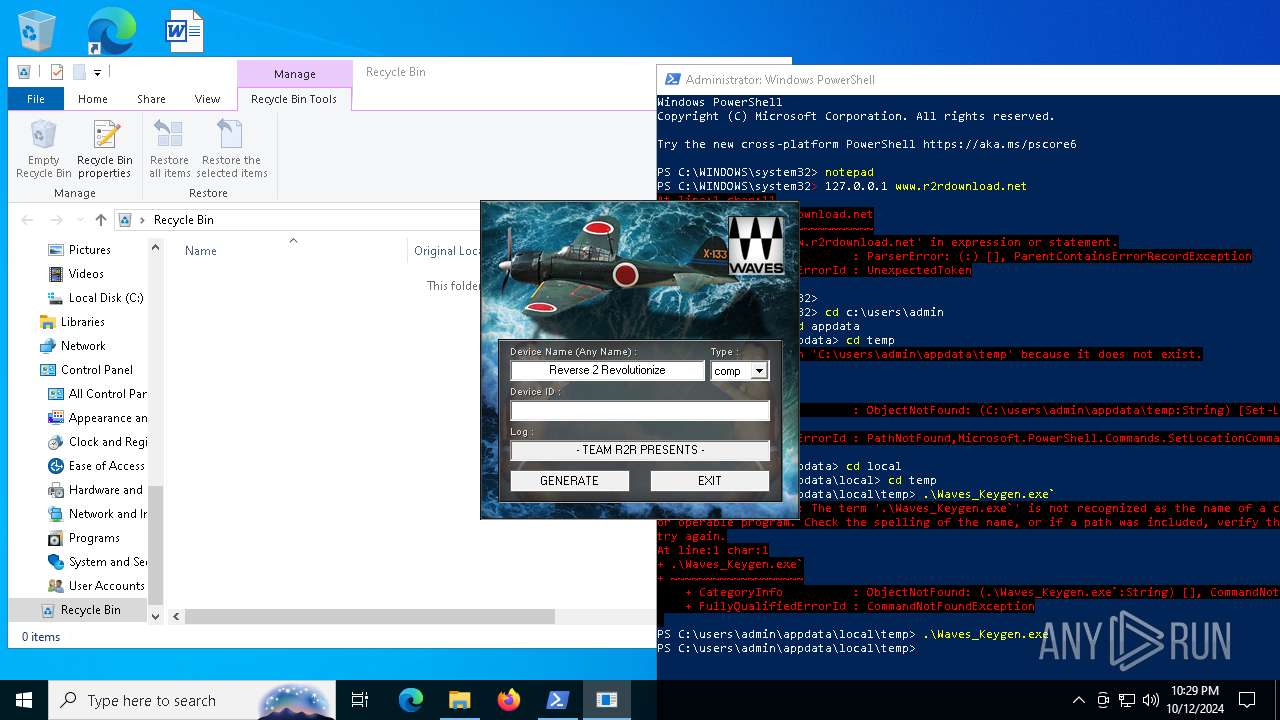
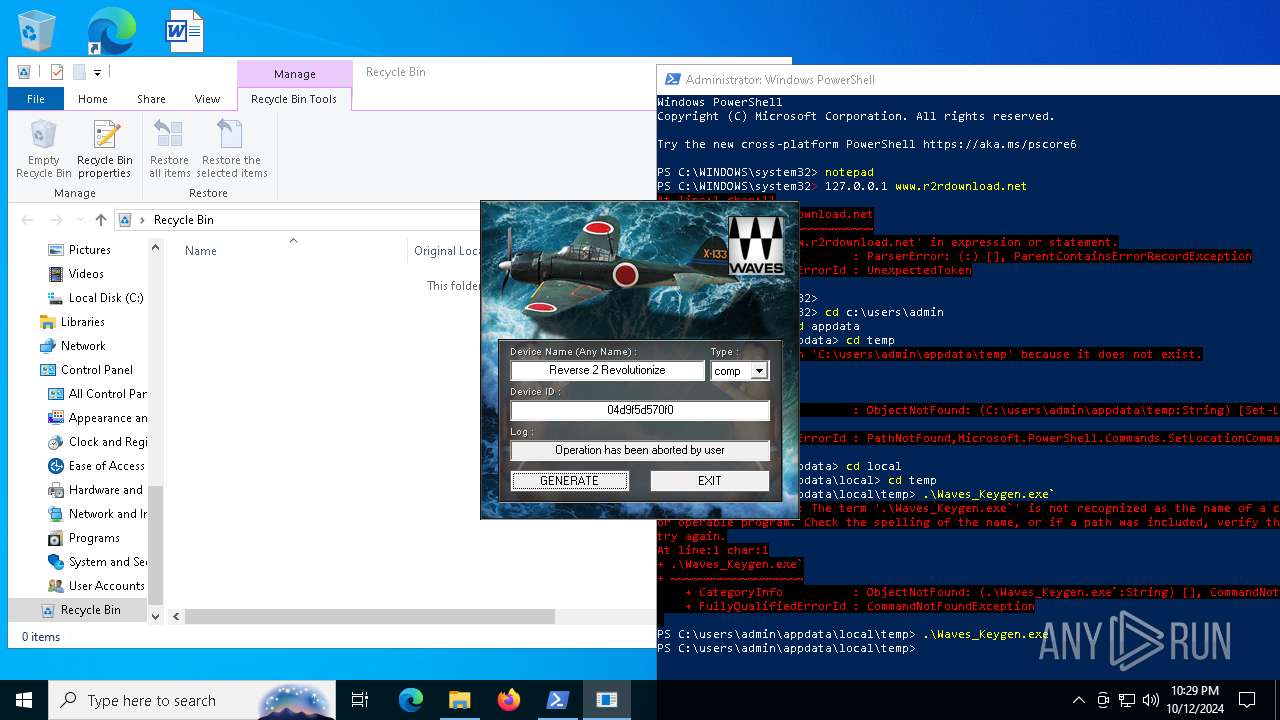
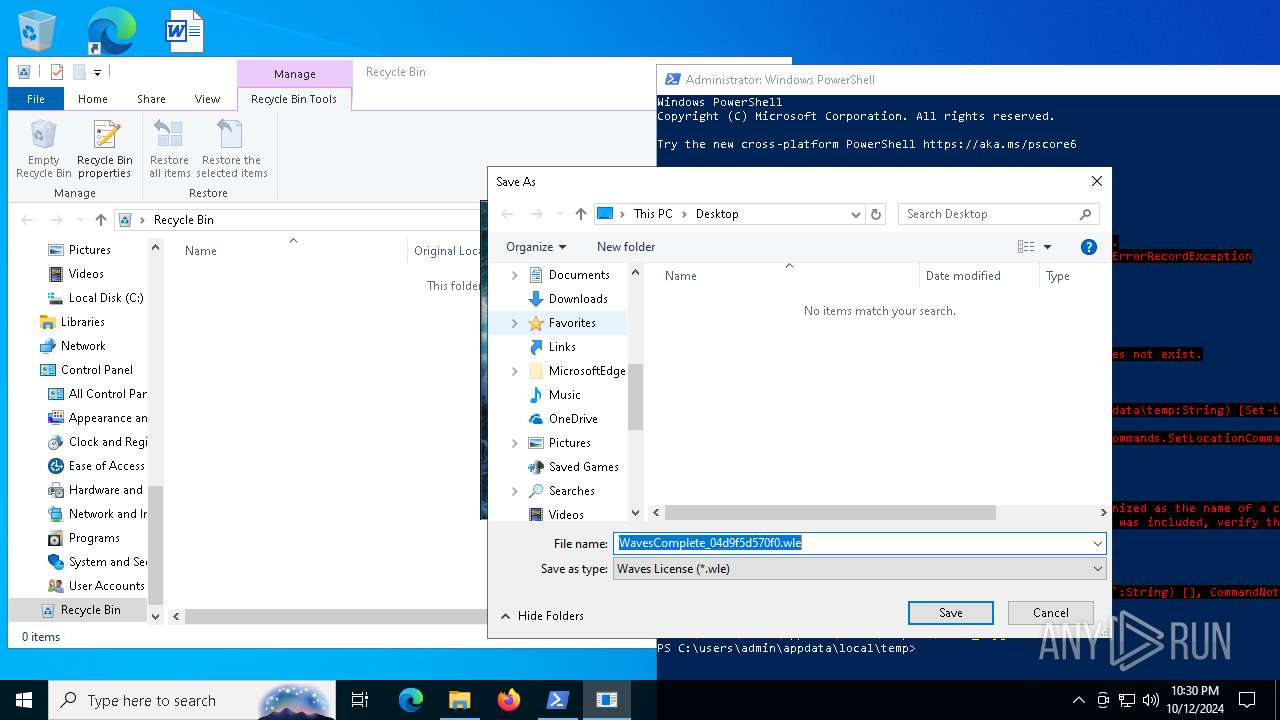
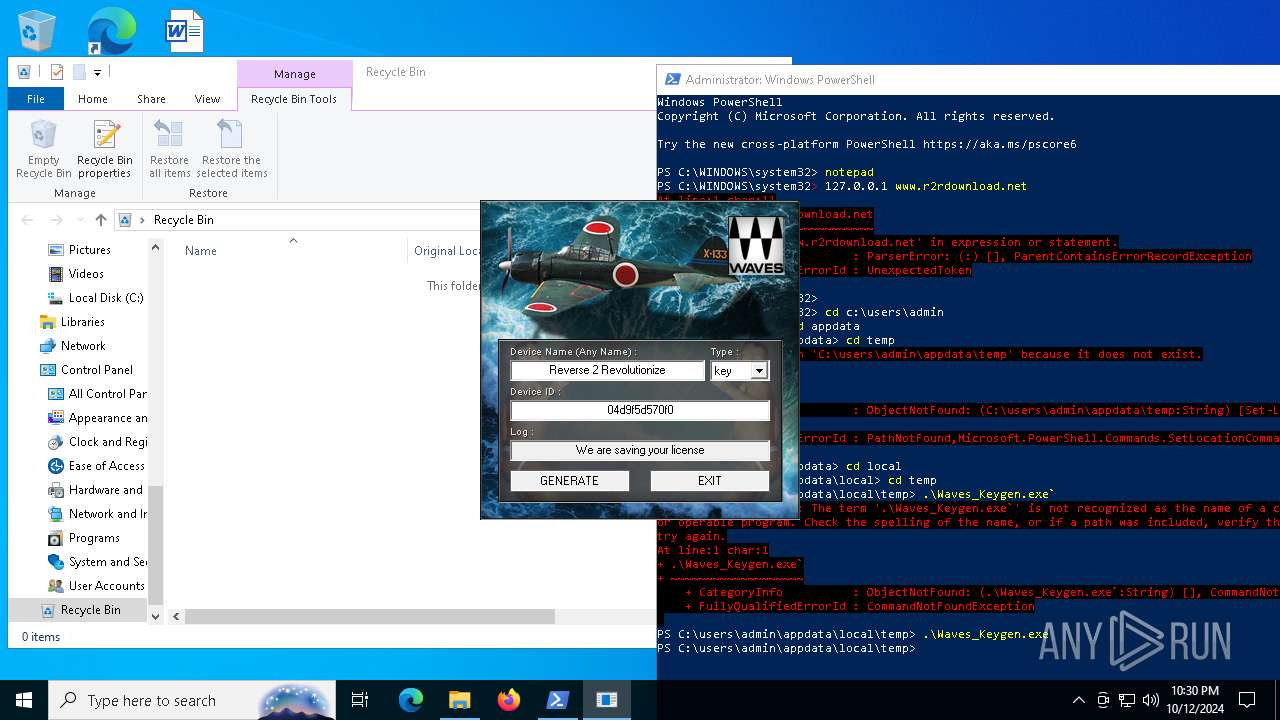
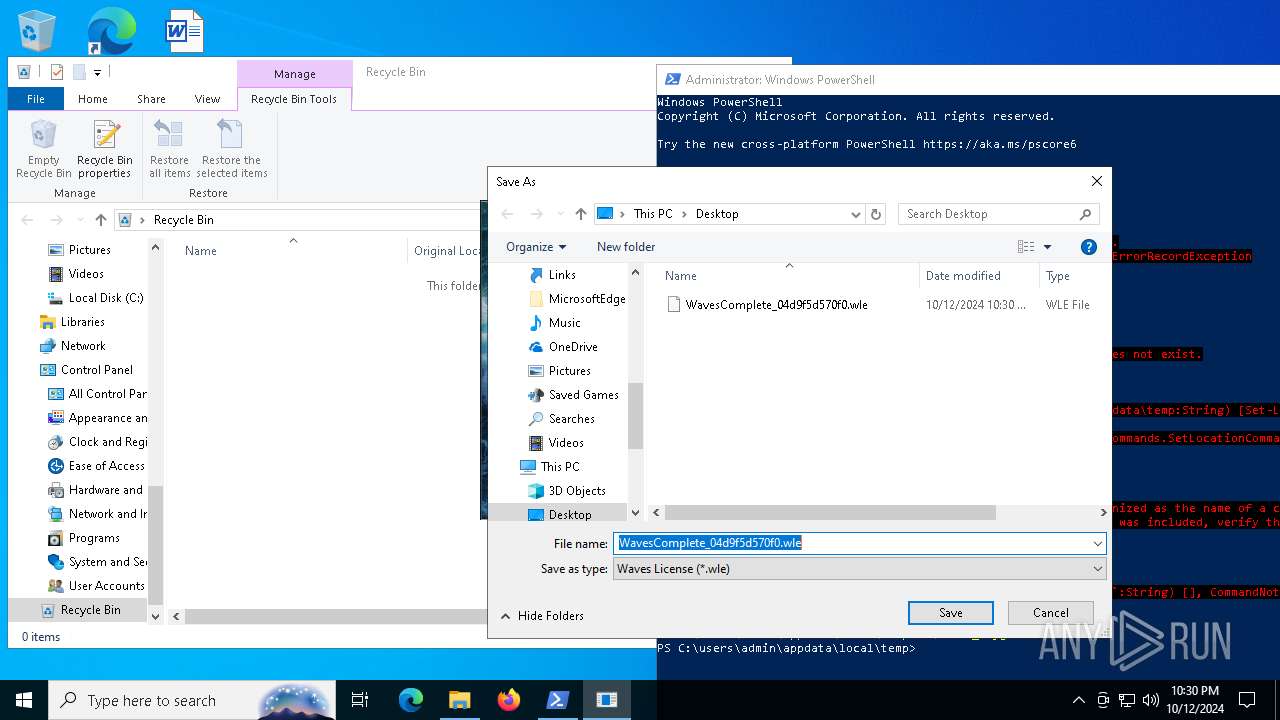
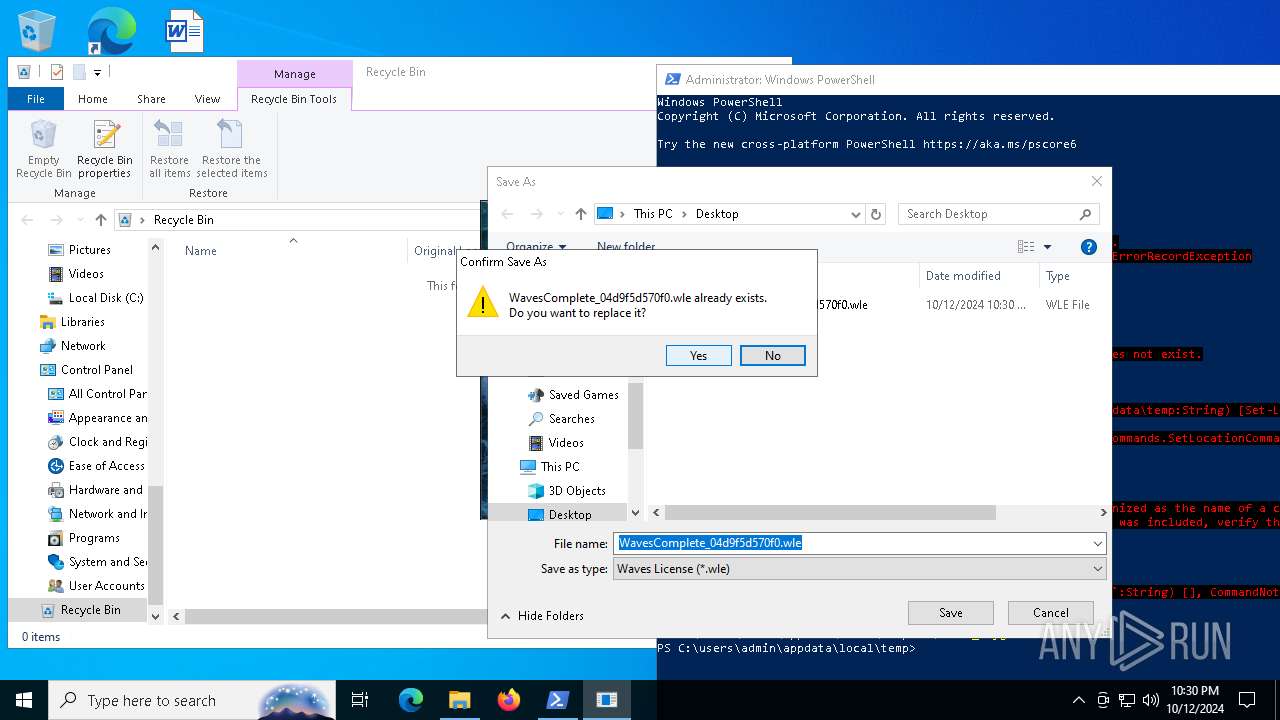
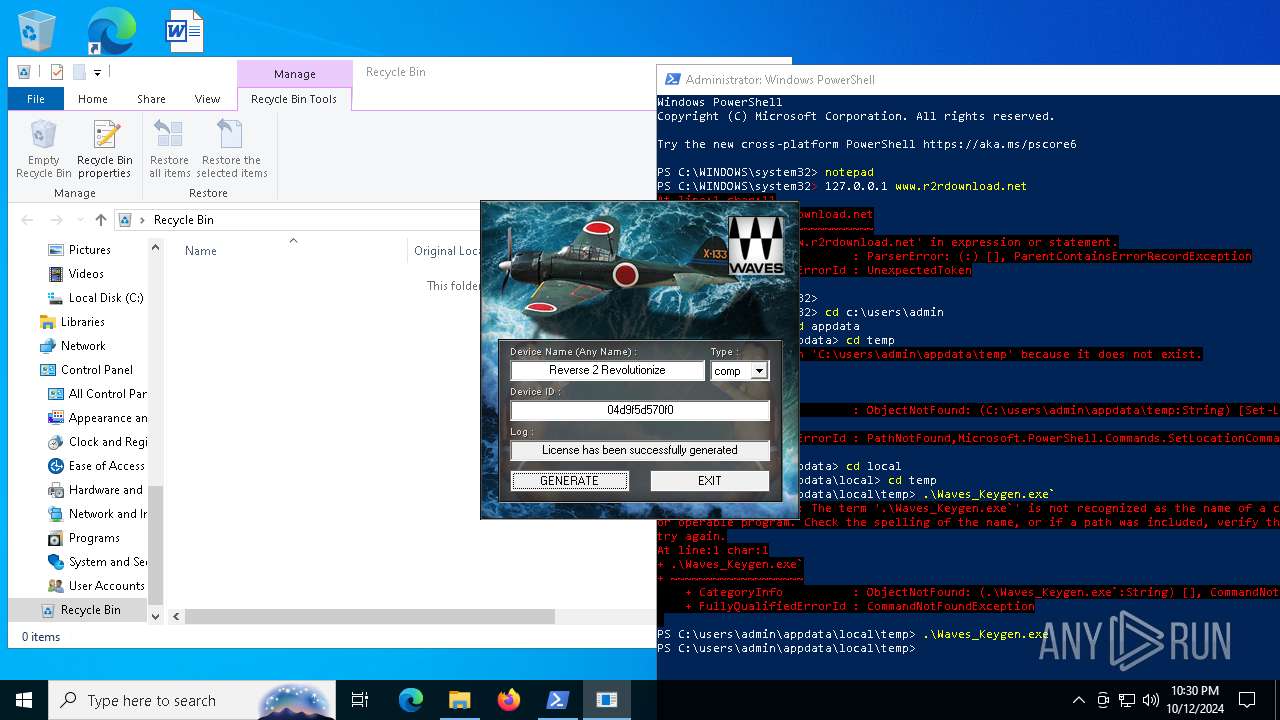
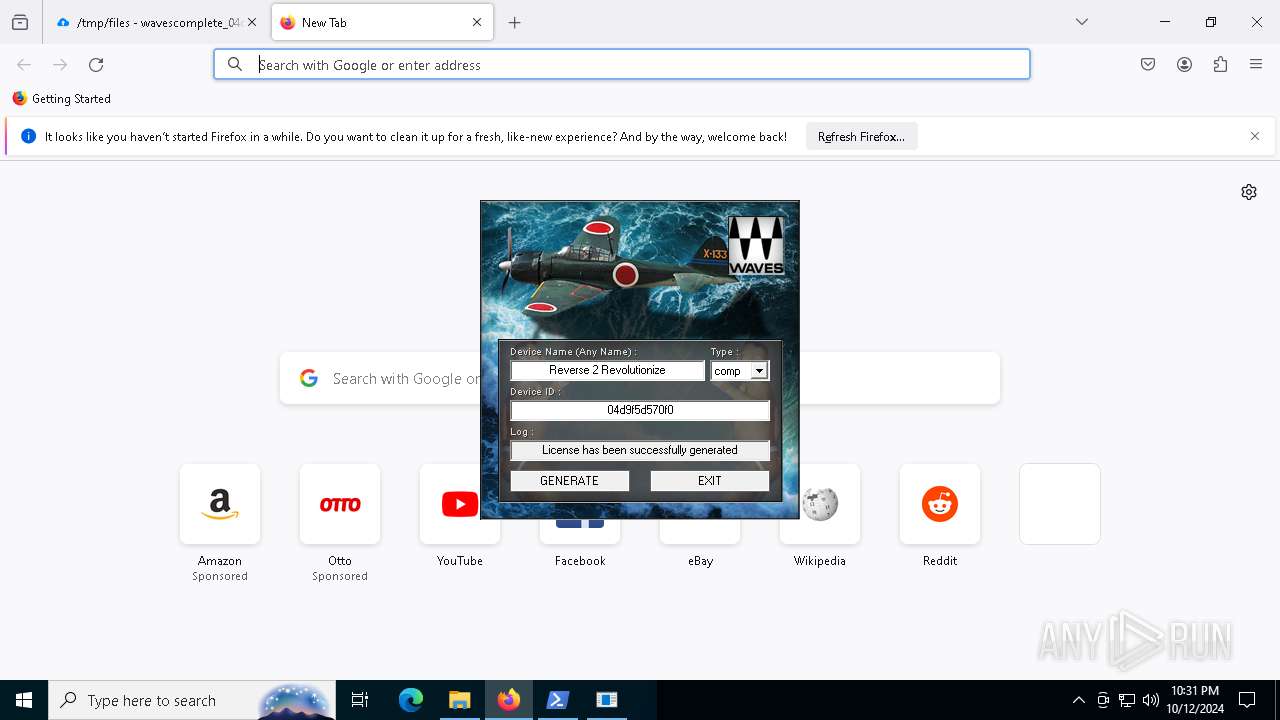
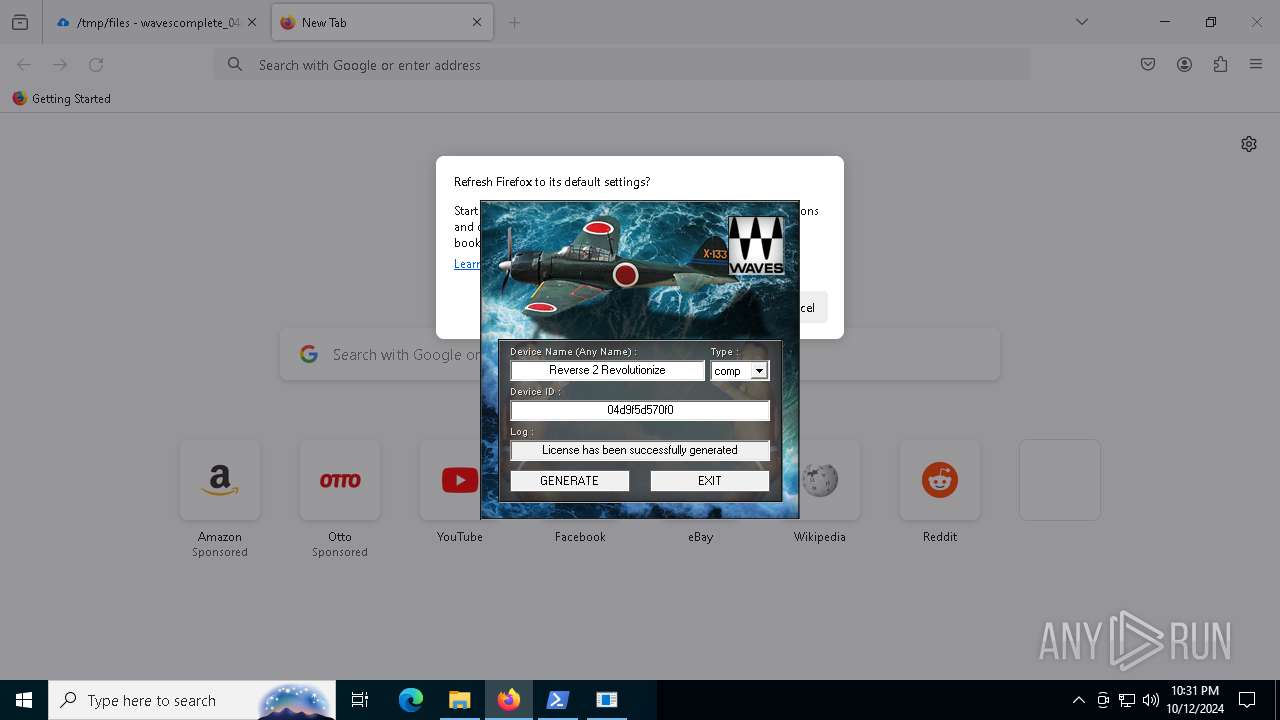
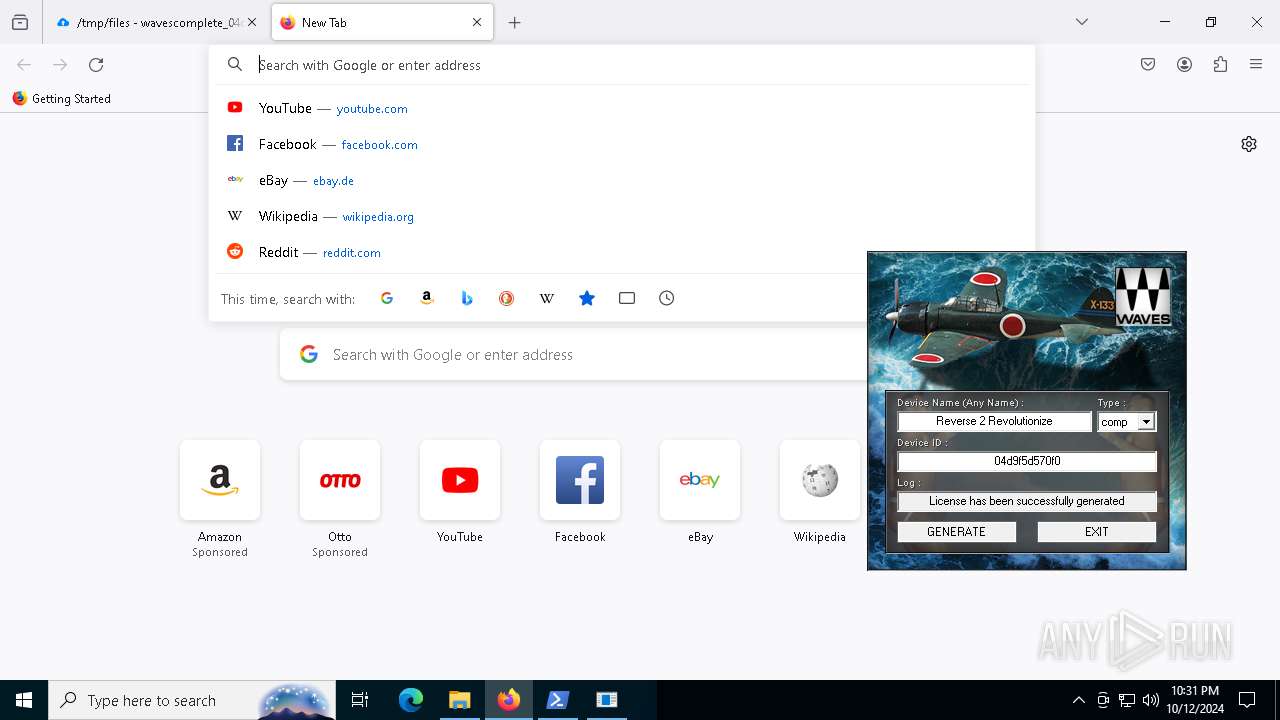
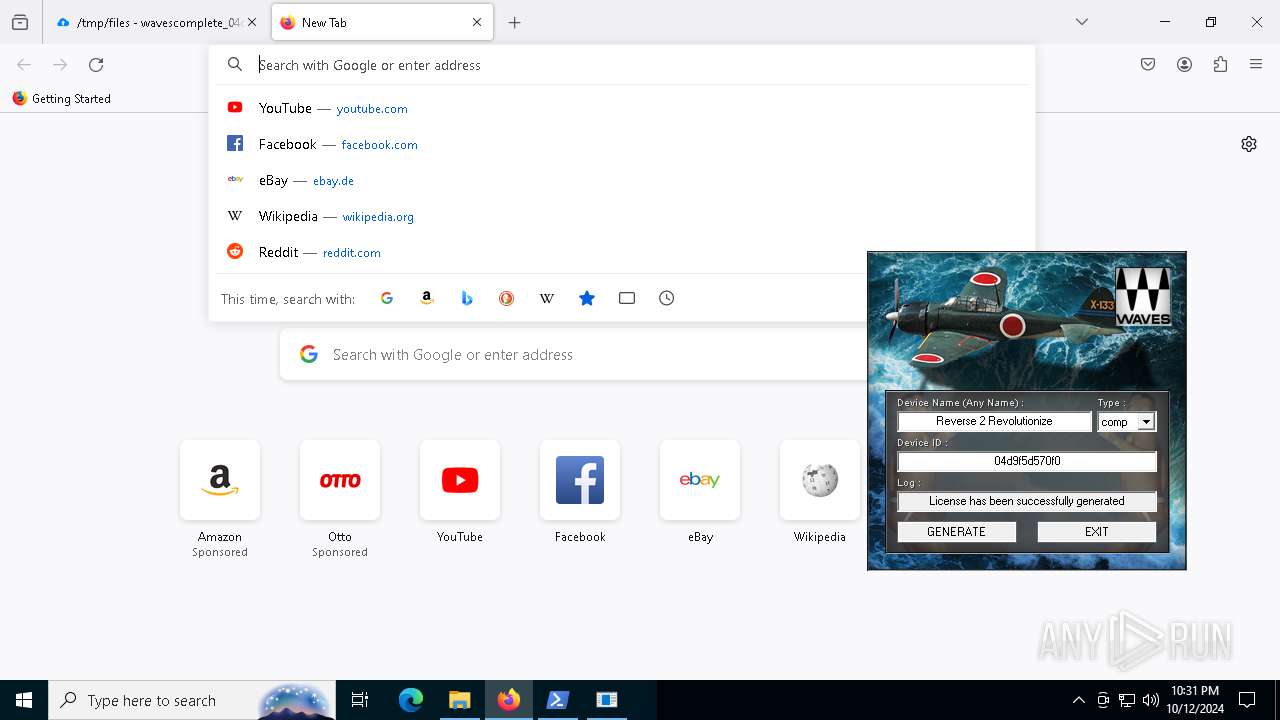
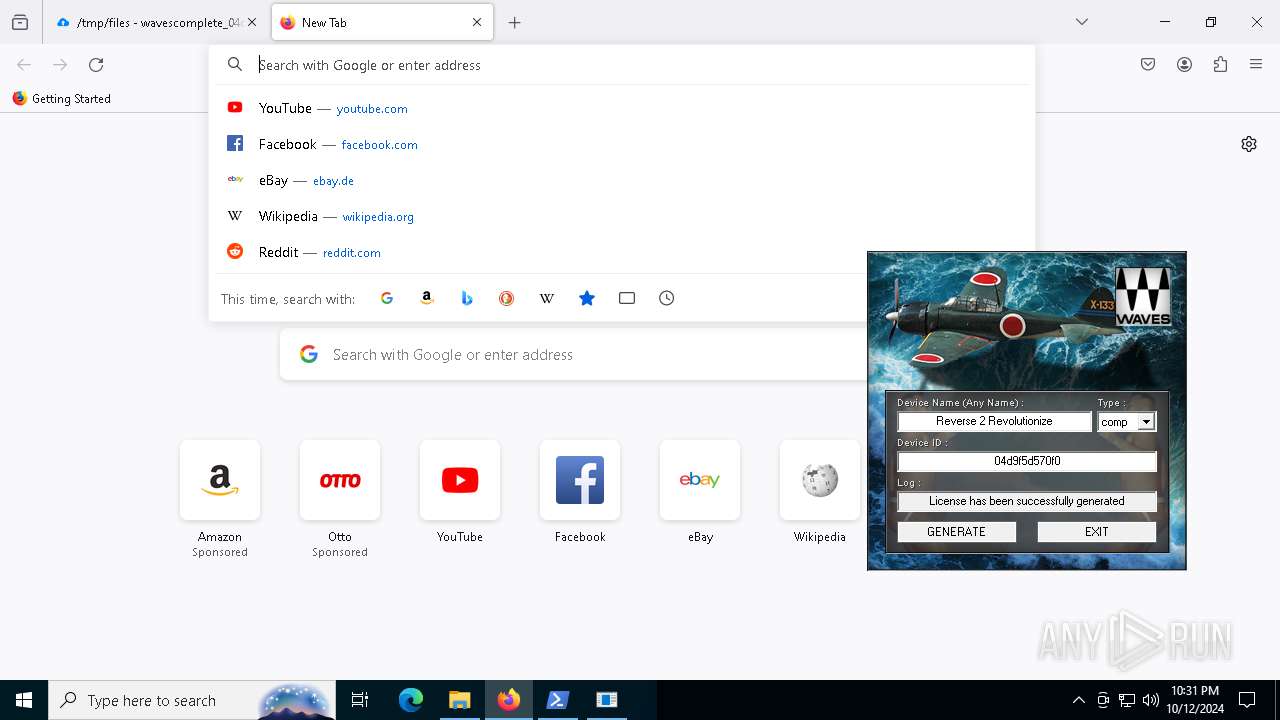
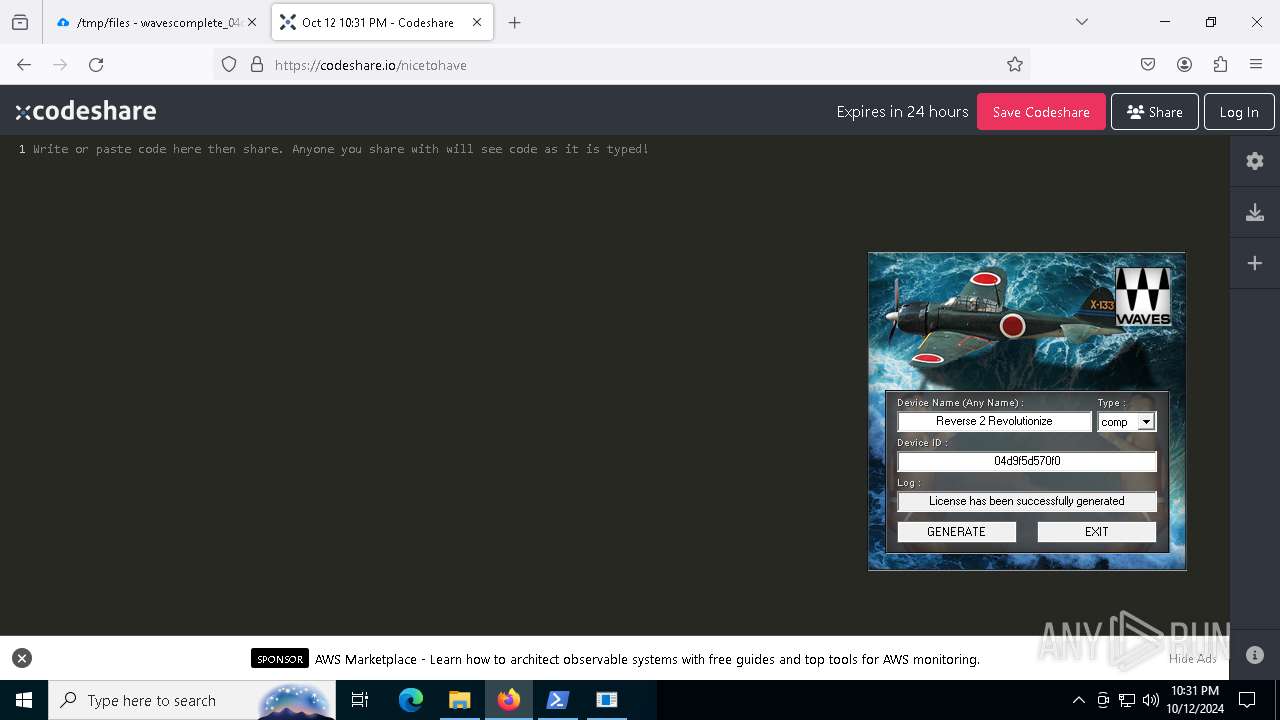
| File name: | Waves_Keygen.exe |
| Full analysis: | https://app.any.run/tasks/0a63a0da-e420-4cc3-af60-4a41f15c602d |
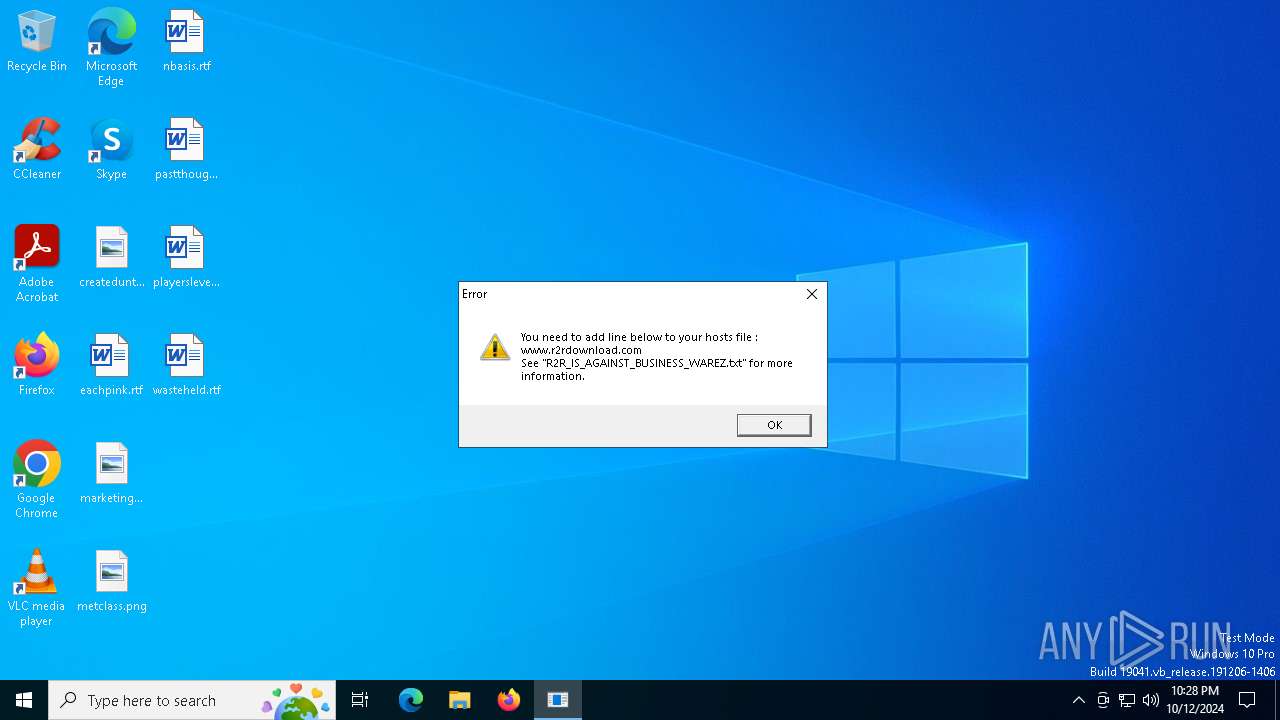
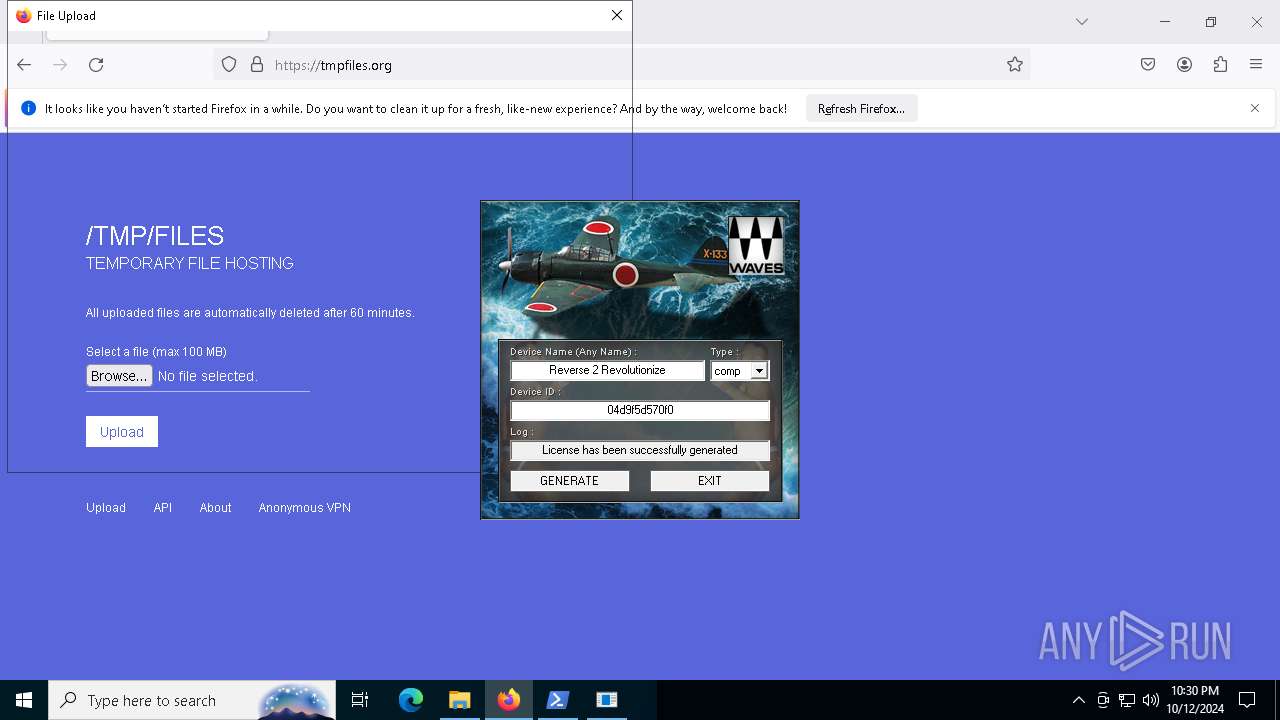
| Verdict: | Malicious activity |
| Analysis date: | October 12, 2024, 22:27:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 668CB4E7EBF1E012EDE87825F73FBDB3 |
| SHA1: | 6C48B5BC4681F3D9D0CD0C2E5C95D81FF14D095F |
| SHA256: | DB23FA2E60FA2850A17BF7DBDA6700CCDDEA7FB9908B98D23018F6CBF2425740 |
| SSDEEP: | 49152:gD8deEVoaMo0q/VQKYL/EzwIuW/aHPc/Z6fOb7YBVHRZ0CZXvpxtowRwZyfivk9y:gwoaSq/2KyczwsGPtOb7Y/HRZvZXvTkp |
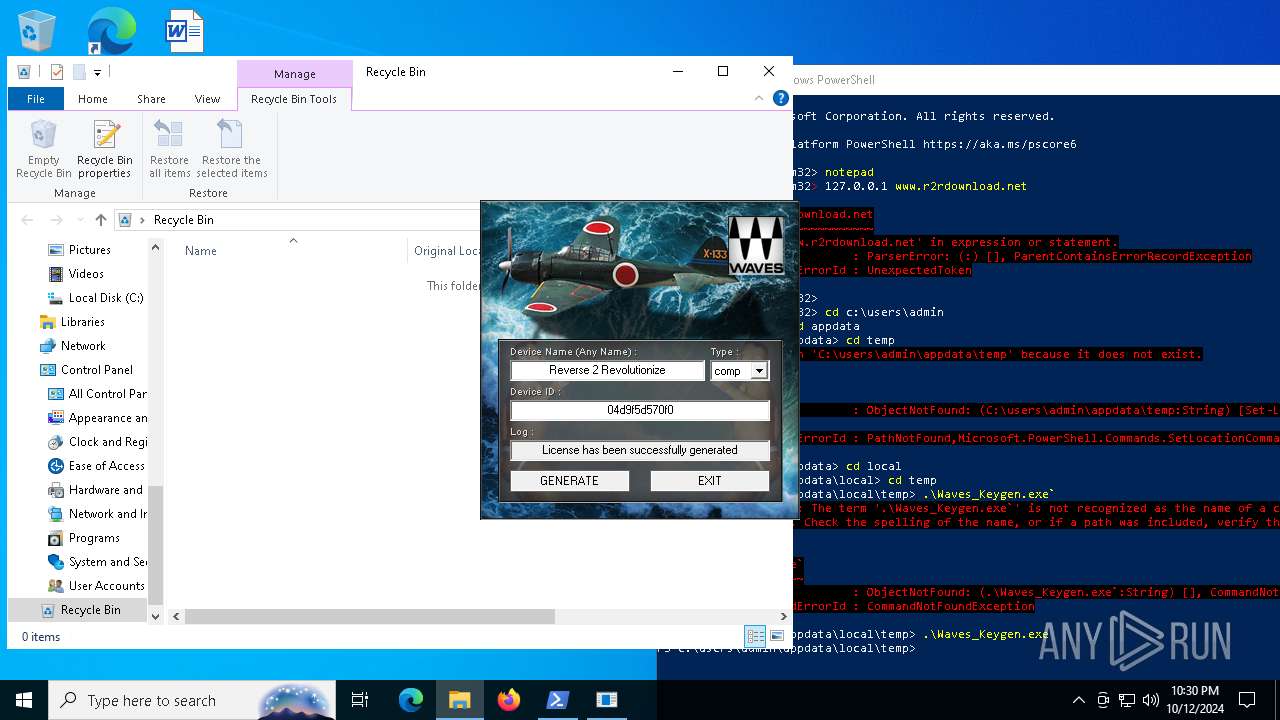
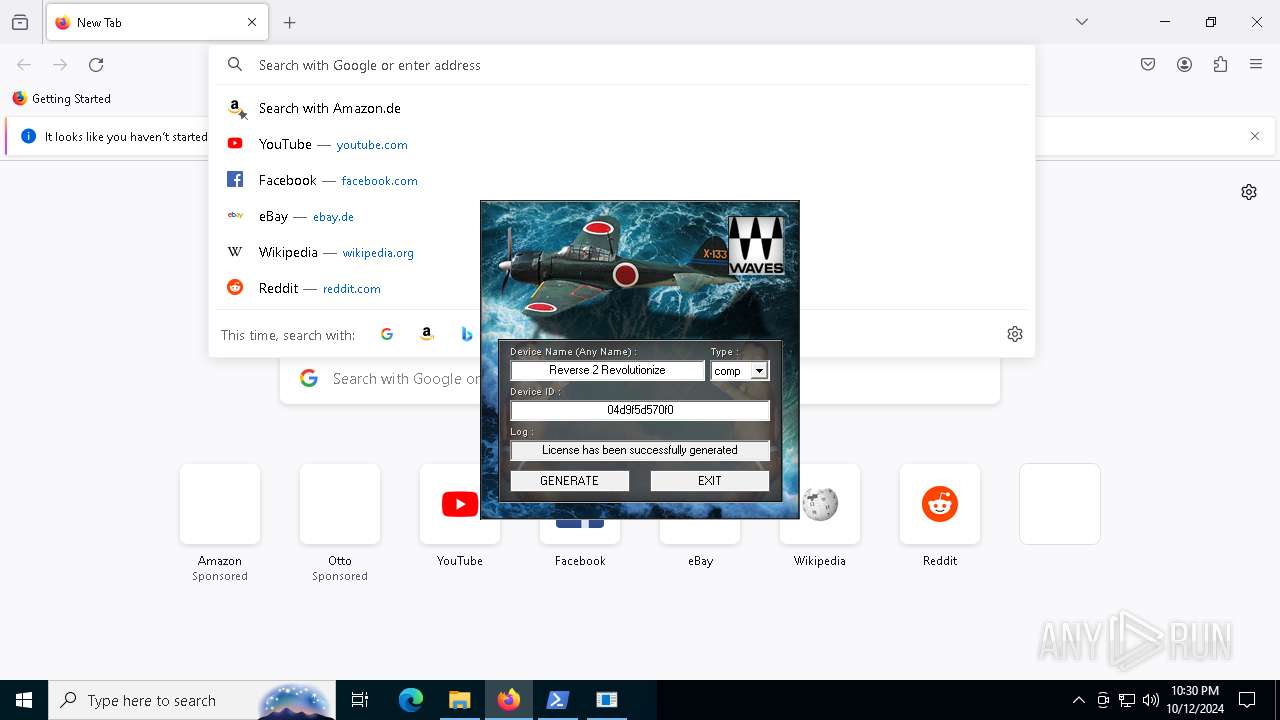
MALICIOUS
No malicious indicators.SUSPICIOUS
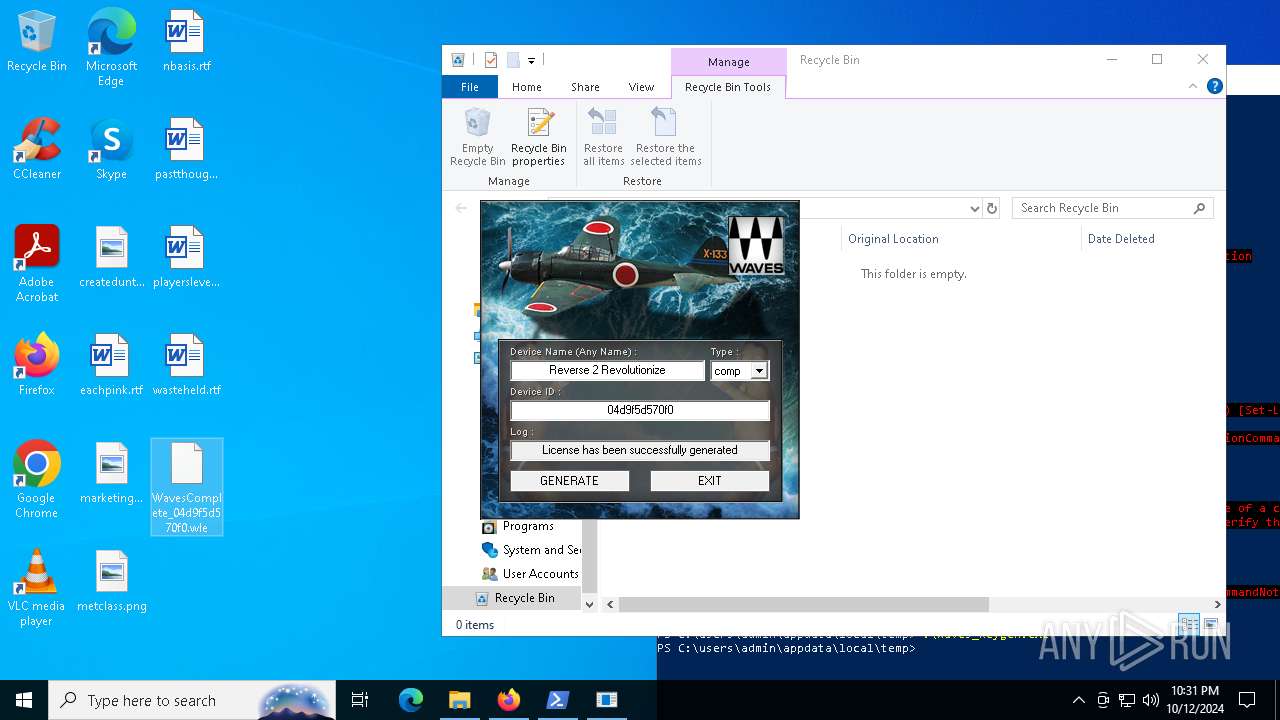
Executable content was dropped or overwritten
- Waves_Keygen.exe (PID: 6216)
- Waves_Keygen.exe (PID: 3824)
INFO
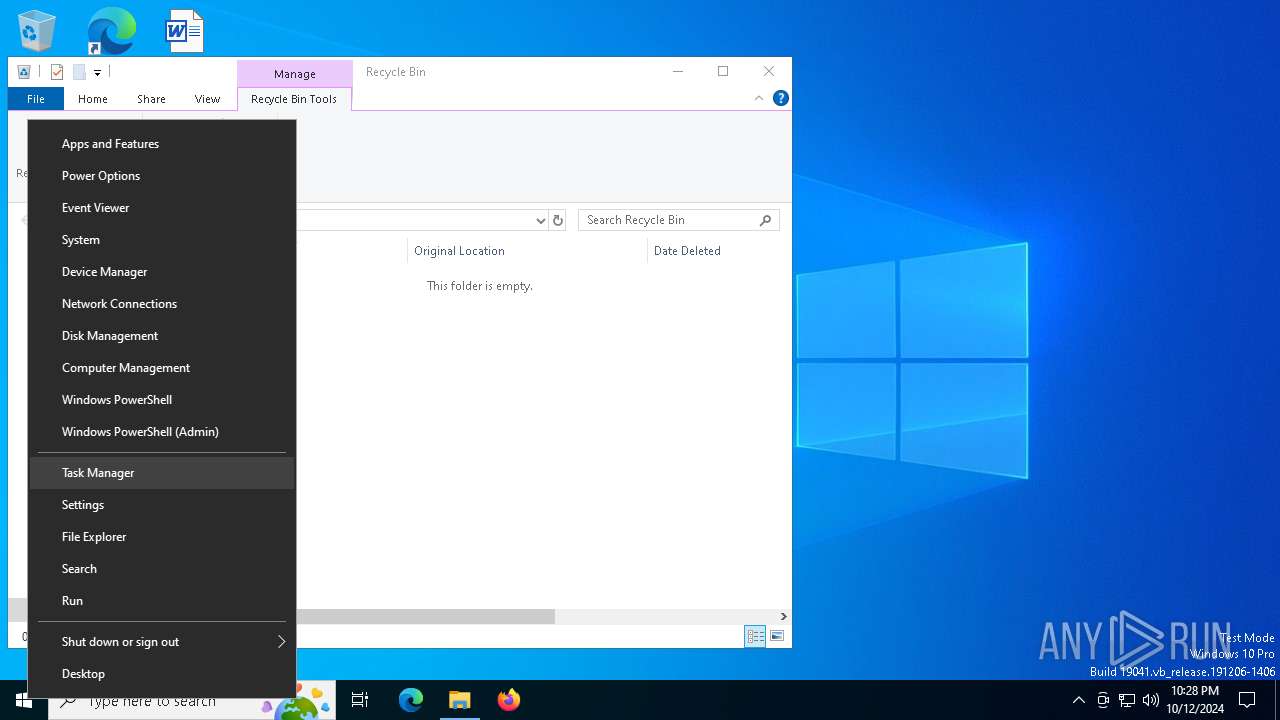
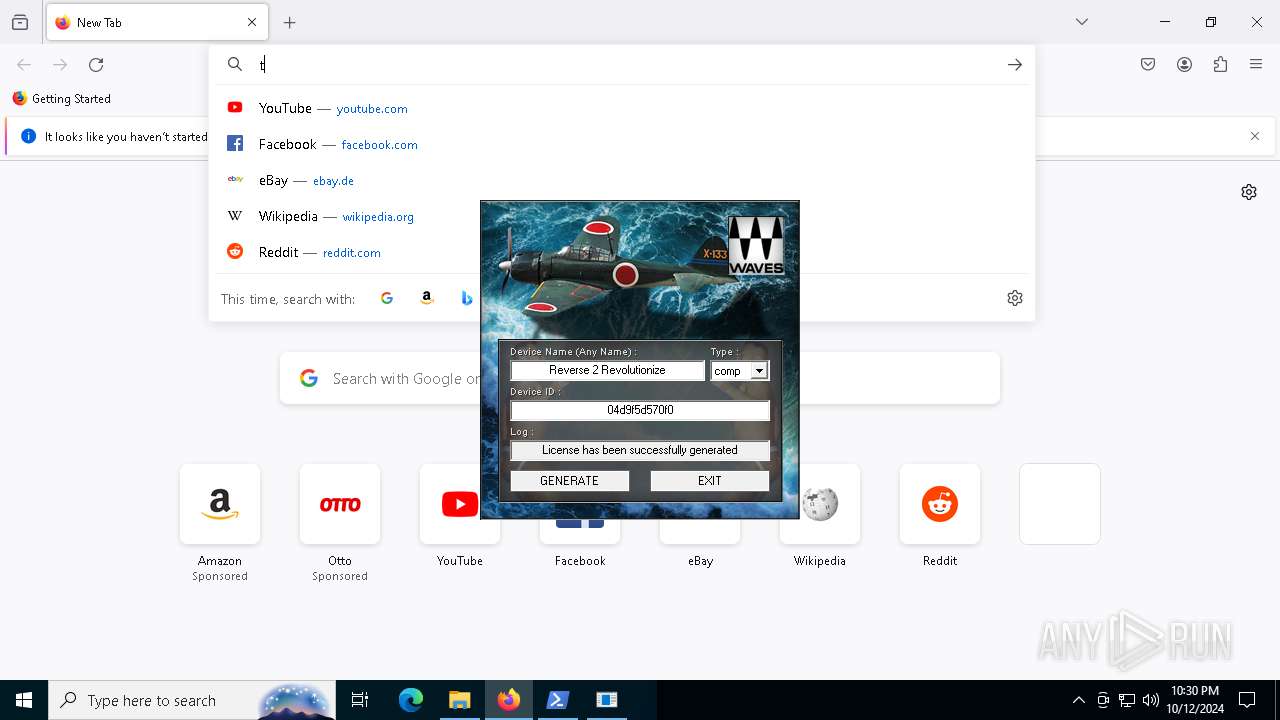
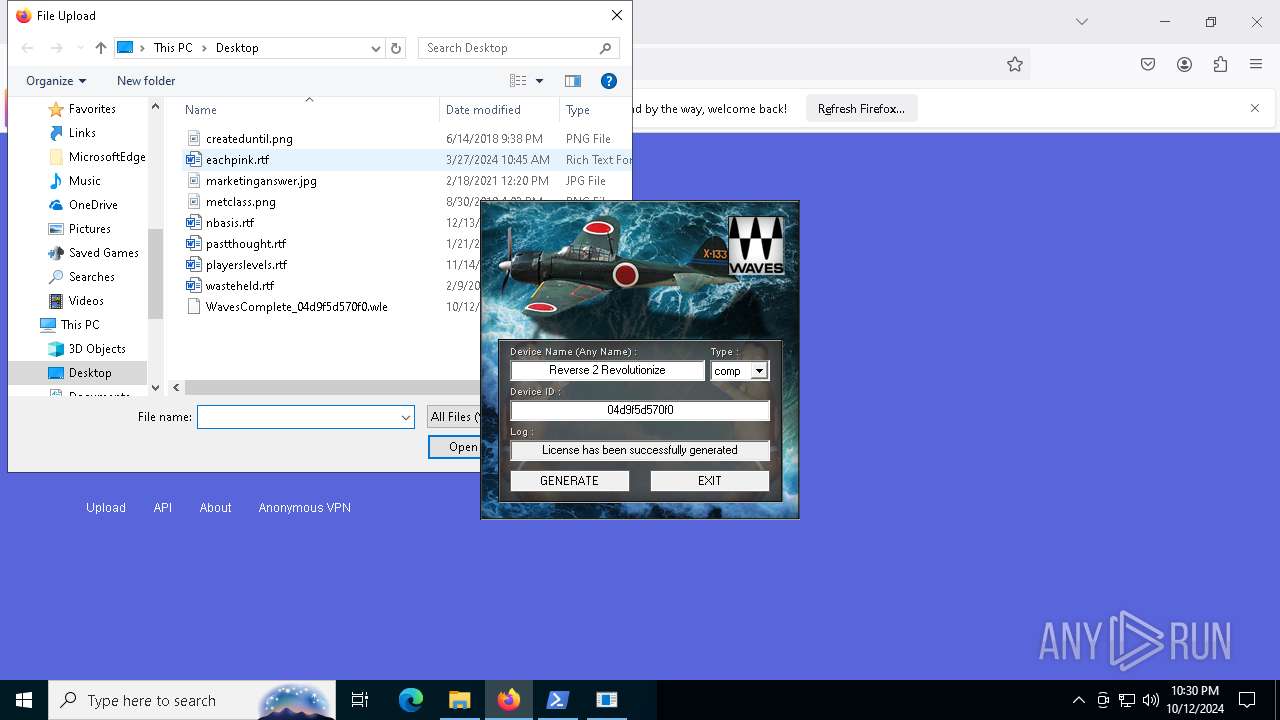
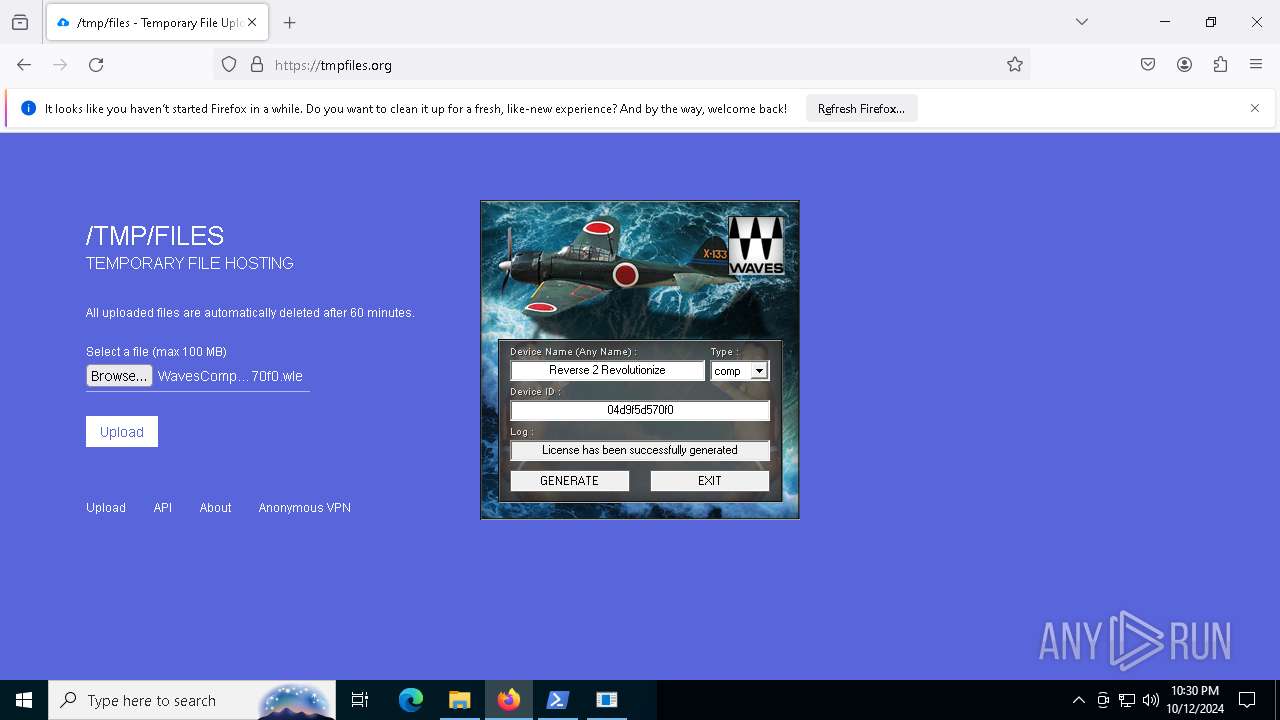
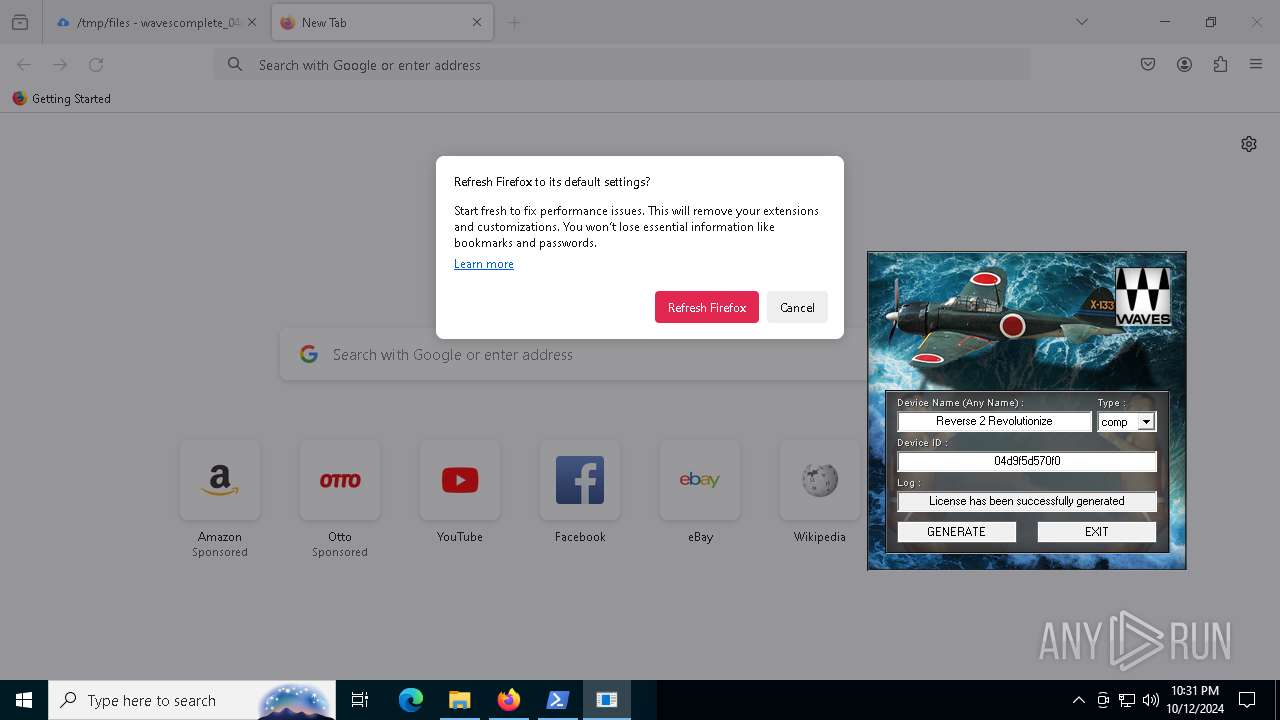
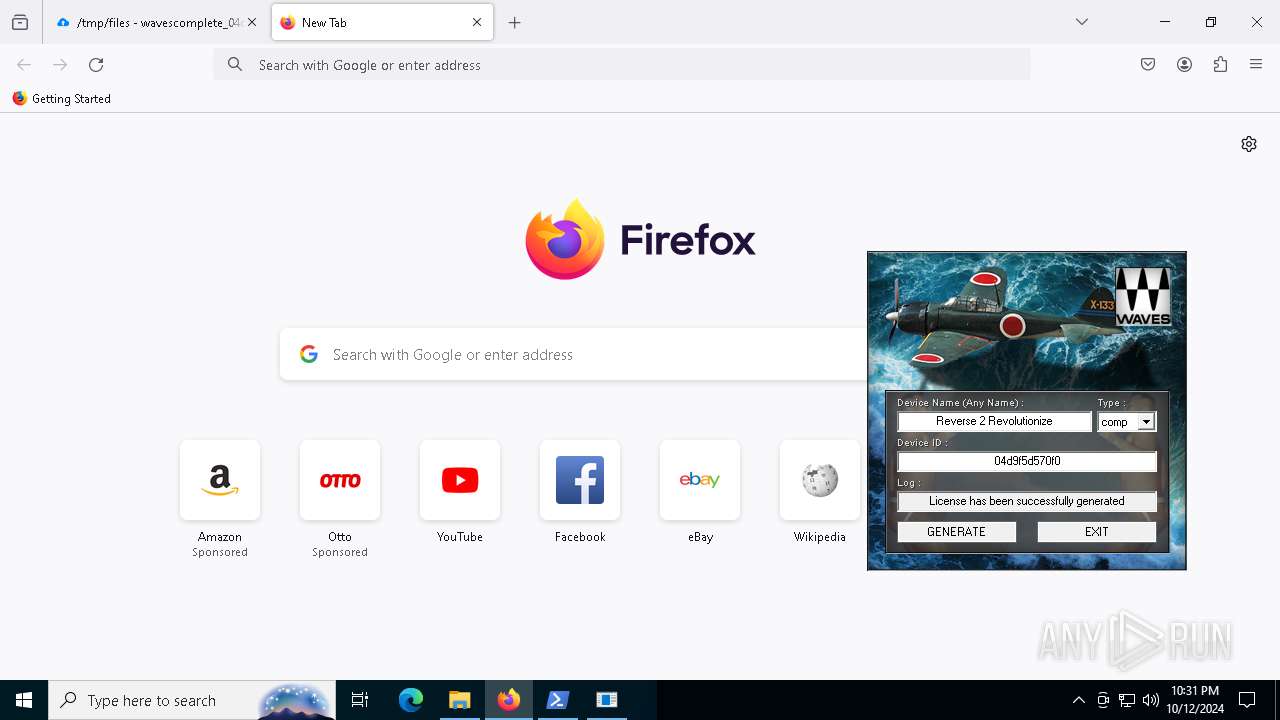
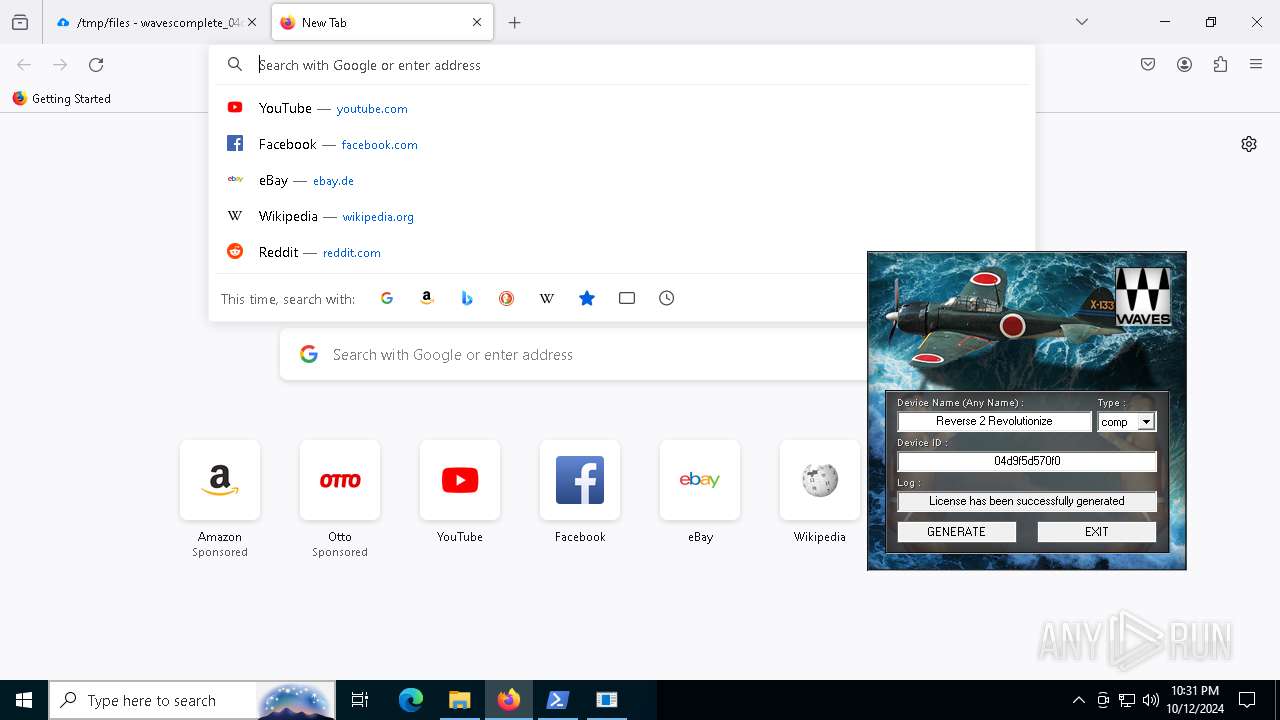
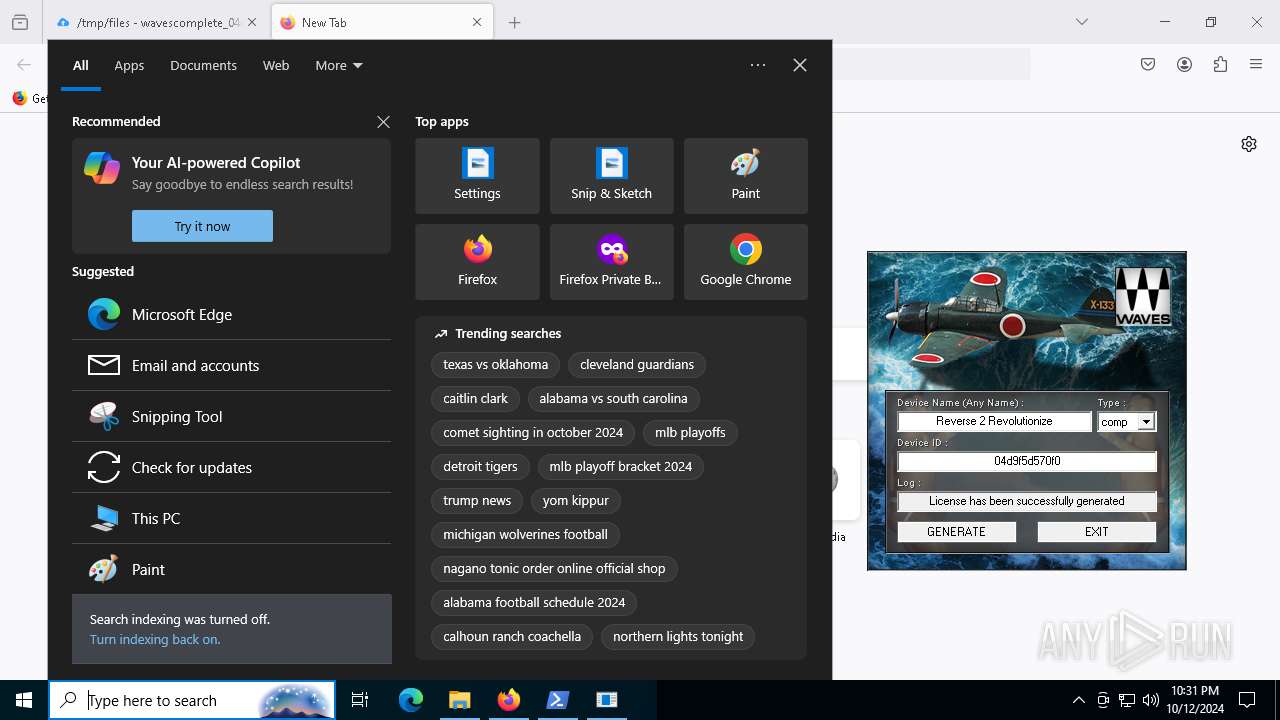
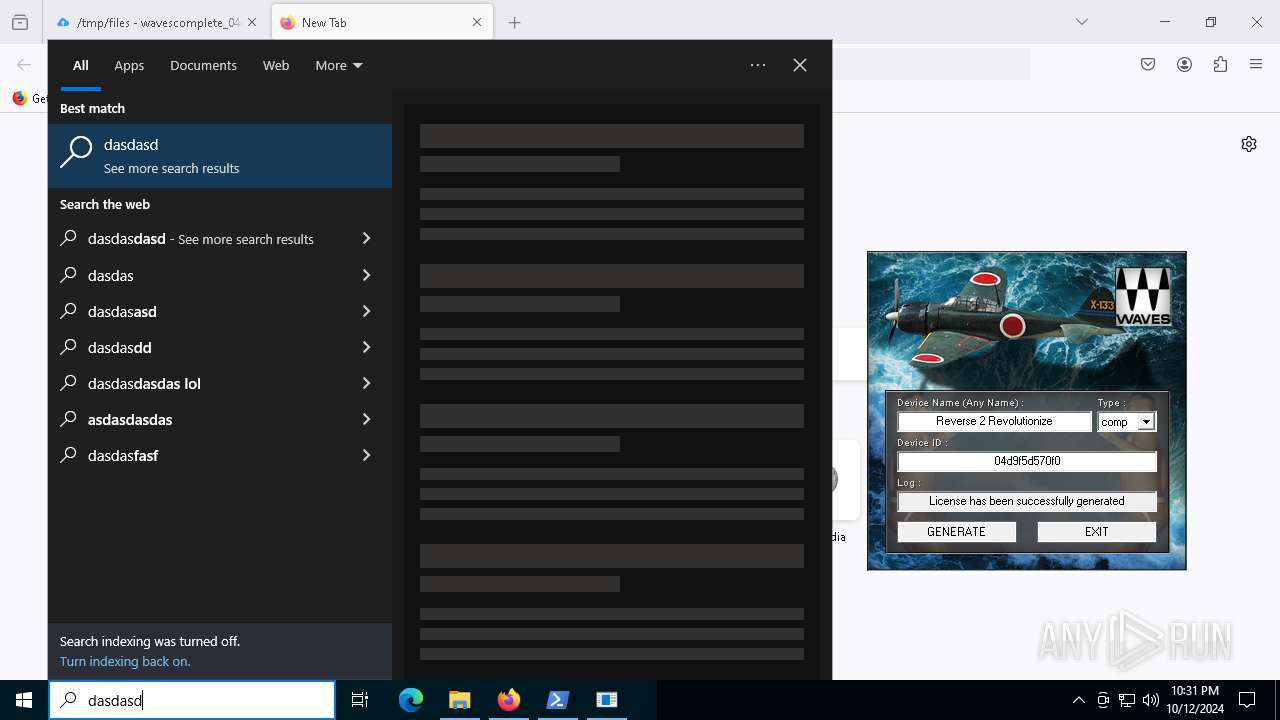
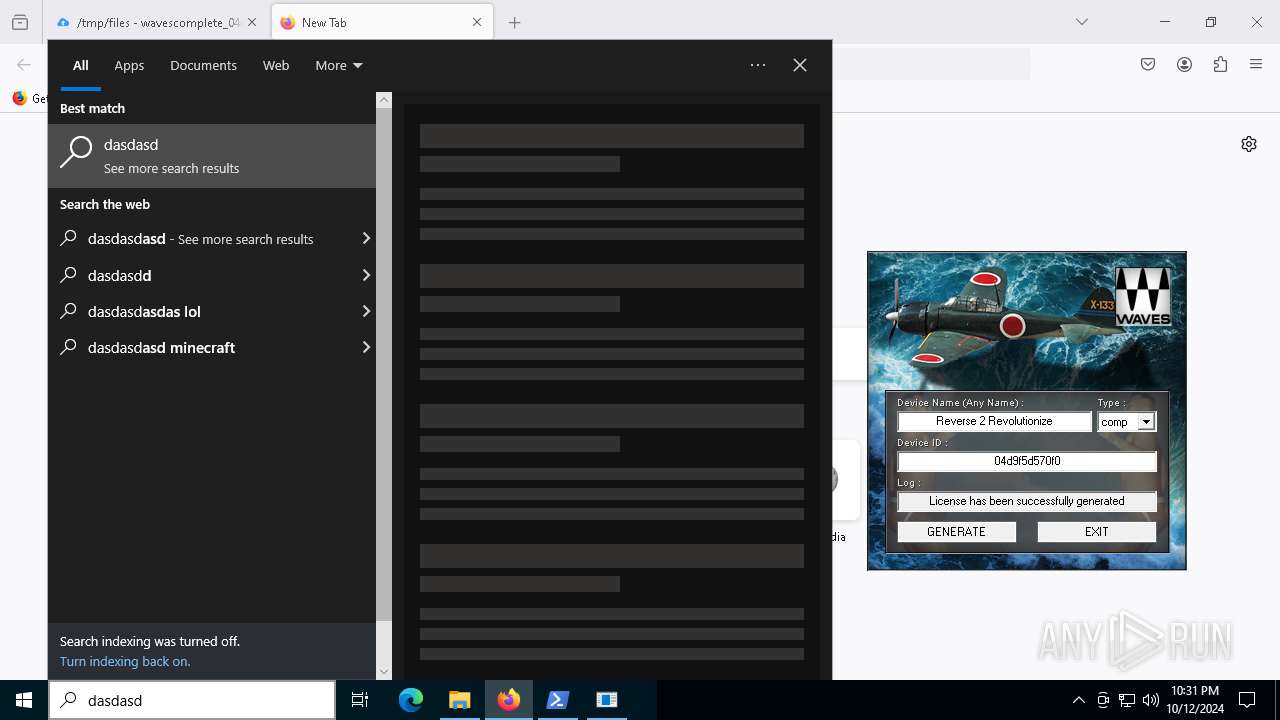
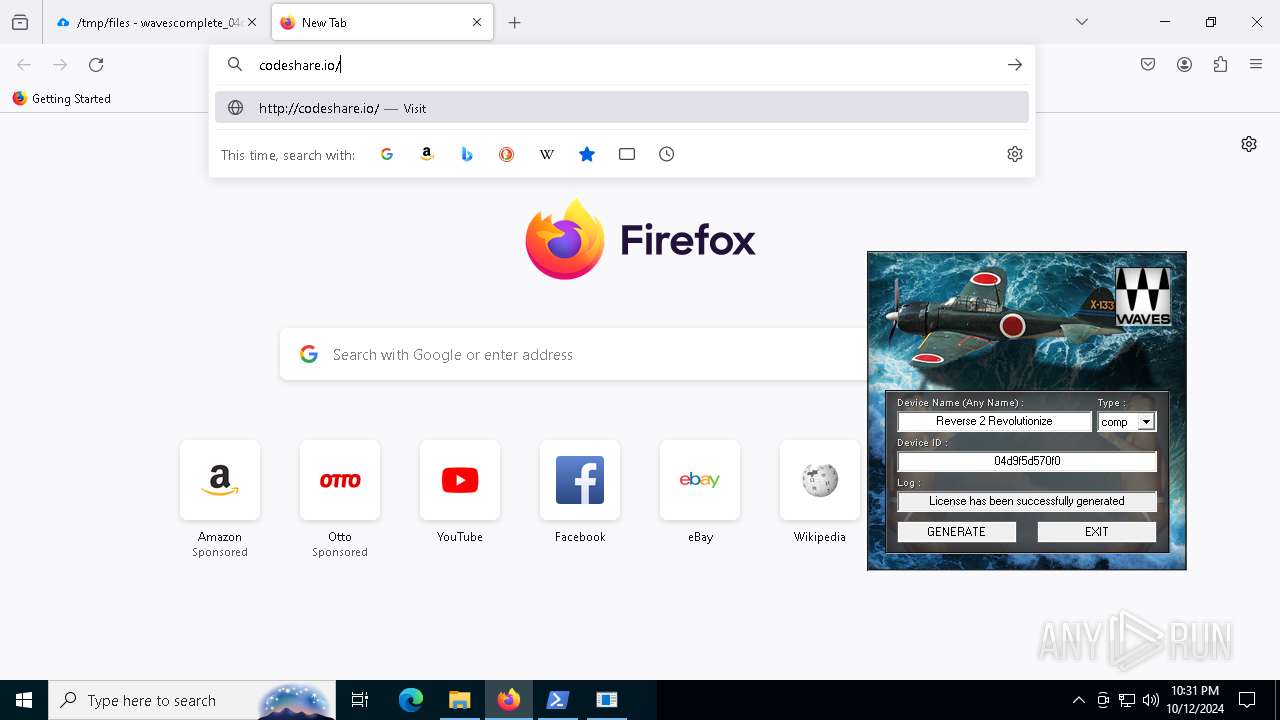
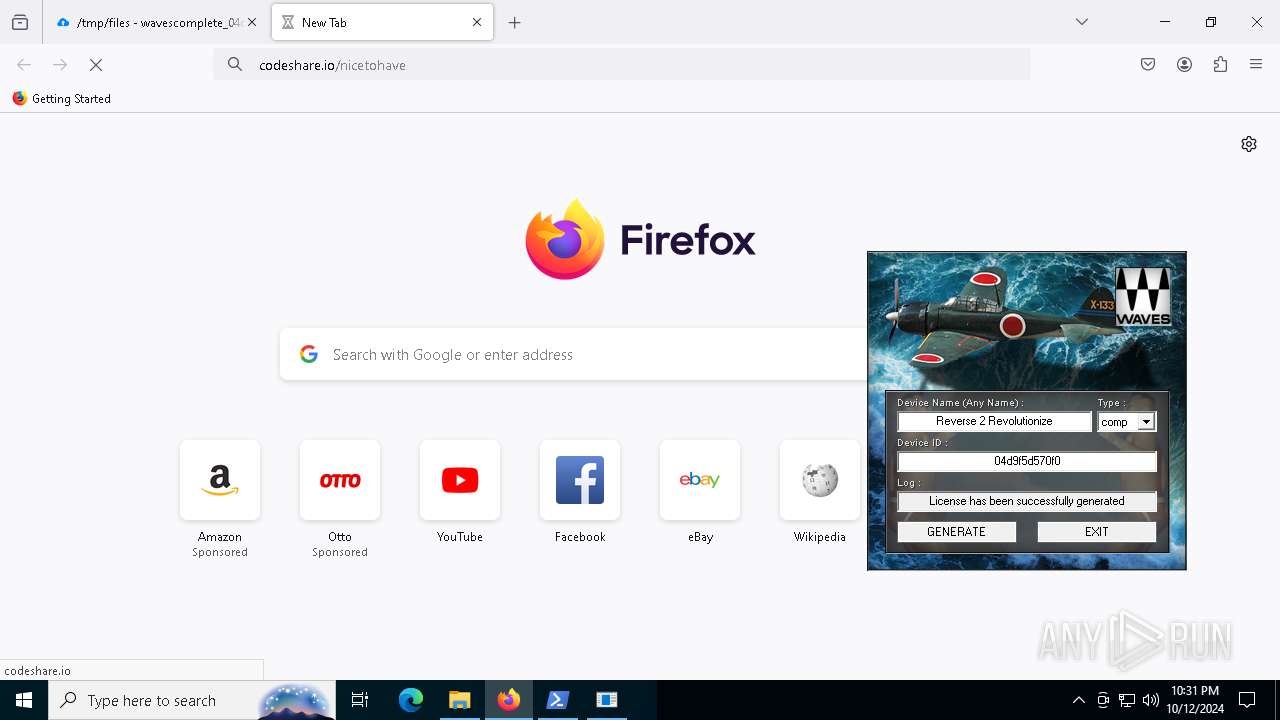
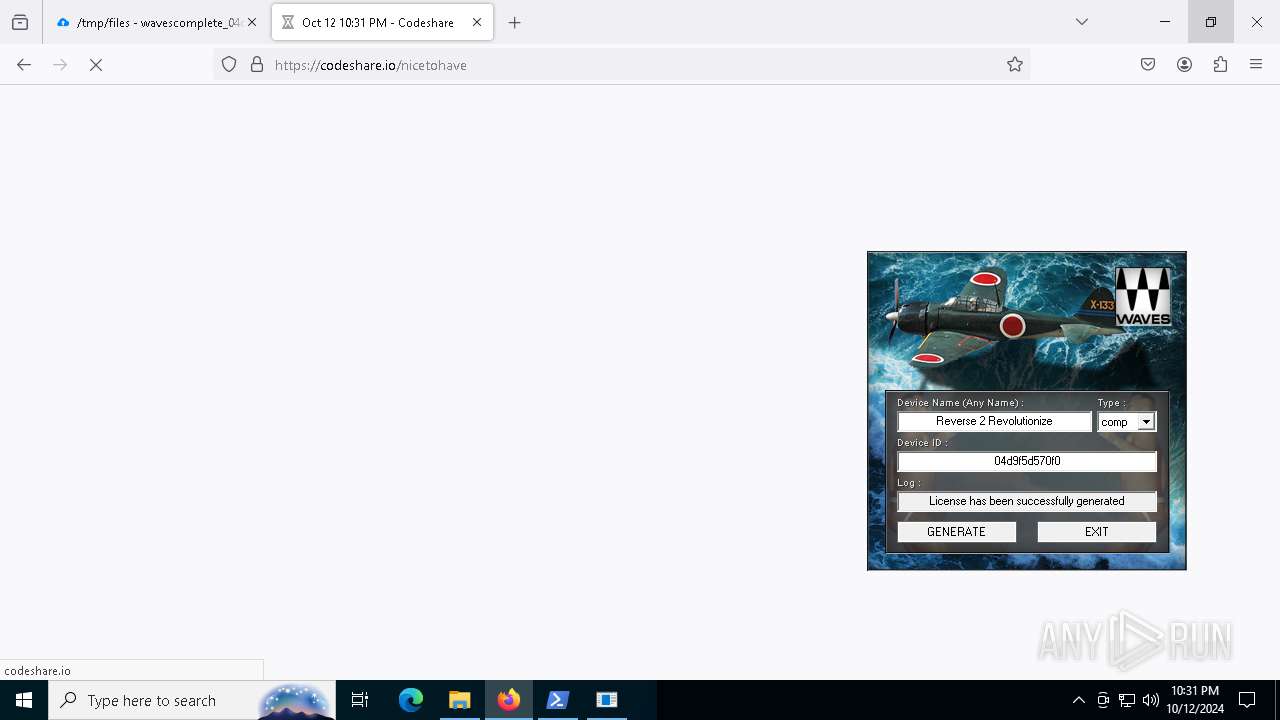
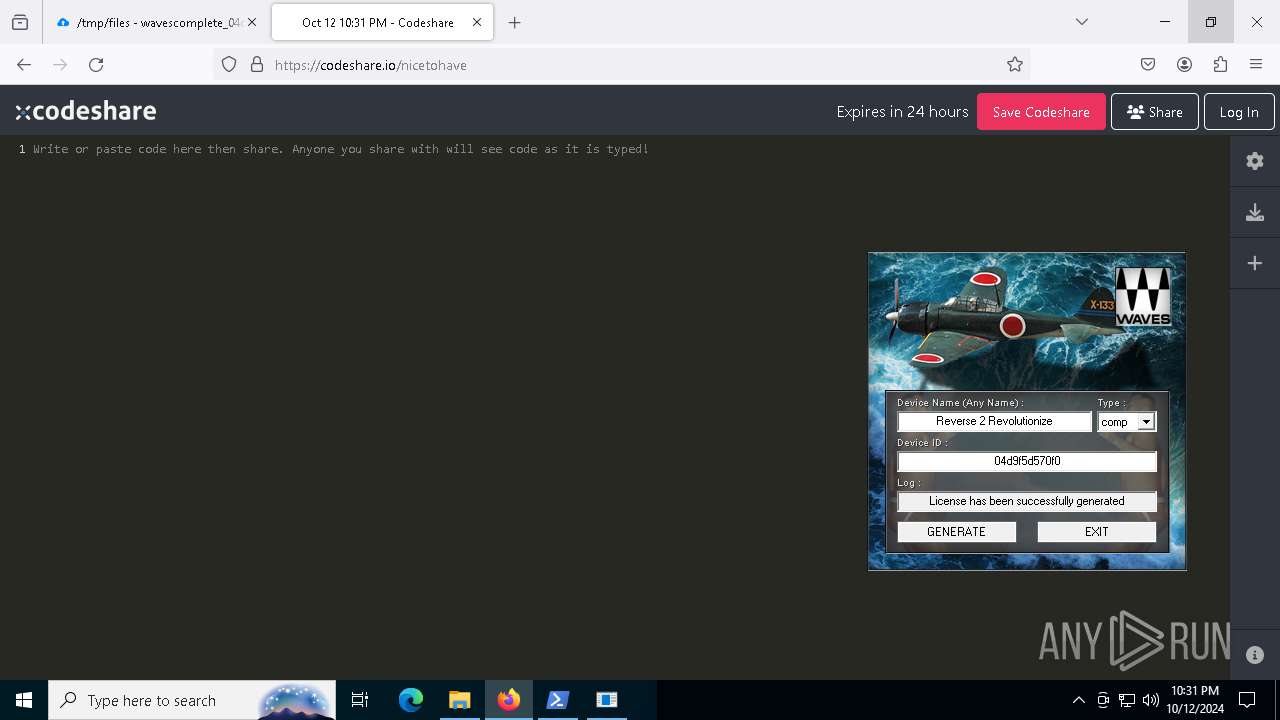
Manual execution by a user
- firefox.exe (PID: 2124)
