| File name: | $R8CGOC8.exe |
| Full analysis: | https://app.any.run/tasks/80613b22-3c5a-4444-b938-bcaf3a1965ab |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2023, 06:53:48 |
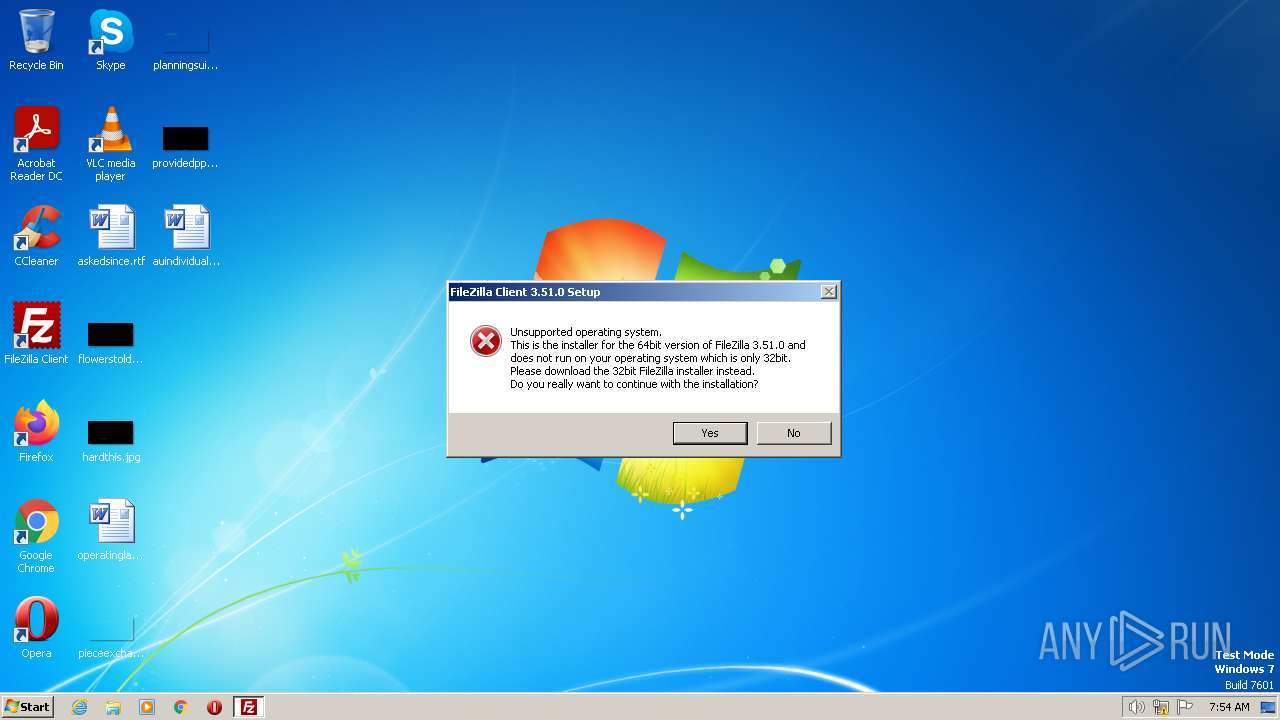
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | FAADC03D9A58925BA4784002DC48A81F |
| SHA1: | C8427258F566F22F7117D3B86B16F806A6EEB9AE |
| SHA256: | DB5B1CC525BC2F57876667CD8B67E99EEEAB7784CFCBD1CCFFB9104FB317BCC9 |
| SSDEEP: | 393216:8fJAUnXJNQwNUXGhQsgzI2UdchjkJ7MPbeI:8xBnZNZqXGhfgYWhkObf |
MALICIOUS
Loads dropped or rewritten executable
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Actions looks like stealing of personal data
- $R8CGOC8.exe (PID: 3696)
SUSPICIOUS
Application launched itself
- $R8CGOC8.exe (PID: 2340)
The process creates files with name similar to system file names
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Executable content was dropped or overwritten
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Reads the Internet Settings
- $R8CGOC8.exe (PID: 3696)
Reads Microsoft Outlook installation path
- $R8CGOC8.exe (PID: 3696)
Reads Internet Explorer settings
- $R8CGOC8.exe (PID: 3696)
Searches for installed software
- $R8CGOC8.exe (PID: 3696)
INFO
Checks supported languages
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
The process checks LSA protection
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Reads the computer name
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Create files in a temporary directory
- $R8CGOC8.exe (PID: 2340)
- $R8CGOC8.exe (PID: 3696)
- uninstall.exe (PID: 3476)
Checks proxy server information
- $R8CGOC8.exe (PID: 3696)
Reads the machine GUID from the registry
- $R8CGOC8.exe (PID: 3696)
Reads product name
- $R8CGOC8.exe (PID: 3696)
Reads Environment values
- $R8CGOC8.exe (PID: 3696)
Creates files in the program directory
- $R8CGOC8.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
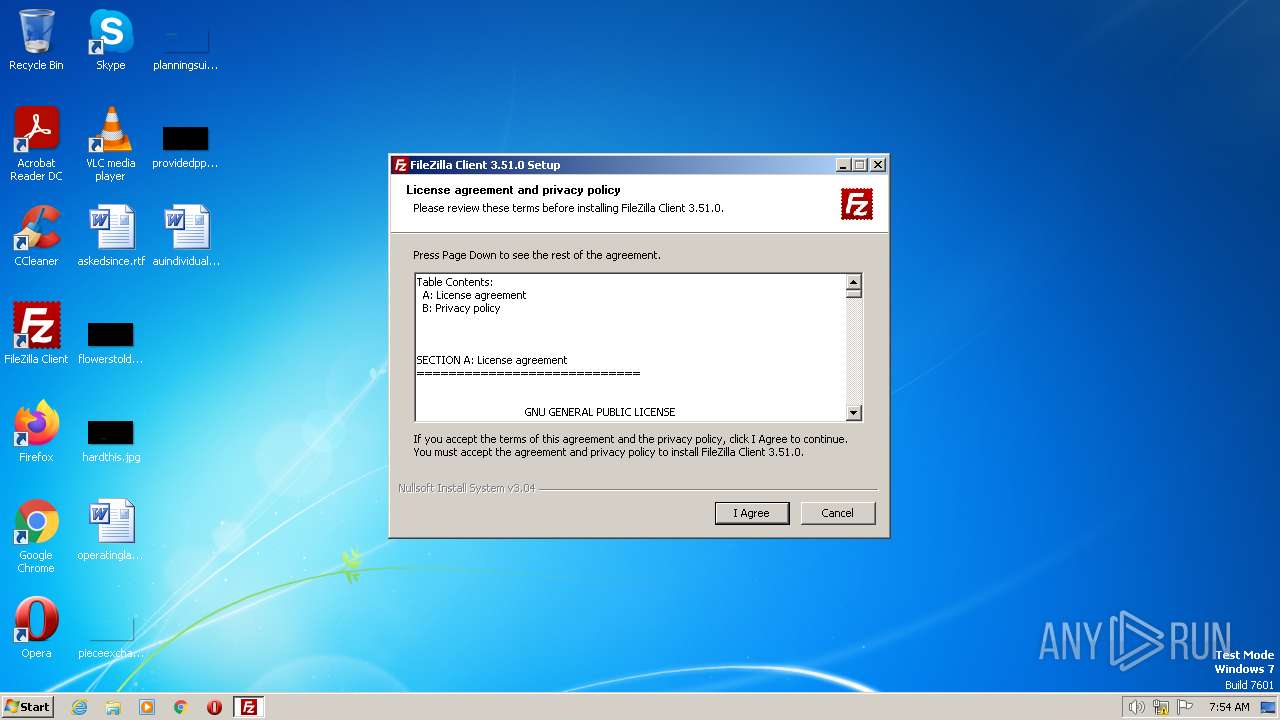
| ProductVersion: | 3.51.0 |
|---|---|
| ProductName: | FileZilla |
| OriginalFileName: | FileZilla_3.51.0_win32-setup.exe |
| LegalCopyright: | Tim Kosse |
| FileVersion: | 3.51.0 |
| FileDescription: | FileZilla FTP Client |
| CompanyName: | Tim Kosse |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.51.0.0 |
| FileVersionNumber: | 3.51.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x34a5 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2018:12:15 22:24:36+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:36 |
| Detected languages: |
|
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.51.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFilename: | FileZilla_3.51.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.51.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41619 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15491 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00040000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006B000 | 0x0000A3A0 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57303 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.69314 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.16834 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.66044 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.91531 | 1384 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.63186 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
48
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
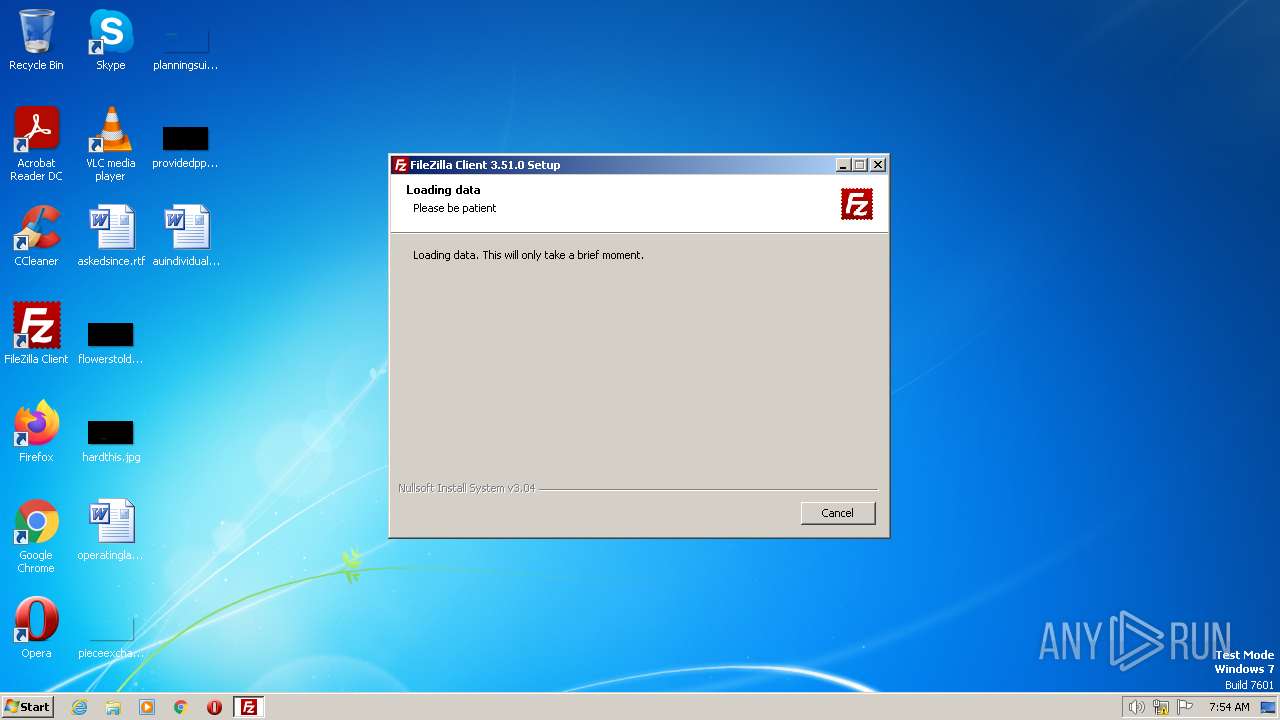
| 2340 | "C:\Users\admin\AppData\Local\Temp\$R8CGOC8.exe" | C:\Users\admin\AppData\Local\Temp\$R8CGOC8.exe | explorer.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3.51.0 Modules
| |||||||||||||||
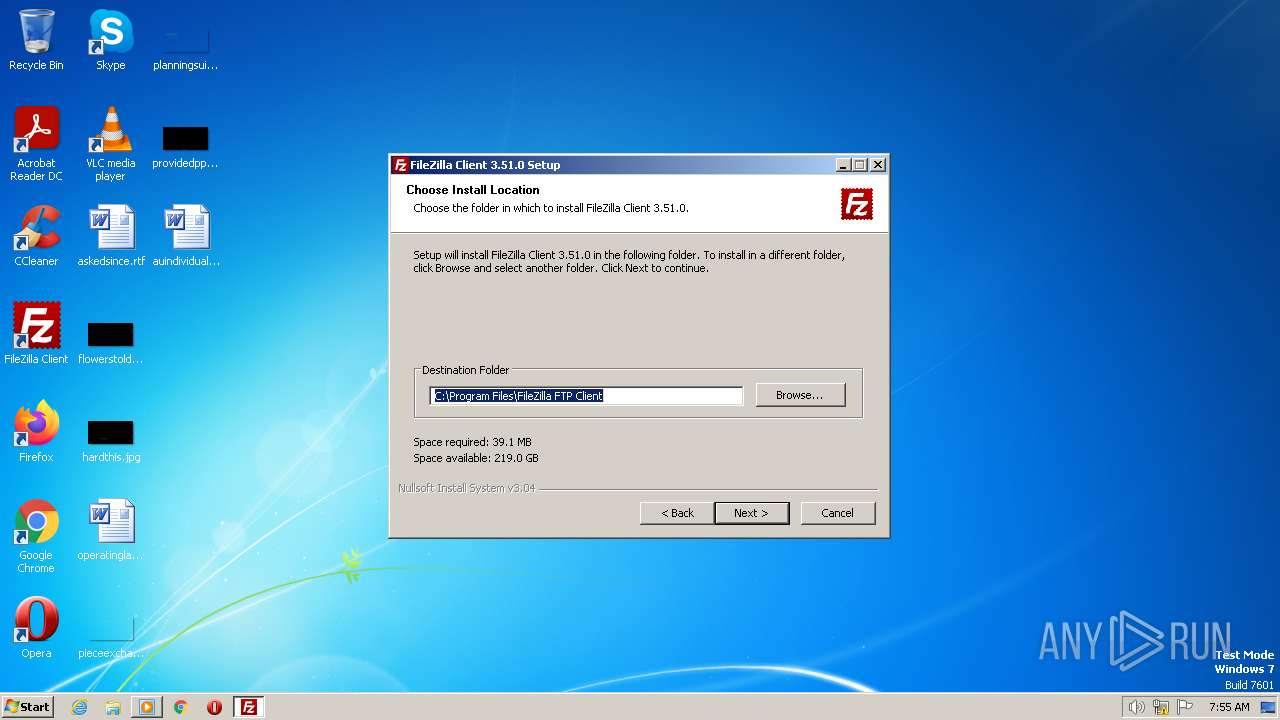
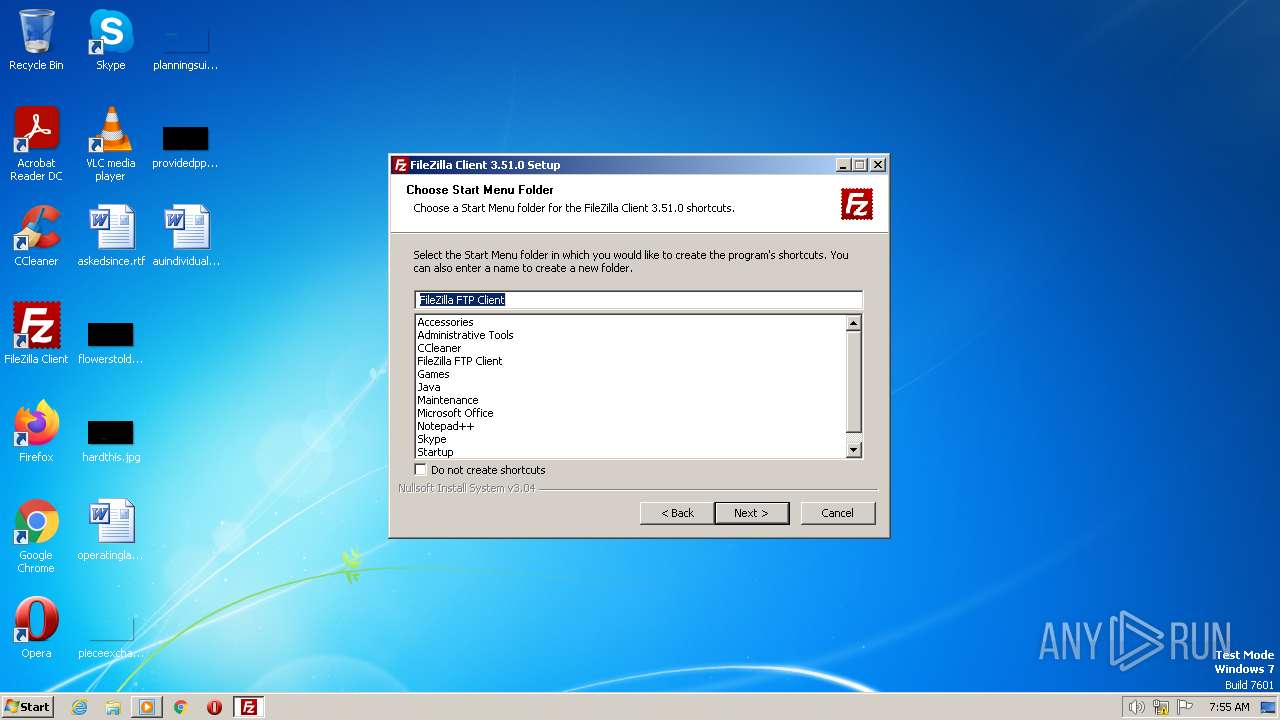
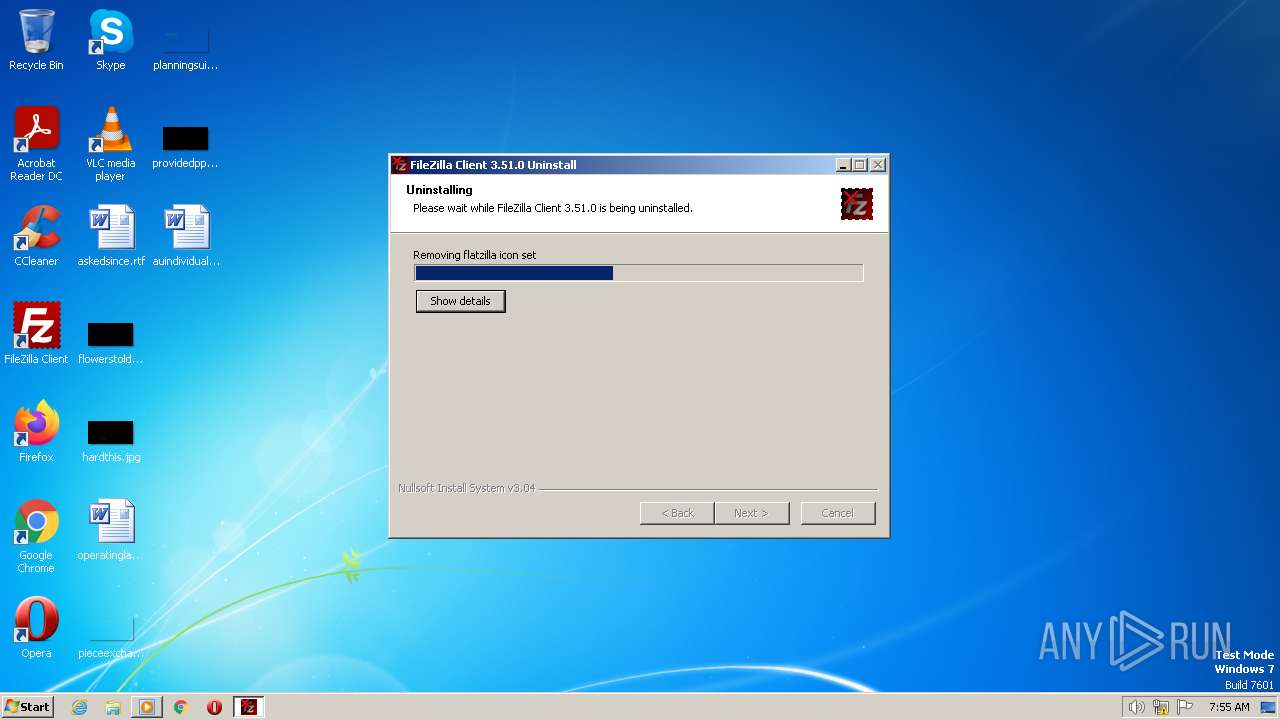
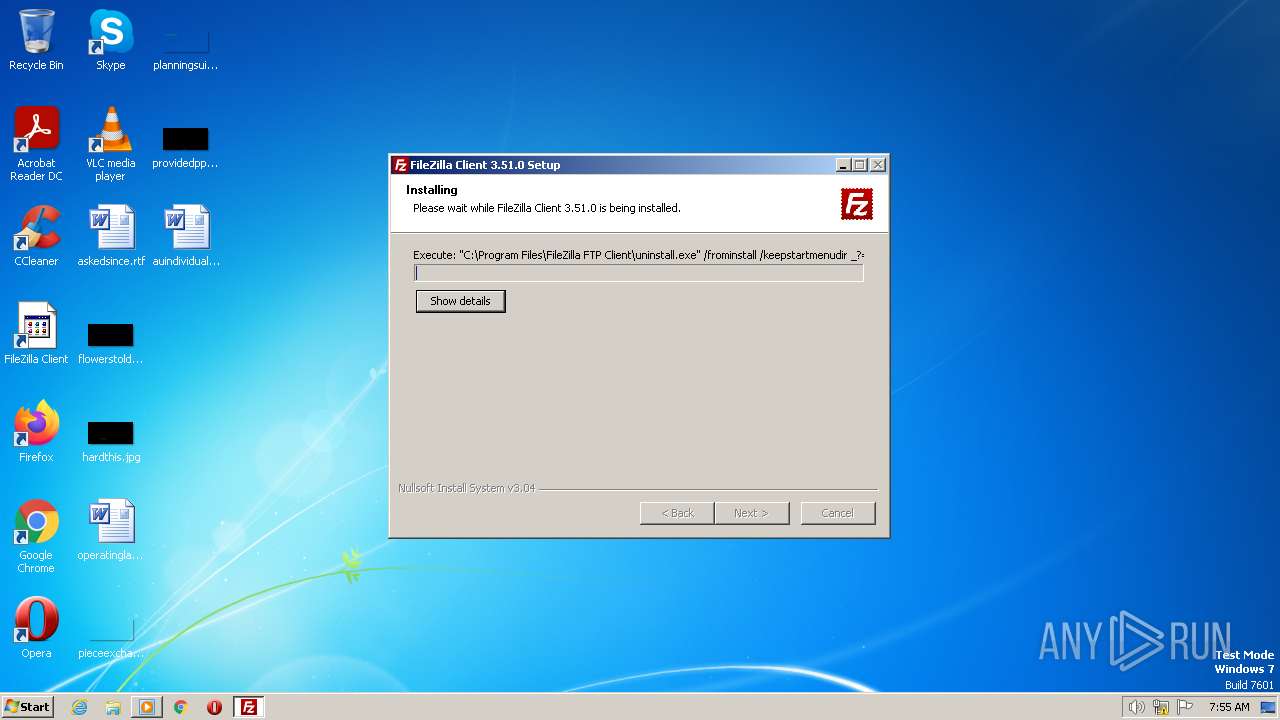
| 3476 | "C:\Program Files\FileZilla FTP Client\uninstall.exe" /frominstall /keepstartmenudir _?=C:\Program Files\FileZilla FTP Client | C:\Program Files\FileZilla FTP Client\uninstall.exe | $R8CGOC8.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.51.0 Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\AppData\Local\Temp\$R8CGOC8.exe" /UAC:F0194 /NCRC | C:\Users\admin\AppData\Local\Temp\$R8CGOC8.exe | $R8CGOC8.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.51.0 Modules
| |||||||||||||||
Total events
3 053
Read events
2 837
Write events
199
Delete events
17
Modification events
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (3696) $R8CGOC8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionTime |
Value: 4495E00C8D9ED901 | |||
Executable files
39
Suspicious files
7
Text files
732
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
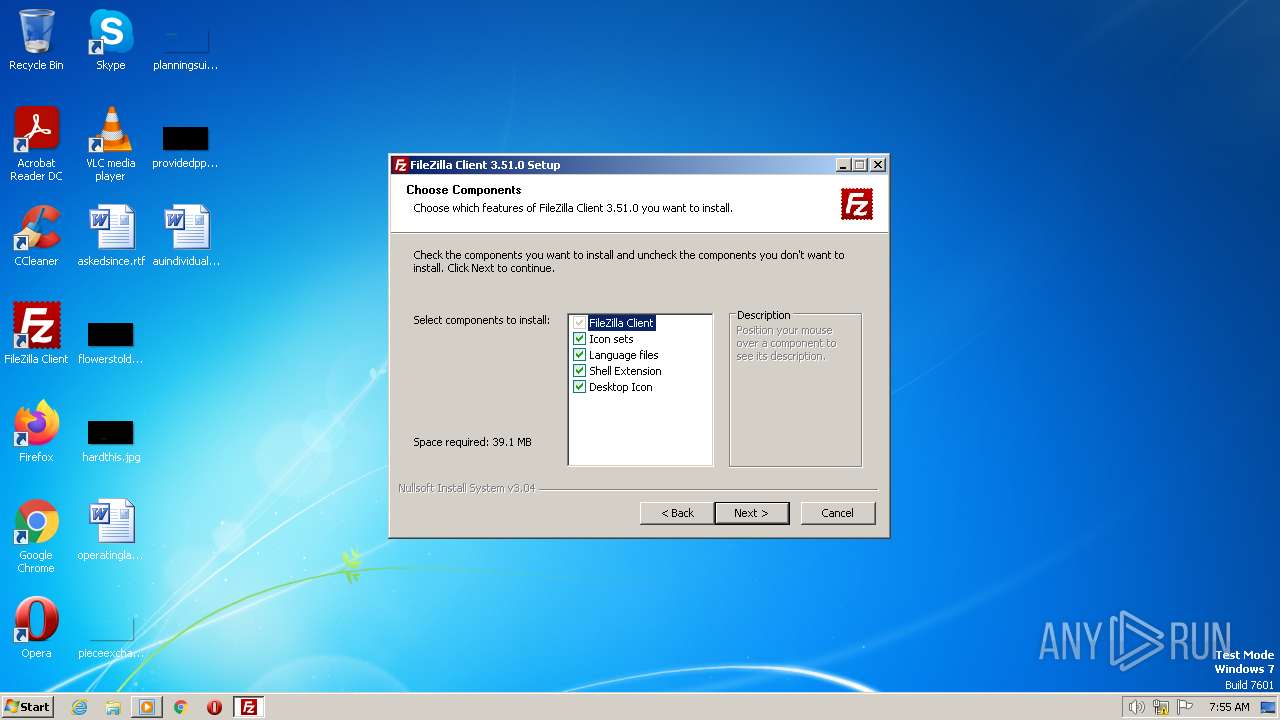
| 2340 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsr787B.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsv9D29.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsv9D29.tmp\INetC.dll | executable | |
MD5:640BFF73A5F8E37B202D911E4749B2E9 | SHA256:C1E568E25EC111184DEB1B87CFDA4BFEC529B1ABEAB39B66539D998012F33502 | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsv9D29.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsv9D29.tmp\UserInfo.dll | executable | |
MD5:9EB662F3B5FBDA28BFFE020E0AB40519 | SHA256:9AA388C7DE8E96885ADCB4325AF871B470AC50EDB60D4B0D876AD43F5332FFD1 | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsd121021811475\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsv9D29.tmp\nsDialogs.dll | executable | |
MD5:466179E1C8EE8A1FF5E4427DBB6C4A01 | SHA256:1E40211AF65923C2F4FD02CE021458A7745D28E2F383835E3015E96575632172 | |||
| 2340 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsr787B.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsd121021811475\css\sdk-ui\checkbox.css | text | |
MD5:64773C6B0E3413C81AEBC46CCE8C9318 | SHA256:B09504C1BF0486D3EC46500592B178A3A6C39284672AF8815C3687CC3D29560D | |||
| 3696 | $R8CGOC8.exe | C:\Users\admin\AppData\Local\Temp\nsd121021811475\css\sdk-ui\images\progress-bg-corner.png | image | |
MD5:608F1F20CD6CA9936EAA7E8C14F366BE | SHA256:86B6E6826BCDE2955D64D4600A4E01693522C1FDDF156CE31C4BA45B3653A7BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
47
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1476 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3696 | $R8CGOC8.exe | 49.12.121.47:443 | offers.filezilla-project.org | Hetzner Online GmbH | DE | suspicious |
1076 | svchost.exe | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
offers.filezilla-project.org |
| whitelisted |
dns.msftncsi.com |
| shared |
cloud.nitehe-nutete.com |
| whitelisted |
remote.nitehe-nutete.com |
| shared |
ww1.nitehe-nutete.com |
| shared |