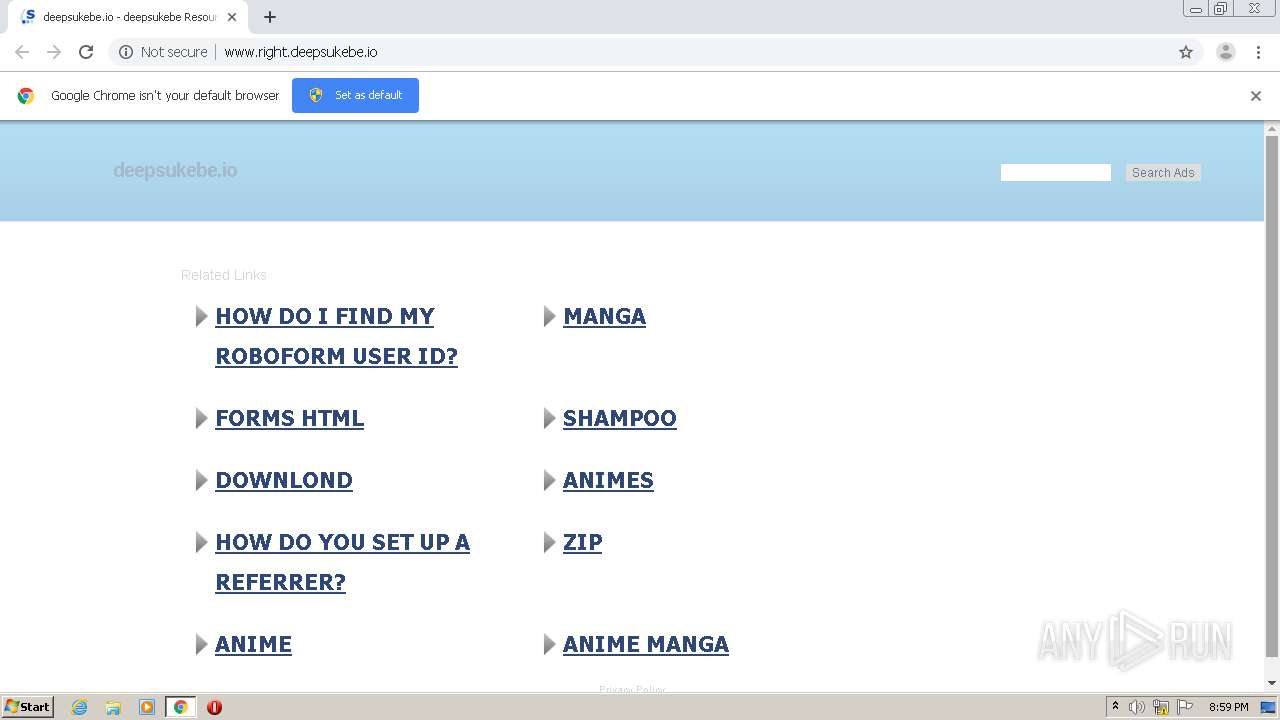
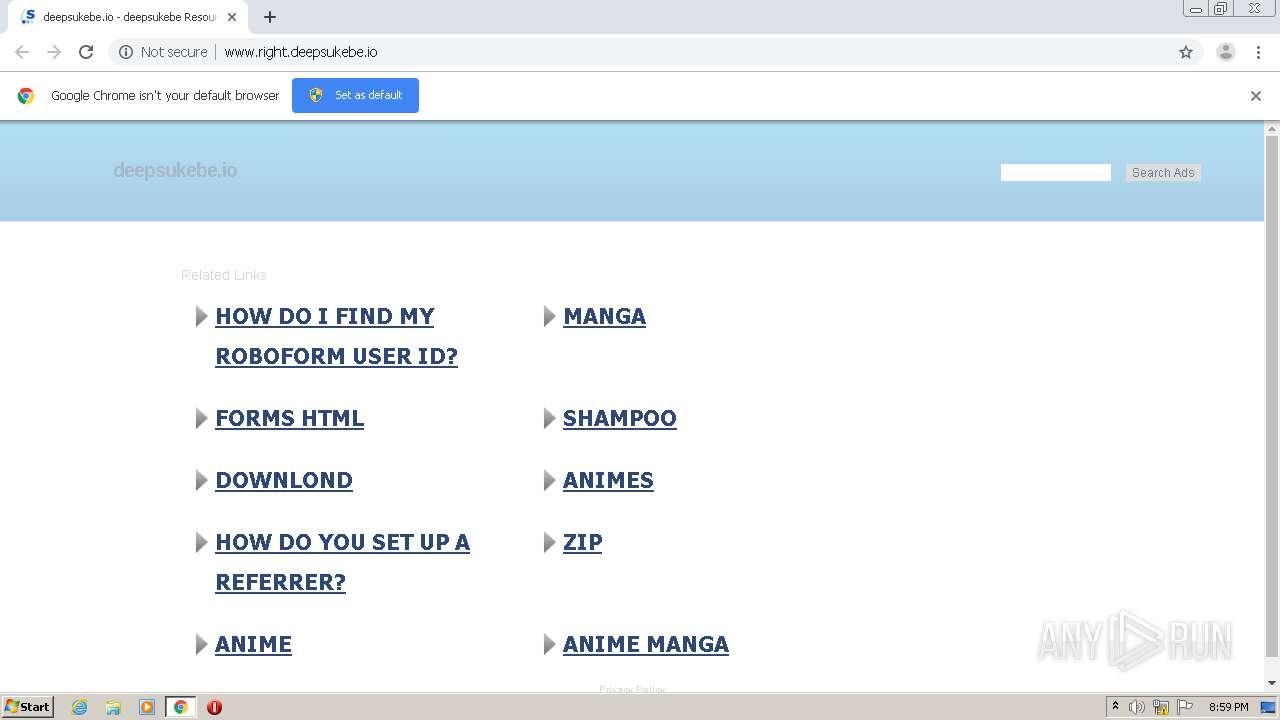
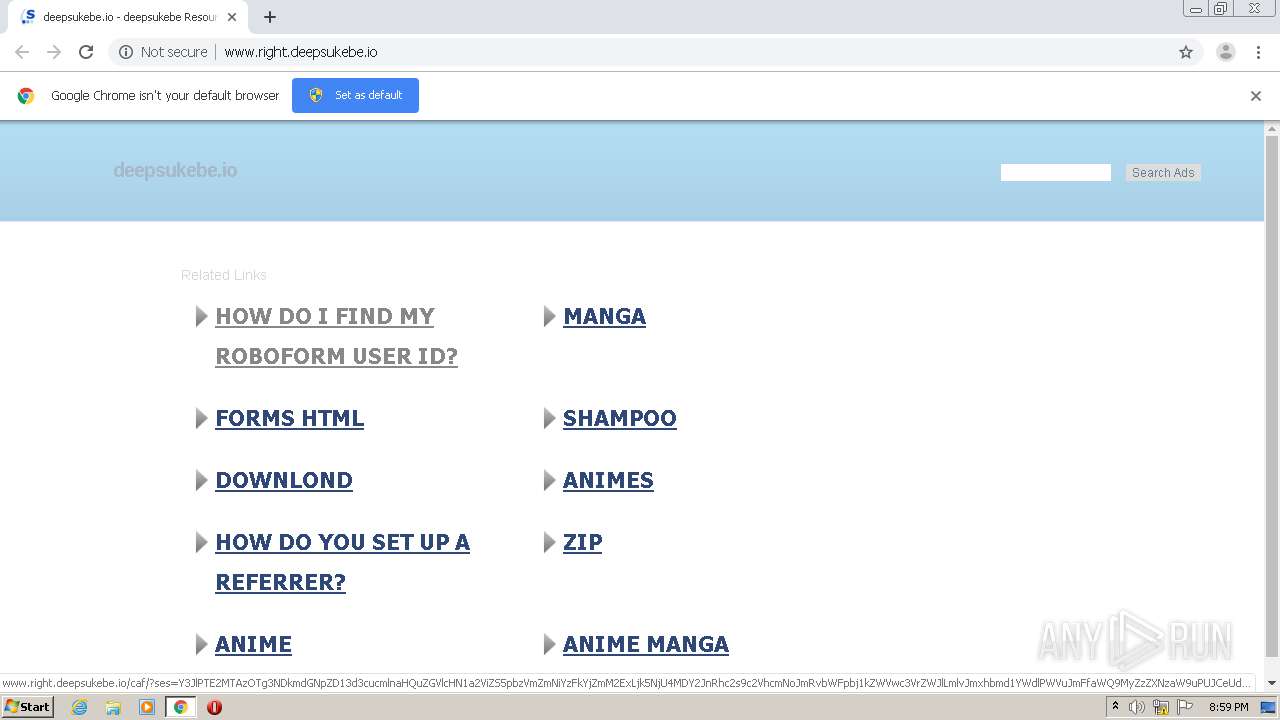
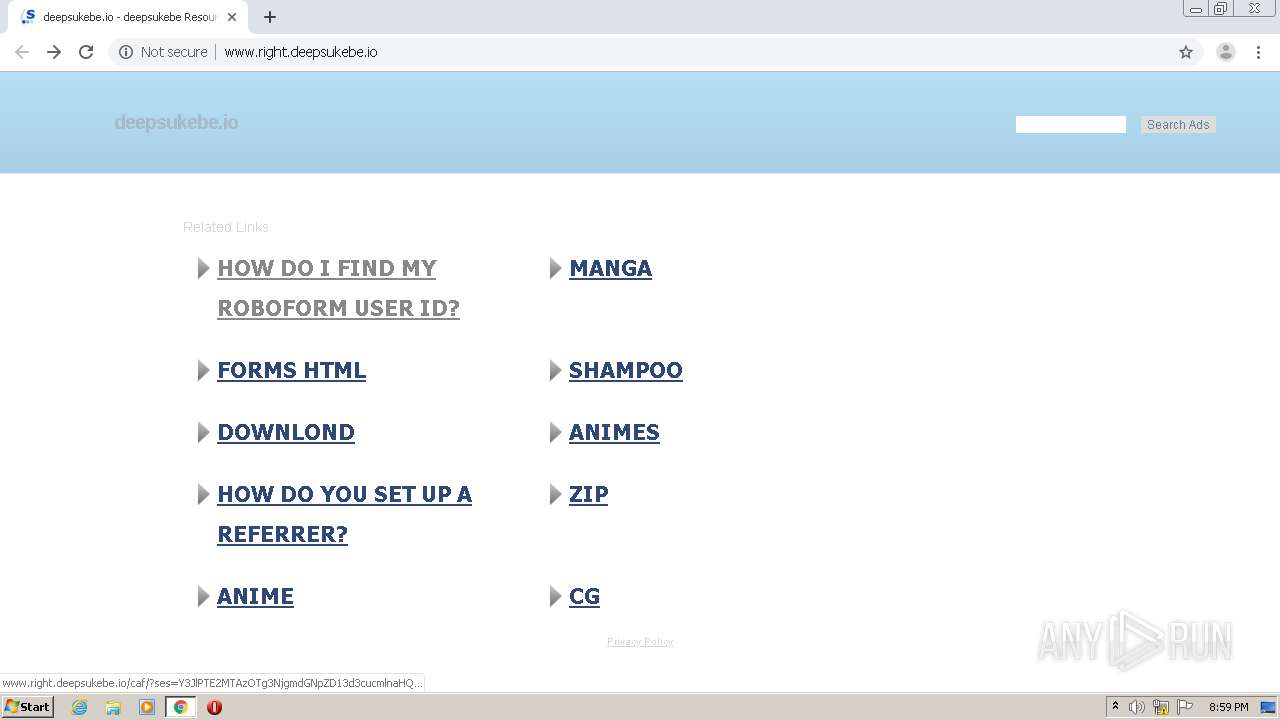
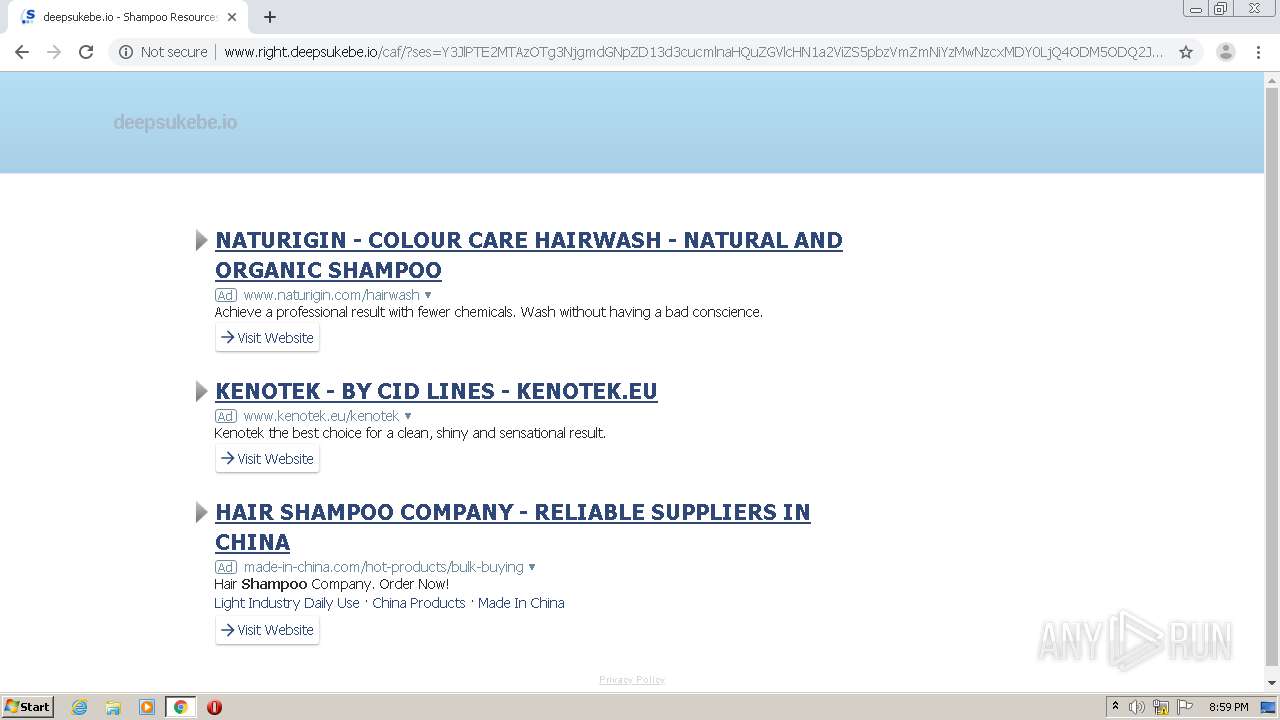
| URL: | http://www.right.deepsukebe.io |
| Full analysis: | https://app.any.run/tasks/10425fee-b822-4411-b004-634c923b7795 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2021, 20:58:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8D46BCBC4B979FE6675249CD48F11D50 |
| SHA1: | 620AC44857F865957037FD0CB434088D2435D3DF |
| SHA256: | DB408ED27761163A0071AC06263838B1B834881EC750BA3DA15D582311E6645F |
| SSDEEP: | 3:N1KJS4c04jH:Cc4c04jH |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2324)
Application launched itself
- chrome.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8753179356347639283 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8532432005705626453 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7537928558374682571 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2543294973218502291 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6513453833278207517 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10842231124425043550 --mojo-platform-channel-handle=1468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13746079551265284367 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2552 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13455662722010504180 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,17107949165162813378,3637174323734420872,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18231298936866430294 --mojo-platform-channel-handle=3696 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
590
Read events
532
Write events
55
Delete events
3
Modification events
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2544-13254872347934375 |
Value: 259 | |||
Executable files
0
Suspicious files
45
Text files
71
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FFCBC1C-9F0.pma | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9121025d-b82b-417b-a308-4f46a1649f69.tmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF154158.TMP | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15432d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
34
DNS requests
26
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
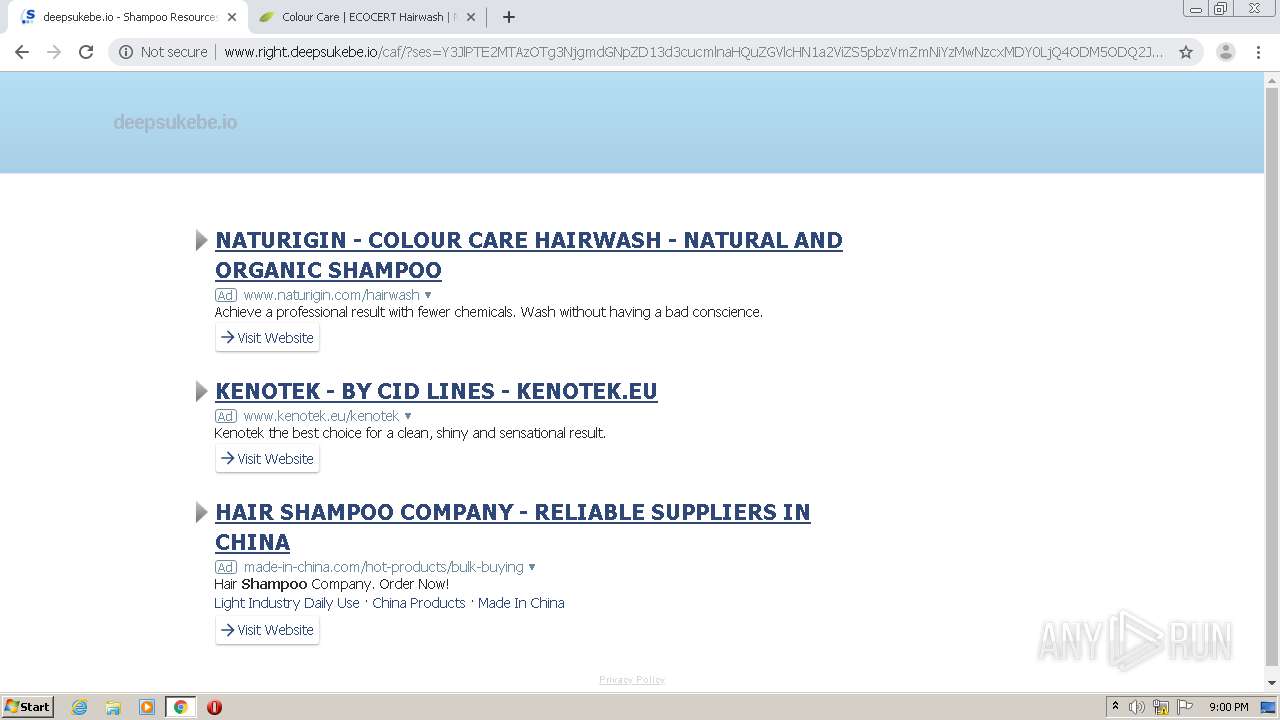
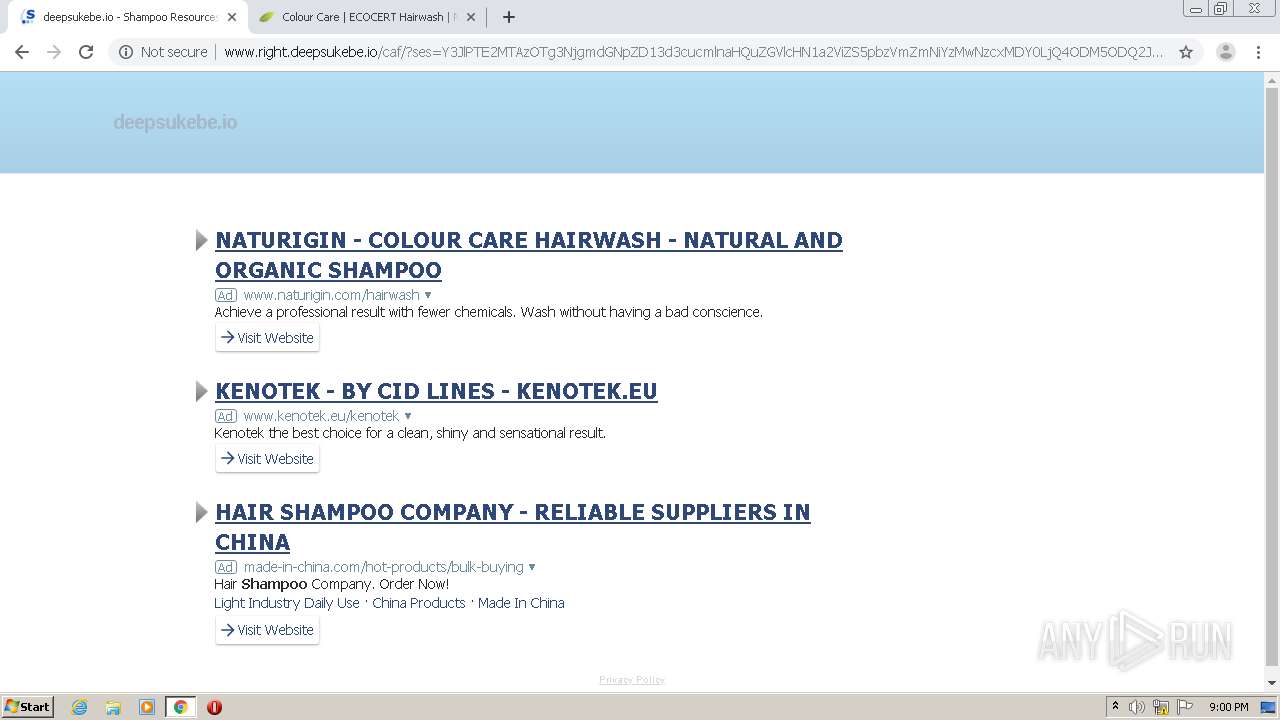
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/ | DE | compressed | 9.24 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/caf/?ses=Y3JlPTE2MTAzOTg4MDgmdGNpZD13d3cucmlnaHQuZGVlcHN1a2ViZS5pbzVmZmNiYzU4MDAxZmMyLjA3MTIzNTM5JnRhc2s9c2VhcmNoJmRvbWFpbj1kZWVwc3VrZWJlLmlvJmxhbmd1YWdlPWVuJmFfaWQ9MyZzZXNzaW9uPUJCeUdNNkpuSW9jdXQ1czVxbi1t&query=Torrent&afdToken=3B1gxW_zHO-14nClwvTMG0_Lk5Iw2mkU7KtSrX-vPTTb-_js6dALDrHVqsFsb5p8Y3IP1FHrXmTEt7AfidtH4Tu1_pVQC8vzEppLkxLFFTWD | DE | compressed | 8.86 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/tsc.php?200=MzU5NjEzMzMw&21=MTU0LjE2LjE3OS4yMQ==&681=MTYxMDM5ODc0OTI0MWU0YTBiMjk3YTU3MzhhN2RmMTA3Yjk0MjU4ZTlk&crc=6d33e2611016b04d05e6f4fdc39f767d8500736b&cv=1 | DE | compressed | 9.28 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/fb.php?ses=dee6cc34838adff301610398749f8b7b3b4c5044d9,dee6cc34838adff301610398749f8b7b3b4c5044d9&as=false&gc=partner-dp-sedo80_3ph | DE | compressed | 9.28 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/tsc.php?200=MzU5NjEzMzMw&21=MTU0LjE2LjE3OS4yMQ==&681=MTYxMDM5ODc3MTAwZGFiYjU5NjlmZGM0MjMxOTEyNWI4OGNmNWI2NDJm&crc=cd54f61b61c720416c10a96d5c4307da8bb6375c&cv=1 | DE | compressed | 8.89 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/tsc.php?200=MzU5NjEzMzMw&21=MTU0LjE2LjE3OS4yMQ==&681=MTYxMDM5ODgxMThhYzExOGVjMTFhZjZkOGJjNjVmZjlkODdjYjI2YjU5&crc=7e9b2bdd4ee80097db2efab94867c662d08c6012&cv=1 | DE | compressed | 8.86 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/fb.php?ses=3f937866ccca121f01610398768ac802a72147d1d0,3f937866ccca121f01610398768ac802a72147d1d0&as=false&gc=partner-dp-sedo80_3ph | DE | compressed | 9.24 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/fb.php?ses=0a359e53c10ced9a01610398771c8d0c3ba01528f0,0a359e53c10ced9a01610398771c8d0c3ba01528f0&as=false&gc=partner-dp-sedo80_3ph | DE | compressed | 8.89 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/search/fb.php?ses=5df6bbed3433f8d101610398761a12e95b43aebdc2,5df6bbed3433f8d101610398761a12e95b43aebdc2&as=false&gc=partner-dp-sedo80_3ph | DE | compressed | 8.90 Kb | malicious |
2324 | chrome.exe | GET | 200 | 91.195.240.103:80 | http://www.right.deepsukebe.io/caf/?ses=Y3JlPTE2MTAzOTg3NjgmdGNpZD13d3cucmlnaHQuZGVlcHN1a2ViZS5pbzVmZmNiYzMwNzcxMDY0LjQ4ODM5ODQ2JnRhc2s9c2VhcmNoJmRvbWFpbj1kZWVwc3VrZWJlLmlvJmxhbmd1YWdlPWVuJmFfaWQ9MyZzZXNzaW9uPUJCeUdNNkpuSW9jdXQ1czVxbi1t&query=Shampoo&afdToken=3B1ggVL5Rp384C6SwvTMWgHg4JMw2mkUOJburX-rSTk4-_jsqJ4gfbDVqsFsu6fAY3ILoFwIXmTEt7AfidtH4Tu1_t1jHrn1MKI11BLFFzWD | DE | compressed | 8.89 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2324 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
2324 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 216.58.206.193:443 | afs.googleusercontent.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2324 | chrome.exe | 172.217.23.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 91.195.240.210:443 | cc.sedoparking.com | SEDO GmbH | DE | suspicious |
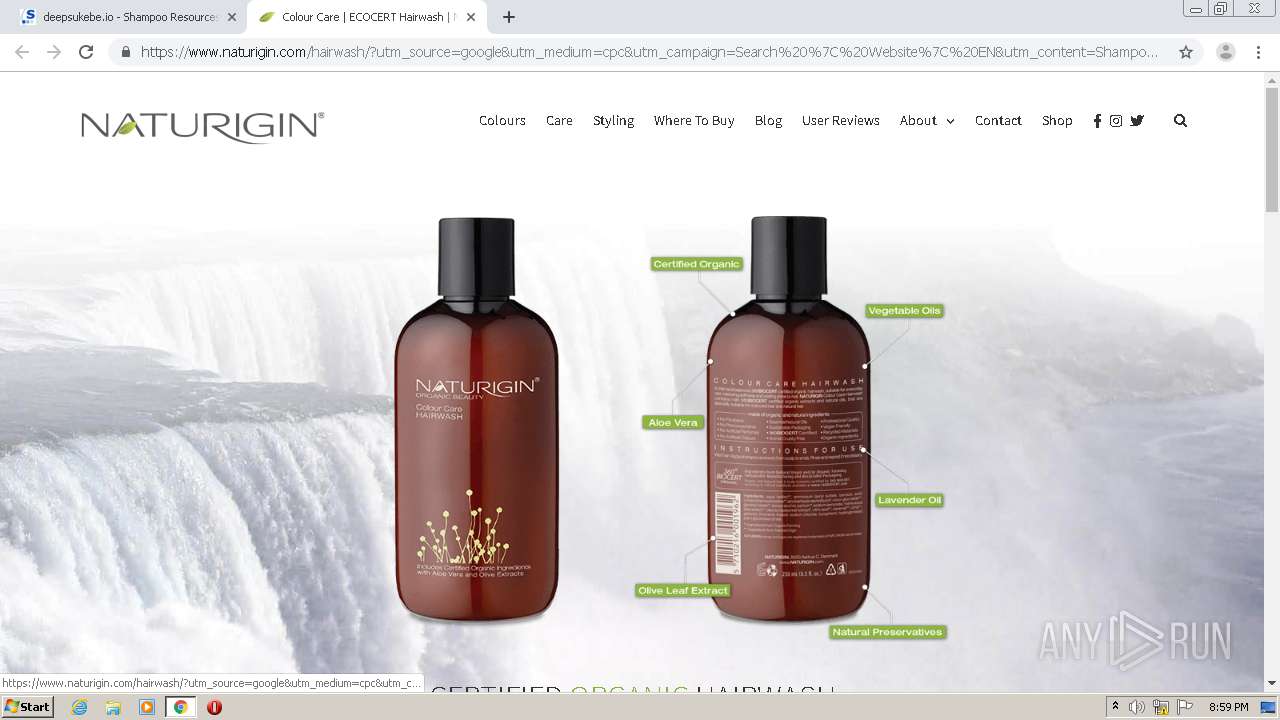
2324 | chrome.exe | 195.242.131.106:443 | www.naturigin.com | carbon14.dk v/Lars Brun Nielsen | DK | unknown |
2324 | chrome.exe | 172.217.18.98:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 216.58.212.163:443 | www.google.com.pk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.right.deepsukebe.io |
| malicious |
accounts.google.com |
| shared |
img.sedoparking.com |
| whitelisted |
www.google.com |
| malicious |
afs.googleusercontent.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
cc.sedoparking.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.naturigin.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2324 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2324 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |