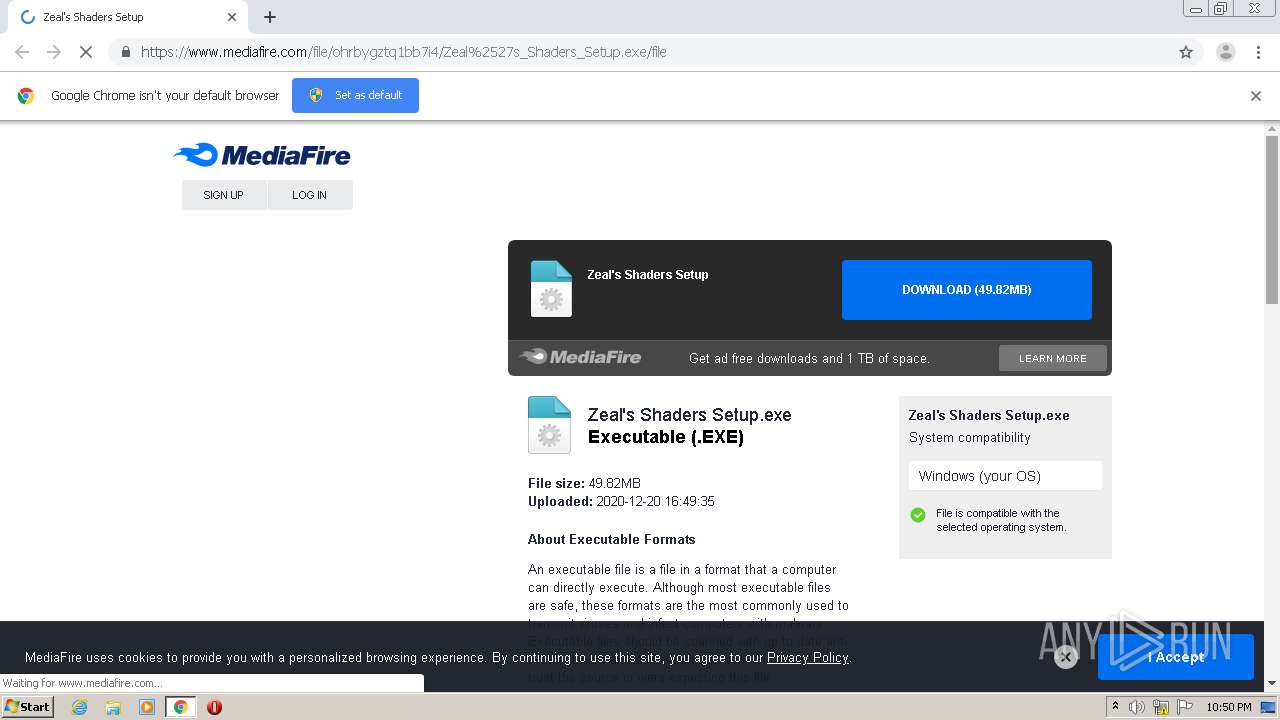
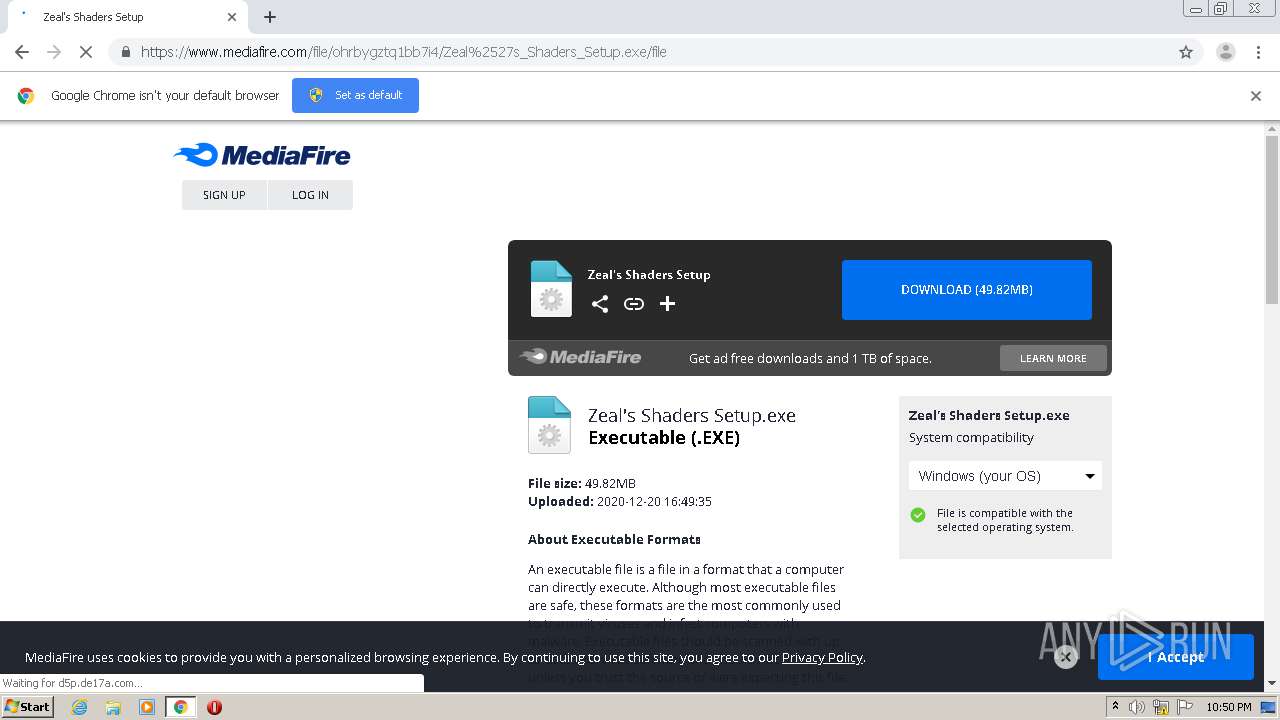
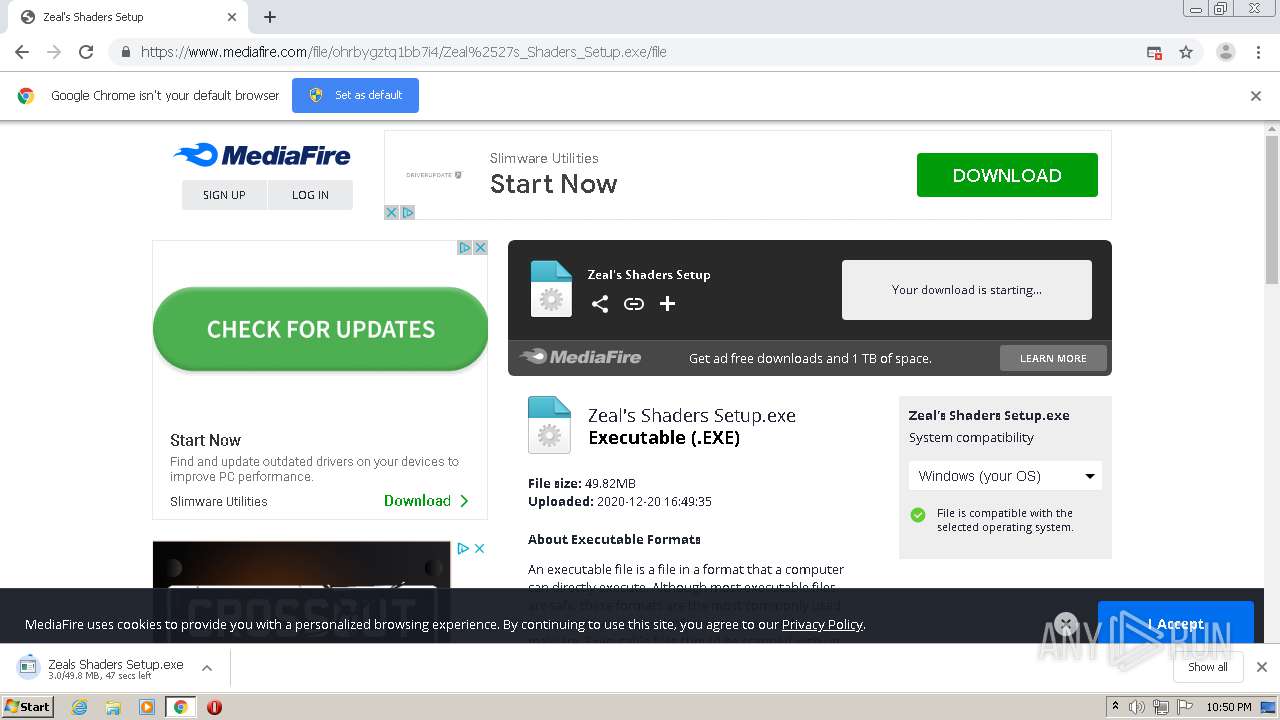
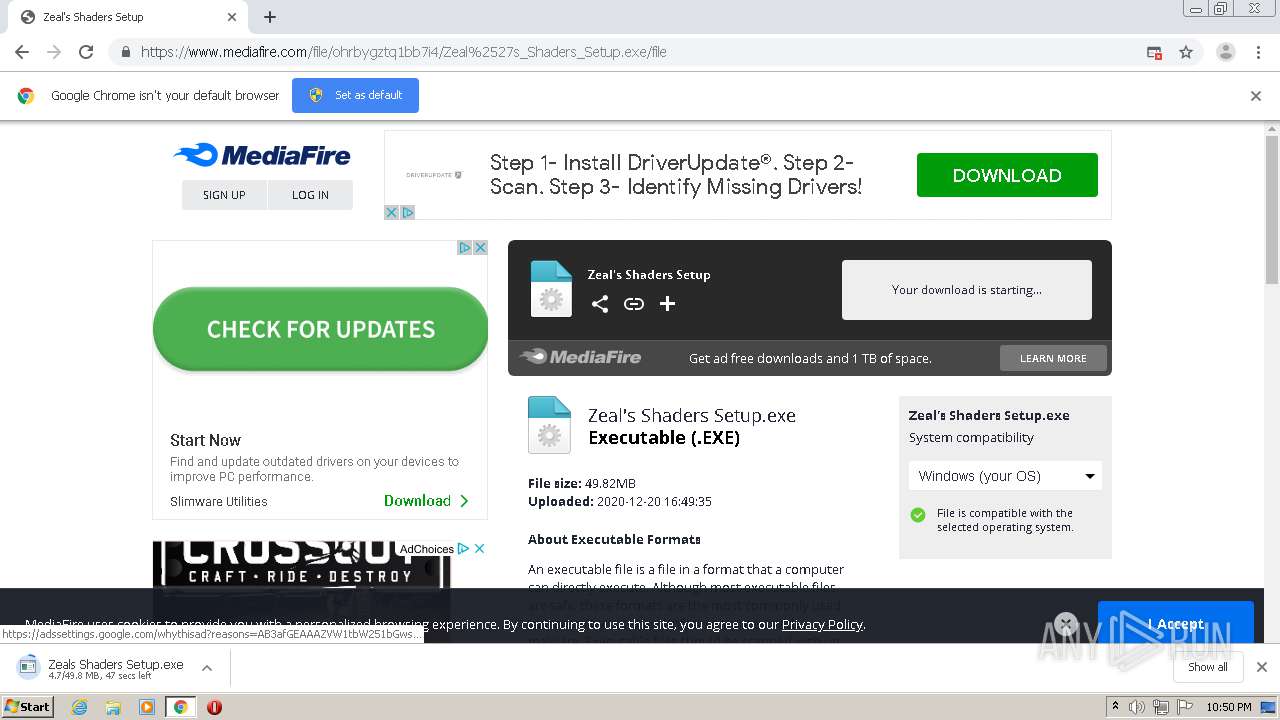
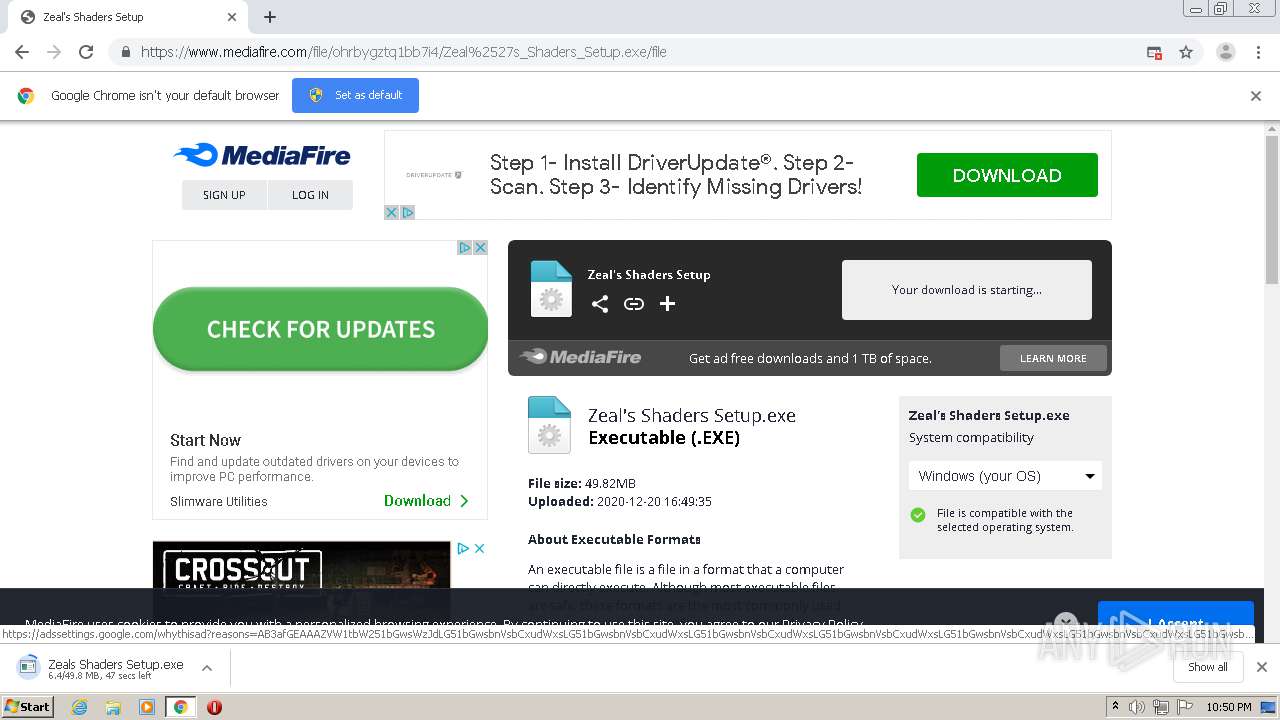
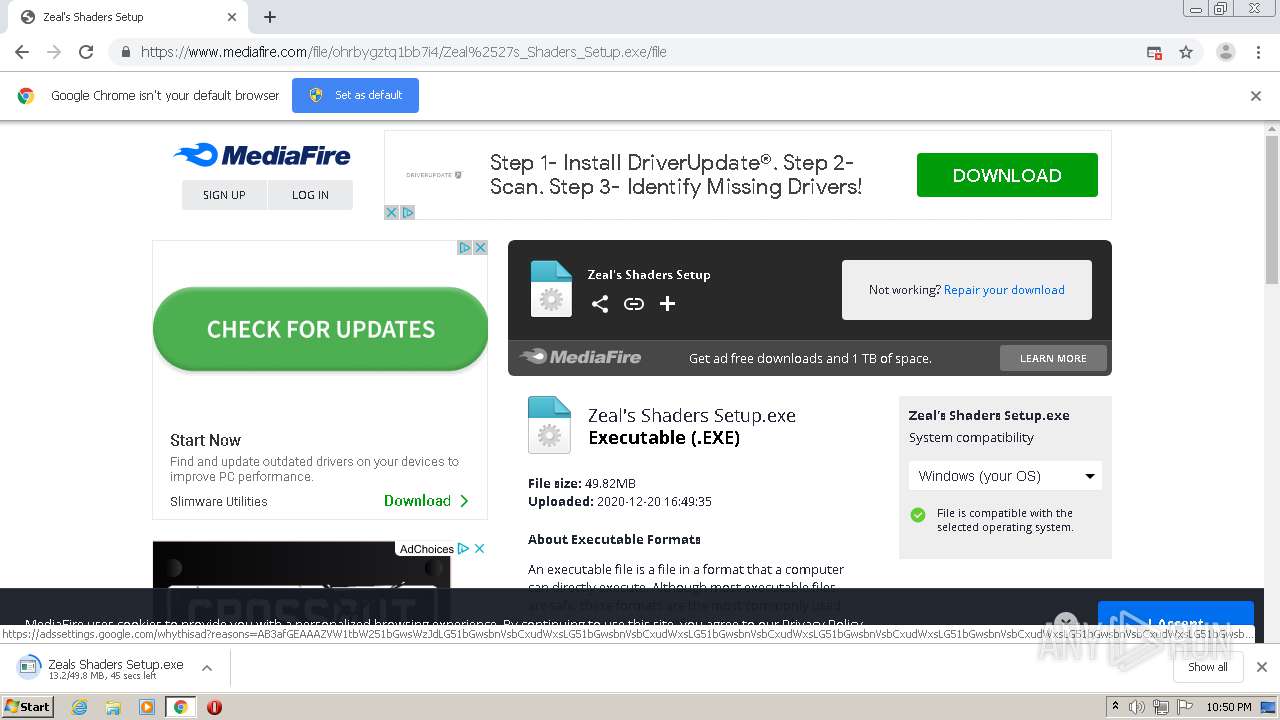
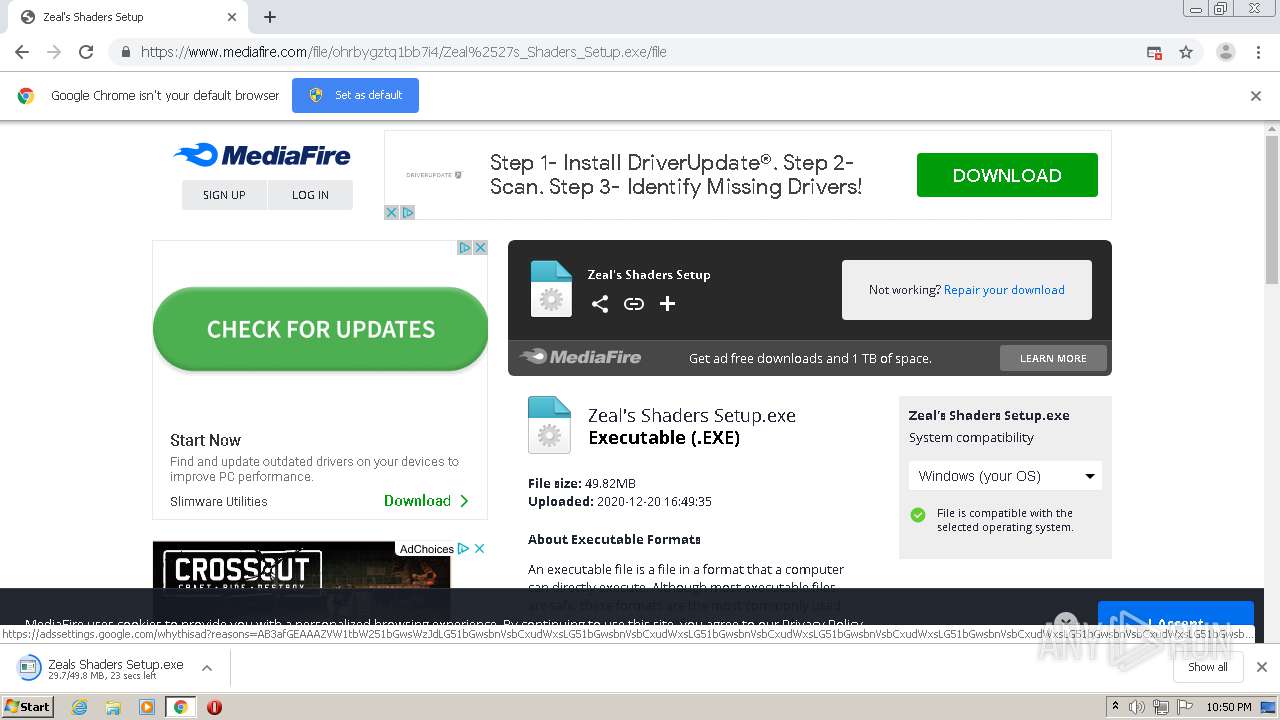
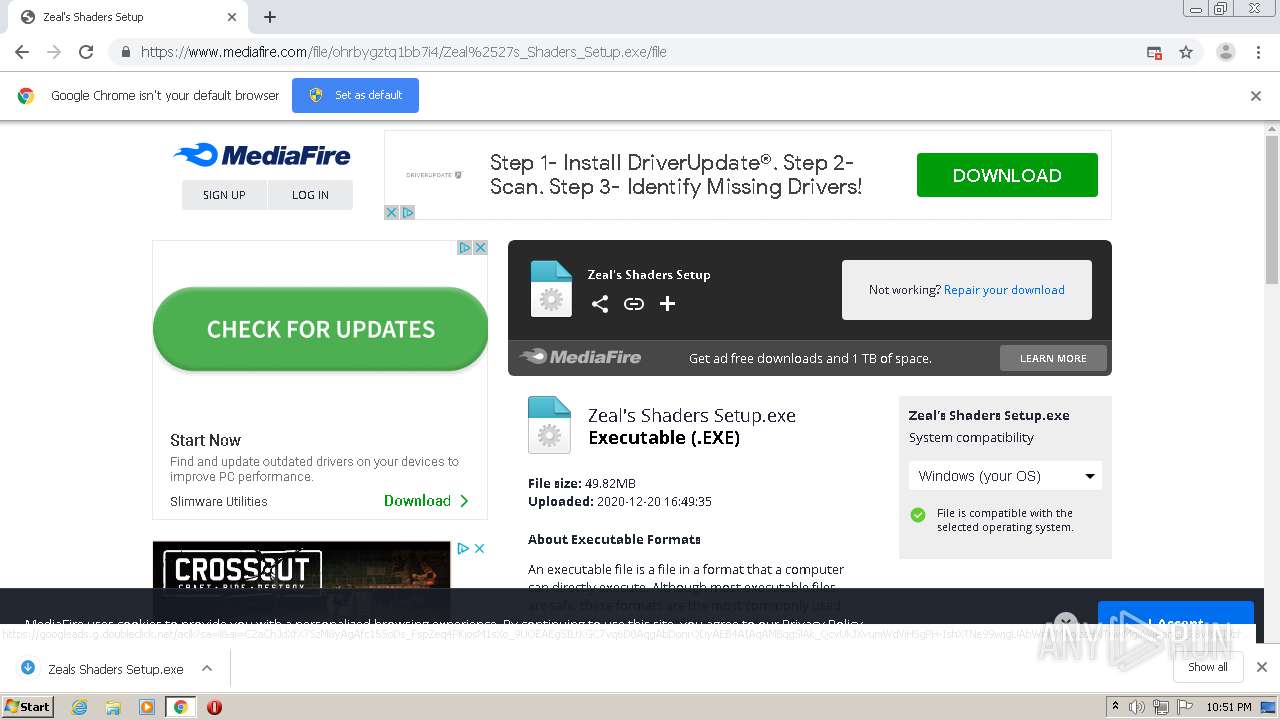
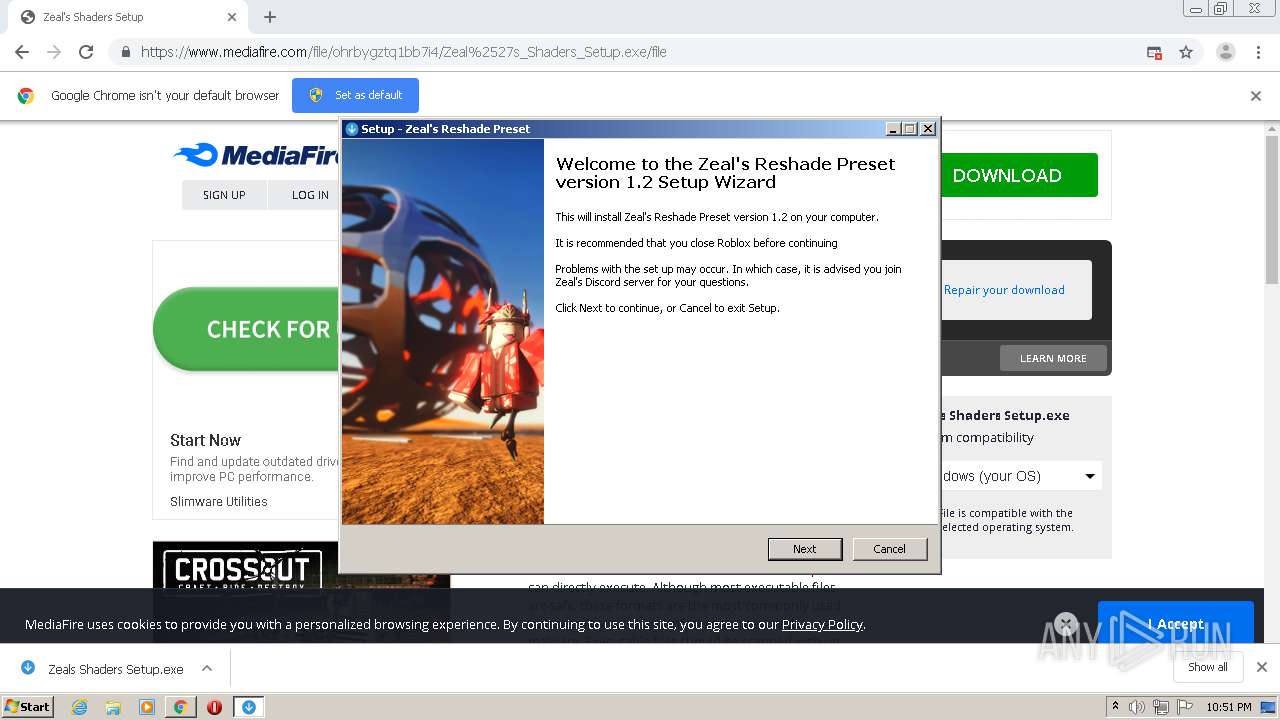
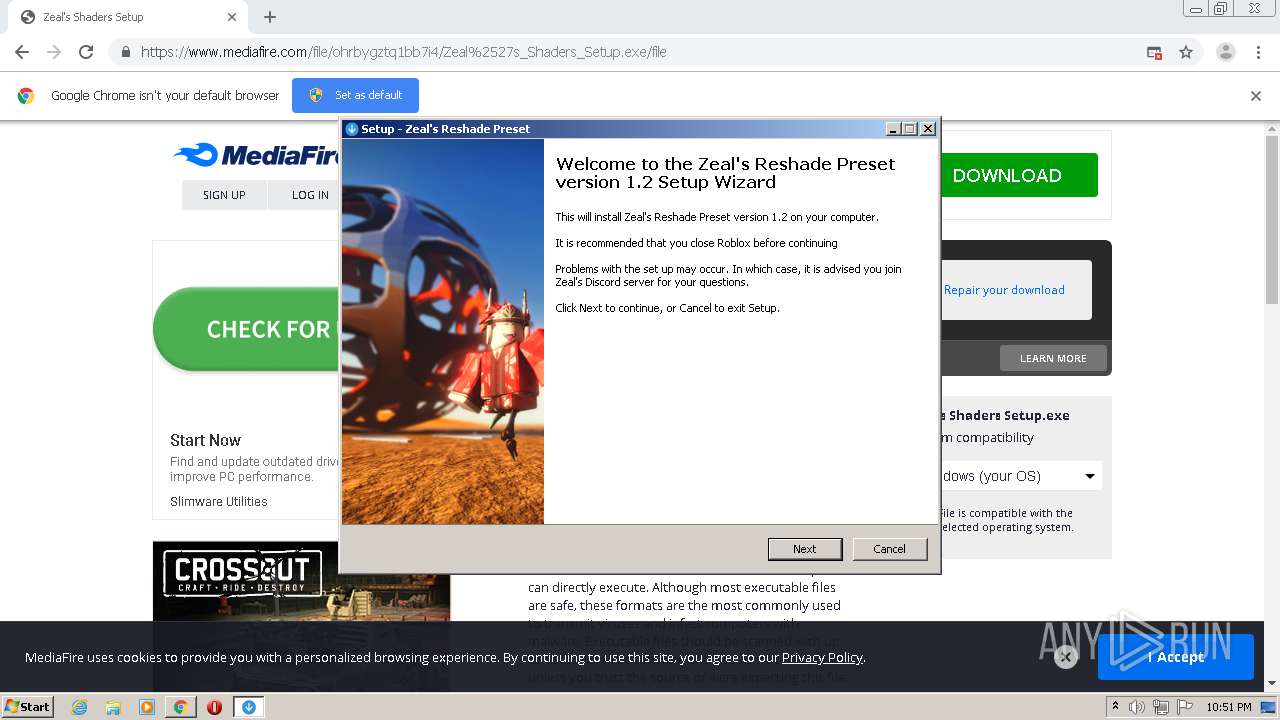
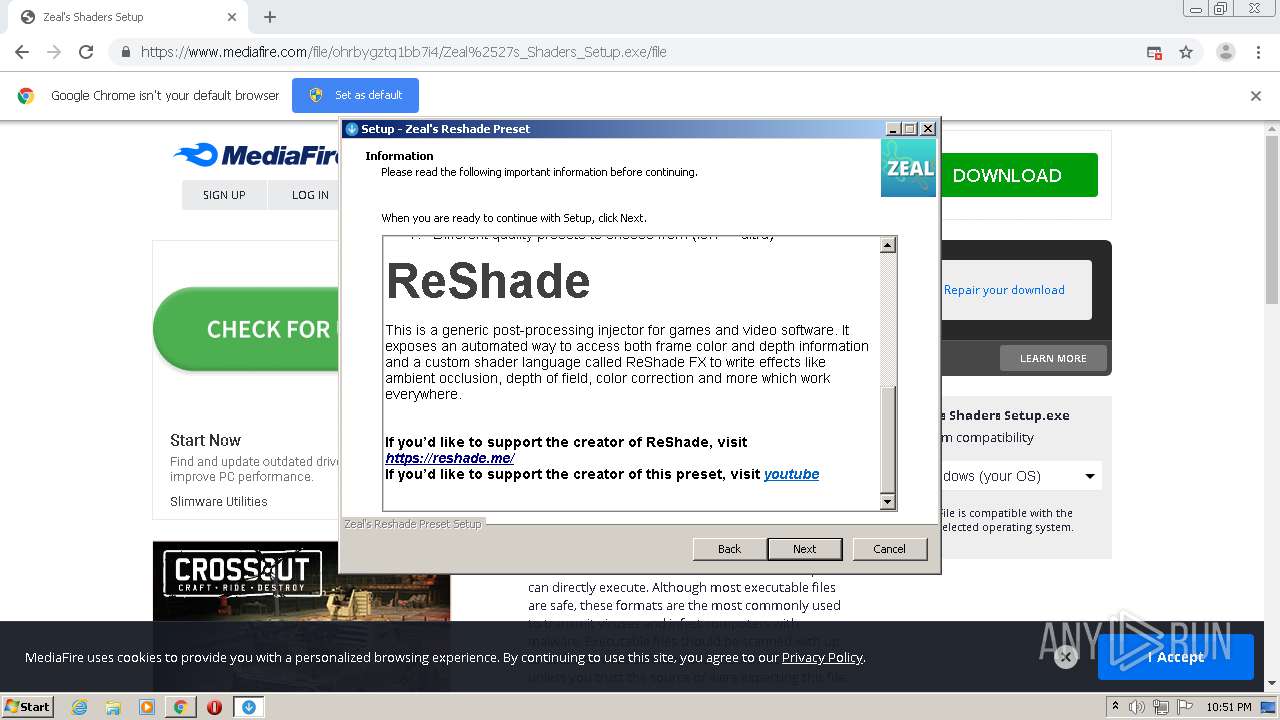
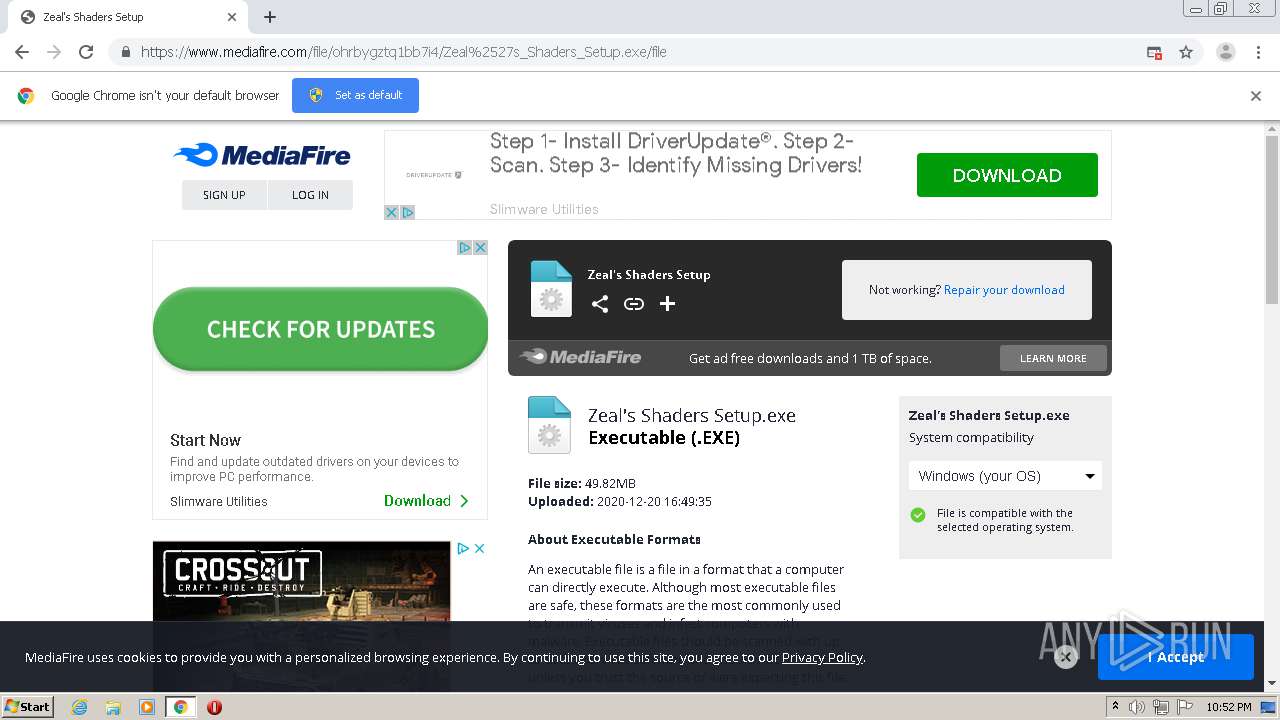
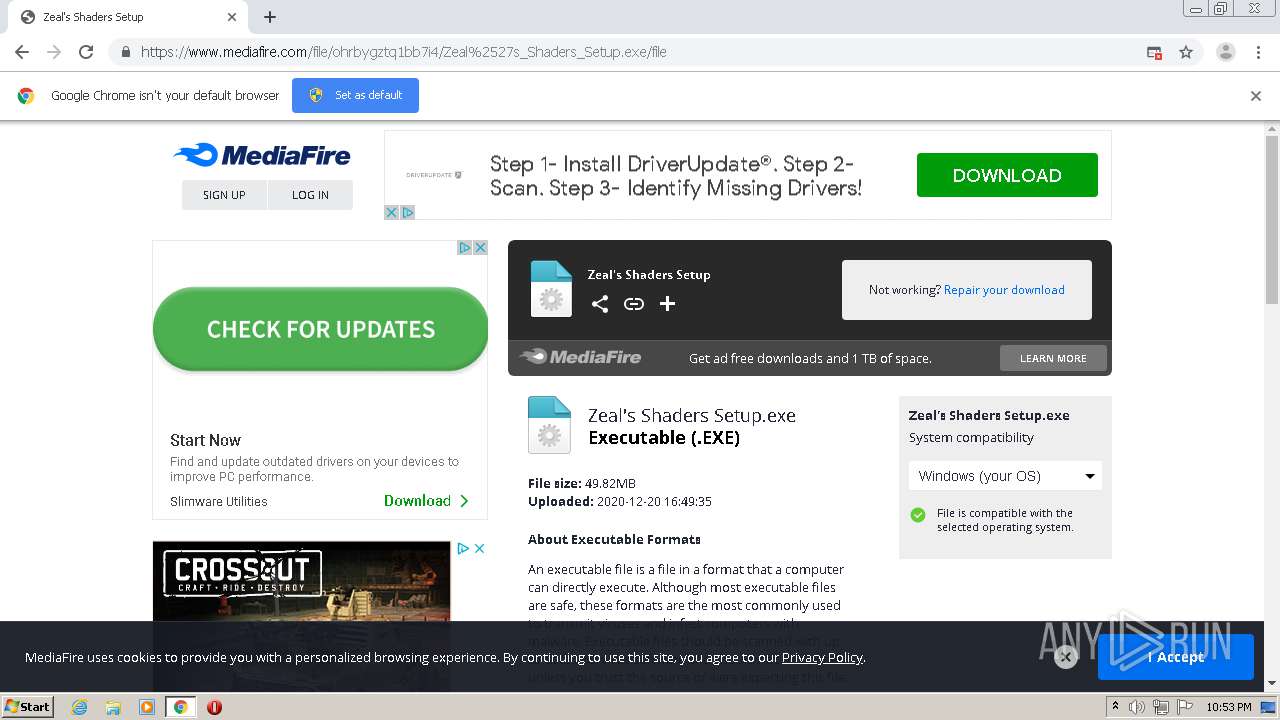
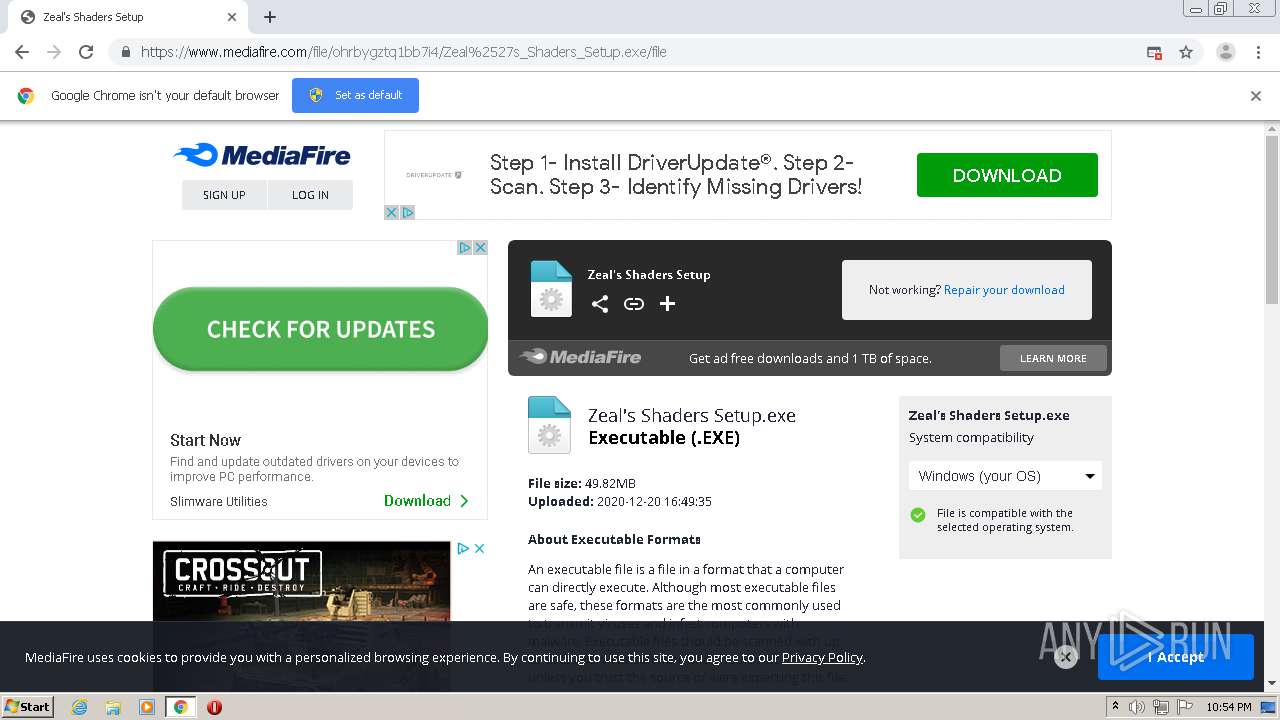
| URL: | https://www.mediafire.com/file/ohrbygztq1bb7i4/Zeal%2527s_Shaders_Setup.exe/file |
| Full analysis: | https://app.any.run/tasks/727492a9-31b3-439e-b46a-f480d4089b92 |
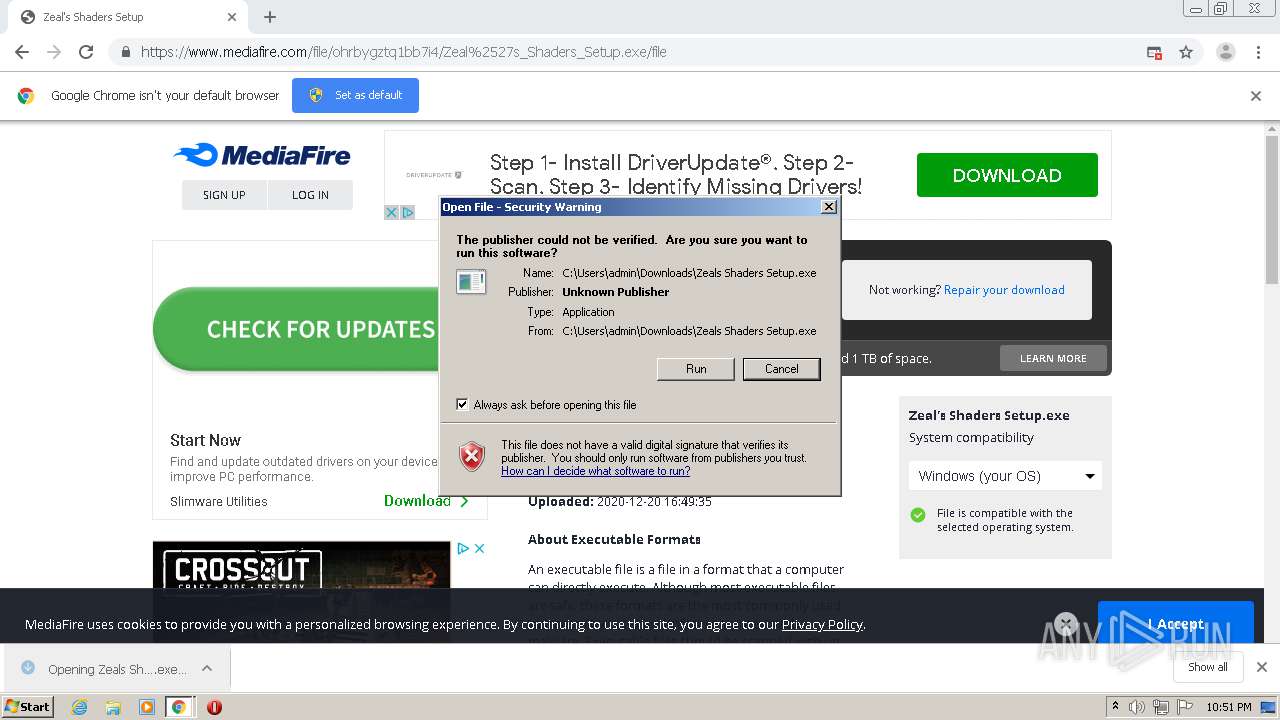
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2020, 22:49:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 34CBBDD41FBFC5F0E7A75C41E72A2A2C |
| SHA1: | AED39EBEB1693368B6CAB52ECD5E00B21FC17C63 |
| SHA256: | DB66CA3459E8CFEA53E015B178BF81273BB185DABF32E099E269A79DE9F4E2B8 |
| SSDEEP: | 3:N8DSLw3eGUoUyiCl6/BAX9vvcA:2OLw3eGAkSBy9vx |
MALICIOUS
Application was dropped or rewritten from another process
- Zeals Shaders Setup.exe (PID: 3428)
- Zeals Shaders Setup.exe (PID: 1700)
Drops executable file immediately after starts
- Zeals Shaders Setup.exe (PID: 3428)
- Zeals Shaders Setup.exe (PID: 1700)
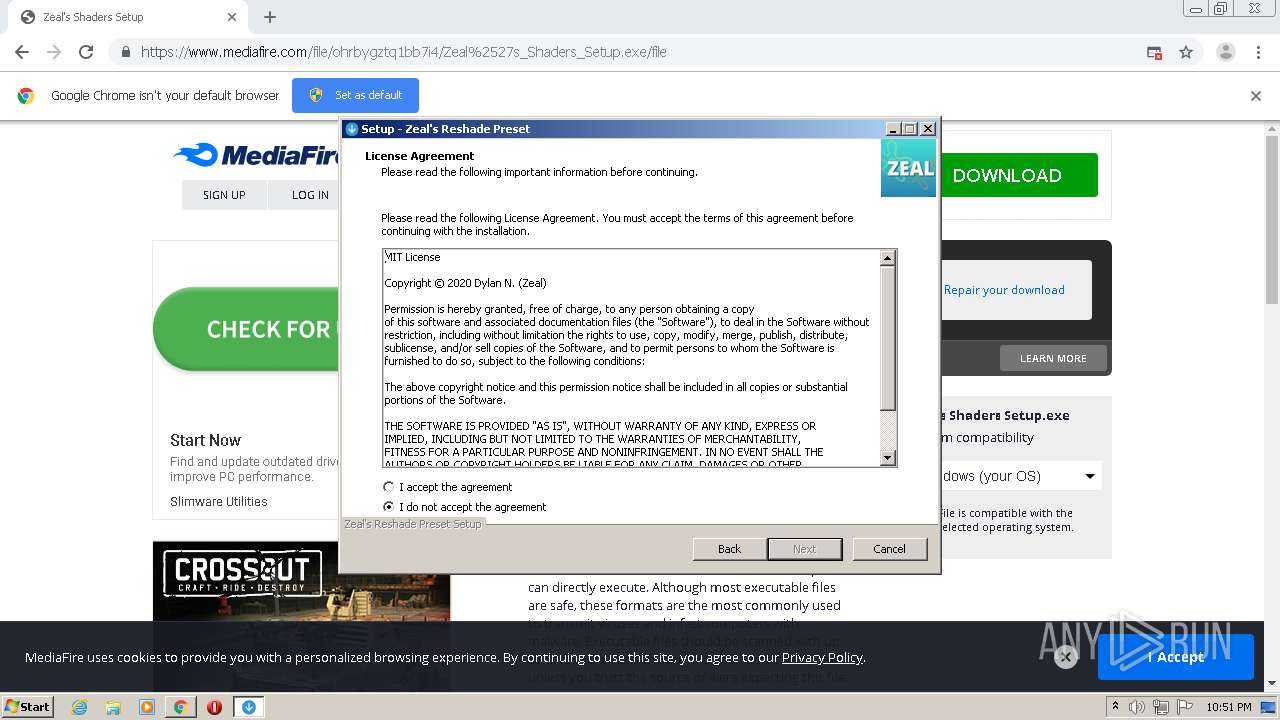
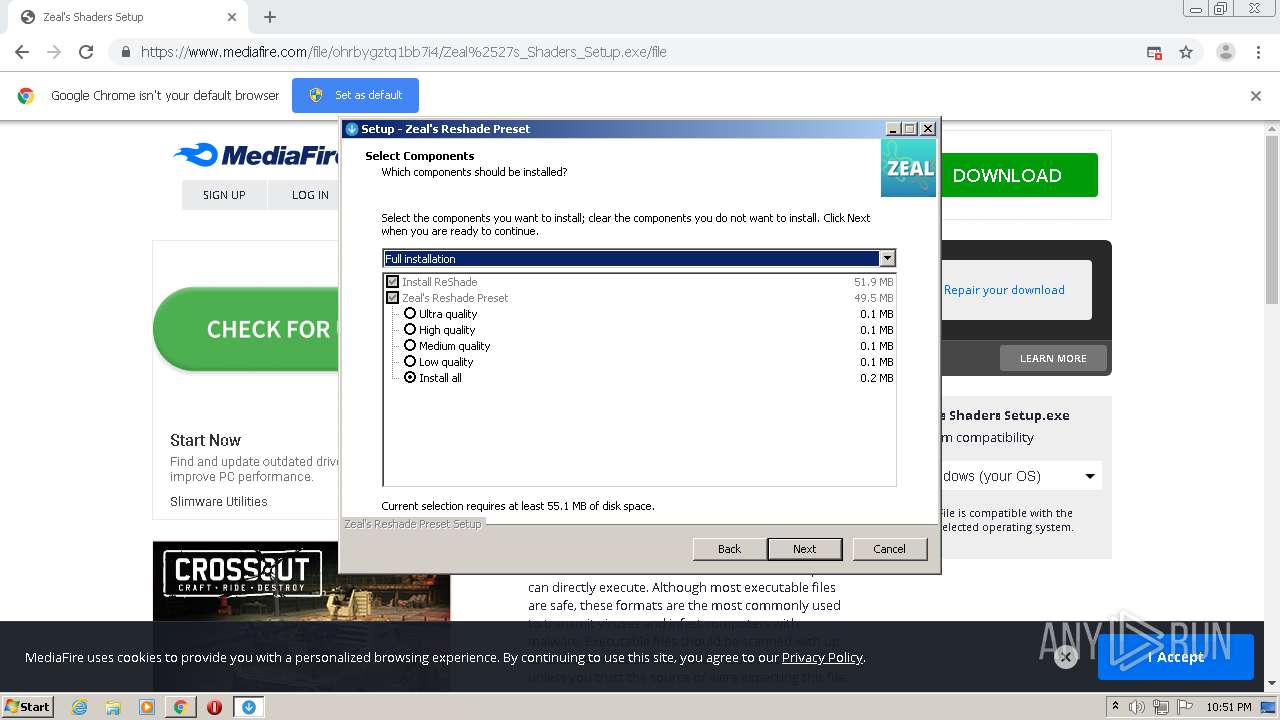
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2420)
- Zeals Shaders Setup.exe (PID: 1700)
- Zeals Shaders Setup.exe (PID: 3428)
- Zeals Shaders Setup.tmp (PID: 2248)
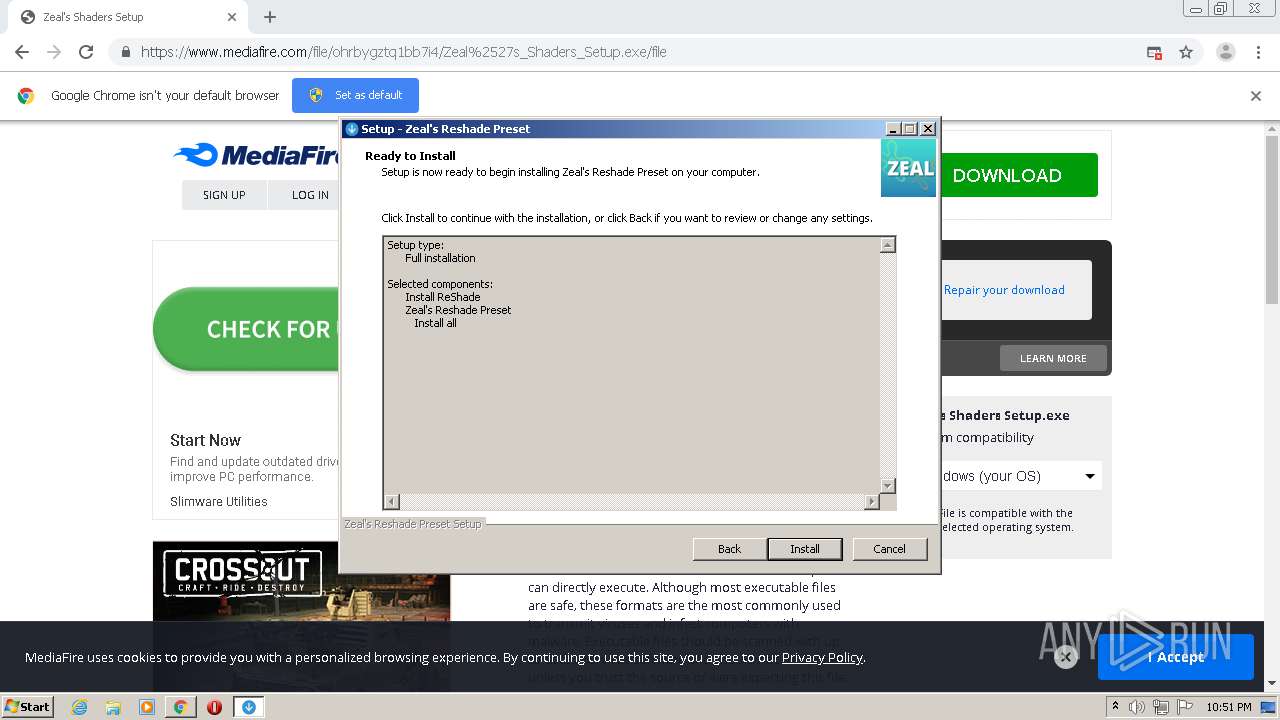
Reads Windows owner or organization settings
- Zeals Shaders Setup.tmp (PID: 2248)
Reads the Windows organization settings
- Zeals Shaders Setup.tmp (PID: 2248)
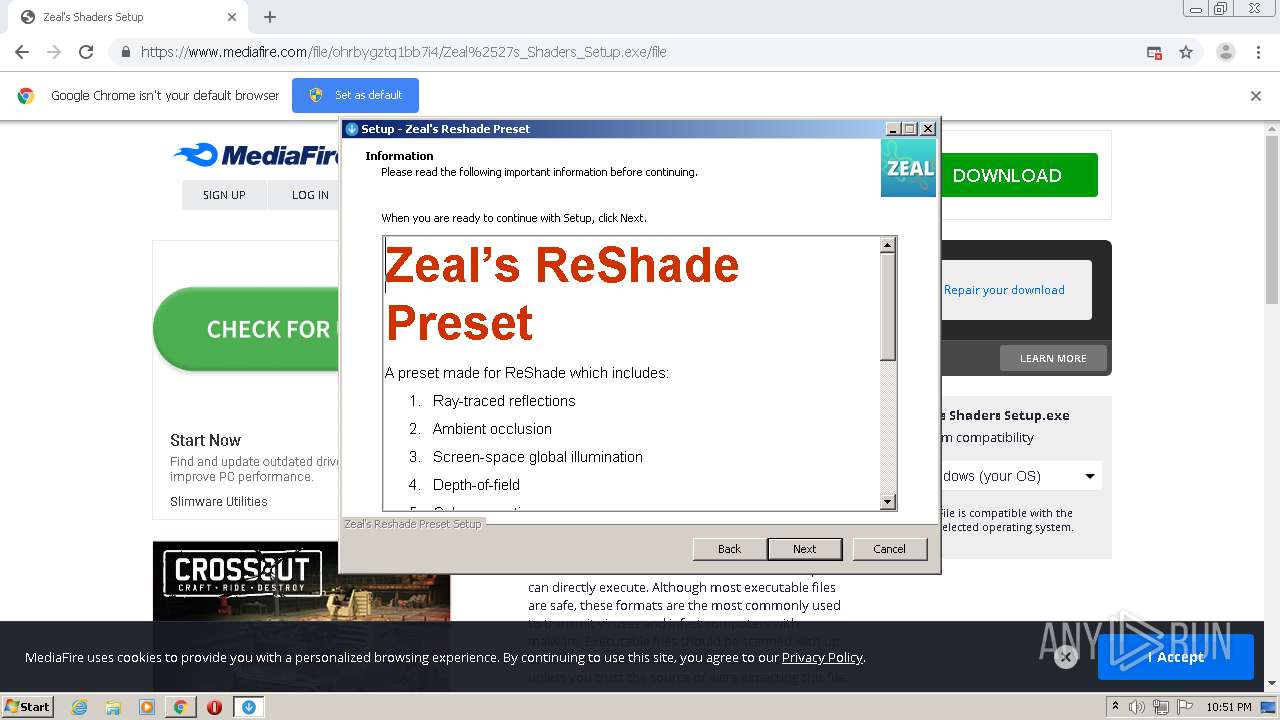
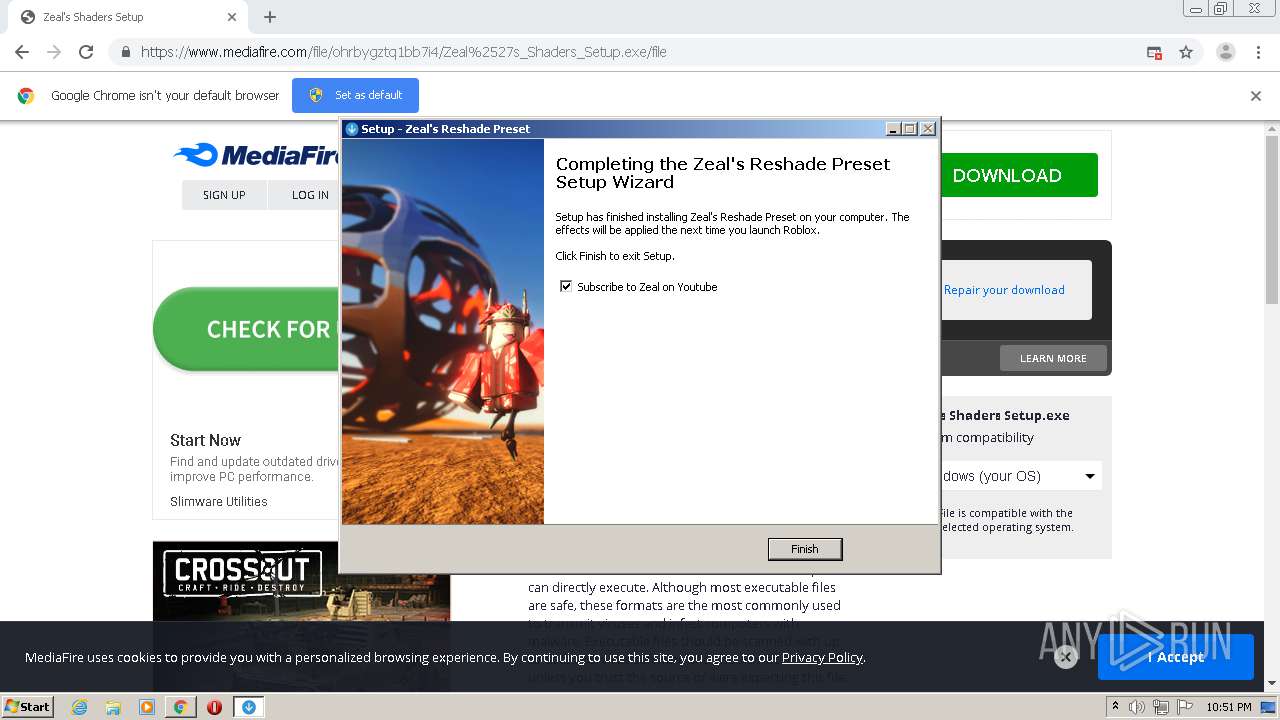
INFO
Reads the hosts file
- chrome.exe (PID: 2420)
- chrome.exe (PID: 1872)
Application launched itself
- chrome.exe (PID: 2420)
Reads settings of System Certificates
- chrome.exe (PID: 2420)
Application was dropped or rewritten from another process
- Zeals Shaders Setup.tmp (PID: 3088)
- Zeals Shaders Setup.tmp (PID: 2248)
Dropped object may contain Bitcoin addresses
- Zeals Shaders Setup.tmp (PID: 2248)
Creates a software uninstall entry
- Zeals Shaders Setup.tmp (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
39
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8400902603397586158 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14915850949909534594 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12481006012065797485 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1775003095474164570 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16711269747572353007 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15168621320664978971 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13839489405788495056 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13293531982910032530 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Users\admin\Downloads\Zeals Shaders Setup.exe" /SPAWNWND=$20174 /NOTIFYWND=$40166 | C:\Users\admin\Downloads\Zeals Shaders Setup.exe | Zeals Shaders Setup.tmp | ||||||||||||
User: admin Company: crosire Integrity Level: HIGH Description: ReShade made by crosire Exit code: 0 Version: Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11217635602504035405,11467751266585712396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17526397341475021246 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 435
Read events
1 315
Write events
113
Delete events
7
Modification events
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2420-13252978205269375 |
Value: 259 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2420-13252978205269375 |
Value: 259 | |||
Executable files
6
Suspicious files
75
Text files
440
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FDFD51D-974.pma | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9f754b7c-016e-46f3-b84b-a04575936103.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF150568.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150681.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
158
DNS requests
112
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1872 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1872 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 216.58.207.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1872 | chrome.exe | 216.58.207.78:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 172.217.15.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 104.84.85.138:443 | c.aaxads.com | Vodafone NZ Ltd. | US | unknown |
1872 | chrome.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1872 | chrome.exe | 185.33.221.14:443 | ib.adnxs.com | AppNexus, Inc | — | unknown |
1872 | chrome.exe | 172.217.2.110:443 | translate.google.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 216.58.212.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
fundingchoicesmessages.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
cdn.otnolatrnup.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1872 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1872 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |