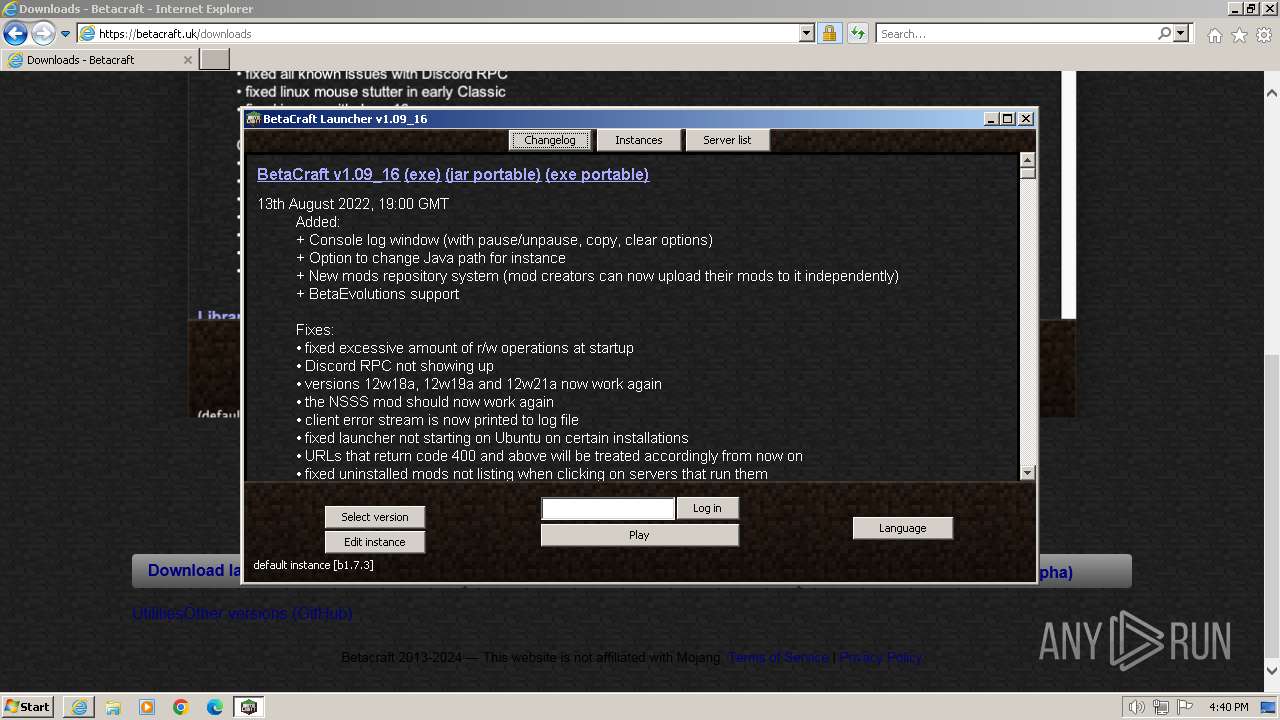
| URL: | https://betacraft.uk/ |
| Full analysis: | https://app.any.run/tasks/6e9e7eef-40d6-43d2-b023-97ce209cfcc4 |
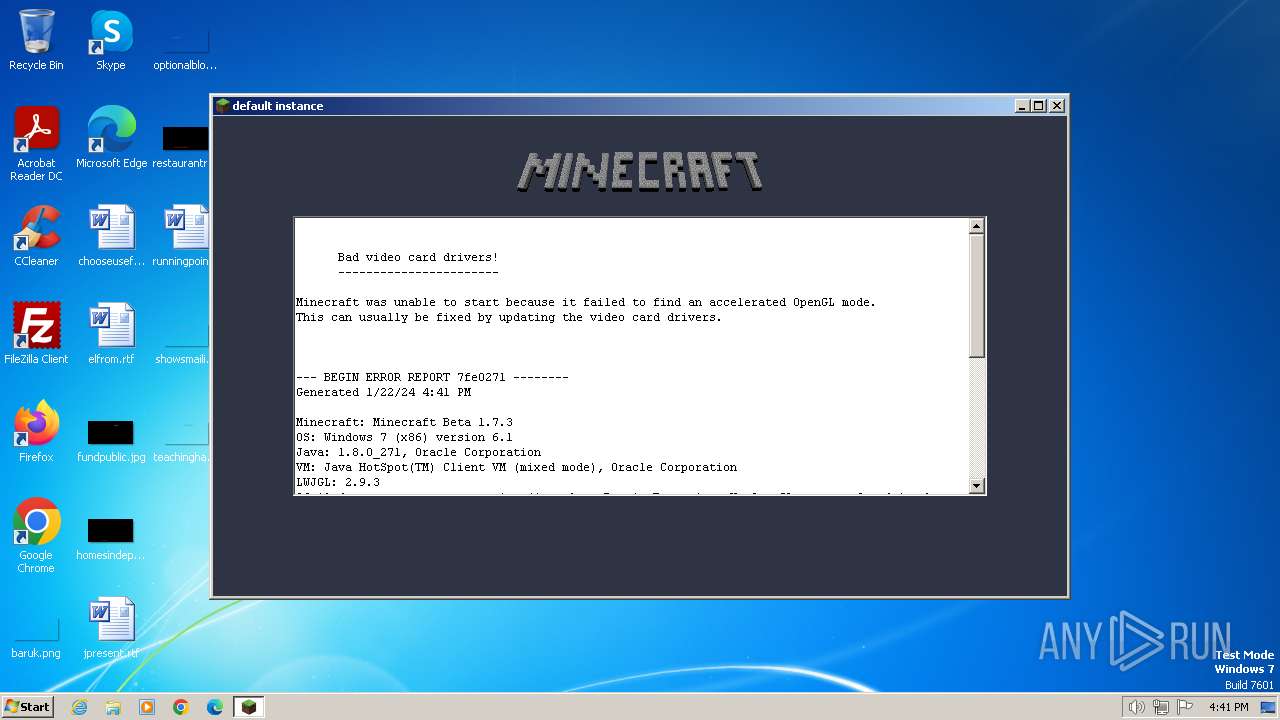
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2024, 16:40:01 |
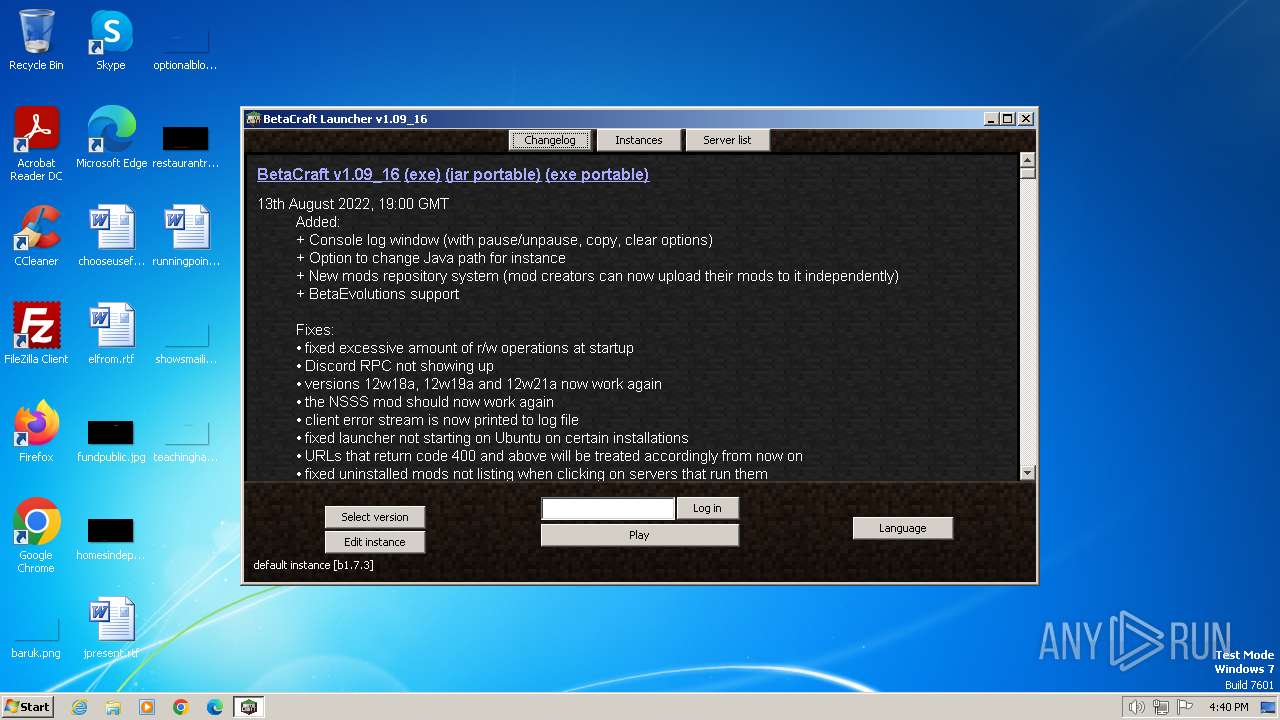
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6D59B53ABBEABE135EE5A3478FBDCD54 |
| SHA1: | 78450897ACBF2323C18267BD1ED670CB4DF678B3 |
| SHA256: | DBBFA85AC06B4B0C7A19A86976320000CE7198D4C087BED5E5453CDEF4863A8D |
| SSDEEP: | 3:N8bGatQOKn:2EOK |
MALICIOUS
Actions looks like stealing of personal data
- java.exe (PID: 2672)
Drops the executable file immediately after the start
- java.exe (PID: 2672)
- javaw.exe (PID: 1768)
SUSPICIOUS
Process requests binary or script from the Internet
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
Executable content was dropped or overwritten
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
Connects to unusual port
- java.exe (PID: 2672)
INFO
Create files in a temporary directory
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
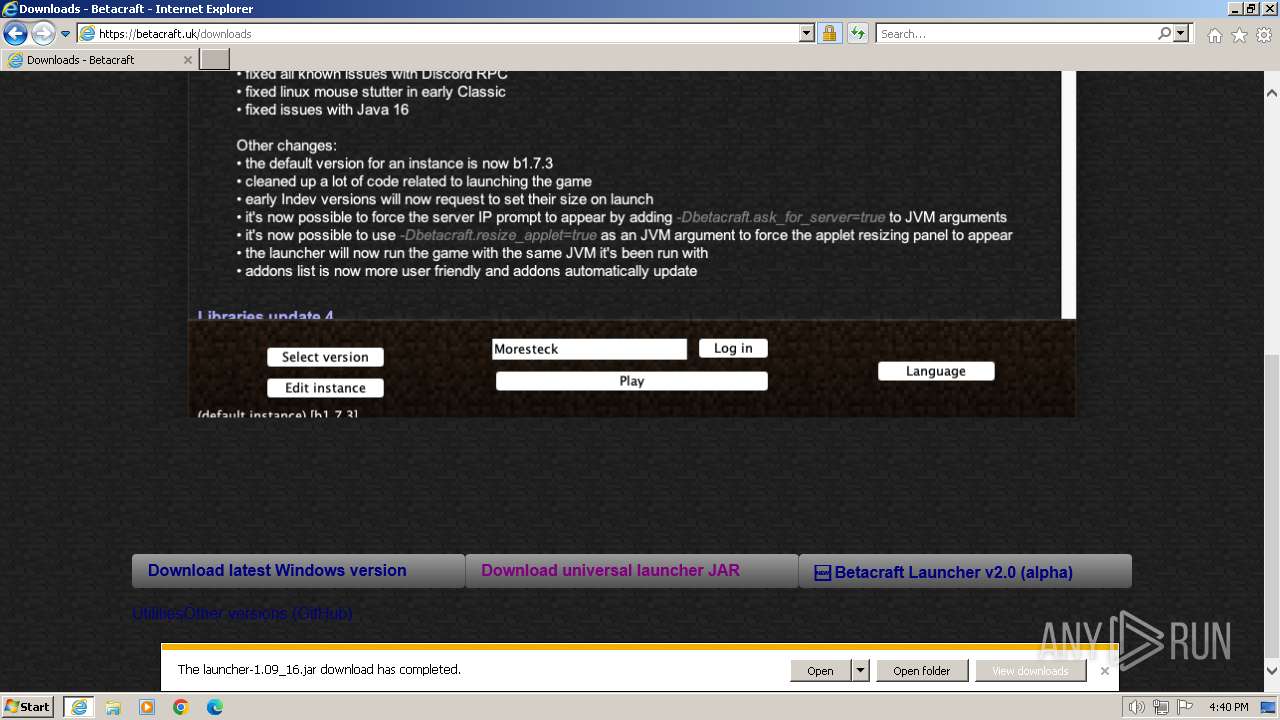
The process uses the downloaded file
- iexplore.exe (PID: 2040)
Checks supported languages
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
Application launched itself
- iexplore.exe (PID: 2040)
Creates files in the program directory
- javaw.exe (PID: 1768)
Creates files or folders in the user directory
- java.exe (PID: 2672)
- javaw.exe (PID: 1768)
Reads the computer name
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
Reads the machine GUID from the registry
- javaw.exe (PID: 1768)
- java.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225547 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
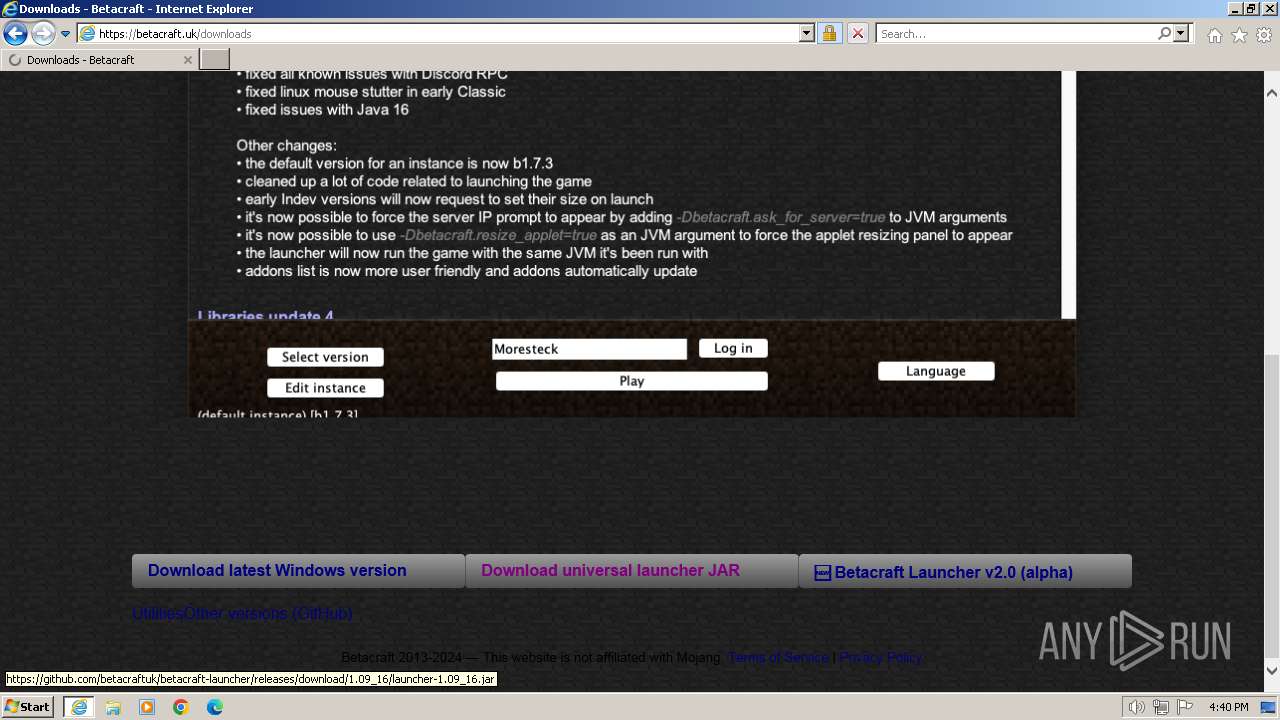
| 1768 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\Downloads\launcher-1.09_16.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://betacraft.uk/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
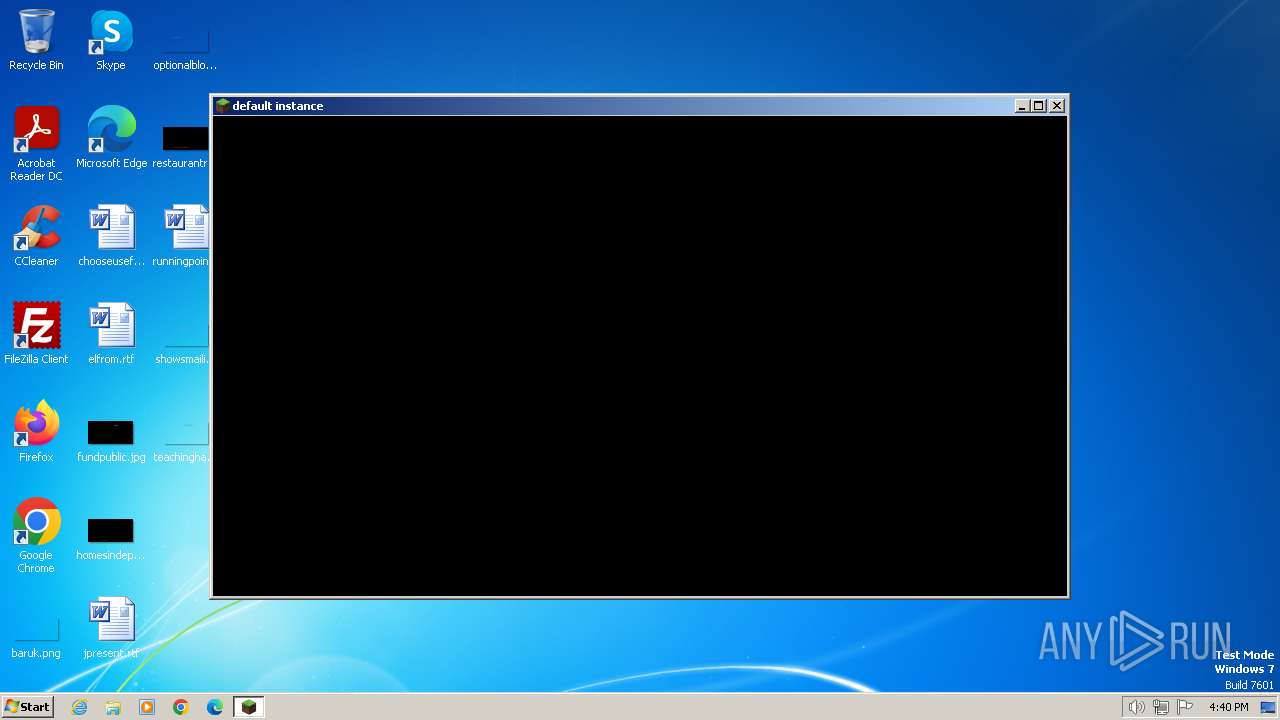
| 2672 | "C:\Program Files\Java\jre1.8.0_271\bin\java.exe" -XX:HeapDumpPath=java.exe_minecraft.exe.heapdump -Djava.util.Arrays.useLegacyMergeSort=true -Dhttp.nonProxyHosts=api.betacraft.uk|files.betacraft.uk|checkip.amazonaws.com -Xmx1G -Dhttp.proxyHost=betacraft.uk -Dhttp.proxyPort=11705 -cp C:\Users\admin\AppData\Roaming\.betacraft\launcher\betacraft_wrapper.jar;C:\Users\admin\AppData\Roaming\.betacraft\launcher\discord_rpc.jar org.betacraft.launcher.Launcher wrap AAA - - - - "default instance" | C:\Program Files\Java\jre1.8.0_271\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2760 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 717
Read events
18 631
Write events
81
Delete events
5
Modification events
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
11
Suspicious files
46
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:40413D502DC60E411A32818C8E5E46A2 | SHA256:229A051933BA0A2157FE14D53B775D3DFBC50C2960C3CC8D0FE35E0439DD7B6E | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab964.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:69140148FF4FBD97B121B8BD3651D129 | SHA256:5B96D354D5883E441BF2DF82BC6C5620288721917691205C85FCE154B5AD255E | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MMWFX6P1.txt | text | |
MD5:9FBF09297BD0B2EBFFBD6988585A5D98 | SHA256:7CA6561D2F184306E8B3E828D70B625EEBE699DB2DBB96C09D5F9E79B4BD9935 | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\LCKTQH20.htm | html | |
MD5:9F9E208CE930E209BC0D7730504D5622 | SHA256:9A6432639D13710B46CD2291B03AC058B2718FB68237E0B44AA9E12411E01343 | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\BluemapBanner[1].png | image | |
MD5:38A69B3E6DB3FC2C56652AD0DDBDCA11 | SHA256:0E01B9D62C3FE8C37BEAC8614CF4A159D0D9461F86ECD1E577B5C4AD096A437B | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\logo[1].png | image | |
MD5:538843A8F01F2AC8171D84645FFA9D6E | SHA256:32085081693091F830143CE5B5999931F463DBDE3B87AFDCF227B024BB265E26 | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\trailer[1].webp | image | |
MD5:22D5D64A6D15EC728C26296453FCAC59 | SHA256:499607A868AE9A24514251B995CC98424EACC697767F41C2F4CBA7DA11828514 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
44
DNS requests
21
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | iexplore.exe | GET | 200 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6f825234c2810feb | unknown | compressed | 4.66 Kb | unknown |
864 | iexplore.exe | GET | 200 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f1ccb56d74be6756 | unknown | compressed | 4.66 Kb | unknown |
864 | iexplore.exe | GET | 200 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7a9d8baceff24343 | unknown | compressed | 65.2 Kb | unknown |
864 | iexplore.exe | GET | 200 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b25bf5dc542a1974 | unknown | compressed | 65.2 Kb | unknown |
864 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
864 | iexplore.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTxDAl0%2FPpEvD7NFMDkjgeIlg%3D%3D | unknown | binary | 503 b | unknown |
2040 | iexplore.exe | GET | 304 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | unknown | — | — | unknown |
2040 | iexplore.exe | GET | 304 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?973bc8aa769c2f5e | unknown | — | — | unknown |
2040 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | unknown |
864 | iexplore.exe | 49.12.205.146:443 | betacraft.uk | Hetzner Online GmbH | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
864 | iexplore.exe | 184.24.77.193:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
864 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
864 | iexplore.exe | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2040 | iexplore.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2040 | iexplore.exe | 49.12.205.146:443 | betacraft.uk | Hetzner Online GmbH | DE | unknown |
2040 | iexplore.exe | 184.24.77.193:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
betacraft.uk |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
ocsp.digicert.com |
| whitelisted |
github.com |
| shared |
objects.githubusercontent.com |
| shared |
files.betacraft.uk |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1768 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1768 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
2672 | java.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
2 ETPRO signatures available at the full report