| download: | /AreaDownload/Controlli/FatturaPaWS.exe |
| Full analysis: | https://app.any.run/tasks/8b8e8f43-73de-46a1-97c4-5f0f7c9f6fdd |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 10:12:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 5CFC87F8BD6949F07BCD32BB75B6AE98 |
| SHA1: | AE962C3D1EC57B714A394A12242418ADDC3A4F6C |
| SHA256: | DB98D20A1974E30D4E30A15D2670FB41D67359AE5AB72B53C9C92FB0FE0C57BE |
| SSDEEP: | 6144:Ip5cen+47N5FNG3idcOF7mAEn2jIMoJ7sgx5e5tKC5QKslvP3v2SOo6M:Ip/+S7FiMoJ7sgqiC58vP3+Sr6M |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- FatturaPaWS.exe (PID: 2136)
Reads security settings of Internet Explorer
- FatturaPaWS.exe (PID: 2136)
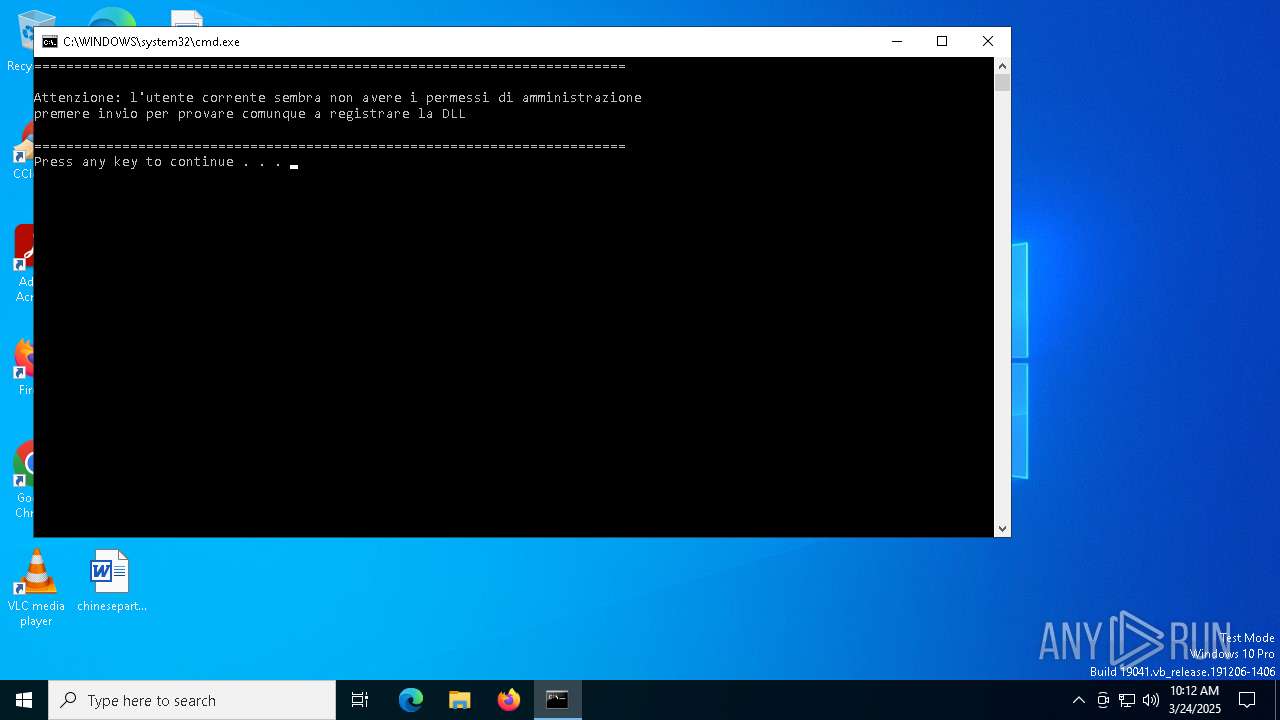
Executing commands from ".cmd" file
- FatturaPaWS.exe (PID: 2136)
Starts CMD.EXE for commands execution
- FatturaPaWS.exe (PID: 2136)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5960)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 5960)
- net.exe (PID: 7240)
There is functionality for taking screenshot (YARA)
- FatturaPaWS.exe (PID: 2136)
INFO
Reads the computer name
- FatturaPaWS.exe (PID: 2136)
Create files in a temporary directory
- FatturaPaWS.exe (PID: 2136)
Checks supported languages
- FatturaPaWS.exe (PID: 2136)
- RegAsm.exe (PID: 1012)
Process checks computer location settings
- FatturaPaWS.exe (PID: 2136)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4692)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 4336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:30 08:50:02+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 90624 |
| InitializedDataSize: | 22016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x168bf |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.2712 |
| ProductVersionNumber: | 1.5.0.2712 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Oleg N. Scherbakov |
| FileDescription: | 7z Setup SFX (x86) |
| FileVersion: | 1.5.0.2712 |
| InternalName: | 7ZSfxMod |
| LegalCopyright: | Copyright © 2005-2012 Oleg N. Scherbakov |
| OriginalFileName: | 7ZSfxMod_x86.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 7-Zip SFX |
| ProductVersion: | 1.5.0.2712 |
Total processes
157
Monitored processes
19
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
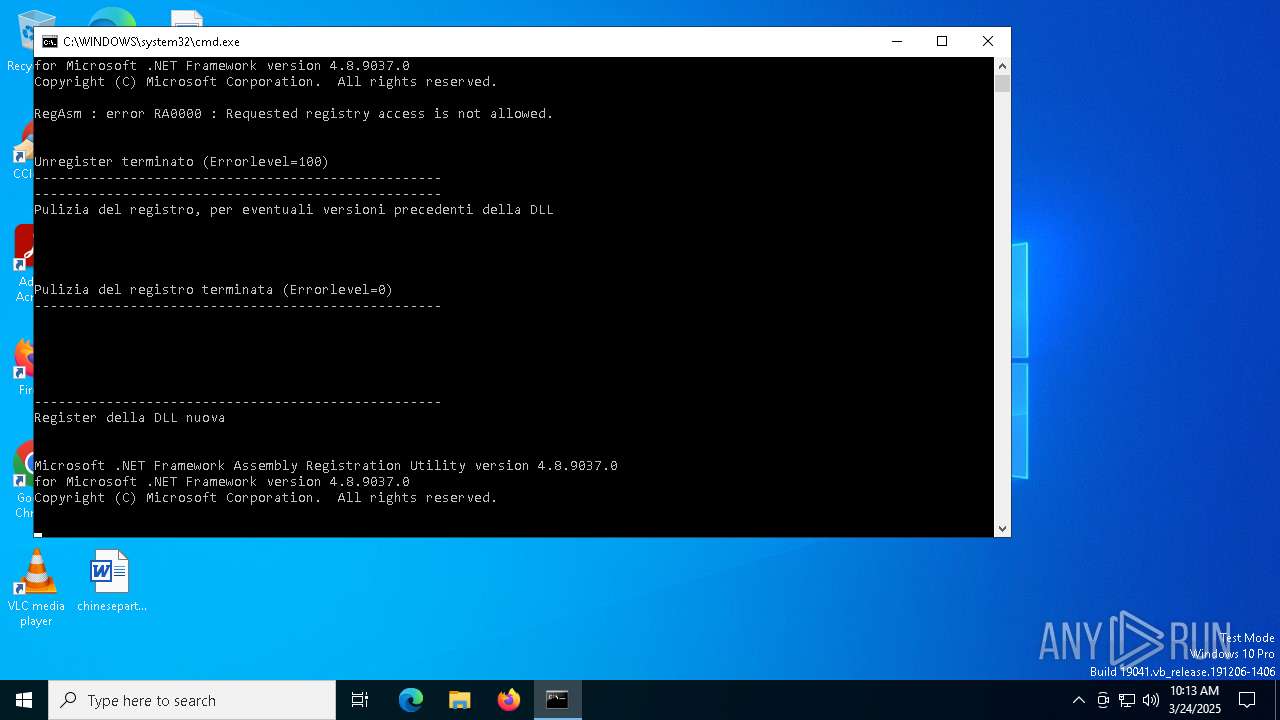
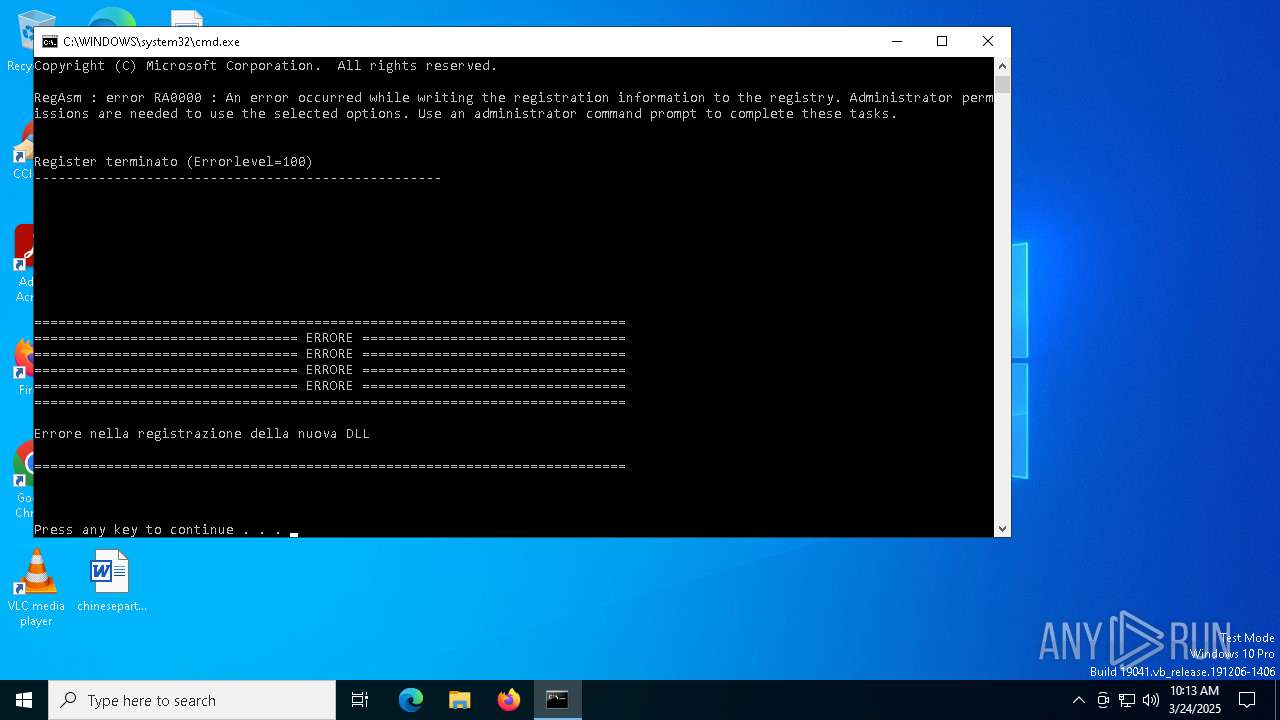
| 1012 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm" "C:\Users\admin\AppData\Local\Temp\FatturaPaDtoNetCOM.dll" /tlb /verbose /unregister | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 100 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2040 | "regedit" /s "C:\Users\admin\AppData\Local\Temp\FatturaPaWsCleanReg.reg" | C:\Windows\SysWOW64\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\FatturaPaWS.exe" | C:\Users\admin\AppData\Local\Temp\FatturaPaWS.exe | explorer.exe | ||||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Version: 1.5.0.2712 Modules
| |||||||||||||||
| 4336 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\InstallDLL.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | FatturaPaWS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7216 | reg query "HKLM\SOFTWARE\Microsoft\NET Framework Setup\NDP\v4" /s /v Install | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | "C:\WINDOWS\SysWOW64\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\FatturaPaWsCleanReg.reg" | C:\Windows\SysWOW64\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 952
Read events
3 935
Write events
17
Delete events
0
Modification events
| (PID) Process: | (8104) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8104) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8104) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4692) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4692) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4692) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4336) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4336) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4336) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7288) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
6
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4692 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b9db51e8-e577-4ab2-80a7-4375f4507c0f.down_data | — | |
MD5:— | SHA256:— | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\RegDLL.cmd | text | |
MD5:74DBE133EAB41C8F06011E24B02D8454 | SHA256:7E4A7179AAFD4510D15581455CD49A5D29FCF8BAAD69378956F9151C83F0E06F | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\RegDLL_CreaFileRegistro.cmd | text | |
MD5:19E5187AC4966F661BCE1313CFAD601E | SHA256:CD0533FD830C993182C4F32588E41064CEF245394C2DC769886D1A85C3B4451F | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\RegDLL_PAUSA.cmd | text | |
MD5:58037AF29BD1C741AB99D5F4BE0B981E | SHA256:E9F232224BB38796E2D98E0616841E800533AA05B48EC30890992AA8D28FBA76 | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\InstallDLL.cmd | text | |
MD5:8EFB5F97494ABD261E127F174AF82779 | SHA256:B4642C7FB9A6E0F93FB58A280C946841E1B1DCD248EED77208D9A6B169396F9F | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\InstallDLL_PAUSA.cmd | text | |
MD5:C848843D0198552E1E42B2158B4B9532 | SHA256:C458E5232348BBC05A95698183223B22F9E0B691F1F1397FC4AC57D81E5A9DA0 | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\ChangeLog.txt | text | |
MD5:D5F9D35C779CE3EF6E08D7B6B9FF9381 | SHA256:59A2D1981CD893CFABBBA3CE2C4EB99675E5F37072500FE1C943E587793AAB9C | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\FatturaPaDtoNetCOM.tlb | binary | |
MD5:8D9E05C2906384EF8CCED733CE712EFA | SHA256:67231B4F5DB2A64A0FA4687D42EA2F3547E3B8EFC96D62A82888791F9BDA330D | |||
| 2136 | FatturaPaWS.exe | C:\Users\admin\AppData\Local\Temp\FatturaPaWS.dll | executable | |
MD5:C3DF87E54EAB09454F7F249C80CBF3FD | SHA256:5F249C59AC9AD508F92EF96489DEF649EA8C14BFBD8994472598B19C8E3596CC | |||
| 4692 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\13dac5f9-2a66-43c7-ae02-a776f05f0ae2.e66034b7-ea17-4e11-906e-a840958c447b.down_meta | binary | |
MD5:CC2B3D492A8B6B549082B098CF0443BB | SHA256:80D7B25526E5D35FE3C9A44EB9A93D90D91747600E6310D8FEA48F9B7D1AD50A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7744 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4692 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5024 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5024 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7744 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |