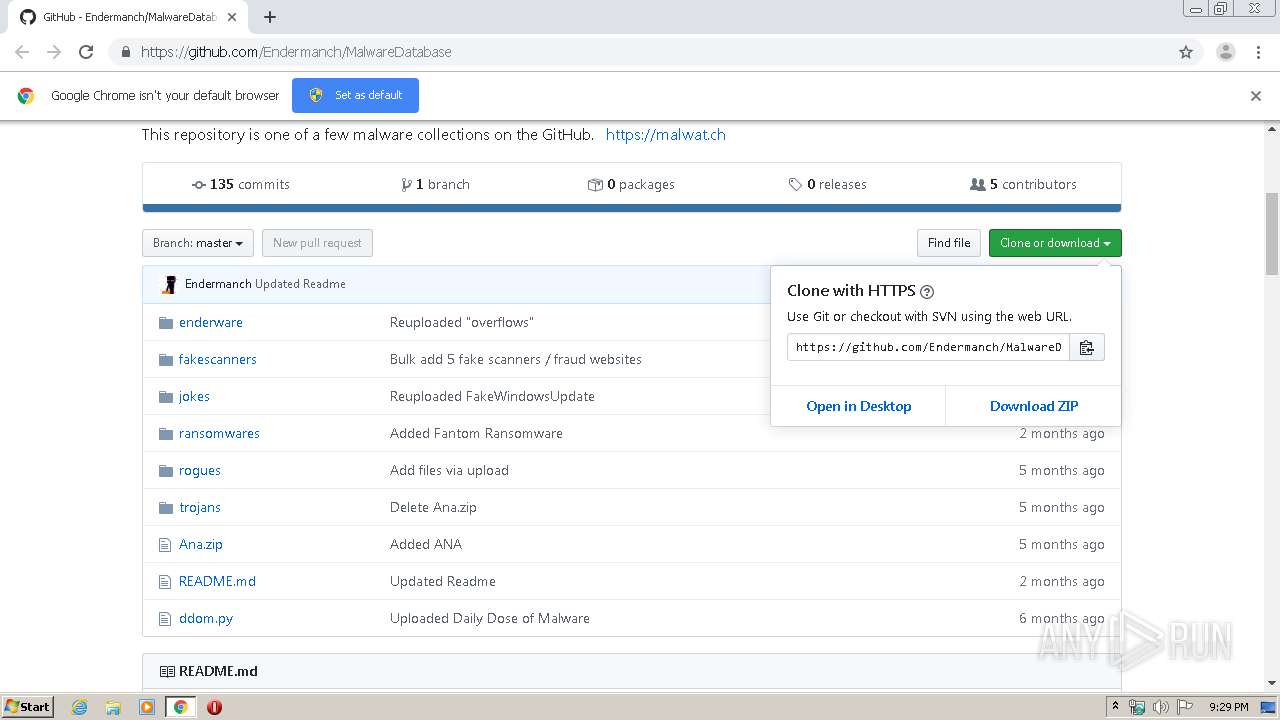
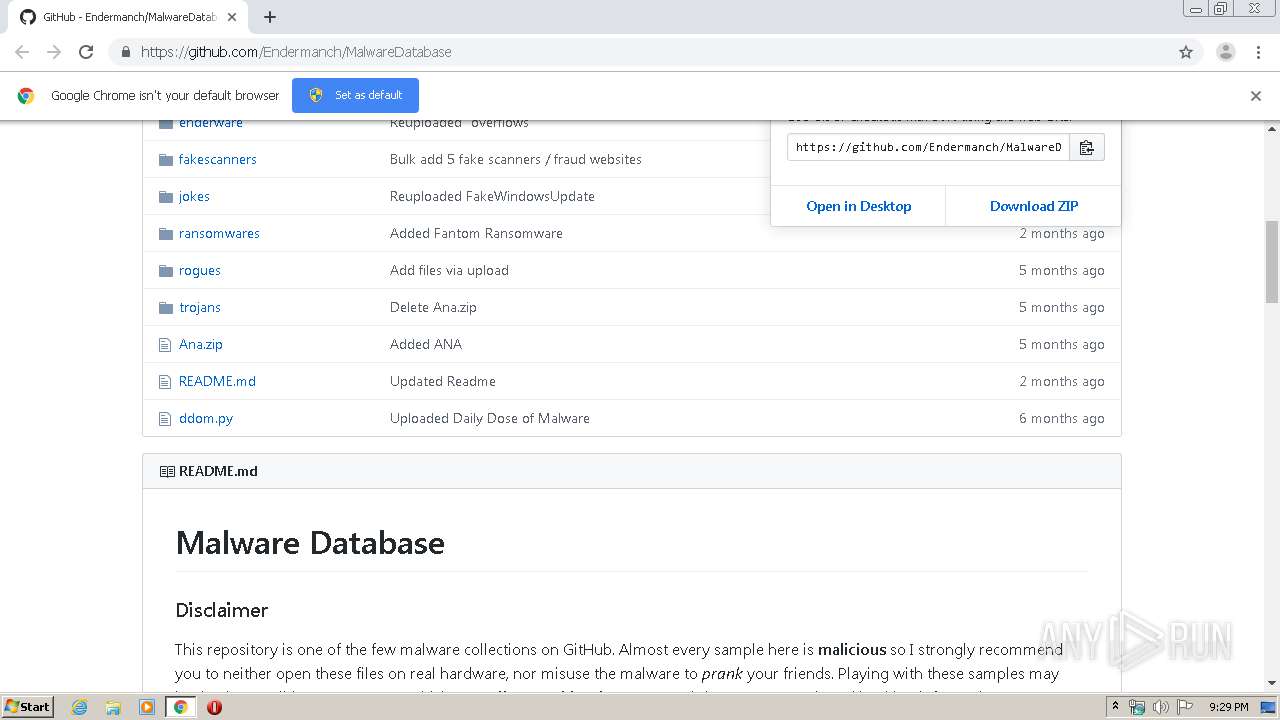
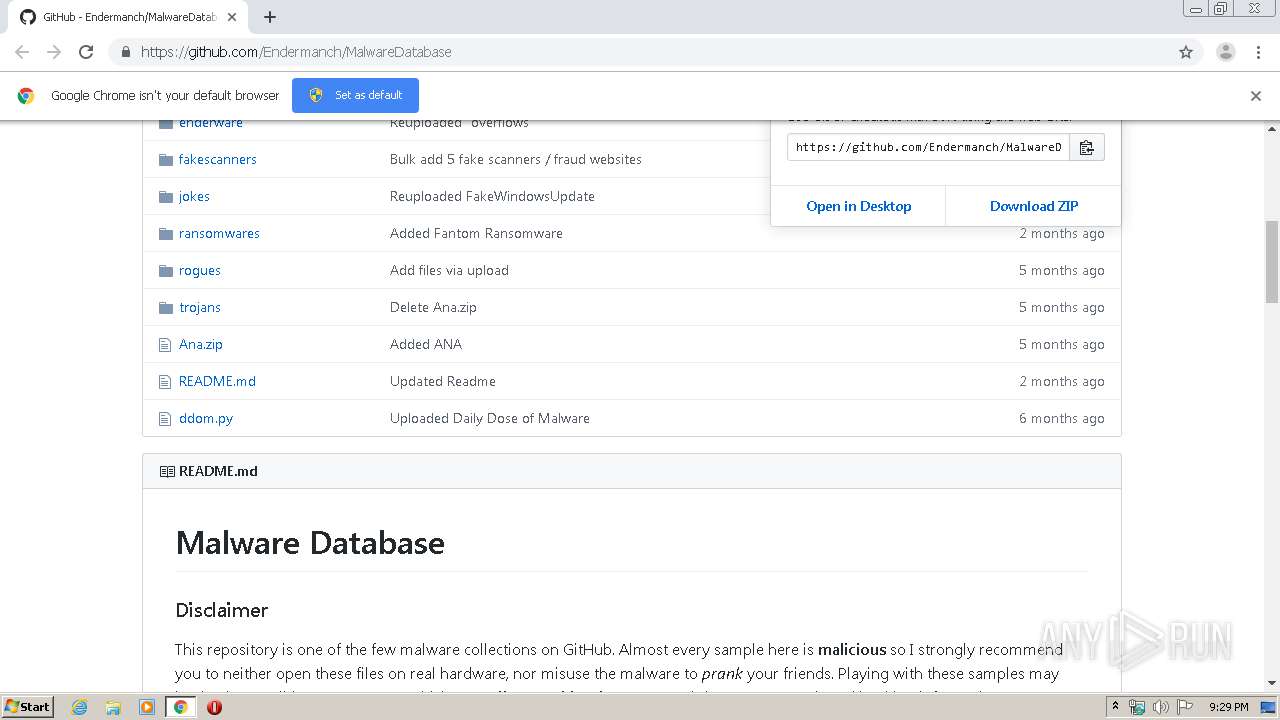
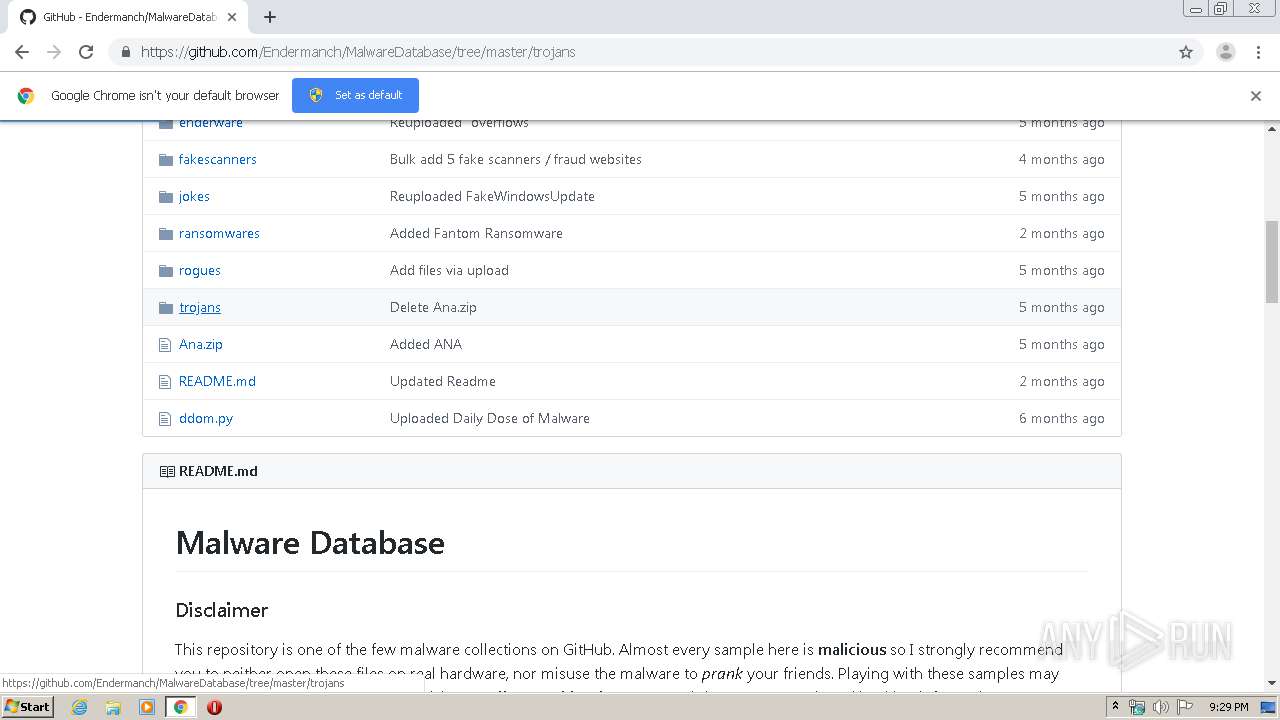
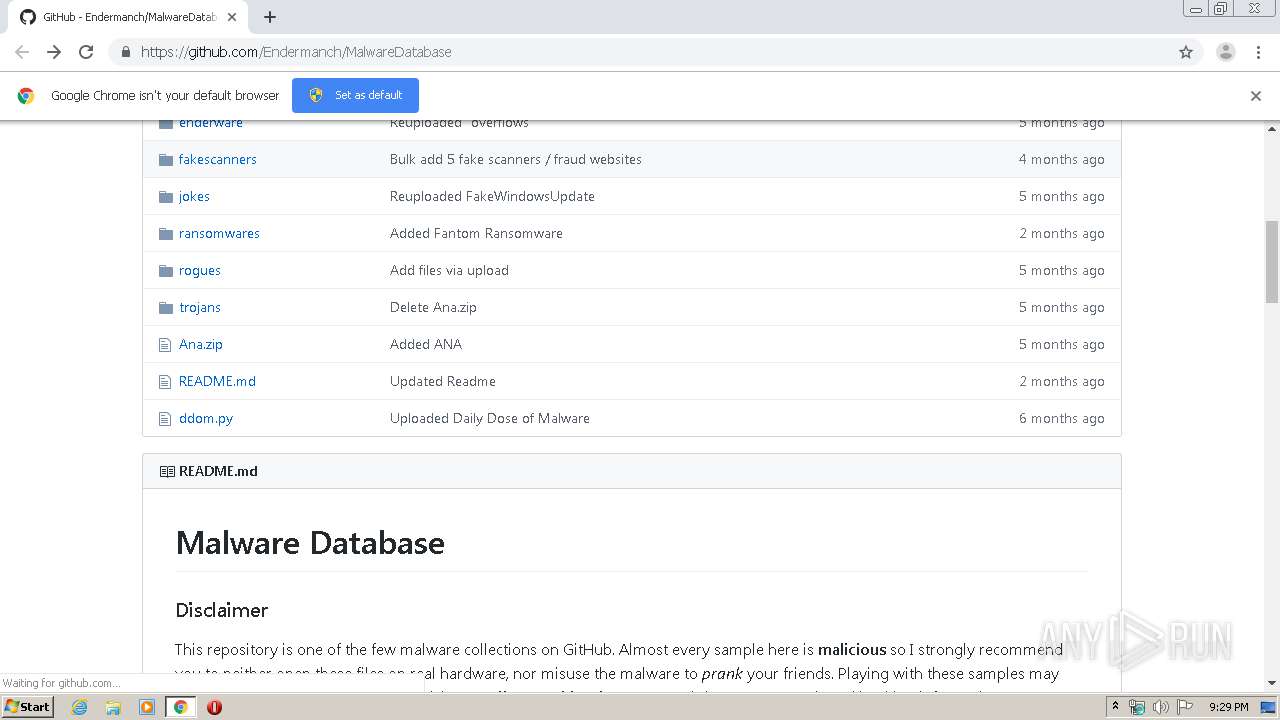
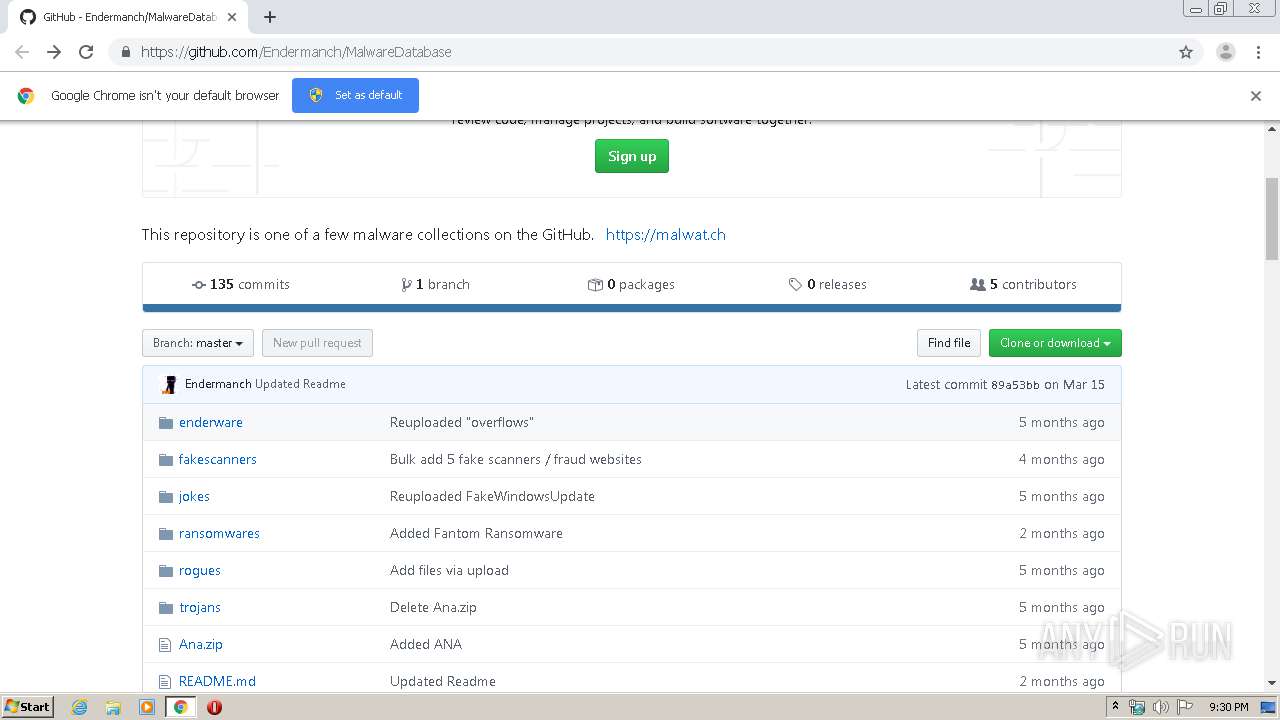
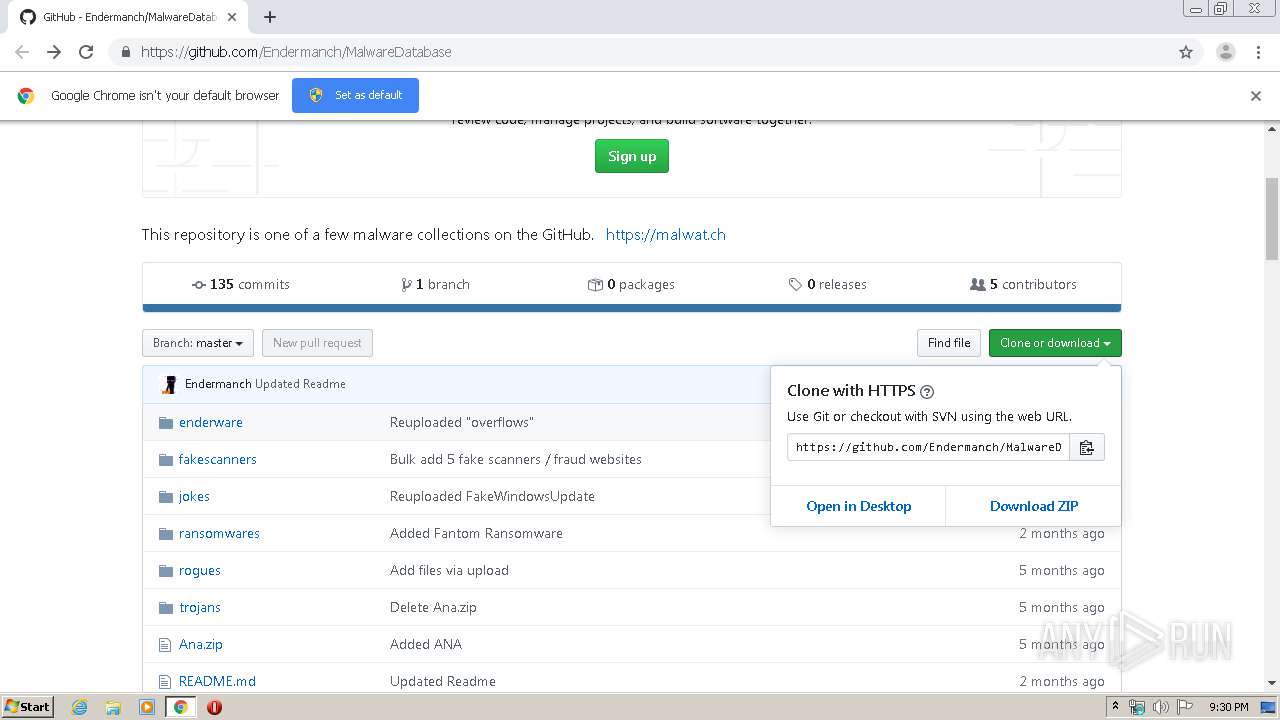
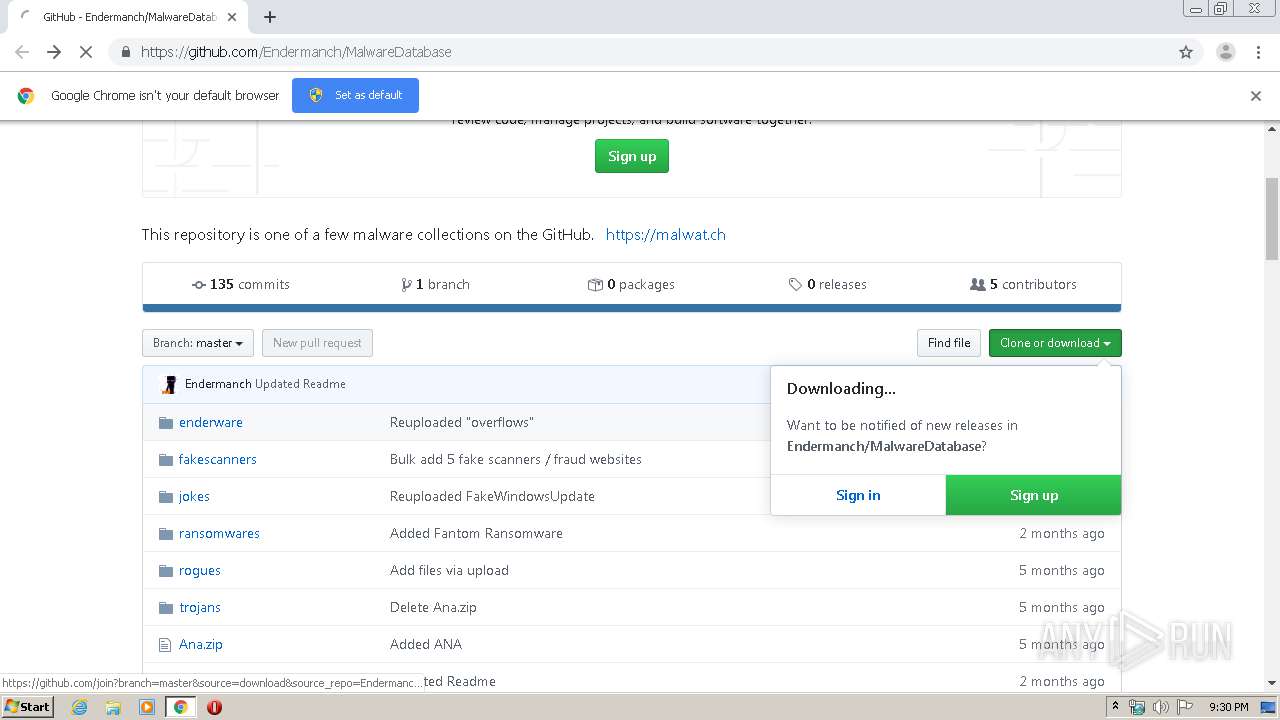
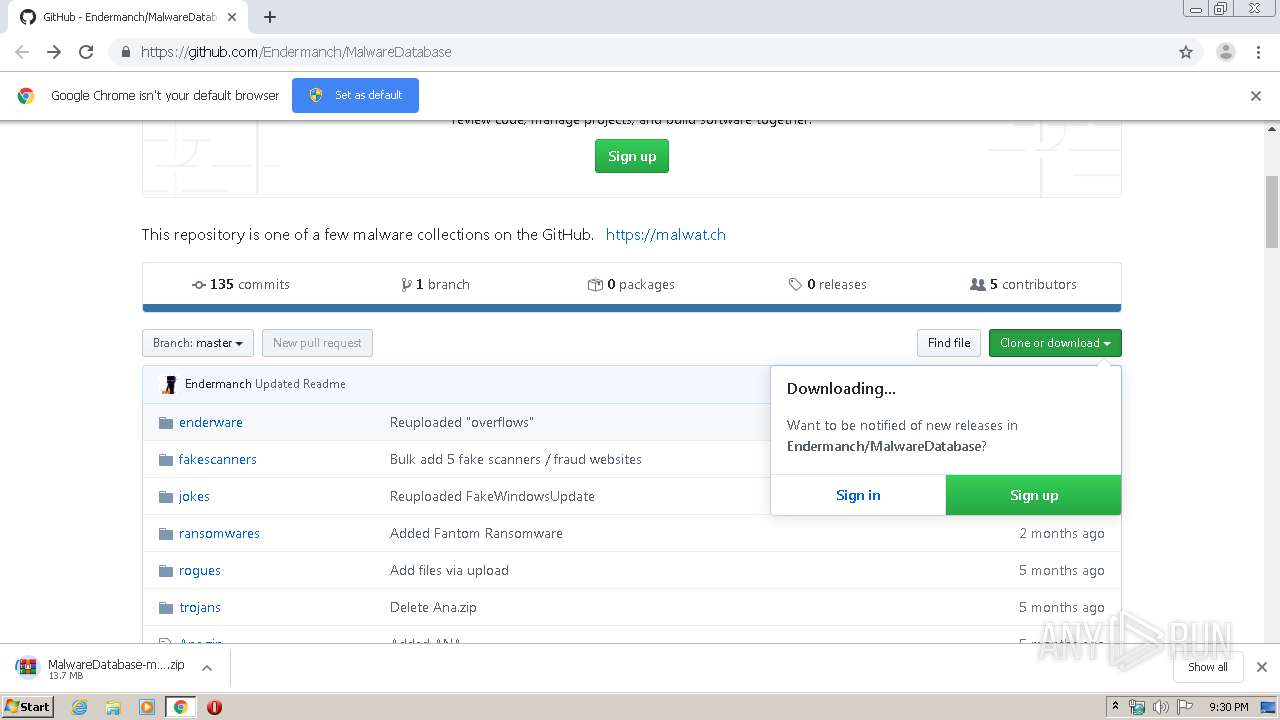
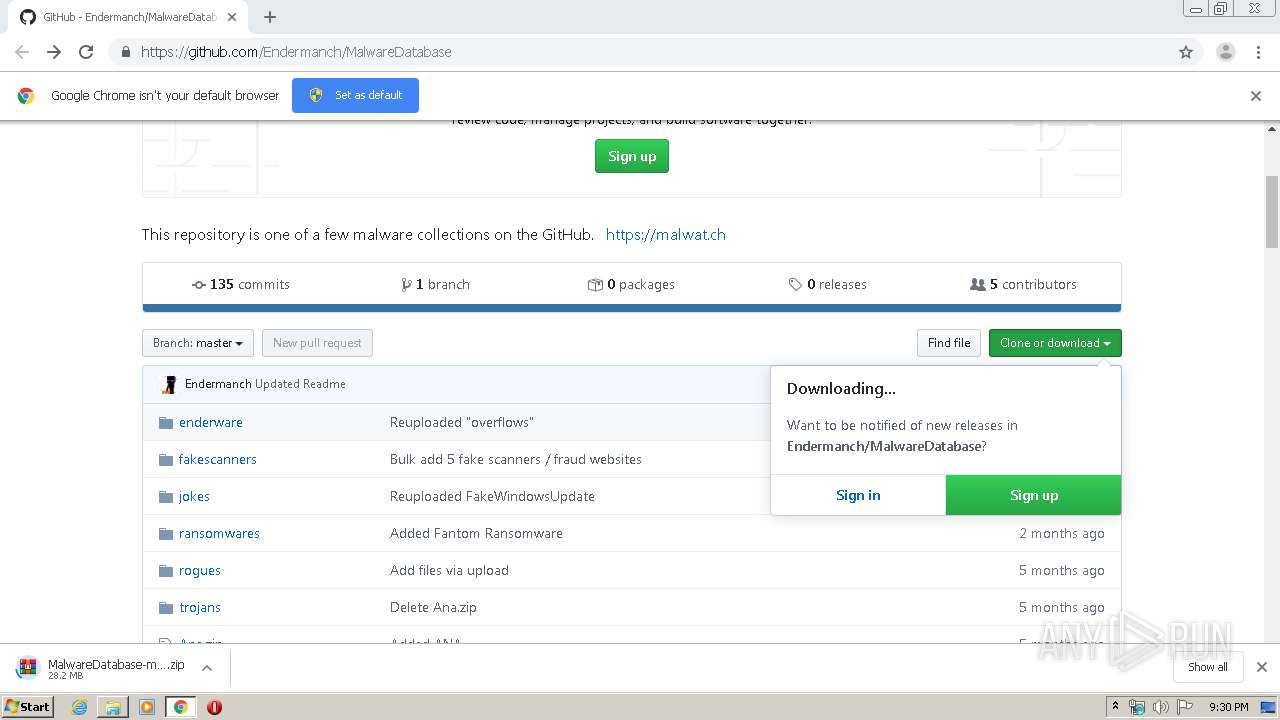
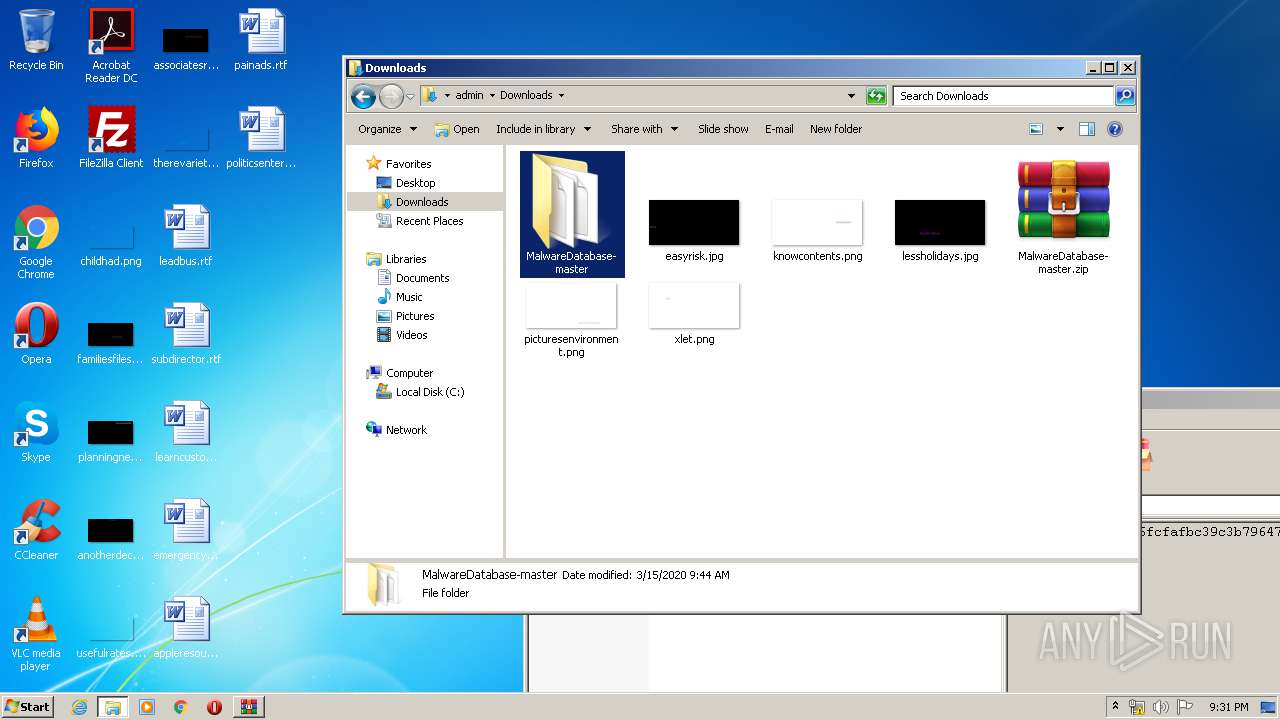
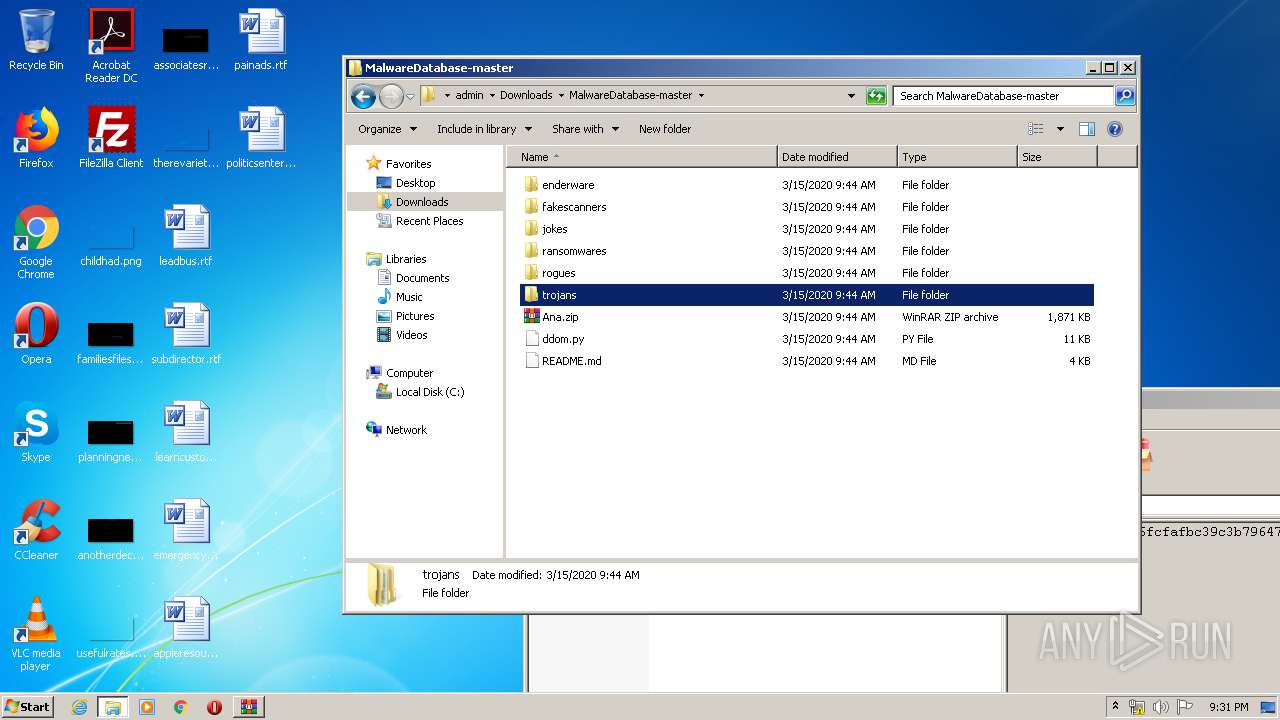
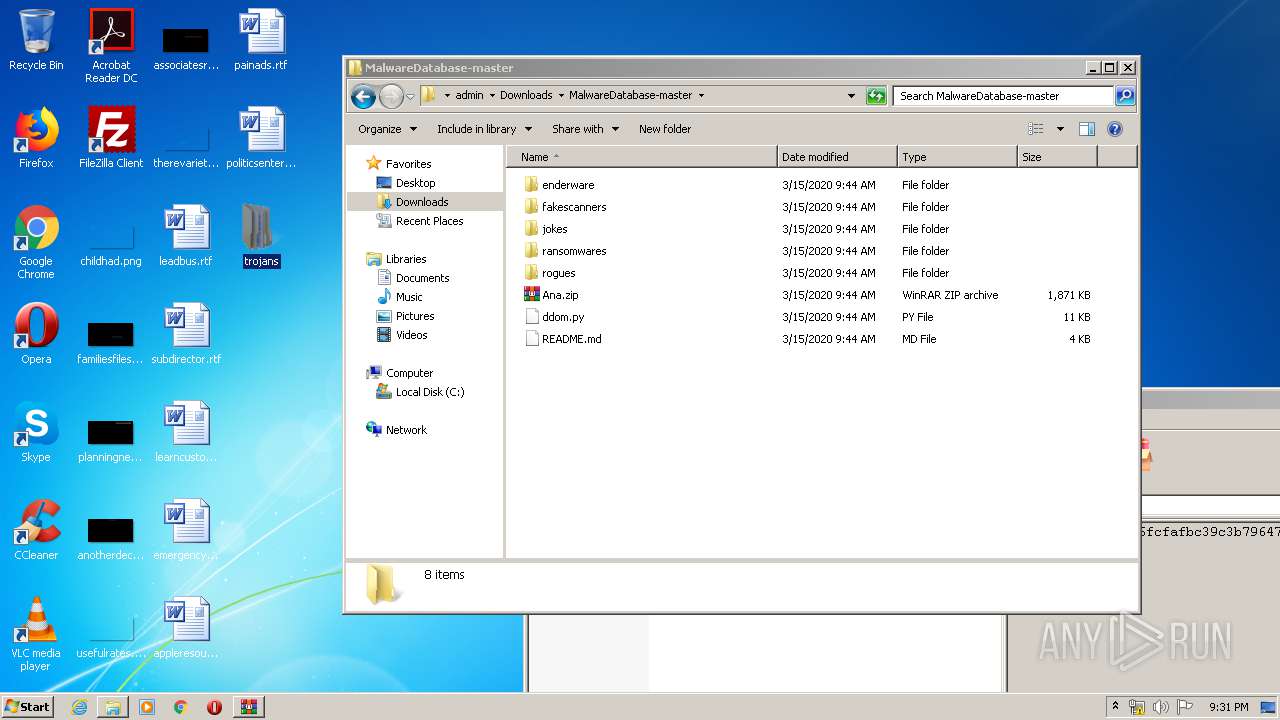
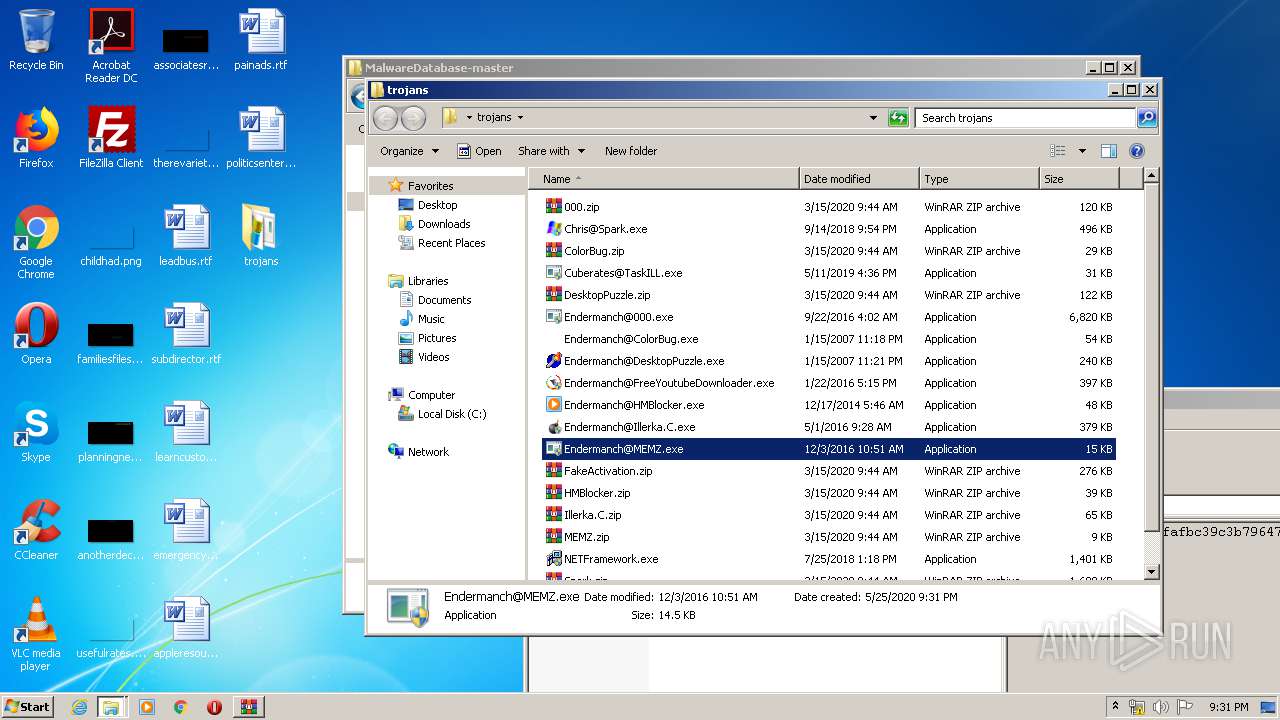
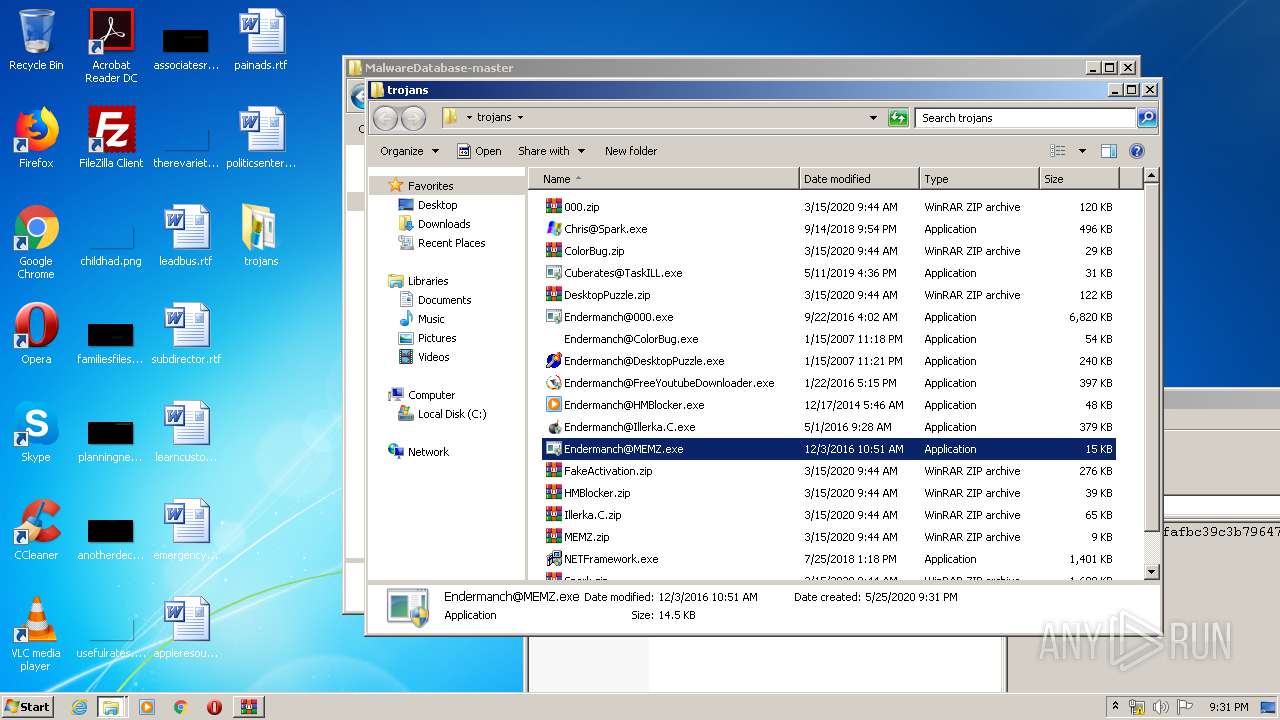
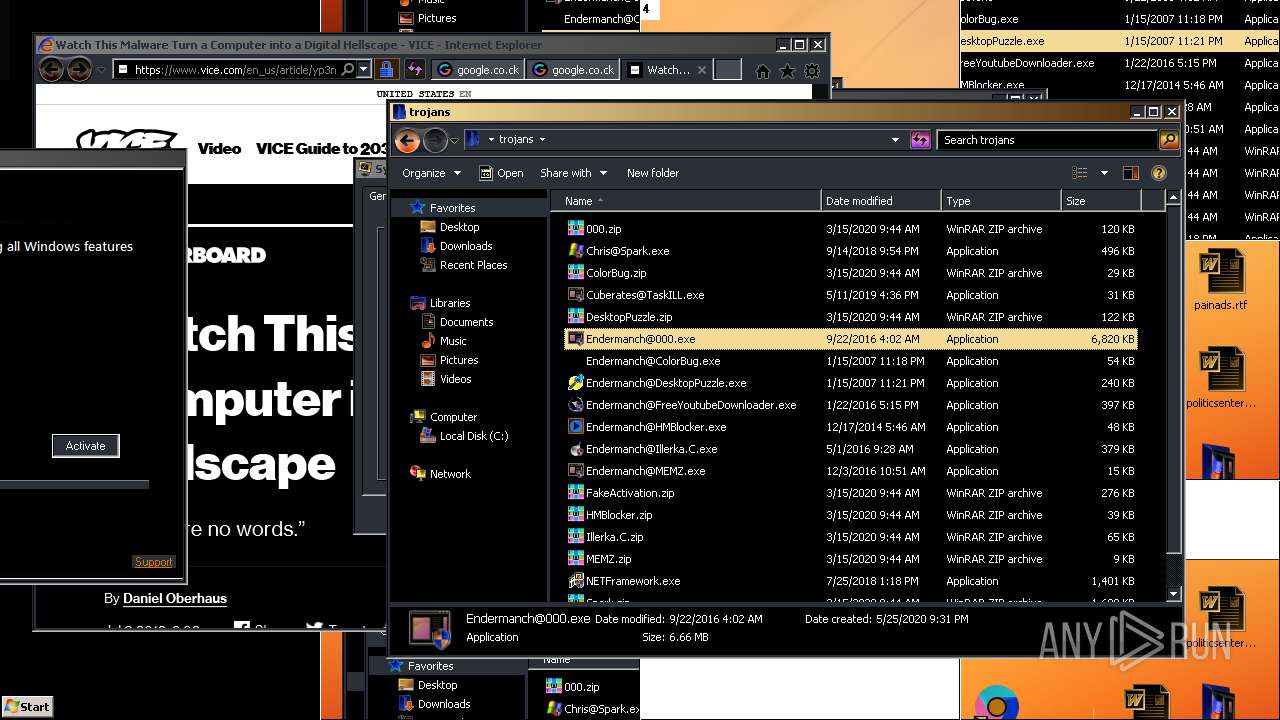
| URL: | https://github.com/Endermanch/MalwareDatabase |
| Full analysis: | https://app.any.run/tasks/e45f2859-92c5-4173-b486-e097c8fb5cd6 |
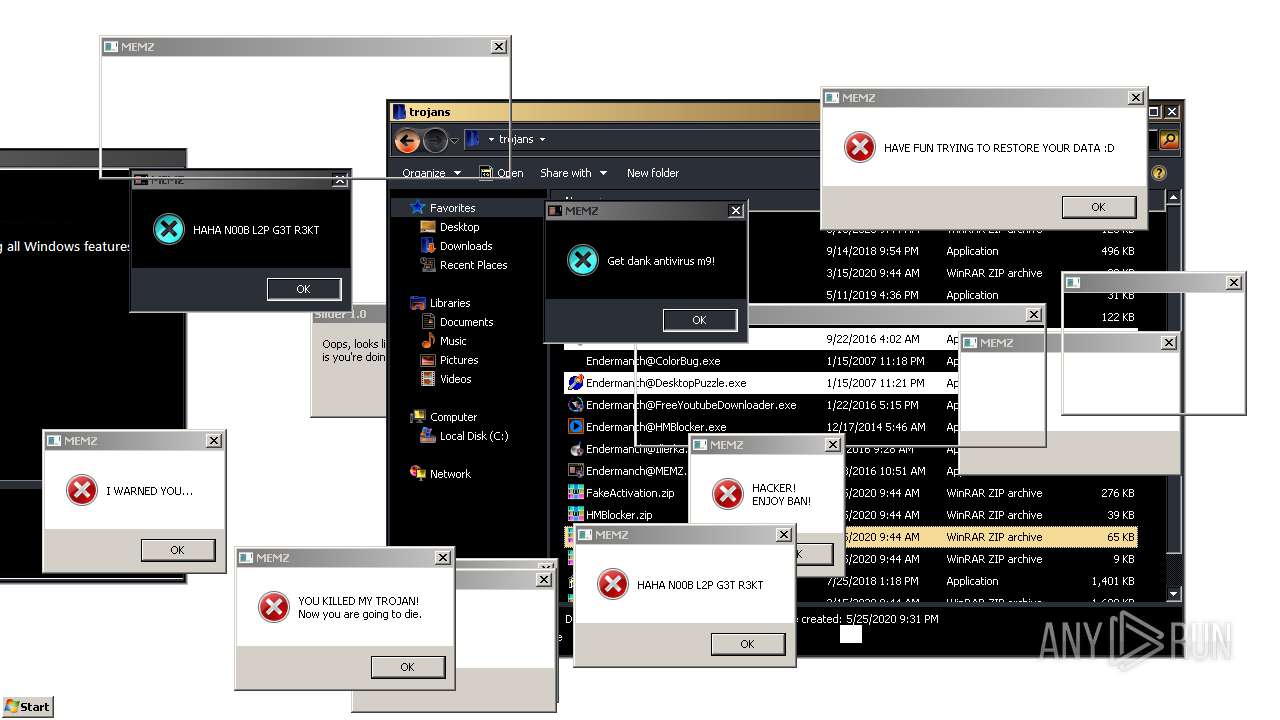
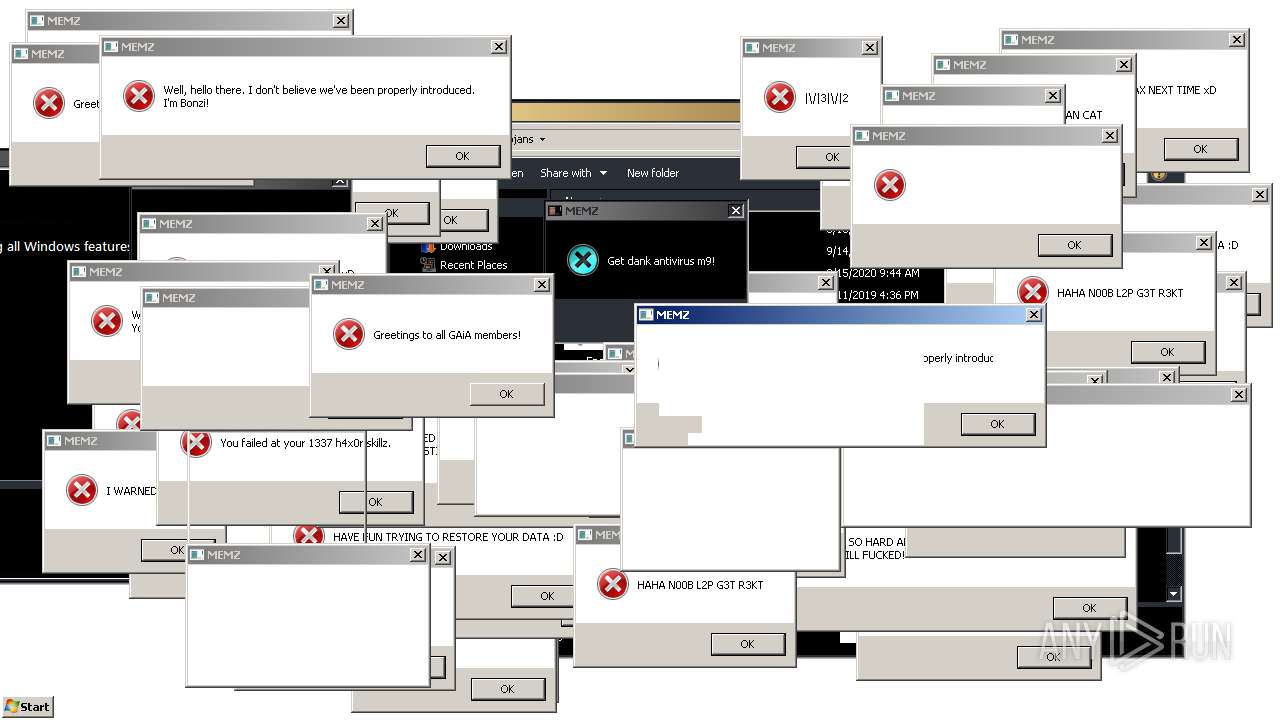
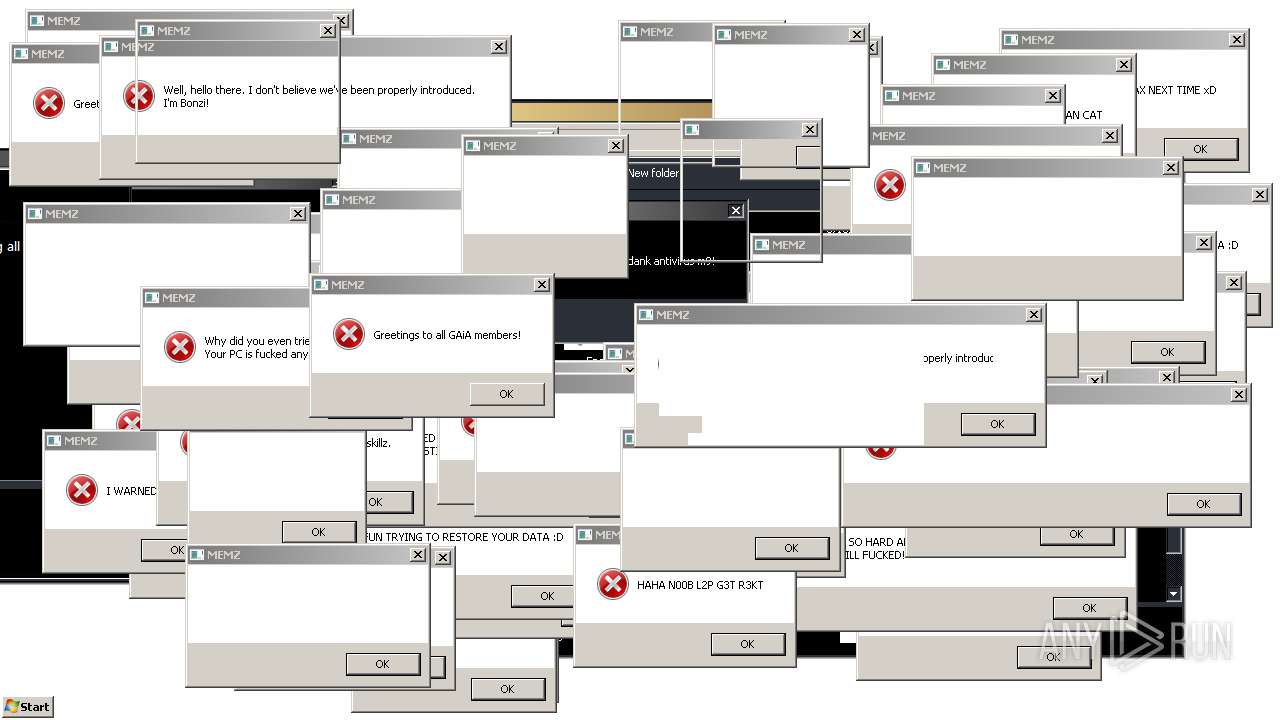
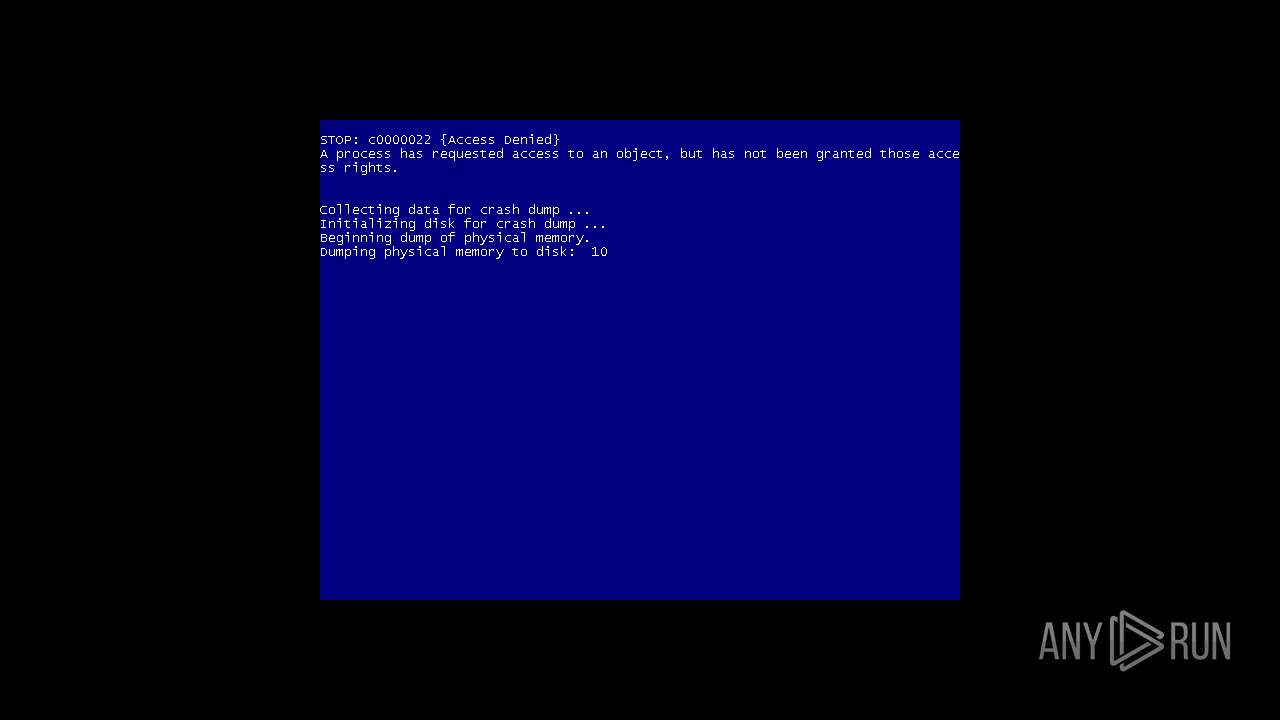
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2020, 20:29:19 |
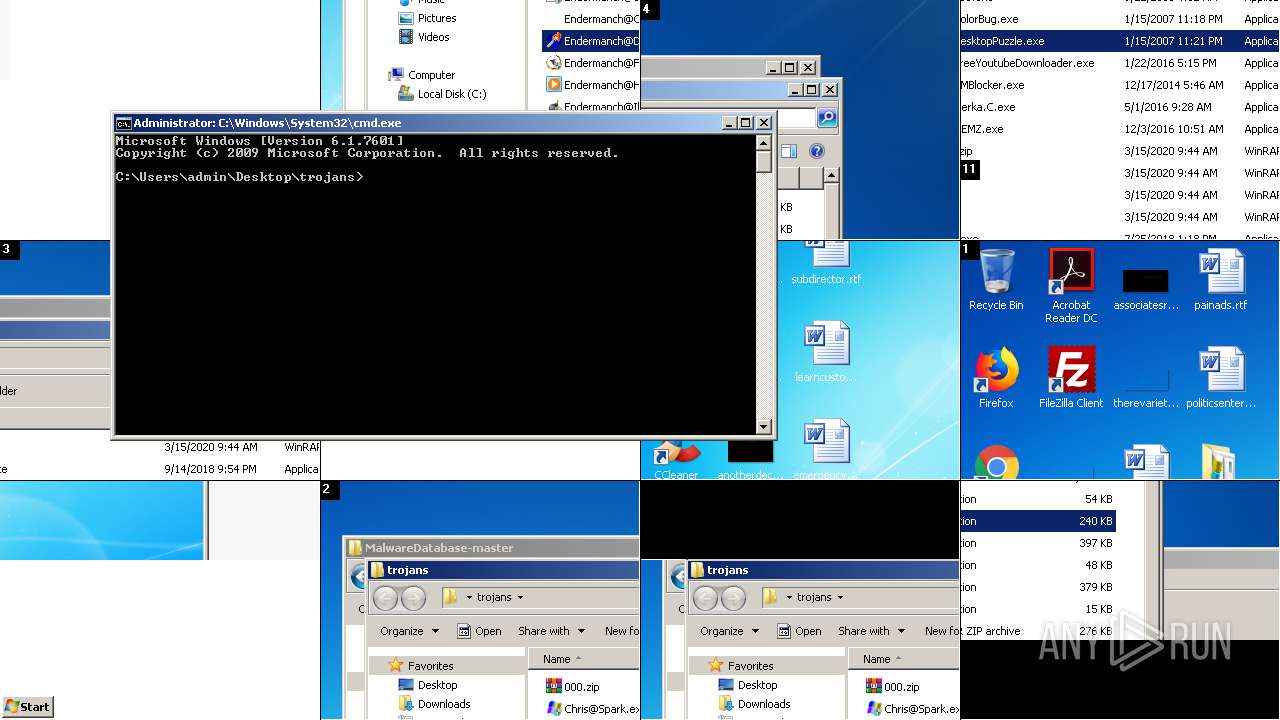
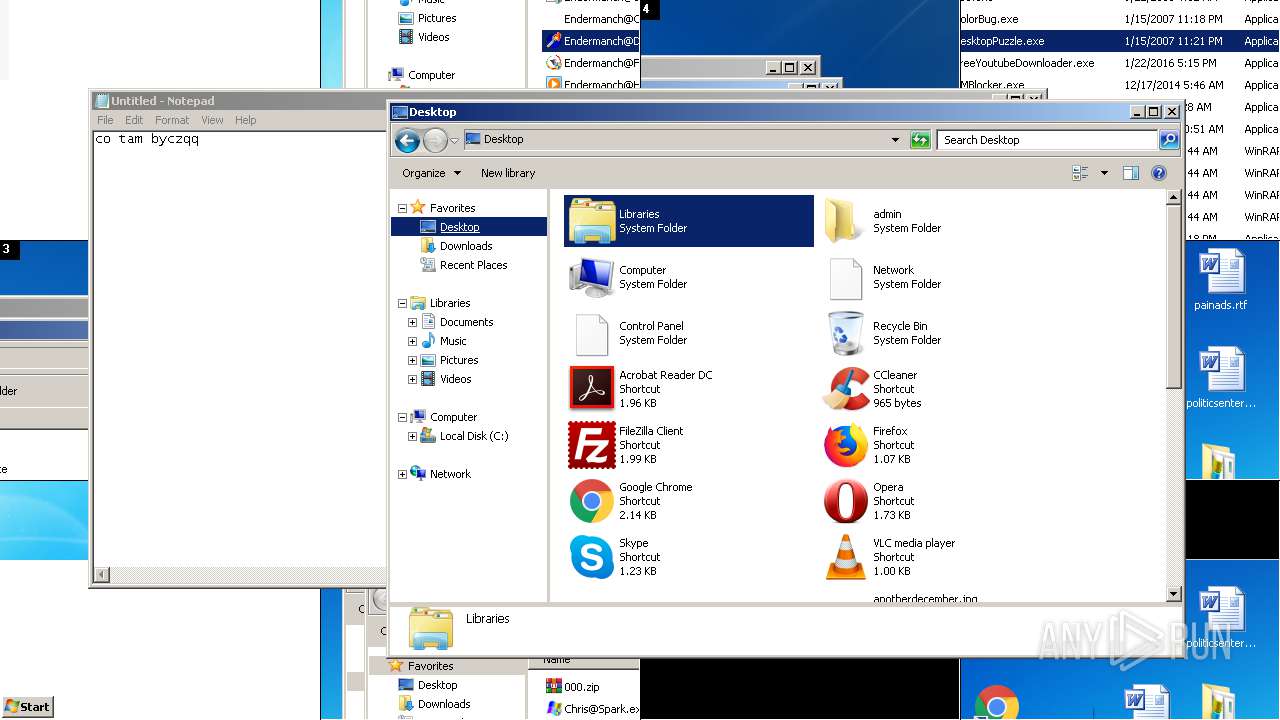
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
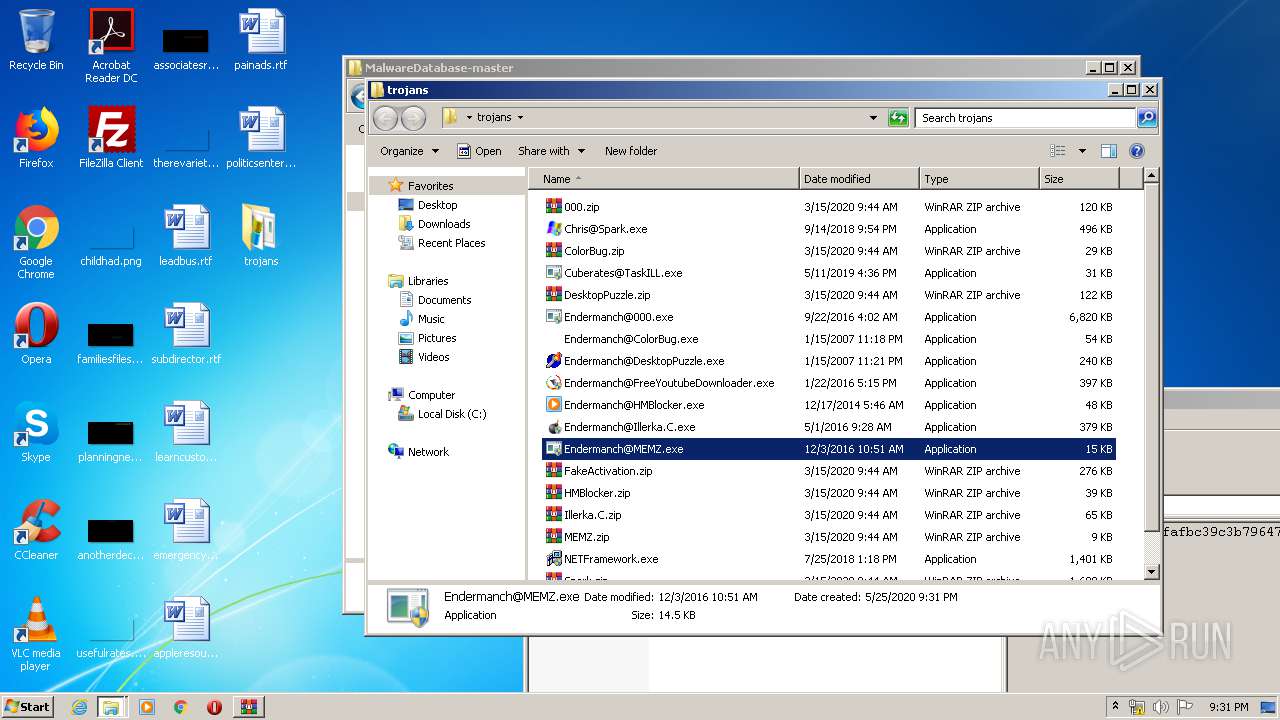
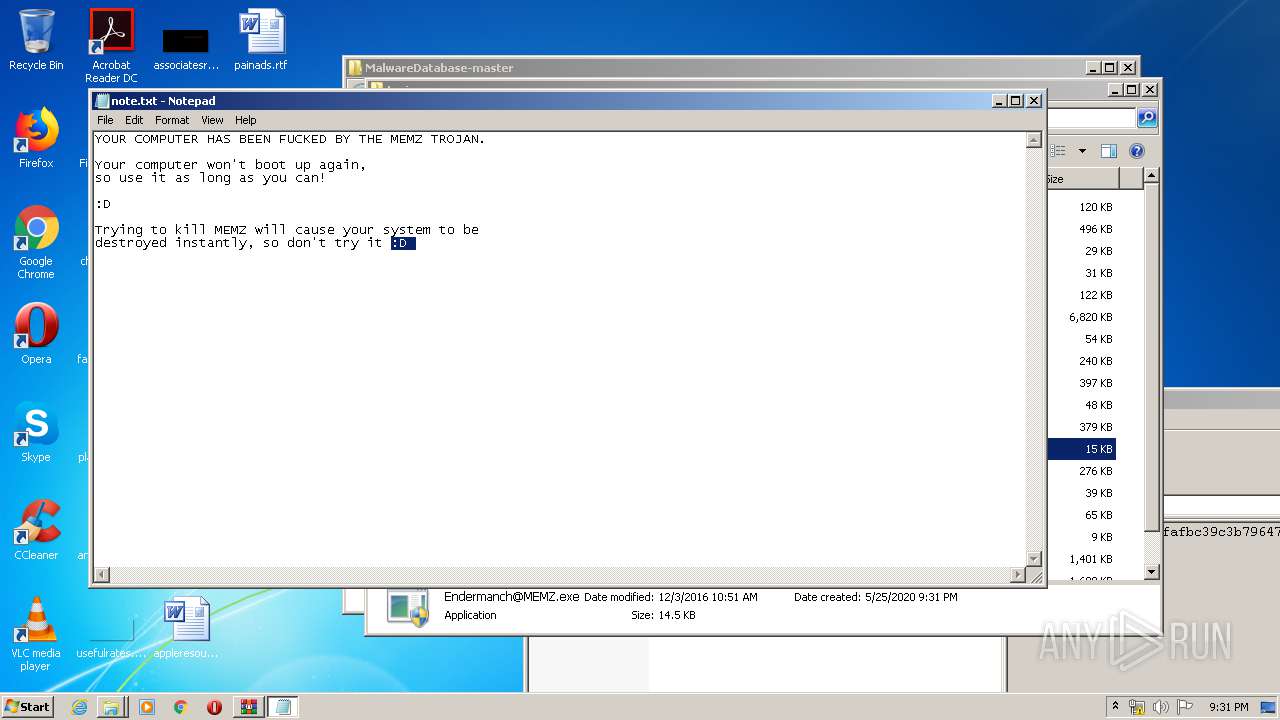
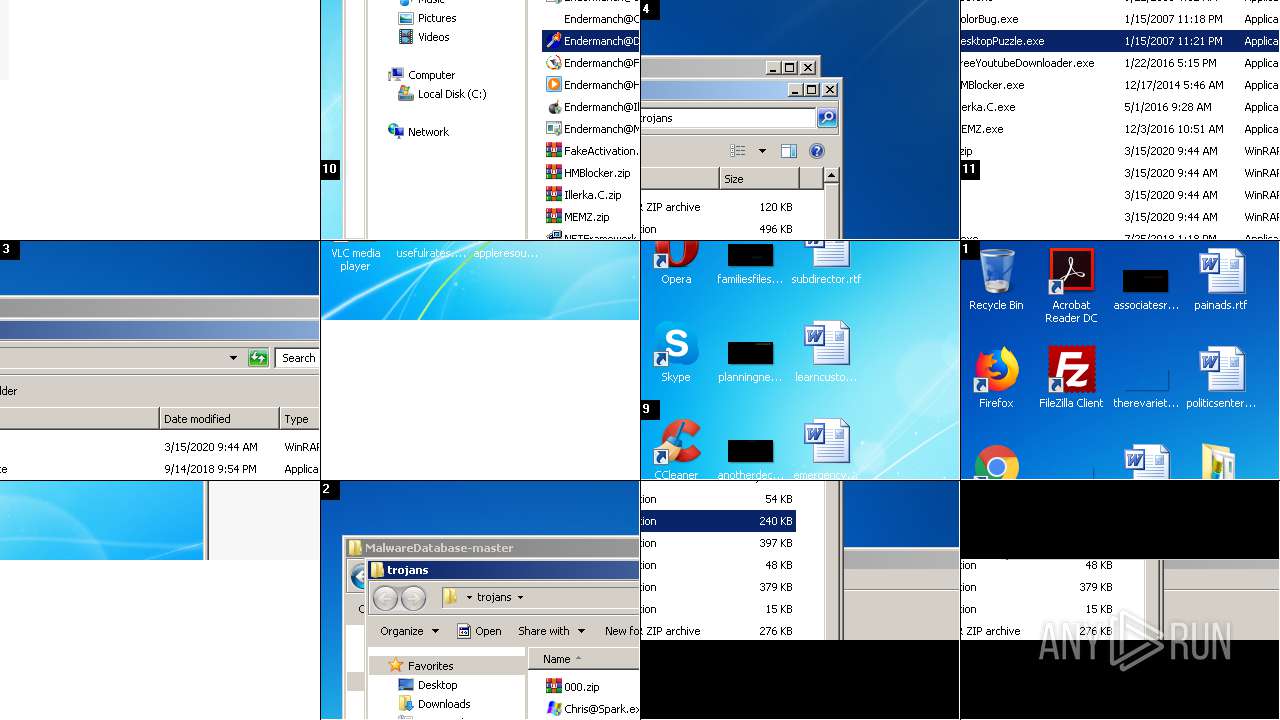
MALICIOUS
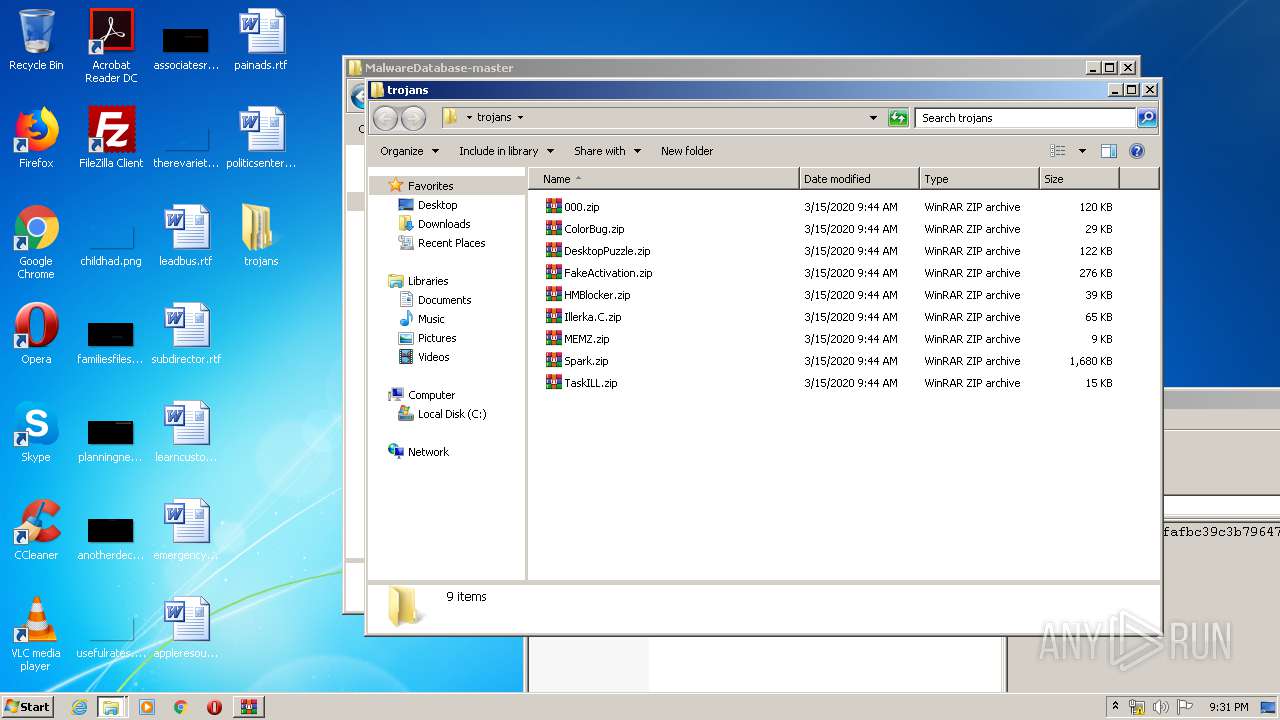
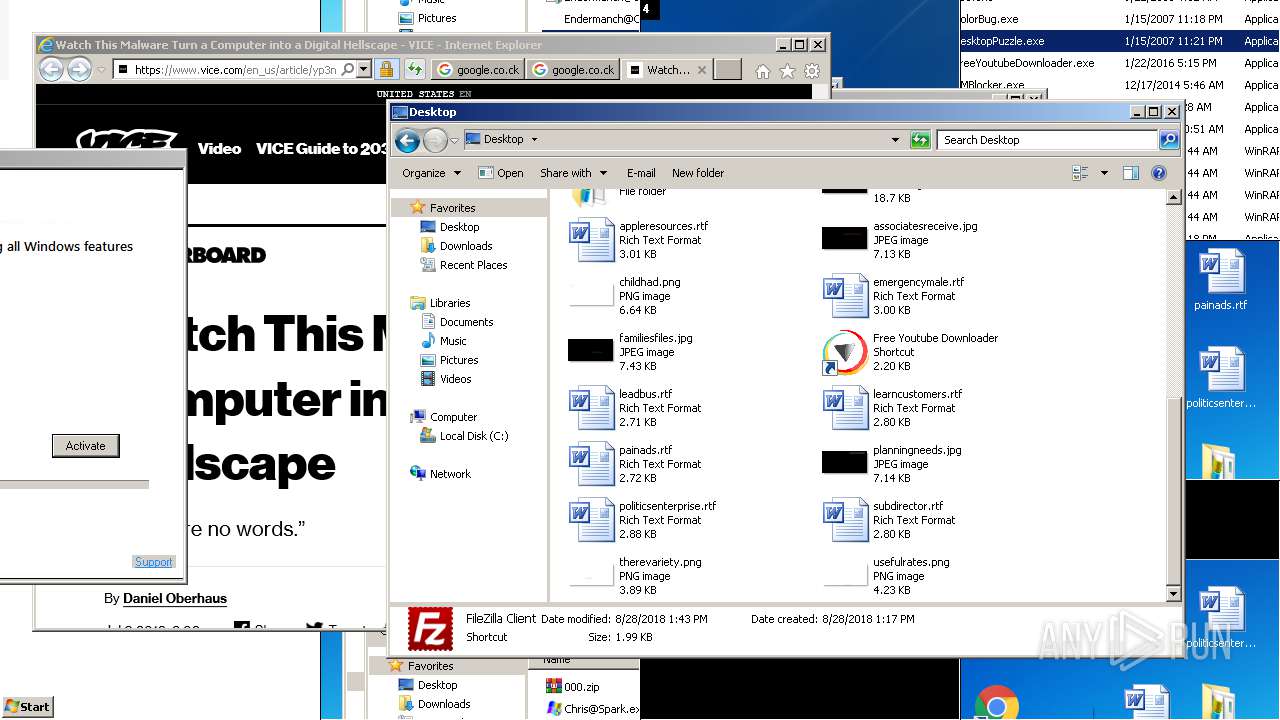
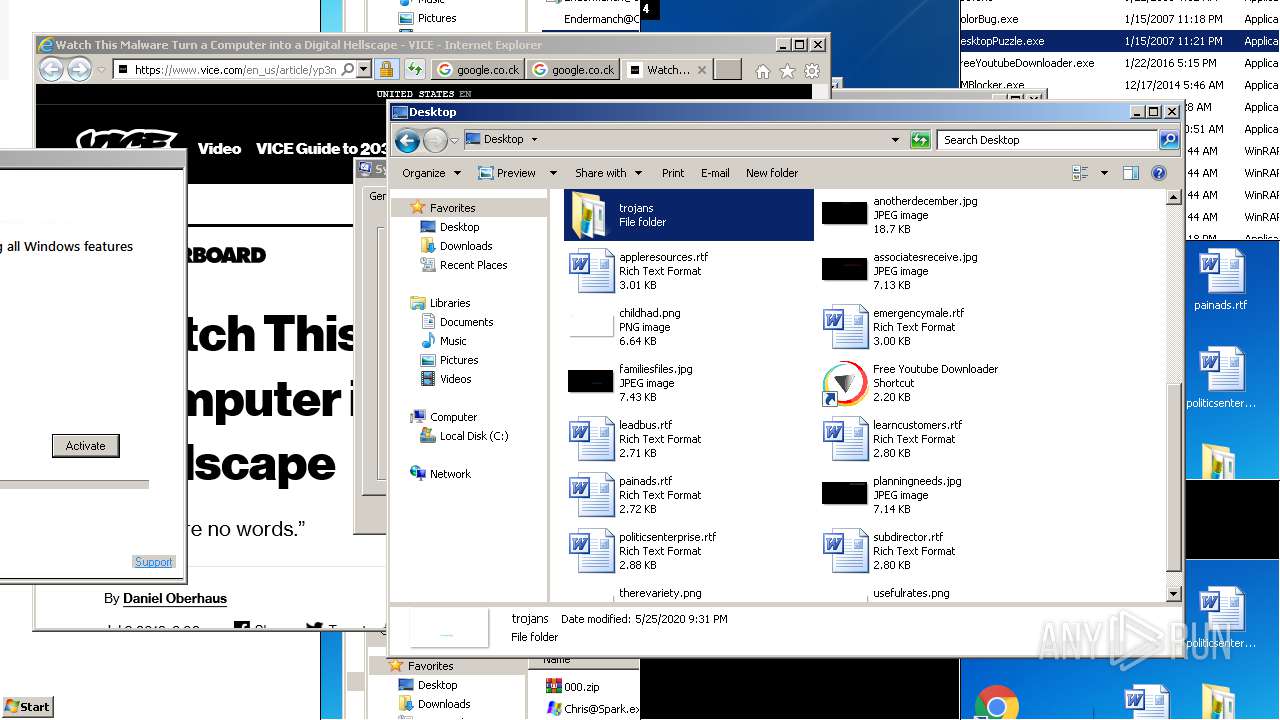
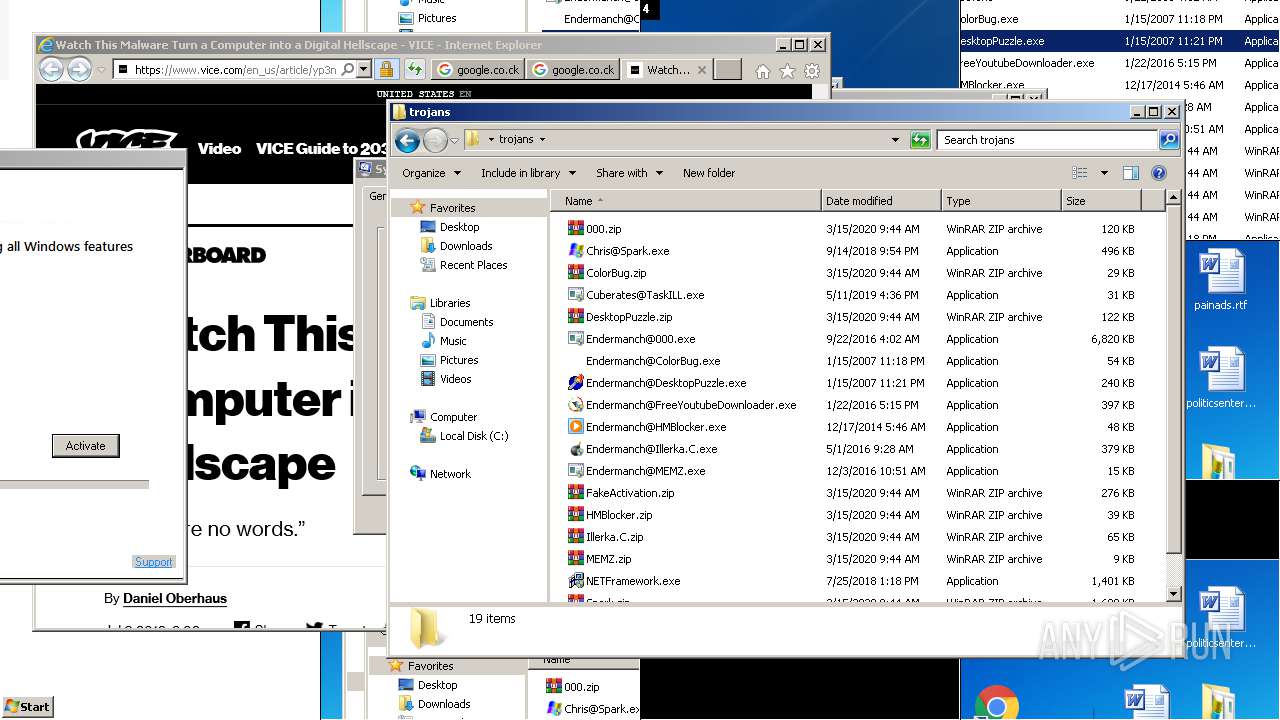
Application was dropped or rewritten from another process
- Endermanch@MEMZ.exe (PID: 3344)
- Endermanch@MEMZ.exe (PID: 3728)
- Endermanch@MEMZ.exe (PID: 2928)
- Endermanch@MEMZ.exe (PID: 3080)
- Endermanch@MEMZ.exe (PID: 1460)
- Endermanch@MEMZ.exe (PID: 2852)
- Endermanch@MEMZ.exe (PID: 1928)
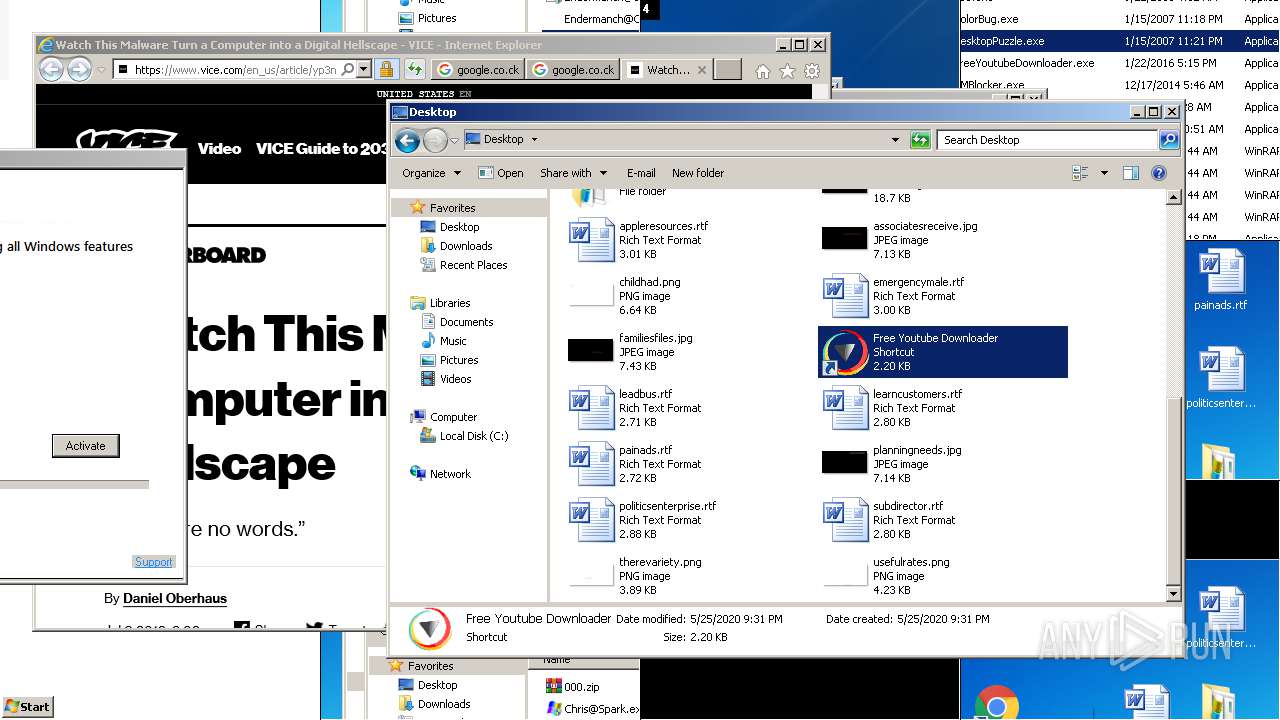
- Free YouTube Downloader.exe (PID: 792)
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
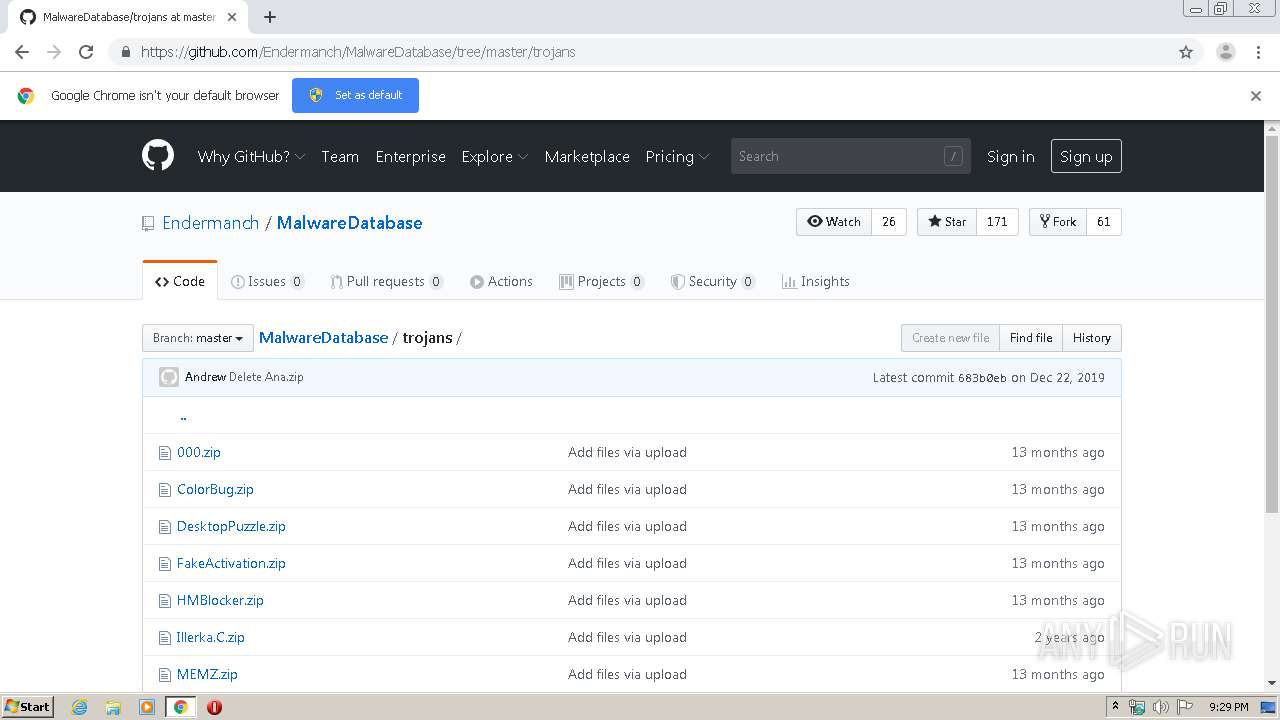
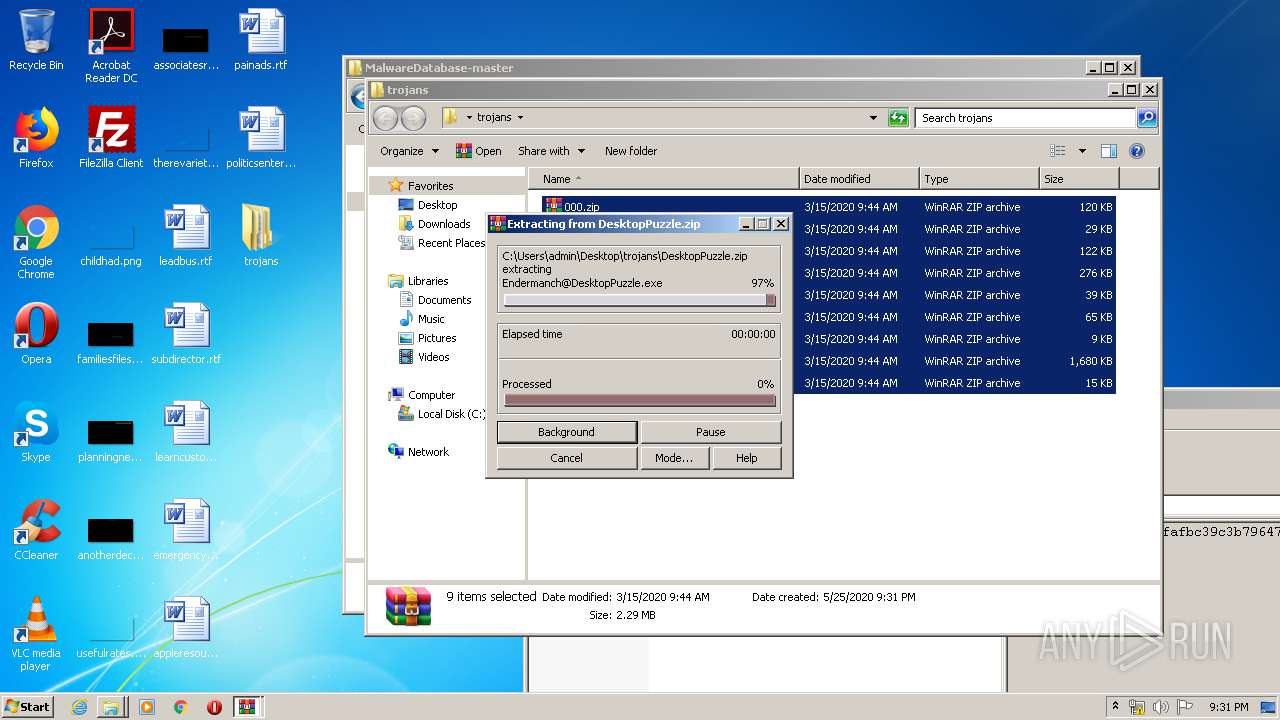
- Endermanch@DesktopPuzzle.exe (PID: 3816)
- Endermanch@MEMZ.exe (PID: 2588)
- Endermanch@FreeYoutubeDownloader.exe (PID: 3860)
- Box.exe (PID: 1440)
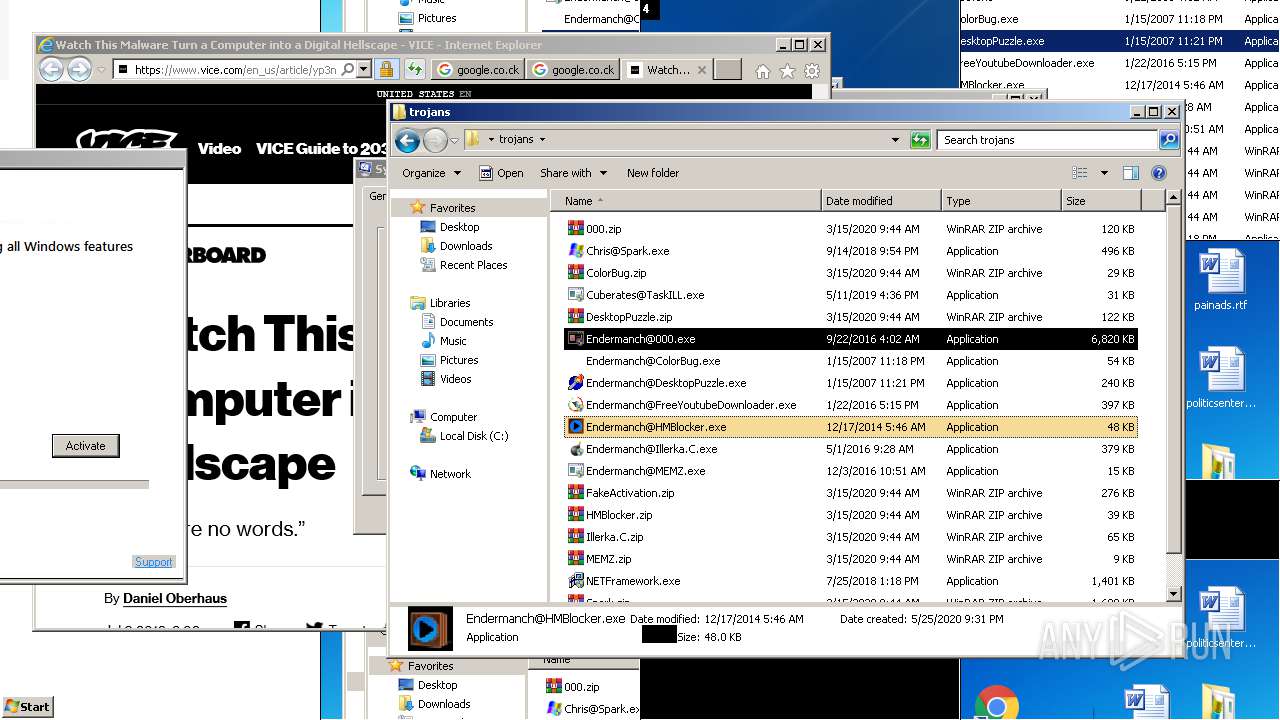
- Endermanch@HMBlocker.exe (PID: 3280)
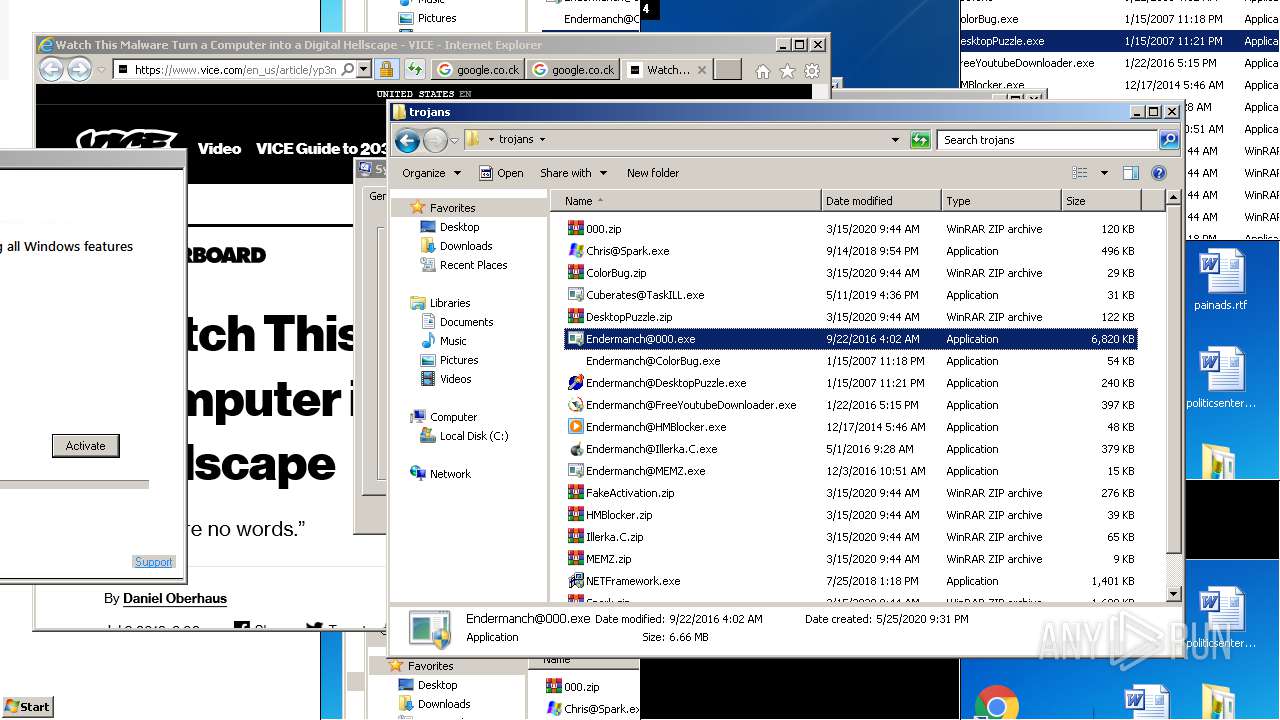
- Endermanch@000.exe (PID: 2208)
- Endermanch@000.exe (PID: 3112)
- Endermanch@HMBlocker.exe (PID: 552)
- Endermanch@HMBlocker.exe (PID: 1832)
- Endermanch@DesktopPuzzle.exe (PID: 608)
- Endermanch@MEMZ.exe (PID: 1812)
- Endermanch@HMBlocker.exe (PID: 1084)
Changes the autorun value in the registry
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
- reg.exe (PID: 1640)
- reg.exe (PID: 3024)
Low-level write access rights to disk partition
- Endermanch@MEMZ.exe (PID: 2588)
Runs app for hidden code execution
- Endermanch@MEMZ.exe (PID: 2588)
Changes the login/logoff helper path in the registry
- Endermanch@000.exe (PID: 3112)
Task Manager has been disabled (taskmgr)
- Endermanch@000.exe (PID: 3112)
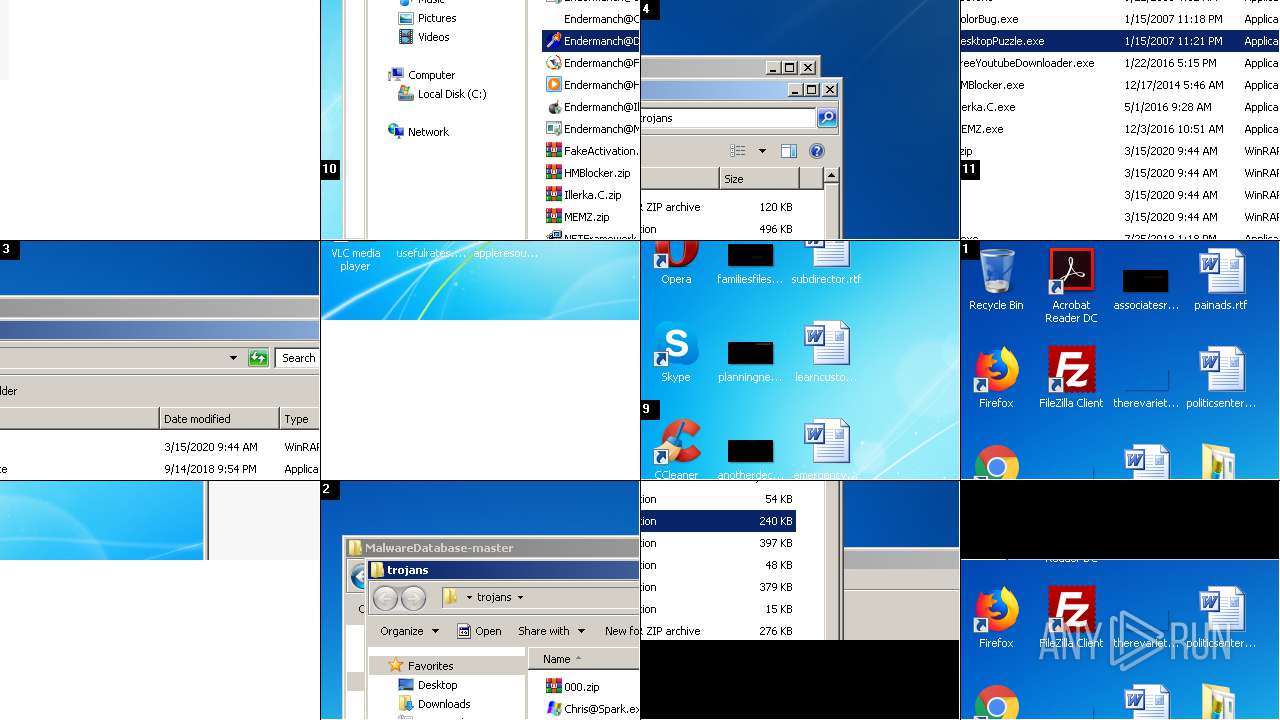
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 4088)
Executable content was dropped or overwritten
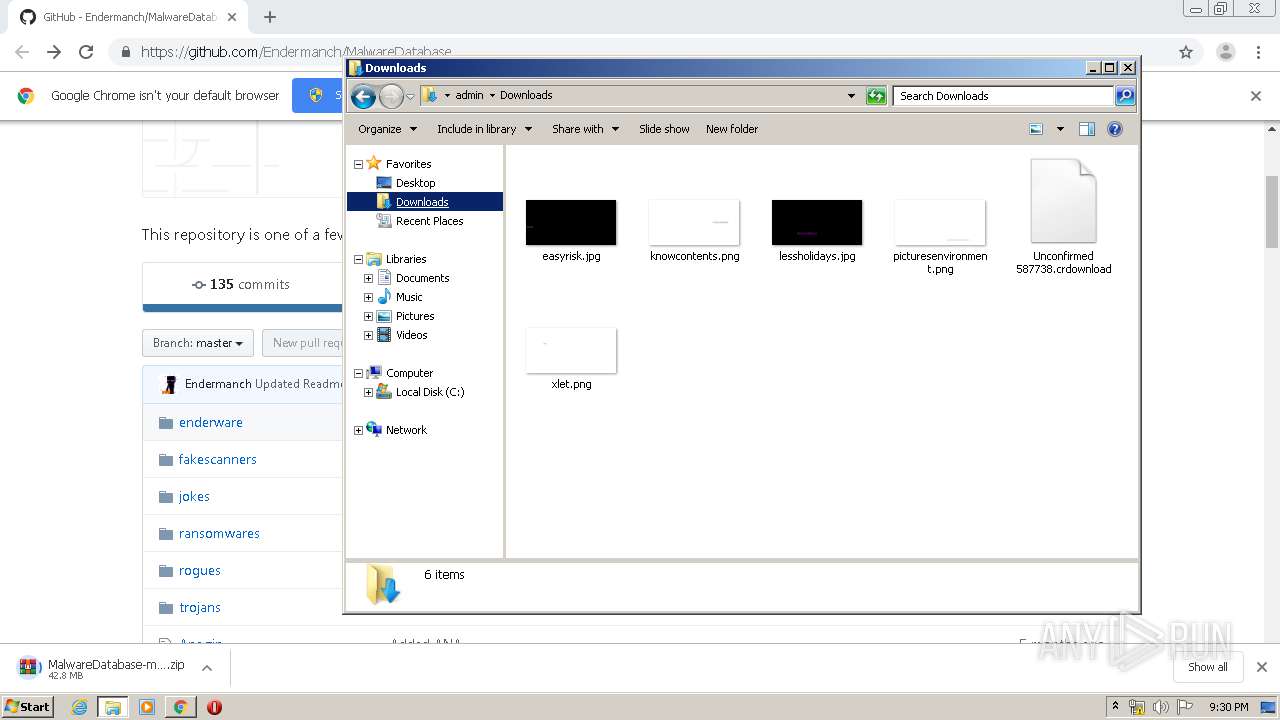
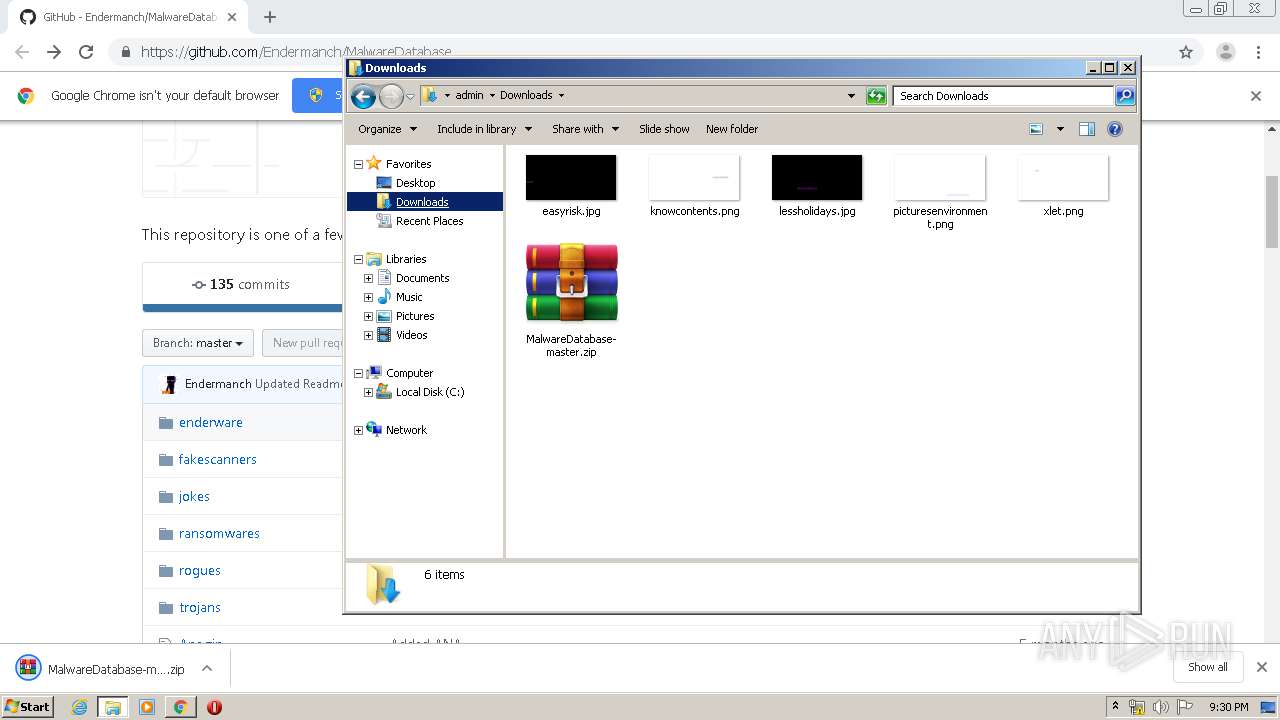
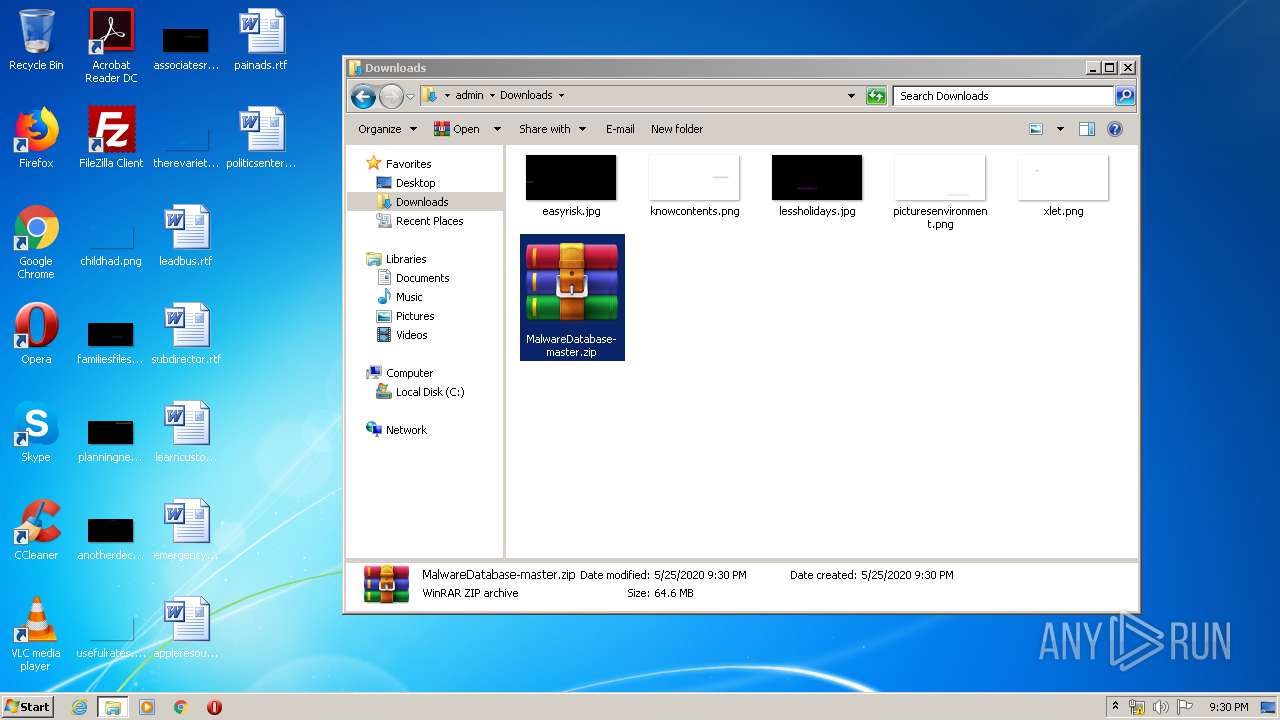
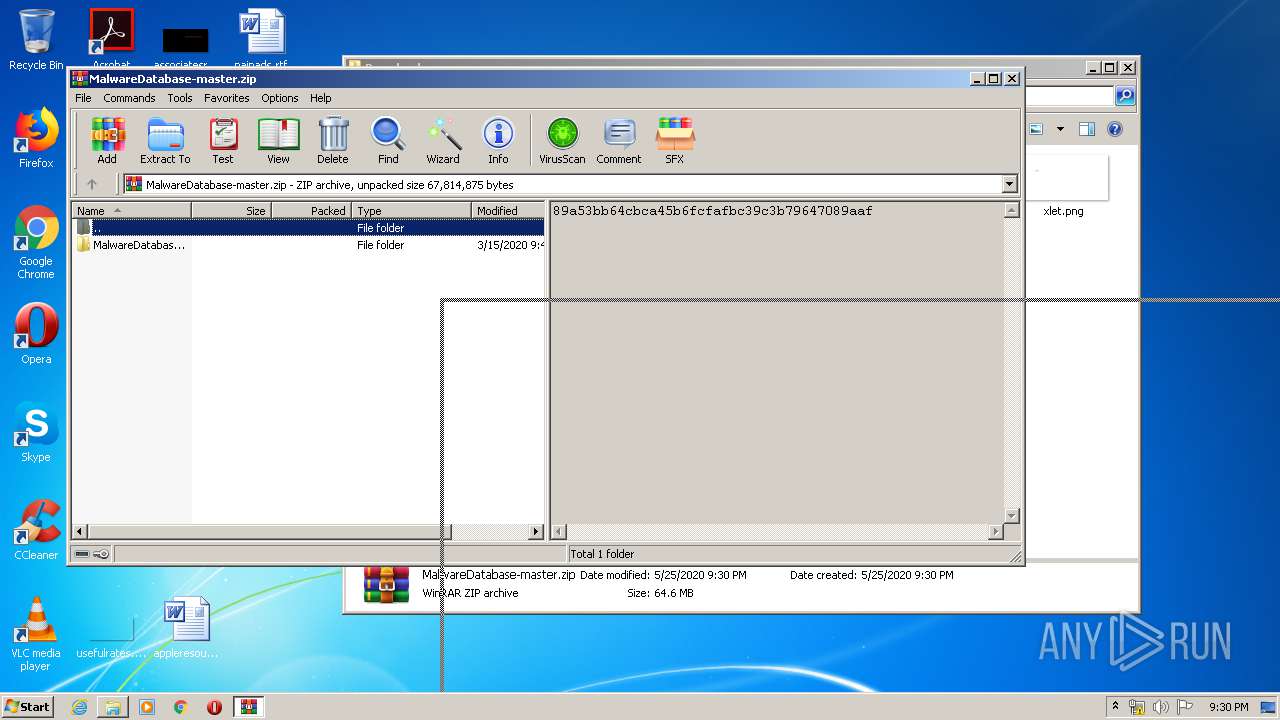
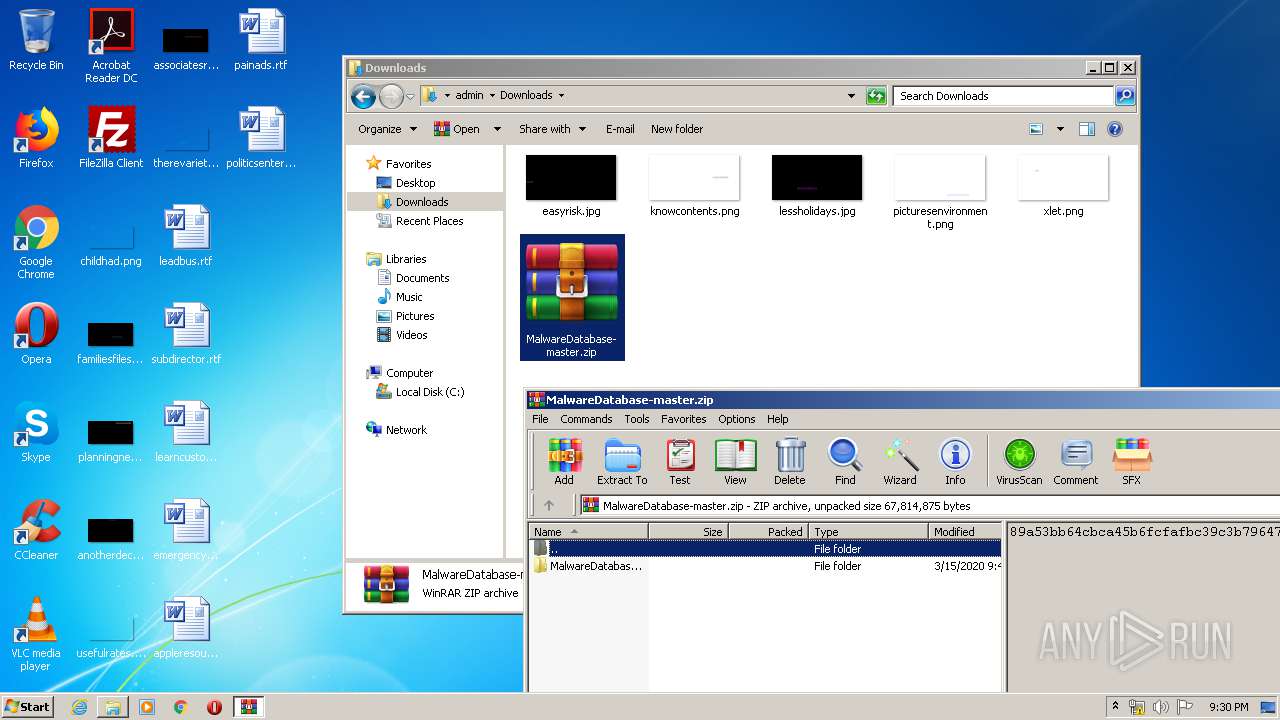
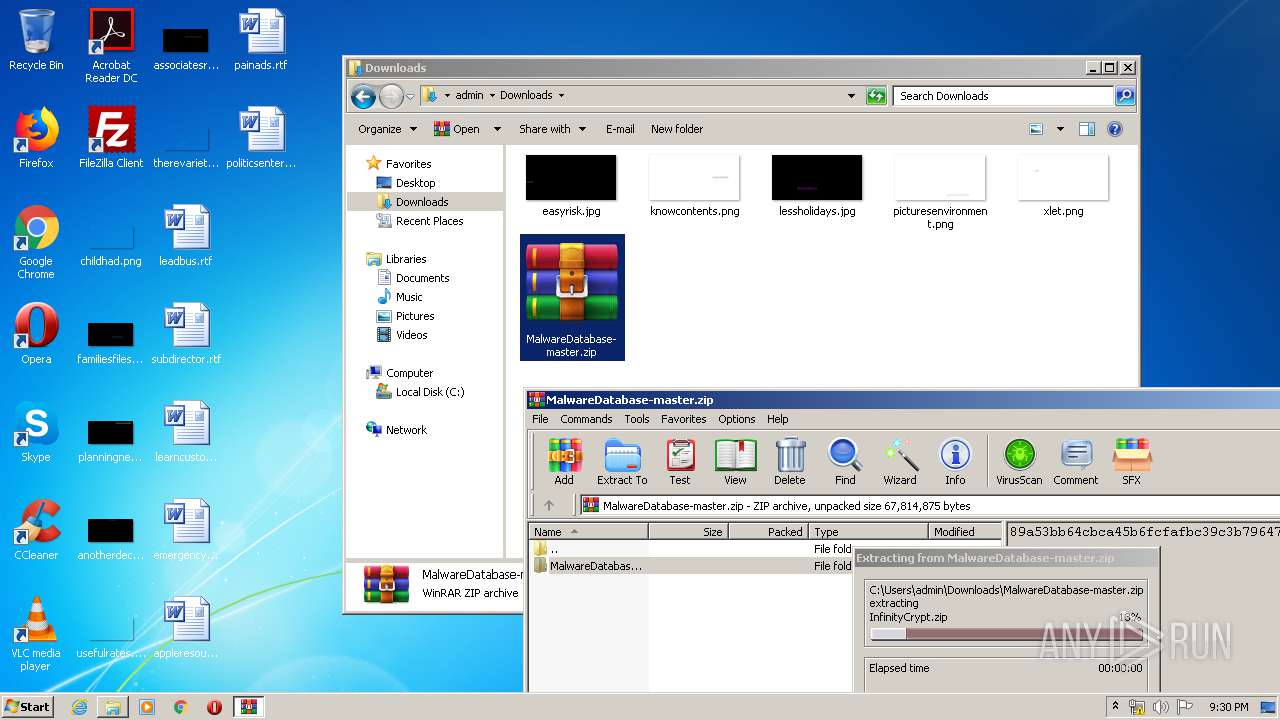
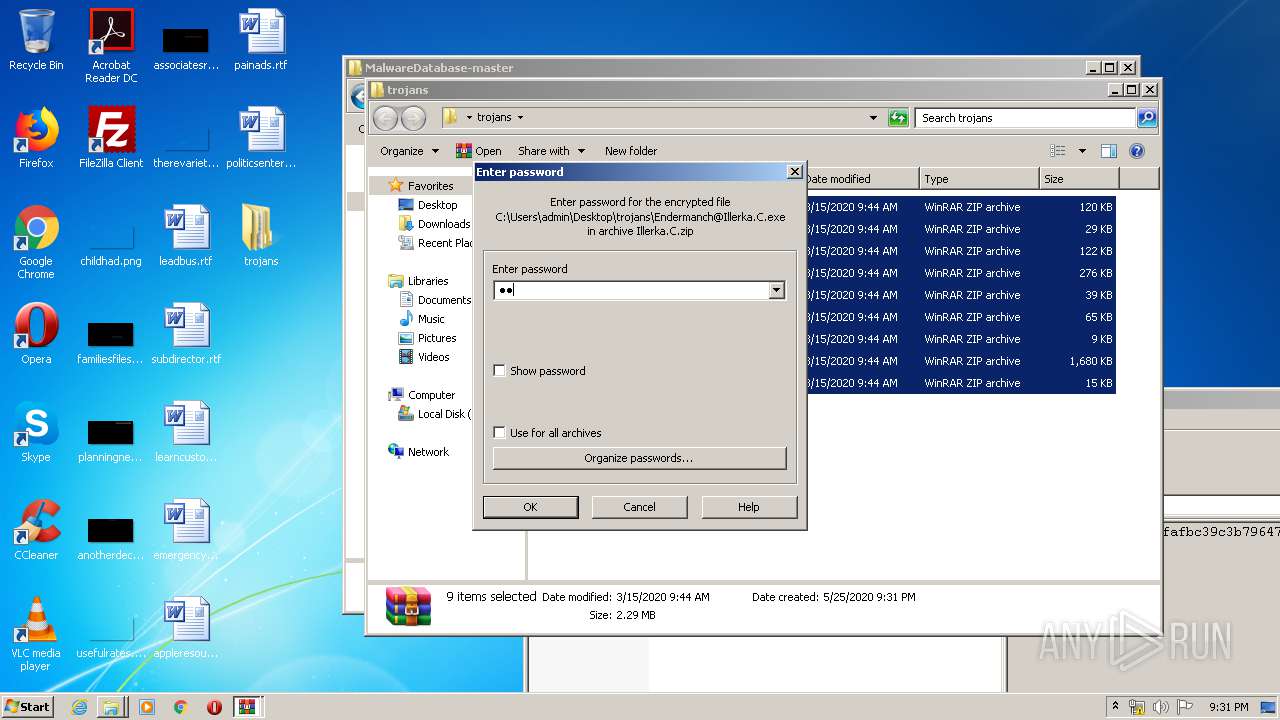
- WinRAR.exe (PID: 3296)
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
- Endermanch@000.exe (PID: 3112)
Application launched itself
- Endermanch@MEMZ.exe (PID: 2928)
Creates files in the Windows directory
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
Creates a software uninstall entry
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
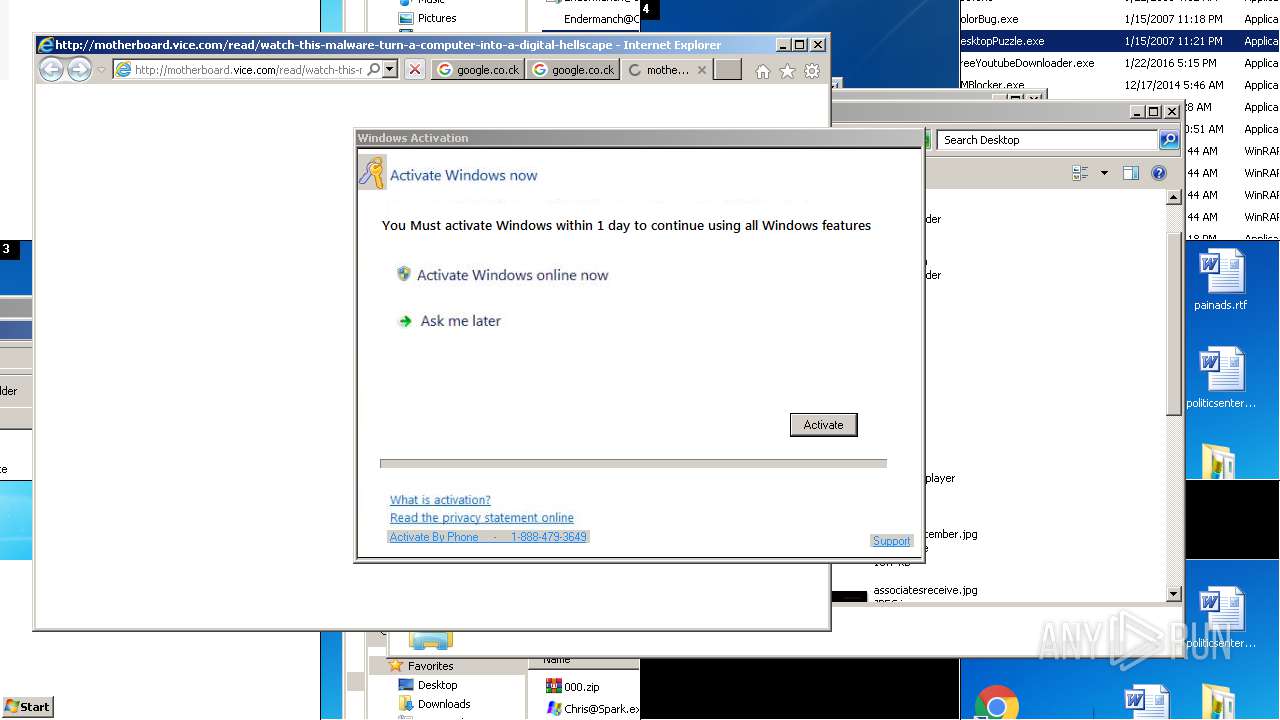
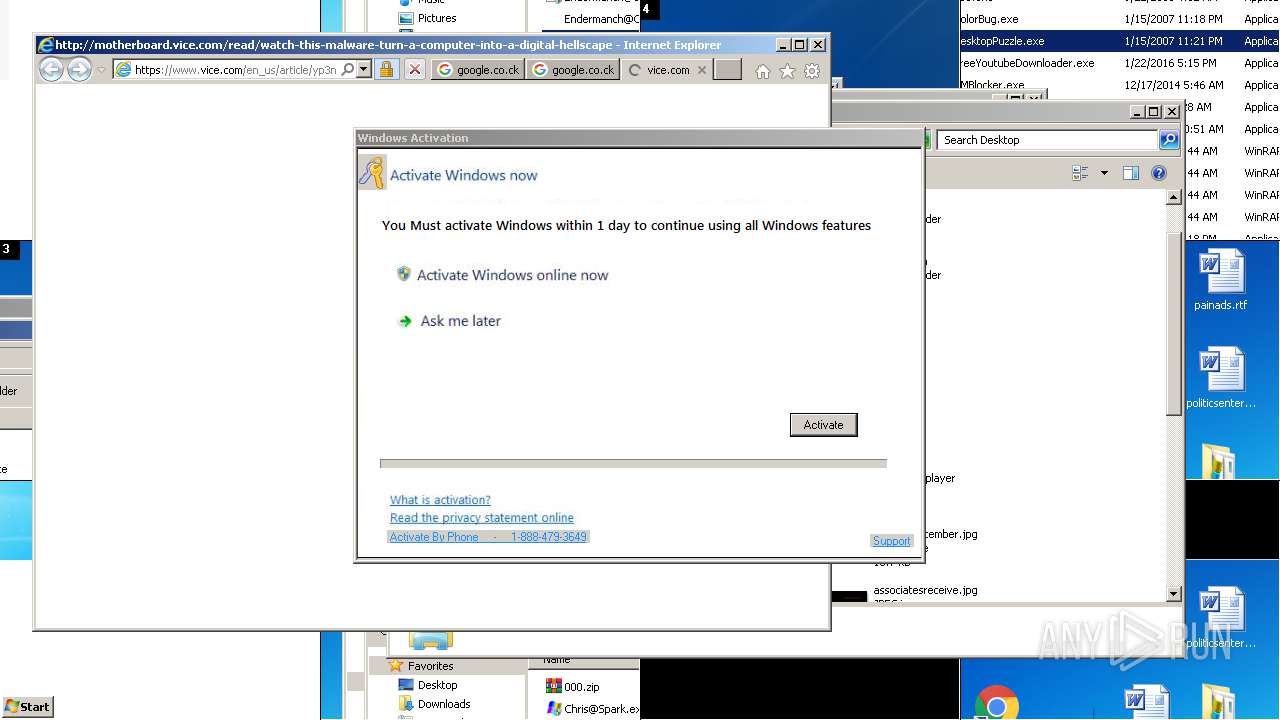
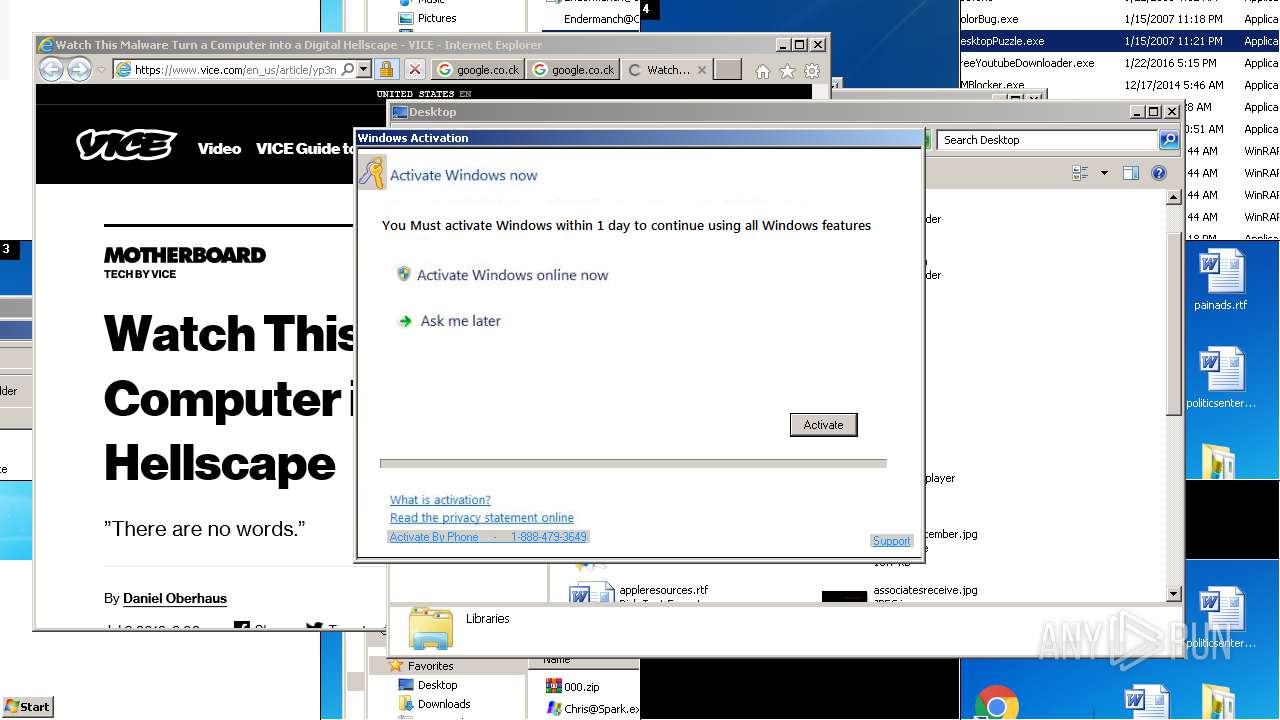
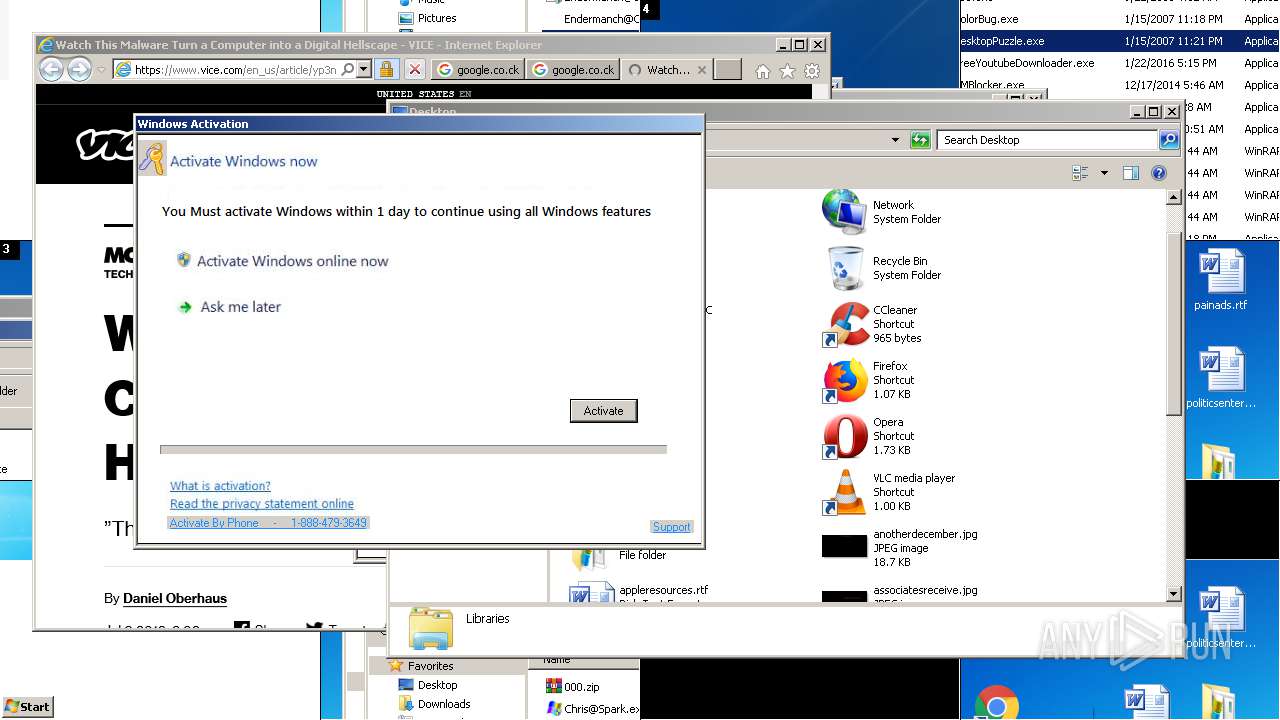
Starts Internet Explorer
- Endermanch@MEMZ.exe (PID: 2588)
Low-level read access rights to disk partition
- Endermanch@MEMZ.exe (PID: 2588)
- msconfig.exe (PID: 1912)
Starts CMD.EXE for commands execution
- Endermanch@MEMZ.exe (PID: 2588)
- Endermanch@HMBlocker.exe (PID: 3280)
- Endermanch@000.exe (PID: 3112)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1064)
- cmd.exe (PID: 2848)
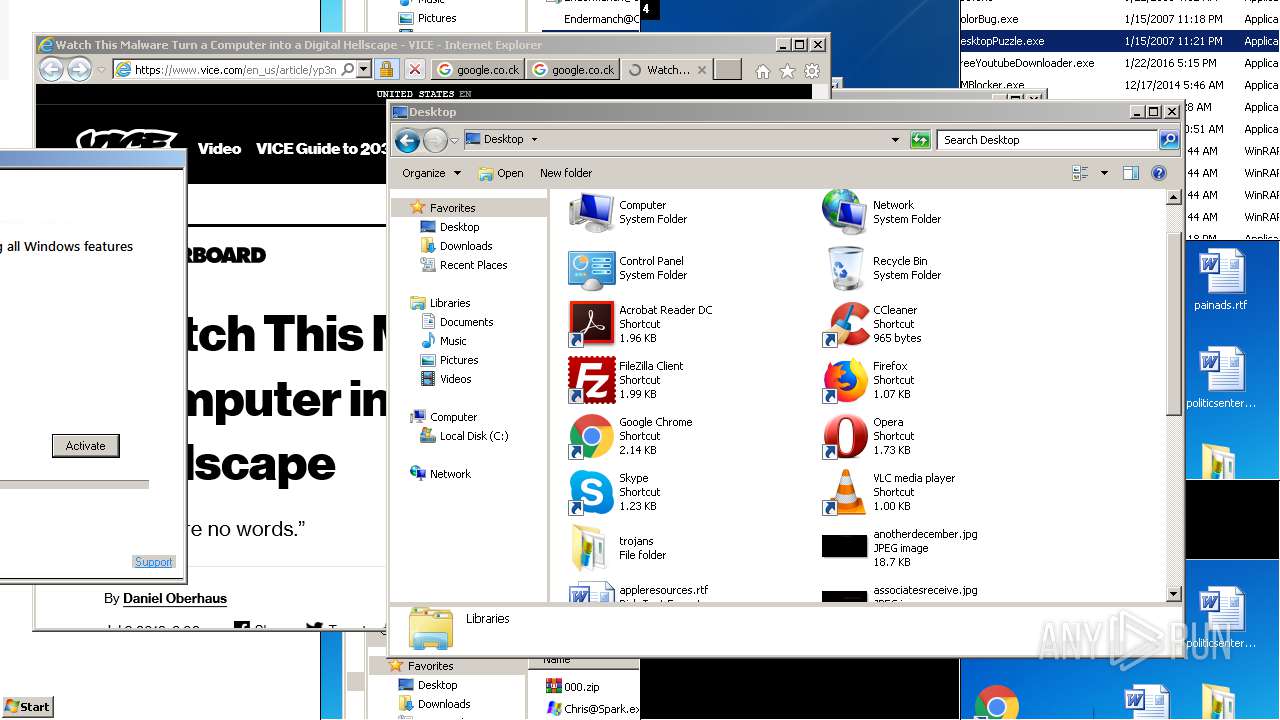
Changes the desktop background image
- Endermanch@000.exe (PID: 3112)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3192)
Reads Internet Cache Settings
- Endermanch@000.exe (PID: 3112)
INFO
Application launched itself
- chrome.exe (PID: 4088)
- iexplore.exe (PID: 3968)
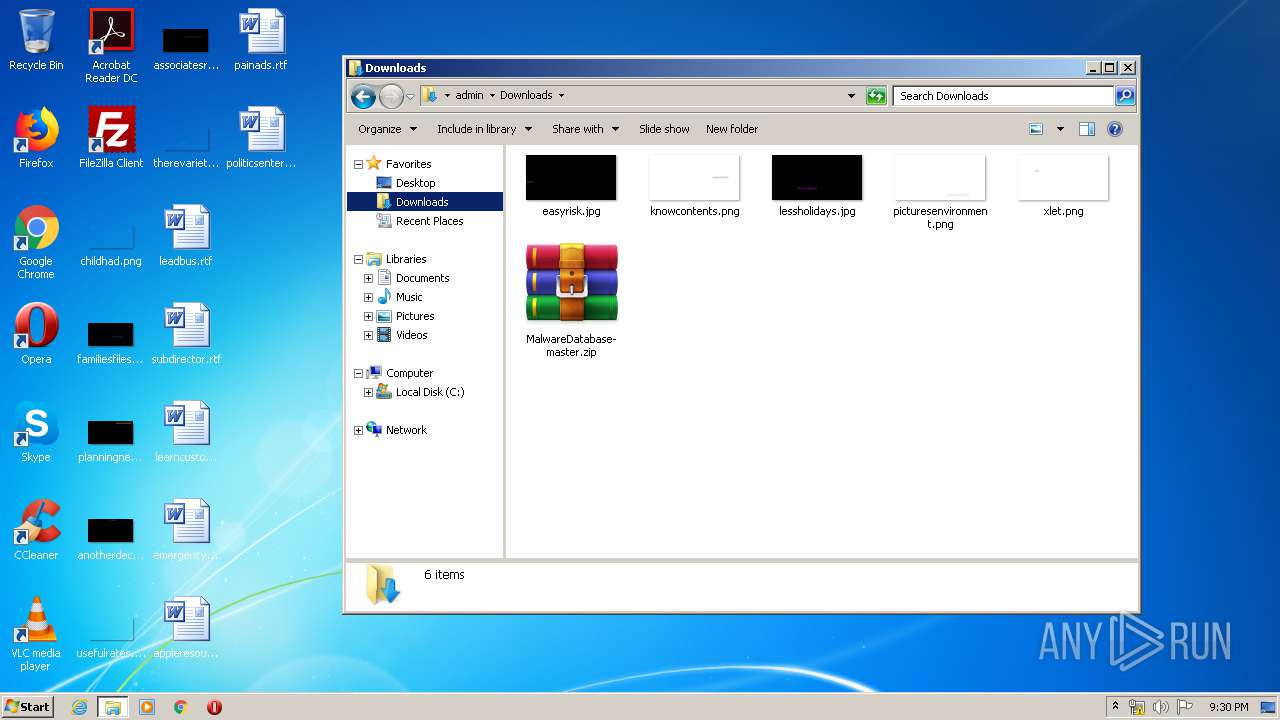
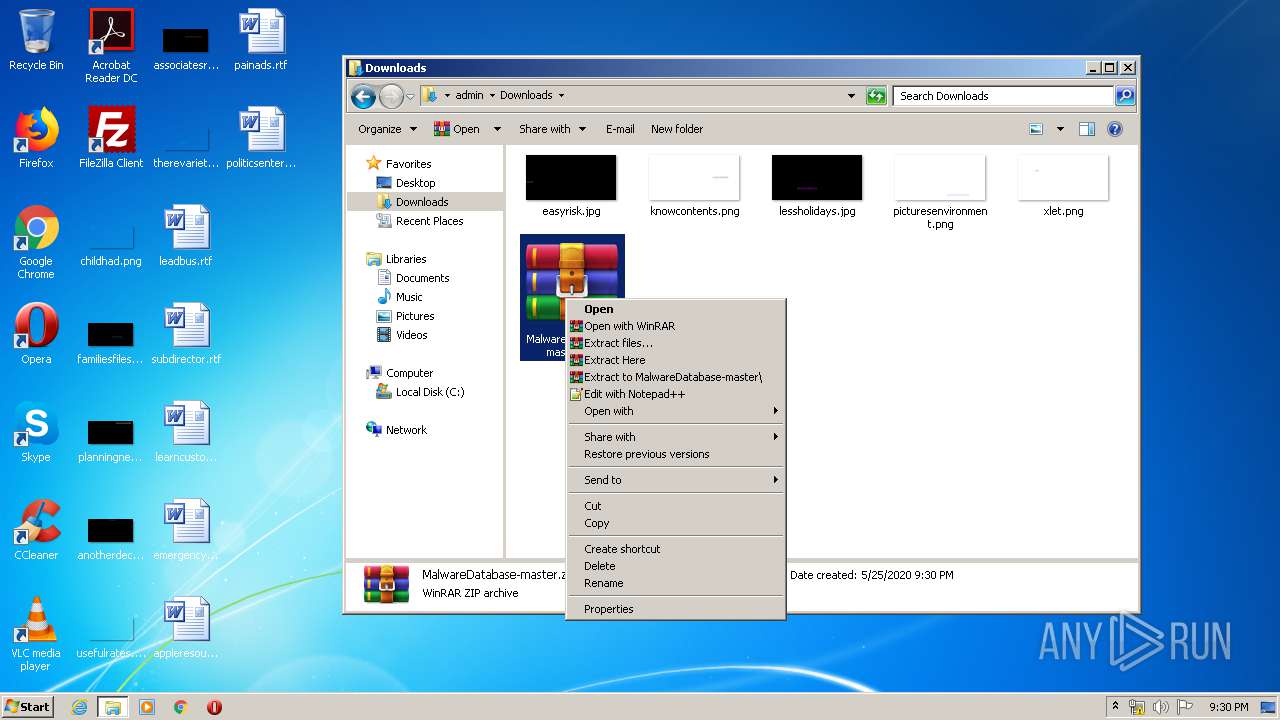
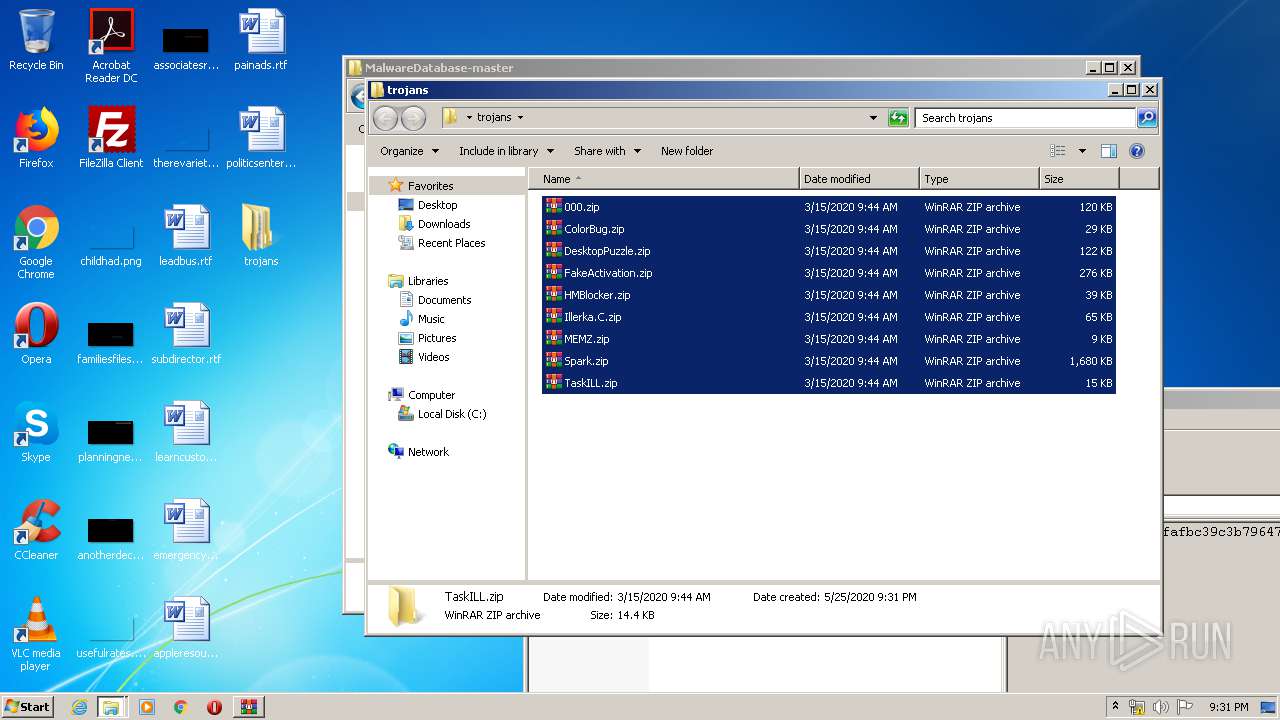
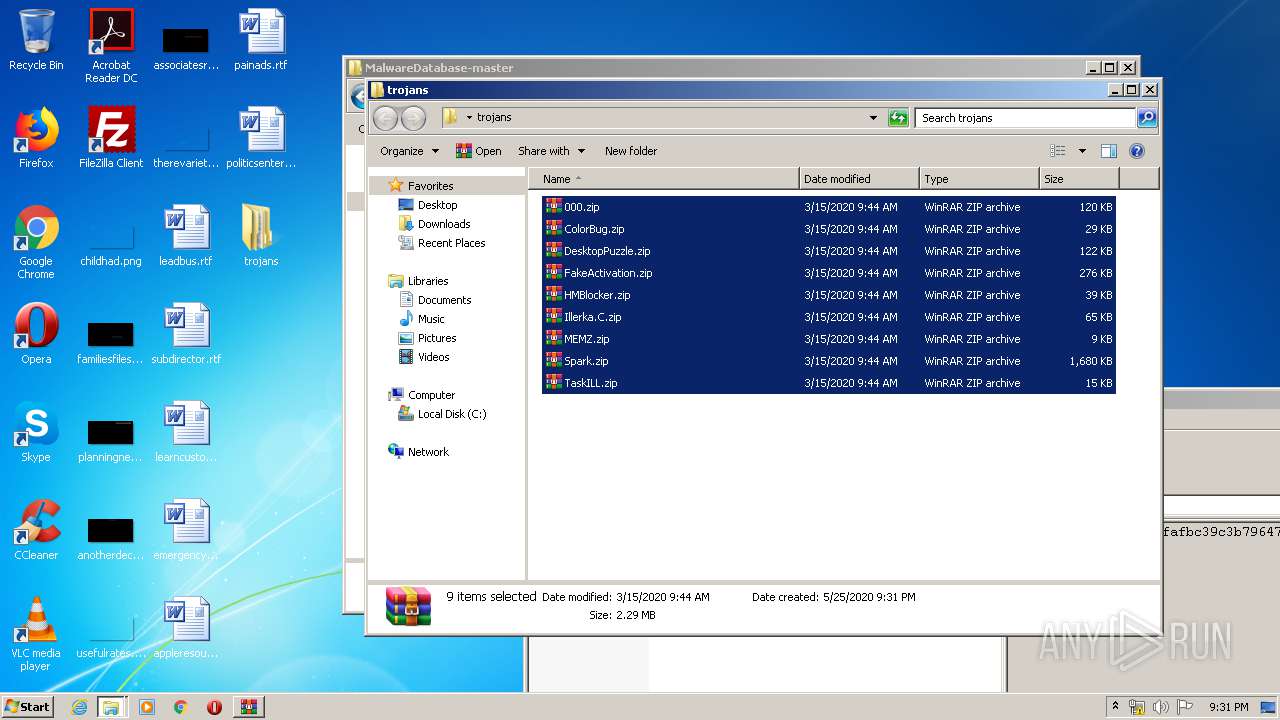
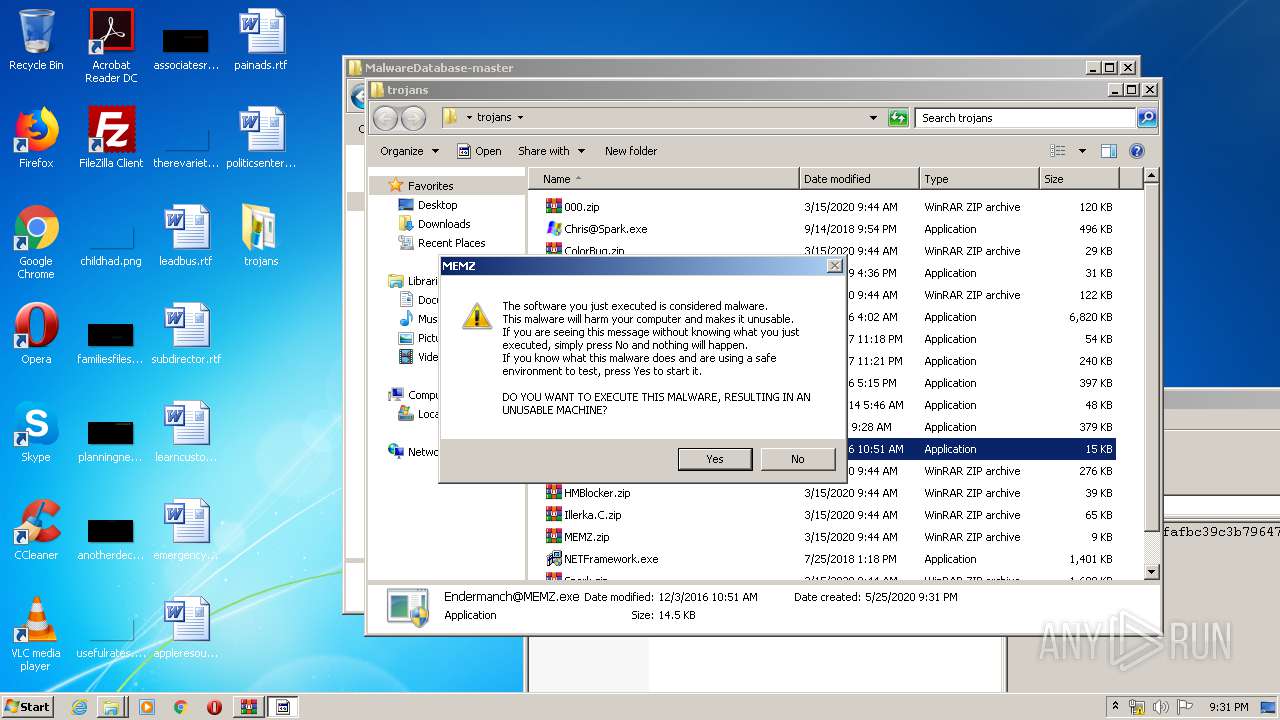
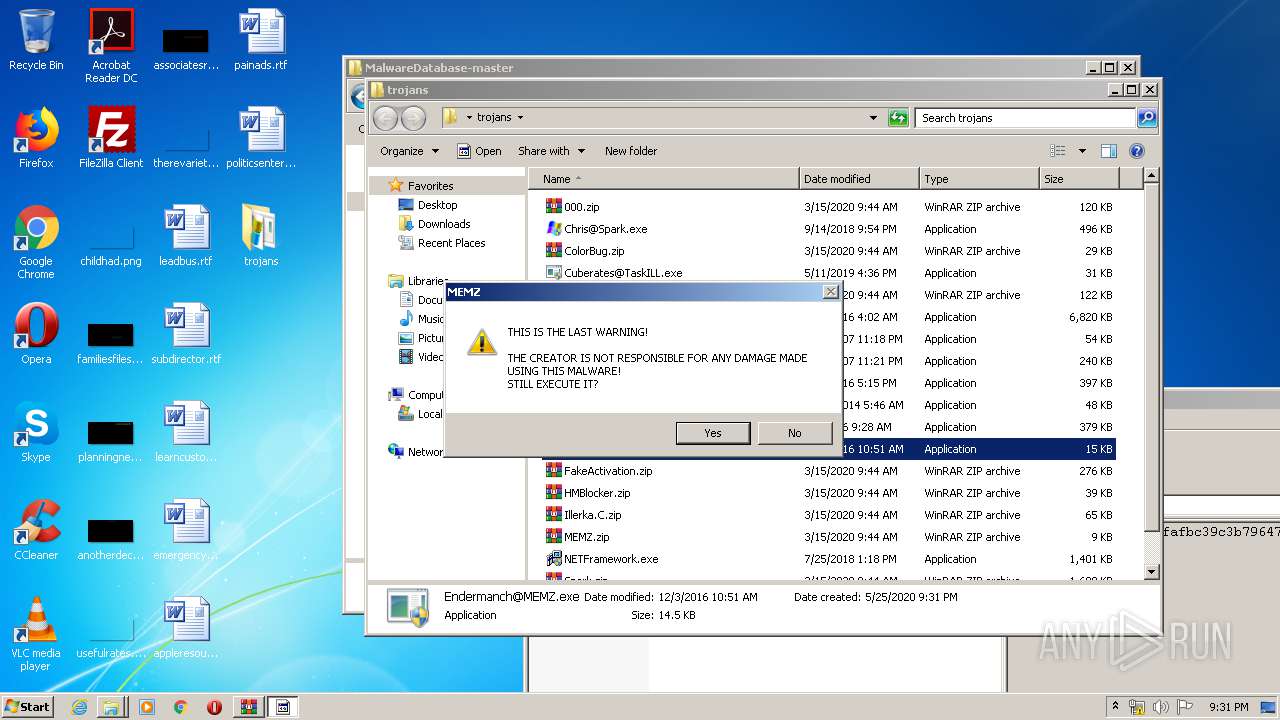
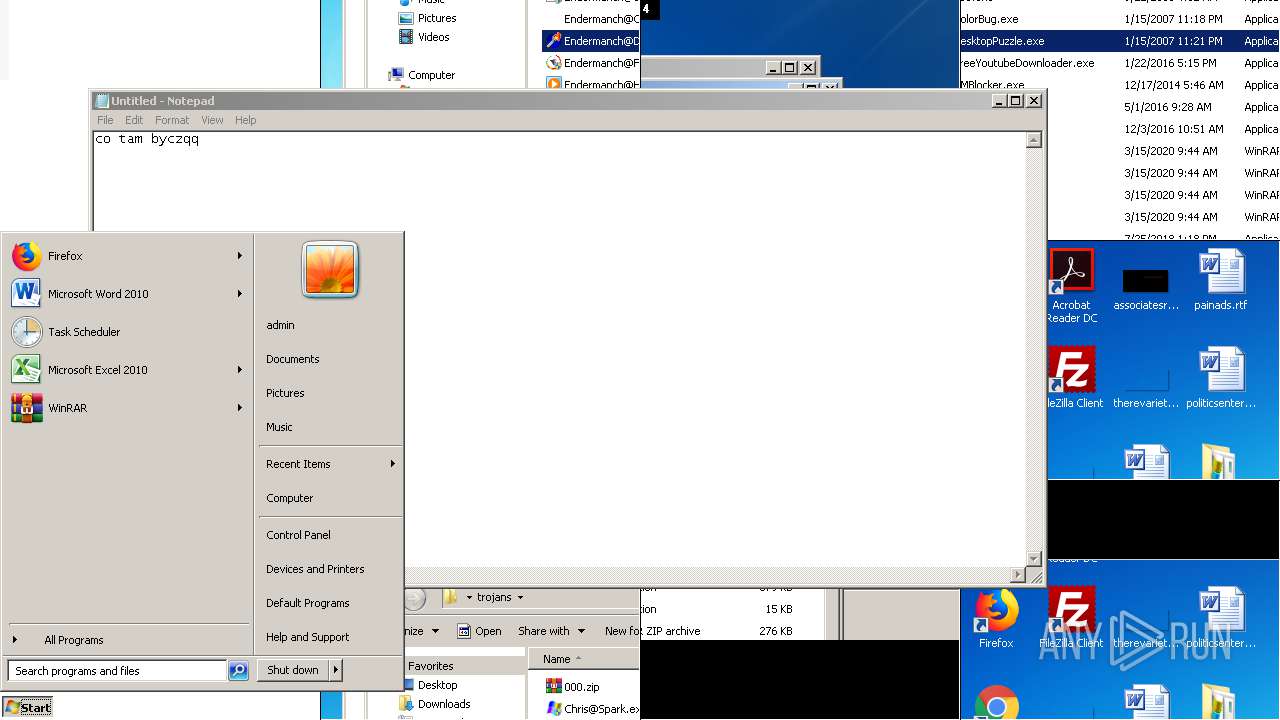
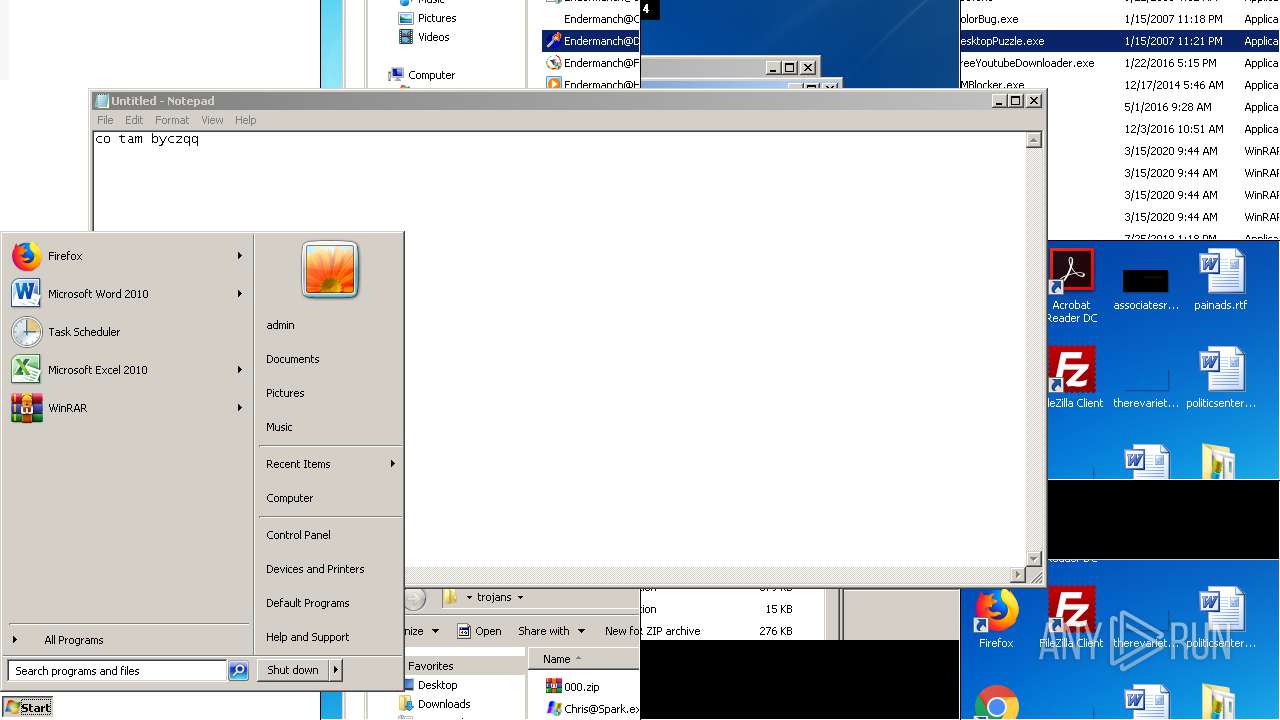
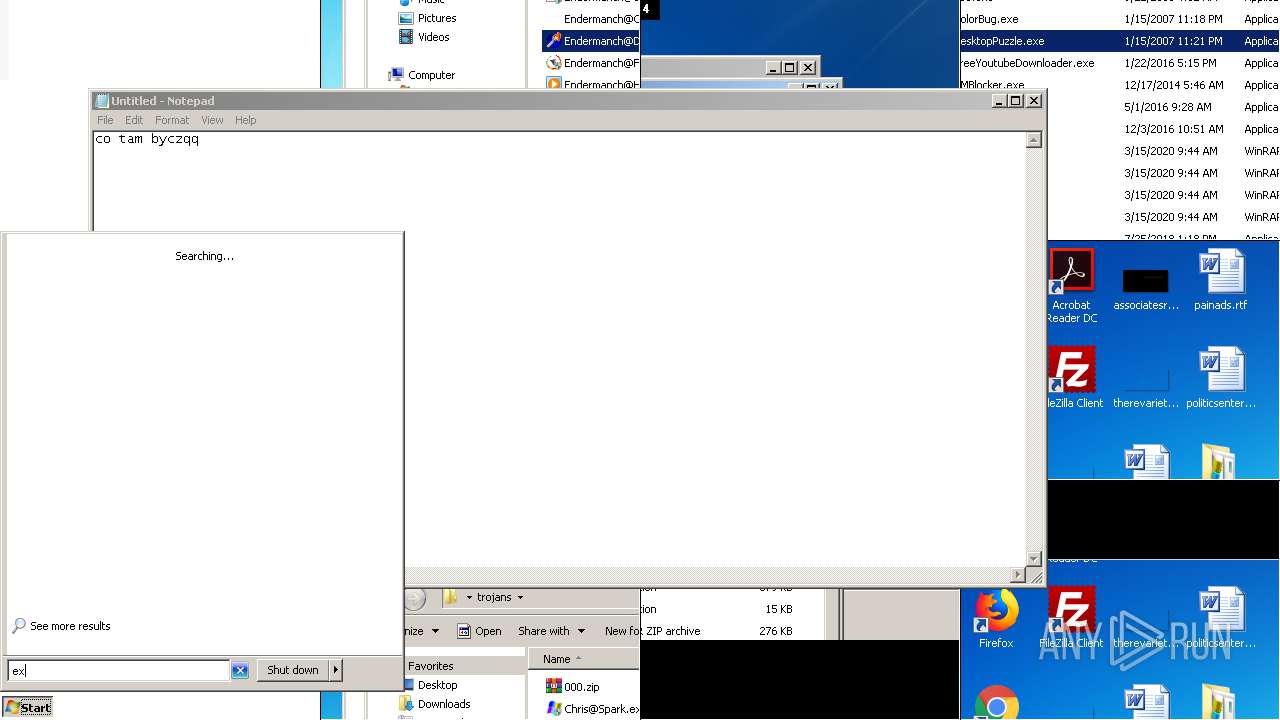
Manual execution by user
- WinRAR.exe (PID: 3180)
- WinRAR.exe (PID: 3296)
- Endermanch@MEMZ.exe (PID: 3080)
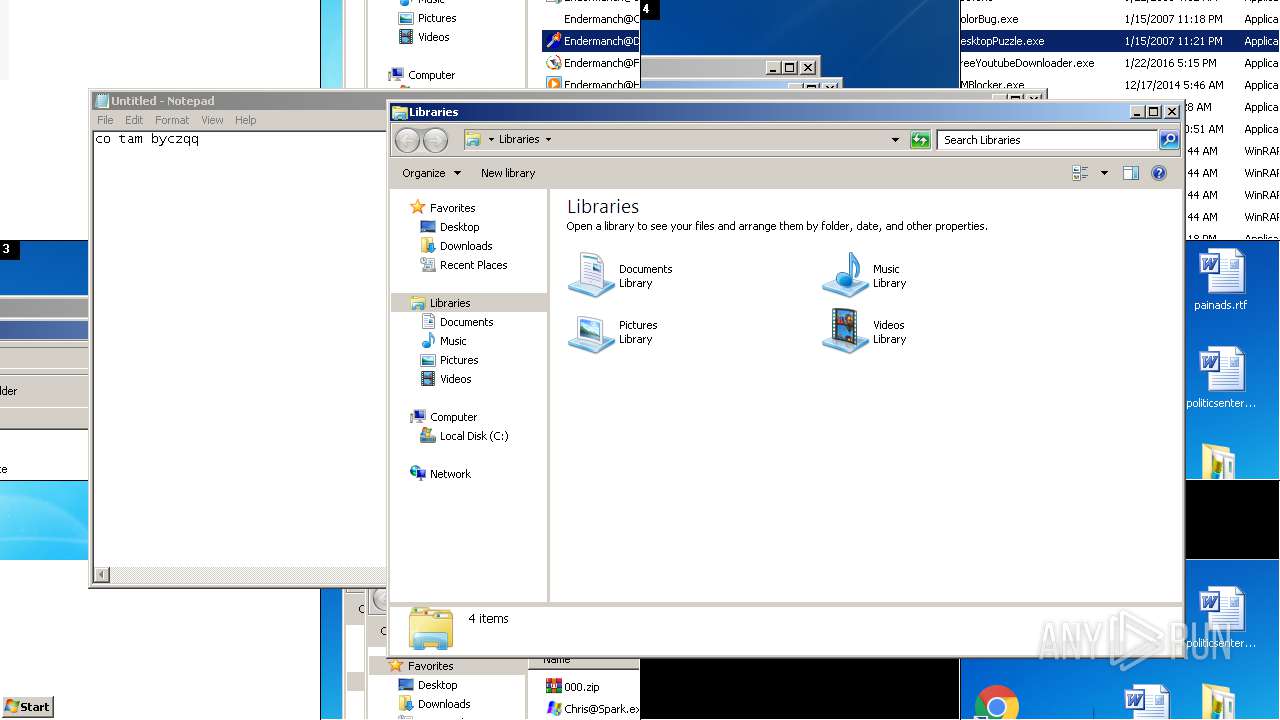
- explorer.exe (PID: 4052)
- Endermanch@MEMZ.exe (PID: 2928)
- Endermanch@FreeYoutubeDownloader.exe (PID: 2244)
- Endermanch@FreeYoutubeDownloader.exe (PID: 3860)
- Endermanch@DesktopPuzzle.exe (PID: 3816)
- explorer.exe (PID: 3840)
- Endermanch@HMBlocker.exe (PID: 3280)
- Endermanch@000.exe (PID: 2208)
- Endermanch@000.exe (PID: 3112)
- Endermanch@HMBlocker.exe (PID: 552)
- Endermanch@DesktopPuzzle.exe (PID: 608)
- Endermanch@MEMZ.exe (PID: 1812)
- Endermanch@HMBlocker.exe (PID: 1832)
- Endermanch@HMBlocker.exe (PID: 1084)
- WinRAR.exe (PID: 3548)
Reads the hosts file
- chrome.exe (PID: 2892)
- chrome.exe (PID: 4088)
Reads Internet Cache Settings
- chrome.exe (PID: 4088)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 944)
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 1448)
Reads settings of System Certificates
- chrome.exe (PID: 2892)
- iexplore.exe (PID: 1448)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 944)
- iexplore.exe (PID: 3968)
Creates files in the user directory
- iexplore.exe (PID: 1448)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 944)
Changes internet zones settings
- iexplore.exe (PID: 3968)
Reads internet explorer settings
- iexplore.exe (PID: 1448)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 944)
Changes settings of System certificates
- iexplore.exe (PID: 944)
- iexplore.exe (PID: 1448)
Adds / modifies Windows certificates
- iexplore.exe (PID: 944)
- iexplore.exe (PID: 1448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
69
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9300002264985639560,11788275974485487918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4932885503081529544 --mojo-platform-channel-handle=3572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 480 | "C:\Windows\System32\shutdown.exe" /r /t 6 /f | C:\Windows\System32\shutdown.exe | — | Endermanch@HMBlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 1190 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Users\admin\Desktop\trojans\Endermanch@HMBlocker.exe" | C:\Users\admin\Desktop\trojans\Endermanch@HMBlocker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9300002264985639560,11788275974485487918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9089296016271748326 --mojo-platform-channel-handle=4344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
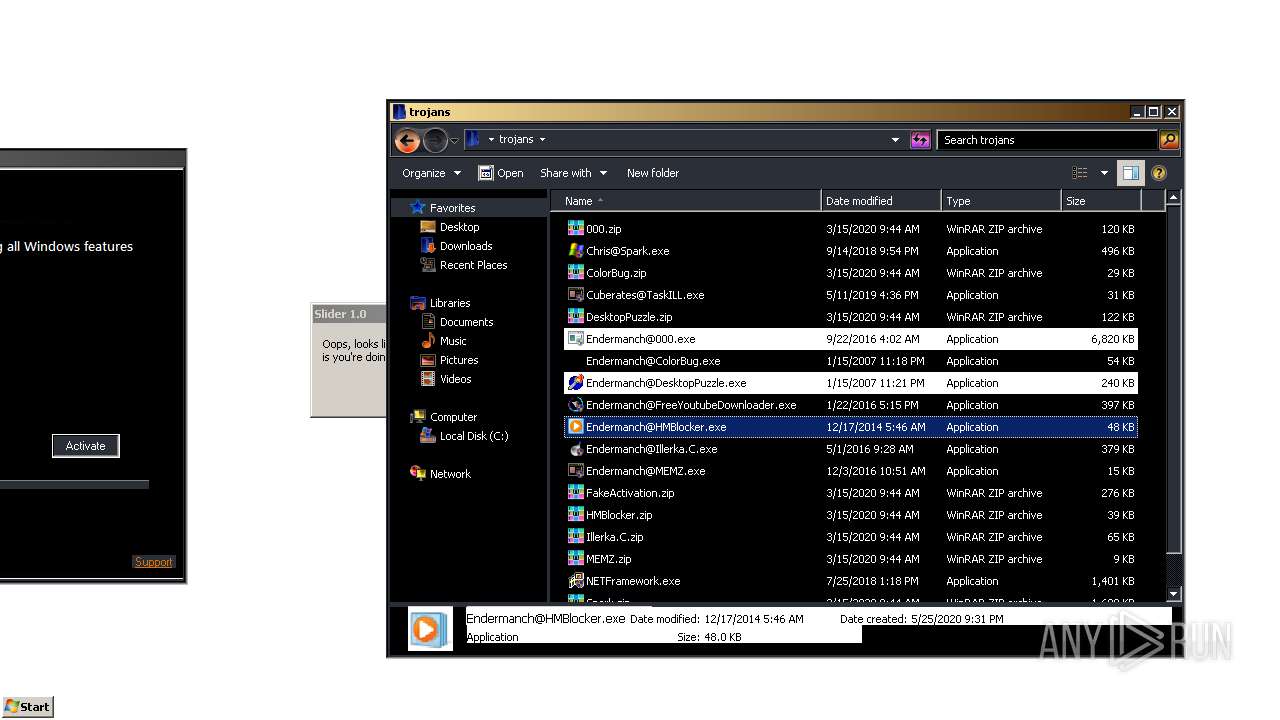
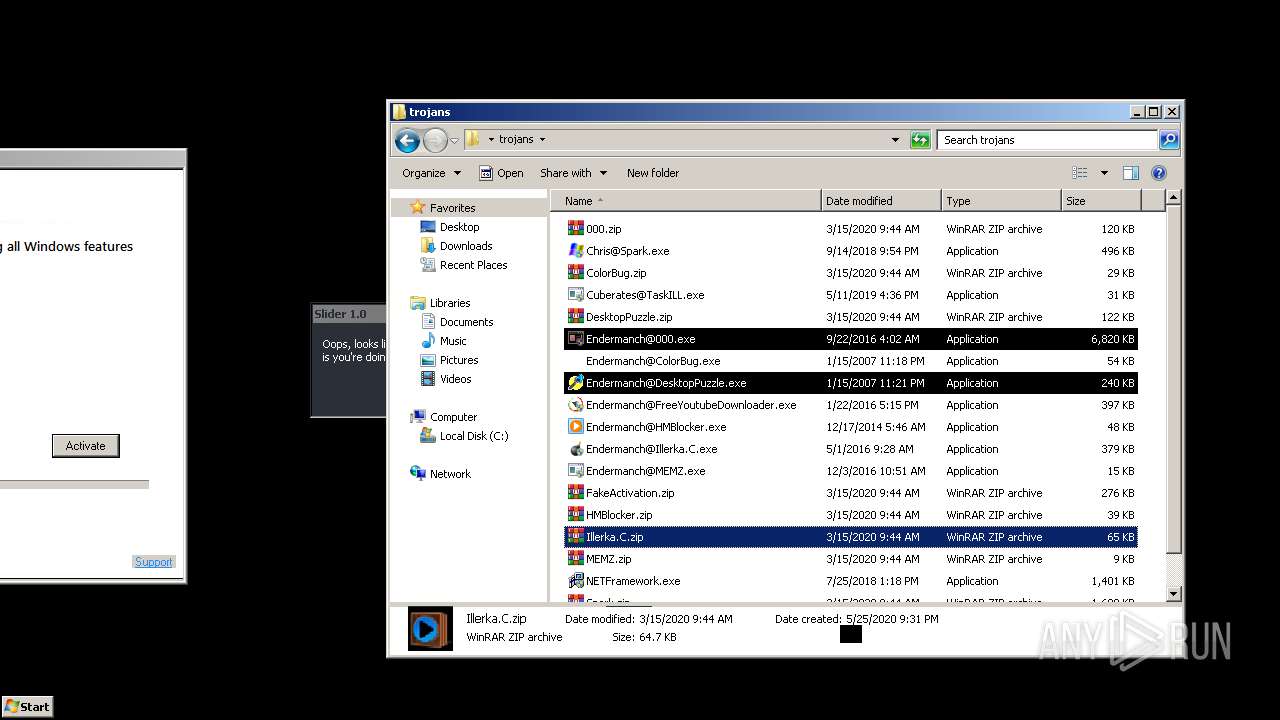
| 608 | "C:\Users\admin\Desktop\trojans\Endermanch@DesktopPuzzle.exe" | C:\Users\admin\Desktop\trojans\Endermanch@DesktopPuzzle.exe | — | explorer.exe | |||||||||||
User: admin Company: Andy Feys Integrity Level: MEDIUM Description: Slider Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 792 | "C:\Windows\Free Youtube Downloader\Free Youtube Downloader\Free YouTube Downloader.exe" | C:\Windows\Free Youtube Downloader\Free Youtube Downloader\Free YouTube Downloader.exe | — | Endermanch@FreeYoutubeDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Free YouTube Downloader Exit code: 0 Version: 4.1.1.1 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9300002264985639560,11788275974485487918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6643297934160523513 --mojo-platform-channel-handle=3672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9300002264985639560,11788275974485487918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14369186949153405415 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3968 CREDAT:472084 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1064 | "C:\Windows\System32\cmd.exe" /c REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v 2503326475 /t REG_SZ /d "C:\Users\admin\2503326475\2503326475.exe" /f | C:\Windows\System32\cmd.exe | — | Endermanch@HMBlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 963
Read events
3 345
Write events
1 612
Delete events
6
Modification events
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4088-13234912180104125 |
Value: 259 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
15
Suspicious files
150
Text files
343
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ECC2AB4-FF8.pma | — | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5656ac4a-dfdd-4f7d-a408-d1b1166ff40a.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa884a0.TMP | text | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa8852c.TMP | text | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa88701.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
113
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
944 | iexplore.exe | GET | 301 | 151.101.1.132:80 | http://motherboard.vice.com/read/watch-this-malware-turn-a-computer-into-a-digital-hellscape | US | — | — | whitelisted |
2892 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2892 | chrome.exe | GET | 200 | 173.194.160.200:80 | http://r2---sn-hpa7zn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.128.27.151&mm=28&mn=sn-hpa7zn76&ms=nvh&mt=1590438491&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2892 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
1448 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1448 | iexplore.exe | GET | 429 | 216.58.207.36:80 | http://www.google.com/sorry/index?continue=http://google.co.ck/search%3Fq%3Dmy%2Bcomputer%2Bis%2Bdoing%2Bweird%2Bthings%2Bwtf%2Bis%2Bhappenin%2Bplz%2Bhalp&q=EgS5gBuXGMDWsPYFIhkA8aeDS0kq_qmS-SZ8N0UMNuzRH422yezZMgFy | US | html | 2.92 Kb | malicious |
944 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCJIRnrbzaAWwIAAAAAZzJX | US | der | 472 b | whitelisted |
944 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCJIRnrbzaAWwIAAAAAZzJX | US | der | 472 b | whitelisted |
1448 | iexplore.exe | GET | 302 | 172.217.22.36:80 | http://google.co.ck/search?q=my+computer+is+doing+weird+things+wtf+is+happenin+plz+halp | US | html | 414 b | whitelisted |
1448 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDvkDzv2QYa2AgAAAABnMwk%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 140.82.118.3:443 | — | — | US | malicious |
2892 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2892 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 172.217.21.202:443 | github.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 151.101.0.133:443 | avatars2.githubusercontent.com | Fastly | US | malicious |
2892 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2892 | chrome.exe | 3.214.233.124:443 | collector.githubapp.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
avatars0.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |