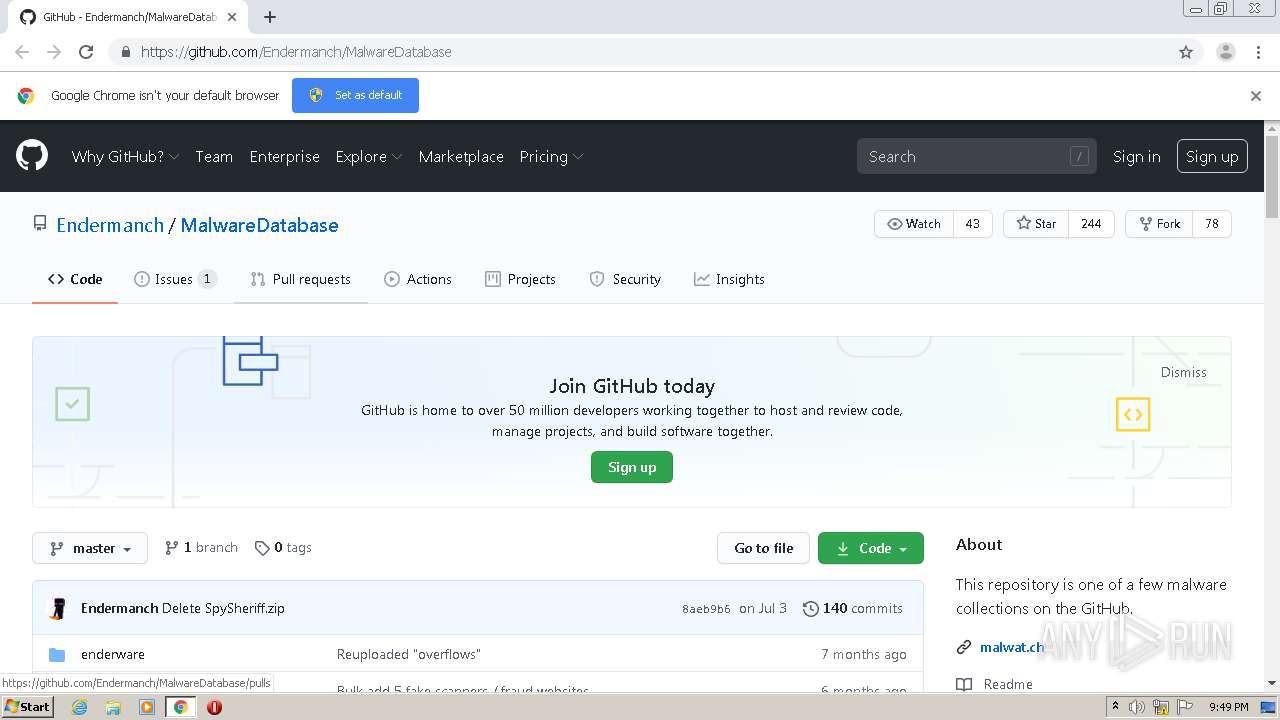
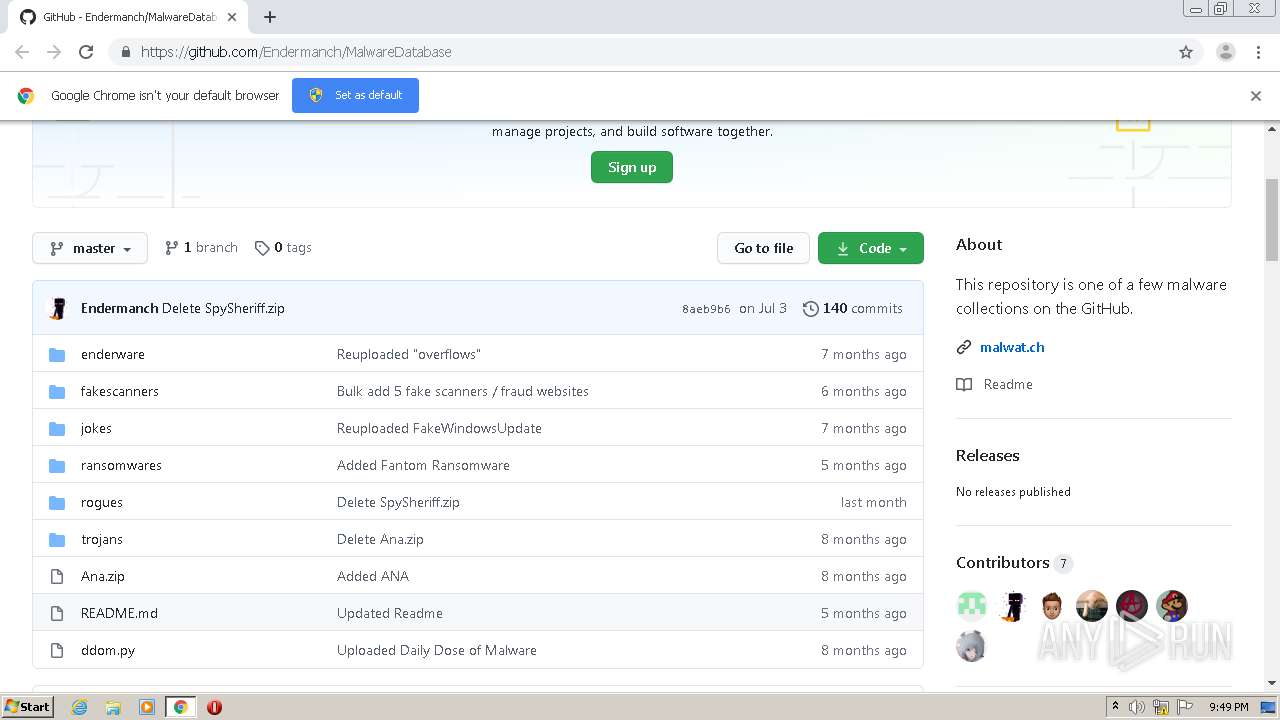
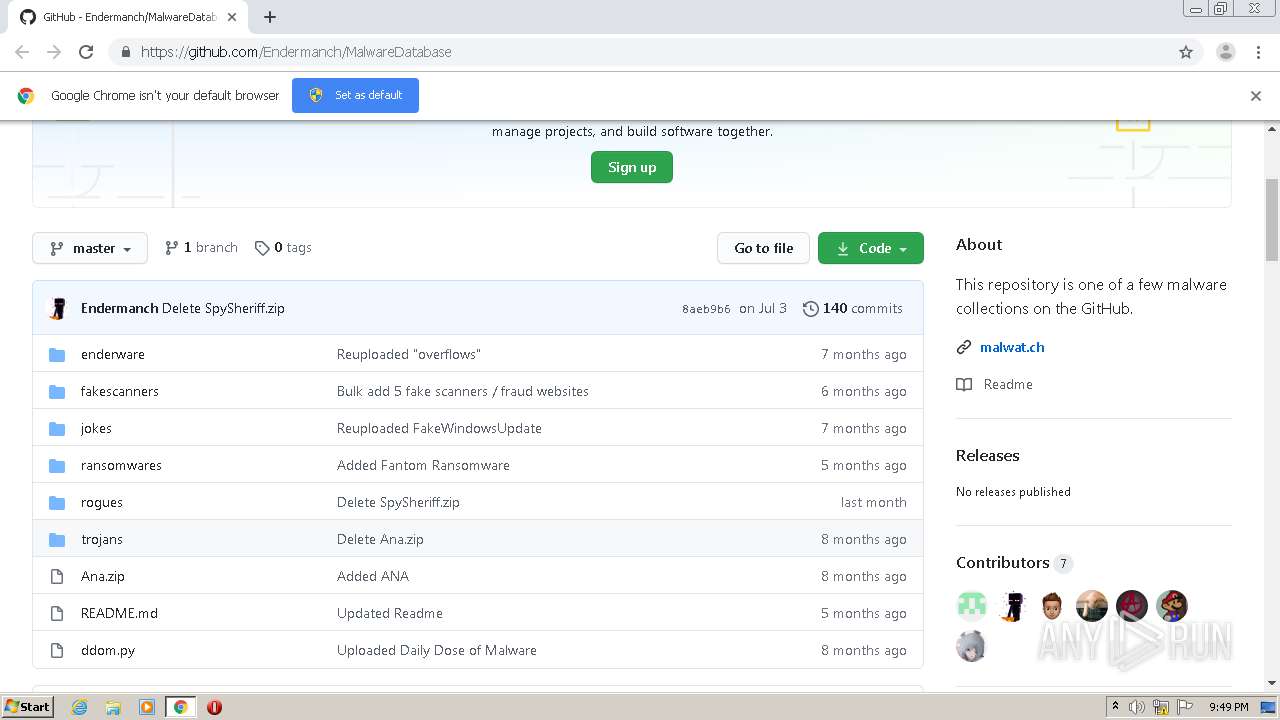
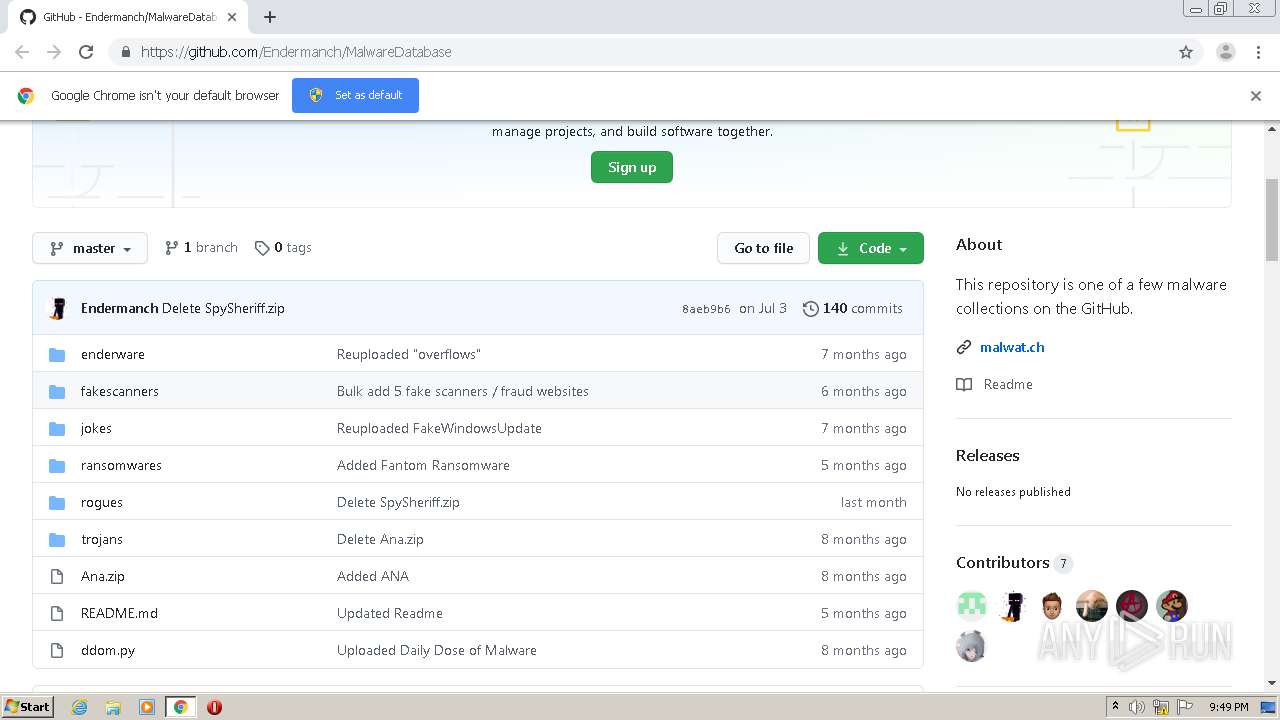
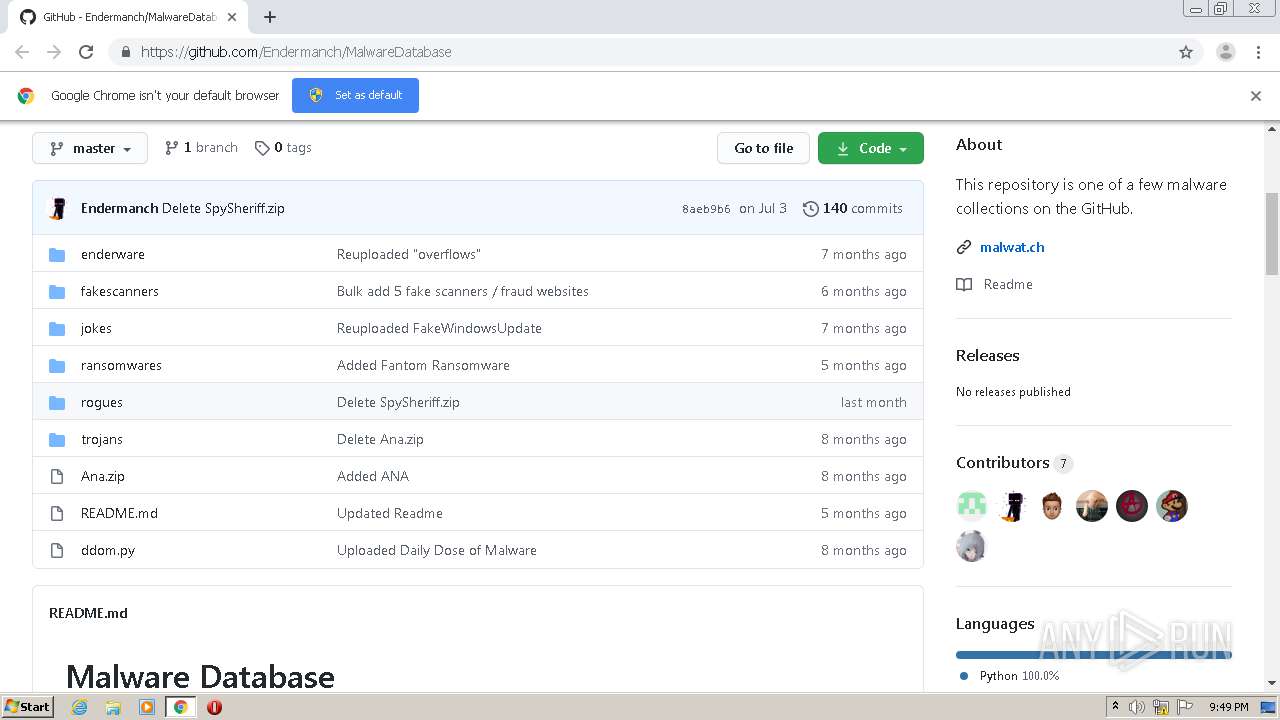
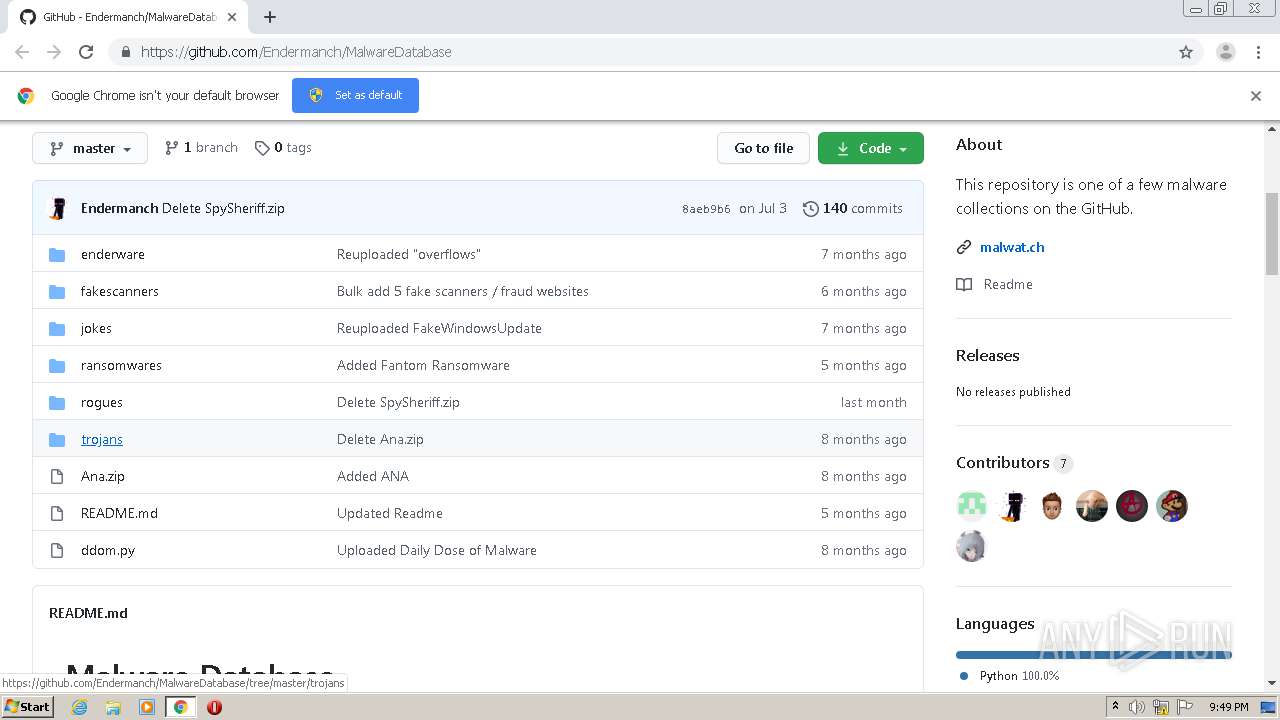
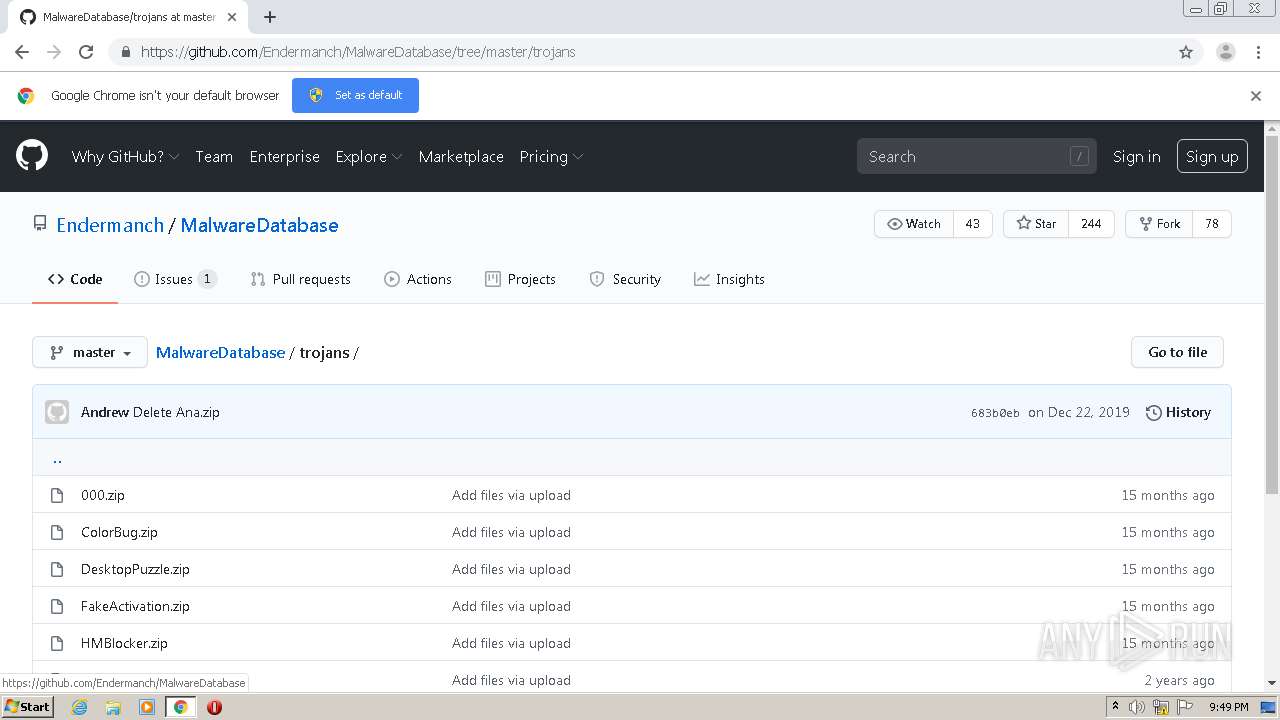
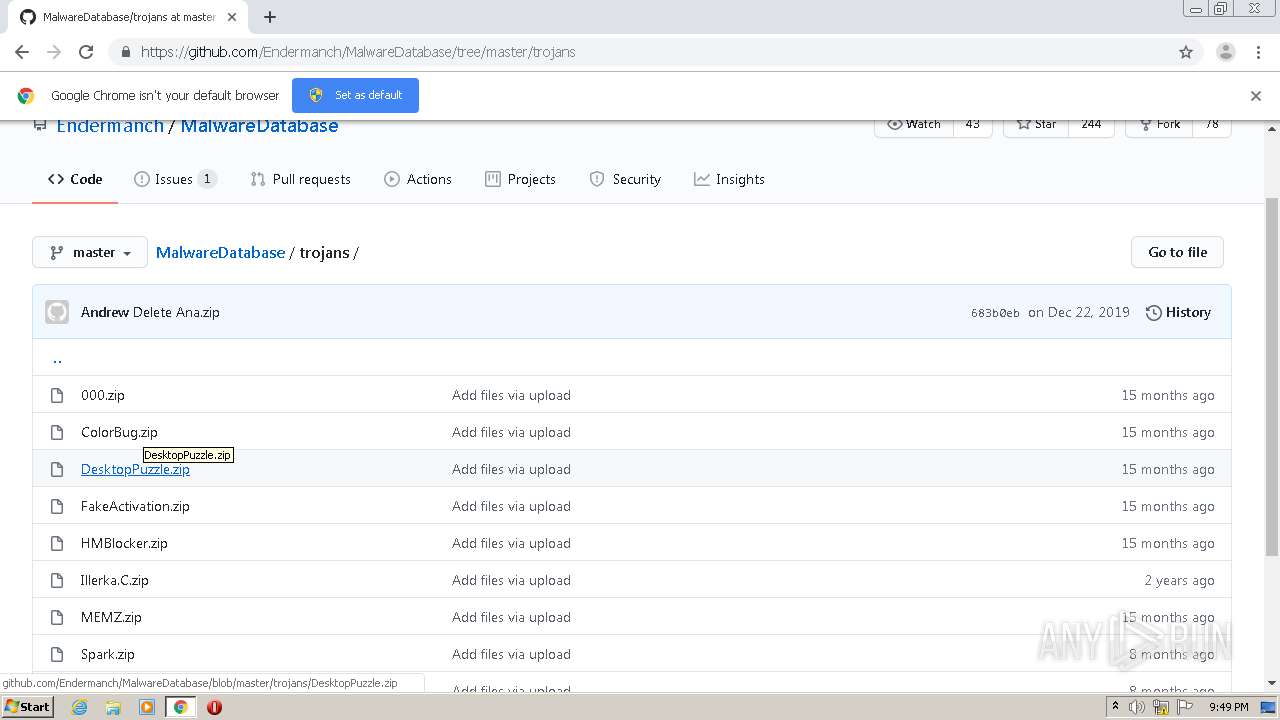
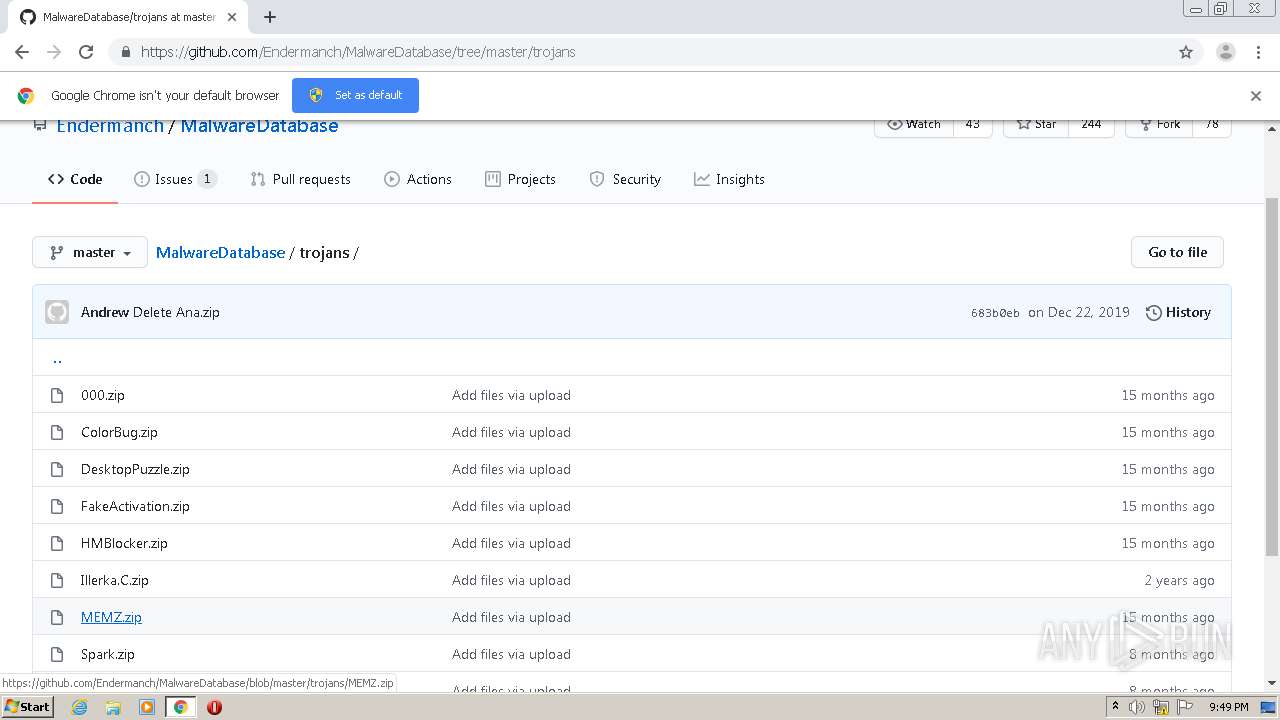
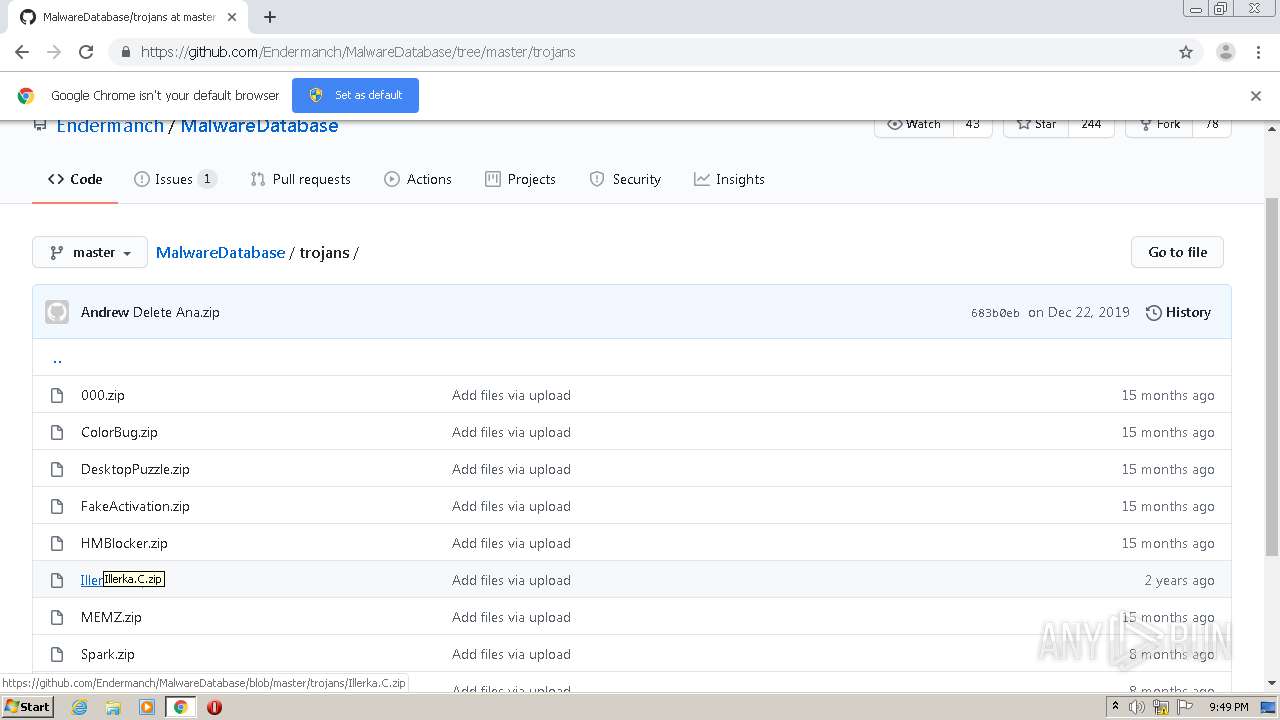
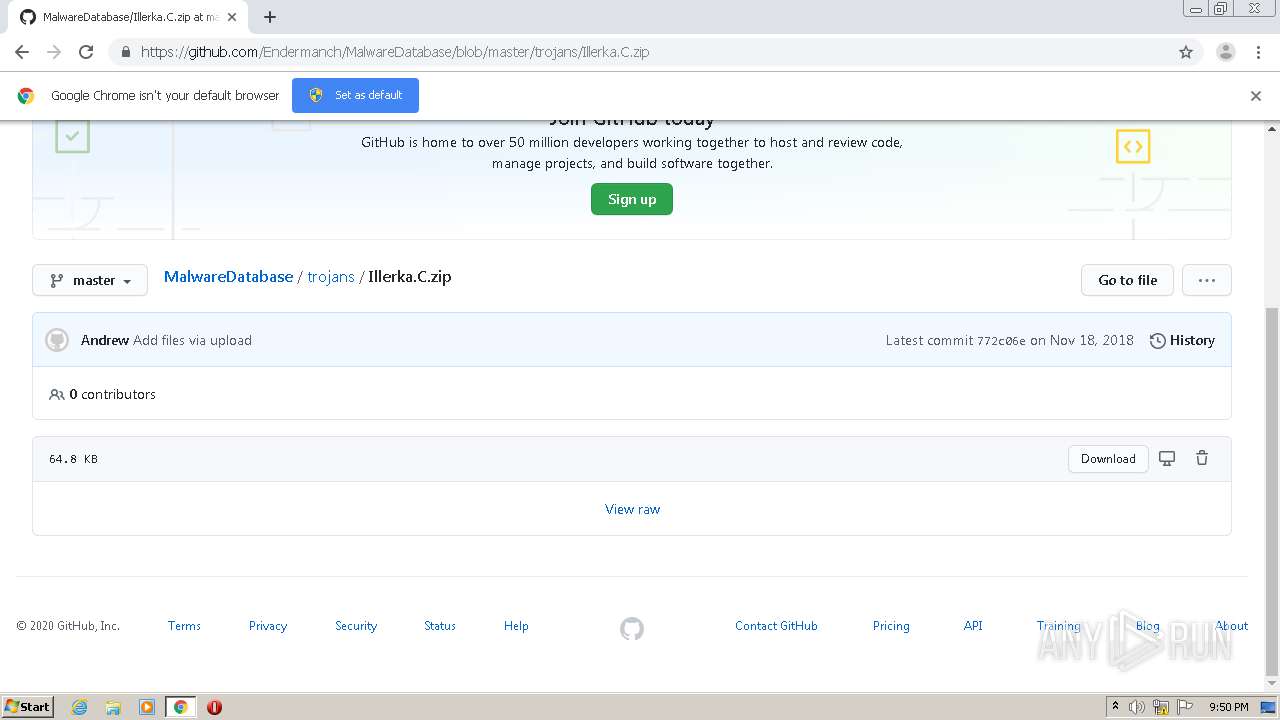
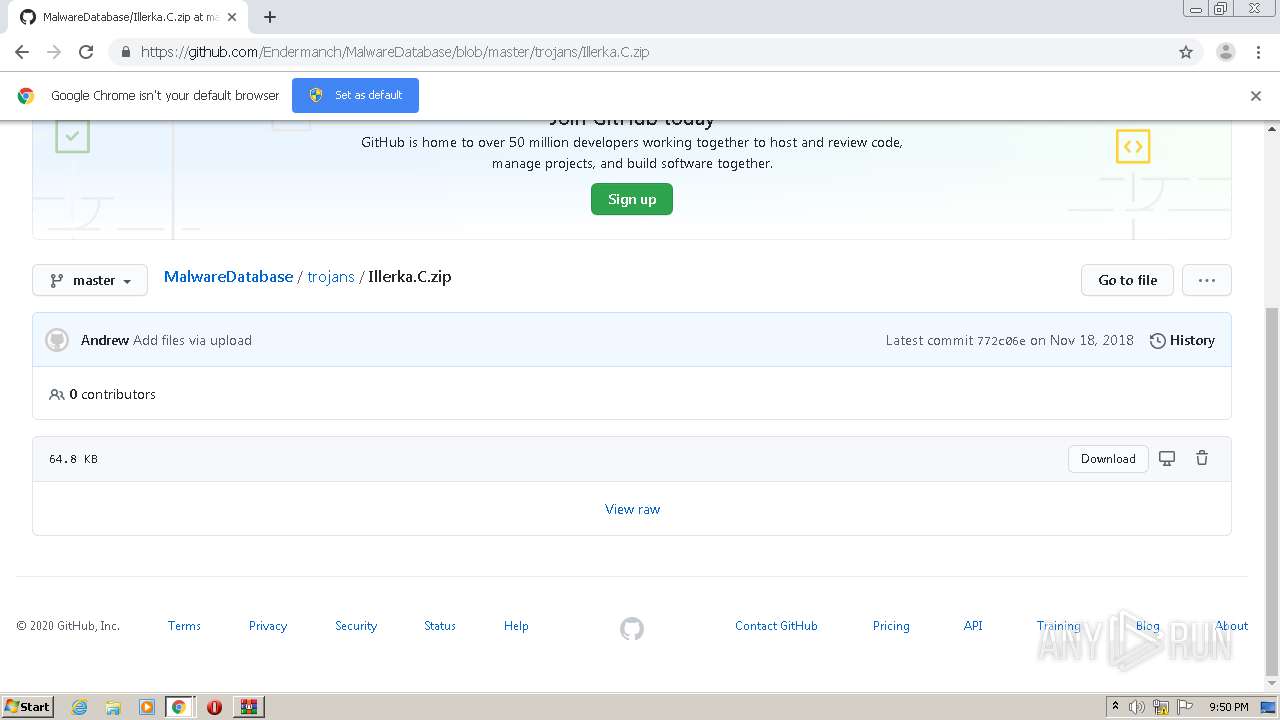
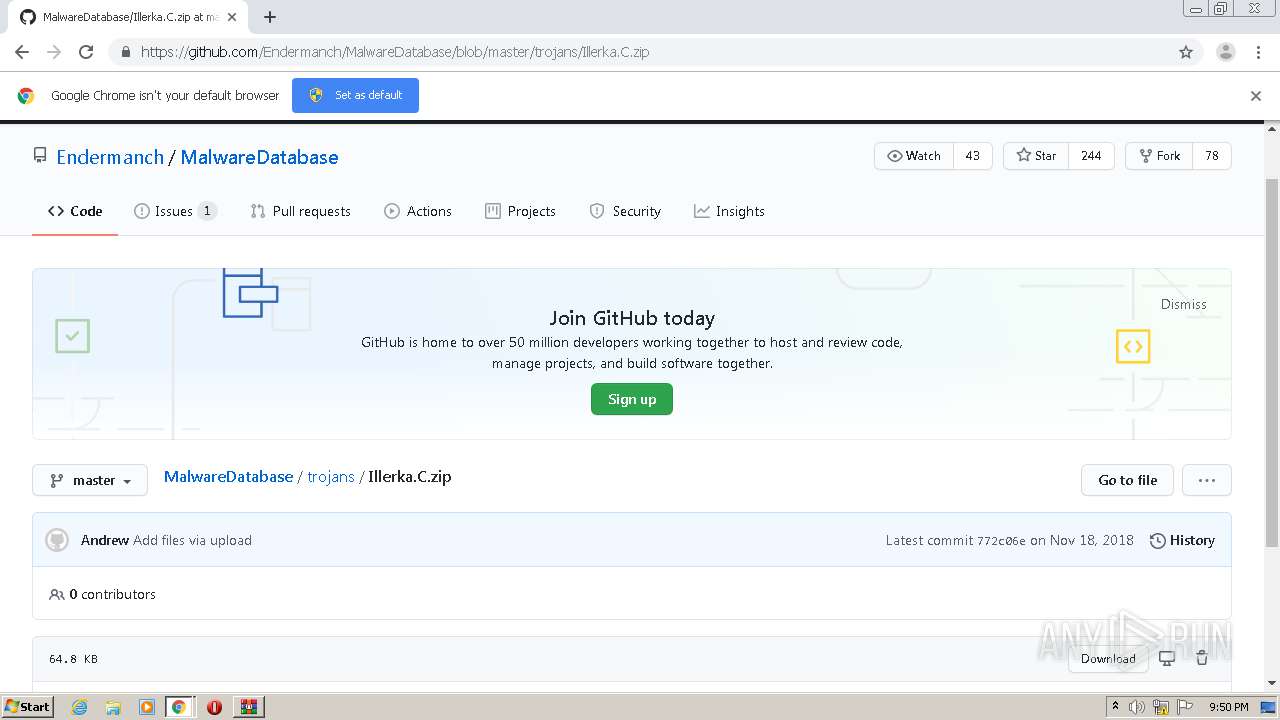
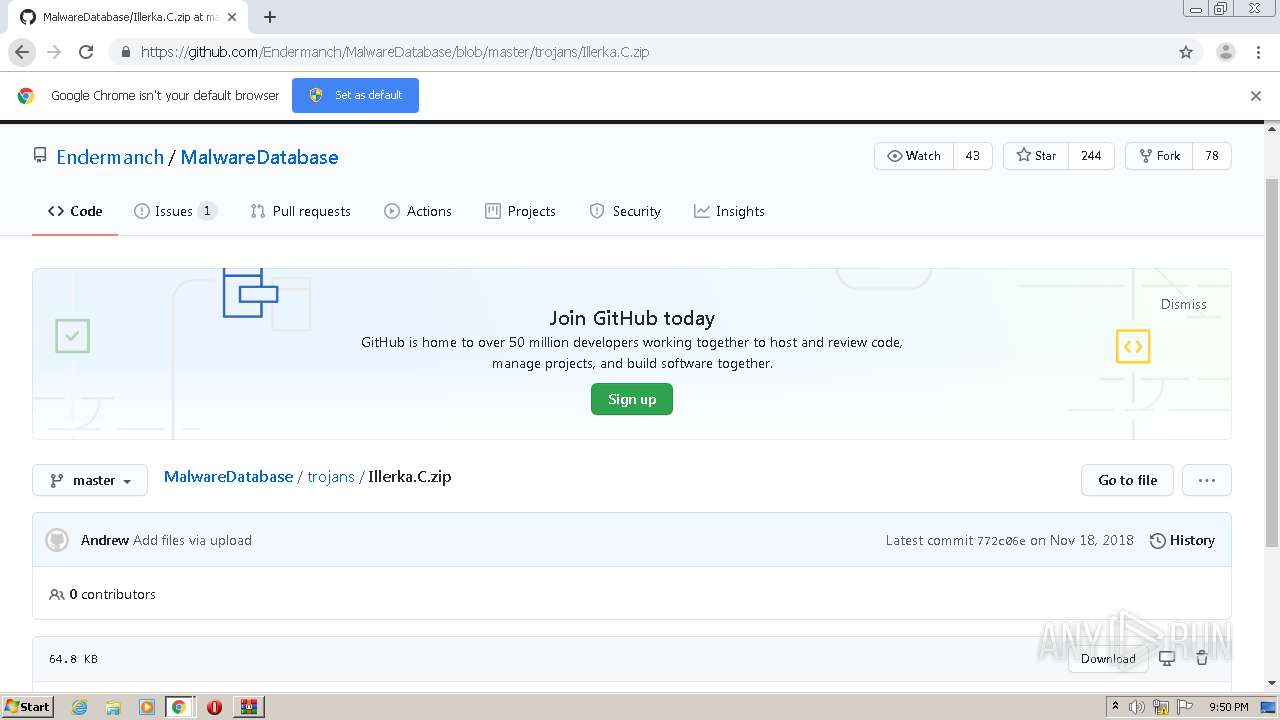
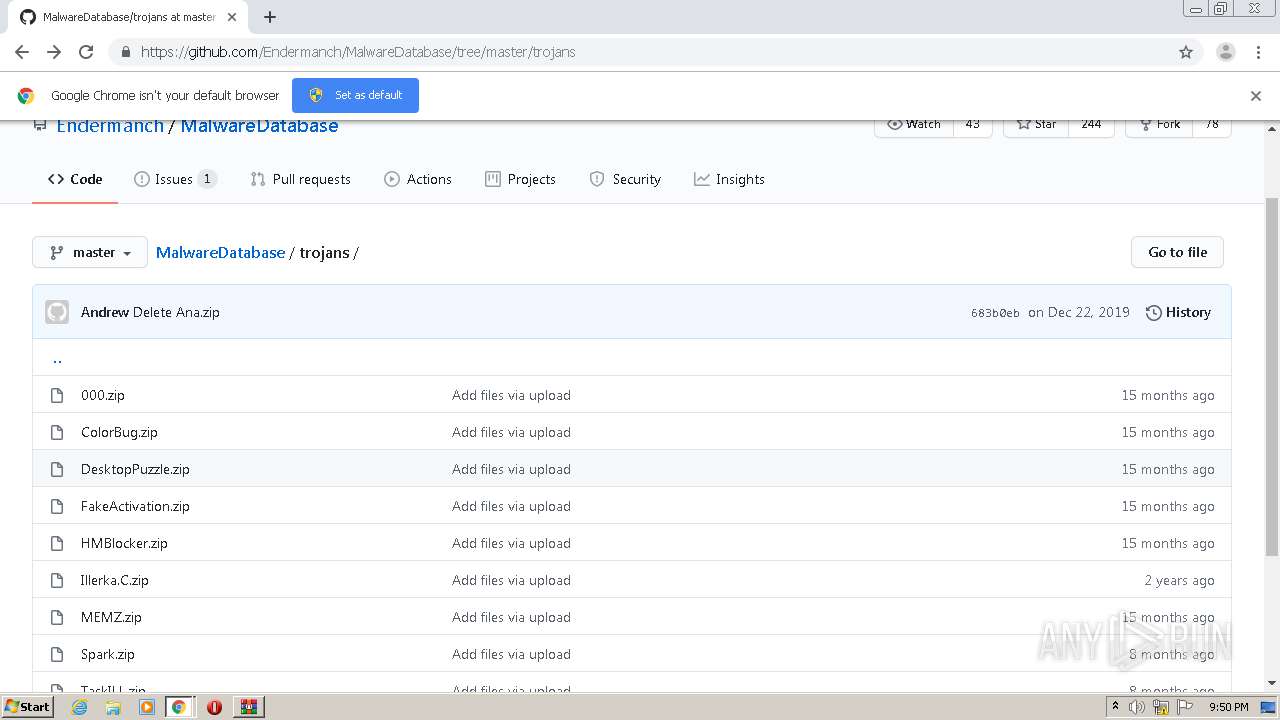
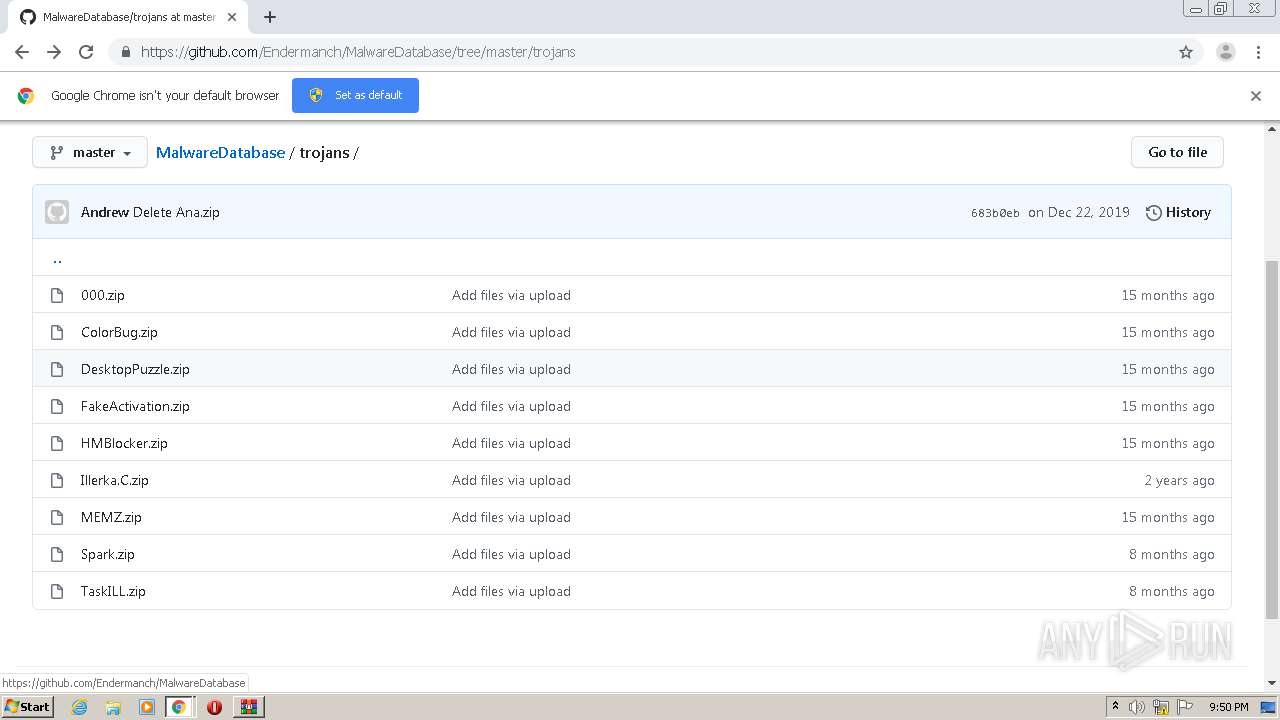
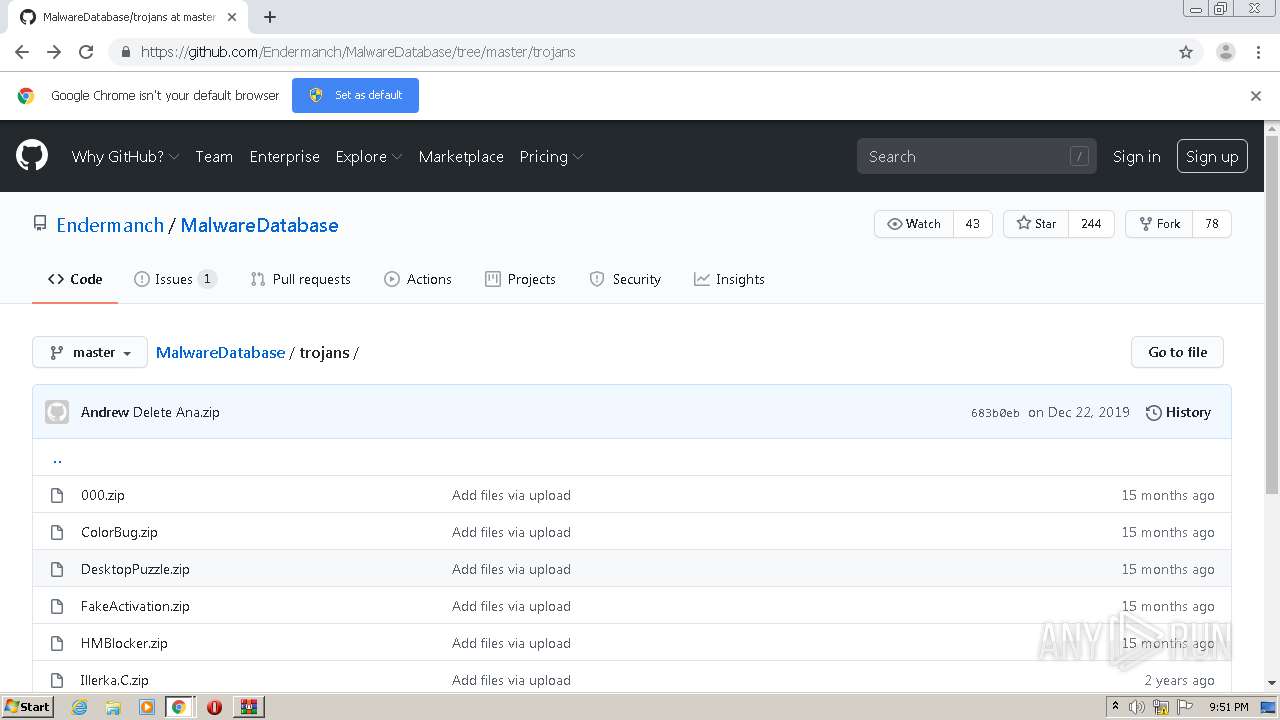
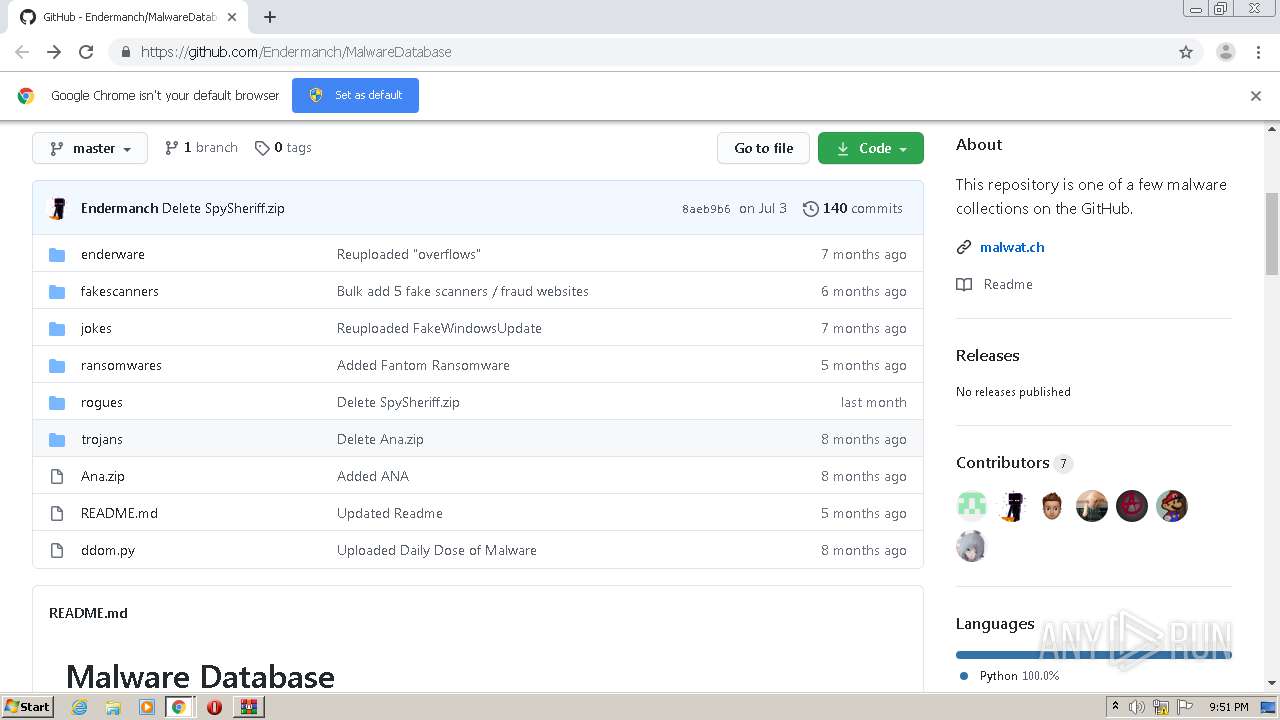
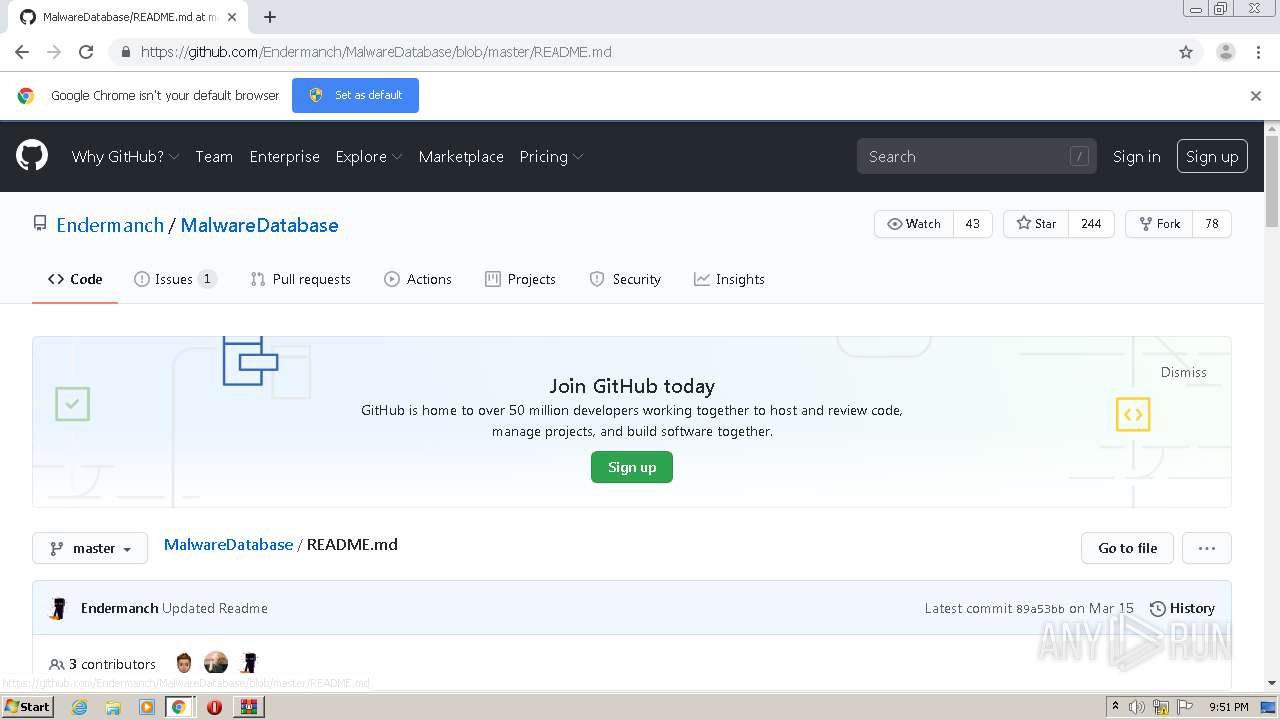
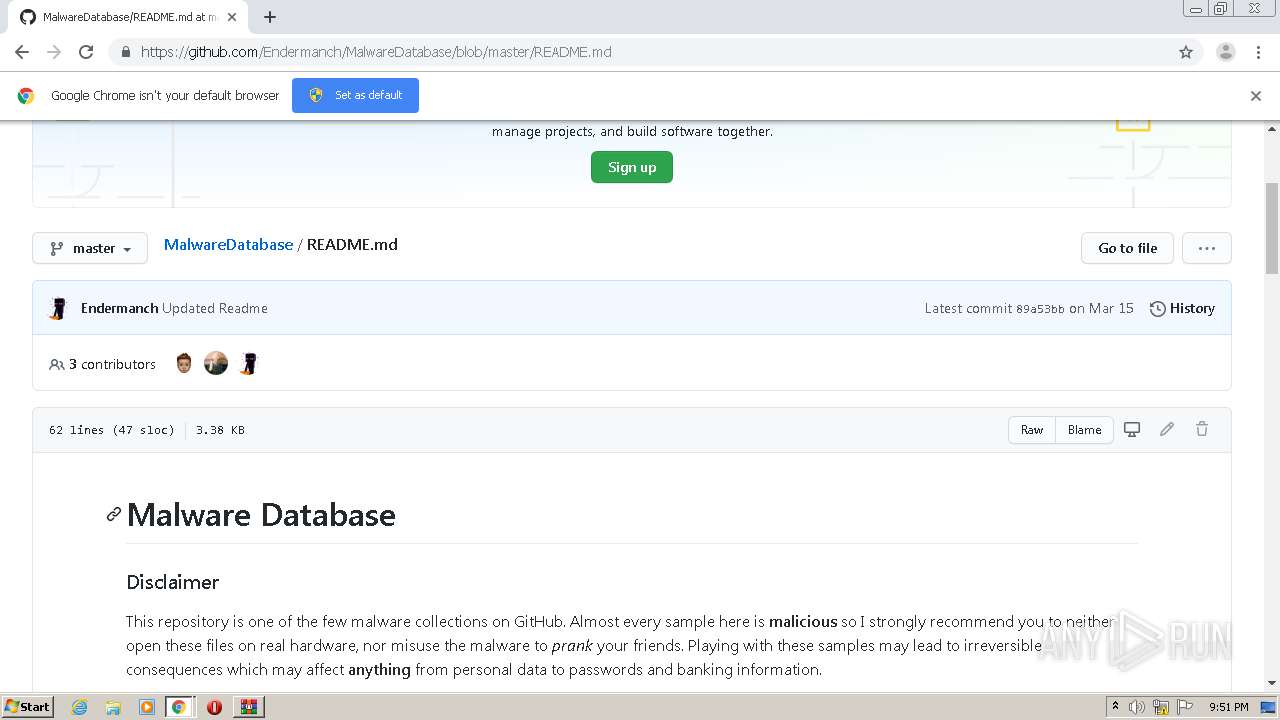
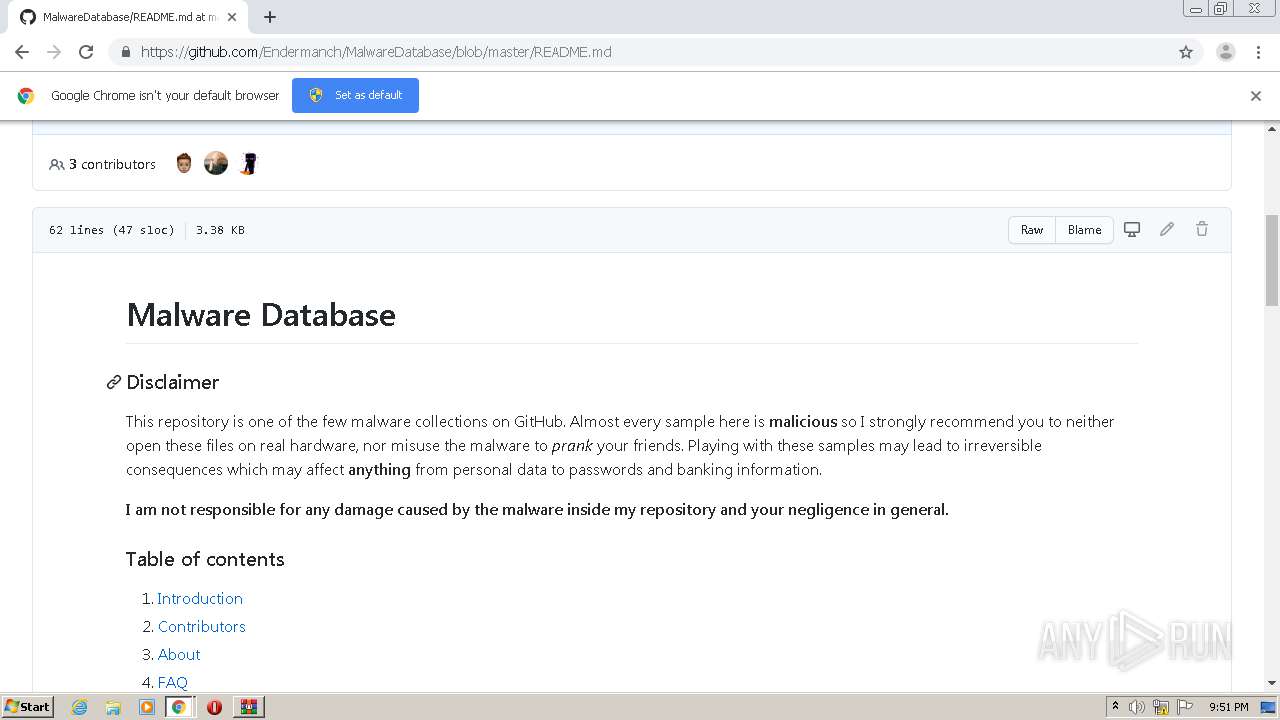
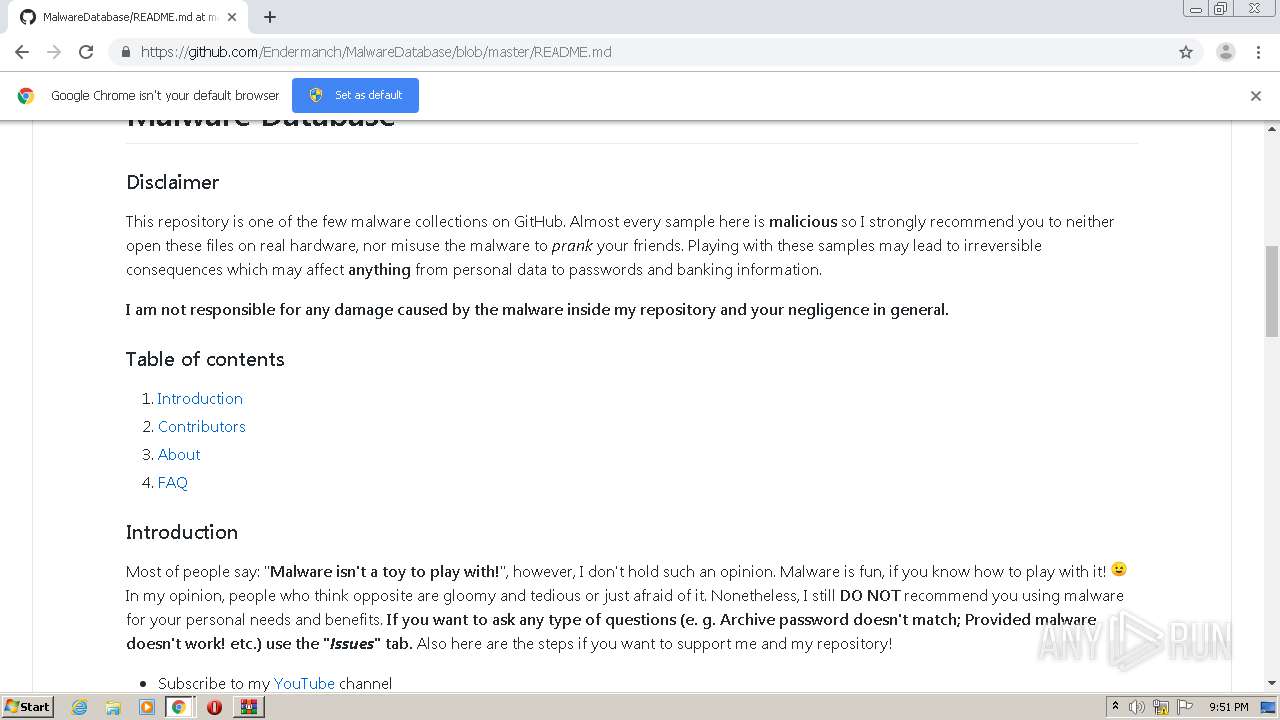
| URL: | https://github.com/Endermanch/MalwareDatabase |
| Full analysis: | https://app.any.run/tasks/5a8380f9-4e92-4df9-aee4-97f57fe64f07 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 20:49:09 |
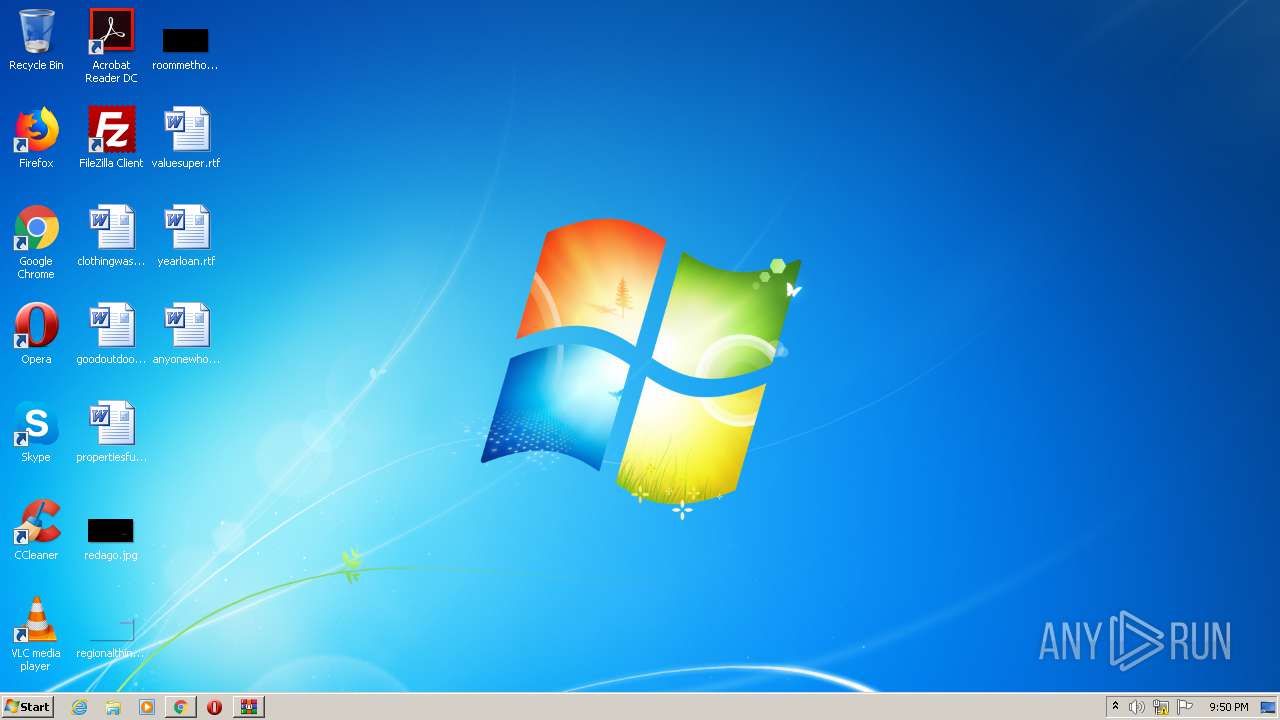
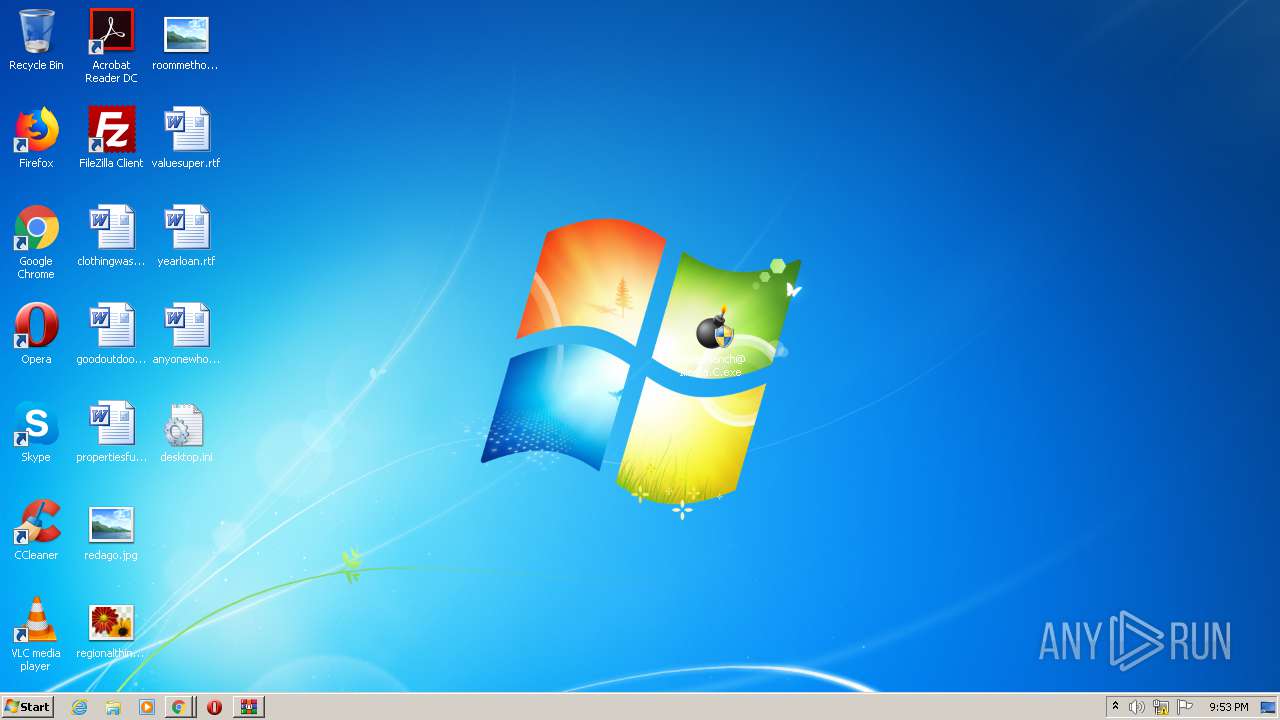
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
MALICIOUS
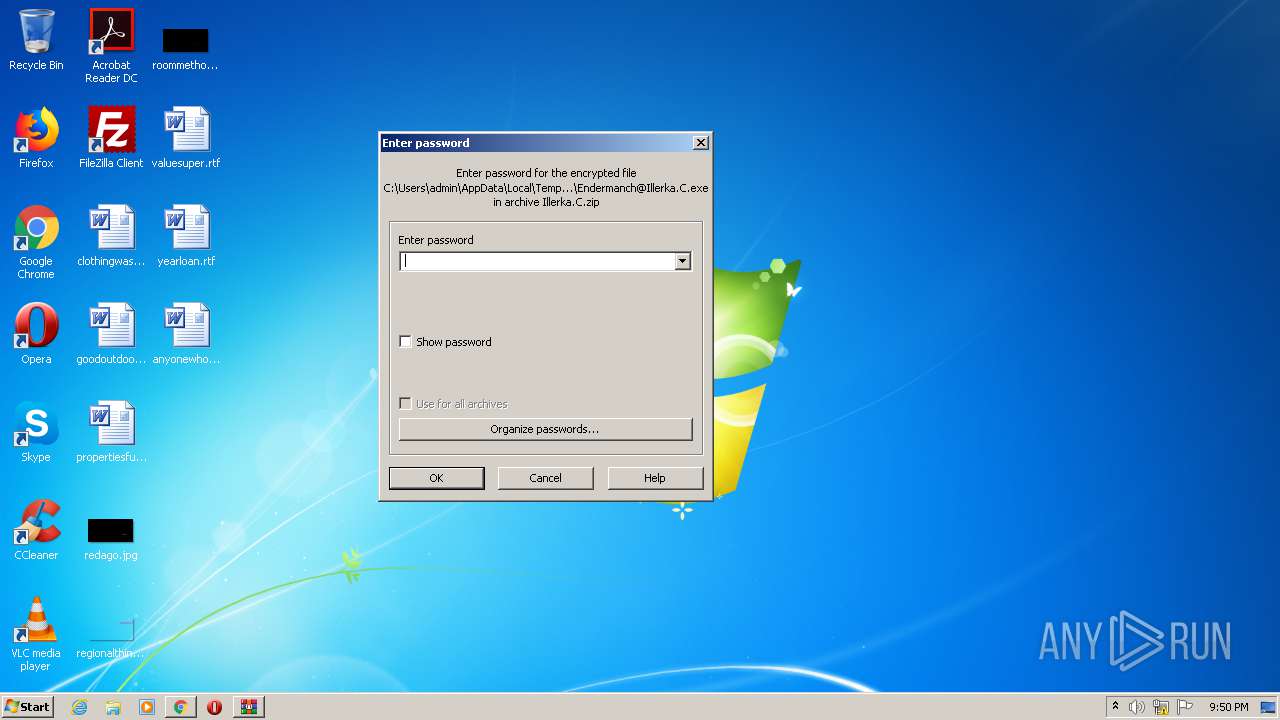
Application was dropped or rewritten from another process
- Endermanch@Illerka.C.exe (PID: 1528)
- Endermanch@Illerka.C.exe (PID: 2264)
- Endermanch@Illerka.C.exe (PID: 1396)
- Endermanch@Illerka.C.exe (PID: 2892)
UAC/LUA settings modification
- Endermanch@Illerka.C.exe (PID: 1528)
- Endermanch@Illerka.C.exe (PID: 2892)
SUSPICIOUS
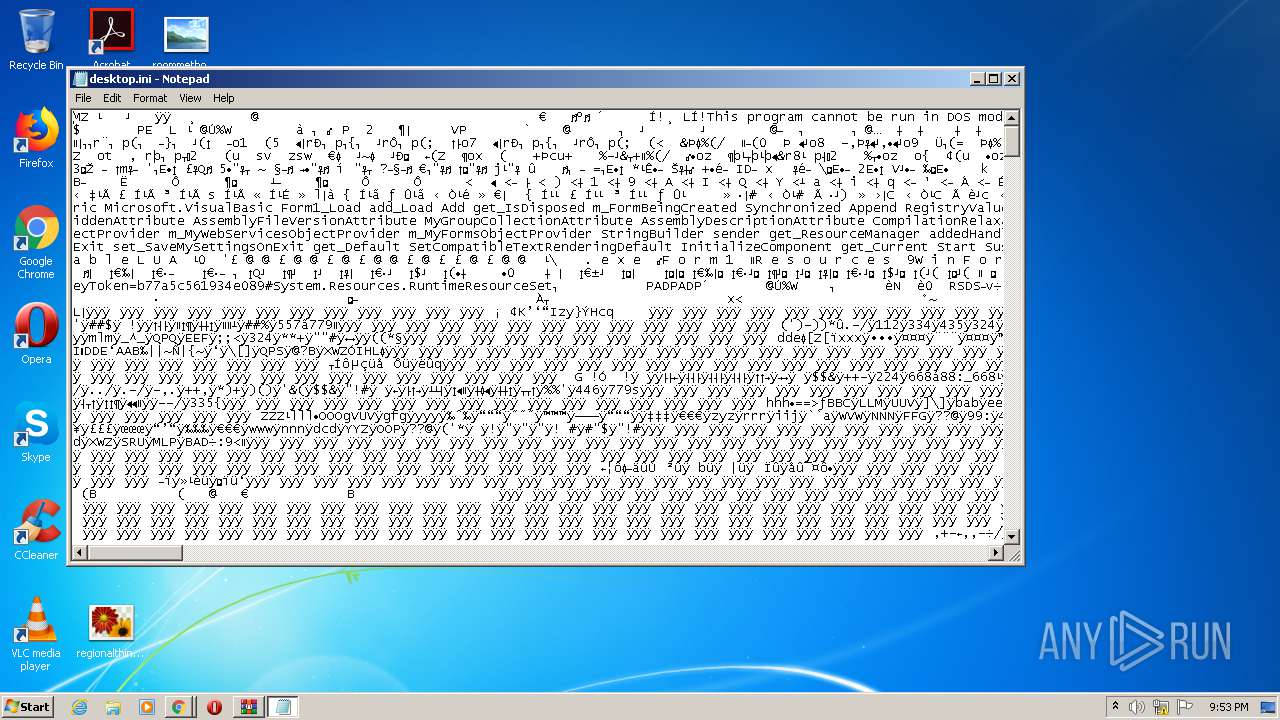
Executable content was dropped or overwritten
- Endermanch@Illerka.C.exe (PID: 1528)
- Endermanch@Illerka.C.exe (PID: 2892)
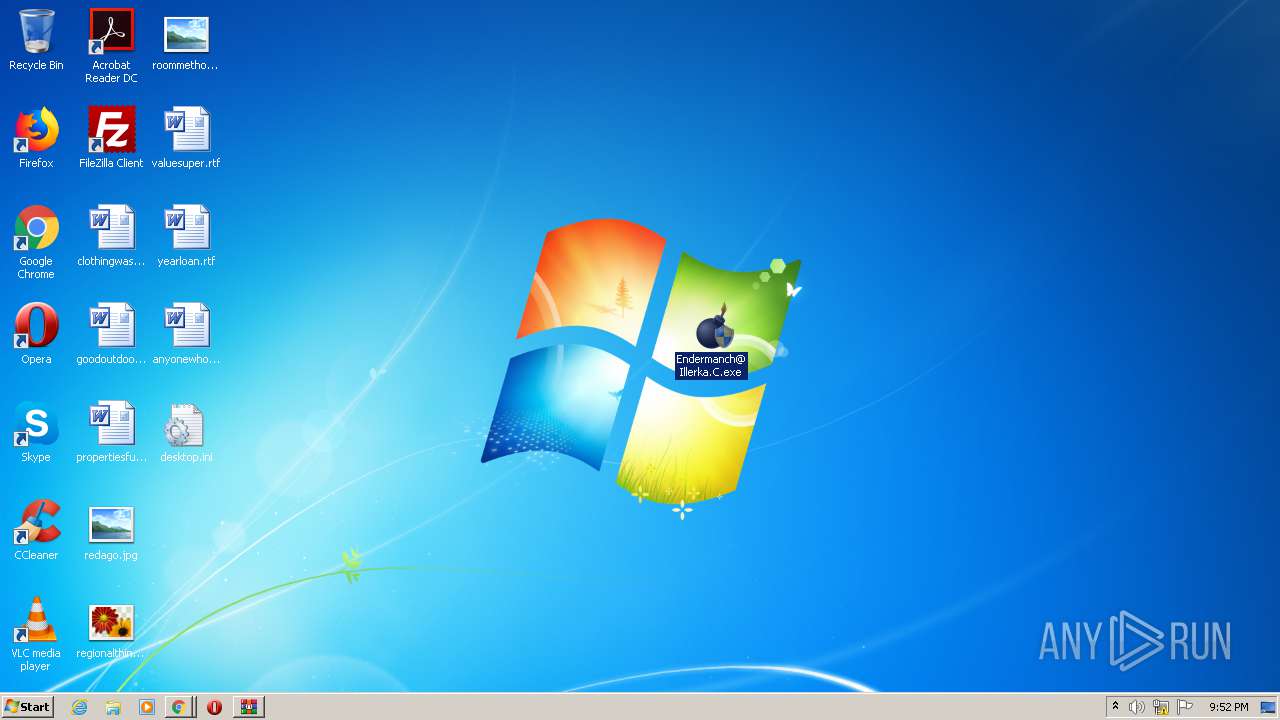
Writes to a desktop.ini file (may be used to cloak folders)
- Endermanch@Illerka.C.exe (PID: 1528)
- Endermanch@Illerka.C.exe (PID: 2892)
Executed via COM
- DllHost.exe (PID: 3508)
INFO
Reads the hosts file
- chrome.exe (PID: 1508)
- chrome.exe (PID: 852)
Reads settings of System Certificates
- chrome.exe (PID: 1508)
Reads Internet Cache Settings
- chrome.exe (PID: 852)
Application launched itself
- chrome.exe (PID: 852)
- chrome.exe (PID: 3552)
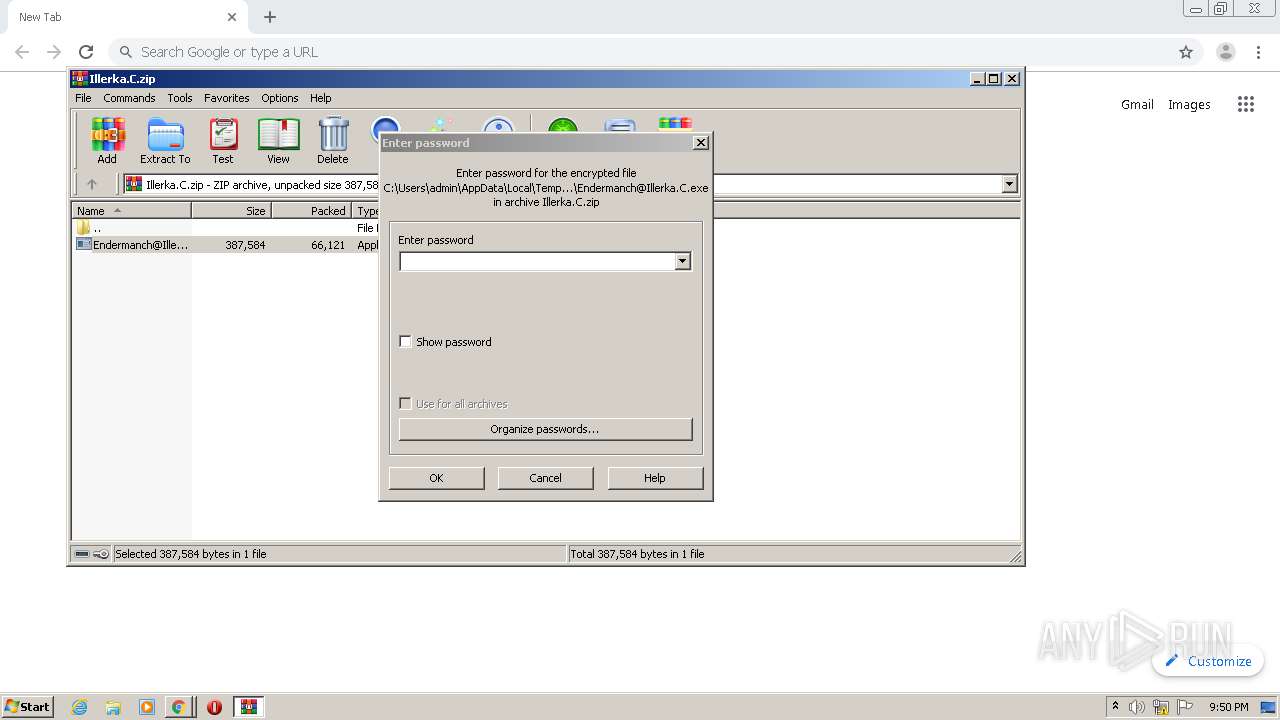
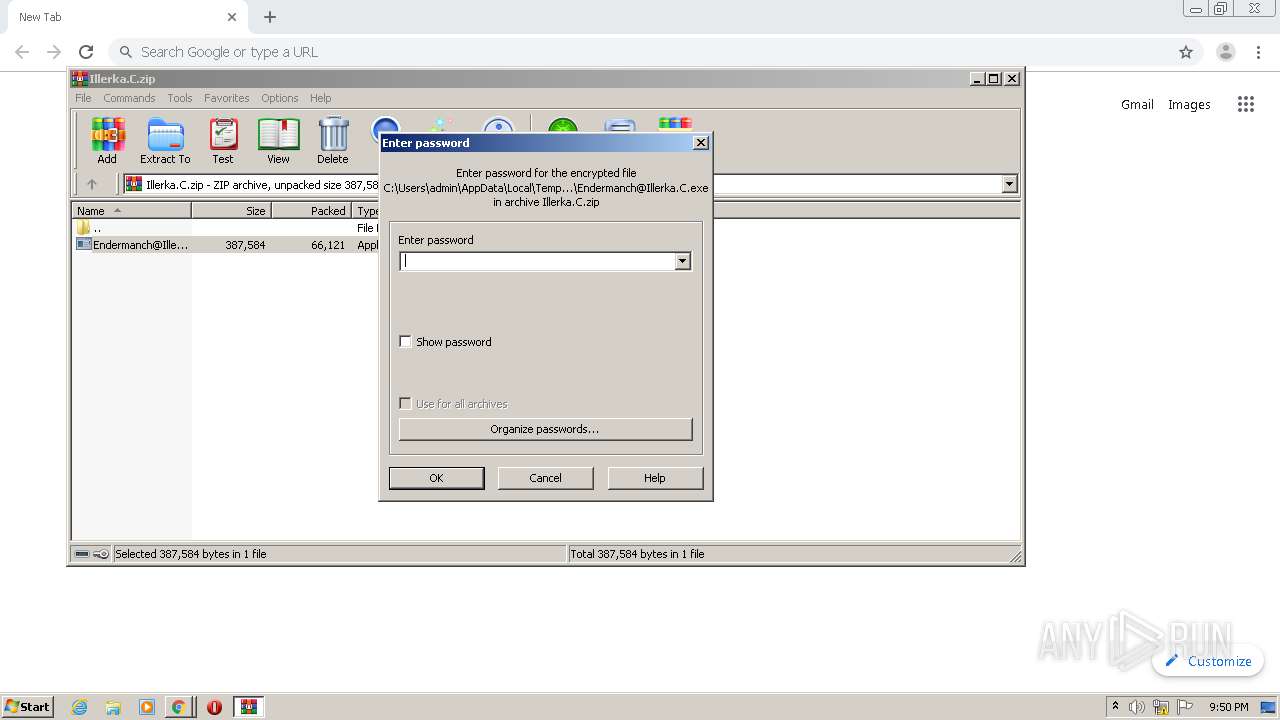
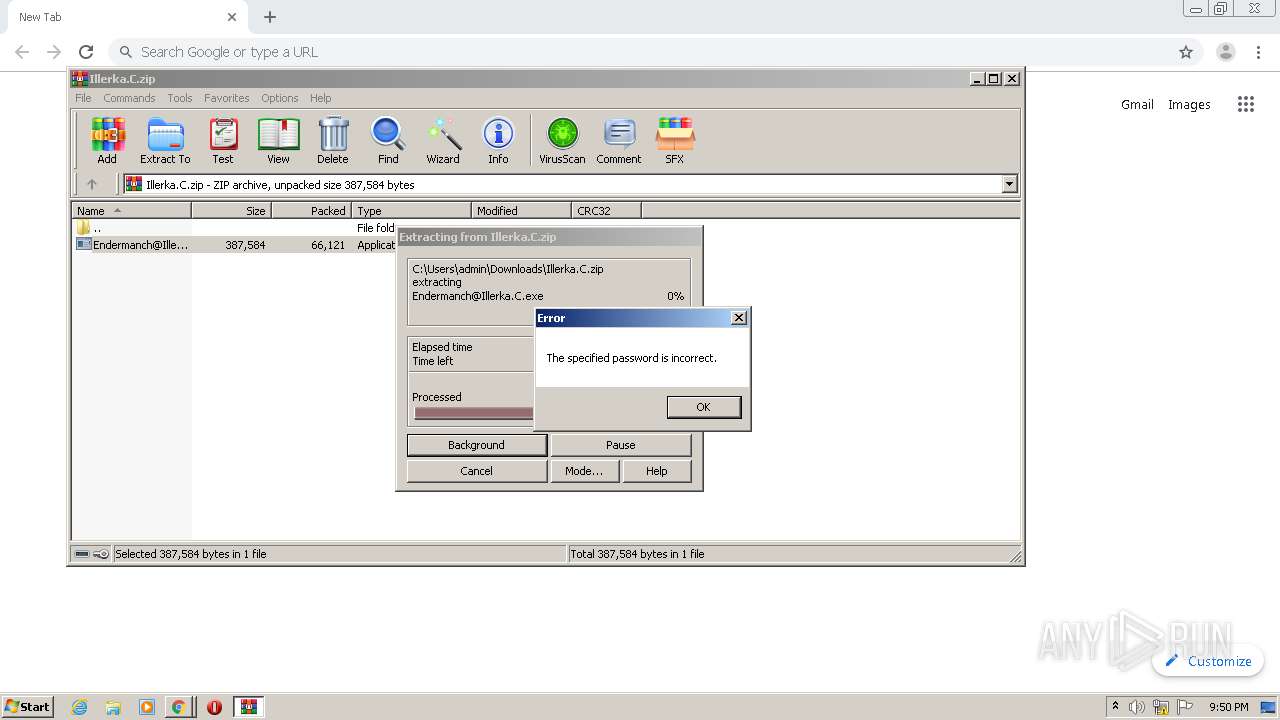
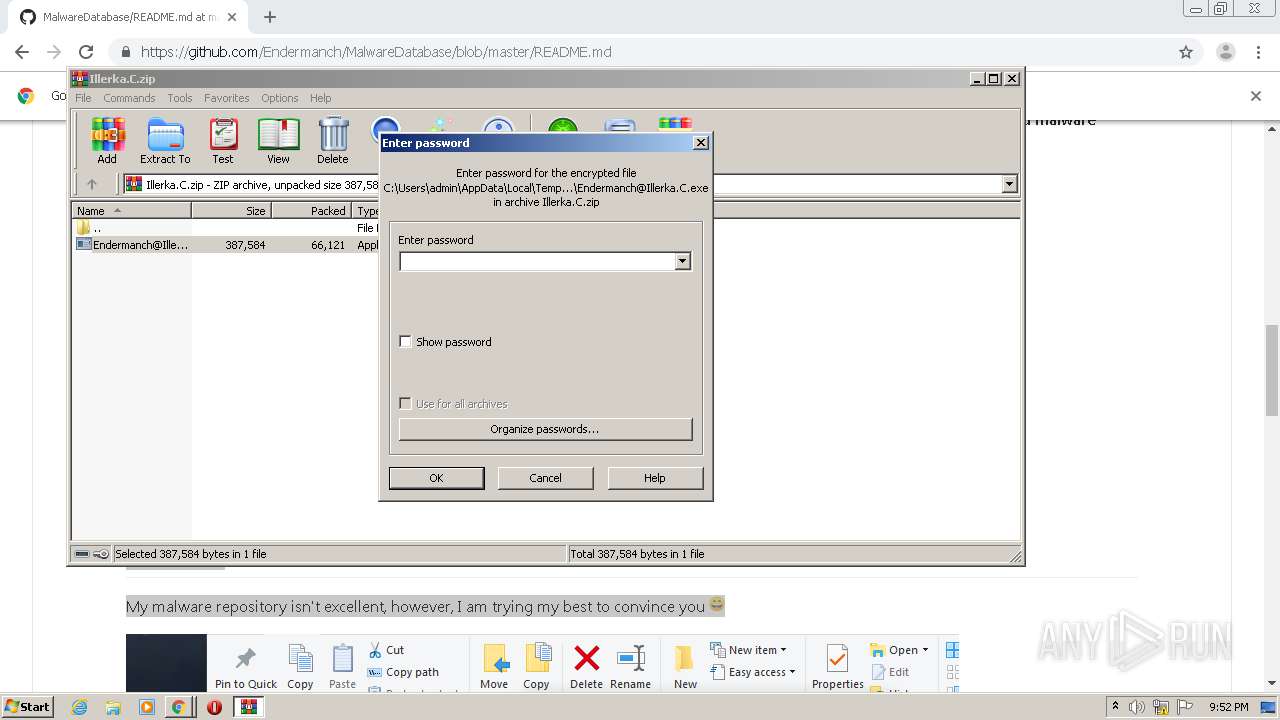
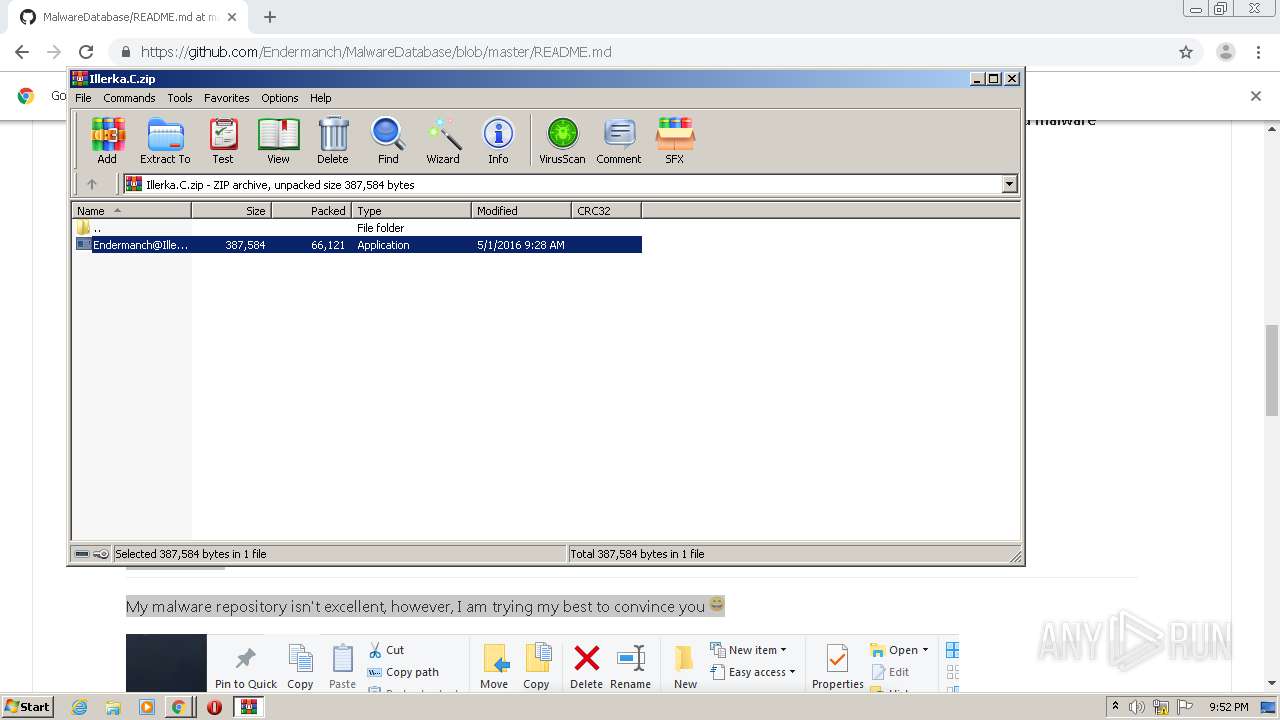
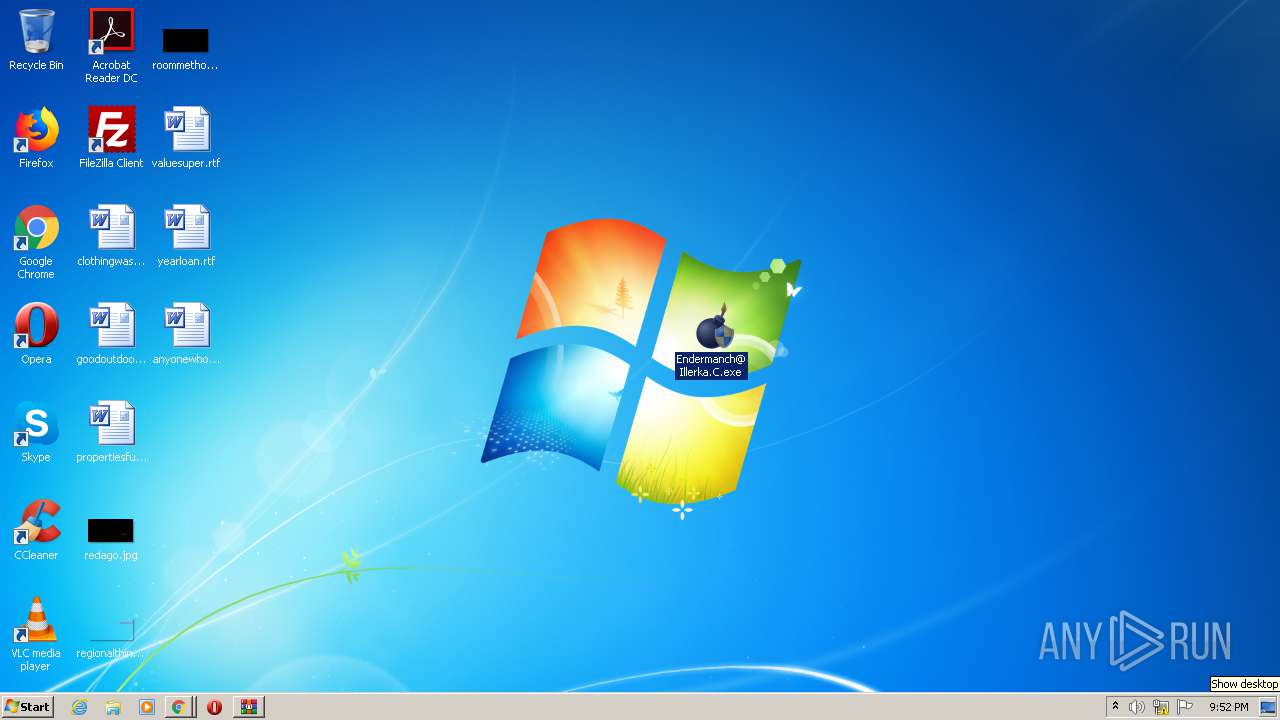
Manual execution by user
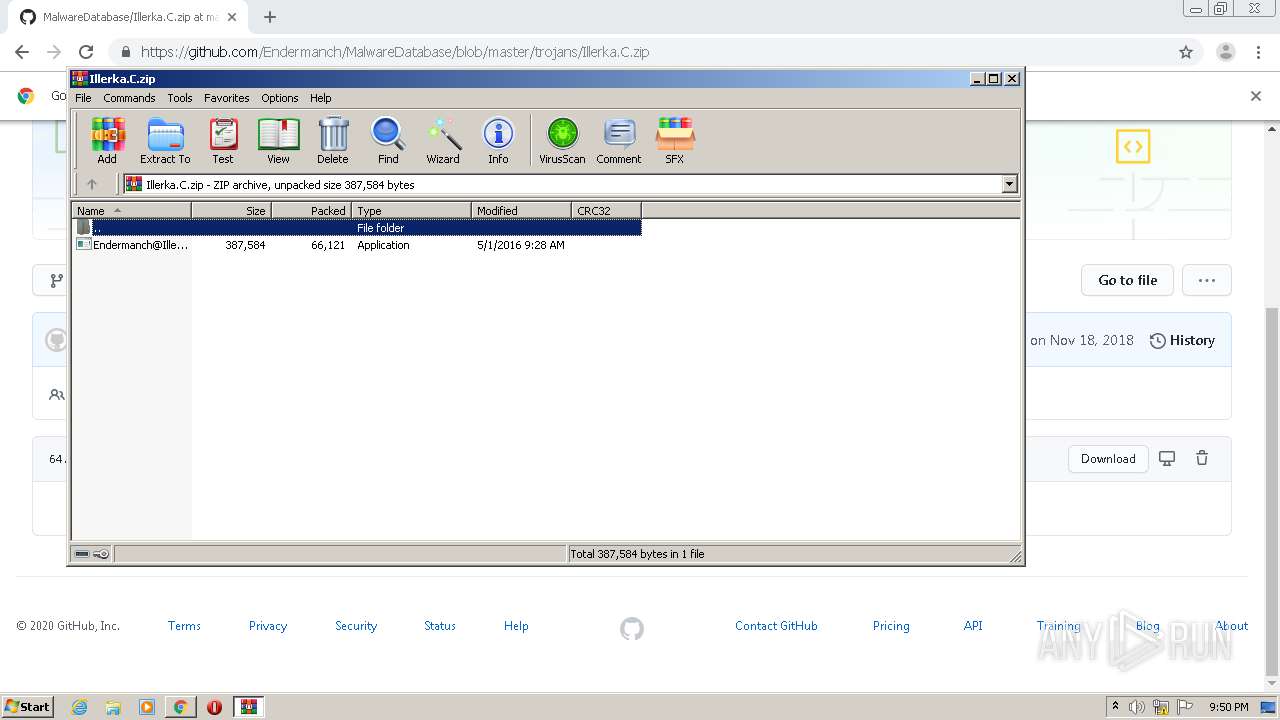
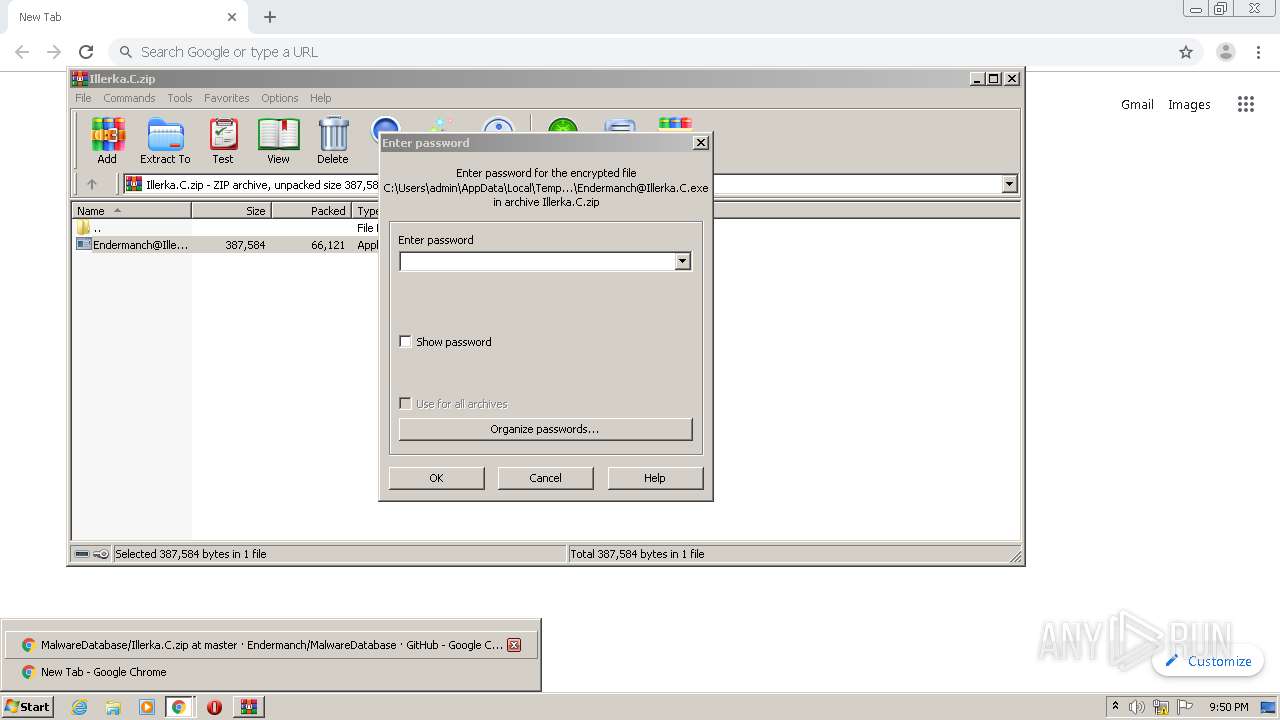
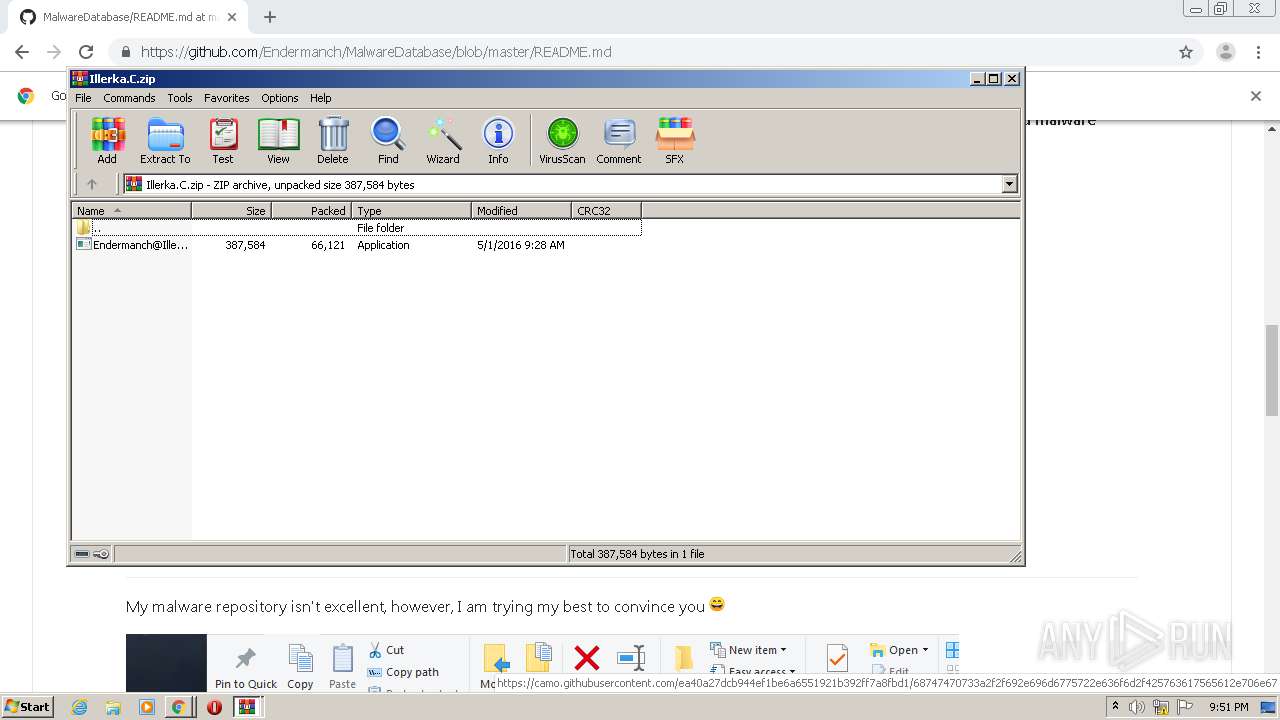
- chrome.exe (PID: 3552)
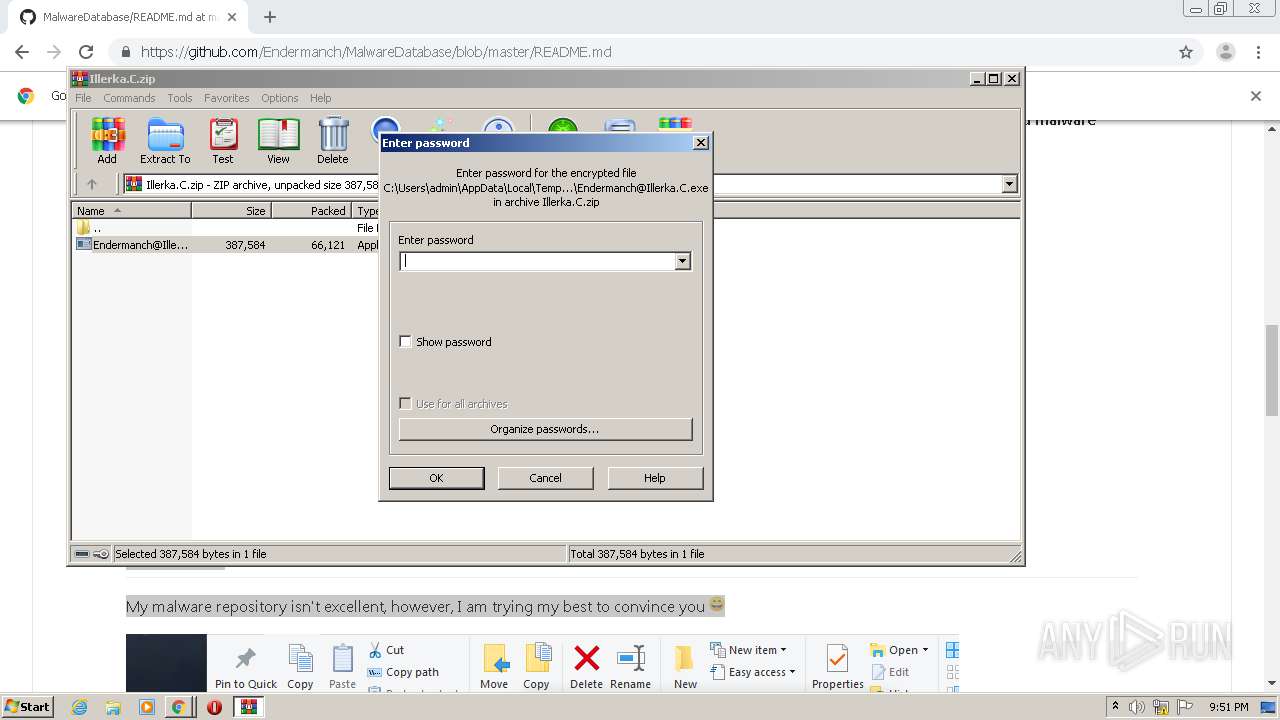
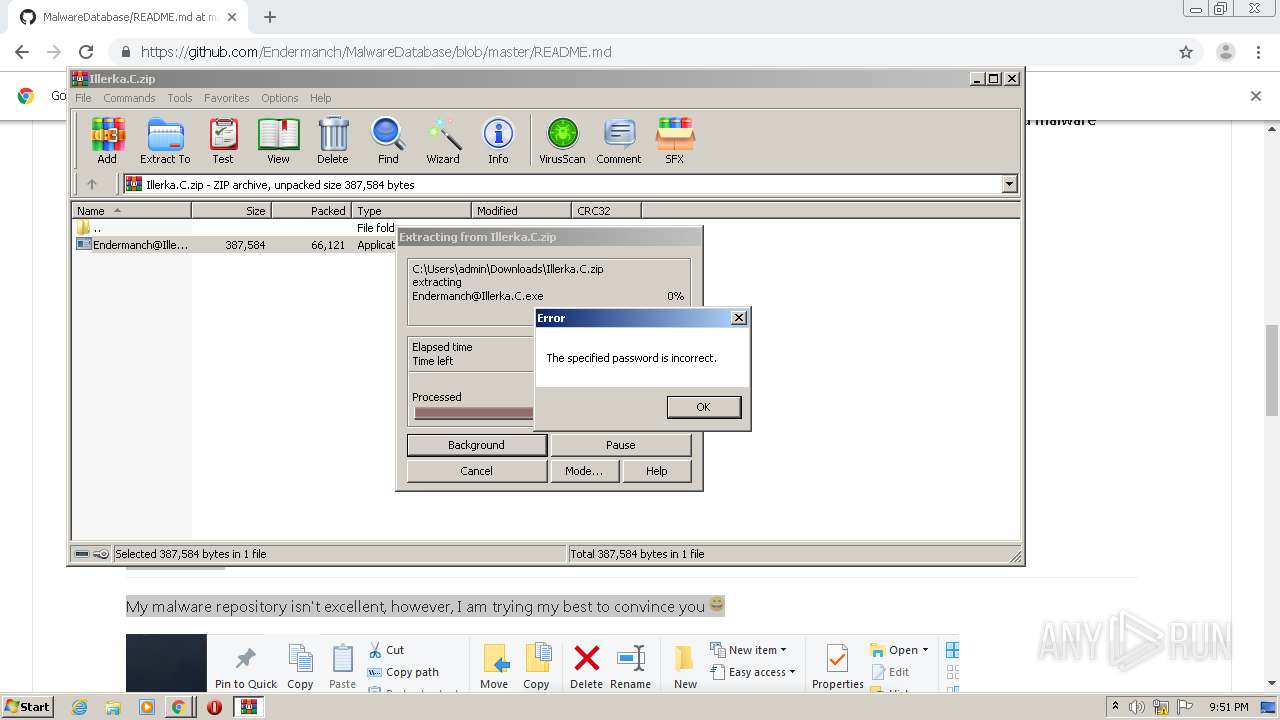
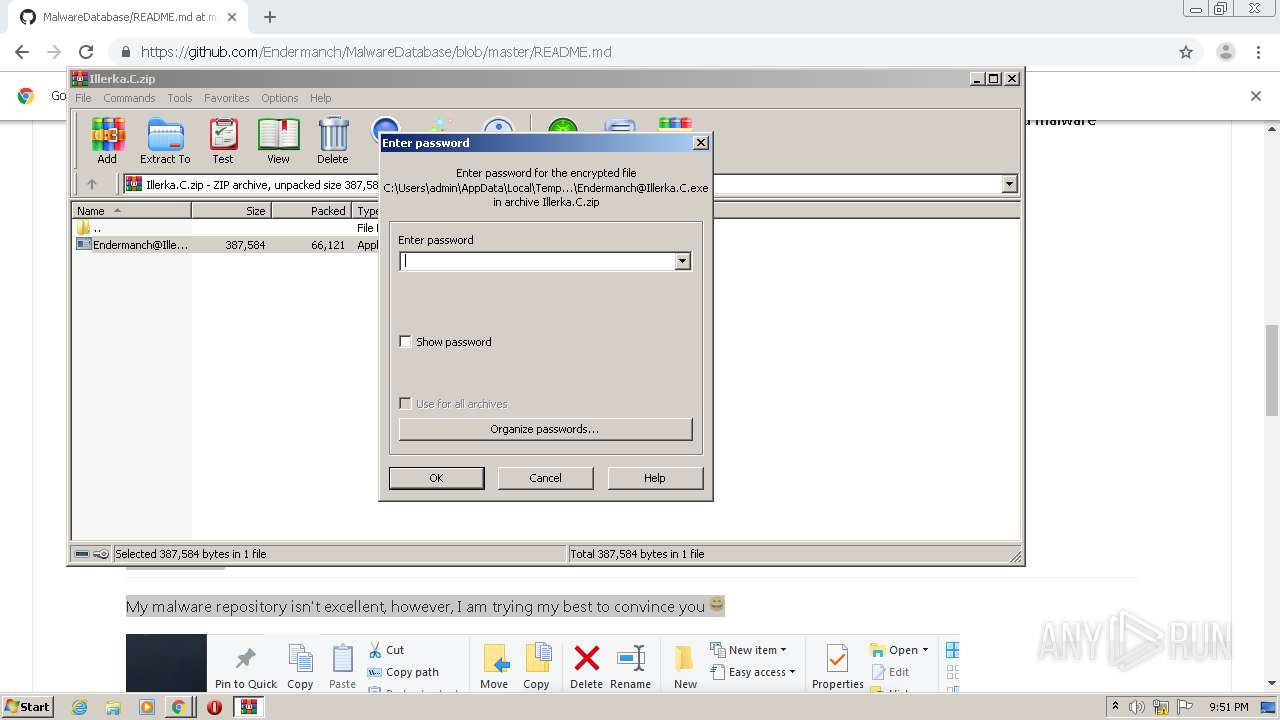
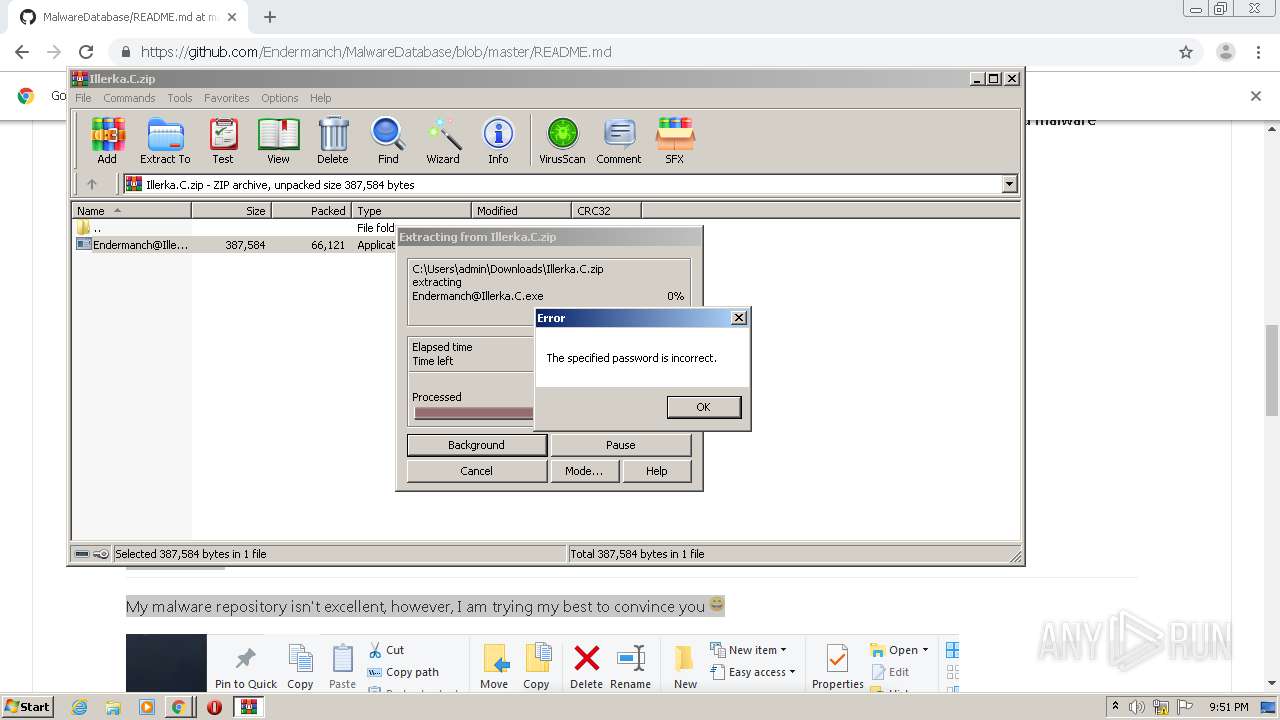
- WinRAR.exe (PID: 2160)
- Endermanch@Illerka.C.exe (PID: 2264)
- Endermanch@Illerka.C.exe (PID: 1396)
- Endermanch@Illerka.C.exe (PID: 1528)
- Endermanch@Illerka.C.exe (PID: 2892)
- NOTEPAD.EXE (PID: 3152)
- WINWORD.EXE (PID: 2788)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2788)
Creates files in the user directory
- WINWORD.EXE (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
33
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1084 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1163507776618471334,7946646876512747210,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=935550935313131435 --mojo-platform-channel-handle=3504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
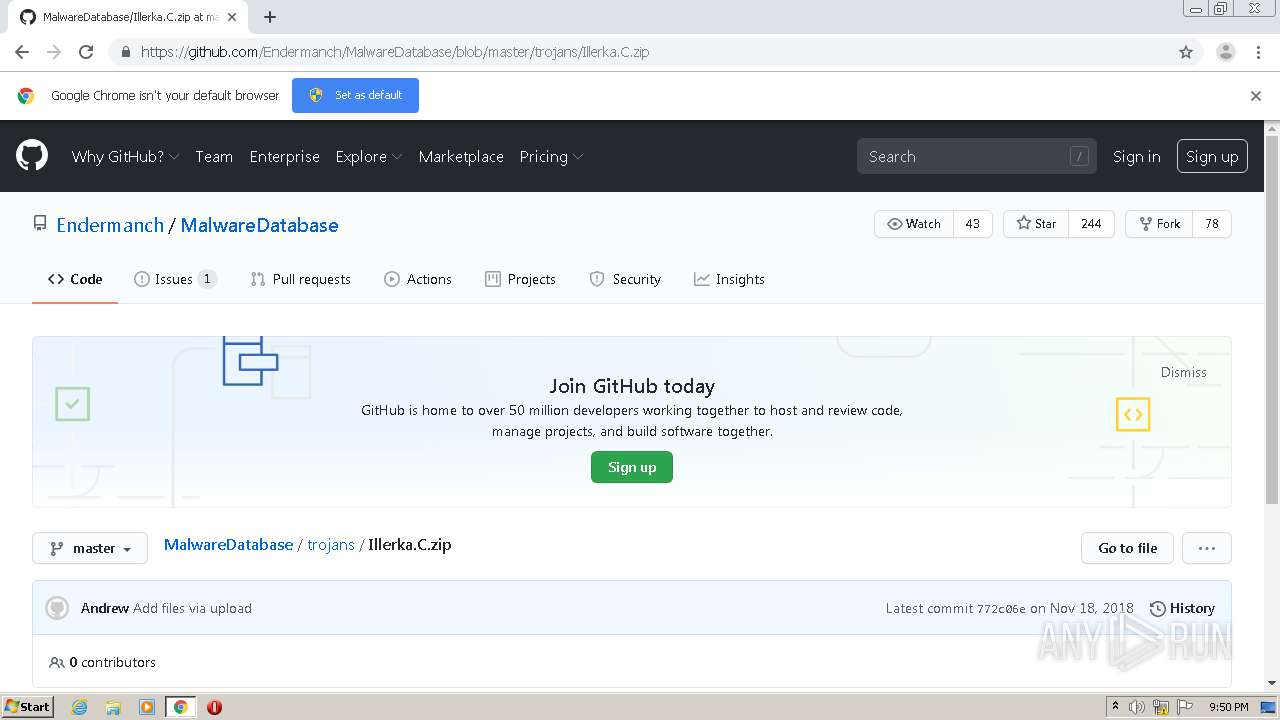
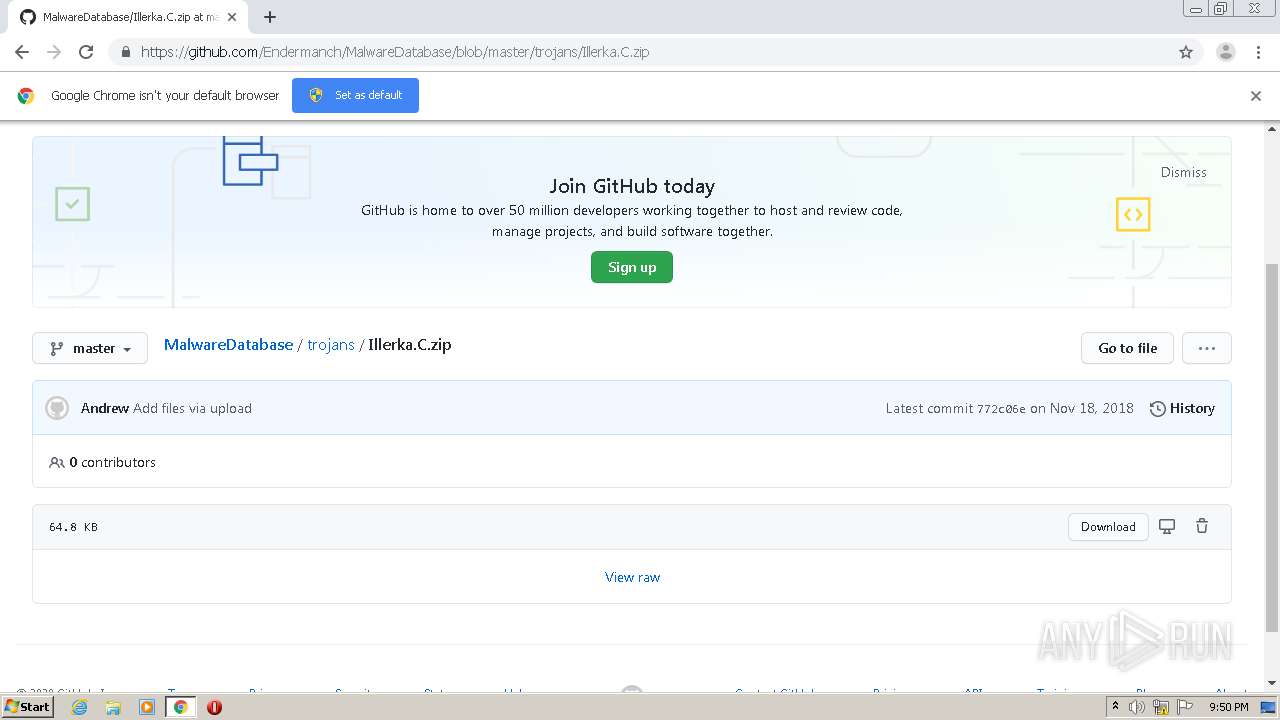
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/Endermanch/MalwareDatabase" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,1163507776618471334,7946646876512747210,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9119995487722048389 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\Desktop\Endermanch@Illerka.C.exe" | C:\Users\admin\Desktop\Endermanch@Illerka.C.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1163507776618471334,7946646876512747210,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10048522317135196238 --mojo-platform-channel-handle=2036 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1163507776618471334,7946646876512747210,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9343942157703071831 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\Desktop\Endermanch@Illerka.C.exe" | C:\Users\admin\Desktop\Endermanch@Illerka.C.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6da2a9d0,0x6da2a9e0,0x6da2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1163507776618471334,7946646876512747210,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5923086604728214726 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 962
Read events
2 408
Write events
296
Delete events
258
Modification events
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (612) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 852-13241393364612500 |
Value: 259 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
20
Suspicious files
54
Text files
120
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4087406e-c4ad-459c-8261-51cfecb4a9d3.tmp | — | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF157c5d.TMP | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF157c1f.TMP | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF157c4e.TMP | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
43
DNS requests
30
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1508 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 140.82.118.4:443 | github.com | — | US | malicious |
1508 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1508 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 151.101.0.133:443 | avatars0.githubusercontent.com | Fastly | US | malicious |
1508 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 172.217.16.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 52.206.227.240:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
avatars3.githubusercontent.com |
| whitelisted |