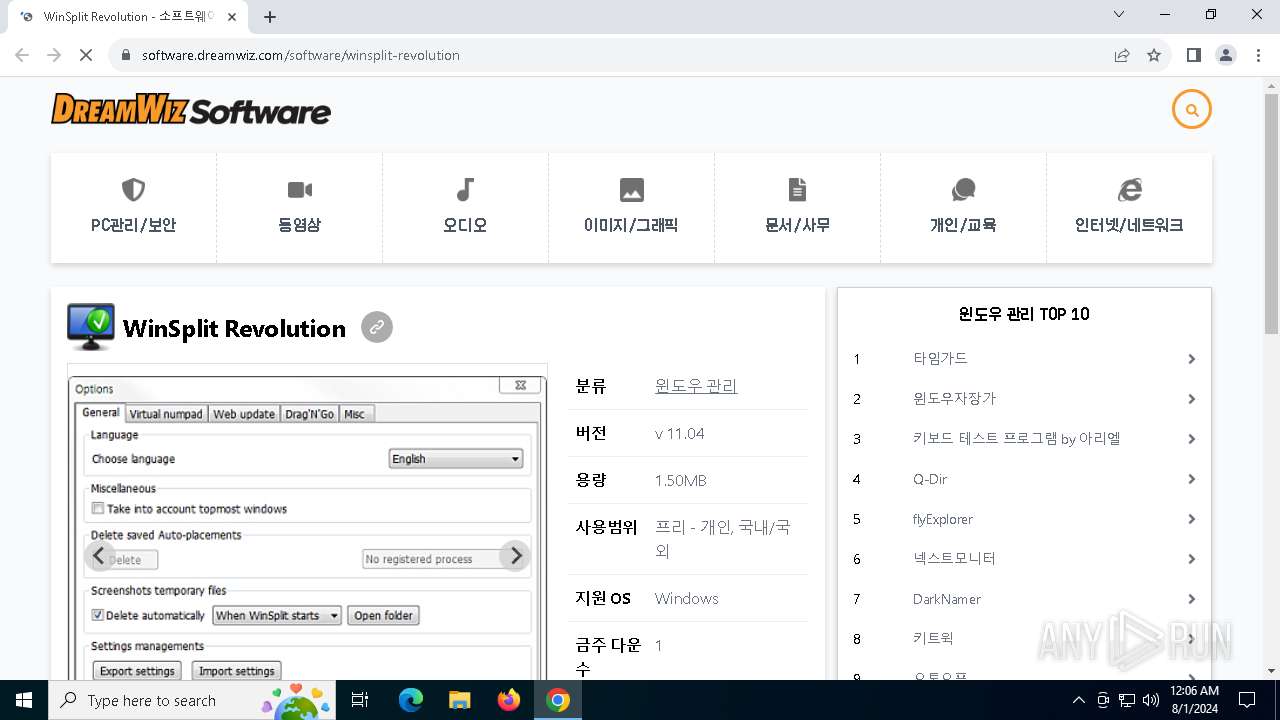
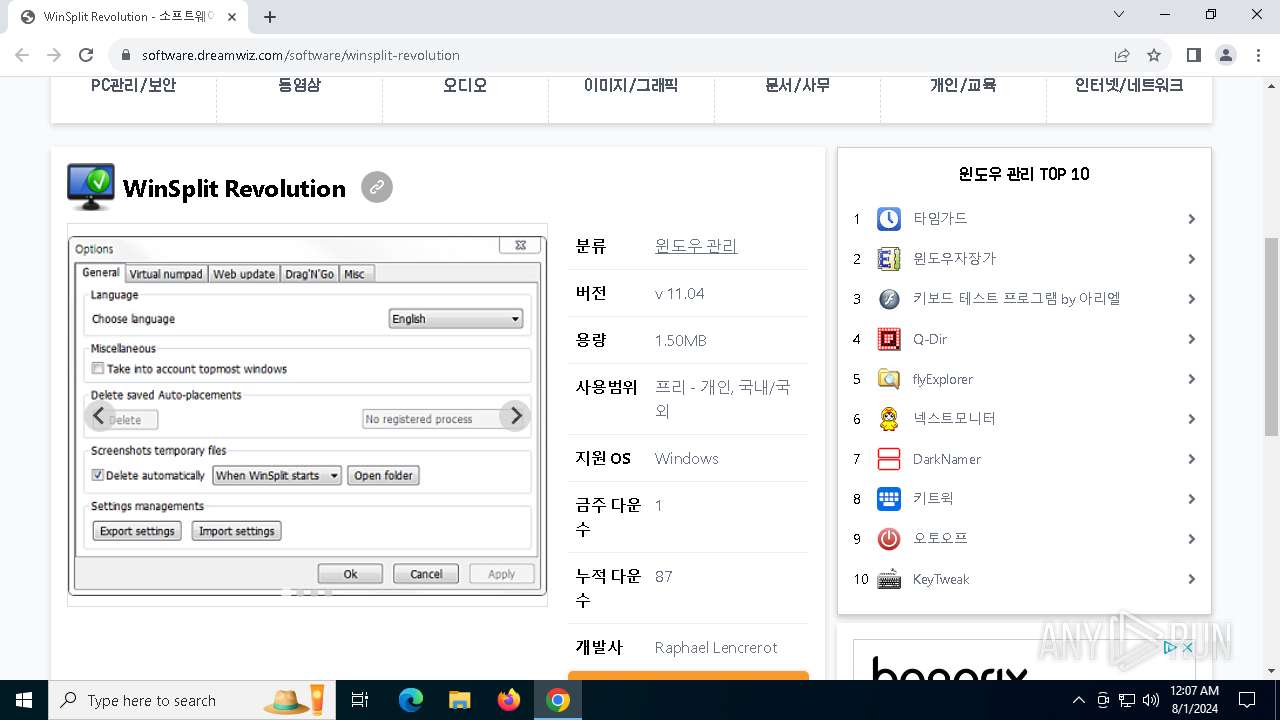
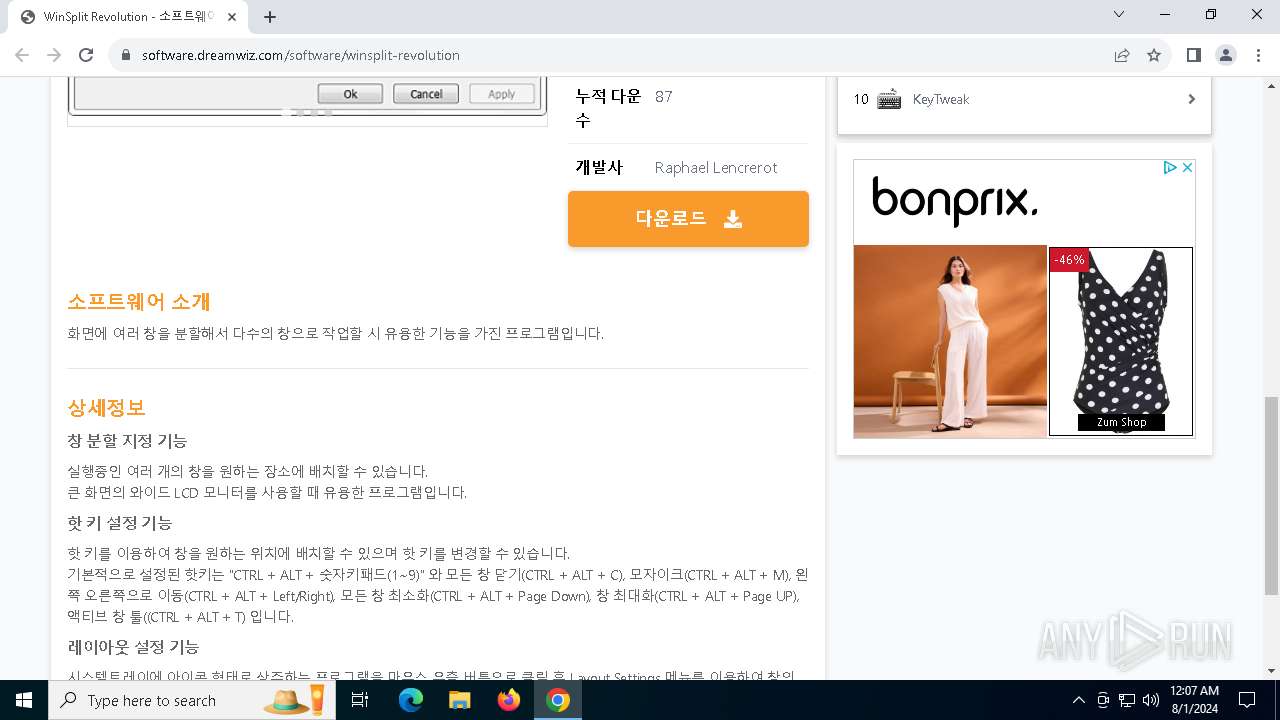
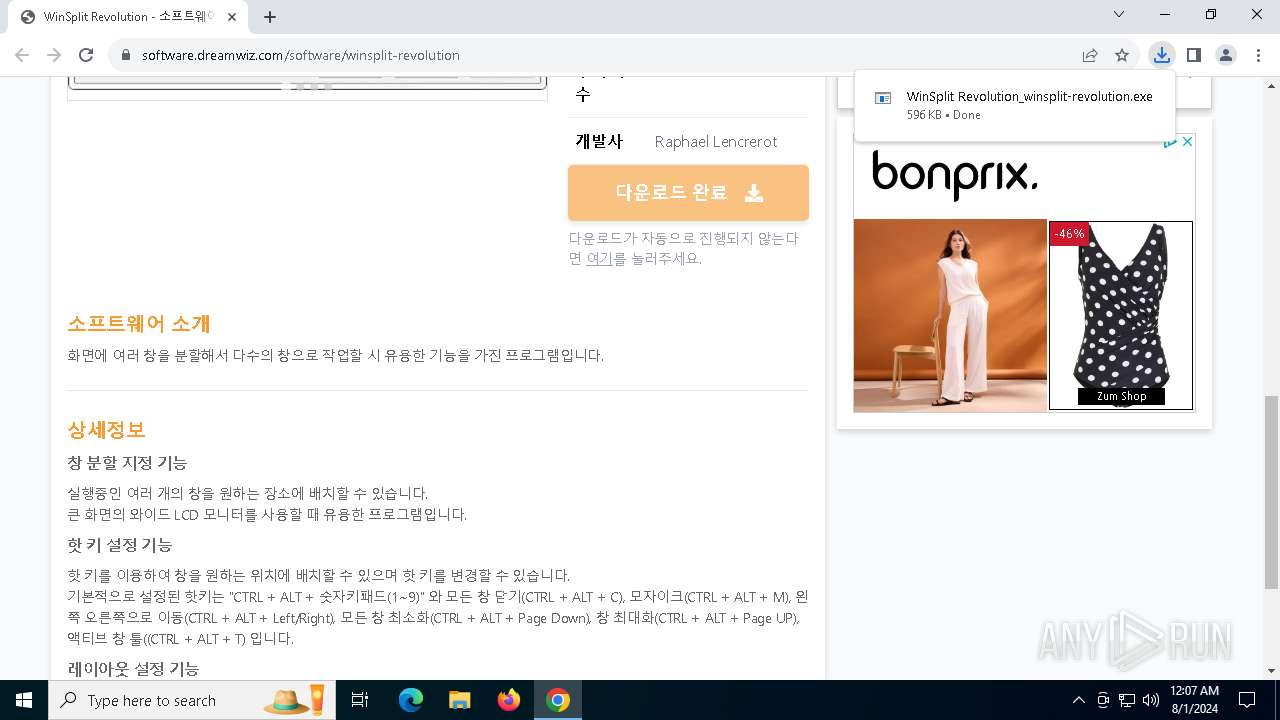
| URL: | https://software.dreamwiz.com/software/winsplit-revolution |
| Full analysis: | https://app.any.run/tasks/57a58adf-7a0e-4cf9-a788-324afb950744 |
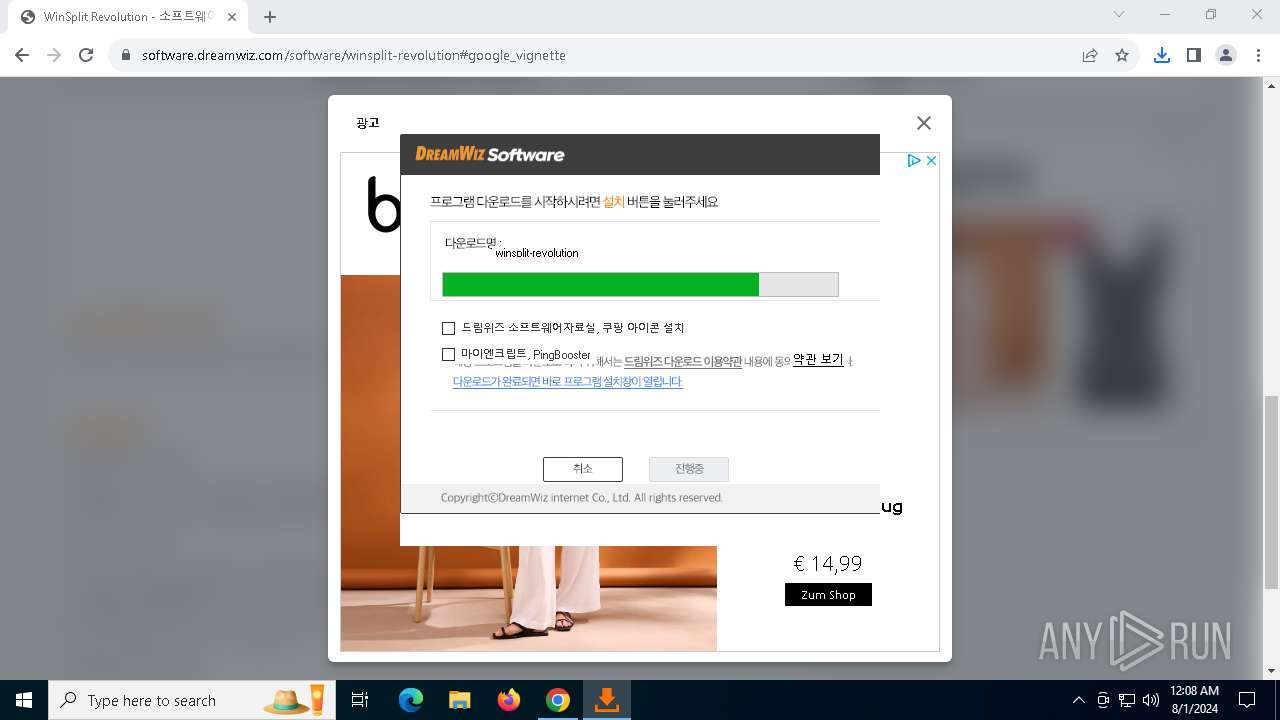
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2024, 00:06:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 6762D7F4BAB253C4CB43901D168CFE33 |
| SHA1: | 787F8F820883EA052C5E57605AD94D4714B5933D |
| SHA256: | DB53D7931E2E5A3218C8793478F400AA0B2068BE7B715186DF4120F8C63A8B1B |
| SSDEEP: | 3:N8HSAhXyKmK0CT:2TFyKmtCT |
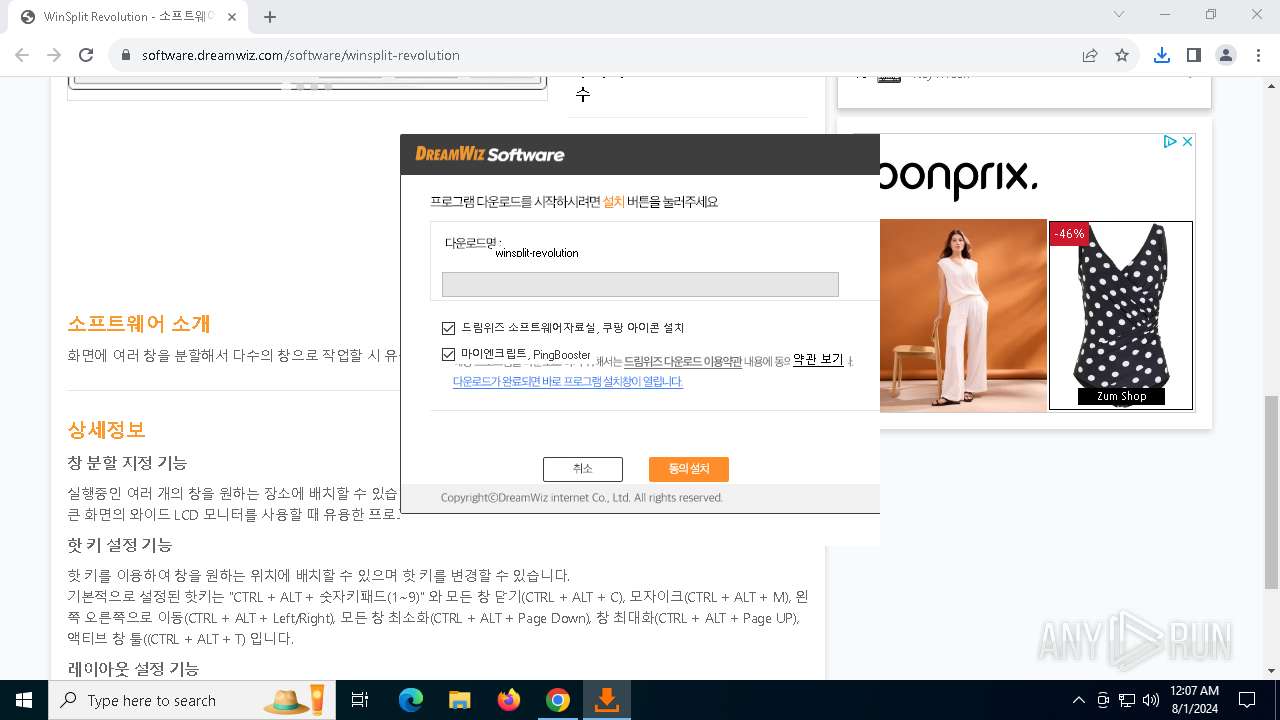
MALICIOUS
Drops the executable file immediately after the start
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- winsplit-revolution.exe (PID: 32)
Changes the autorun value in the registry
- winsplit-revolution.exe (PID: 32)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- WinSplit.exe (PID: 2092)
Executable content was dropped or overwritten
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- winsplit-revolution.exe (PID: 32)
Reads the date of Windows installation
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- WinSplit.exe (PID: 2092)
Executing commands from a ".bat" file
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Starts CMD.EXE for commands execution
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Creates a software uninstall entry
- winsplit-revolution.exe (PID: 32)
Malware-specific behavior (creating "System.dll" in Temp)
- winsplit-revolution.exe (PID: 32)
The process creates files with name similar to system file names
- winsplit-revolution.exe (PID: 32)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6300)
- chrome.exe (PID: 7020)
The process uses the downloaded file
- chrome.exe (PID: 6300)
- chrome.exe (PID: 7248)
Reads the computer name
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- WinSplit.exe (PID: 2092)
- winsplit-revolution.exe (PID: 32)
- TextInputHost.exe (PID: 6268)
- WinSplit.exe (PID: 7304)
Application launched itself
- chrome.exe (PID: 6300)
Drops the executable file immediately after the start
- chrome.exe (PID: 6300)
- chrome.exe (PID: 7020)
Reads the machine GUID from the registry
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Reads Environment values
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Reads the software policy settings
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6300)
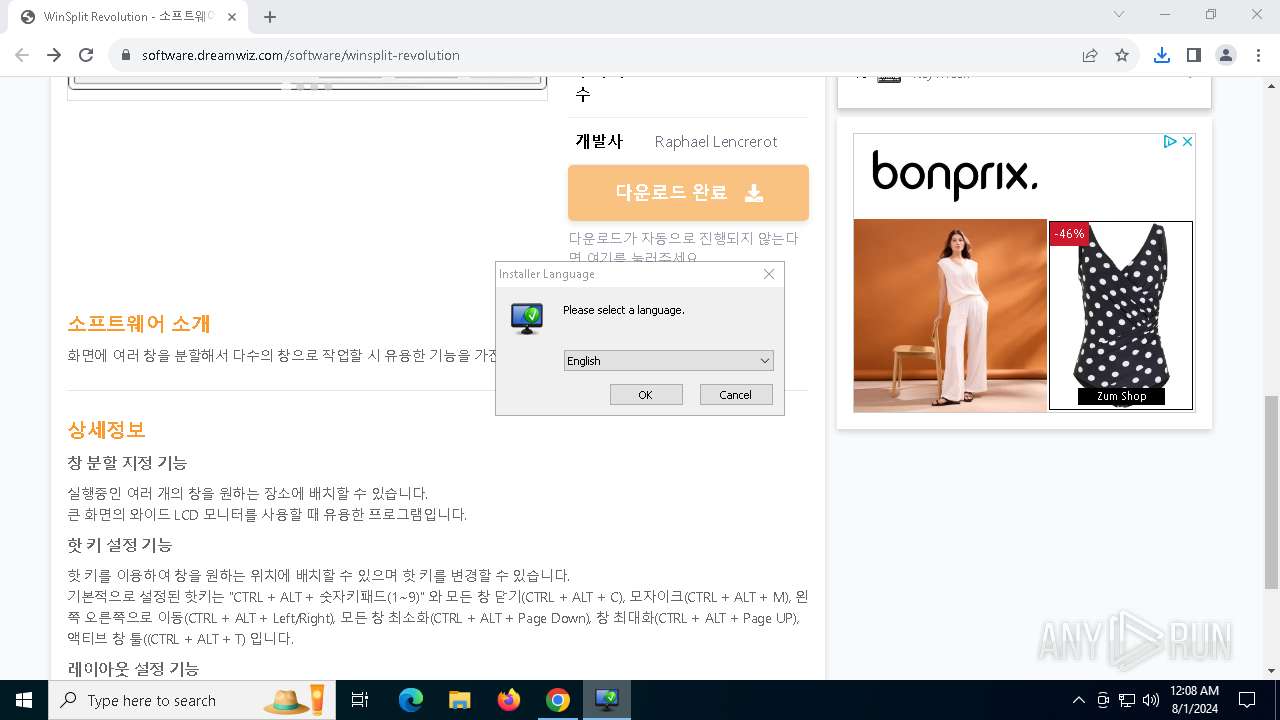
Checks supported languages
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- winsplit-revolution.exe (PID: 32)
- WinSplit.exe (PID: 2092)
- WinSplitDrvr64.exe (PID: 6140)
- WinSplitDrvr32.exe (PID: 3188)
- TextInputHost.exe (PID: 6268)
- WinSplit.exe (PID: 7304)
Checks proxy server information
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Disables trace logs
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
Process checks computer location settings
- WinSplit Revolution_winsplit-revolution.exe (PID: 1184)
- WinSplit.exe (PID: 2092)
Create files in a temporary directory
- winsplit-revolution.exe (PID: 32)
Creates files in the program directory
- winsplit-revolution.exe (PID: 32)
Creates files or folders in the user directory
- winsplit-revolution.exe (PID: 32)
- WinSplit.exe (PID: 2092)
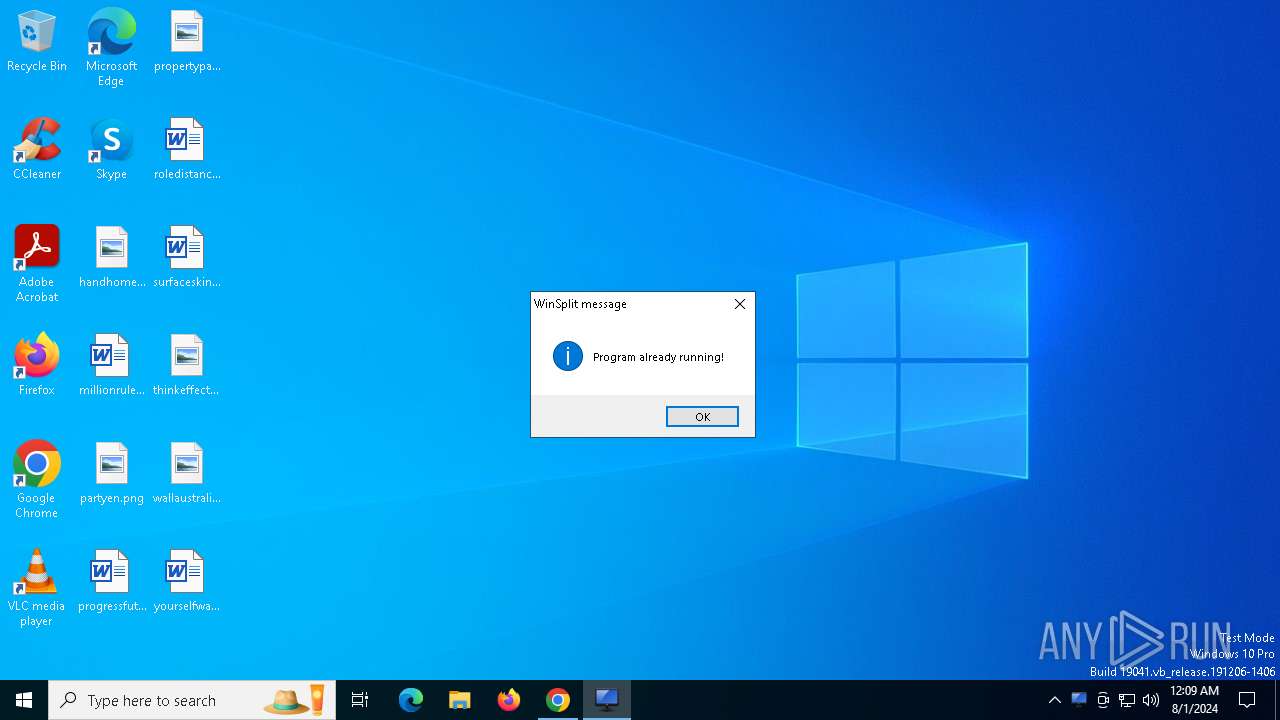
Manual execution by a user
- WinSplit.exe (PID: 7304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
179
Monitored processes
33
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Users\admin\Downloads\winsplit-revolution.exe" | C:\Users\admin\Downloads\winsplit-revolution.exe | WinSplit Revolution_winsplit-revolution.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5892 --field-trial-handle=1916,i,241101616287578396,316036550355806466,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5900 --field-trial-handle=1916,i,241101616287578396,316036550355806466,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5112 --field-trial-handle=1916,i,241101616287578396,316036550355806466,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1184 | "C:\Users\admin\Downloads\WinSplit Revolution_winsplit-revolution.exe" | C:\Users\admin\Downloads\WinSplit Revolution_winsplit-revolution.exe | chrome.exe | ||||||||||||
User: admin Company: (주)드림위즈 인터넷 Integrity Level: HIGH Description: 드림위즈 소프트웨어 Exit code: 0 Version: 2024.03.14.1 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5004 --field-trial-handle=1916,i,241101616287578396,316036550355806466,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
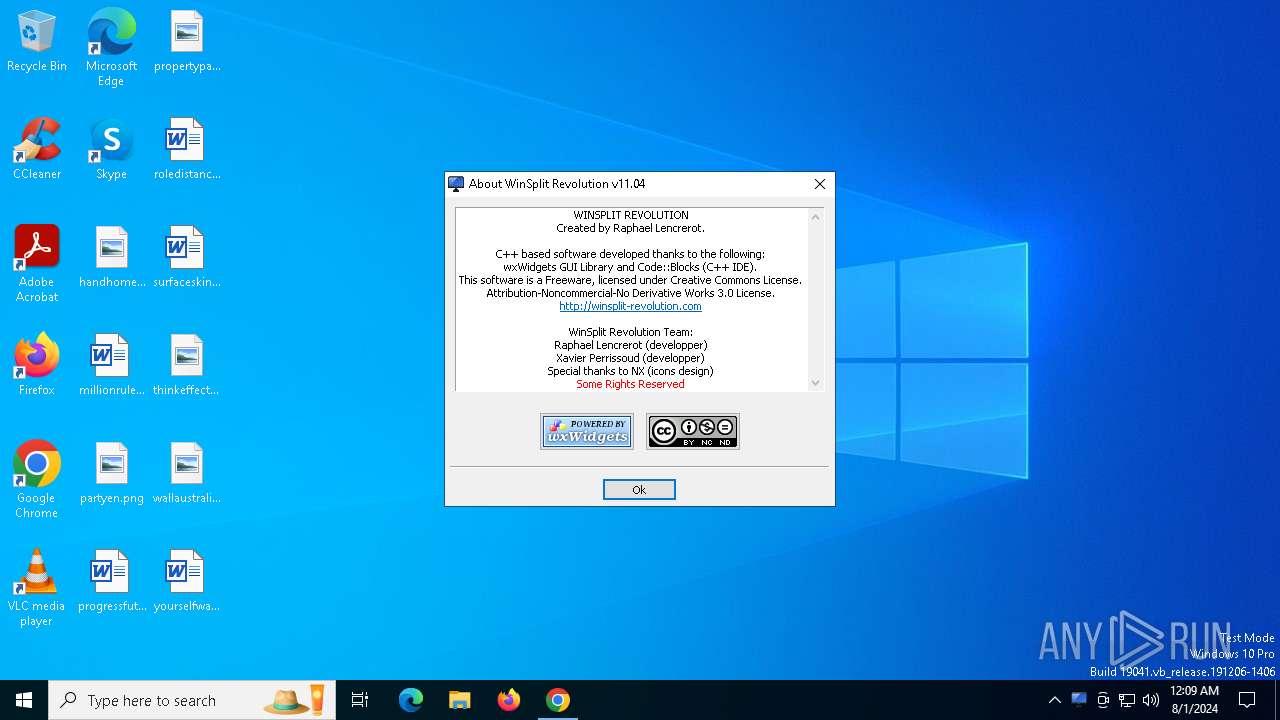
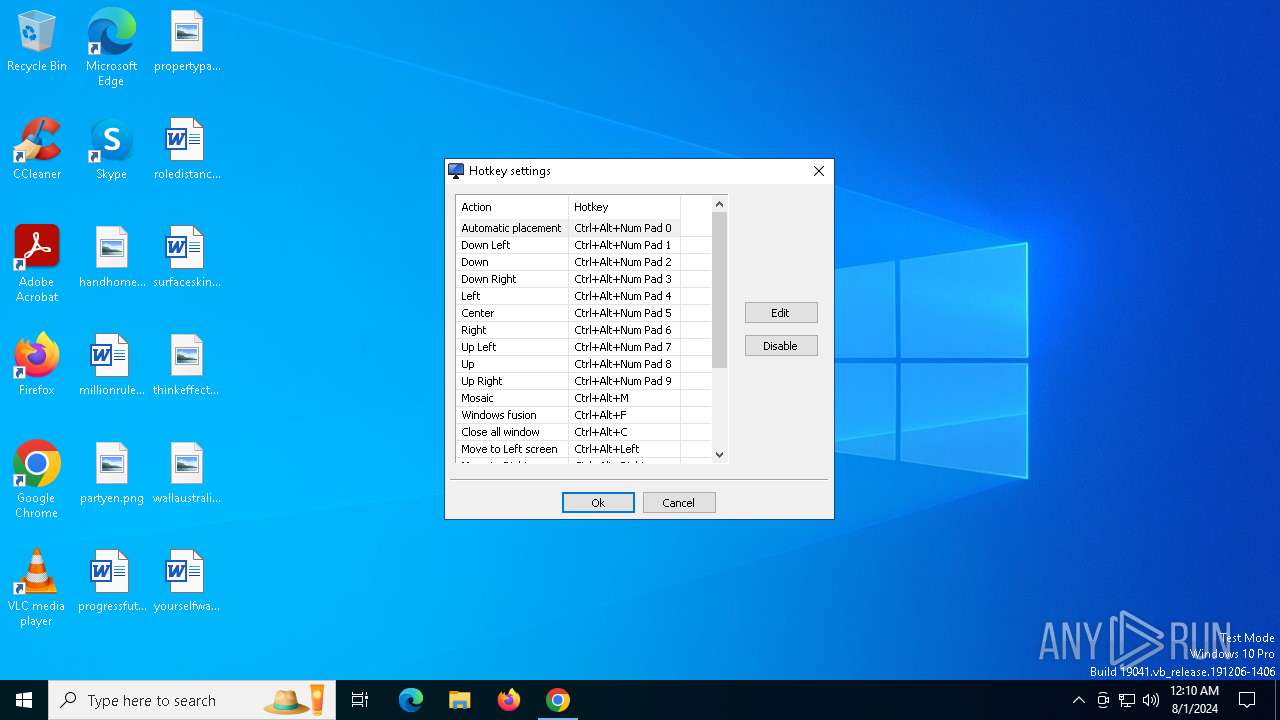
| 2092 | "C:\Program Files (x86)\WinSplit Revolution\WinSplit.exe" | C:\Program Files (x86)\WinSplit Revolution\WinSplit.exe | winsplit-revolution.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WinSplit executable Version: 11.04 Modules
| |||||||||||||||
| 3188 | "C:\Program Files (x86)\WinSplit Revolution\WinSplitDrvr32.exe" 393892 | C:\Program Files (x86)\WinSplit Revolution\WinSplitDrvr32.exe | — | WinSplit.exe | |||||||||||
User: admin Integrity Level: HIGH Description: WinSplit Hook System Version: 11.04 Modules
| |||||||||||||||
| 4044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5336 --field-trial-handle=1916,i,241101616287578396,316036550355806466,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
20 317
Read events
20 216
Write events
95
Delete events
6
Modification events
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
21
Suspicious files
213
Text files
45
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5ddb.TMP | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5ddb.TMP | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFe5ea6.TMP | text | |
MD5:390E3C6EDCE7036BB6F52670DC24ABAD | SHA256:D6F1B47CD05A8E1FAD989DEEC22ED67EA9A013C2DE0CCAFD68A539F69BD0DD70 | |||
| 6300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:DF81465C6FD3C271021EFEF60DC3C105 | SHA256:C3099E8B290EC2DB598E8516BE5D963729363E0FB6D8C3F89131F9B747CDDA7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
128
DNS requests
86
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7932 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7932 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6996 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1120 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3036 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6300 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6576 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6576 | chrome.exe | 183.110.214.137:443 | software.dreamwiz.com | Korea Telecom | KR | unknown |
6576 | chrome.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
6576 | chrome.exe | 151.101.1.229:443 | cdn.jsdelivr.net | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
software.dreamwiz.com |
| whitelisted |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6576 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6576 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5336 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |