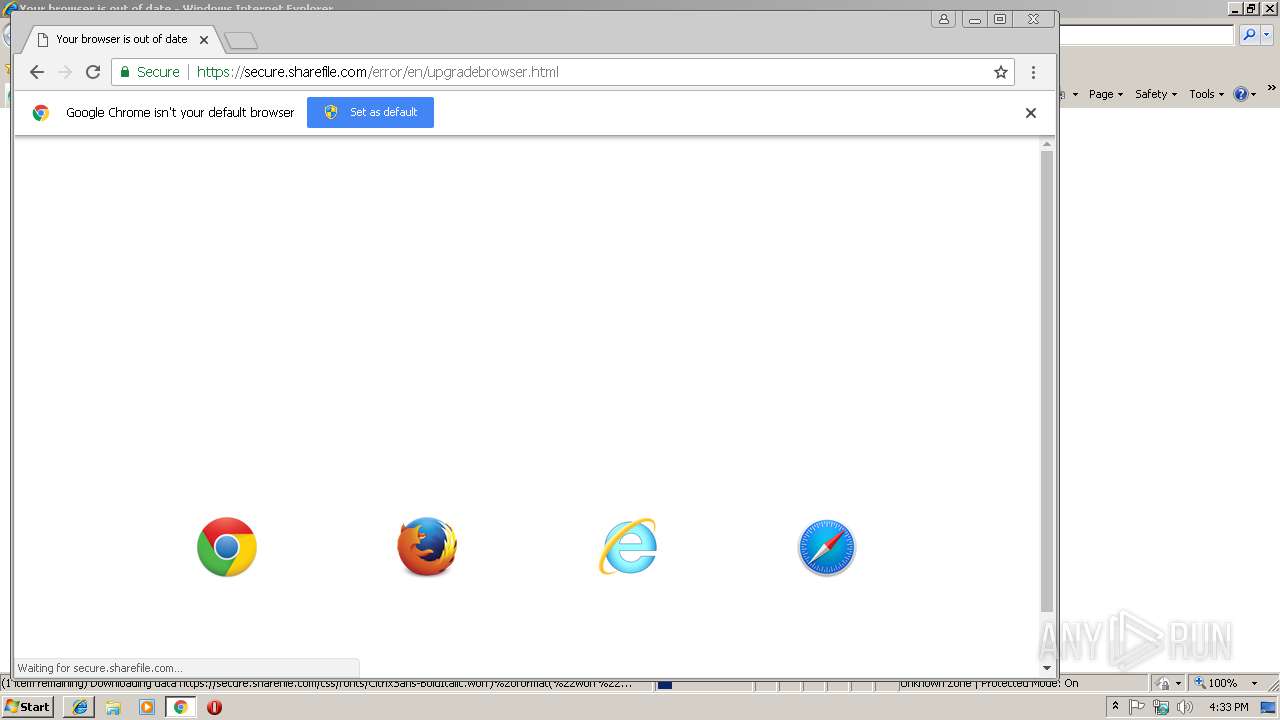
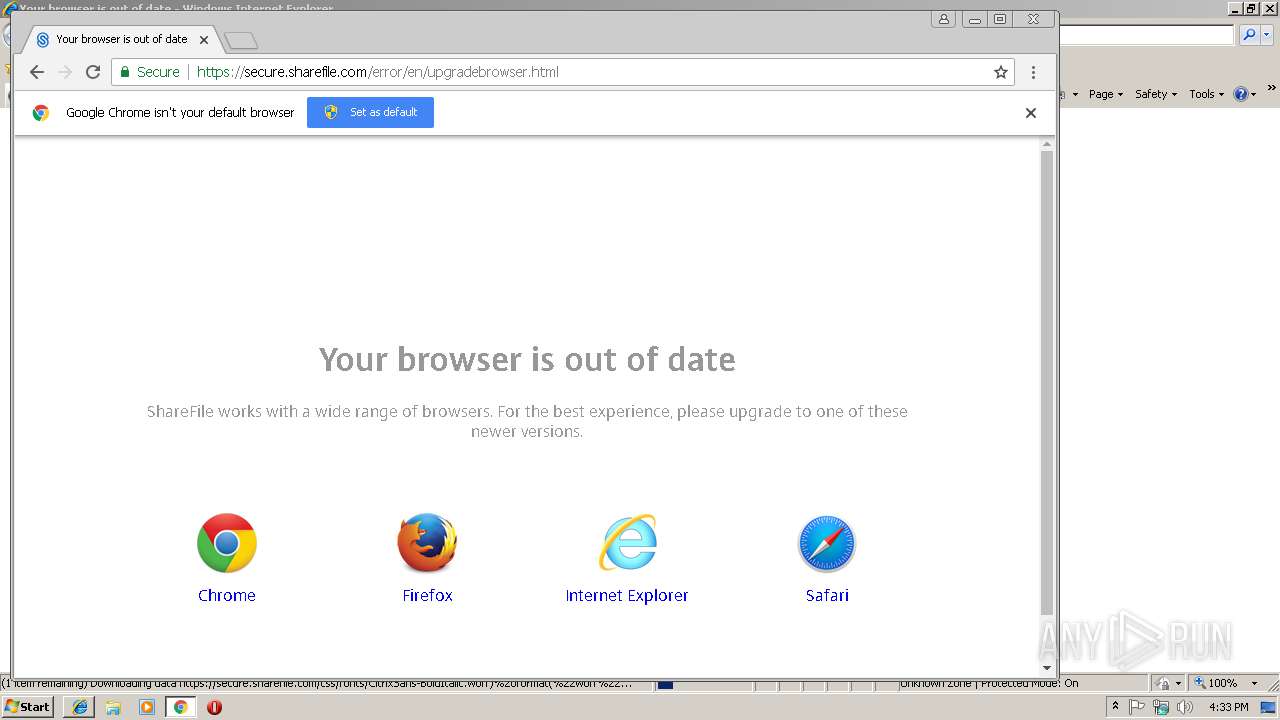
| URL: | https://secure.sharefile.com/Authentication/Login#ForgotPassword |
| Full analysis: | https://app.any.run/tasks/0b8d53df-6df4-4164-aee6-e400a391e9a2 |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2018, 16:33:24 |
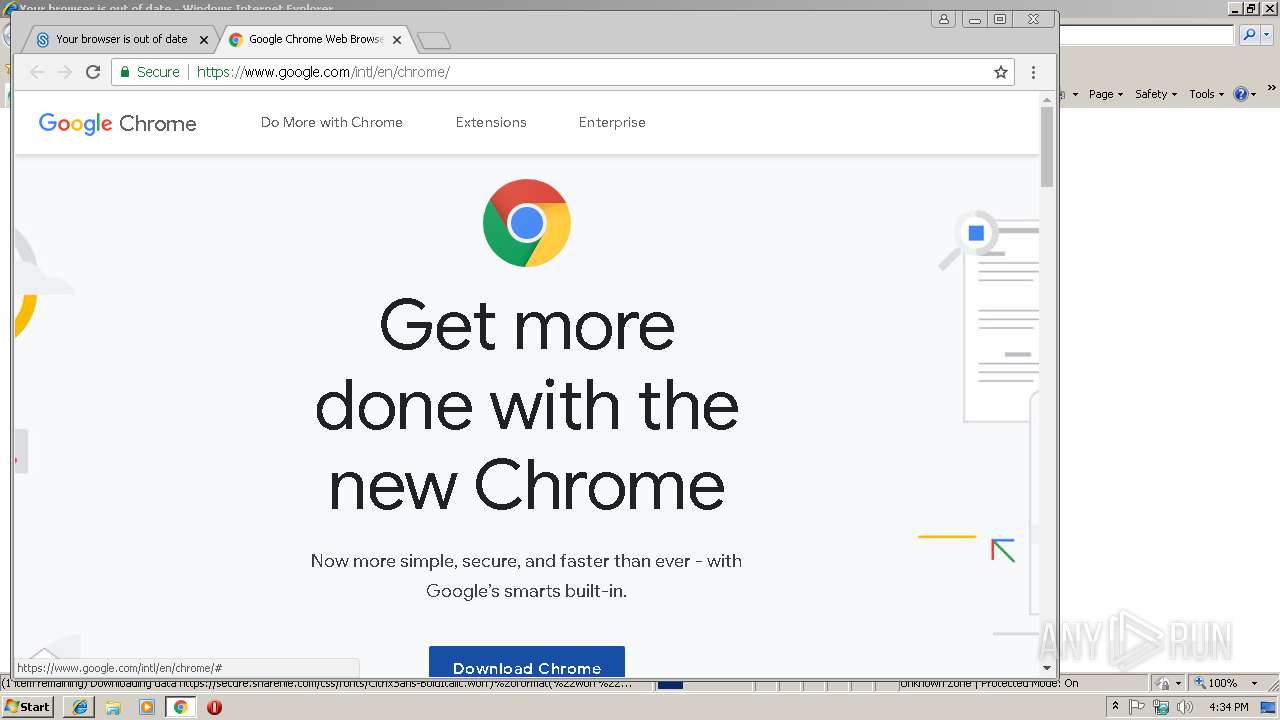
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 998297C33487AB45A4C38B84EC3B871A |
| SHA1: | 1804929EB9FBF9F5D41D49B256DE7B9D06A6EC8C |
| SHA256: | DB2FB1ADCFD78967FC2067C136FF322A707F244648CC8464511200EB8F684E96 |
| SSDEEP: | 3:N8N3uKEL4kadfJROFn:2ZuKEL4xfI |
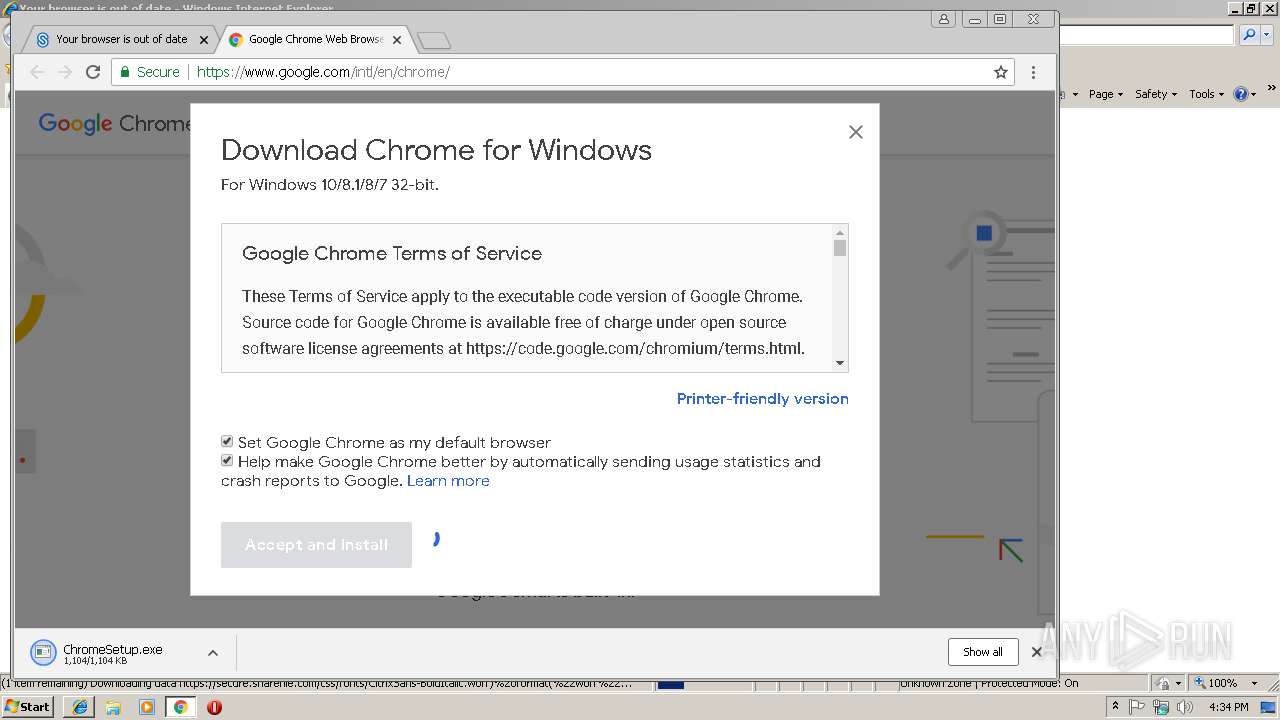
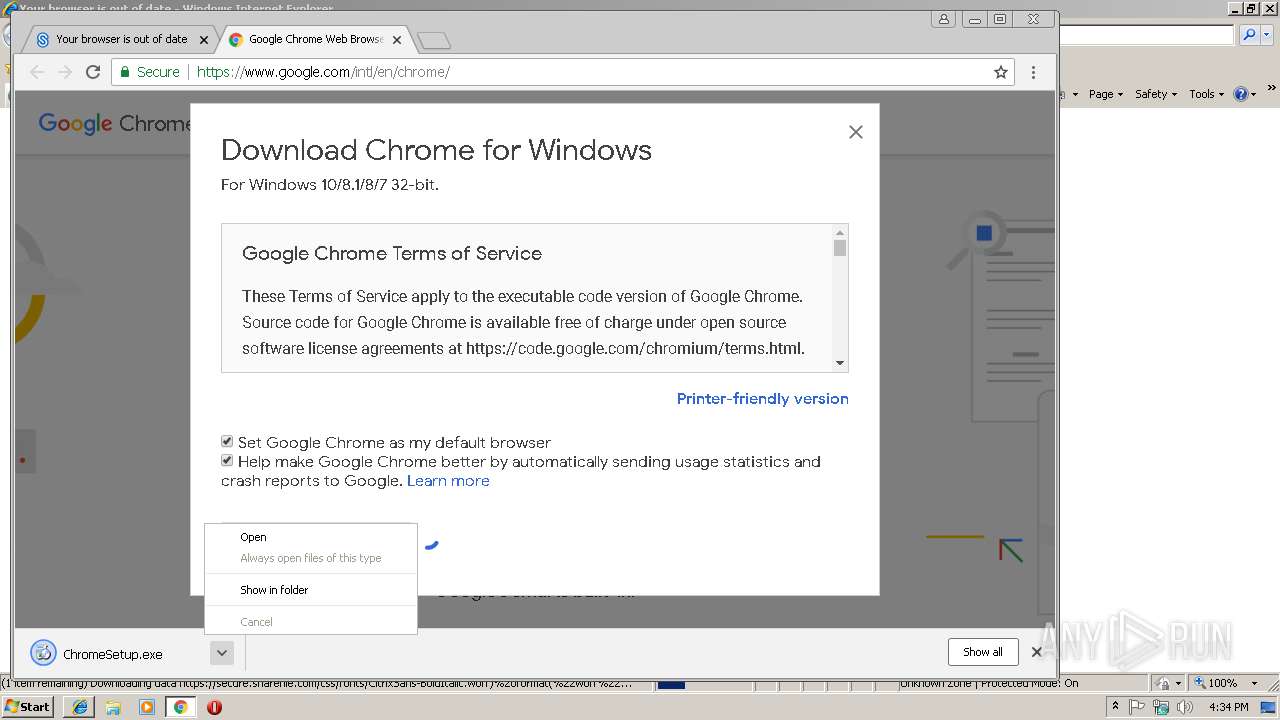
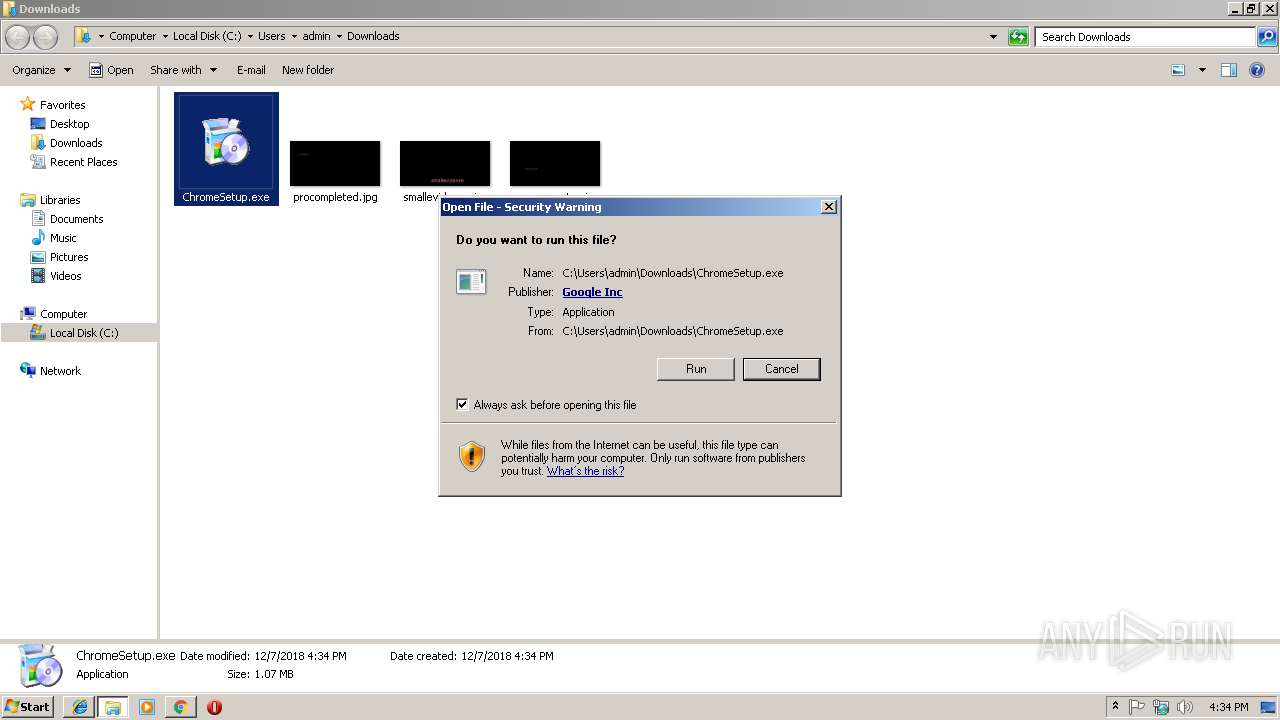
MALICIOUS
Application was dropped or rewritten from another process
- ChromeSetup.exe (PID: 3044)
- GoogleUpdate.exe (PID: 4084)
- GoogleUpdateSetup.exe (PID: 960)
- GoogleUpdate.exe (PID: 2244)
- GoogleUpdate.exe (PID: 2892)
- GoogleUpdate.exe (PID: 3664)
- GoogleUpdate.exe (PID: 3928)
- GoogleUpdate.exe (PID: 2656)
- GoogleUpdate.exe (PID: 3388)
Loads dropped or rewritten executable
- GoogleUpdate.exe (PID: 4084)
- GoogleUpdate.exe (PID: 2244)
- GoogleUpdate.exe (PID: 3388)
- GoogleUpdate.exe (PID: 2892)
- GoogleUpdate.exe (PID: 2656)
- GoogleUpdate.exe (PID: 3664)
- GoogleUpdate.exe (PID: 3928)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 3664)
Loads the Task Scheduler COM API
- GoogleUpdate.exe (PID: 2244)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2040)
- ChromeSetup.exe (PID: 3044)
- GoogleUpdateSetup.exe (PID: 960)
- GoogleUpdate.exe (PID: 2244)
Creates files in the program directory
- GoogleUpdate.exe (PID: 2244)
- GoogleUpdateSetup.exe (PID: 960)
Disables SEHOP
- GoogleUpdate.exe (PID: 2244)
Starts itself from another location
- GoogleUpdate.exe (PID: 2244)
Creates COM task schedule object
- GoogleUpdate.exe (PID: 2892)
- GoogleUpdate.exe (PID: 2244)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 3664)
INFO
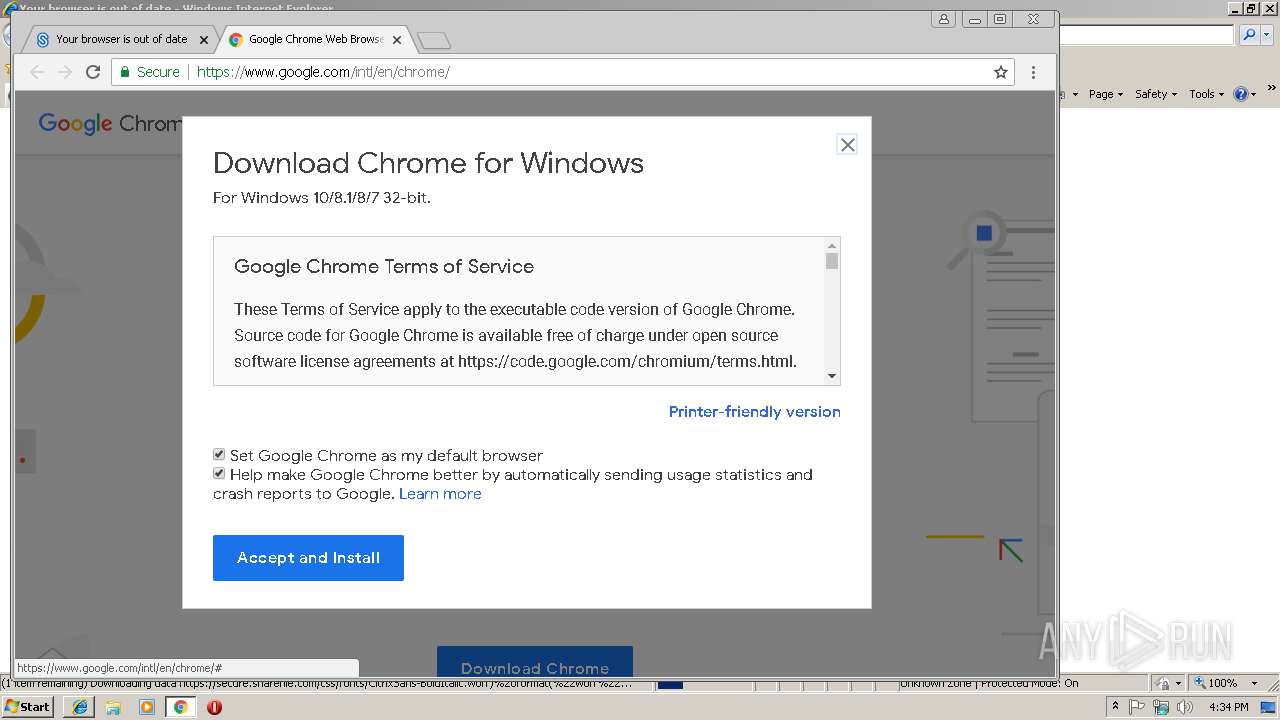
Changes internet zones settings
- iexplore.exe (PID: 2952)
Reads internet explorer settings
- iexplore.exe (PID: 3104)
Reads Internet Cache Settings
- iexplore.exe (PID: 3104)
- chrome.exe (PID: 2040)
Reads settings of System Certificates
- iexplore.exe (PID: 2952)
Changes settings of System certificates
- iexplore.exe (PID: 2952)
Application launched itself
- chrome.exe (PID: 2040)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
20
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Users\admin\AppData\Local\Temp\GUM13A3.tmp\GoogleUpdateSetup.exe" /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={C08897CA-BB69-3E45-7C81-486F97CE1257}&lang=en&browser=4&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=stable-arch_x86-statsdef_1&installdataindex=defaultbrowser" /installelevated /nomitag | C:\Users\admin\AppData\Local\Temp\GUM13A3.tmp\GoogleUpdateSetup.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Update Setup Exit code: 0 Version: 1.3.33.17 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11167965423439855814,3112671678446753900,131072 --enable-features=PasswordImport --service-pipe-token=CA9591B74EE2B16DEEC9A374406F301E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CA9591B74EE2B16DEEC9A374406F301E --renderer-client-id=5 --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\GUM1B06.tmp\GoogleUpdate.exe" /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={C08897CA-BB69-3E45-7C81-486F97CE1257}&lang=en&browser=4&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=stable-arch_x86-statsdef_1&installdataindex=defaultbrowser" /installelevated | C:\Program Files\GUM1B06.tmp\GoogleUpdate.exe | GoogleUpdateSetup.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.17 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2140 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /svc | C:\Program Files\Google\Update\GoogleUpdate.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.33.17 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /regserver | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.17 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6dc100b0,0x6dc100c0,0x6dc100cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11167965423439855814,3112671678446753900,131072 --enable-features=PasswordImport --service-pipe-token=2BBCEA363D50BC65252EBA7412612F68 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2BBCEA363D50BC65252EBA7412612F68 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 332
Read events
1 382
Write events
832
Delete events
118
Modification events
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {DA252D81-FA3D-11E8-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C00050007001000210029002800 | |||
Executable files
149
Suspicious files
54
Text files
72
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\010a0cd0-6825-4529-8f70-419885736844.tmp | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3104 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\fonts[1].css | text | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9e668643-0147-4661-a361-d2ebfd5a6d13.tmp | — | |
MD5:— | SHA256:— | |||
| 3104 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\upgradebrowser[1].html | html | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
48
DNS requests
29
Threats
984
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 173.194.76.198:80 | http://redirector.gvt1.com/edgedl/release2/chrome/W4tpFcs0b30_71.0.3578.80/71.0.3578.80_chrome_installer.exe | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.183.72:80 | http://r3---sn-aigl6ned.gvt1.com/edgedl/release2/chrome/W4tpFcs0b30_71.0.3578.80/71.0.3578.80_chrome_installer.exe?cms_redirect=yes&mip=78.129.233.77&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1544200135&mv=u&pl=24&shardbypass=yes | US | — | — | whitelisted |
— | — | GET | — | 173.194.183.72:80 | http://r3---sn-aigl6ned.gvt1.com/edgedl/release2/chrome/W4tpFcs0b30_71.0.3578.80/71.0.3578.80_chrome_installer.exe?cms_redirect=yes&mip=78.129.233.77&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1544200135&mv=u&pl=24&shardbypass=yes | US | — | — | whitelisted |
2952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2040 | chrome.exe | 216.58.205.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 52.22.72.157:443 | secure.sharefile.com | Amazon.com, Inc. | US | unknown |
2040 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.22.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 108.177.126.198:443 | s.ytimg.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 173.194.76.198:443 | www.youtube.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.22.6:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.21.194:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.22.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
secure.sharefile.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2040 | chrome.exe | unknown | SURICATA TCPv4 invalid checksum |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
— | — | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
— | — | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |