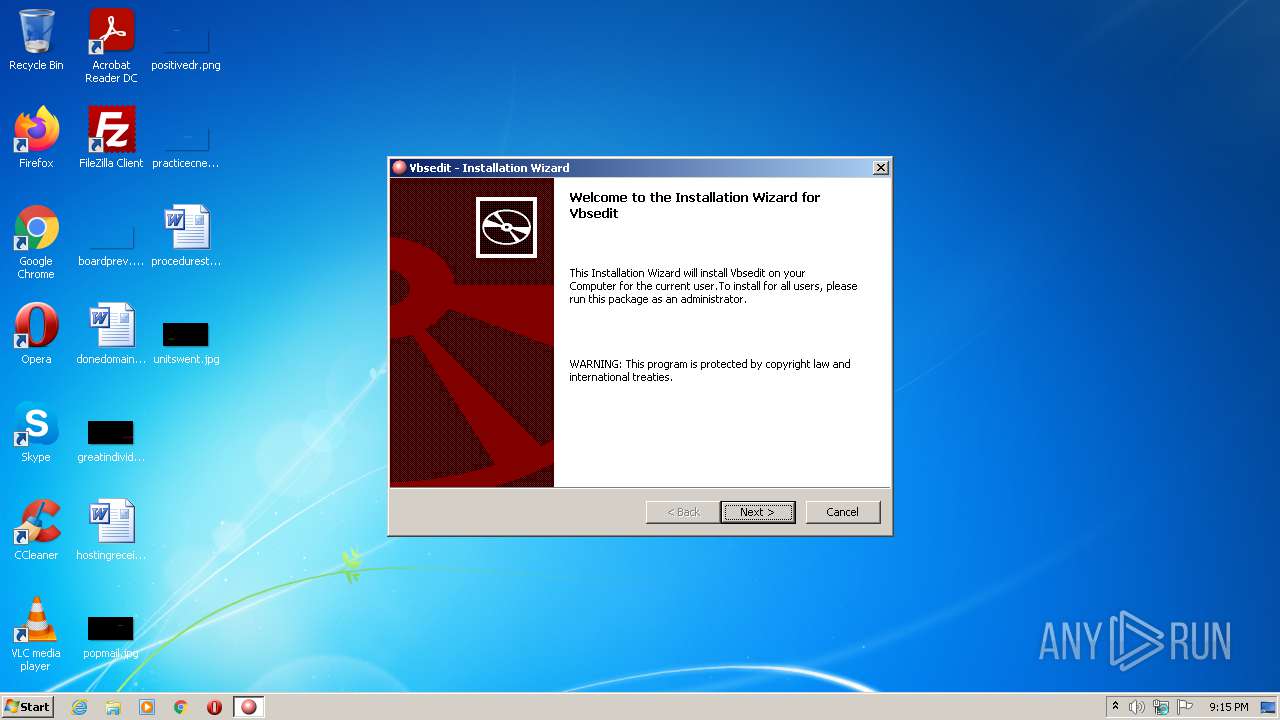
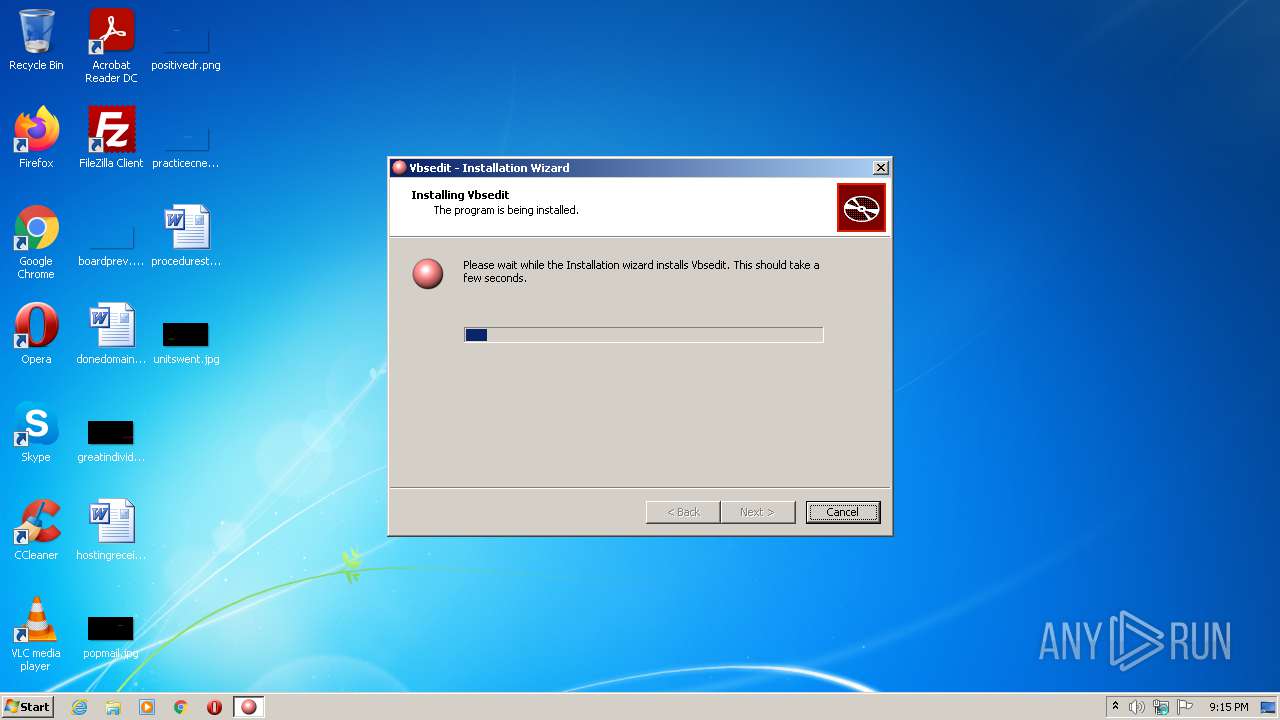
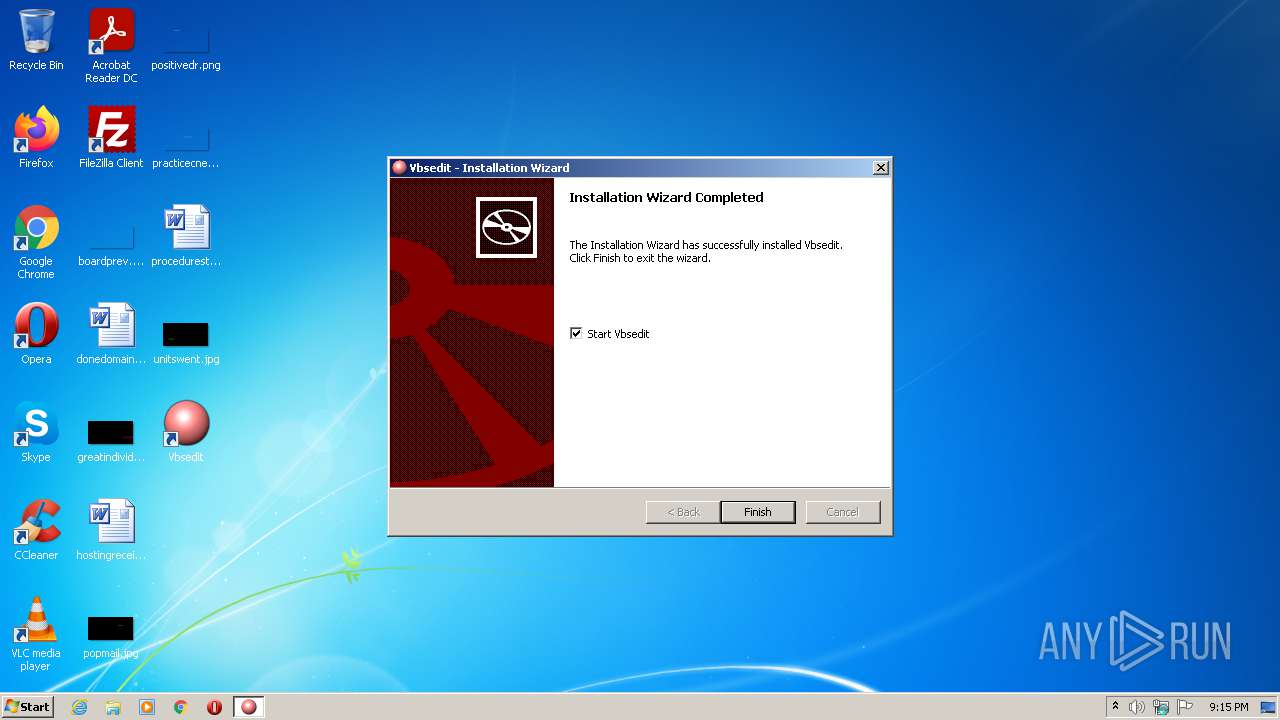
| File name: | VbsEditSetup.exe |
| Full analysis: | https://app.any.run/tasks/943b79b7-52bb-4b61-90c0-d068b0901005 |
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2021, 20:15:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1120DB0BABAD7147115911E797385F43 |
| SHA1: | 5C99296B7146E67C2B6782446115F9FF8A1C20E1 |
| SHA256: | DB35E379AD478872F9309A84D6A4EB720DE134D0D252045B9A6CFF1201C255B8 |
| SSDEEP: | 196608:tDKsZ/P6SMlsblbTF3j80UJEiAfmY1khN96E3WvS97rrBBuMGu9zaTg///lJ08yW:tOr4TM7VYY5mvGrHVvb/VmPdyxt6CSqB |
MALICIOUS
Application was dropped or rewritten from another process
- vbsedit7zip.exe (PID: 1248)
- stickynotes2.exe (PID: 3884)
- uninstall.exe (PID: 1620)
- Vbsedit.exe (PID: 2168)
- Vbsedit.exe (PID: 3176)
- Vbsedit.exe (PID: 1236)
- uninstall.exe (PID: 2348)
- stickynotes2.exe (PID: 3564)
Registers / Runs the DLL via REGSVR32.EXE
- uninstall.exe (PID: 1620)
Drops executable file immediately after starts
- uninstall.exe (PID: 1620)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 688)
- regsvr32.exe (PID: 3304)
- wscript.exe (PID: 2524)
- Vbsedit.exe (PID: 3176)
- uninstall.exe (PID: 1620)
SUSPICIOUS
Checks supported languages
- VbsEditSetup.exe (PID: 372)
- vbsedit7zip.exe (PID: 1248)
- uninstall.exe (PID: 1620)
- stickynotes2.exe (PID: 3564)
- stickynotes2.exe (PID: 3884)
- wscript.exe (PID: 2448)
- Vbsedit.exe (PID: 2168)
- Vbsedit.exe (PID: 3176)
- wscript.exe (PID: 744)
- wscript.exe (PID: 2524)
- uninstall.exe (PID: 2348)
- Vbsedit.exe (PID: 1236)
- wscript.exe (PID: 3264)
Executable content was dropped or overwritten
- vbsedit7zip.exe (PID: 1248)
- VbsEditSetup.exe (PID: 372)
- uninstall.exe (PID: 1620)
Drops a file with a compile date too recent
- vbsedit7zip.exe (PID: 1248)
- uninstall.exe (PID: 1620)
Reads the computer name
- uninstall.exe (PID: 1620)
- stickynotes2.exe (PID: 3564)
- stickynotes2.exe (PID: 3884)
- wscript.exe (PID: 744)
- wscript.exe (PID: 2448)
- Vbsedit.exe (PID: 3176)
- wscript.exe (PID: 2524)
- Vbsedit.exe (PID: 1236)
- wscript.exe (PID: 3264)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3304)
- wscript.exe (PID: 2448)
Drops a file that was compiled in debug mode
- uninstall.exe (PID: 1620)
- vbsedit7zip.exe (PID: 1248)
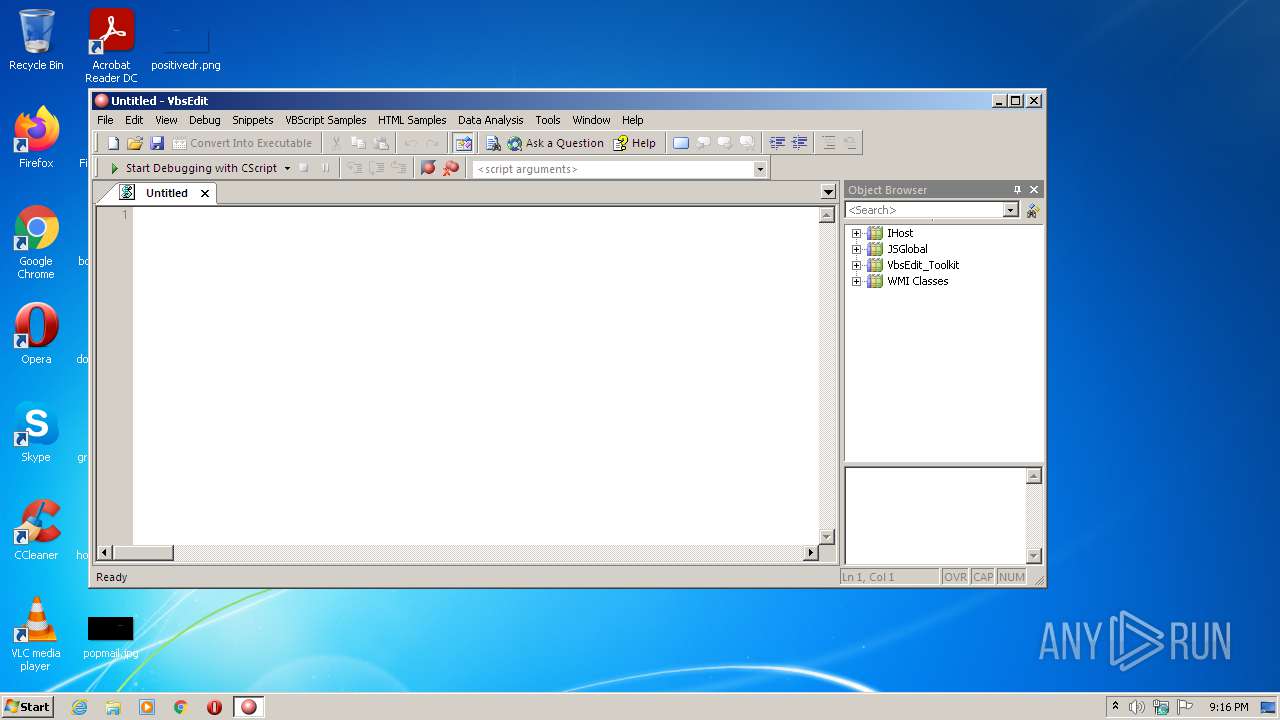
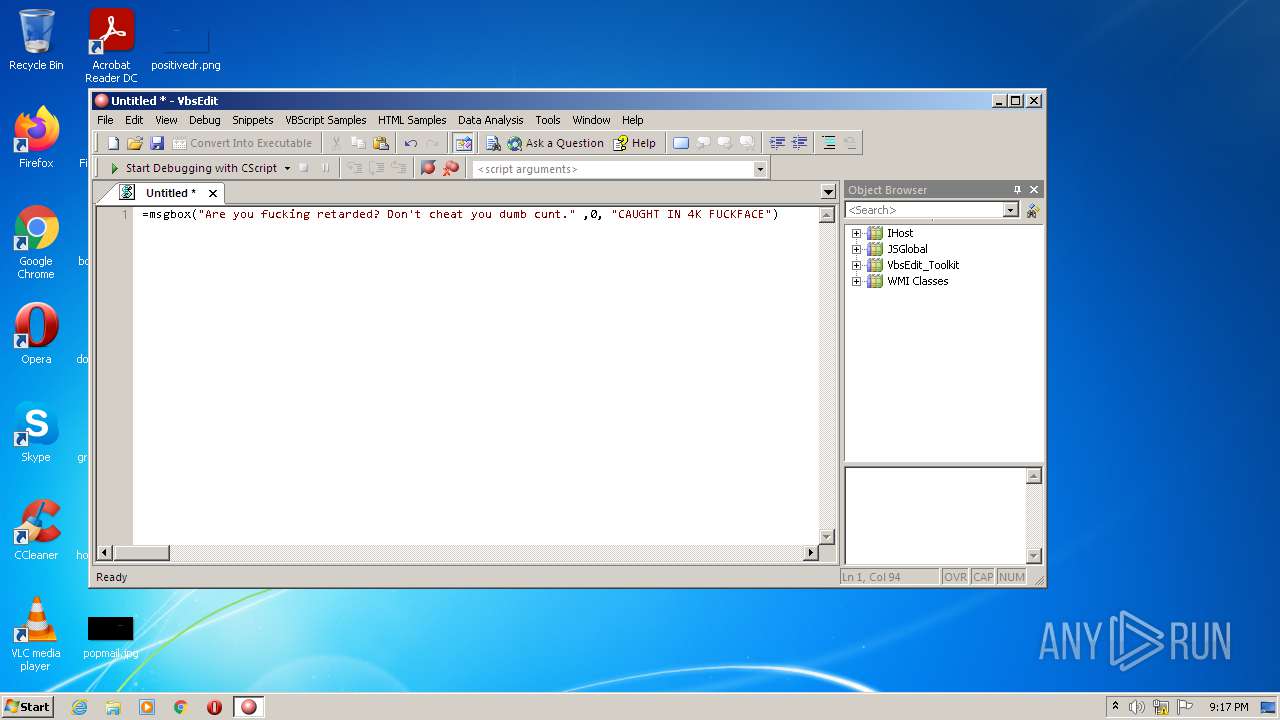
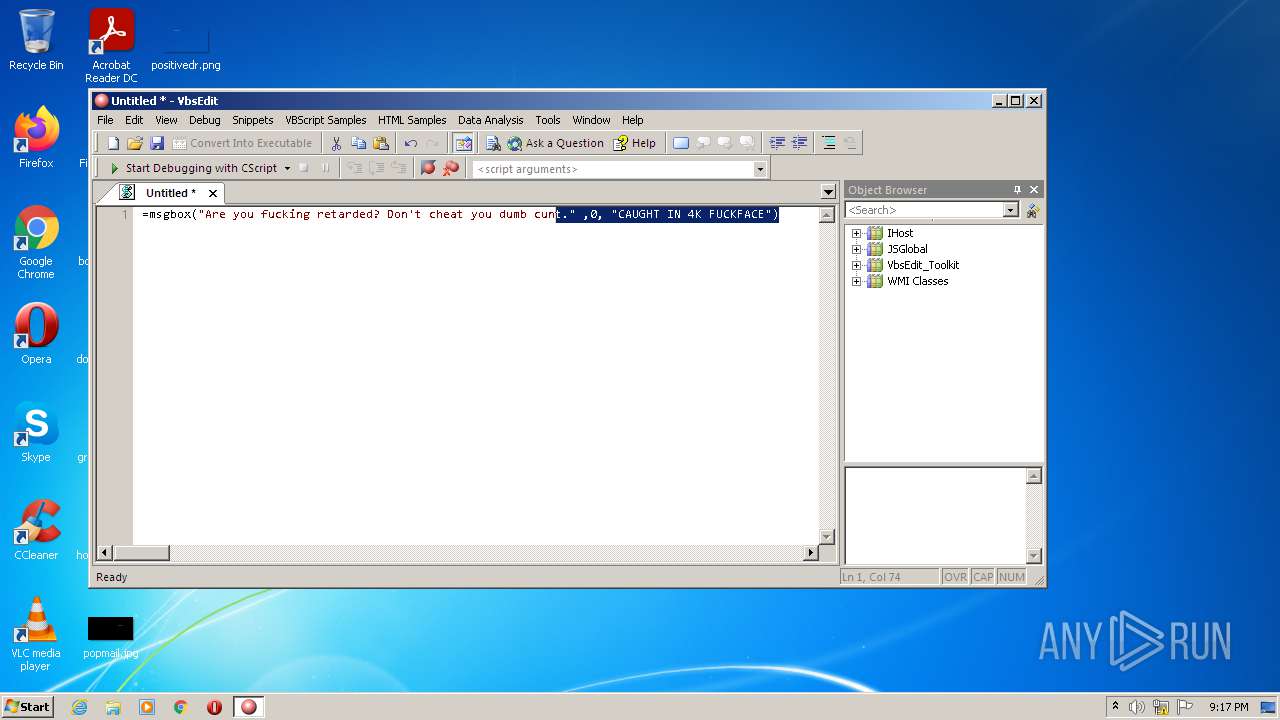
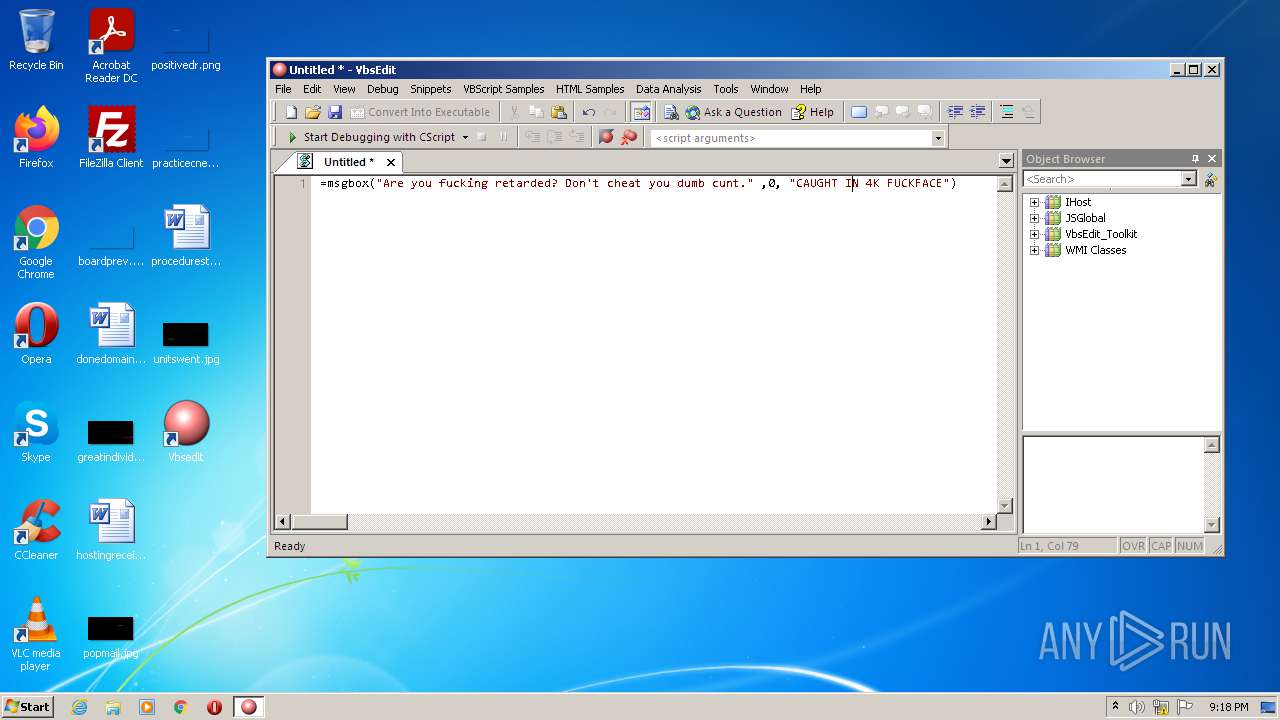
Executes scripts
- uninstall.exe (PID: 1620)
- Vbsedit.exe (PID: 3176)
- VbsEditSetup.exe (PID: 372)
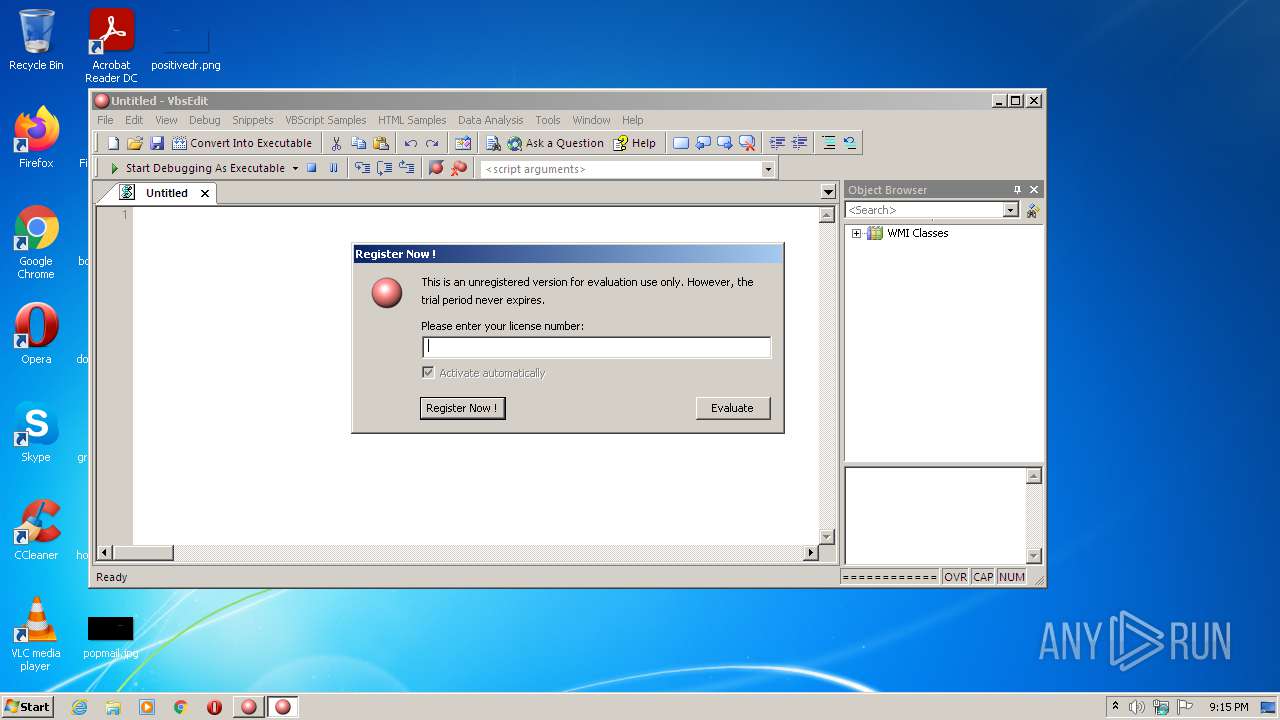
Reads Windows Product ID
- Vbsedit.exe (PID: 2168)
- Vbsedit.exe (PID: 3176)
- Vbsedit.exe (PID: 1236)
Creates files in the user directory
- uninstall.exe (PID: 1620)
Creates a software uninstall entry
- uninstall.exe (PID: 1620)
Changes default file association
- uninstall.exe (PID: 1620)
Searches for installed software
- uninstall.exe (PID: 1620)
Reads internet explorer settings
- Vbsedit.exe (PID: 1236)
Reads Microsoft Outlook installation path
- Vbsedit.exe (PID: 1236)
INFO
Checks supported languages
