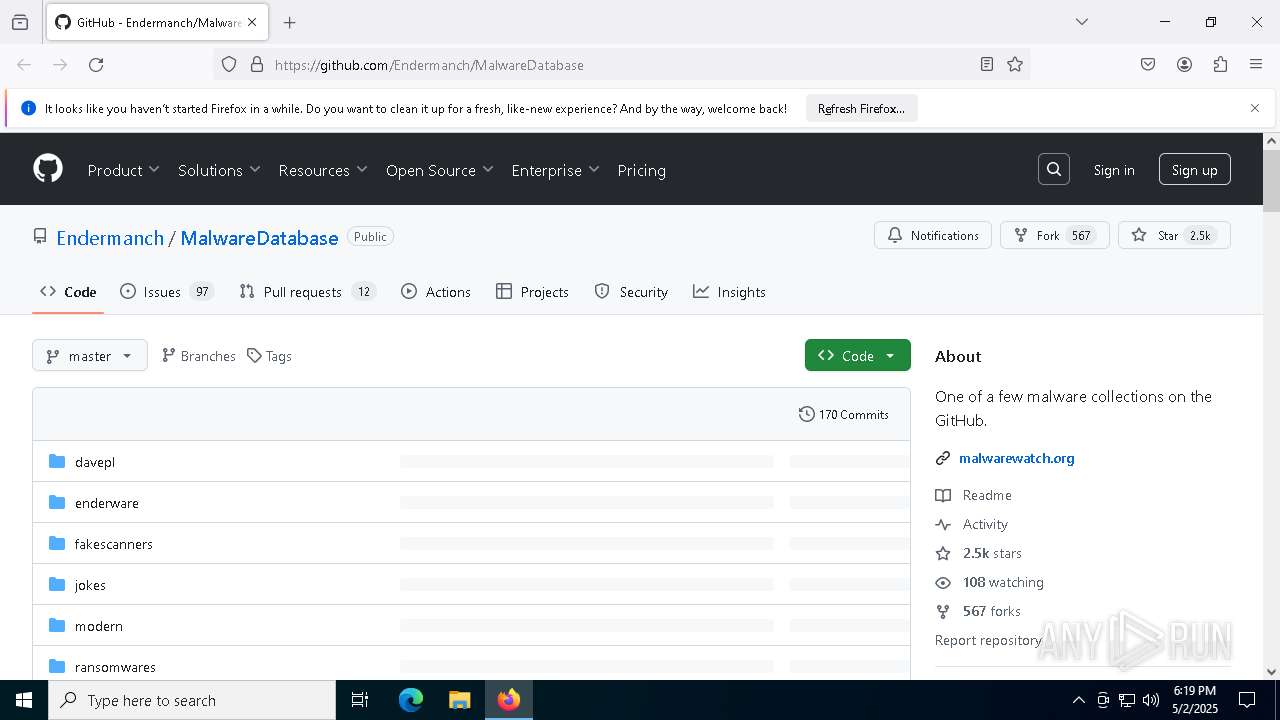
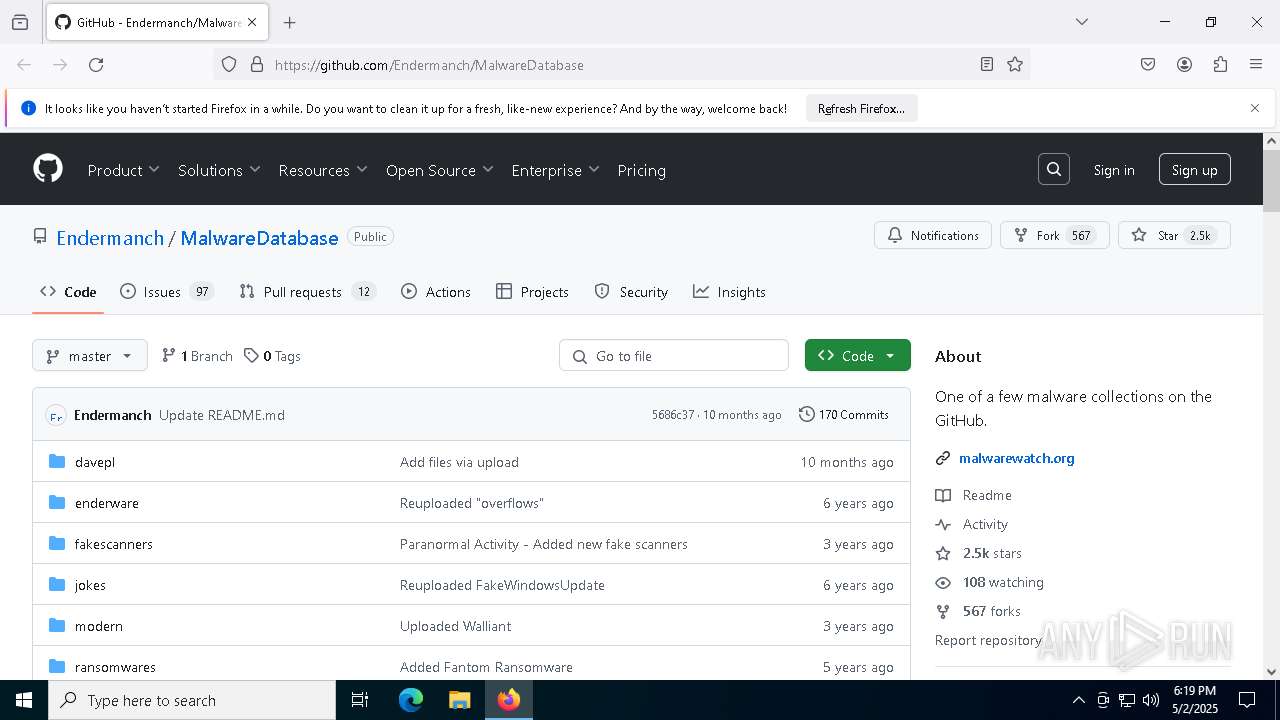
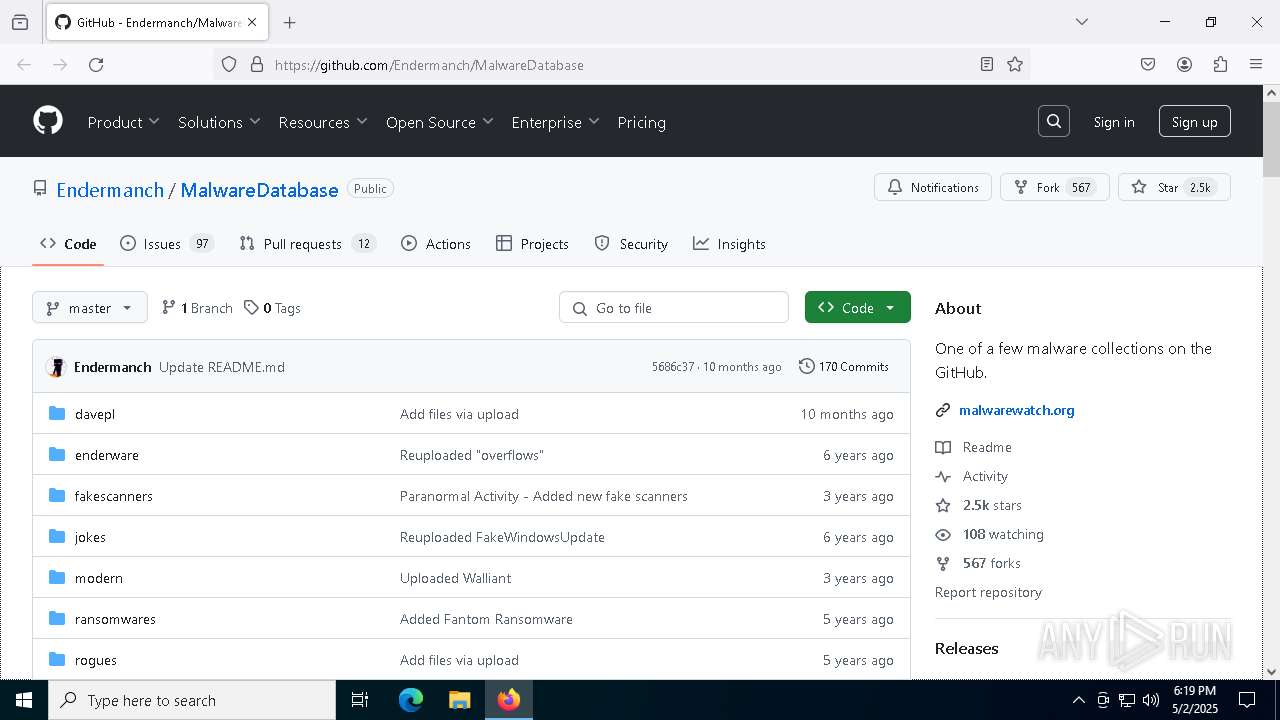
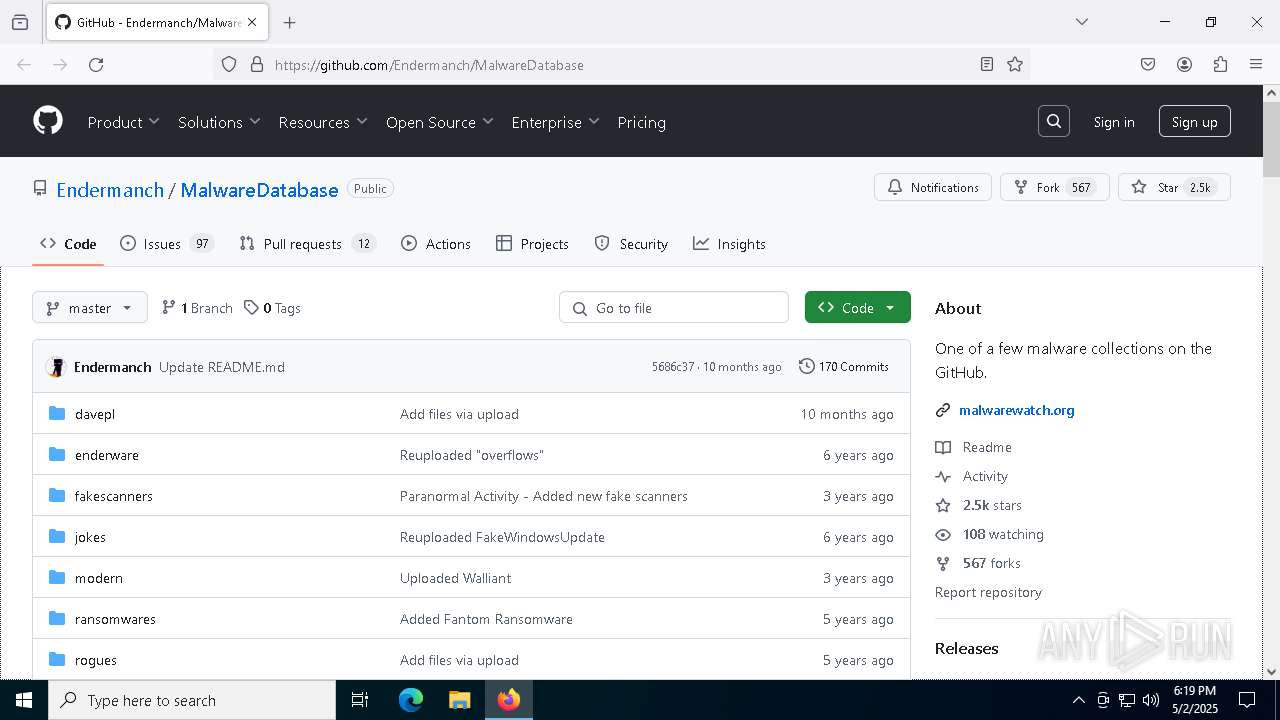
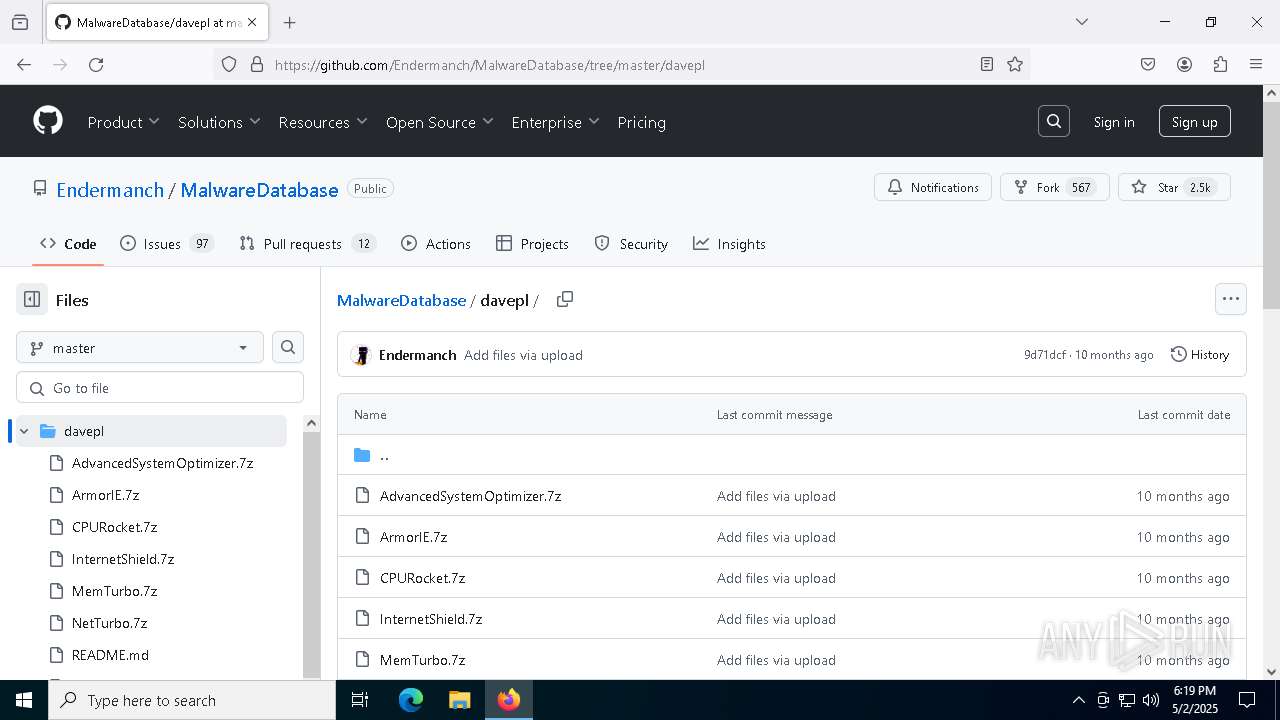
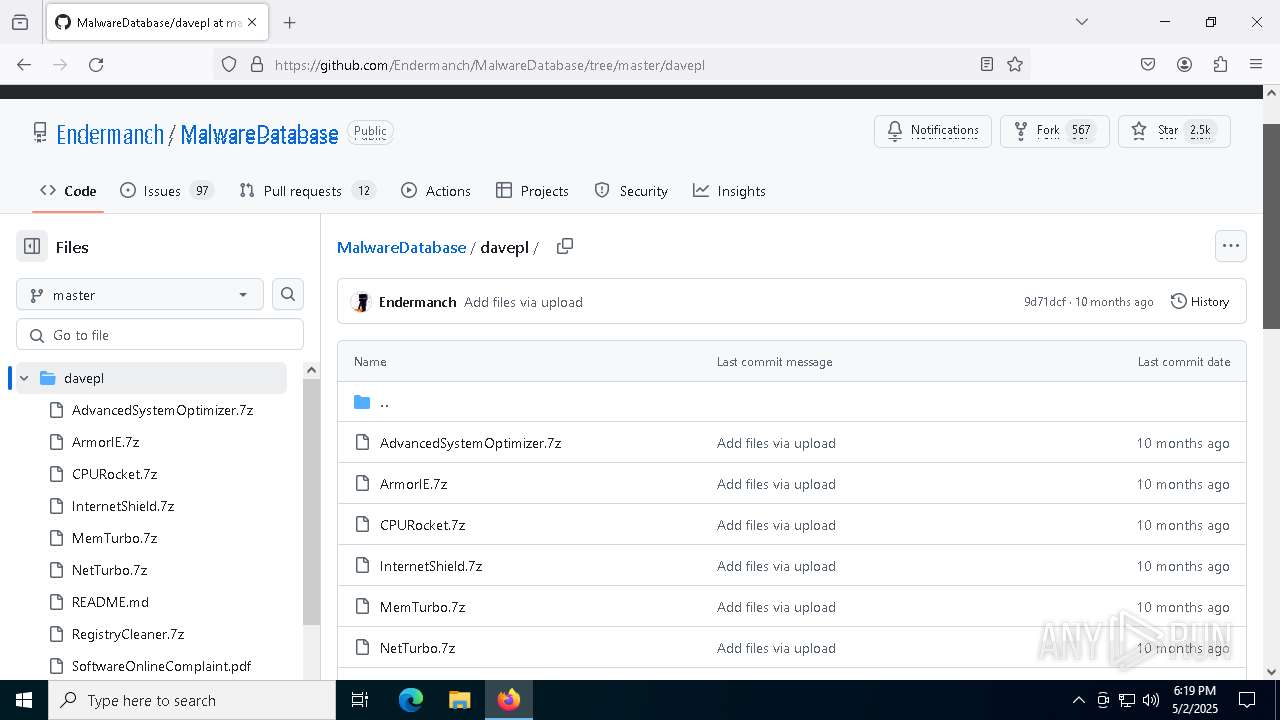
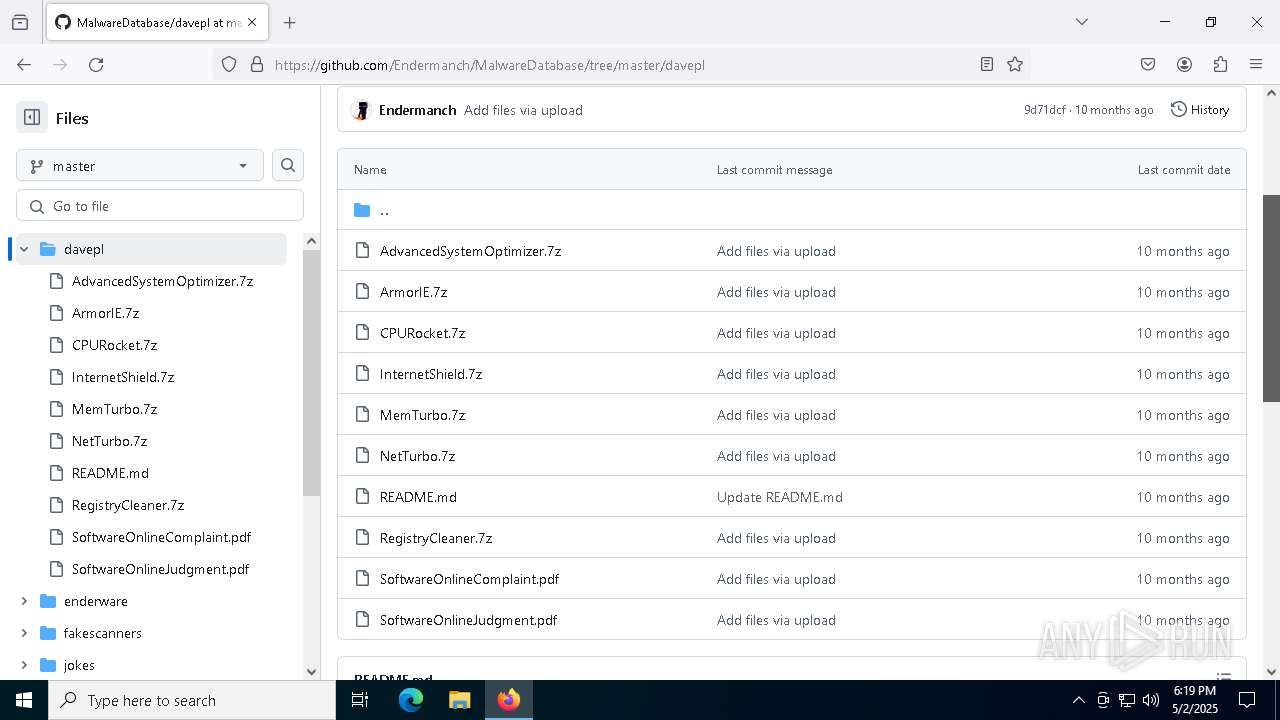
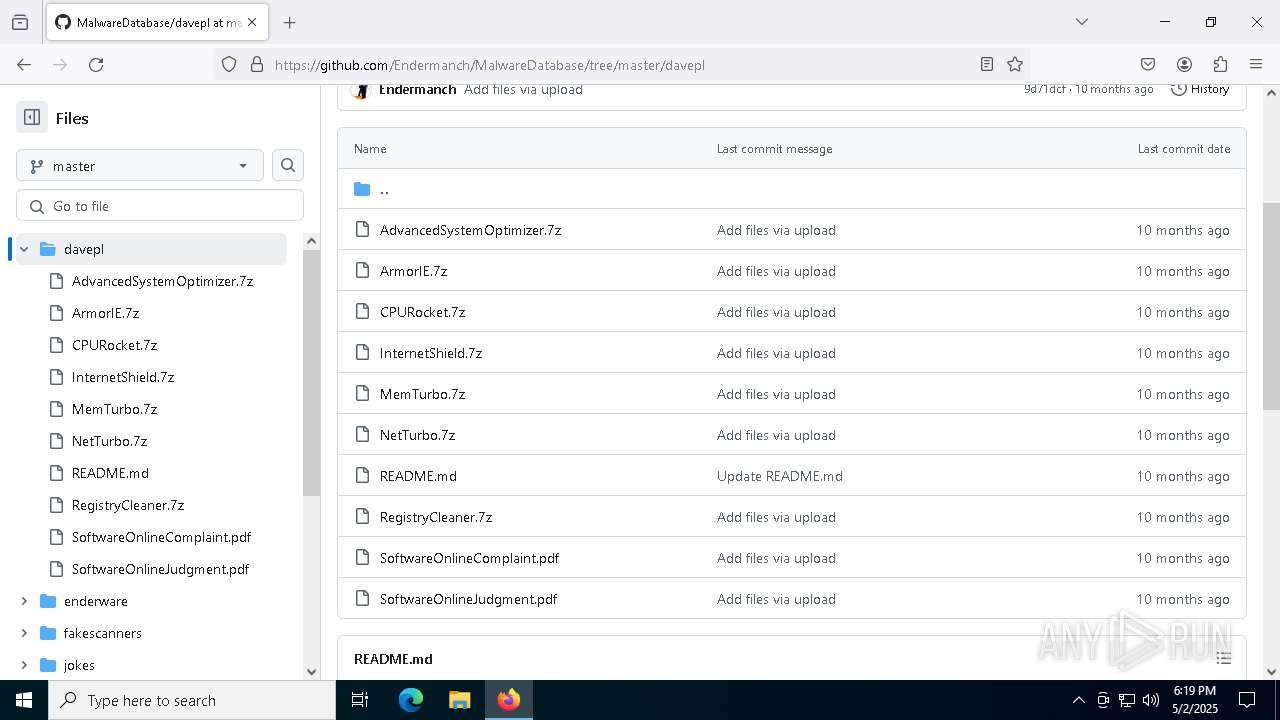
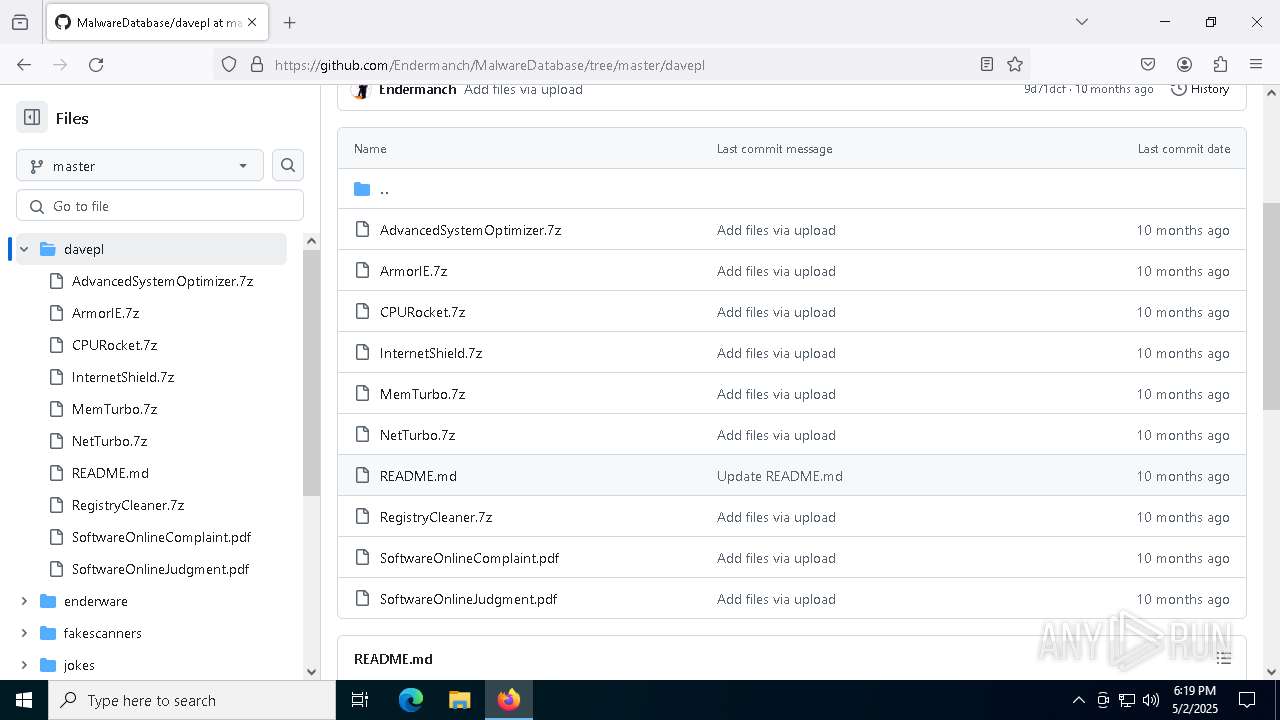
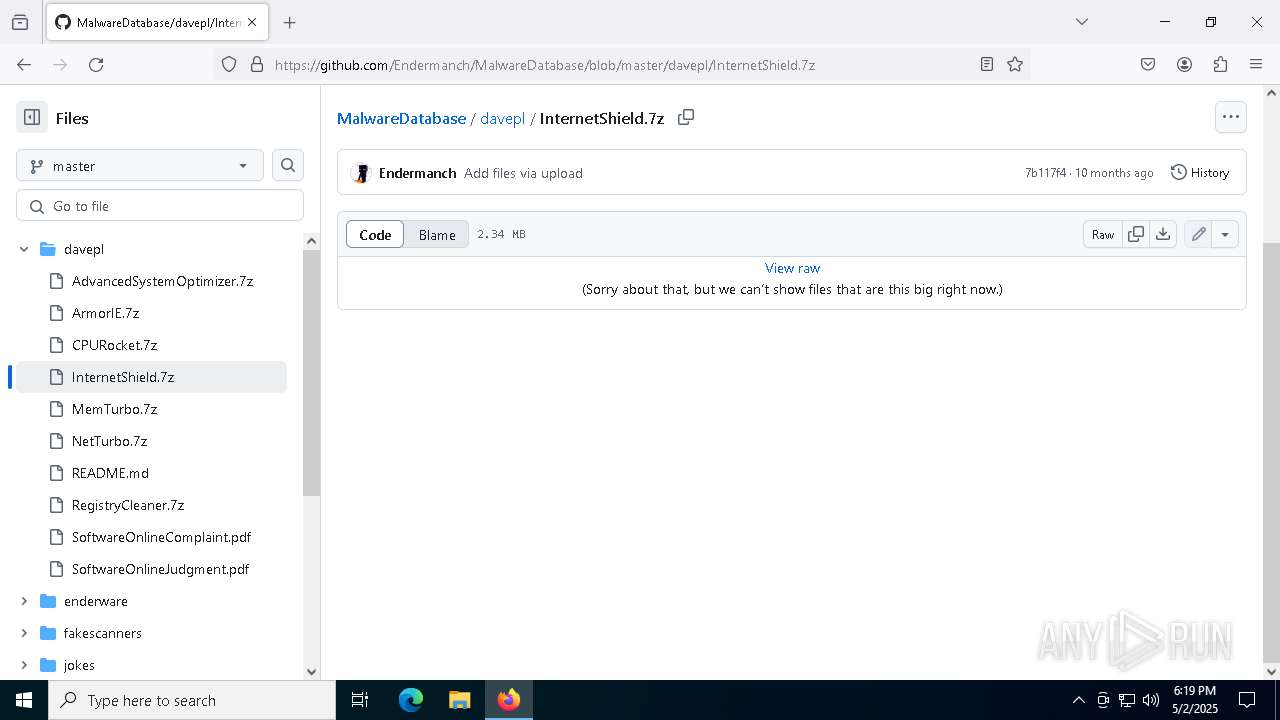
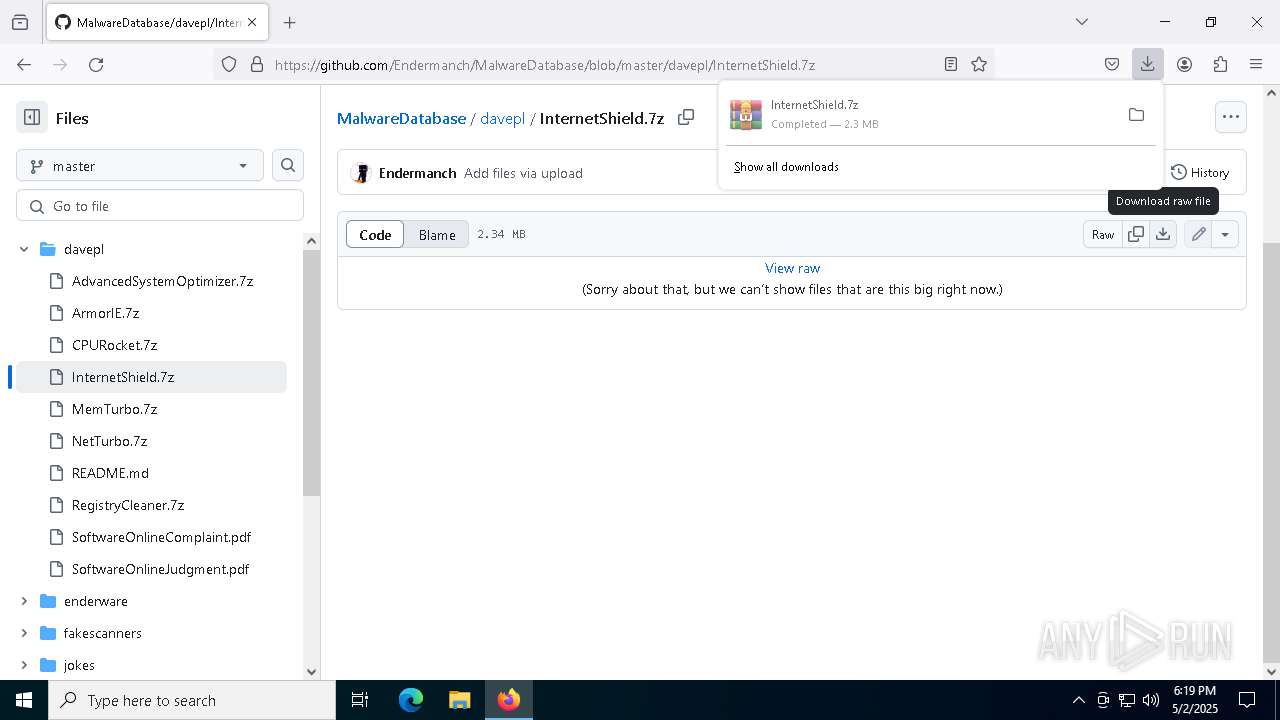
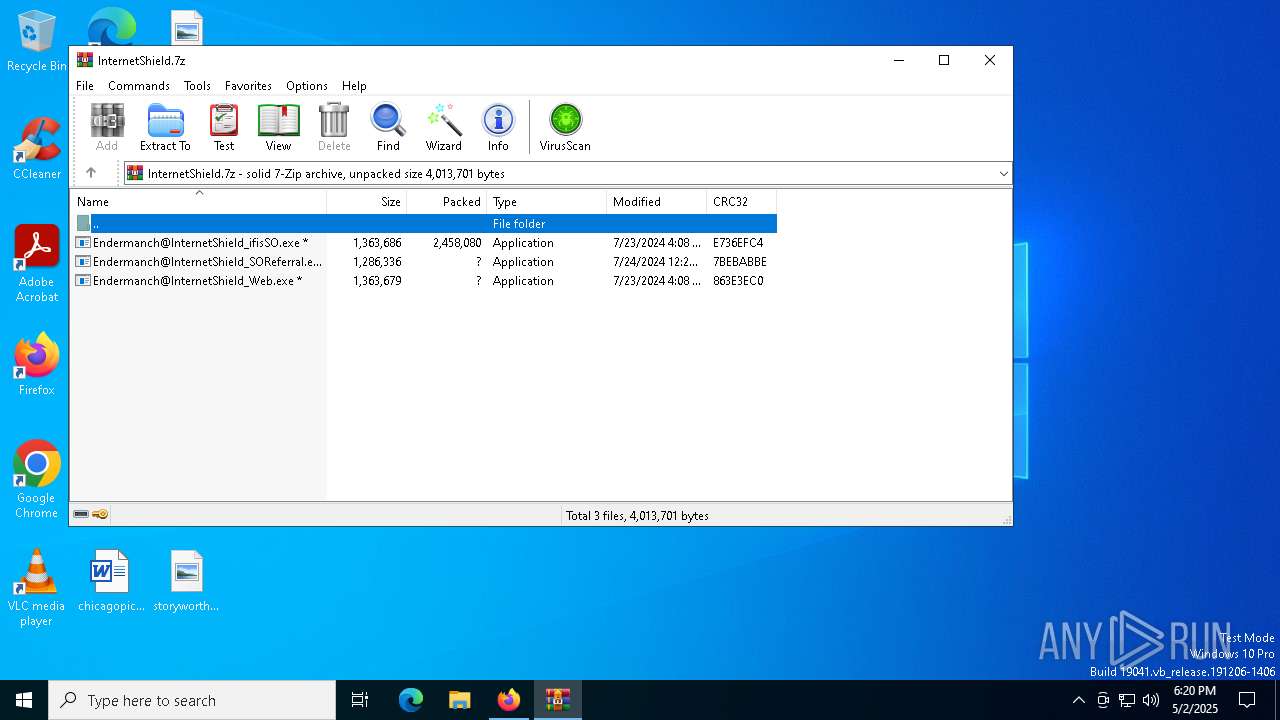
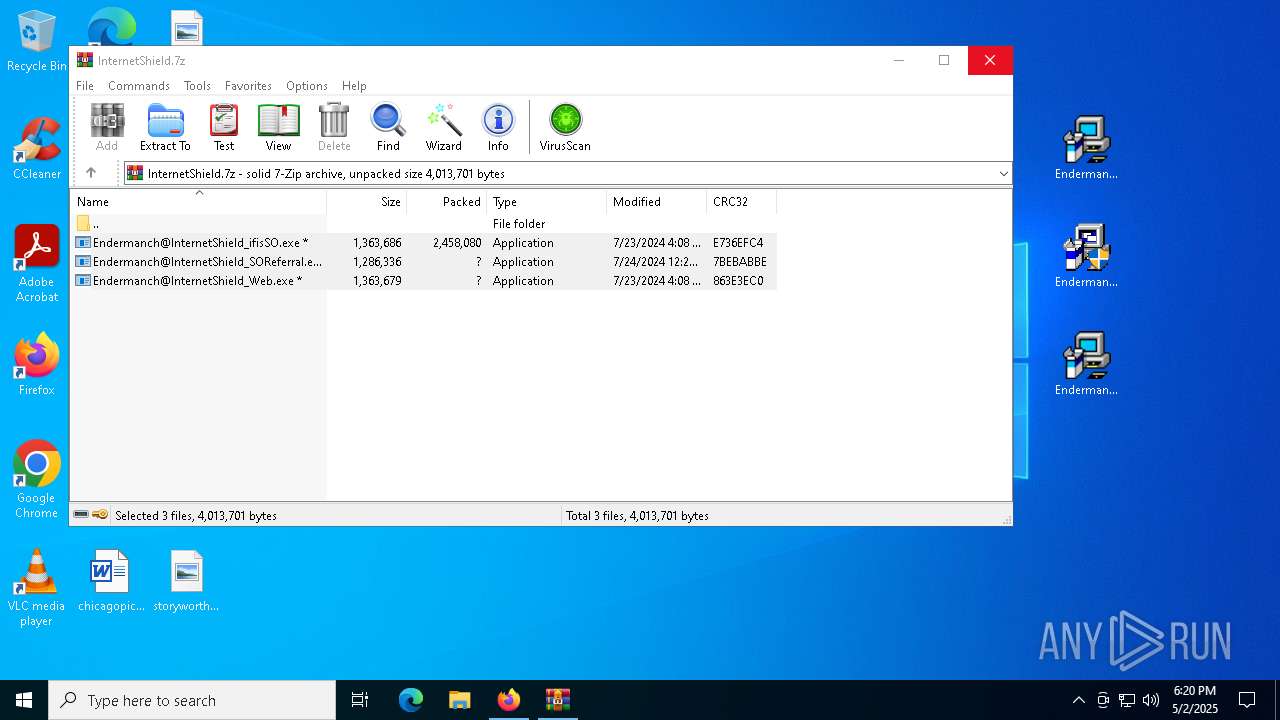
| URL: | https://github.com/Endermanch/MalwareDatabase |
| Full analysis: | https://app.any.run/tasks/a8eab7d4-cb40-4f1d-94fe-5c34054f146e |
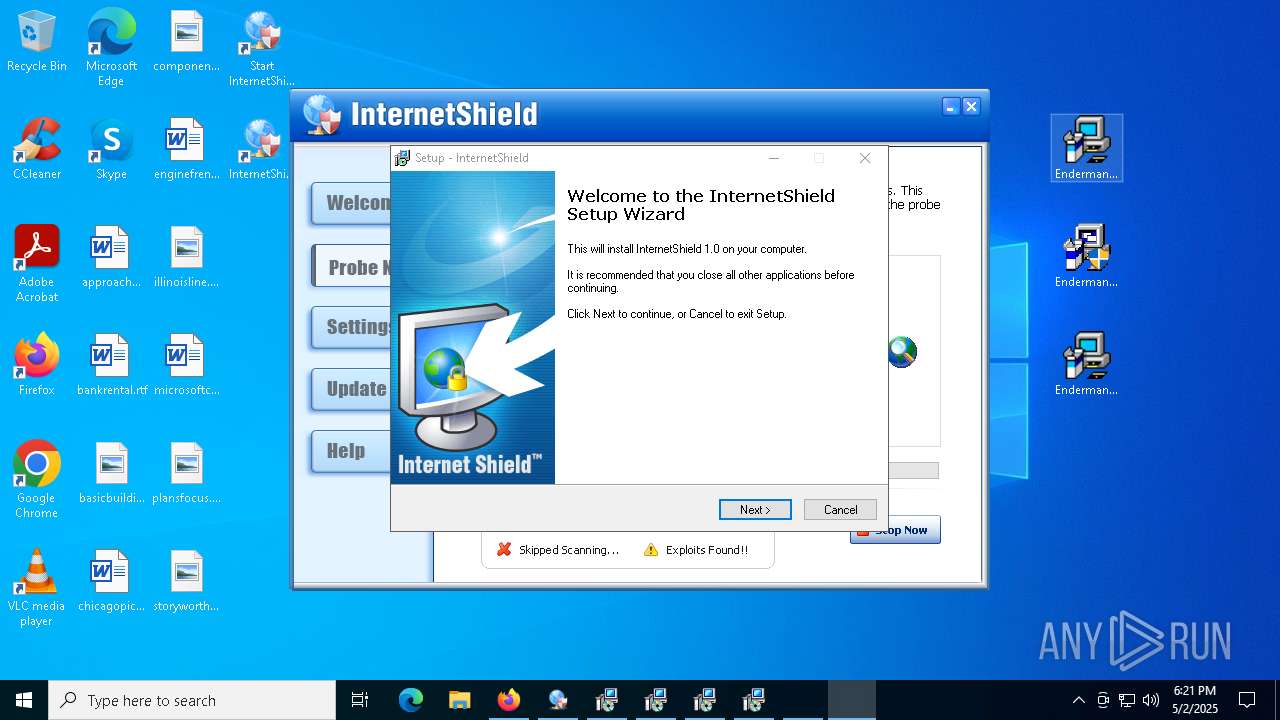
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2025, 18:19:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
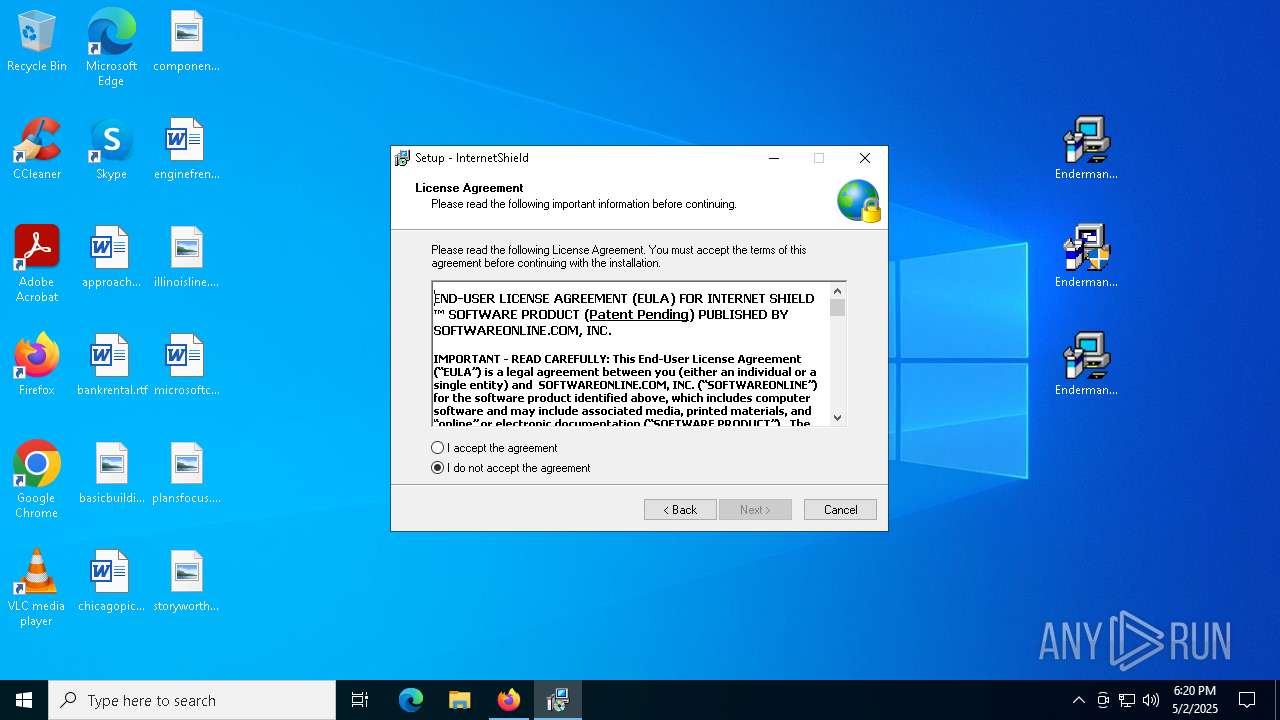
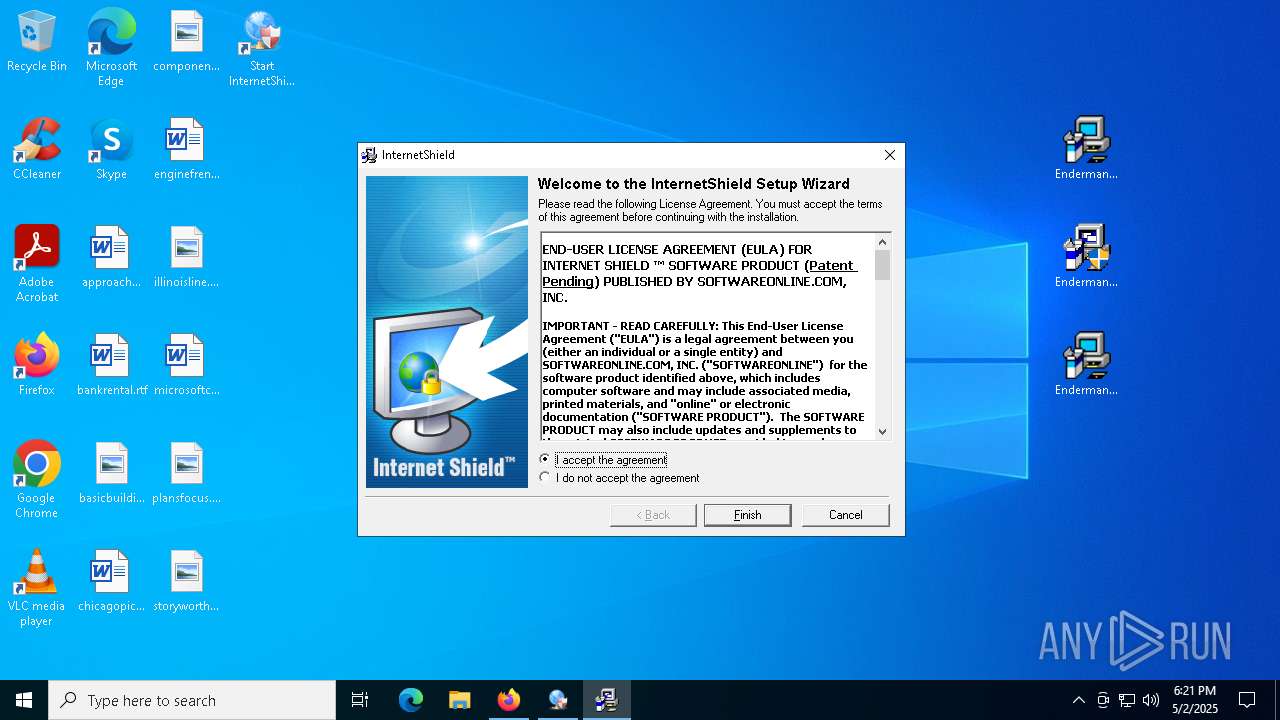
MALICIOUS
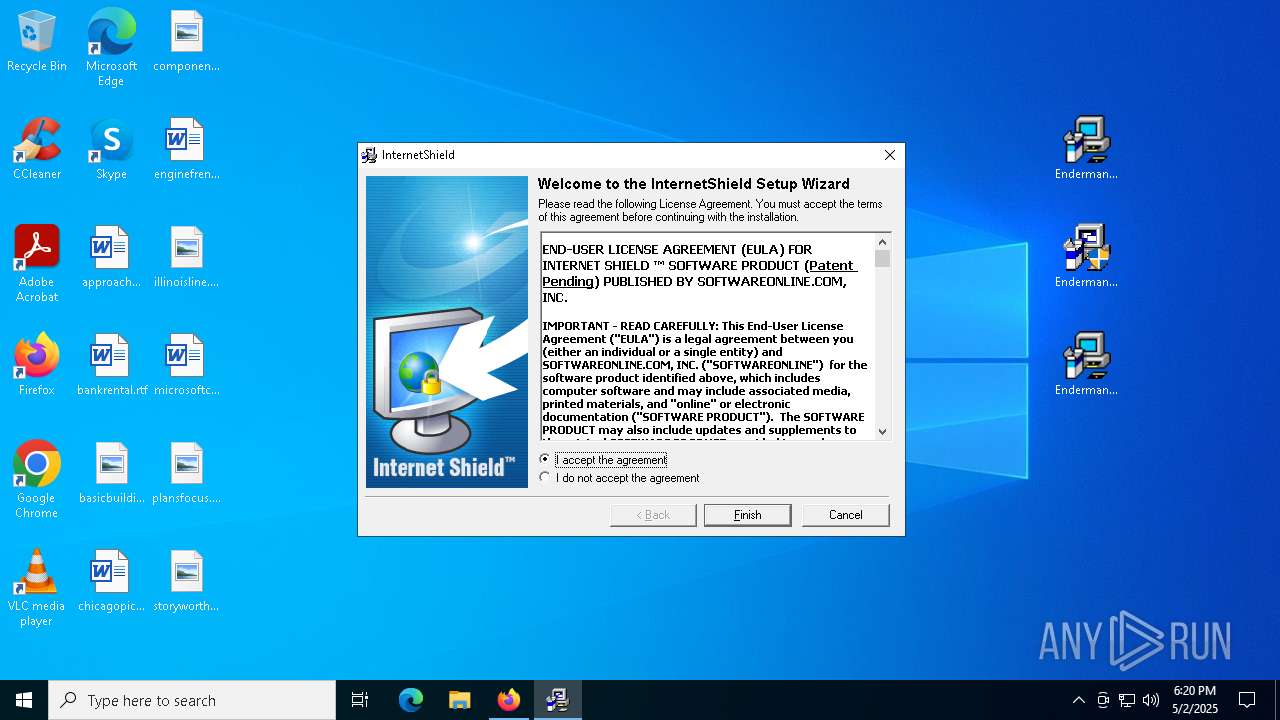
Executing a file with an untrusted certificate
- Endermanch@InternetShield_SOReferral.exe (PID: 9076)
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- Endermanch@InternetShield_SOReferral.exe (PID: 3100)
- Endermanch@InternetShield_SOReferral.exe (PID: 536)
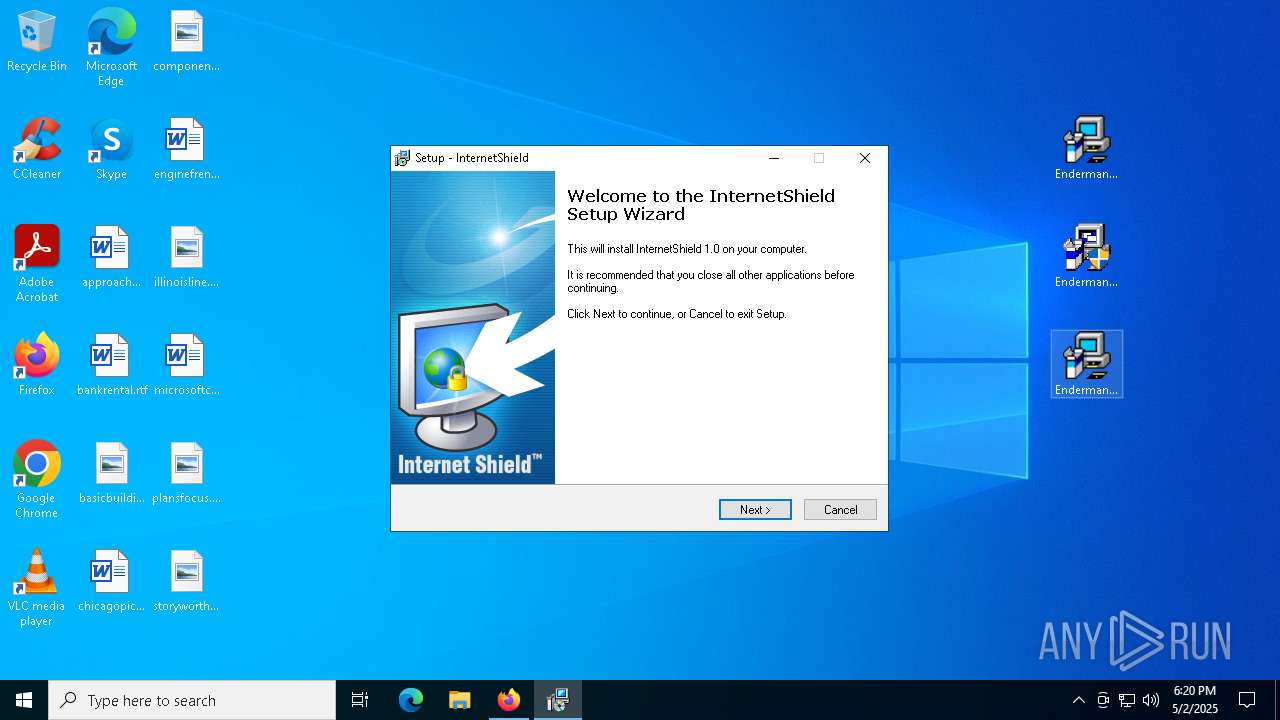
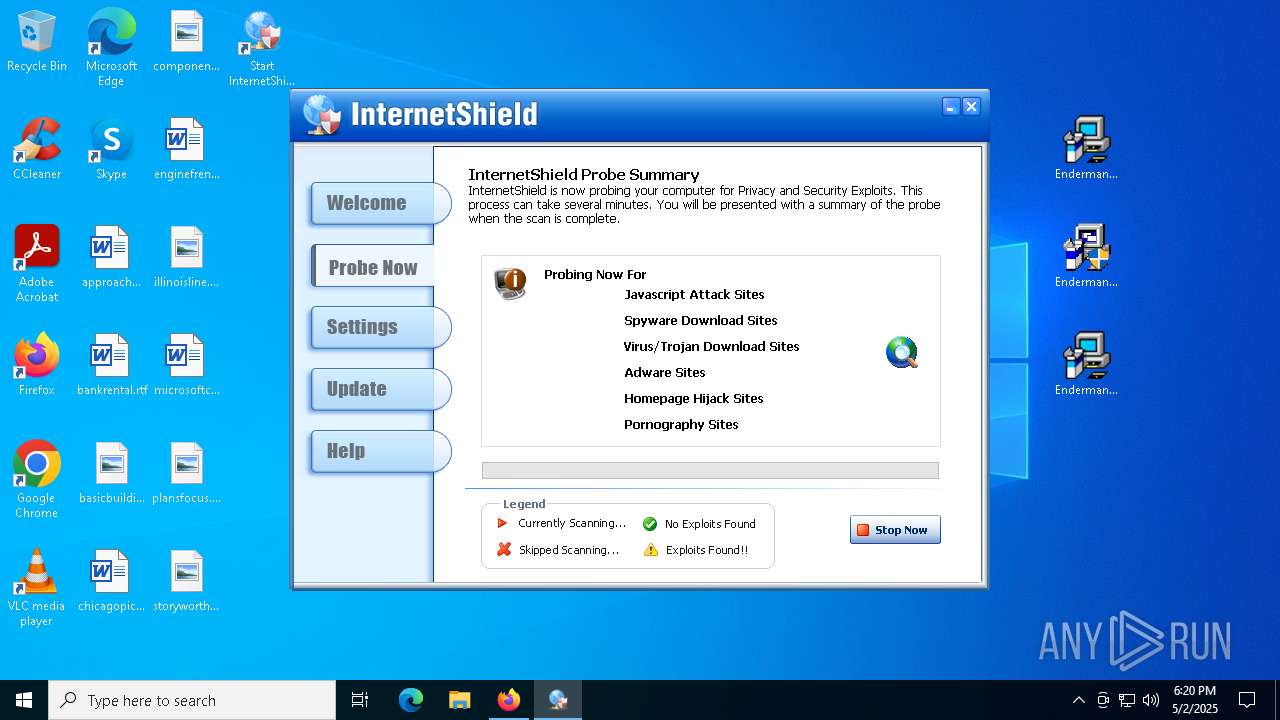
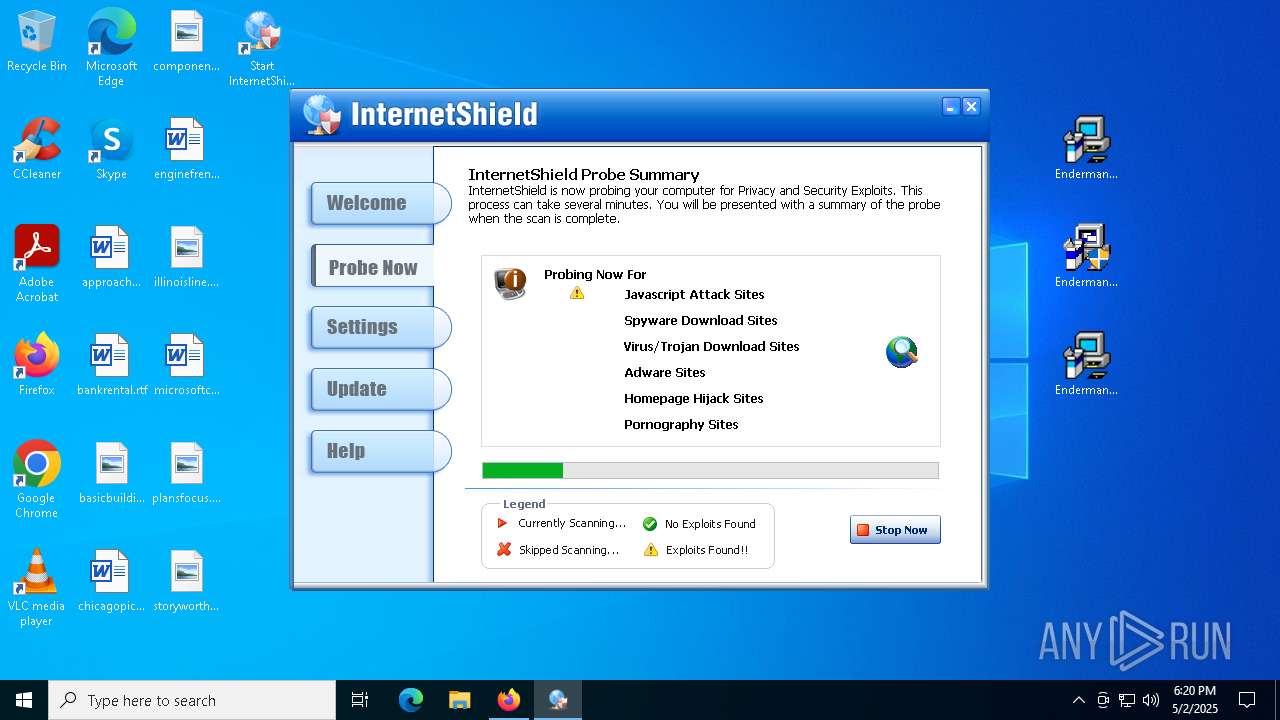
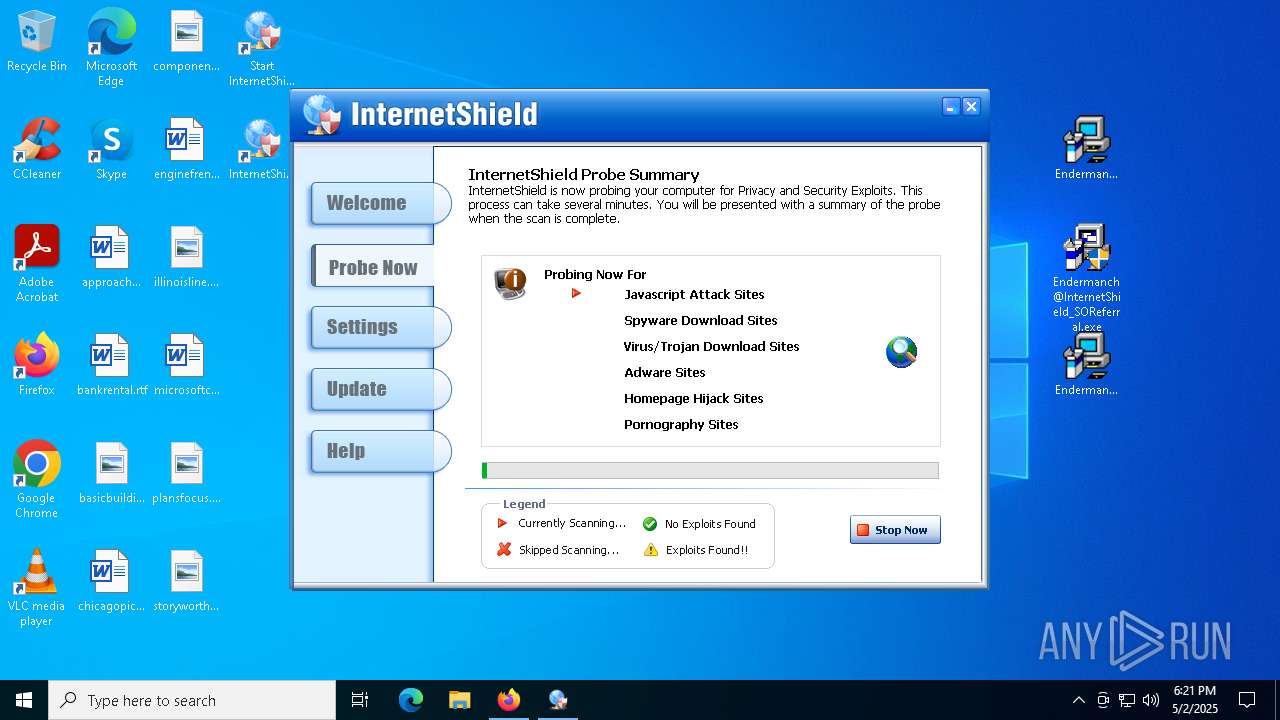
Changes the autorun value in the registry
- internetshield.exe (PID: 8352)
- is-I8K1F.tmp (PID: 8208)
SUSPICIOUS
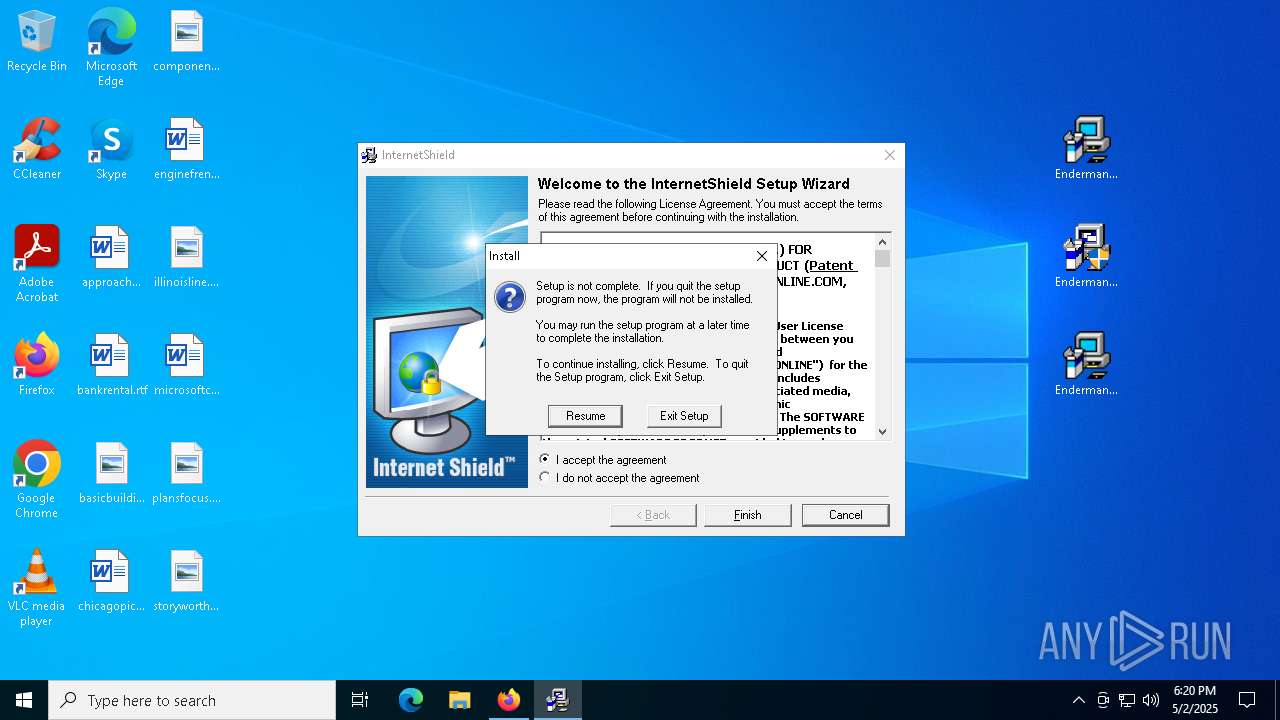
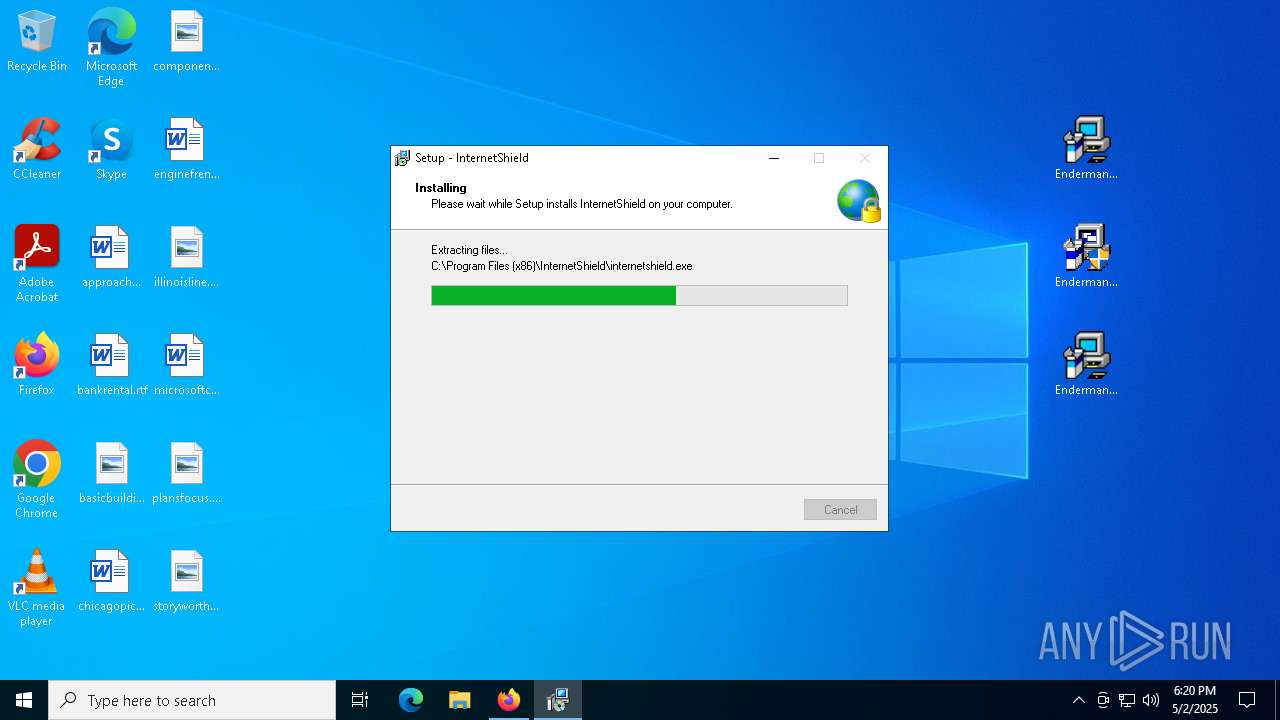
Executable content was dropped or overwritten
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- GLB8819.tmp (PID: 9136)
- setup_trial.exe (PID: 8304)
- is-I8K1F.tmp (PID: 8208)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- Endermanch@InternetShield_SOReferral.exe (PID: 536)
- GLBF41C.tmp (PID: 8500)
- setup_trial.exe (PID: 2664)
- is-SE22R.tmp (PID: 8892)
- setup_trial.exe (PID: 5332)
- is-QF72G.tmp (PID: 3176)
- setup_trial.exe (PID: 6004)
- is-QK8CT.tmp (PID: 3180)
- setup_trial.exe (PID: 8464)
- is-1KO6P.tmp (PID: 8784)
- setup_trial.exe (PID: 7400)
- setup_trial.exe (PID: 8260)
- is-V4ONP.tmp (PID: 240)
- is-071L2.tmp (PID: 2420)
- is-SL40M.tmp (PID: 6908)
- setup_trial.exe (PID: 736)
- setup_trial.exe (PID: 8392)
- is-IQI30.tmp (PID: 5812)
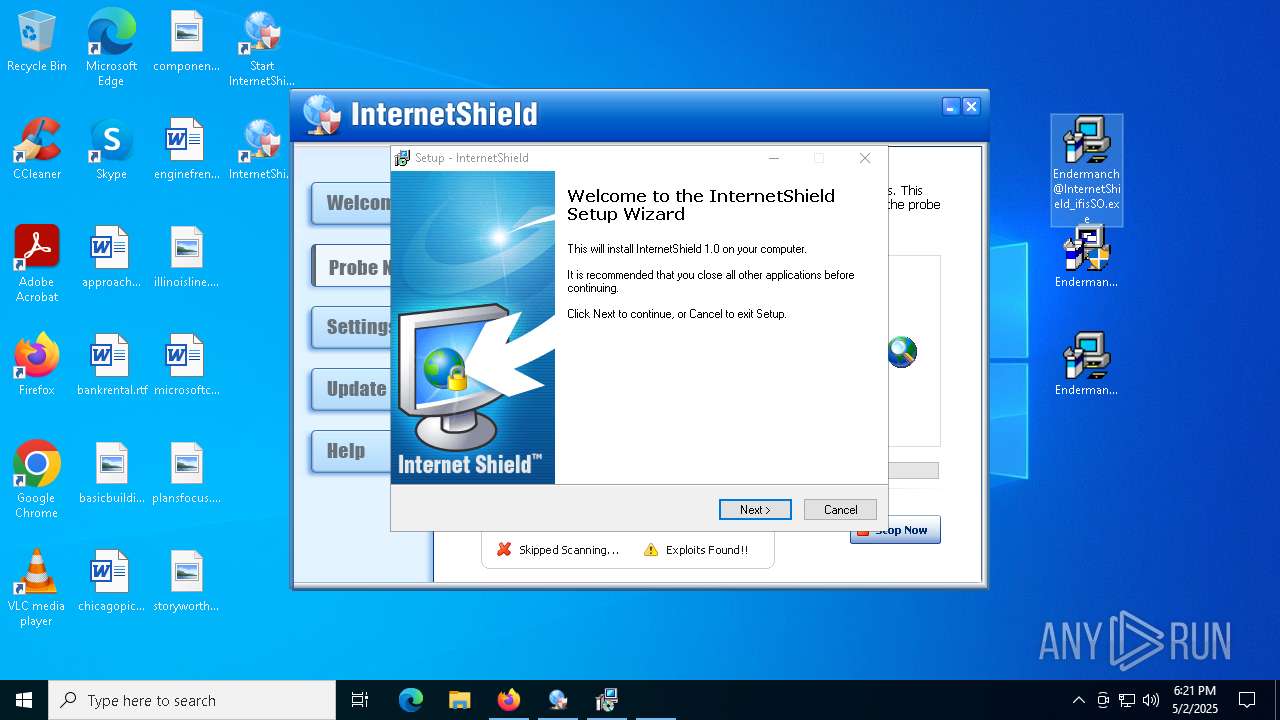
Starts application with an unusual extension
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- Endermanch@InternetShield_SOReferral.exe (PID: 536)
Process drops legitimate windows executable
- is-I8K1F.tmp (PID: 8208)
- is-SE22R.tmp (PID: 8892)
- is-QK8CT.tmp (PID: 3180)
- is-1KO6P.tmp (PID: 8784)
- is-071L2.tmp (PID: 2420)
- is-QF72G.tmp (PID: 3176)
- is-V4ONP.tmp (PID: 240)
- is-IQI30.tmp (PID: 5812)
- is-SL40M.tmp (PID: 6908)
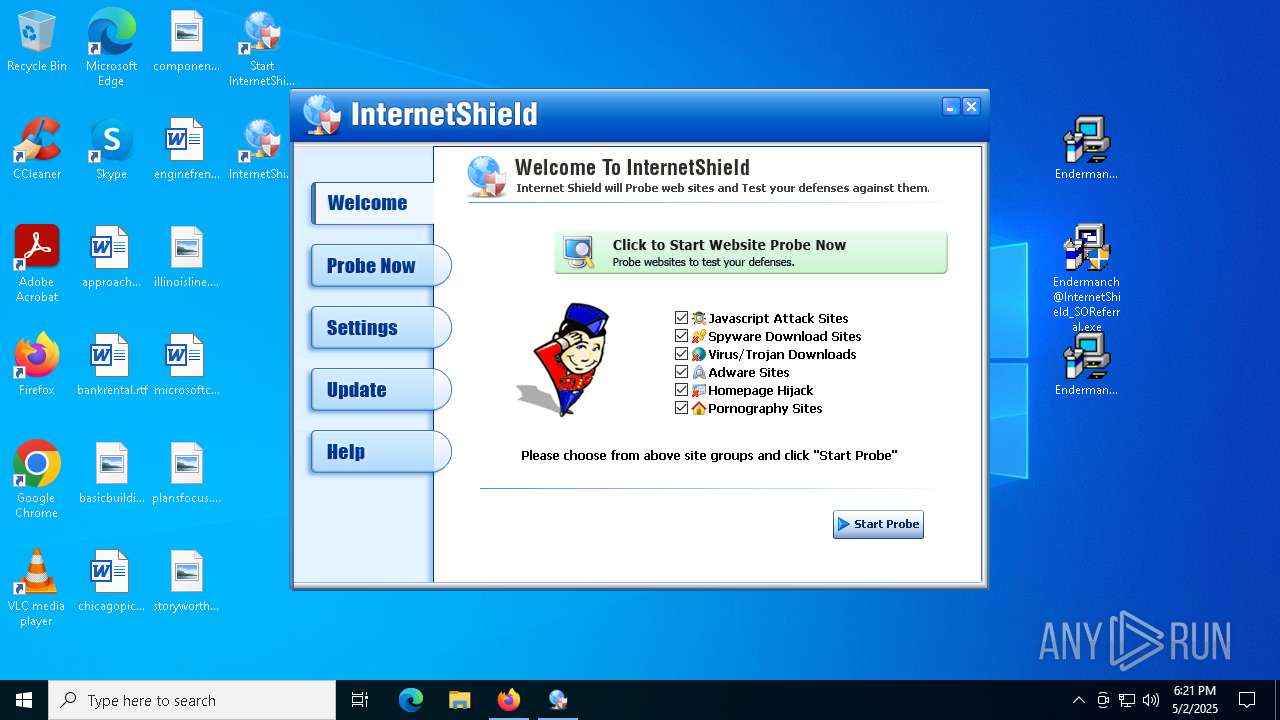
Reads security settings of Internet Explorer
- Endermanch@InternetShield_Web.exe (PID: 5364)
- internetshield.exe (PID: 8352)
Creates/Modifies COM task schedule object
- internetshield.exe (PID: 8352)
Reads Internet Explorer settings
- internetshield.exe (PID: 8352)
There is functionality for taking screenshot (YARA)
- internetshield.exe (PID: 8352)
Reads the BIOS version
- internetshield.exe (PID: 8352)
Reads Microsoft Outlook installation path
- internetshield.exe (PID: 8352)
INFO
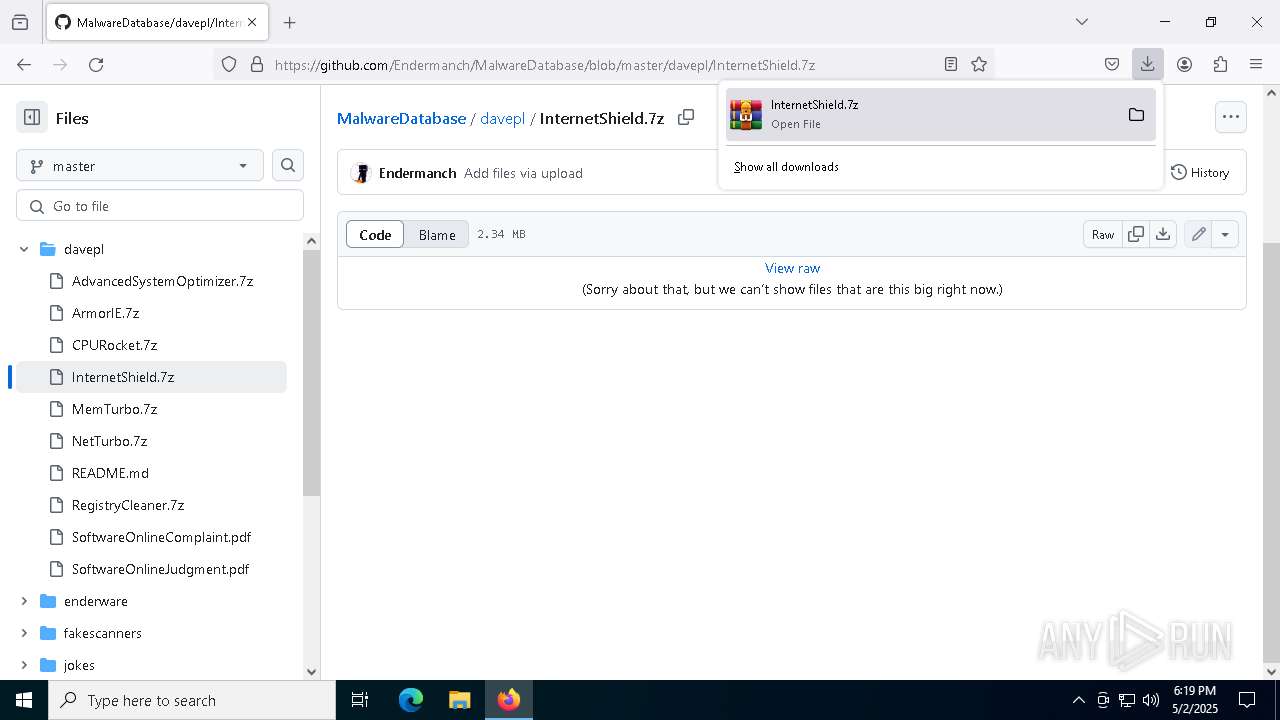
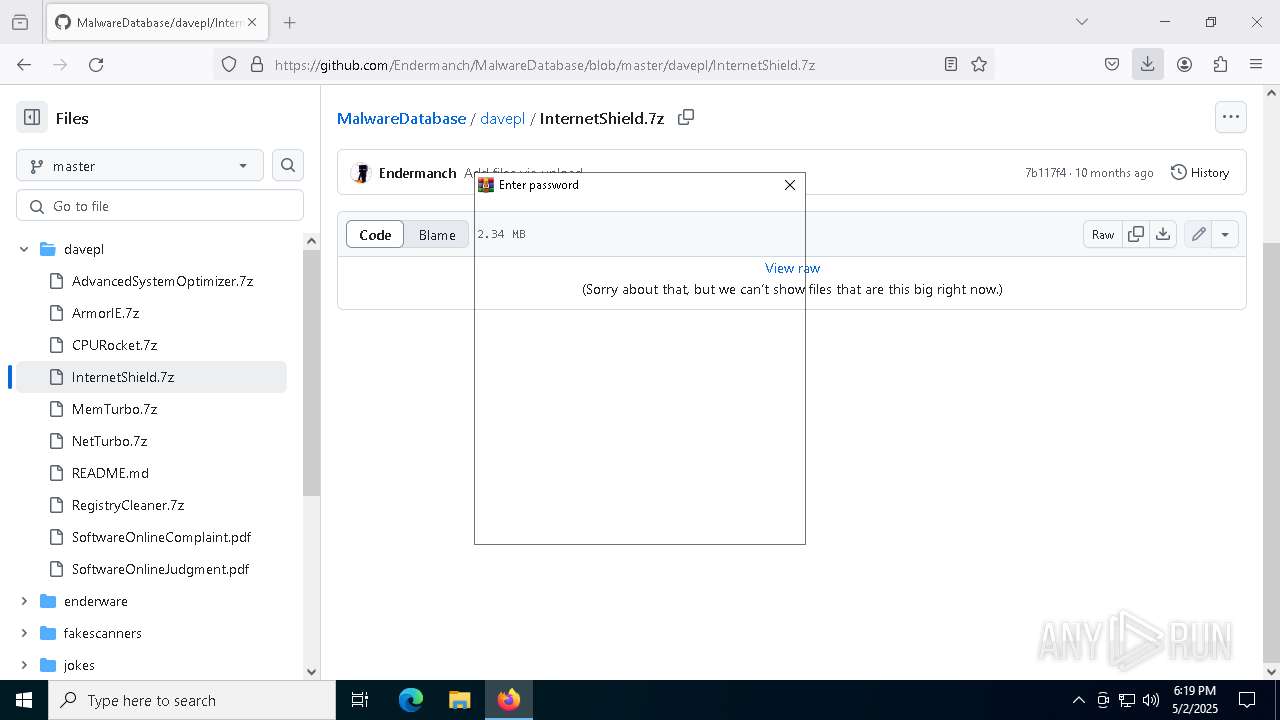
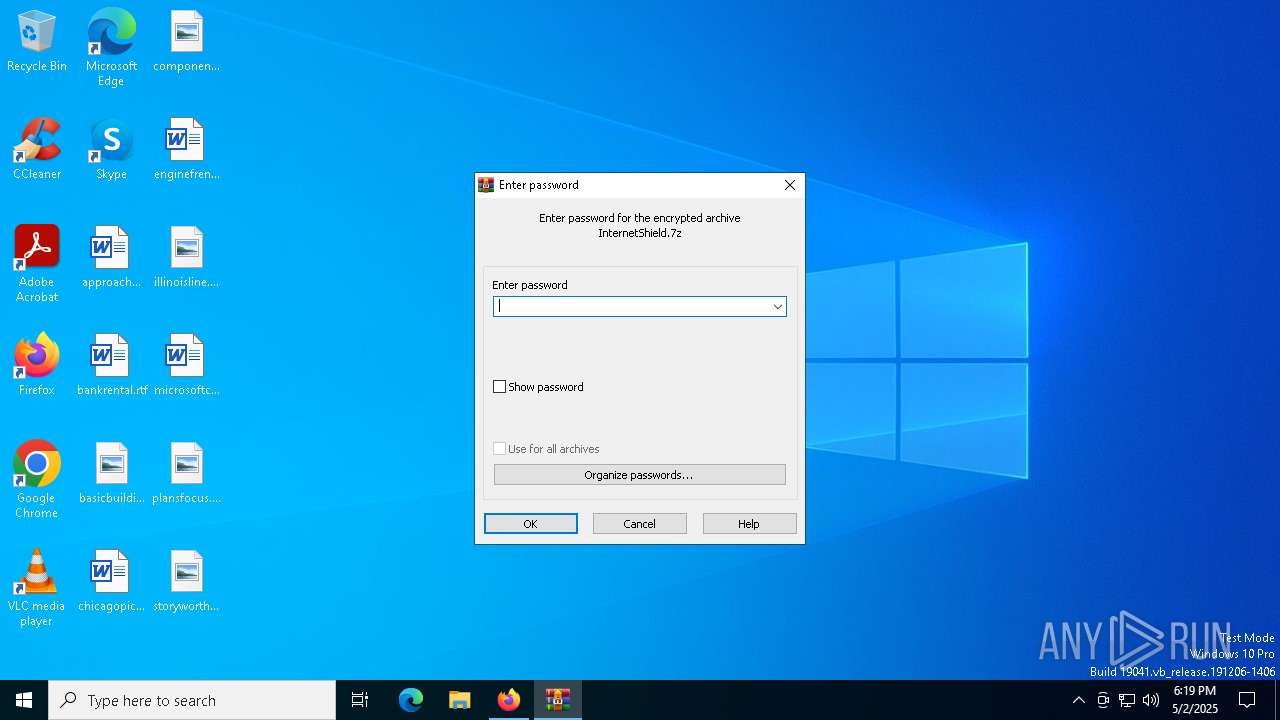
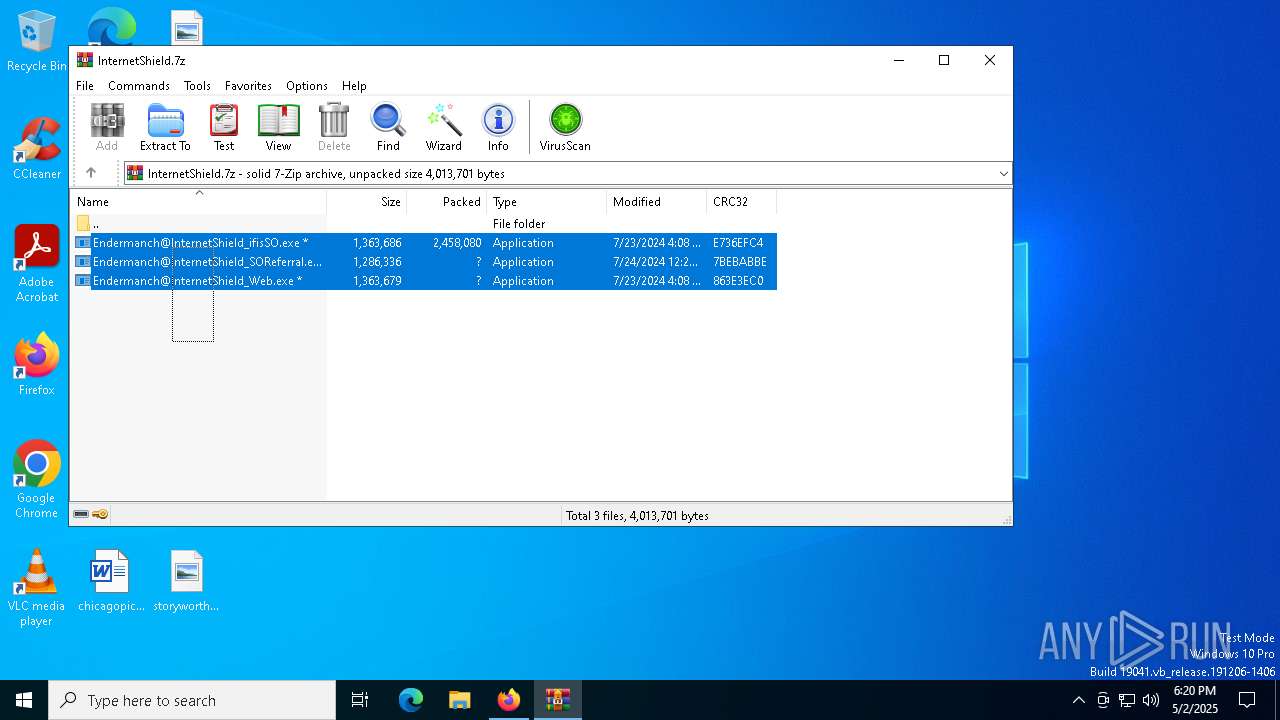
Manual execution by a user
- WinRAR.exe (PID: 8940)
- Endermanch@InternetShield_SOReferral.exe (PID: 9076)
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- msedge.exe (PID: 684)
- Endermanch@InternetShield_SOReferral.exe (PID: 3100)
- Endermanch@InternetShield_ifisSO.exe (PID: 3796)
- Endermanch@InternetShield_ifisSO.exe (PID: 6404)
- Endermanch@InternetShield_ifisSO.exe (PID: 4652)
- Endermanch@InternetShield_SOReferral.exe (PID: 536)
- Endermanch@InternetShield_ifisSO.exe (PID: 8848)
- Endermanch@InternetShield_ifisSO.exe (PID: 8996)
- Endermanch@InternetShield_ifisSO.exe (PID: 8216)
- Endermanch@InternetShield_ifisSO.exe (PID: 6964)
- Endermanch@InternetShield_ifisSO.exe (PID: 6592)
Application launched itself
- firefox.exe (PID: 1676)
- firefox.exe (PID: 7192)
- msedge.exe (PID: 7992)
- msedge.exe (PID: 6108)
- msedge.exe (PID: 684)
The sample compiled with english language support
- WinRAR.exe (PID: 8940)
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- setup_trial.exe (PID: 8304)
- is-I8K1F.tmp (PID: 8208)
- Endermanch@InternetShield_SOReferral.exe (PID: 536)
- GLBF41C.tmp (PID: 8500)
- setup_trial.exe (PID: 2664)
- is-SE22R.tmp (PID: 8892)
- setup_trial.exe (PID: 6004)
- is-QK8CT.tmp (PID: 3180)
- setup_trial.exe (PID: 8464)
- is-1KO6P.tmp (PID: 8784)
- setup_trial.exe (PID: 7400)
- setup_trial.exe (PID: 5332)
- is-QF72G.tmp (PID: 3176)
- is-071L2.tmp (PID: 2420)
- setup_trial.exe (PID: 8260)
- is-V4ONP.tmp (PID: 240)
- is-SL40M.tmp (PID: 6908)
- is-IQI30.tmp (PID: 5812)
- setup_trial.exe (PID: 8392)
- setup_trial.exe (PID: 736)
Executable content was dropped or overwritten
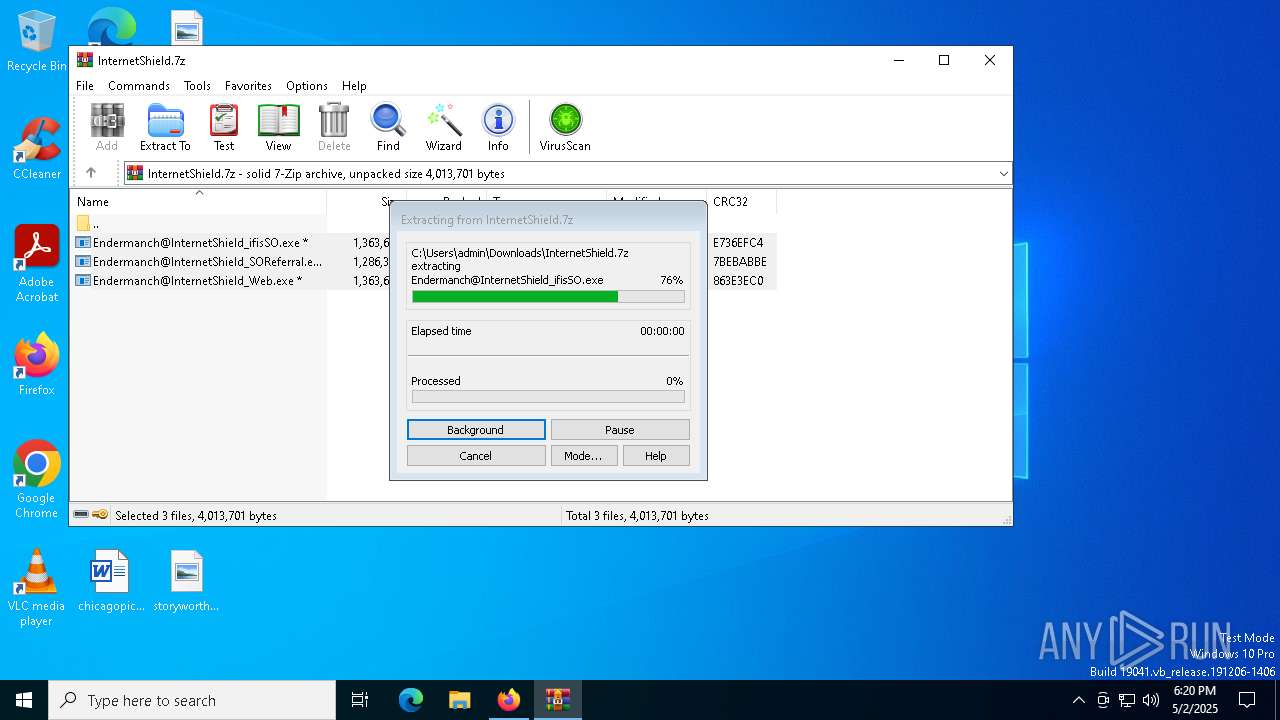
- WinRAR.exe (PID: 8940)
Checks supported languages
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- GLB8819.tmp (PID: 9136)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- setup_trial.exe (PID: 8304)
- is-I8K1F.tmp (PID: 8208)
- internetshield.exe (PID: 8352)
Create files in a temporary directory
- Endermanch@InternetShield_SOReferral.exe (PID: 9124)
- GLB8819.tmp (PID: 9136)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- setup_trial.exe (PID: 8304)
- is-I8K1F.tmp (PID: 8208)
Reads the computer name
- GLB8819.tmp (PID: 9136)
- Endermanch@InternetShield_Web.exe (PID: 5364)
- is-I8K1F.tmp (PID: 8208)
- internetshield.exe (PID: 8352)
Process checks computer location settings
- Endermanch@InternetShield_Web.exe (PID: 5364)
Reads the software policy settings
- slui.exe (PID: 8128)
Checks proxy server information
- internetshield.exe (PID: 8352)
Creates files in the program directory
- is-I8K1F.tmp (PID: 8208)
Creates a software uninstall entry
- is-I8K1F.tmp (PID: 8208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
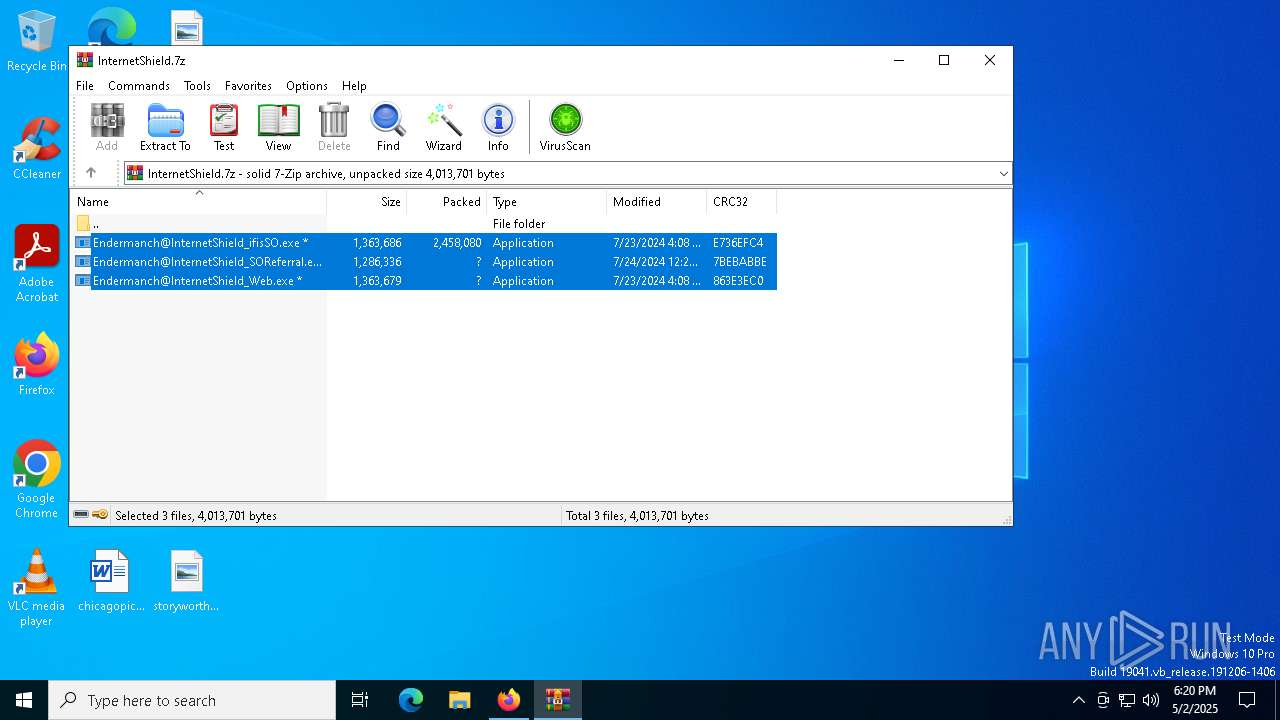
Total processes
245
Monitored processes
101
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5172 --field-trial-handle=2408,i,8252222432379579822,5382305481532407077,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 240 | "C:\Users\admin\AppData\Local\Temp\is-Q3LIN.tmp\is-V4ONP.tmp" /SL4 $104C8 "C:\Users\admin\AppData\Local\Temp\setup_trial.exe" 915441 52224 | C:\Users\admin\AppData\Local\Temp\is-Q3LIN.tmp\is-V4ONP.tmp | setup_trial.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.42.0.0 Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5860 --field-trial-handle=2408,i,8252222432379579822,5382305481532407077,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Users\admin\Desktop\Endermanch@InternetShield_SOReferral.exe" | C:\Users\admin\Desktop\Endermanch@InternetShield_SOReferral.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5252 --field-trial-handle=2408,i,8252222432379579822,5382305481532407077,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6168 --field-trial-handle=2408,i,8252222432379579822,5382305481532407077,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 --flag-switches-begin --flag-switches-end --do-not-de-elevate -- https://store.sharewareonline.com/emailentry?catalogentry=internetshieldcheckout.xml&Referrer=systweakishld&InstallDate=050225 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Local\Temp\setup_trial.exe" | C:\Users\admin\AppData\Local\Temp\setup_trial.exe | Endermanch@InternetShield_ifisSO.exe | ||||||||||||
User: admin Company: Systweak Inc Integrity Level: HIGH Description: InternetShield Setup Version: InternetShield 1.0 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5464 -childID 6 -isForBrowser -prefsHandle 5384 -prefMapHandle 5388 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1412 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {015e4bc8-be64-471f-bff5-4b45bbe79cee} 7192 "\\.\pipe\gecko-crash-server-pipe.7192" 2379f211a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
41 886
Read events
41 718
Write events
125
Delete events
43
Modification events
| (PID) Process: | (7192) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\InternetShield.7z | |||
Executable files
85
Suspicious files
417
Text files
136
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:EFE362FF00C6A6DC9FB3B5166568F705 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 7192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
102
DNS requests
172
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7192 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7192 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
7192 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7192 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7192 | firefox.exe | 142.250.185.106:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7192 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7192 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
7192 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |