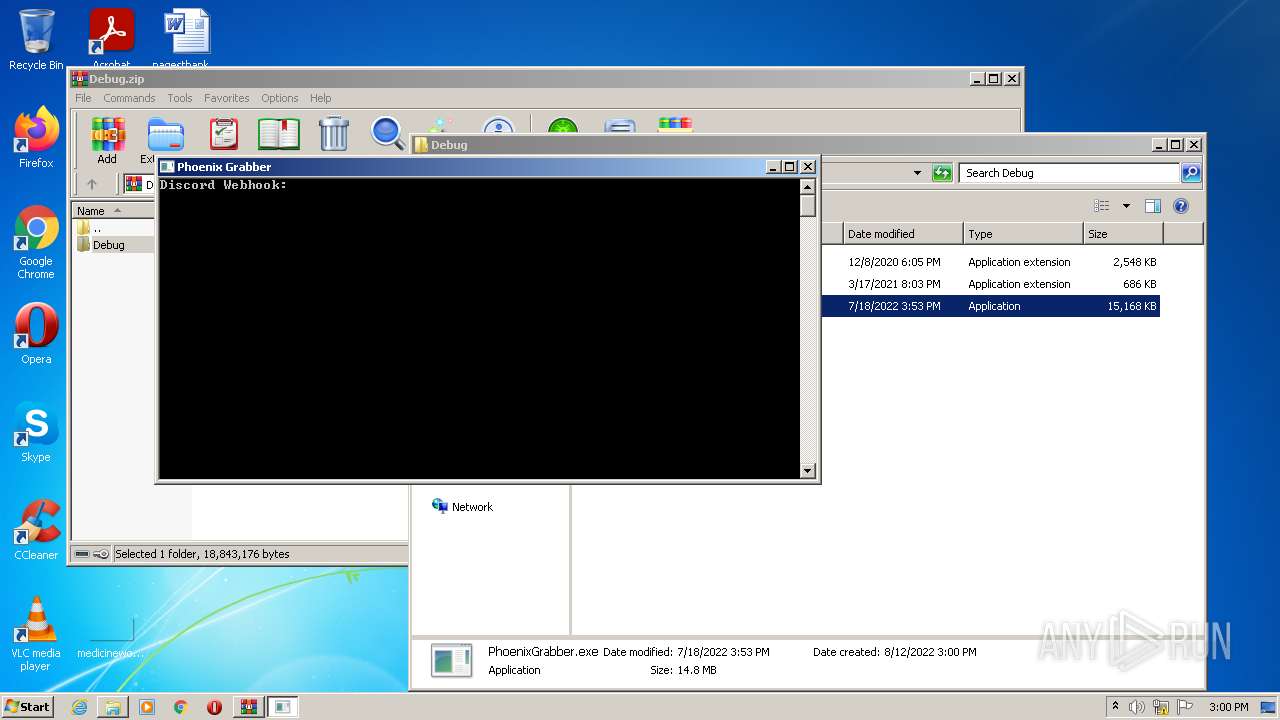
| File name: | Debug.zip |
| Full analysis: | https://app.any.run/tasks/044ef2f7-b5fd-4414-9dec-cc6c5e597817 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 14:00:13 |
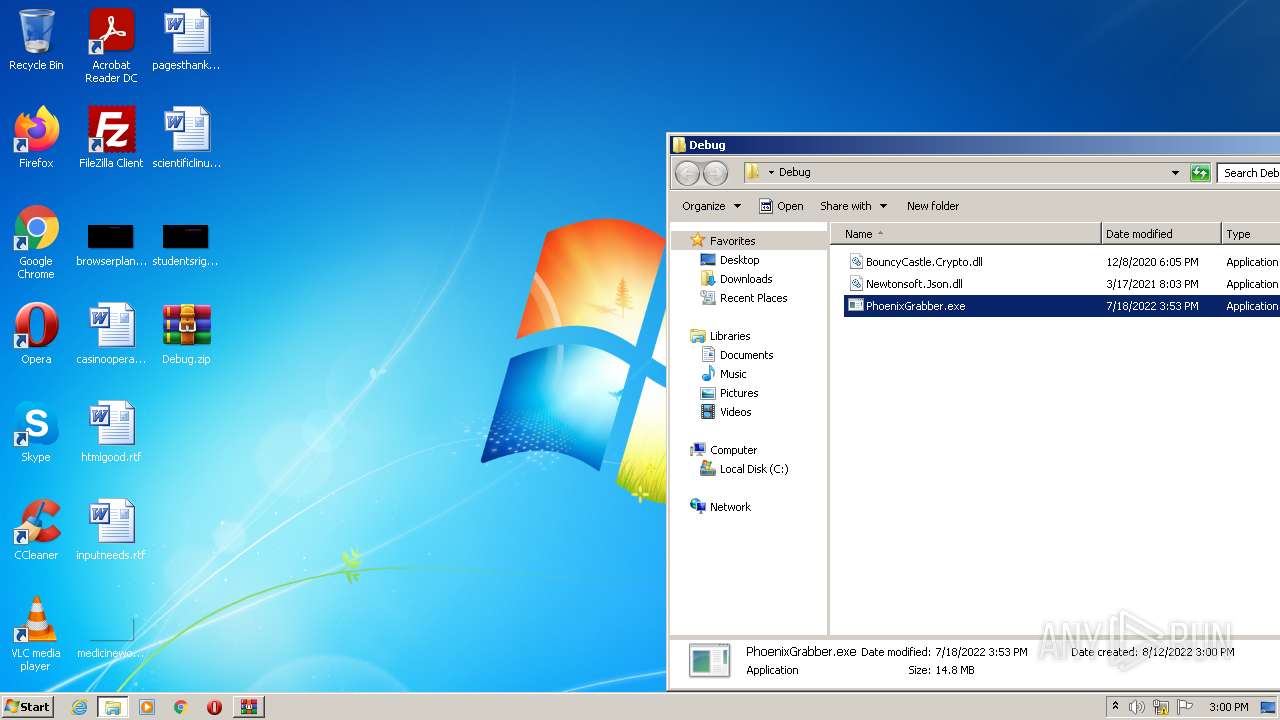
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 946A382AE0DA6182C483651785CCF4BC |
| SHA1: | 4CA91B3477330919E3D984E533DD06A49CD2827F |
| SHA256: | DB0FA2E172995EE6E16038332C69A83B76B70B798B70918960E47E8331FE91D6 |
| SSDEEP: | 393216:QTe7x/9tB0F6lG/y1Tk5KobJ7iWPiP5MPTyoW71HxVi2RwQB0gPBIU:QTe7x/9tB0Ecy1TkkgiWqxyW71Rg2BIU |
MALICIOUS
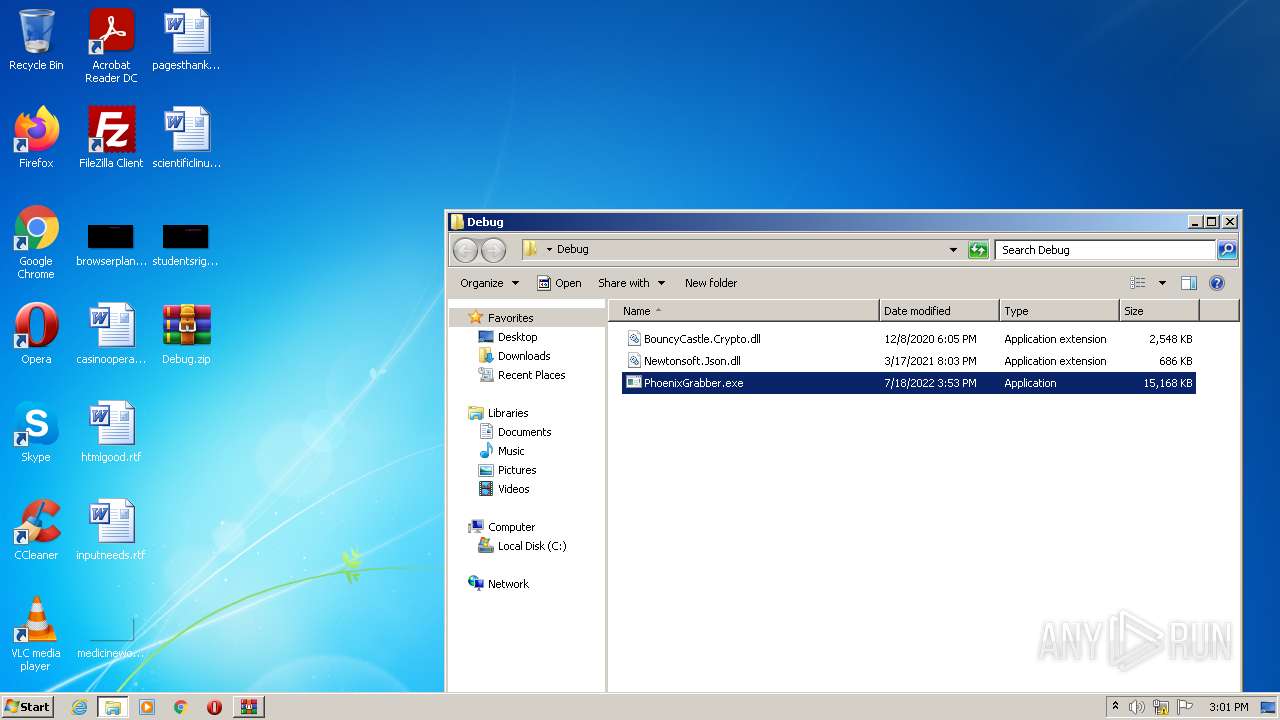
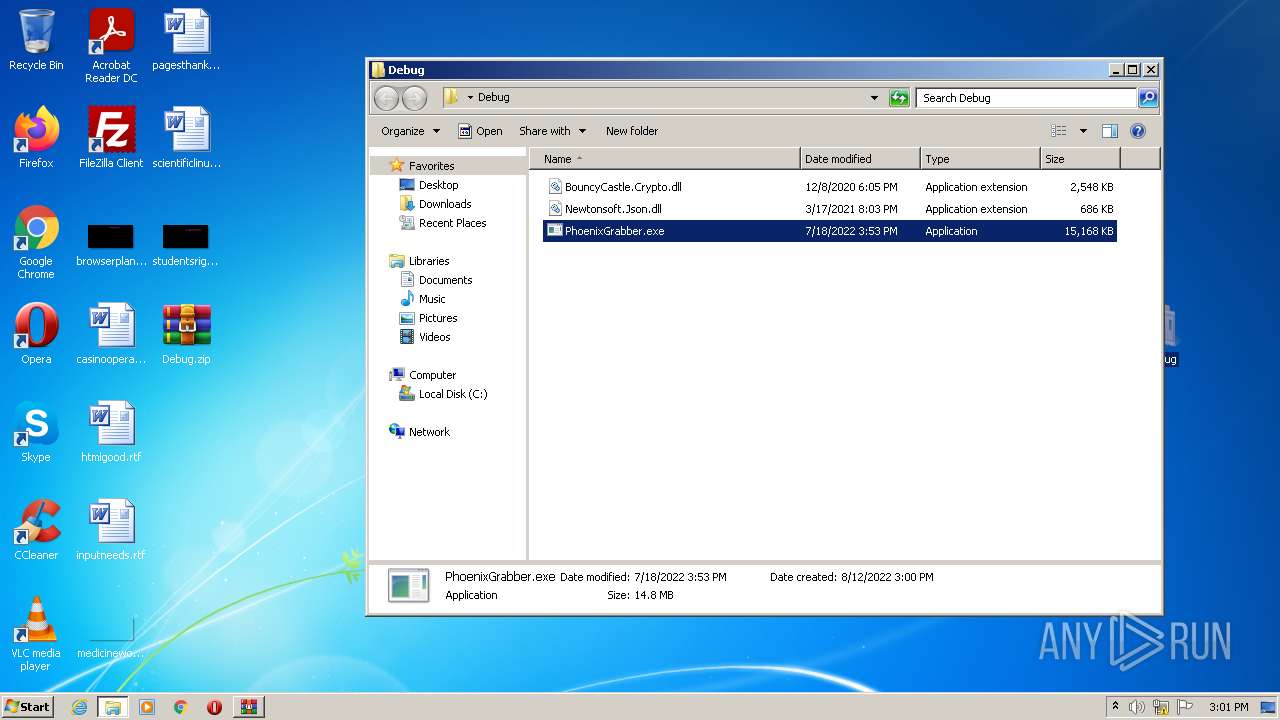
Drops executable file immediately after starts
- WinRAR.exe (PID: 3864)
- csc.exe (PID: 2232)
- PhoenixGrabber.exe (PID: 3028)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3796)
Application was dropped or rewritten from another process
- PhoenixGrabber.exe (PID: 3028)
Starts Visual C# compiler
- PhoenixGrabber.exe (PID: 3028)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3864)
- csc.exe (PID: 2232)
- PhoenixGrabber.exe (PID: 3028)
Checks supported languages
- WinRAR.exe (PID: 3864)
- PhoenixGrabber.exe (PID: 3028)
- csc.exe (PID: 2232)
- cvtres.exe (PID: 2468)
- cmd.exe (PID: 2800)
Reads the computer name
- WinRAR.exe (PID: 3864)
- PhoenixGrabber.exe (PID: 3028)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3864)
- csc.exe (PID: 2232)
- PhoenixGrabber.exe (PID: 3028)
INFO
Manual execution by user
- PhoenixGrabber.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
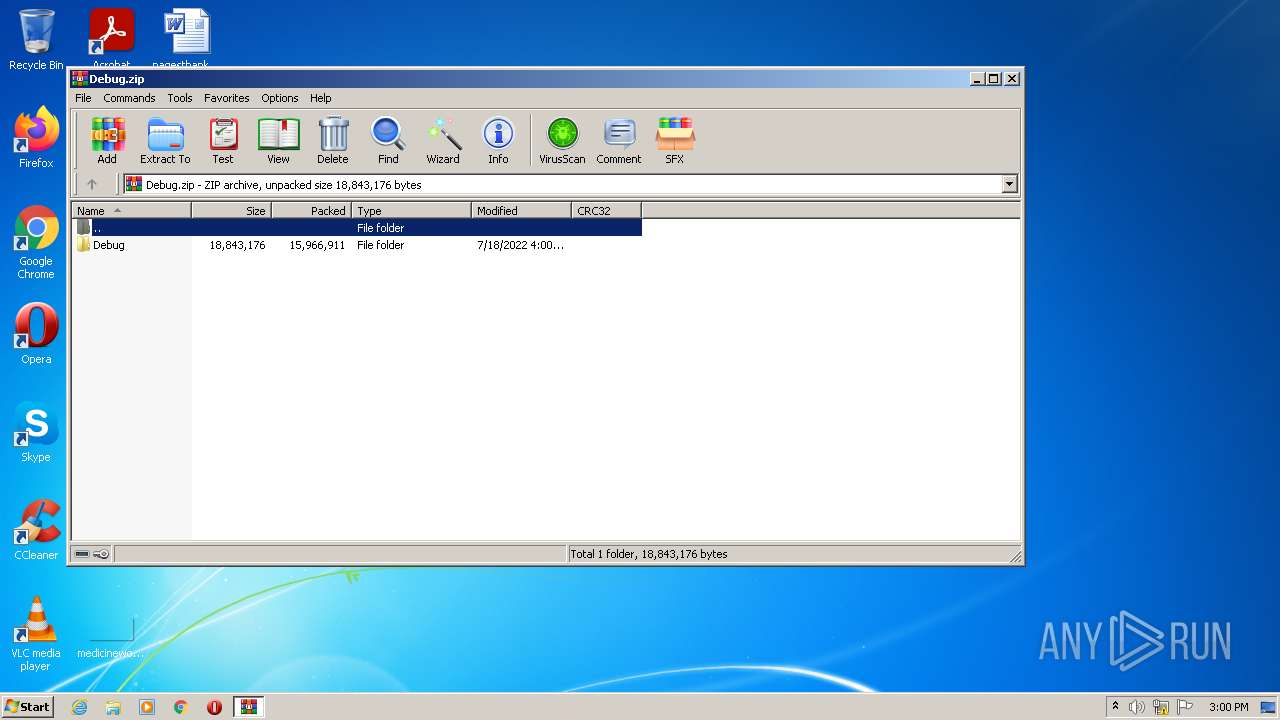
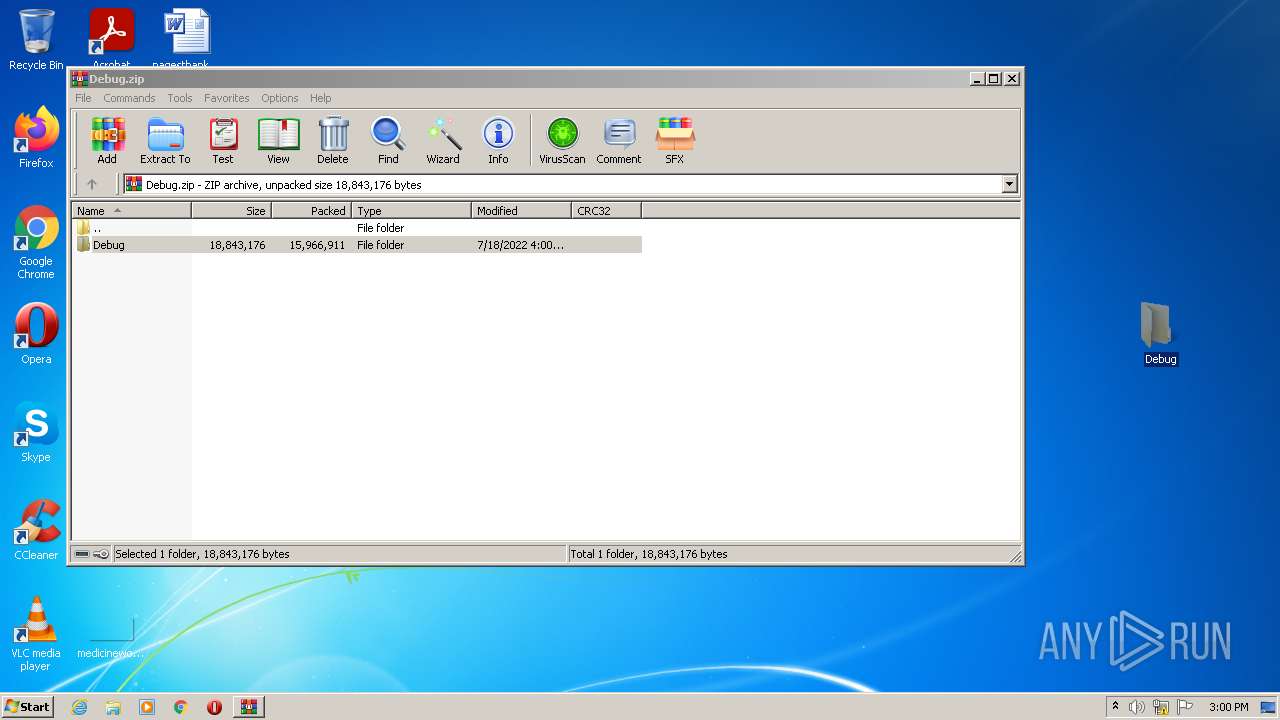
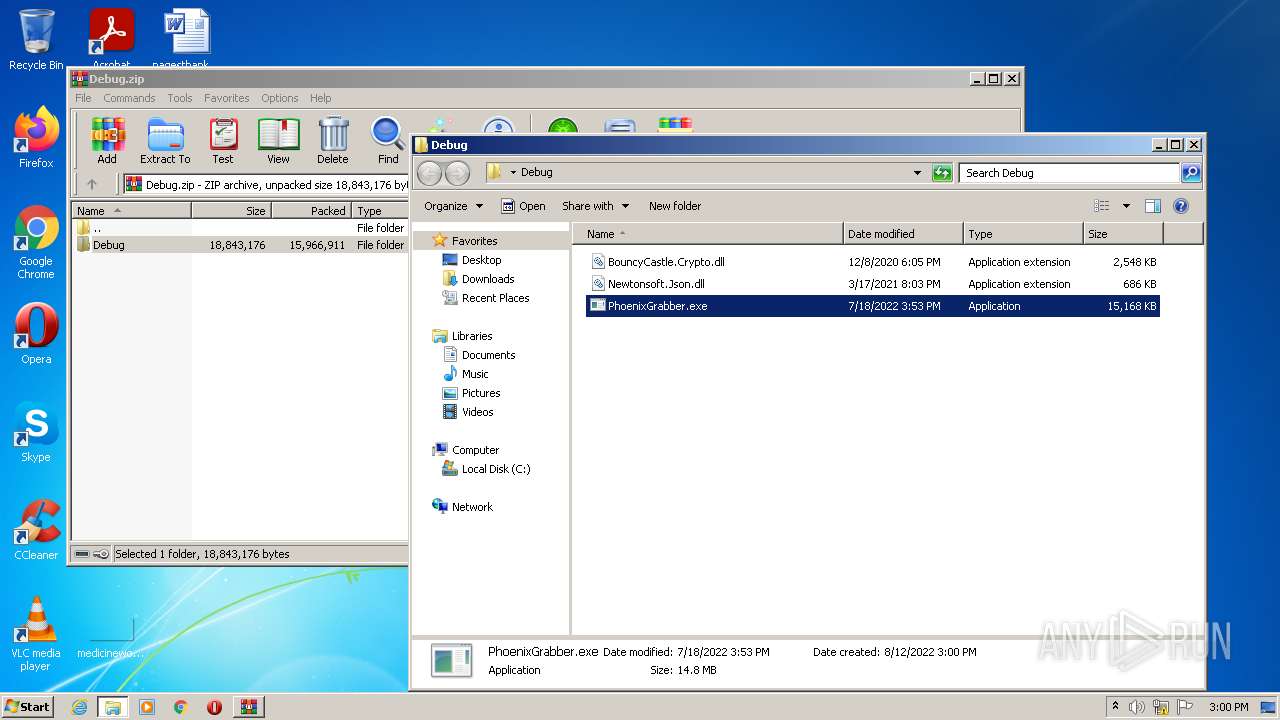
| ZipFileName: | Debug/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:07:18 18:00:04 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2232 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ecgmmevk.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | PhoenixGrabber.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2468 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB7BF.tmp" "c:\Users\admin\AppData\Local\Temp\CSCDB86F5FA66754CB0B667E6B8A52DDB1C.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.51209.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2800 | "C:\Windows\System32\cmd.exe" /C VMProtect_Con C:\Users\admin\AppData\Local\Temp\\lol.exe C:\Users\admin\Desktop\Debug\lol.exe | C:\Windows\System32\cmd.exe | — | PhoenixGrabber.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\Desktop\Debug\PhoenixGrabber.exe" | C:\Users\admin\Desktop\Debug\PhoenixGrabber.exe | Explorer.EXE | ||||||||||||
User: admin Company: extatent Integrity Level: MEDIUM Description: Phoenix Grabber Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3796 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3864 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Debug.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 128
Read events
2 110
Write events
18
Delete events
0
Modification events
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Debug.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
5
Suspicious files
0
Text files
3
Unknown types
2
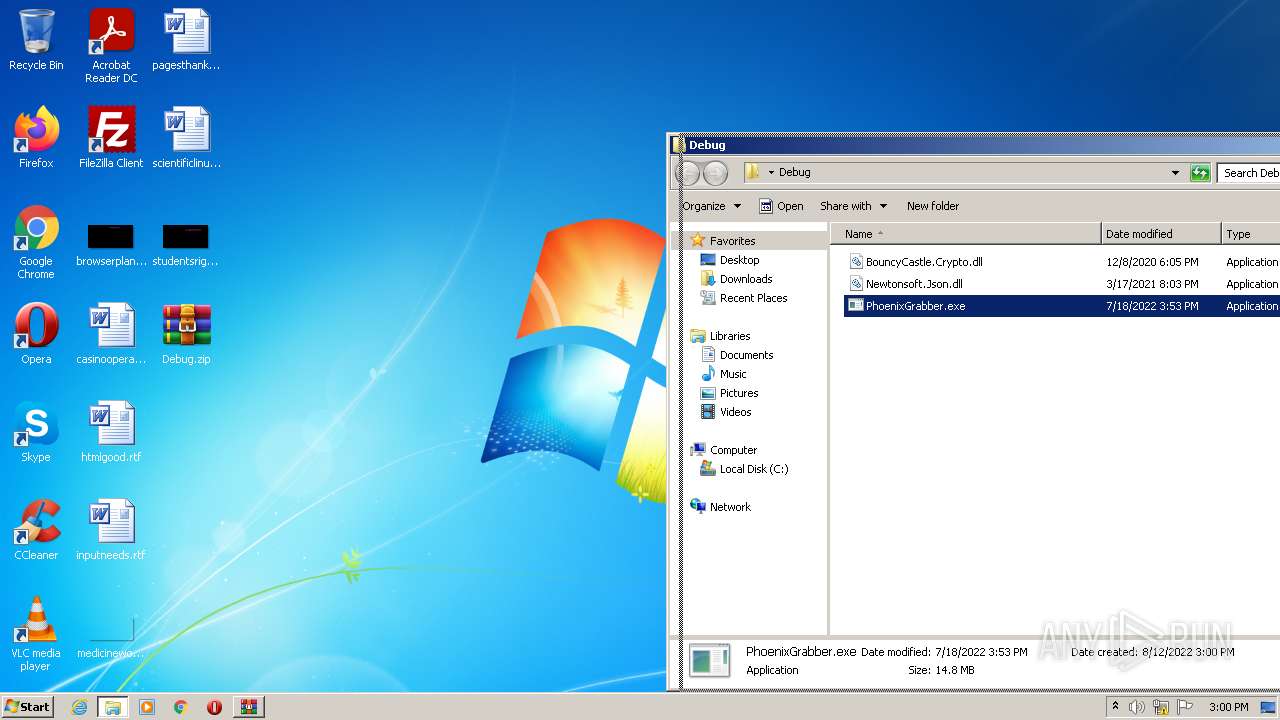
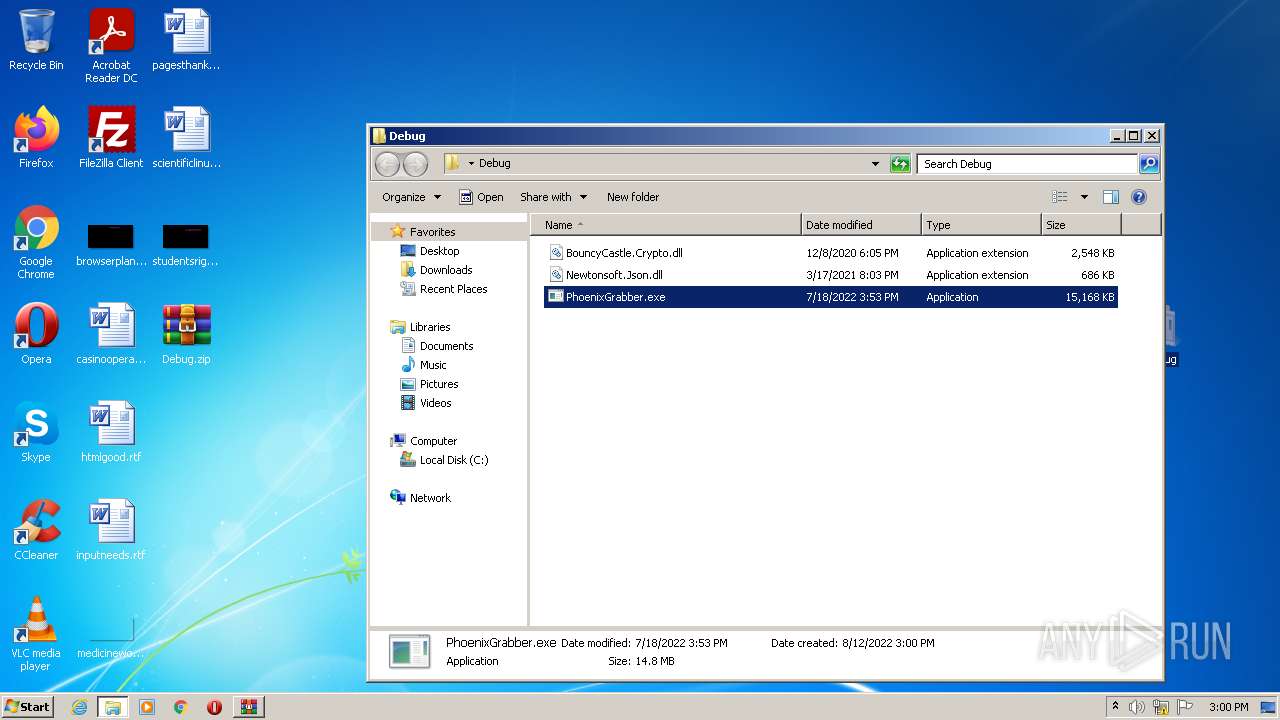
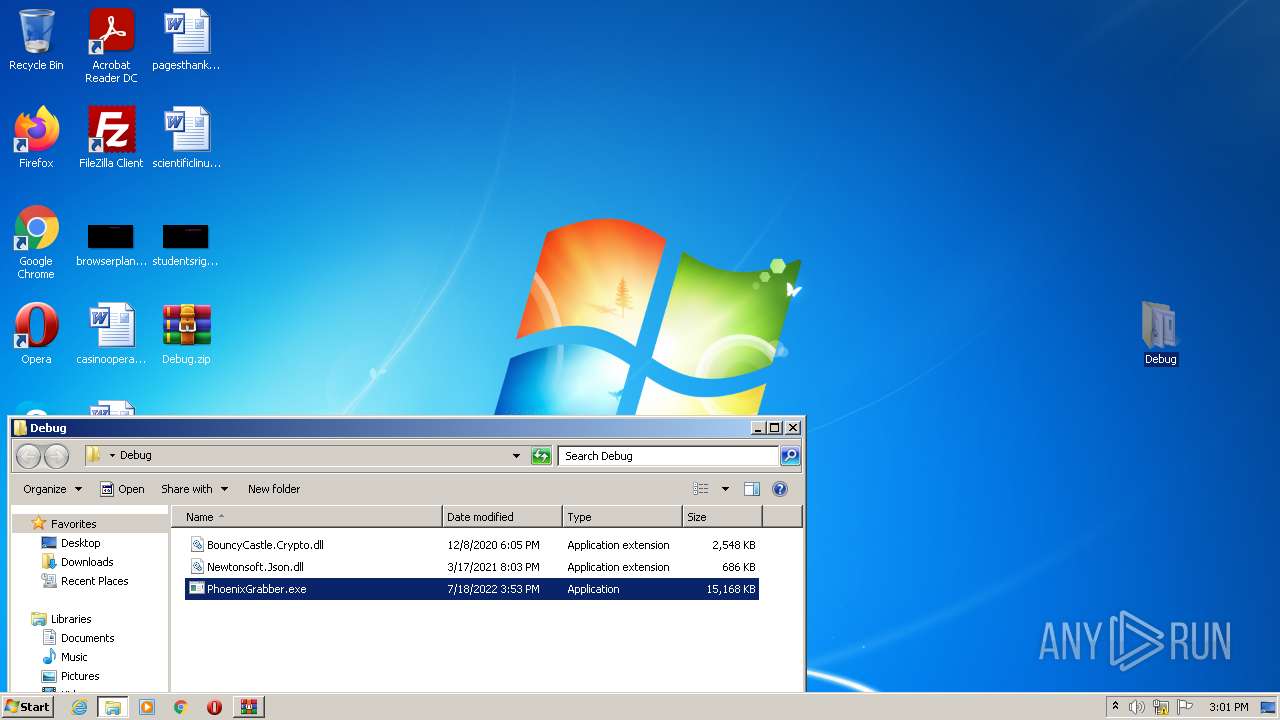
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | PhoenixGrabber.exe | C:\Users\admin\AppData\Local\Temp\ecgmmevk.0.cs | text | |
MD5:— | SHA256:— | |||
| 3028 | PhoenixGrabber.exe | C:\Users\admin\AppData\Local\Temp\ecgmmevk.cmdline | text | |
MD5:— | SHA256:— | |||
| 2232 | csc.exe | C:\Users\admin\AppData\Local\Temp\lol.exe | executable | |
MD5:— | SHA256:— | |||
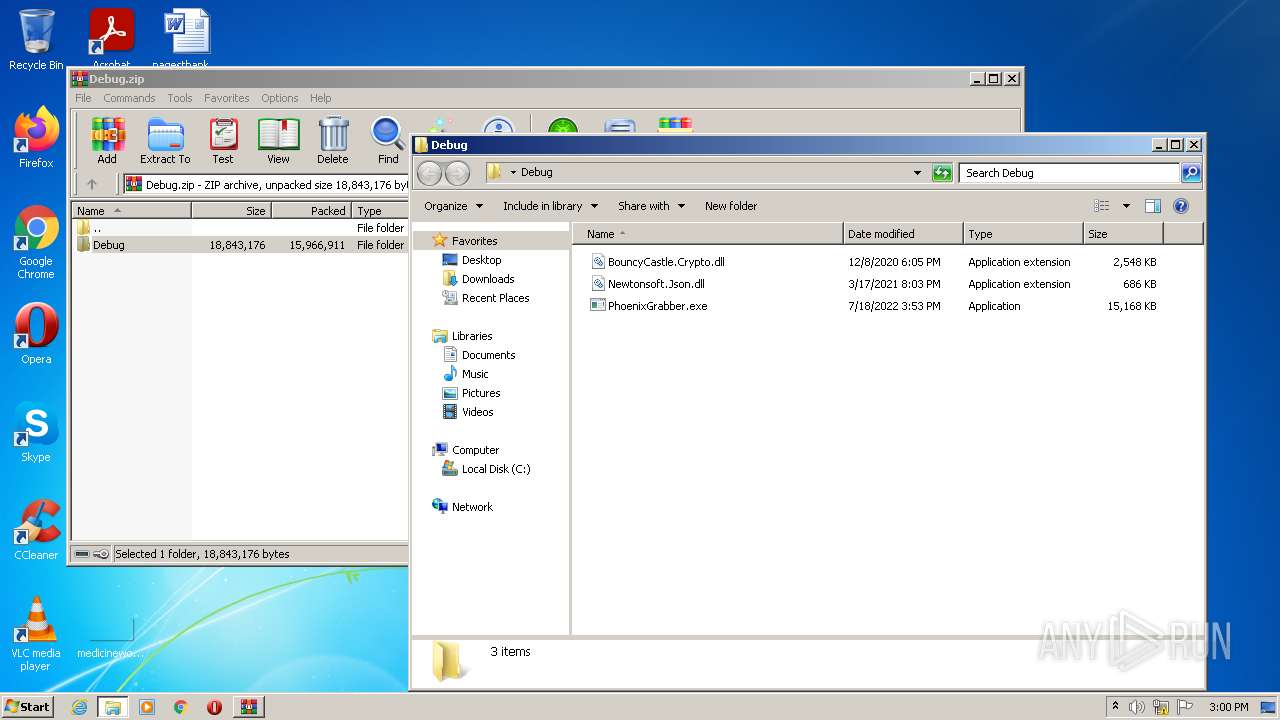
| 3864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3864.48378\Debug\PhoenixGrabber.exe | executable | |
MD5:— | SHA256:— | |||
| 3864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3864.48378\Debug\BouncyCastle.Crypto.dll | executable | |
MD5:F0B3E112CE4807A28E2B5D66A840ED7F | SHA256:333903C7D22A27098E45FC64B77A264AA220605CFBD3E329C200D7E4B42C881C | |||
| 2468 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESB7BF.tmp | o | |
MD5:— | SHA256:— | |||
| 2232 | csc.exe | C:\Users\admin\AppData\Local\Temp\ecgmmevk.out | text | |
MD5:— | SHA256:— | |||
| 3864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3864.48378\Debug\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 3028 | PhoenixGrabber.exe | C:\Users\admin\AppData\Local\Temp\VMProtect_Con.exe | executable | |
MD5:49FBD72C3A4AF4000E8BAFD34A5D9547 | SHA256:F3ADCB446E1A7FB713B34EA2F675CDD059473C094E1B777291443769D6B359A5 | |||
| 2232 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCDB86F5FA66754CB0B667E6B8A52DDB1C.TMP | res | |
MD5:8AE326488A7F6784DAB8B7D6E78E007E | SHA256:B2576CB40EED800BFCB9E54458A69F23656B6AD37C19FF271F98DAF9DEDBA716 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report