| File name: | db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe |
| Full analysis: | https://app.any.run/tasks/96099859-7627-4144-928c-20f63456a31d |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 07:35:42 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | FD6A372E2AEF6D3A304EE47BE4DF5C66 |
| SHA1: | 168CFA40A4AE5B7CDD64233ED39889CA1713F010 |
| SHA256: | DB15F45F69F863510986FB2198A8A6B3D55D8CCC8A2ED4BB30BC27BDD1BF151C |
| SSDEEP: | 98304:N+mFhZnDGSPRRGpBnmnTFrel3pu7QqAXbQyJbqiKta3FhbOXXrazR:wbH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe (PID: 2036)
Starts itself from another location
- db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe (PID: 2036)
There is functionality for taking screenshot (YARA)
- Kaspersky.exe (PID: 4696)
Connects to unusual port
- Kaspersky.exe (PID: 4696)
INFO
Checks supported languages
- db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe (PID: 2036)
- Kaspersky.exe (PID: 4696)
The sample compiled with chinese language support
- db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe (PID: 2036)
Creates files or folders in the user directory
- db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe (PID: 2036)
- Kaspersky.exe (PID: 4696)
Reads the computer name
- Kaspersky.exe (PID: 4696)
Potential library load (Base64 Encoded 'LoadLibrary')
- Kaspersky.exe (PID: 4696)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- Kaspersky.exe (PID: 4696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (78.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (11.3) |
| .exe | | | Generic Win/DOS Executable (5) |
| .exe | | | DOS Executable Generic (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:21 12:42:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 2074624 |
| InitializedDataSize: | 1336320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ad31d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | |
| FileVersion: | 2, 0, 0, 0 |
| LegalCopyright: | 版权所有 (C) 2025 |
| ProductVersion: | 2, 0, 0, 0 |
Total processes
104
Monitored processes
3
Malicious processes
2
Suspicious processes
0
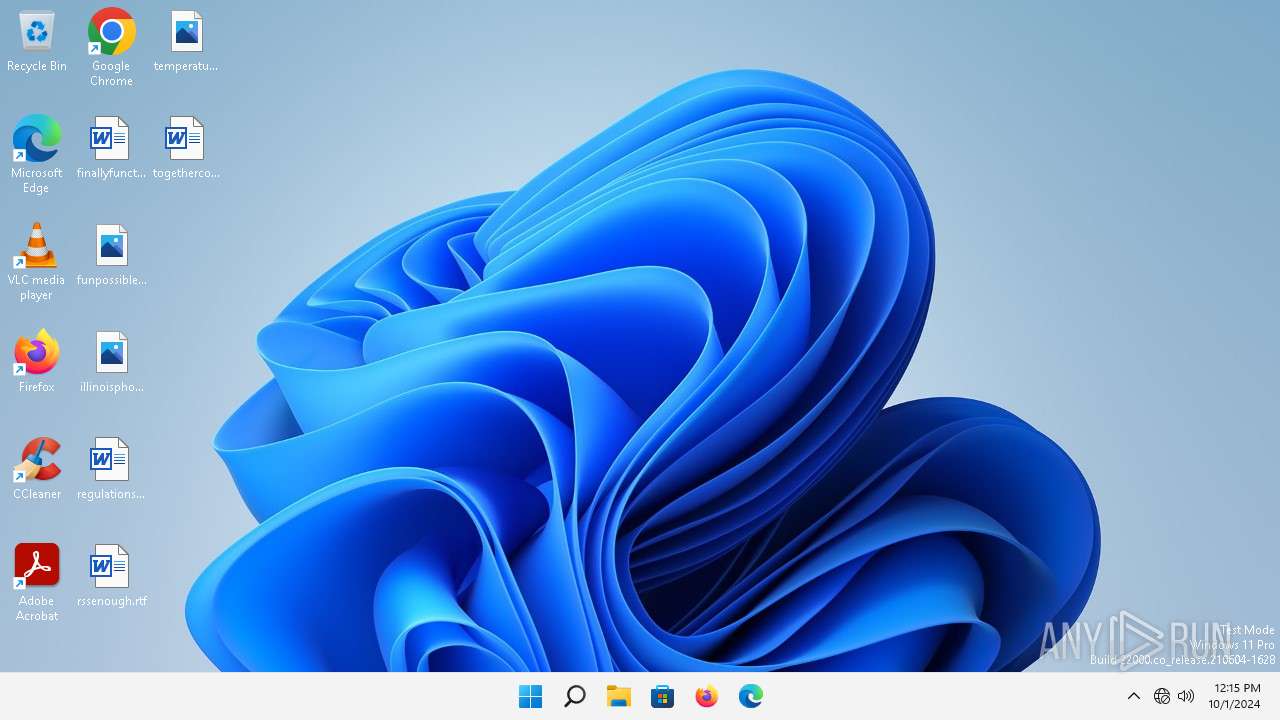
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\Users\admin\AppData\Local\Temp\db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe" | C:\Users\admin\AppData\Local\Temp\db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\AppData\Local\KasperskyServer.exe" | C:\Users\admin\AppData\Local\KasperskyServer.exe | — | db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4696 | "C:\Users\admin\AppData\Local\Kaspersky.exe" | C:\Users\admin\AppData\Local\Kaspersky.exe | db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe | ||||||||||||
User: admin Company: Google Integrity Level: MEDIUM Version: 2, 0, 0, 0 Modules
| |||||||||||||||
Total events
194
Read events
194
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe | C:\Users\admin\AppData\Local\KasperskyServer.exe | executable | |
MD5:32C72E872A5F2E890A6B7E3476298436 | SHA256:1D7C83E0182D3F0EDB5848B6A1FF5E2796715AEAFCA5CBF4BA0BA5CBA777A558 | |||
| 4696 | Kaspersky.exe | C:\Users\admin\AppData\Local\line.dat | text | |
MD5:08E34BE8D2D7F3E14AC4574053B7564C | SHA256:6AE7D1CC3D39A37241CE615F12256083E4620D6EDB1169F76868E872FED2AC69 | |||
| 2036 | db15f45f69f863510986fb2198a8a6b3d55d8ccc8a2ed4bb30bc27bdd1bf151c.exe | C:\Users\admin\AppData\Local\Kaspersky.exe | executable | |
MD5:FD6A372E2AEF6D3A304EE47BE4DF5C66 | SHA256:DB15F45F69F863510986FB2198A8A6B3D55D8CCC8A2ED4BB30BC27BDD1BF151C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
150
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | smartscreen.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2564 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5285eed922150247 | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 23.53.42.66:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?95ffe5009287b7a1 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?74f19306e9a7f92f | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?2108c32fe6310541 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e99424fd8905572e | unknown | — | — | whitelisted |
2988 | OfficeClickToRun.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | smartscreen.exe | 4.209.164.61:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2564 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2564 | smartscreen.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1352 | svchost.exe | 23.53.42.64:80 | — | Akamai International B.V. | DE | unknown |
4696 | Kaspersky.exe | 206.238.115.207:18088 | — | TERAEXCH | ZA | unknown |
2412 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2776 | svchost.exe | 52.182.141.63:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |