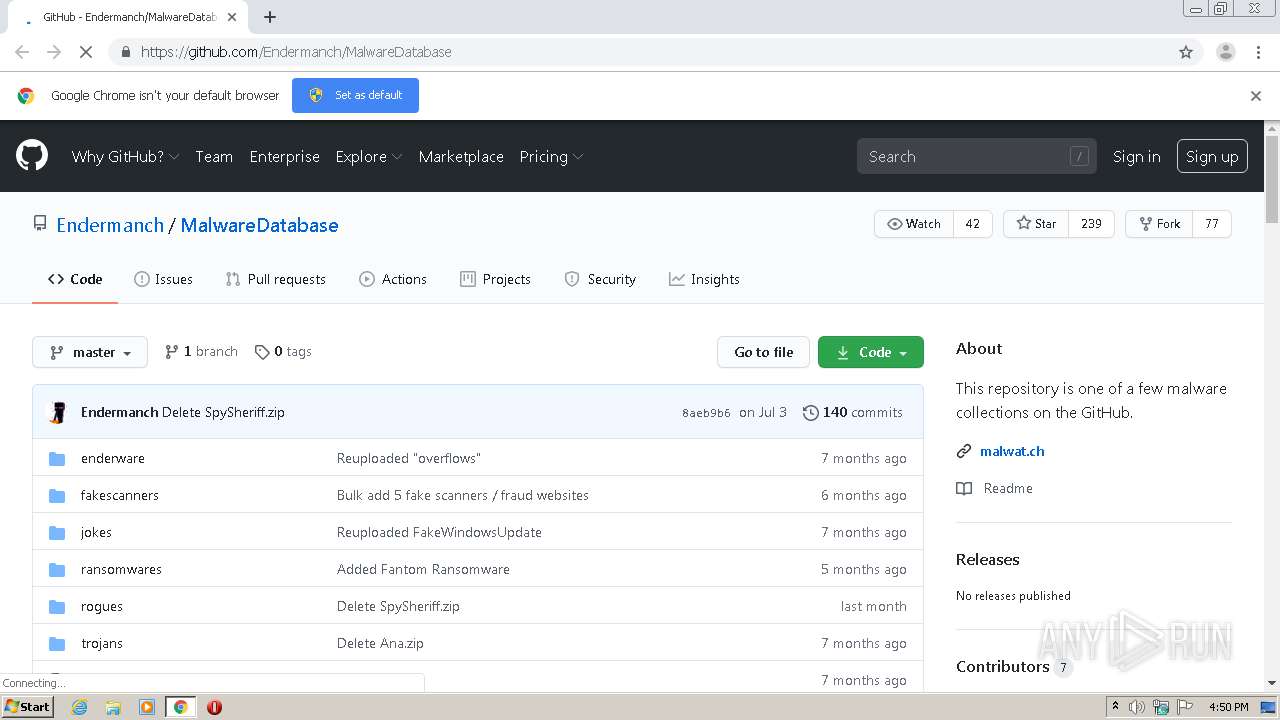
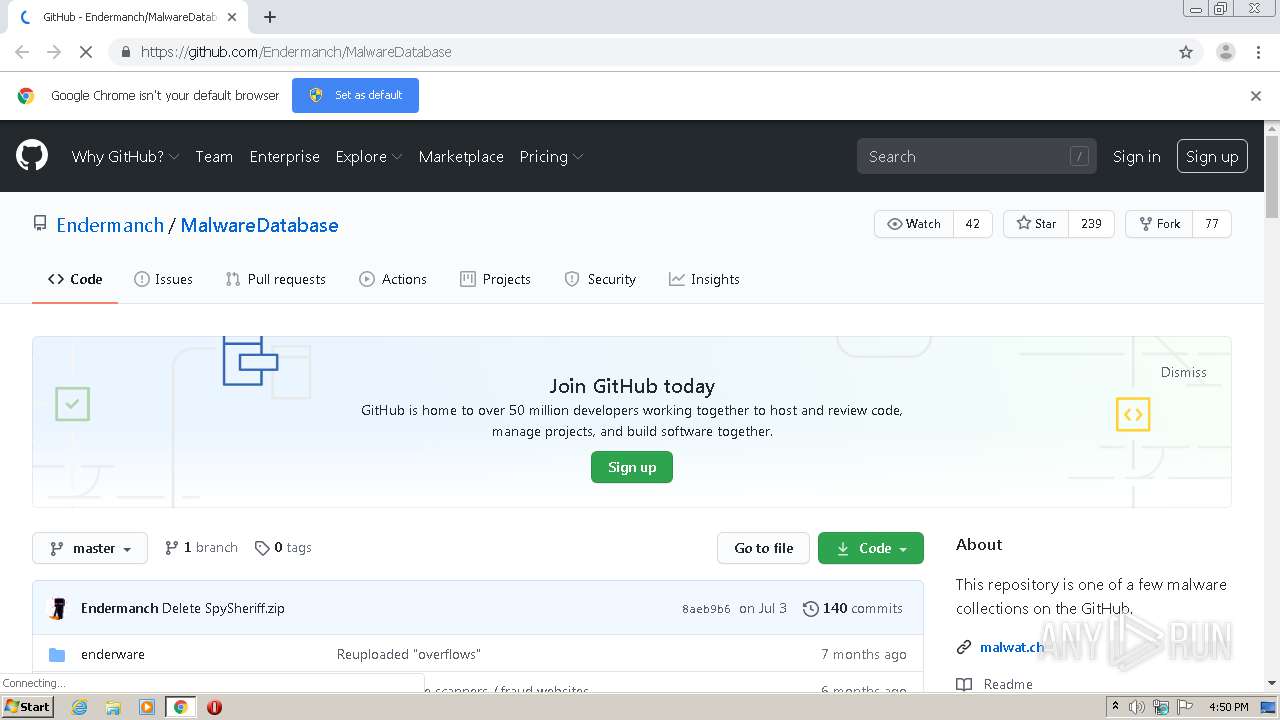
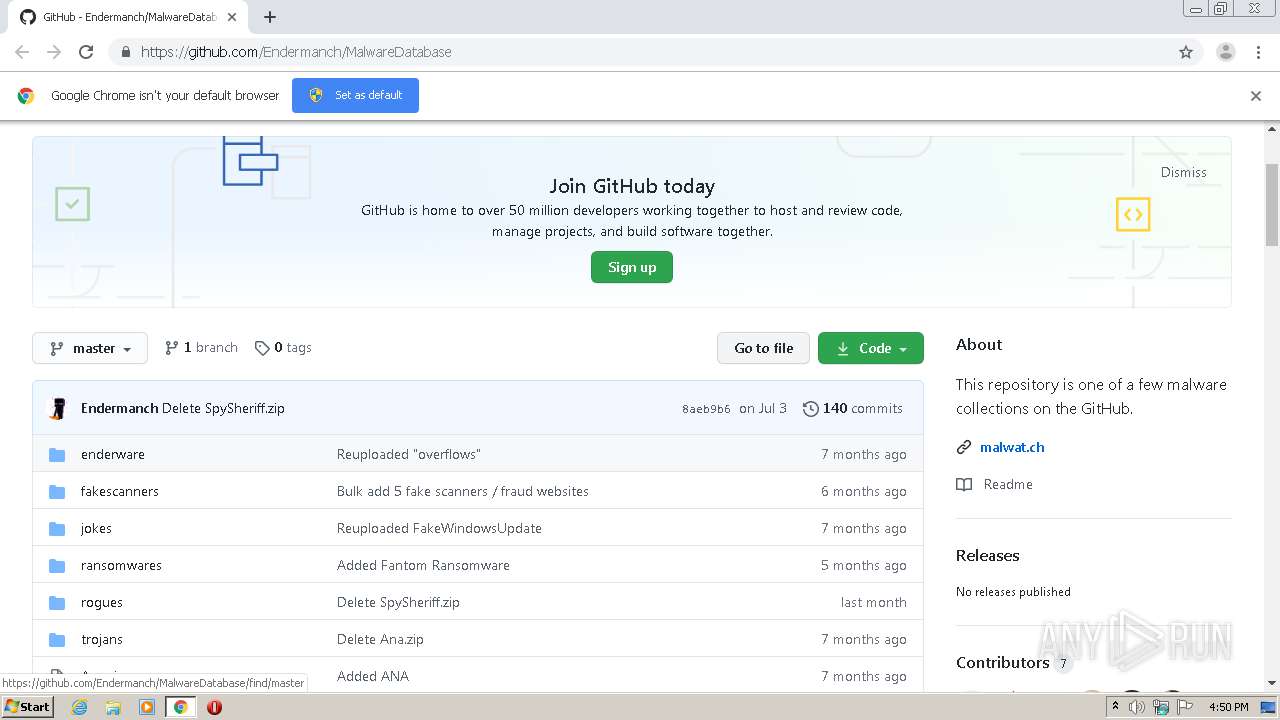
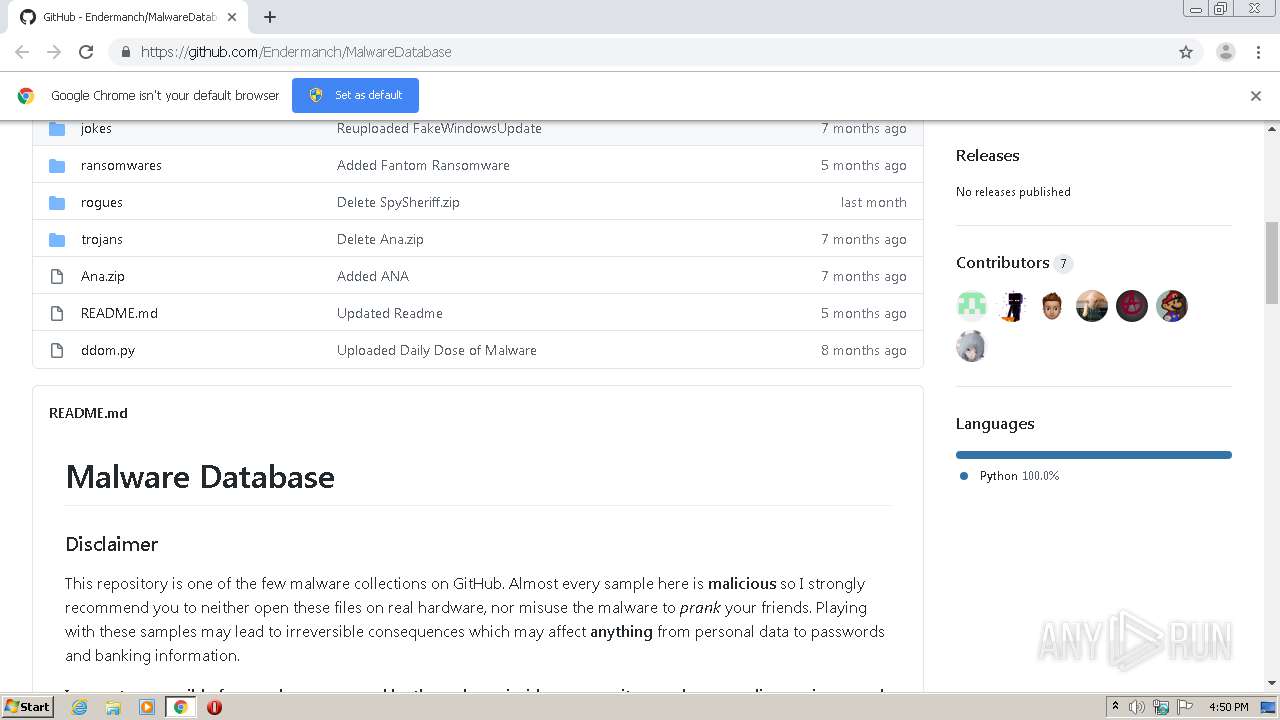
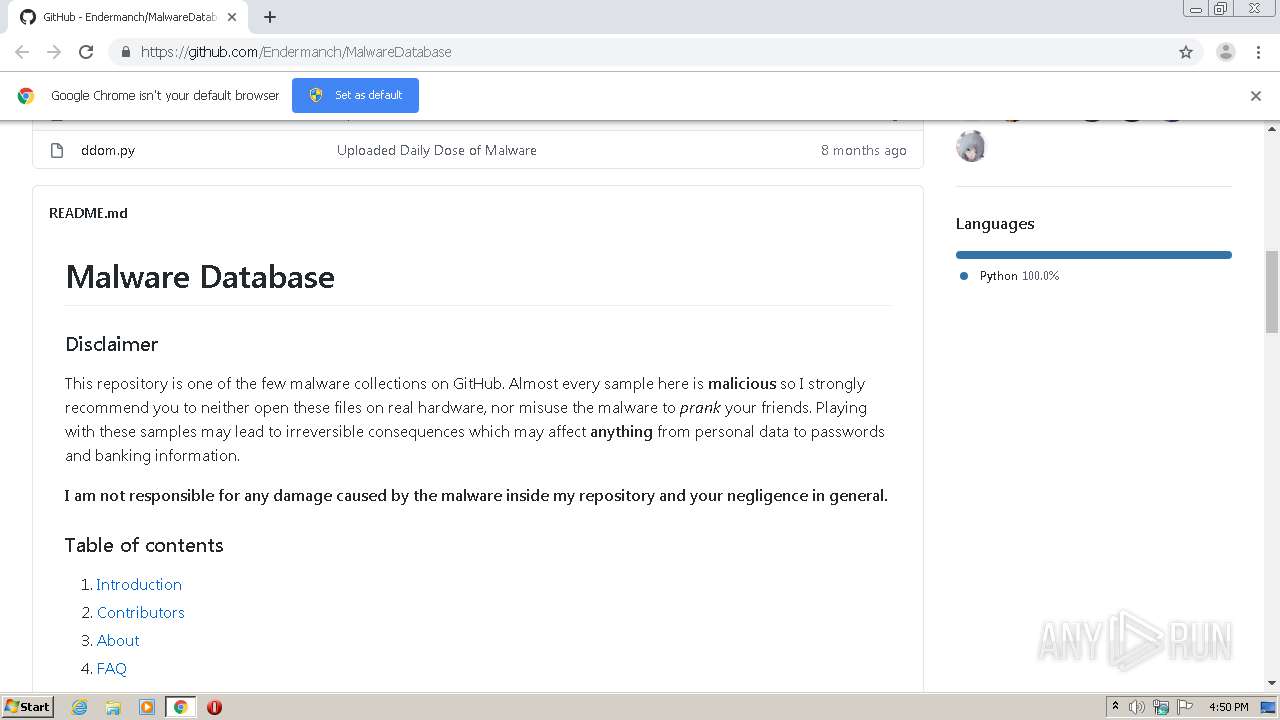
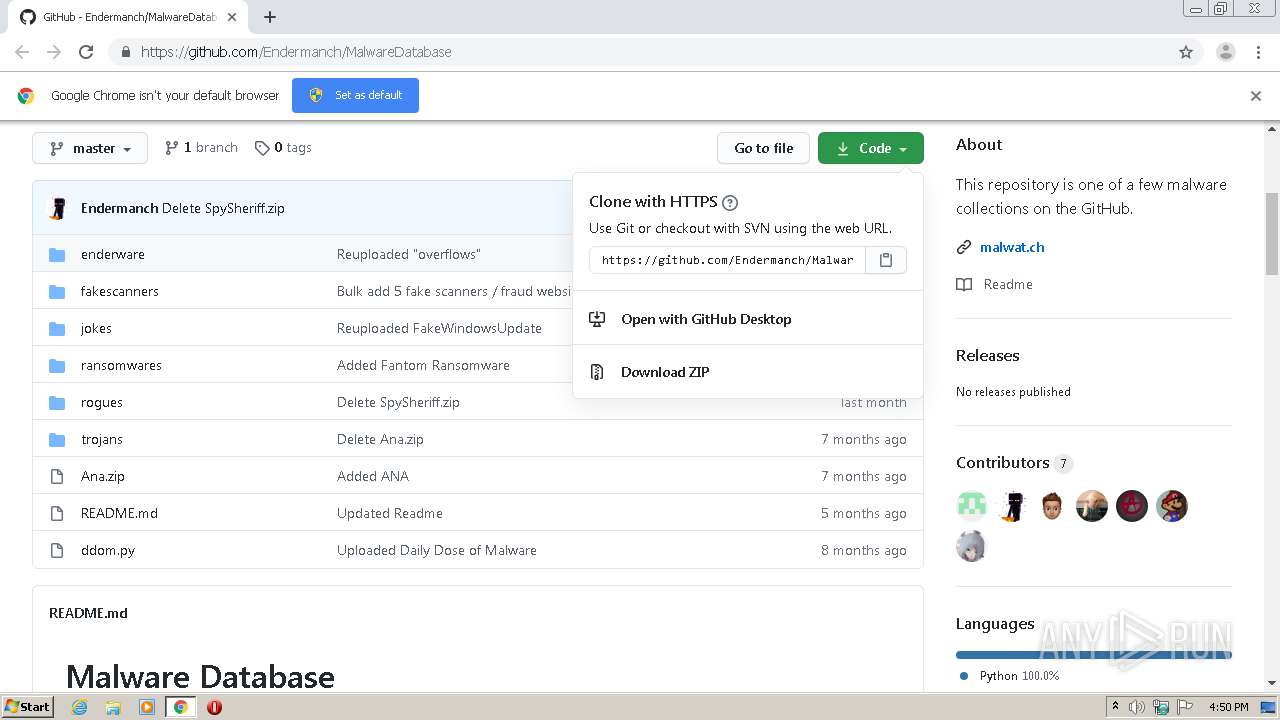
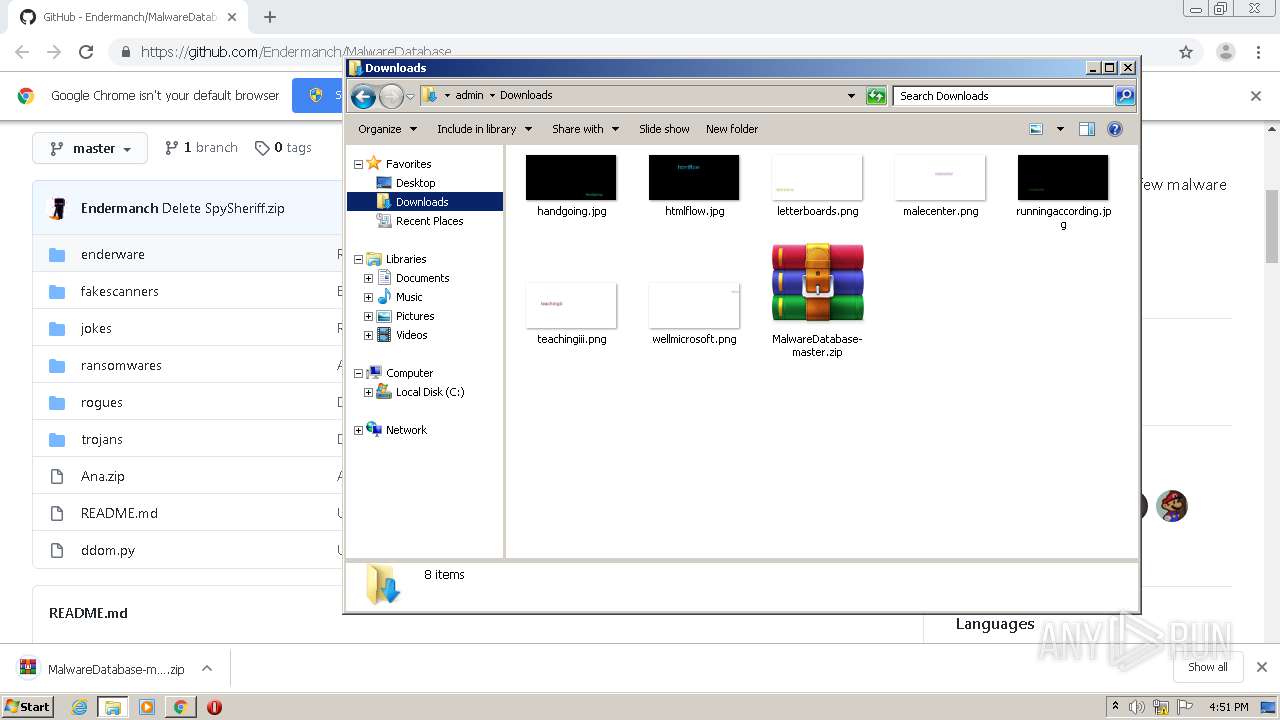
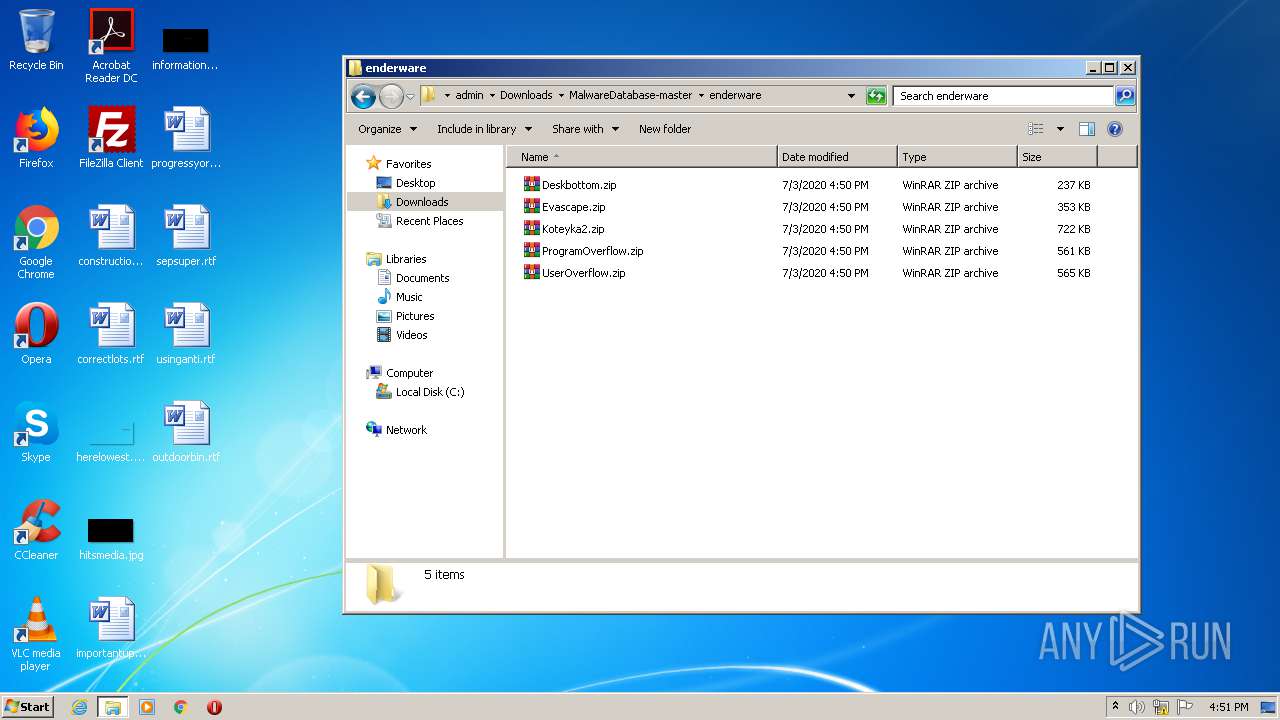
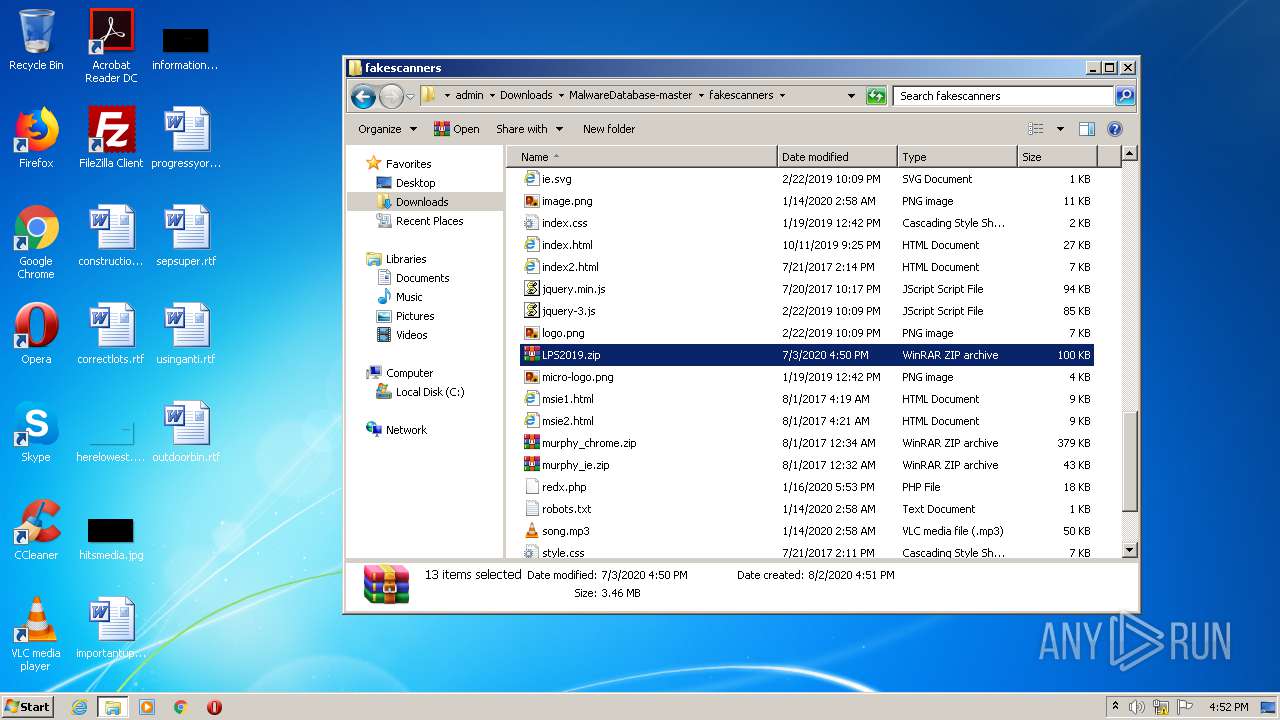
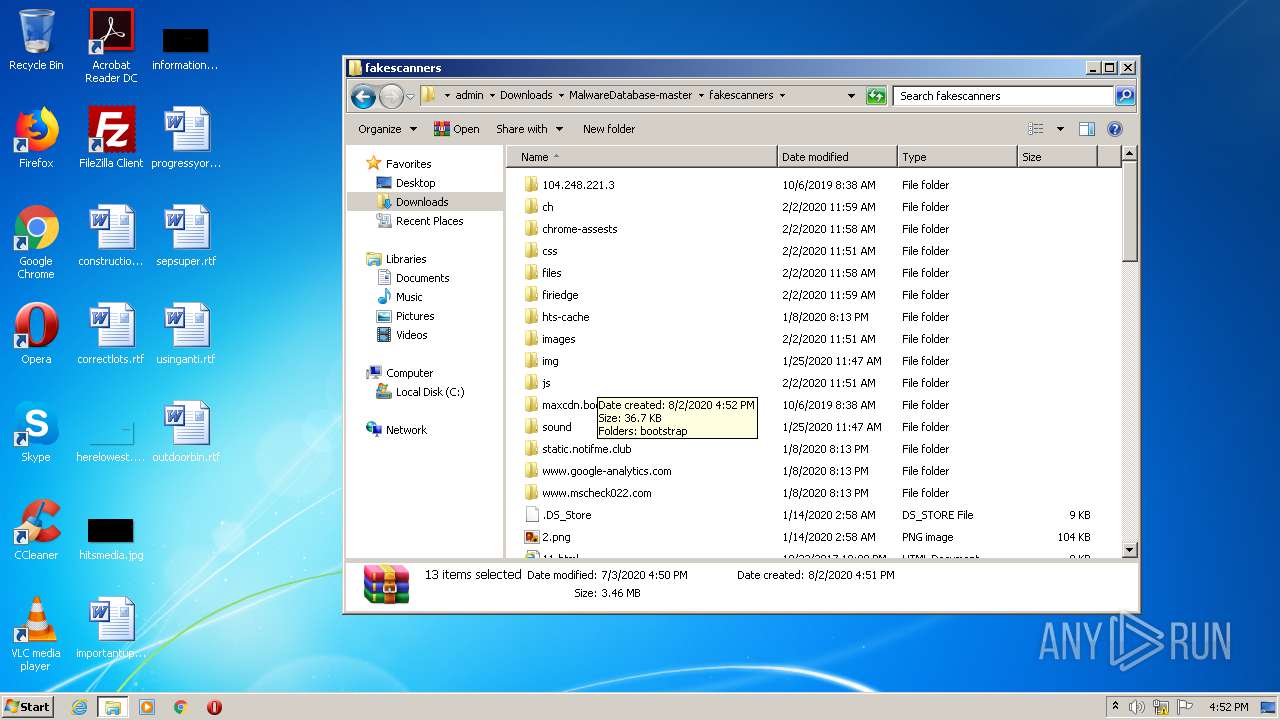
| URL: | https://github.com/Endermanch/MalwareDatabase |
| Full analysis: | https://app.any.run/tasks/5caf0698-14ce-40e1-8e6a-51f35a8485c8 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2020, 15:50:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
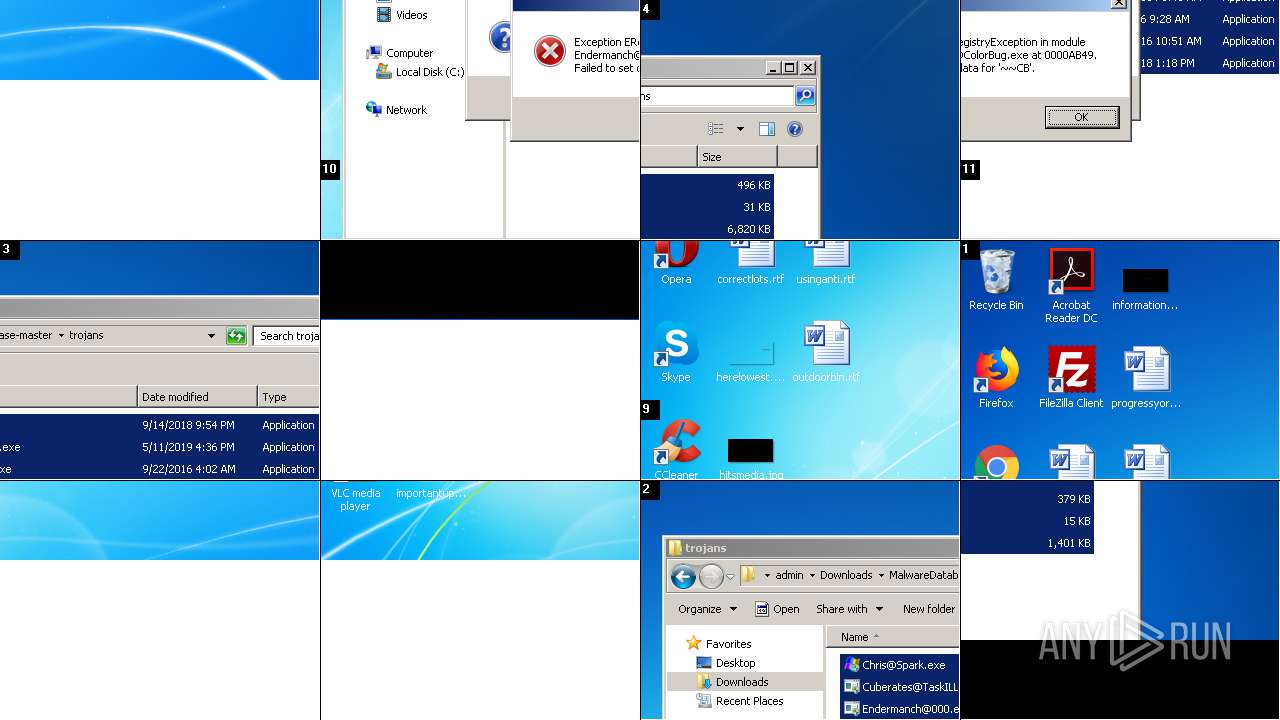
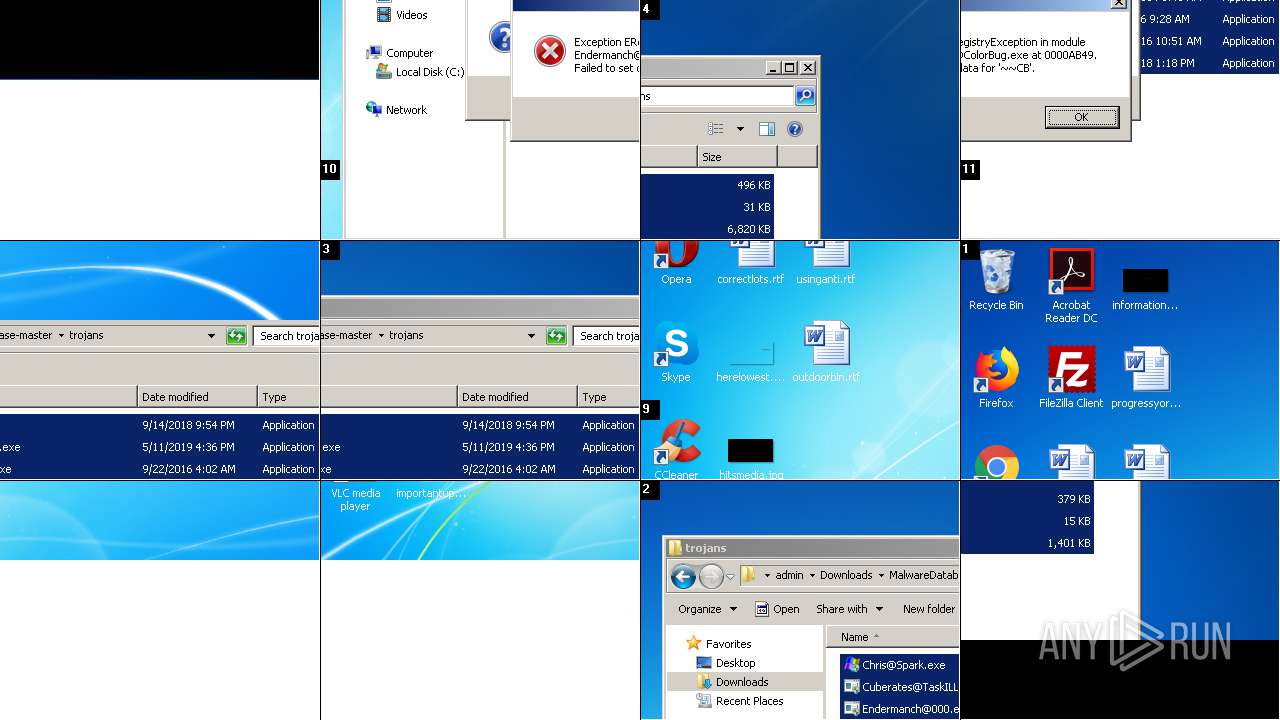
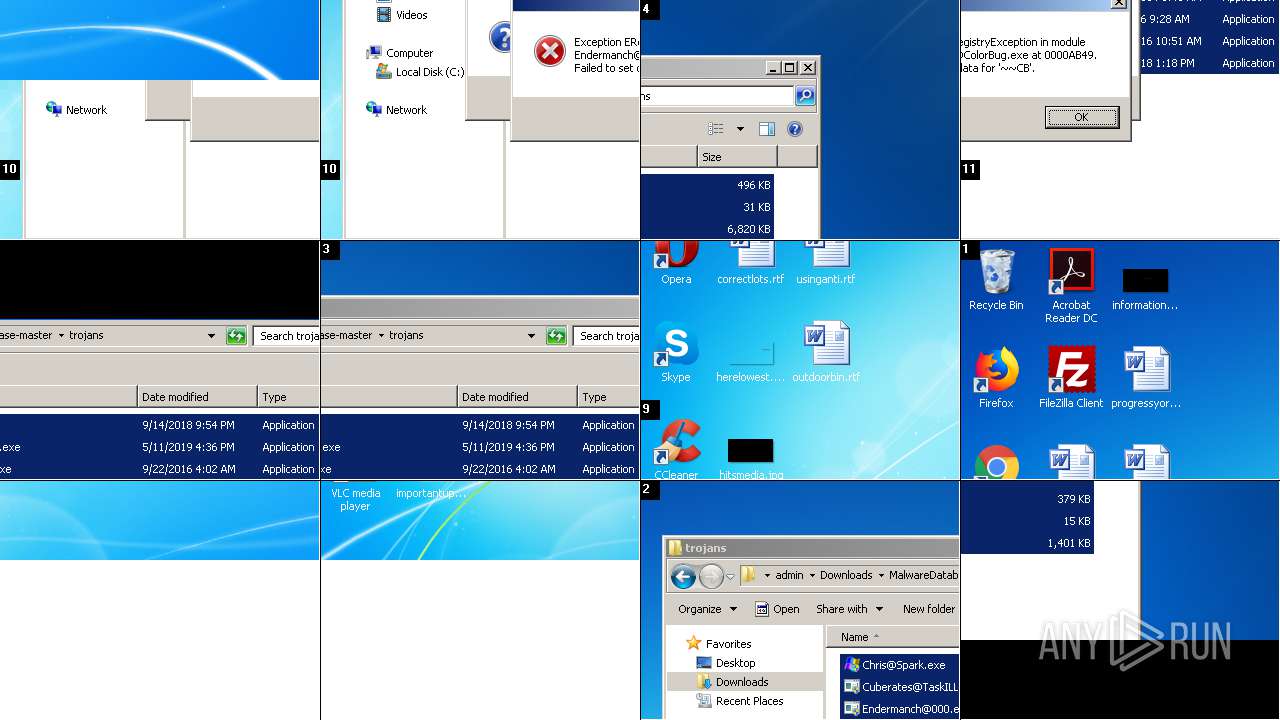
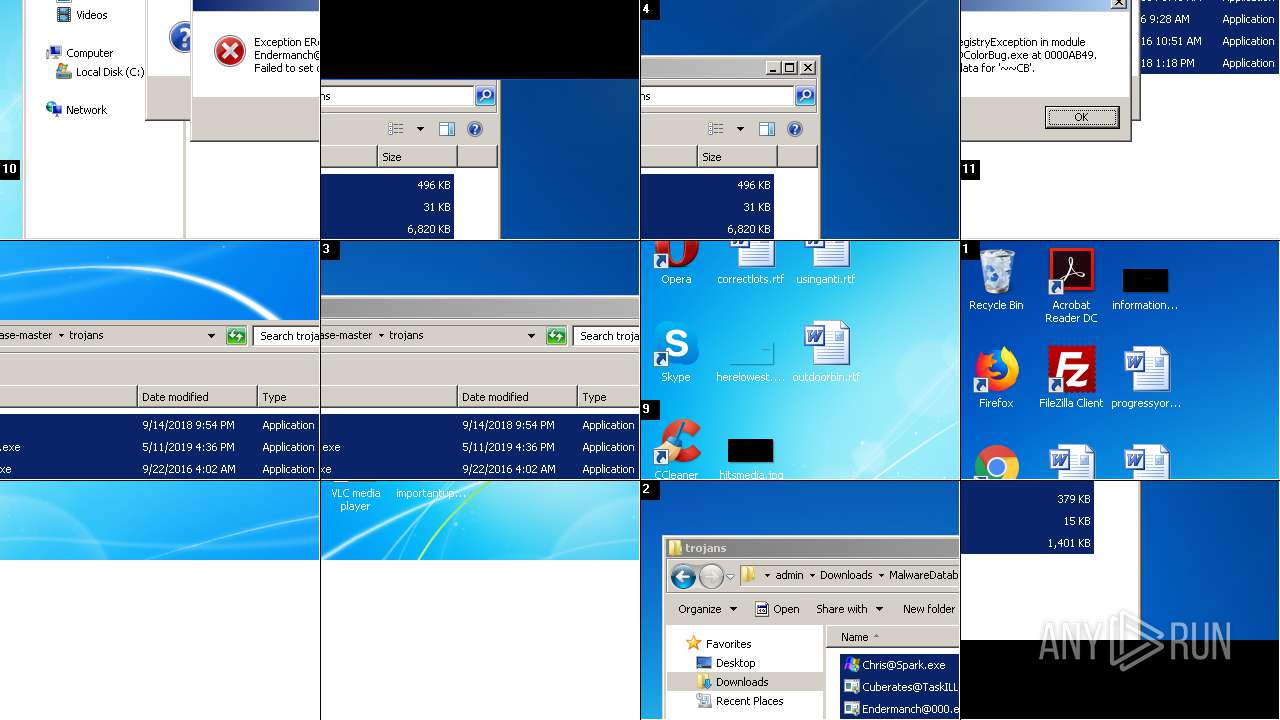
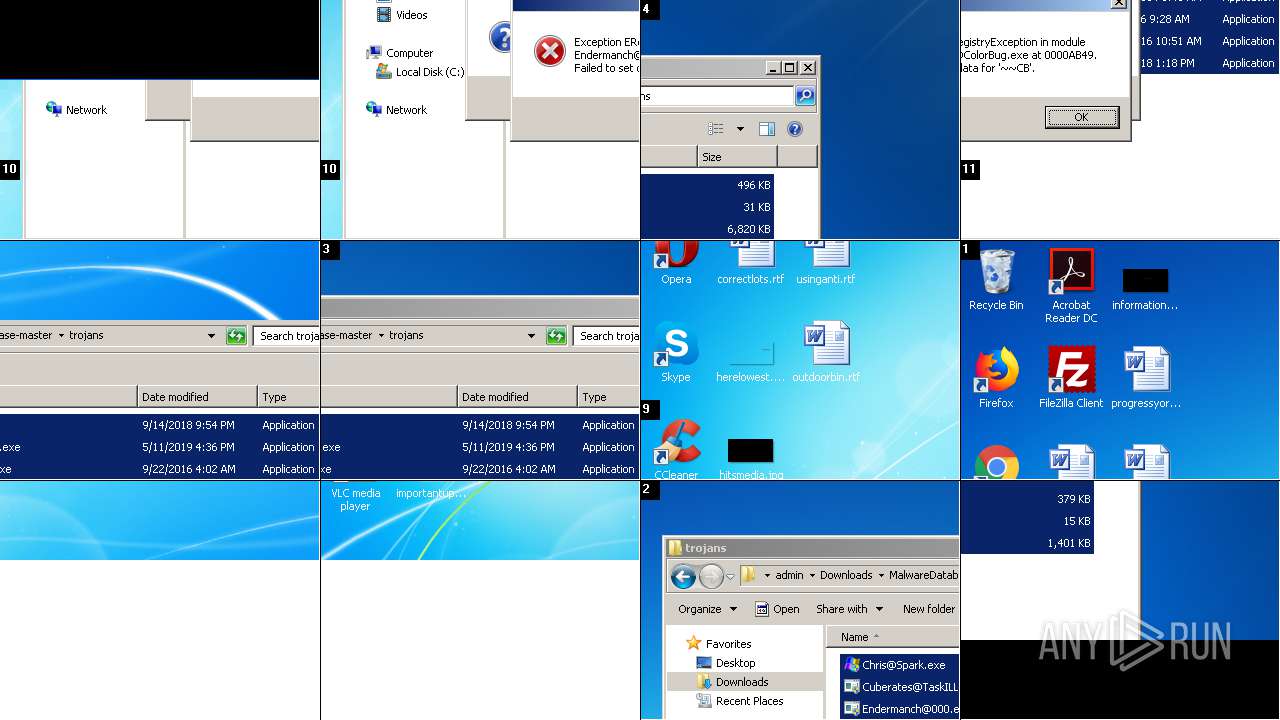
MALICIOUS
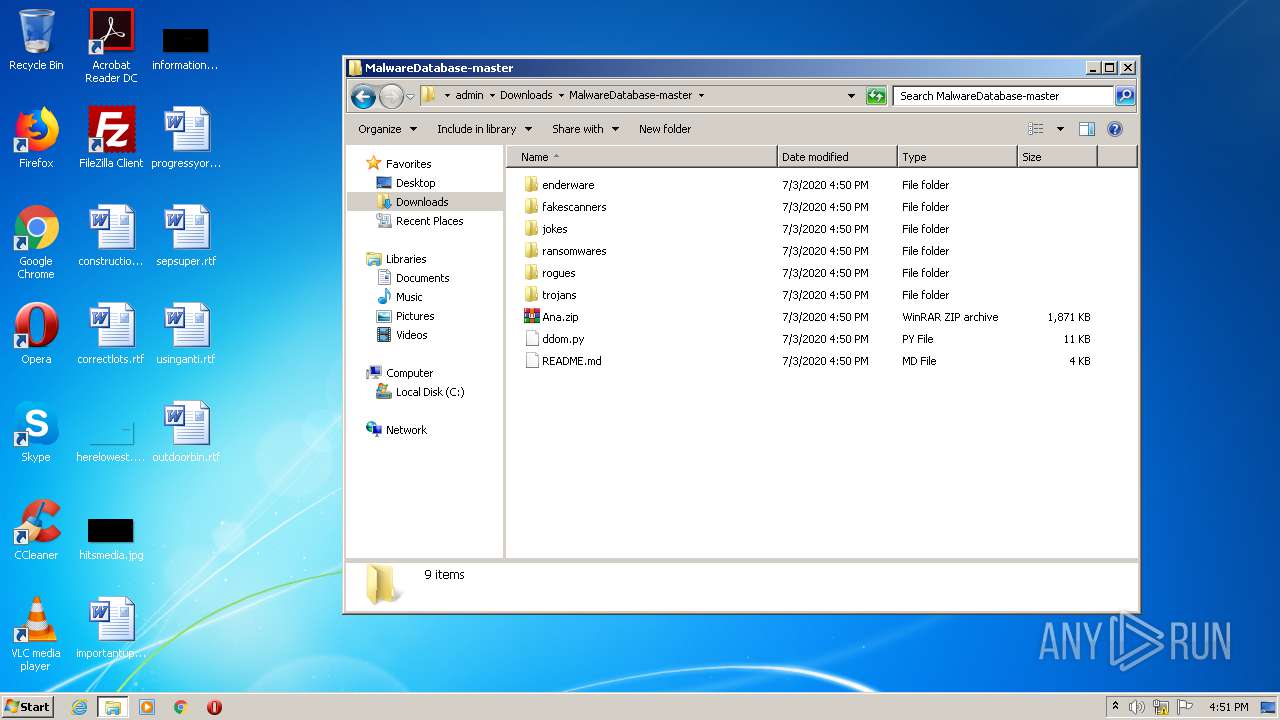
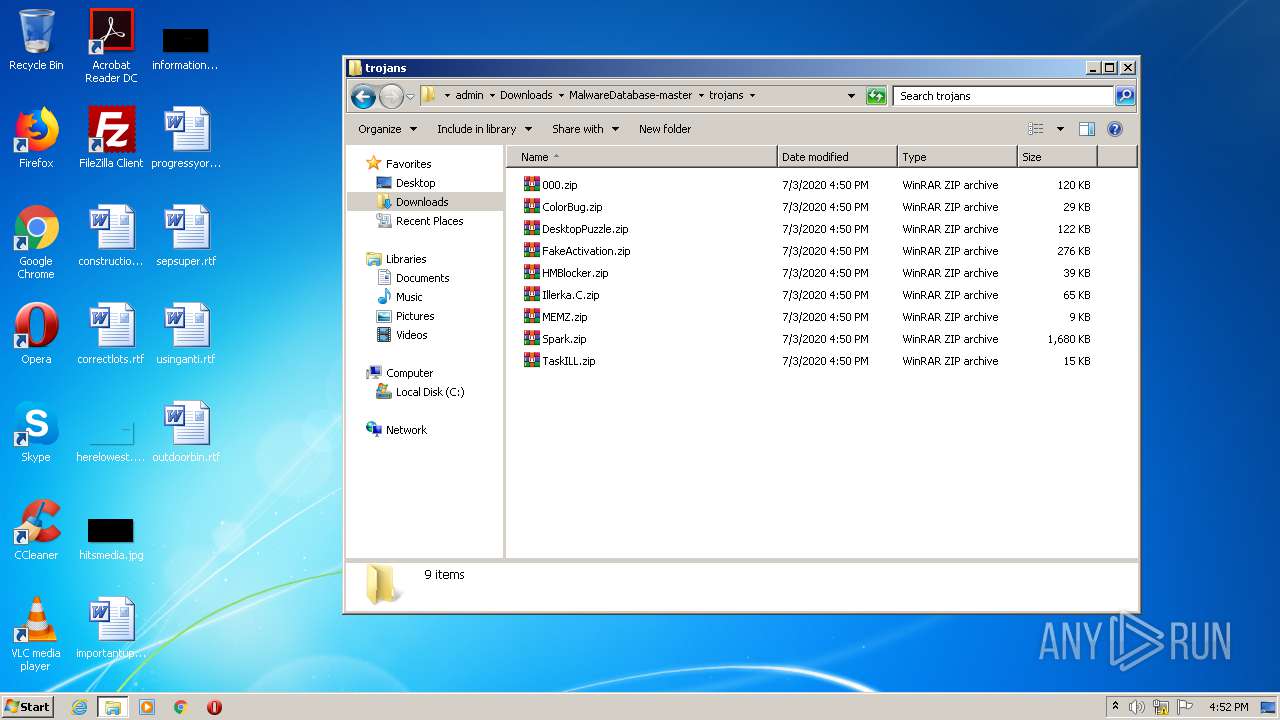
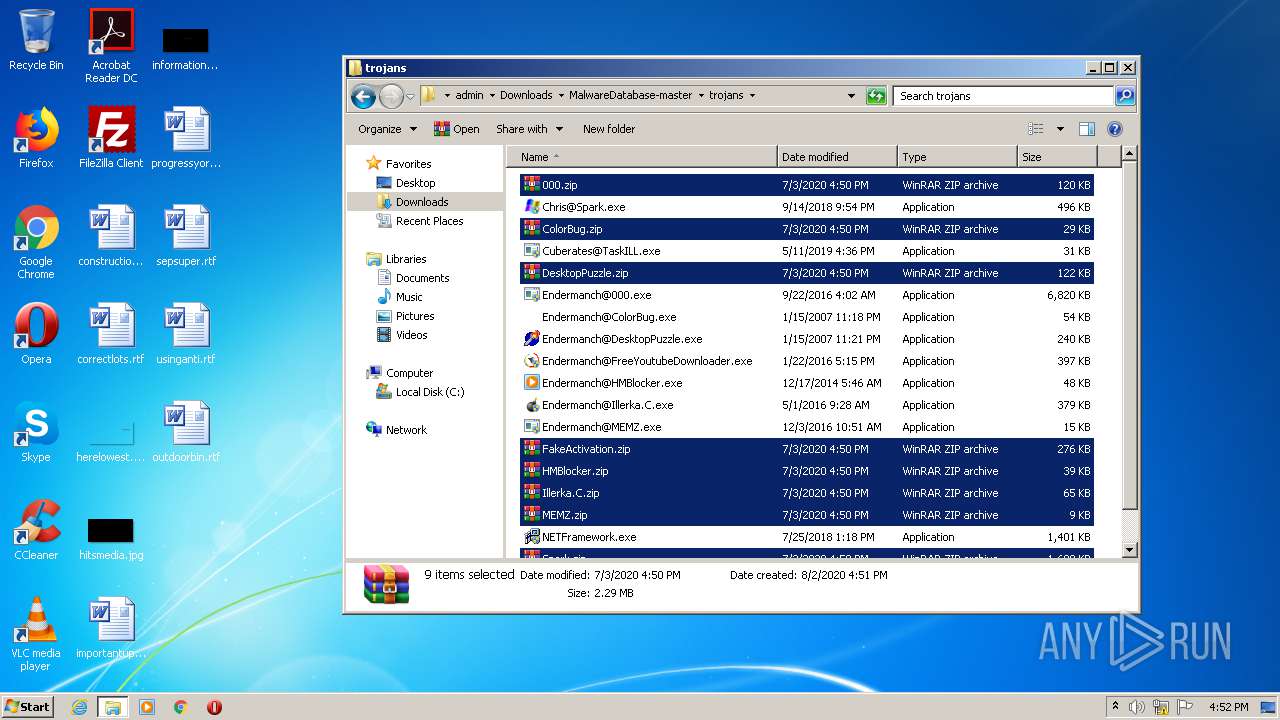
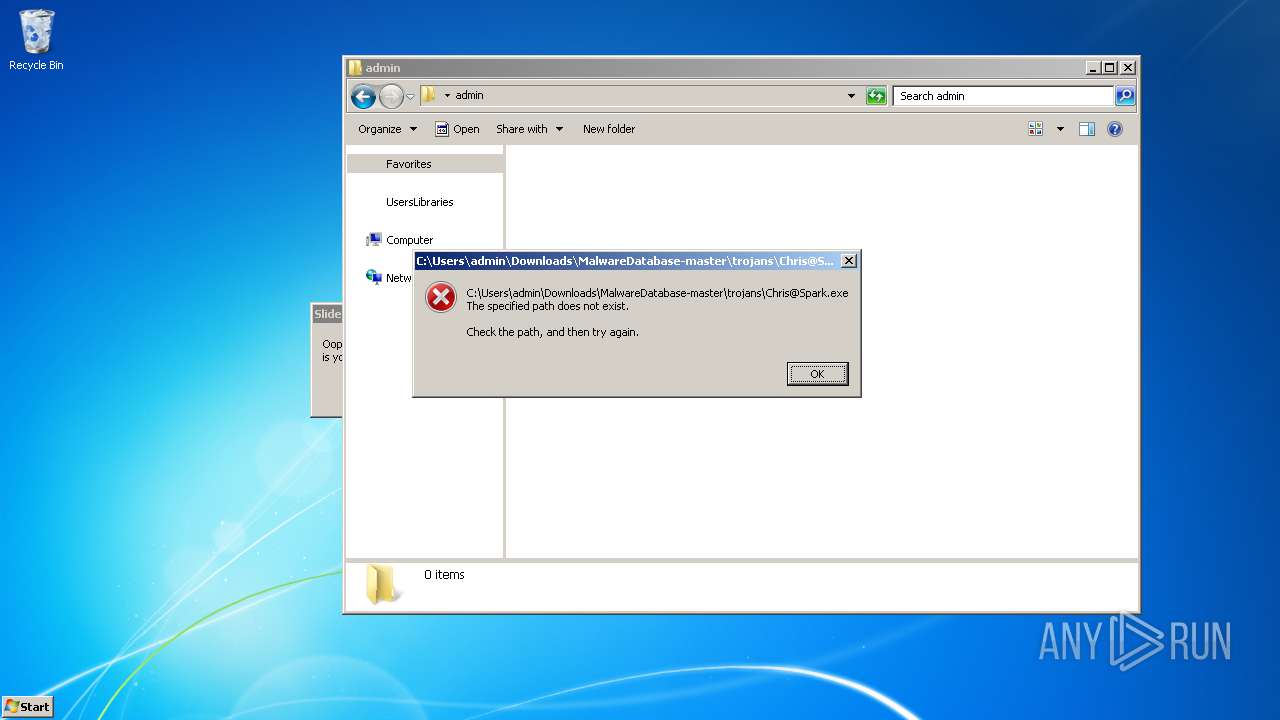
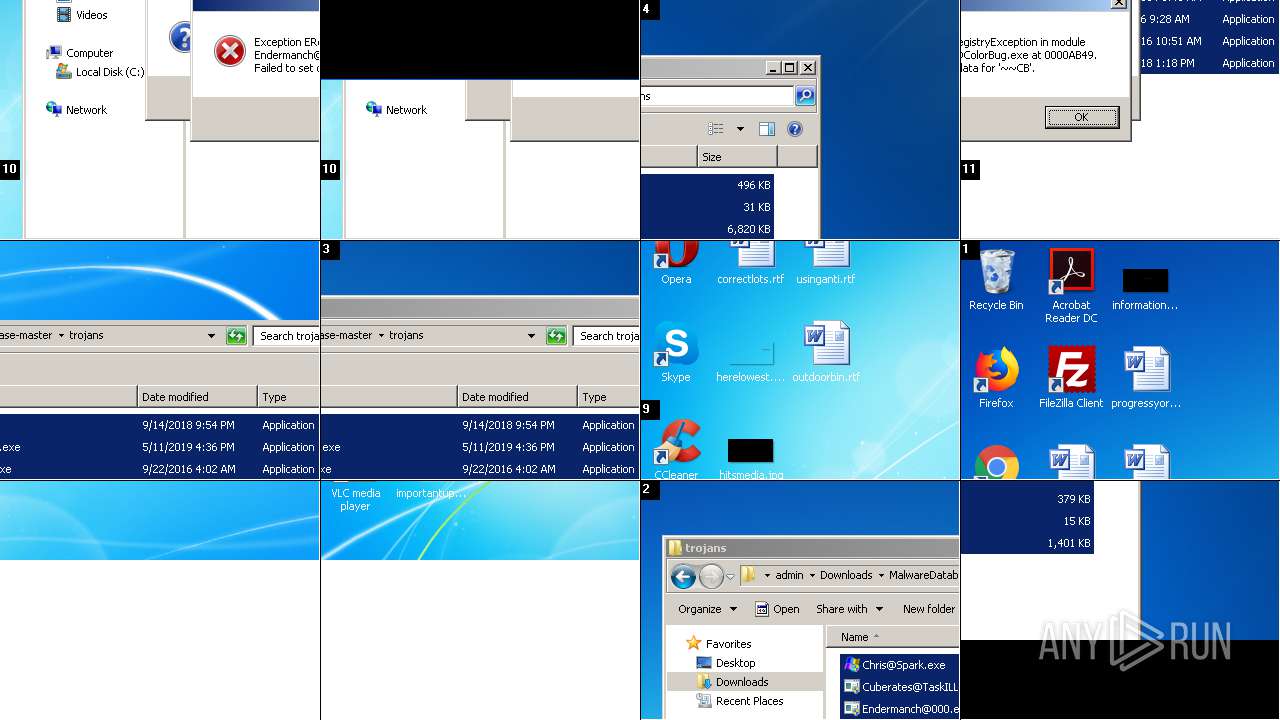
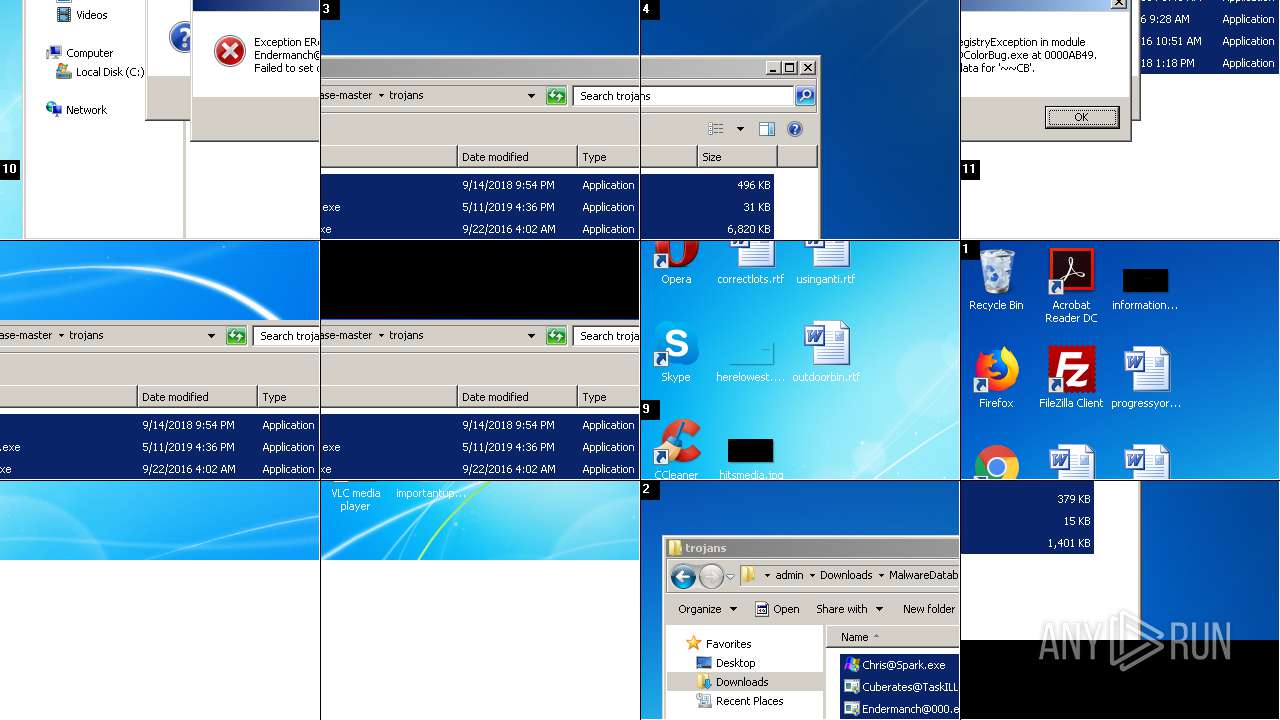
Application was dropped or rewritten from another process
- Chris@Spark.exe (PID: 3048)
- Cuberates@TaskILL.exe (PID: 3388)
- Chris@Spark.exe (PID: 3692)
- Cuberates@TaskILL.exe (PID: 1444)
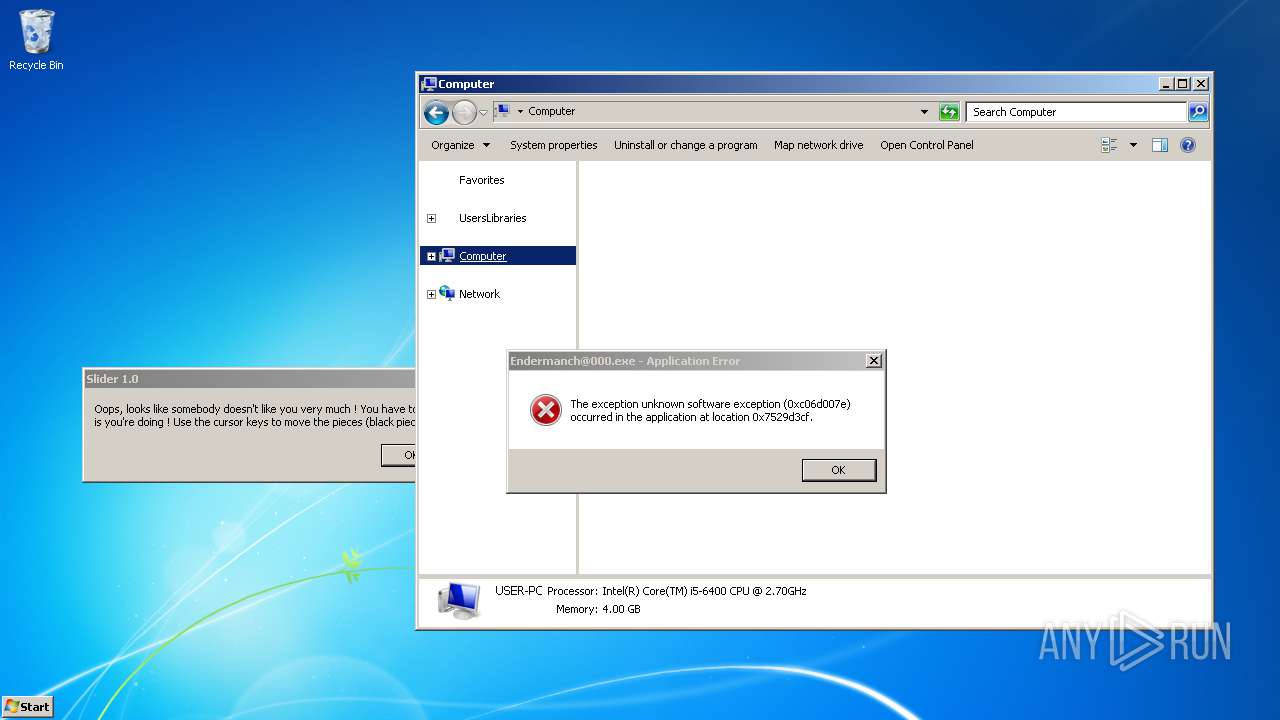
- Endermanch@000.exe (PID: 2112)
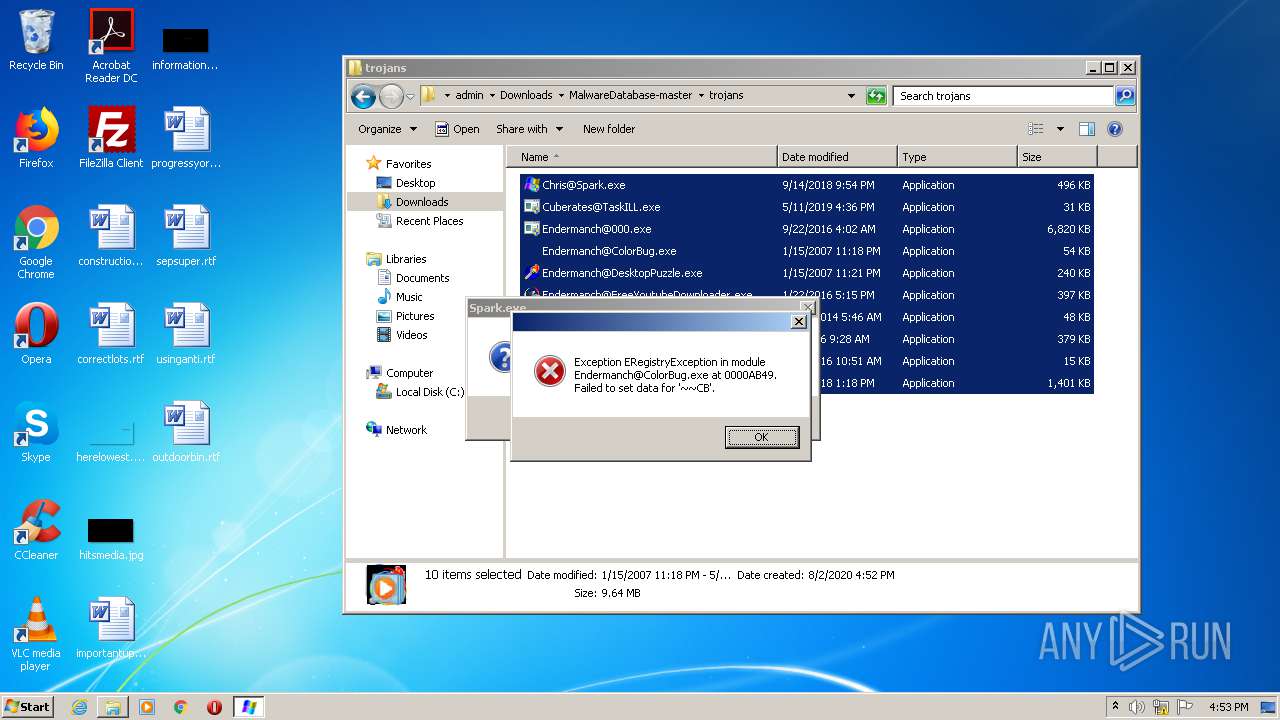
- Endermanch@ColorBug.exe (PID: 2560)
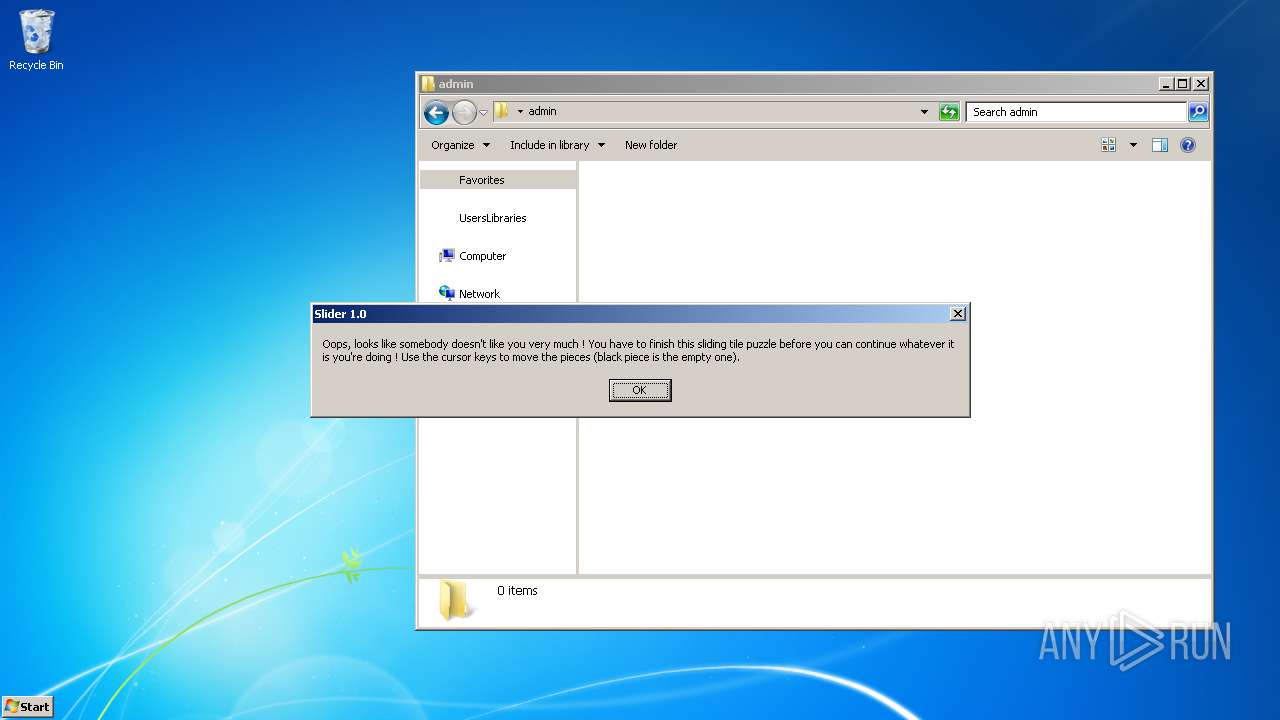
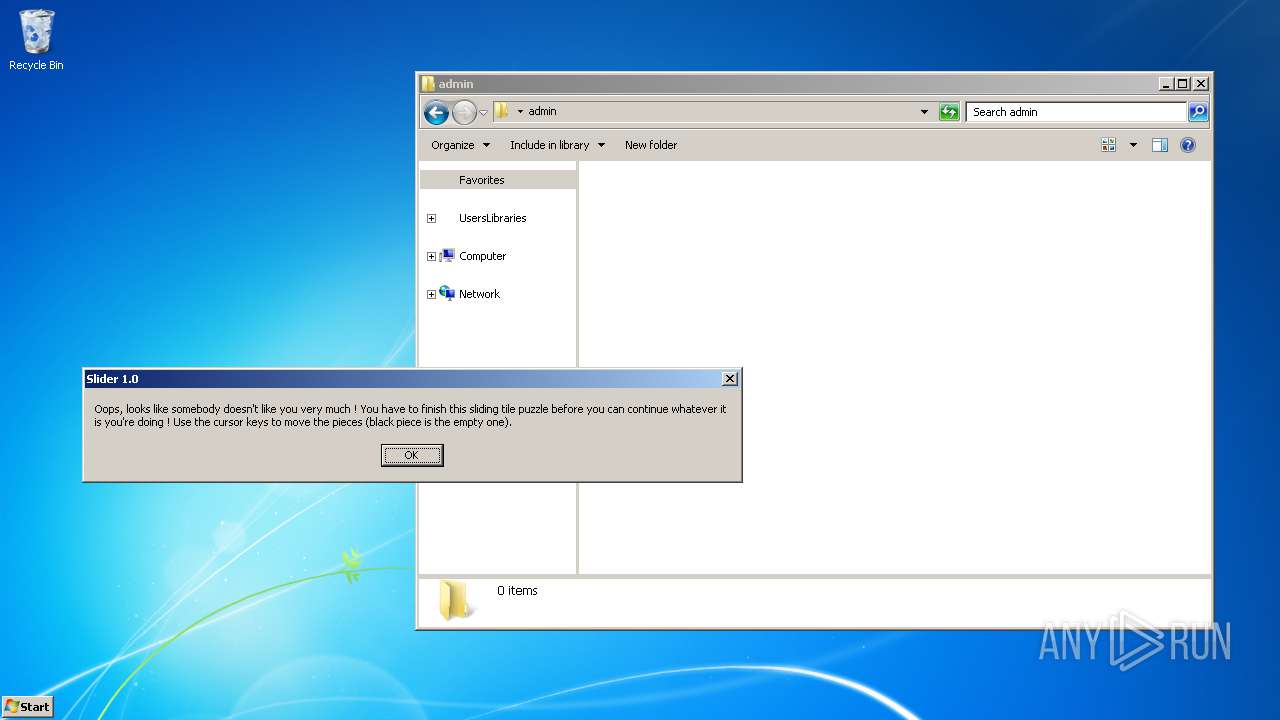
- Endermanch@DesktopPuzzle.exe (PID: 2944)
- Endermanch@FreeYoutubeDownloader.exe (PID: 3080)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
- Endermanch@HMBlocker.exe (PID: 2376)
- Endermanch@Illerka.C.exe (PID: 1384)
- Endermanch@000.exe (PID: 2332)
Actions looks like stealing of personal data
- Chris@Spark.exe (PID: 3692)
Changes the autorun value in the registry
- Endermanch@ColorBug.exe (PID: 2560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
Changes the login/logoff helper path in the registry
- Endermanch@000.exe (PID: 2332)
Task Manager has been disabled (taskmgr)
- Endermanch@000.exe (PID: 2332)
SUSPICIOUS
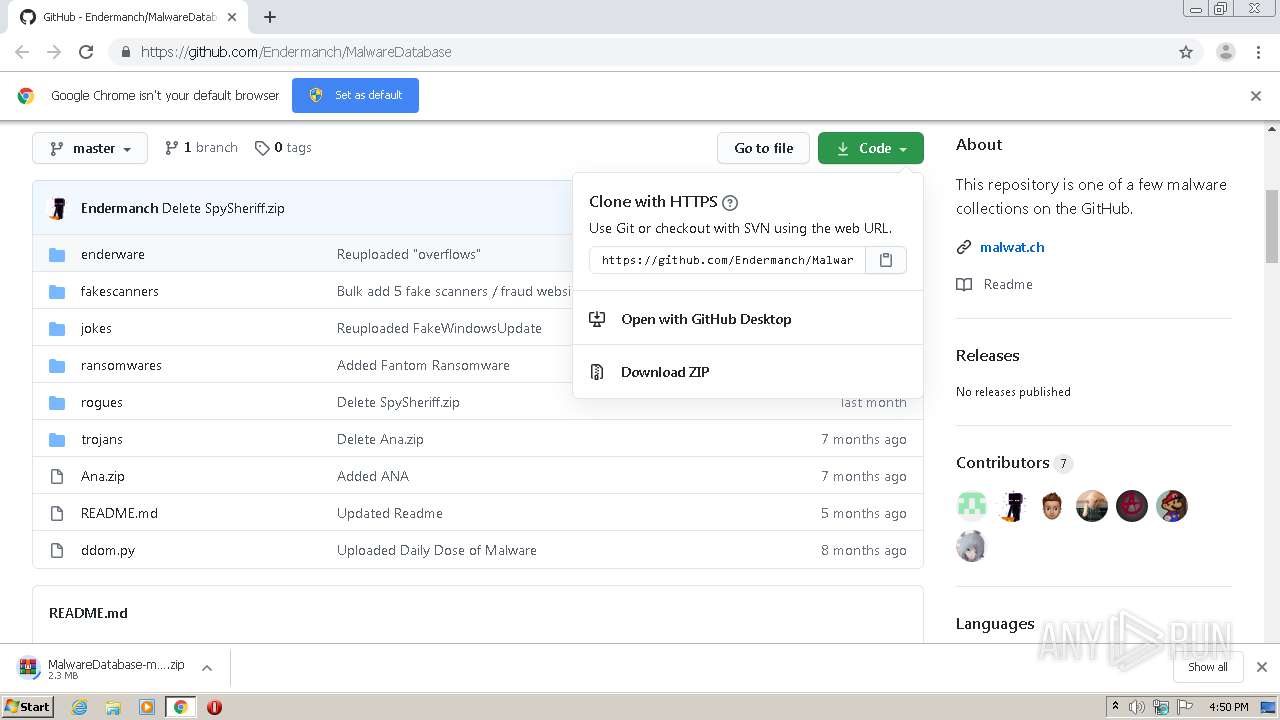
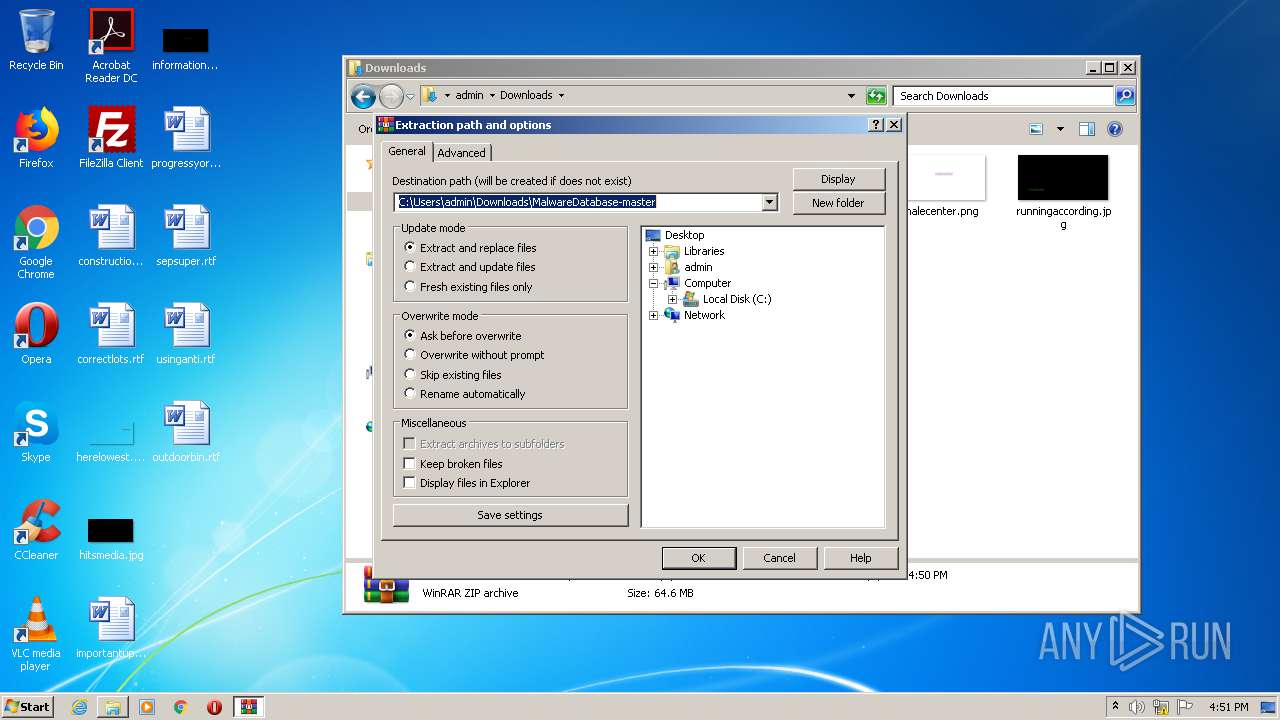
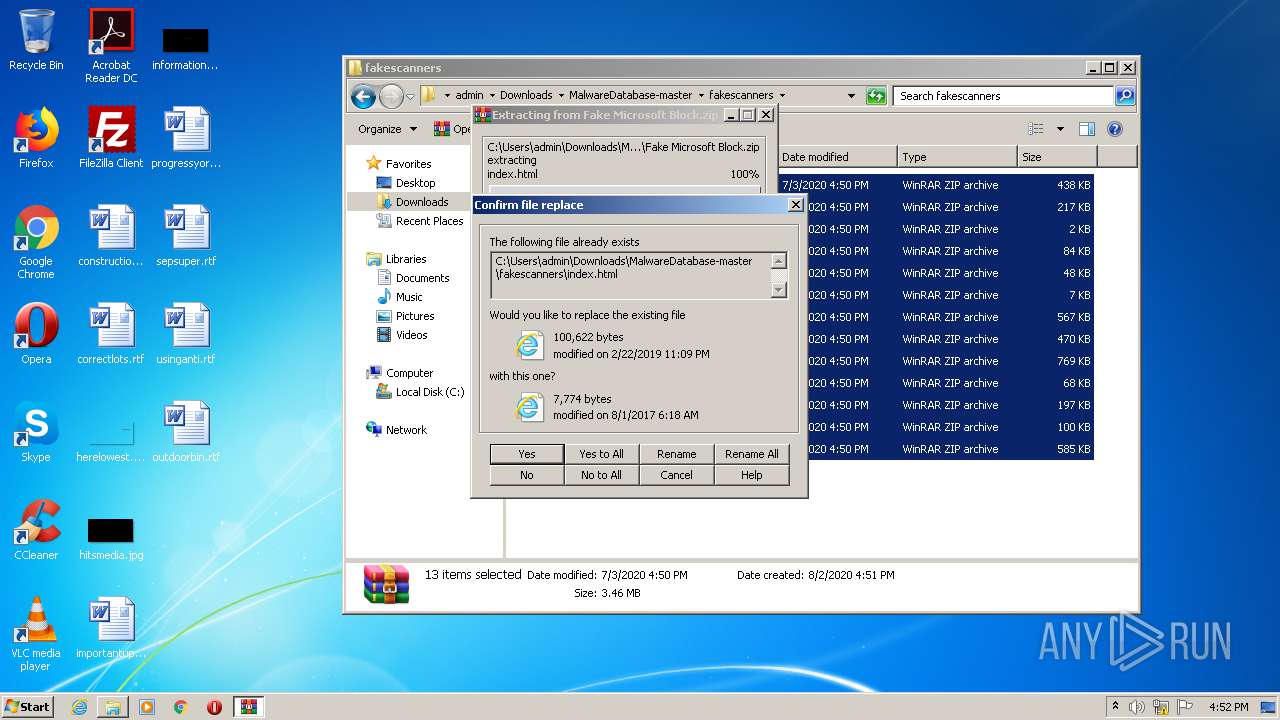
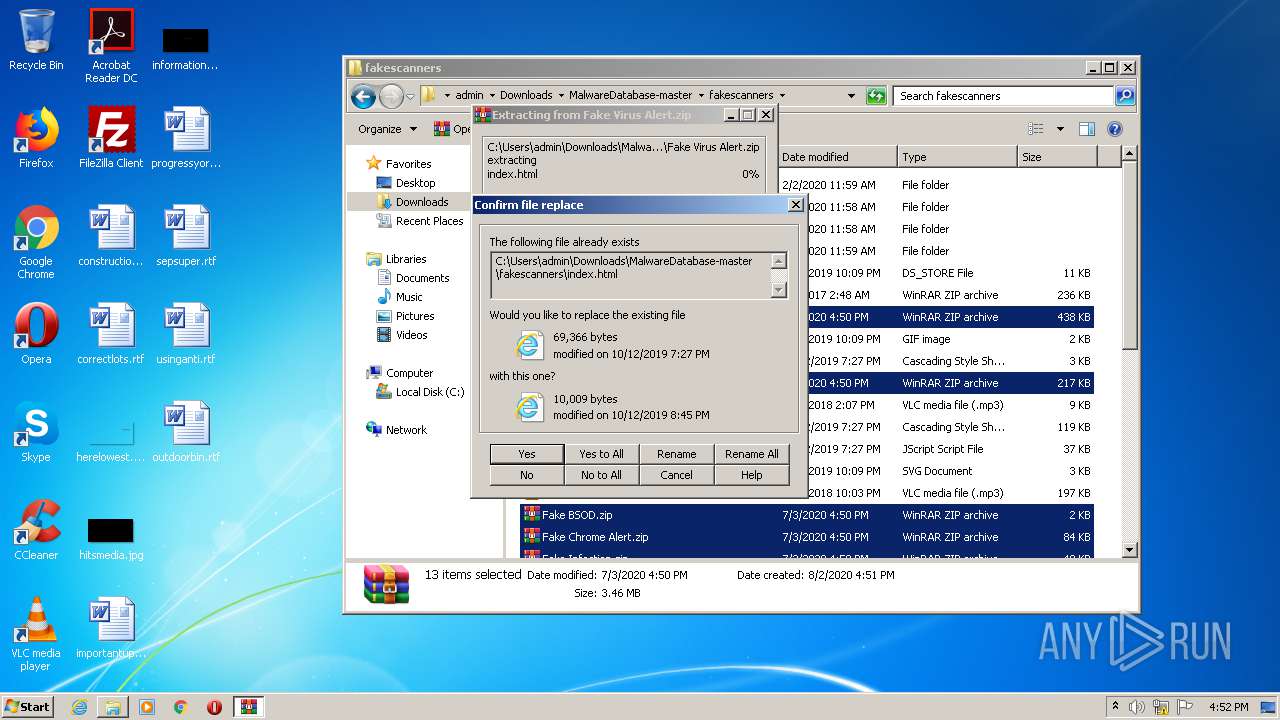
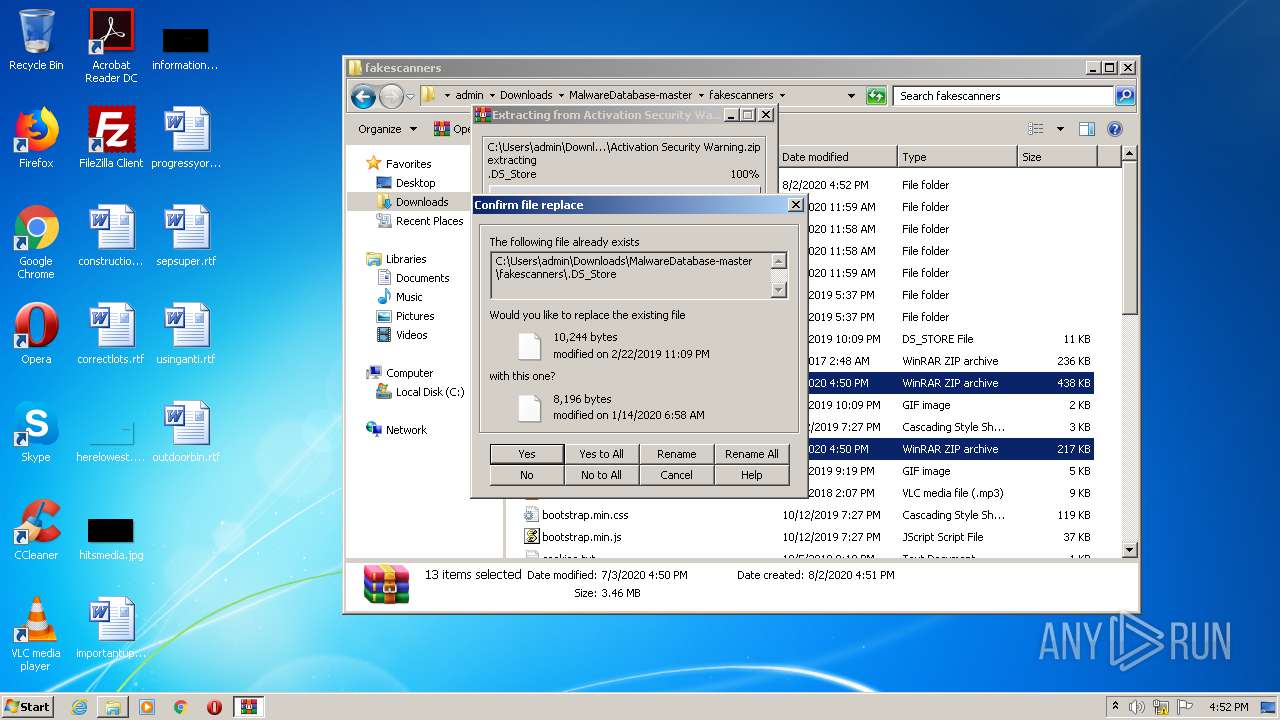
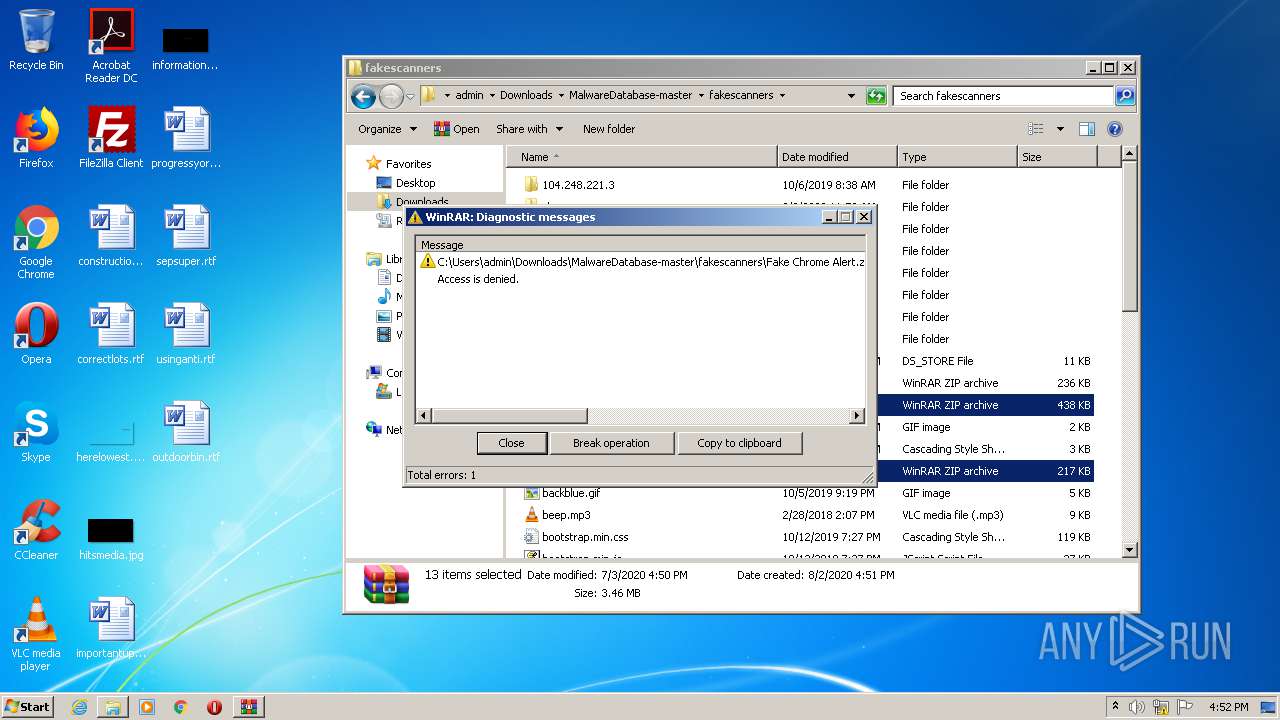
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1664)
- Endermanch@000.exe (PID: 2332)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
Changes the desktop background image
- Endermanch@000.exe (PID: 2332)
Creates files in the Windows directory
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
Creates a software uninstall entry
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
Starts CMD.EXE for commands execution
- Endermanch@000.exe (PID: 2332)
INFO
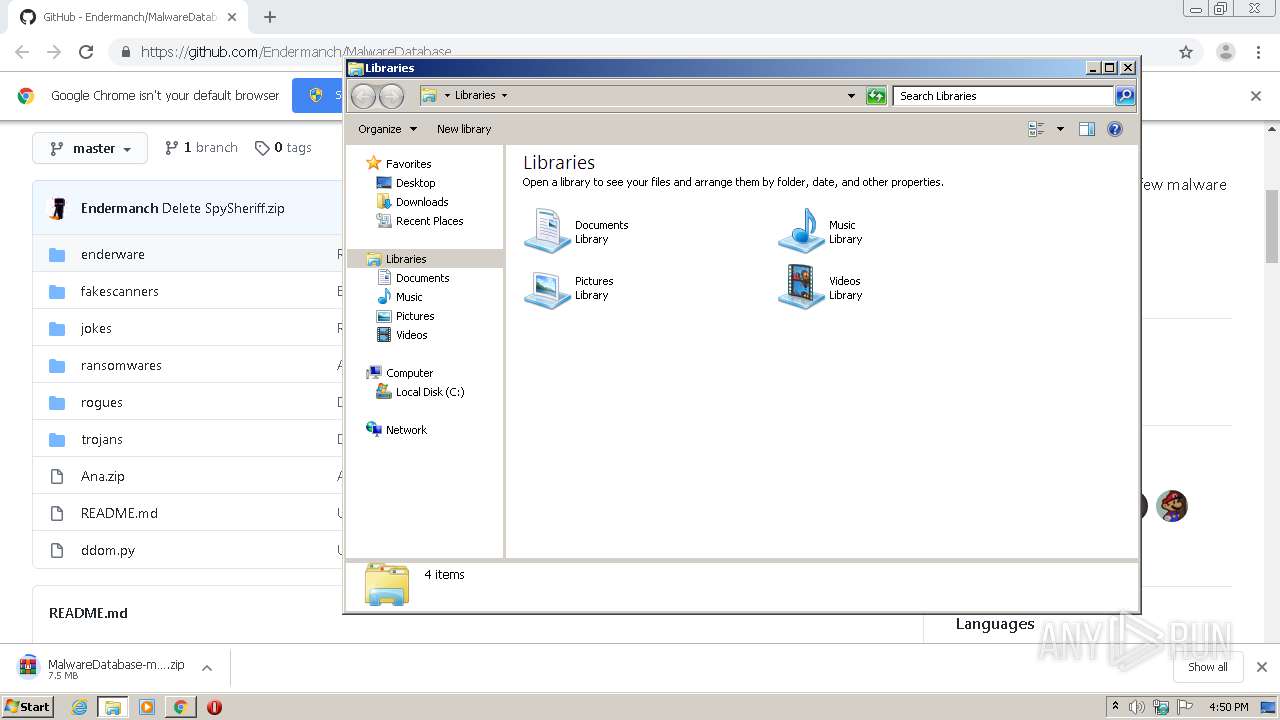
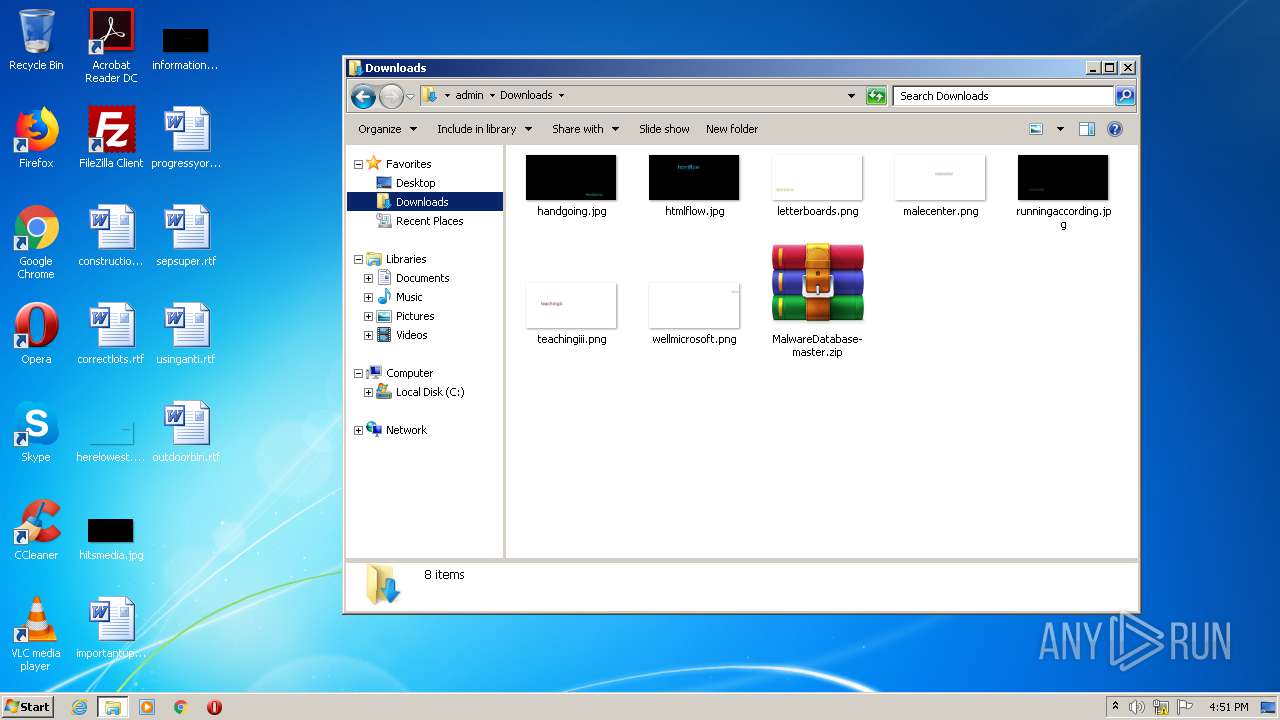
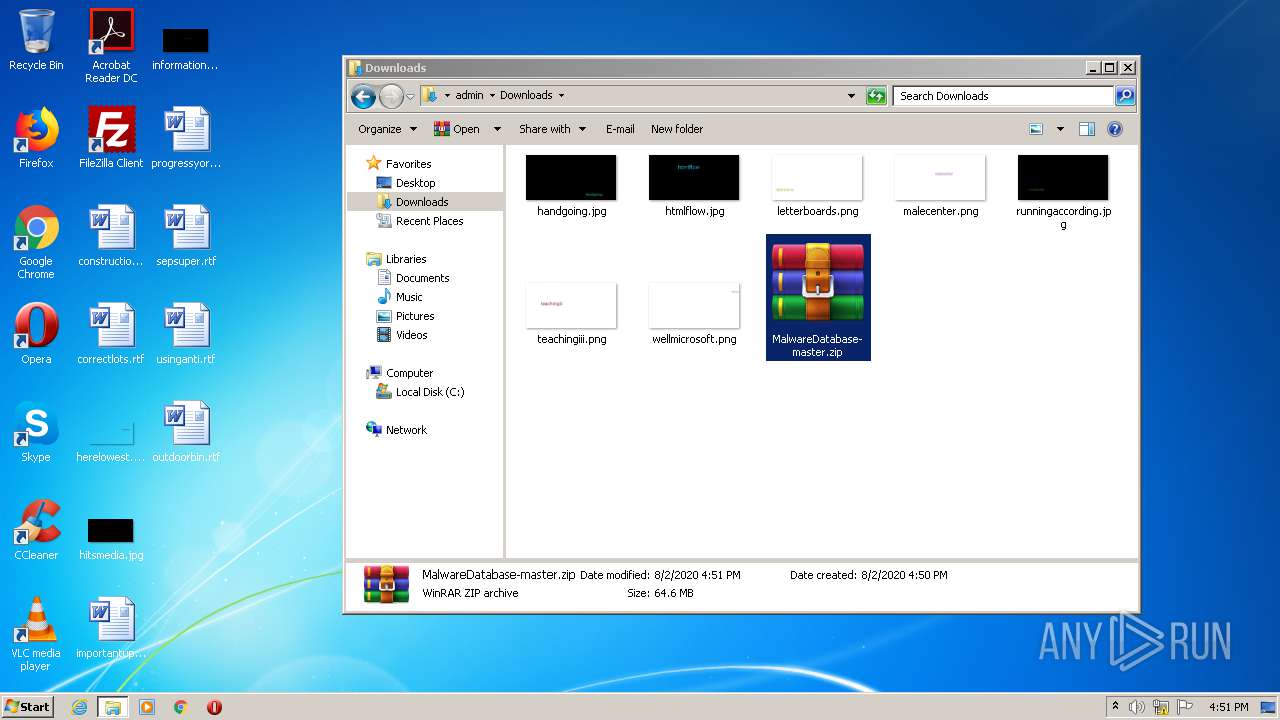
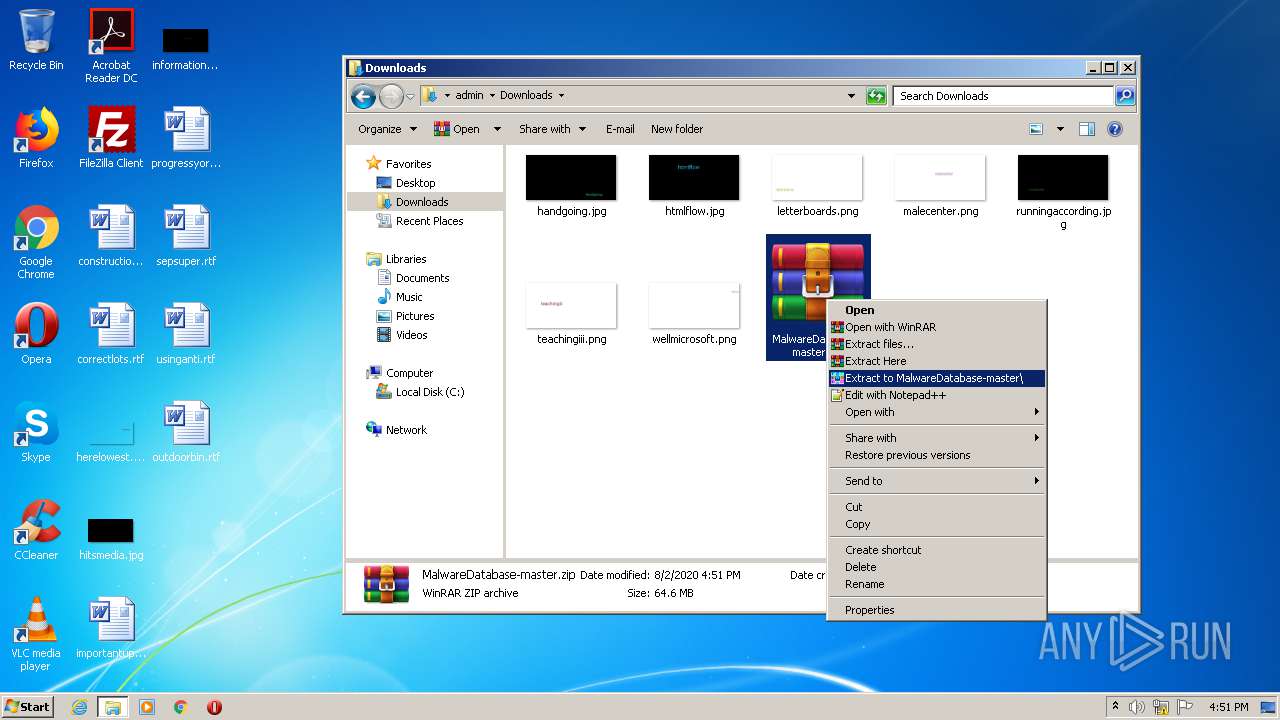
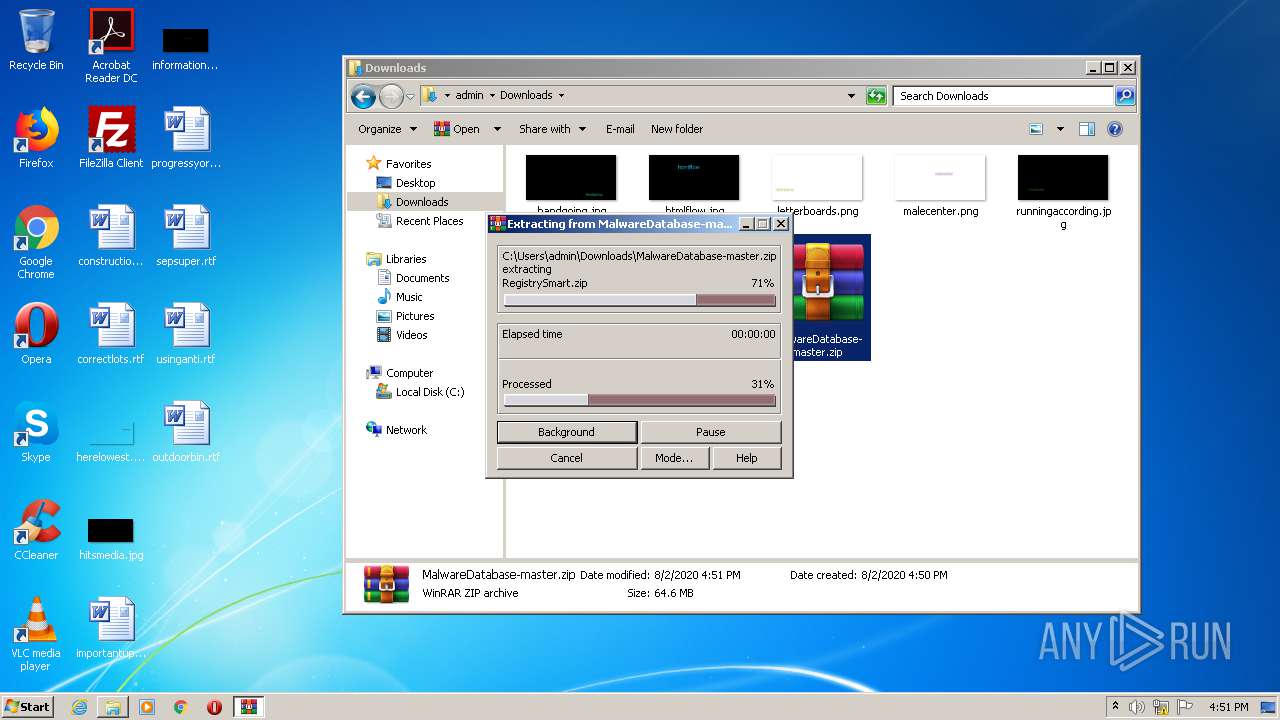
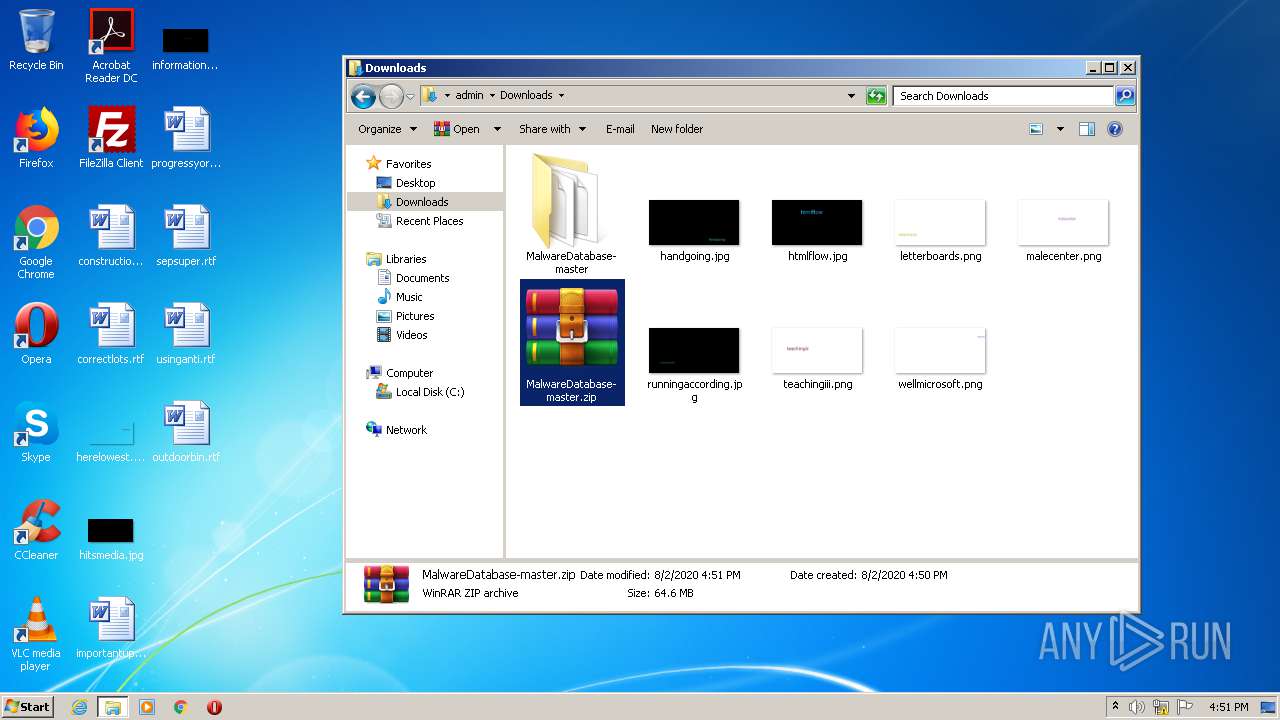
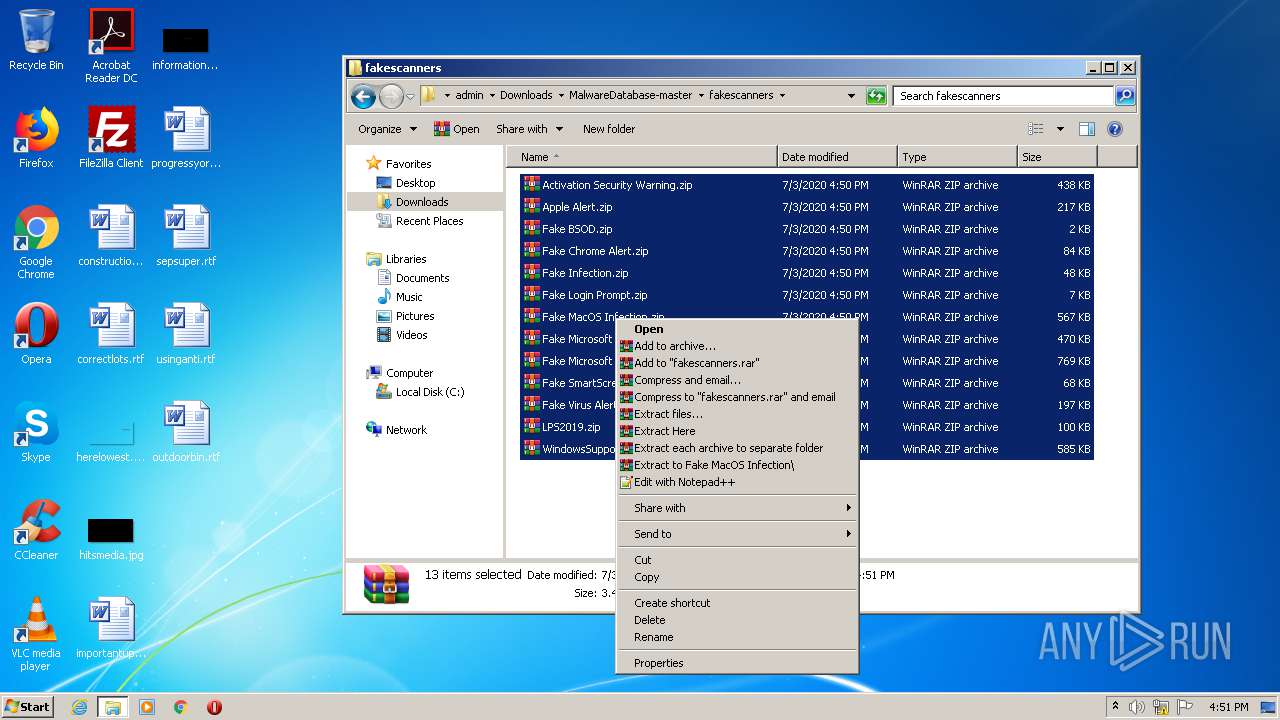
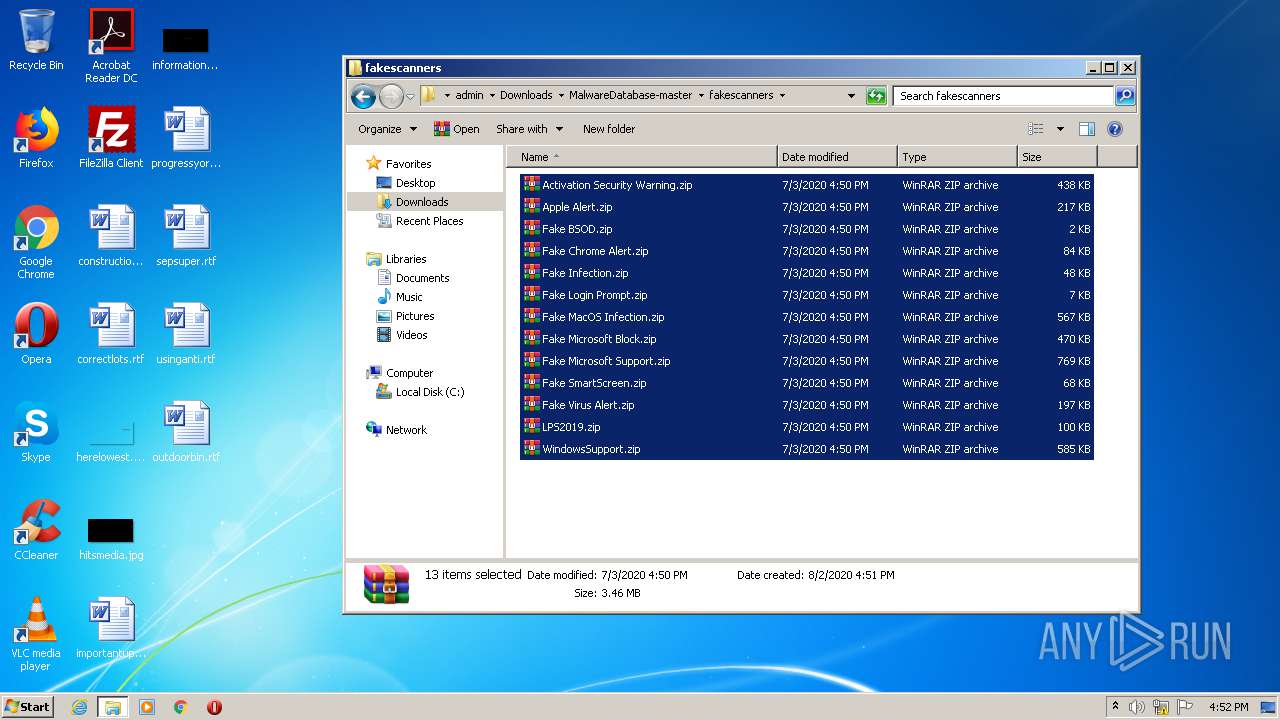
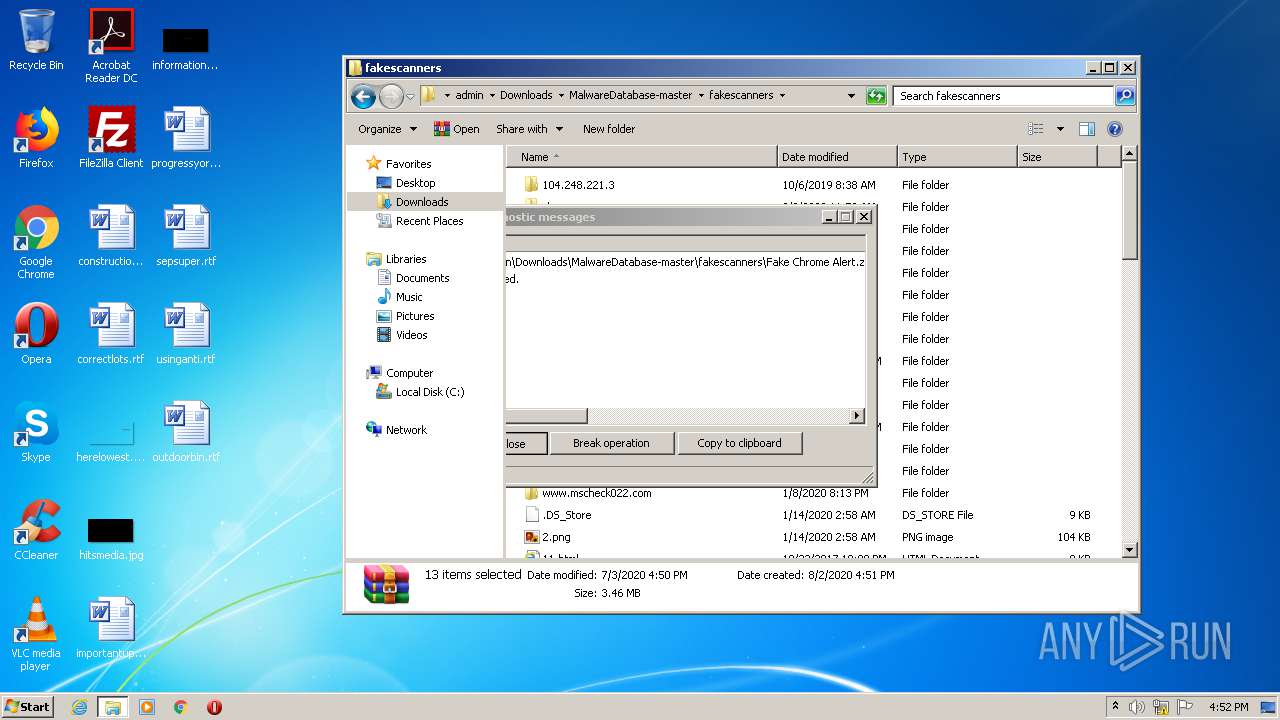
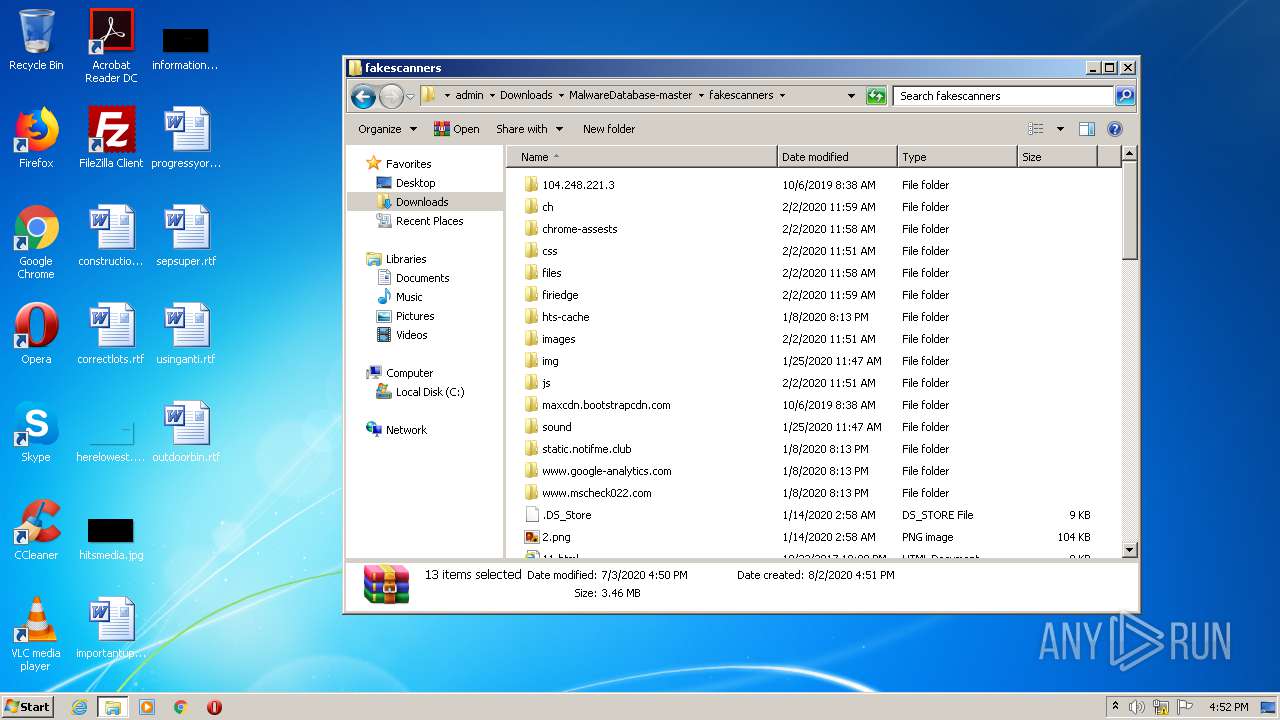
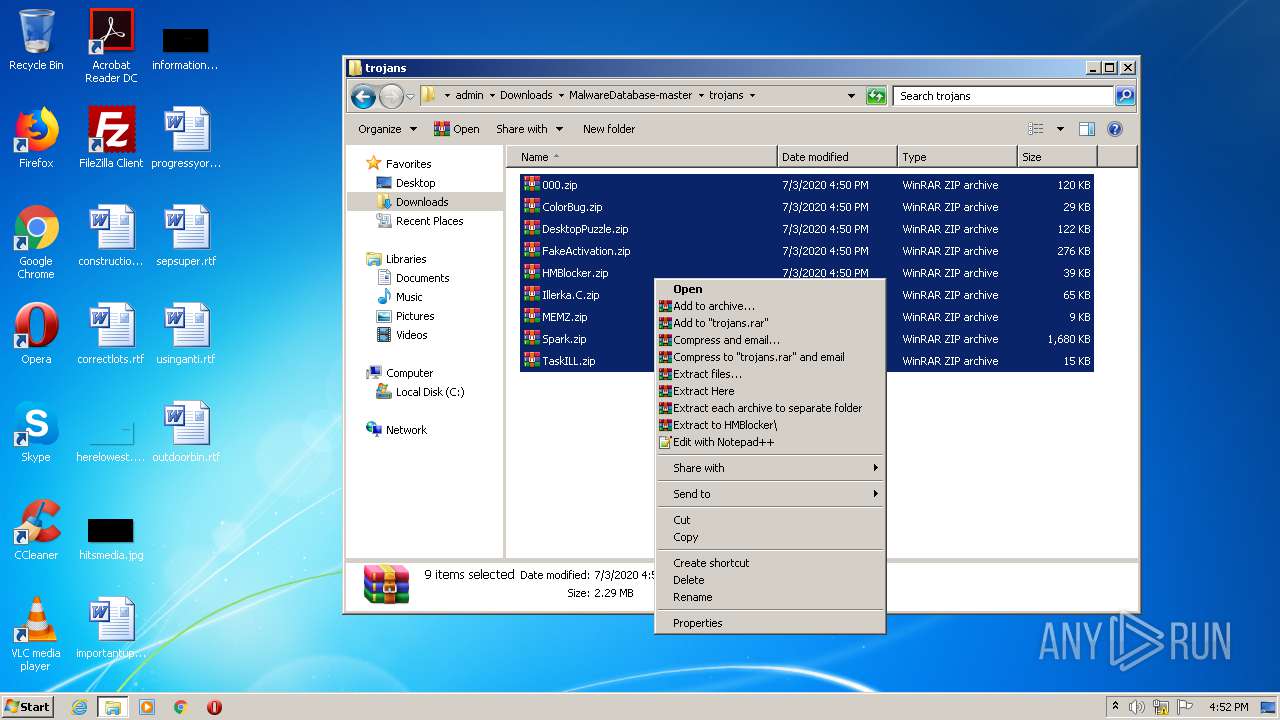
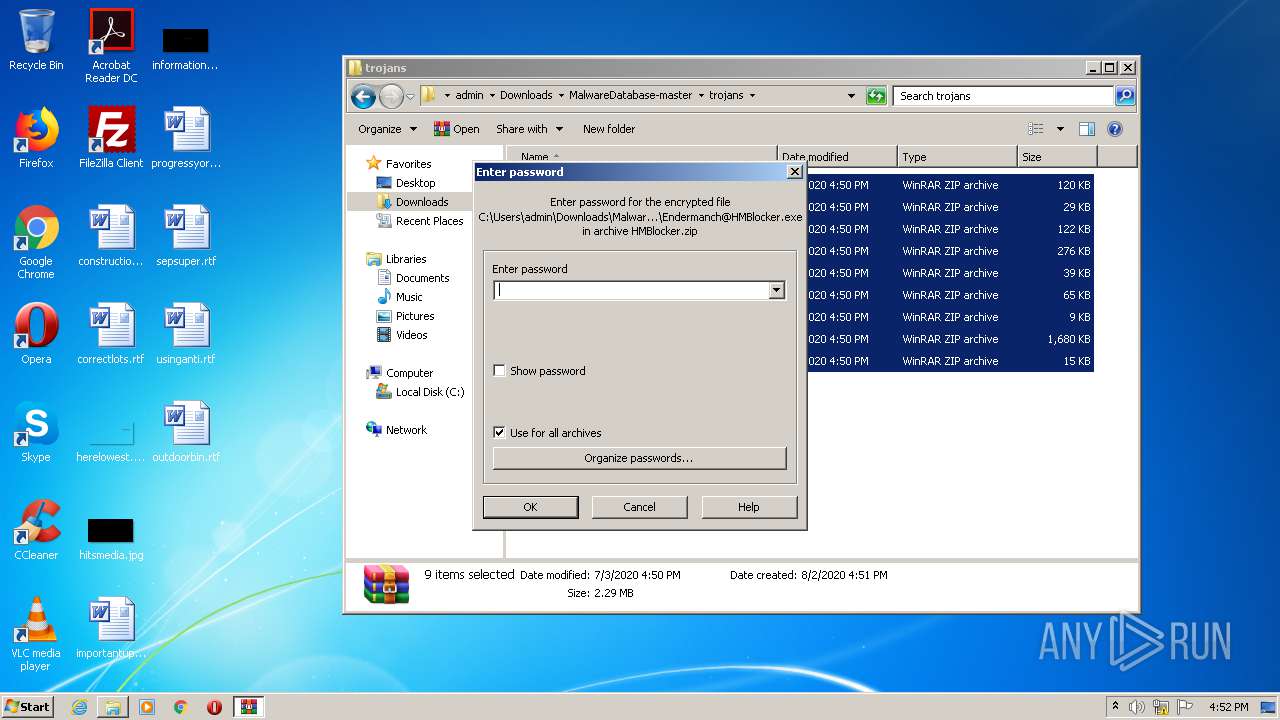
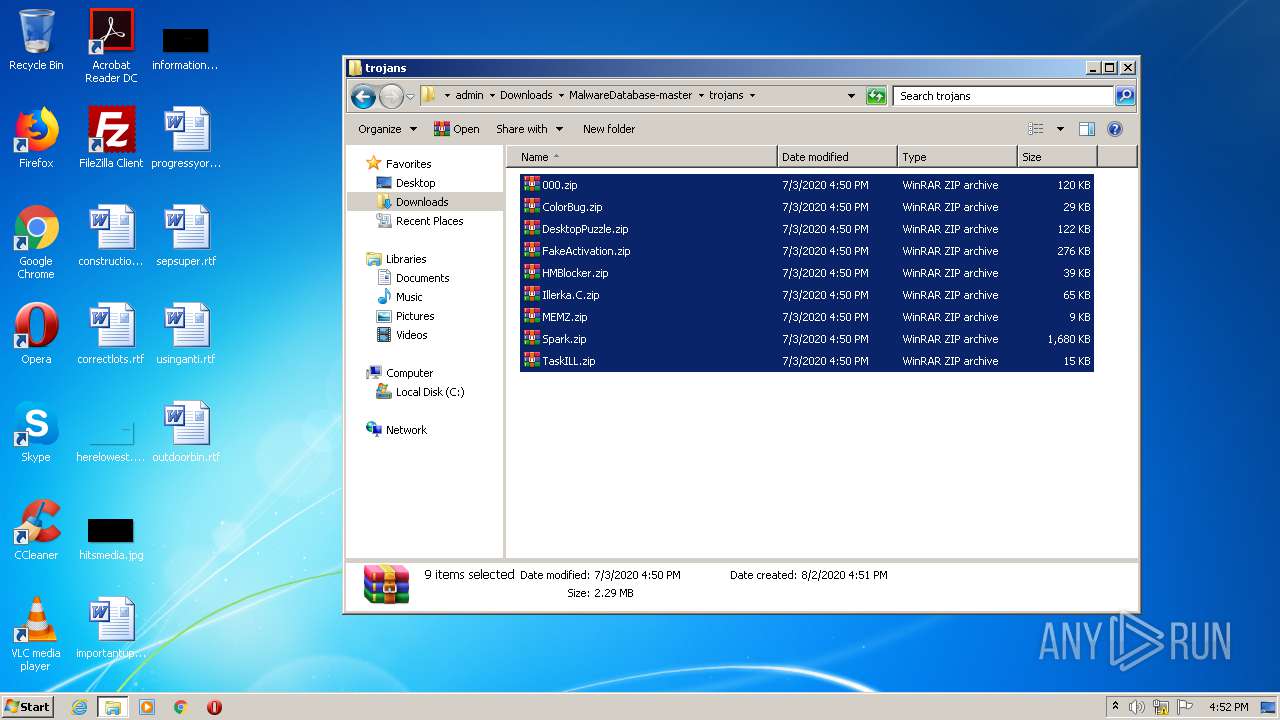
Manual execution by user
- WinRAR.exe (PID: 2096)
- WinRAR.exe (PID: 1664)
- Chris@Spark.exe (PID: 3048)
- Cuberates@TaskILL.exe (PID: 3388)
- Cuberates@TaskILL.exe (PID: 1444)
- explorer.exe (PID: 1548)
- WinRAR.exe (PID: 4028)
- WinRAR.exe (PID: 3976)
- Chris@Spark.exe (PID: 3692)
- Endermanch@000.exe (PID: 2332)
- Endermanch@000.exe (PID: 2112)
- Endermanch@ColorBug.exe (PID: 2560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 3080)
- Endermanch@DesktopPuzzle.exe (PID: 2944)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4024)
- Endermanch@HMBlocker.exe (PID: 2376)
- Endermanch@Illerka.C.exe (PID: 1384)
Reads the hosts file
- chrome.exe (PID: 1244)
- chrome.exe (PID: 1704)
Application launched itself
- chrome.exe (PID: 1244)
Reads settings of System Certificates
- chrome.exe (PID: 1704)
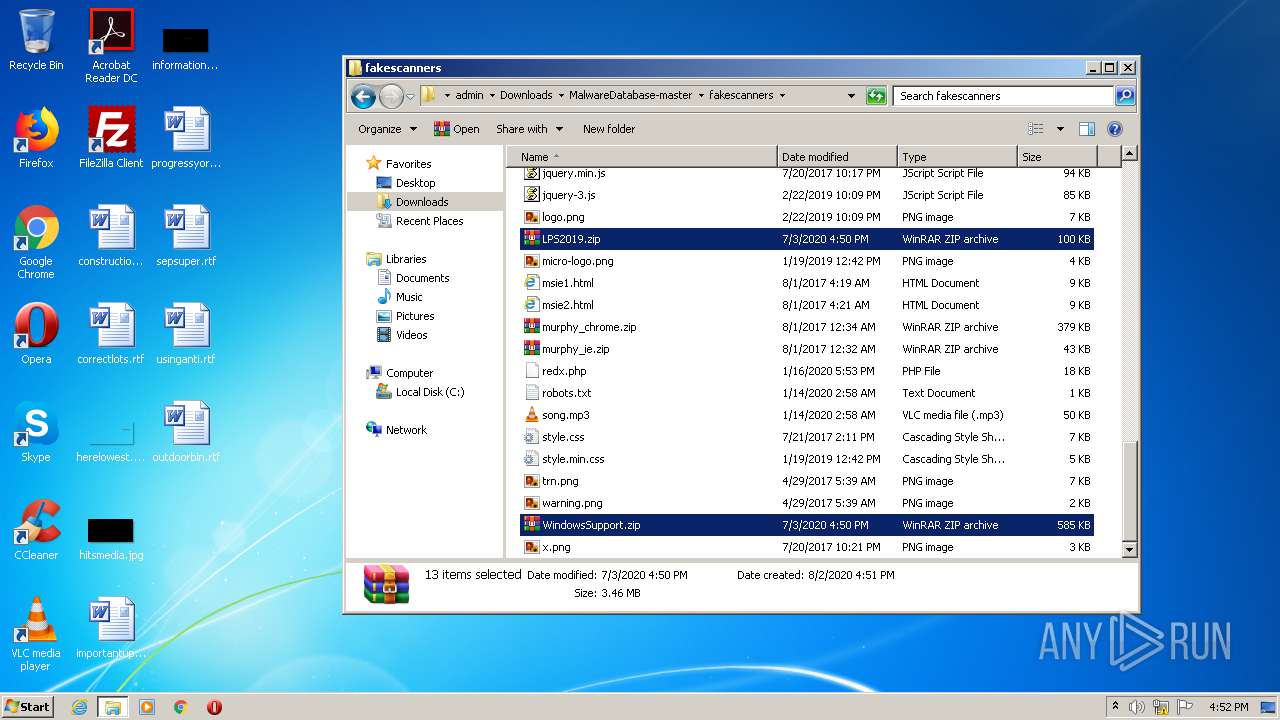
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3976)
Reads Internet Cache Settings
- chrome.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
33
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,16521087061386652699,4277967542510048881,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6765016004387417605 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1132 | cmd /c ""C:\Users\admin\AppData\Local\Temp\windl.bat"" | C:\Windows\system32\cmd.exe | — | Endermanch@000.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/Endermanch/MalwareDatabase" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Users\admin\Downloads\MalwareDatabase-master\trojans\Endermanch@Illerka.C.exe" | C:\Users\admin\Downloads\MalwareDatabase-master\trojans\Endermanch@Illerka.C.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\Downloads\MalwareDatabase-master\trojans\Cuberates@TaskILL.exe" | C:\Users\admin\Downloads\MalwareDatabase-master\trojans\Cuberates@TaskILL.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TaskILL.exe Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,16521087061386652699,4277967542510048881,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13364386476215203422 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver "-anf=C:\Users\admin\AppData\Local\Temp\Rar$LS352.38619" -scul -- "C:\Users\admin\Downloads\MalwareDatabase-master\trojans\FakeActivation.zip" C:\Users\admin\Downloads\MalwareDatabase-master\trojans\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,16521087061386652699,4277967542510048881,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3895004687071269167 --mojo-platform-channel-handle=2864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,16521087061386652699,4277967542510048881,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17729012432615680259 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 426
Read events
2 288
Write events
133
Delete events
5
Modification events
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1244-13240857027355250 |
Value: 259 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
Executable files
14
Suspicious files
143
Text files
268
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b00139a-aad7-4edd-82ad-907cff7a895a.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFd70db.TMP | text | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd707d.TMP | text | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
29
DNS requests
20
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1704 | chrome.exe | 151.101.0.133:443 | avatars2.githubusercontent.com | Fastly | US | malicious |
1704 | chrome.exe | 140.82.118.3:443 | github.com | — | US | malicious |
1704 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 52.206.227.240:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
1704 | chrome.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
avatars3.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Endermanch@000.exe | |
Endermanch@000.exe | Error - |
Endermanch@000.exe | |
Endermanch@000.exe | Error - |
Endermanch@000.exe | |
Endermanch@000.exe | |
Endermanch@000.exe | |
Endermanch@000.exe | StartCrashVertial failed |
Endermanch@000.exe | Error - |