- powershell.exe (PID: 1376)
Application launched itself
- firefox.exe (PID: 2124)
- firefox.exe (PID: 3912)
Executable content was dropped or overwritten
- firefox.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
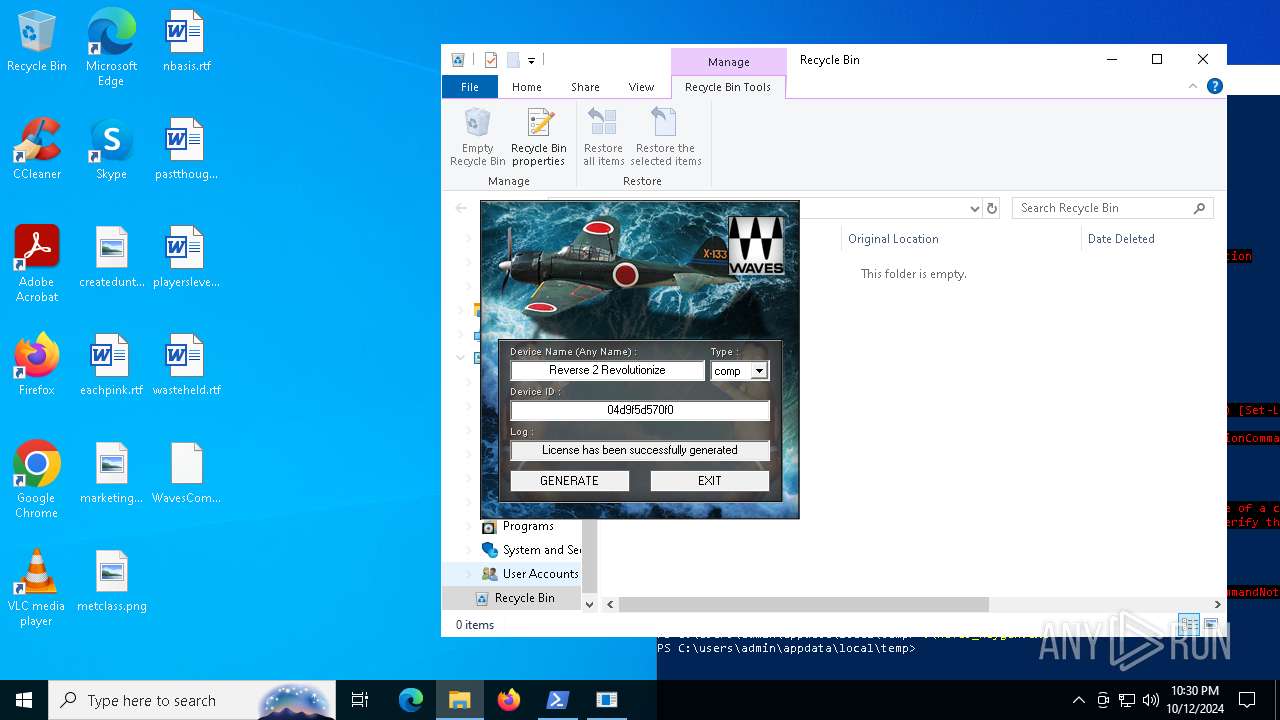
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
166
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
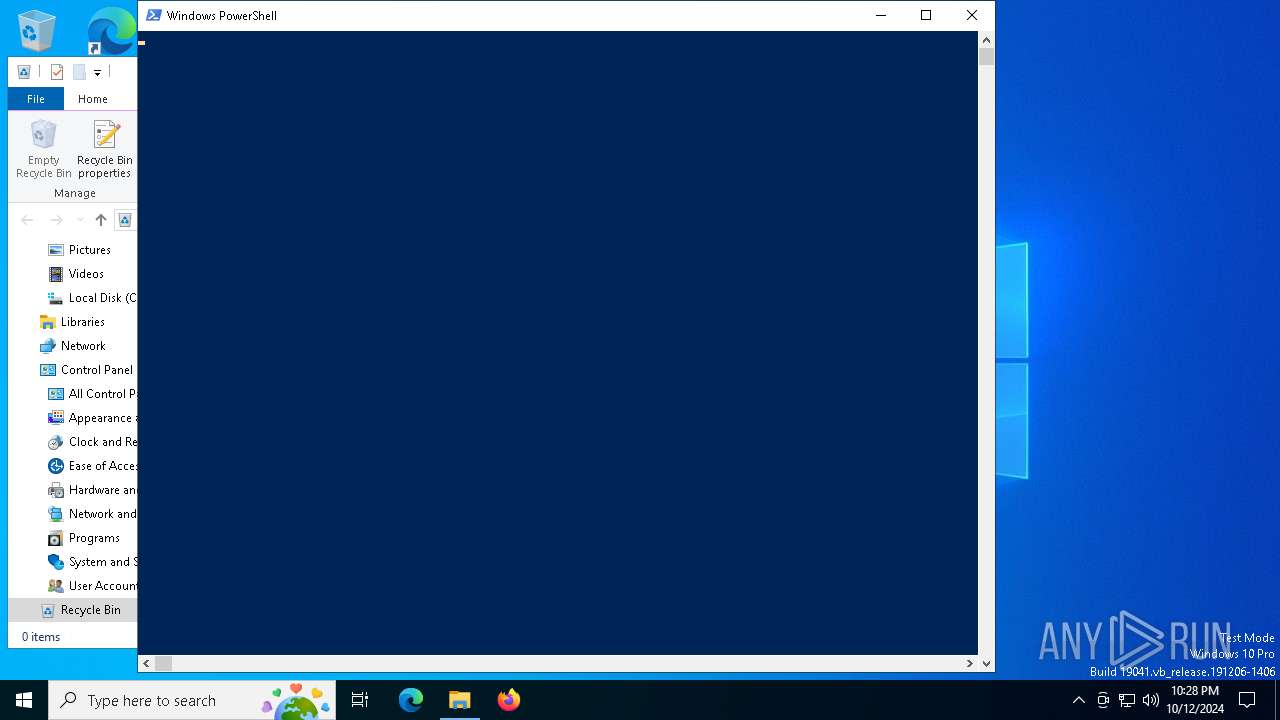
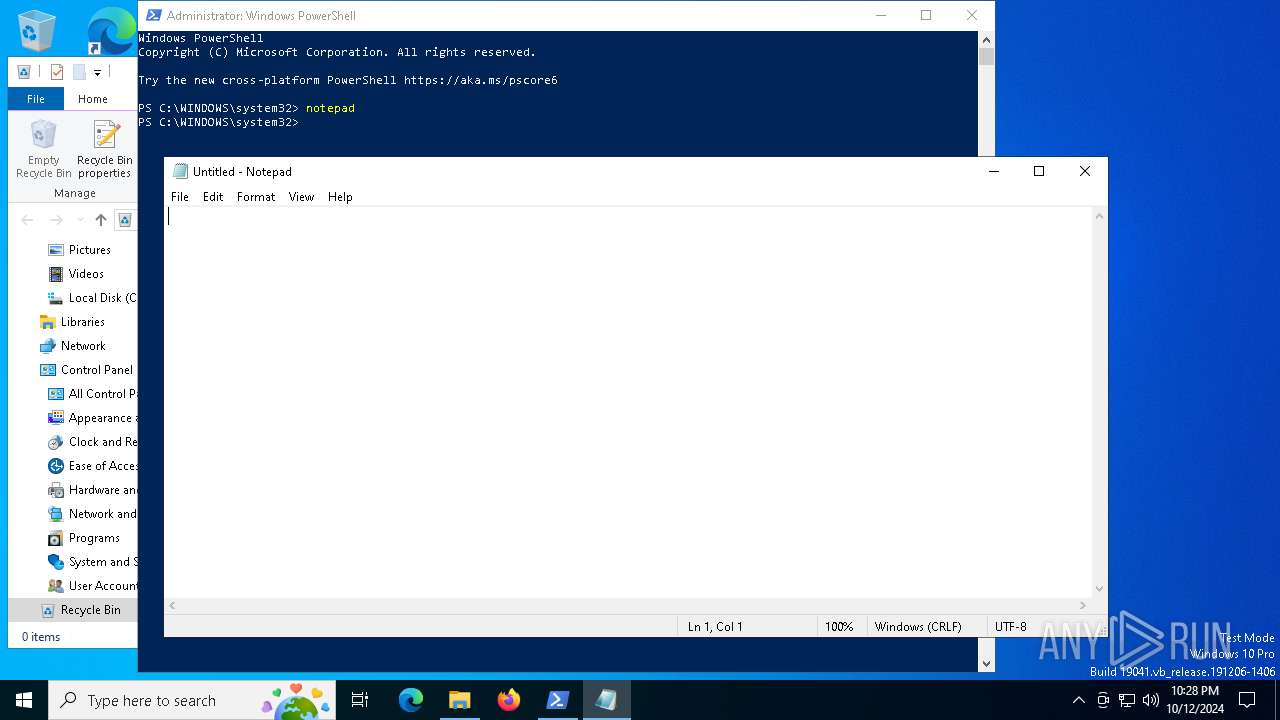
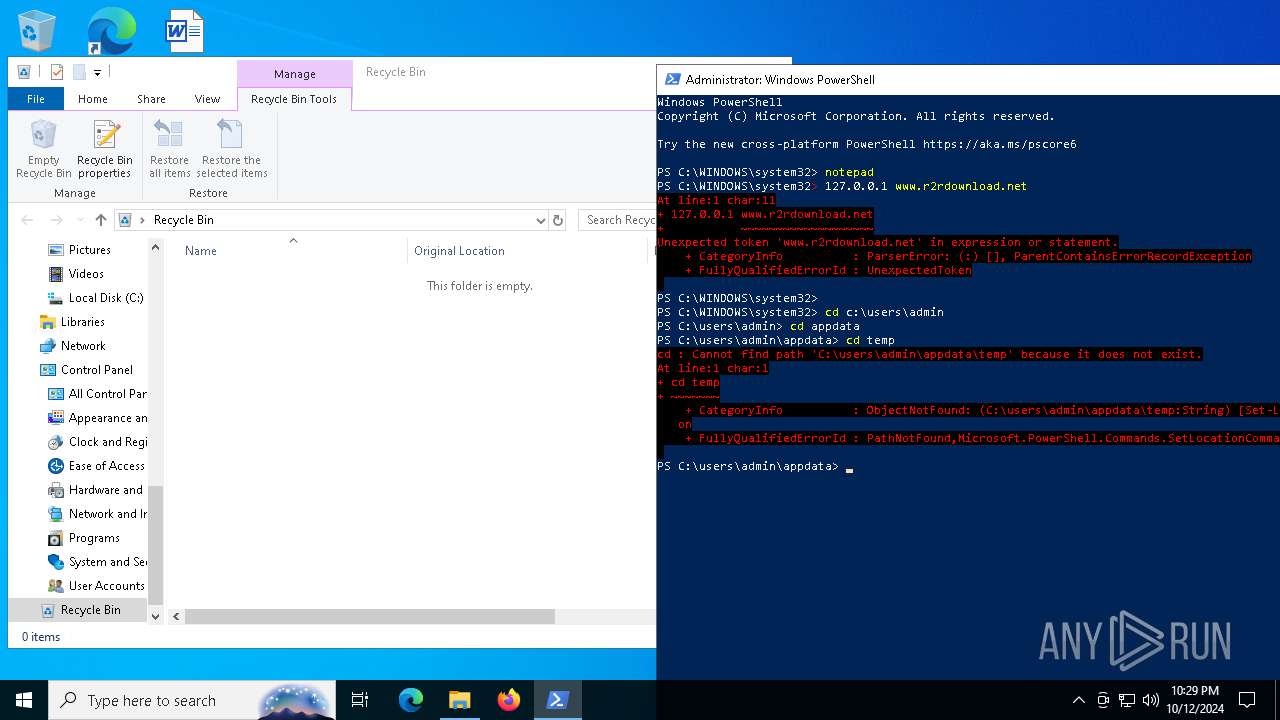
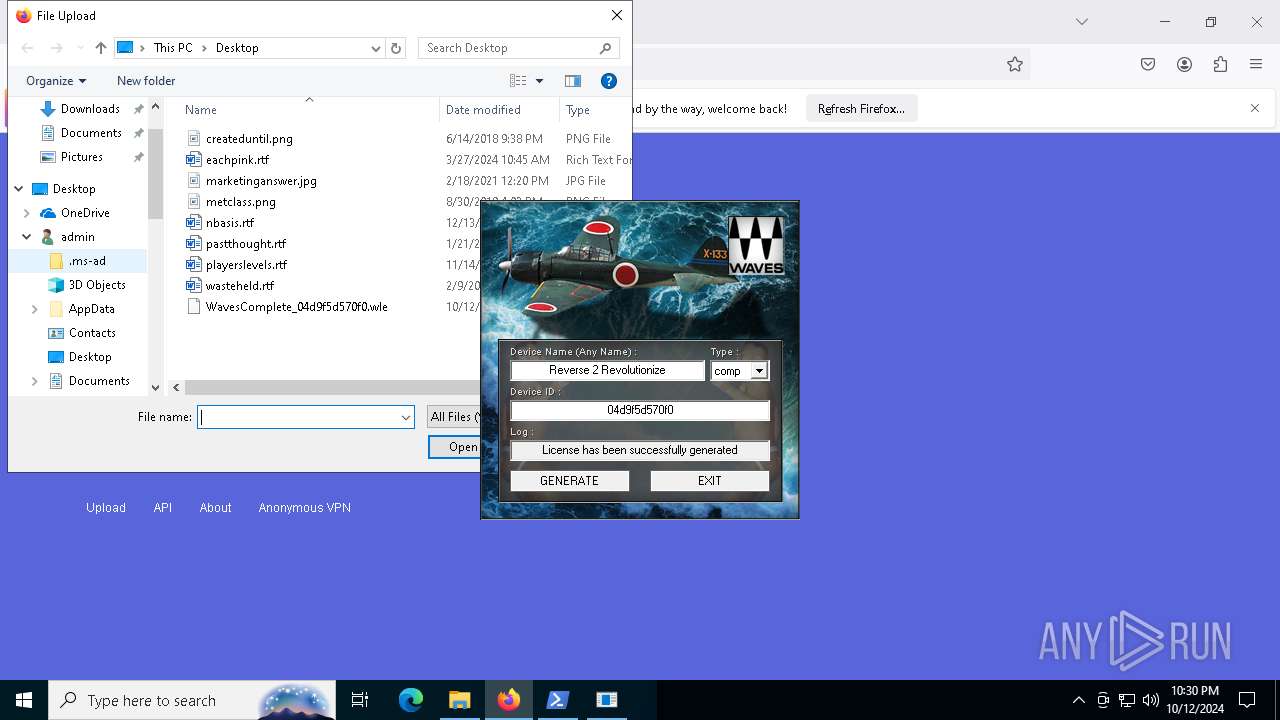
| 1376 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3824 | "C:\users\admin\appdata\local\temp\Waves_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Waves_Keygen.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
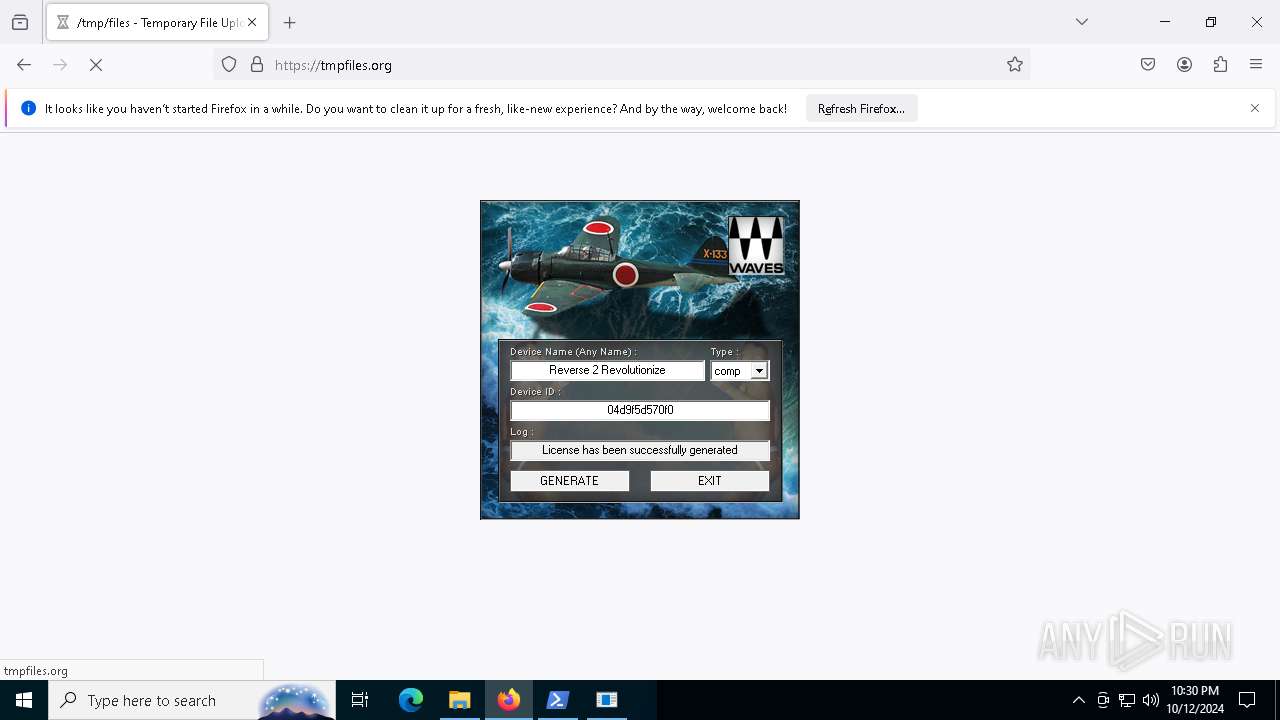
| 3912 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4476 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5884 -childID 5 -isForBrowser -prefsHandle 5660 -prefMapHandle 5680 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {45d6d224-1b15-4705-86d7-bf63e68ba45d} 3912 "\\.\pipe\gecko-crash-server-pipe.3912" 22b9b235150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5084 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6520 -childID 6 -isForBrowser -prefsHandle 6528 -prefMapHandle 5268 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {dc451ca0-bc5f-4cfa-b3f4-2bba21ab2ae2} 3912 "\\.\pipe\gecko-crash-server-pipe.3912" 22b9b365a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5240 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1908 -parentBuildID 20240213221259 -prefsHandle 1836 -prefMapHandle 1816 -prefsLen 30705 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {c4280e96-f171-450c-85d6-691792617945} 3912 "\\.\pipe\gecko-crash-server-pipe.3912" 22b8fae6c10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
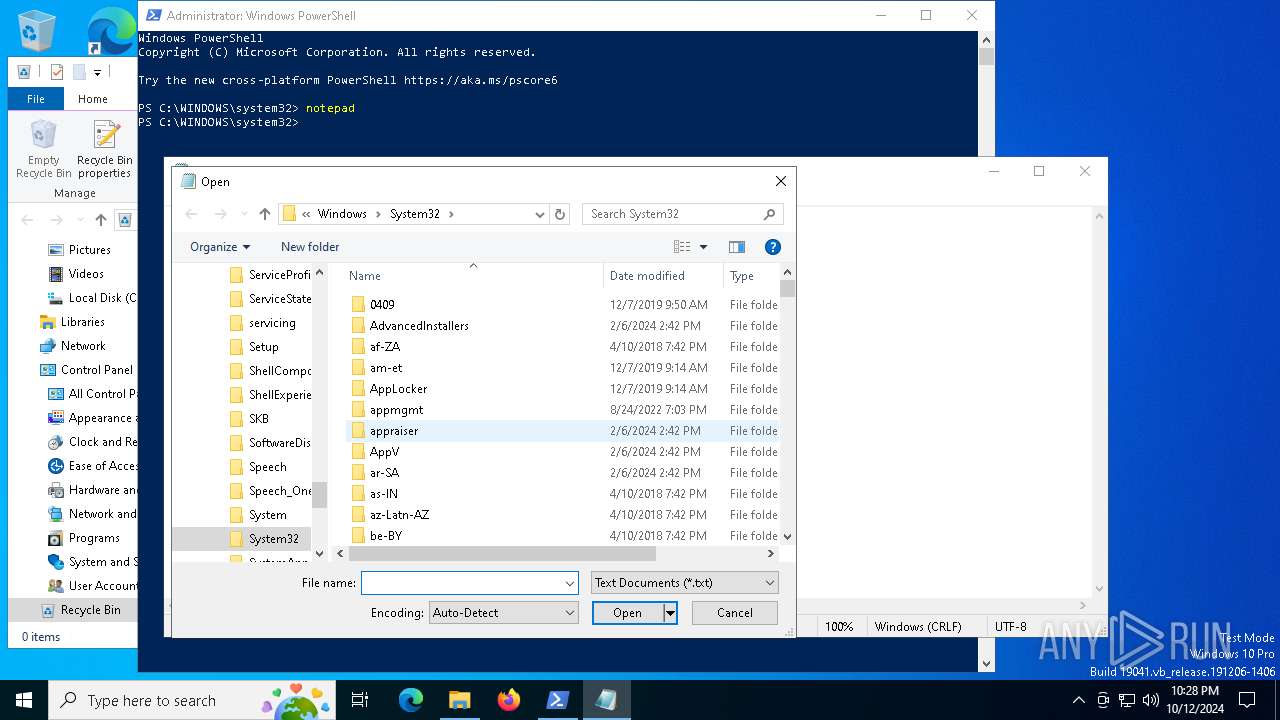
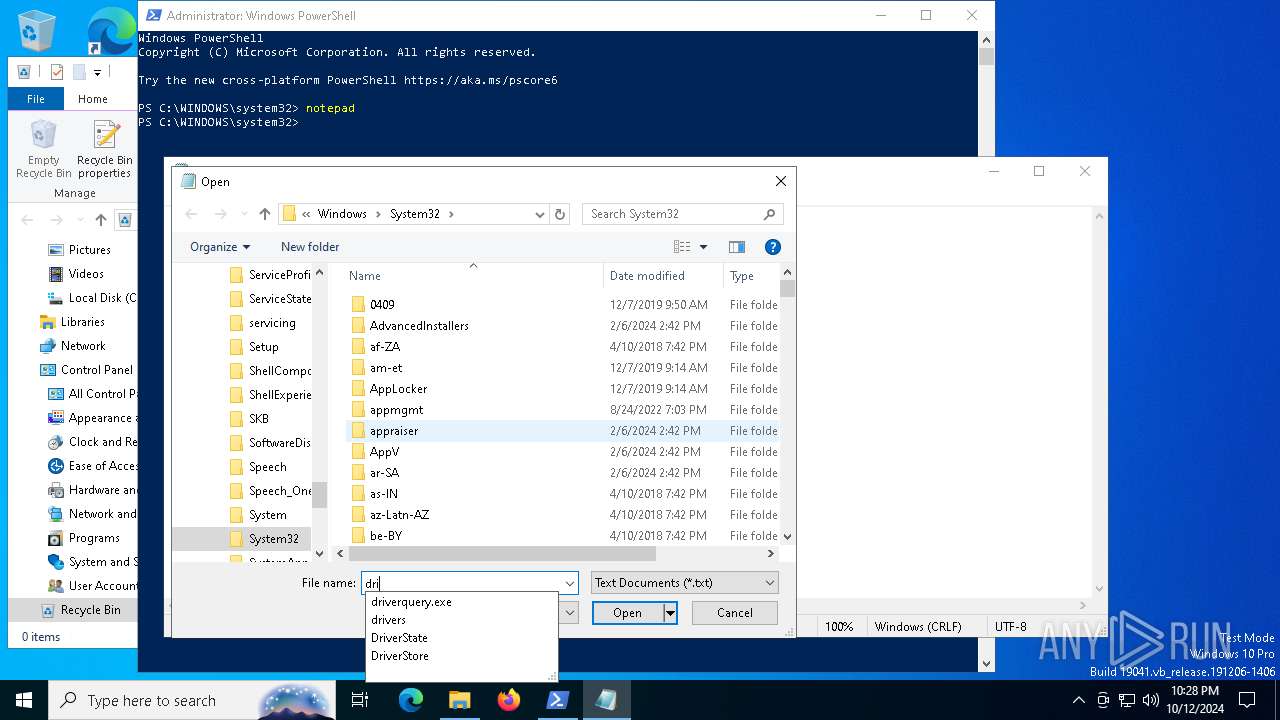
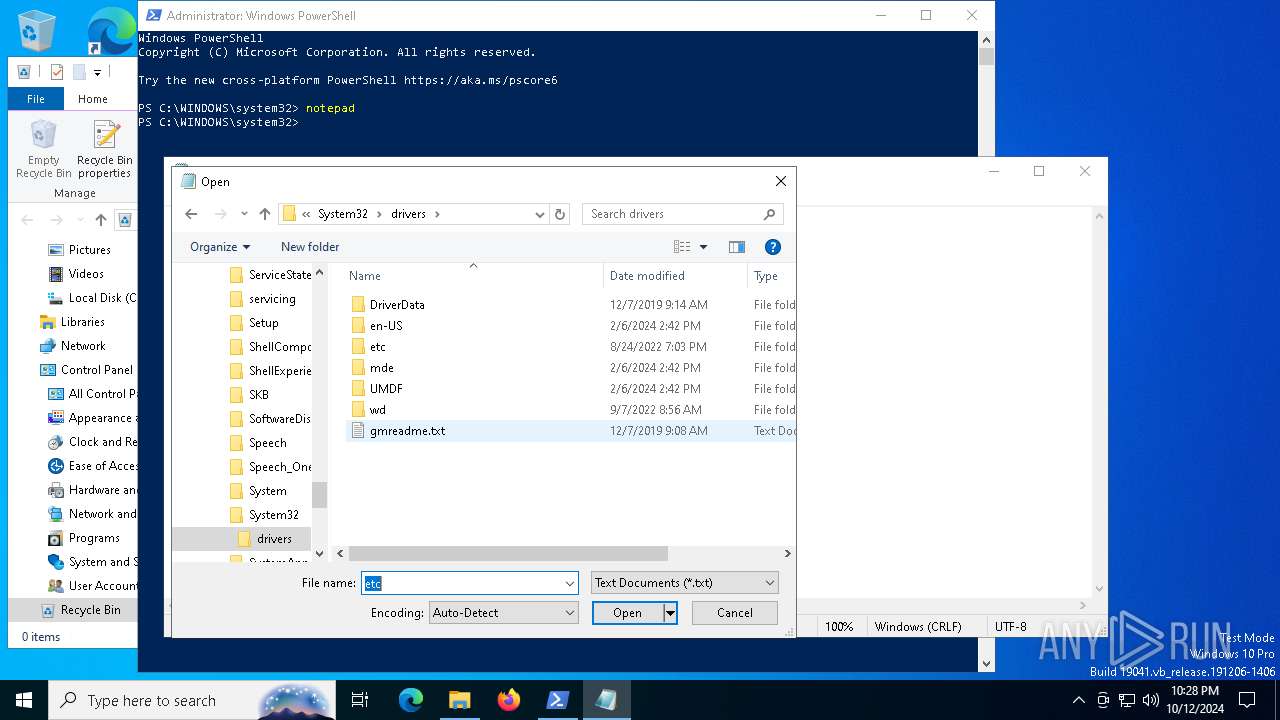
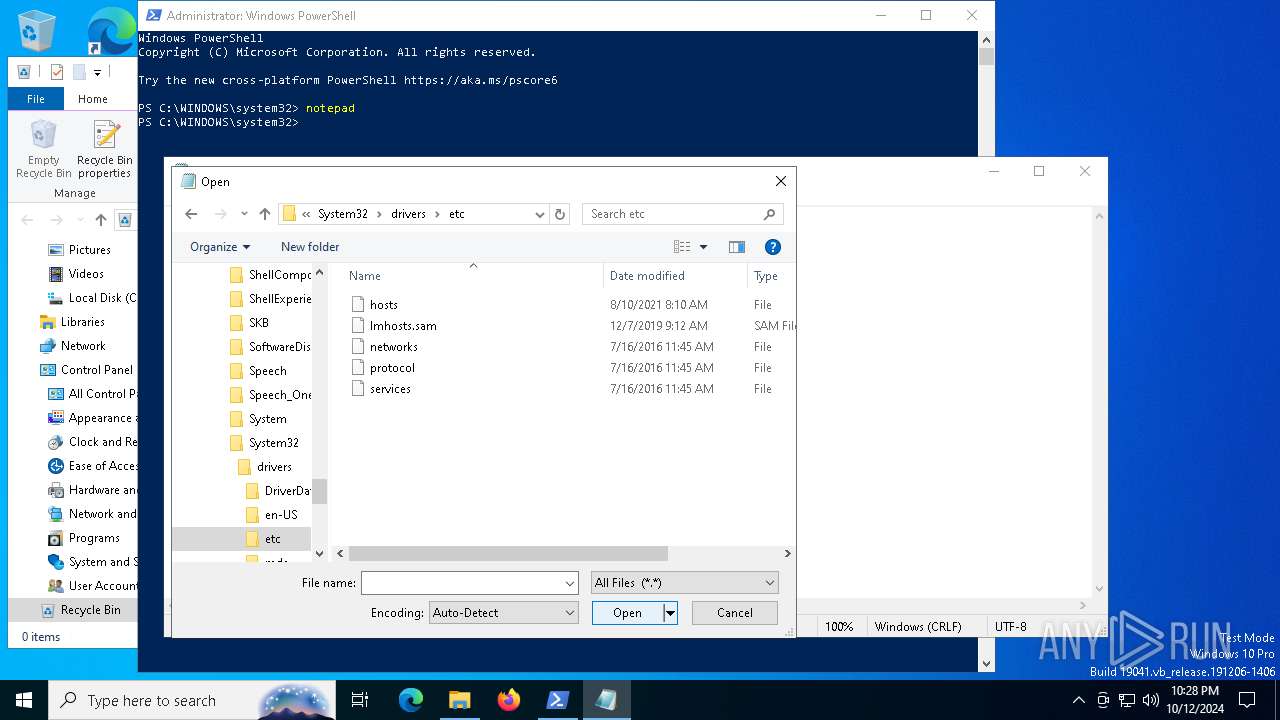
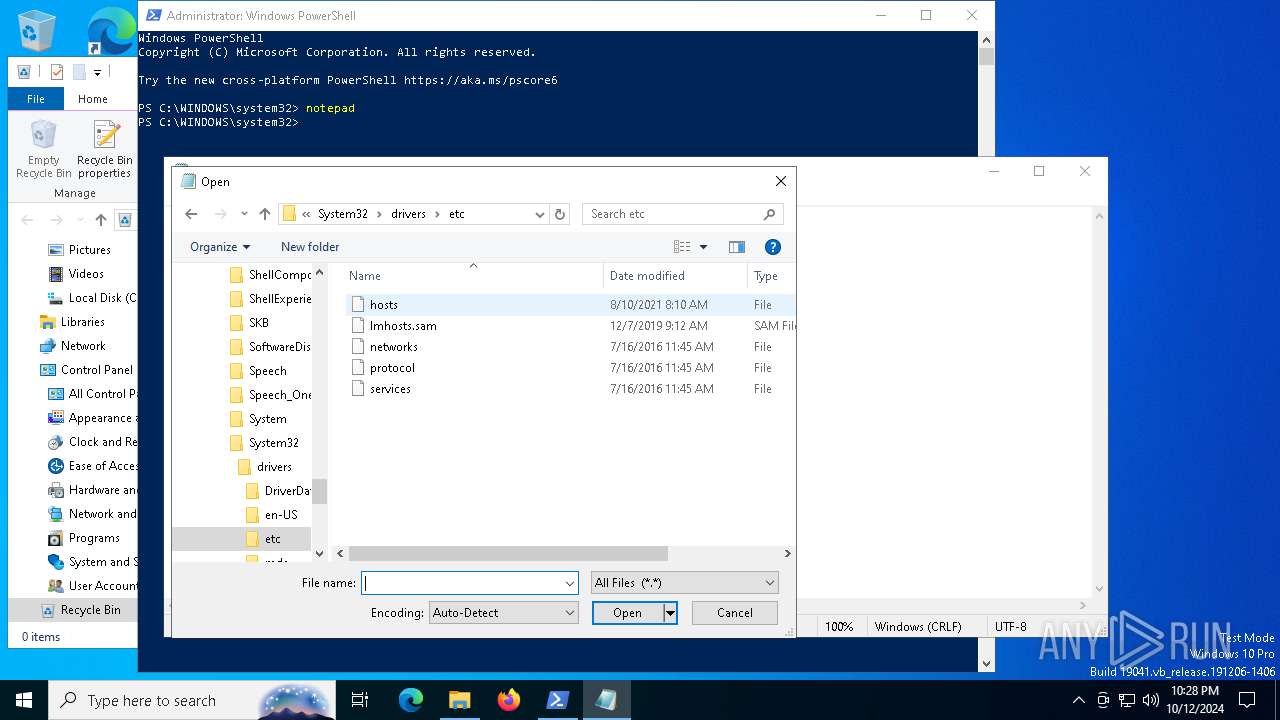
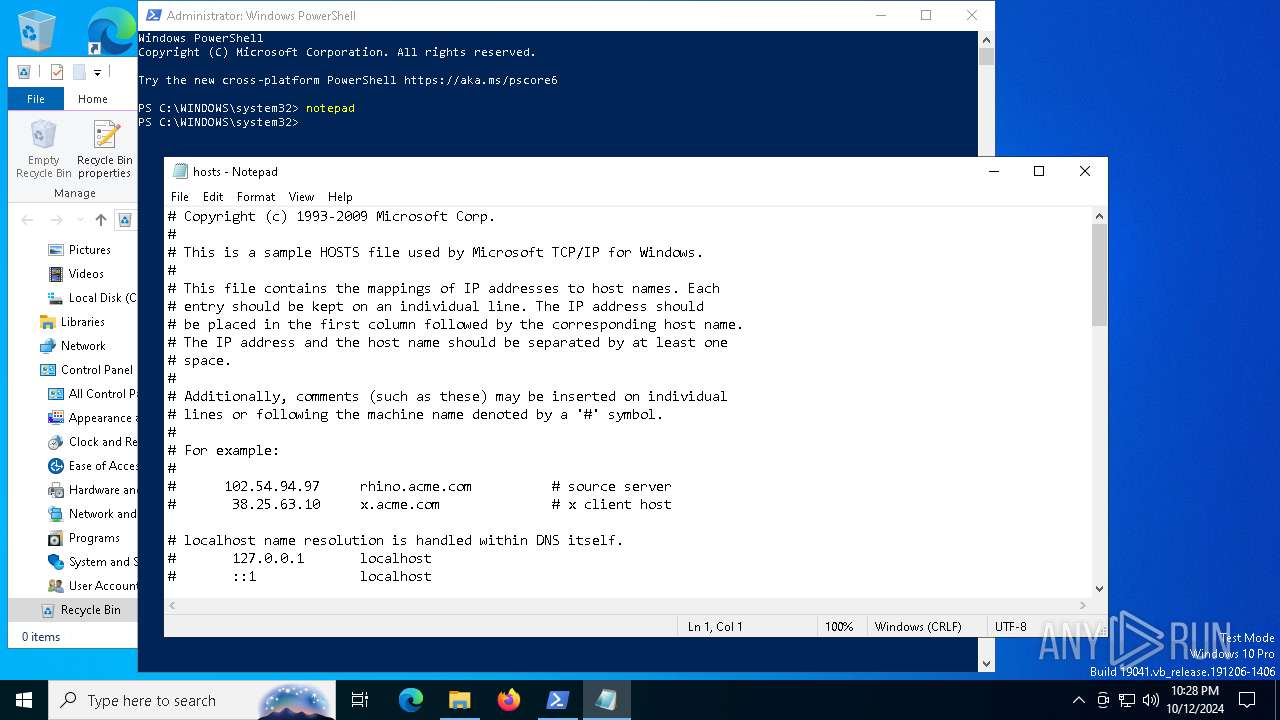
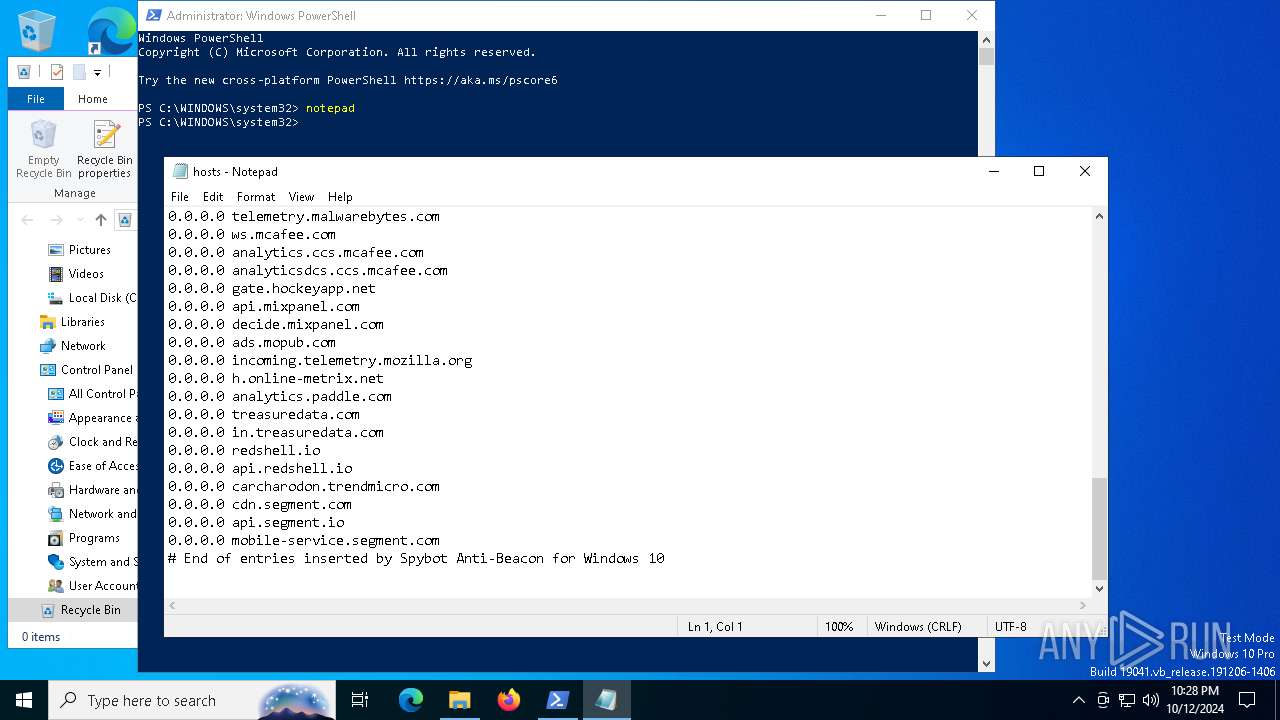
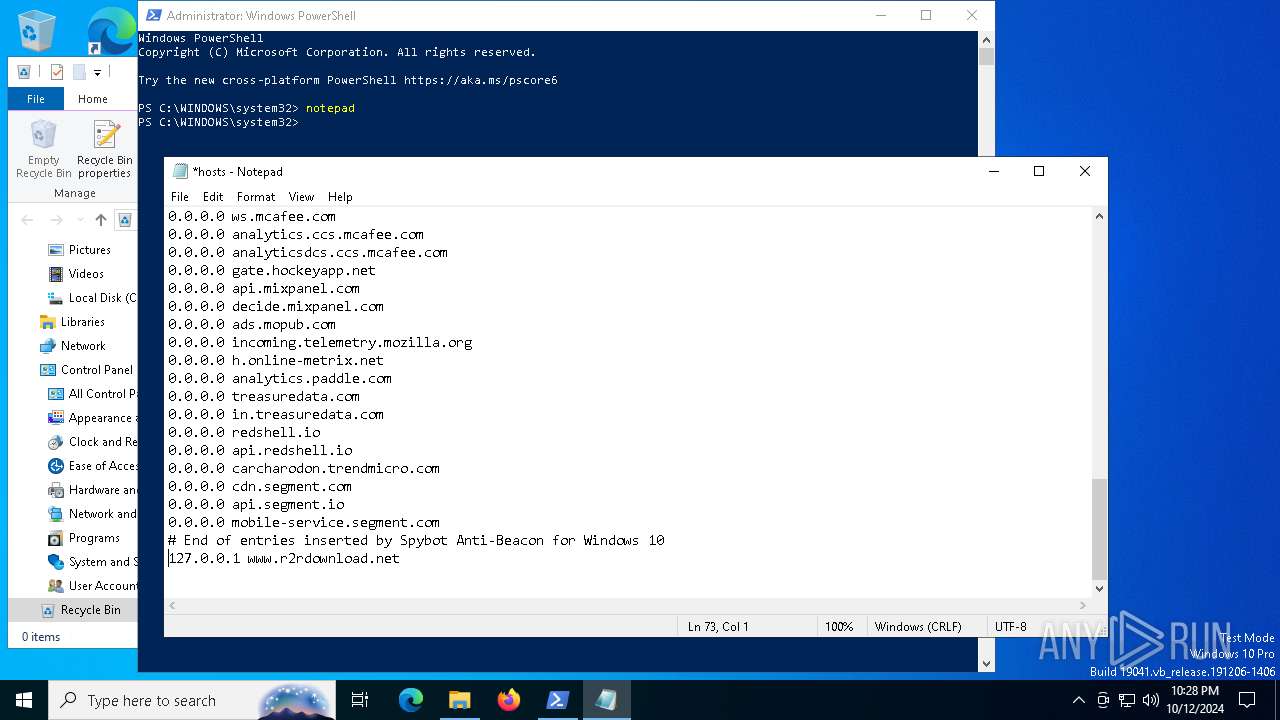
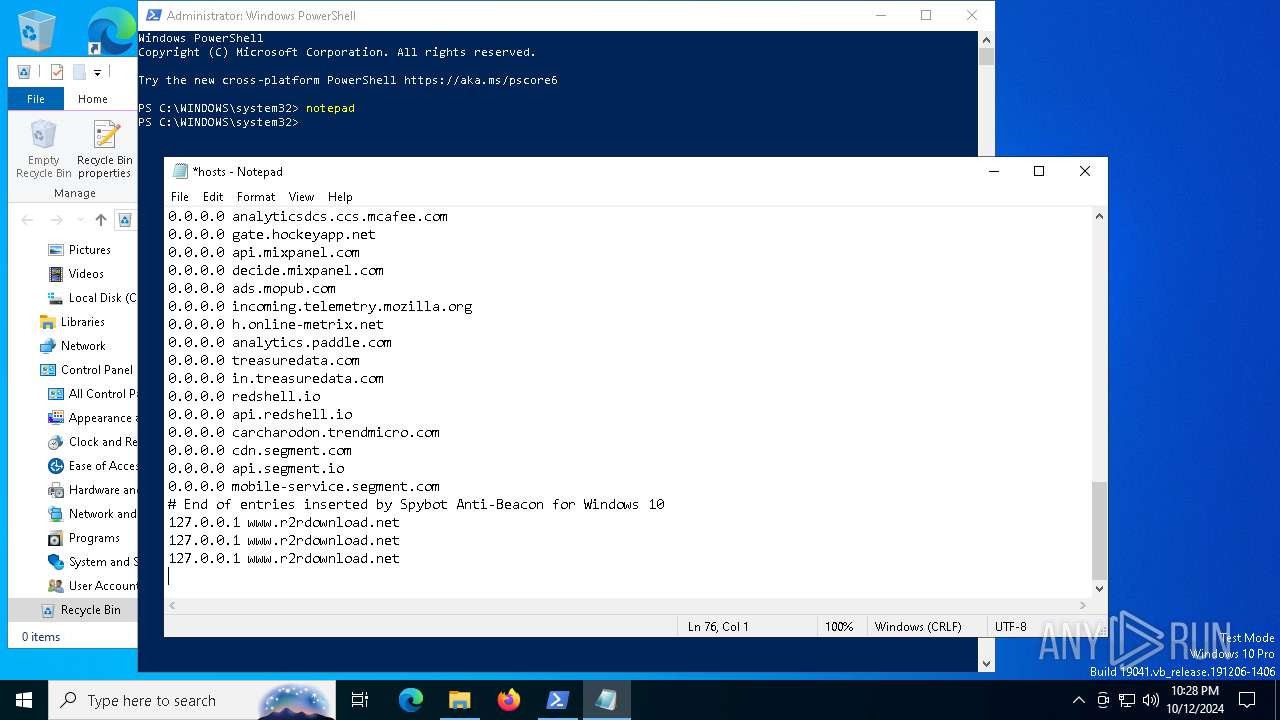
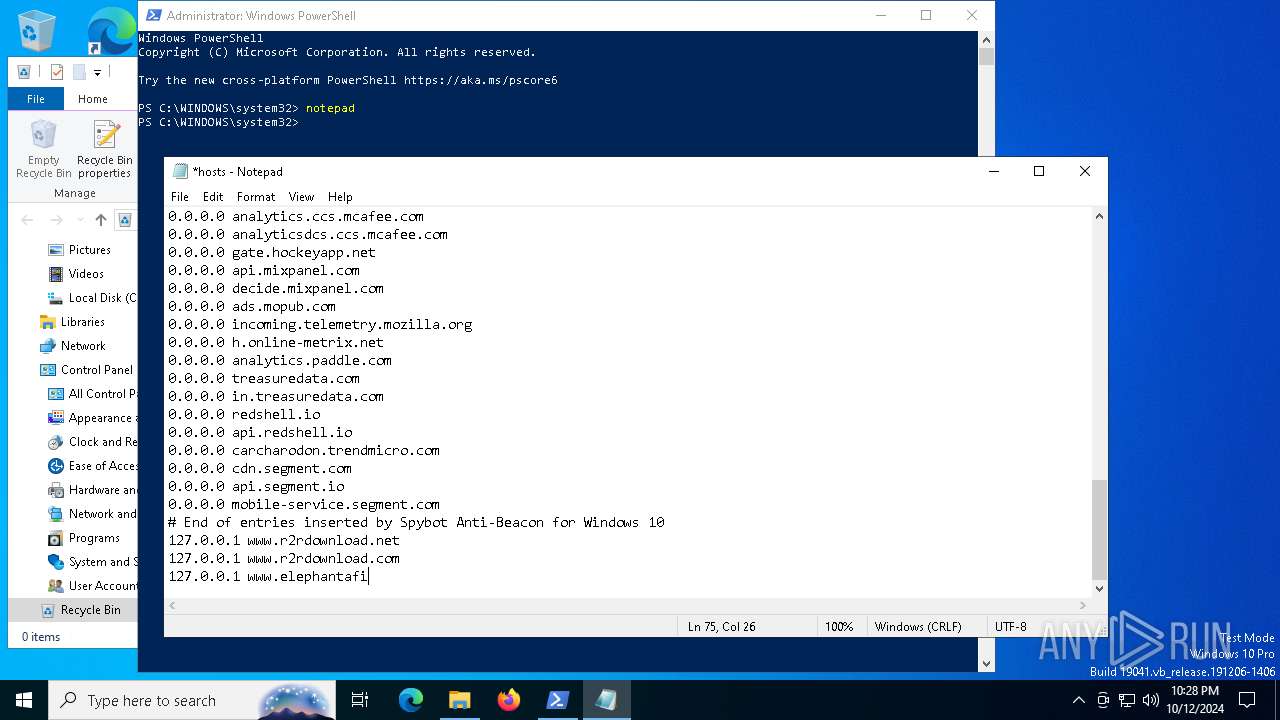
| 5264 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 785
Read events
34 573
Write events
202
Delete events
10
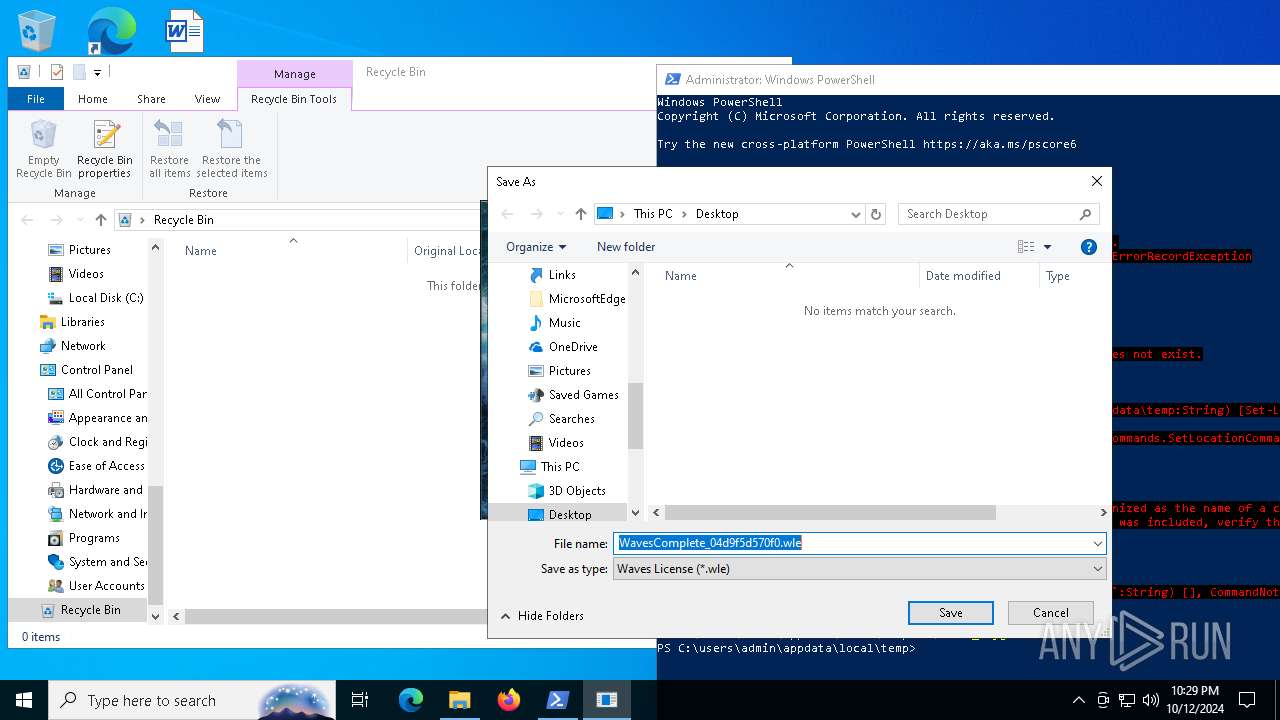
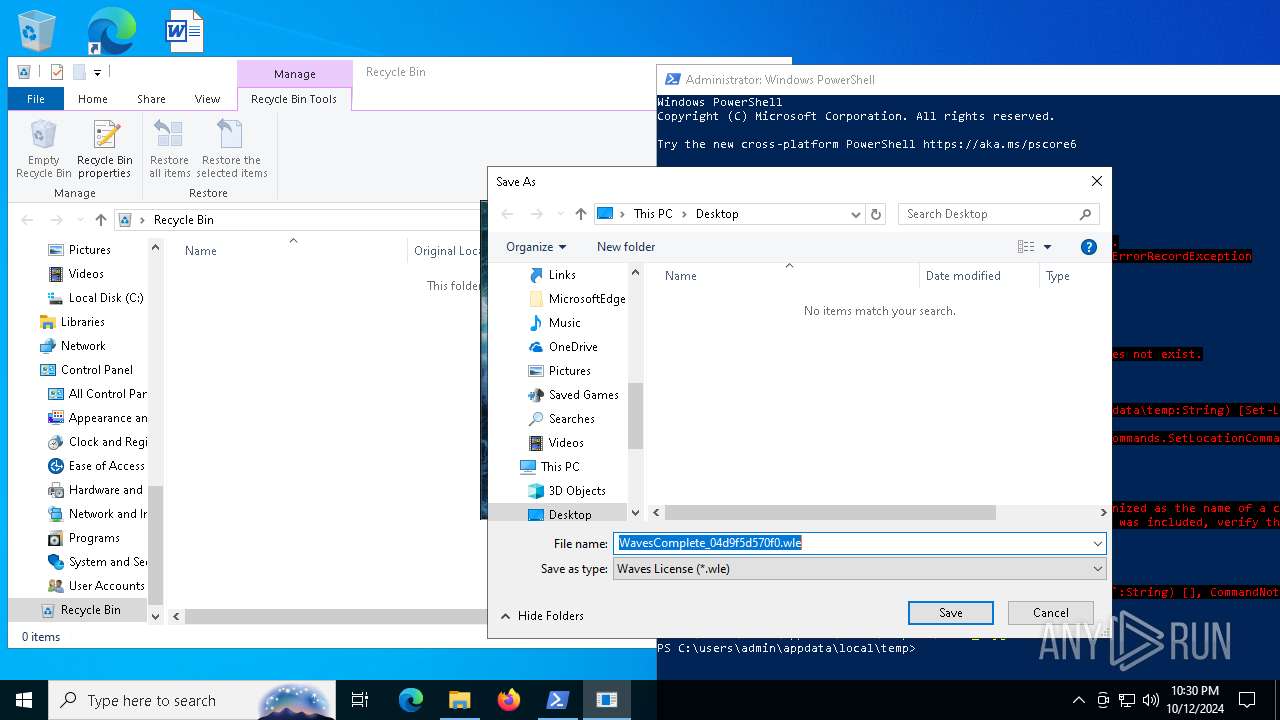
Modification events
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000006000000040000000500000008000000020000000C0000000B0000000A00000009000000070000000000000003000000FFFFFFFF | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\0\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000070000000300000006000000050000000200000001000000FFFFFFFF | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
| (PID) Process: | (5264) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\28\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Sort |
Value: 000000000000000000000000000000000100000030F125B7EF471A10A5F102608C9EEBAC0A00000001000000 | |||
Executable files
8
Suspicious files
195
Text files
43
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6216 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\nsbBCD2.tmp | binary | |
MD5:66732AAEDEF20EBBE8F976251AA4764C | SHA256:7F27984E881343CF697ADB93483143E12EDCBFB3D28EE35D75ABBF848EA84BA1 | |||
| 6216 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\R2ROPENSSL.dll | executable | |
MD5:34FE92E0DC877A7F1A891920A1875320 | SHA256:B7D3B7C11278F9A8E9A2FD4513772671F9DA7C60C80A83CC727EE22B78D8BF7E | |||
| 1376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cz243pgz.gwy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6216 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:C2BC2621865030F86316F051B5006BE1 | SHA256:A2B1CFE5ACB9C5A6ACACC8D17749BD96E6C2DBCCD17103A83DAA283312920596 | |||
| 6216 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 1376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wcxdrmqm.clh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3824 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:C2BC2621865030F86316F051B5006BE1 | SHA256:A2B1CFE5ACB9C5A6ACACC8D17749BD96E6C2DBCCD17103A83DAA283312920596 | |||
| 3824 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 3824 | Waves_Keygen.exe | C:\Users\admin\AppData\Local\Temp\bgm.it | binary | |
MD5:E5F0FB9378B3438C07D7501BBDDC364C | SHA256:EDD5692A6CFD7CC7499989A92B52690311162920375688C86CCAEBFB82E214AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
163
DNS requests
192
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5652 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5652 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3912 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
3076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3912 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
3912 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2464 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
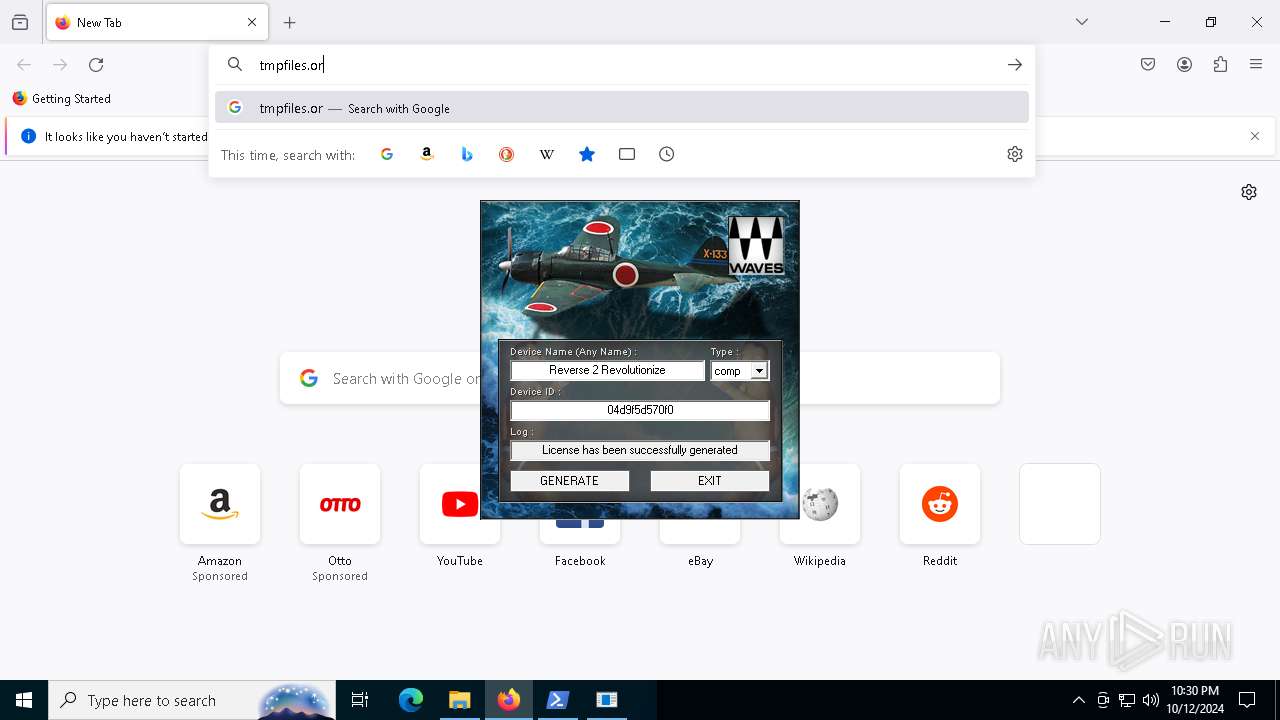
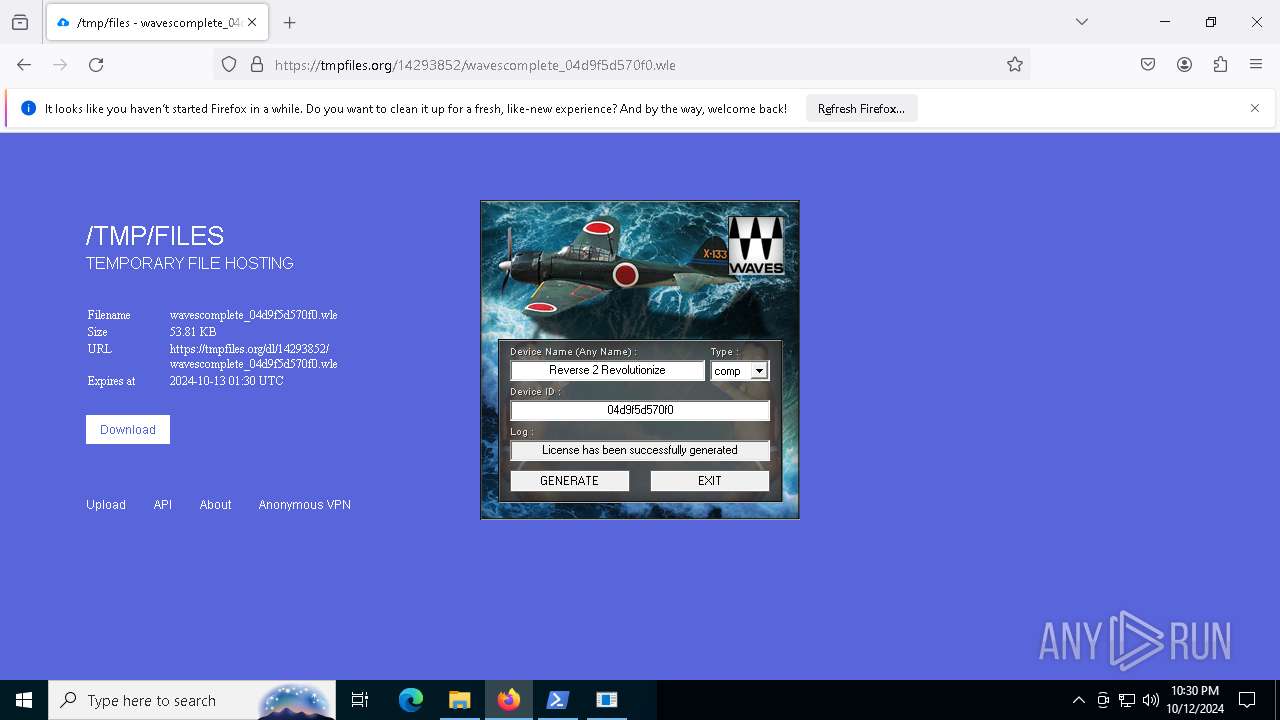
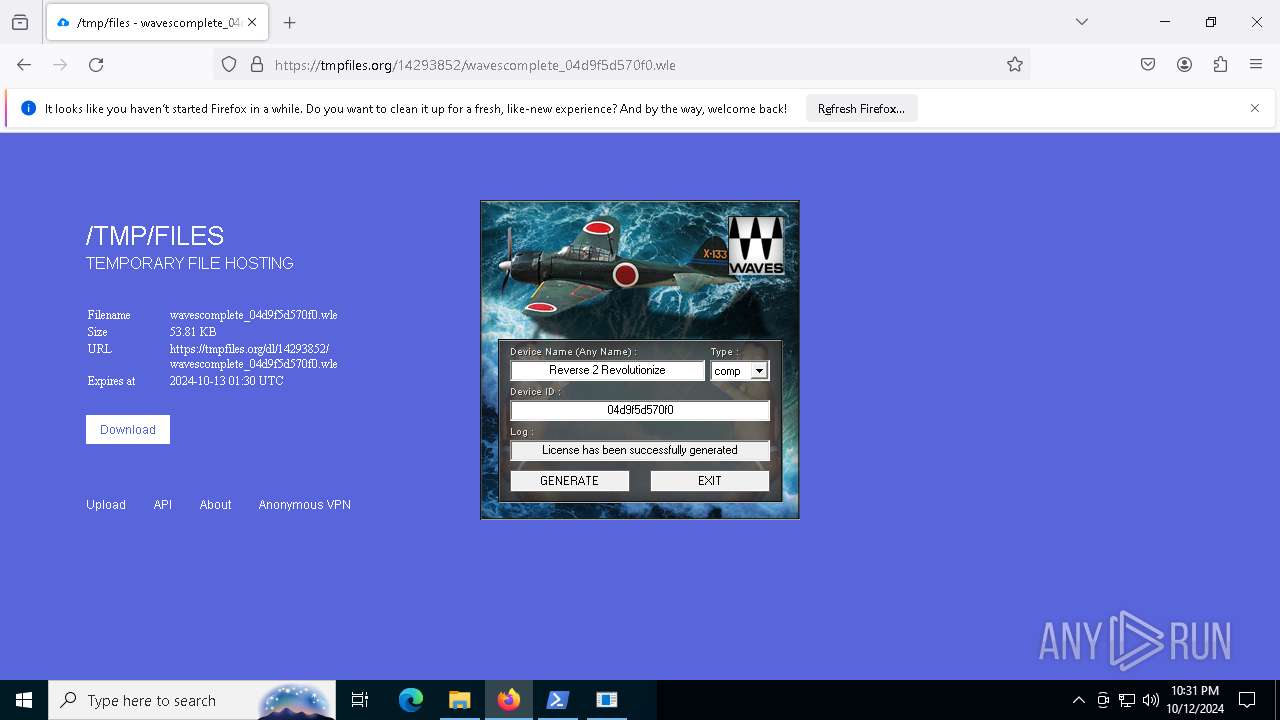
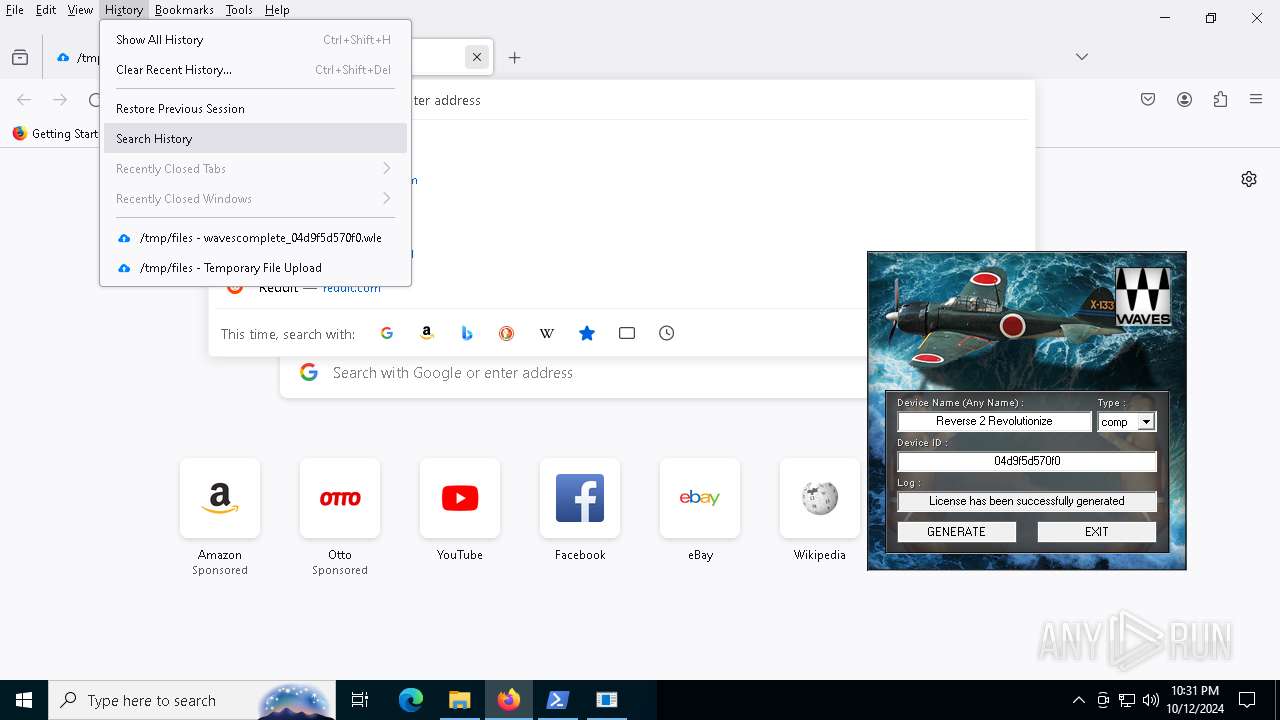
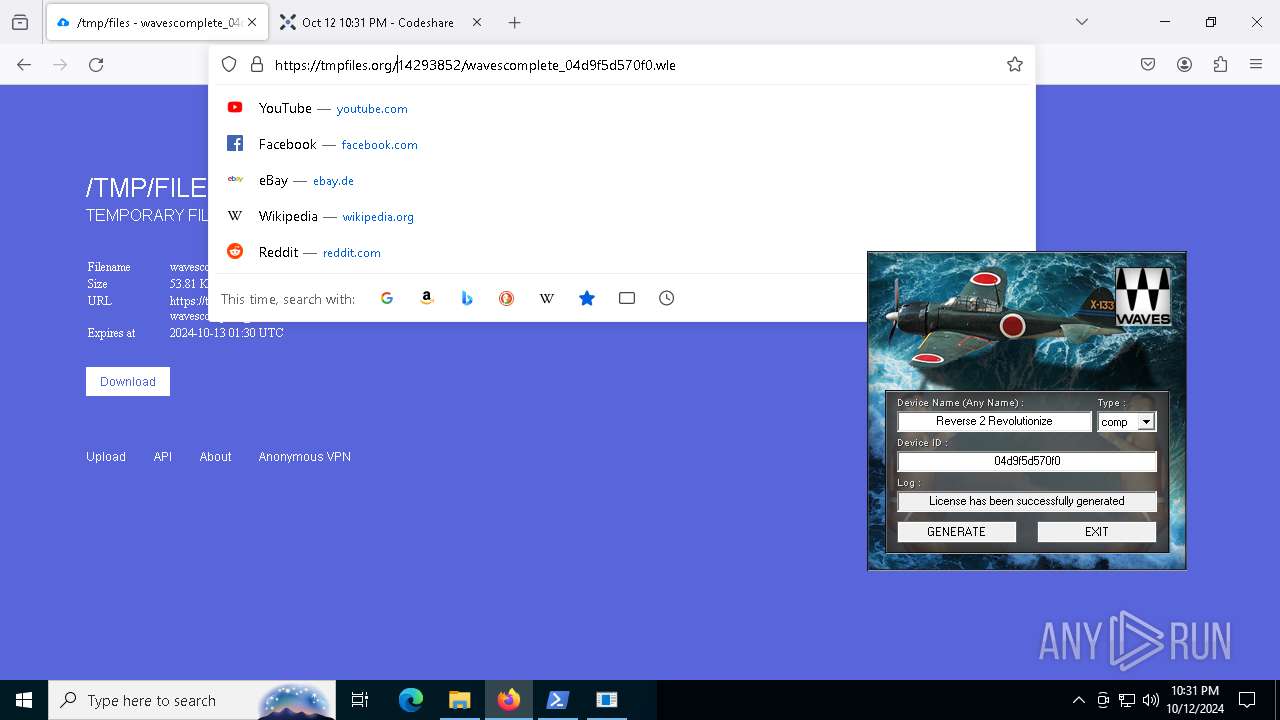
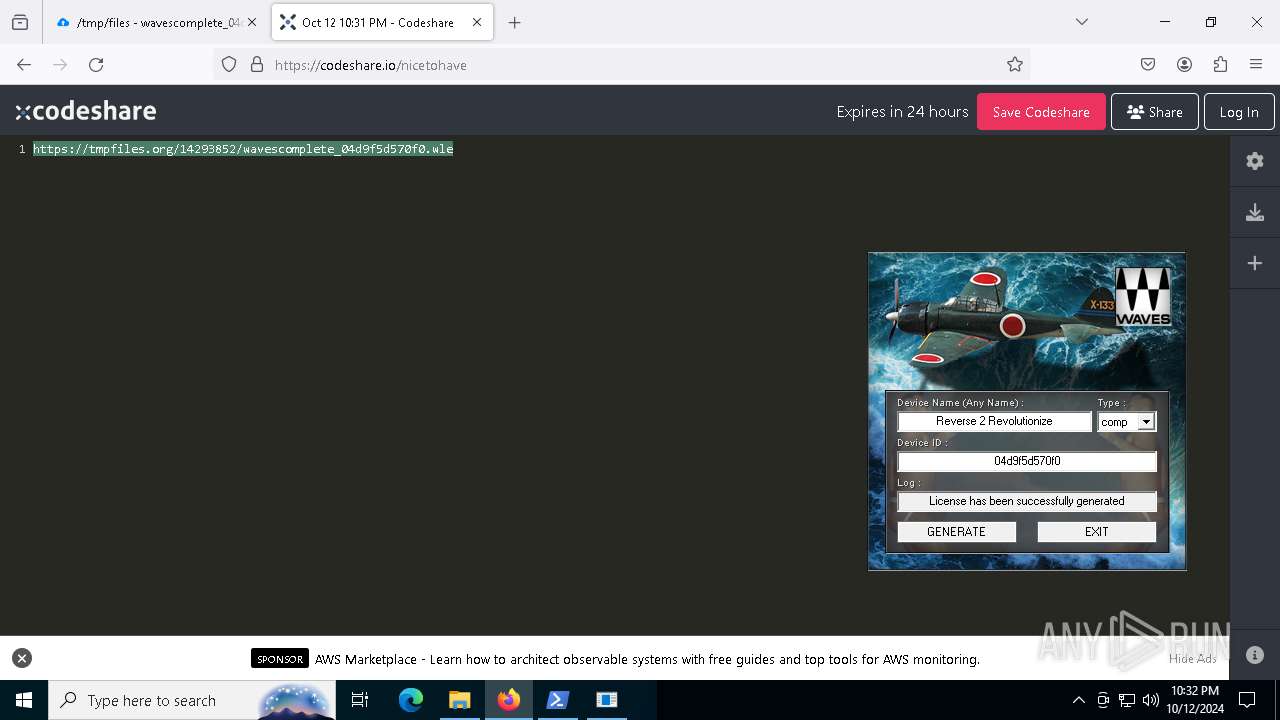
2172 | svchost.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
2172 | svchost.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
2172 | svchost.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
3912 | firefox.exe | Misc activity | ET INFO Observed Temporary File Hosting Domain (tmpfiles .org in TLS SNI) |
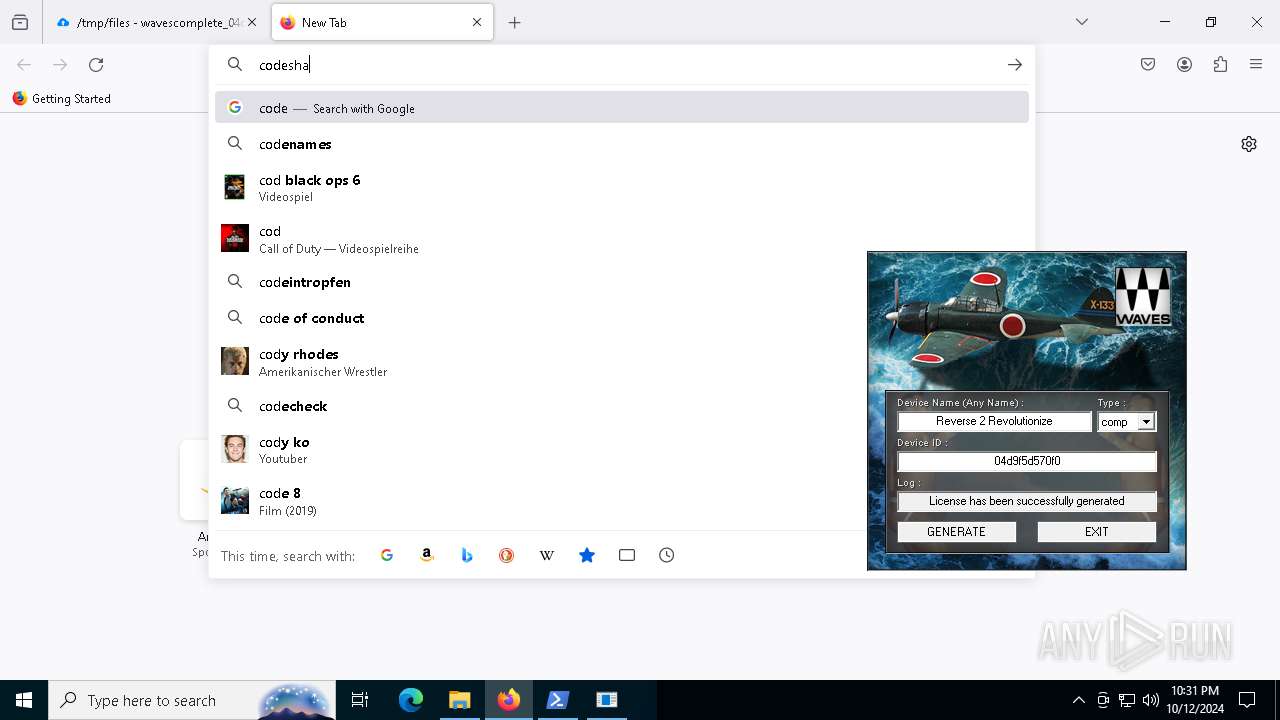
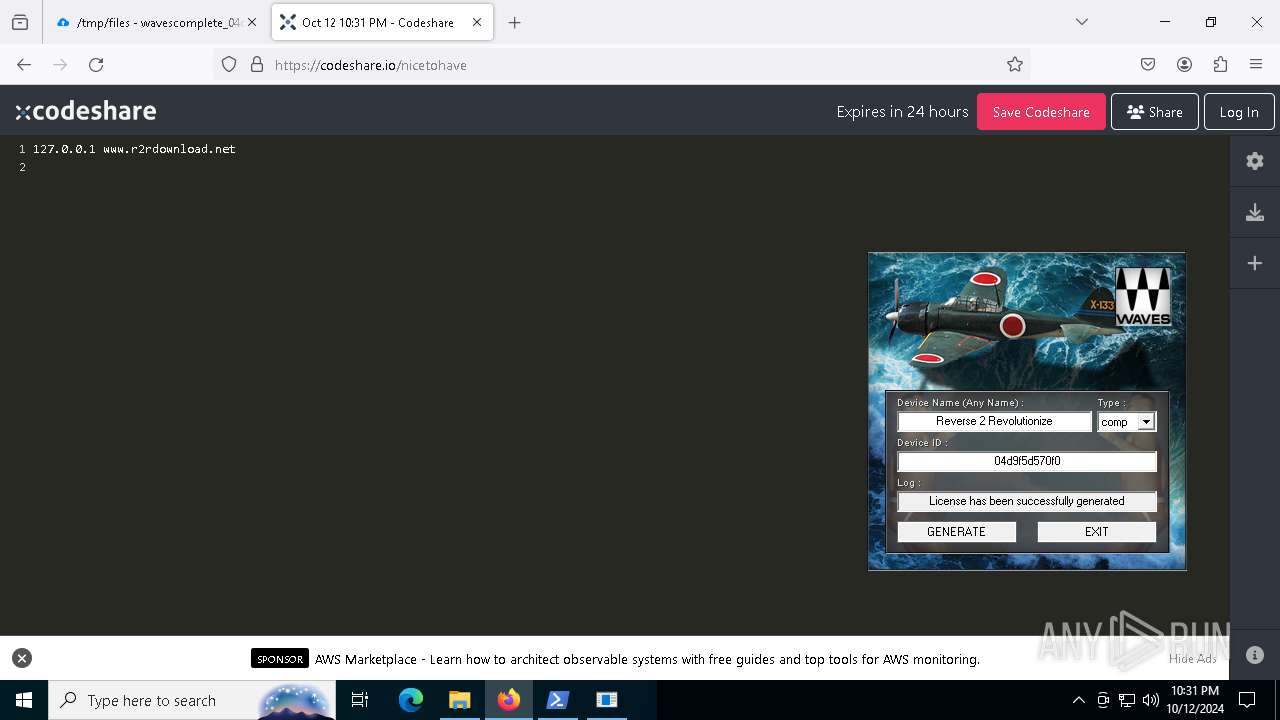
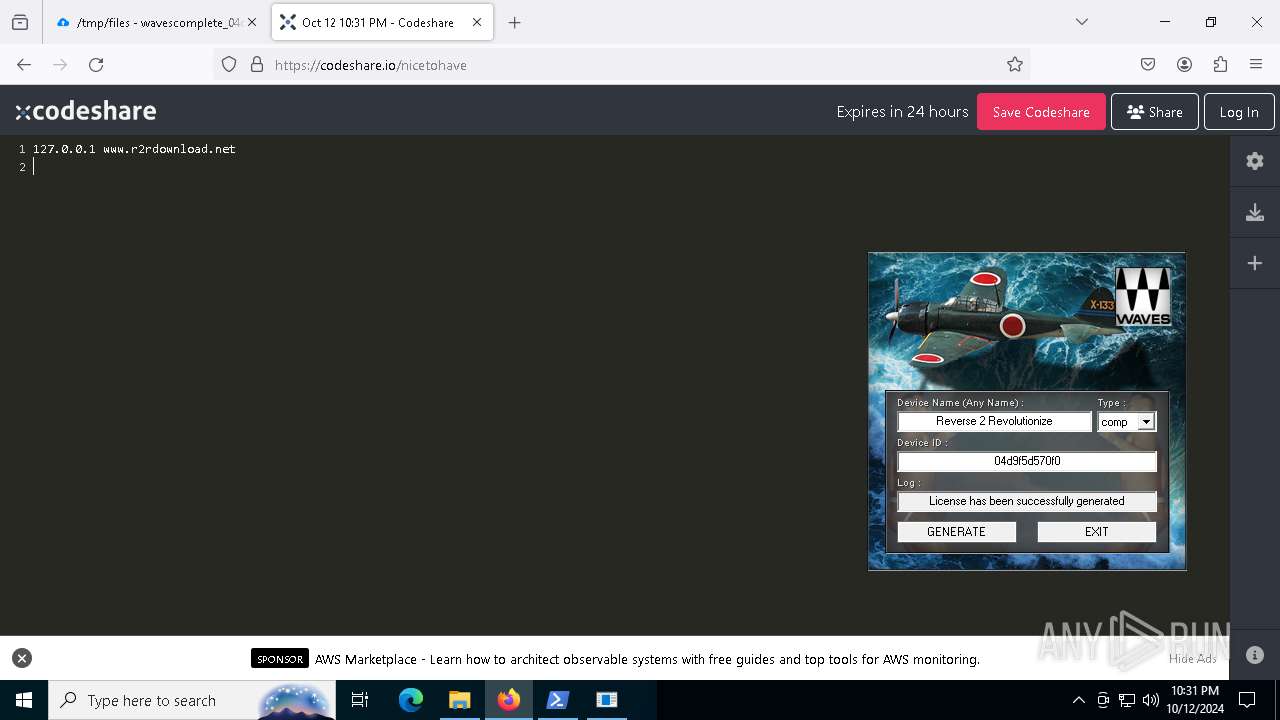
2172 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (codeshare .io) |
2172 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (codeshare .io) |
2172 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (codeshare .io) |
3912 | firefox.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (codeshare .io) in TLS SNI |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |