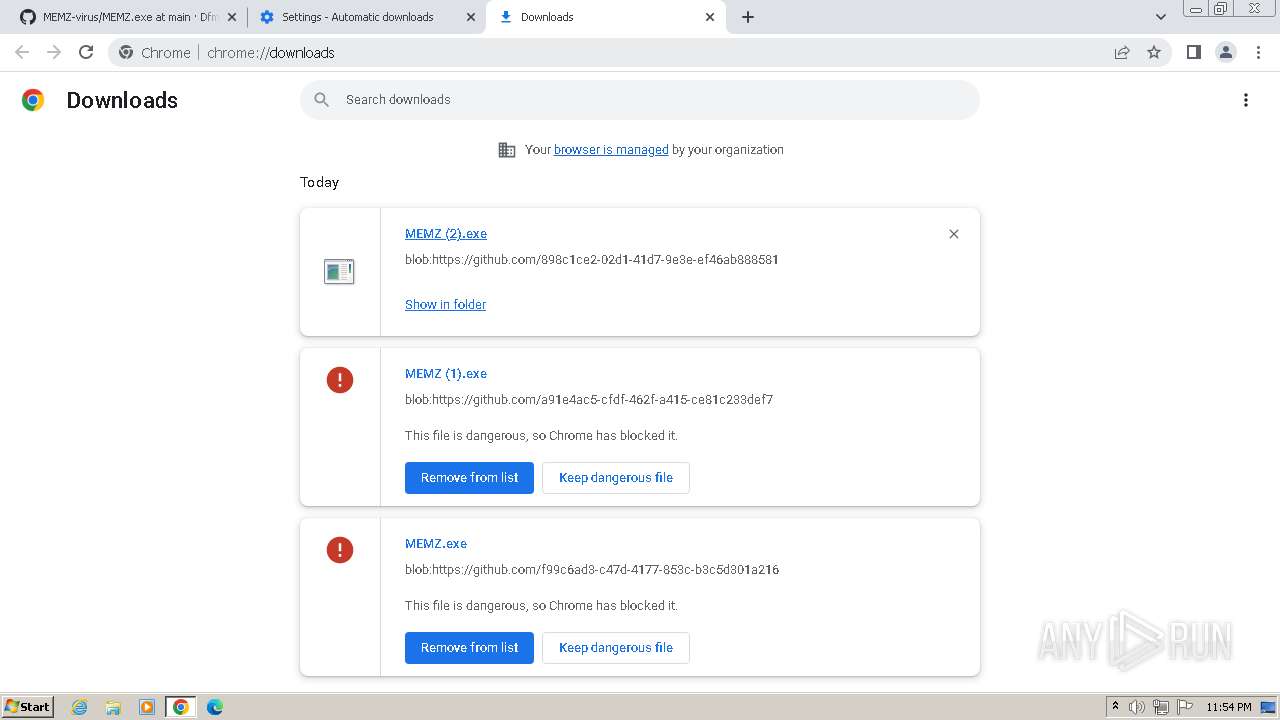
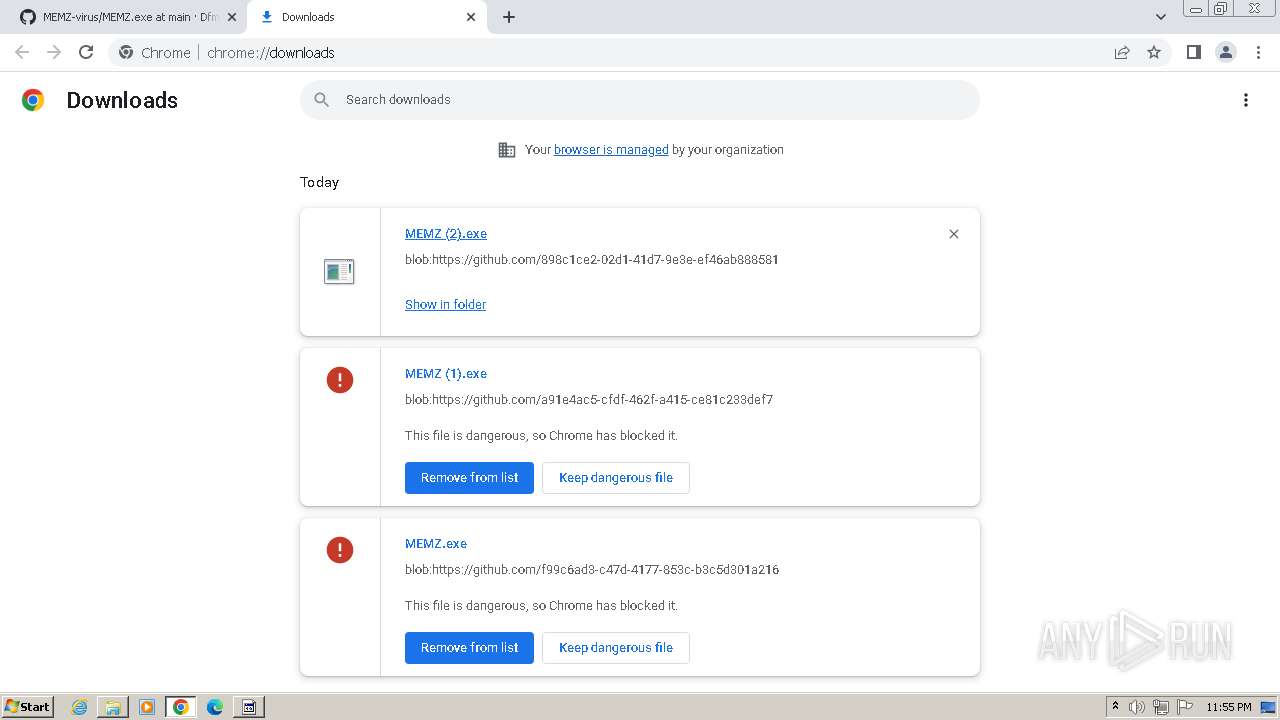
Process drops legitimate windows executable
- chrome.exe (PID: 3264)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1572)
- sipnotify.exe (PID: 1656)
Reads settings of System Certificates
- sipnotify.exe (PID: 1656)
INFO
Application launched itself
- chrome.exe (PID: 3264)
The process uses the downloaded file
- MEMZ (2).exe (PID: 2968)
- chrome.exe (PID: 3260)
- MEMZ (2).exe (PID: 2960)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 1436)
Reads the machine GUID from the registry
- MEMZ (2).exe (PID: 2968)
- MEMZ (2).exe (PID: 3496)
- MEMZ (2).exe (PID: 1760)
- MEMZ (2).exe (PID: 3492)
- MEMZ (2).exe (PID: 1528)
- MEMZ (2).exe (PID: 1868)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2472)
- MEMZ (2).exe (PID: 2960)
- wmpnscfg.exe (PID: 3148)
Checks supported languages
- MEMZ (2).exe (PID: 3496)
- wmpnscfg.exe (PID: 3052)
- MEMZ (2).exe (PID: 1760)
- MEMZ (2).exe (PID: 1868)
- MEMZ (2).exe (PID: 1528)
- MEMZ (2).exe (PID: 3492)
- MEMZ (2).exe (PID: 916)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2472)
- MEMZ (2).exe (PID: 2960)
- MEMZ (2).exe (PID: 2968)
- wmpnscfg.exe (PID: 3148)
Reads the computer name
- wmpnscfg.exe (PID: 3052)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2472)
- MEMZ (2).exe (PID: 2960)
- wmpnscfg.exe (PID: 3148)
- MEMZ (2).exe (PID: 2968)
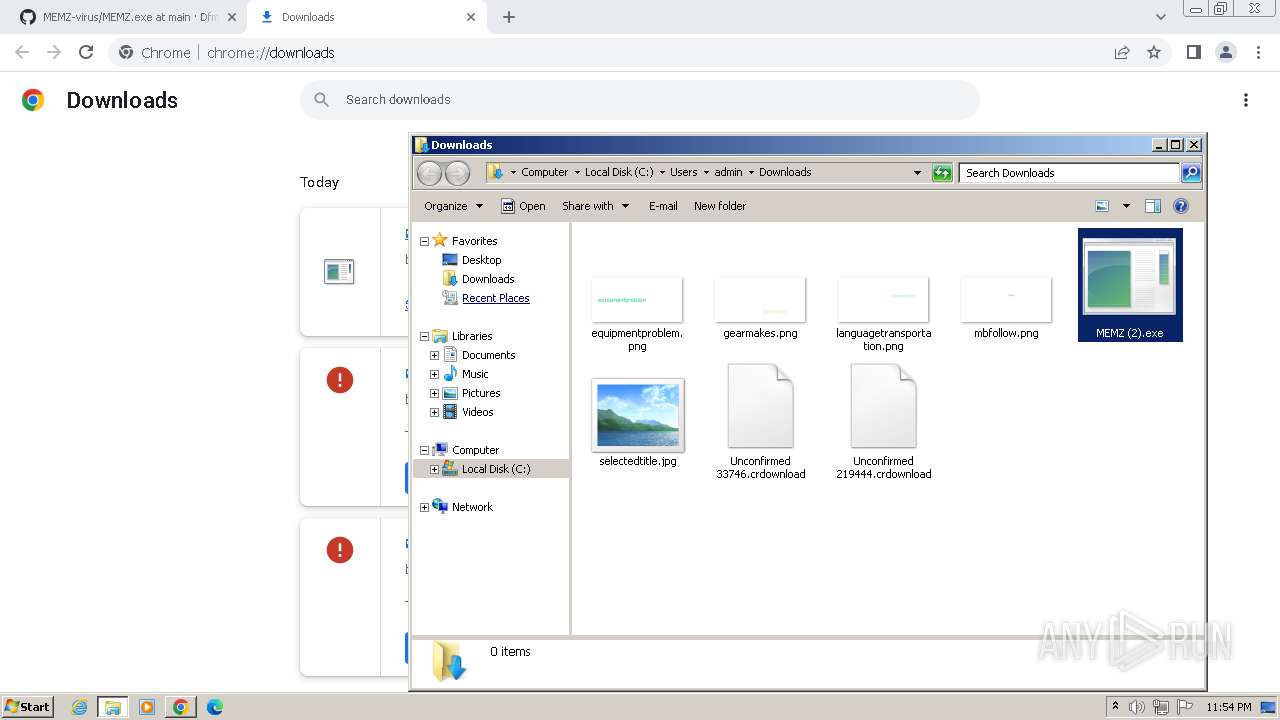
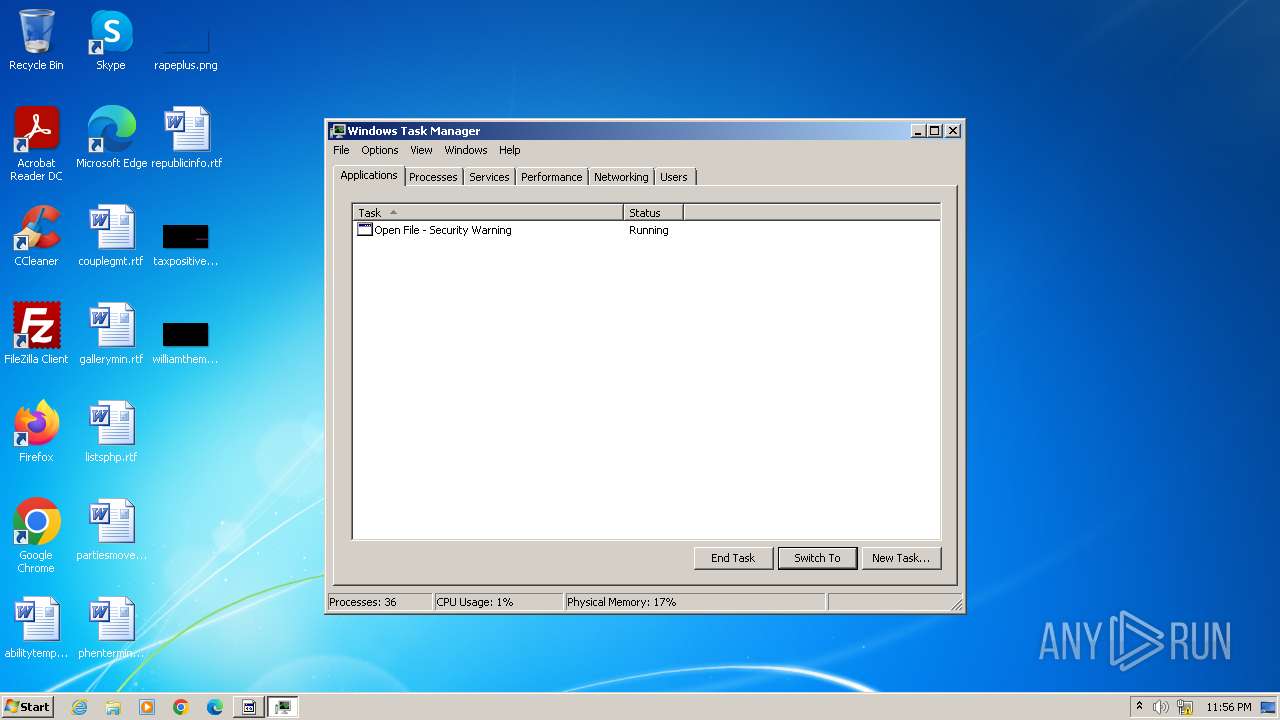
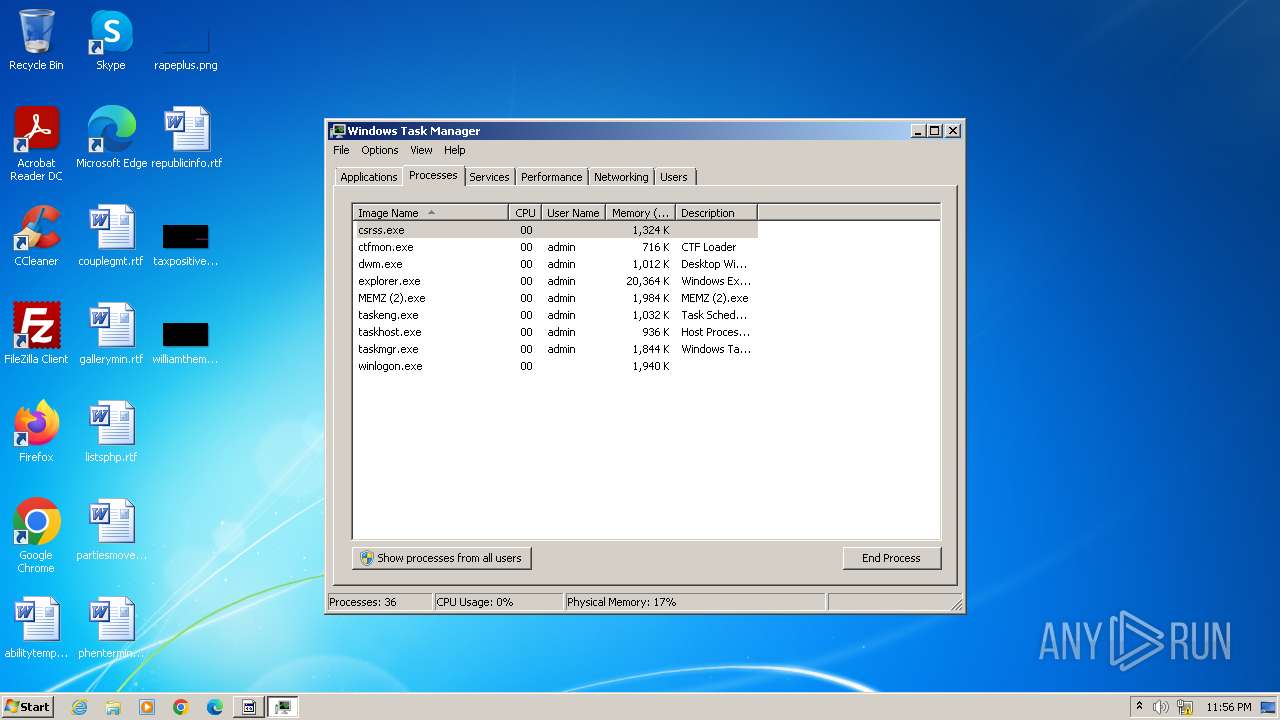
Manual execution by a user
- wmpnscfg.exe (PID: 3052)
- runonce.exe (PID: 352)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2472)
- explorer.exe (PID: 2768)
- MEMZ (2).exe (PID: 2960)
- wmpnscfg.exe (PID: 3148)
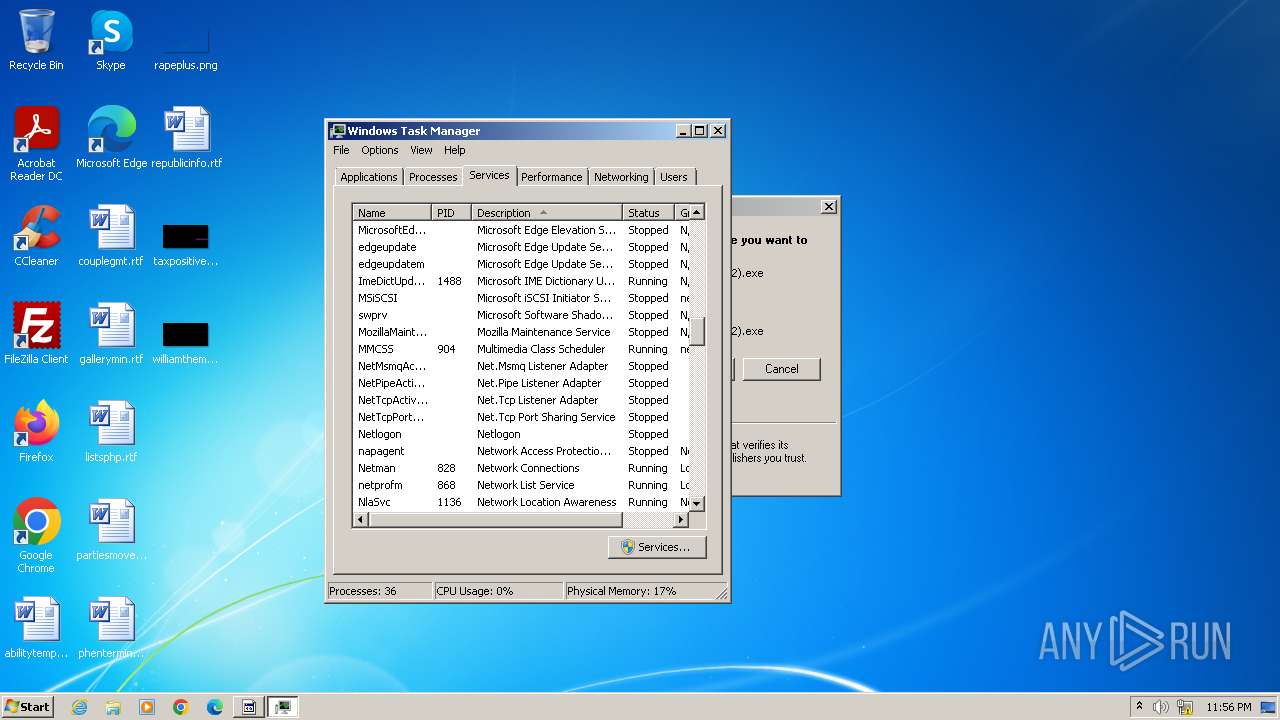
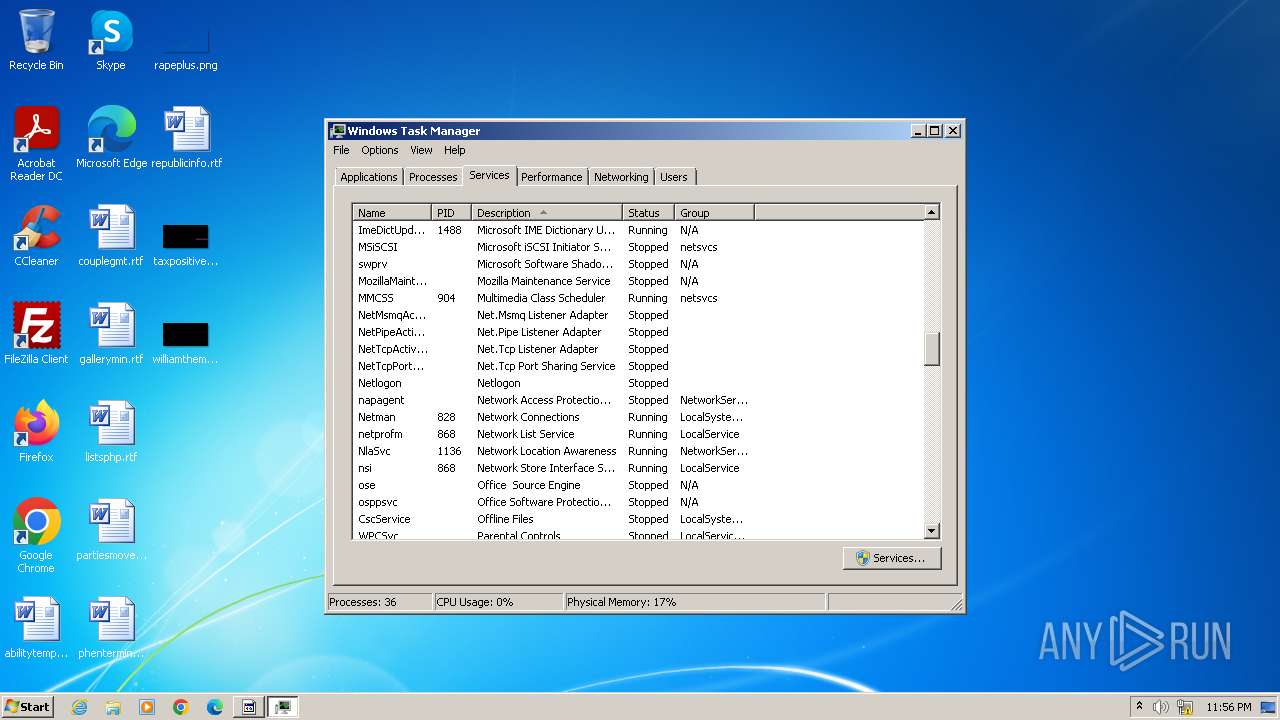
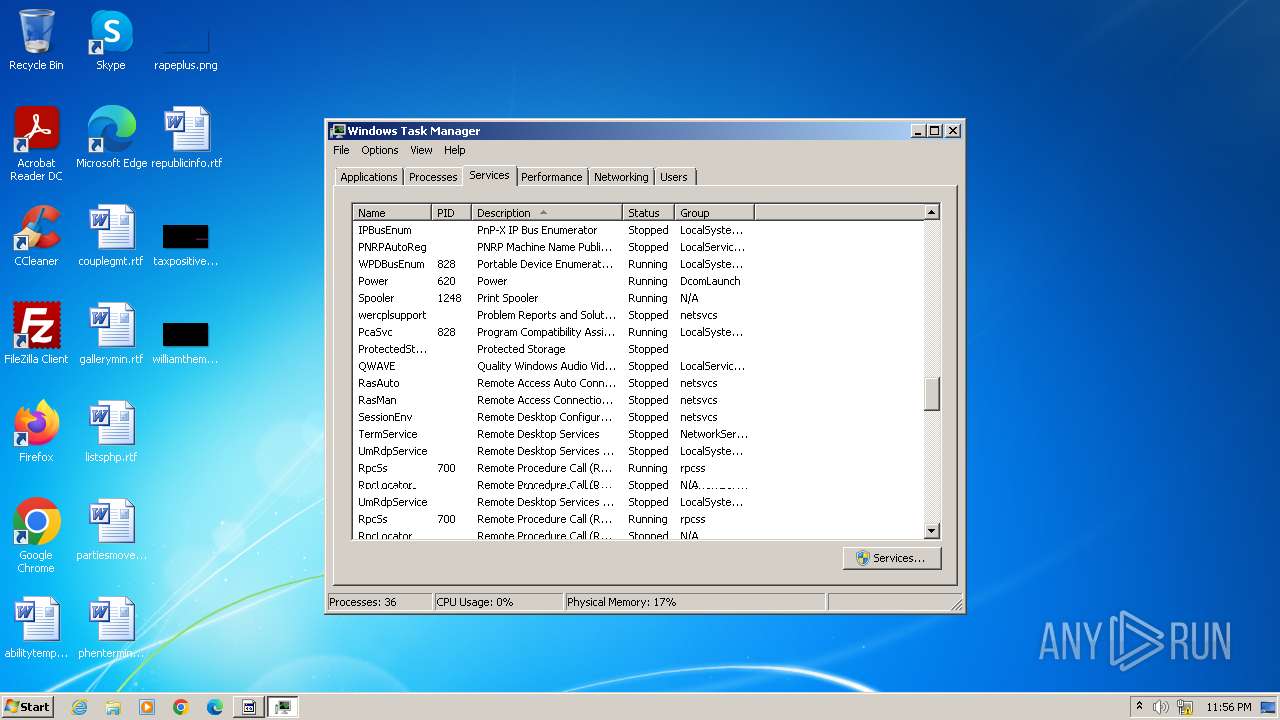
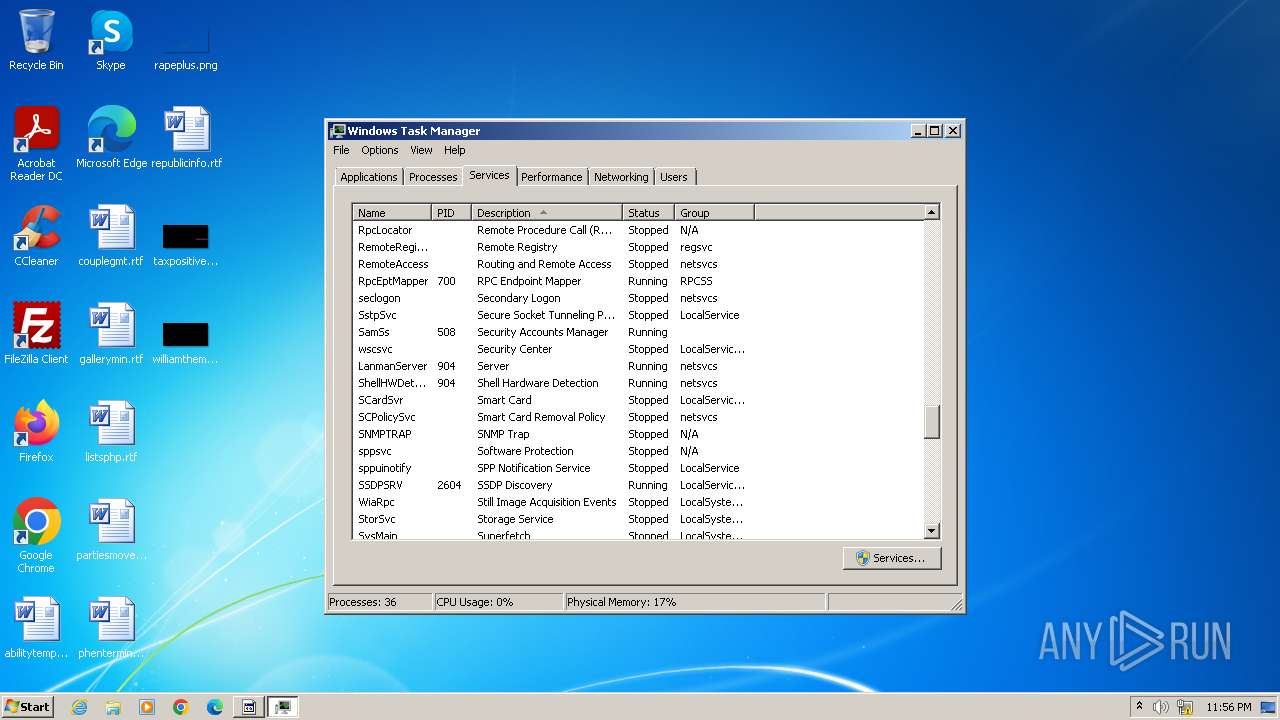
- taskmgr.exe (PID: 3036)
- MEMZ (2).exe (PID: 2968)
Drops the executable file immediately after the start
- chrome.exe (PID: 3264)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1656)
Reads the time zone
- runonce.exe (PID: 352)
Create files in a temporary directory
- WerFault.exe (PID: 1508)
Process checks are UAC notifies on
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
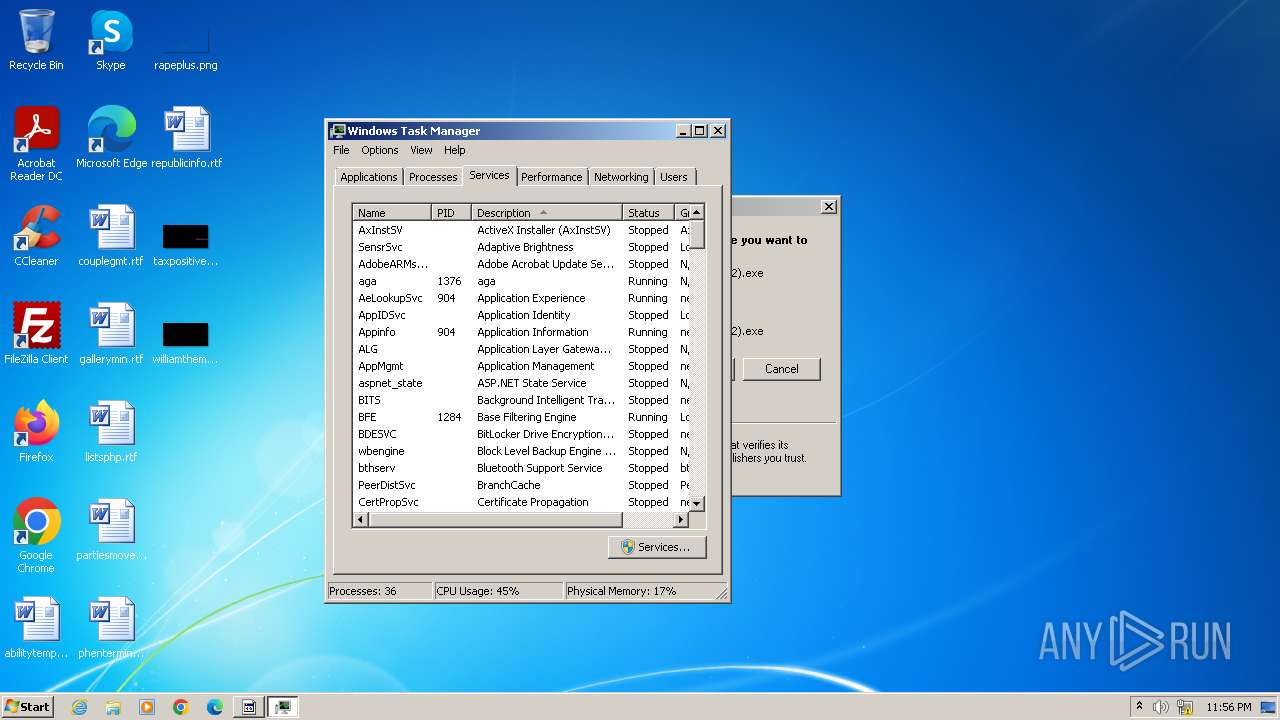
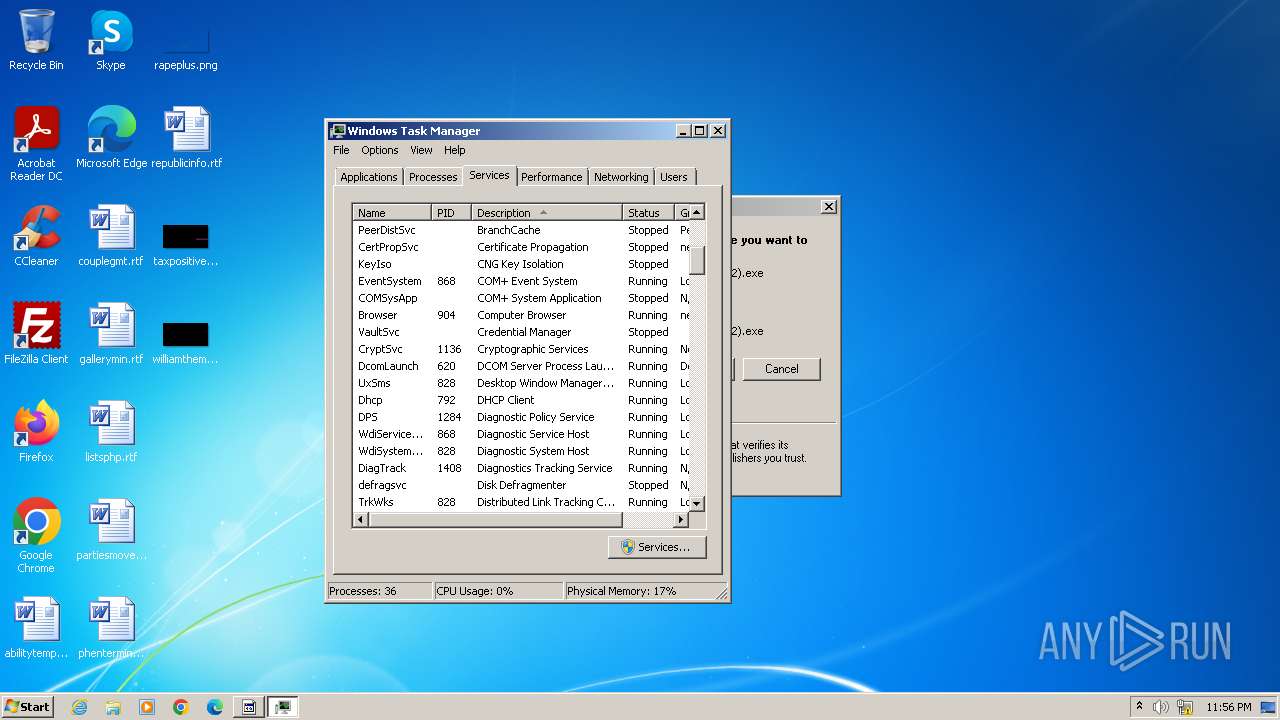
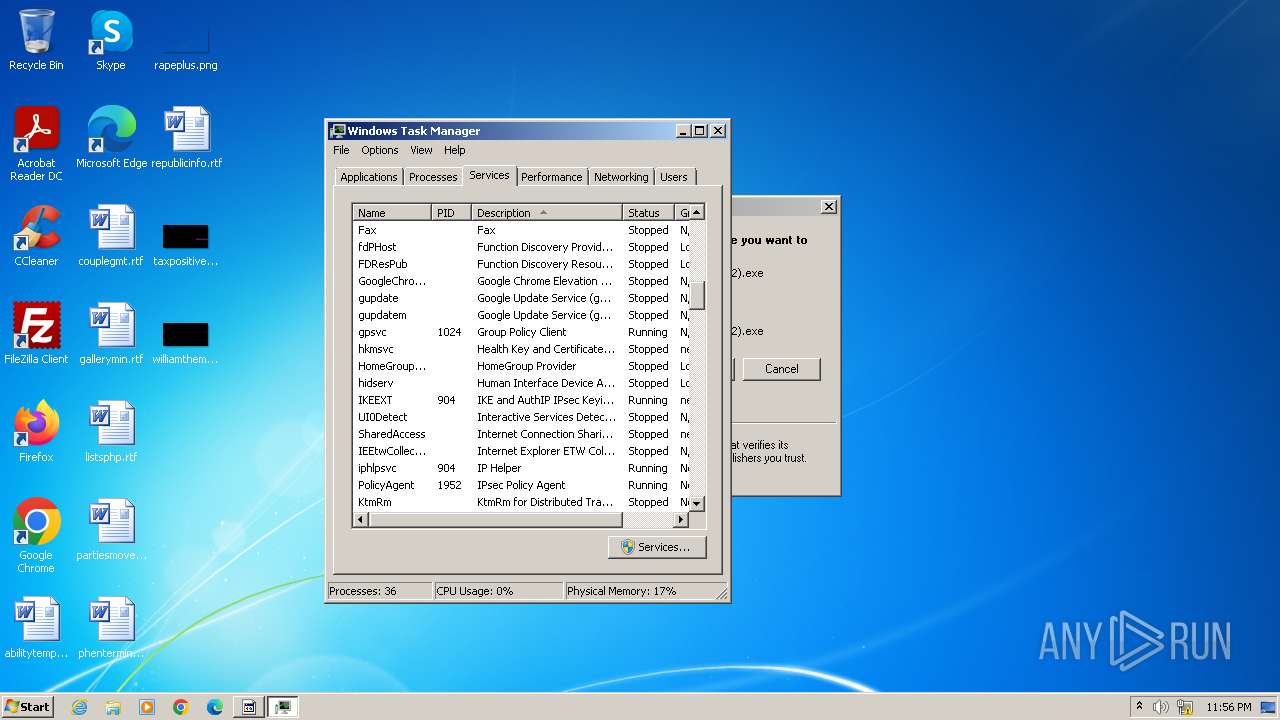
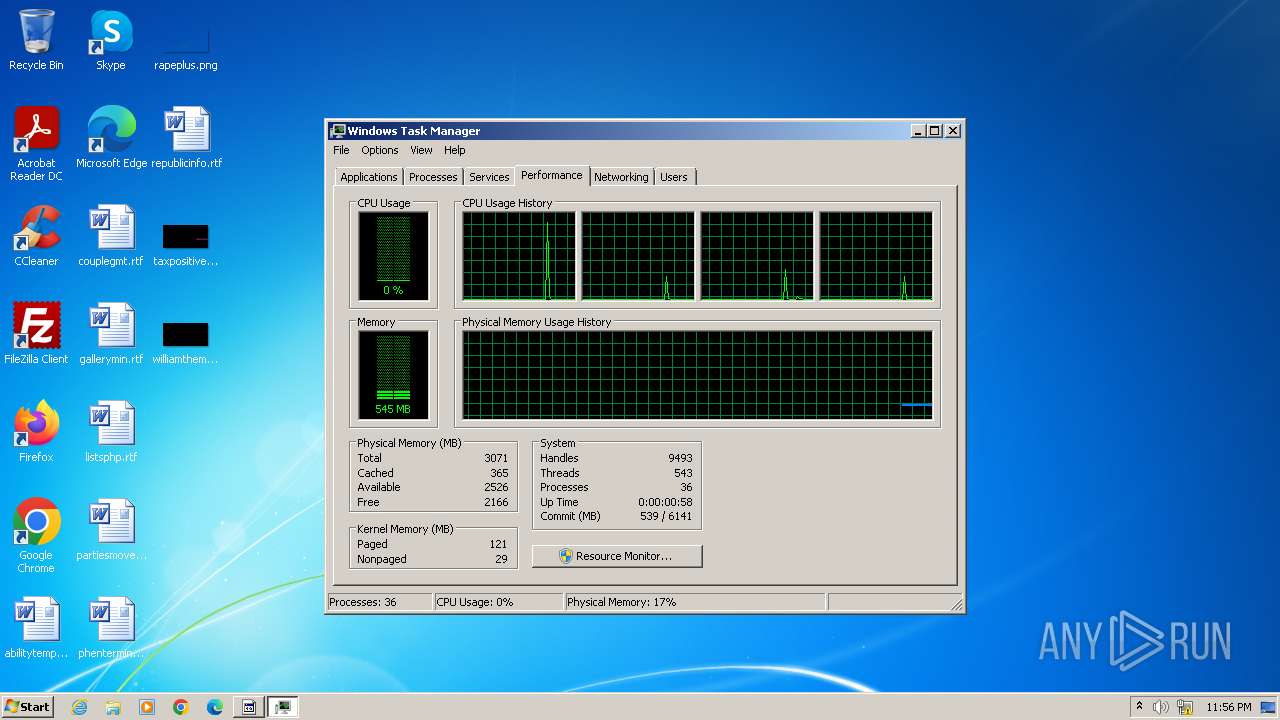
Total processes
132
Monitored processes
50
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Windows\System32\WerFault.exe" -k -rq | C:\Windows\System32\WerFault.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | runonce.exe /Explorer | C:\Windows\System32\runonce.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1460 --field-trial-handle=880,i,16613811320951606024,14007003494206106314,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\Downloads\MEMZ (2).exe" /main | C:\Users\admin\Downloads\MEMZ (2).exe | — | MEMZ (2).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3556 --field-trial-handle=880,i,16613811320951606024,14007003494206106314,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1508 | C:\Windows\System32\WerFault.exe -k -q | C:\Windows\System32\WerFault.exe | — | WerFault.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\Downloads\MEMZ (2).exe" /watchdog | C:\Users\admin\Downloads\MEMZ (2).exe | — | MEMZ (2).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a7a8b38,0x6a7a8b48,0x6a7a8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1572 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
Total events
11 341
Read events
11 172
Write events
151
Delete events
18
Modification events
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
8
Suspicious files
83
Text files
32
Unknown types
2
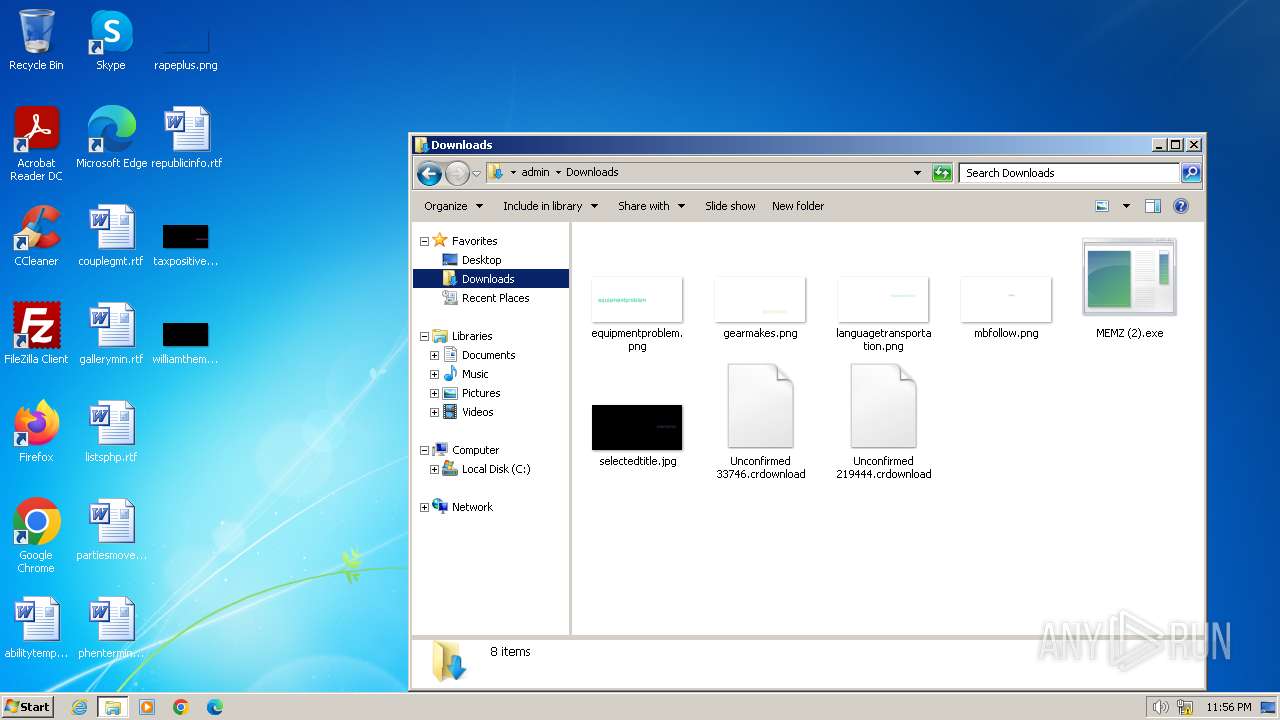
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF20ffd0.TMP | — | |
MD5:— | SHA256:— | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\64718d97-4f1f-4641-8b47-e4fff1dd63e2.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF210138.TMP | text | |
MD5:8268A4D53A6A9432A8266584CBD7D624 | SHA256:F785C42945CFE320C52C763837CD41541A8CAAB3E5FD567999EED5343CF0FD7A | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF210677.TMP | — | |
MD5:— | SHA256:— | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:43550DBA2277BE44F5F842196E084145 | SHA256:D19055342C06316F8B80D0B029BD233A3E48AD4C591953AF7B712ADA7F68F403 | |||
| 3264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF20ffc1.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
42
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 8.13 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 8.13 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 17.7 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 81.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.6 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.07 Mb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 166 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 335 Kb | unknown |
1656 | sipnotify.exe | HEAD | 200 | 23.212.215.38:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133468125505150000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2532 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3264 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2532 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2532 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | unknown |
2532 | chrome.exe | 142.250.186.42:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
2532 | chrome.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |