| File name: | skype.exe |
| Full analysis: | https://app.any.run/tasks/ebefdcf9-c1f8-41af-955b-72d50032f0a1 |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2021, 03:37:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | D11743B11A65AB7CA9A61913151BAC40 |
| SHA1: | 42E182D0CD1D3BB2F055BE55ABE880C675BA9DAD |
| SHA256: | DB27FD09303A4B73F0635E779269C53938425B7F631345B5F2A96739F2185DF7 |
| SSDEEP: | 98304:t+8Pf8XRAAvTAAkfNvuIVqSR3QH4ewSxepreCQz1p/k6QAM6dBZHtmAqw23jGou:MJWOTAAkNHVq2xWD1p/kzduBJtIbV |
MALICIOUS
Loads dropped or rewritten executable
- skype.exe (PID: 3296)
Drops executable file immediately after starts
- skype.exe (PID: 1904)
SUSPICIOUS
Drops a file with too old compile date
- skype.exe (PID: 1904)
Executable content was dropped or overwritten
- skype.exe (PID: 1904)
Drops a file with a compile date too recent
- skype.exe (PID: 1904)
Drops a file that was compiled in debug mode
- skype.exe (PID: 1904)
Application launched itself
- skype.exe (PID: 1904)
Loads Python modules
- skype.exe (PID: 3296)
INFO
Dropped object may contain Bitcoin addresses
- skype.exe (PID: 1904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:08 14:29:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 116736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x781a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Aug-2020 12:29:54 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 08-Aug-2020 12:29:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F274 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65656 |
.rdata | 0x00021000 | 0x0000B386 | 0x0000B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.1121 |
.data | 0x0002D000 | 0x0000A668 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93189 |
.gfids | 0x00038000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82045 |
.rsrc | 0x00039000 | 0x0000EF6C | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.3503 |
.reloc | 0x00048000 | 0x000017FC | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6693 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27386 | 1263 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.05629 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
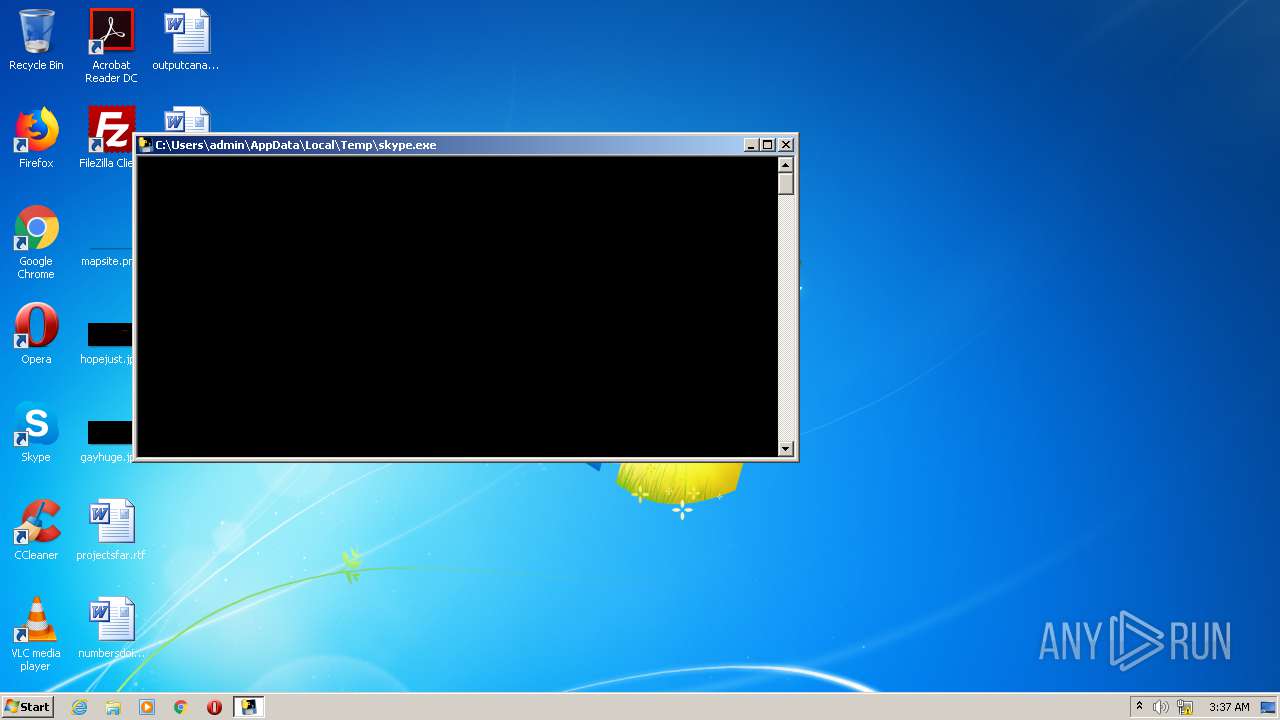
| 1904 | "C:\Users\admin\AppData\Local\Temp\skype.exe" | C:\Users\admin\AppData\Local\Temp\skype.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\skype.exe" | C:\Users\admin\AppData\Local\Temp\skype.exe | skype.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
9
Read events
9
Write events
0
Delete events
0
Modification events
Executable files
53
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_ssl.pyd | executable | |
MD5:2E2B2B0C18E5D897CA79A3BD70685233 | SHA256:98558E6F4FA2706F011B324721CEB884795549C1A863C8B46AF08F2B15CFDA5E | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_queue.pyd | executable | |
MD5:CB9F4B92F130B564767359A8DAC8D05B | SHA256:297A96DC95709034C4B802E25F769105F9EB4866B70991208C4BD8315171CAF6 | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_bz2.pyd | executable | |
MD5:754B62BE2DBAB2C25DC3DD65AAC9EBB2 | SHA256:15A8B8543A3A485321C310FC51531F2BAD14C8CB51B98C7B039A68FB34DE8DDA | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_ctypes.pyd | executable | |
MD5:3D63BFE259A091DEE1FF2B5A375FAE6B | SHA256:E740232C68E08DB0CFD3FE615817117CAA80BDEF5276C536D3CD22E9C18987C1 | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_hashlib.pyd | executable | |
MD5:CC867B685F9D4AB258437D86663E2839 | SHA256:4504720C2DFD09770D53BA71C8BA64D128B51284F3942A5964390416DE481D2F | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\_socket.pyd | executable | |
MD5:2C77EBD0C69DE8DC3FEEC3FF8A26A6BF | SHA256:A05BA444C837FB4D43174B6552FCAEFA2952AD31C620A3EAD9B001CE4BF7928A | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:E479444BDD4AE4577FD32314A68F5D28 | SHA256:C85DC081B1964B77D289AAC43CC64746E7B141D036F248A731601EB98F827719 | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:D97A1CB141C6806F0101A5ED2673A63D | SHA256:DECCD75FC3FC2BB31338B6FE26DEFFBD7914C6CD6A907E76FD4931B7D141718C | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CB978304B79EF53962408C611DFB20F5 | SHA256:90FAE0E7C3644A6754833C42B0AC39B6F23859F9A7CF4B6C8624820F59B9DAD3 | |||
| 1904 | skype.exe | C:\Users\admin\AppData\Local\Temp\_MEI19042\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:E2F648AE40D234A3892E1455B4DBBE05 | SHA256:C8C499B012D0D63B7AFC8B4CA42D6D996B2FCF2E8B5F94CACFBEC9E6F33E8A03 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report