- regsvr32.exe (PID: 688)
- regsvr32.exe (PID: 3304)
Dropped object may contain Bitcoin addresses
- vbsedit7zip.exe (PID: 1248)
- uninstall.exe (PID: 1620)
Checks Windows Trust Settings
- wscript.exe (PID: 744)
- wscript.exe (PID: 2448)
- wscript.exe (PID: 2524)
- Vbsedit.exe (PID: 1236)
- wscript.exe (PID: 3264)
Reads settings of System Certificates
- Vbsedit.exe (PID: 1236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| ProductVersion: | 9.4.92.5 |
|---|---|
| ProductName: | Vbsedit |
| OriginalFileName: | vbsedit.exe |
| LegalCopyright: | Copyright 2001-2021 Adersoft |
| InternalName: | vbsedit.exe |
| FileVersion: | 9.4.92.5 |
| FileDescription: | Vbsedit |
| CompanyName: | Adersoft |
| Comments: | Vbsedit |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 9.4.92.5 |
| FileVersionNumber: | 9.4.92.5 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x15214e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 10024960 |
| CodeSize: | 1564672 |
| LinkerVersion: | 14.27 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:10 14:24:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2021 12:24:46 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Vbsedit |
| CompanyName: | Adersoft |
| FileDescription: | Vbsedit |
| FileVersion: | 9.4.92.5 |
| InternalName: | vbsedit.exe |
| LegalCopyright: | Copyright 2001-2021 Adersoft |
| OriginalFilename: | vbsedit.exe |
| ProductName: | Vbsedit |
| ProductVersion: | 9.4.92.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jun-2021 12:24:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0017DED9 | 0x0017E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48961 |
.rdata | 0x0017F000 | 0x00053554 | 0x00053600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99748 |
.data | 0x001D3000 | 0x0000AB98 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70482 |
.rsrc | 0x001DE000 | 0x0090E298 | 0x0090E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99236 |
.reloc | 0x00AED000 | 0x00023184 | 0x00023200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56846 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1424 | 1455 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.29306 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 4.30133 | 488 | UNKNOWN | English - United States | RT_ICON |
4 | 3.81038 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 6.19292 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 6.35566 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 6.3836 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 5.07849 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 5.24172 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 5.45426 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
53
Monitored processes
15
Malicious processes
8
Suspicious processes
1
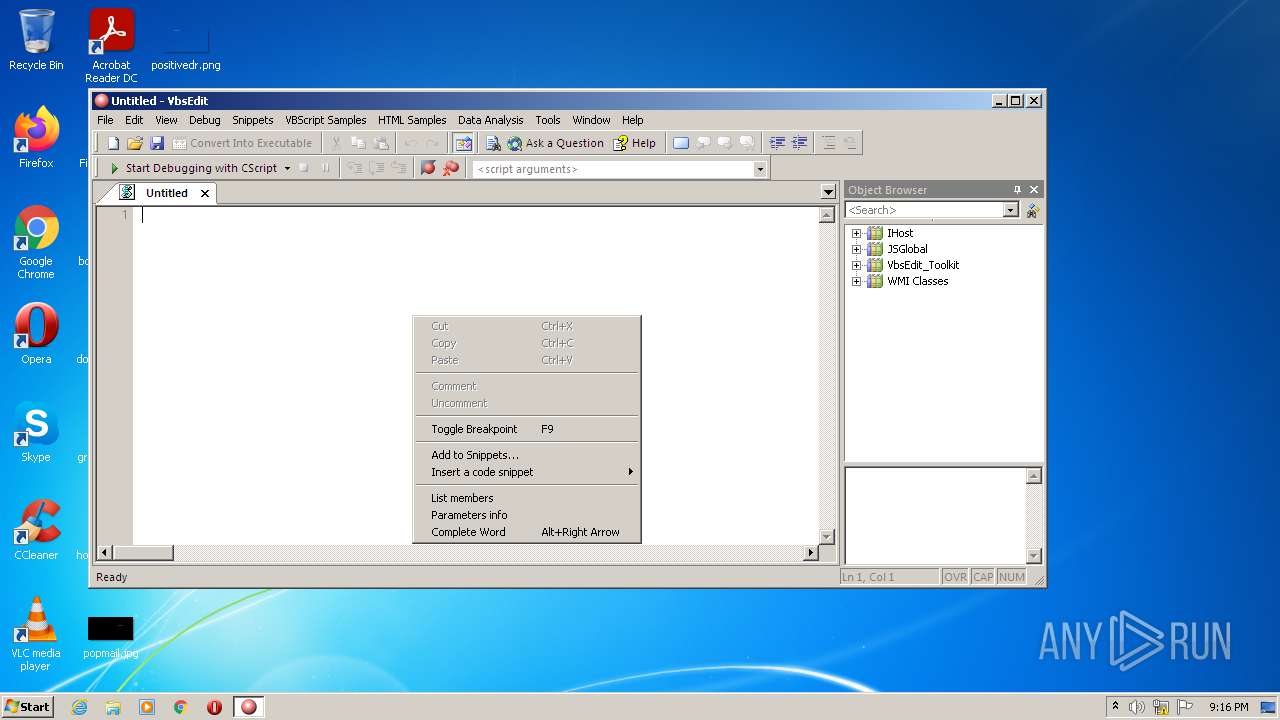
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Users\admin\AppData\Local\Temp\VbsEditSetup.exe" | C:\Users\admin\AppData\Local\Temp\VbsEditSetup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adersoft Integrity Level: MEDIUM Description: Vbsedit Exit code: 0 Version: 9.4.92.5 Modules
| |||||||||||||||
| 688 | regsvr32.exe /s /u /n /i:user "C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86\Vbsedit32.dll" | C:\Windows\system32\regsvr32.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 744 | wscript.exe //B "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\install_automation.vbs" "C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86" HKCU | C:\Windows\system32\wscript.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 200 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86\Vbsedit.exe" | C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86\Vbsedit.exe | — | uninstall.exe | |||||||||||
User: admin Company: Adersoft Integrity Level: MEDIUM Description: VbsEdit Exit code: 0 Version: 9.4.92.5 Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\vbsedit7zip.exe" -o"C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925" -p123VBSEDIT987 -y | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\vbsedit7zip.exe | VbsEditSetup.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1620 | "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\x86\uninstall.exe" "C:\Users\admin\AppData\Local\Temp" "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925" myself pdm | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\x86\uninstall.exe | VbsEditSetup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86\Vbsedit.exe" /testdebugger | C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86\Vbsedit.exe | — | uninstall.exe | |||||||||||
User: admin Company: Adersoft Integrity Level: MEDIUM Description: VbsEdit Exit code: 57 Version: 9.4.92.5 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\x86\uninstall.exe" startvbseditmyself | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\x86\uninstall.exe | — | VbsEditSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2448 | wscript.exe //B "C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\installkeys.vbs" "C:\Users\admin\AppData\Local\Adersoft\Vbsedit\x86" | C:\Windows\system32\wscript.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 200 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2524 | wscript.exe //B //D "C:\Users\admin\AppData\Local\Adersoft\VbsEdit\Temp\test.vbs" | C:\Windows\system32\wscript.exe | — | Vbsedit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
8 032
Read events
6 015
Write events
1 924
Delete events
93
Modification events
| (PID) Process: | (372) VbsEditSetup.exe | Key: | HKEY_CURRENT_USER\Software\Adersoft\VbsEditSetup\Installation |
| Operation: | write | Name: | TemporaryFolder |
Value: | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.PivotTable.1 |
| Operation: | write | Name: | (default) |
Value: PivotTable Class | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.PivotTable.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {438A9411-04DE-4E4D-A877-5503FAFBD670} | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.PivotTable |
| Operation: | write | Name: | (default) |
Value: PivotTable Class | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.PivotTable\CurVer |
| Operation: | write | Name: | (default) |
Value: Vbsedit.PivotTable.1 | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.ImageProcessor.1 |
| Operation: | write | Name: | (default) |
Value: ImageProcessor Class | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.ImageProcessor.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {B6373EBD-8A98-401D-AA34-EAF6A12B841B} | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.ImageProcessor |
| Operation: | write | Name: | (default) |
Value: ImageProcessor Class | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.ImageProcessor\CurVer |
| Operation: | write | Name: | (default) |
Value: Vbsedit.ImageProcessor.1 | |||
| (PID) Process: | (3304) regsvr32.exe | Key: | HKEY_CLASSES_ROOT\Vbsedit.IpToCountry.1 |
| Operation: | write | Name: | (default) |
Value: IpToCountry Class | |||
Executable files
56
Suspicious files
13
Text files
35
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | VbsEditSetup.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\vbsedit7zip.exe | executable | |
MD5:— | SHA256:— | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\samples2.dat | binary | |
MD5:EF5238A37521AF2931755902EFA1B16B | SHA256:237DD3FBDC150F353F886CFB0AD9B4EDBFF5F6A5769AD780C01AAAE4E77D2082 | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\asp.intellisense | text | |
MD5:674CA508A6E24BC003BDB8245690DD35 | SHA256:032E88010277F2BCC3FA3BBEFEF76A6CA836B365CEAD88DE55FFE1700C8A6163 | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\vbsedit.chm | chm | |
MD5:B6DAA3FAB5125A0E0DFFB9C2B817A6C4 | SHA256:9F10A5BD9DA20237A14D36EA51692AF2C3117CB735384713ADD051D07CD899BD | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\allcharts.vbs | html | |
MD5:7382B44CBEAE5D3EBE5A2A0D7F3AD22F | SHA256:8B9D1E4A66327356AF3CFA1BC4B85EC79246FAD38EE8808CC38C2589A2C84AFC | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\script56.chm | chm | |
MD5:7E01A2B5A778872B46250A94E0CF69F3 | SHA256:C849812CF3F222CEBB64D5CB43420B4C93EB3CA8F145EF25AB32A2DE950D6911 | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\checkversion.vbs | text | |
MD5:2E8635BCFB7B700BA840BB4EC5282675 | SHA256:D5B2BFE721658F560A6CB3FAECB22C94C79C1205E54B4450A2A83DE20D7A26C4 | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\hta.intellisense | text | |
MD5:CB1F7A5D08B940F52DD6A9D819021319 | SHA256:D3C3606196E79F73253A815DB1F02D7856E2AF24D237221EC4071BA35BD4D88D | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\samples_resource.dat | binary | |
MD5:317C99CA3543E99D5FB40F074BFF2EEB | SHA256:C87E774CAC6BA3A01D7972AD352E0CA3B3BD1D5F91D6BF4717A1D7E4F331BCF8 | |||
| 1248 | vbsedit7zip.exe | C:\Users\admin\AppData\Local\Adersoft\Vbsedit_installation_94925\common\installkeys.vbs | text | |
MD5:6CB8BA66B1FF8D11F76A20BB92DBF075 | SHA256:686427A53479B1DD40FF1B56F05ADF0C9AC6B3B6FBDB96CEDB47B71C5B5B1711 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | wscript.exe | POST | 200 | 192.119.67.28:80 | http://www.vbsedit.com/checkversion2.asp | US | text | 5 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | wscript.exe | 192.119.67.28:80 | www.vbsedit.com | Hostwinds LLC. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.vbsedit.com |
| suspicious |