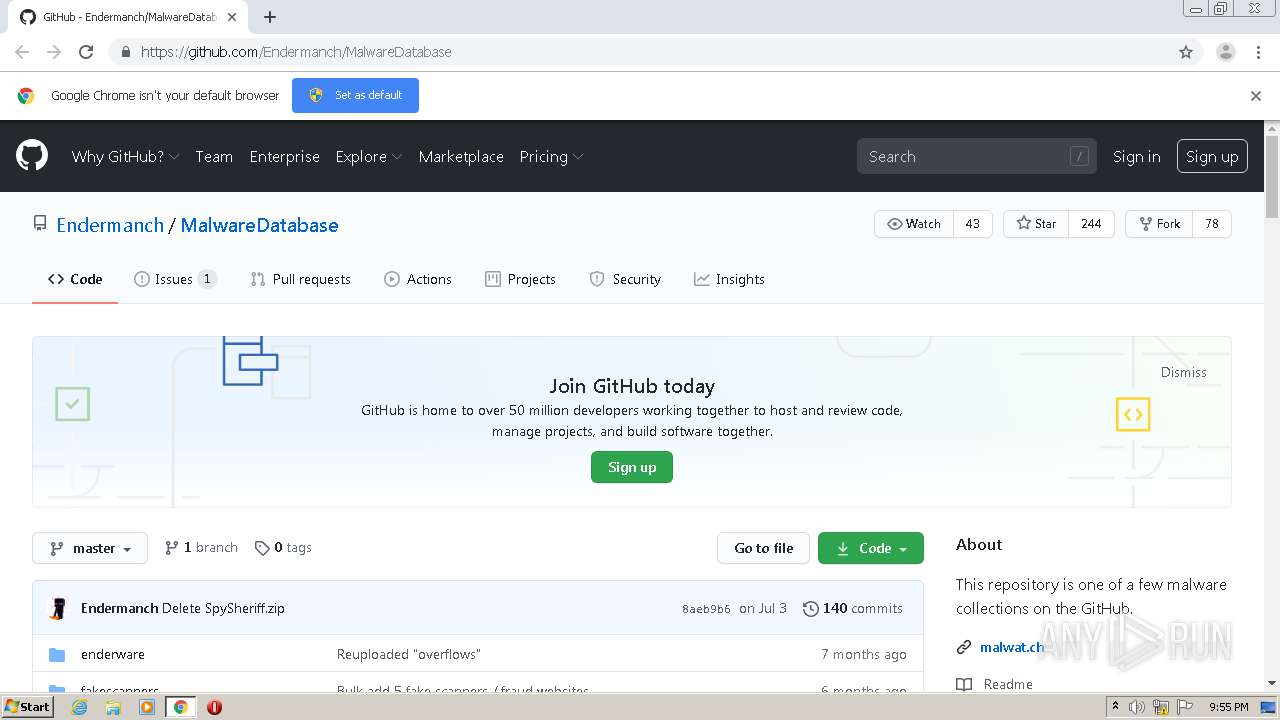
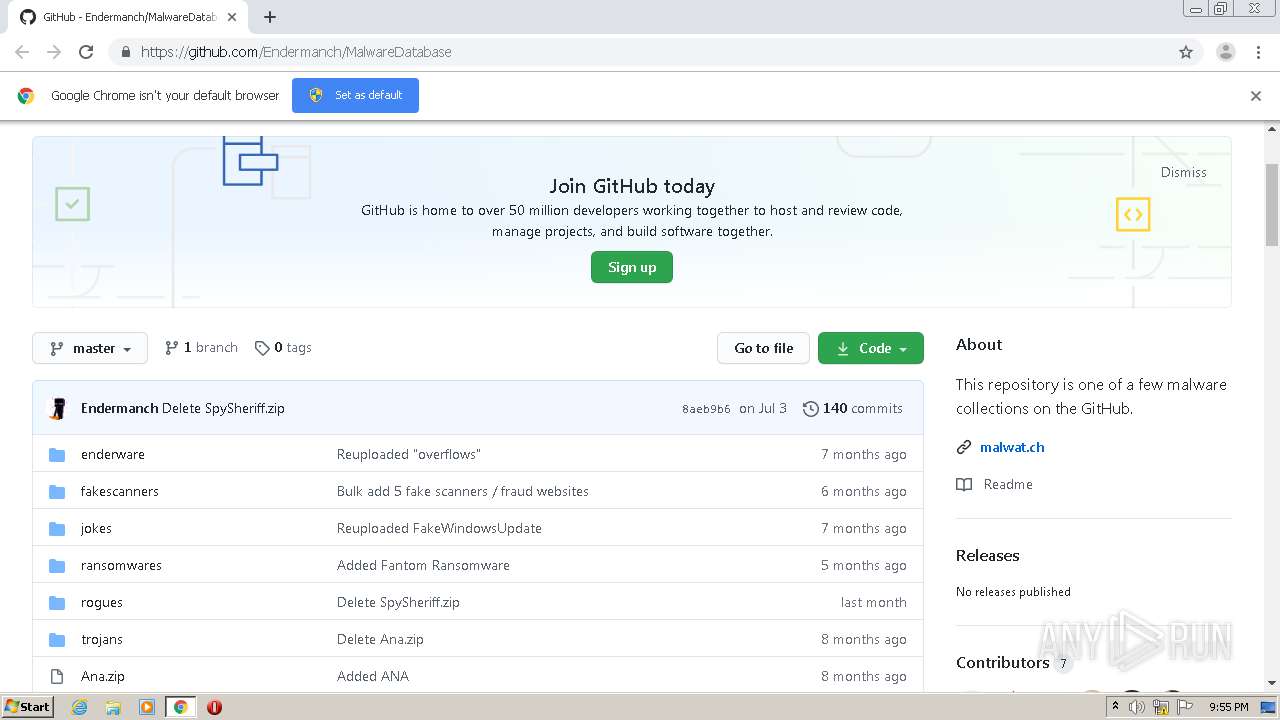
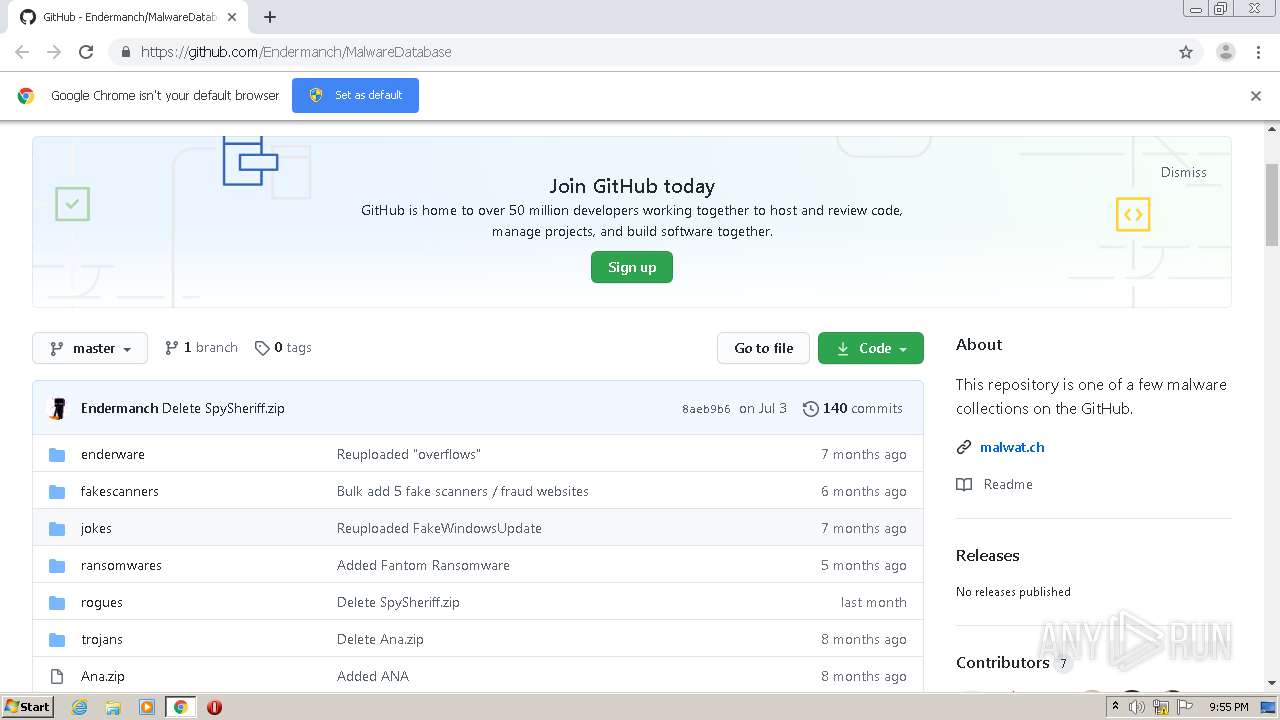
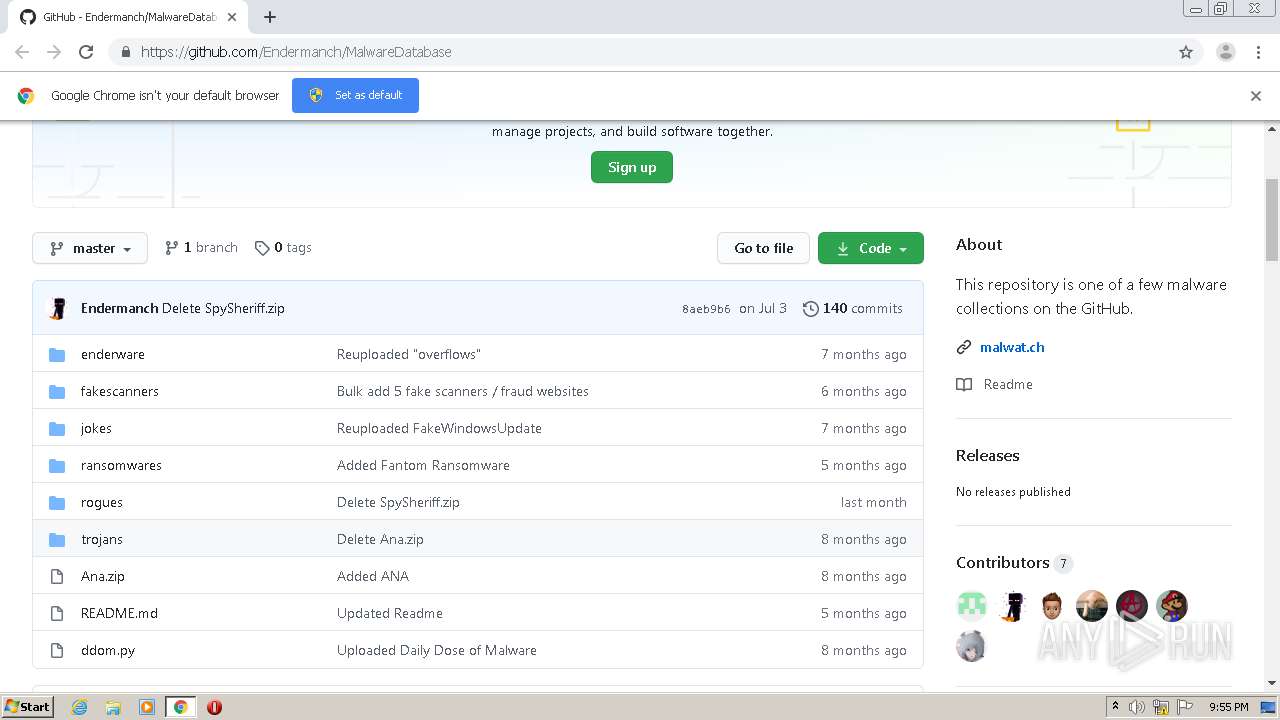
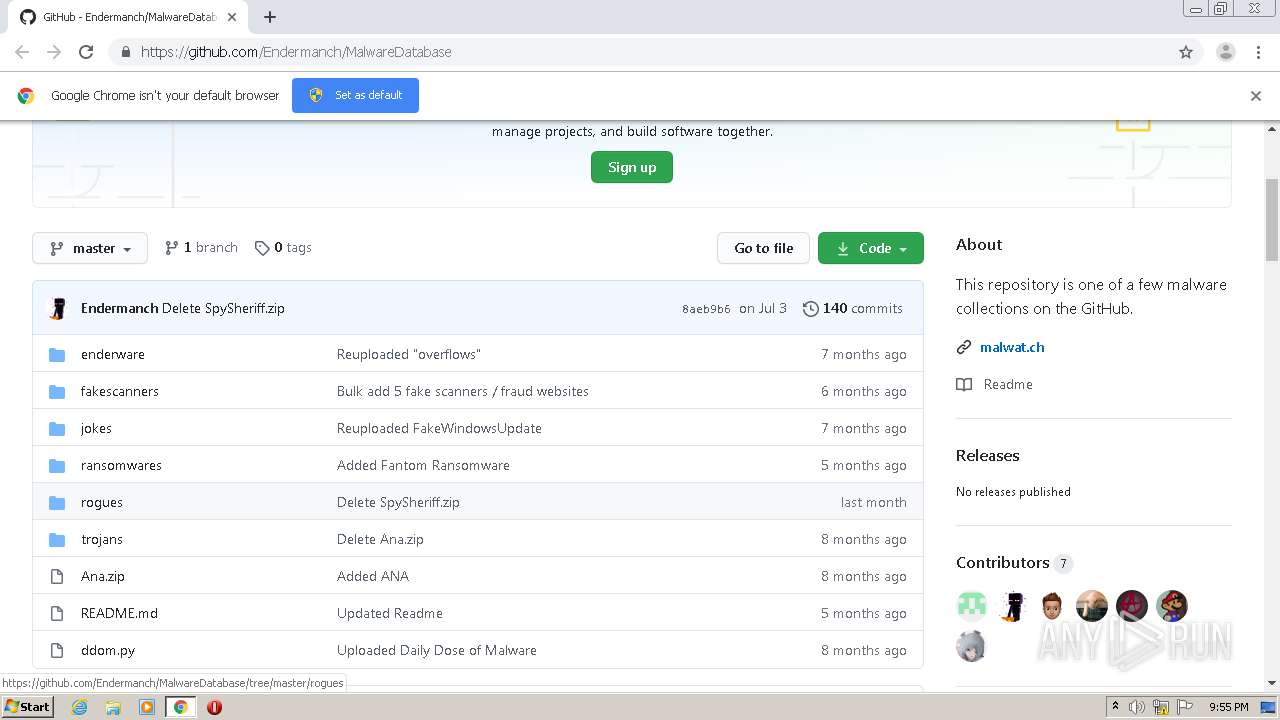
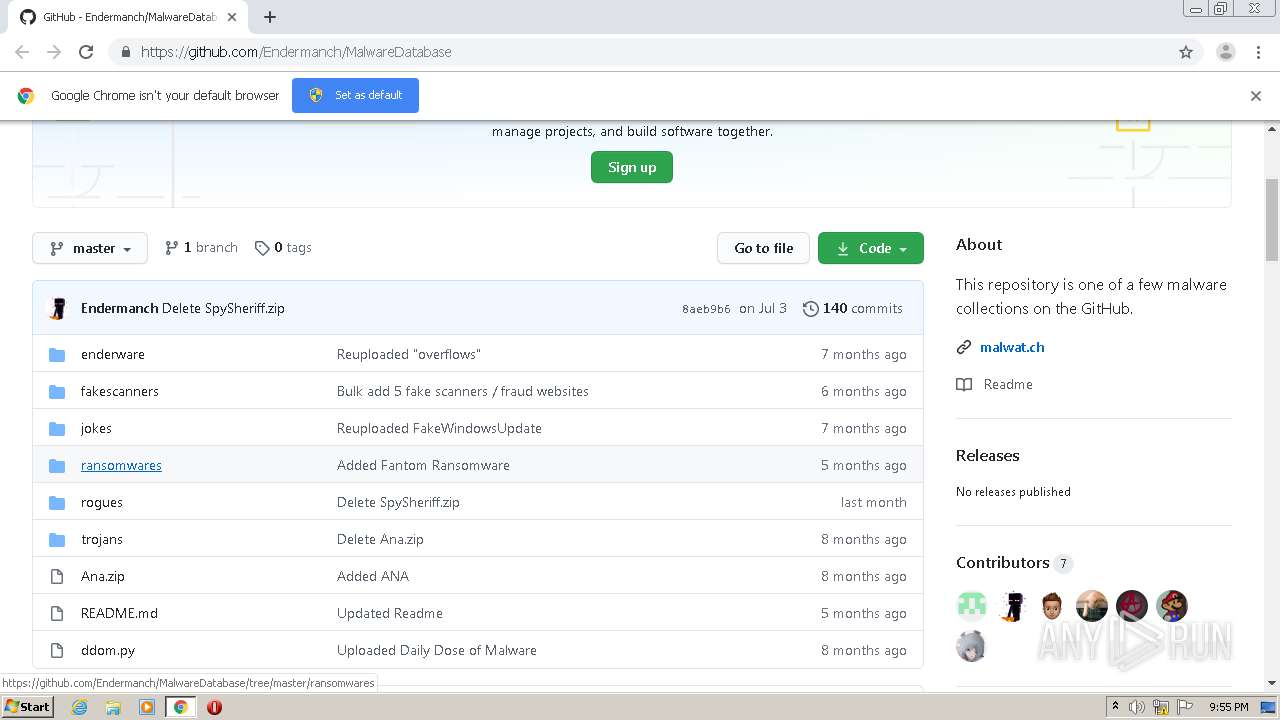
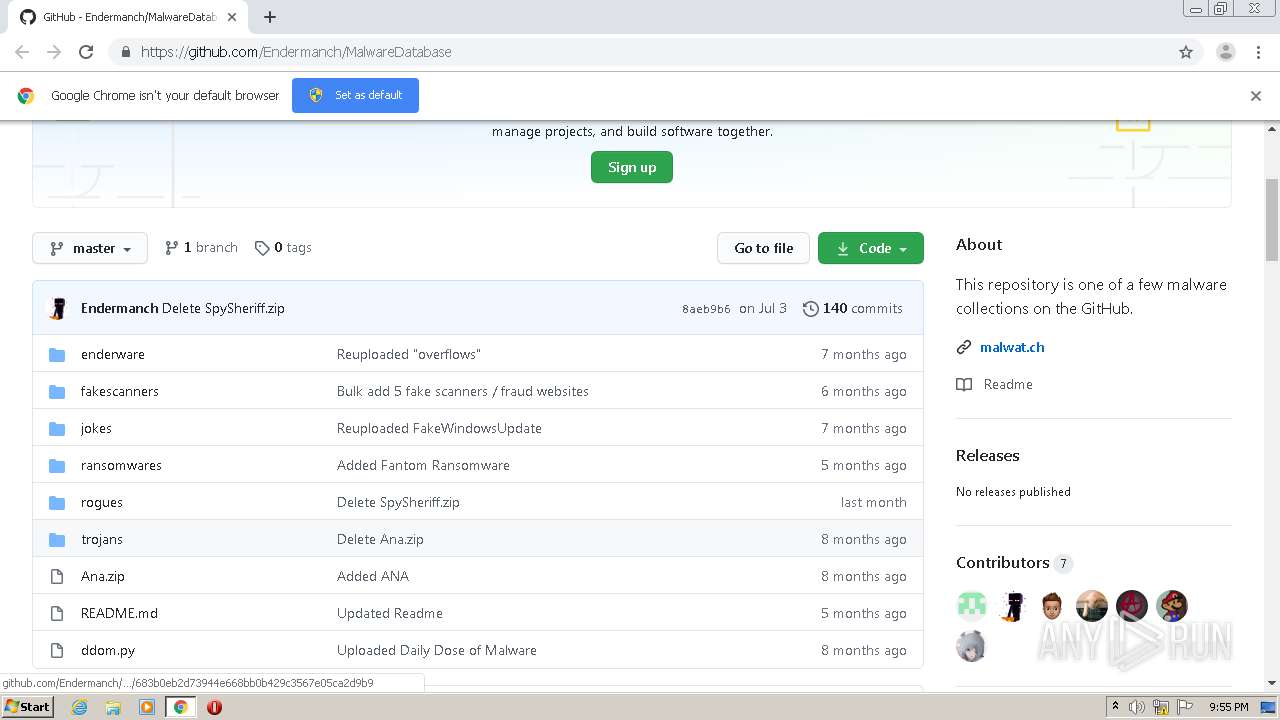
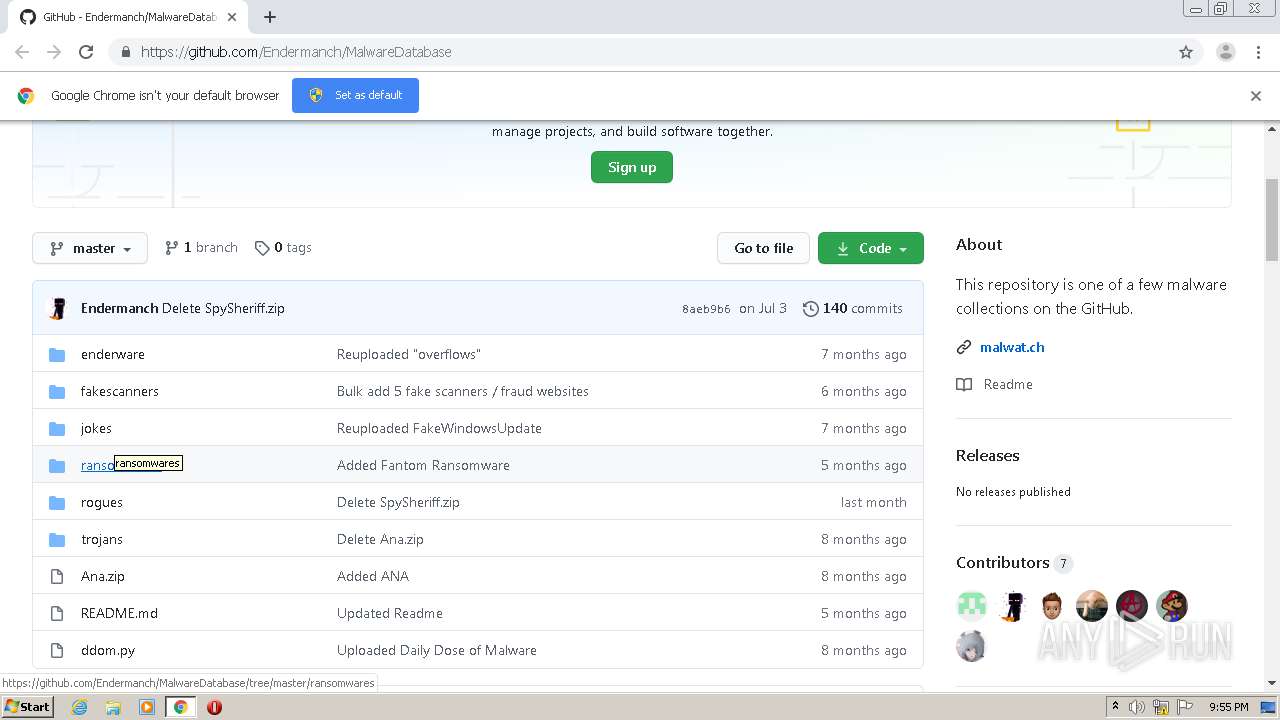
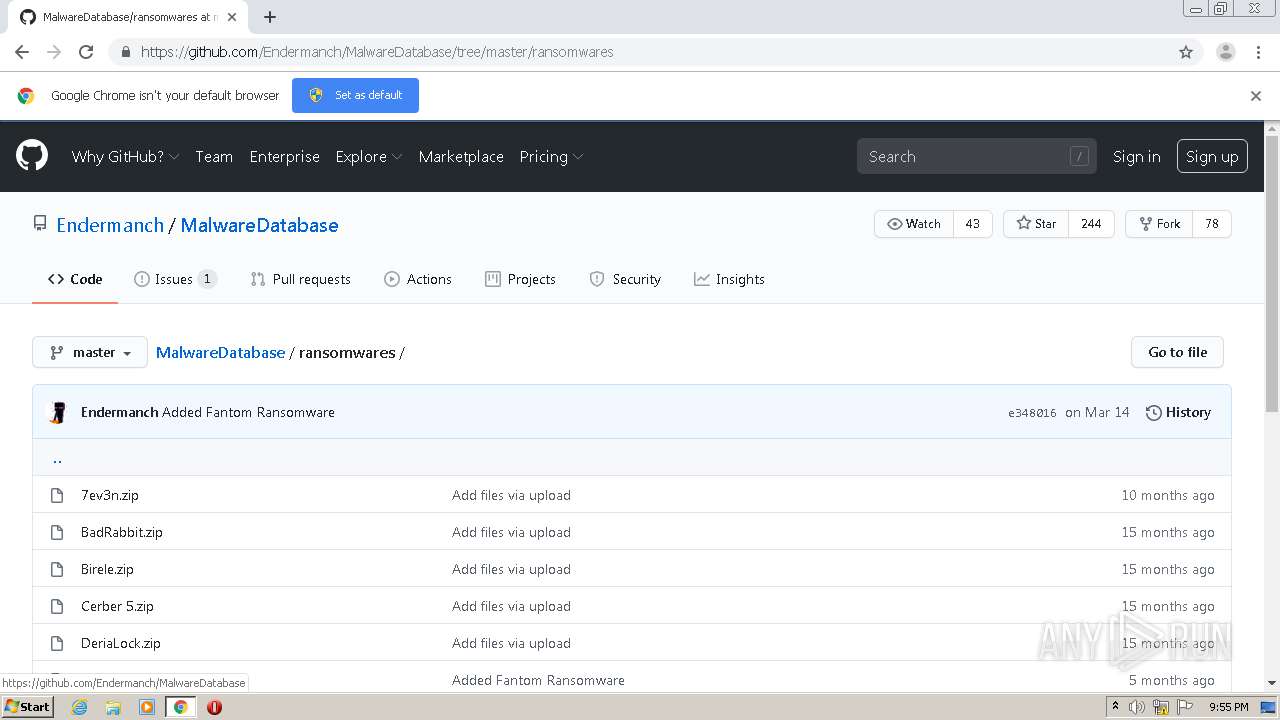
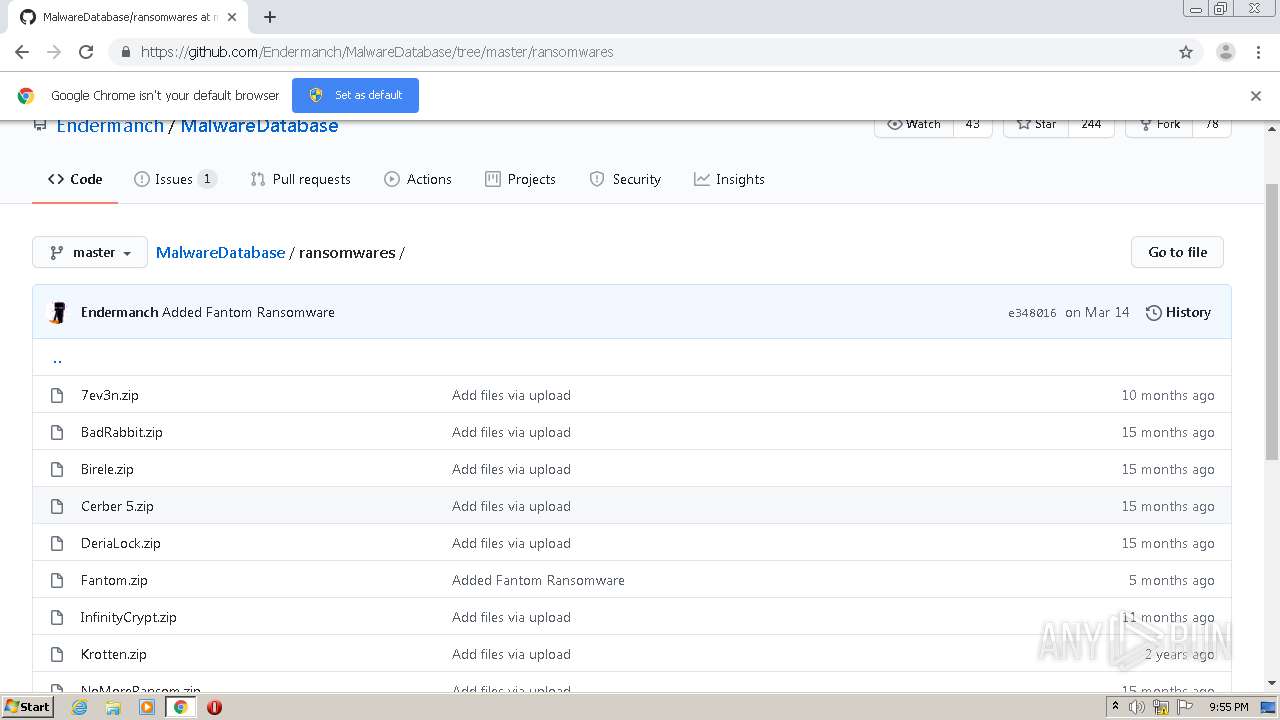
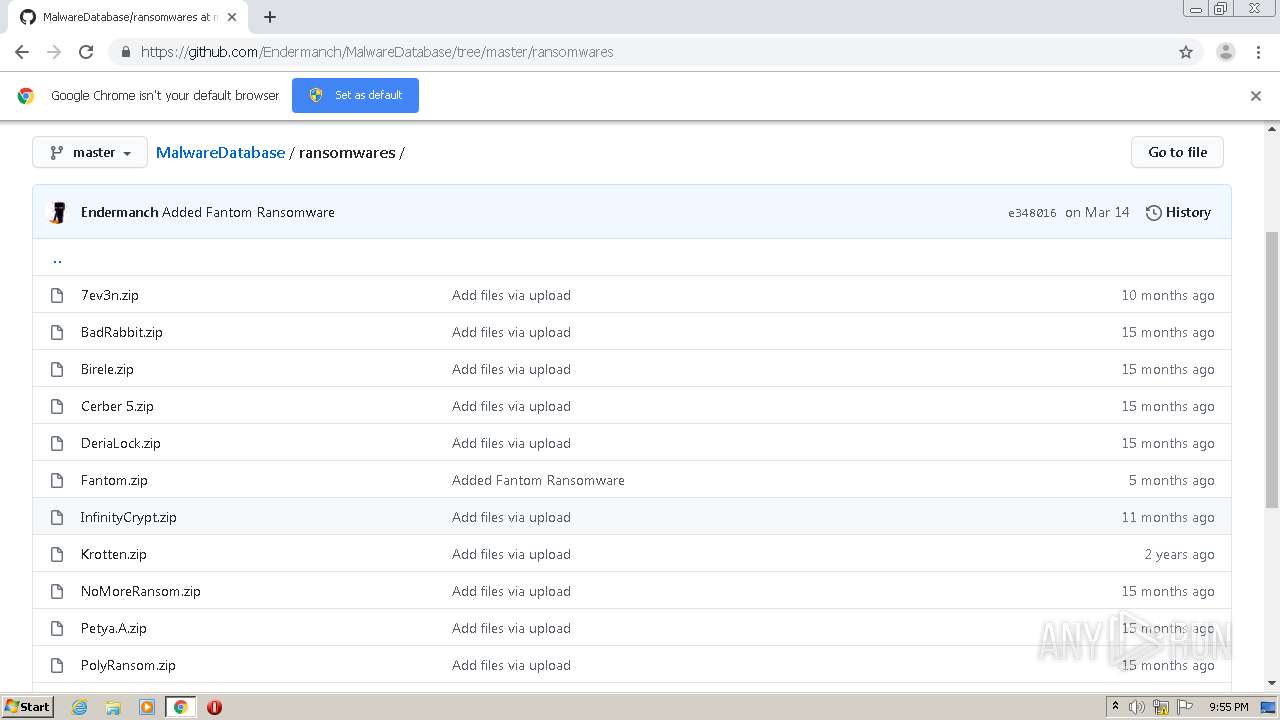
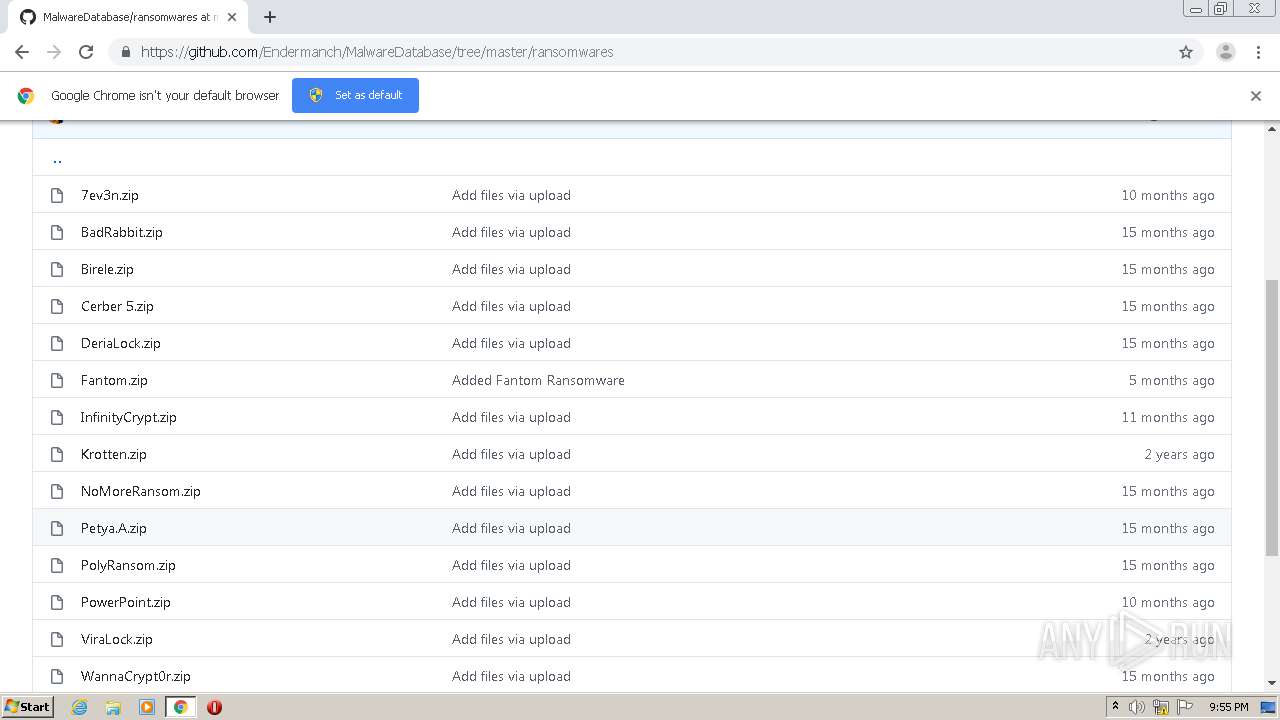
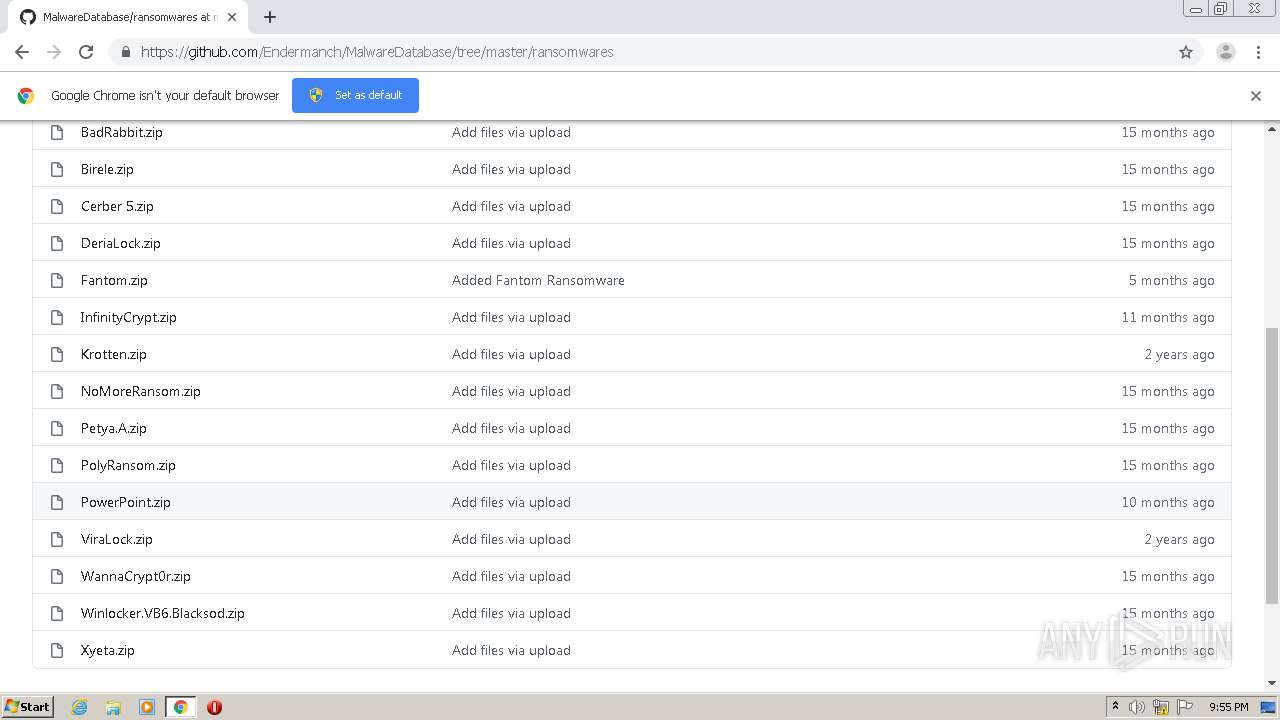
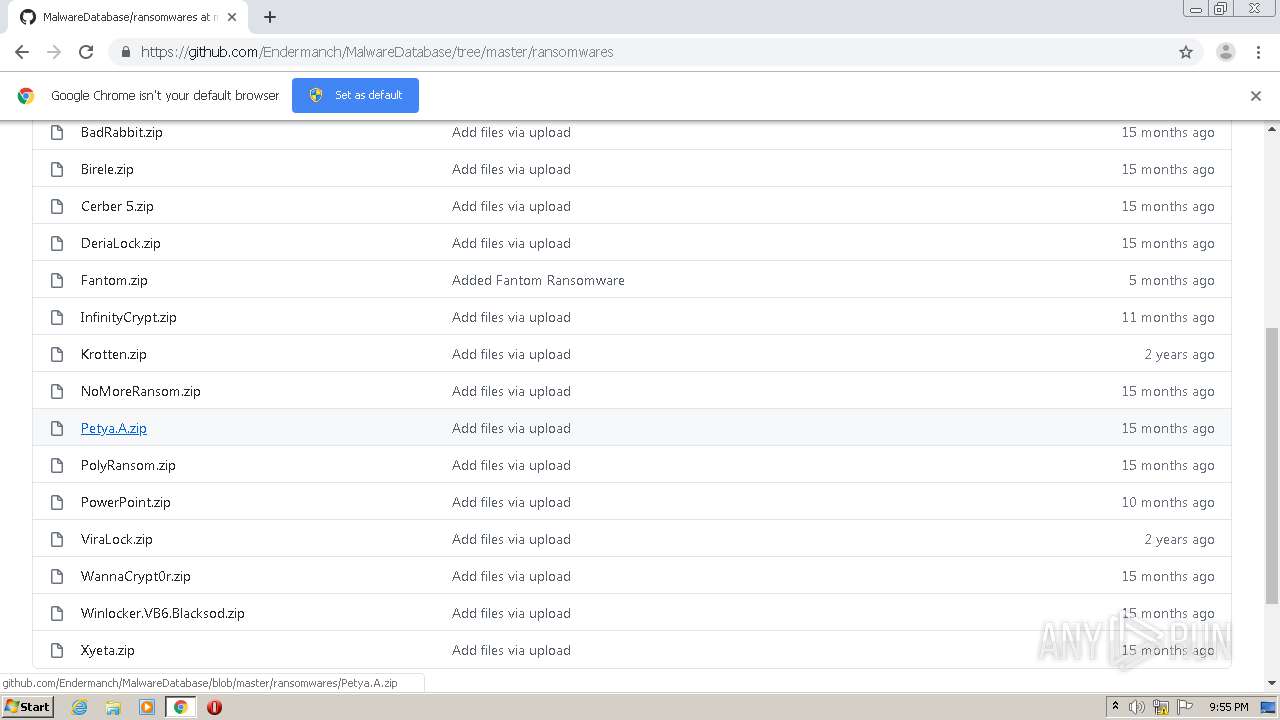
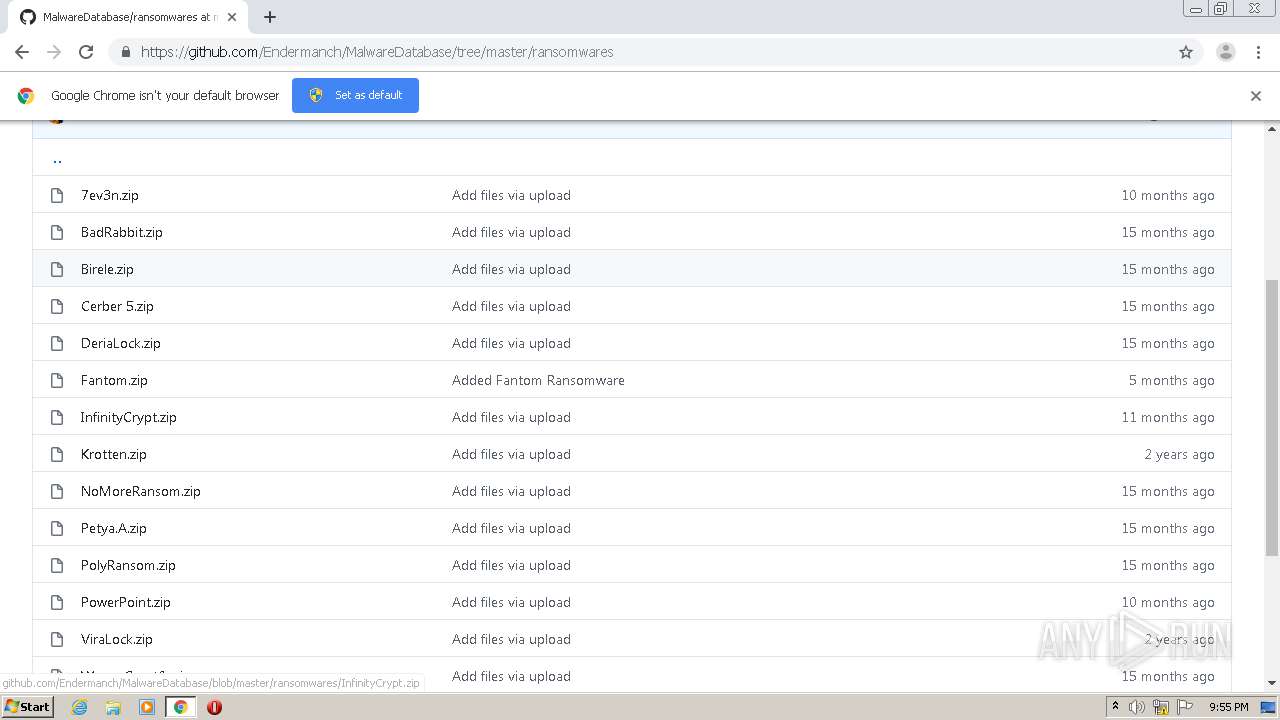
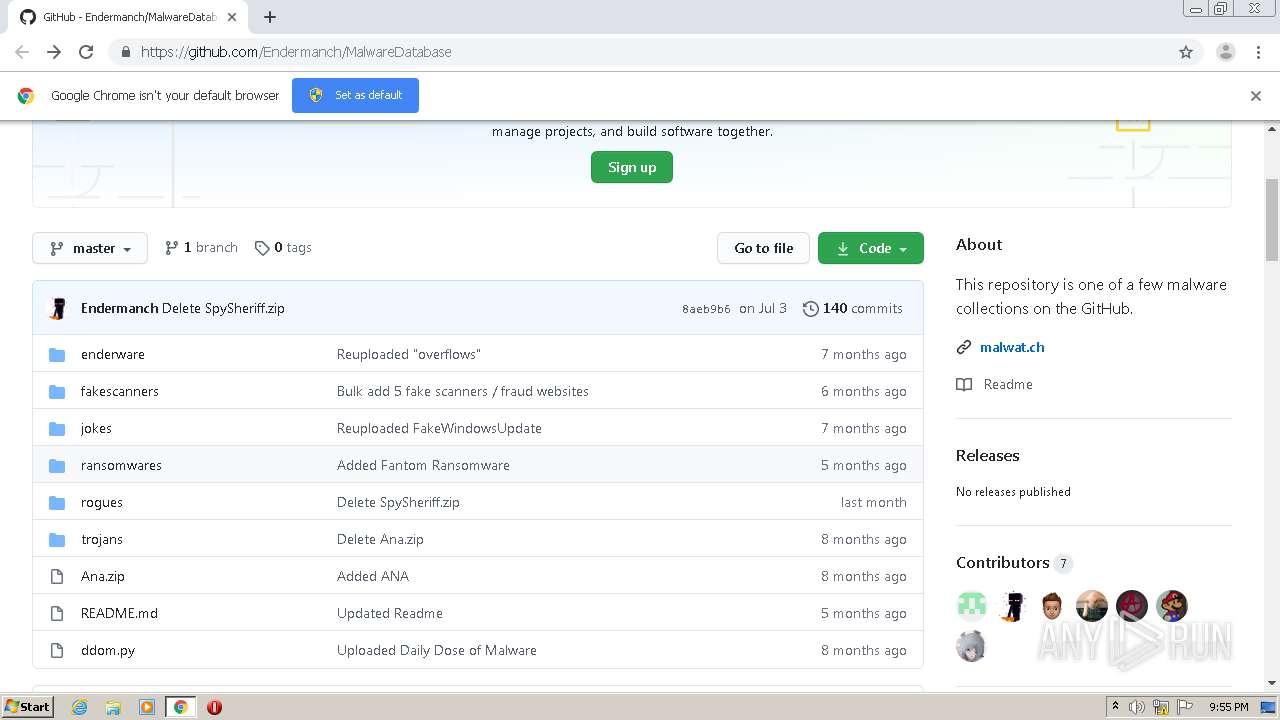
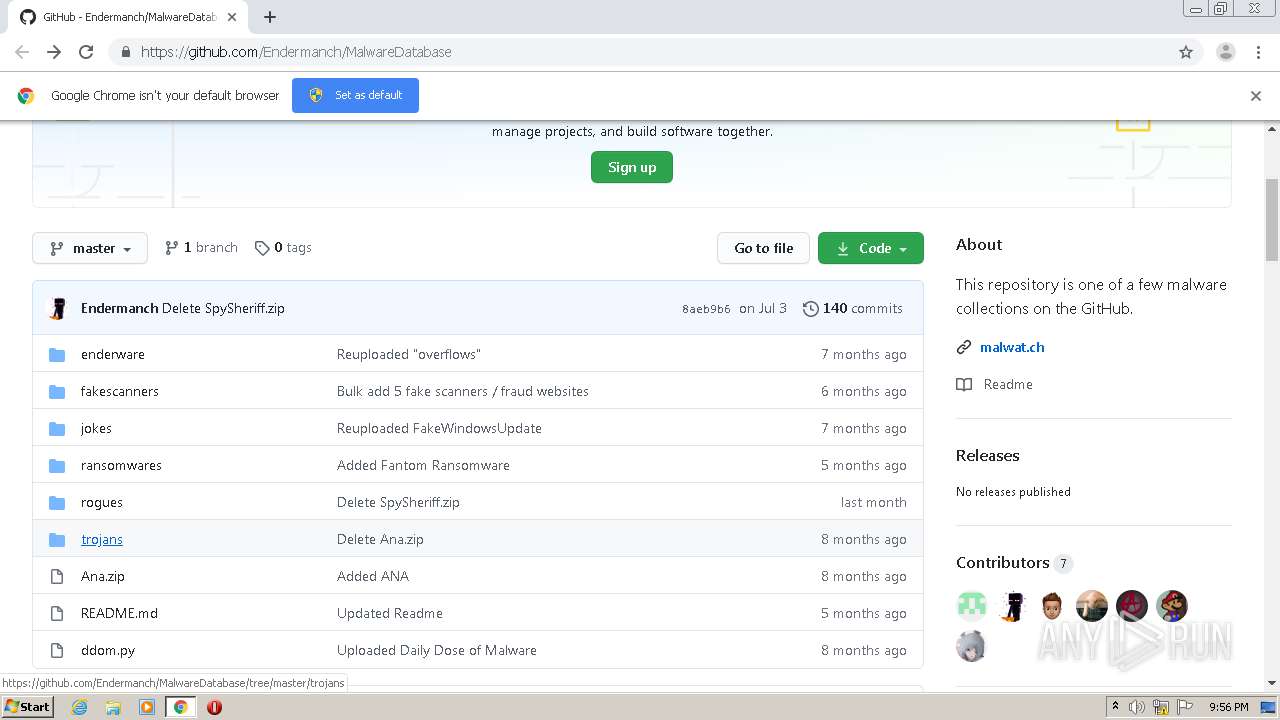
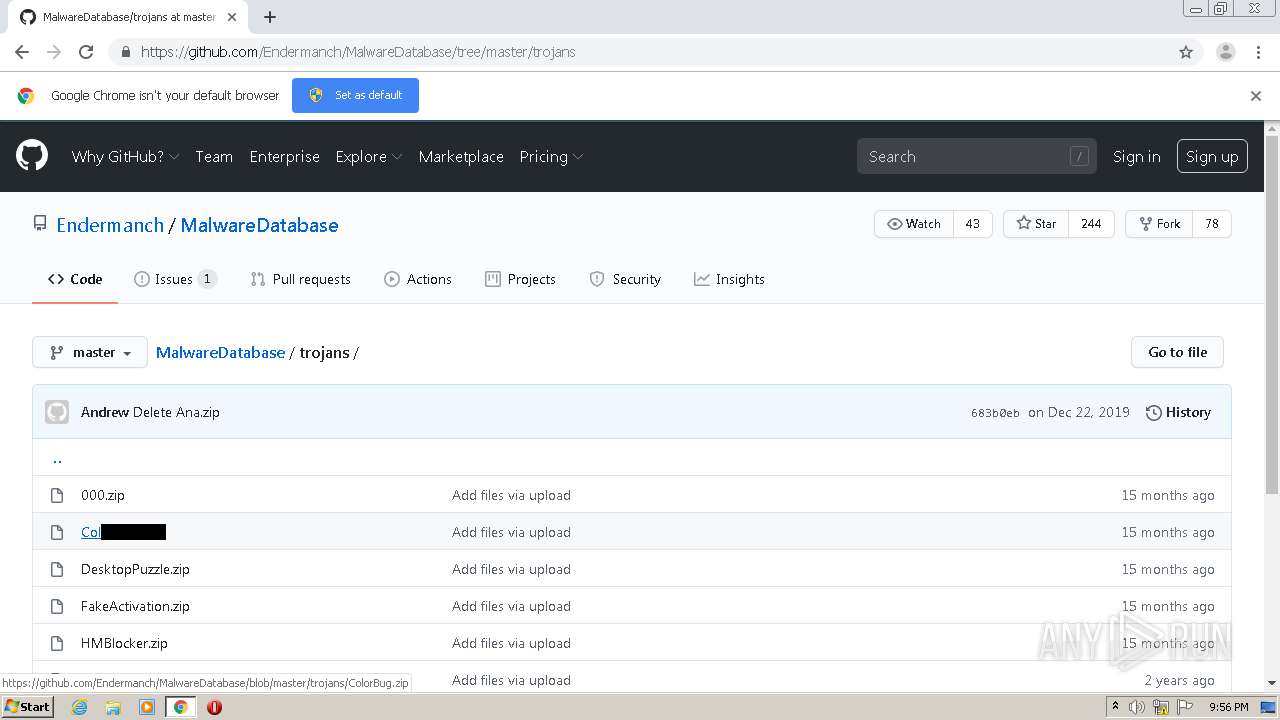
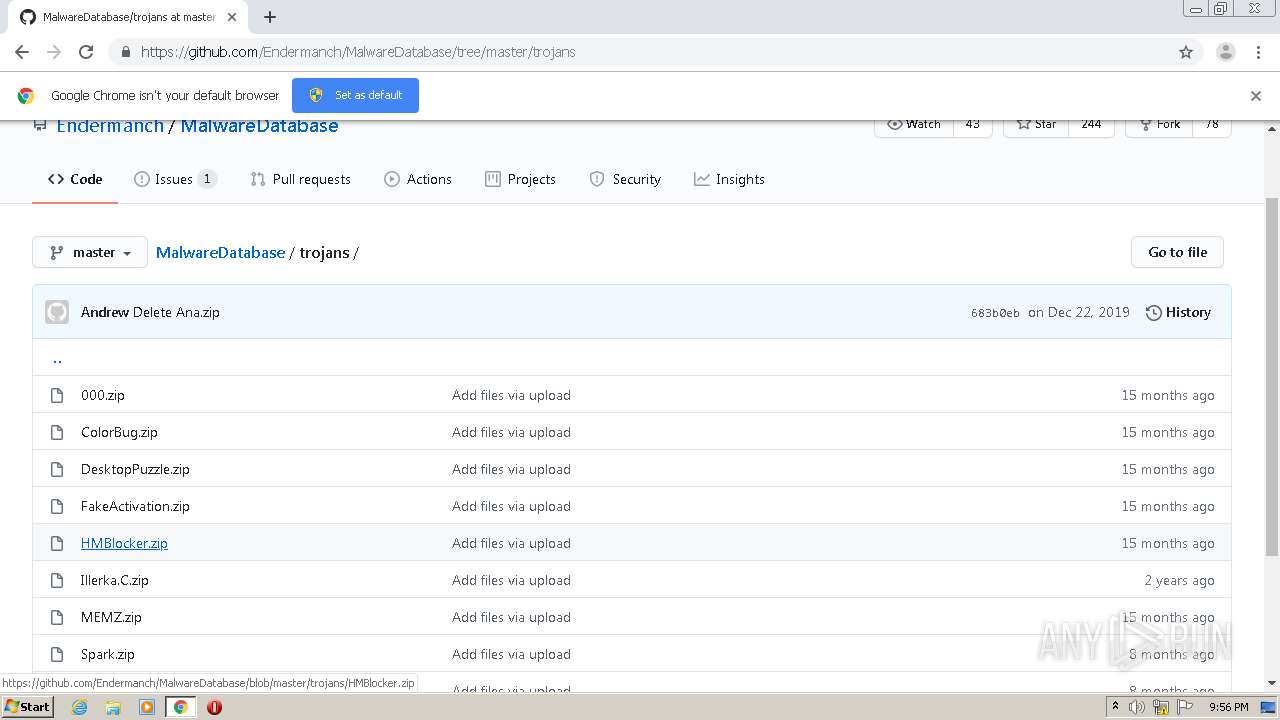
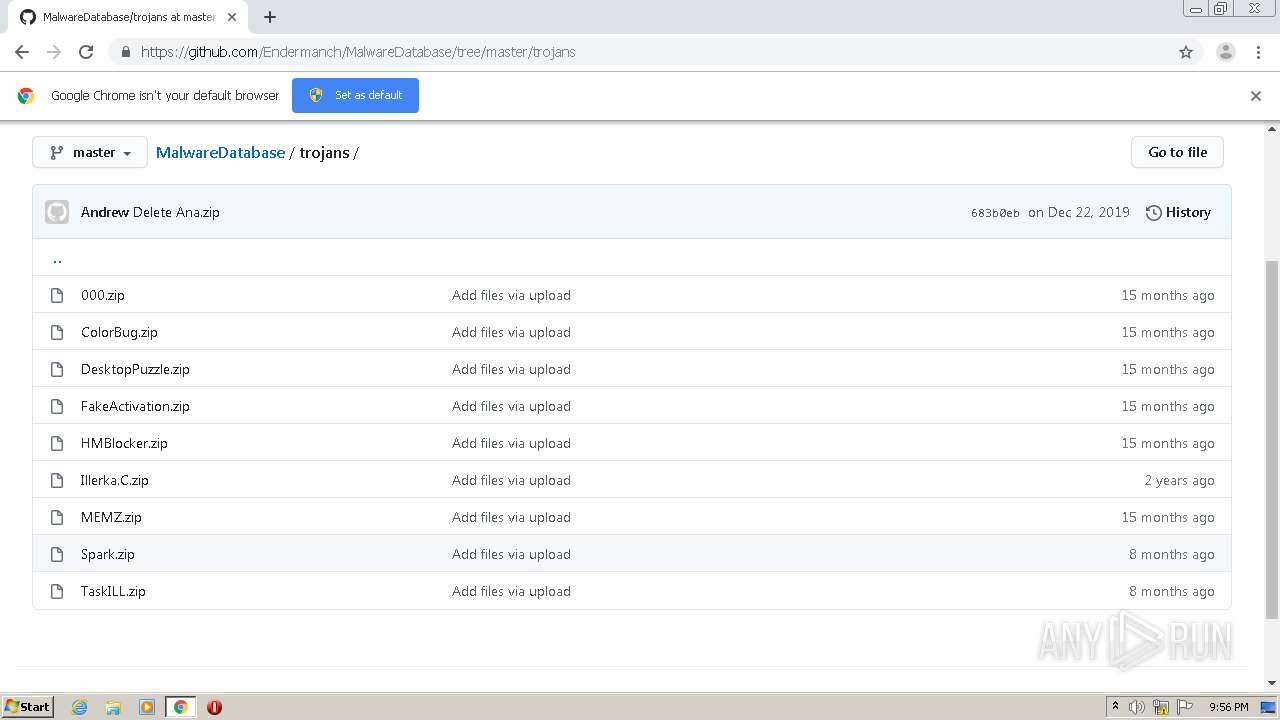
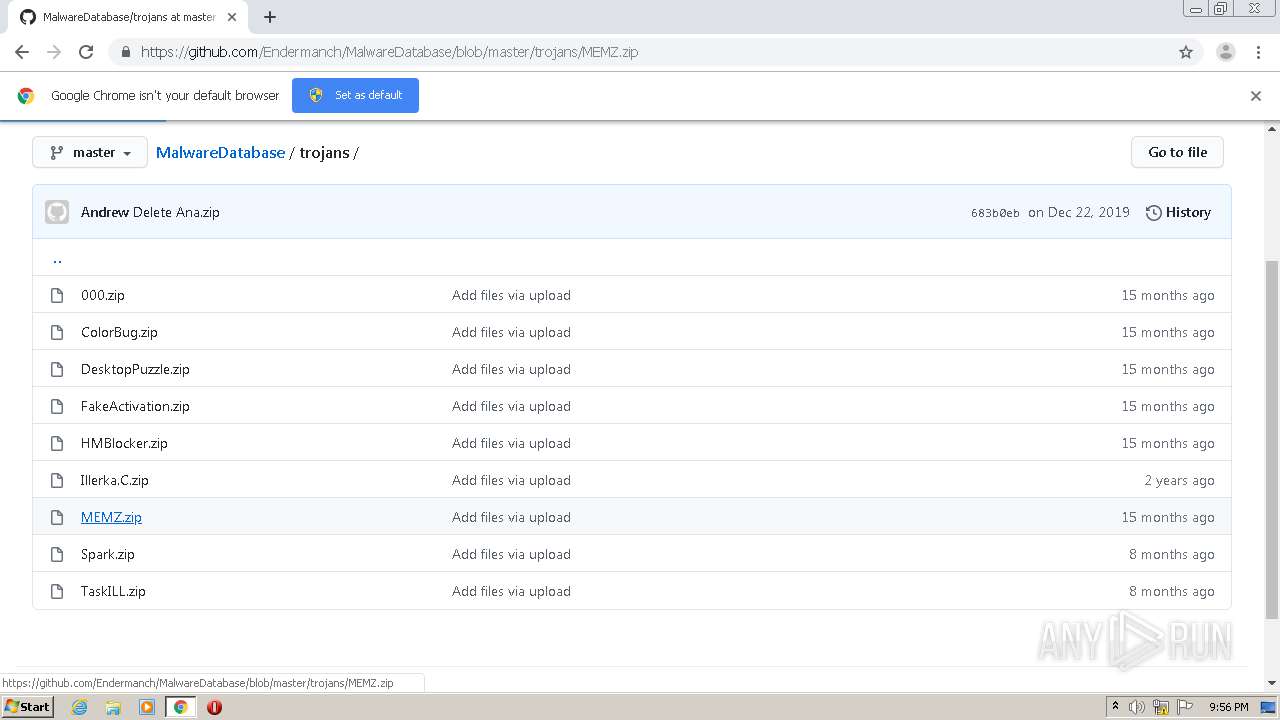
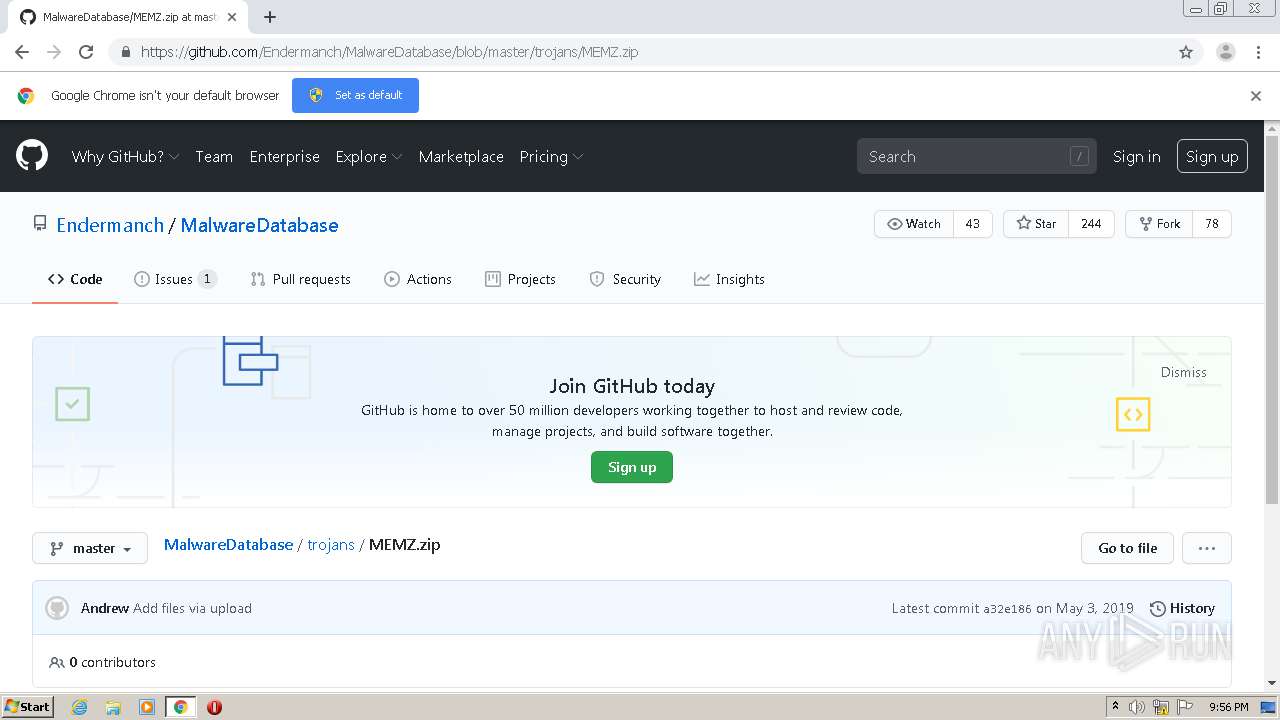
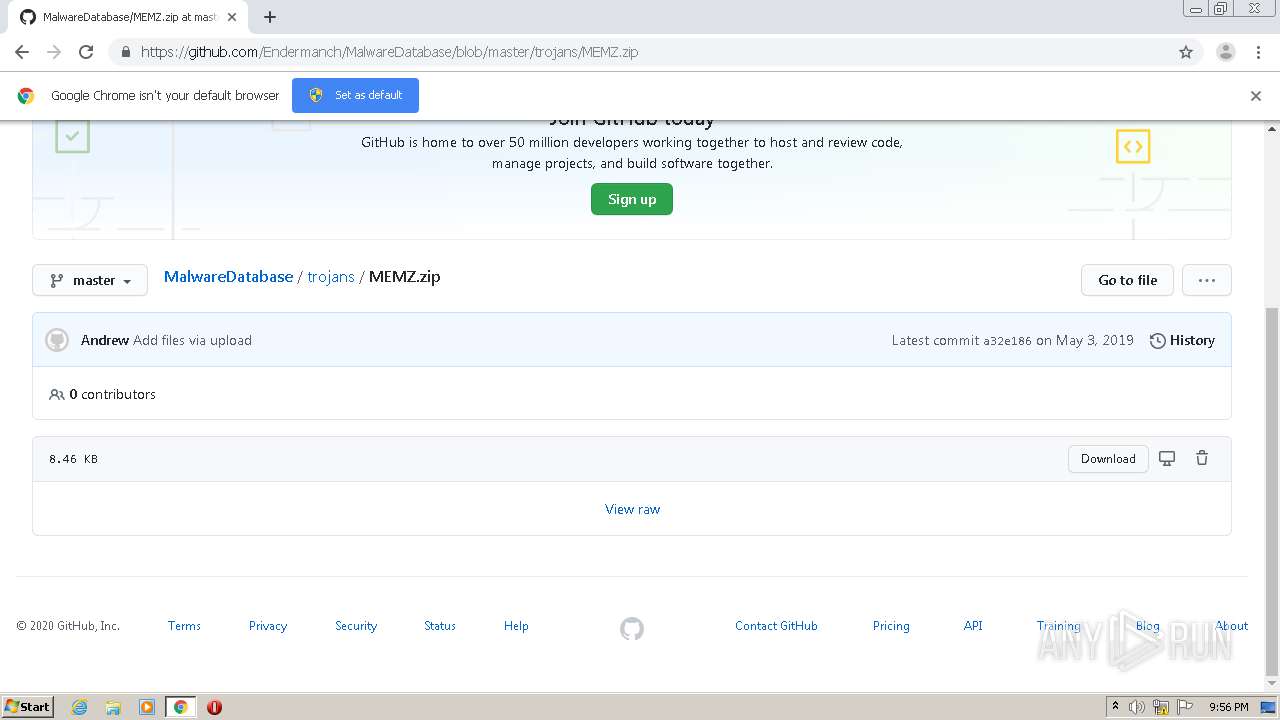
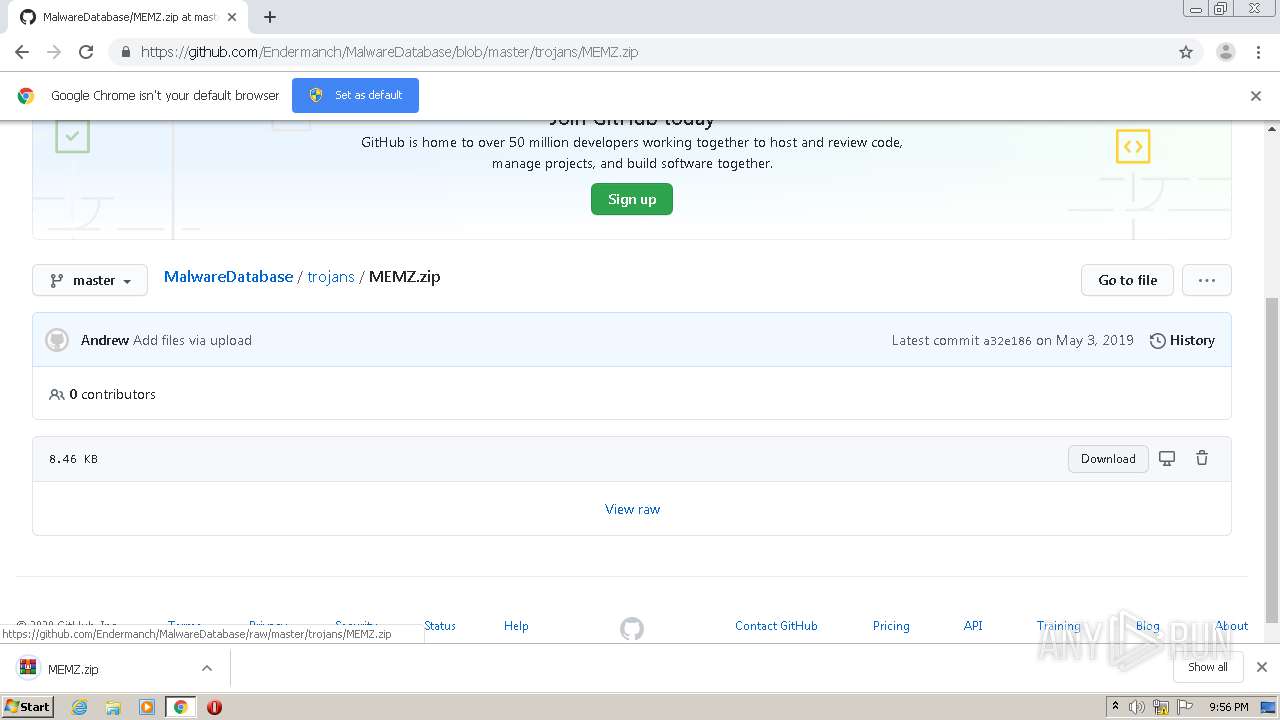
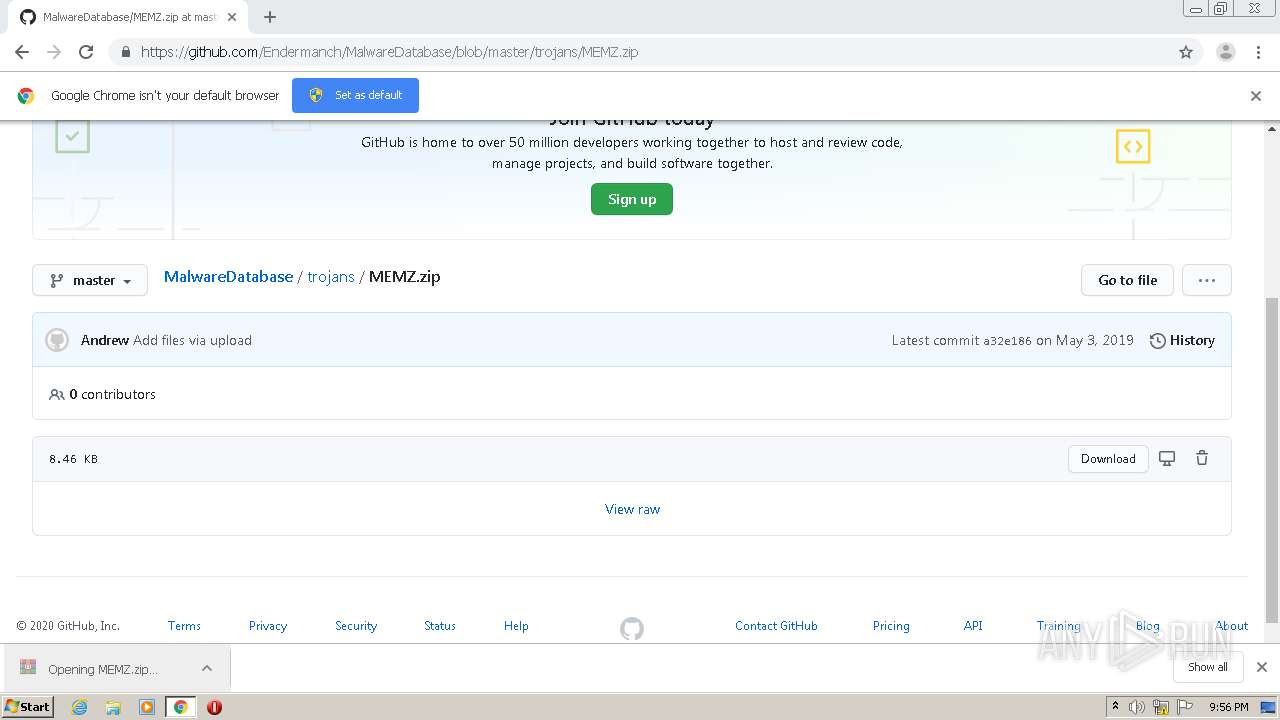
| URL: | https://github.com/Endermanch/MalwareDatabase |
| Full analysis: | https://app.any.run/tasks/a3298633-8406-4692-b4db-7d8c4c52a2cf |
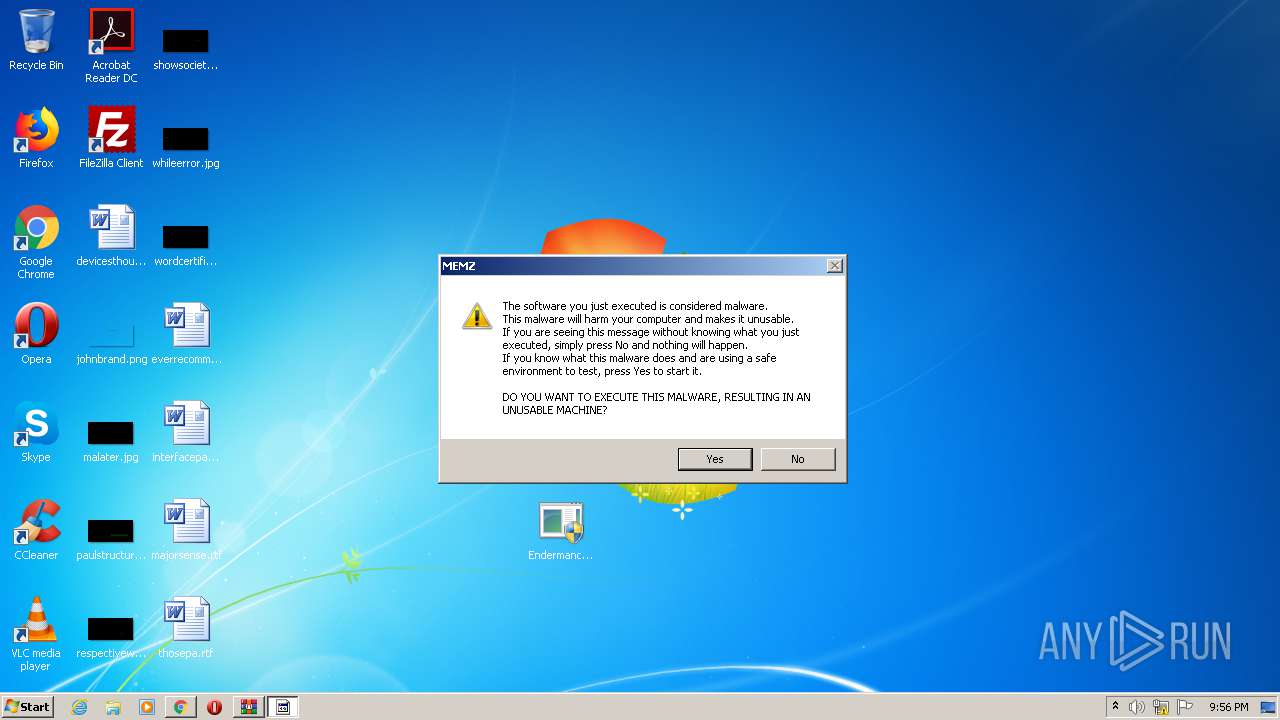
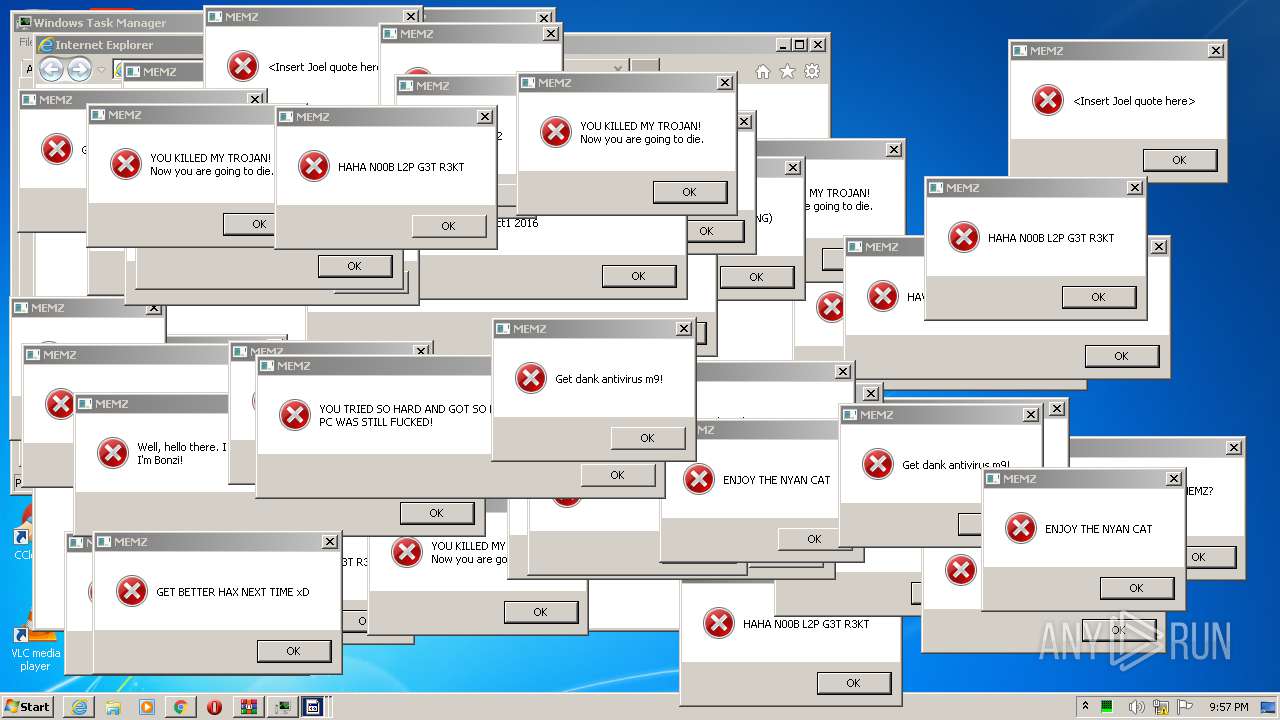
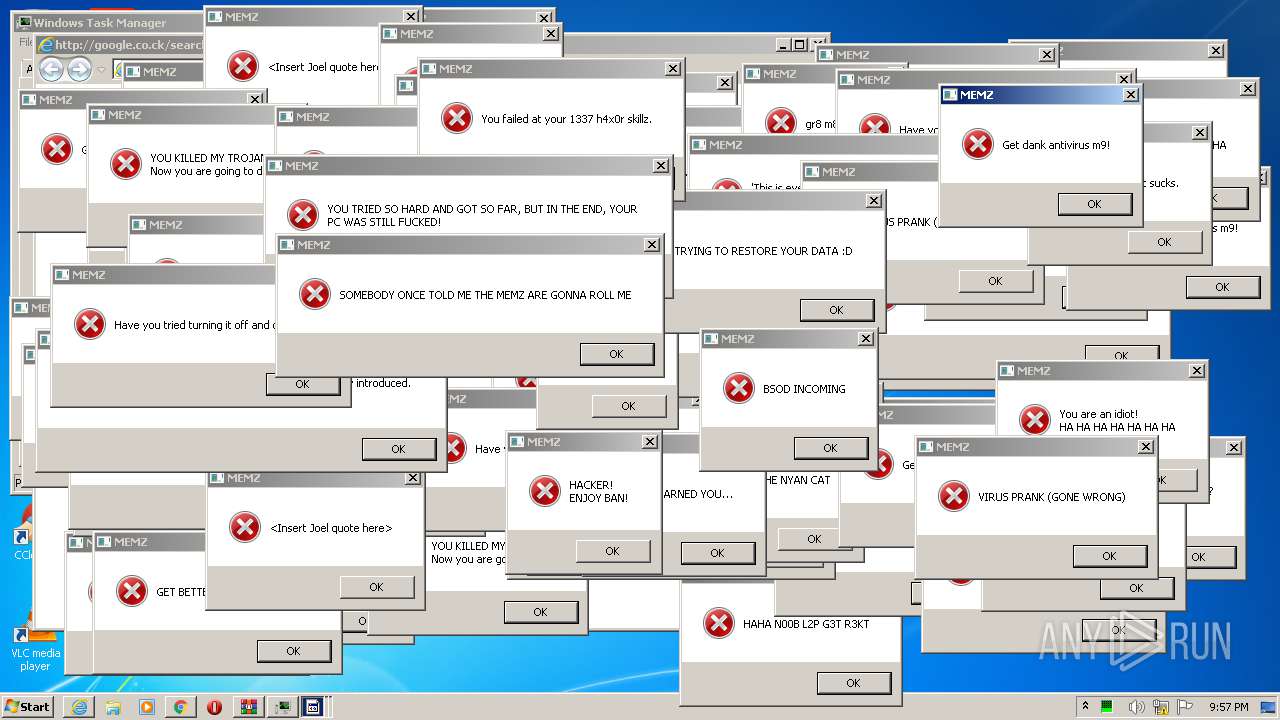
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 20:55:12 |
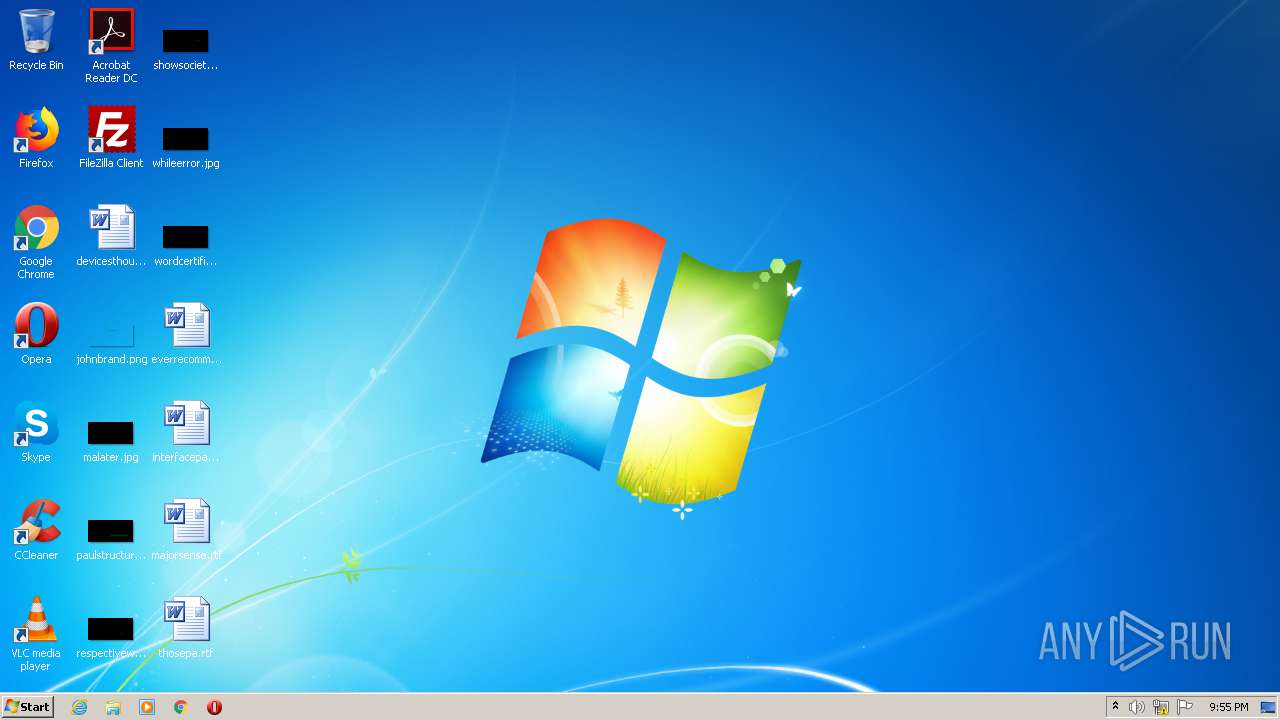
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
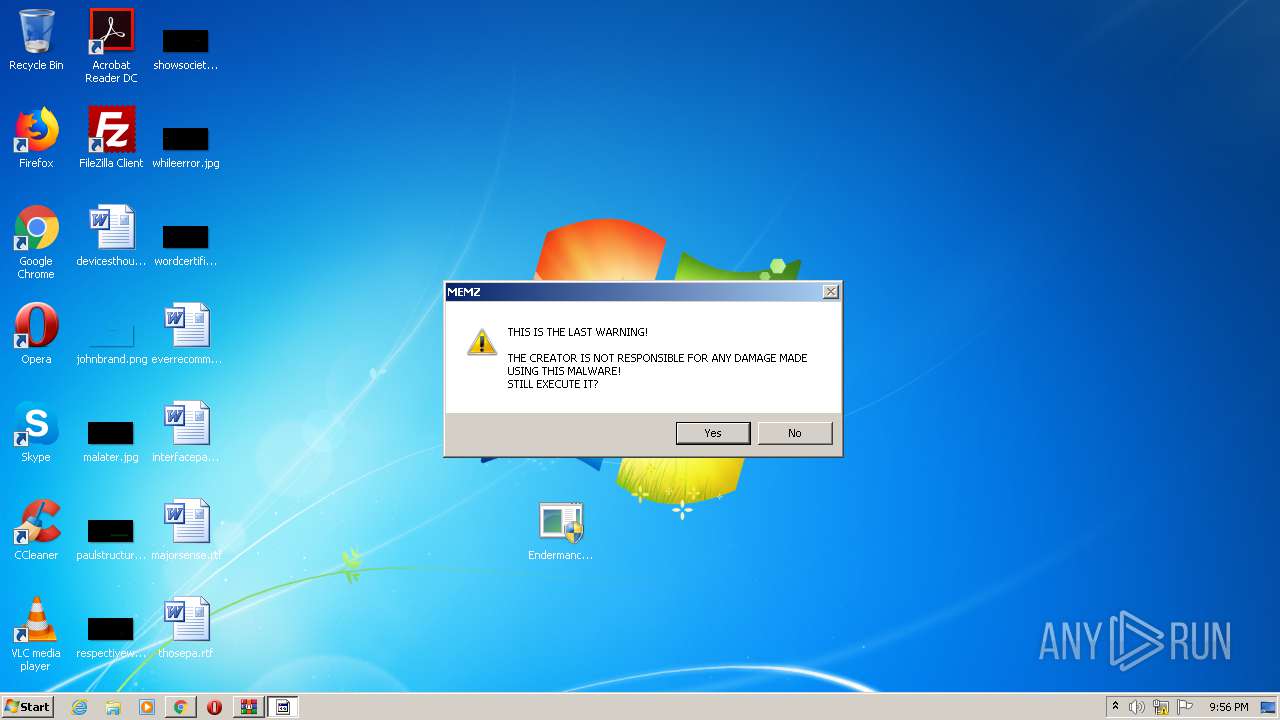
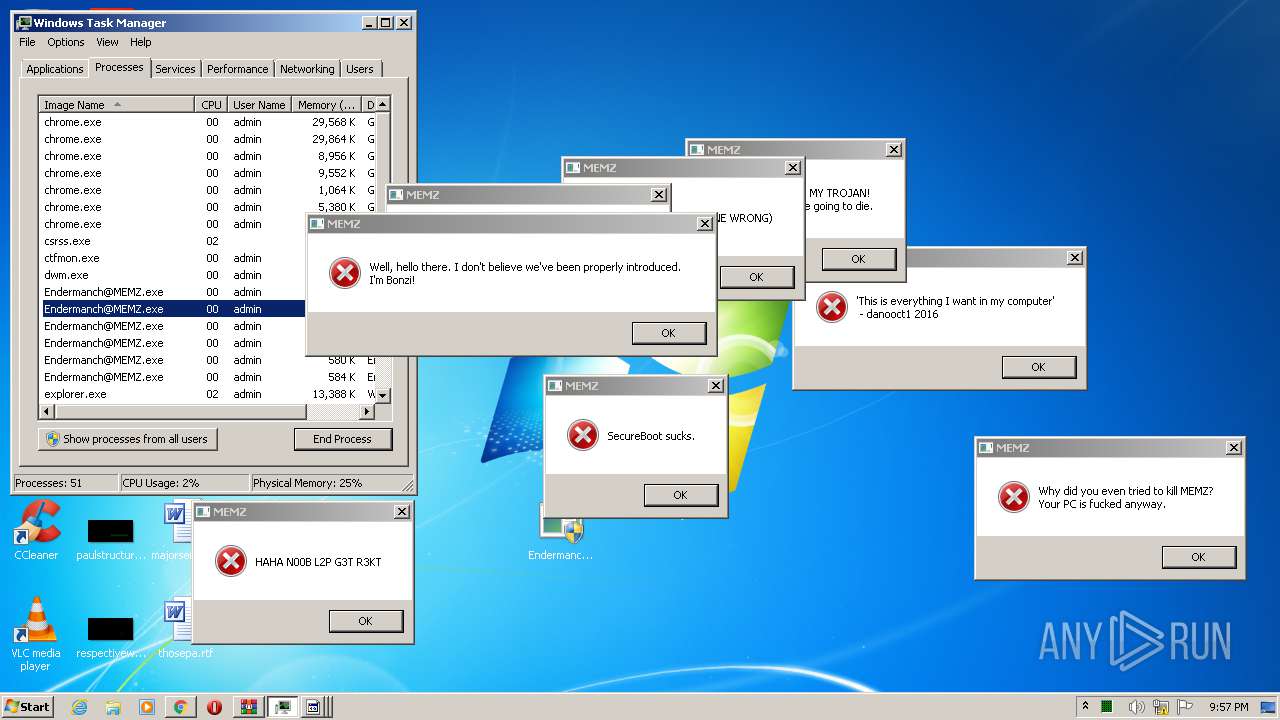
MALICIOUS
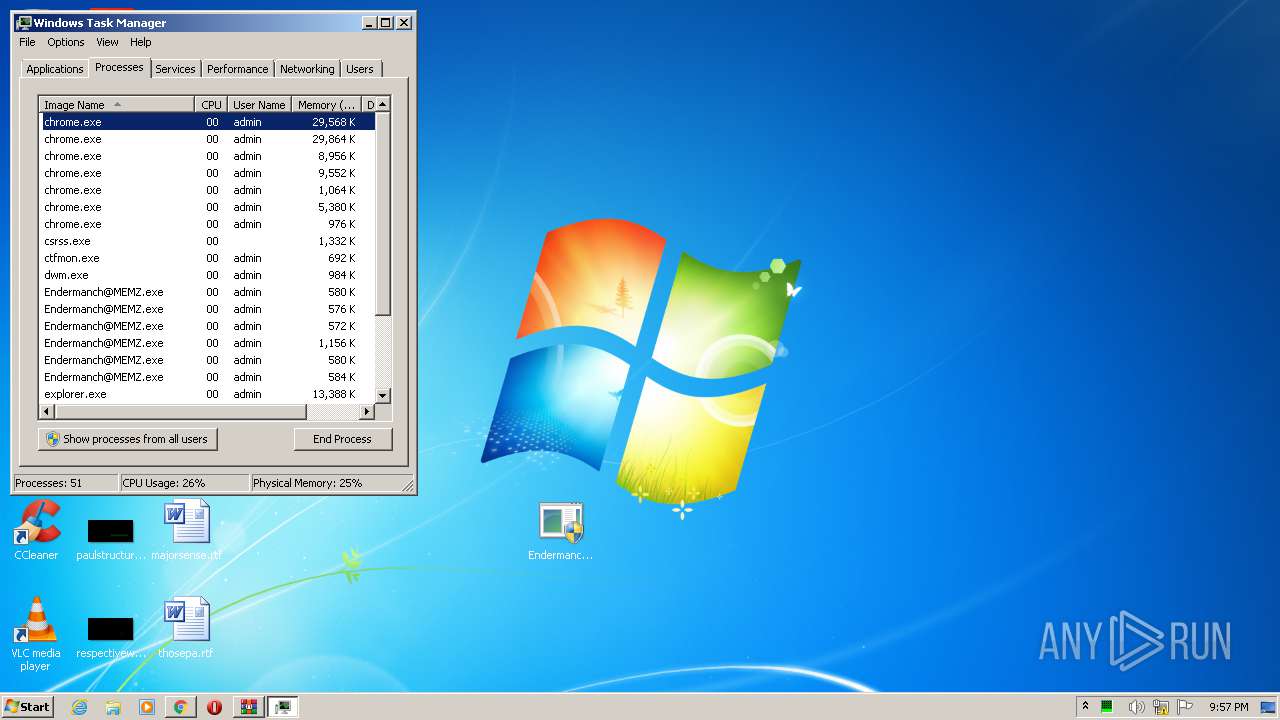
Application was dropped or rewritten from another process
- Endermanch@MEMZ.exe (PID: 840)
- Endermanch@MEMZ.exe (PID: 3100)
- Endermanch@MEMZ.exe (PID: 2224)
- Endermanch@MEMZ.exe (PID: 2476)
- Endermanch@MEMZ.exe (PID: 1972)
- Endermanch@MEMZ.exe (PID: 3356)
- Endermanch@MEMZ.exe (PID: 1756)
- Endermanch@MEMZ.exe (PID: 2860)
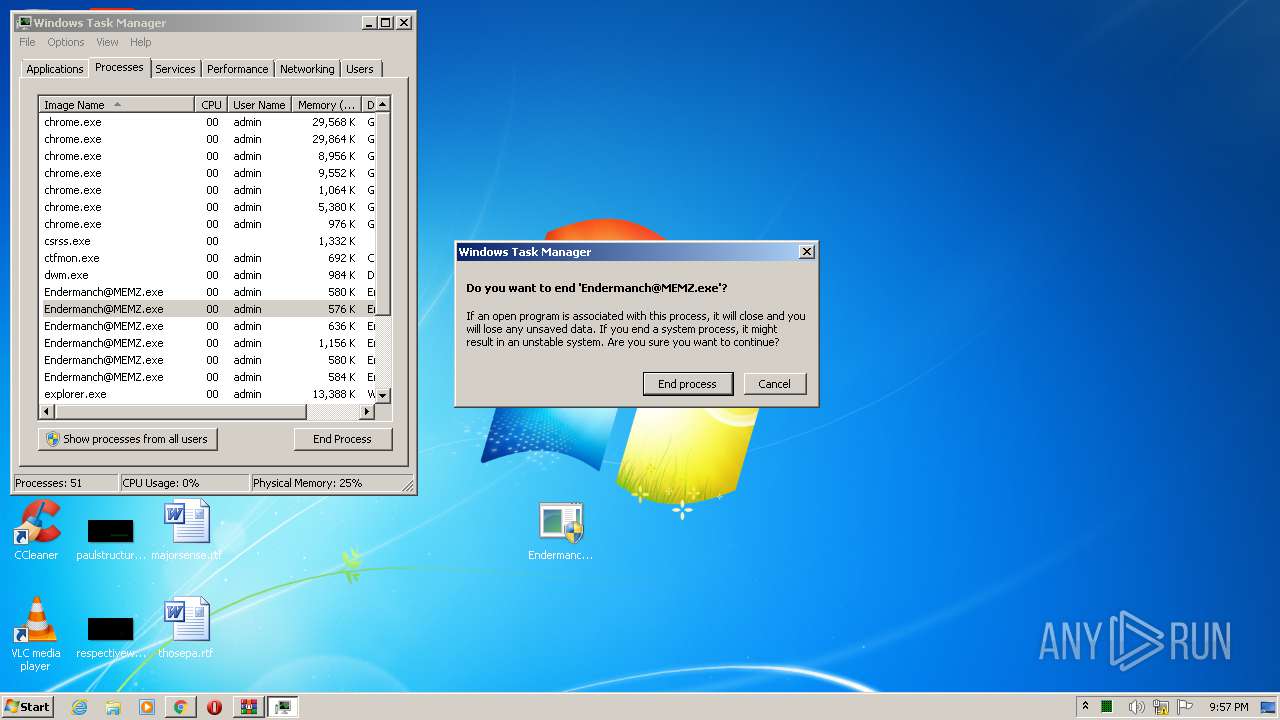
Low-level write access rights to disk partition
- Endermanch@MEMZ.exe (PID: 2476)
SUSPICIOUS
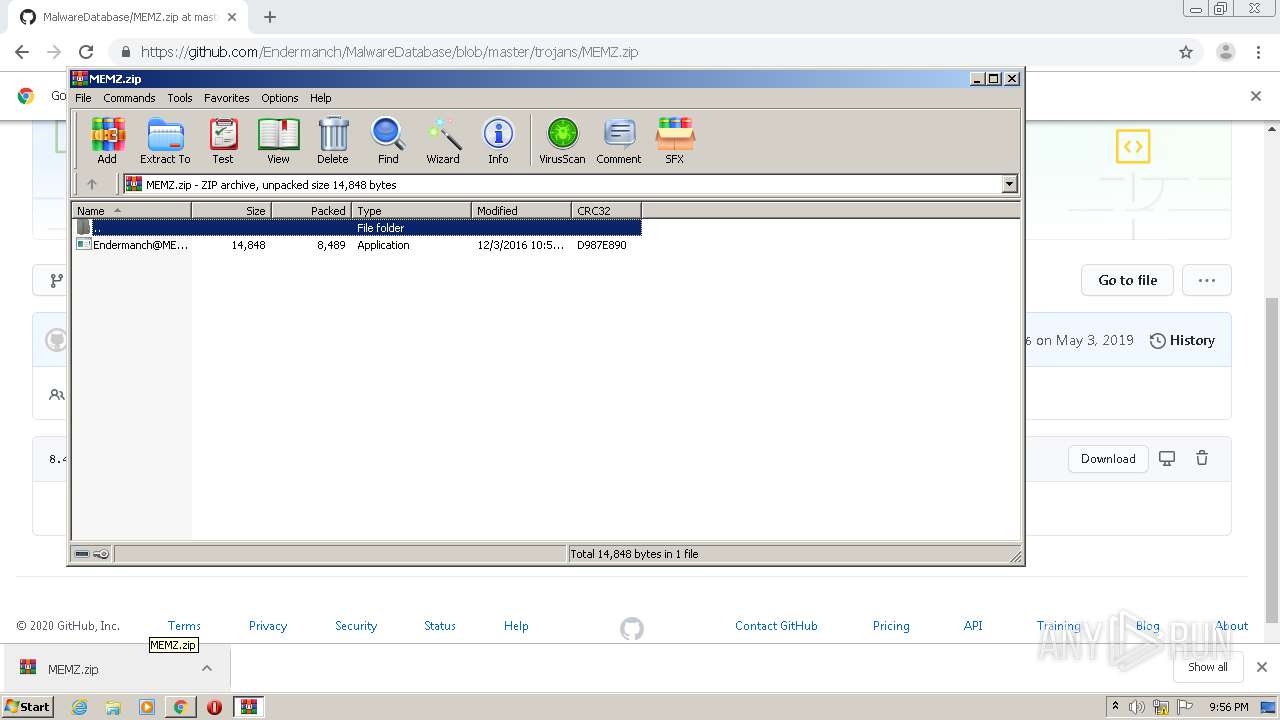
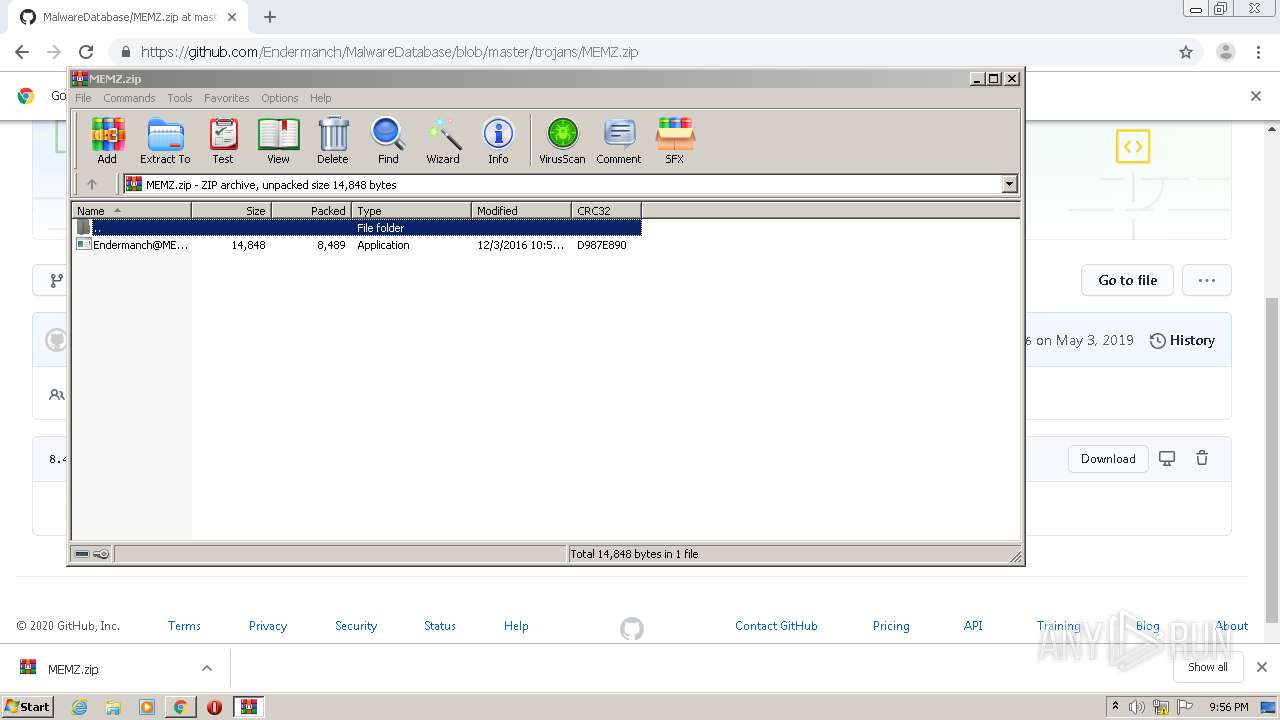
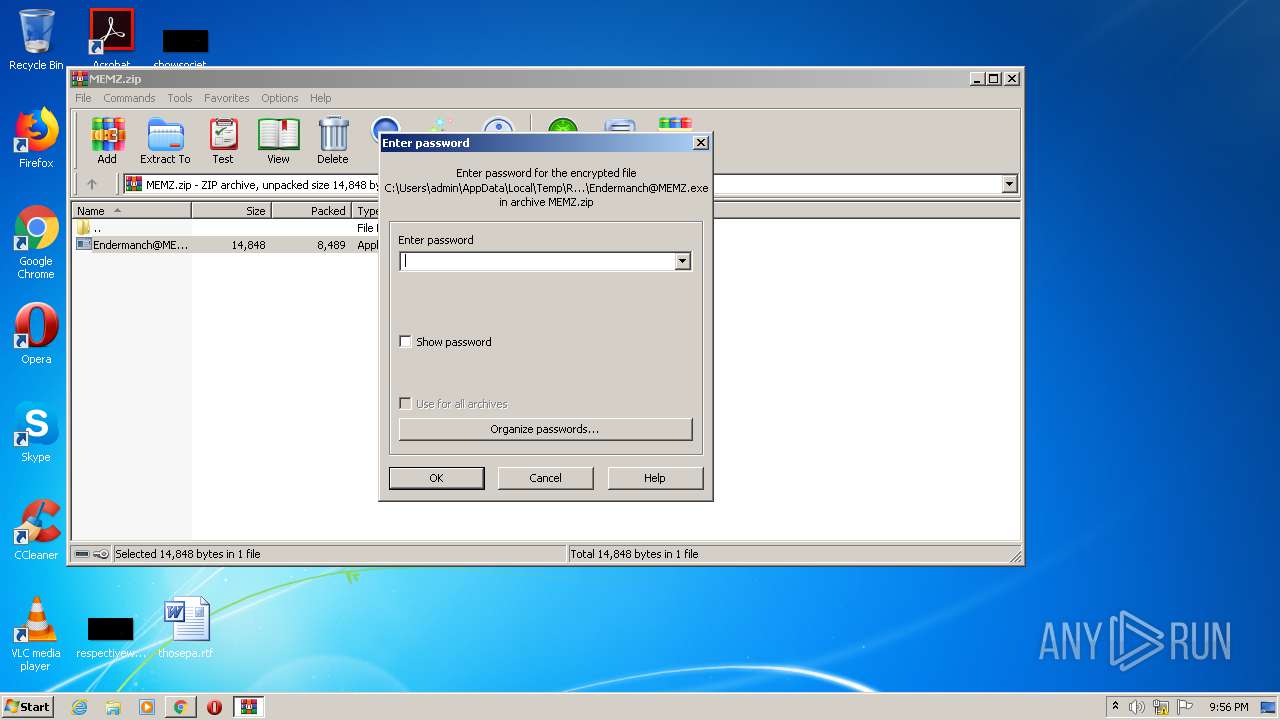
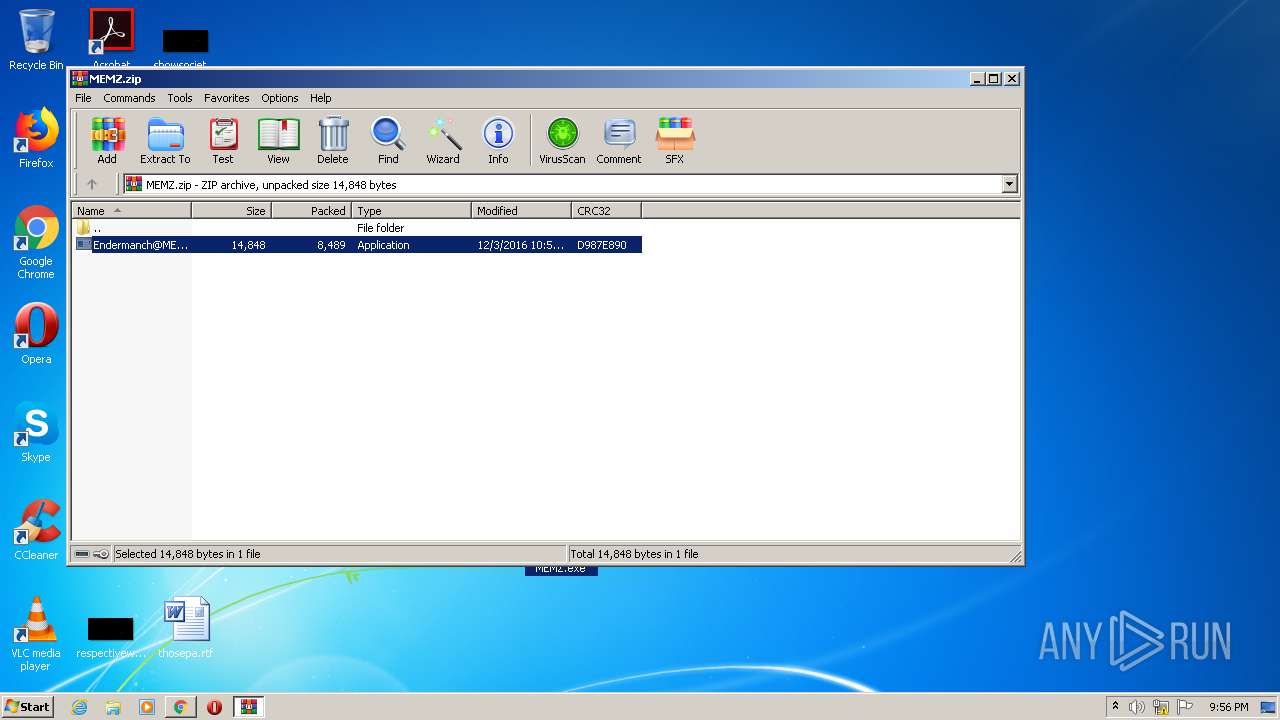
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3748)
Application launched itself
- Endermanch@MEMZ.exe (PID: 840)
Low-level read access rights to disk partition
- Endermanch@MEMZ.exe (PID: 2476)
Starts Internet Explorer
- Endermanch@MEMZ.exe (PID: 2476)
INFO
Application launched itself
- chrome.exe (PID: 908)
- iexplore.exe (PID: 120)
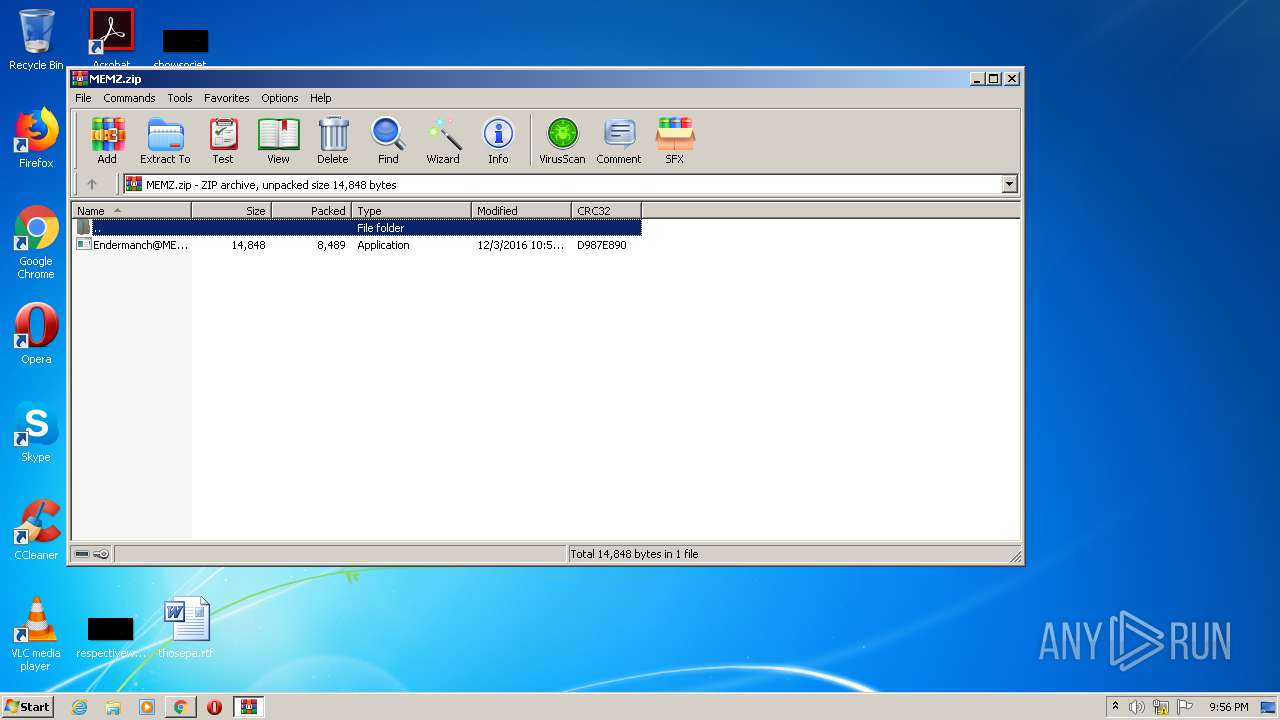
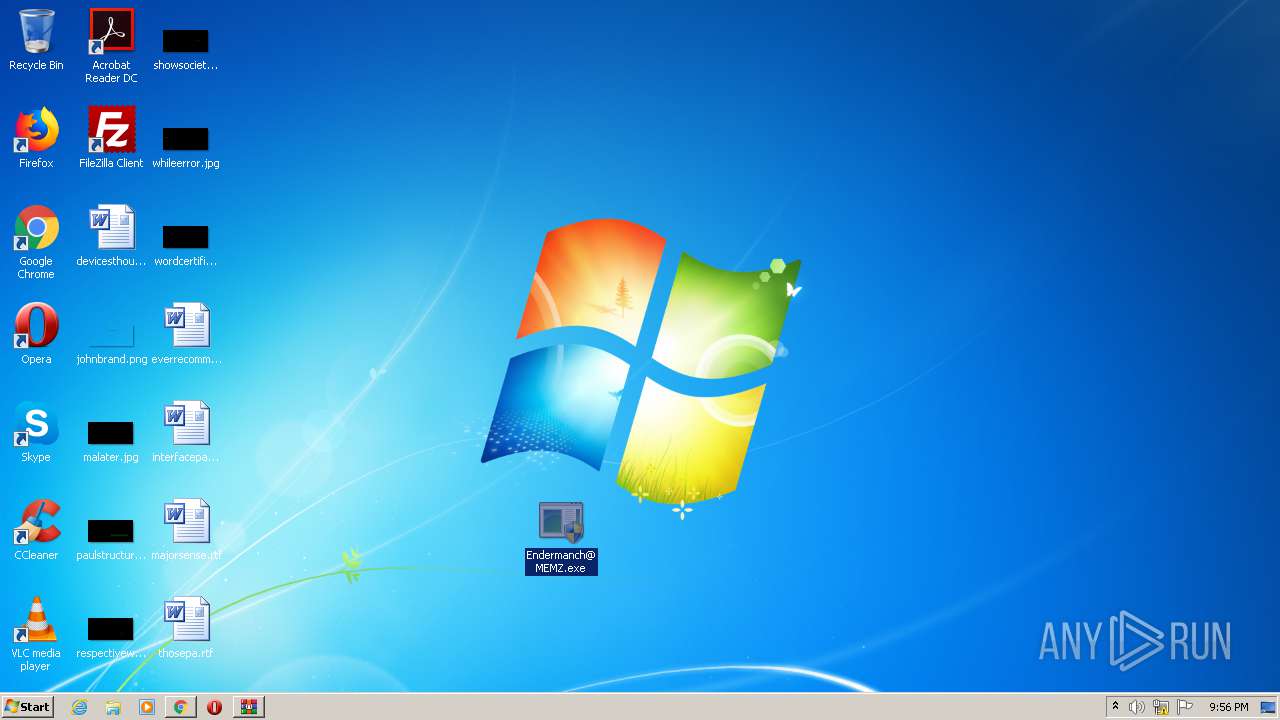
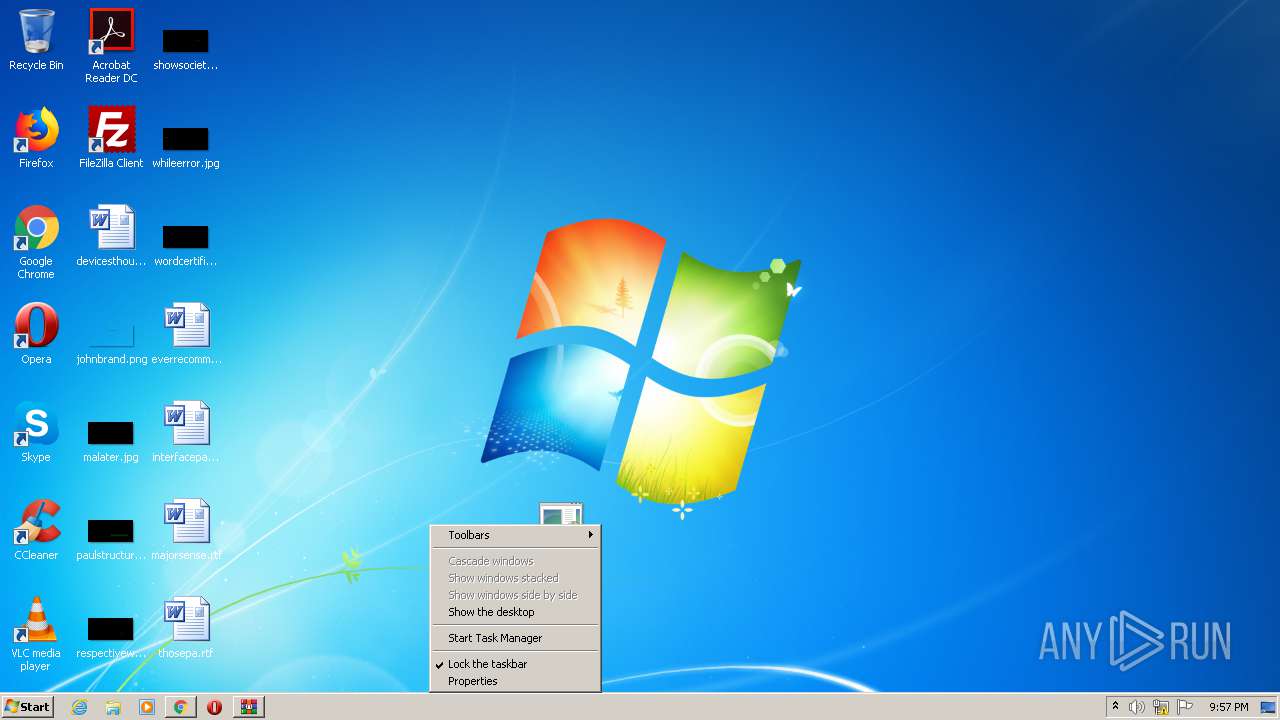
Manual execution by user
- Endermanch@MEMZ.exe (PID: 840)
- Endermanch@MEMZ.exe (PID: 2860)
- taskmgr.exe (PID: 3400)
Changes internet zones settings
- iexplore.exe (PID: 120)
Reads Internet Cache Settings
- iexplore.exe (PID: 120)
- chrome.exe (PID: 908)
- iexplore.exe (PID: 3680)
Reads the hosts file
- chrome.exe (PID: 908)
- chrome.exe (PID: 2532)
Reads settings of System Certificates
- chrome.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
30
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=virus.exe | C:\Program Files\Internet Explorer\iexplore.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11849531455901525865 --mojo-platform-channel-handle=3508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6839836296941118292 --mojo-platform-channel-handle=2636 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Users\admin\Desktop\Endermanch@MEMZ.exe" | C:\Users\admin\Desktop\Endermanch@MEMZ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
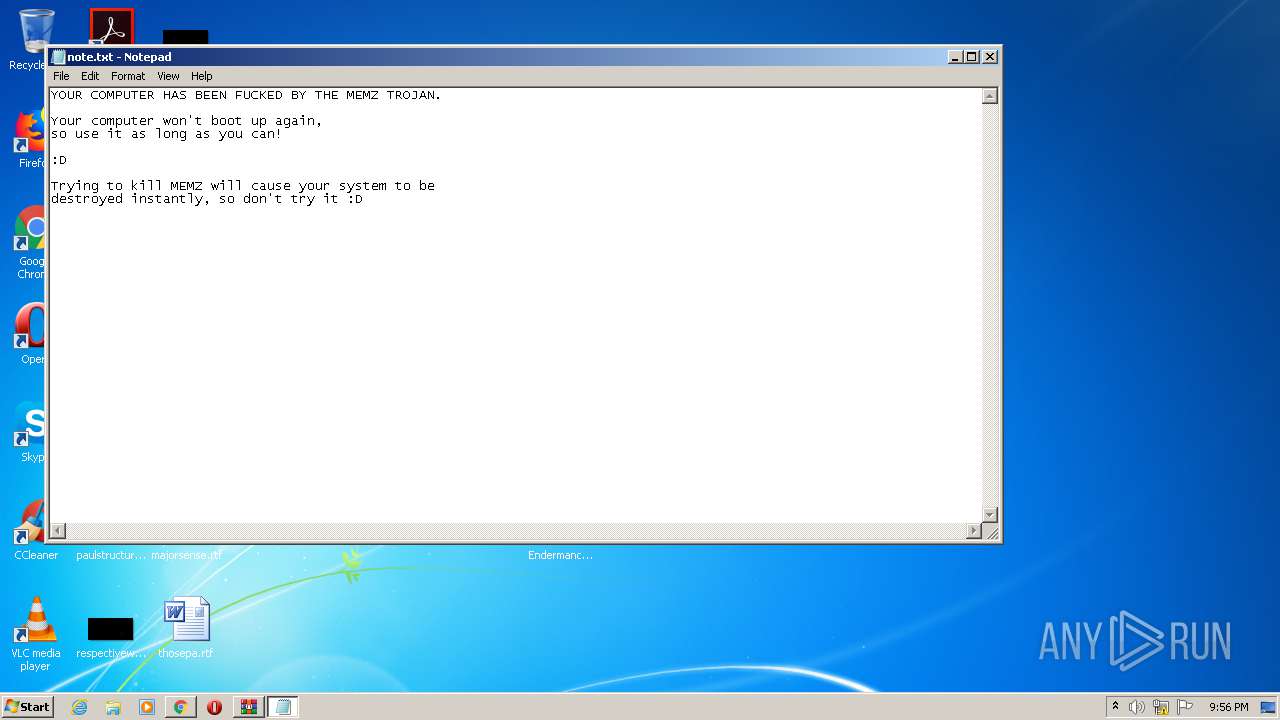
| 872 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\System32\notepad.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11261206010354042979 --mojo-platform-channel-handle=3380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/Endermanch/MalwareDatabase" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8683719917875818242 --mojo-platform-channel-handle=3400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\Desktop\Endermanch@MEMZ.exe" /watchdog | C:\Users\admin\Desktop\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8491502707095798261,12482712264944810567,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6465391886828773421 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 065
Read events
1 872
Write events
188
Delete events
5
Modification events
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 908-13241393726201750 |
Value: 259 | |||
Executable files
1
Suspicious files
40
Text files
93
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6e08bad3-401e-4517-87cb-08d925717ea3.tmp | — | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14e732.TMP | text | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
31
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 302 | 216.58.212.132:80 | http://google.co.ck/search?q=virus.exe | US | html | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 140.82.118.3:443 | github.com | — | US | malicious |
2532 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2532 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 151.101.0.133:443 | avatars0.githubusercontent.com | Fastly | US | malicious |
2532 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 172.217.23.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 52.206.227.240:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
2532 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2532 | chrome.exe | 140.82.118.6:443 | api.github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
avatars3.githubusercontent.com |
| whitelisted |