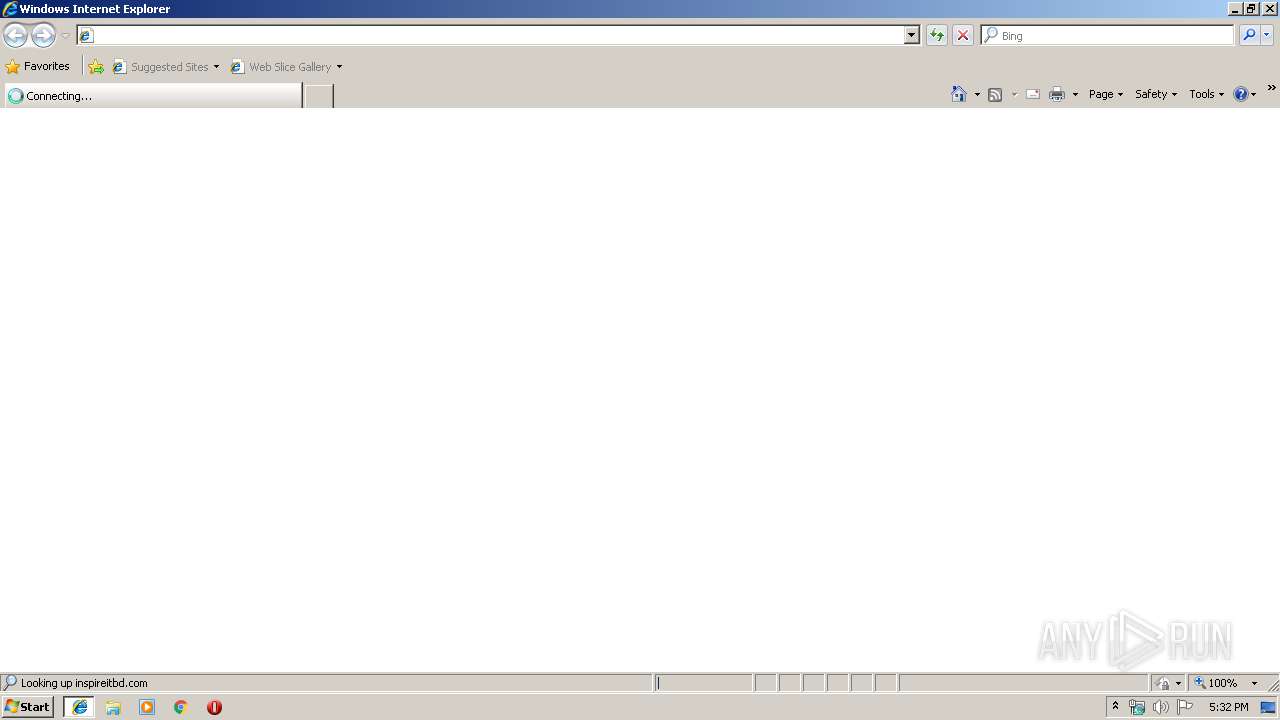
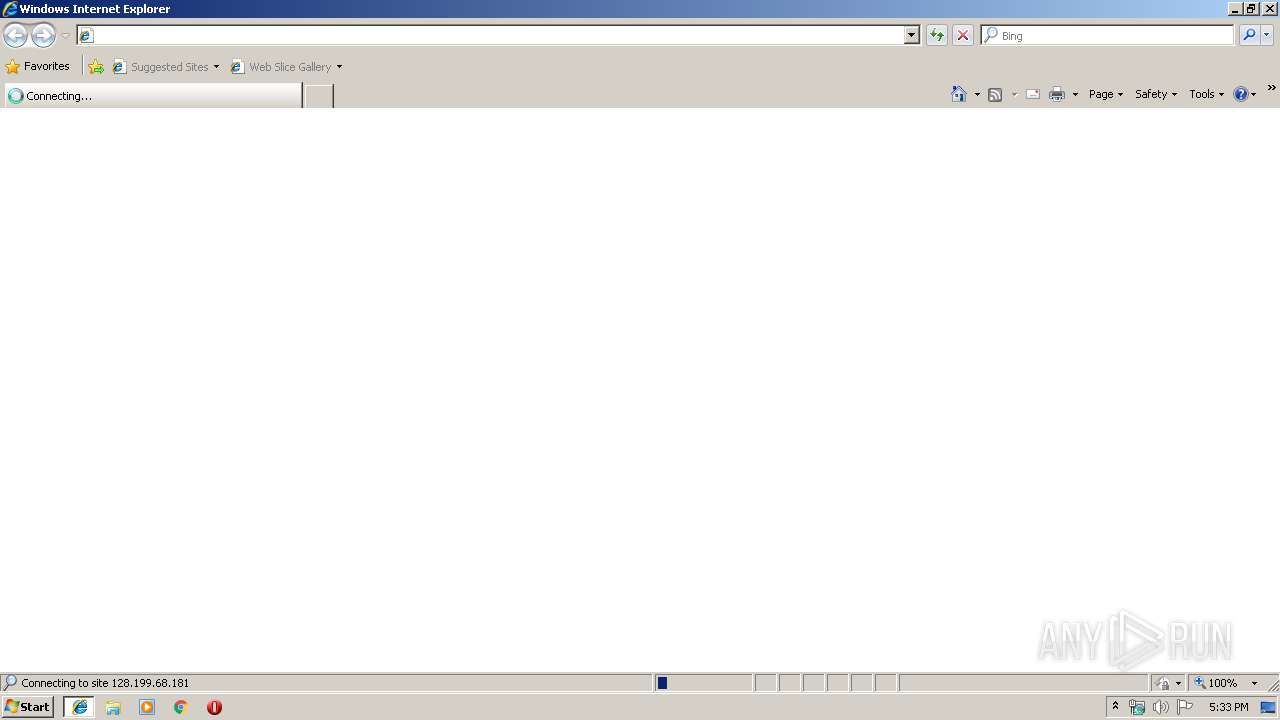
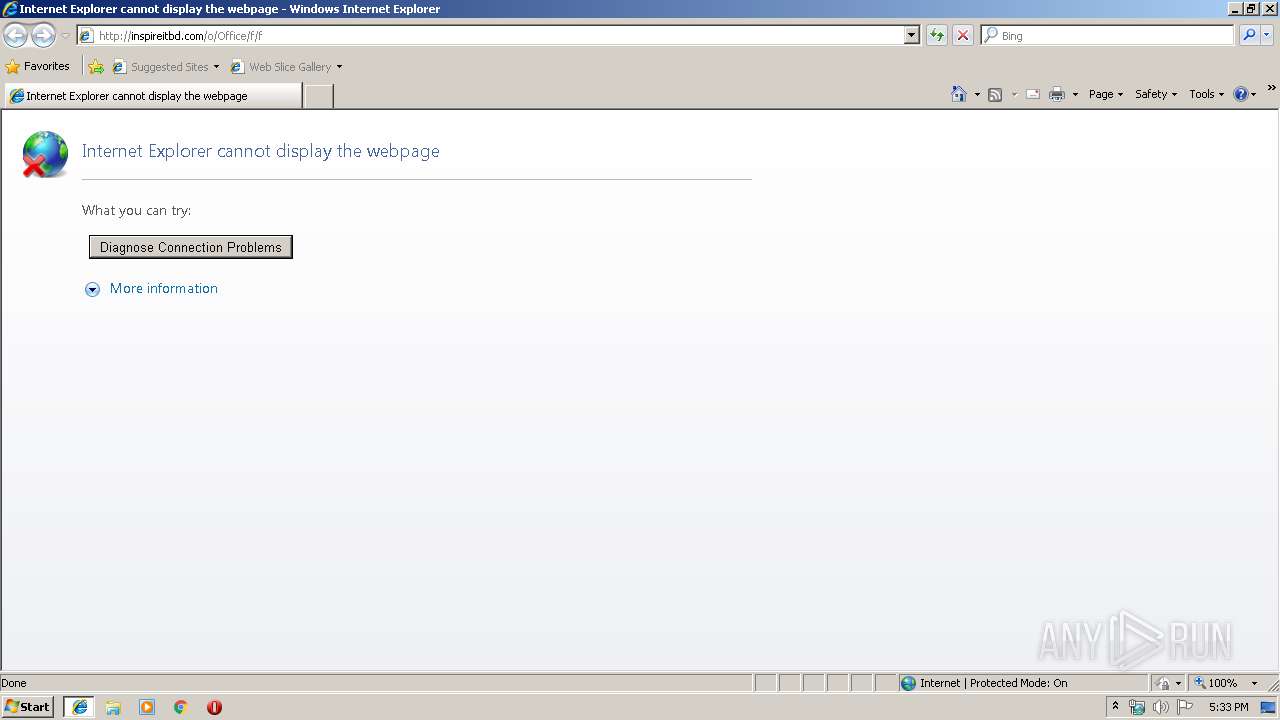
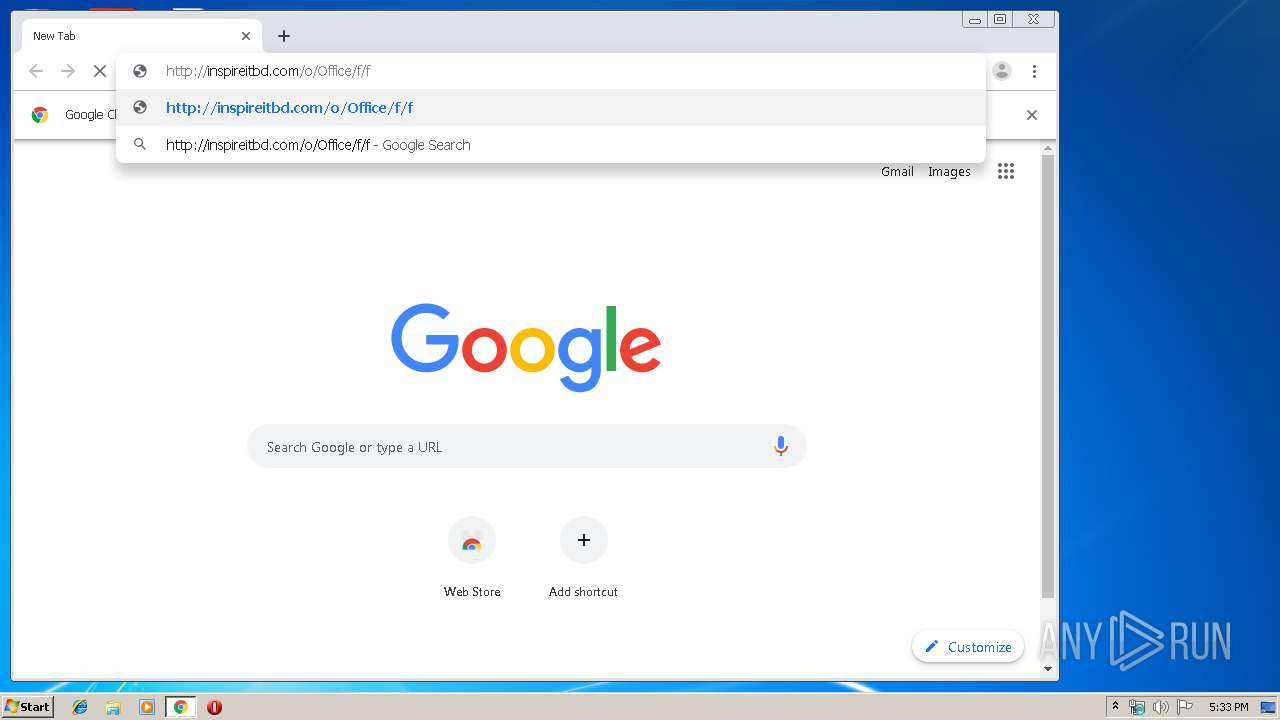
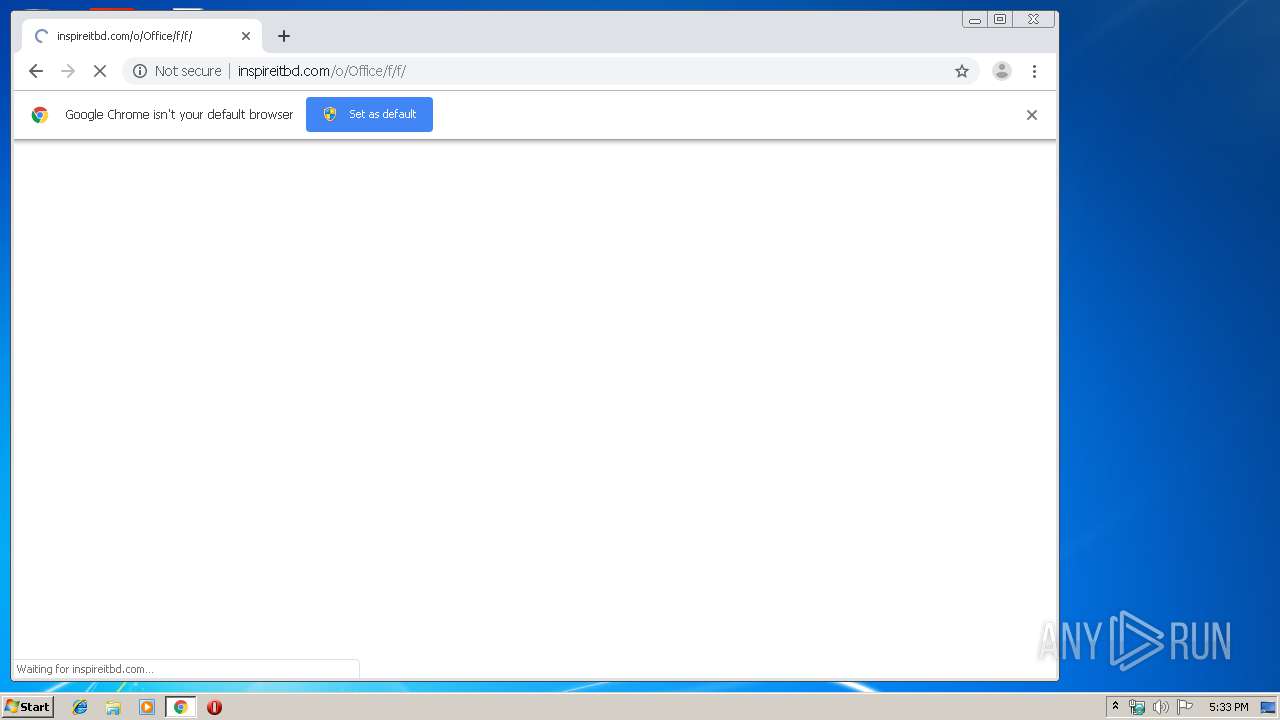
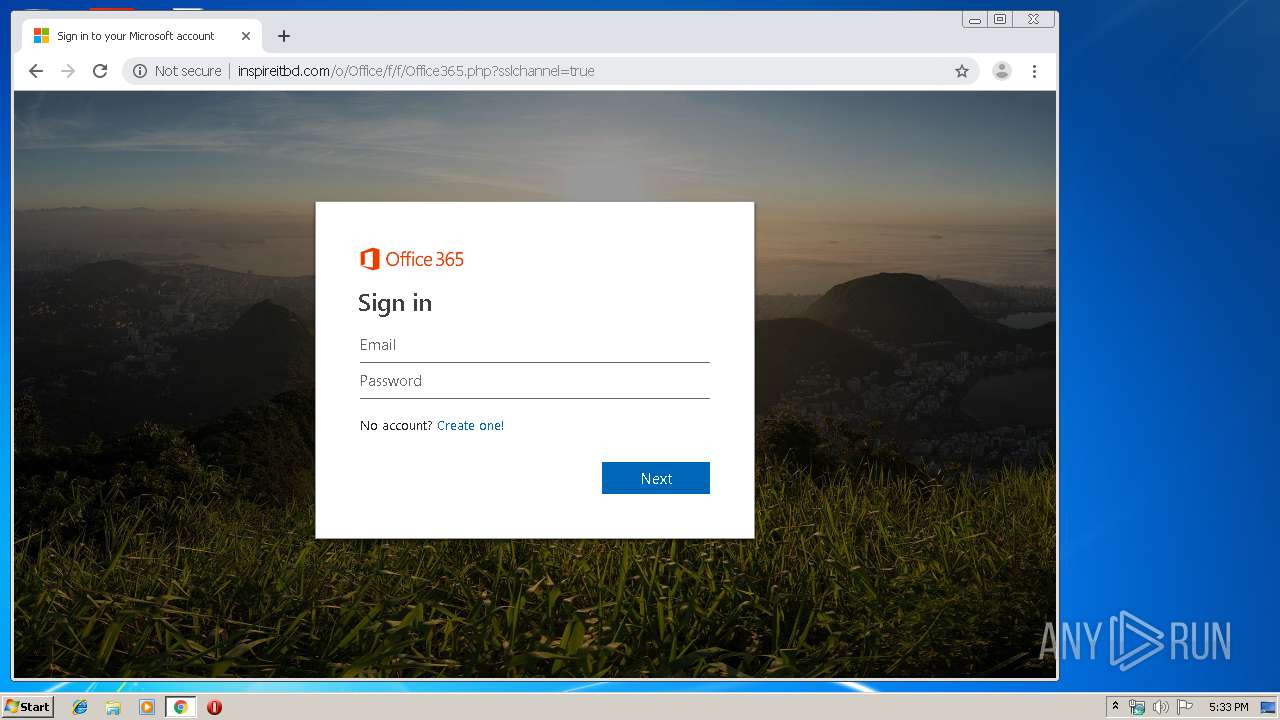
| URL: | http://inspireitbd.com/o/Office/f/f |
| Full analysis: | https://app.any.run/tasks/f98d91ed-fe19-4ab6-bea1-167c5c4e01d4 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 16:32:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8BB5D552C1D8CFDB8F4856A6325A975F |
| SHA1: | 374D3F248B7A7345A600A87000882F290DEB6DEF |
| SHA256: | DB51B071F30C0F5BB9C03F6DE6208931309D1CCB0FA253B538EECB8A8BBF5C22 |
| SSDEEP: | 3:N1KX2MvH9GTDs:CGwd8o |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 3772)
Creates files in the user directory
- iexplore.exe (PID: 3772)
Changes internet zones settings
- iexplore.exe (PID: 3532)
Application launched itself
- chrome.exe (PID: 1824)
Manual execution by user
- chrome.exe (PID: 1824)
Reads settings of System Certificates
- chrome.exe (PID: 2184)
Reads Internet Cache Settings
- iexplore.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8334438321149614188 --mojo-platform-channel-handle=3196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13078798440615313888 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8079471911094537064 --mojo-platform-channel-handle=2452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8057088681684216279 --mojo-platform-channel-handle=2460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2050660579468946303 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1664 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13664064392357824972 --mojo-platform-channel-handle=3052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1724130391717412091 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9057833681431388459,16313244349454905513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6614399766141664270 --mojo-platform-channel-handle=2980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
558
Read events
449
Write events
104
Delete events
5
Modification events
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {872FCFA1-A8B0-11E9-B2FD-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700030011001000200038002201 | |||
Executable files
0
Suspicious files
16
Text files
164
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2B67B0669F990F63.TMP | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF05EEB71961F15A1F.TMP | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7DB78AA9E24075EB.TMP | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{872FCFA2-A8B0-11E9-B2FD-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{9846CABC-A8B0-11E9-B2FD-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\TRADG134\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
27
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
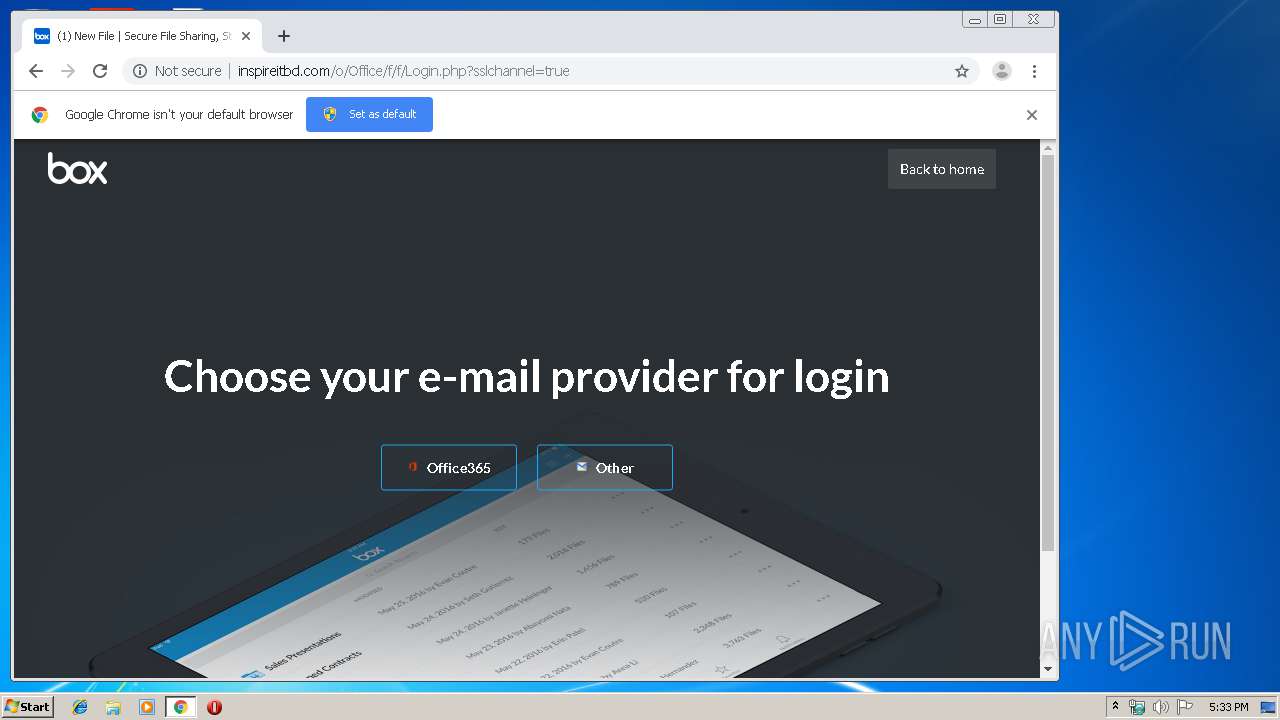
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/Login.php?sslchannel=true | SG | html | 6.80 Kb | suspicious |
2184 | chrome.exe | GET | 301 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f | SG | html | 244 b | suspicious |
2184 | chrome.exe | GET | 200 | 104.24.20.54:80 | http://pngimg.com/uploads/email/email_PNG20.png | US | image | 20.8 Kb | whitelisted |
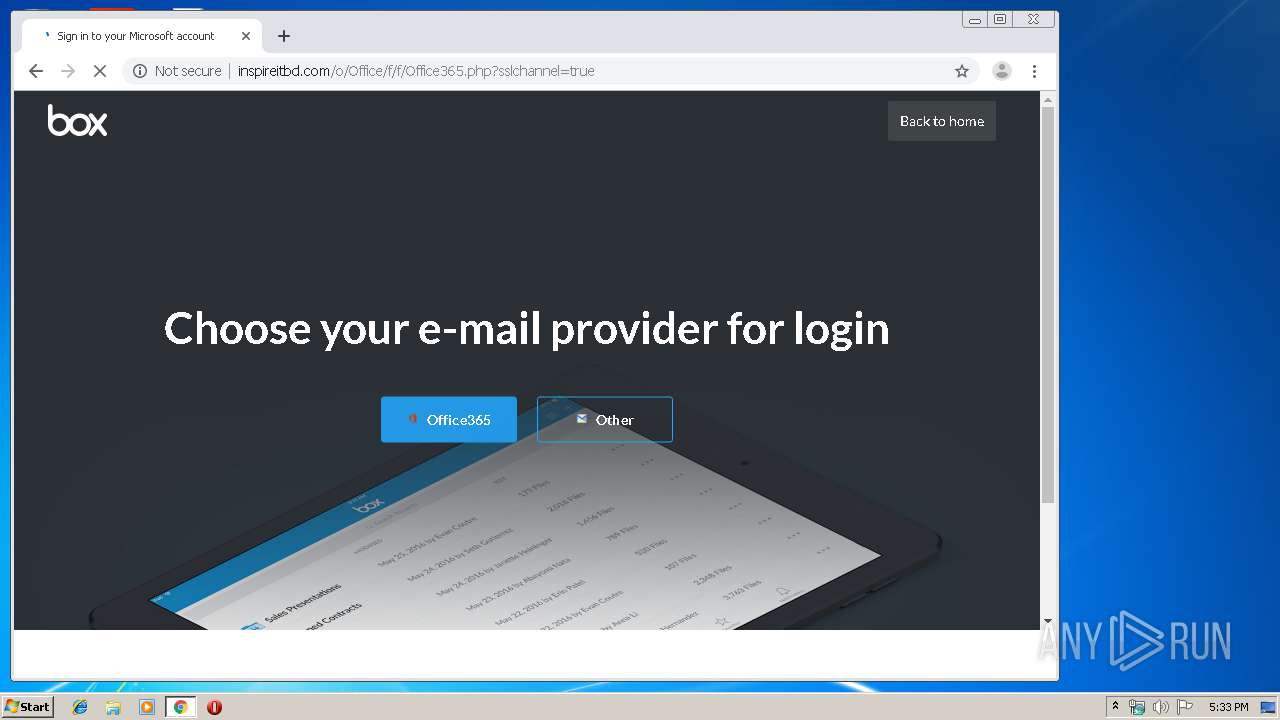
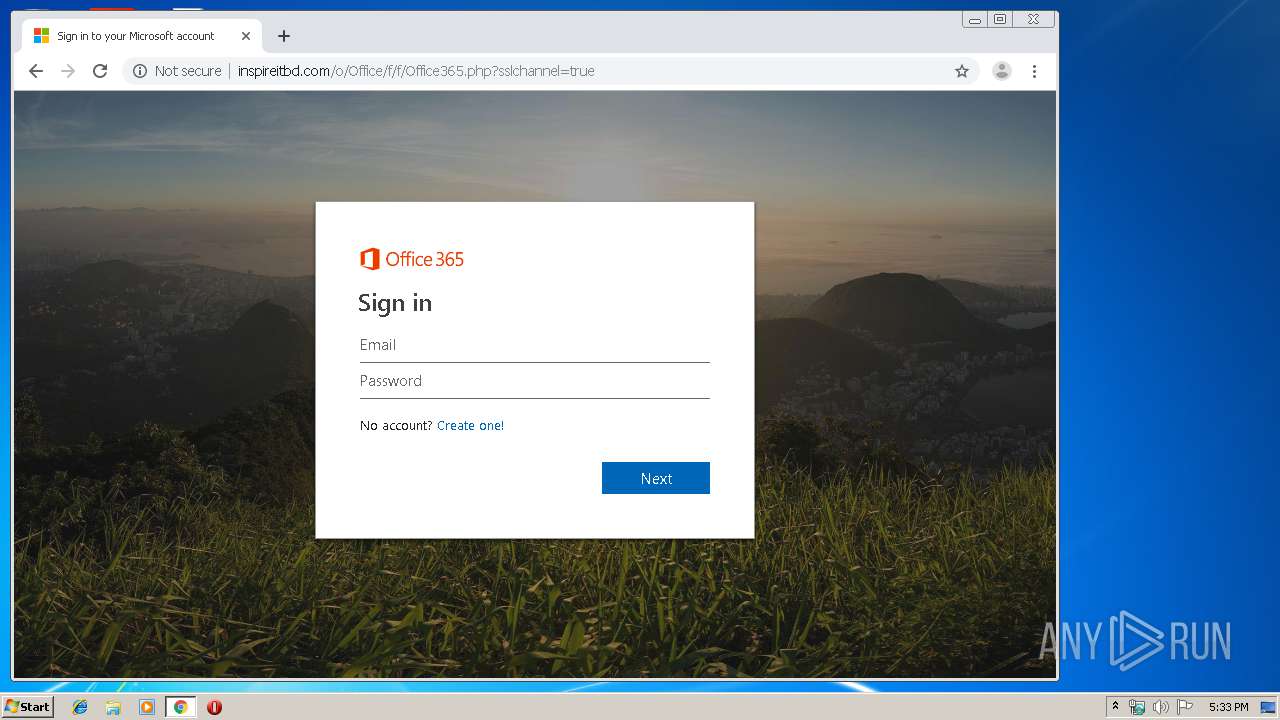
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/Office365.php?sslchannel=true | SG | html | 19.4 Kb | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/ | SG | html | 113 b | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/assets/css/css.css | SG | text | 4.48 Kb | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/assets/css/css_7jDhC7Vm4-oxtUbtZMHwD8LA2Gp2KNpvOzvod9283FA.css | SG | text | 202 Kb | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/assets/img/AstraZeneca_0.png | SG | image | 10.0 Kb | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/assets/css/css_whE_FIKmCdJjmQukMY5DBbmkss9qZjXENYcyIcR-90c.css | SG | text | 18.1 Kb | suspicious |
2184 | chrome.exe | GET | 200 | 128.199.68.181:80 | http://inspireitbd.com/o/Office/f/f/assets/css/css_yXMMnLSSpPunfPzrxqTY5Fxi0thyZrjewLEjqduzimc.css | SG | text | 7.06 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3772 | iexplore.exe | 128.199.68.181:80 | inspireitbd.com | Digital Ocean, Inc. | SG | suspicious |
2184 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.207.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.23.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
inspireitbd.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Microsoft Live Phishing Landing |
2184 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing M1 2018-04-19 |
2184 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |