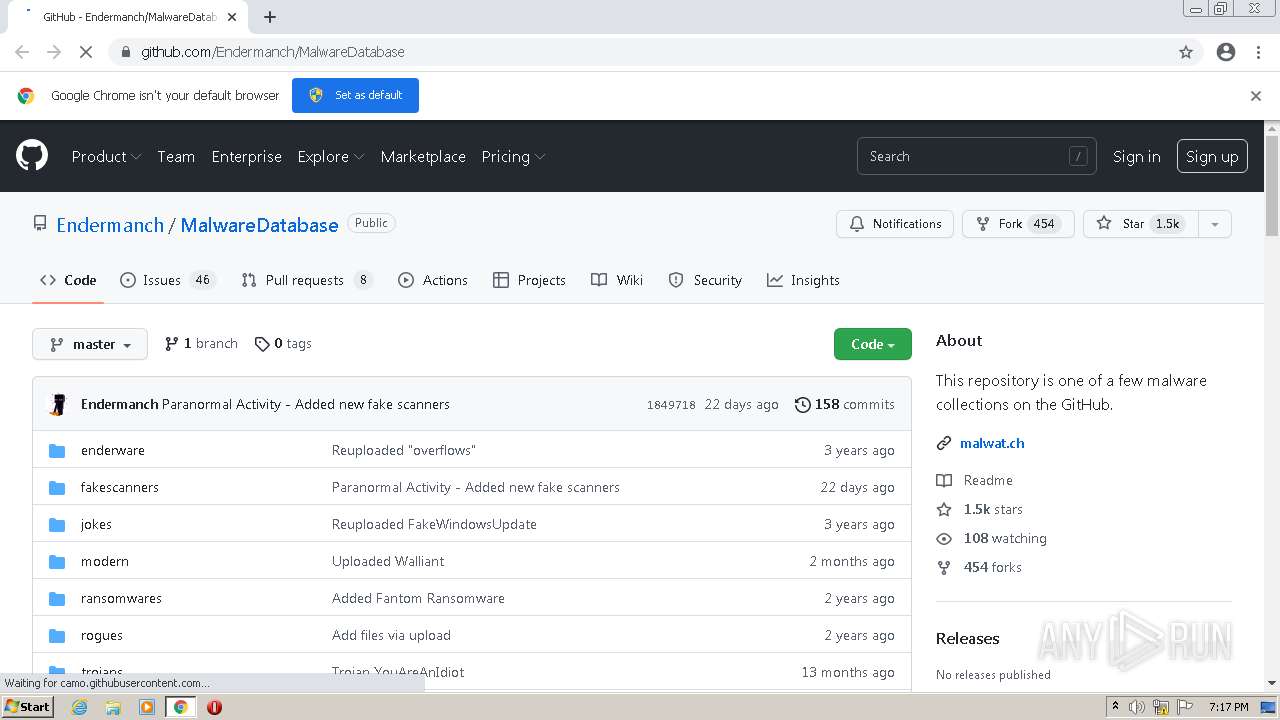
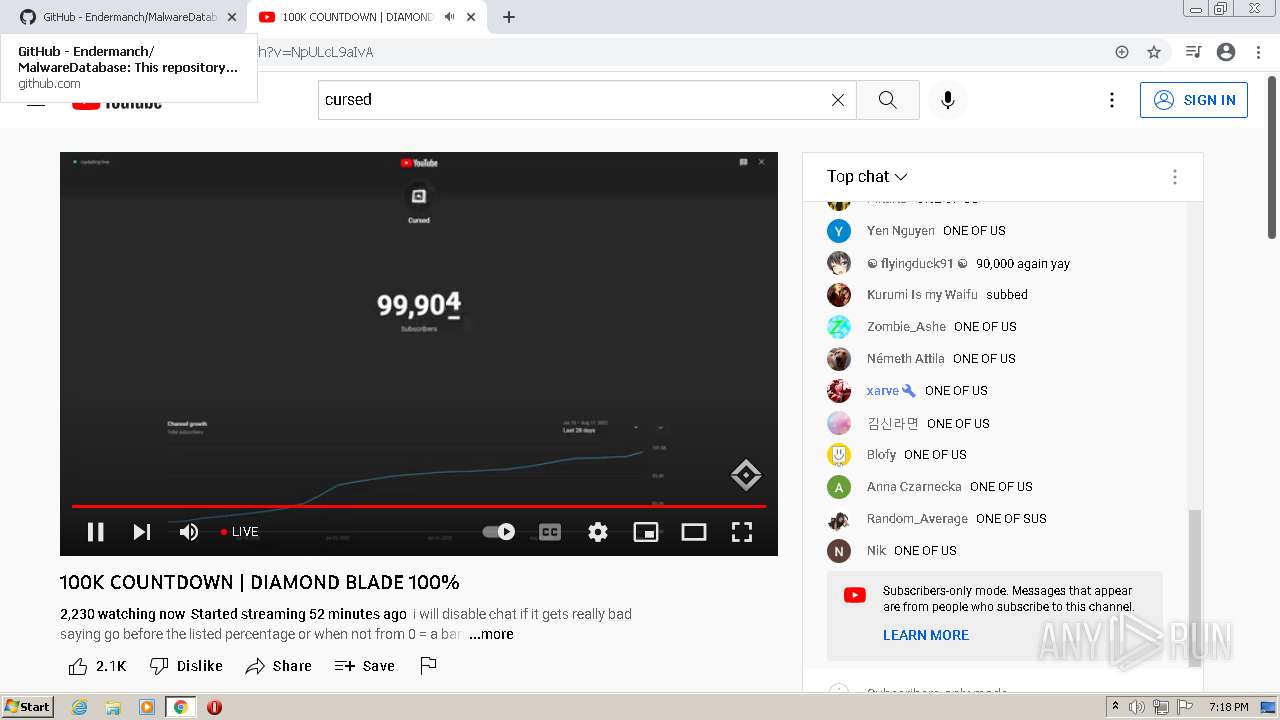
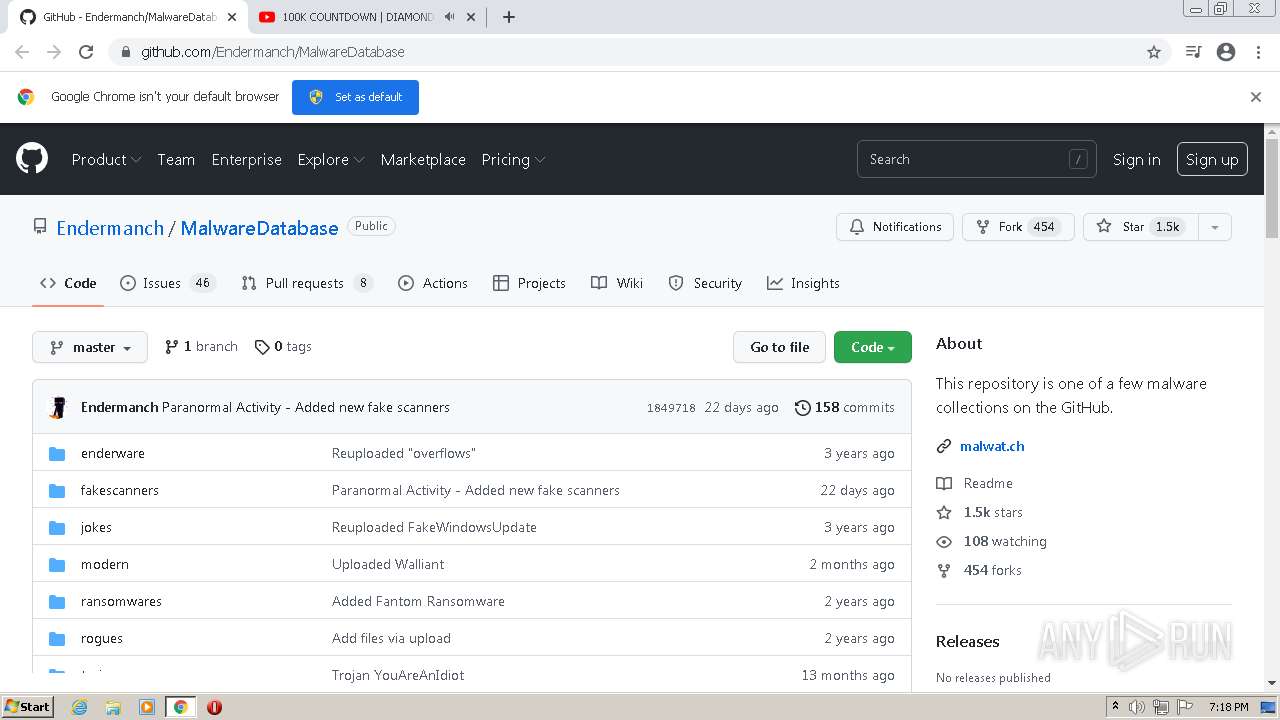
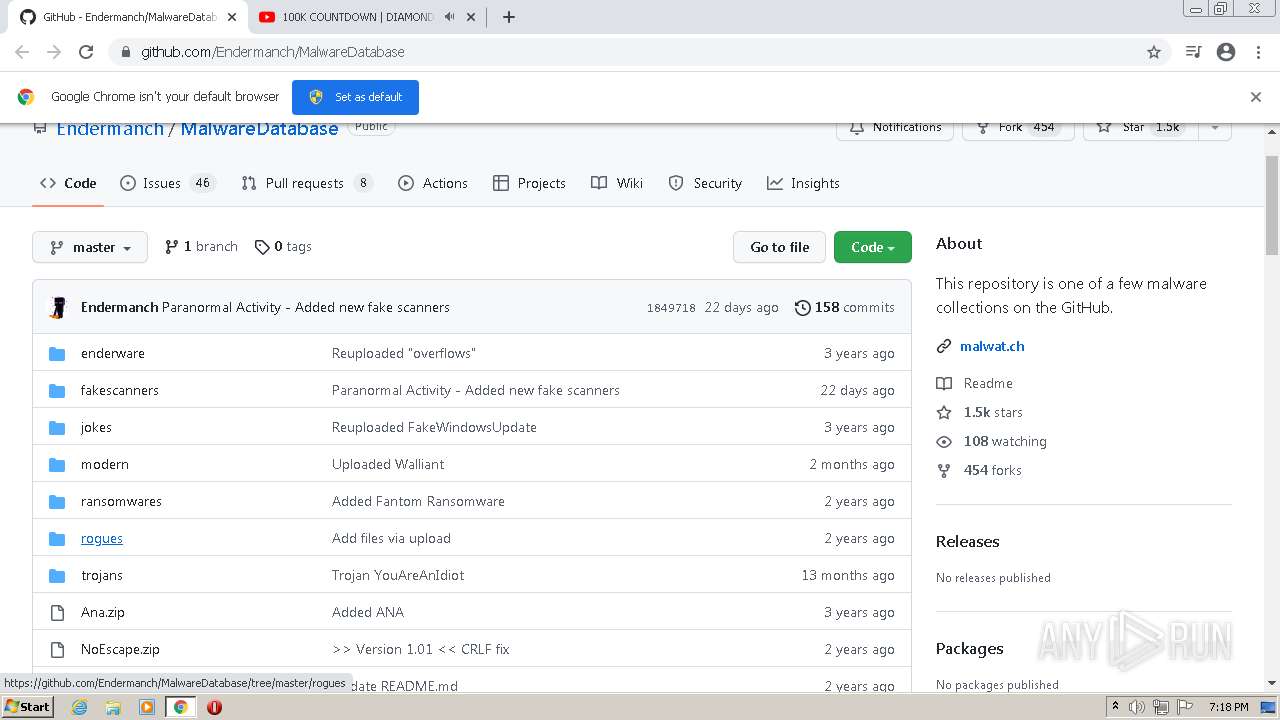
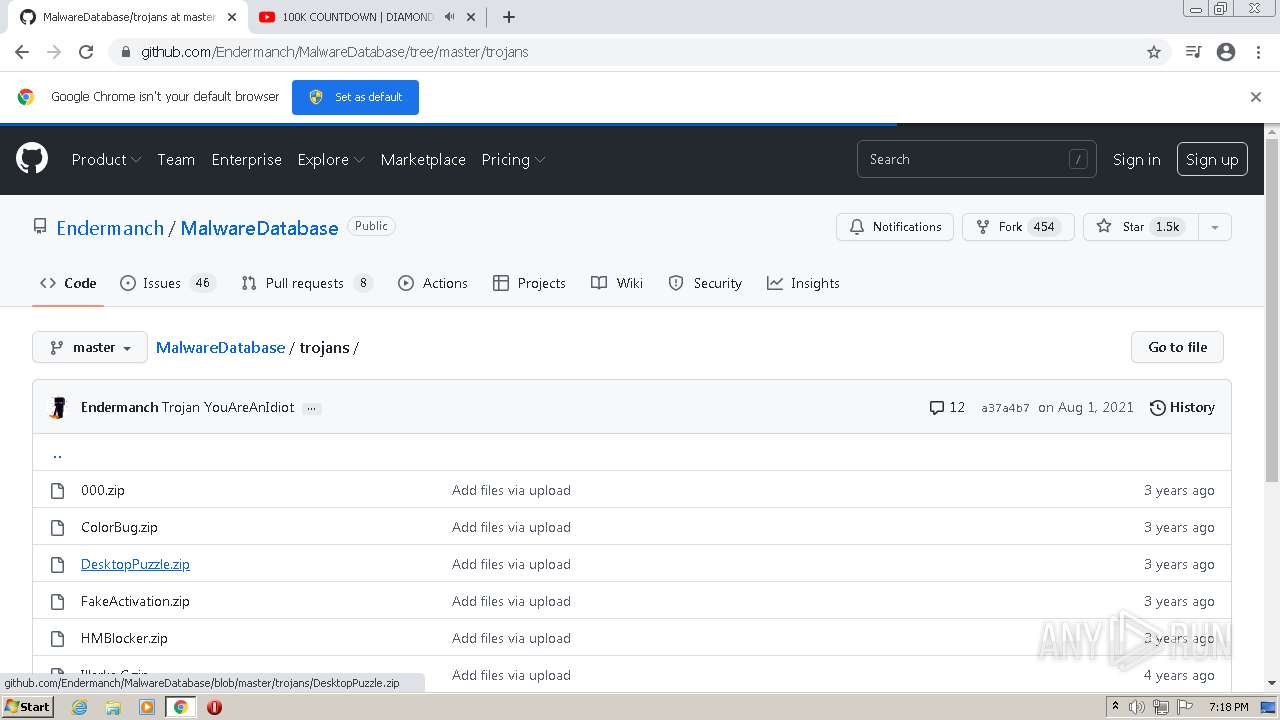
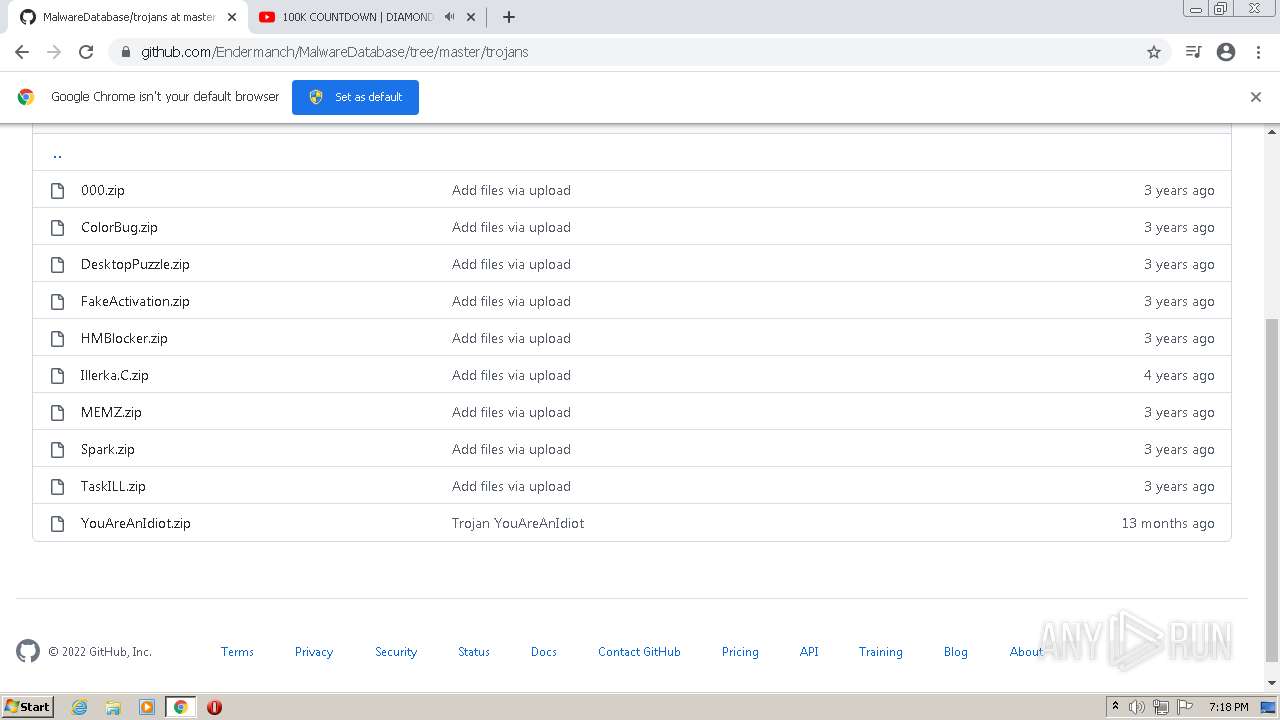
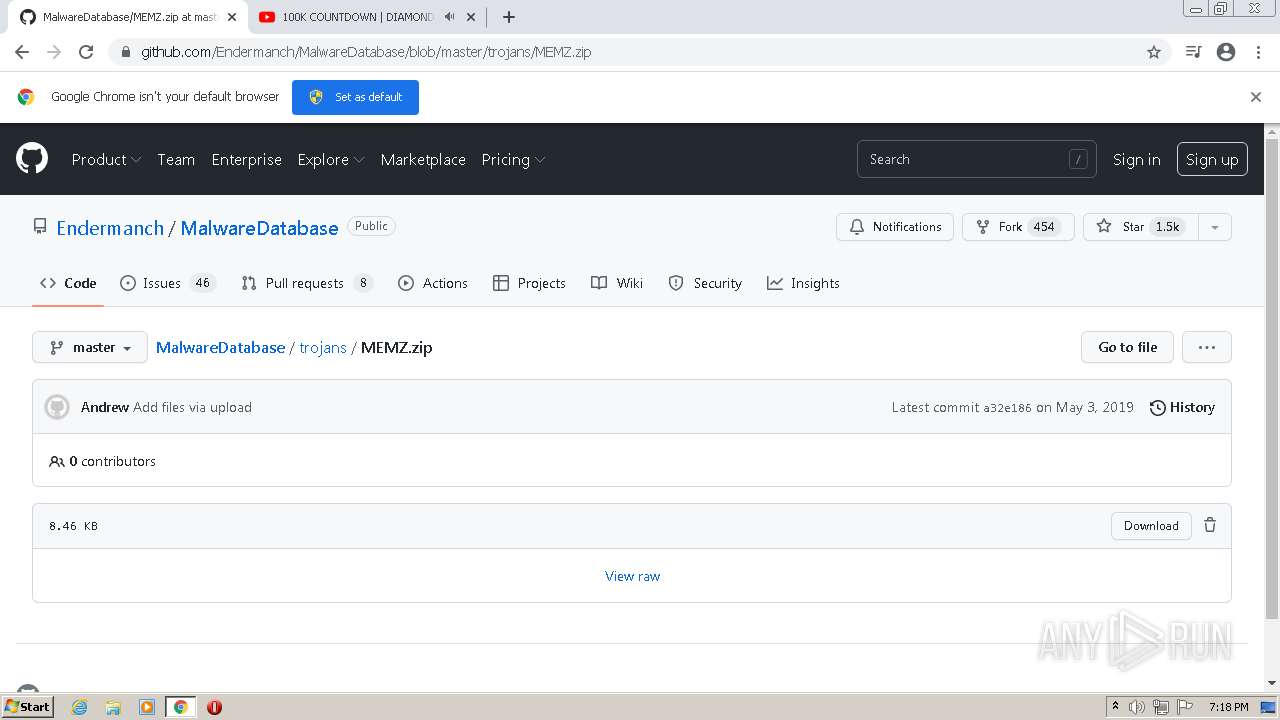
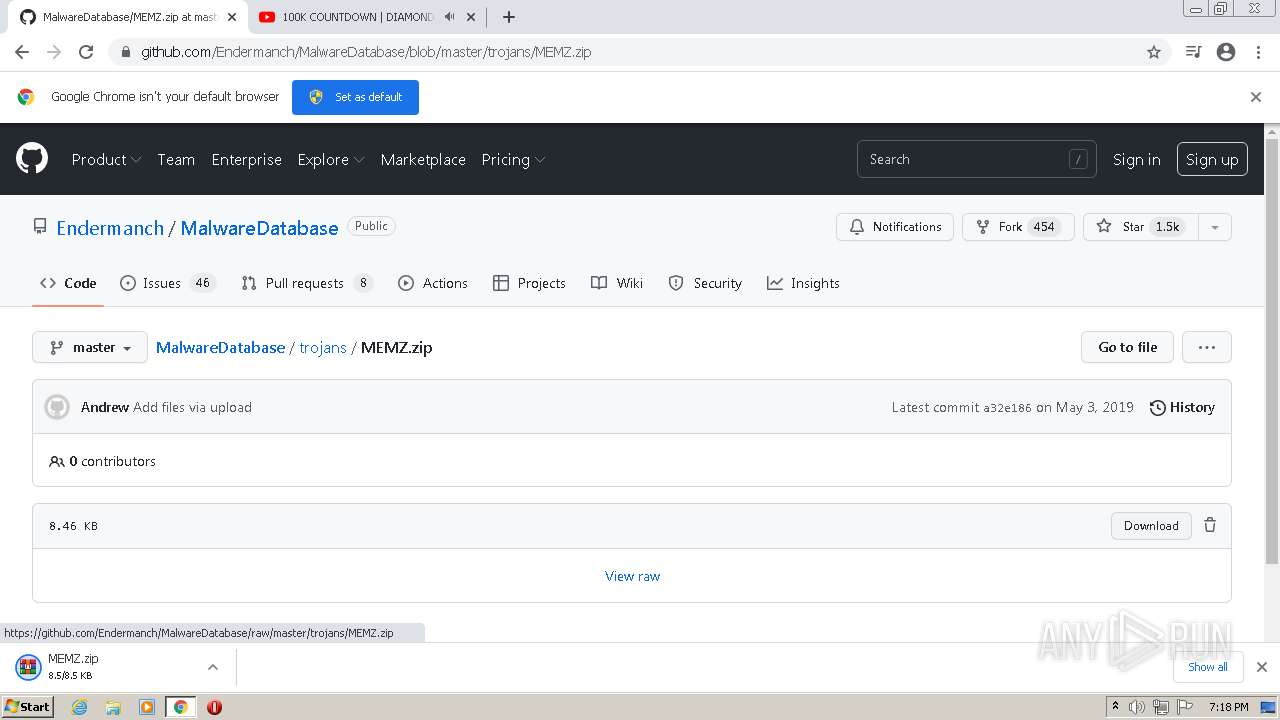
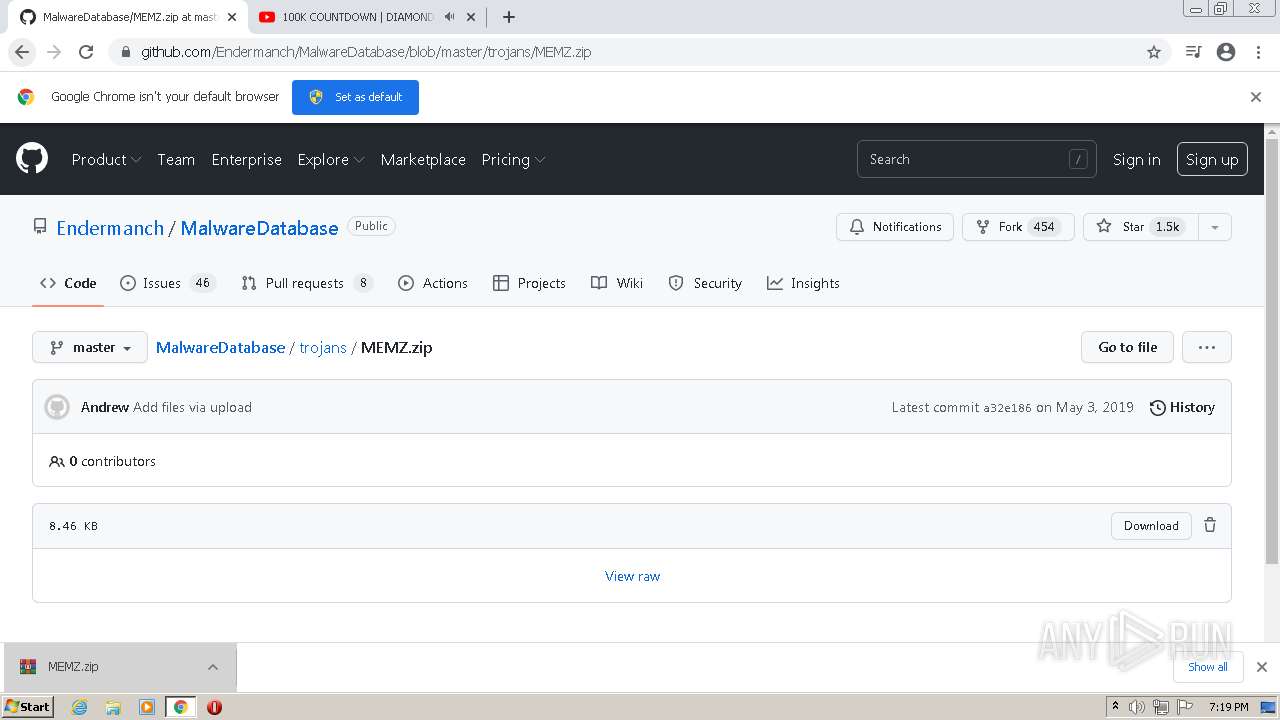
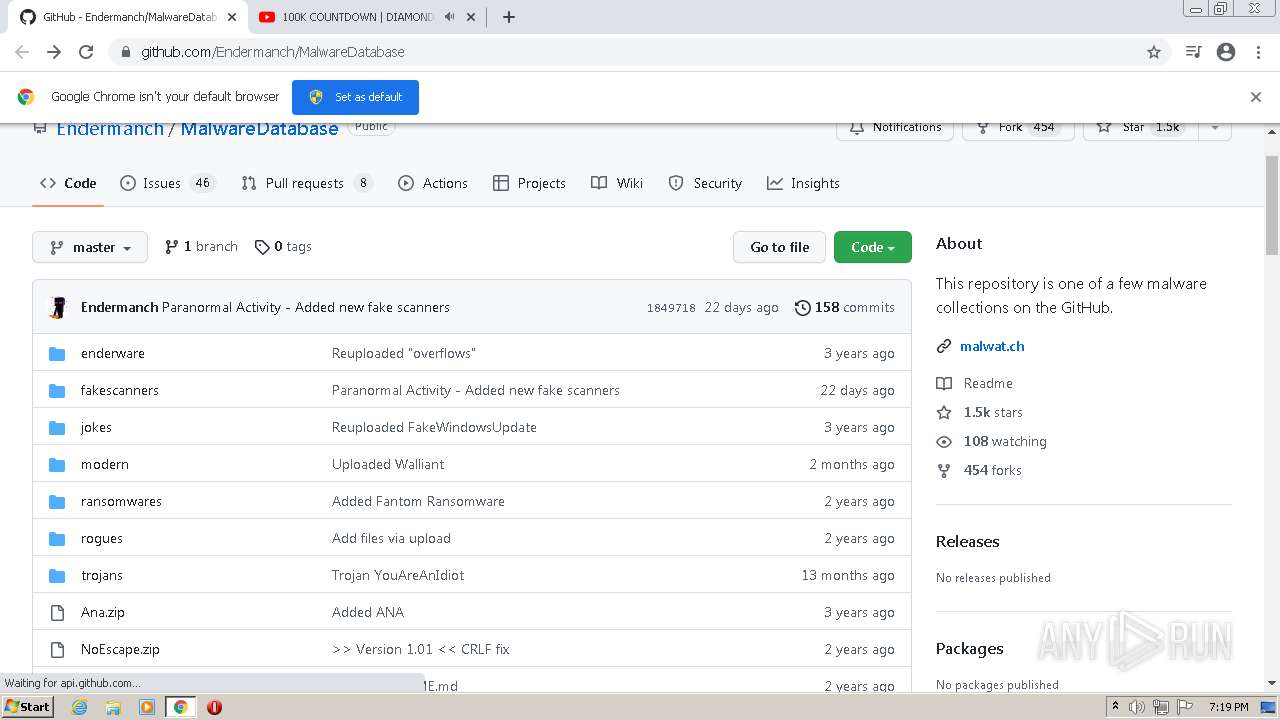
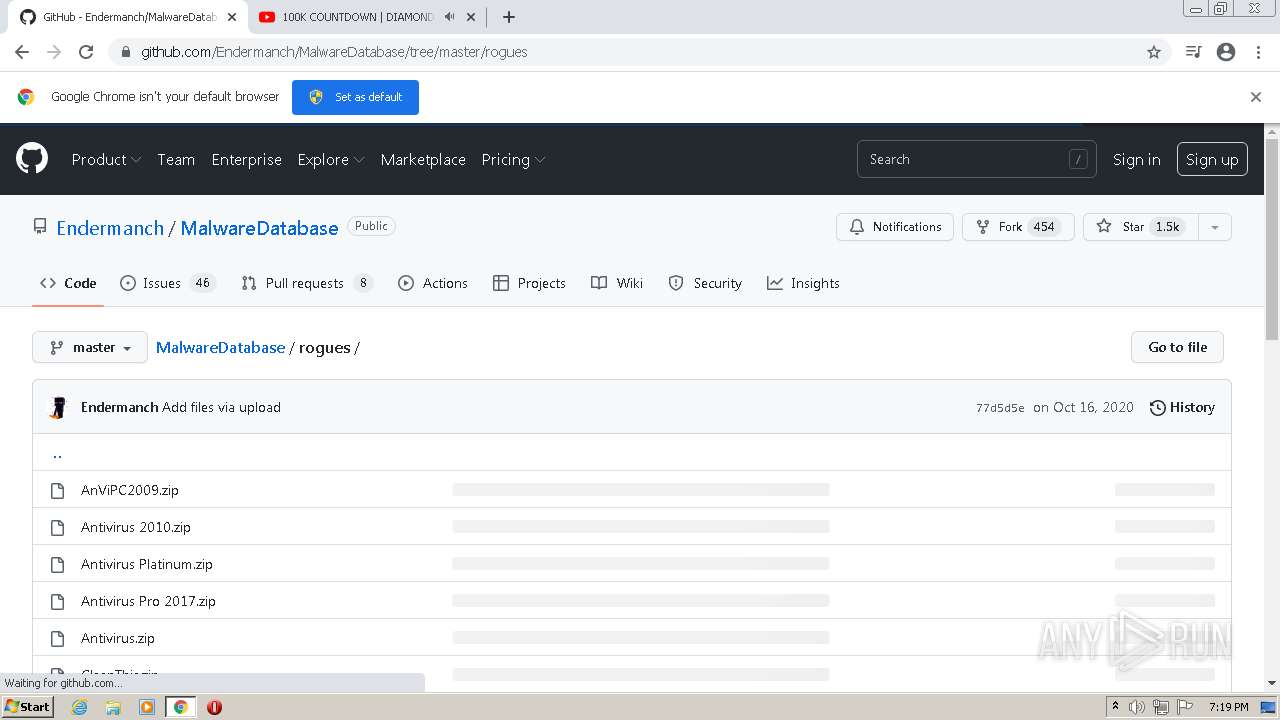
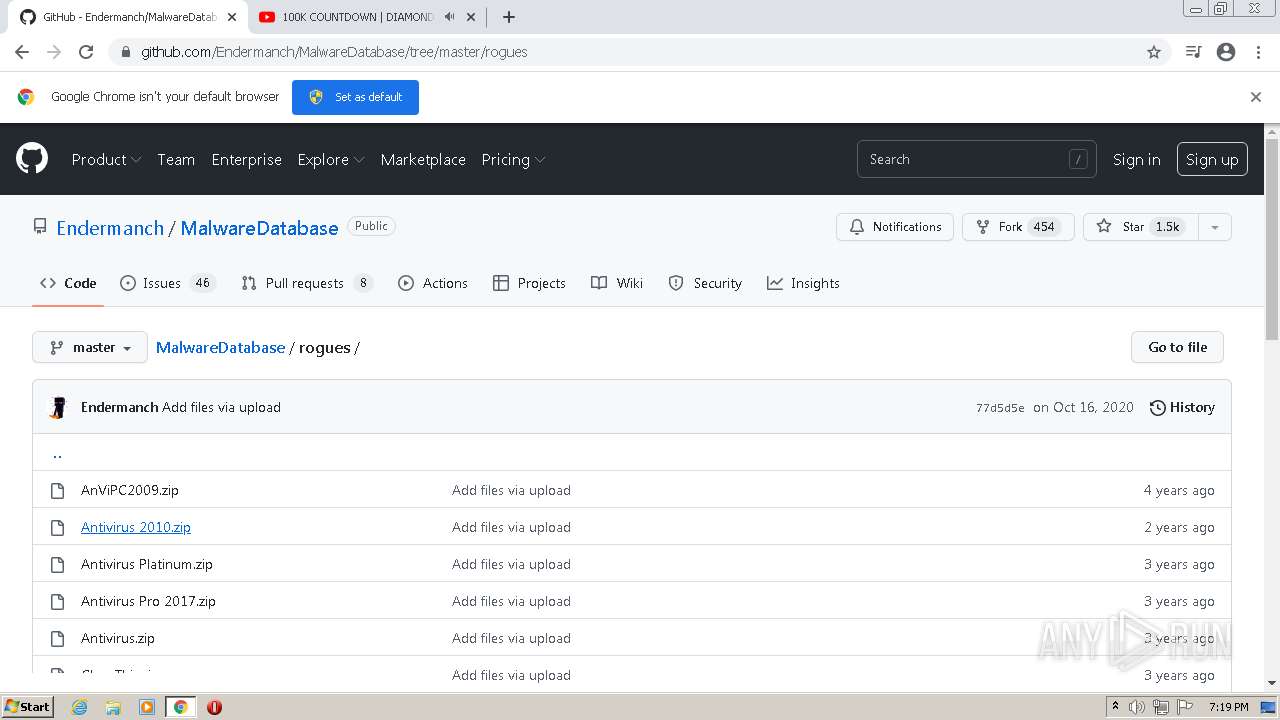
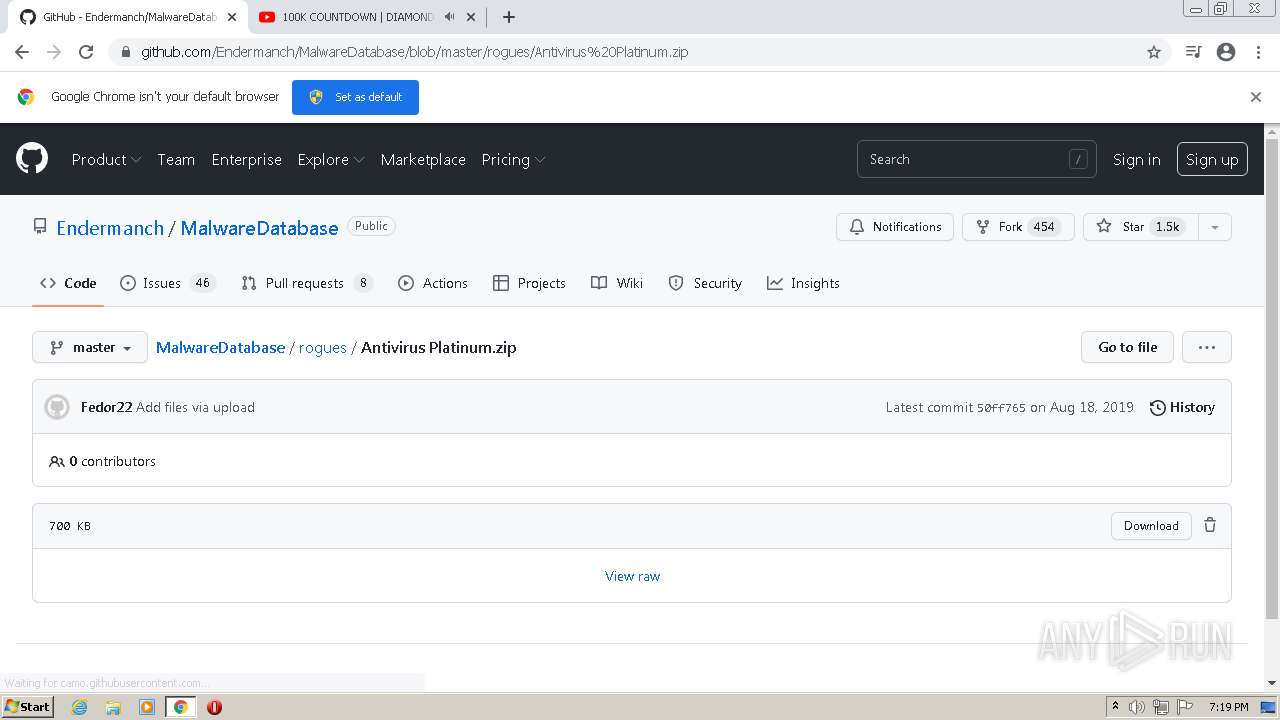
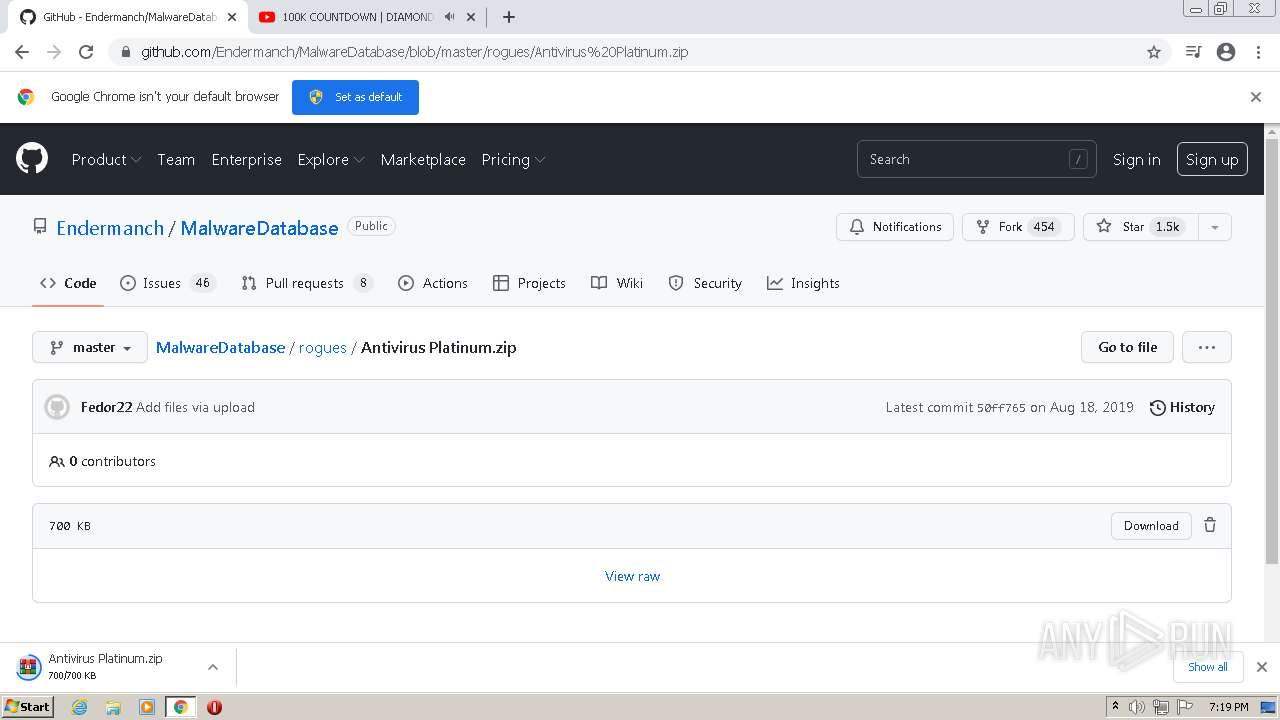
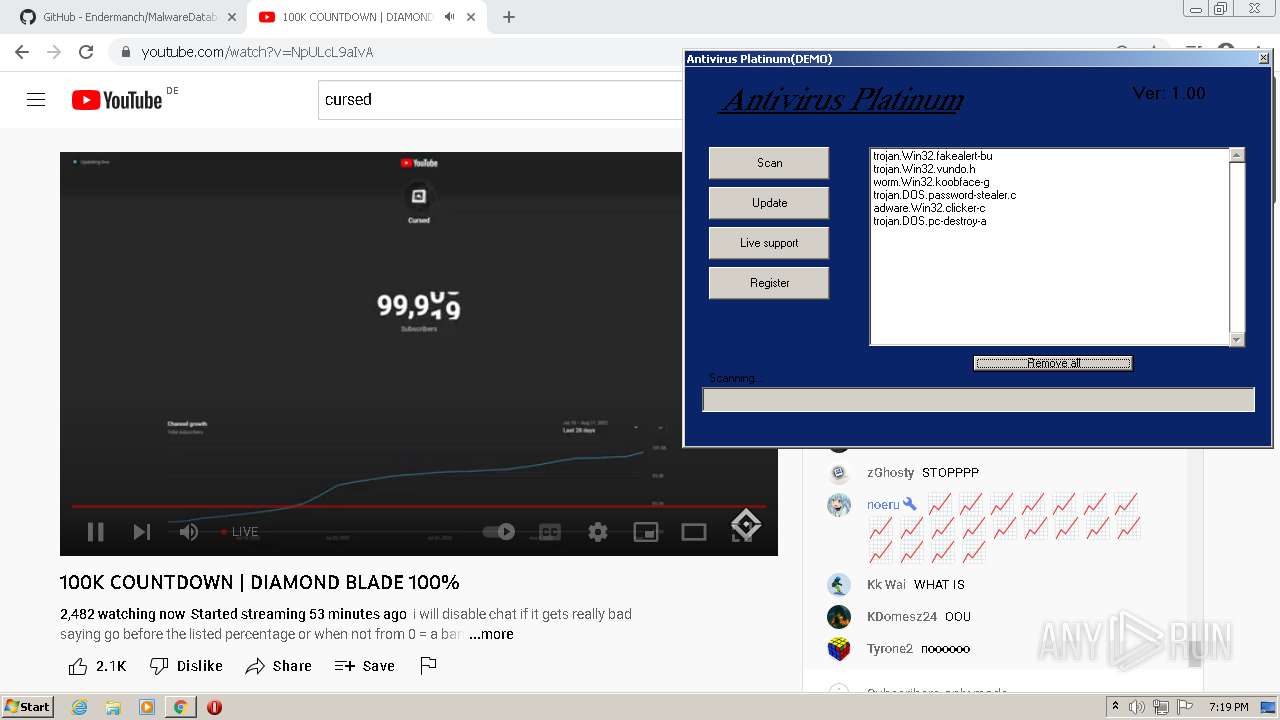
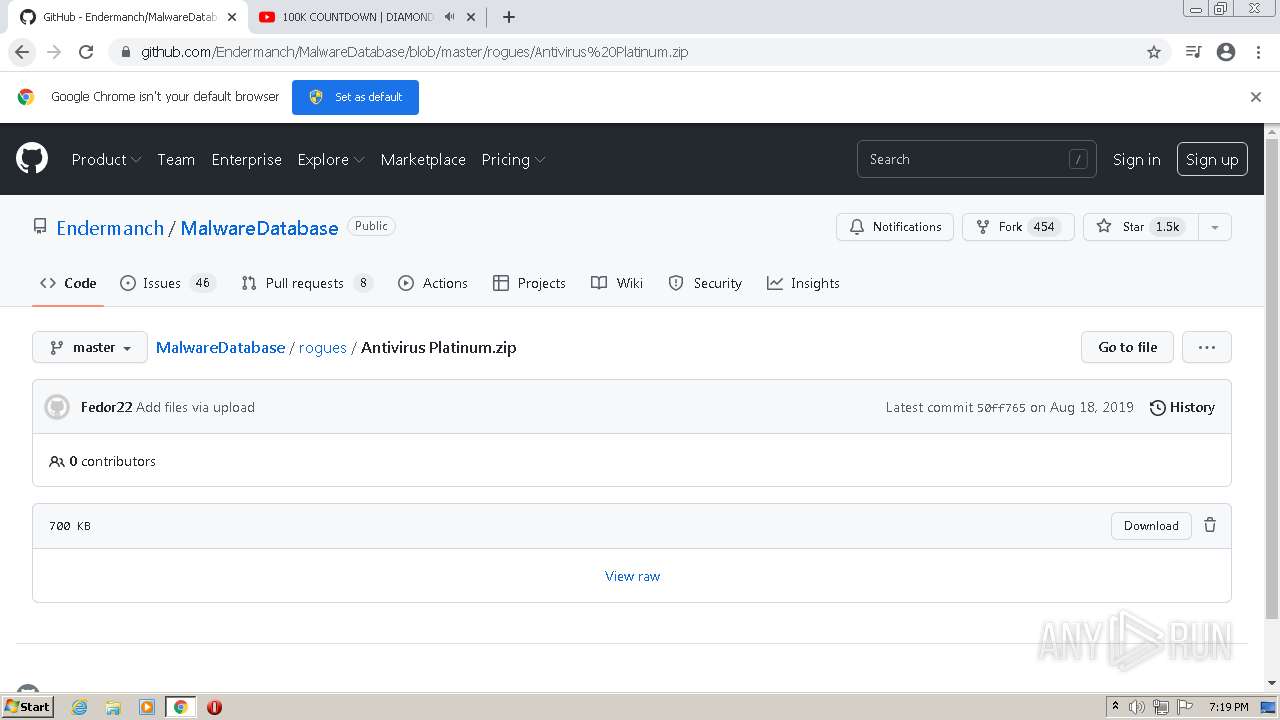
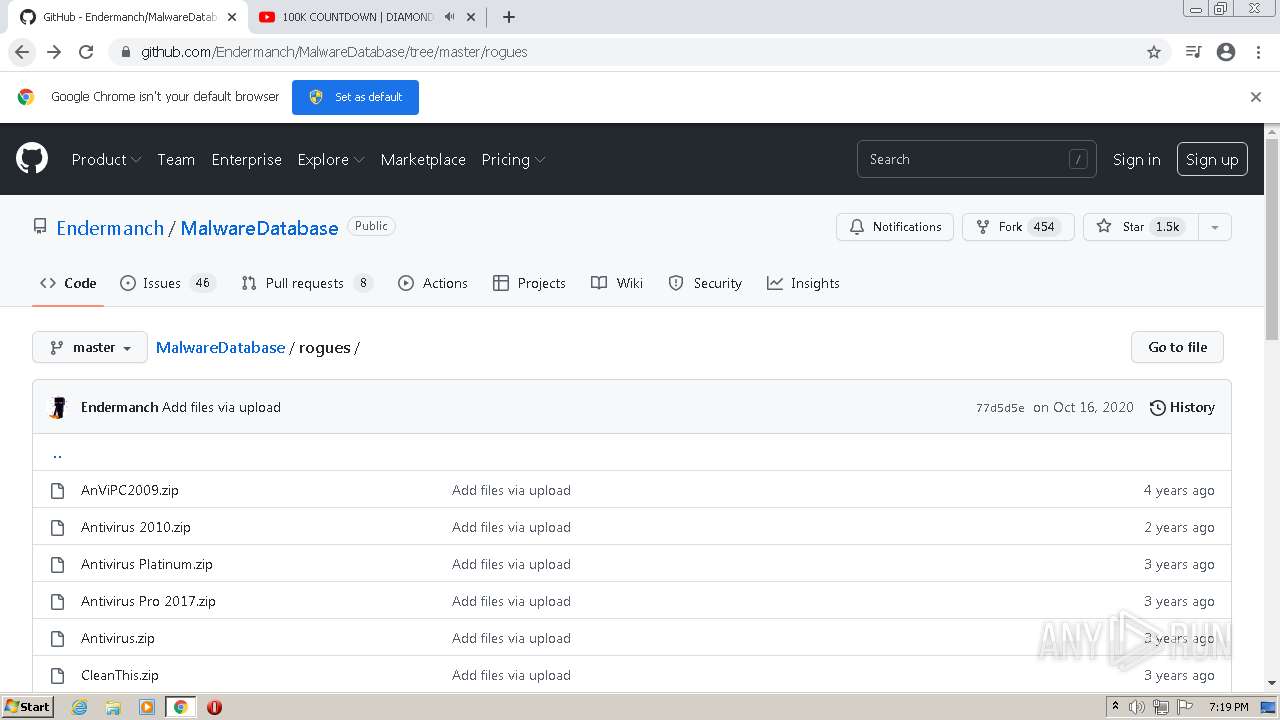
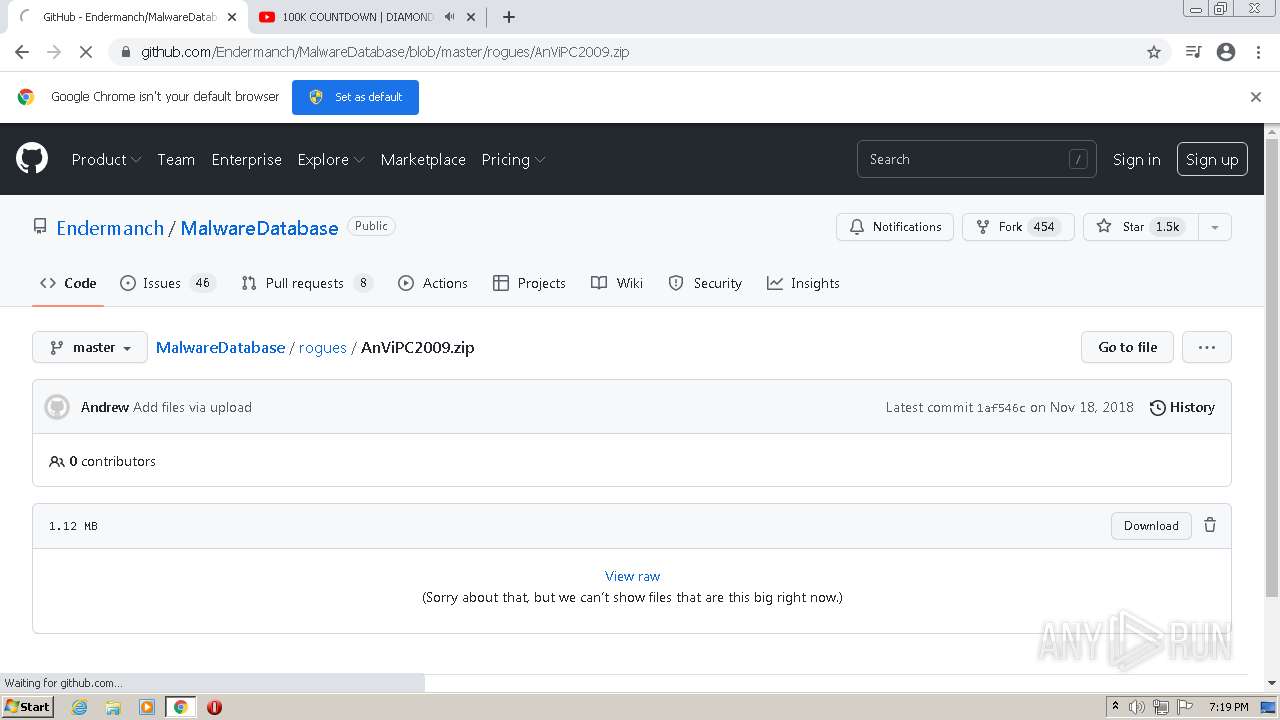
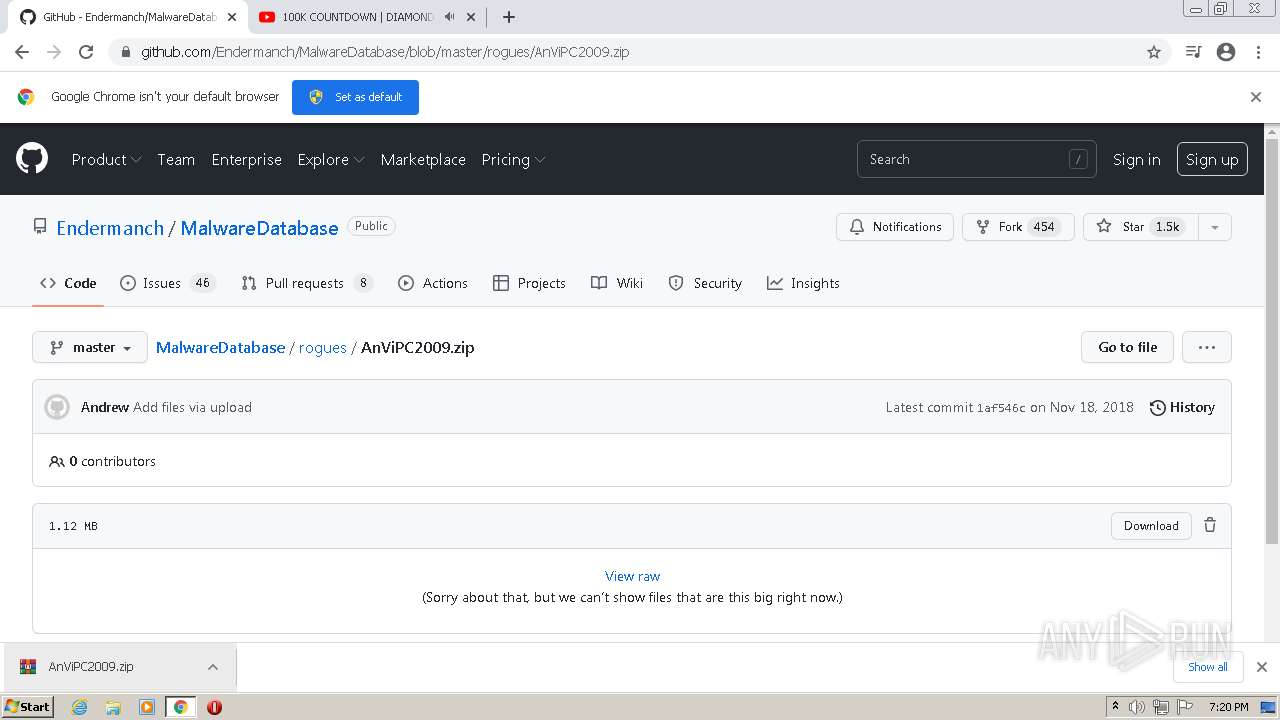
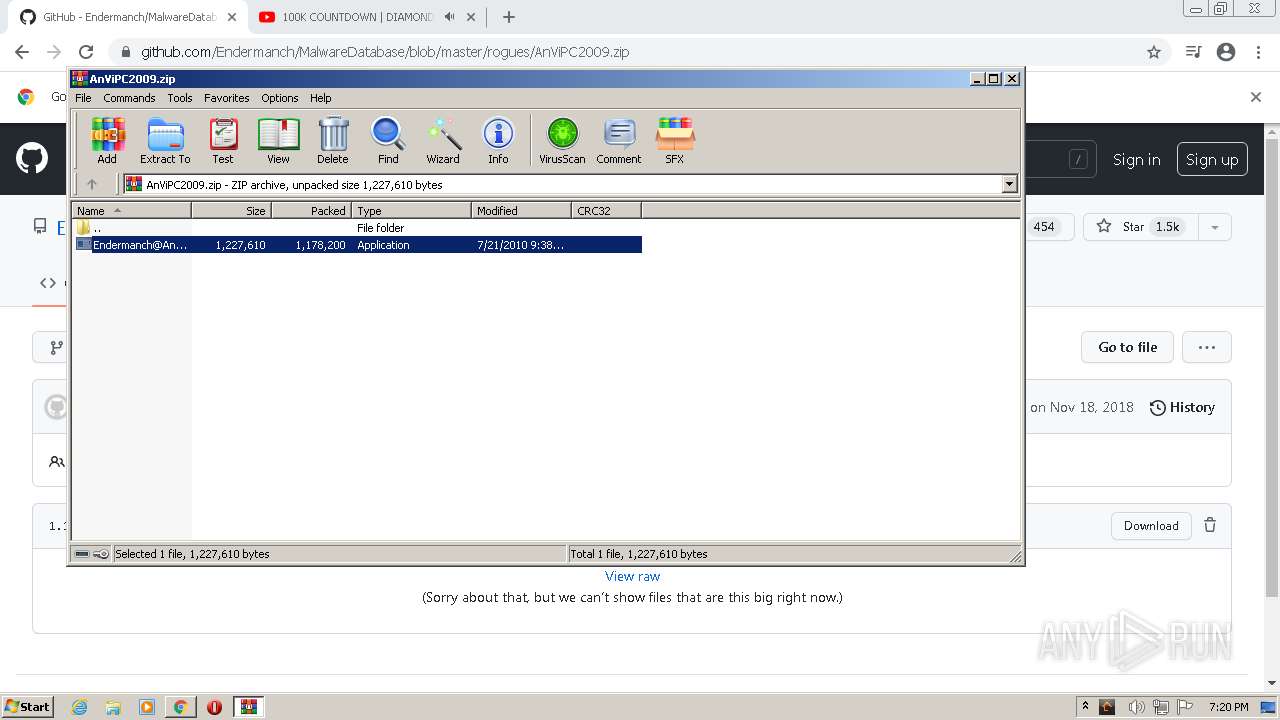
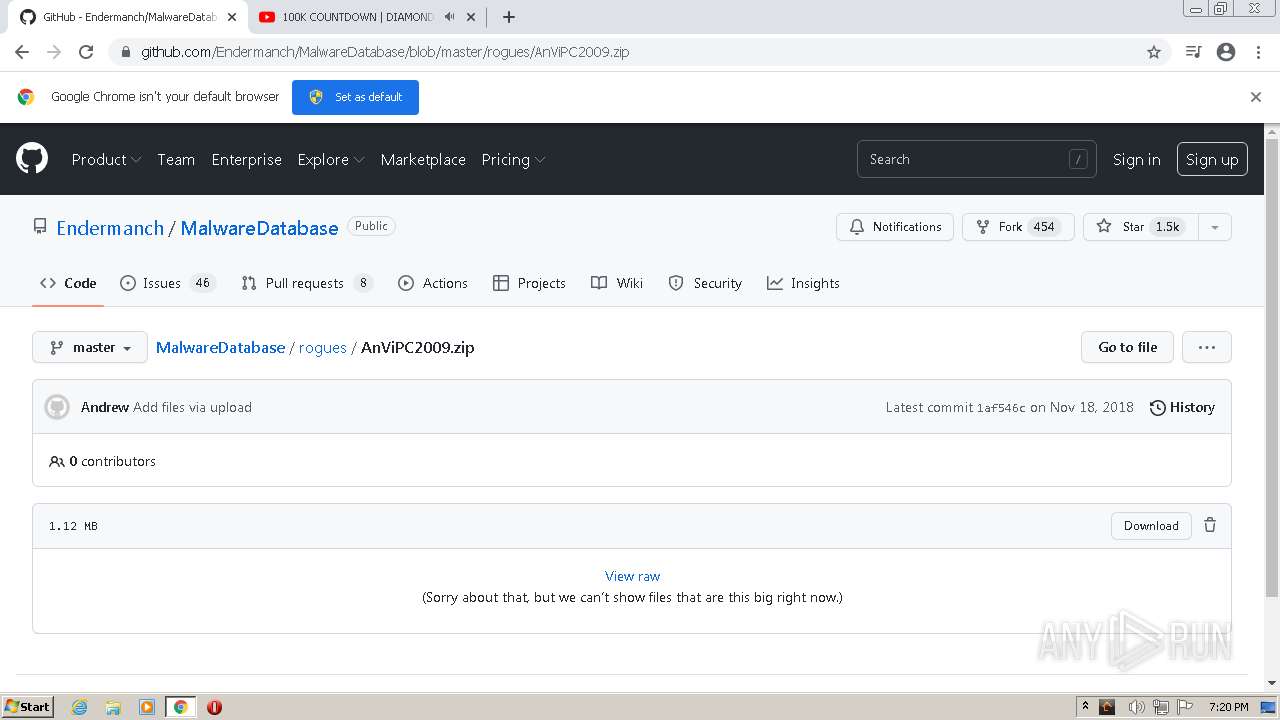
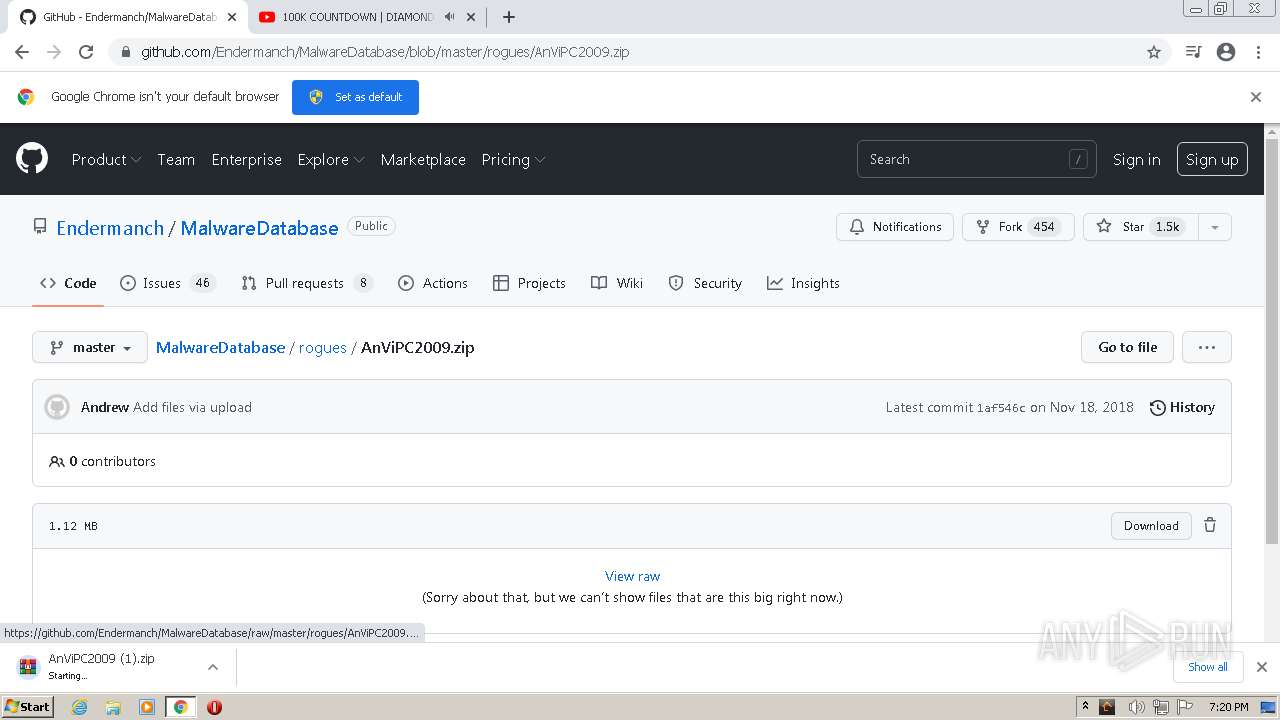
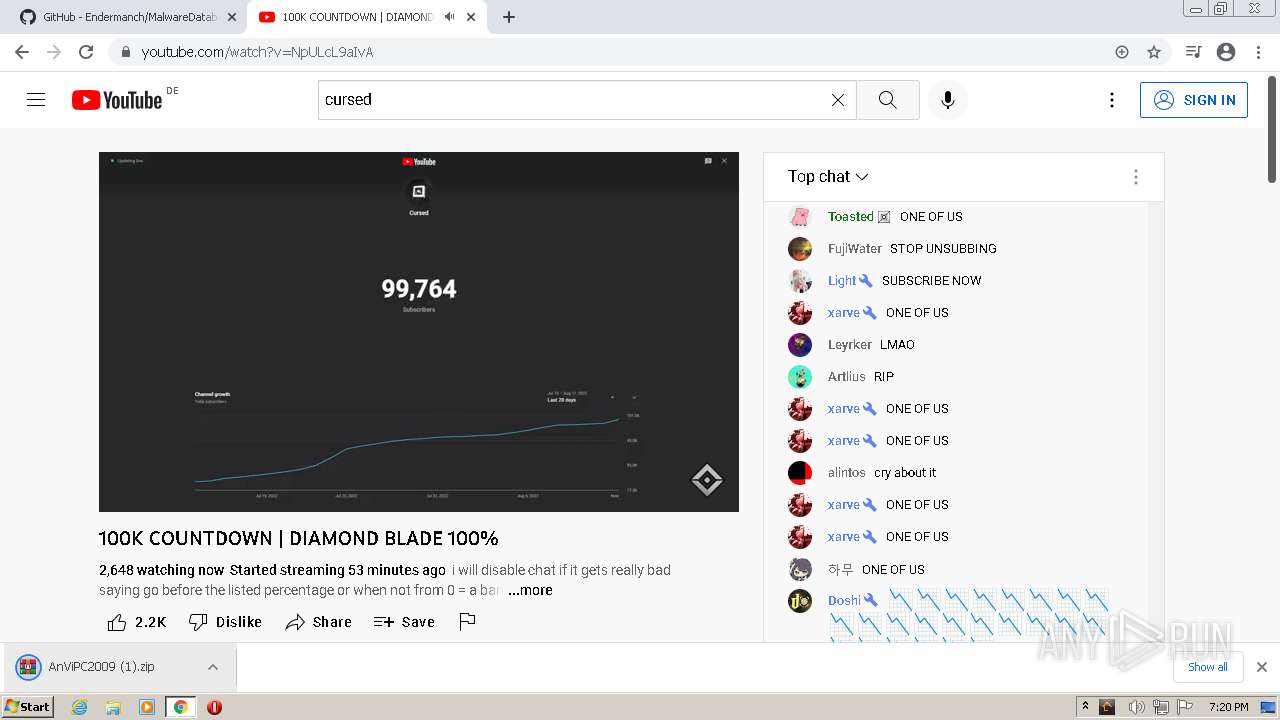
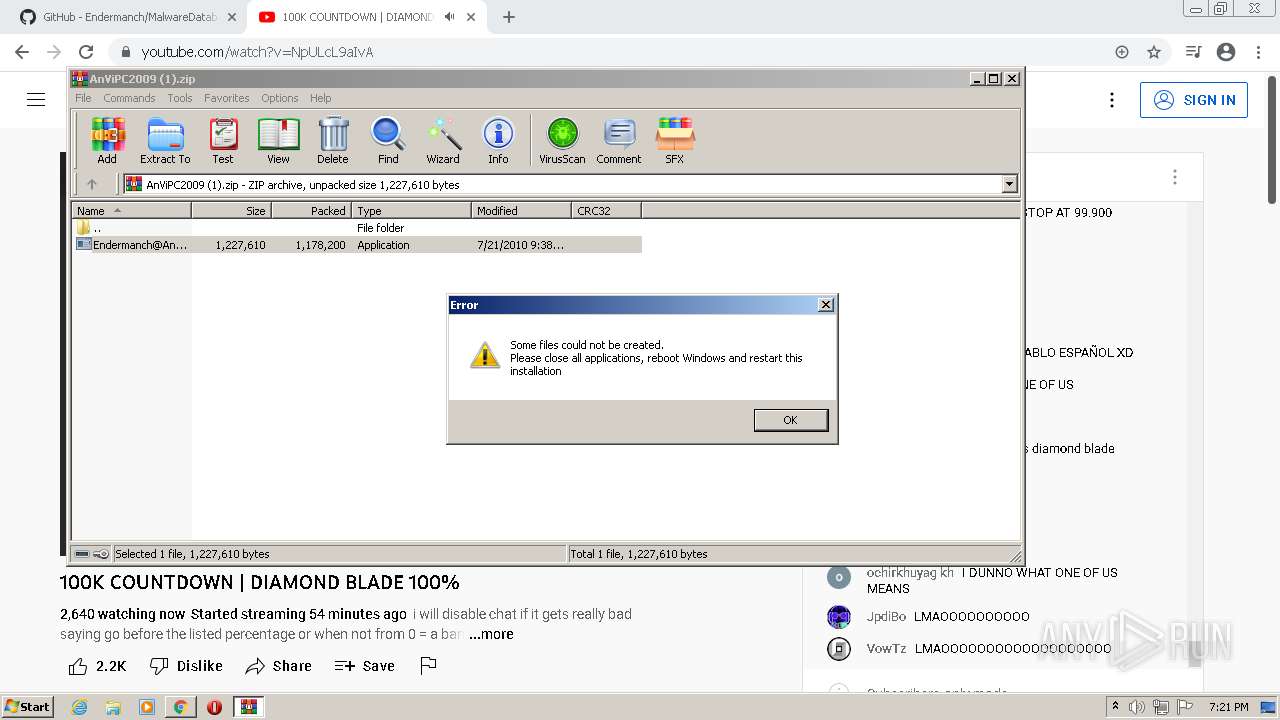
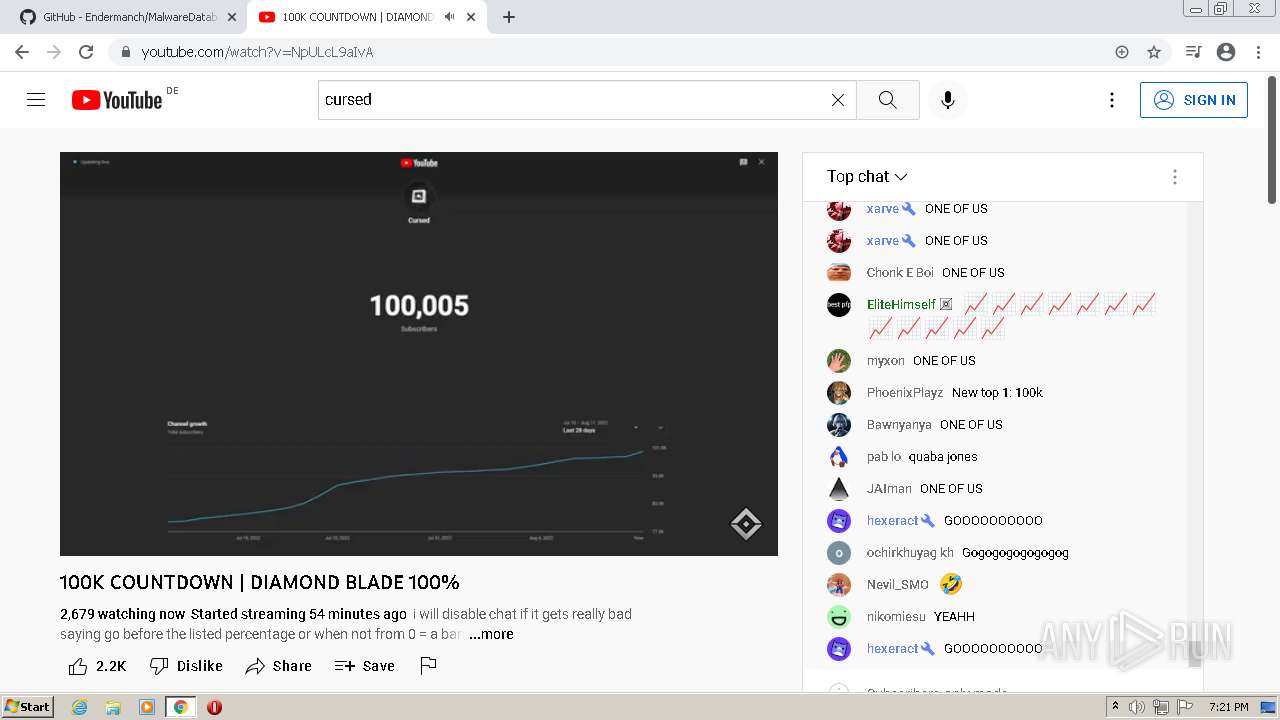
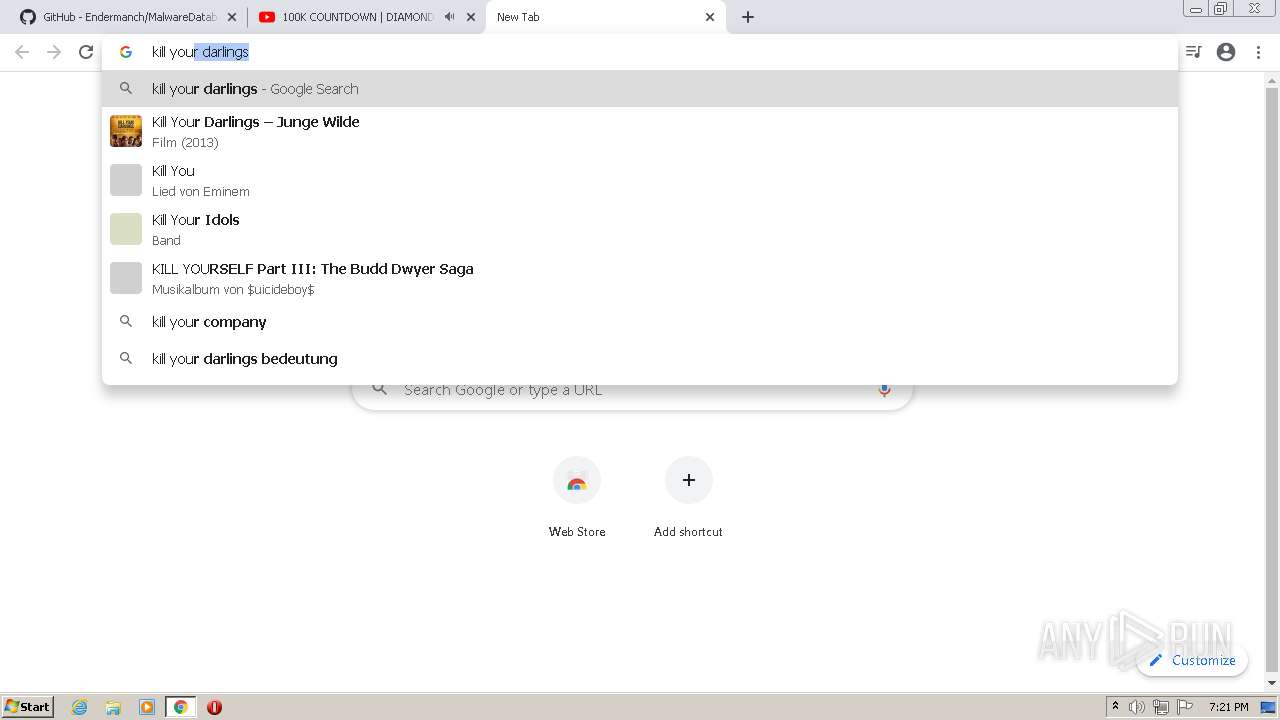
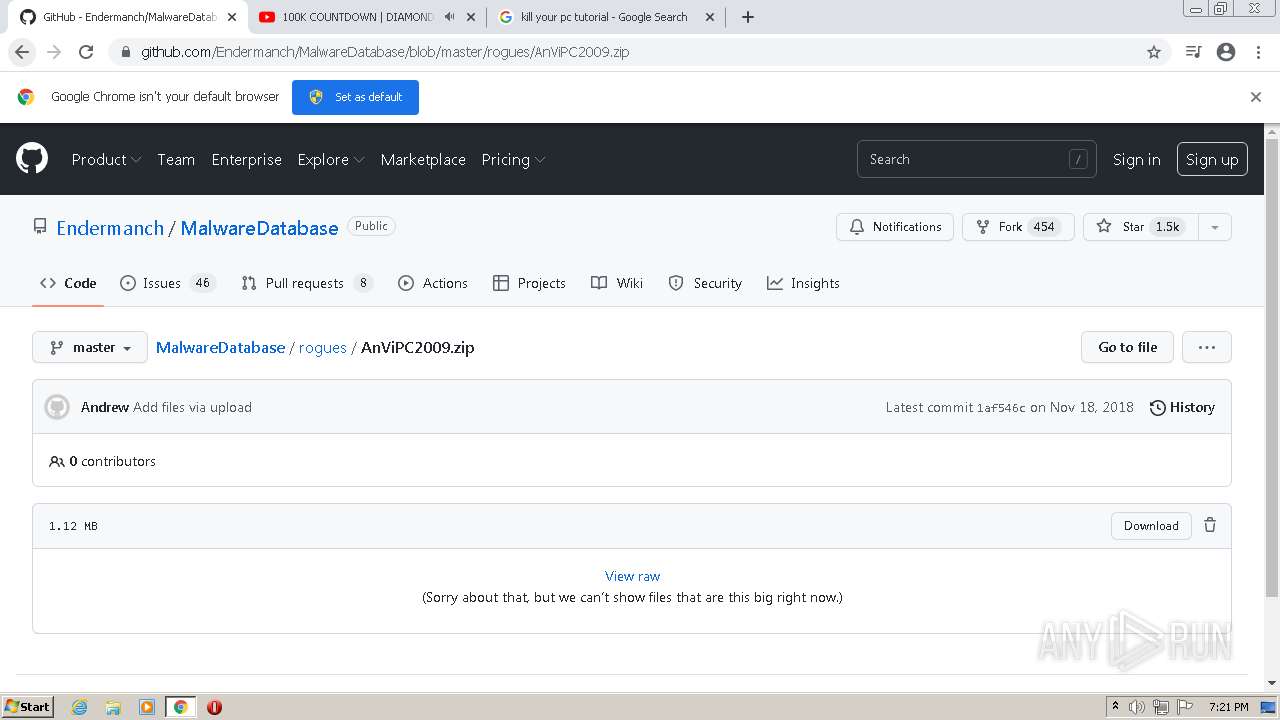
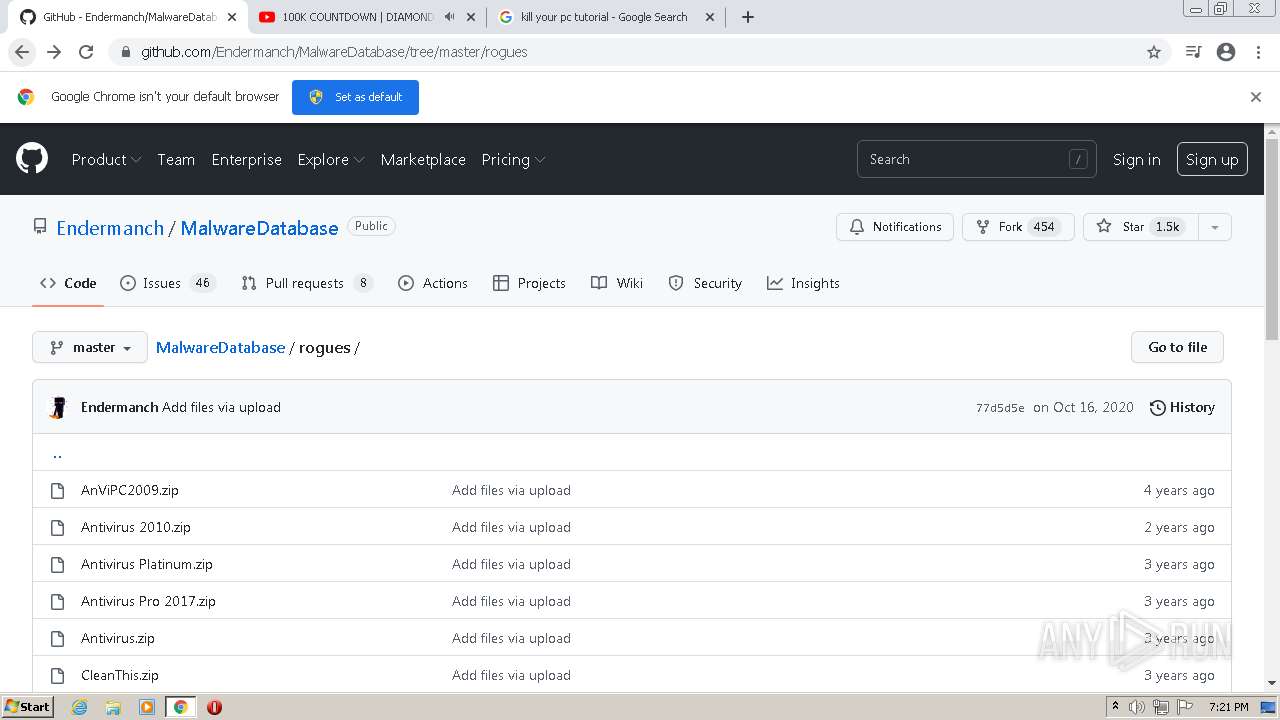
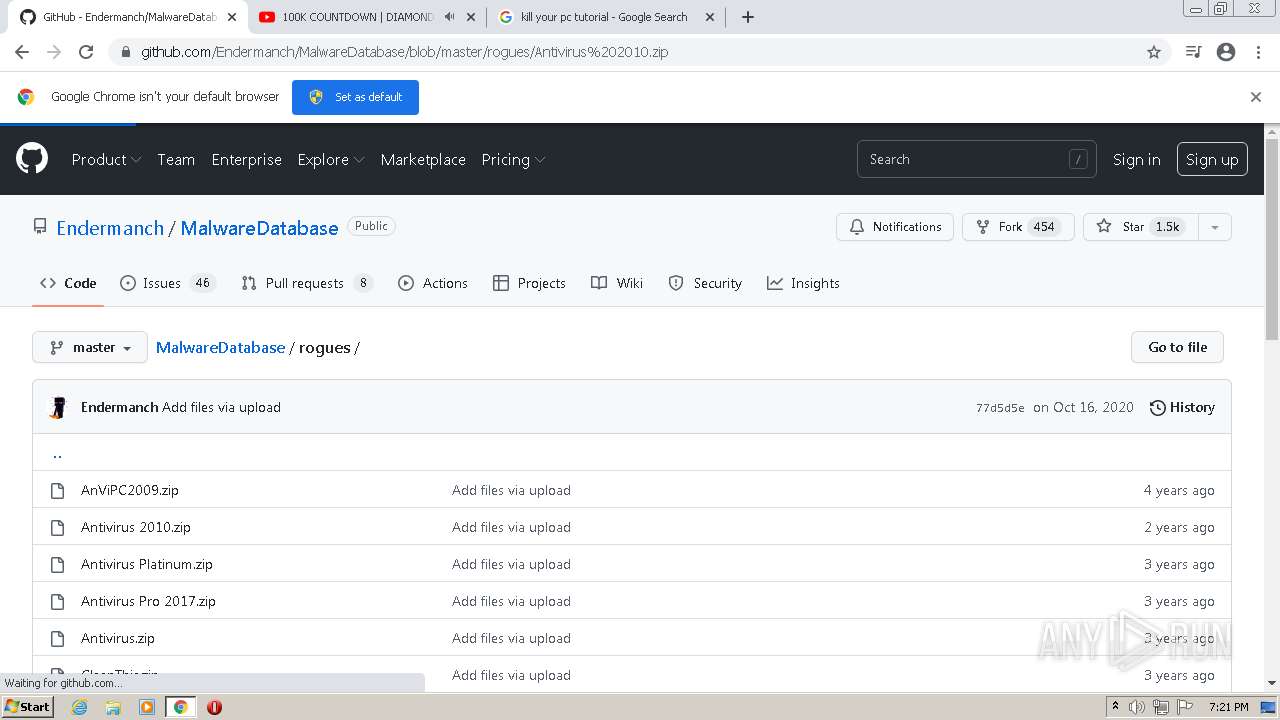
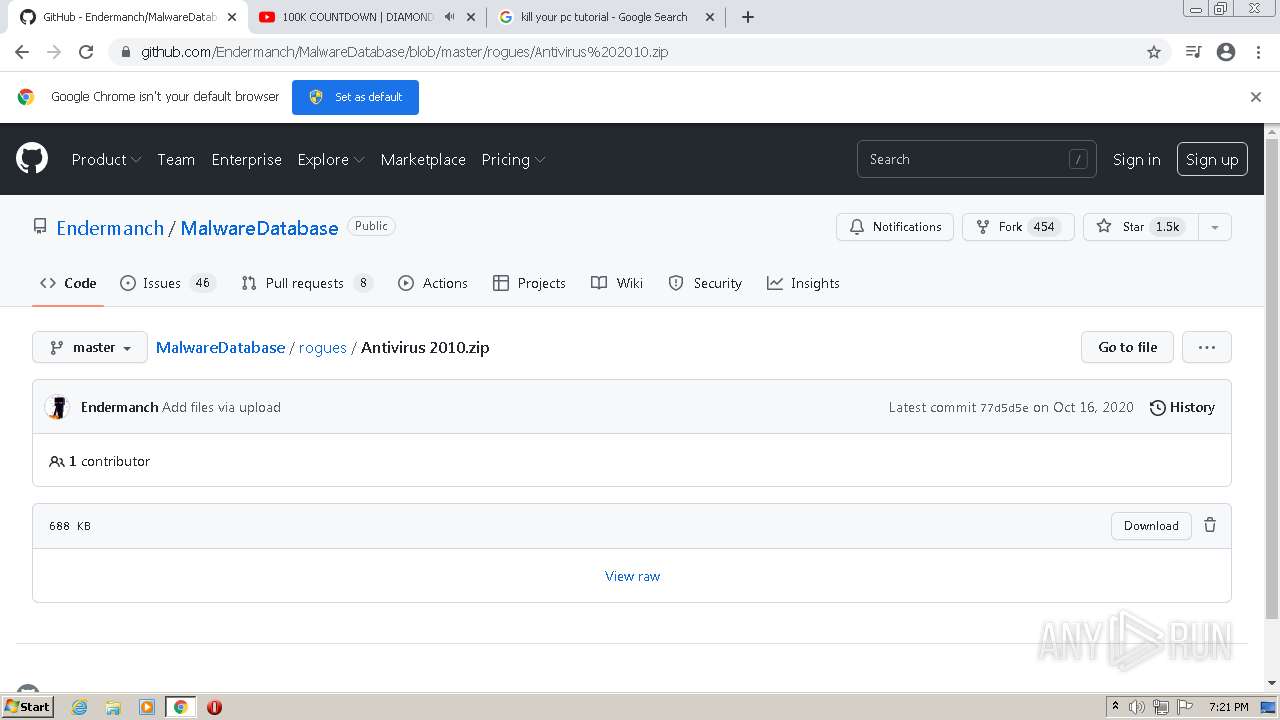
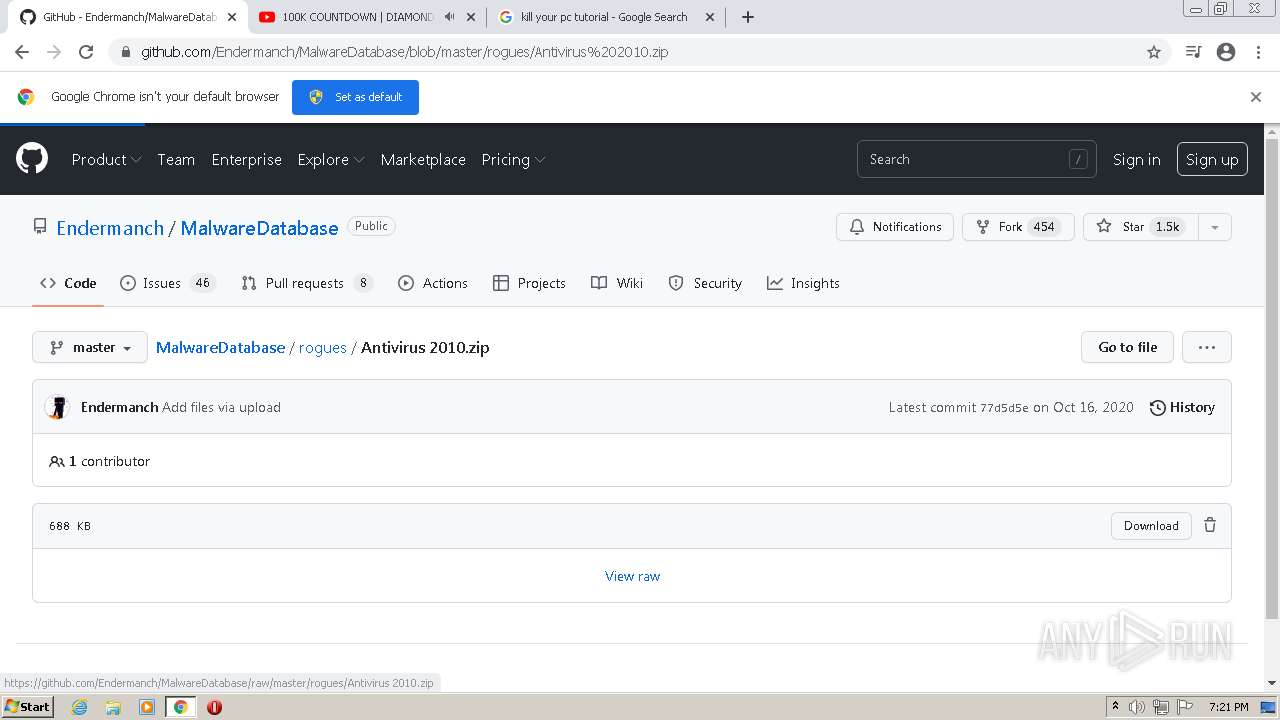
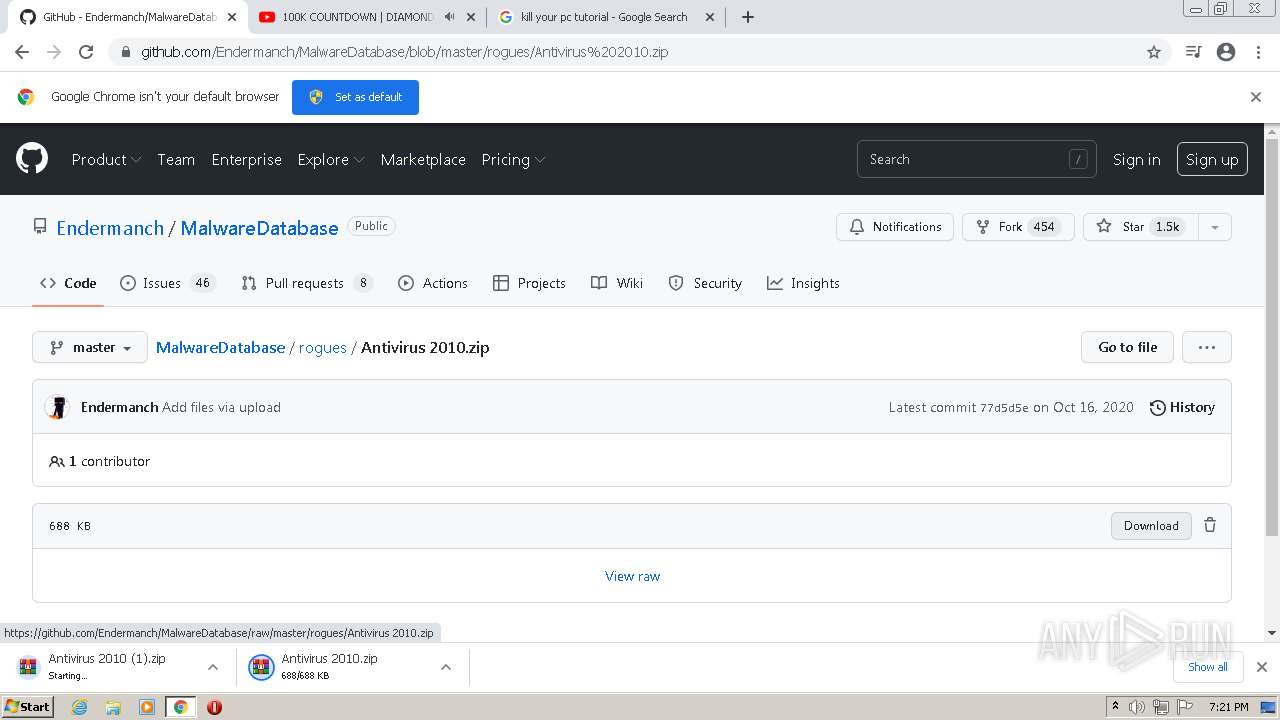
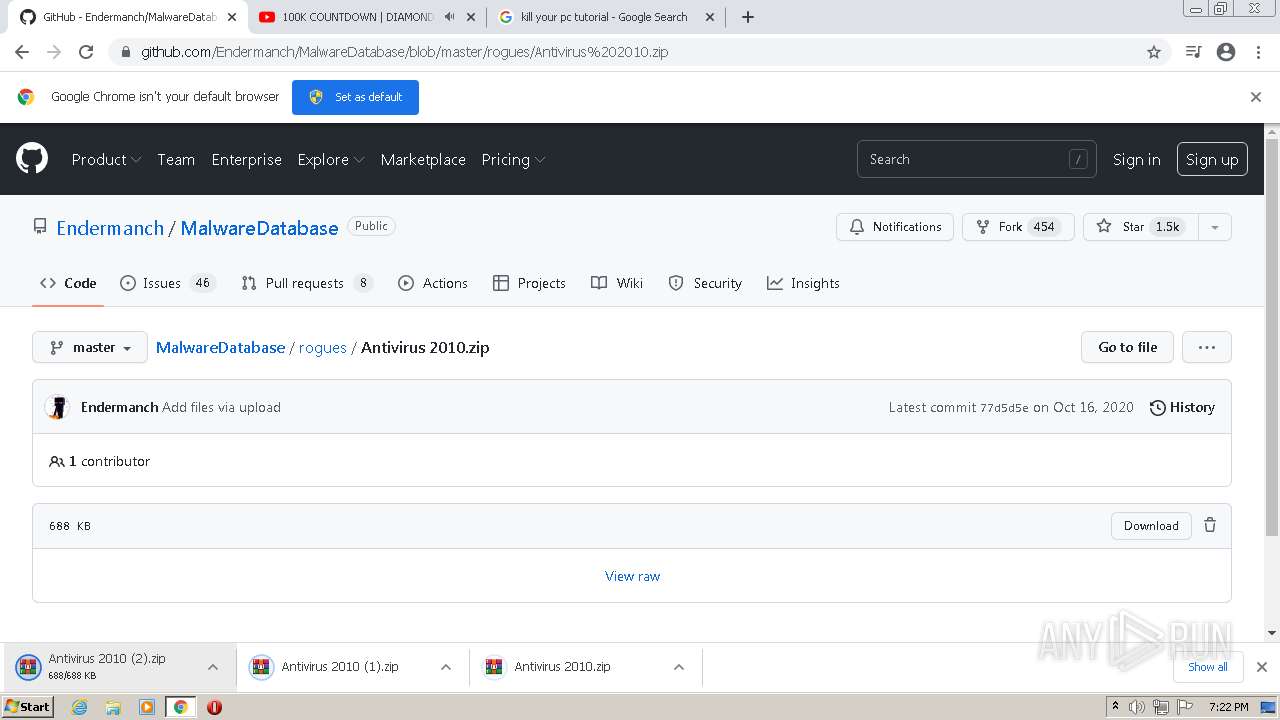
| URL: | https://github.com/Endermanch/MalwareDatabase |
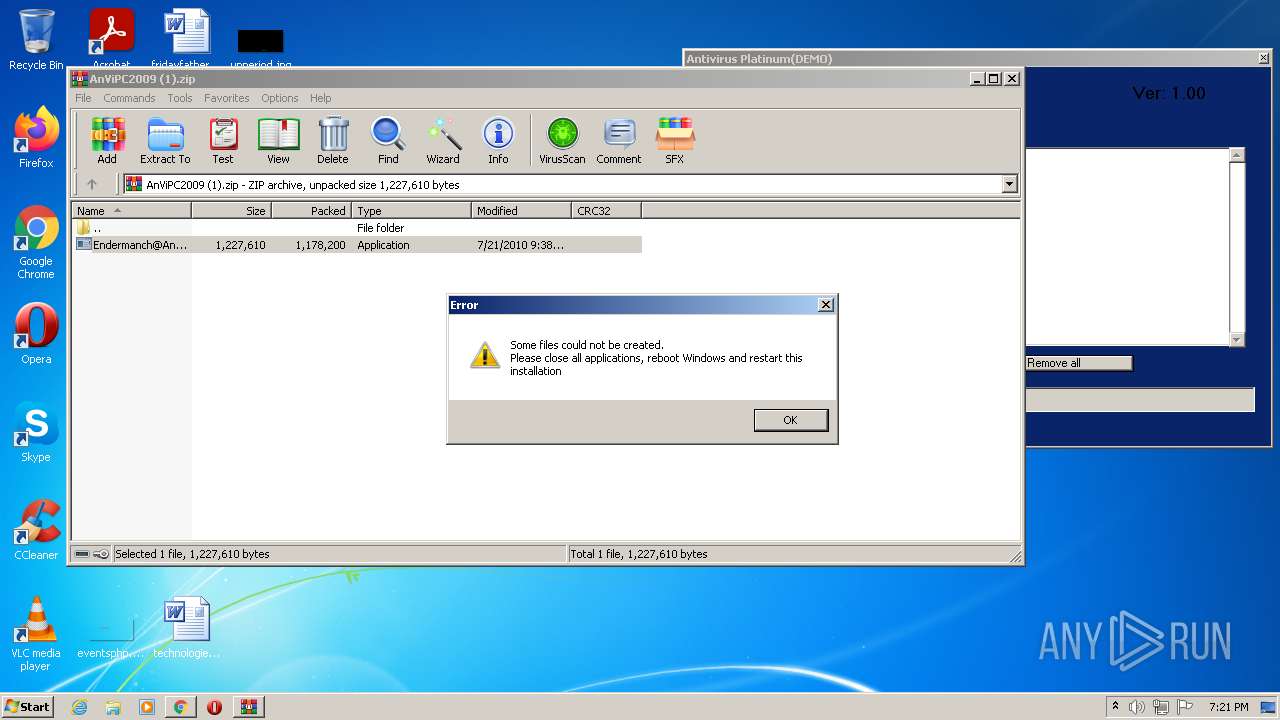
| Full analysis: | https://app.any.run/tasks/115b41d9-036f-4bab-ac36-495d29c876b5 |
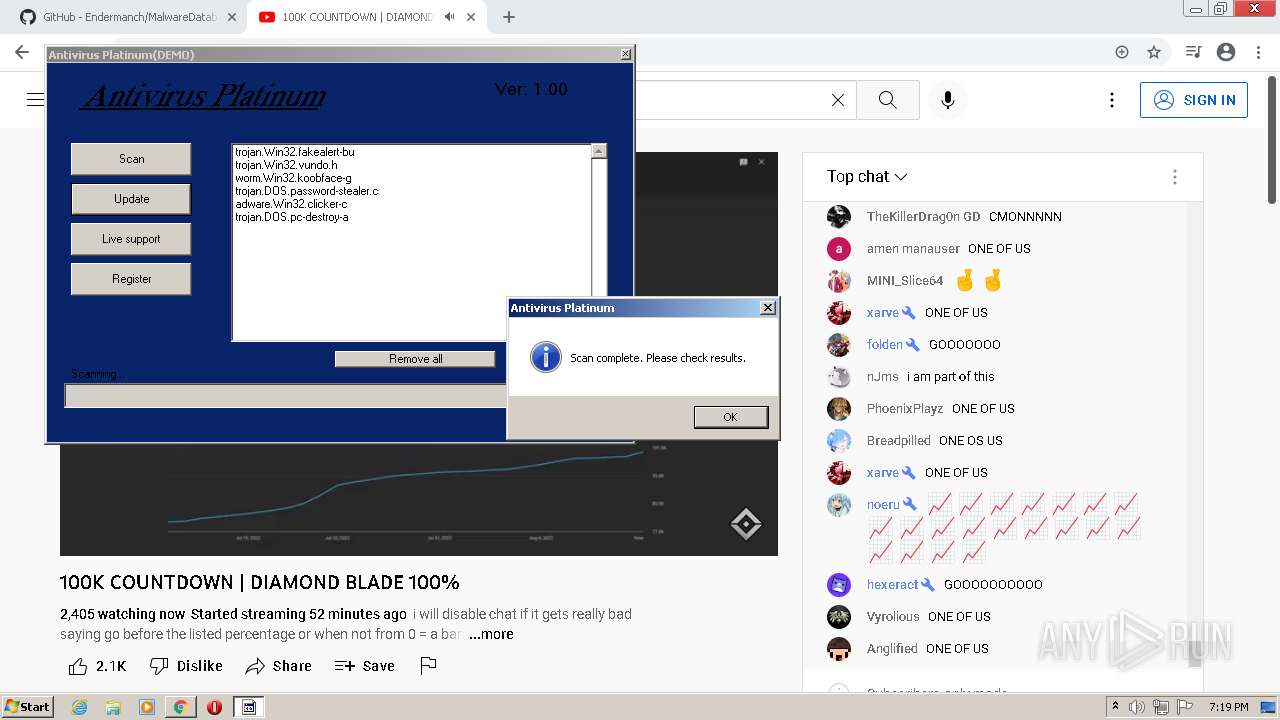
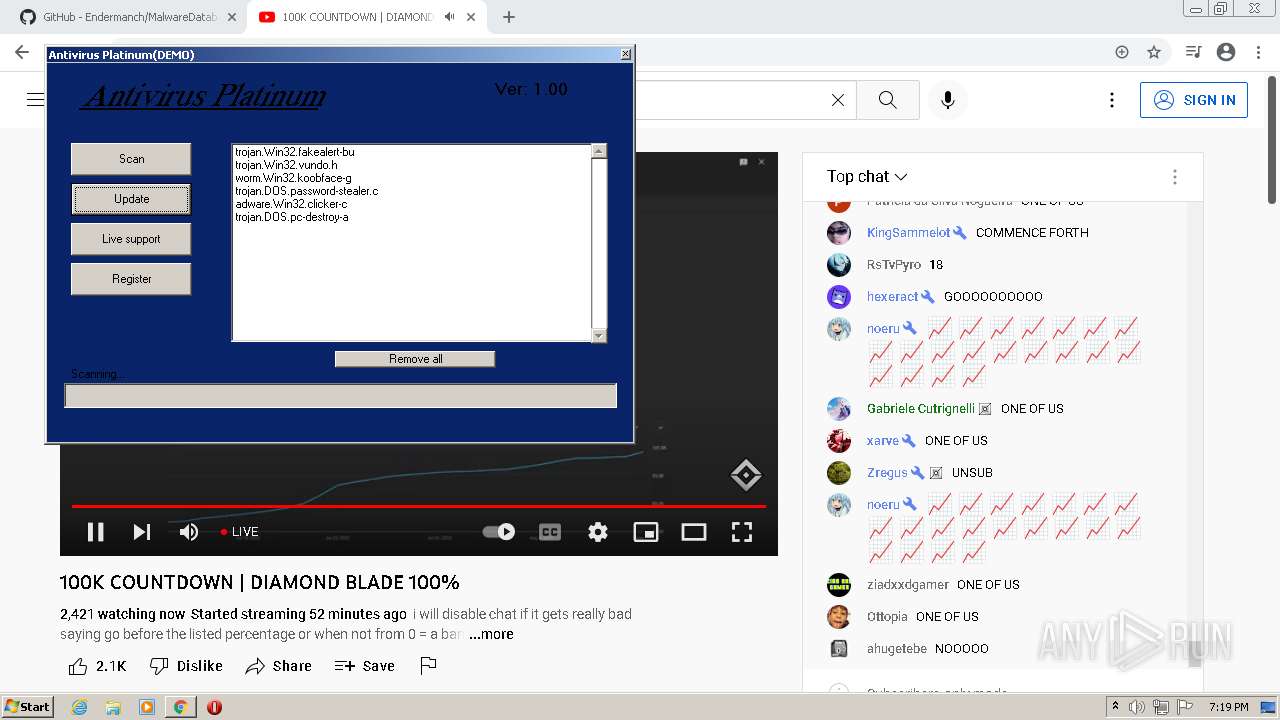
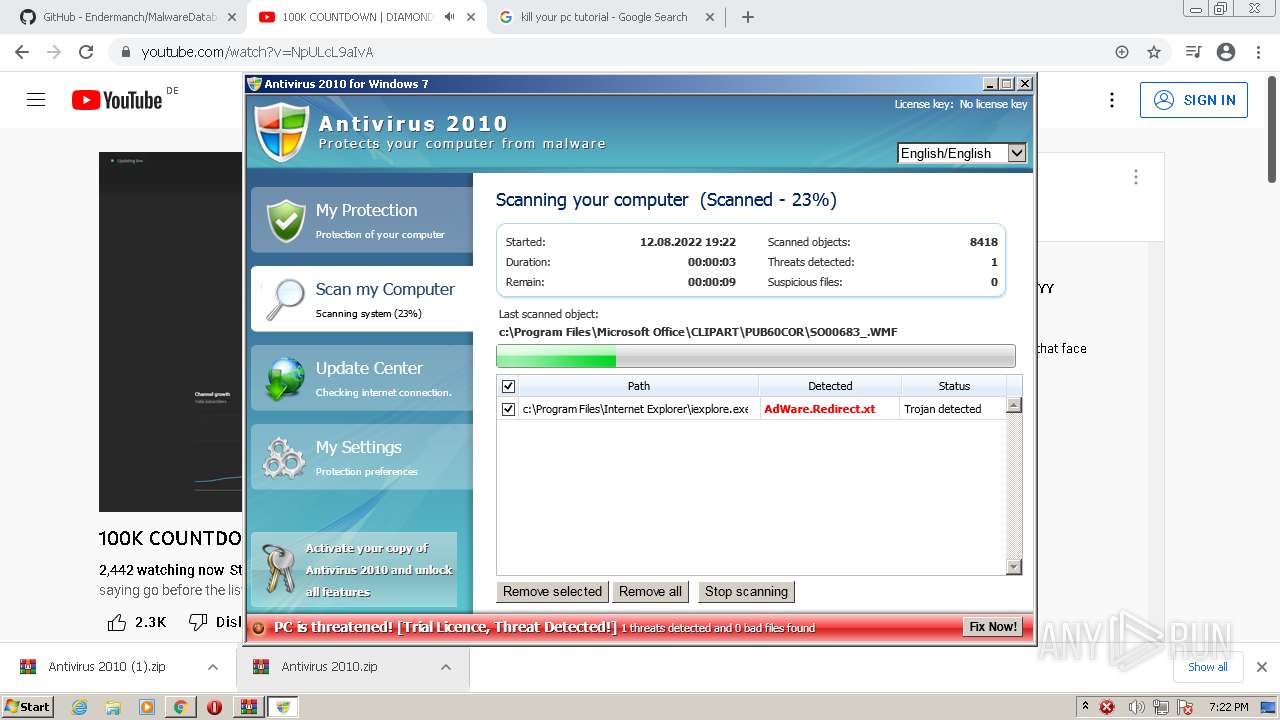
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 18:17:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
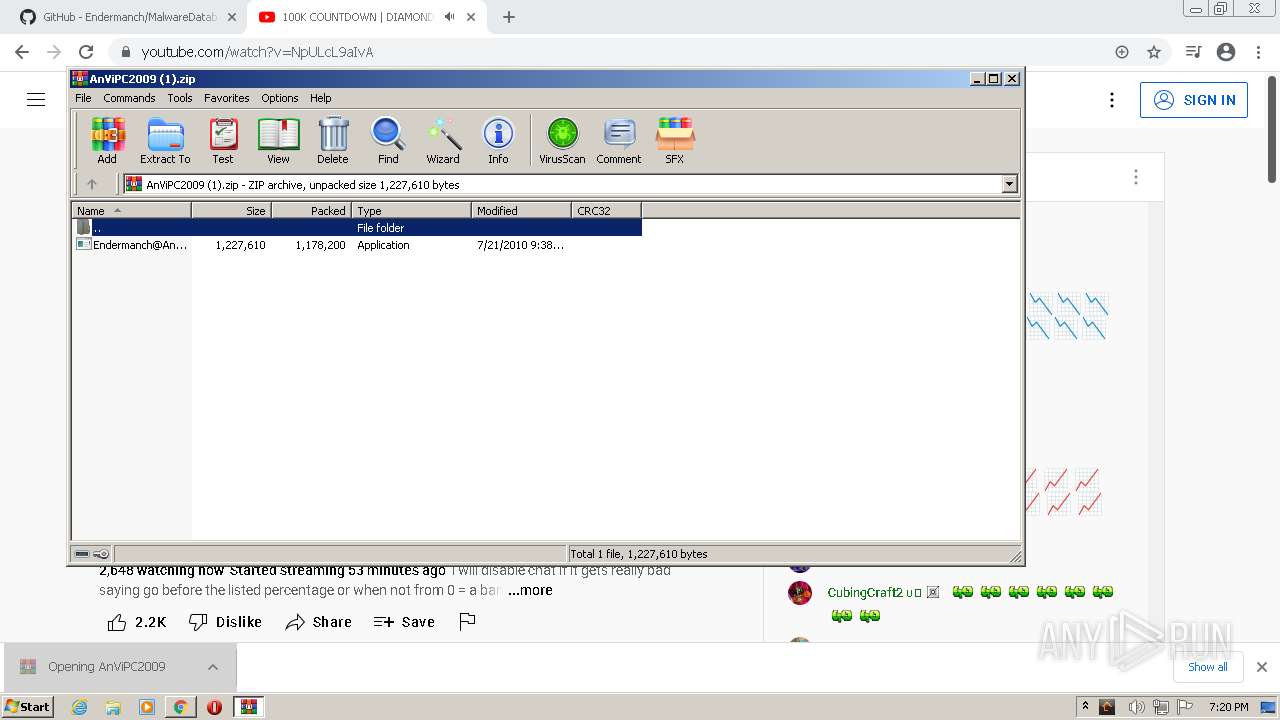
| MD5: | 1852BA87DF67DC59ABFA19966A746E94 |
| SHA1: | 2EF1EEE649E3806D5C375A9424EAB9435504EEE6 |
| SHA256: | DBCE5ACC6561CFA49FB550B9FAC71AA99784ECCF5F442071CAD162C151918452 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PH:2ufLtfH |
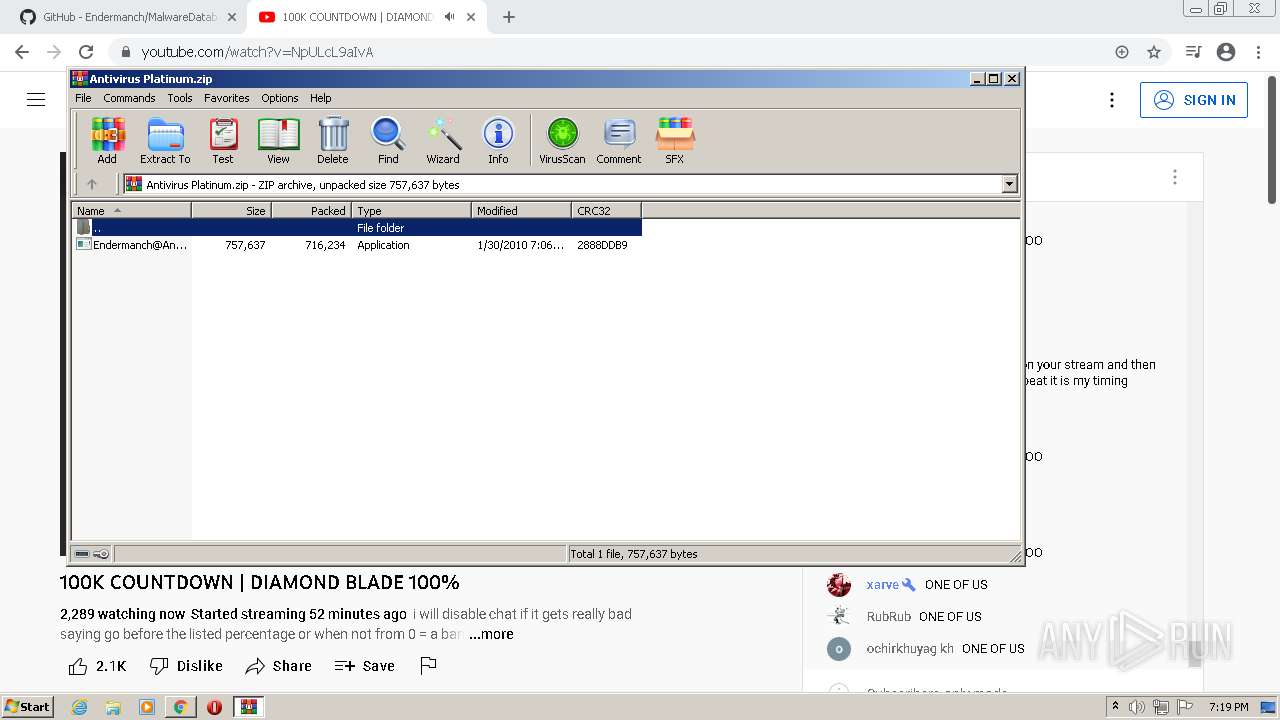
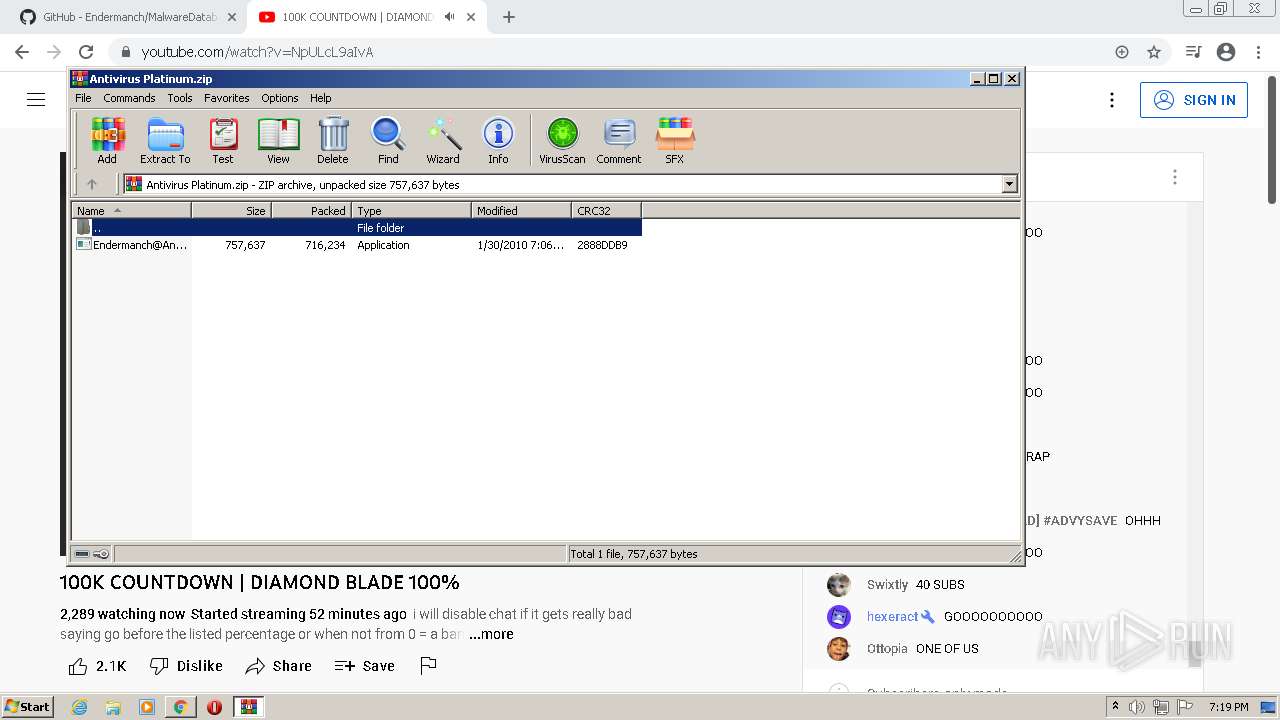
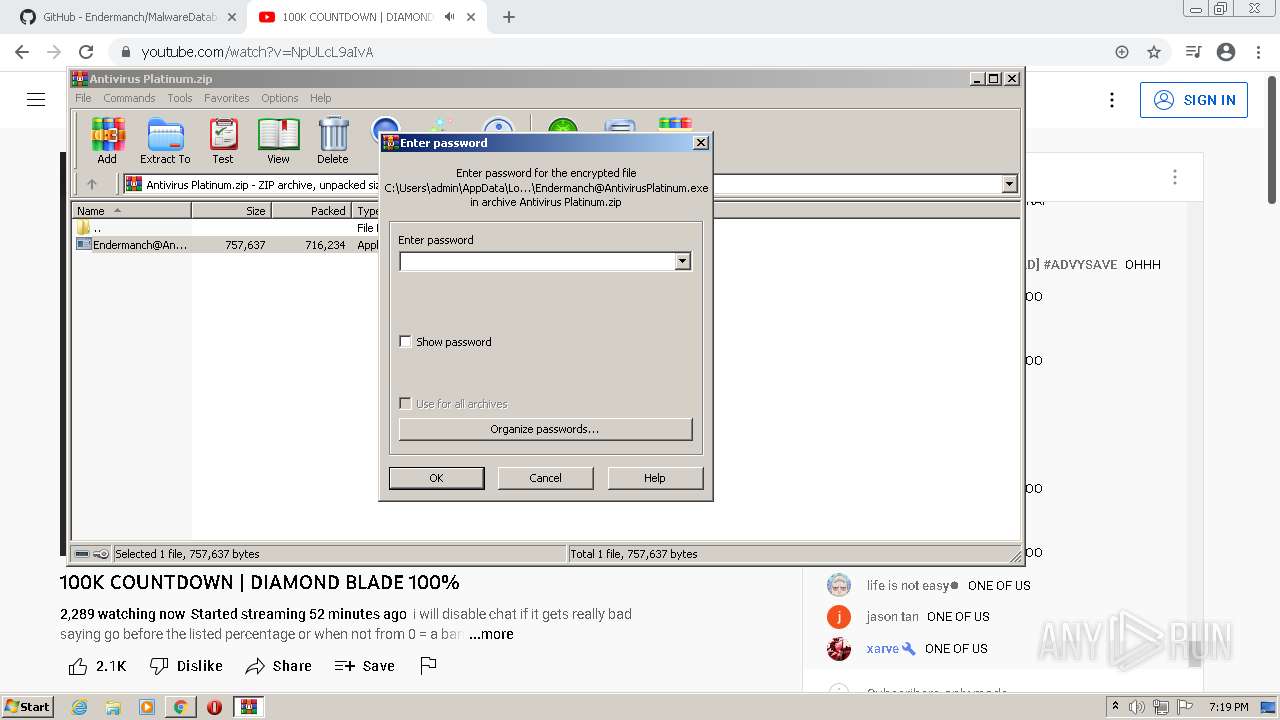
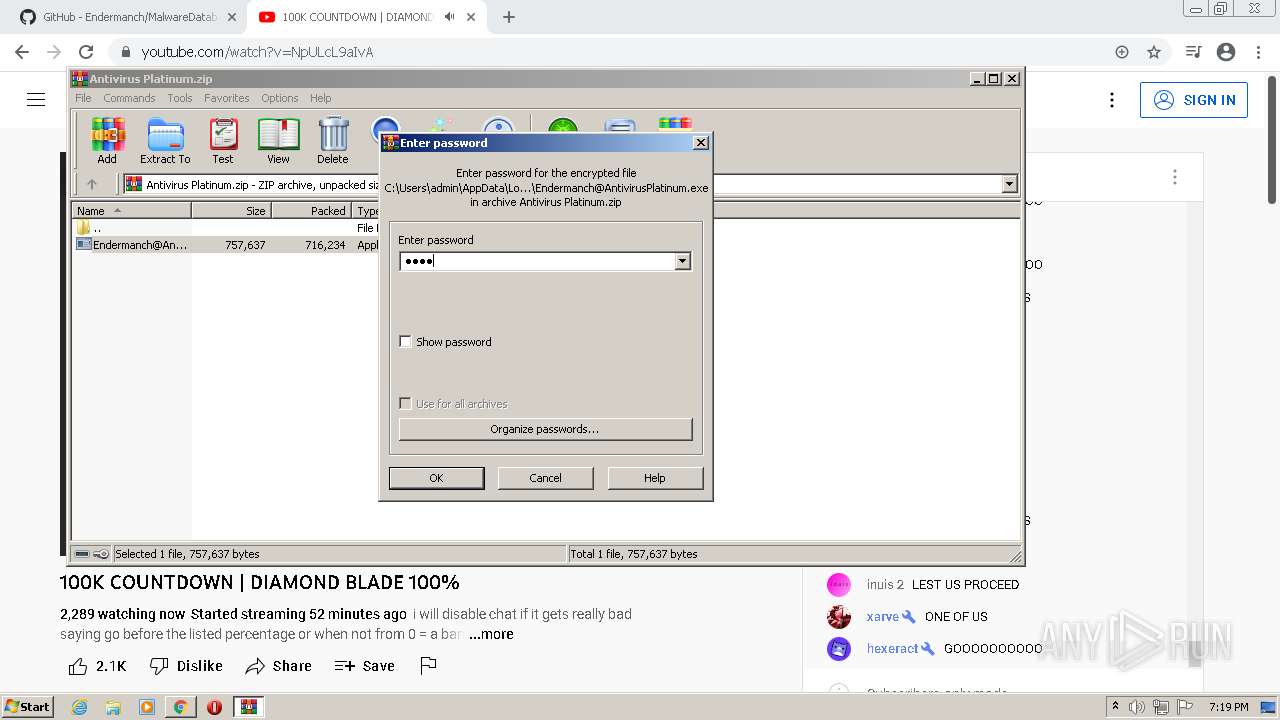
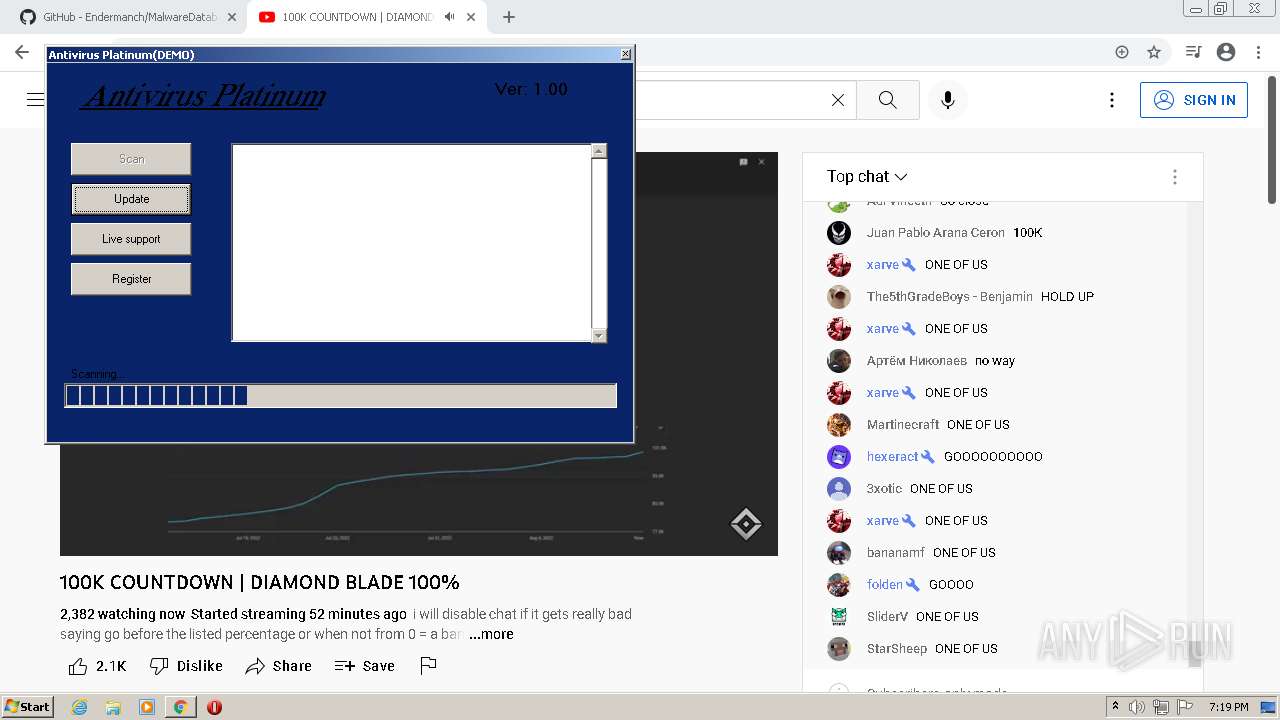
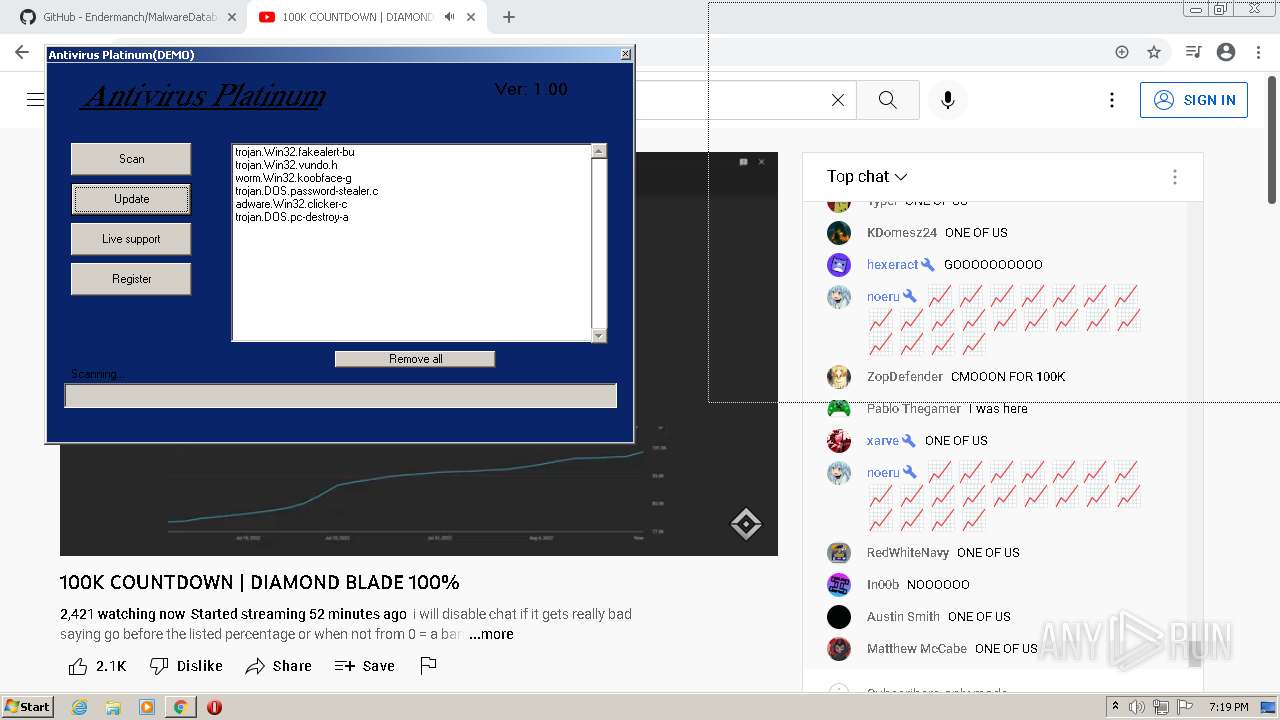
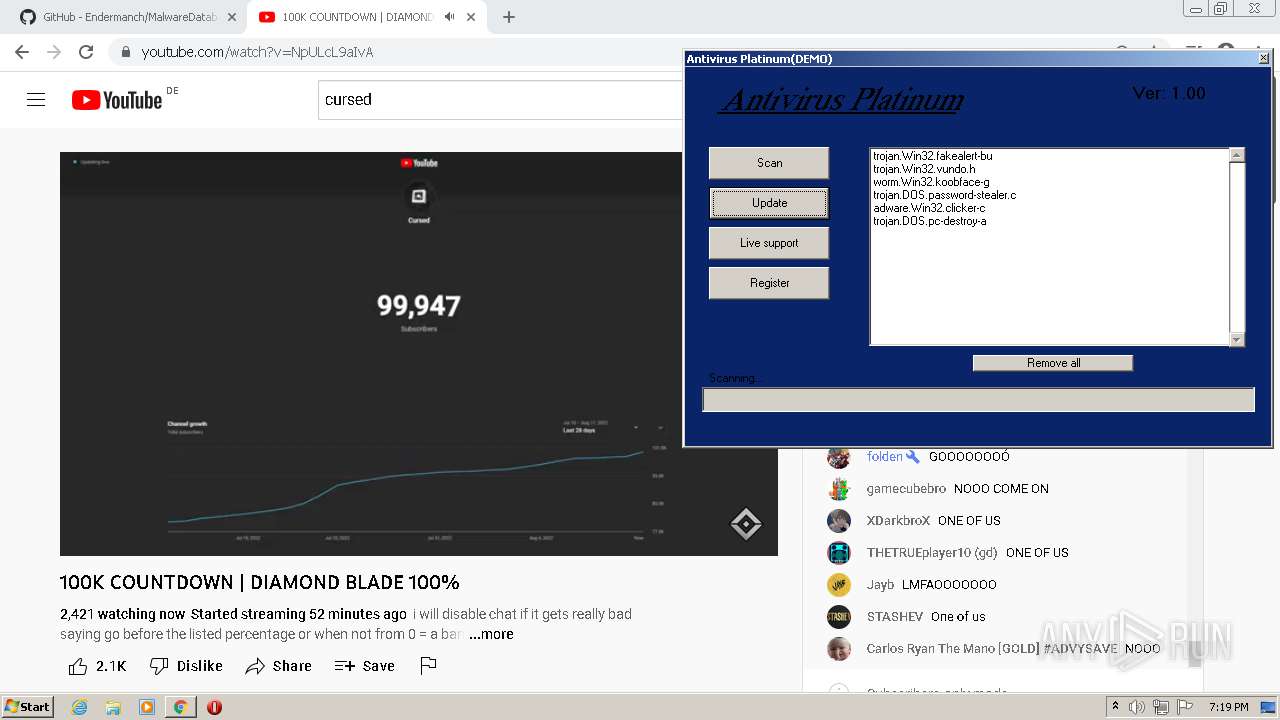
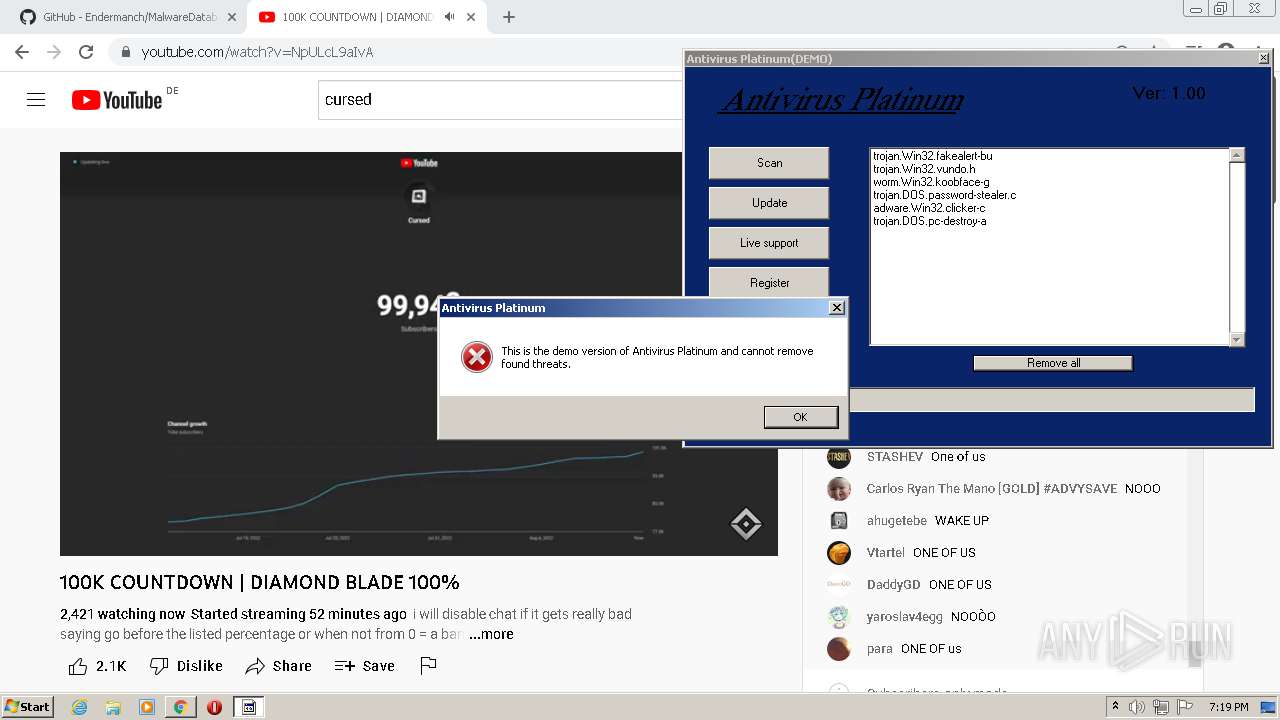
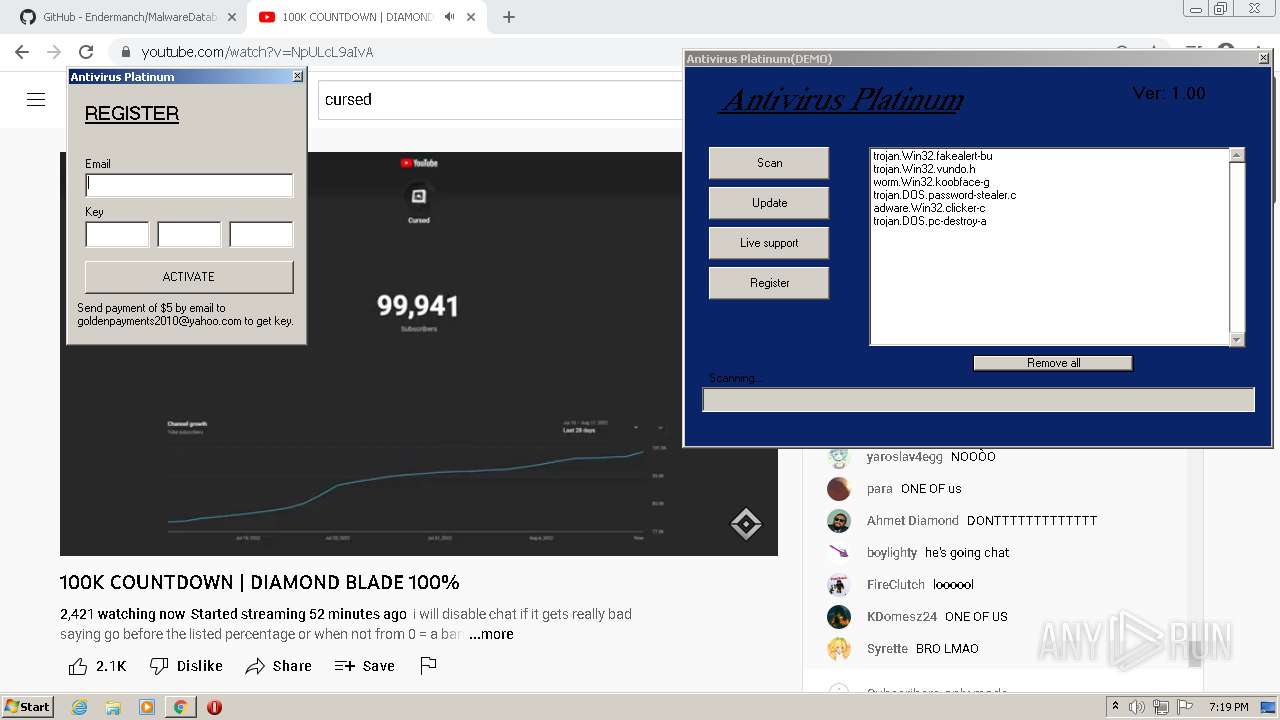
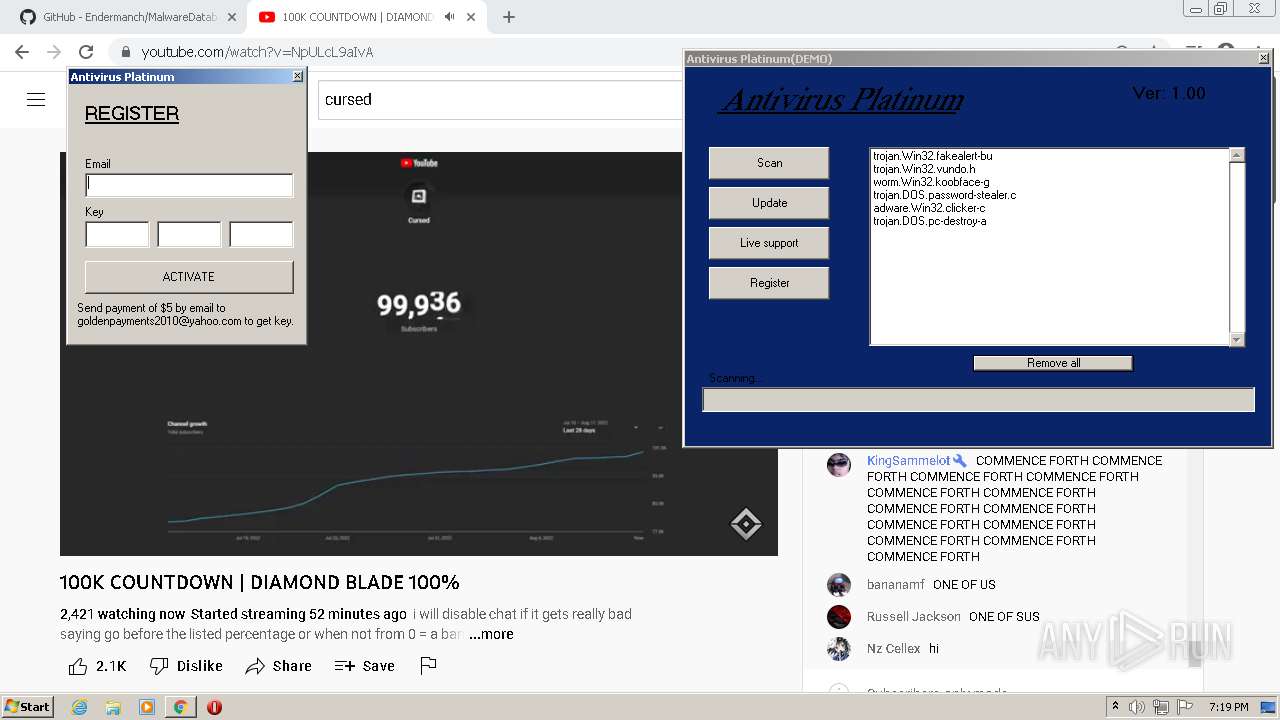
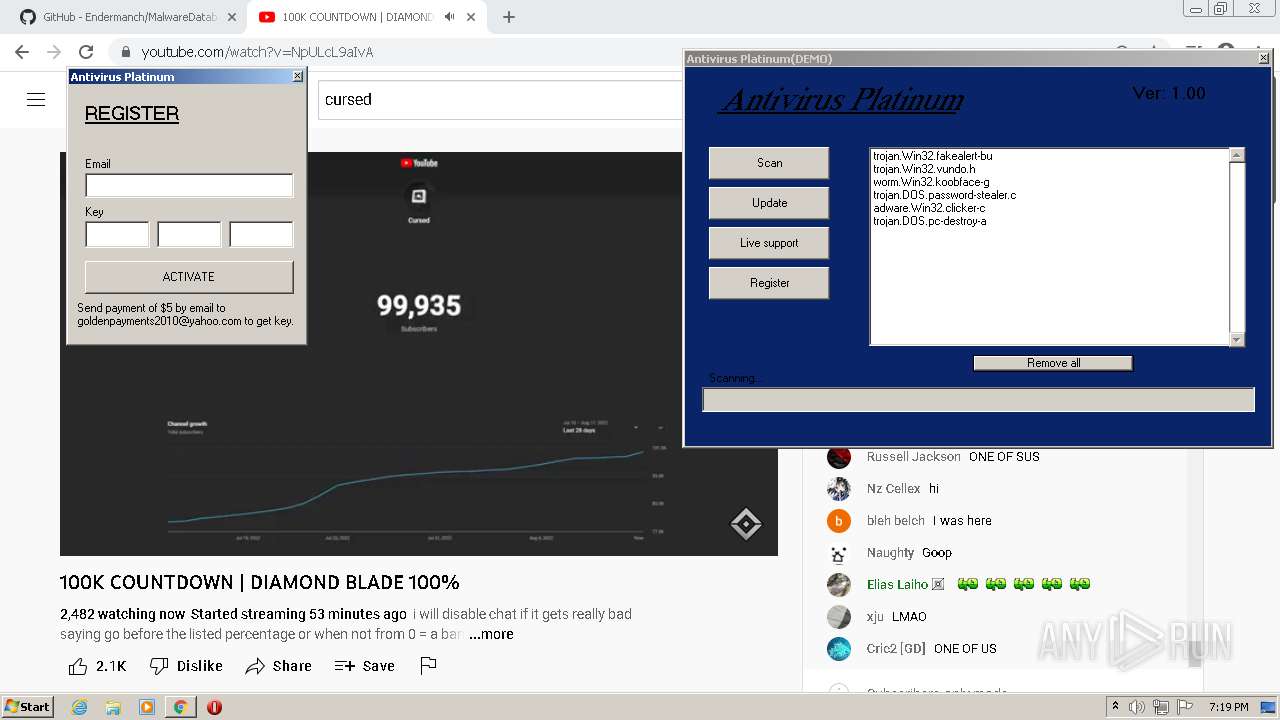
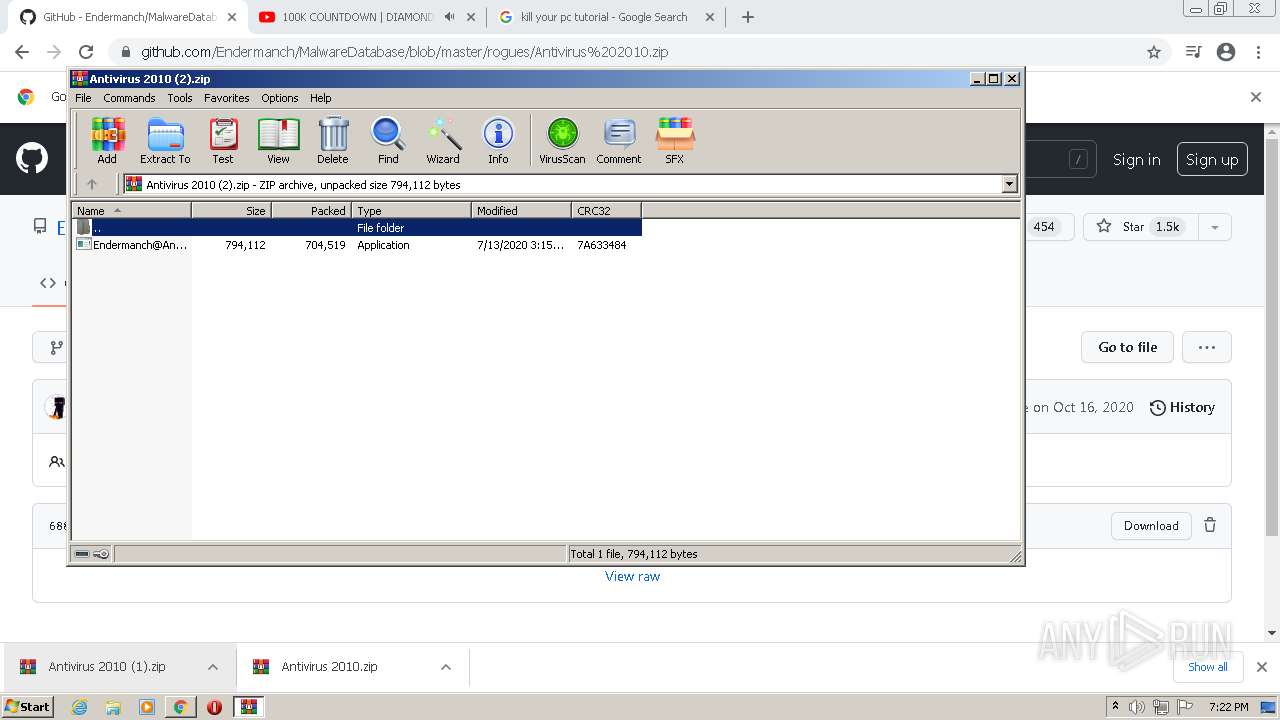
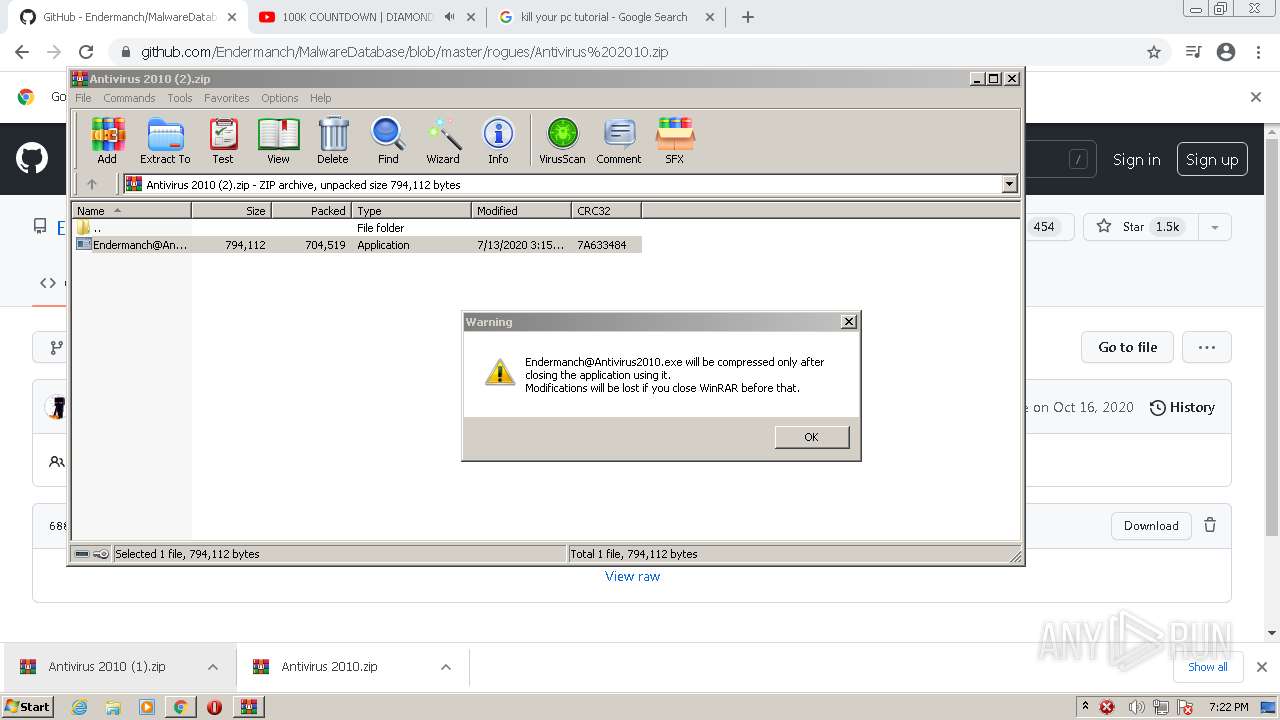
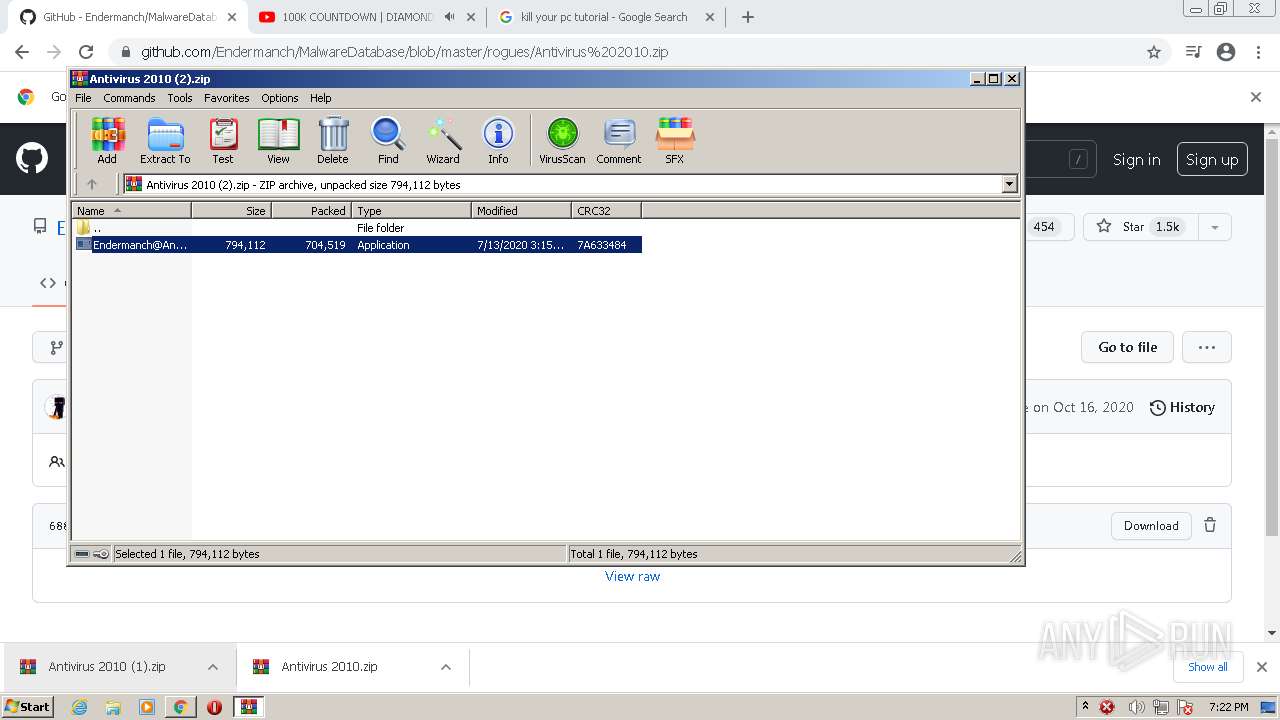
MALICIOUS
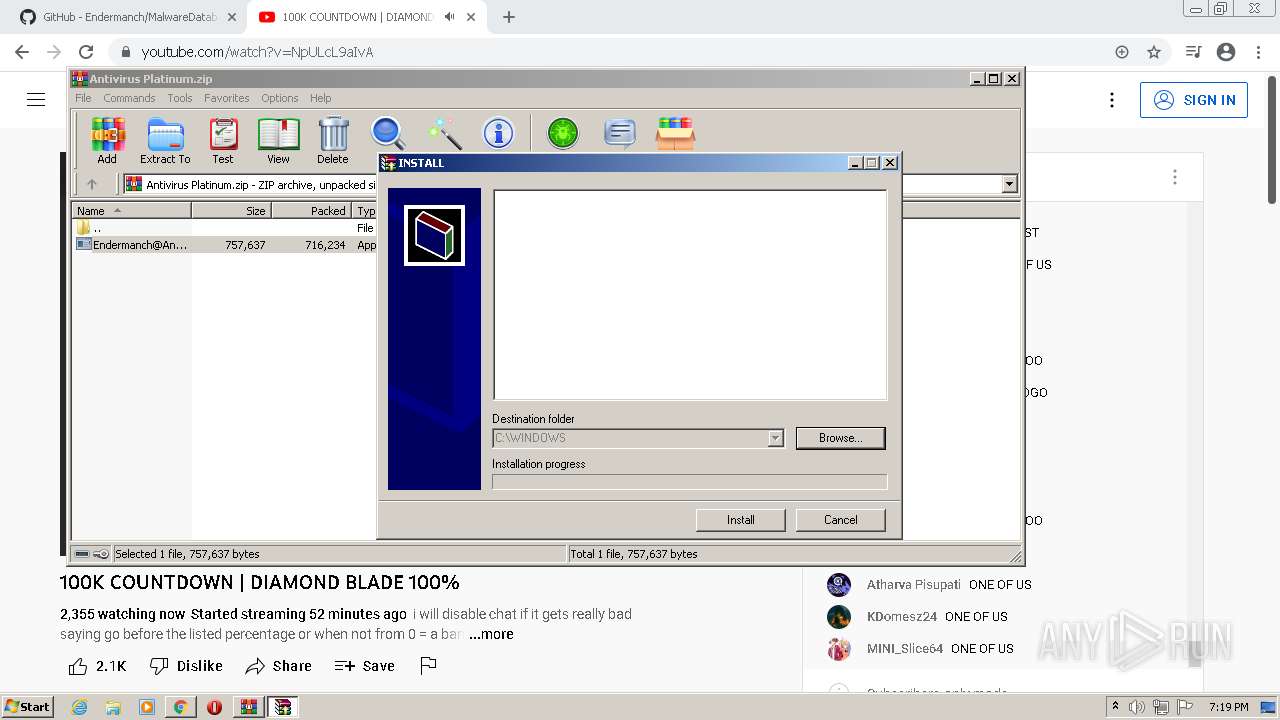
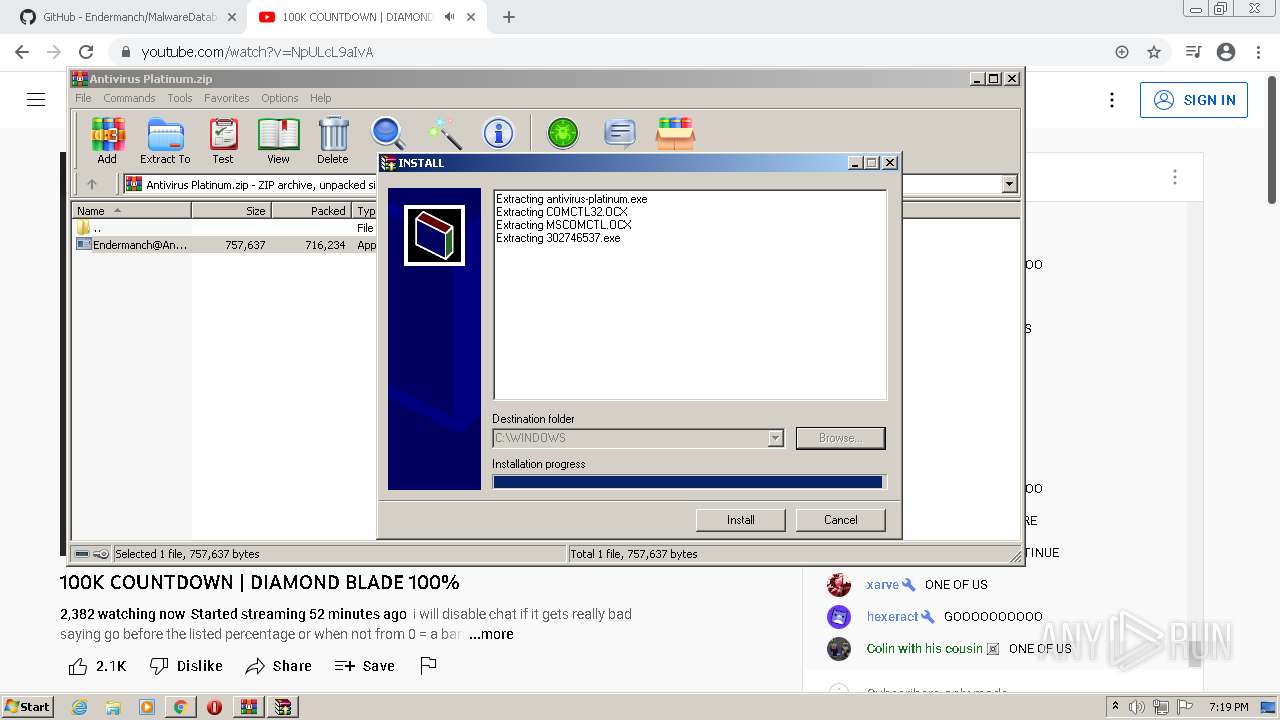
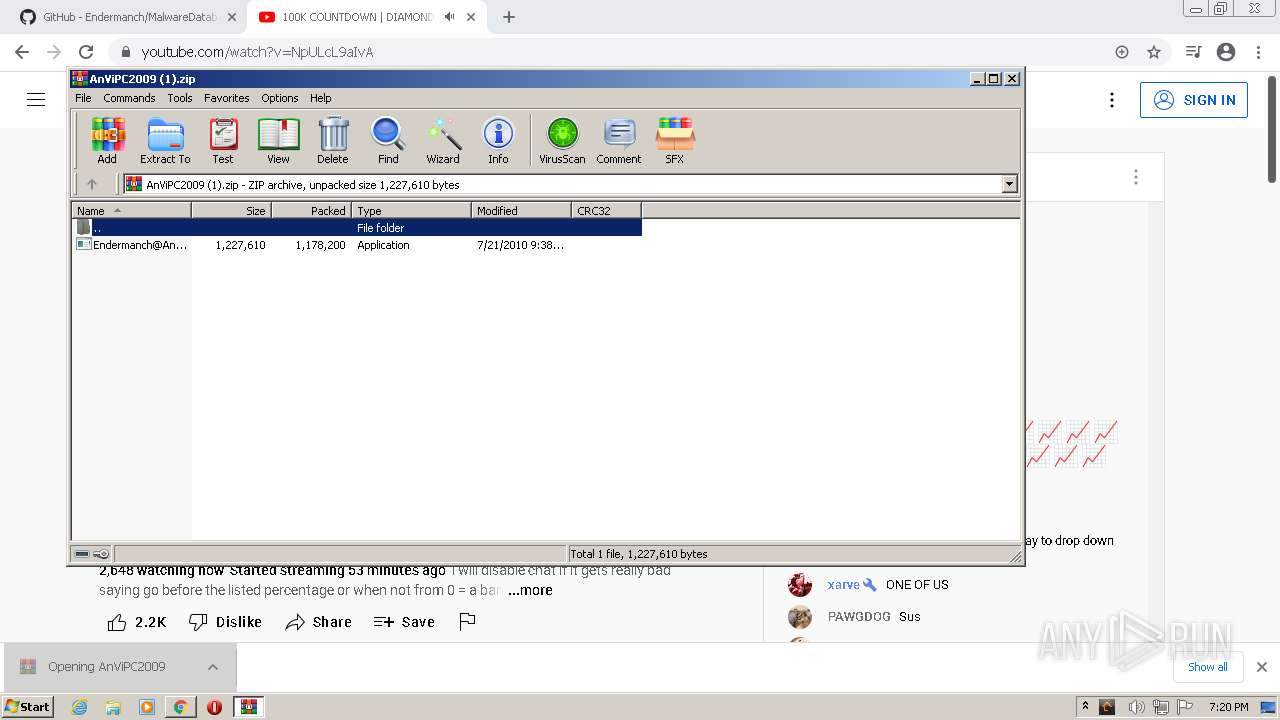
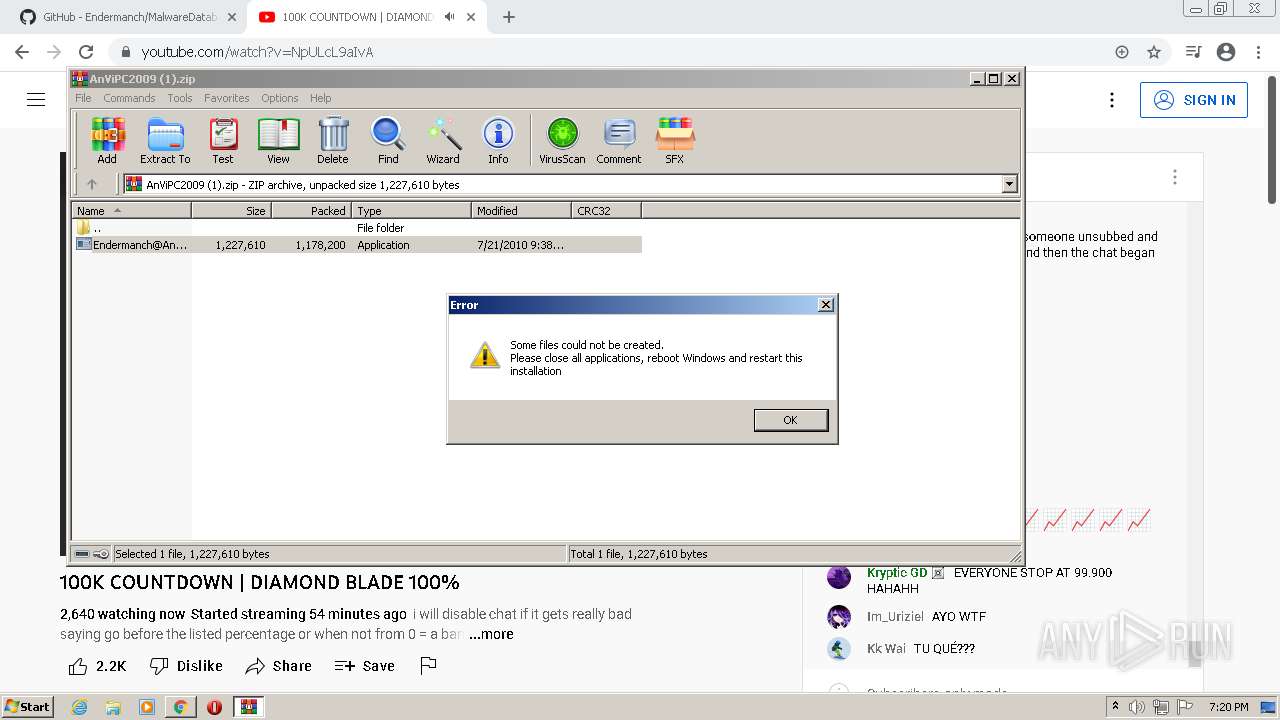
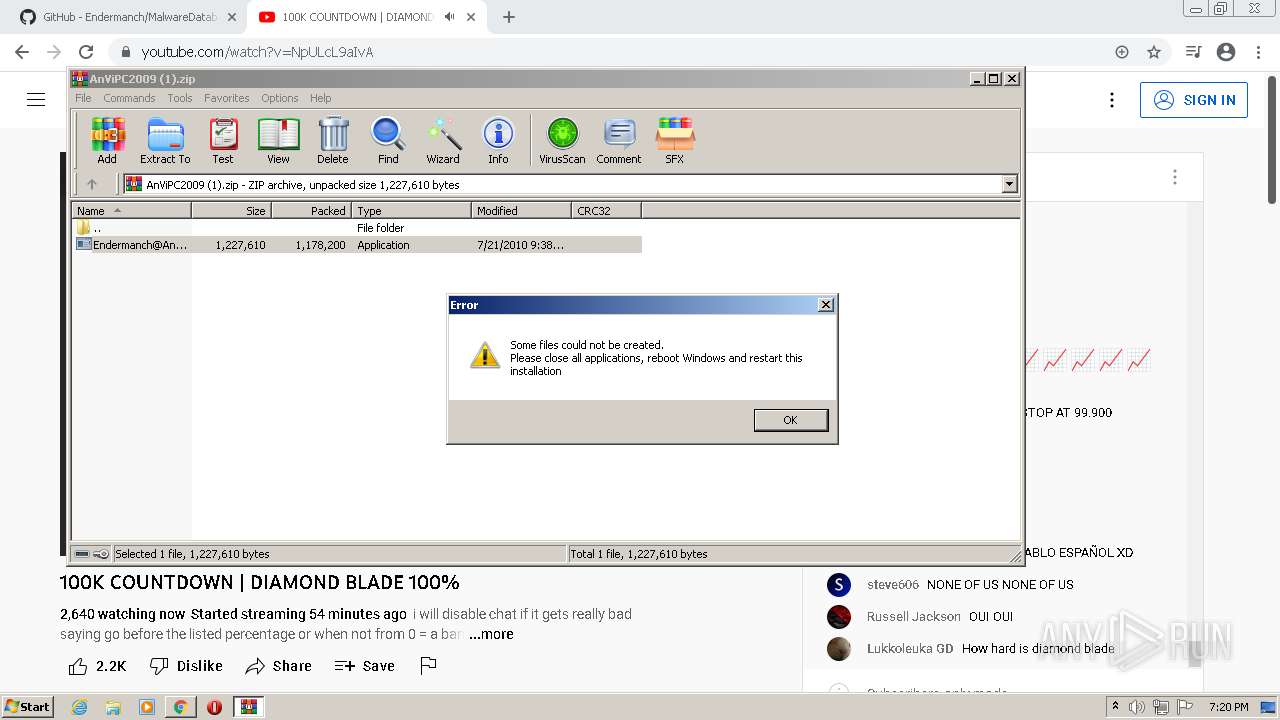
Drops executable file immediately after starts
- chrome.exe (PID: 1880)
- WinRAR.exe (PID: 4048)
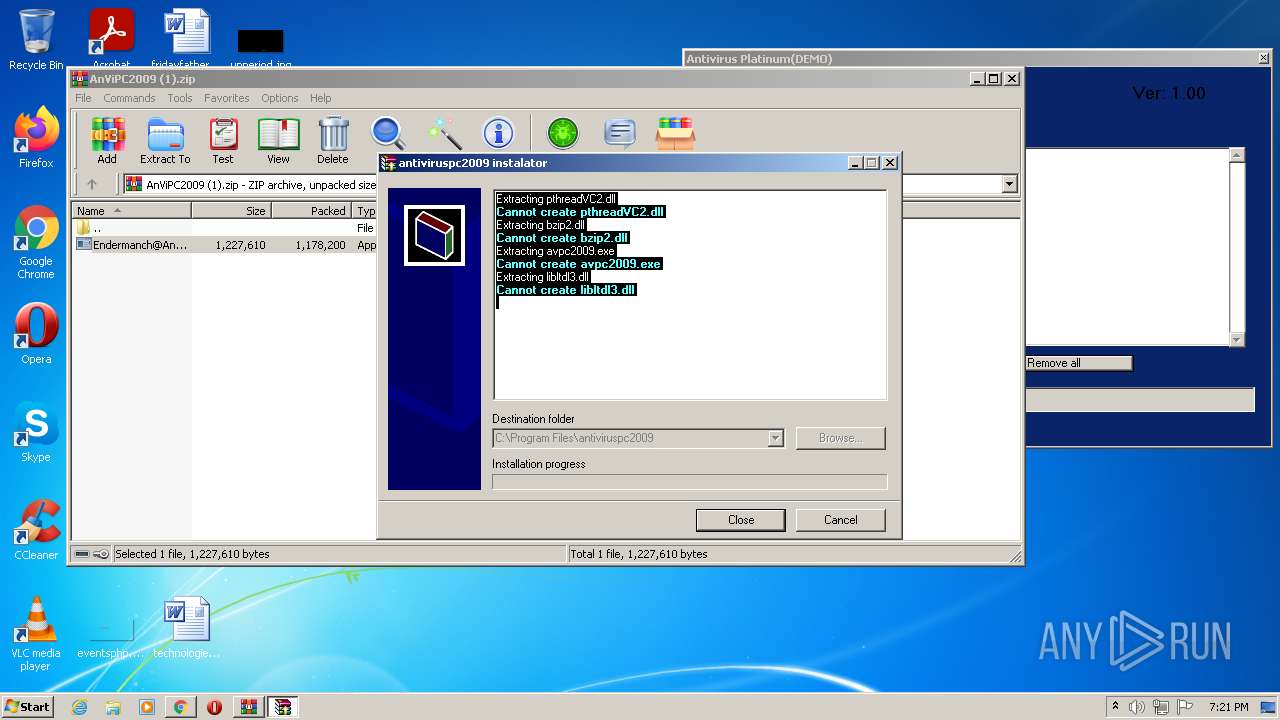
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- WinRAR.exe (PID: 116)
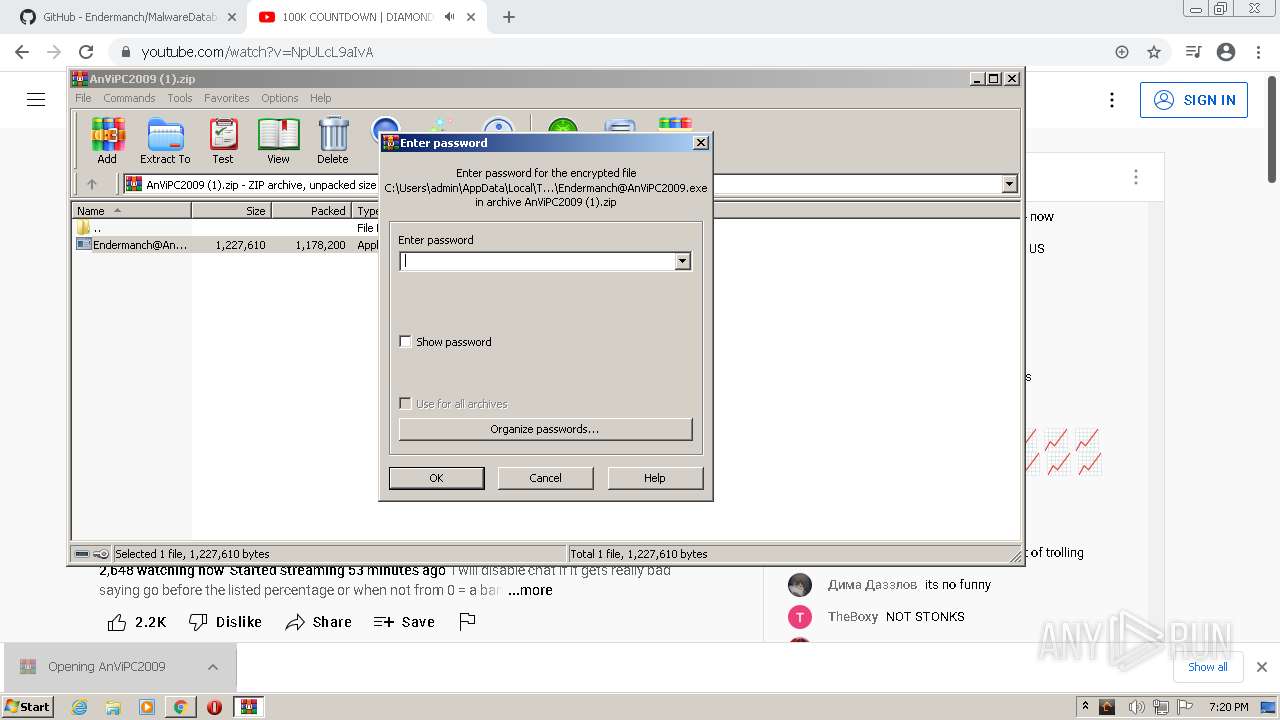
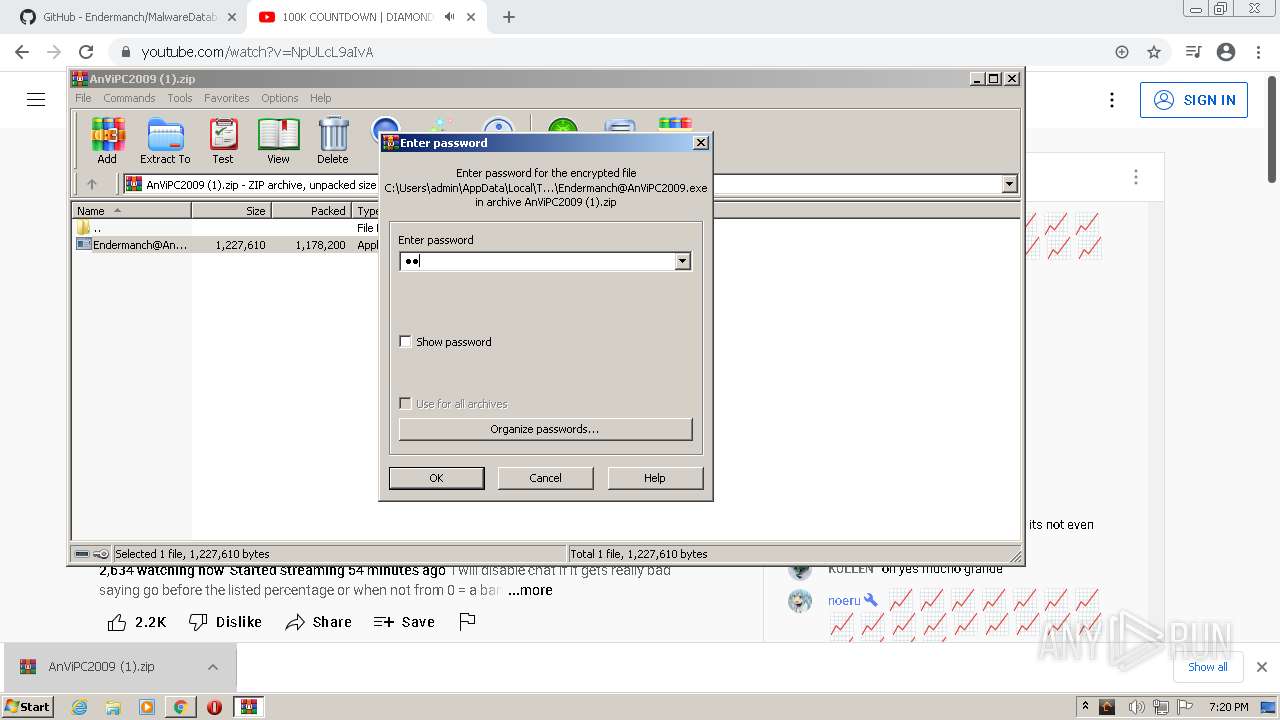
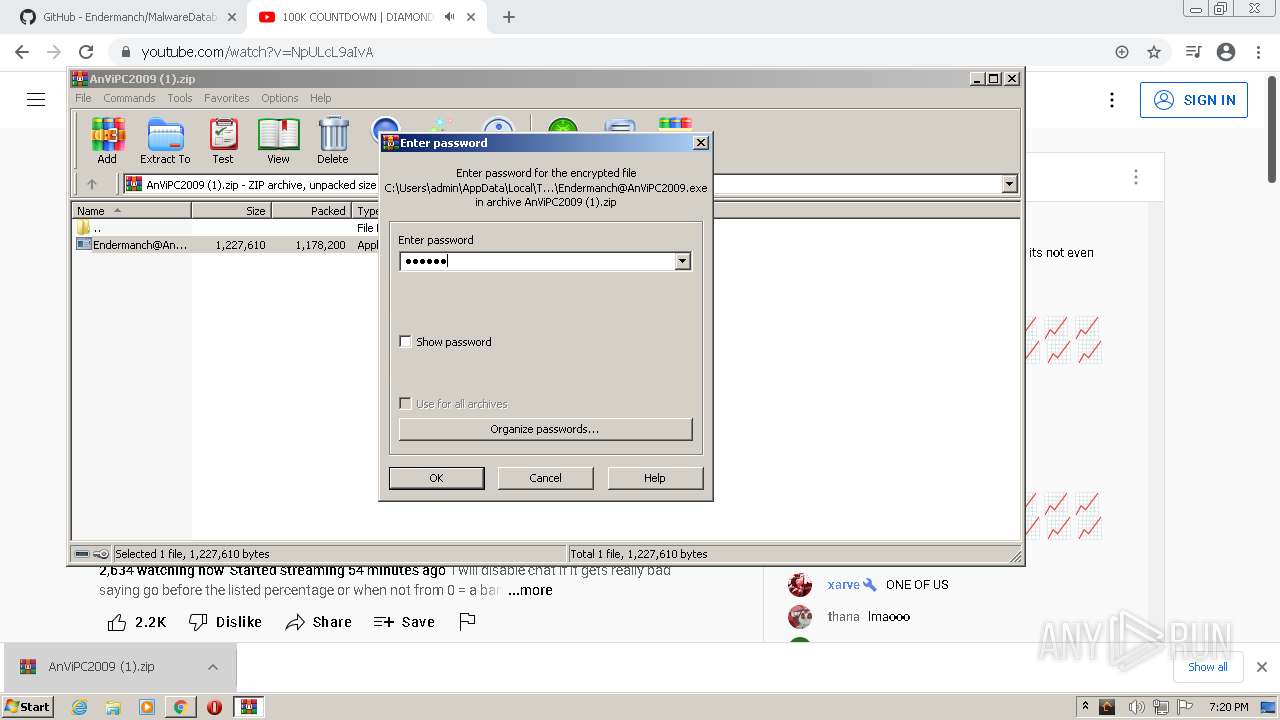
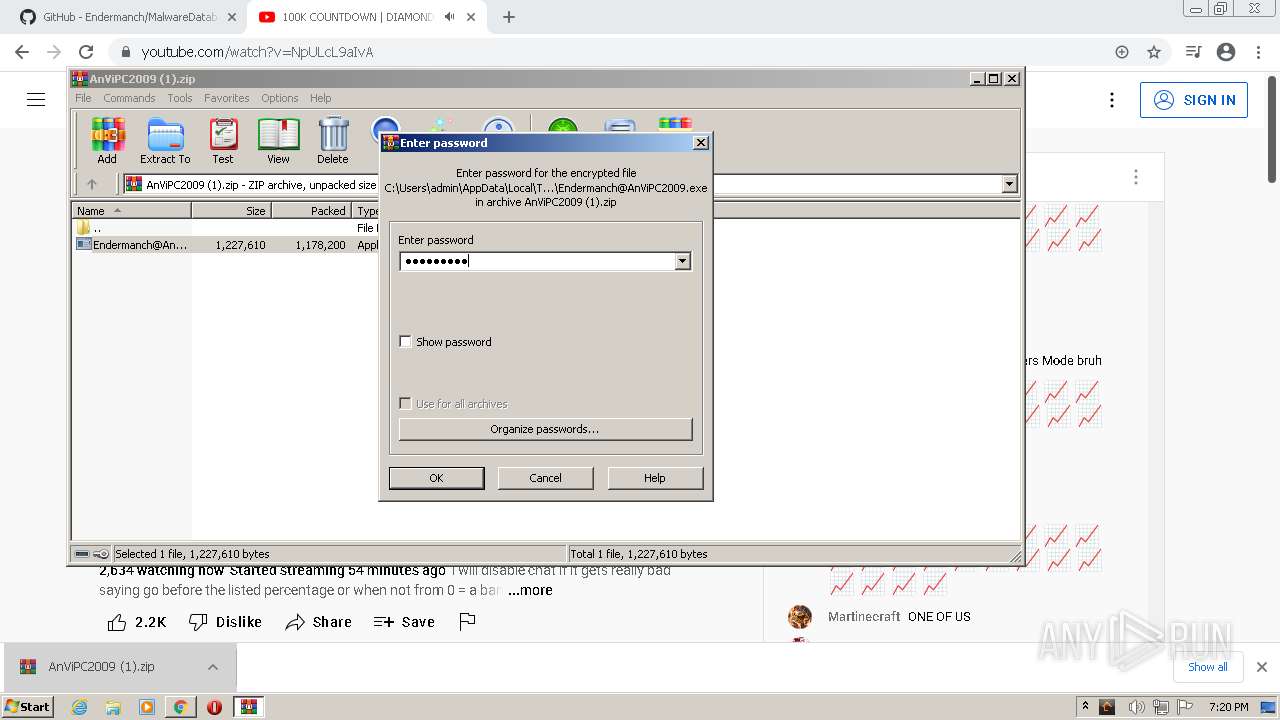
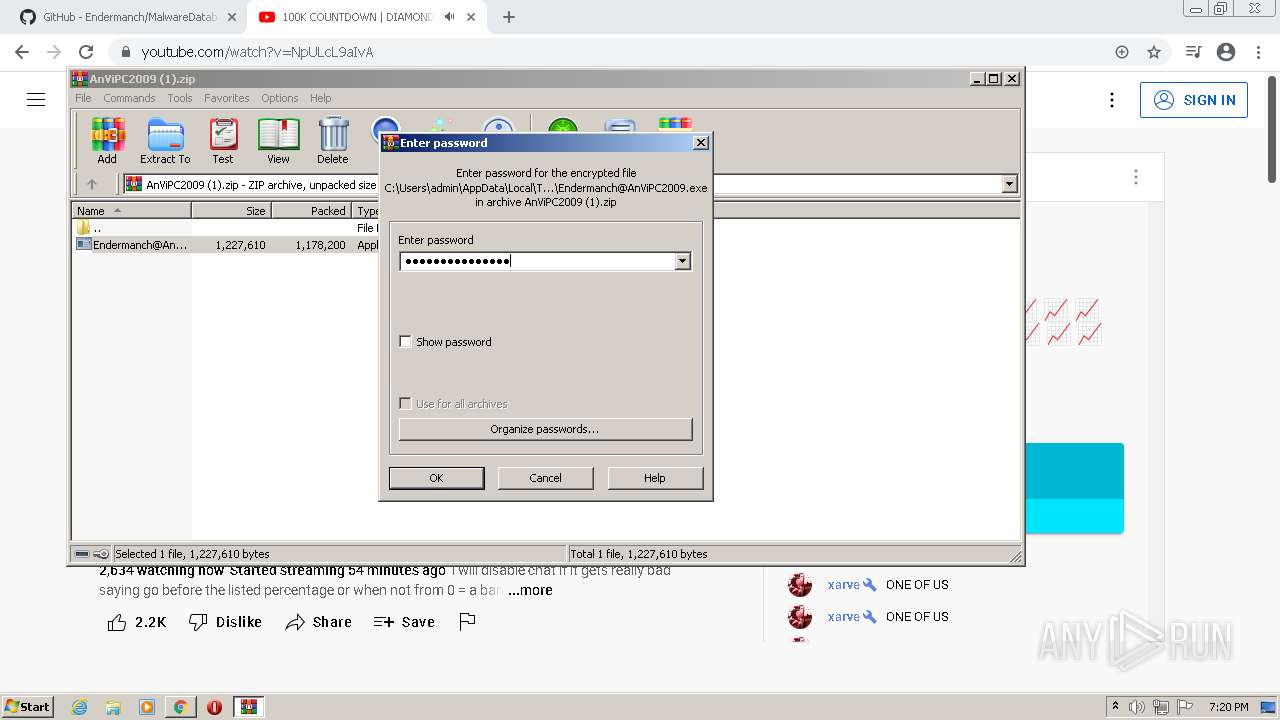
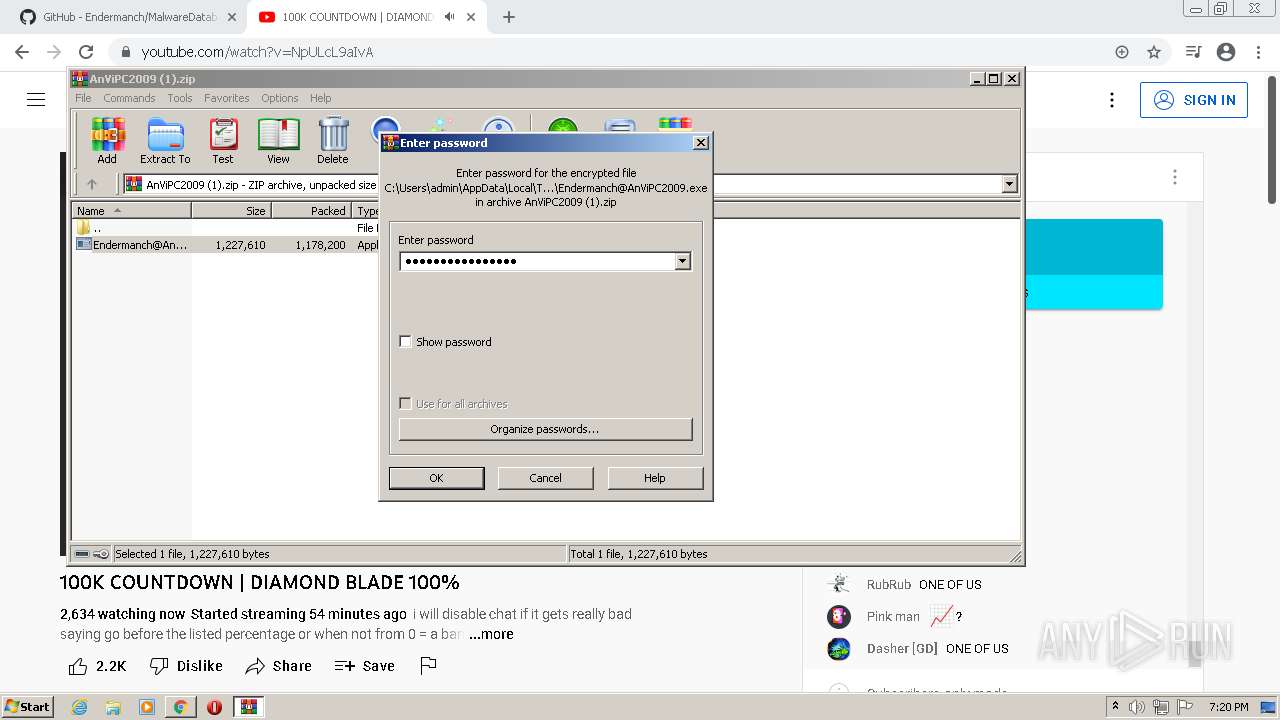
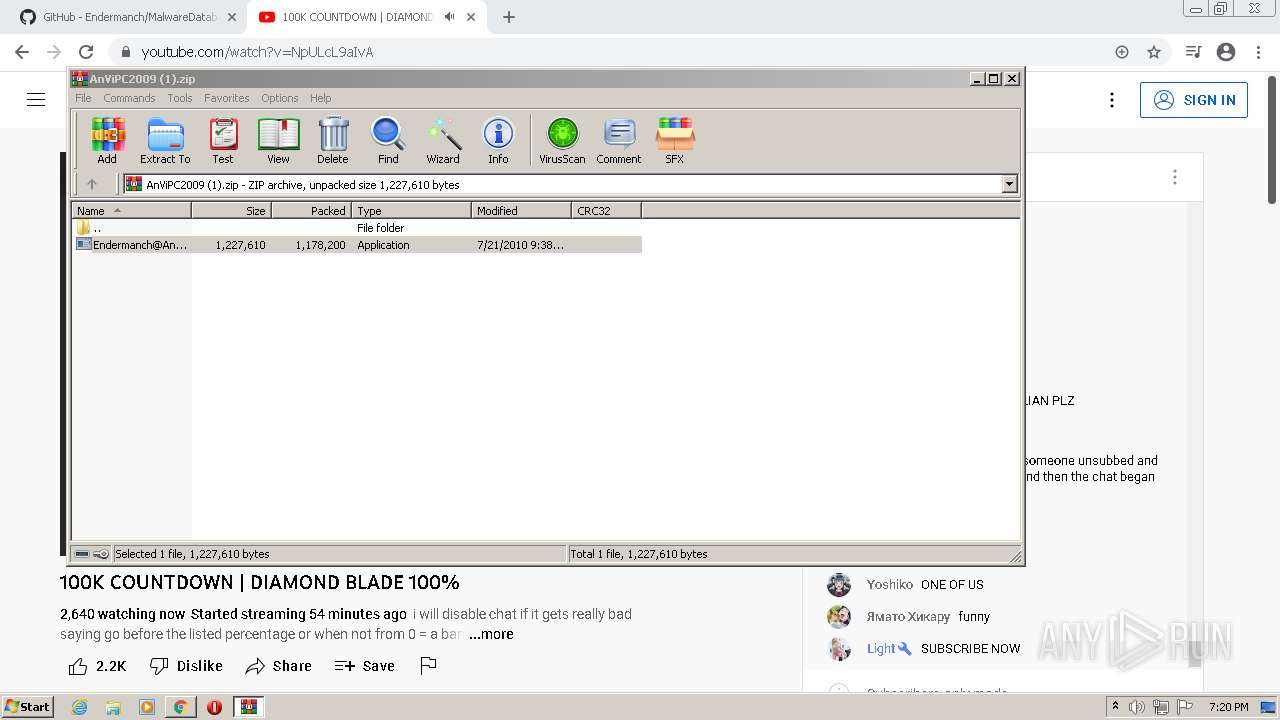
- Endermanch@AnViPC2009.exe (PID: 2232)
- WinRAR.exe (PID: 3020)
- WinRAR.exe (PID: 604)
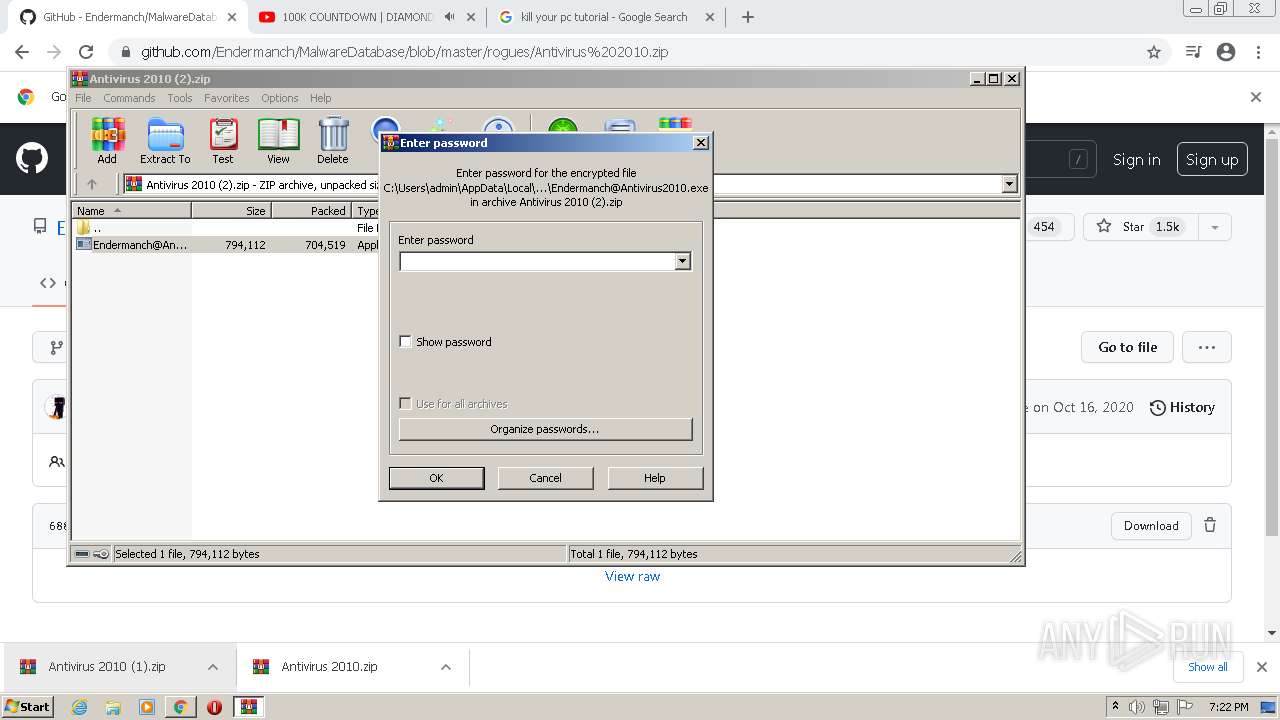
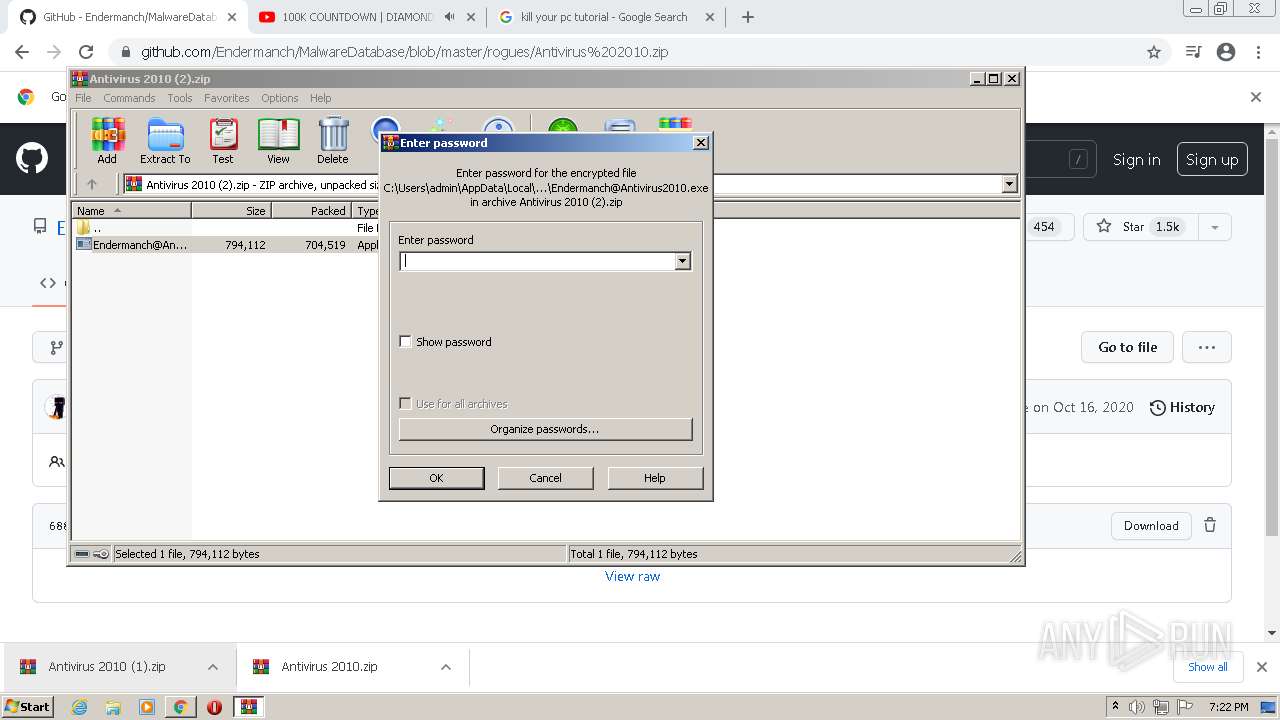
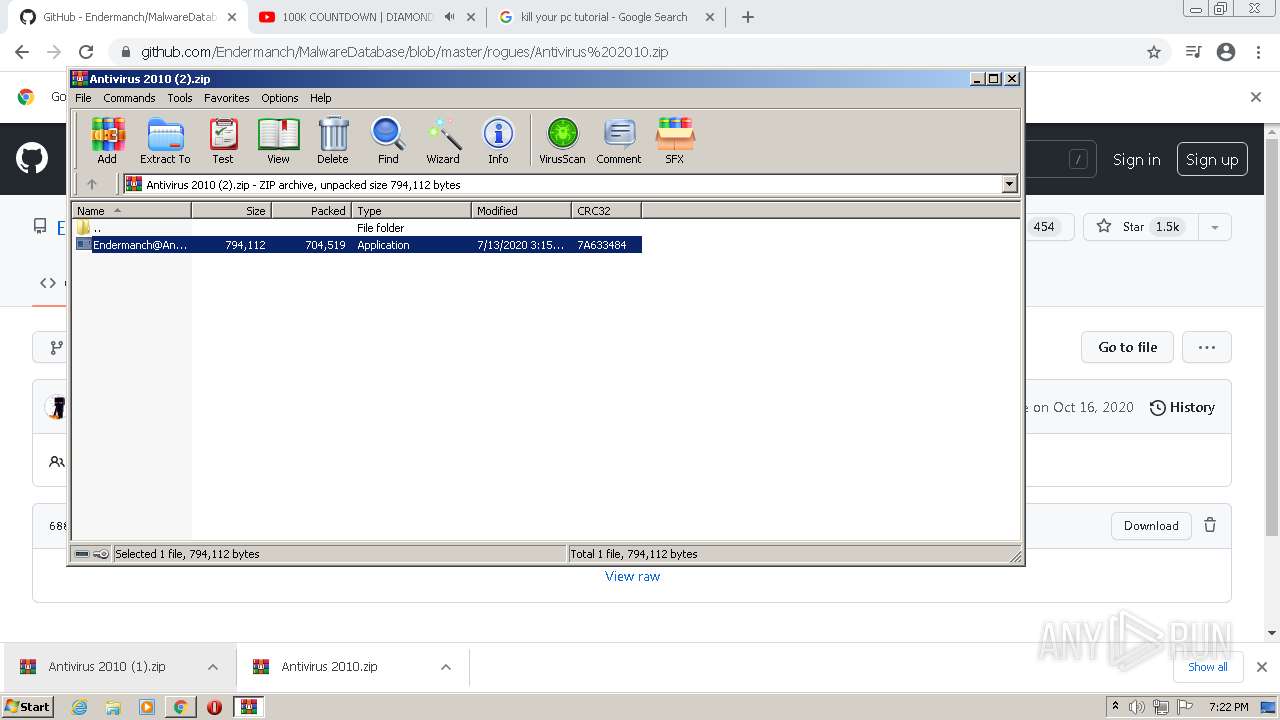
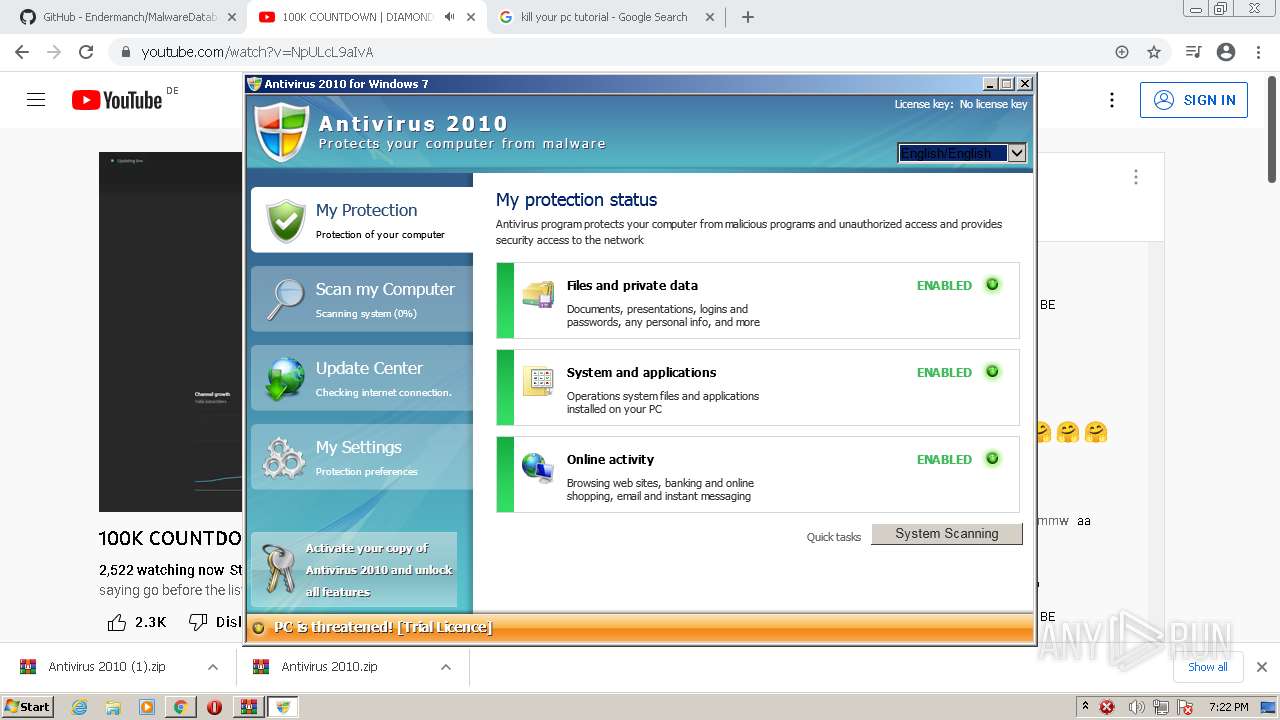
- Endermanch@Antivirus2010.exe (PID: 2820)
Application was dropped or rewritten from another process
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- Endermanch@AntivirusPlatinum.exe (PID: 3484)
- 302746537.exe (PID: 2296)
- antivirus-platinum.exe (PID: 2996)
- Endermanch@AnViPC2009.exe (PID: 652)
- avpc2009.exe (PID: 328)
- Endermanch@AnViPC2009.exe (PID: 2236)
- Endermanch@AnViPC2009.exe (PID: 1100)
- Endermanch@AnViPC2009.exe (PID: 2232)
- Endermanch@AnViPC2009.exe (PID: 2888)
- Endermanch@AnViPC2009.exe (PID: 468)
- Endermanch@AnViPC2009.exe (PID: 2808)
- Endermanch@AnViPC2009.exe (PID: 2600)
- avpc2009.exe (PID: 2020)
- avpc2009.exe (PID: 4032)
- avpc2009.exe (PID: 1252)
- avpc2009.exe (PID: 2452)
- avpc2009.exe (PID: 2340)
- Endermanch@Antivirus2010.exe (PID: 3916)
- Endermanch@Antivirus2010.exe (PID: 2820)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3564)
- avpc2009.exe (PID: 328)
- avpc2009.exe (PID: 2020)
- avpc2009.exe (PID: 4032)
- avpc2009.exe (PID: 2340)
- avpc2009.exe (PID: 1252)
- avpc2009.exe (PID: 2452)
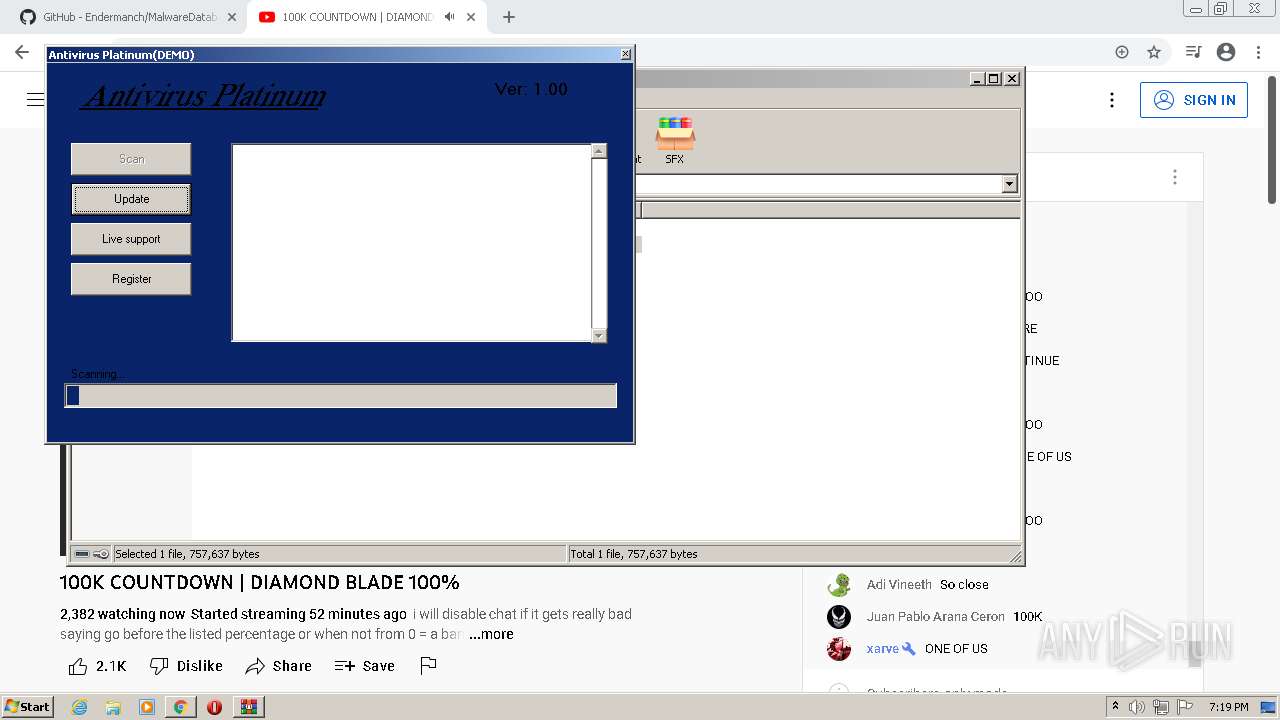
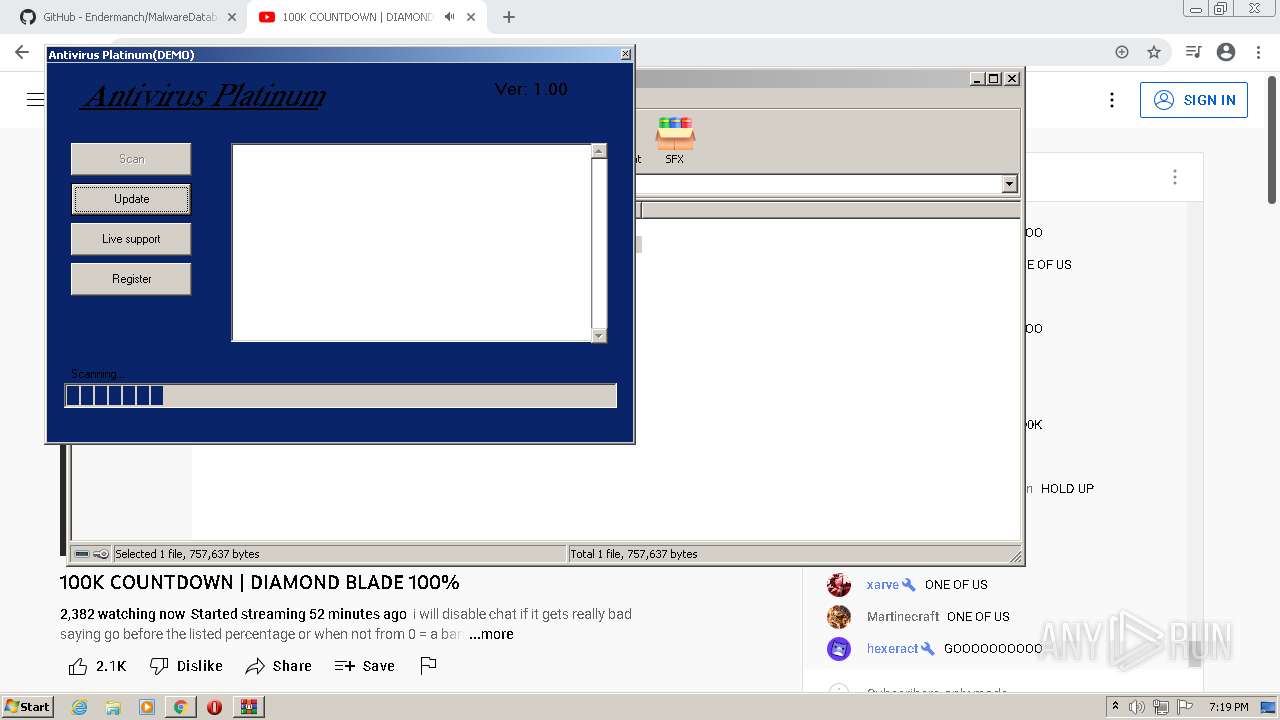
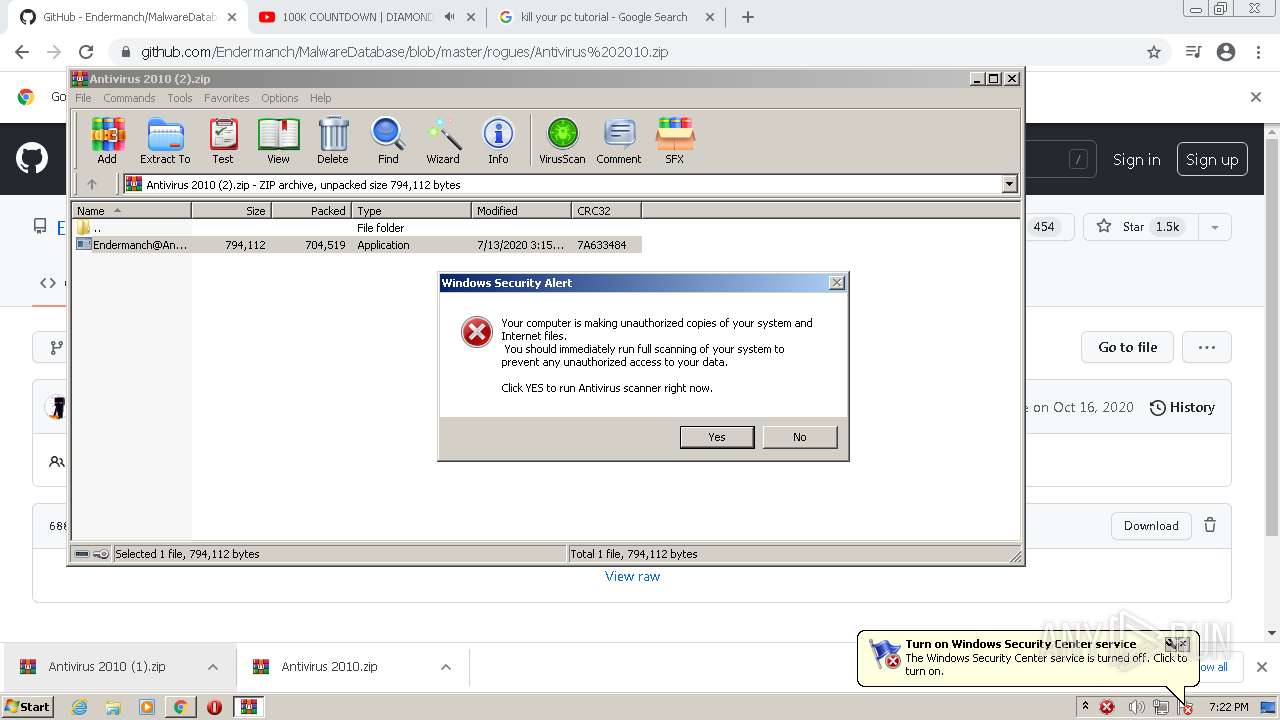
Task Manager has been disabled (taskmgr)
- antivirus-platinum.exe (PID: 2996)
Disables registry editing tools (regedit)
- antivirus-platinum.exe (PID: 2996)
Changes Security Center notification settings
- antivirus-platinum.exe (PID: 2996)
- svchost.exe (PID: 3752)
Disables the Shutdown in Start menu
- antivirus-platinum.exe (PID: 2996)
Disables the LogOff in Start menu
- antivirus-platinum.exe (PID: 2996)
Disables Windows System Restore
- antivirus-platinum.exe (PID: 2996)
Changes settings of System certificates
- svchost.exe (PID: 400)
- avpc2009.exe (PID: 328)
Runs injected code in another process
- svchost.exe (PID: 3752)
Application was injected by another process
- Explorer.EXE (PID: 636)
- svchost.exe (PID: 2004)
- svchost.exe (PID: 1456)
- svchost.exe (PID: 400)
- svchost.exe (PID: 1720)
- svchost.exe (PID: 488)
- svchost.exe (PID: 708)
- svchost.exe (PID: 856)
- svchost.exe (PID: 1552)
Creates or modifies windows services
- svchost.exe (PID: 3752)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2324)
- WinRAR.exe (PID: 4048)
- Endermanch@AntivirusPlatinum.exe (PID: 3484)
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- 302746537.exe (PID: 2296)
- cmd.exe (PID: 2576)
- antivirus-platinum.exe (PID: 2996)
- Endermanch@AnViPC2009.exe (PID: 2232)
- Endermanch@AnViPC2009.exe (PID: 652)
- WinRAR.exe (PID: 116)
- avpc2009.exe (PID: 328)
- Endermanch@AnViPC2009.exe (PID: 2236)
- Endermanch@AnViPC2009.exe (PID: 2888)
- Endermanch@AnViPC2009.exe (PID: 468)
- WinRAR.exe (PID: 3020)
- Endermanch@AnViPC2009.exe (PID: 1100)
- Endermanch@AnViPC2009.exe (PID: 2808)
- Endermanch@AnViPC2009.exe (PID: 2600)
- avpc2009.exe (PID: 2020)
- avpc2009.exe (PID: 4032)
- avpc2009.exe (PID: 2340)
- avpc2009.exe (PID: 1252)
- avpc2009.exe (PID: 2452)
- Endermanch@Antivirus2010.exe (PID: 2820)
- WinRAR.exe (PID: 604)
- cmd.exe (PID: 116)
- usеrinit.exe (PID: 2280)
Reads the computer name
- WinRAR.exe (PID: 2324)
- WinRAR.exe (PID: 4048)
- Endermanch@AntivirusPlatinum.exe (PID: 3484)
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- 302746537.exe (PID: 2296)
- antivirus-platinum.exe (PID: 2996)
- WinRAR.exe (PID: 116)
- Endermanch@AnViPC2009.exe (PID: 652)
- Endermanch@AnViPC2009.exe (PID: 2232)
- avpc2009.exe (PID: 328)
- Endermanch@AnViPC2009.exe (PID: 2236)
- Endermanch@AnViPC2009.exe (PID: 1100)
- Endermanch@AnViPC2009.exe (PID: 2888)
- Endermanch@AnViPC2009.exe (PID: 468)
- WinRAR.exe (PID: 3020)
- Endermanch@AnViPC2009.exe (PID: 2808)
- Endermanch@AnViPC2009.exe (PID: 2600)
- WinRAR.exe (PID: 604)
- usеrinit.exe (PID: 2280)
Executable content was dropped or overwritten
- chrome.exe (PID: 1880)
- WinRAR.exe (PID: 4048)
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- WinRAR.exe (PID: 116)
- Endermanch@AnViPC2009.exe (PID: 2232)
- WinRAR.exe (PID: 3020)
- WinRAR.exe (PID: 604)
- Endermanch@Antivirus2010.exe (PID: 2820)
Drops a file with a compile date too recent
- chrome.exe (PID: 1880)
- WinRAR.exe (PID: 4048)
- Endermanch@AntivirusPlatinum.exe (PID: 2476)
- WinRAR.exe (PID: 116)
- Endermanch@AnViPC2009.exe (PID: 2232)
- WinRAR.exe (PID: 3020)
- WinRAR.exe (PID: 604)
- Endermanch@Antivirus2010.exe (PID: 2820)
Application launched itself
- Endermanch@AntivirusPlatinum.exe (PID: 3484)
- Endermanch@AnViPC2009.exe (PID: 652)
- Endermanch@AnViPC2009.exe (PID: 2236)
- Endermanch@AnViPC2009.exe (PID: 2888)
- Endermanch@AnViPC2009.exe (PID: 2808)
Changes the started page of IE
- antivirus-platinum.exe (PID: 2996)
Reads mouse settings
- antivirus-platinum.exe (PID: 2996)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1756)
- usеrinit.exe (PID: 2280)
- svchost.exe (PID: 3752)
Adds / modifies Windows certificates
- avpc2009.exe (PID: 328)
Searches for installed software
- svchost.exe (PID: 488)
- svchost.exe (PID: 3752)
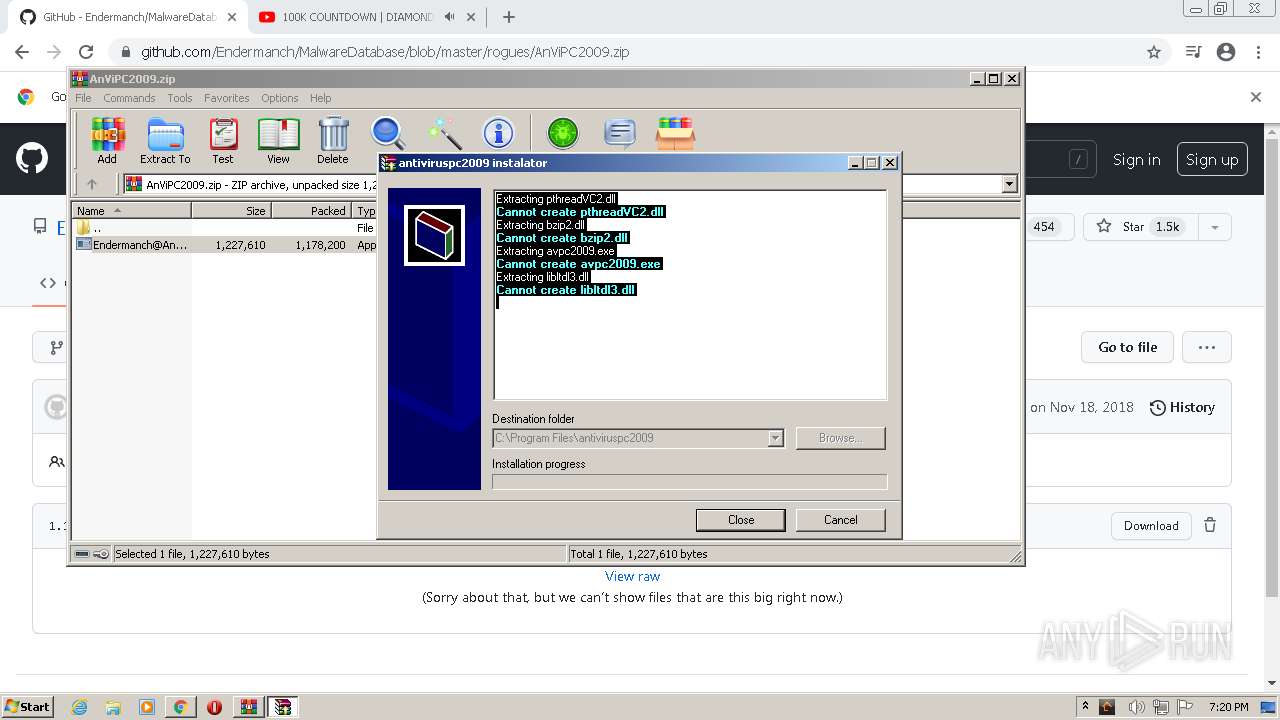
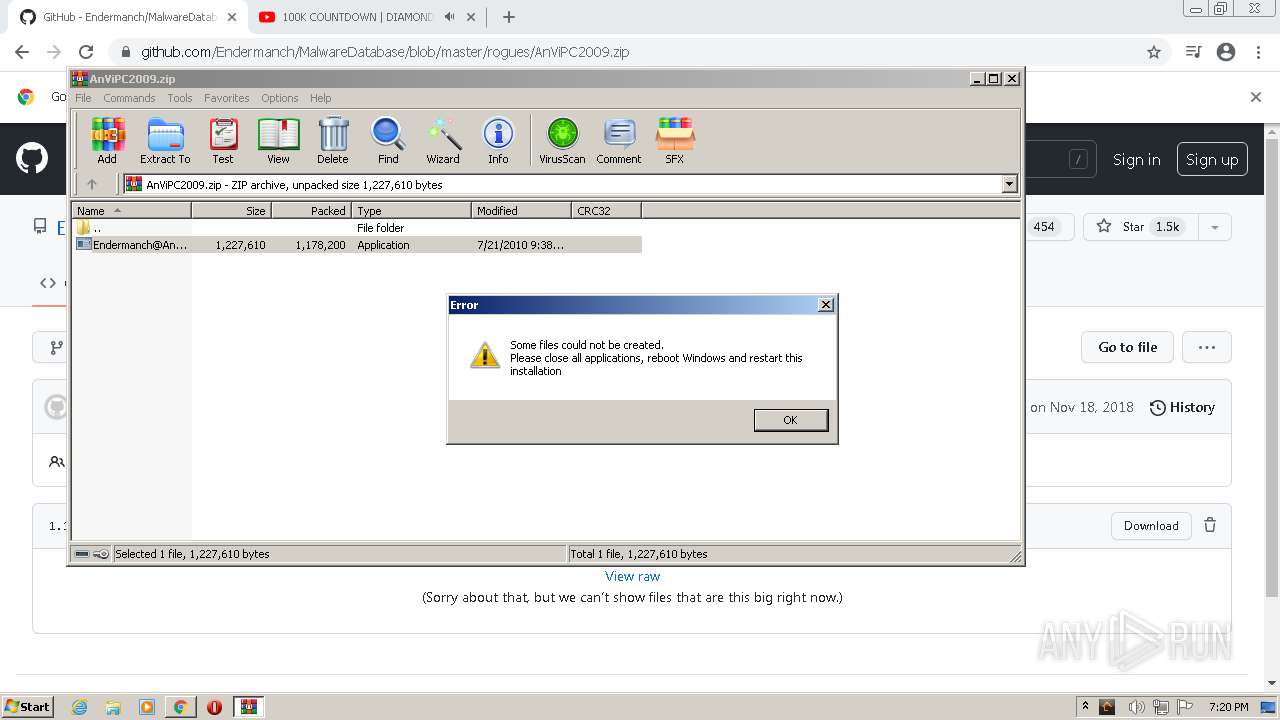
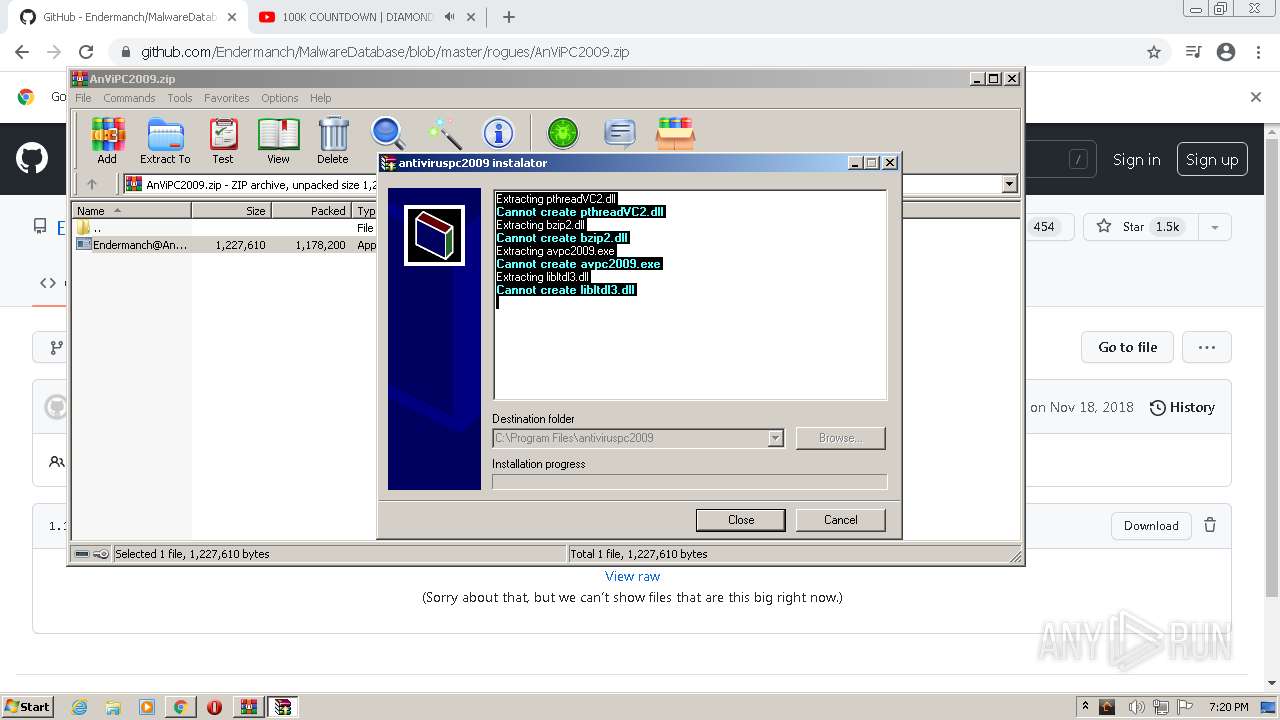
Creates a directory in Program Files
- Endermanch@AnViPC2009.exe (PID: 2232)
Creates files in the program directory
- Endermanch@AnViPC2009.exe (PID: 2232)
- svchost.exe (PID: 3752)
Creates a software uninstall entry
- usеrinit.exe (PID: 2280)
Creates or modifies windows services
- usеrinit.exe (PID: 2280)
- Endermanch@Antivirus2010.exe (PID: 2820)
Changes default file association
- svchost.exe (PID: 3752)
INFO
Checks supported languages
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 288)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2928)
- svchost.exe (PID: 488)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 916)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 532)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 1784)
- svchost.exe (PID: 1456)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1712)
- svchost.exe (PID: 856)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1880)
- regsvr32.exe (PID: 2864)
- regsvr32.exe (PID: 3564)
- attrib.exe (PID: 3696)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 1756)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 2020)
- chrome.exe (PID: 1528)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 684)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 268)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 352)
- chrome.exe (PID: 2836)
- svchost.exe (PID: 3752)
Reads the computer name
- chrome.exe (PID: 1656)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 1712)
- regsvr32.exe (PID: 2864)
- regsvr32.exe (PID: 3564)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 1756)
- chrome.exe (PID: 2804)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 352)
- chrome.exe (PID: 2836)
- svchost.exe (PID: 3752)
Reads settings of System Certificates
- chrome.exe (PID: 3588)
- iexplore.exe (PID: 1756)
- svchost.exe (PID: 400)
- iexplore.exe (PID: 2572)
- avpc2009.exe (PID: 328)
- svchost.exe (PID: 3752)
Application launched itself
- chrome.exe (PID: 1656)
- iexplore.exe (PID: 2572)
Reads the date of Windows installation
- chrome.exe (PID: 1784)
- iexplore.exe (PID: 2572)
Reads mouse settings
- regsvr32.exe (PID: 3564)
Reads Microsoft Office registry keys
- antivirus-platinum.exe (PID: 2996)
Changes internet zones settings
- iexplore.exe (PID: 2572)
Reads internet explorer settings
- iexplore.exe (PID: 1756)
Checks Windows Trust Settings
- iexplore.exe (PID: 1756)
- iexplore.exe (PID: 2572)
- svchost.exe (PID: 3752)
Changes settings of System certificates
- iexplore.exe (PID: 1756)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1756)
Manual execution by user
- avpc2009.exe (PID: 2020)
- avpc2009.exe (PID: 4032)
- avpc2009.exe (PID: 2340)
- avpc2009.exe (PID: 2452)
- avpc2009.exe (PID: 1252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
124
Malicious processes
23
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
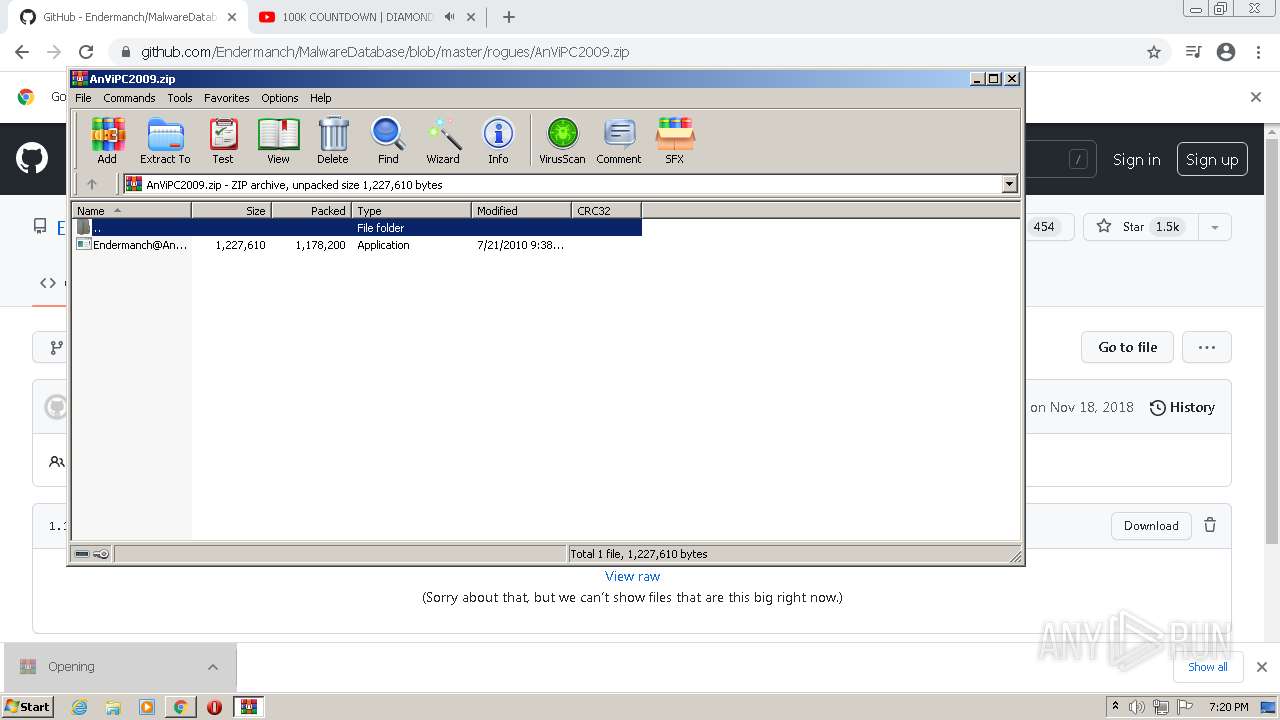
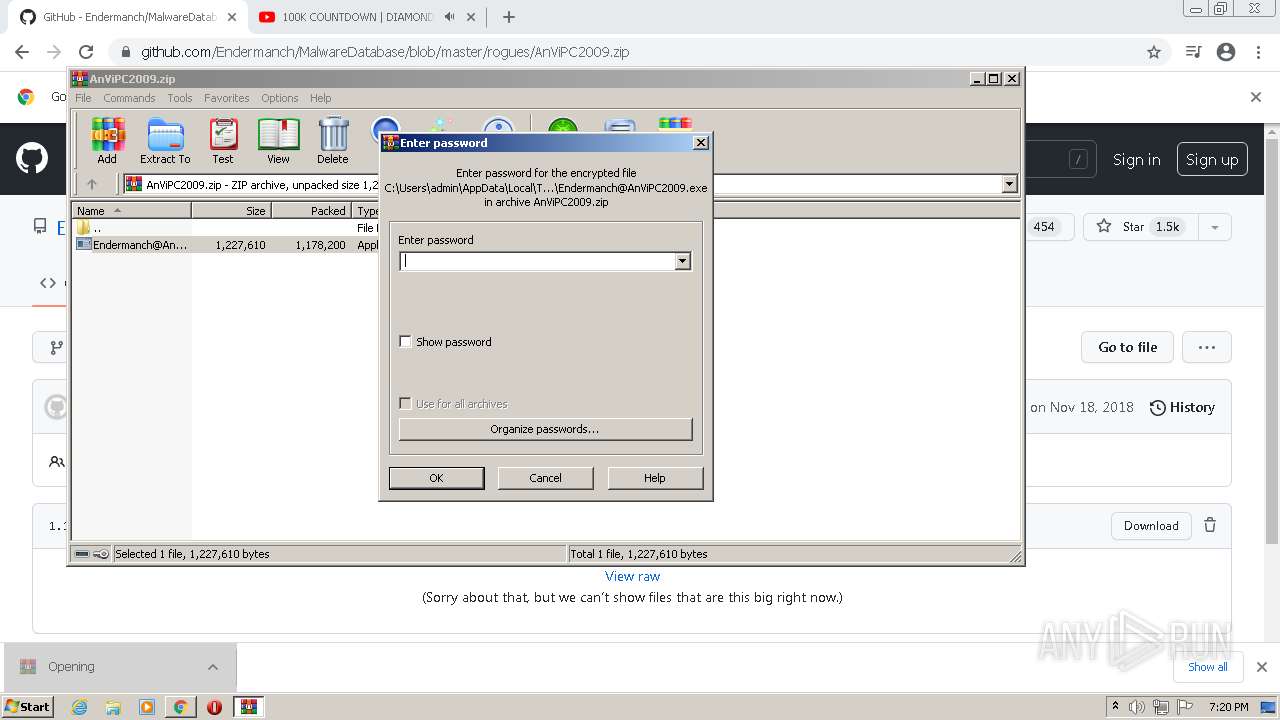
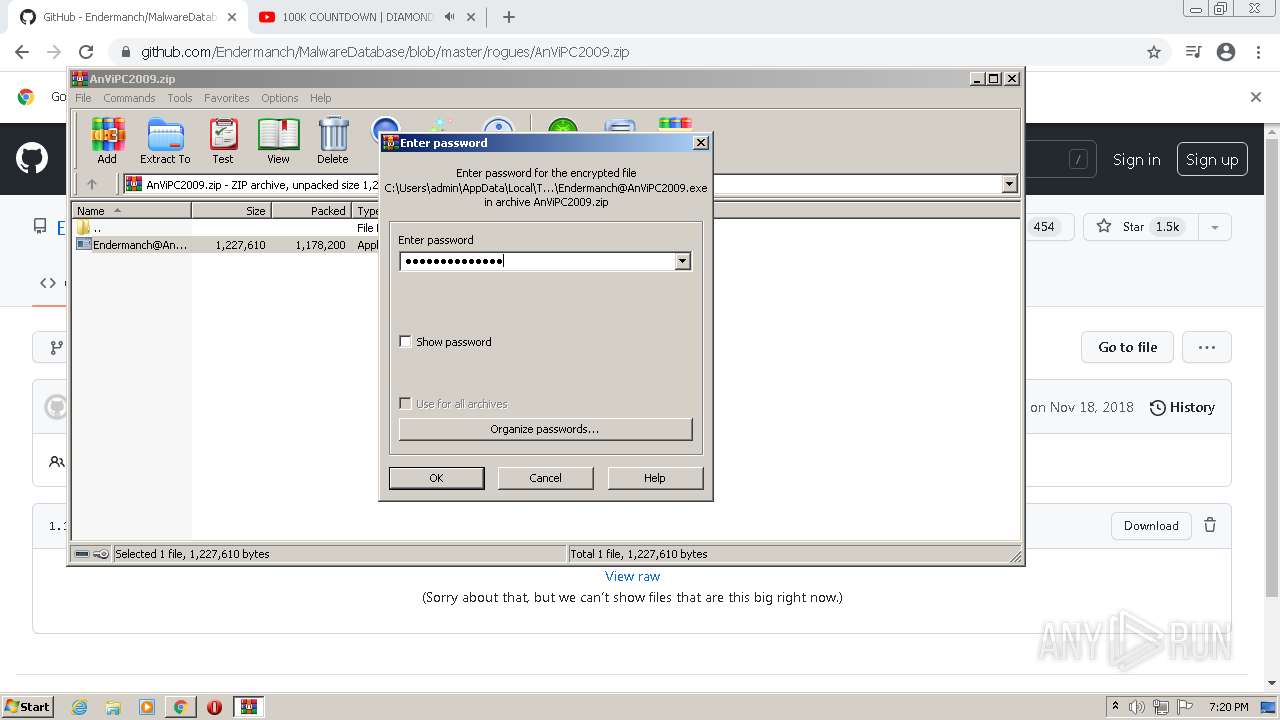
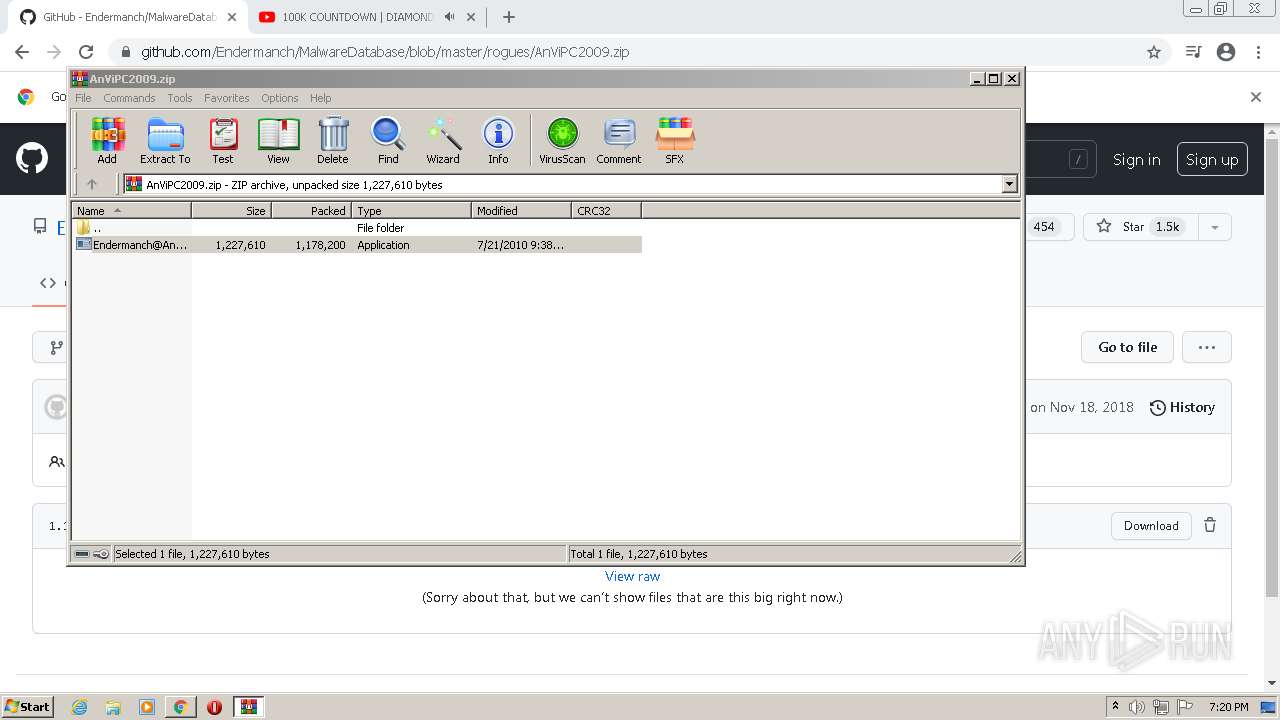
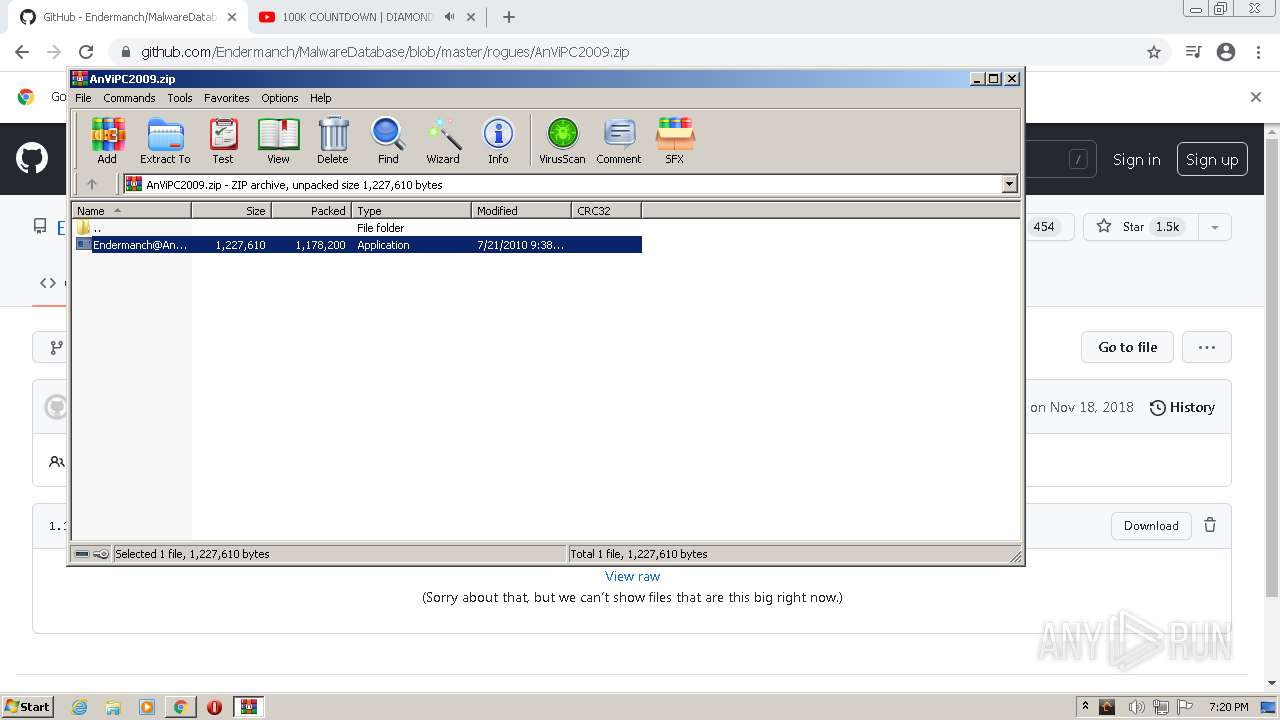
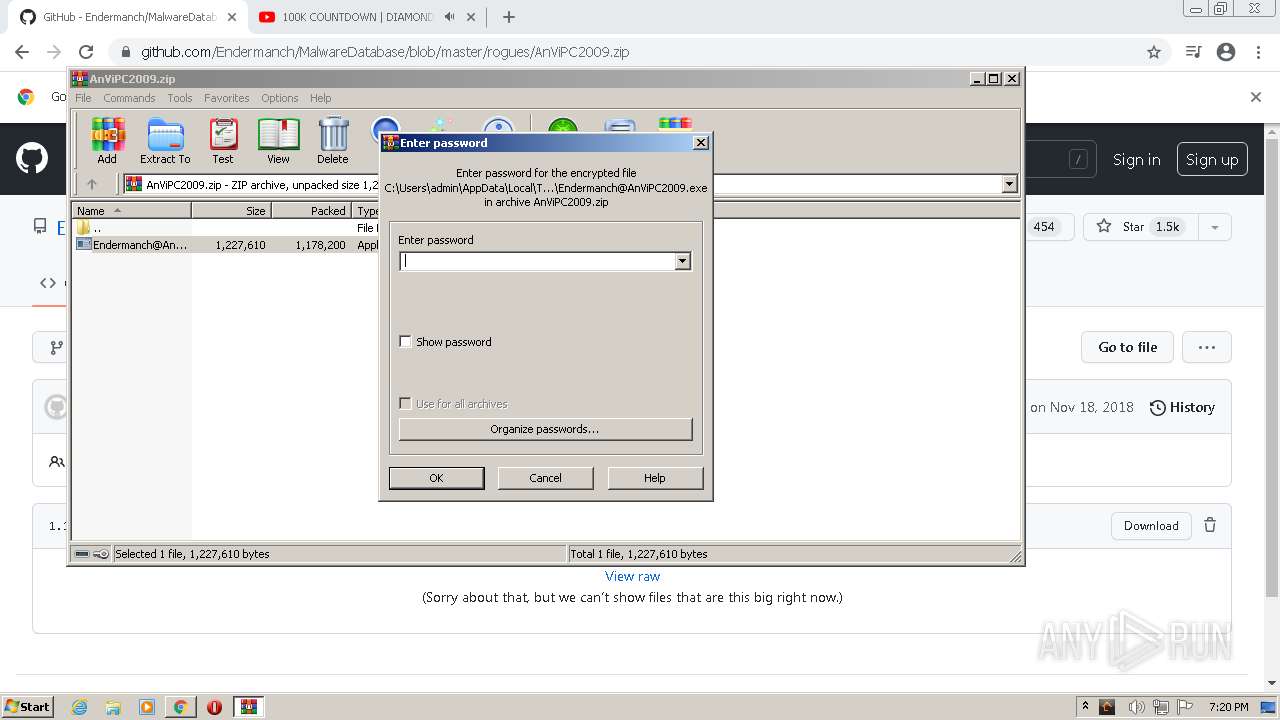
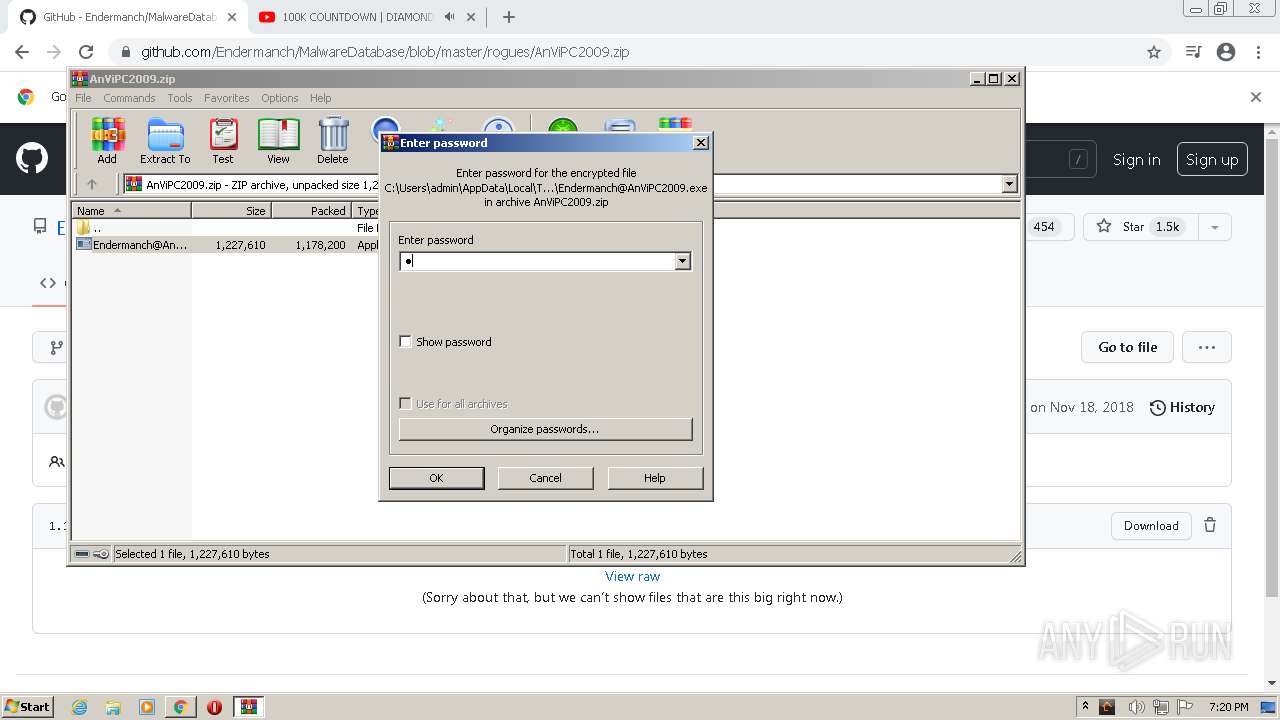
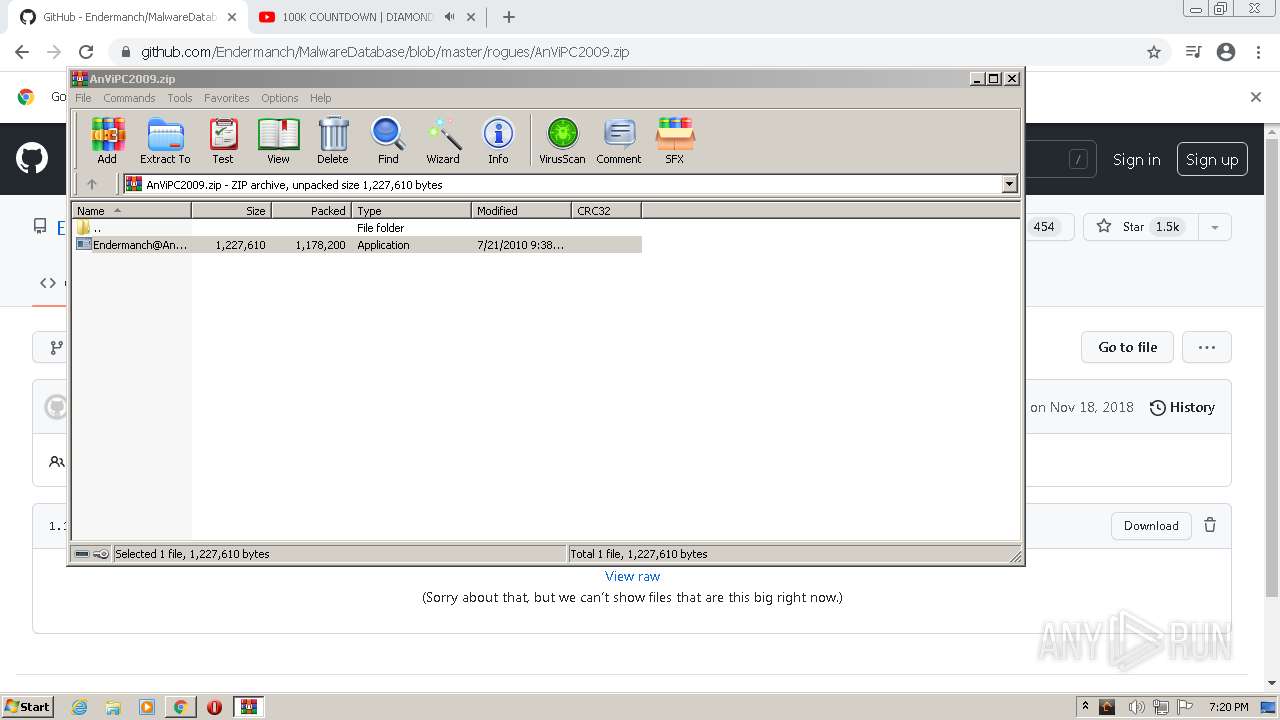
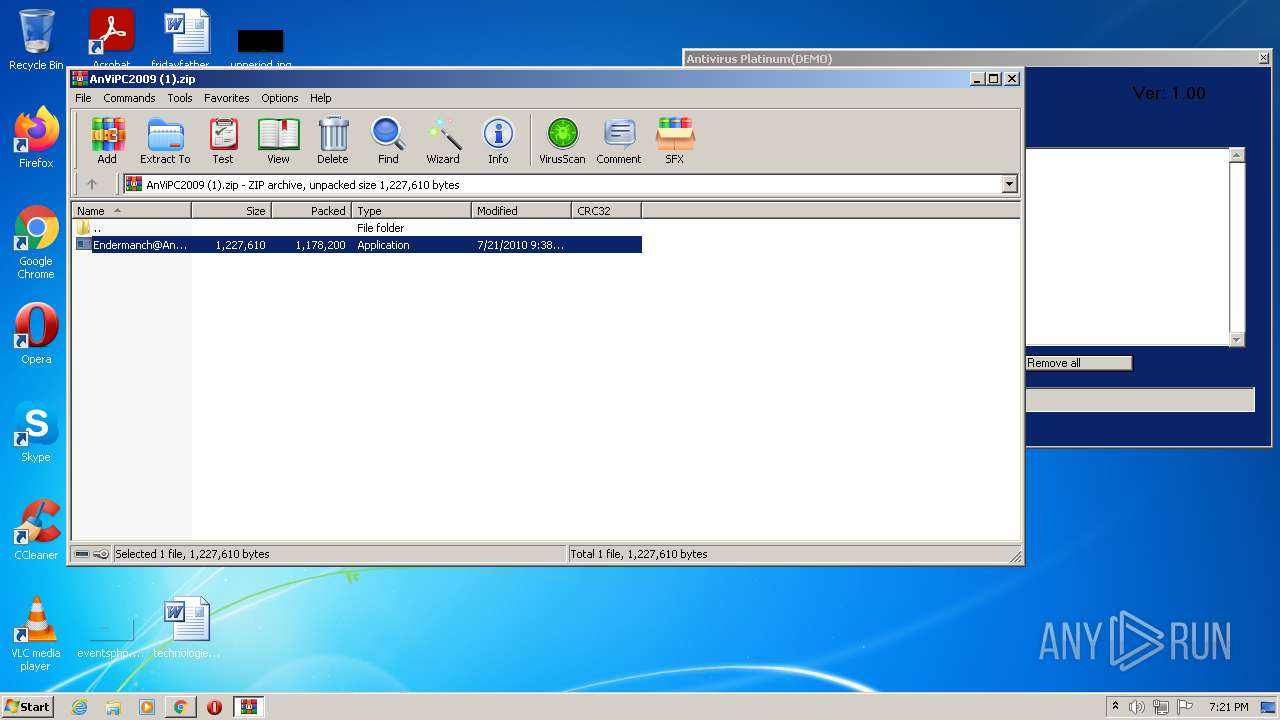
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\AnViPC2009.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 116 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Endermanch@Antivirus2010.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,9951147323252423840,8150529689024770471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9951147323252423840,8150529689024770471,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
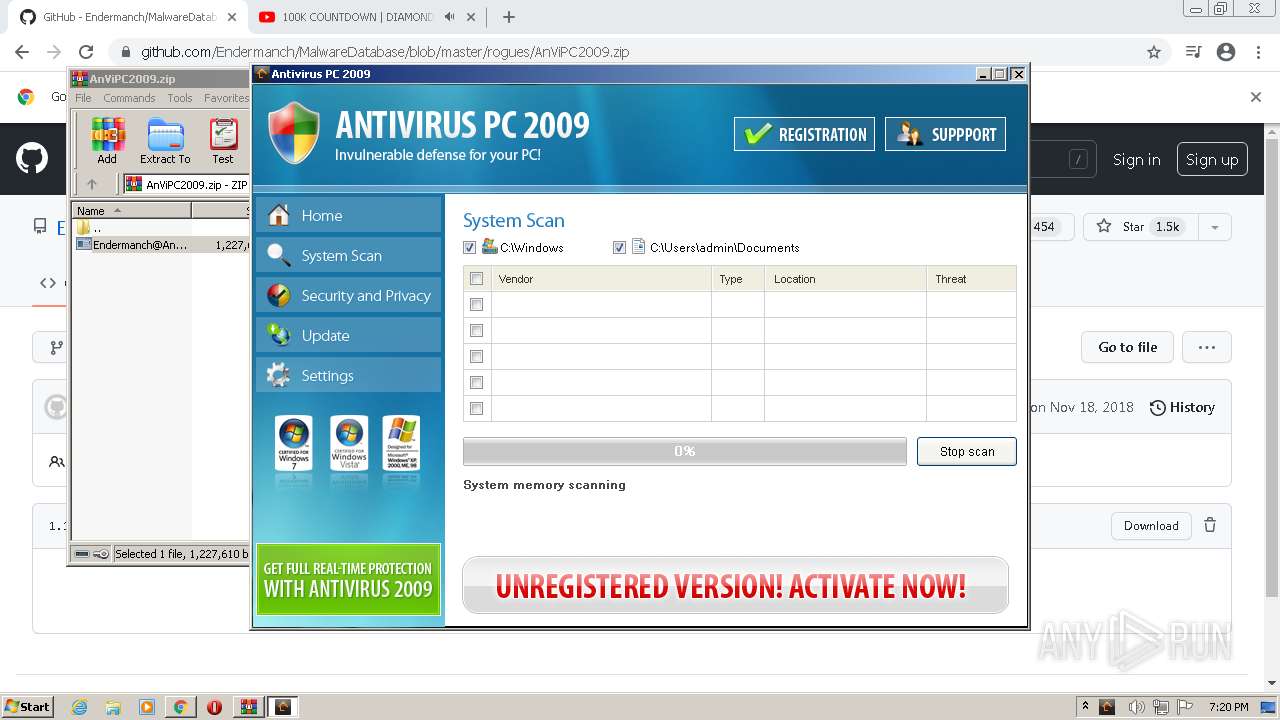
| 328 | "C:\Program Files\antiviruspc2009\avpc2009.exe" | C:\Program Files\antiviruspc2009\avpc2009.exe | Endermanch@AnViPC2009.exe | ||||||||||||
User: admin Company: Antivirus PC 2009 Integrity Level: HIGH Exit code: 0 Version: 2.0.45.1 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1036,9951147323252423840,8150529689024770471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
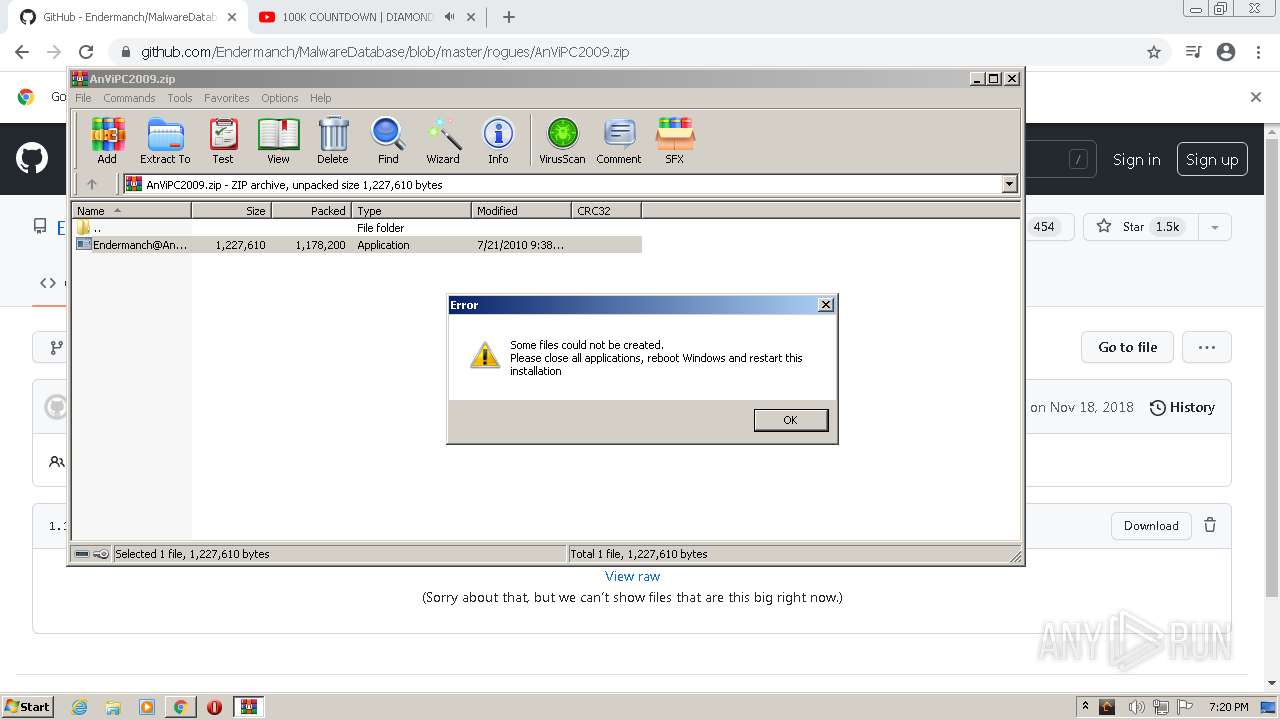
| 468 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb116.8277\Endermanch@AnViPC2009.exe" -el -s2 "-dC:\Program Files\antiviruspc2009" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\Rar$EXb116.8277\Endermanch@AnViPC2009.exe | Endermanch@AnViPC2009.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 9 Modules
| |||||||||||||||
| 488 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9951147323252423840,8150529689024770471,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
73 579
Read events
71 822
Write events
1 678
Delete events
79
Modification events
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
17
Suspicious files
204
Text files
254
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F69947-678.pma | — | |
MD5:— | SHA256:— | |||
| 708 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\~FontCache-S-1-5-21-1302019708-1500728564-335382590-1000.dat | — | |
MD5:— | SHA256:— | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e659fe50-0278-4101-b7cc-653c24cef877.tmp | text | |
MD5:— | SHA256:— | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFda6df.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFda6ef.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
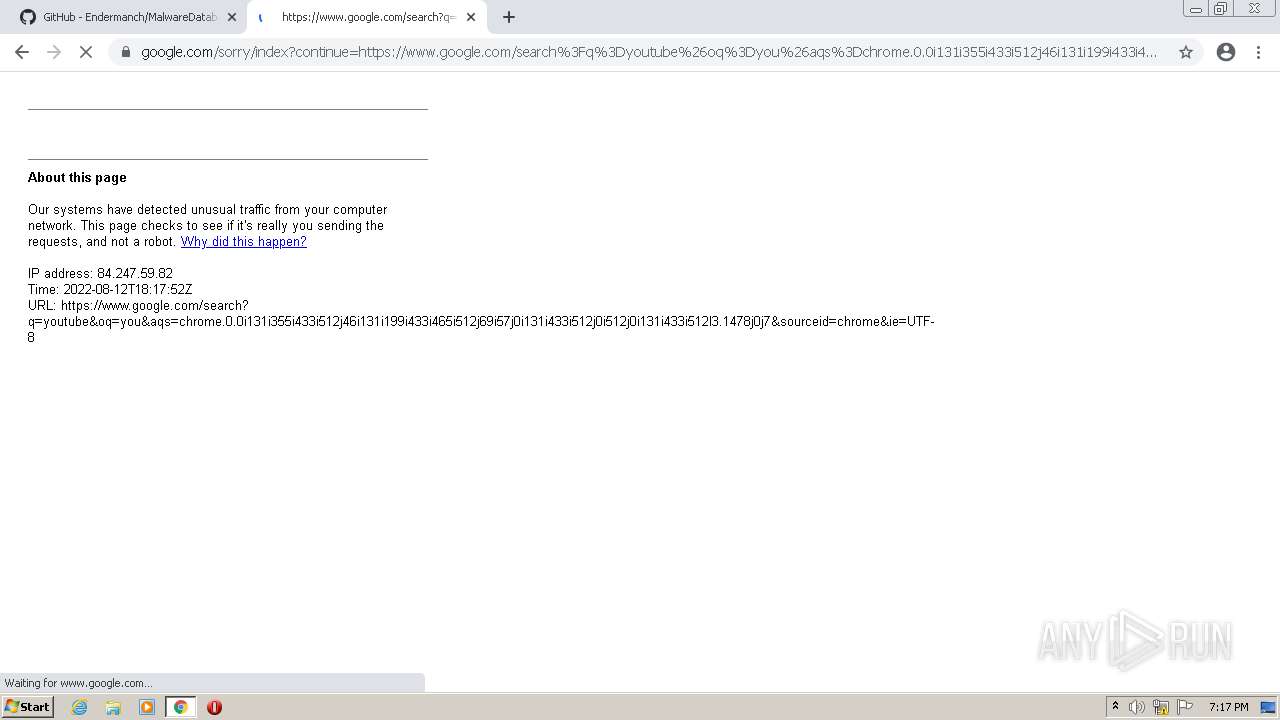
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
115
DNS requests
69
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
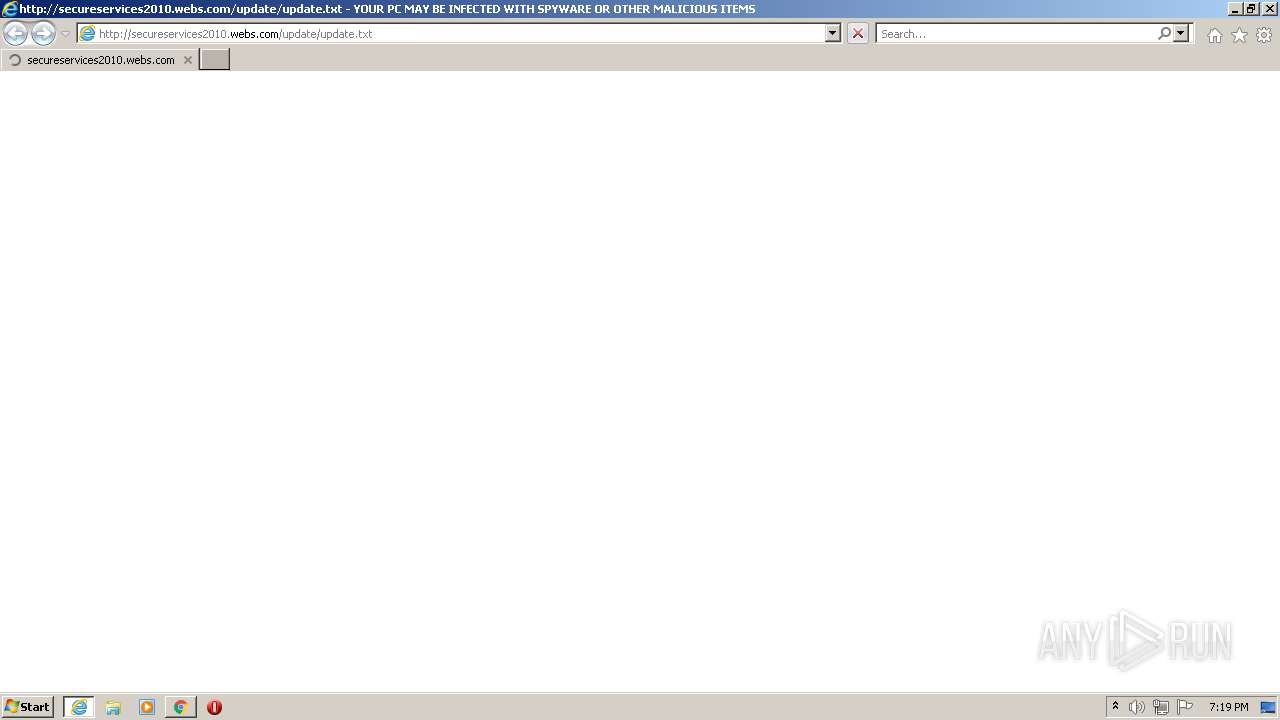
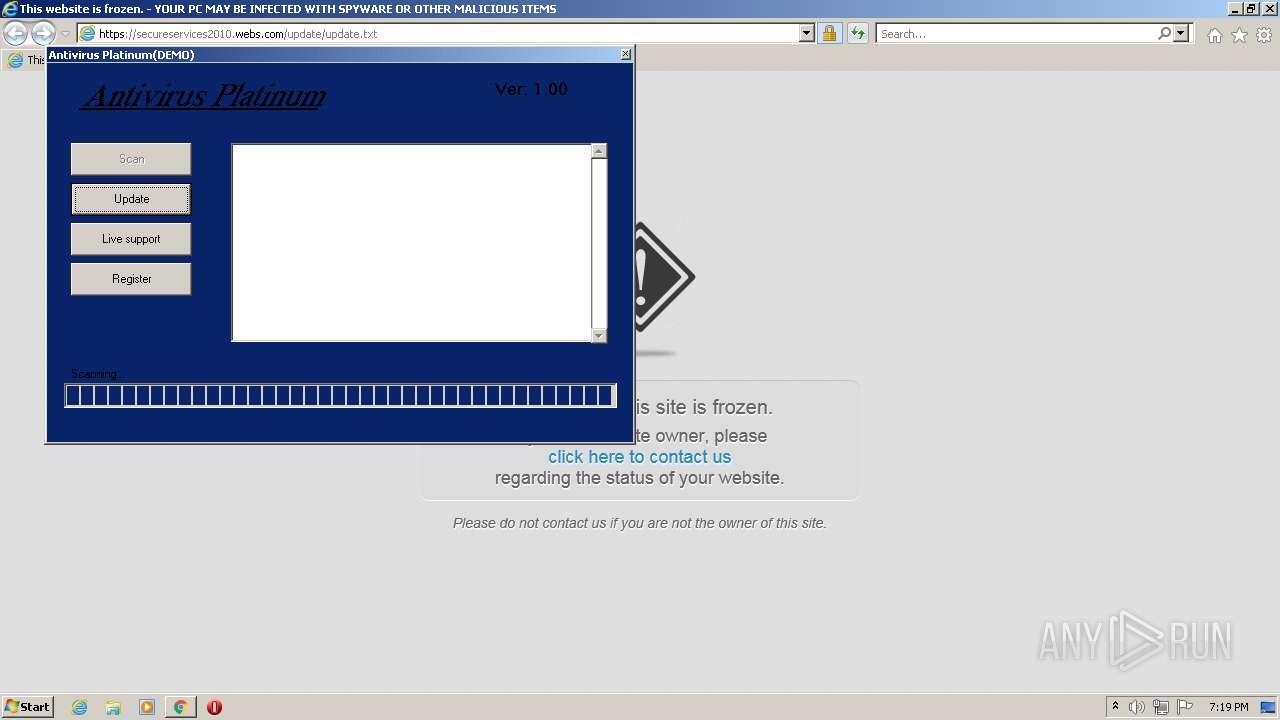
1756 | iexplore.exe | GET | 301 | 104.16.140.31:80 | http://secureservices2010.webs.com/update/update.txt | US | — | — | malicious |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 45.9 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 360 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 20.9 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 2.81 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3588 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3588 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 185.199.108.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | malicious |
3588 | chrome.exe | 172.217.16.138:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
3588 | chrome.exe | 142.250.186.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 140.82.121.6:443 | api.github.com | — | US | suspicious |
3588 | chrome.exe | 140.82.113.22:443 | collector.github.com | — | US | suspicious |
3588 | chrome.exe | 142.250.185.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
github.com |
| malicious |
avatars.githubusercontent.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1756 | iexplore.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |