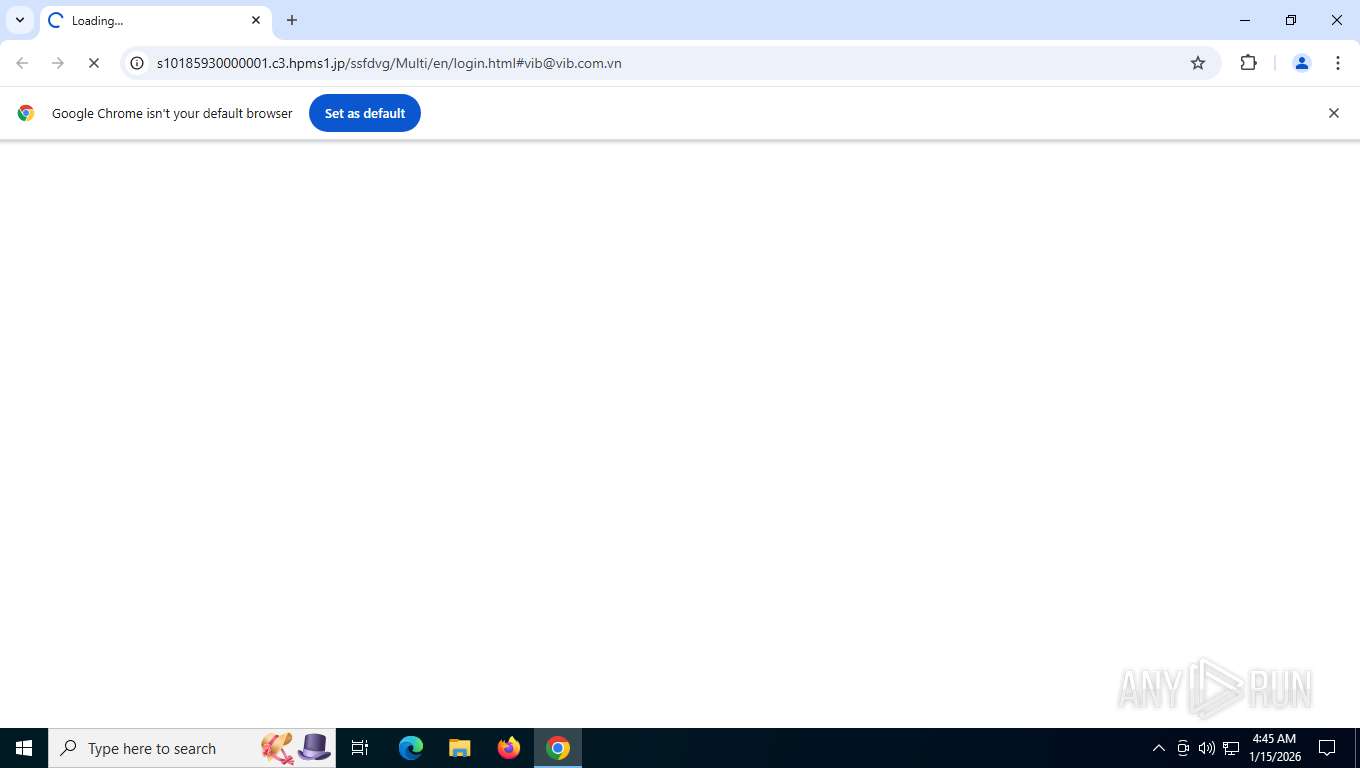
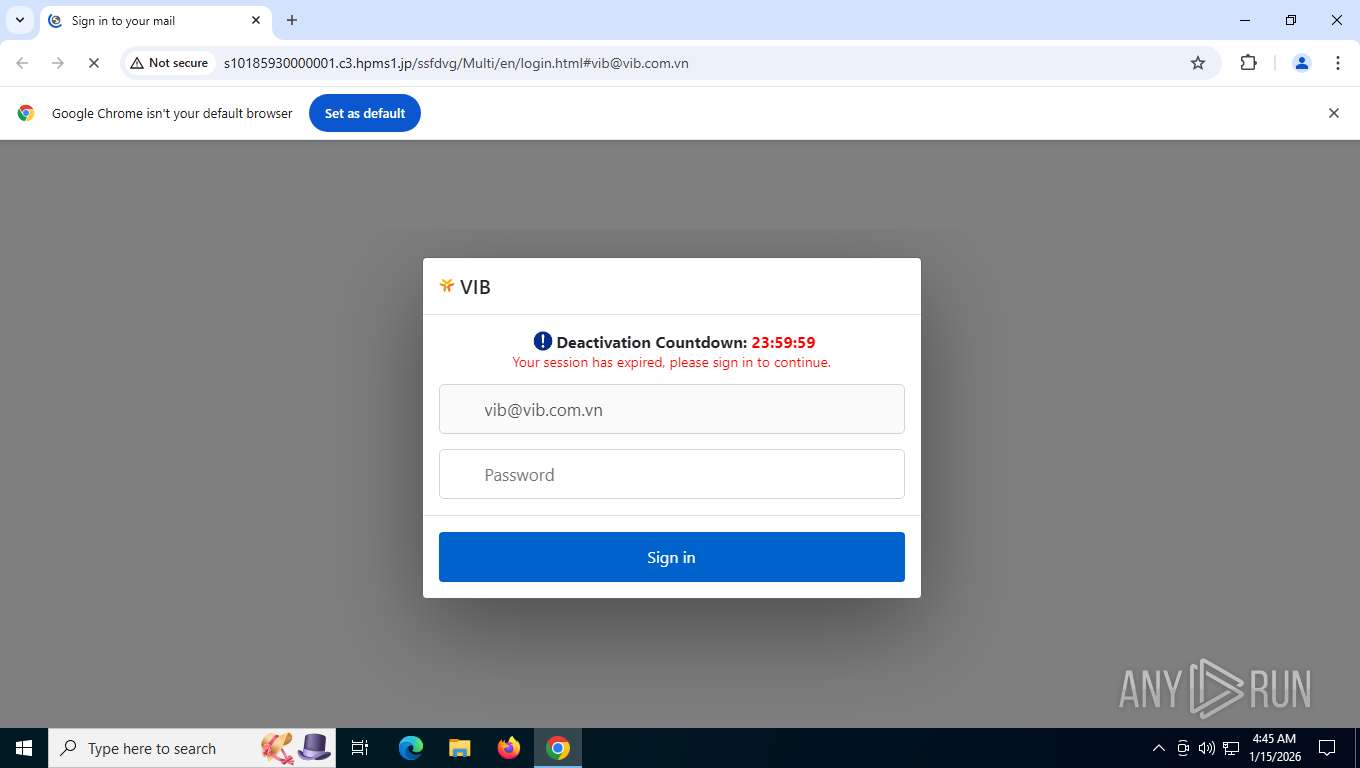
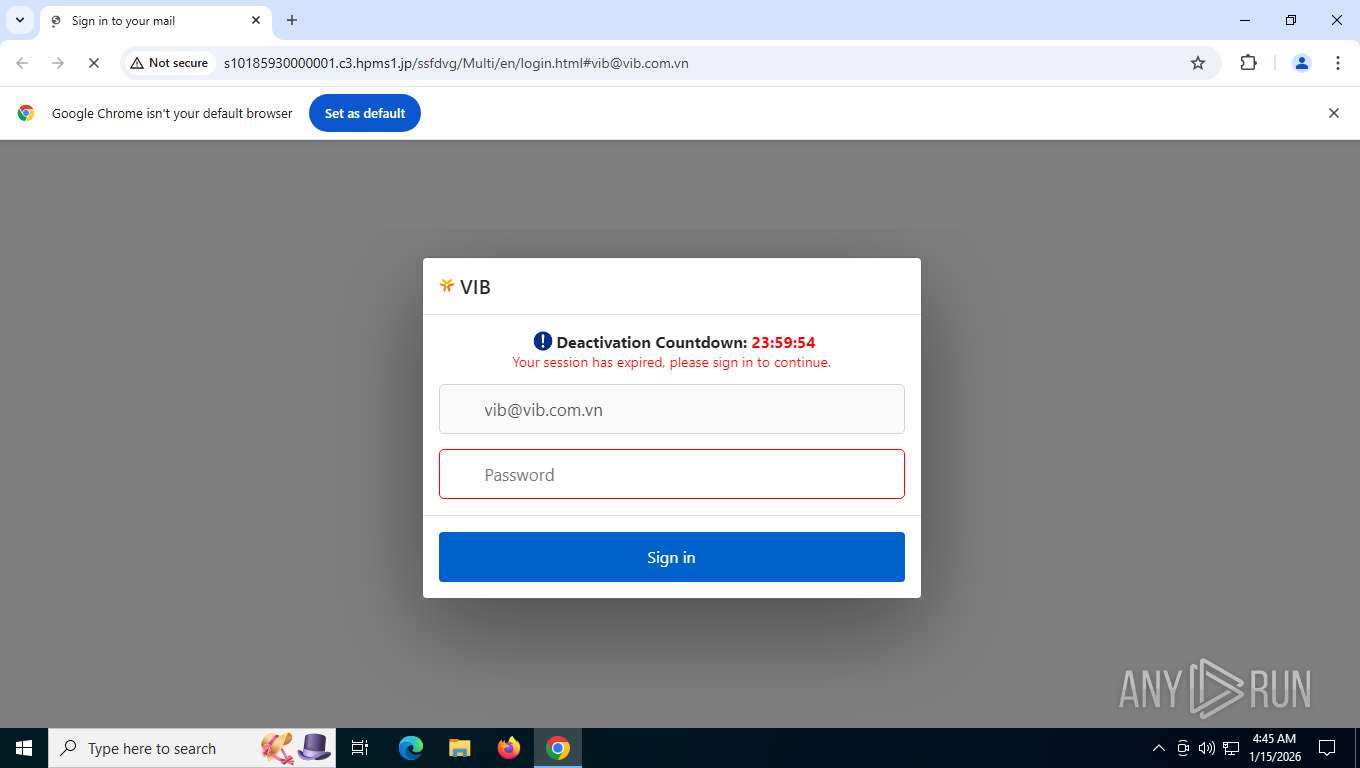
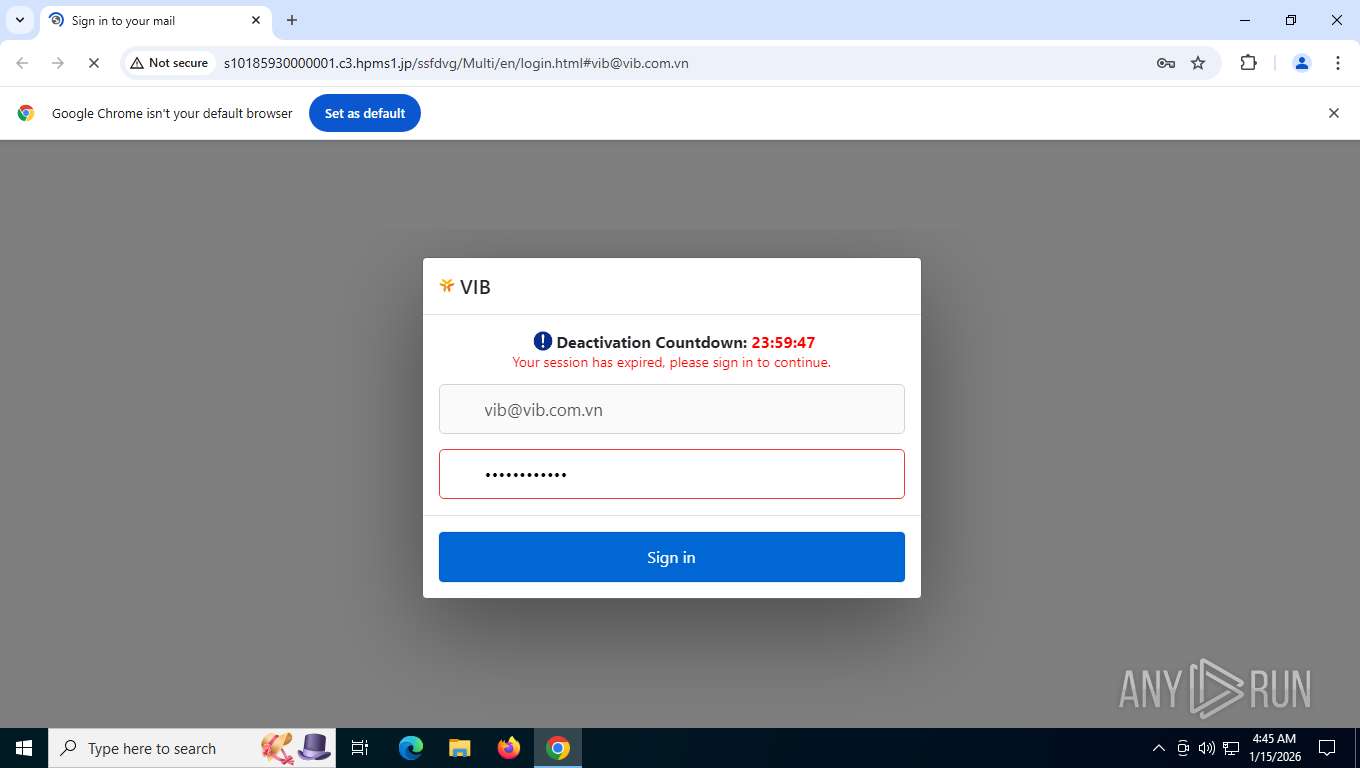
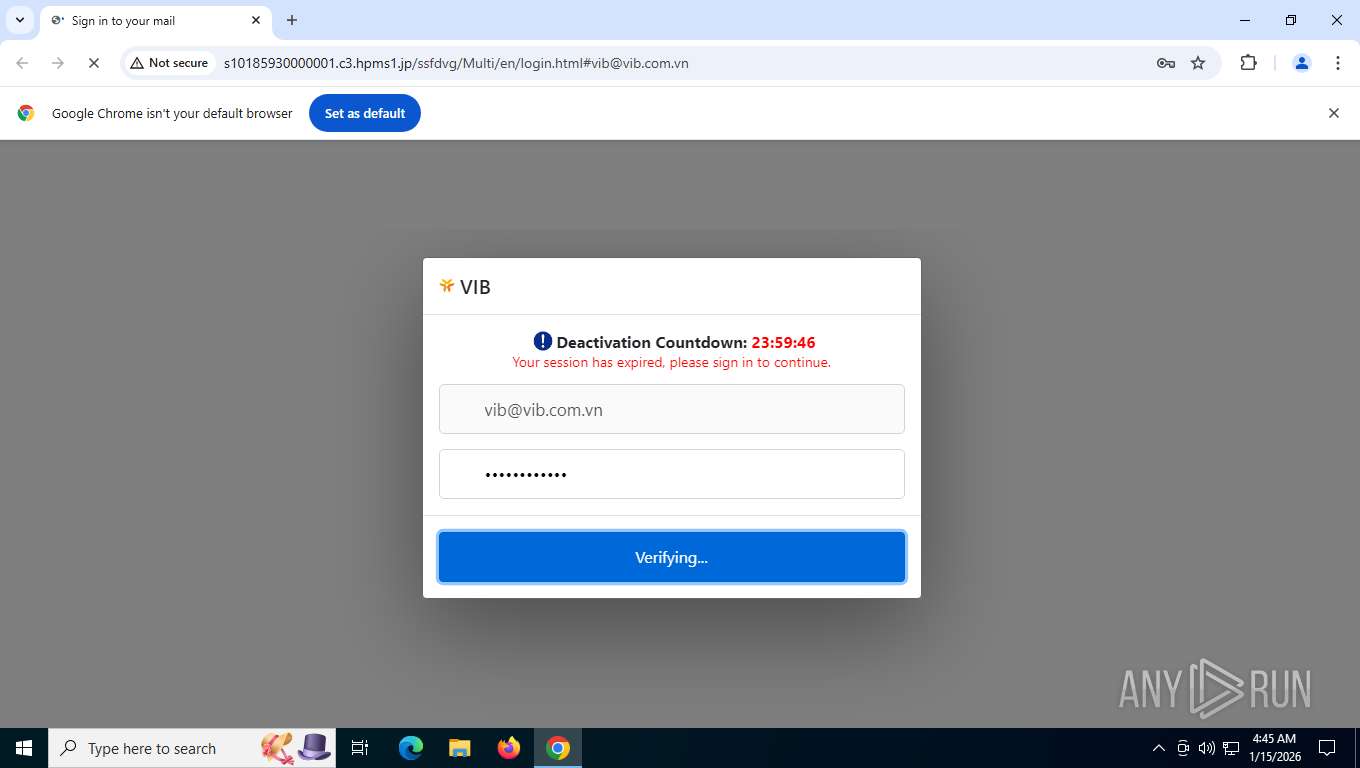
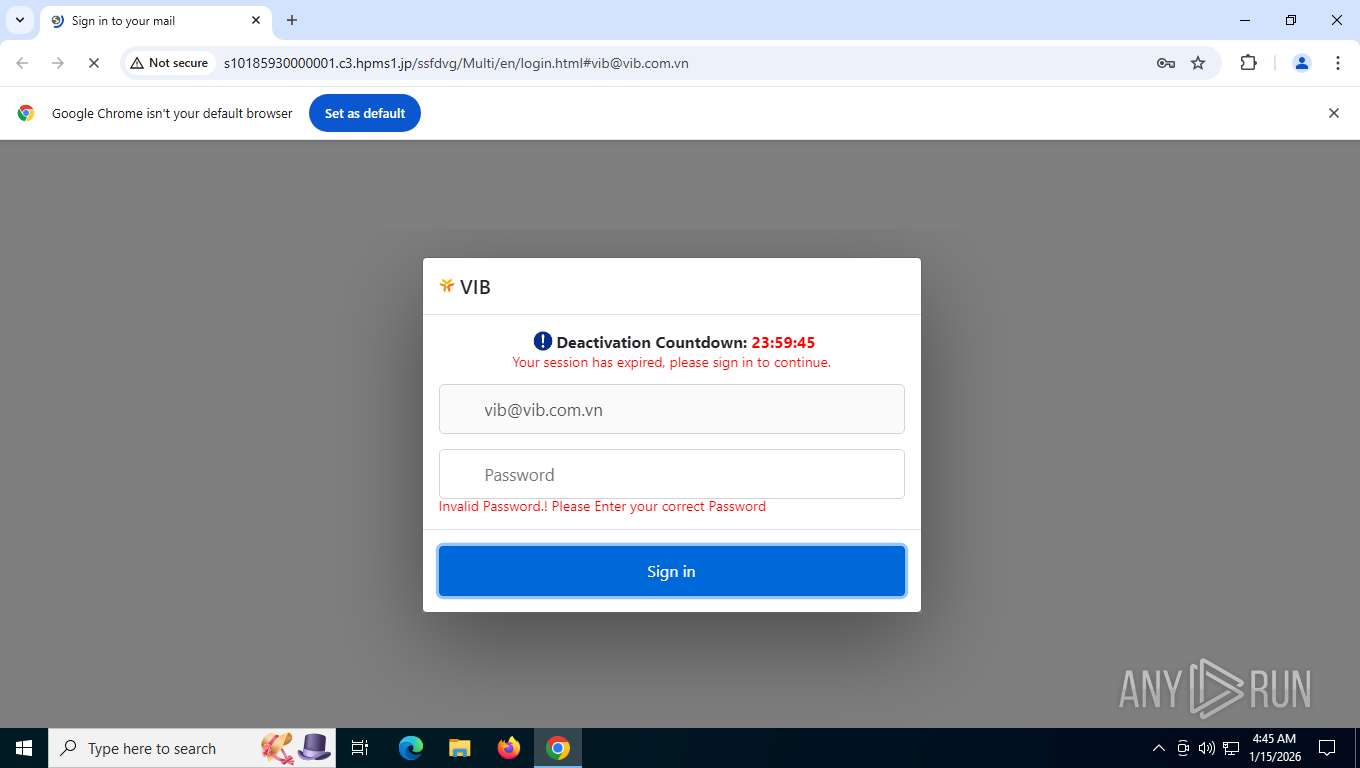
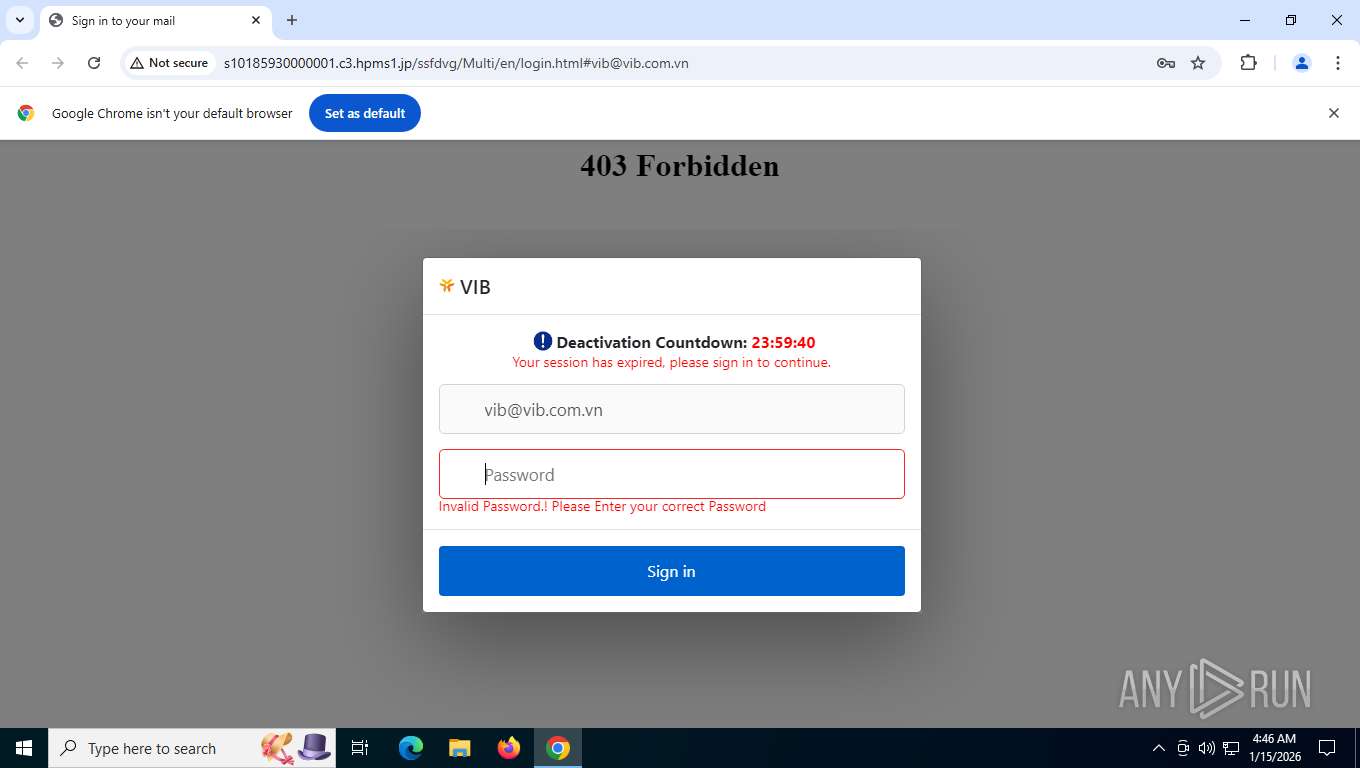
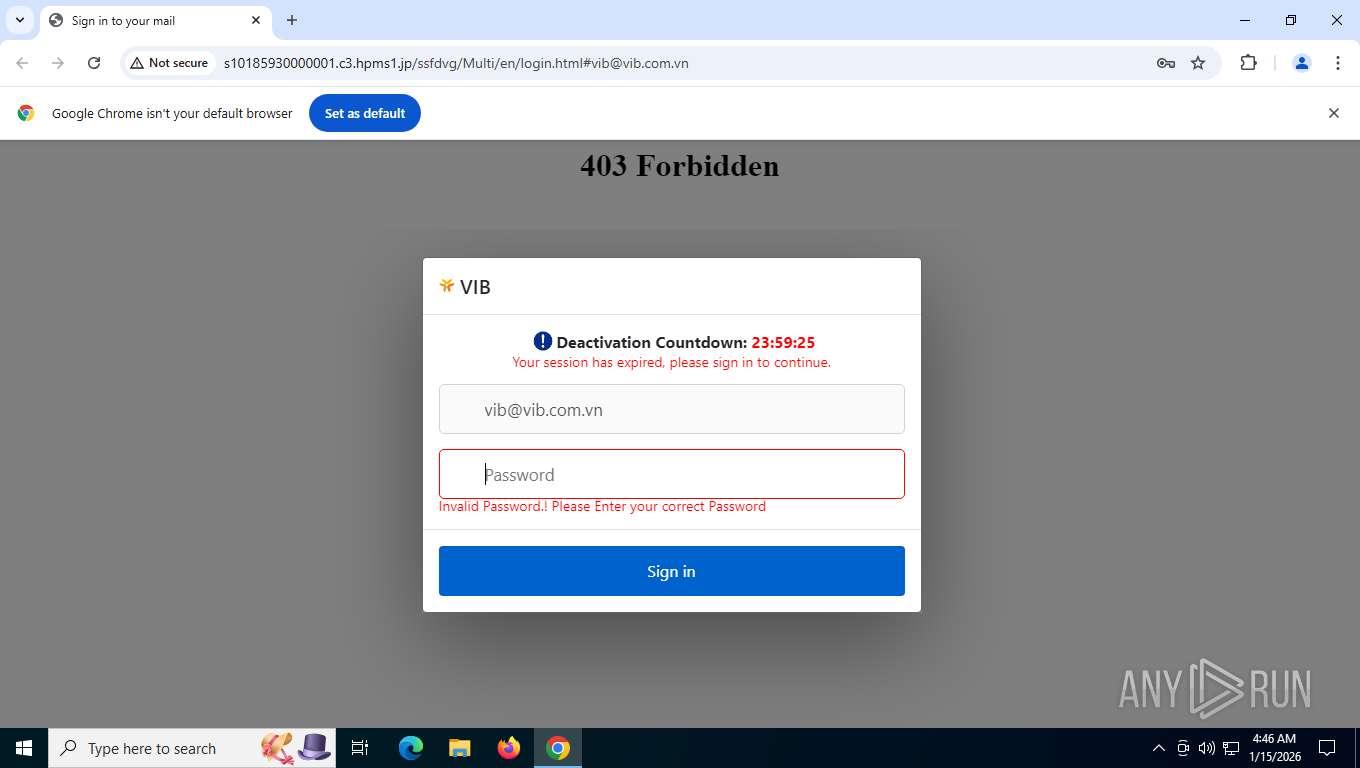
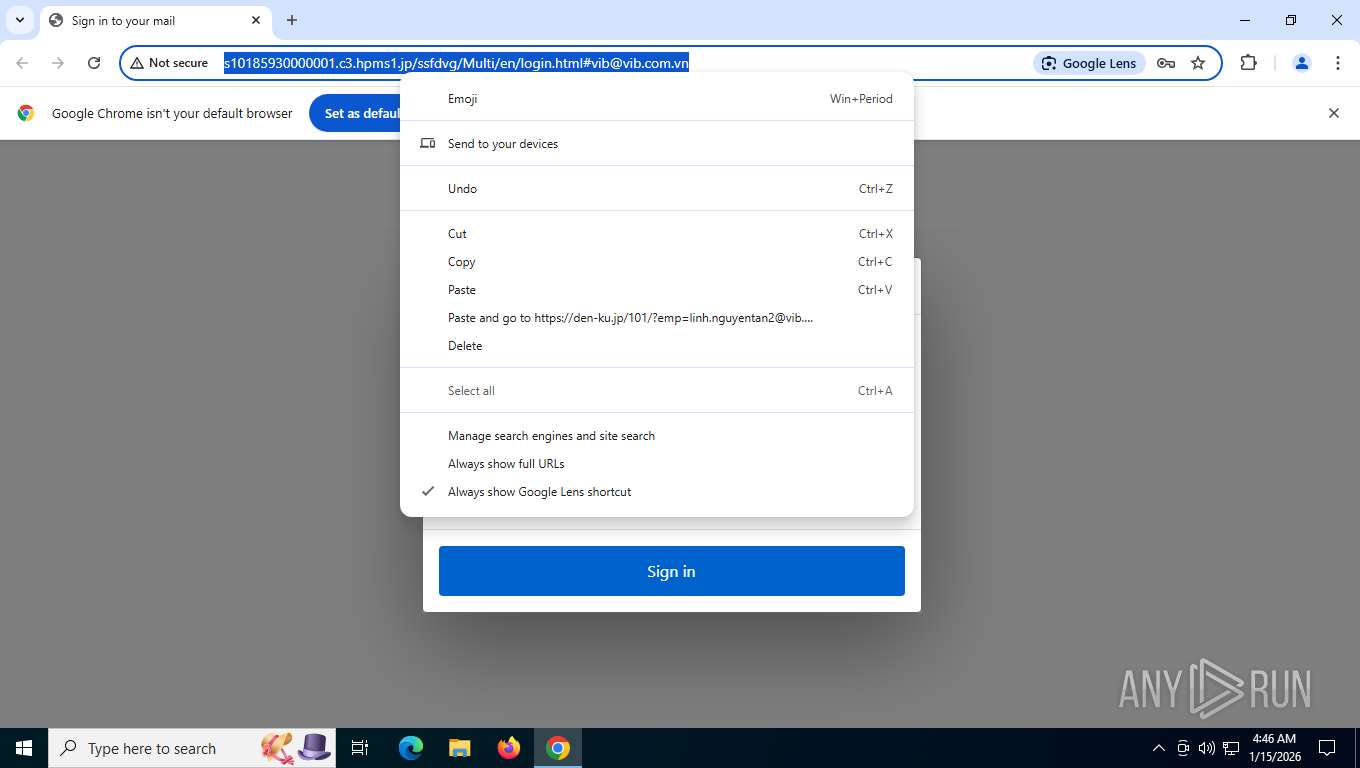
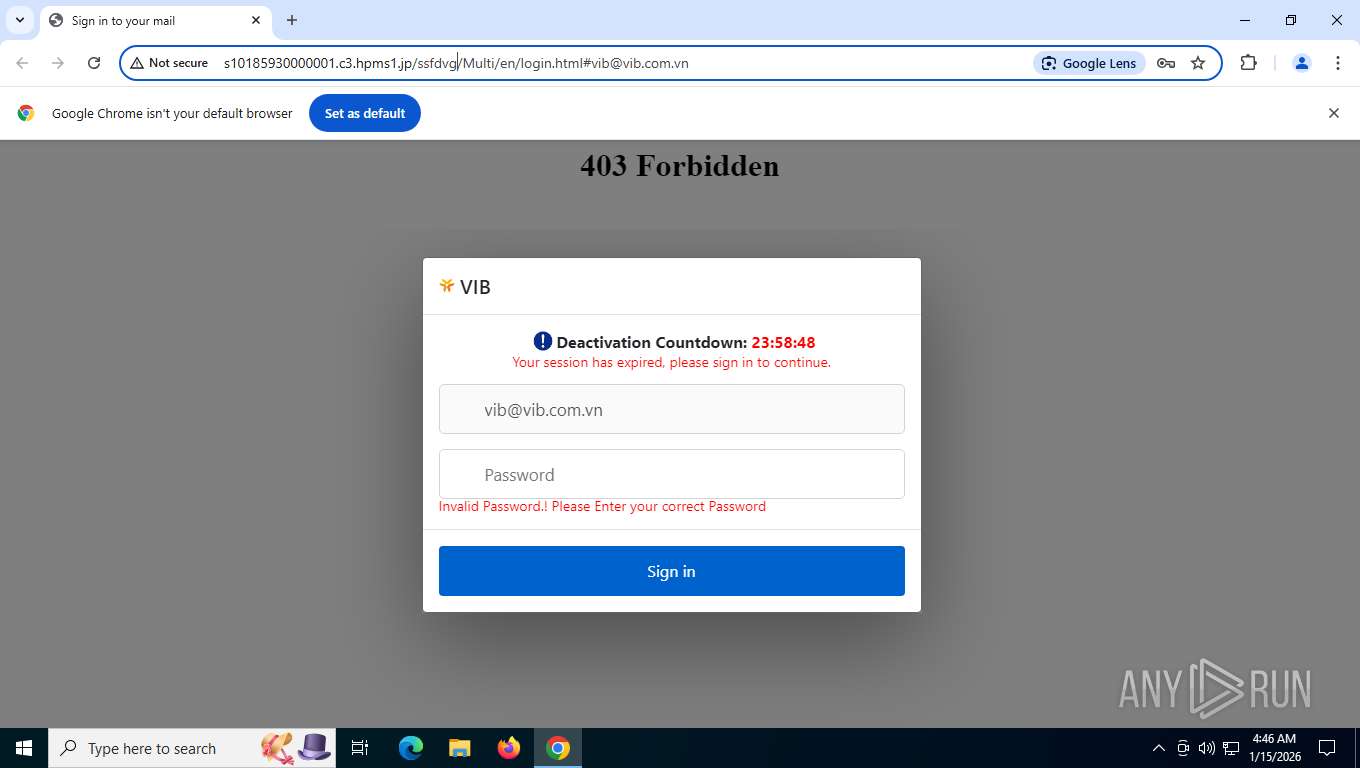
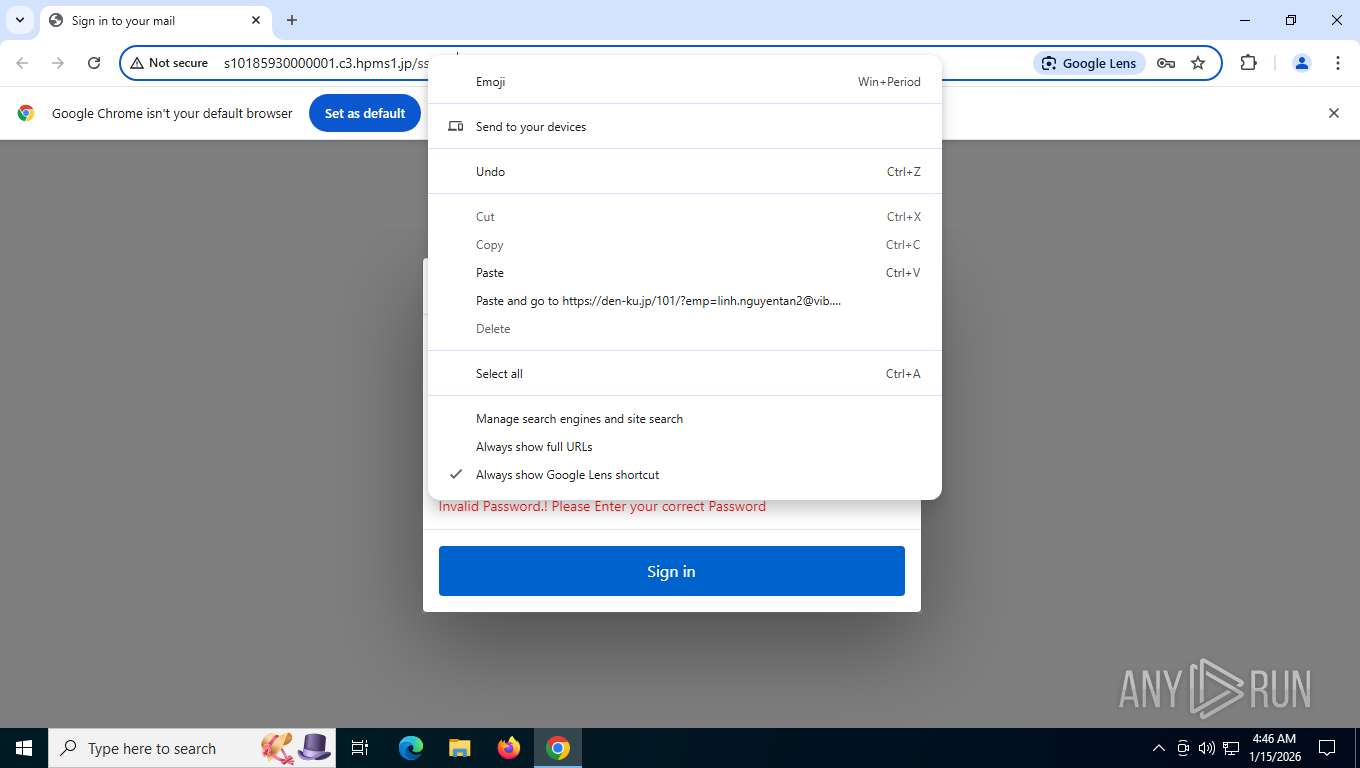
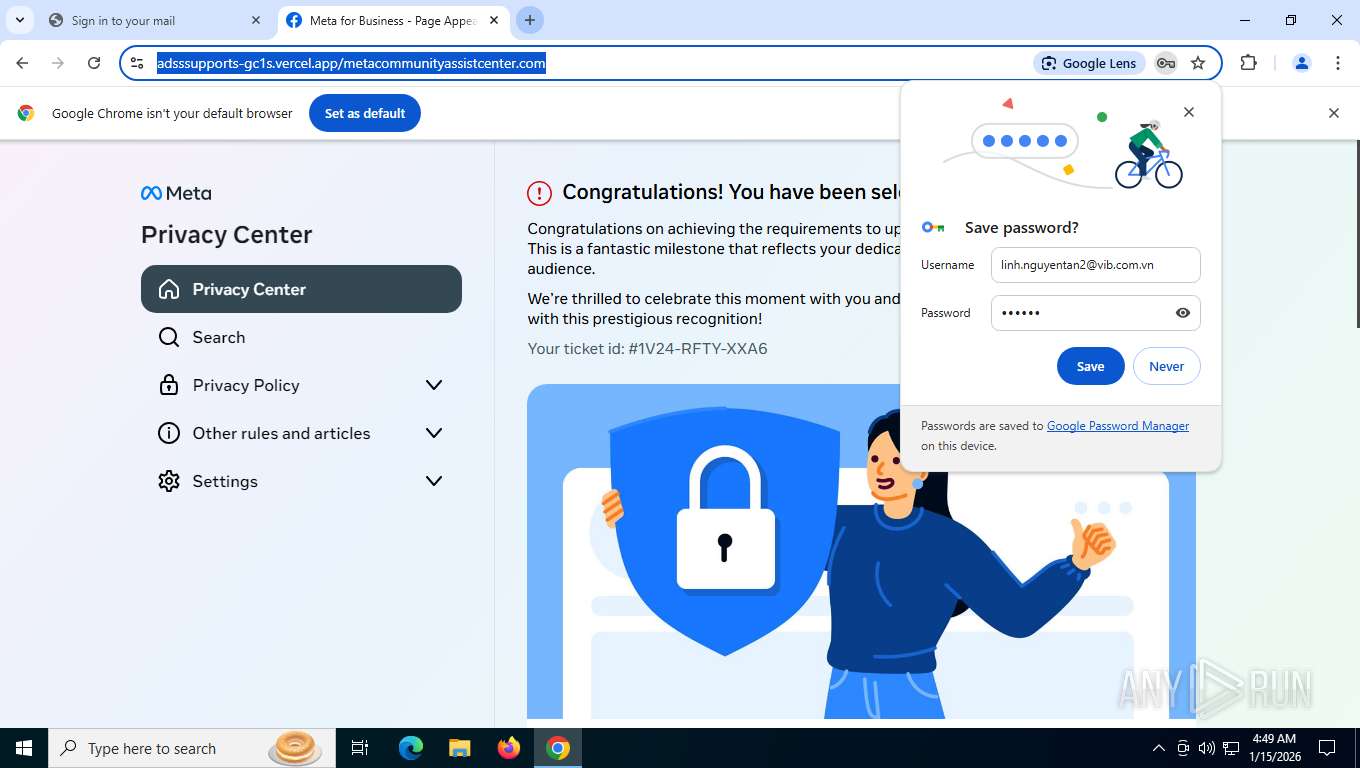
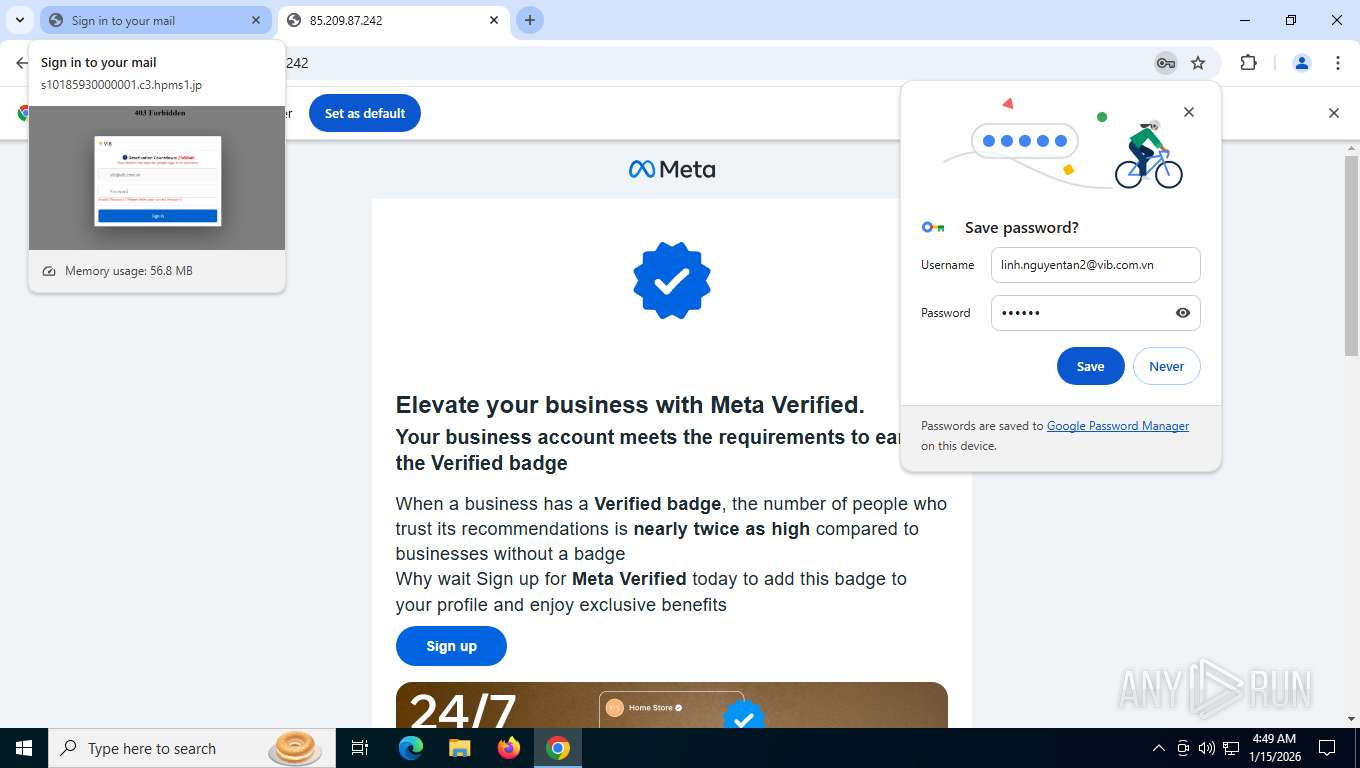
| URL: | http://s10185930000001.c3.hpms1.jp/ssfdvg/Multi/en/login.html#vib@vib.com.vn |
| Full analysis: | https://app.any.run/tasks/4562ed4e-e8a7-4159-acbb-090b22cc2d35 |
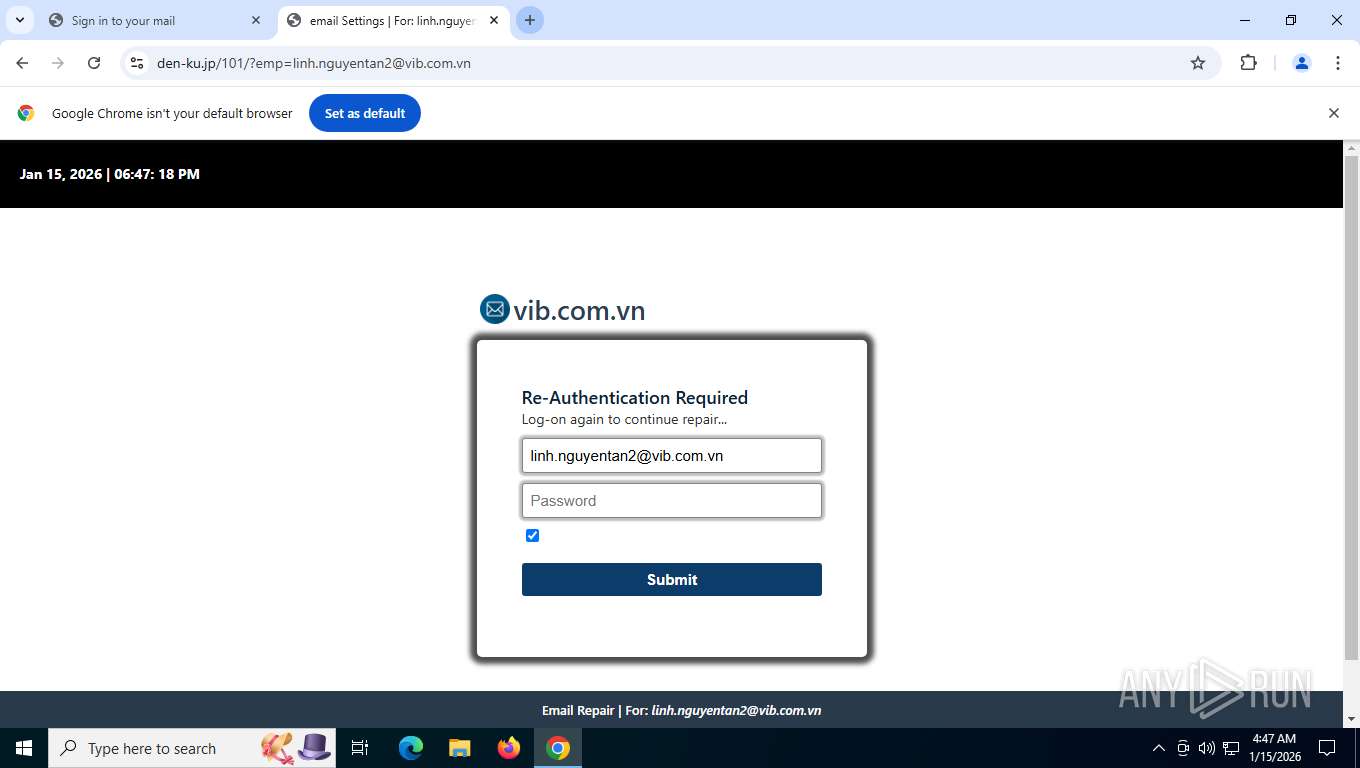
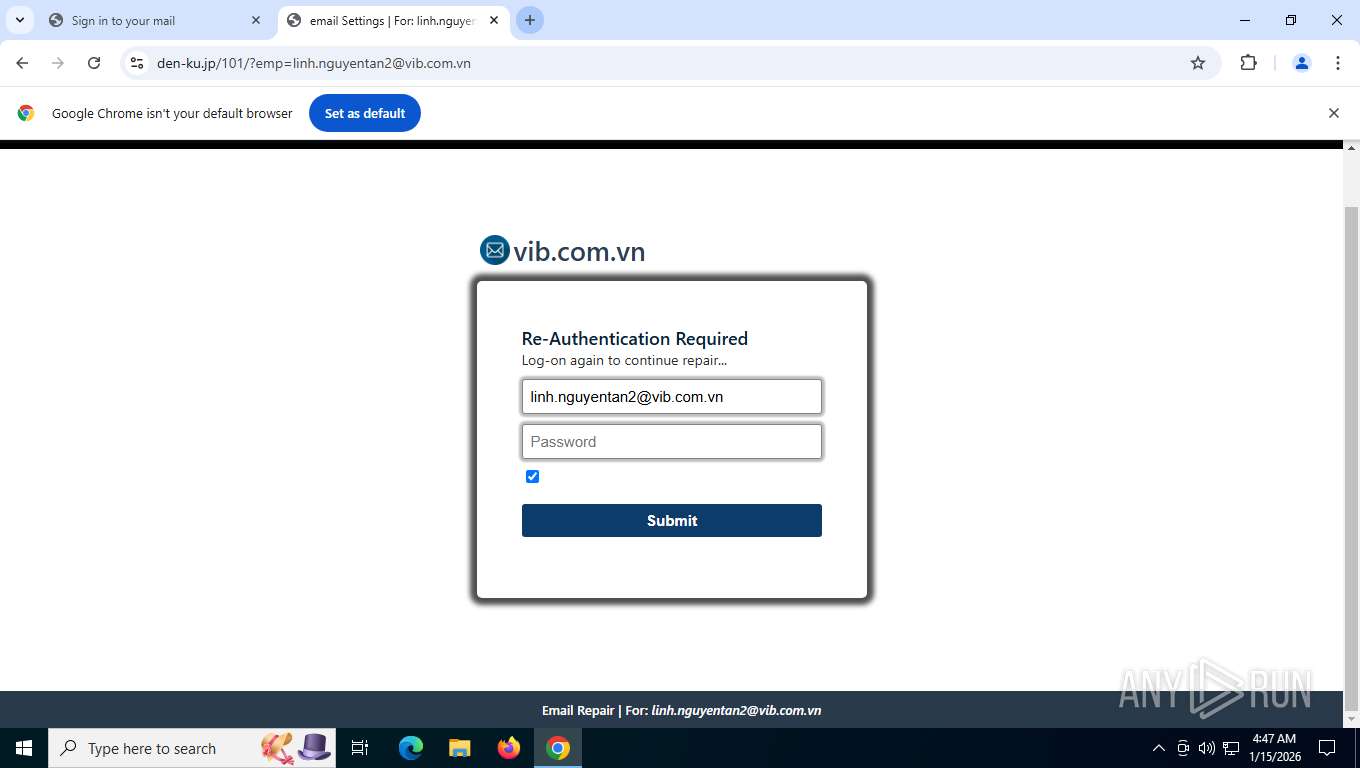
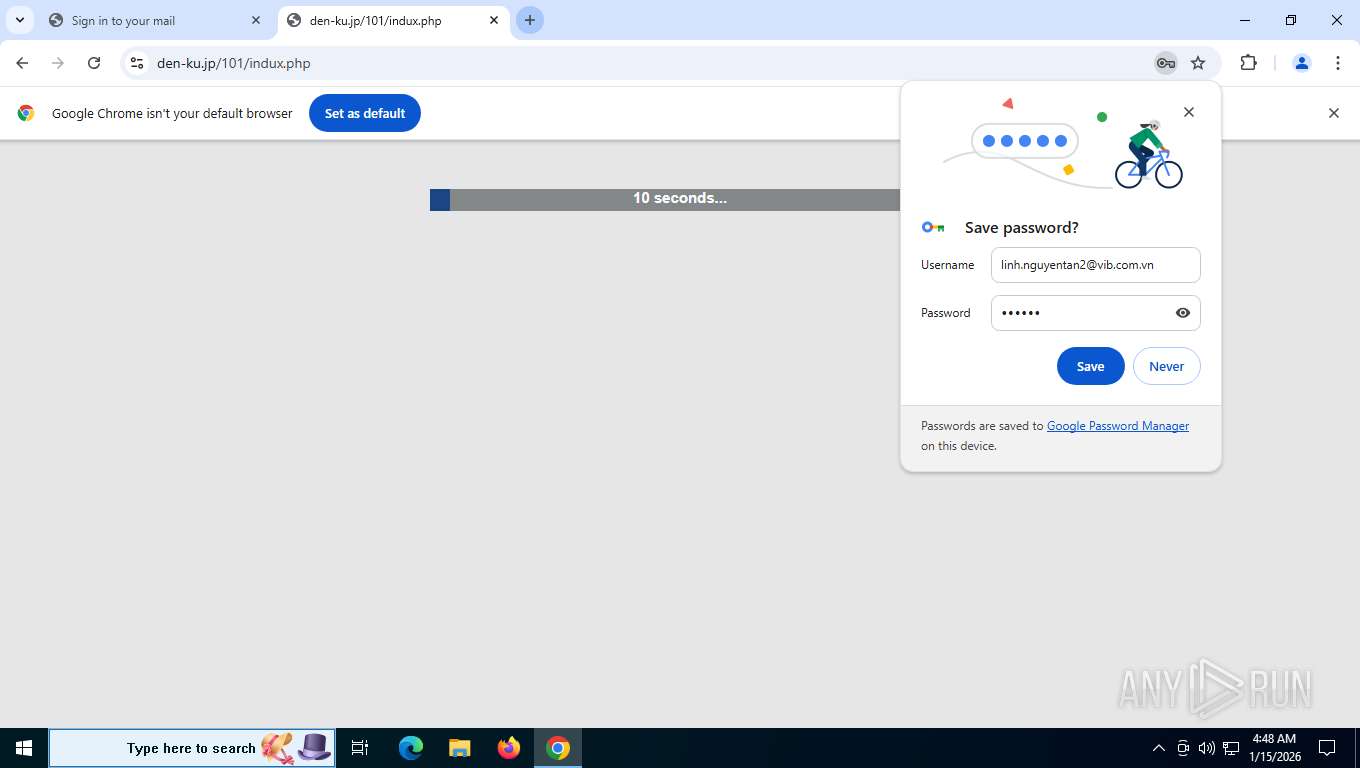
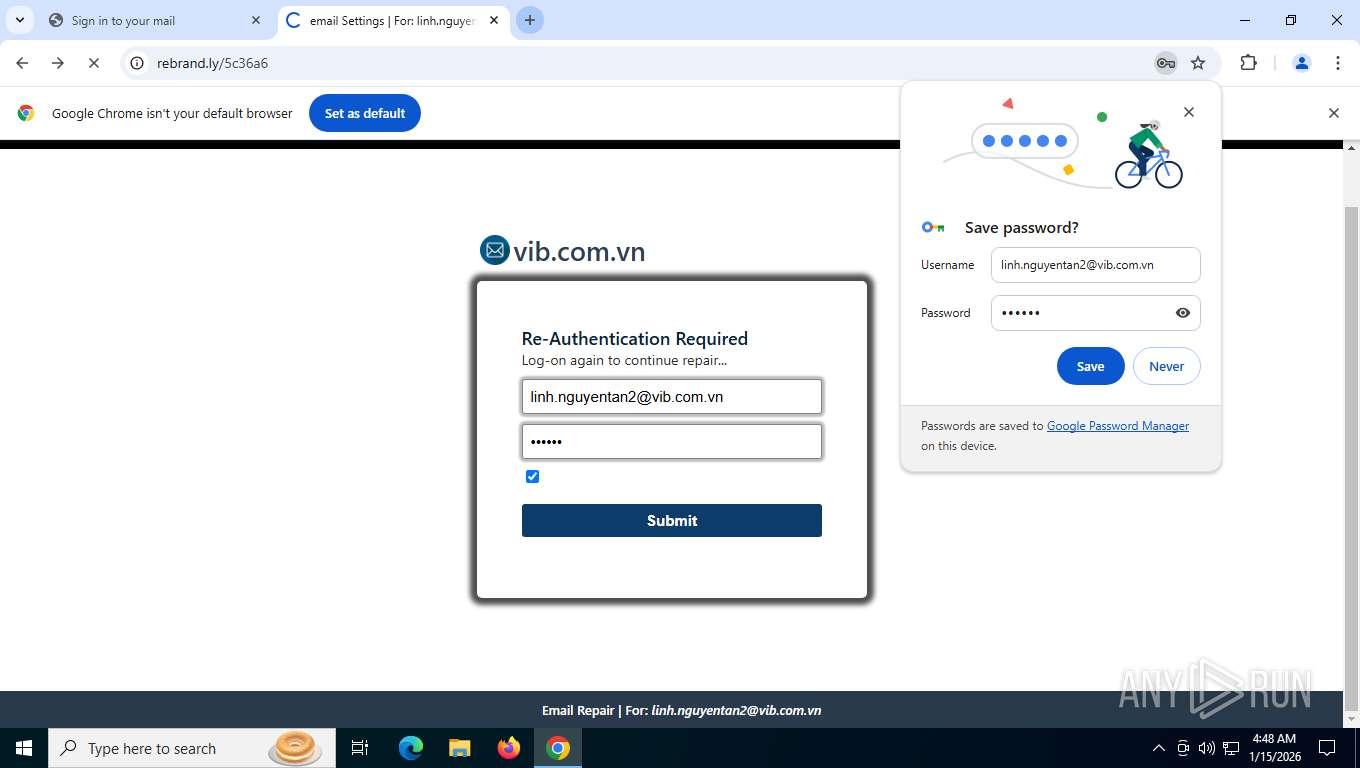
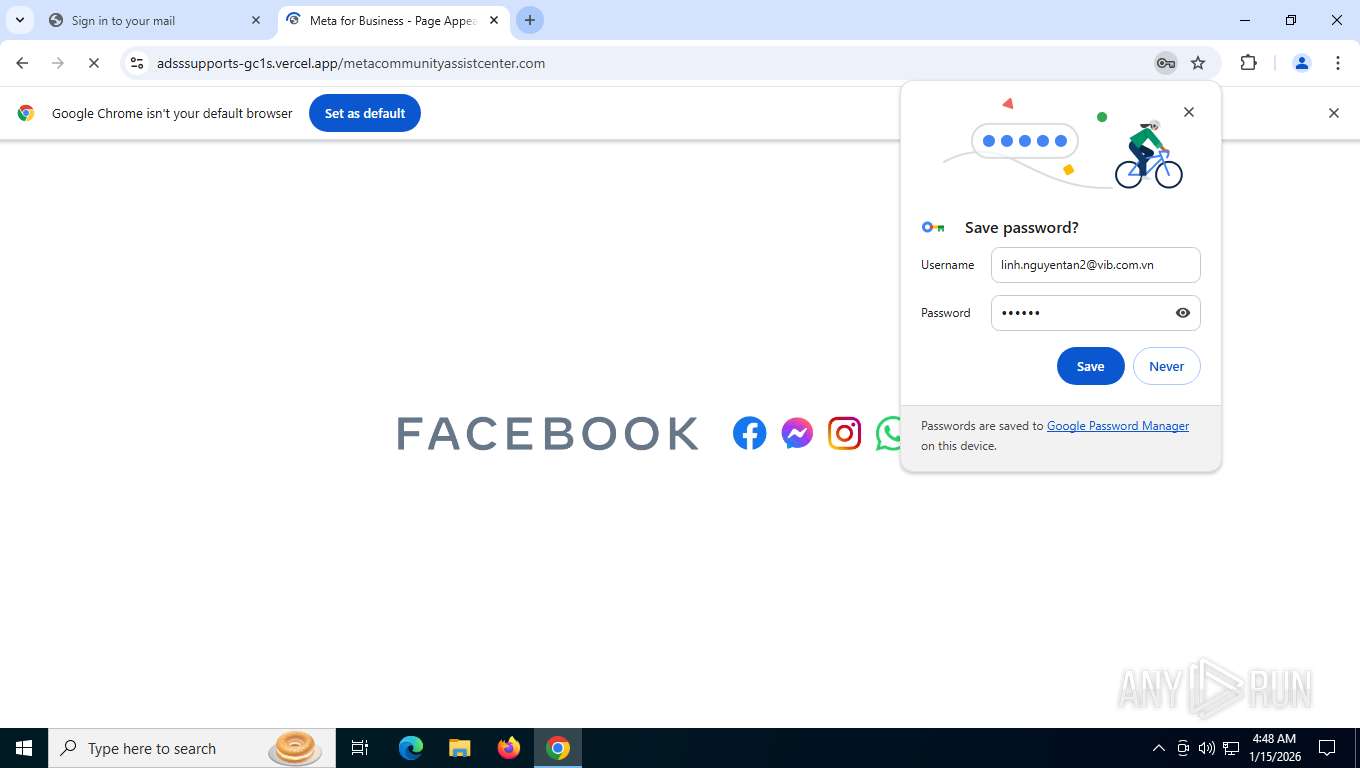
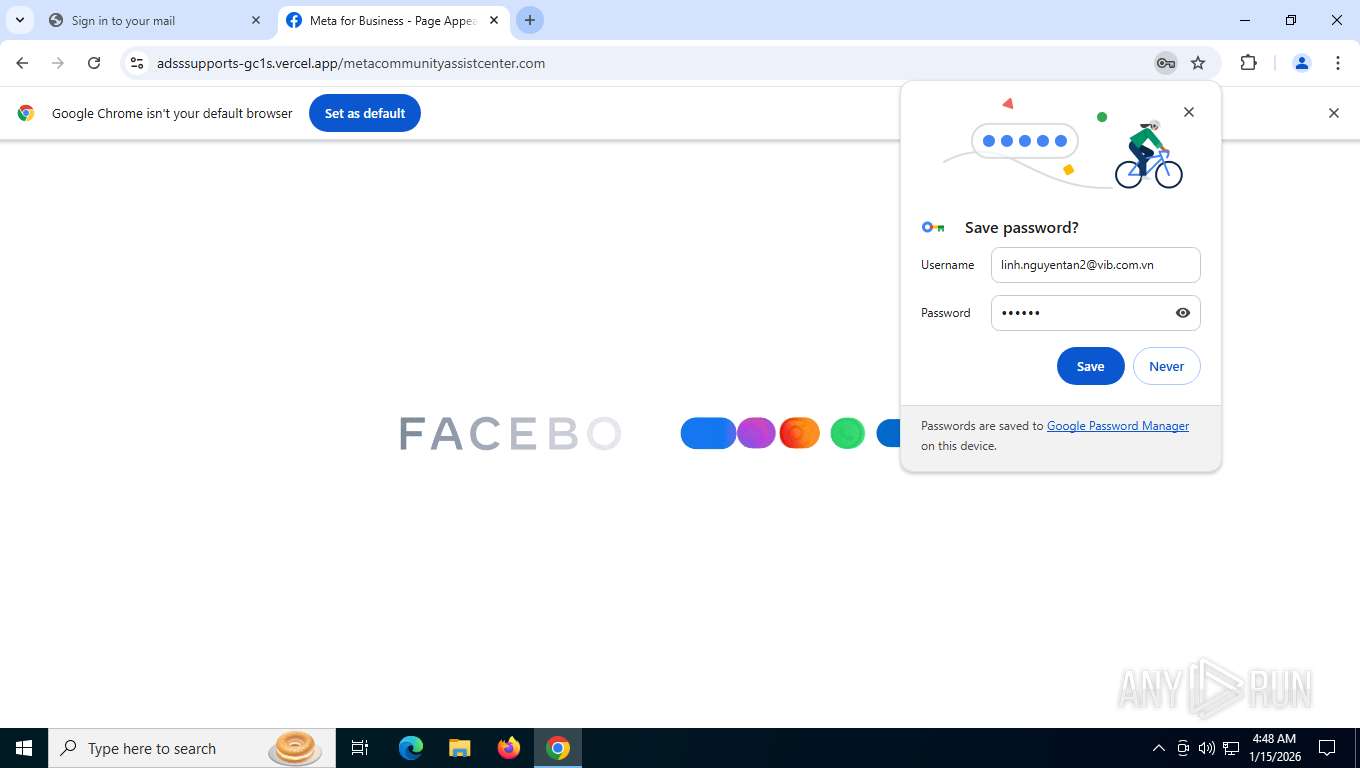
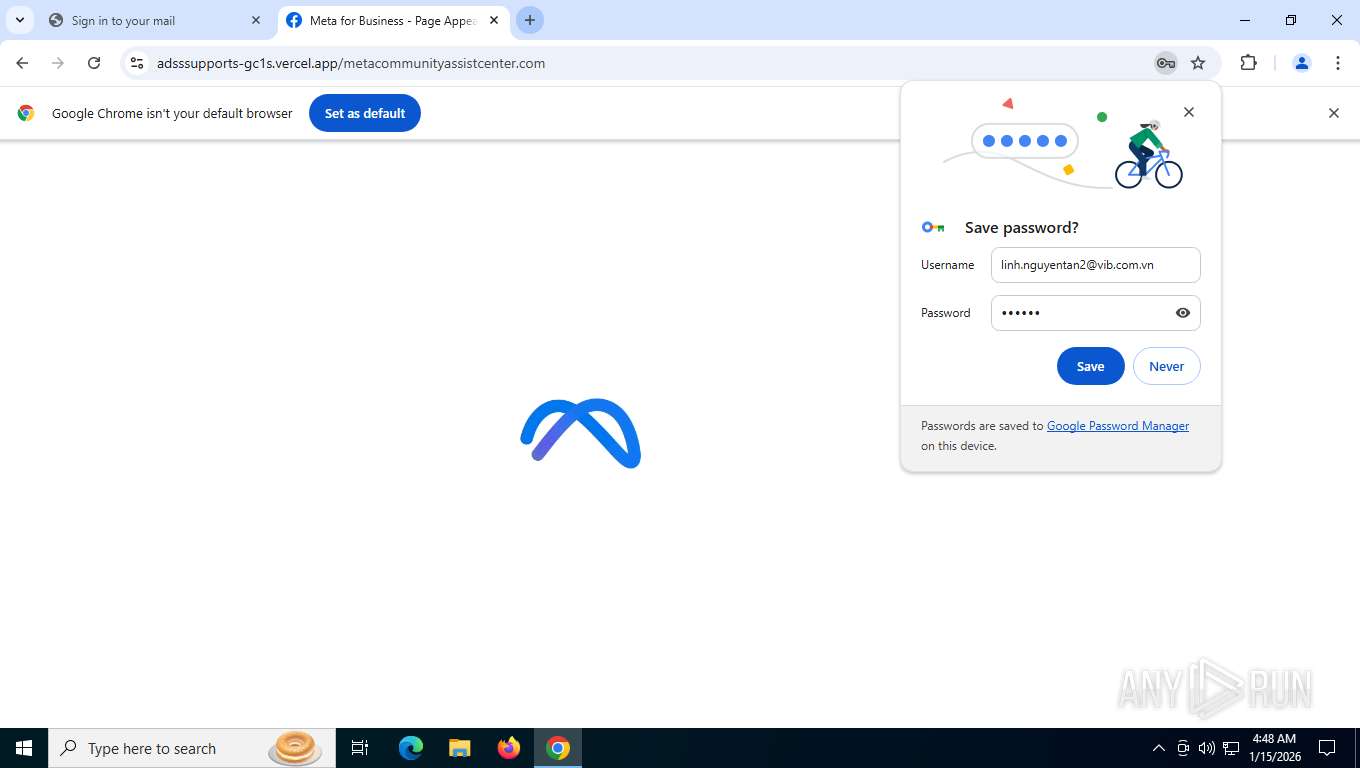
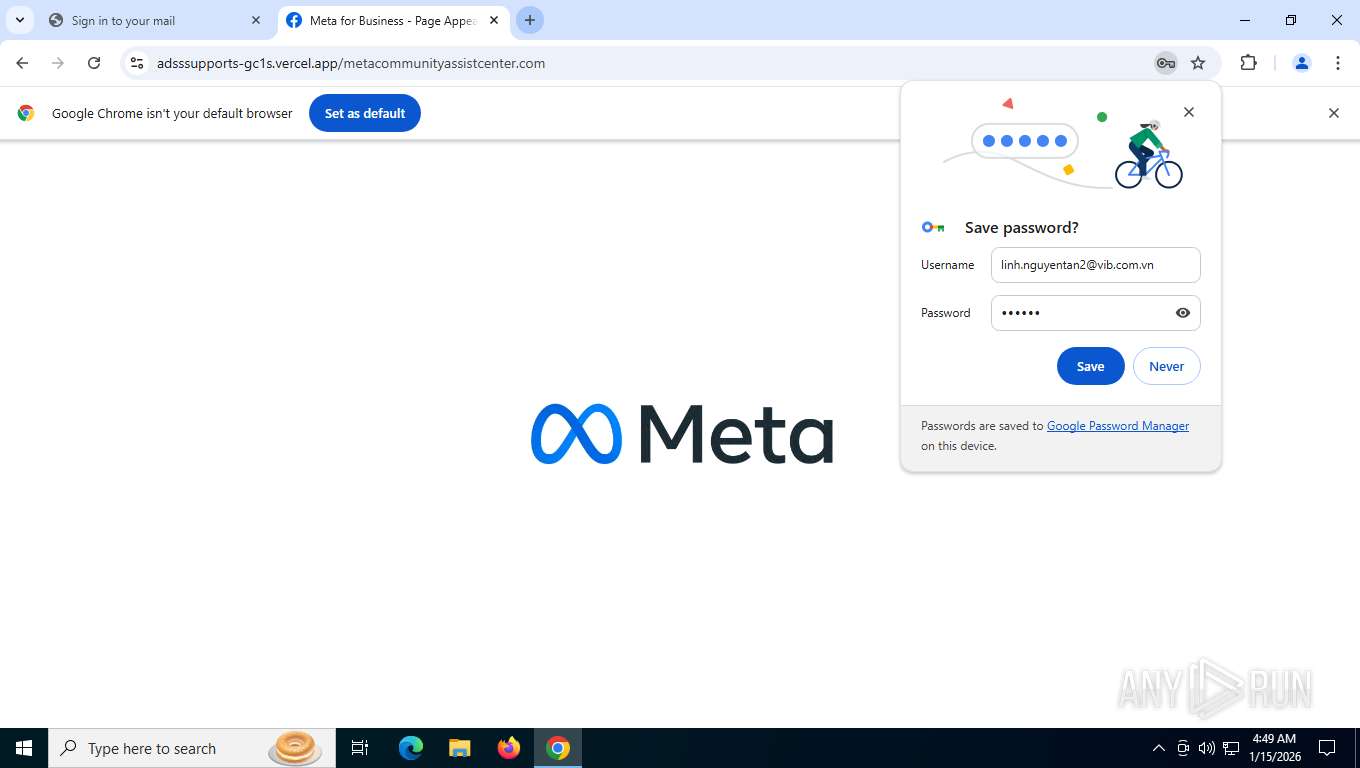
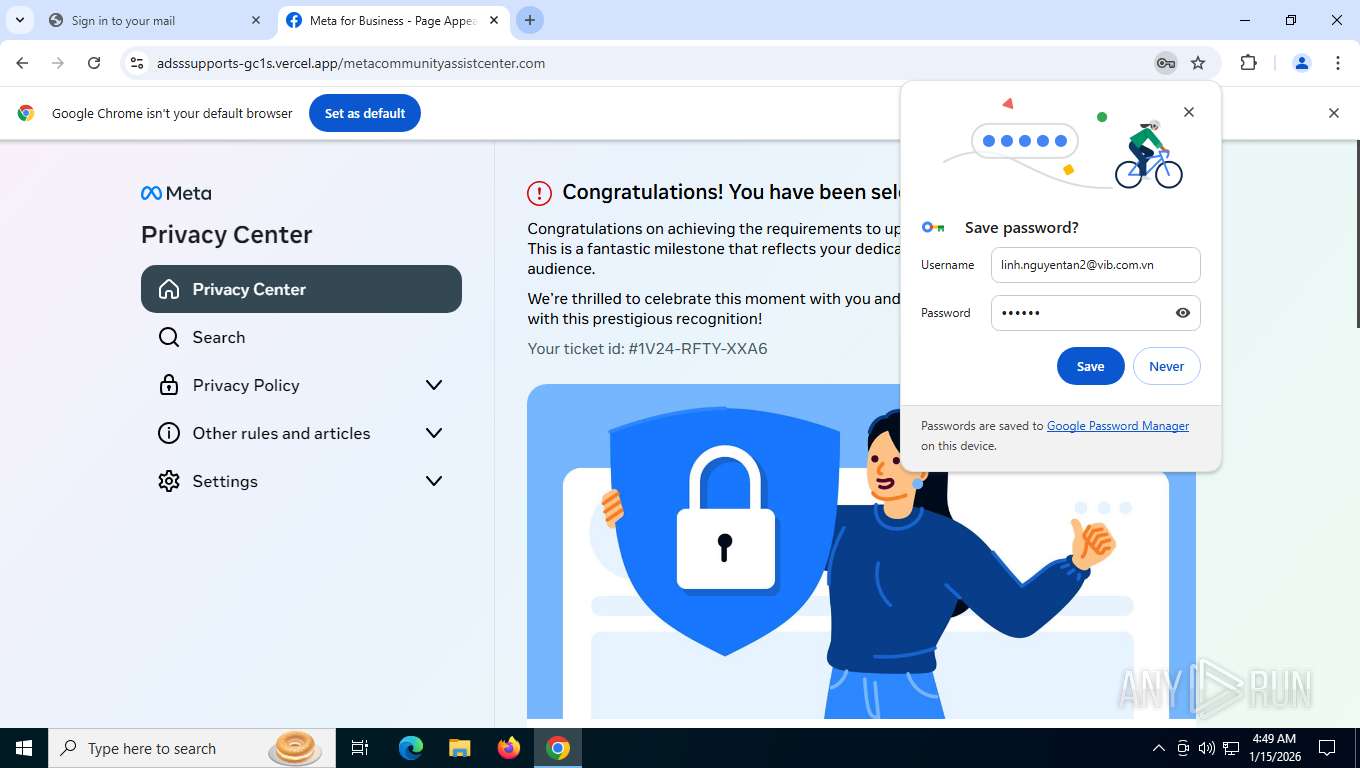
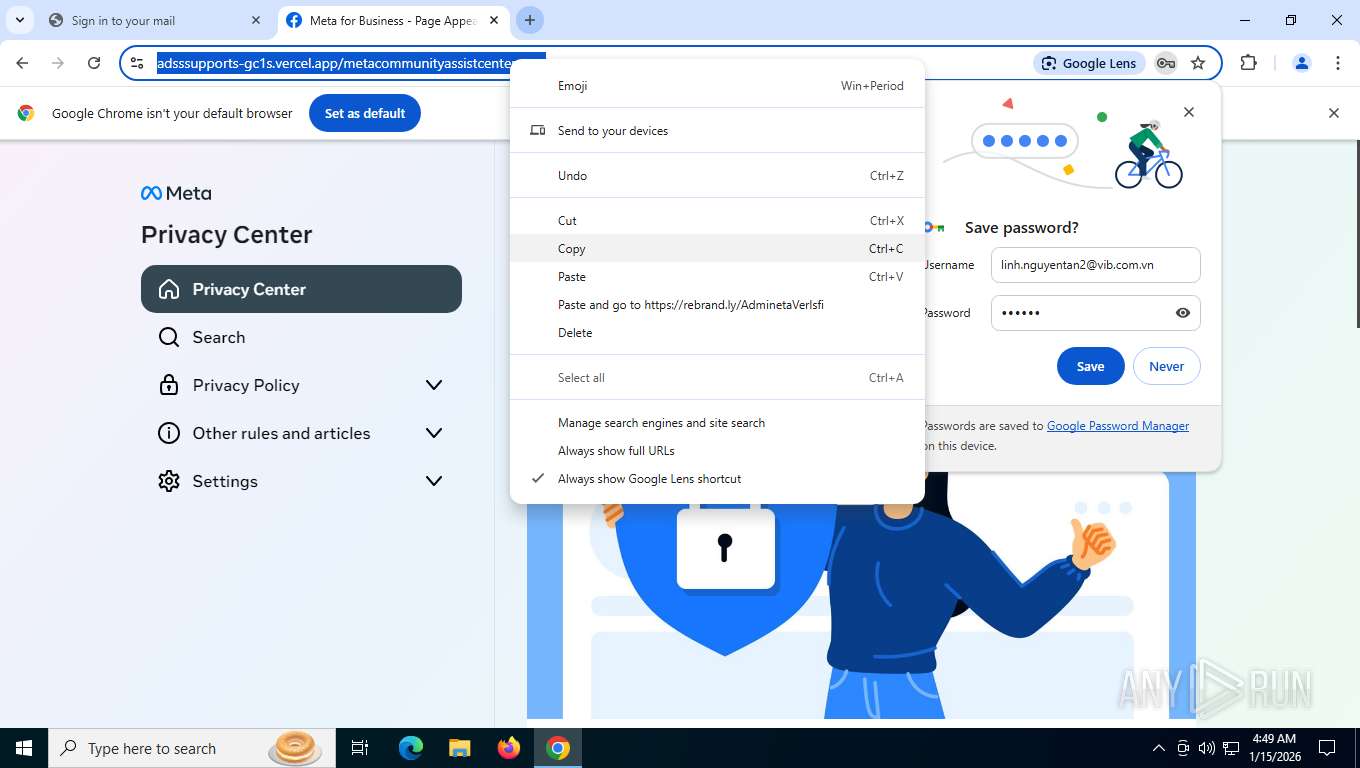
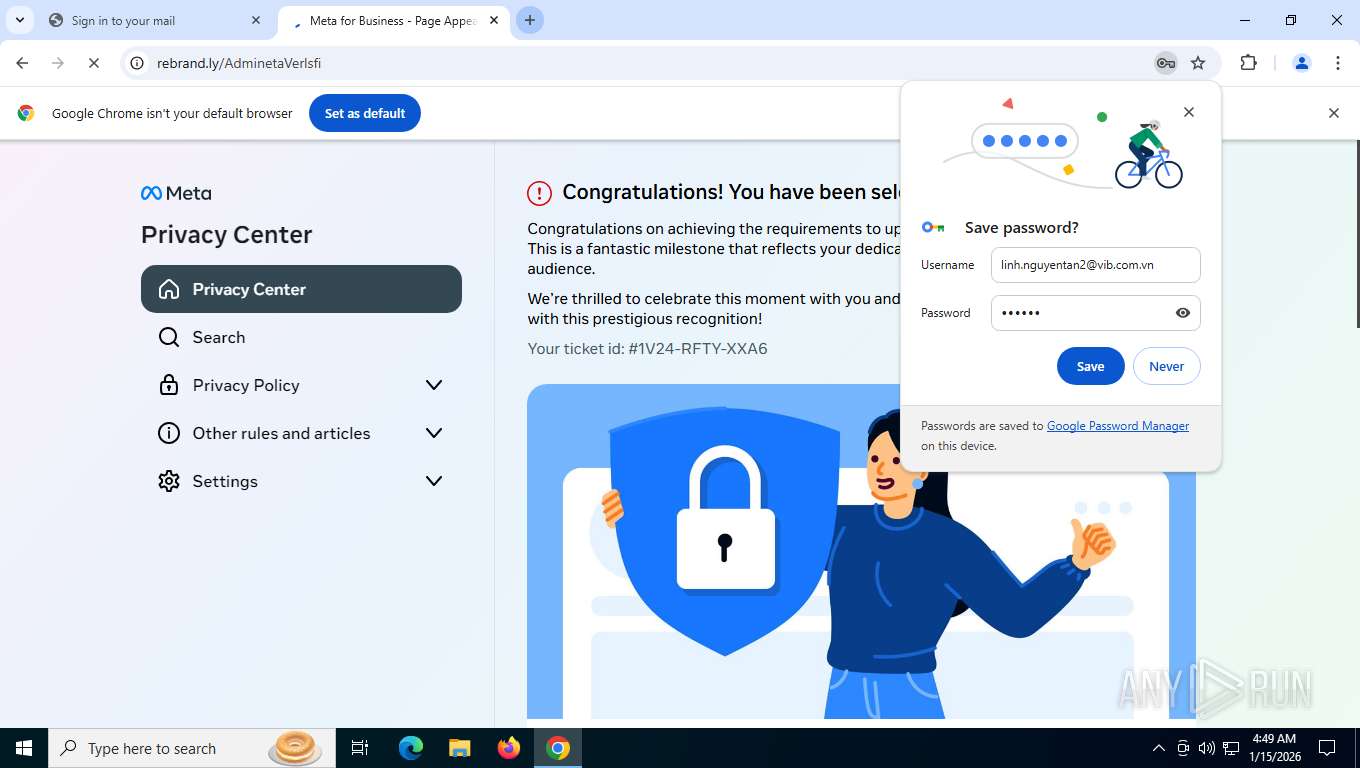
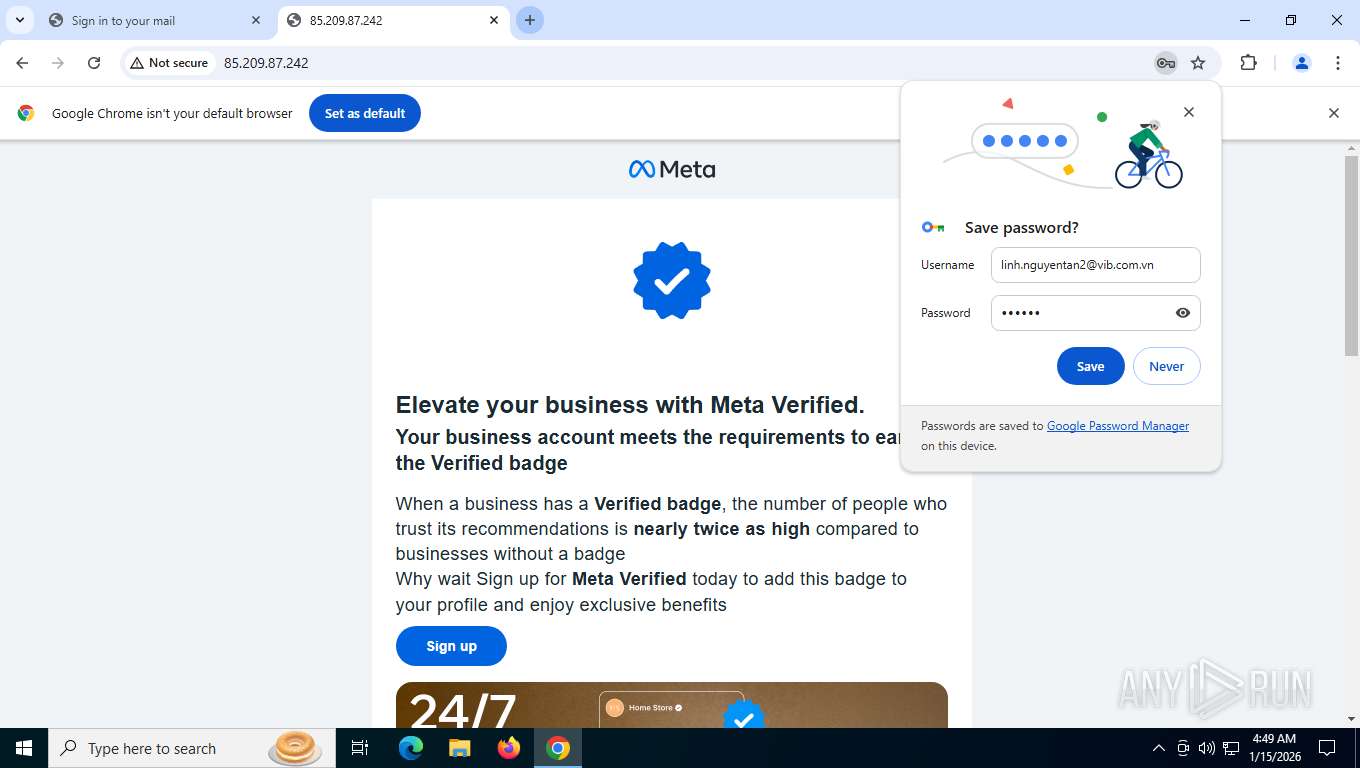
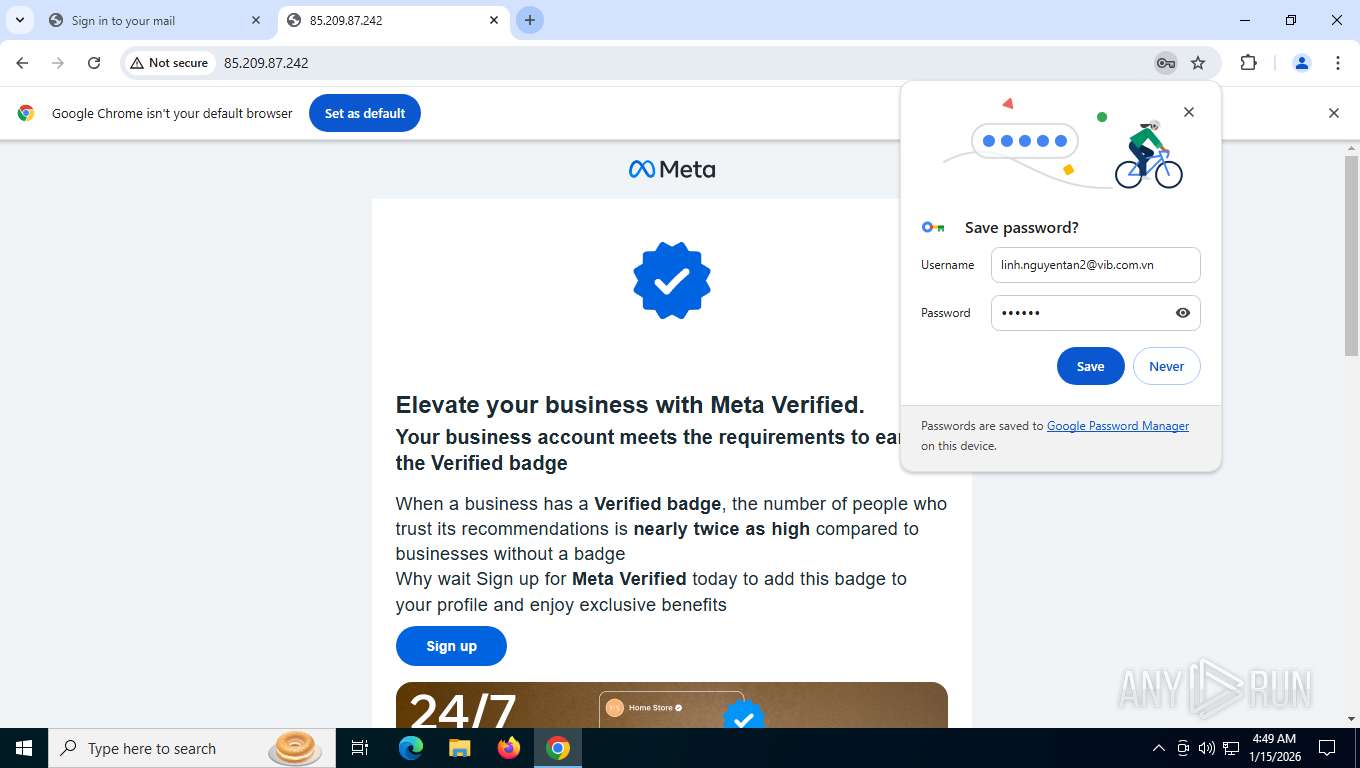
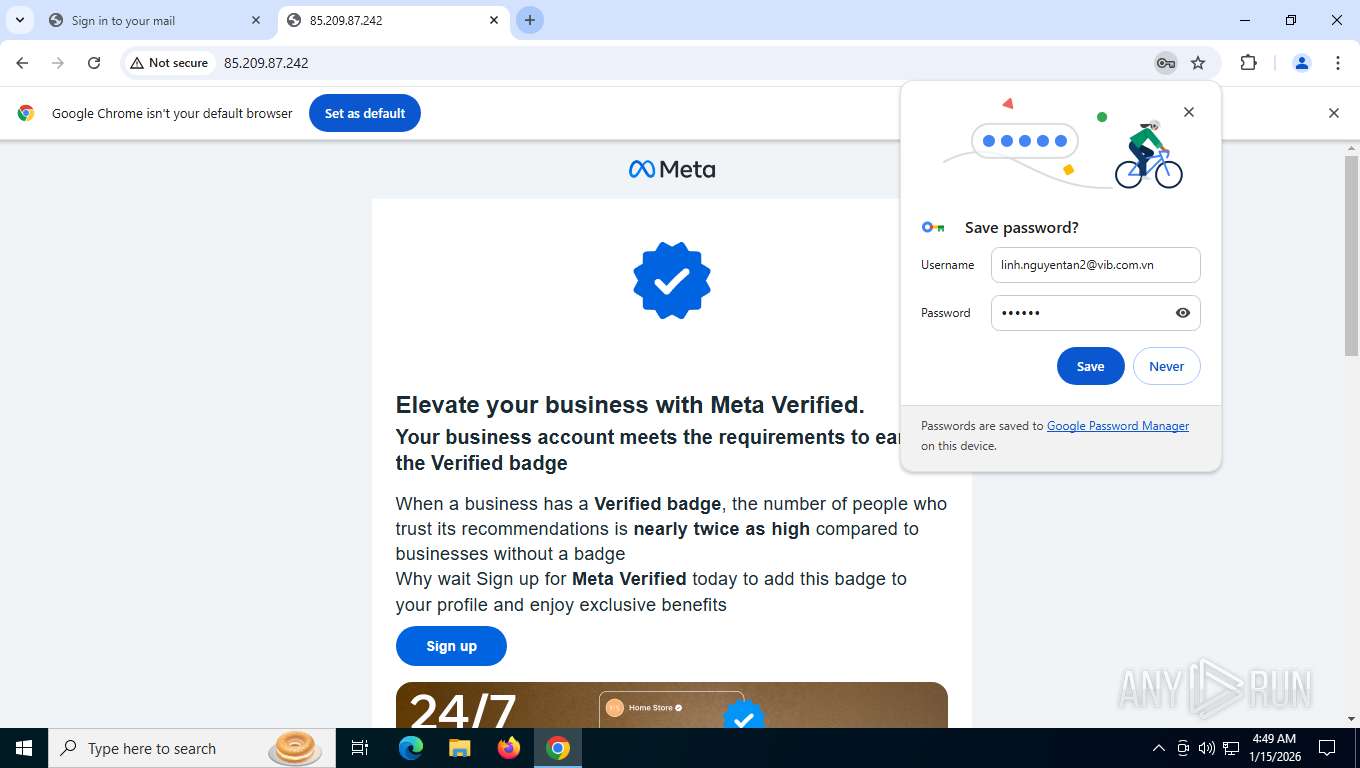
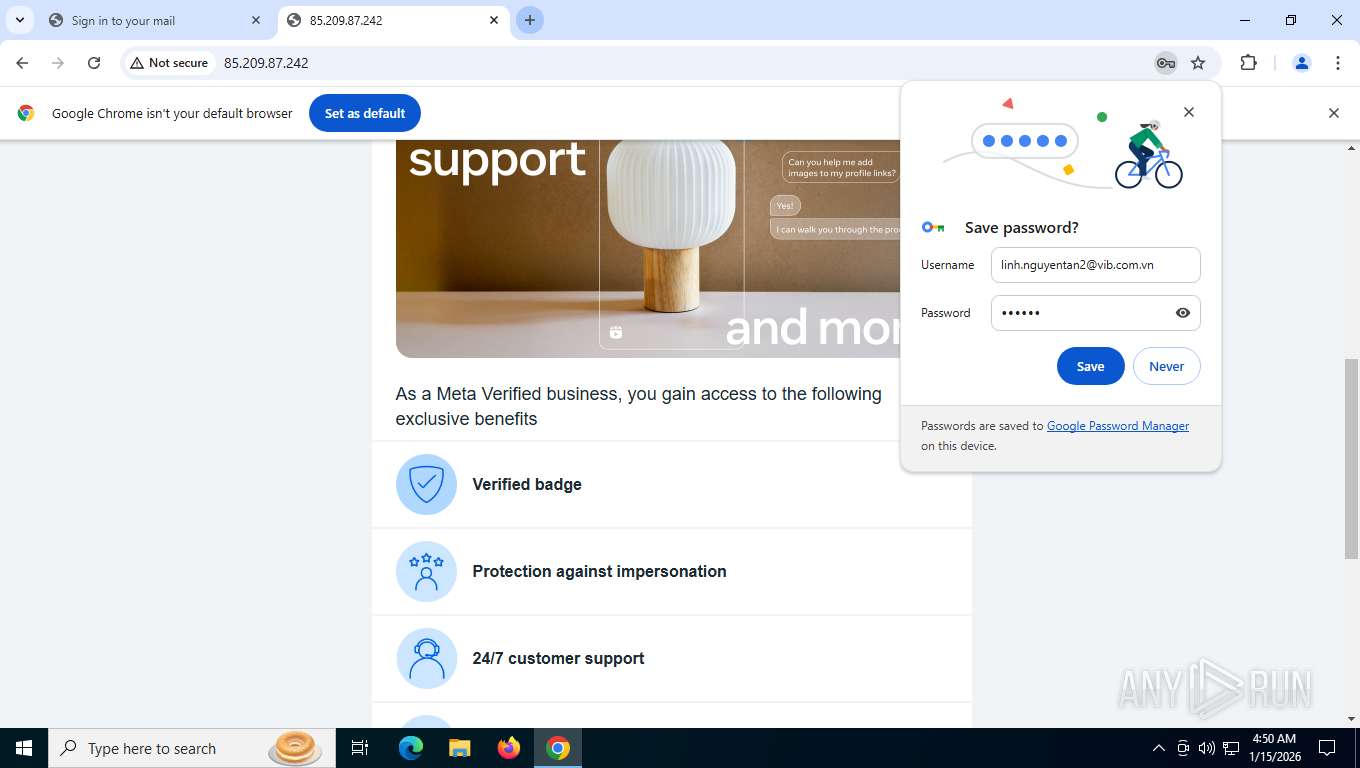
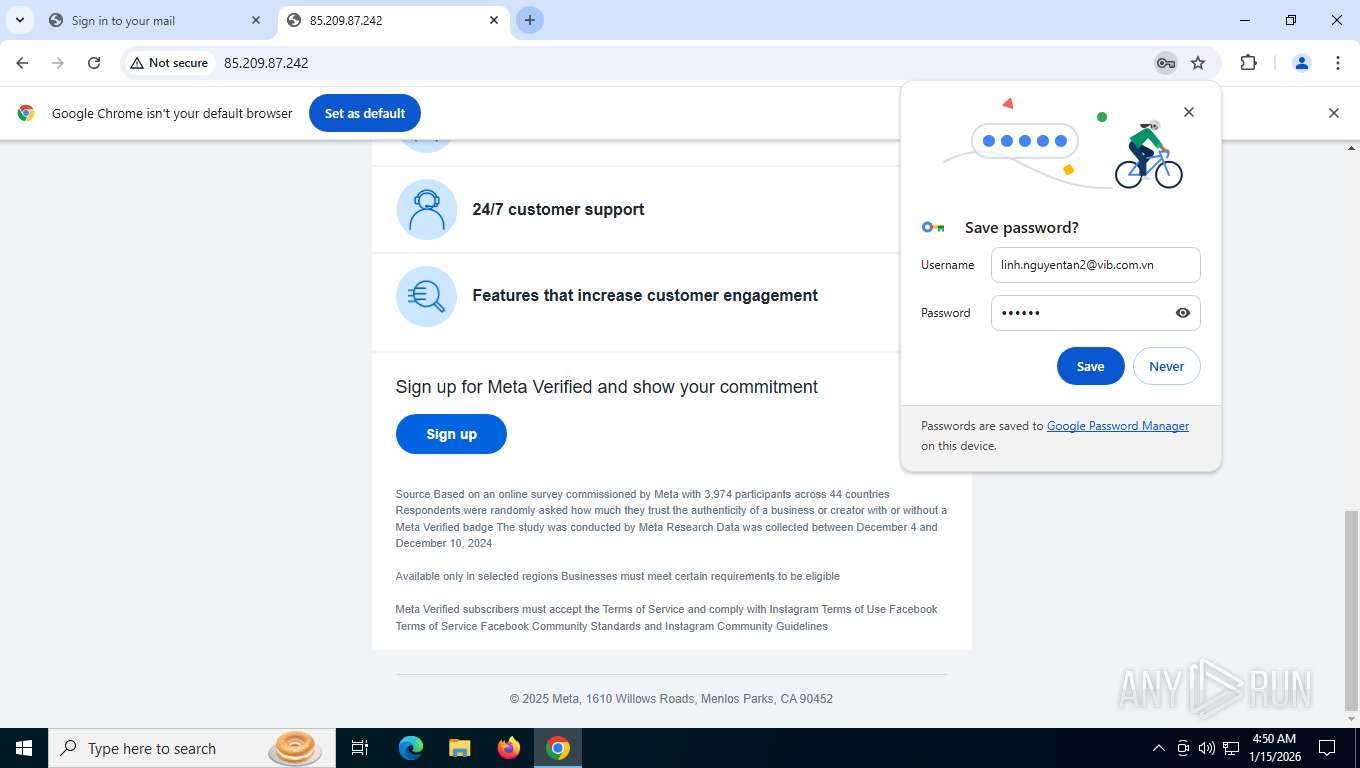
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2026, 09:45:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8FBAC0ABD53082B2214D5DCE33DB129D |
| SHA1: | BC716E449244B88DB5B824E13B8BFA2E50D4F8FD |
| SHA256: | DBB0DA0558FD59B94433FFC866AE8FCE022FC786375B7BEEFFE8CB9F277F6CFC |
| SSDEEP: | 3:N1KN3JWKBL+WDlCIA5r/TMpGZIL:CNVBL+SA1/A9L |
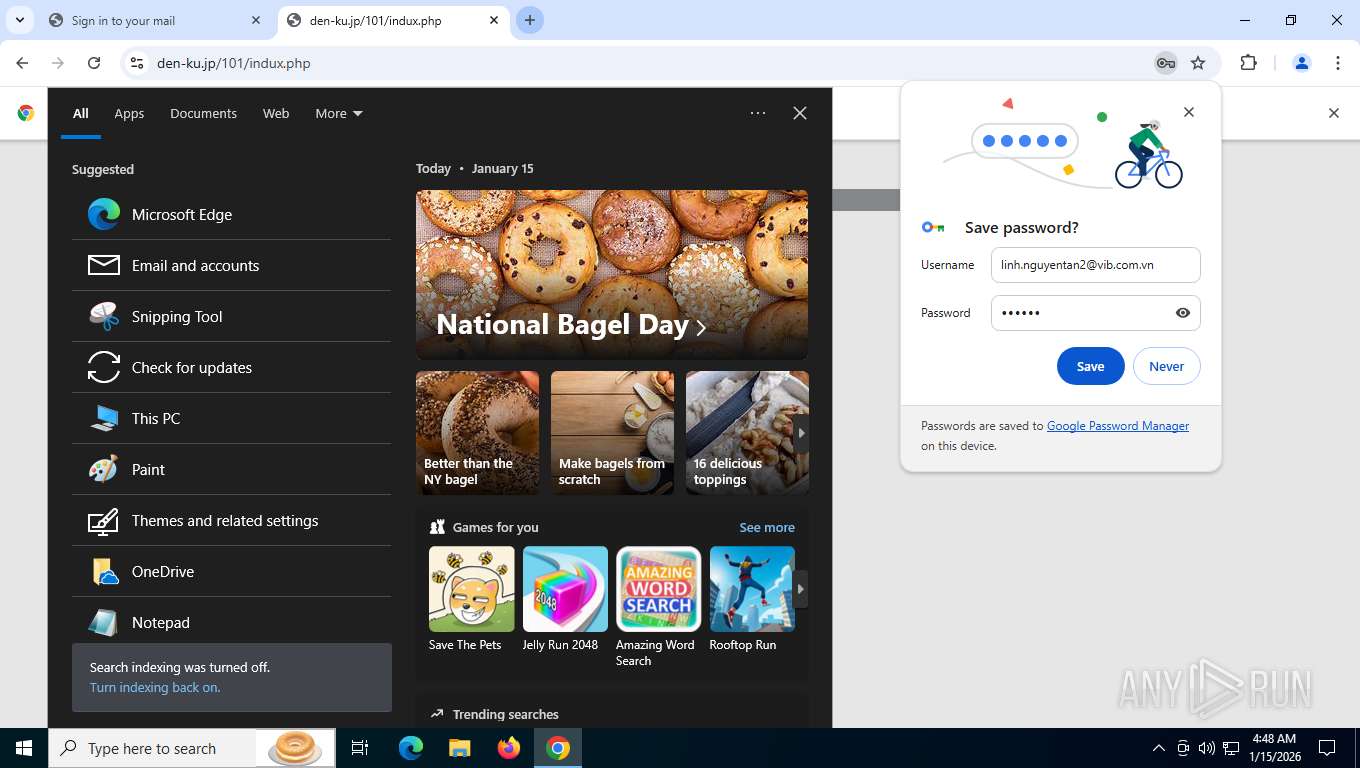
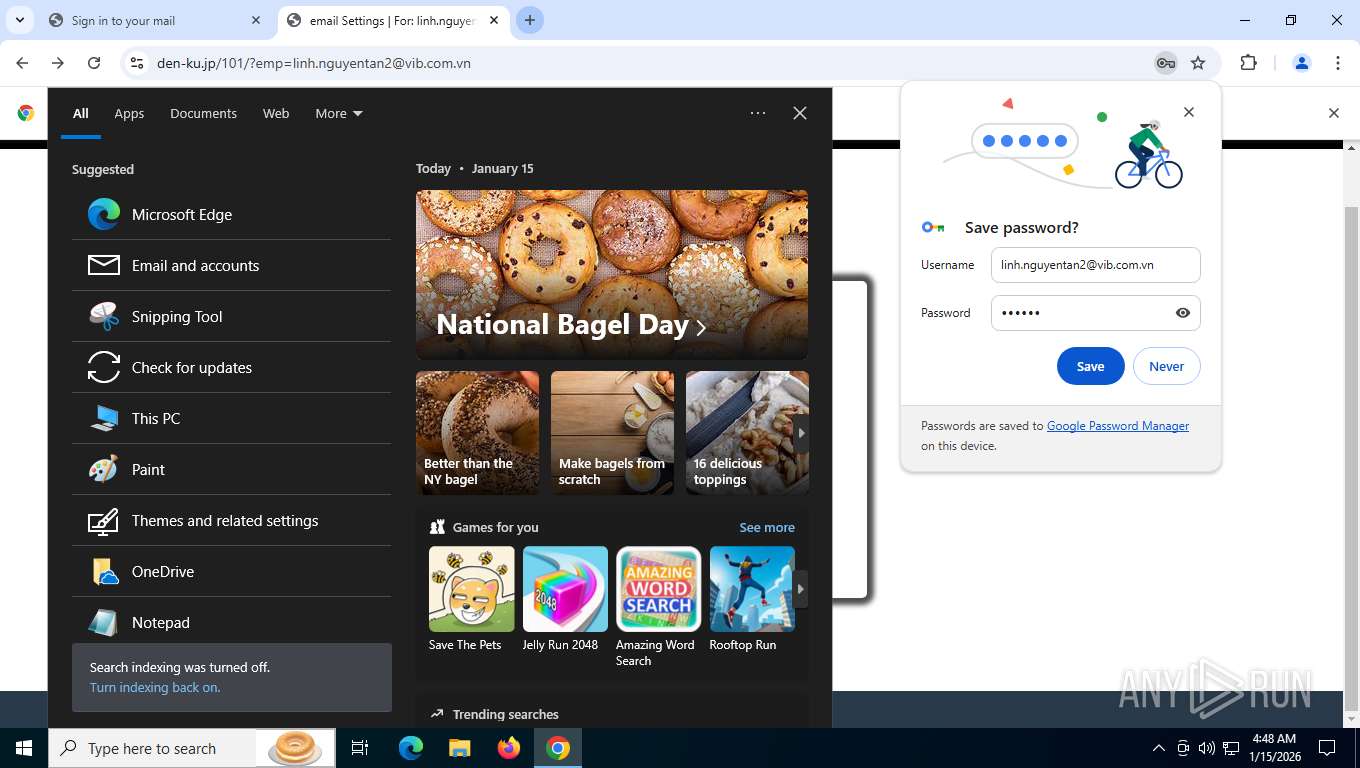
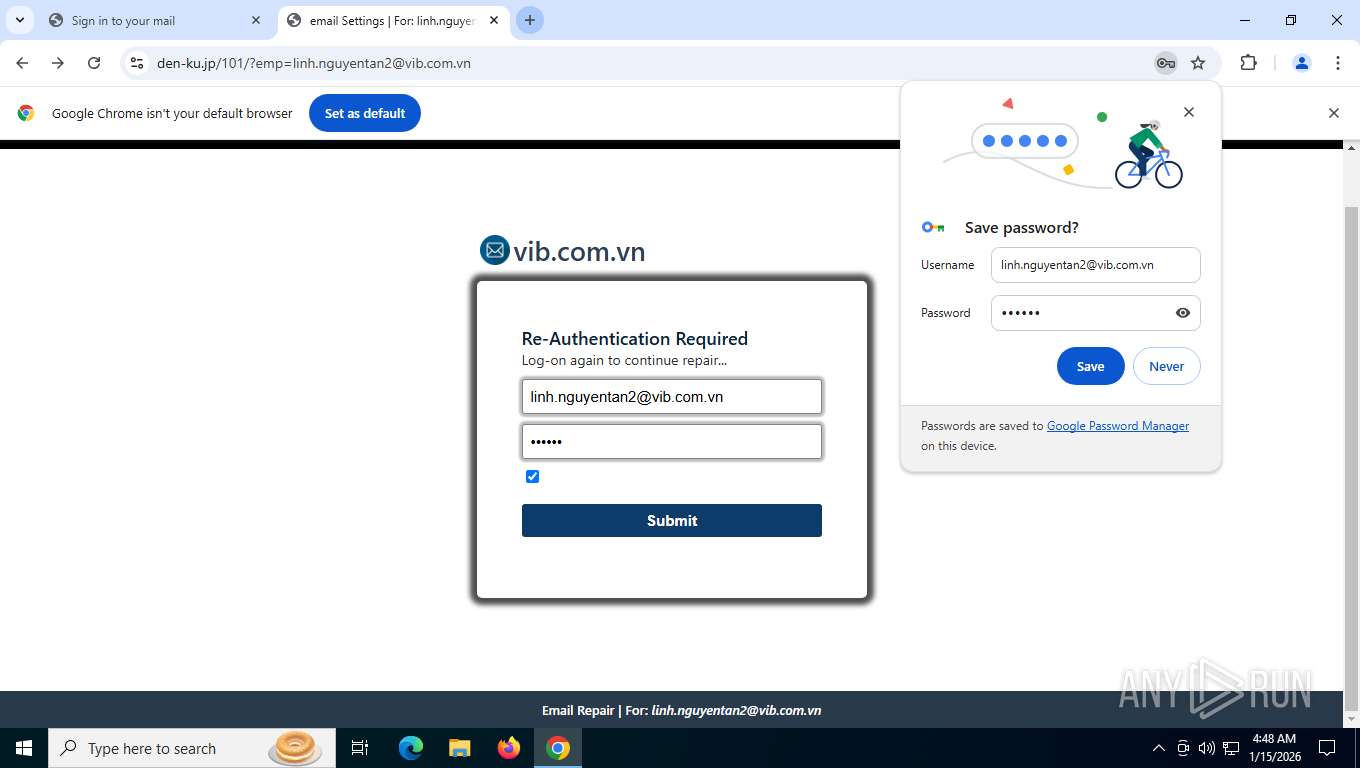
MALICIOUS
Phishing has been detected
- chrome.exe (PID: 7604)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7876)
PHISHING has been detected (ML)
- chrome.exe (PID: 7604)
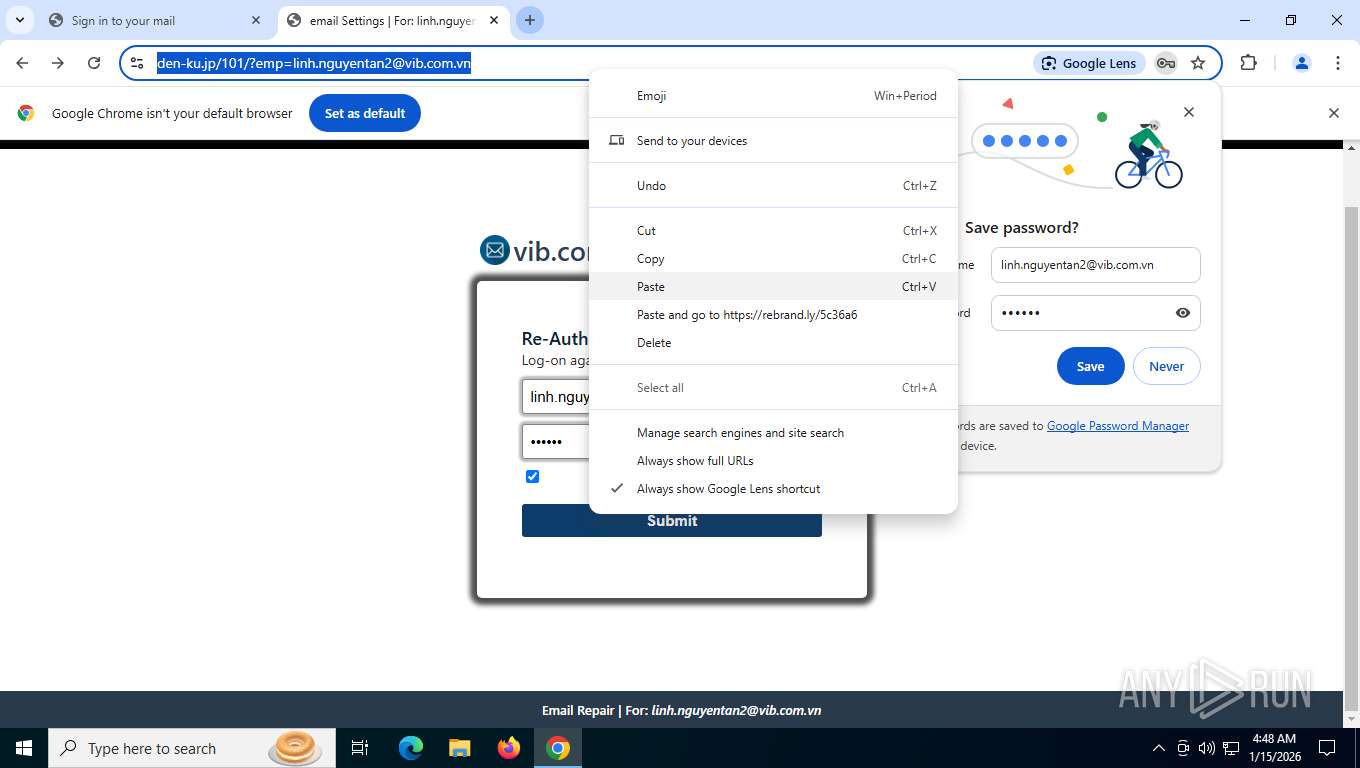
SUSPICIOUS
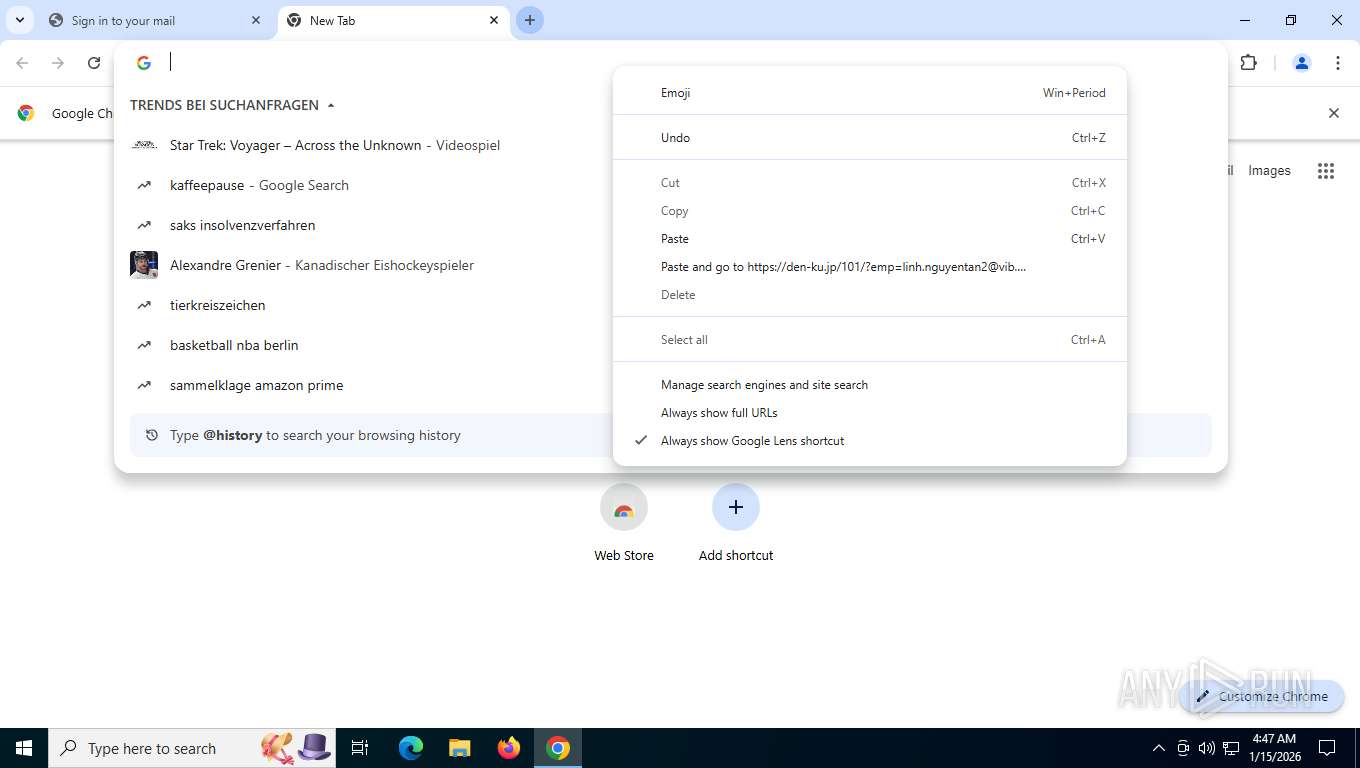
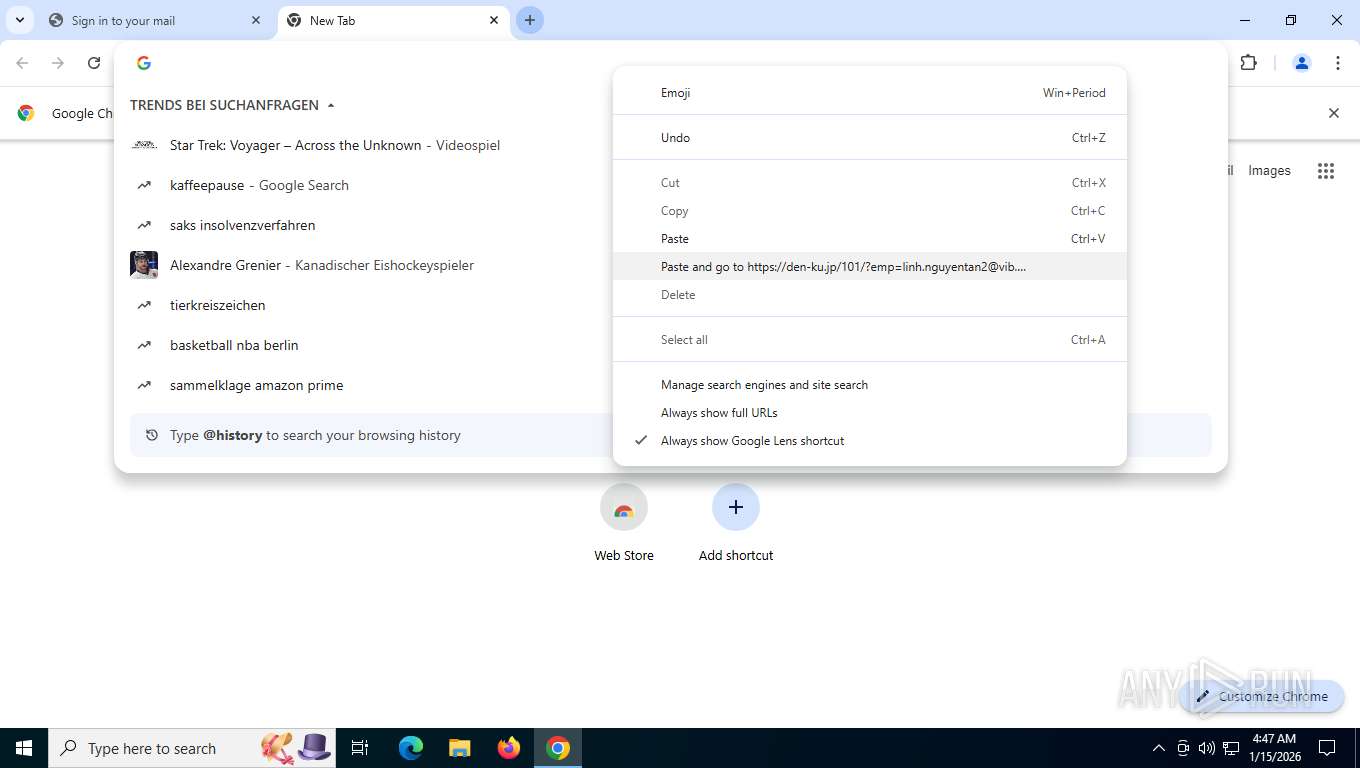
Email pattern detected in URL fragment
- chrome.exe (PID: 7604)
INFO
Reads the computer name
- TextInputHost.exe (PID: 6548)
Application launched itself
- chrome.exe (PID: 7604)
Checks supported languages
- TextInputHost.exe (PID: 6548)
Checks proxy server information
- slui.exe (PID: 5984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=20 --field-trial-handle=3020,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4360,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --field-trial-handle=3592,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=500,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=15 --field-trial-handle=4756,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6076,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 4340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=13 --field-trial-handle=5044,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 5984 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=22 --field-trial-handle=5000,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 6440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=21 --field-trial-handle=4768,i,15793126638503304513,3888829820140312381,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
3 878
Read events
3 878
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
9
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfdece.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFfdeed.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfdedd.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfdeed.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfdeed.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RFfdeed.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
268
TCP/UDP connections
129
DNS requests
110
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7876 | chrome.exe | GET | 302 | 207.241.237.3:443 | https://web.archive.org/web/vib.com.vn | unknown | — | — | unknown |
7876 | chrome.exe | GET | 200 | 172.217.20.138:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
7876 | chrome.exe | GET | 200 | 216.58.206.78:80 | http://clients2.google.com/time/1/current?cup2key=8:GdvJjK4W49QX4G02VPbbmbovkIveeyNKJKkqGN8ttYc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7876 | chrome.exe | POST | 200 | 64.233.166.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7876 | chrome.exe | GET | 200 | 104.18.10.207:443 | https://stackpath.bootstrapcdn.com/bootstrap/4.4.1/css/bootstrap.min.css | unknown | text | 128 Kb | whitelisted |
7876 | chrome.exe | GET | 200 | 183.90.183.22:80 | http://s10185930000001.c3.hpms1.jp/ssfdvg/Multi/en/login.html | unknown | — | — | unknown |
7876 | chrome.exe | GET | 200 | 104.18.10.207:443 | https://stackpath.bootstrapcdn.com/bootstrap/4.4.1/js/bootstrap.min.js | unknown | text | 58.6 Kb | whitelisted |
7876 | chrome.exe | GET | 403 | 104.18.40.68:443 | https://kit.fontawesome.com/585b051251.js | unknown | text | 9 b | unknown |
7876 | chrome.exe | GET | 400 | 142.251.208.10:443 | https://fonts.googleapis.com/css?family=Yellowtail%26display=swap | unknown | html | 6.24 Kb | whitelisted |
7876 | chrome.exe | GET | 200 | 183.90.183.22:80 | http://s10185930000001.c3.hpms1.jp/ssfdvg/Multi/en/files/jquery-1.js | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2480 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1188 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7876 | chrome.exe | 216.58.206.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 172.217.20.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 183.90.183.22:443 | s10185930000001.c3.hpms1.jp | DIGIROCK DigiRock, Inc. | JP | unknown |
7876 | chrome.exe | 183.90.183.22:80 | s10185930000001.c3.hpms1.jp | DIGIROCK DigiRock, Inc. | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
s10185930000001.c3.hpms1.jp |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
7876 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Signs of phishing were detected in the page code |
7876 | chrome.exe | Possible Social Engineering Attempted | ET PHISHING Generic Multibrand Ajax XHR CredPost Phishing Landing |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7876 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspicious unencrypted POST request sending an email address |
7876 | chrome.exe | Possible Social Engineering Attempted | ET PHISHING Generic Multibrand Ajax XHR CredPost Phishing Landing |
7876 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Signs of phishing were detected in the page code |