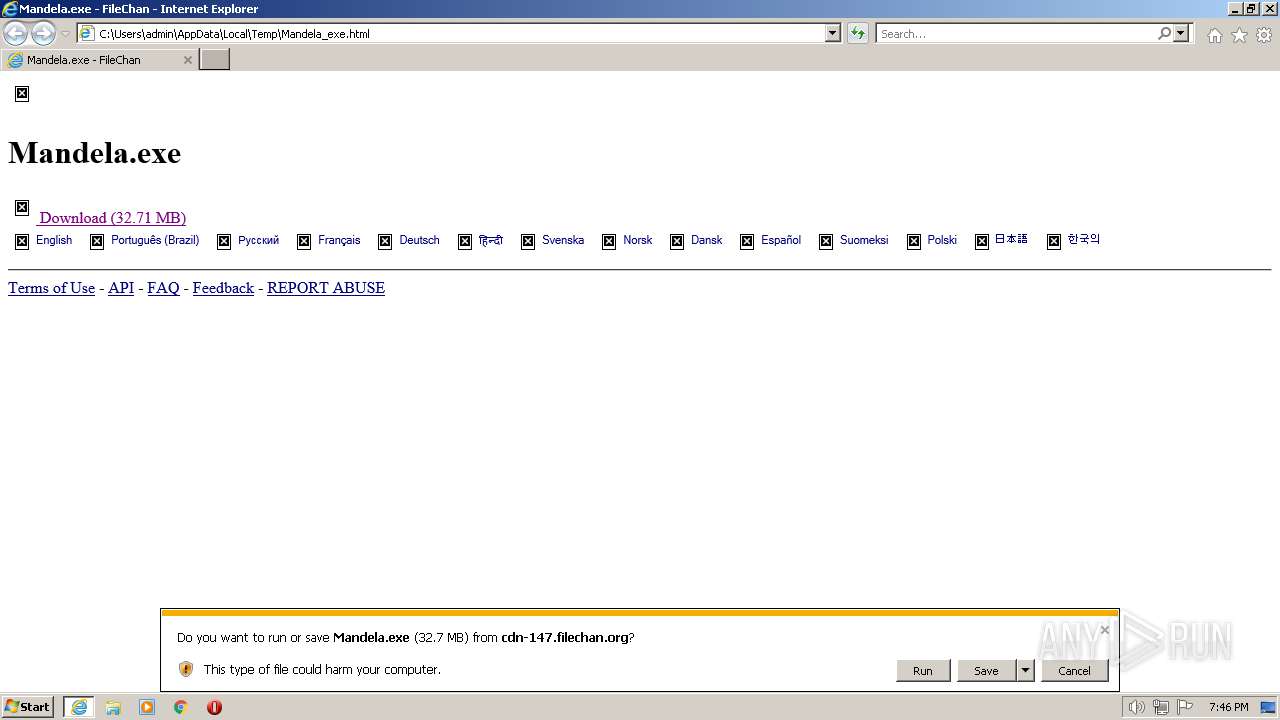
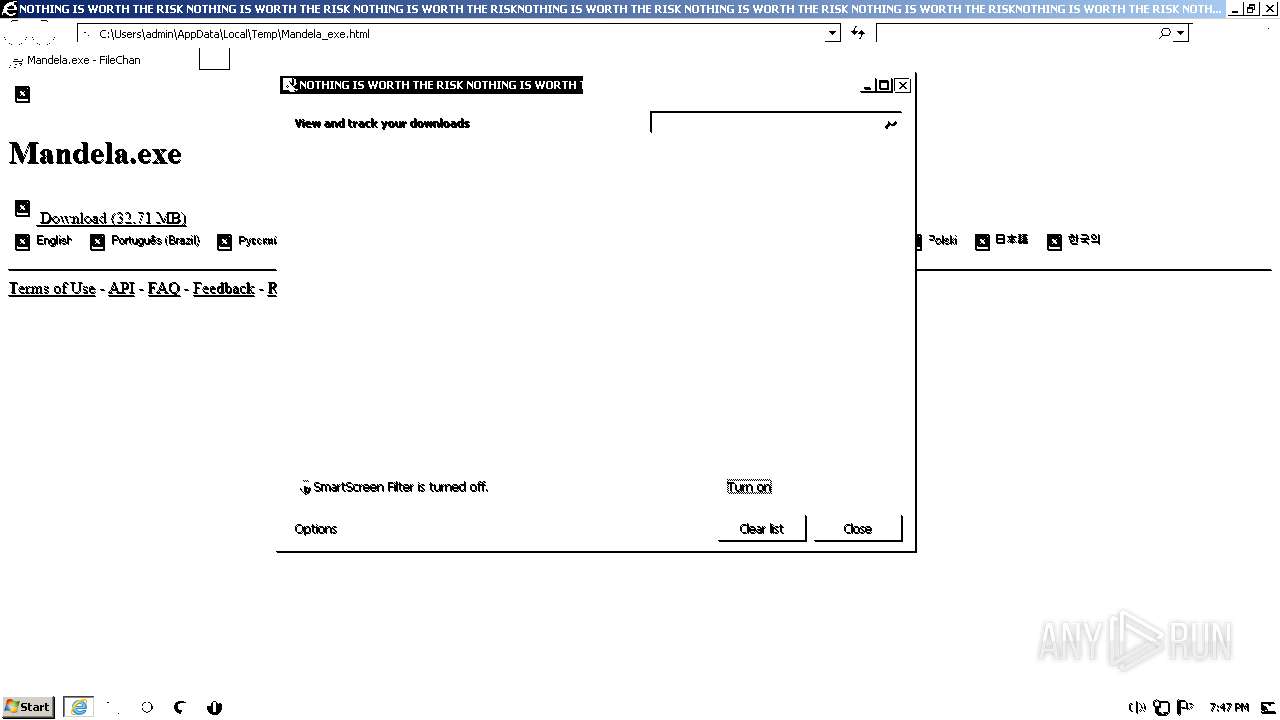
| download: | Mandela_exe |
| Full analysis: | https://app.any.run/tasks/0d87946c-e5c1-4d23-8832-c7880f6bd23f |
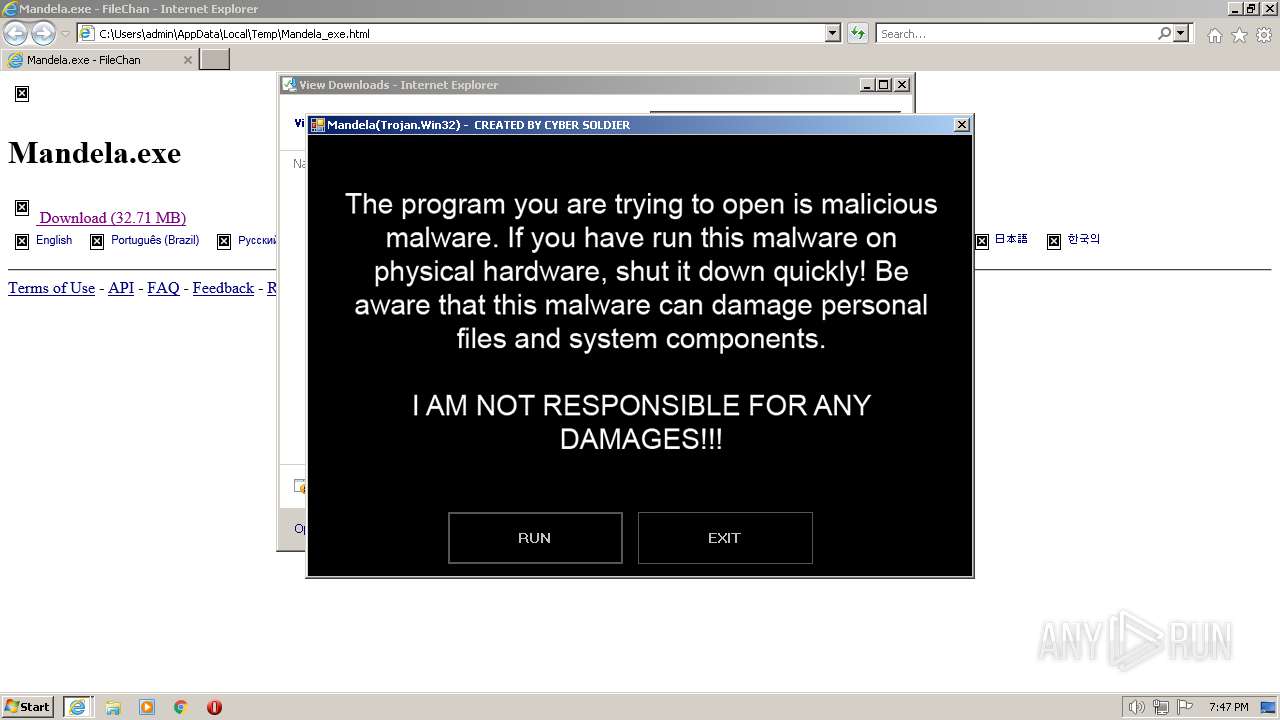
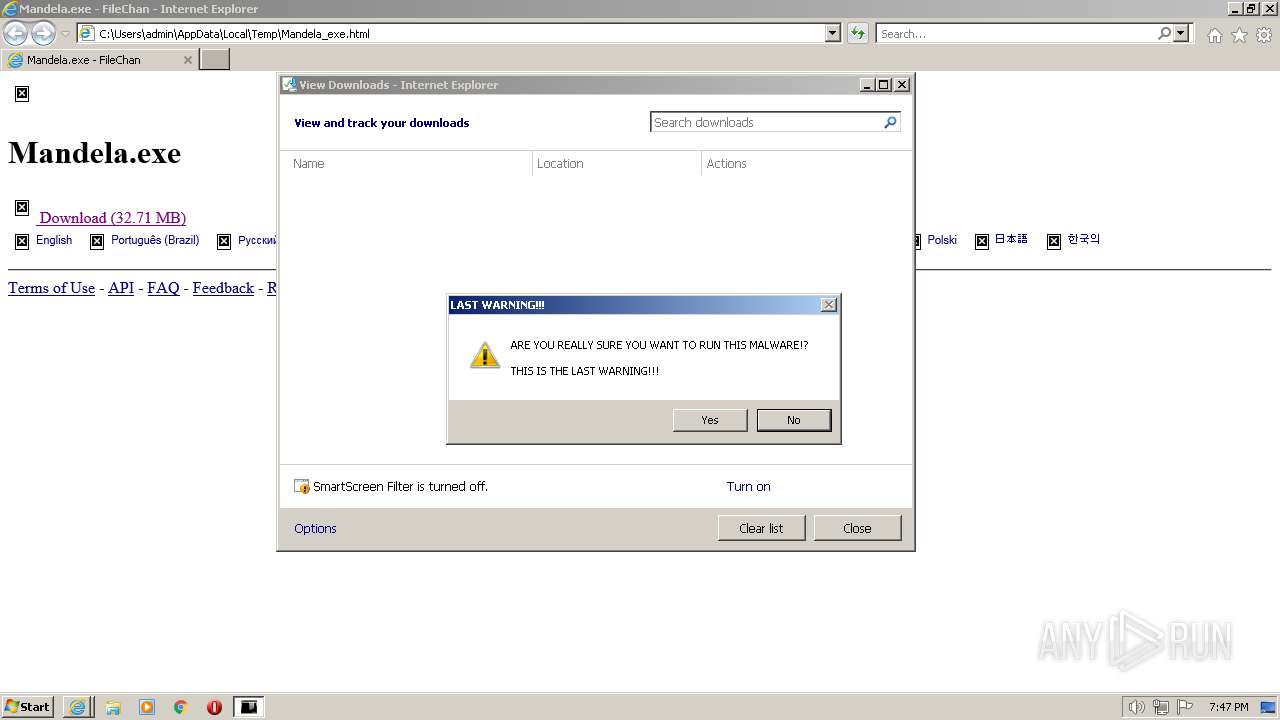
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2023, 18:45:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | B872F960106284447D97B29064BD5B4A |
| SHA1: | E13D46C7E2CBC754254869FD2C69A1E4FB6FD99E |
| SHA256: | DB5569742C543815649796A263C65A917DF4CF19D10418C5CFE62A6A2822C3DC |
| SSDEEP: | 192:/fxibAFi7avnGcOadF4+mP6SGOaJrNQfavV2iJyc:8bui7avTOadF4+tSGOaJrNQfav0S |
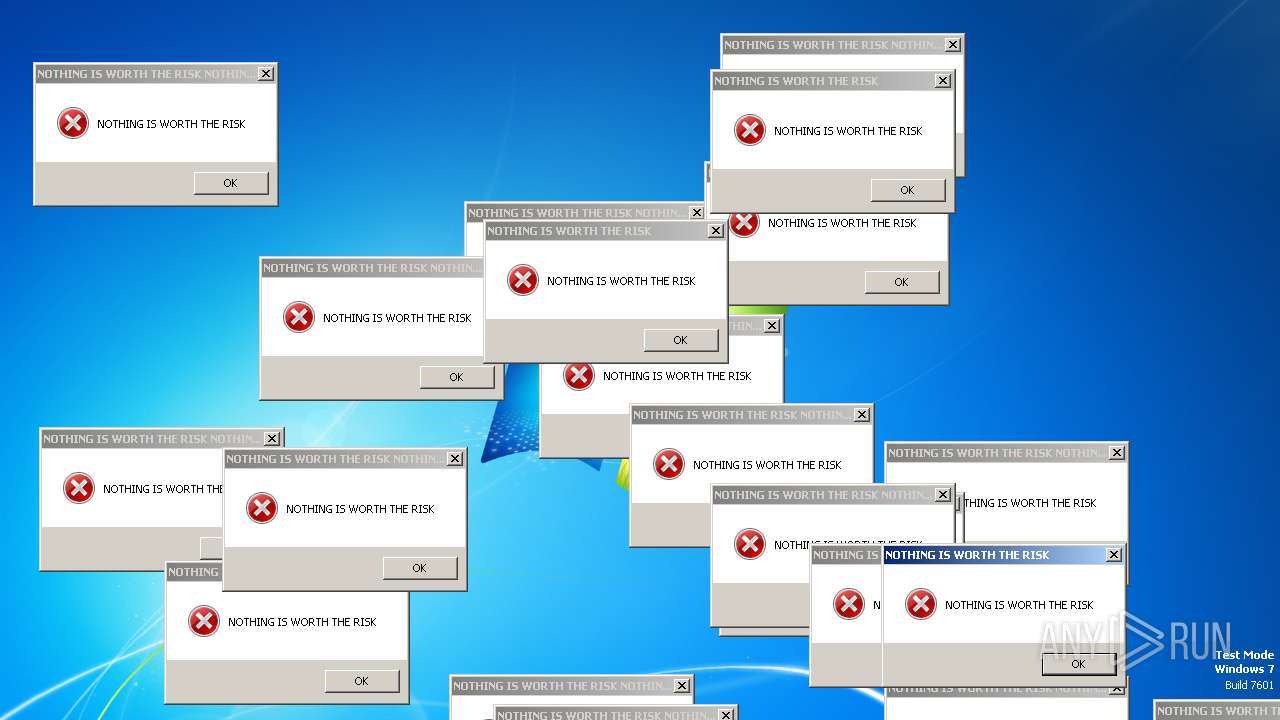
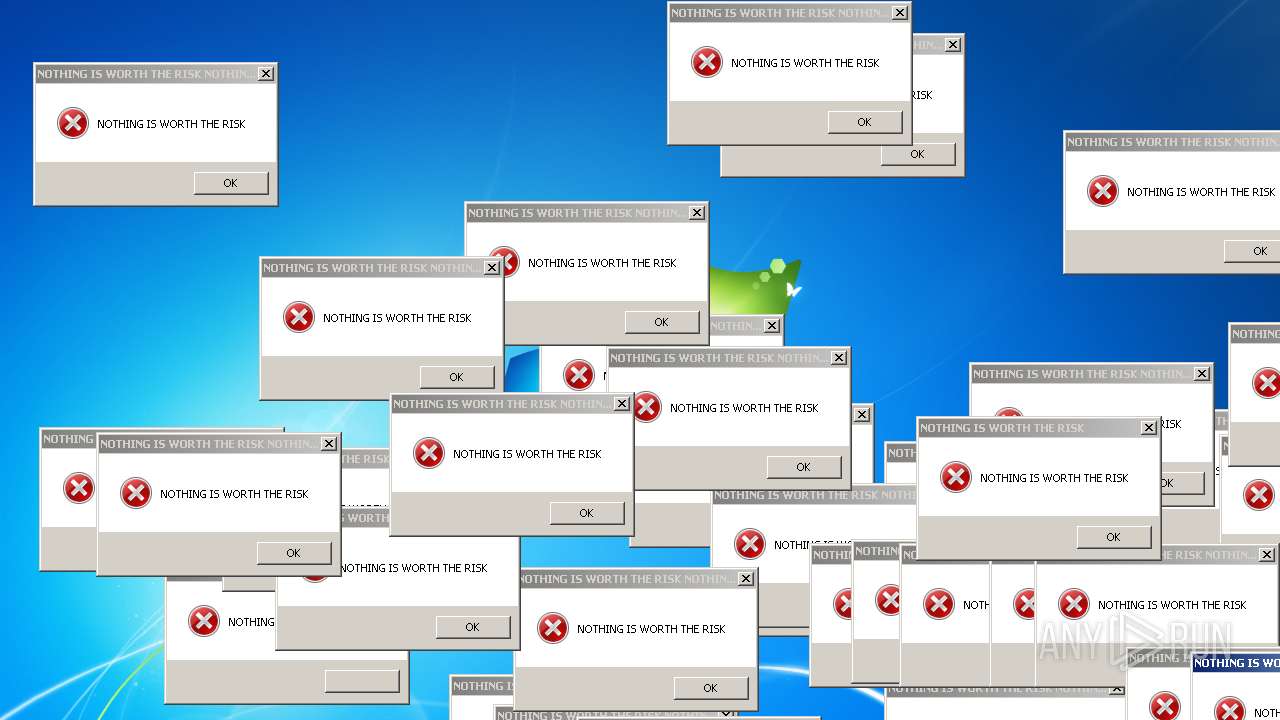
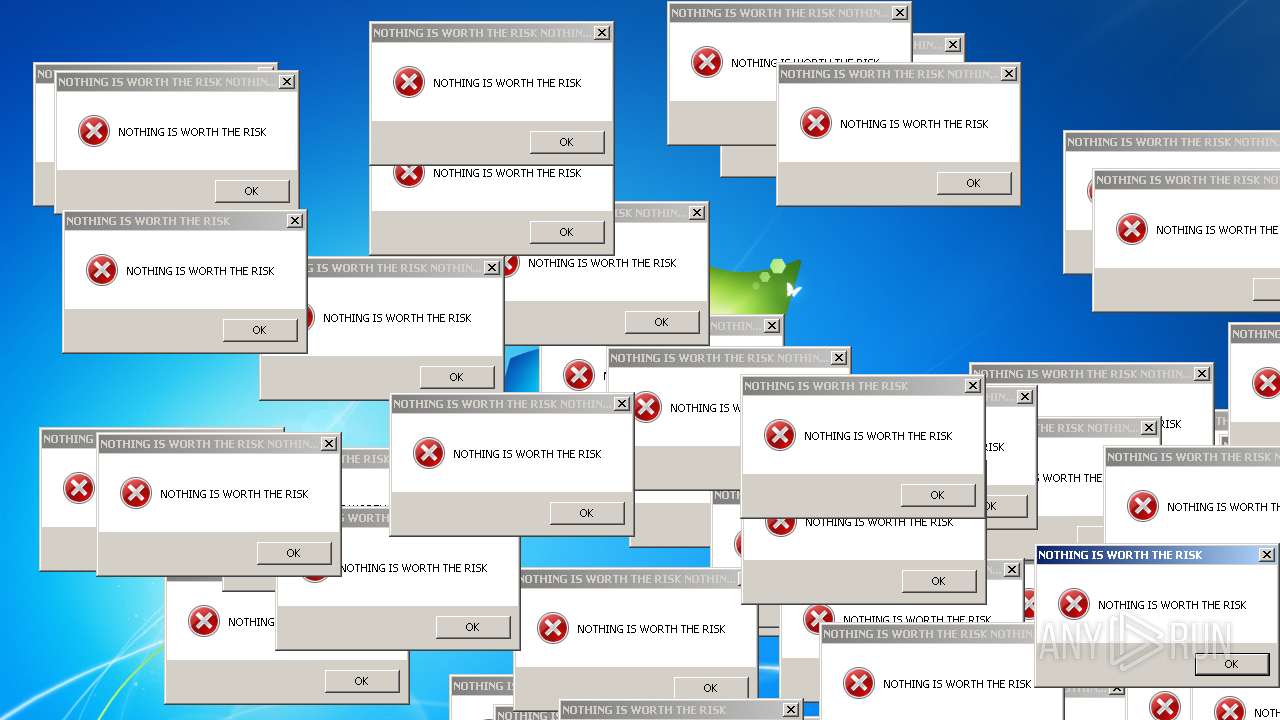
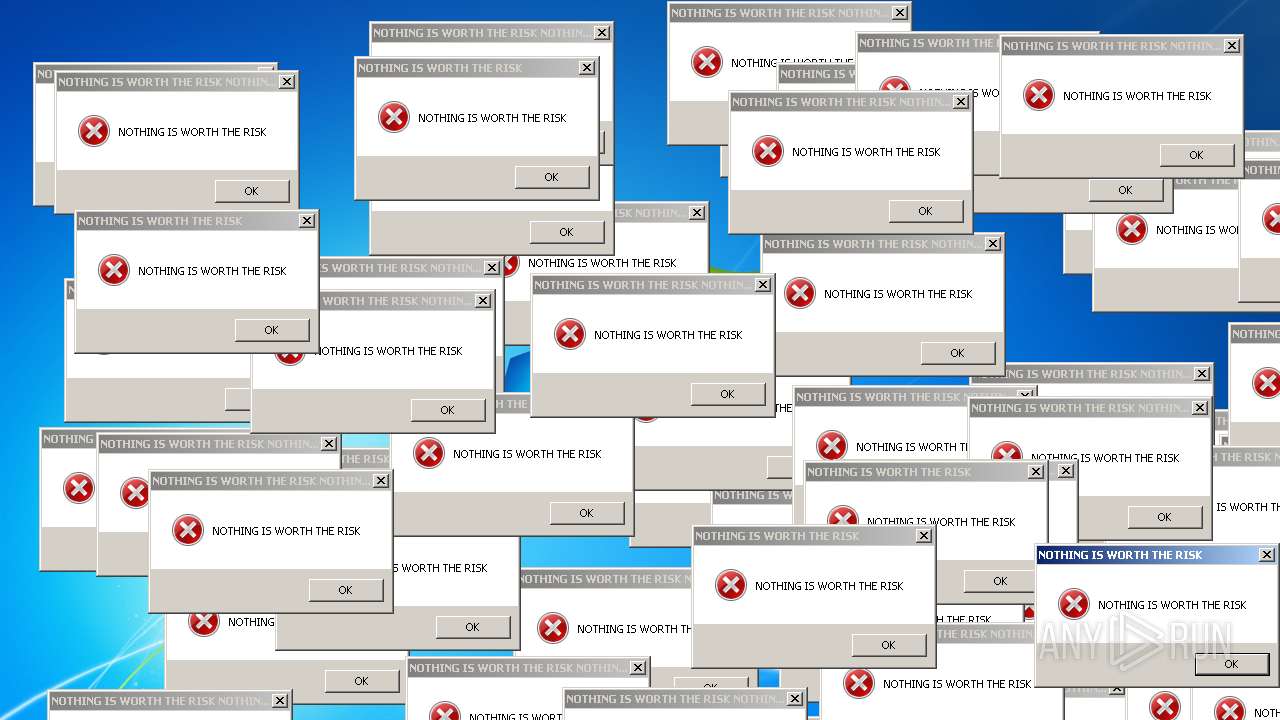
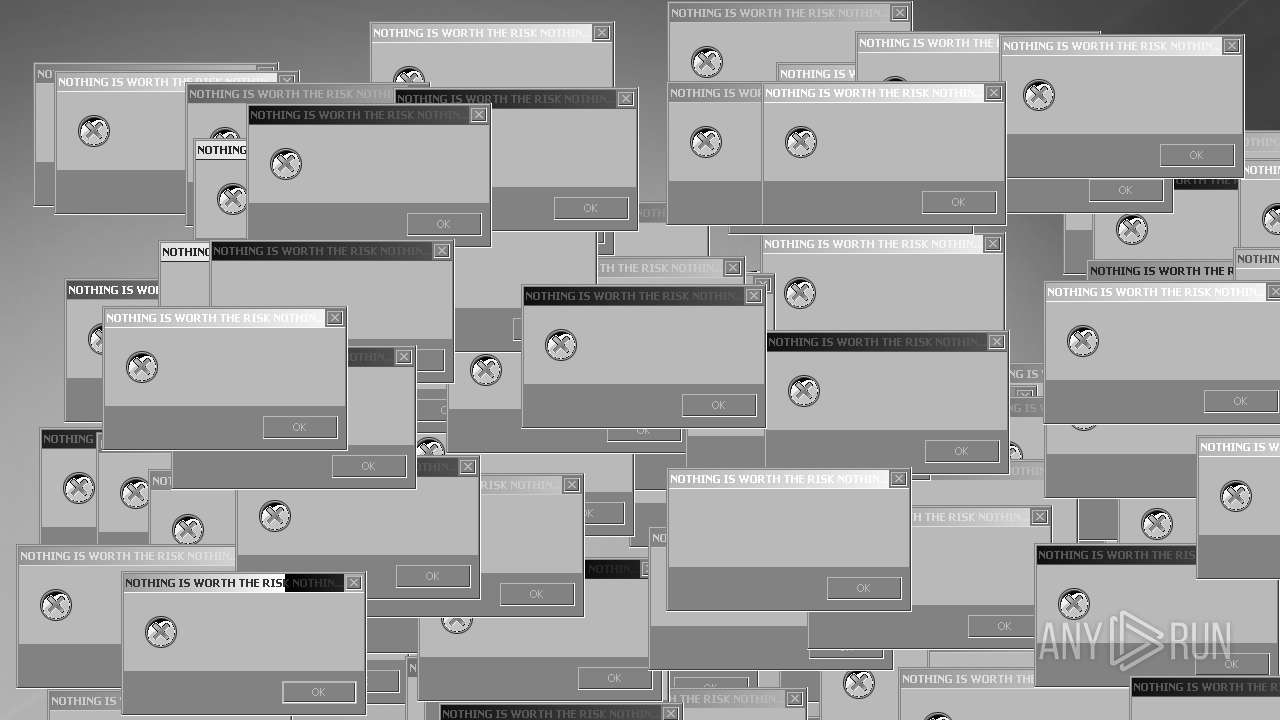
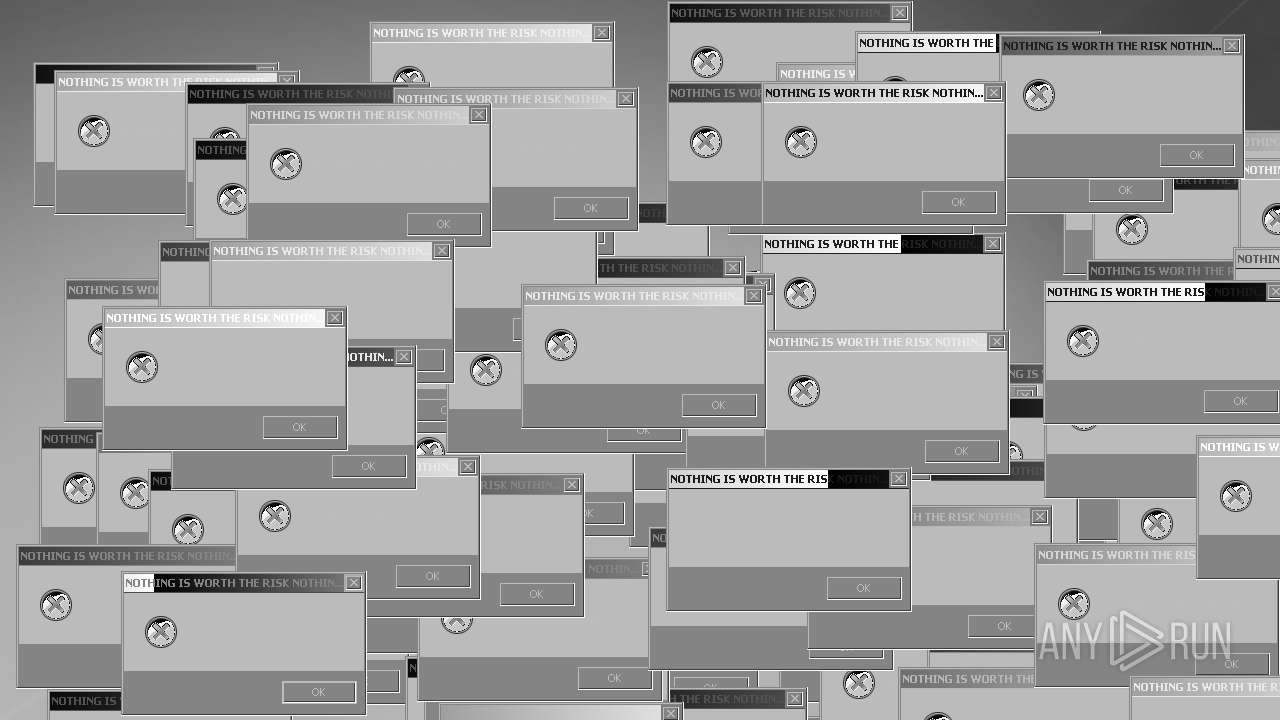
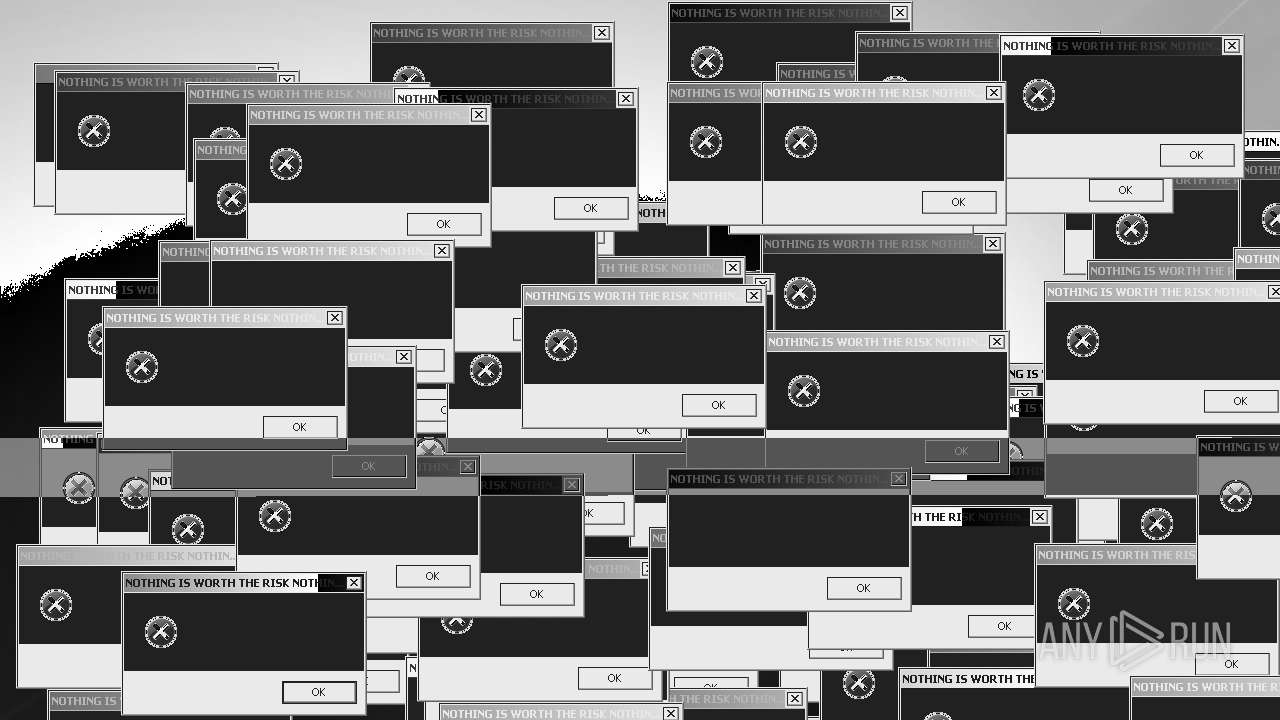
MALICIOUS
Changes the login/logoff helper path in the registry
- Mandela.exe (PID: 3320)
UAC/LUA settings modification
- Mandela.exe (PID: 3320)
Disables Windows Defender
- Mandela.exe (PID: 3320)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Mandela.exe (PID: 3320)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1168)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3224)
- Mandela.exe (PID: 3320)
Application launched itself
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 1924)
Manual execution by a user
- wmpnscfg.exe (PID: 3224)
Checks supported languages
- wmpnscfg.exe (PID: 3224)
- Mandela.exe (PID: 3320)
The process checks LSA protection
- wmpnscfg.exe (PID: 3224)
- Mandela.exe (PID: 3320)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3224)
- Mandela.exe (PID: 3320)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2028)
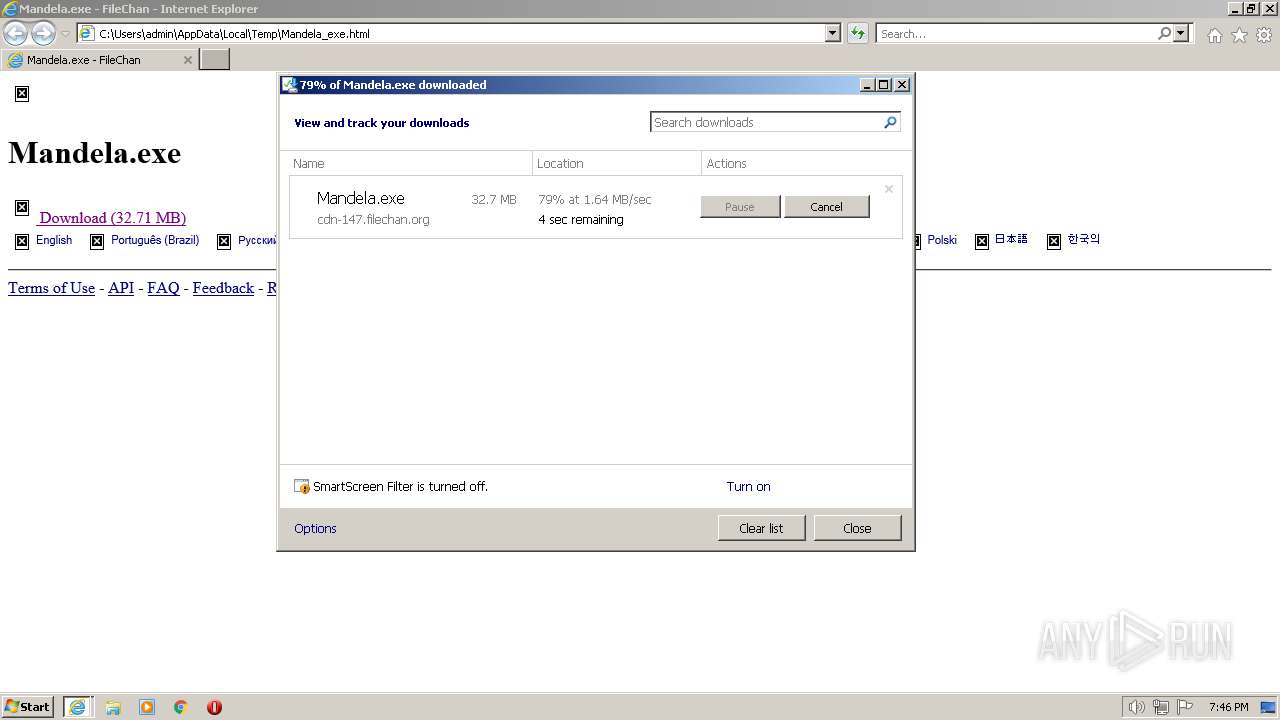
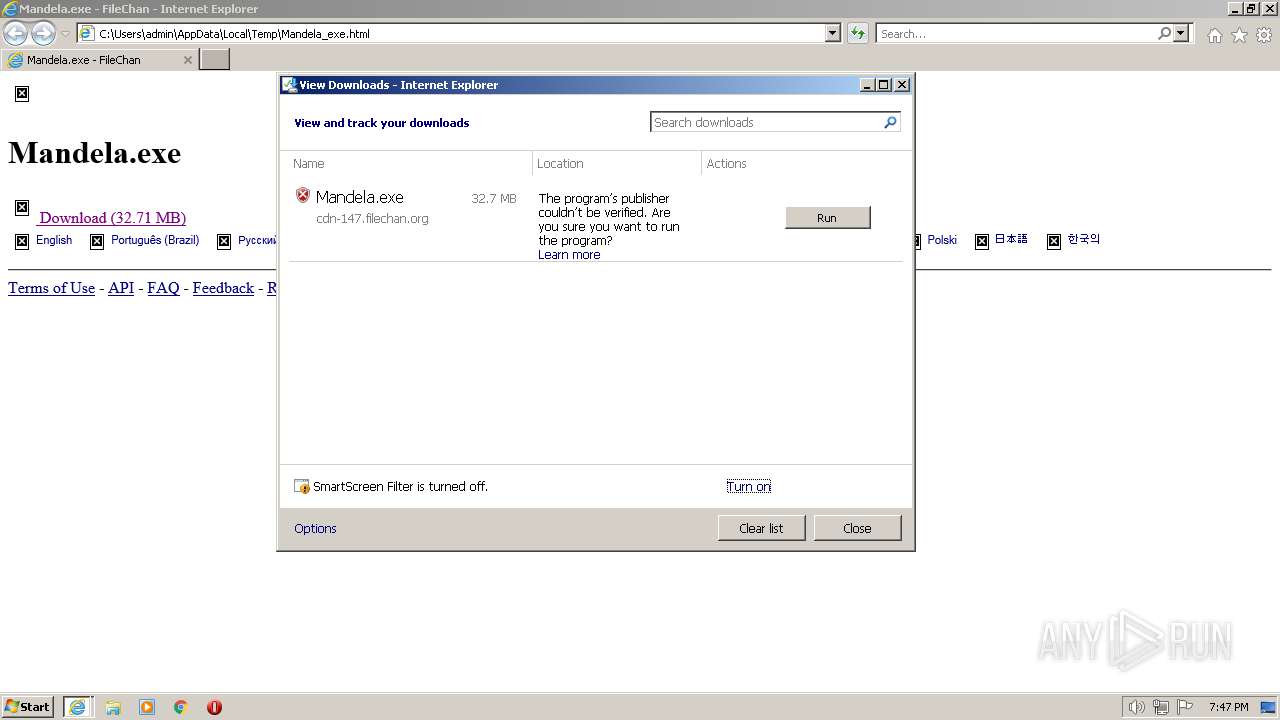
The process uses the downloaded file
- iexplore.exe (PID: 3964)
- Mandela.exe (PID: 3320)
Create files in a temporary directory
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 2028)
Creates files or folders in the user directory
- Mandela.exe (PID: 3320)
Process checks are UAC notifies on
- Mandela.exe (PID: 3320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
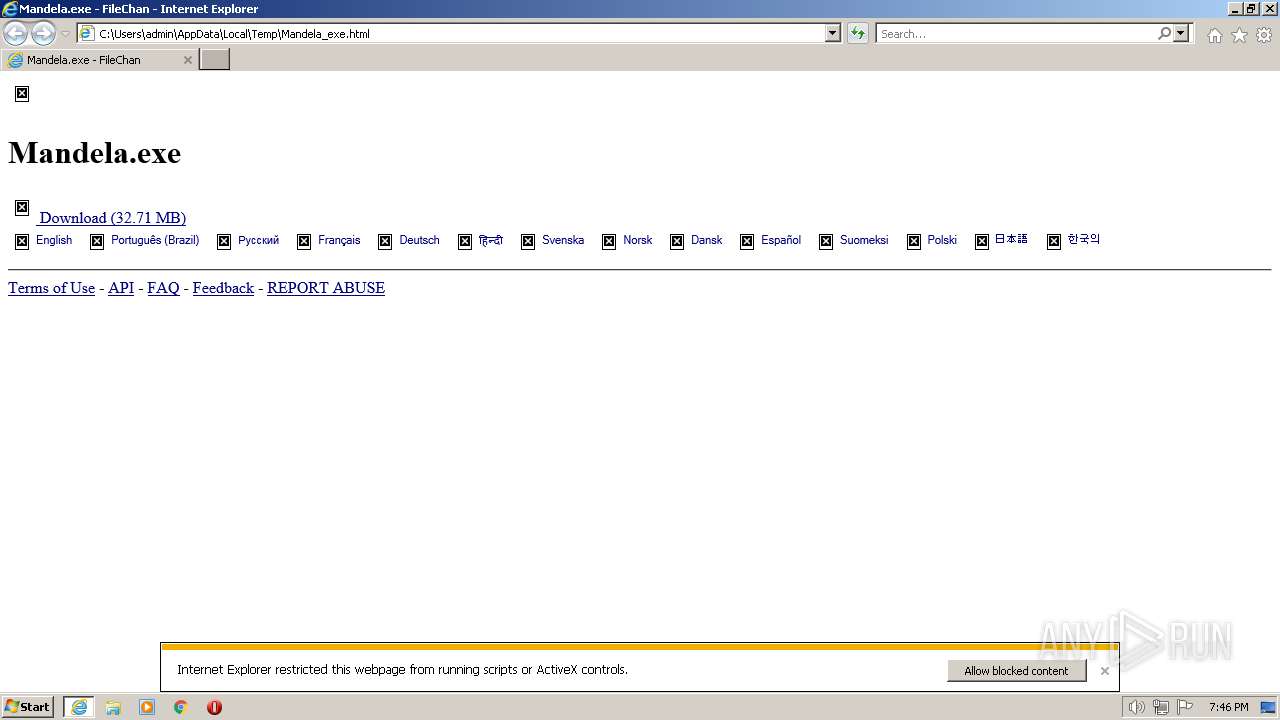
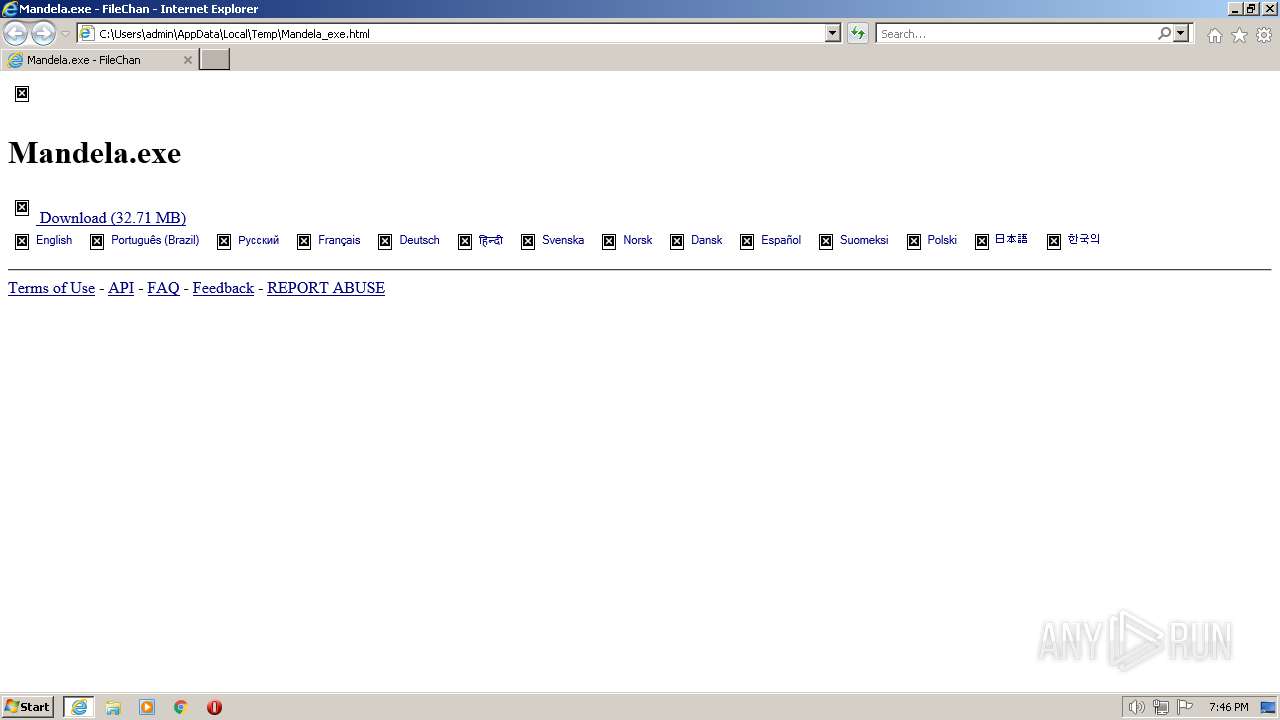
| Title: | Mandela.exe - FileChan |
|---|---|
| Robots: | index, follow |
| Viewport: | width=device-width, initial-scale=1, maximum-scale=1, user-scalable=no |
| HTTPEquivXUACompatible: | IE=edge |
Total processes
51
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe | C:\Windows\System32\cmd.exe | — | Mandela.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3964 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3964 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2248 | taskkill /f /im explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
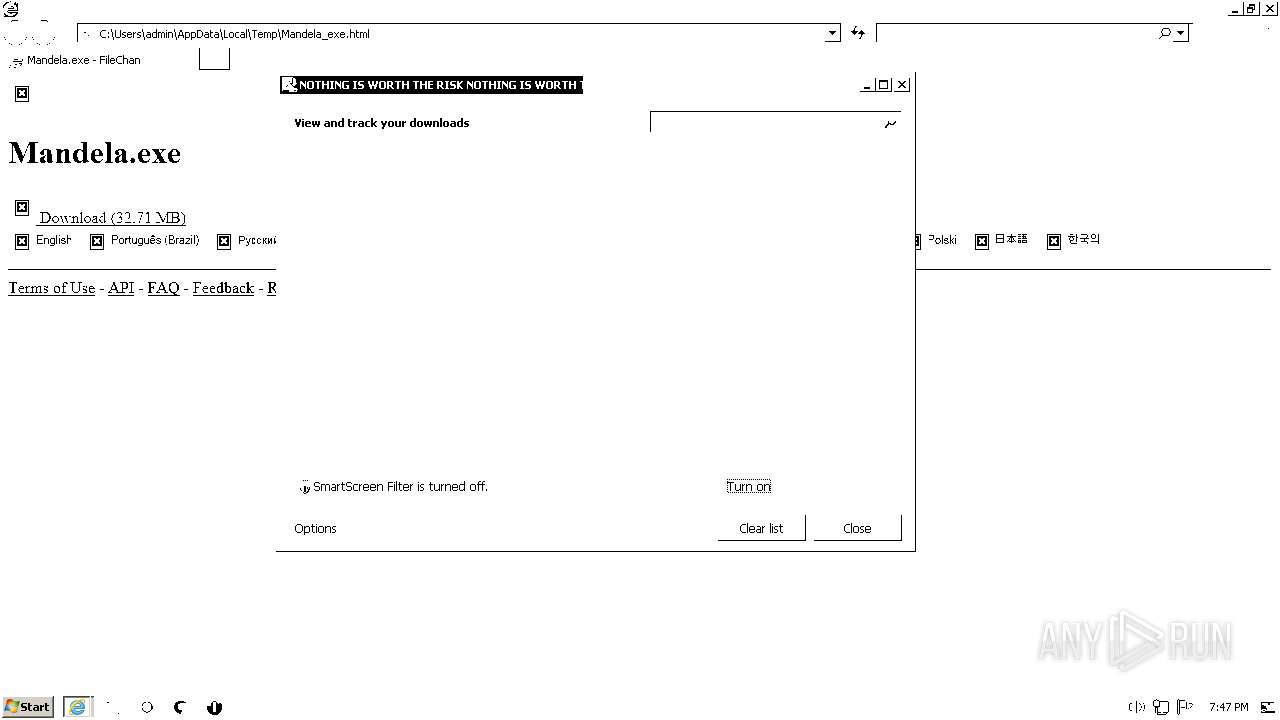
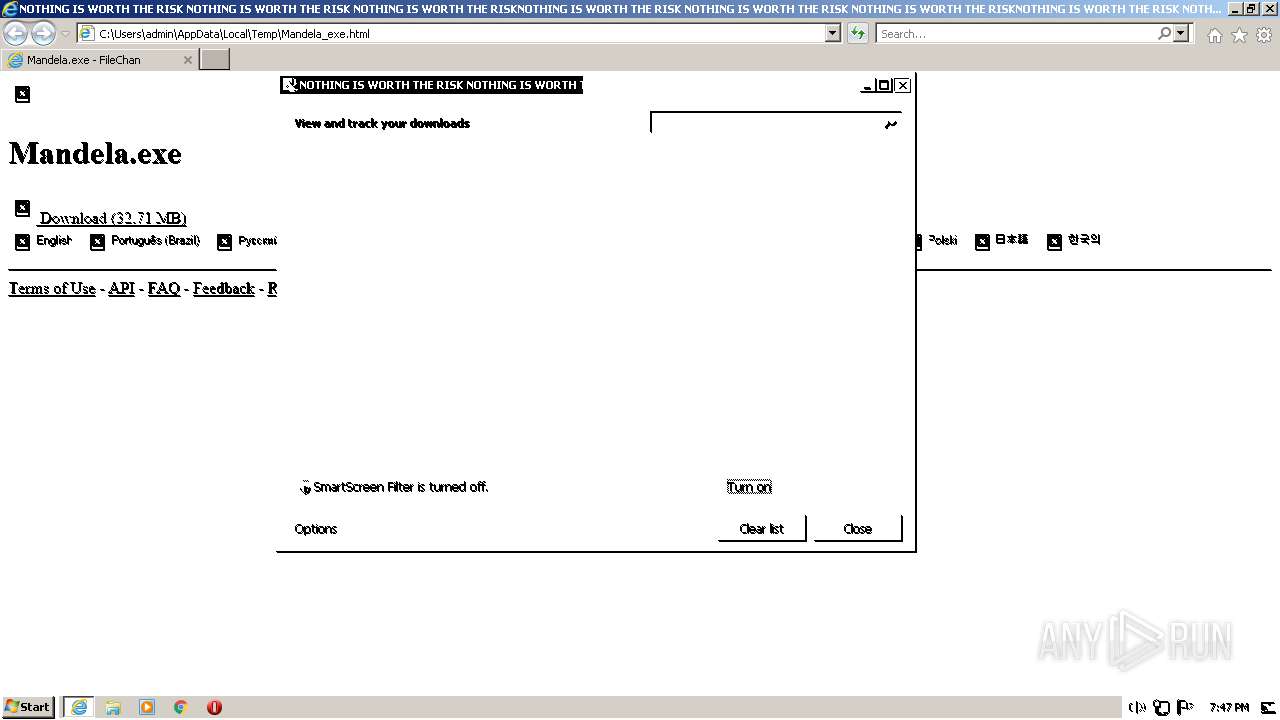
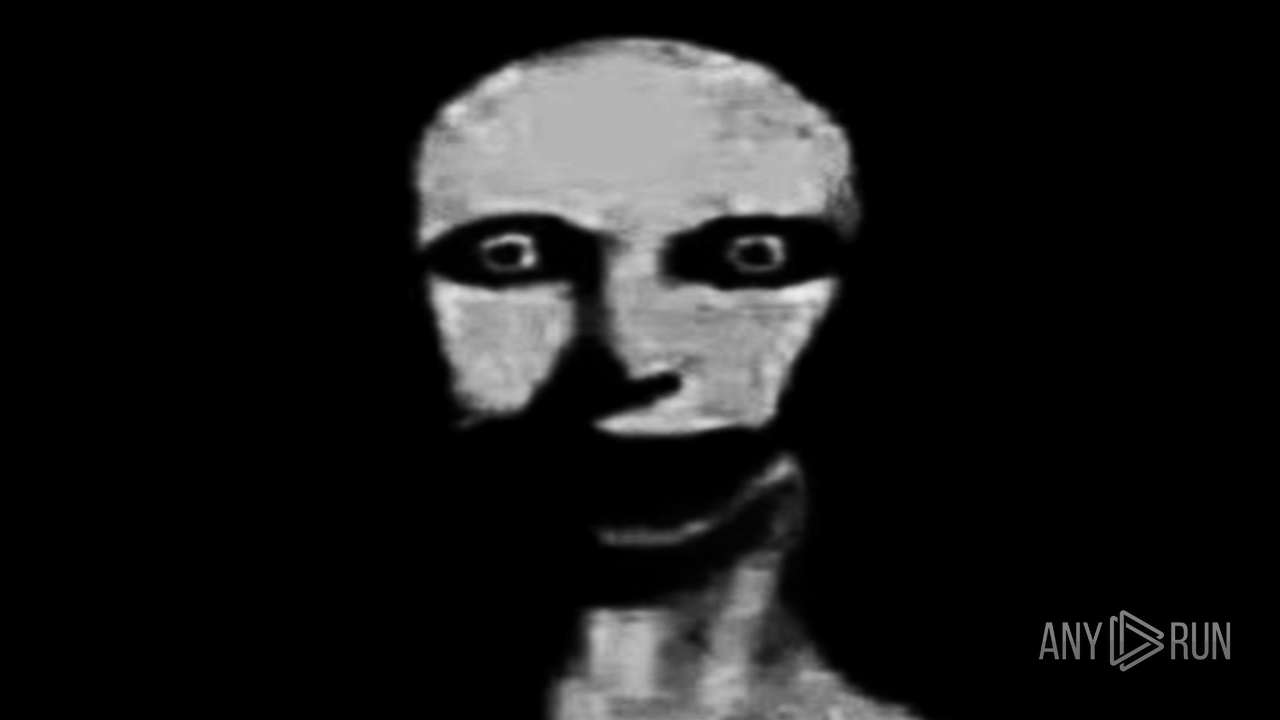
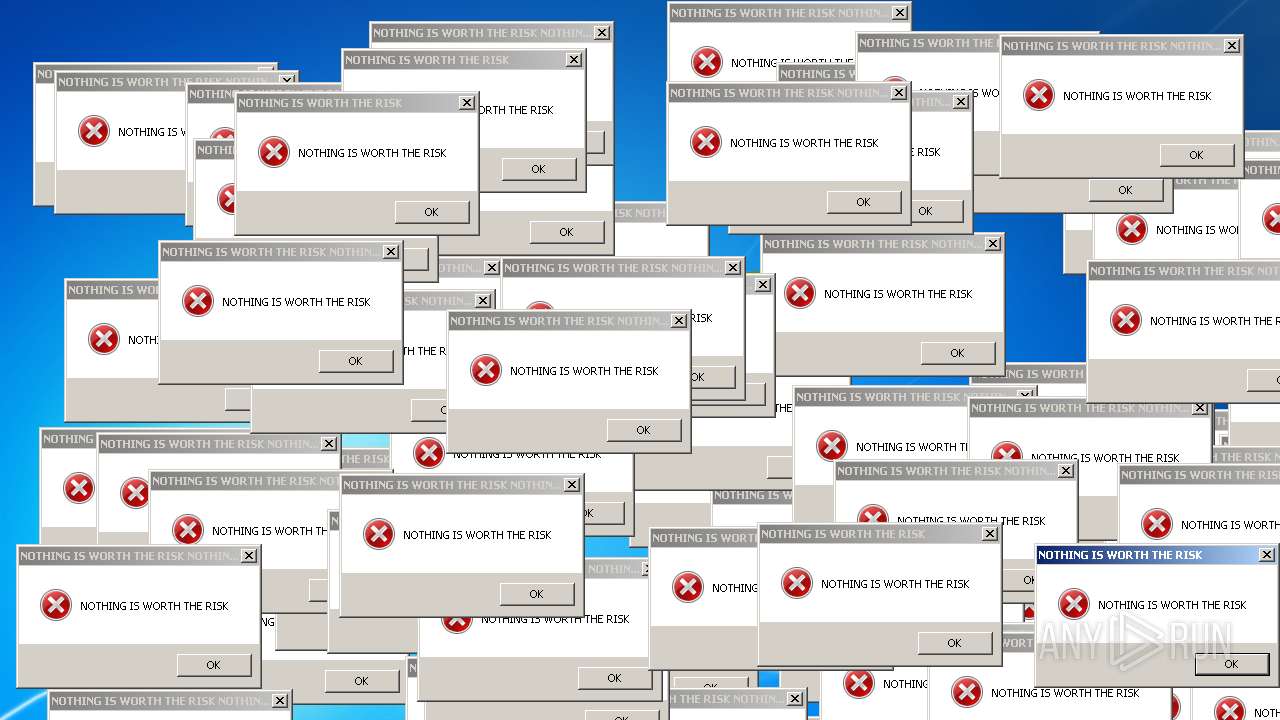
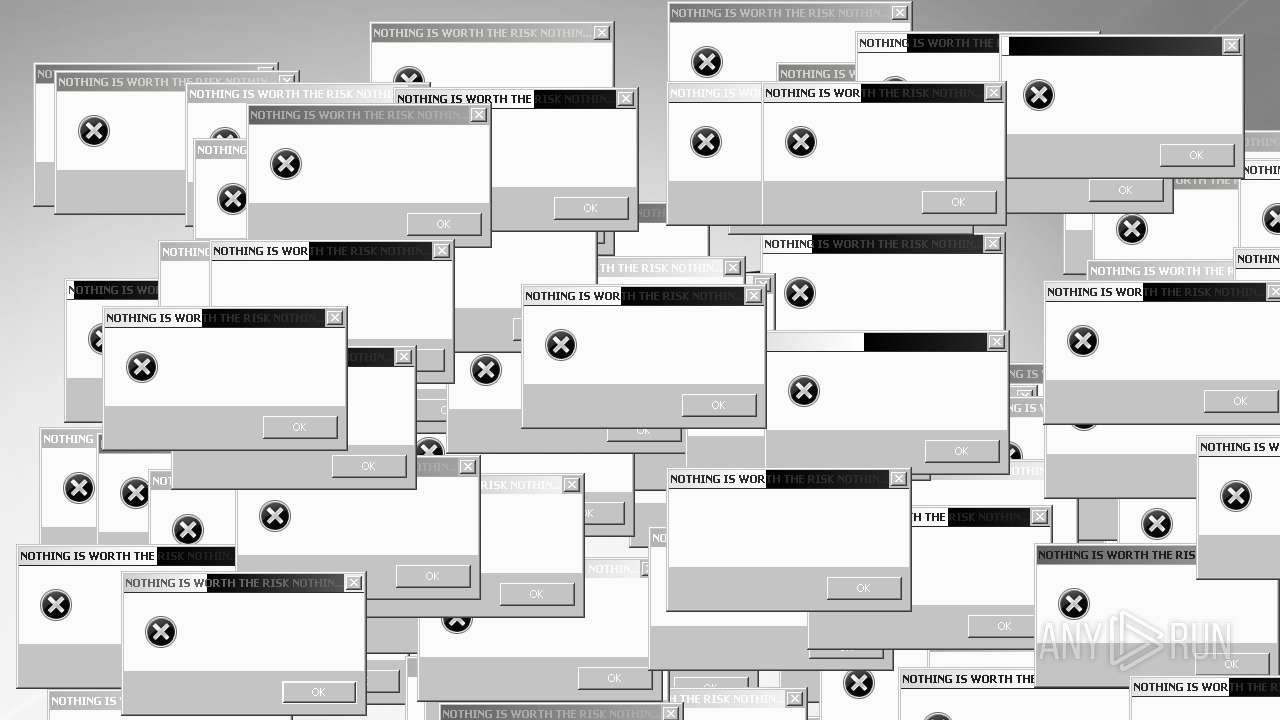
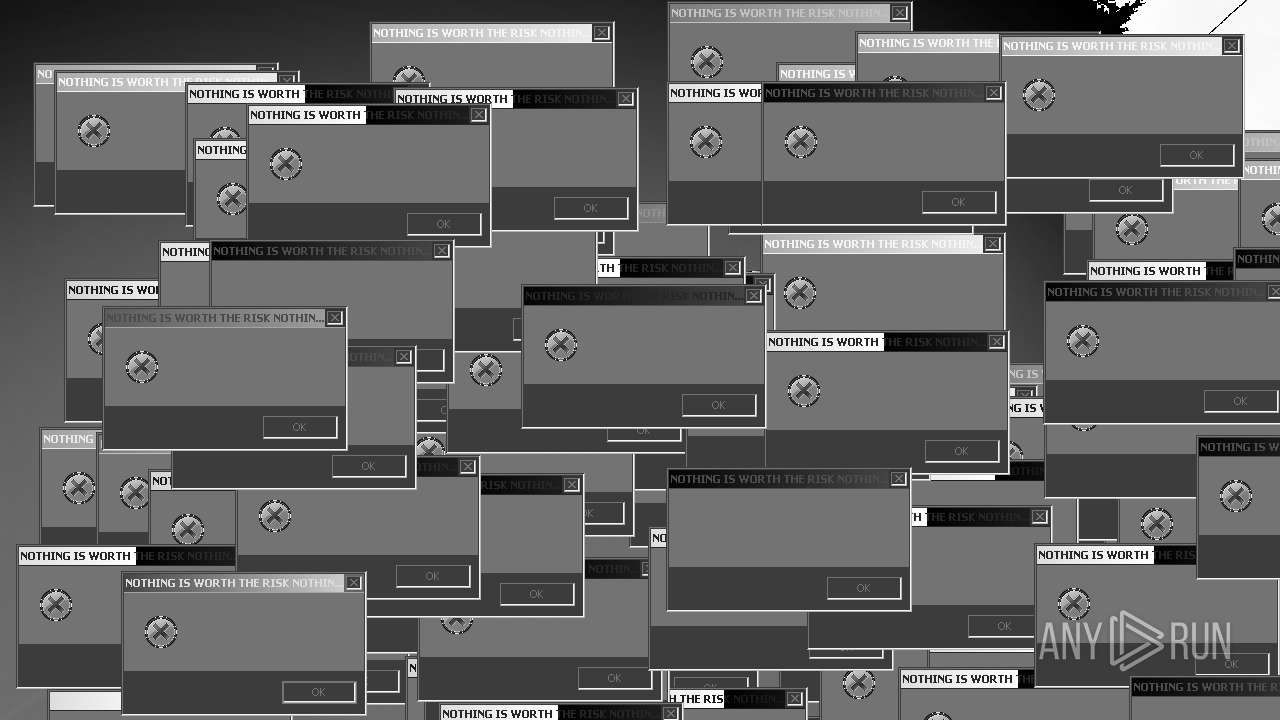
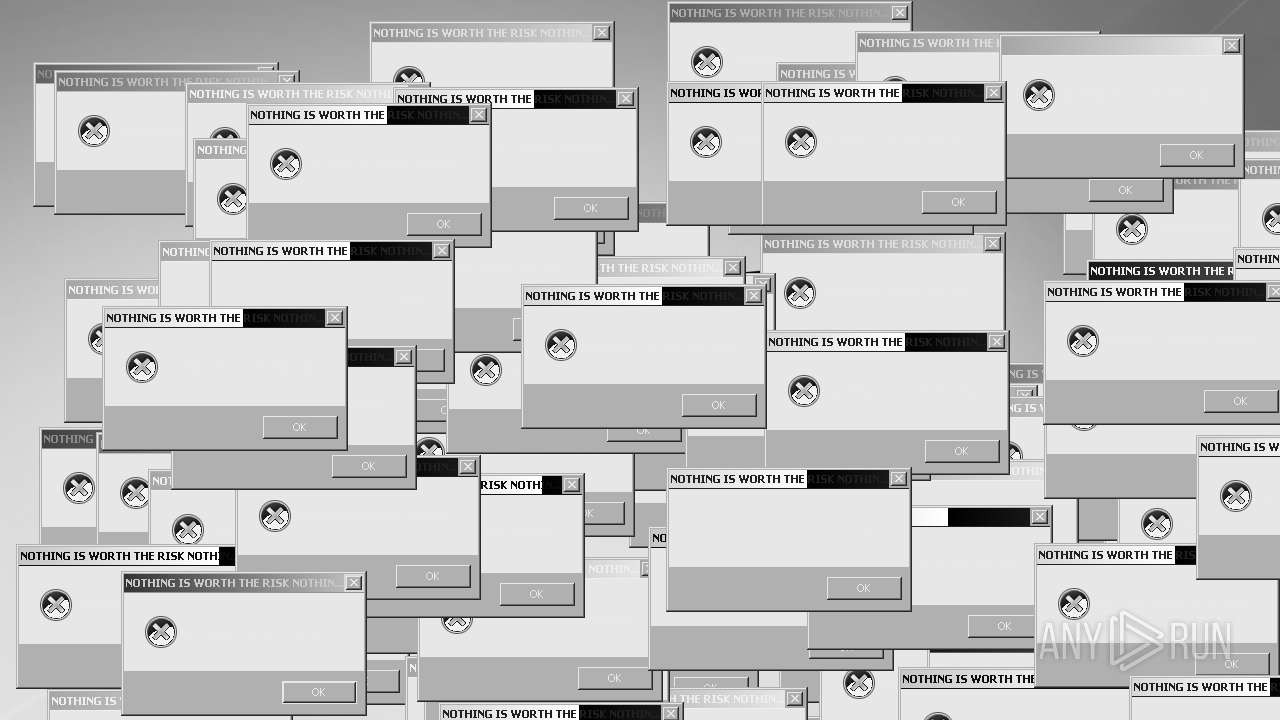
| 3320 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe | iexplore.exe | ||||||||||||
User: admin Company: NOTHING IS WORTH THE RISK Integrity Level: HIGH Description: NOTHING IS WORTH THE RISK Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe | — | iexplore.exe | |||||||||||
User: admin Company: NOTHING IS WORTH THE RISK Integrity Level: MEDIUM Description: NOTHING IS WORTH THE RISK Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\Mandela_exe.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
309 244
Read events
176 282
Write events
132 950
Delete events
12
Modification events
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
72
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:01E2226C9D8036FA74E475F238F8AE01 | SHA256:3509A9038B4D2FB45E39ABD03D0B0F3FC2B723F3F58A8E7C05A050ACD787A589 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver40CF.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:AA901B483396F21CCDFDA6C64681BFD2 | SHA256:6E1C22EB8001585E8D0658ACC97A520429E64AFB2E4CC797F51813661959CE43 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe.ad4mznl.partial | — | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:45754A5C3170E0310A28777A38F55617 | SHA256:D78DD3B91149B9176CC9731F64CC917EA431E8E91527FD40B92FF9EE0165E99C | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:C8ACC7EBD0274710AD136E9EBBF77B30 | SHA256:5FAFFEA9FD8C3FD5CCCB9ACB4FC3DCDA1B50E9F69E382ACB3E07C893918A53D5 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Mandela.exe | — | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:8140916115152FBF1B846D0C827D121D | SHA256:6EB2E58A2B618A2868EA245B976AB437B96DEF575B627C073D530A31638AD92E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
32
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2028 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | AU | der | 717 b | whitelisted |
— | — | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8d0b743d37176072 | US | compressed | 4.70 Kb | whitelisted |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2028 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b23de37be575ef85 | US | compressed | 4.70 Kb | whitelisted |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2028 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9d84828474d5d24d | US | compressed | 62.3 Kb | whitelisted |
2028 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ab69c562fd7c1430 | US | compressed | 62.3 Kb | whitelisted |
2028 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bbc1fe9cb4f769a8 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 151.101.194.217:445 | vjs.zencdn.net | FASTLY | US | suspicious |
4 | System | 151.101.2.217:445 | vjs.zencdn.net | FASTLY | US | suspicious |
4 | System | 151.101.130.217:445 | vjs.zencdn.net | FASTLY | US | suspicious |
3416 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3964 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3964 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3964 | iexplore.exe | 2.16.186.240:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2028 | iexplore.exe | 195.96.151.40:443 | cdn-147.filechan.org | Svea Hosting AB | SE | suspicious |
3964 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2028 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vjs.zencdn.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn-147.filechan.org |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |