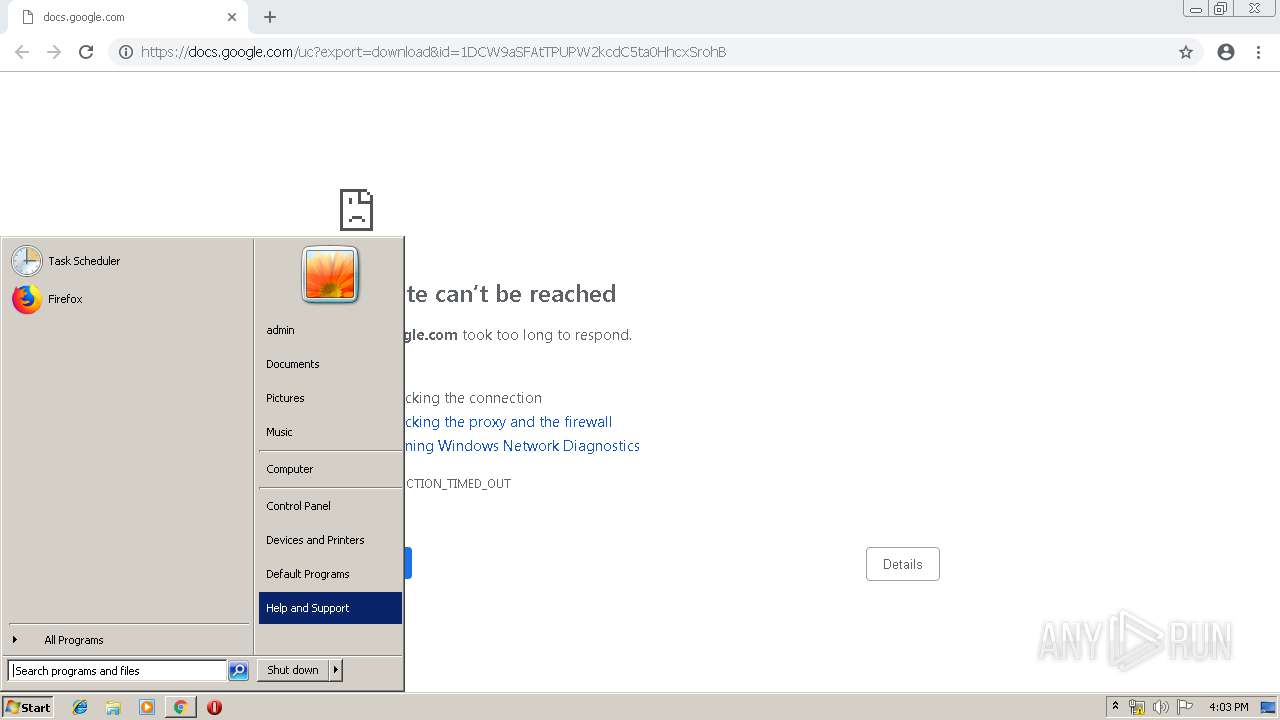
| URL: | https://docs.google.com/uc?export=download&id=1DCW9aSFAtTPUPW2kcdC5ta0HhcxSrohB |
| Full analysis: | https://app.any.run/tasks/60b0ea5b-59cd-4566-b06a-8404d74e76b4 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 15:01:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2B96638BEF22EDB5B1ACBE8AAC6C8C0E |
| SHA1: | 49E5835EDF880ECEF1983450A3952263918A0AF9 |
| SHA256: | DB0D00586F33E225E5E5BE011E3EF6374A72DA2A1AB43DA643ACF0B10265DFAD |
| SSDEEP: | 3:N8SP3u2NAaBrC2hF8ZEHnn:2Sm2BB+2hF8Zgn |
MALICIOUS
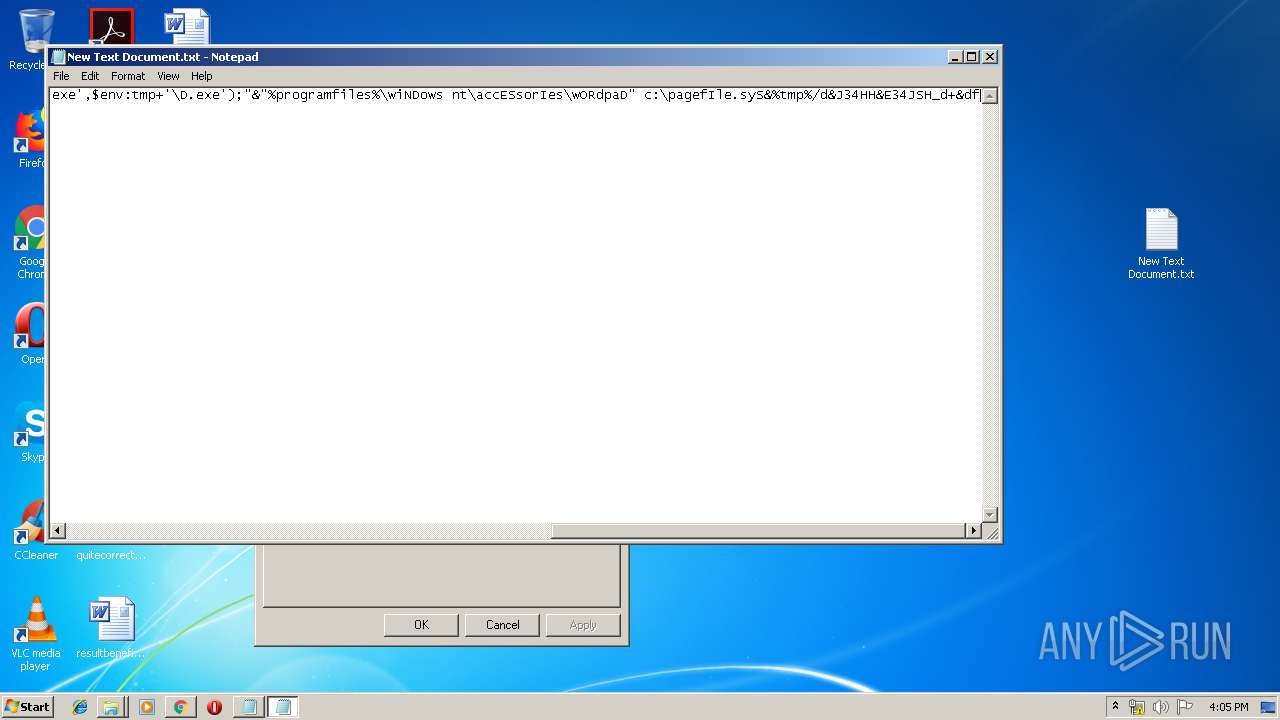
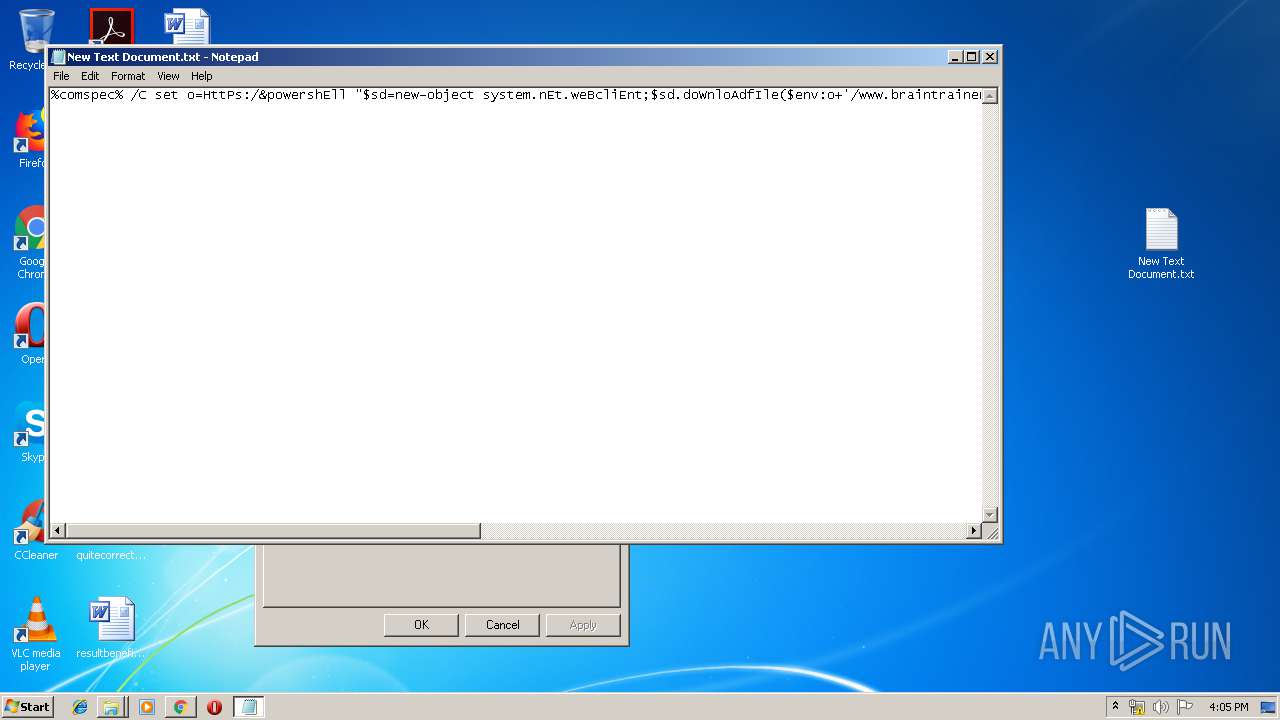
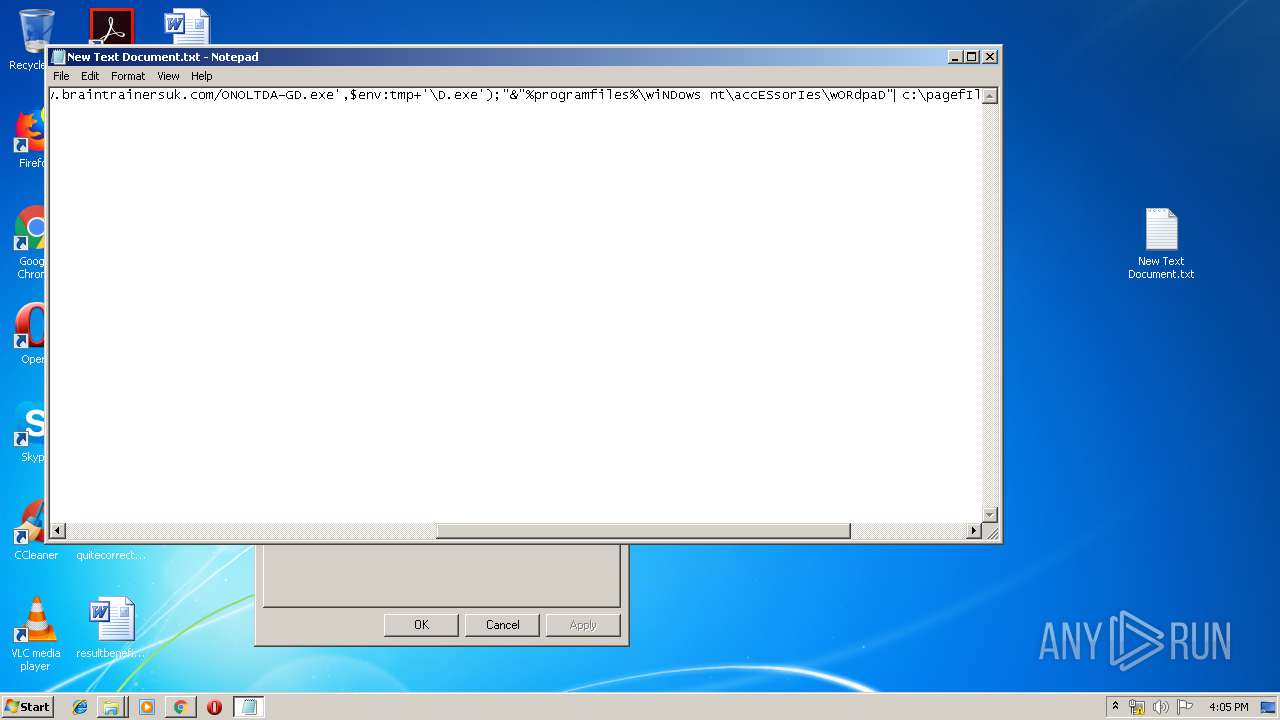
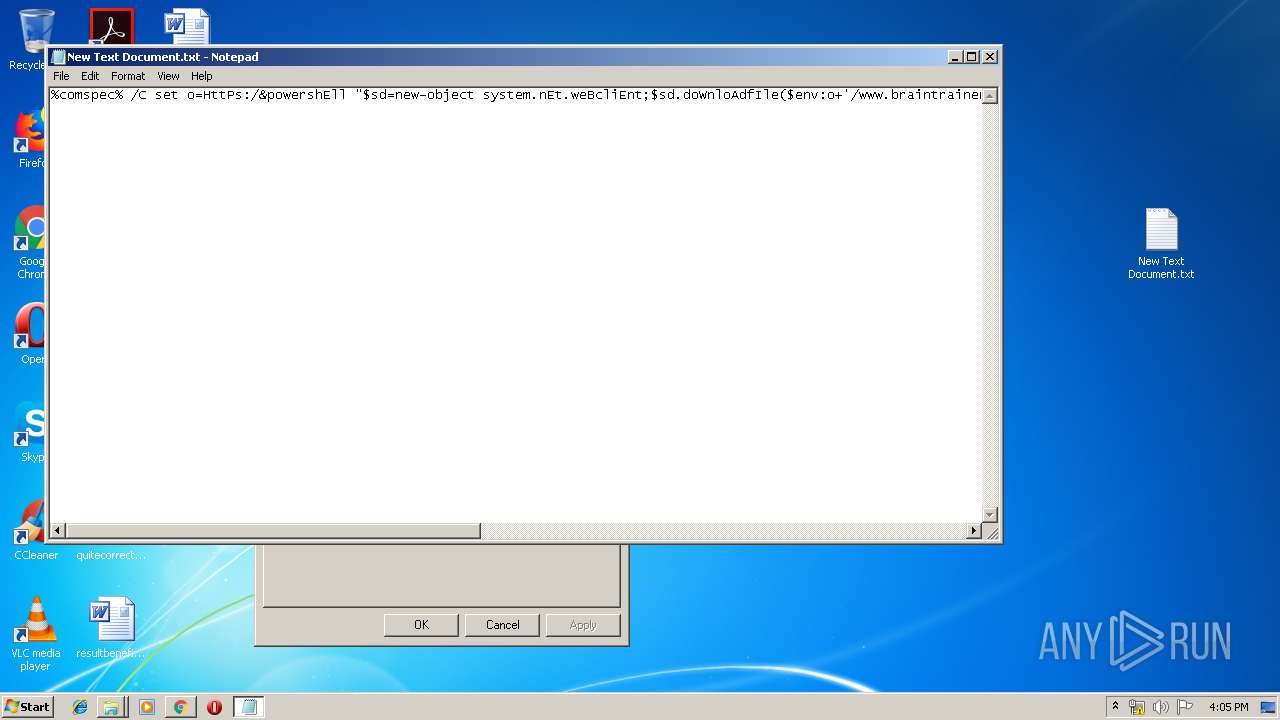
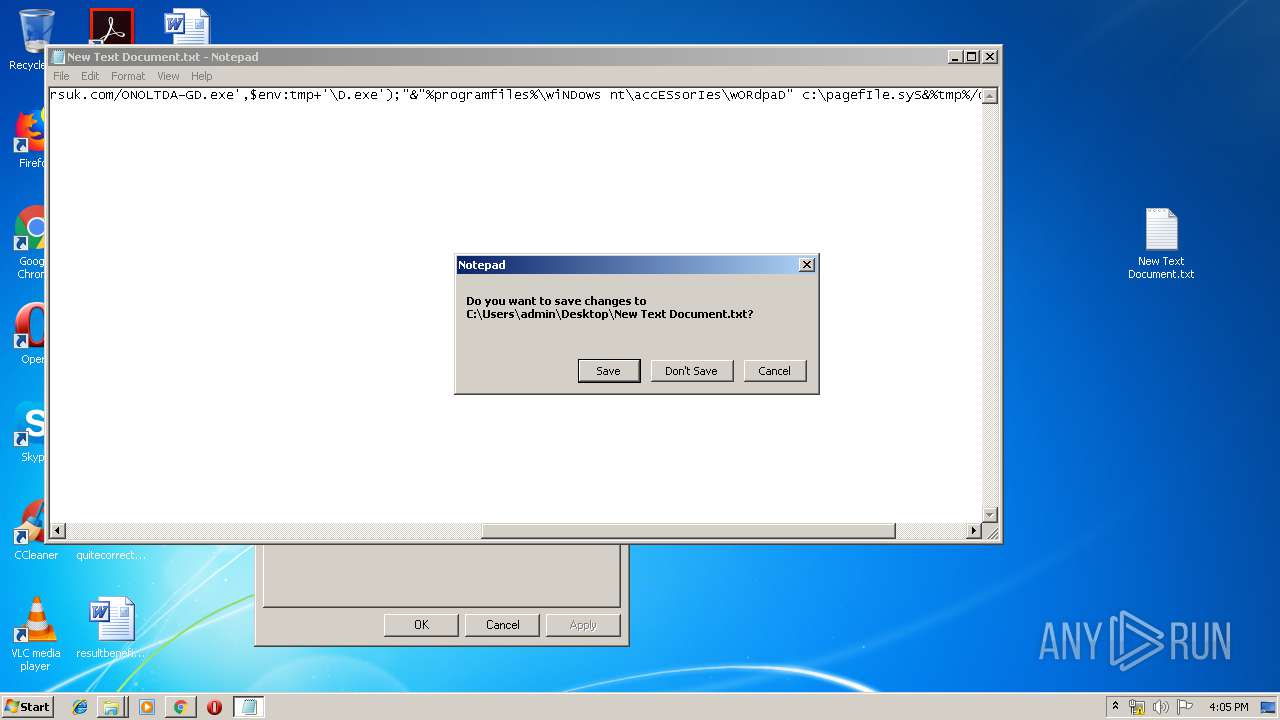
Executes PowerShell scripts
- cmd.exe (PID: 1180)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 1000)
- cmd.exe (PID: 2752)
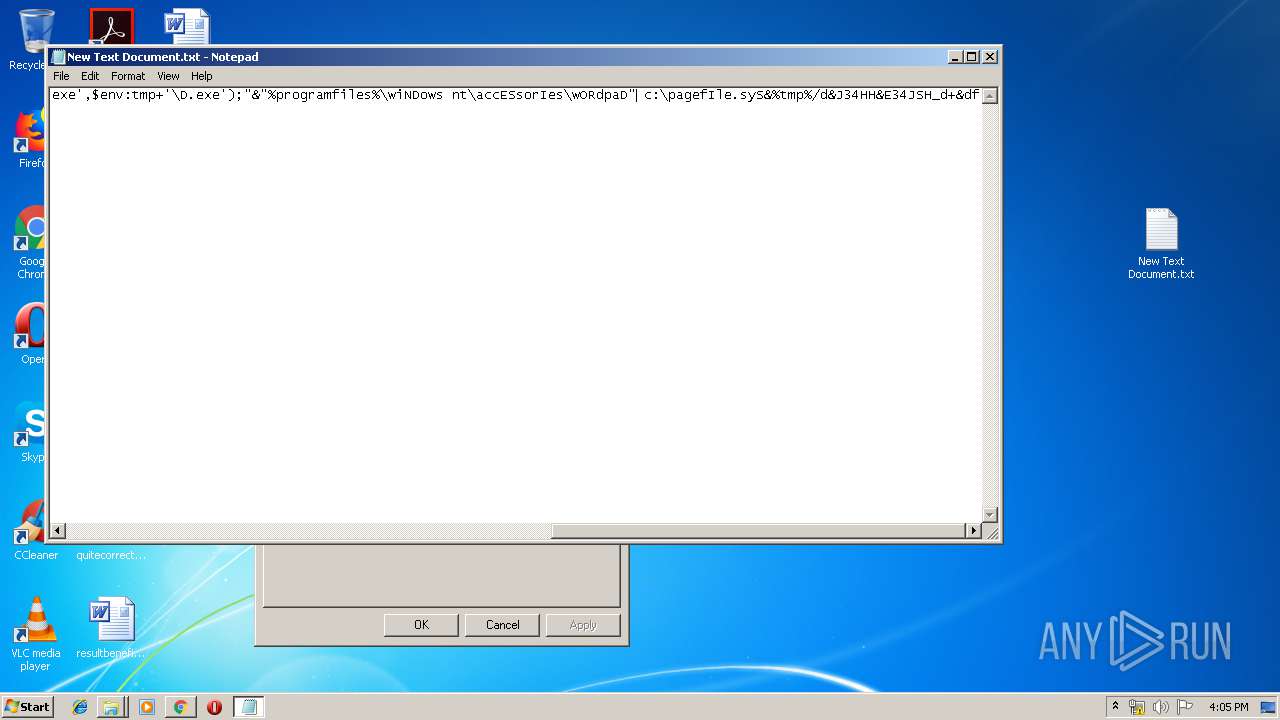
Application was dropped or rewritten from another process
- D.exe (PID: 3132)
- D.exe (PID: 1976)
- D.exe (PID: 2852)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 1904)
- cmd.exe (PID: 3356)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 596)
- cmd.exe (PID: 1004)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 1656)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 2968)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 1976)
- D.exe (PID: 2852)
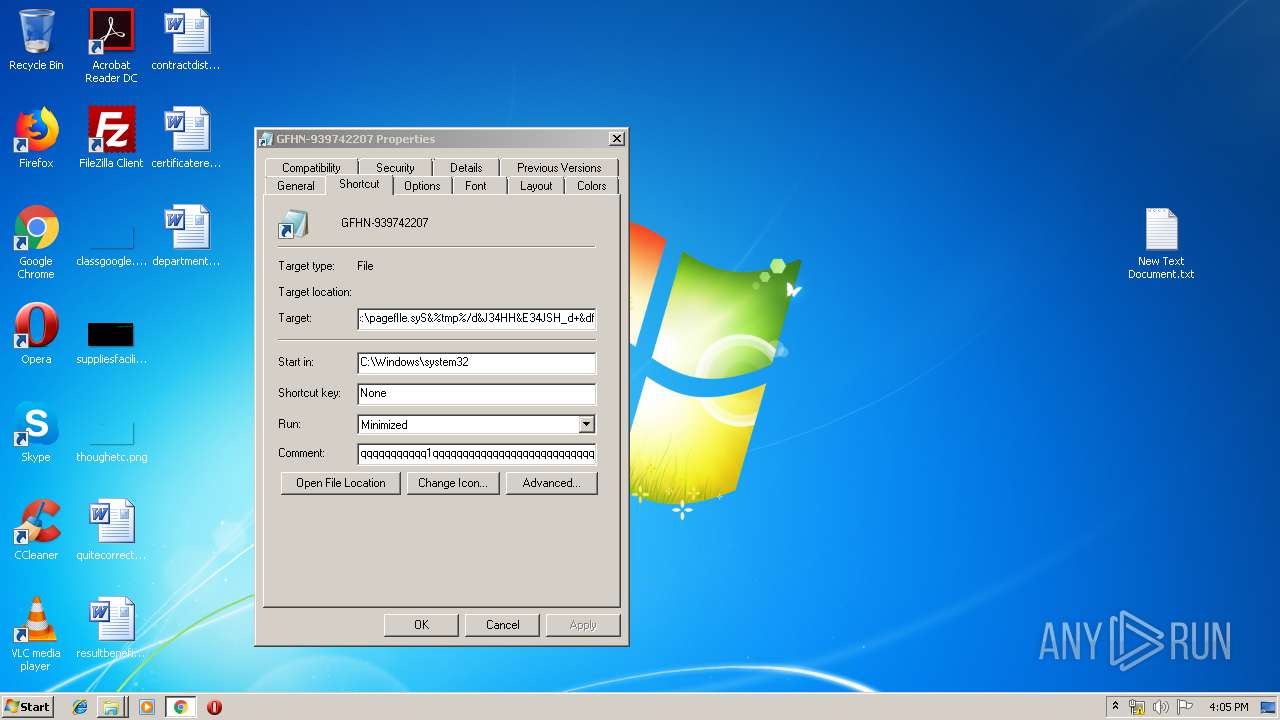
Known privilege escalation attack
- DllHost.exe (PID: 3972)
Loads the Task Scheduler COM API
- D.exe (PID: 1976)
- D.exe (PID: 2852)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1812)
Executable content was dropped or overwritten
- powershell.exe (PID: 1732)
- D.exe (PID: 1976)
Starts CMD.EXE for commands execution
- D.exe (PID: 3132)
- D.exe (PID: 1976)
- D.exe (PID: 2852)
Creates files in the user directory
- powershell.exe (PID: 1732)
- powershell.exe (PID: 1688)
- powershell.exe (PID: 860)
- powershell.exe (PID: 2744)
- powershell.exe (PID: 2536)
- D.exe (PID: 1976)
- D.exe (PID: 2852)
Executed via COM
- DllHost.exe (PID: 3972)
Executes PowerShell scripts
- cmd.exe (PID: 2624)
- cmd.exe (PID: 1240)
Executed via Task Scheduler
- D.exe (PID: 2852)
Creates files in the program directory
- D.exe (PID: 2852)
INFO
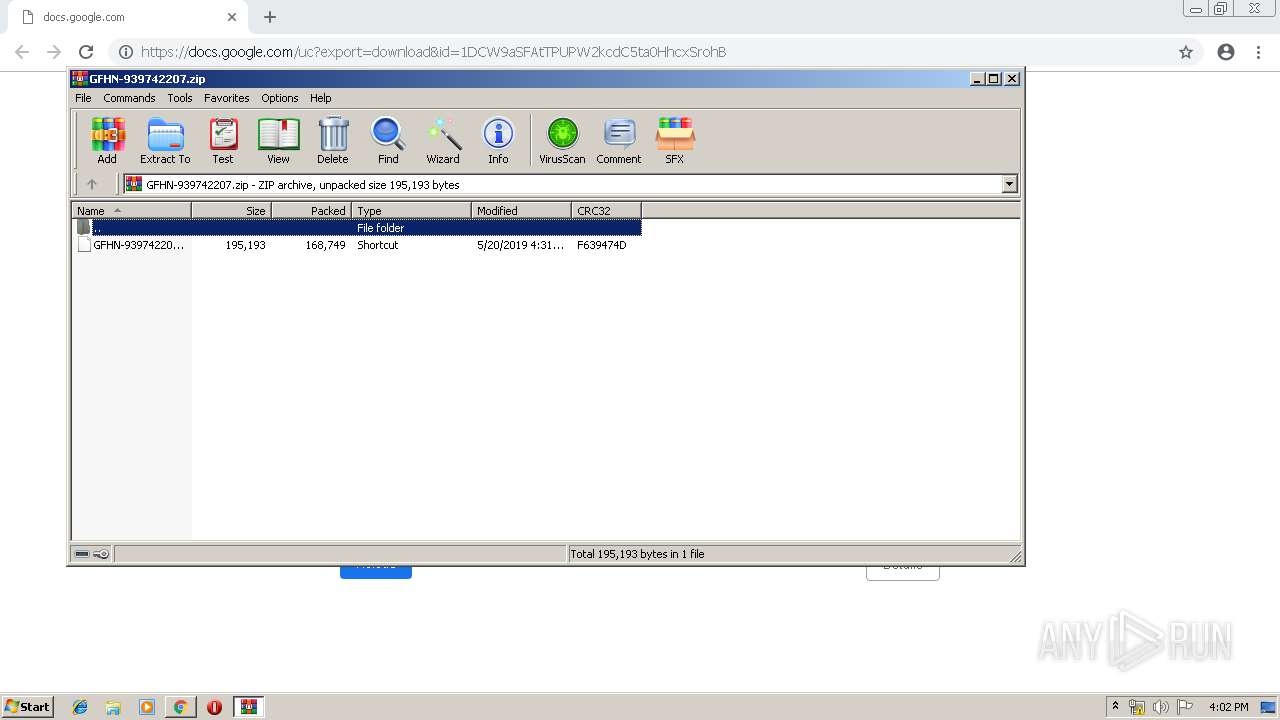
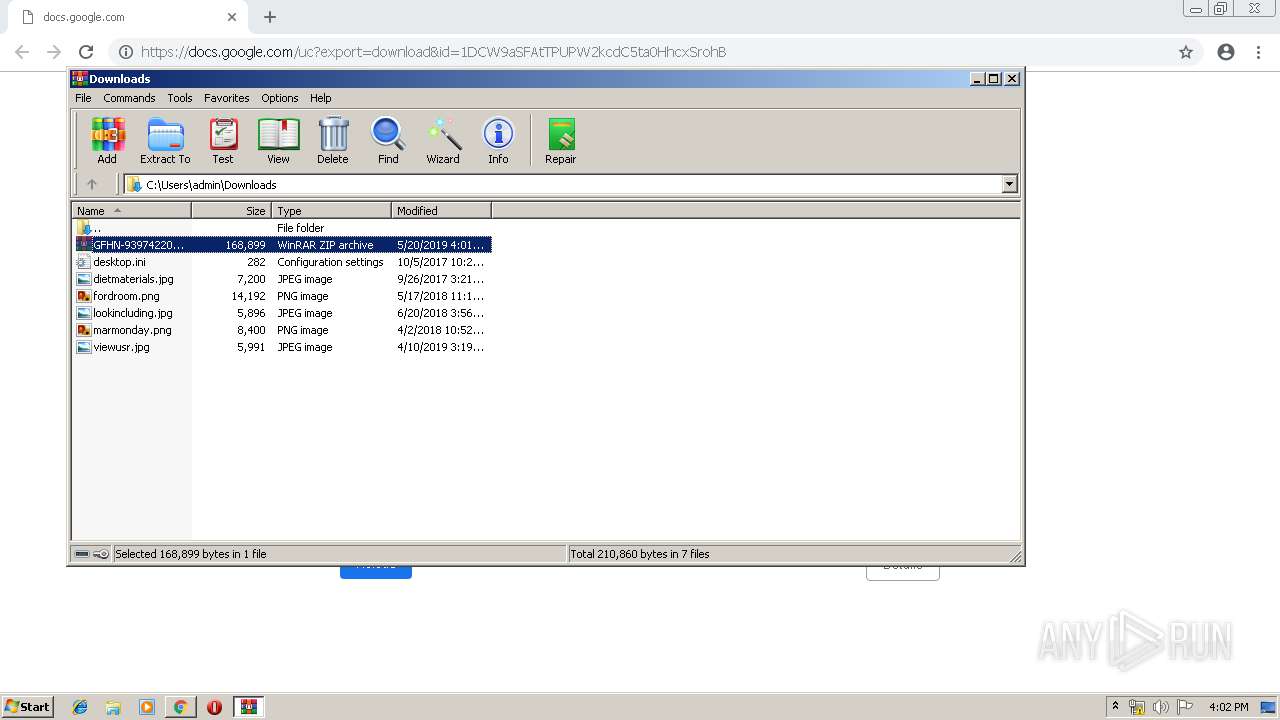
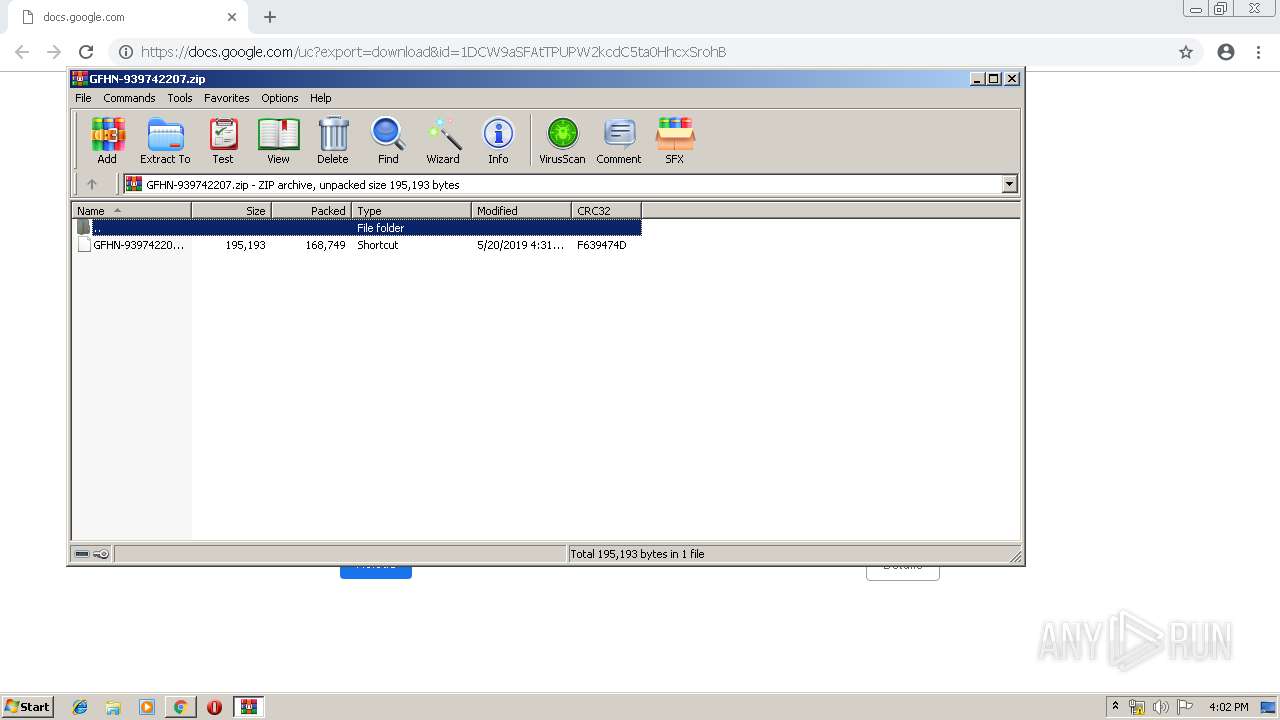
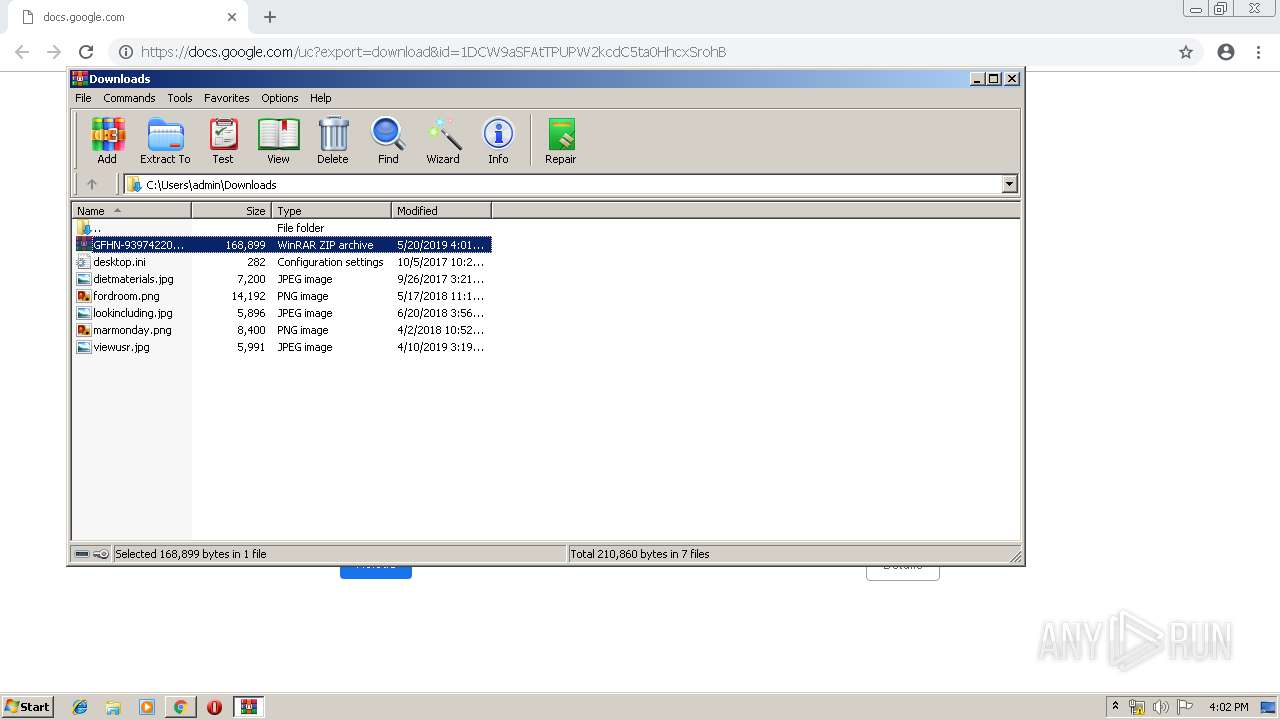
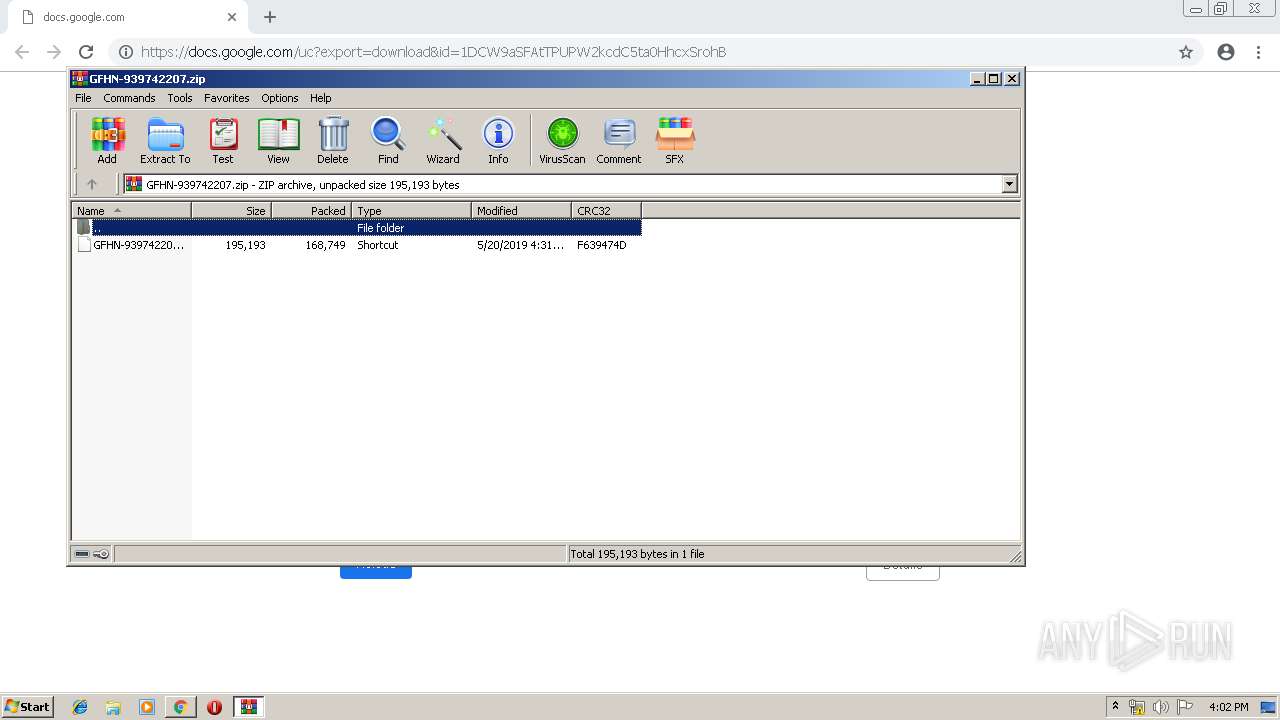
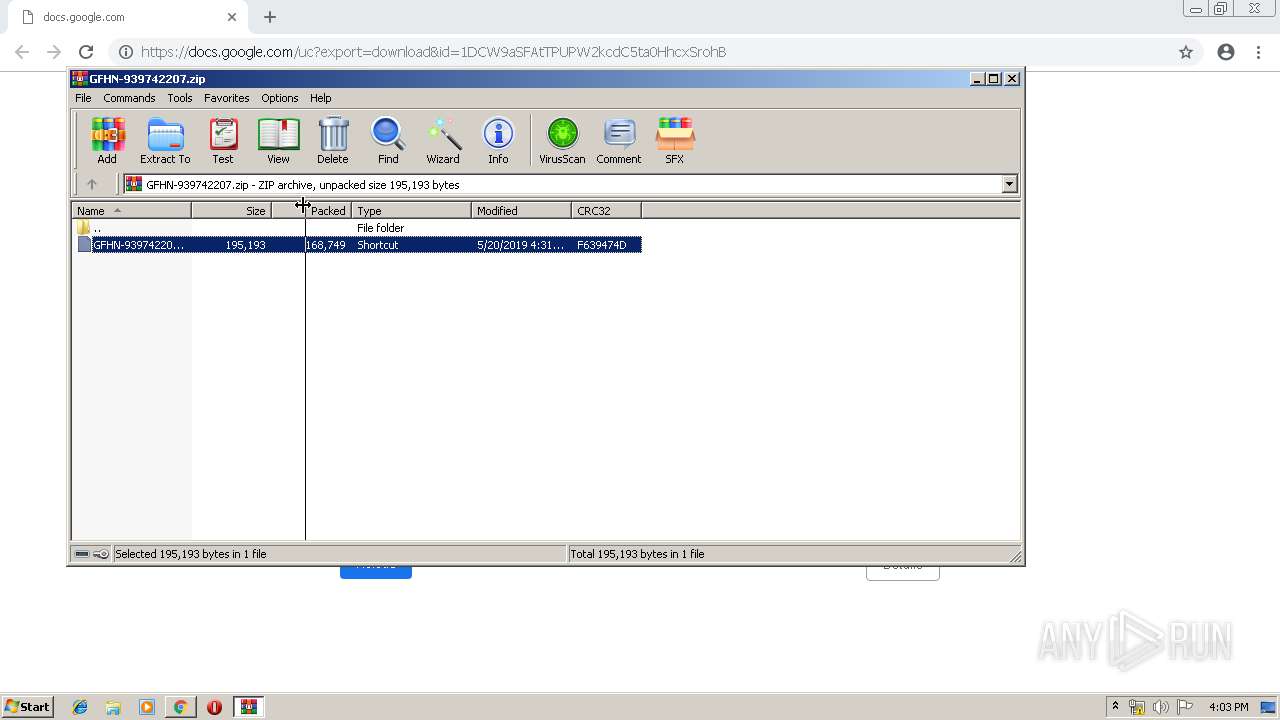
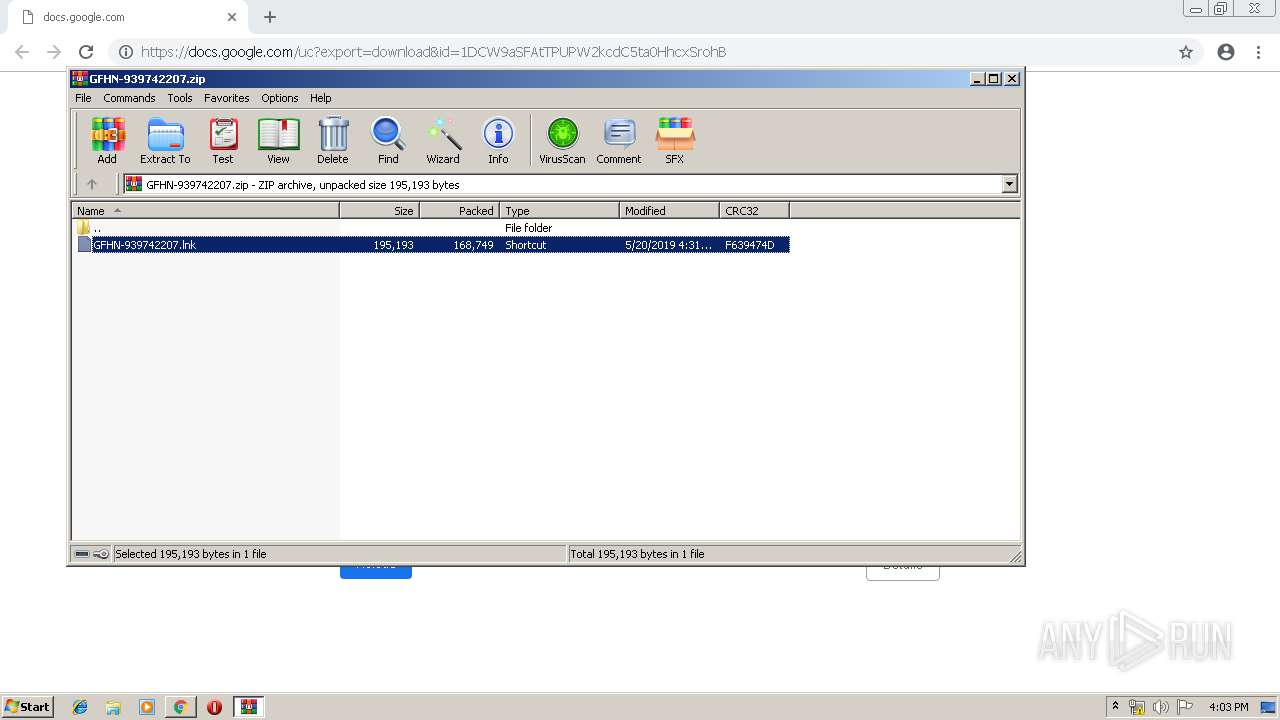
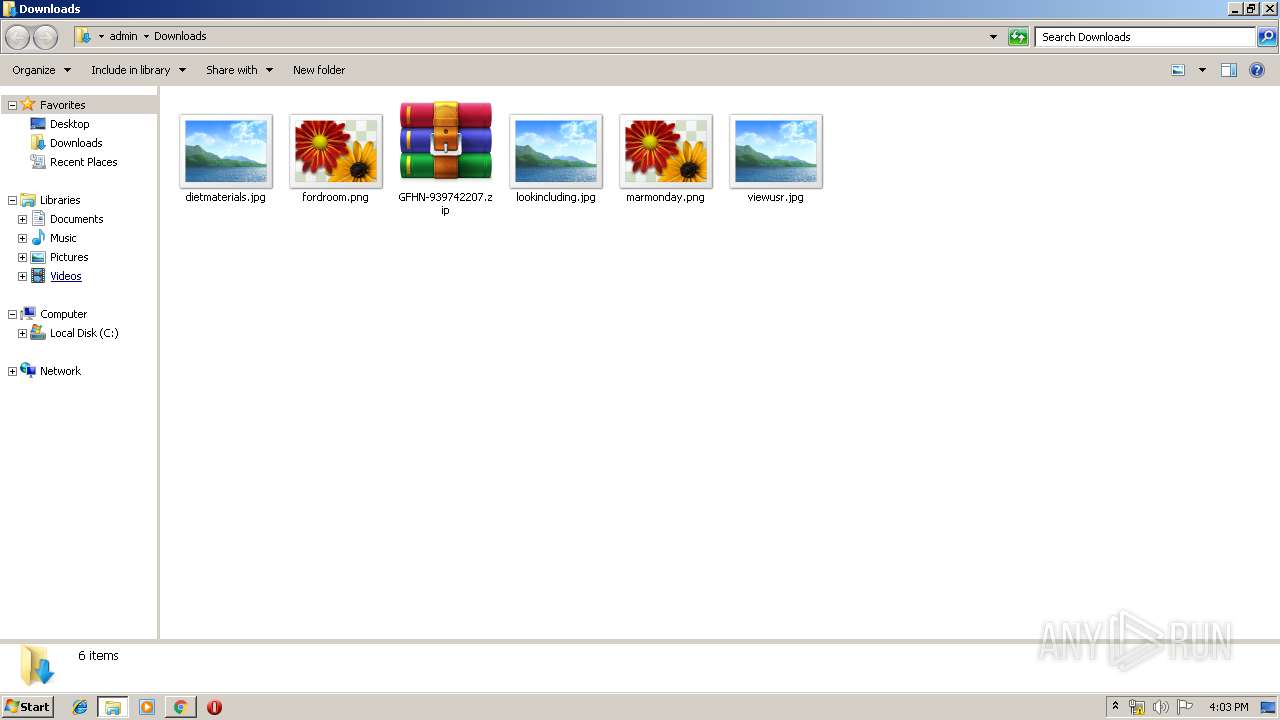
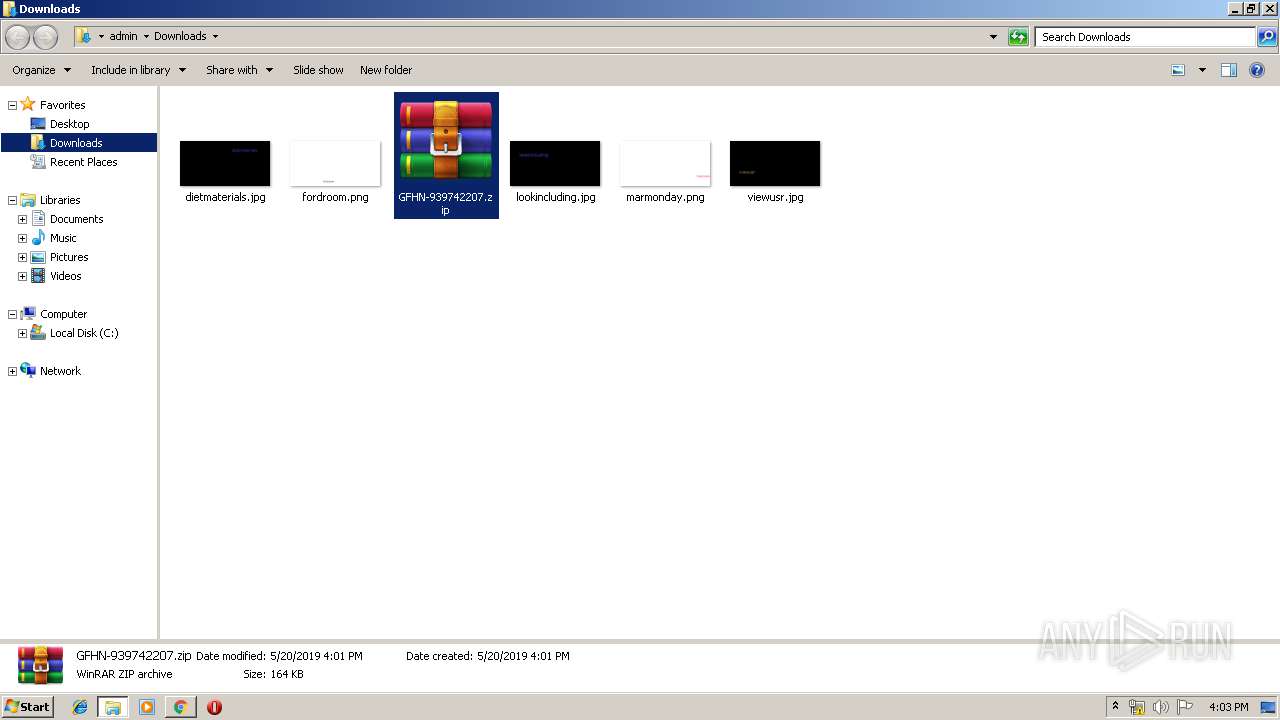
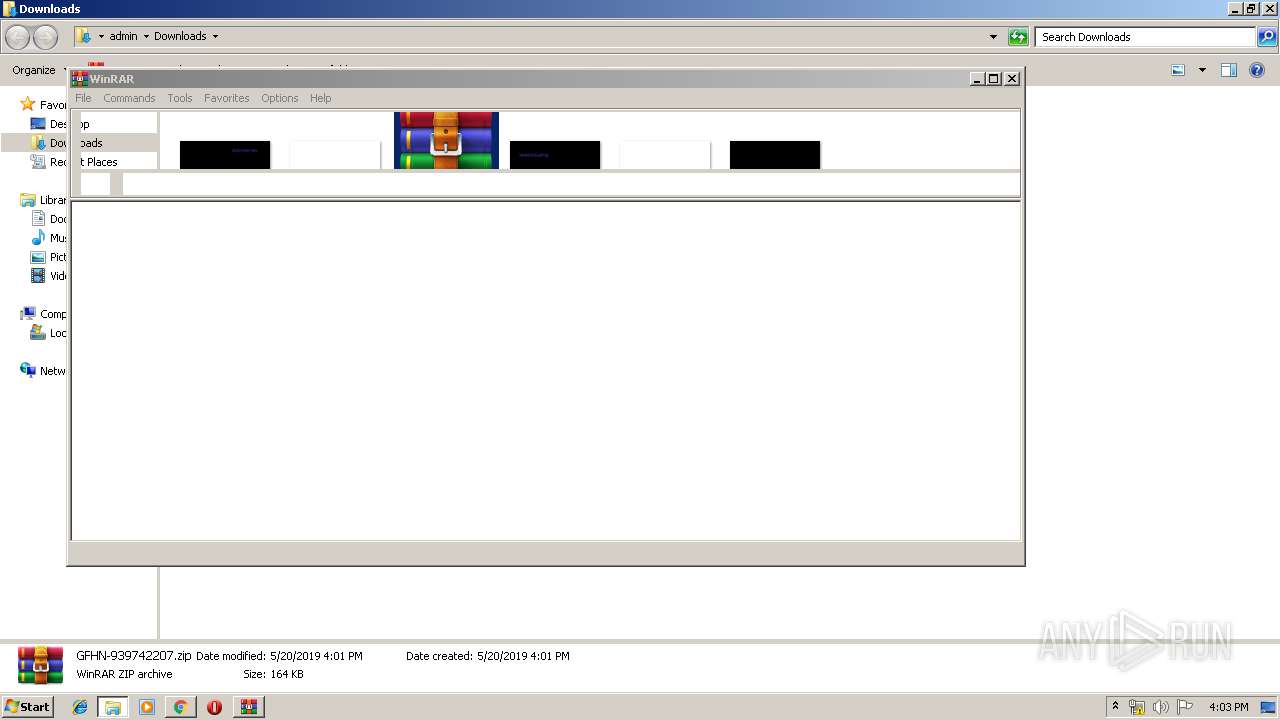
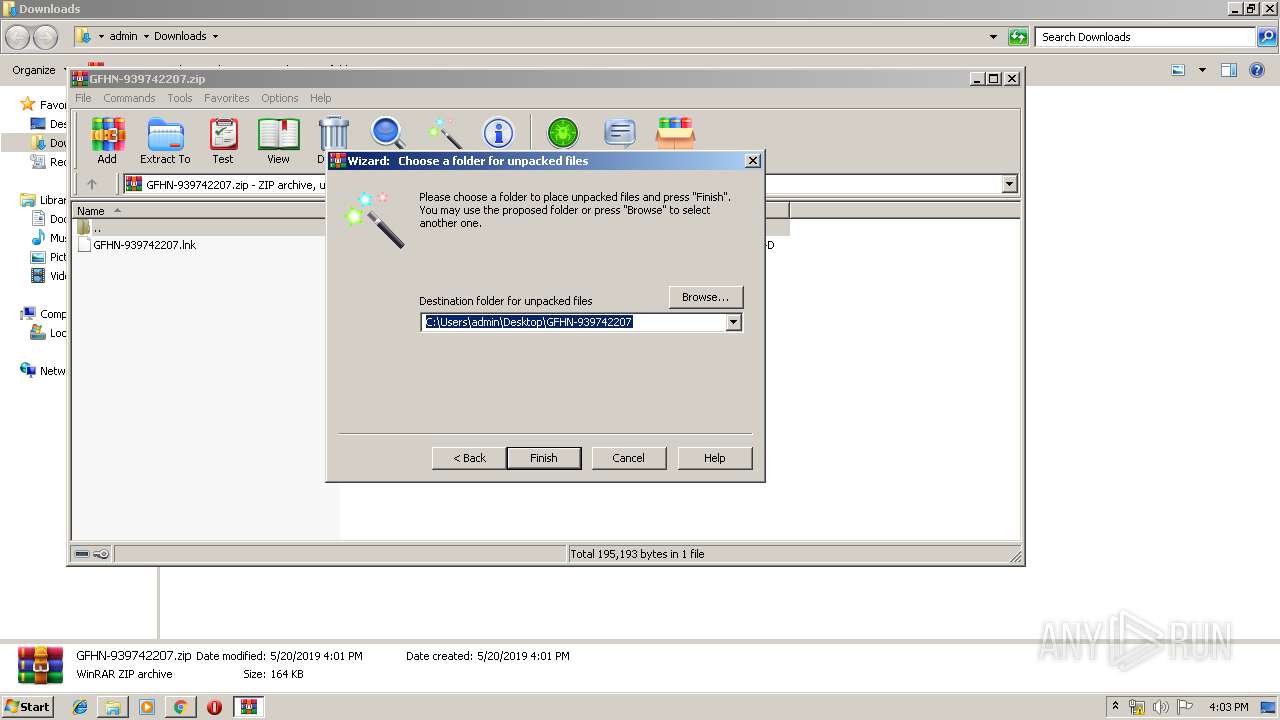
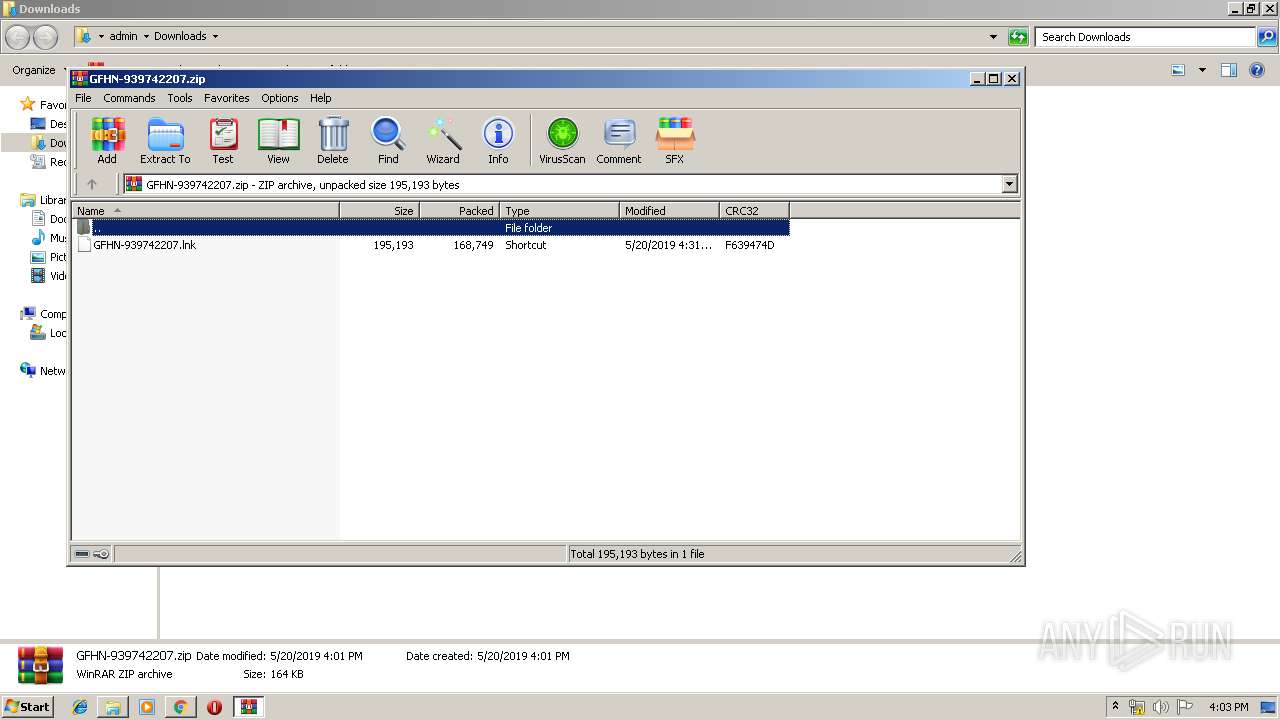
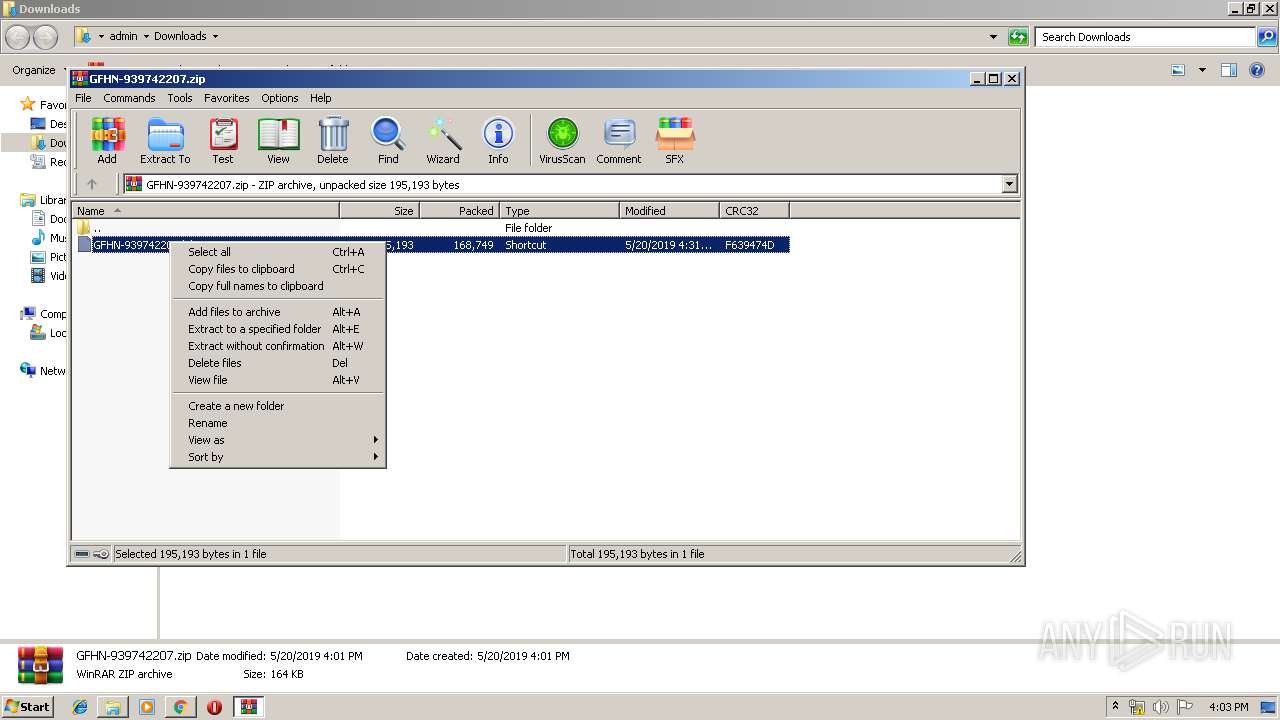
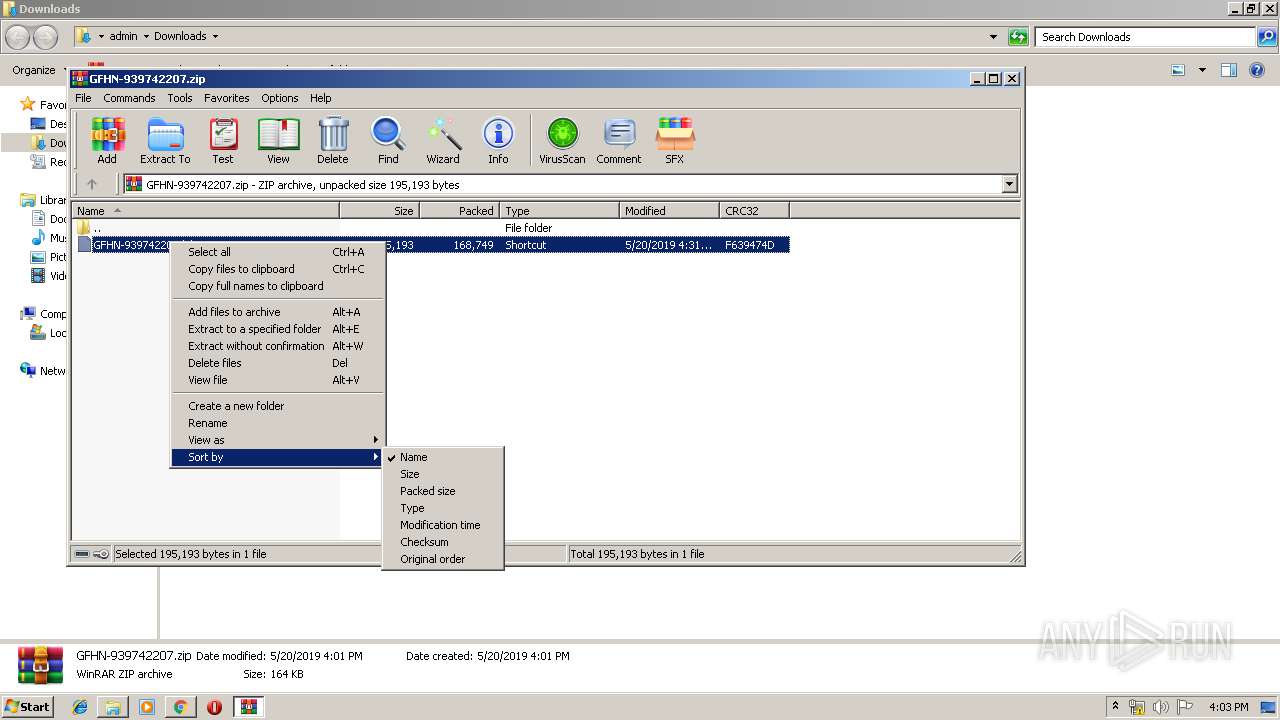
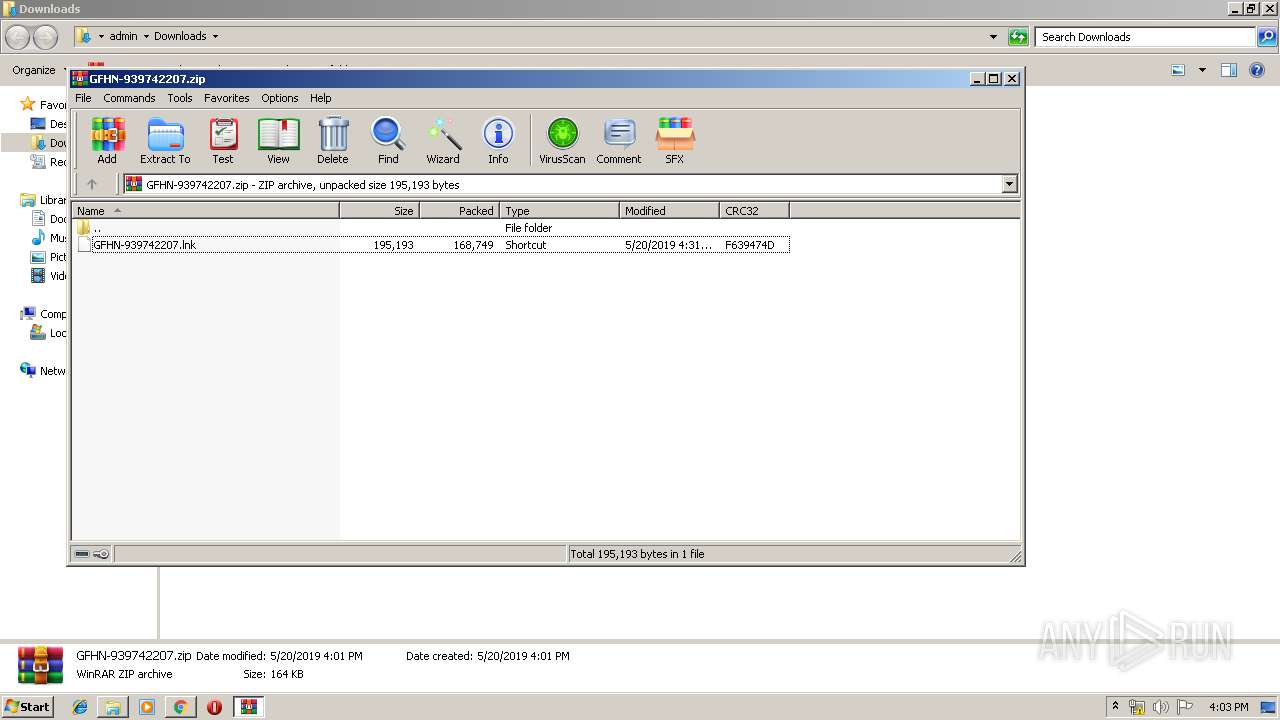
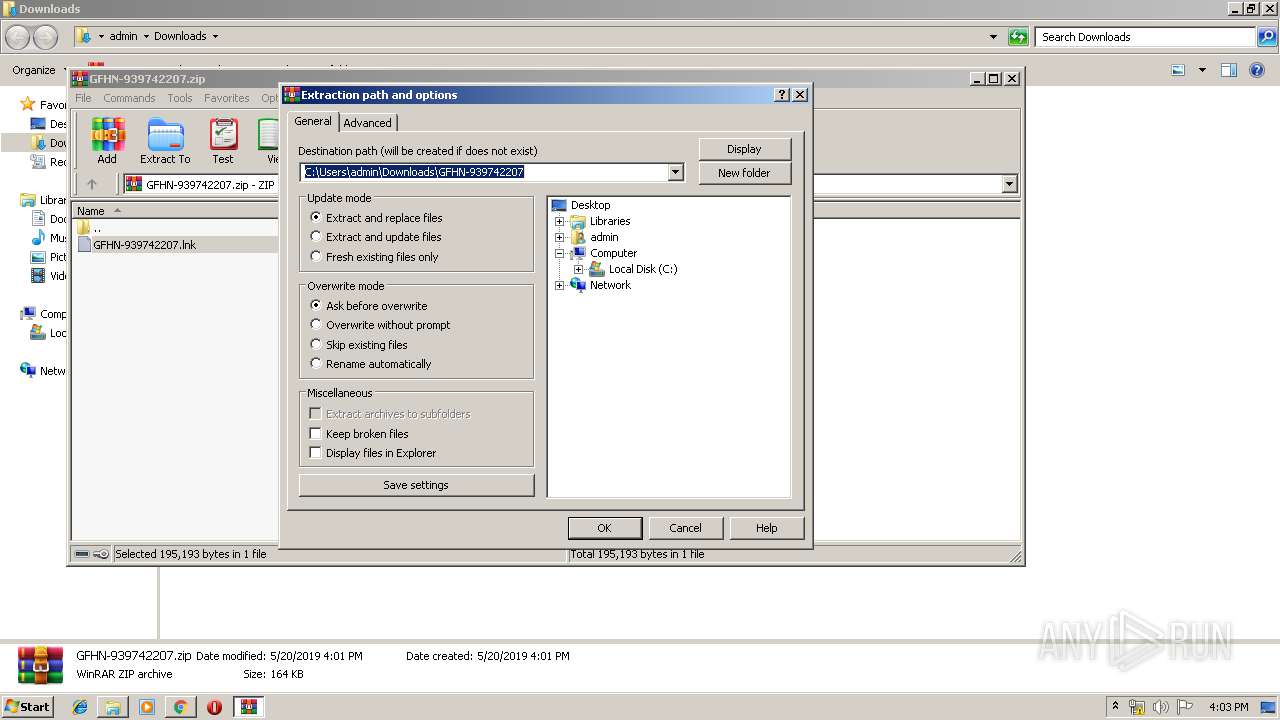
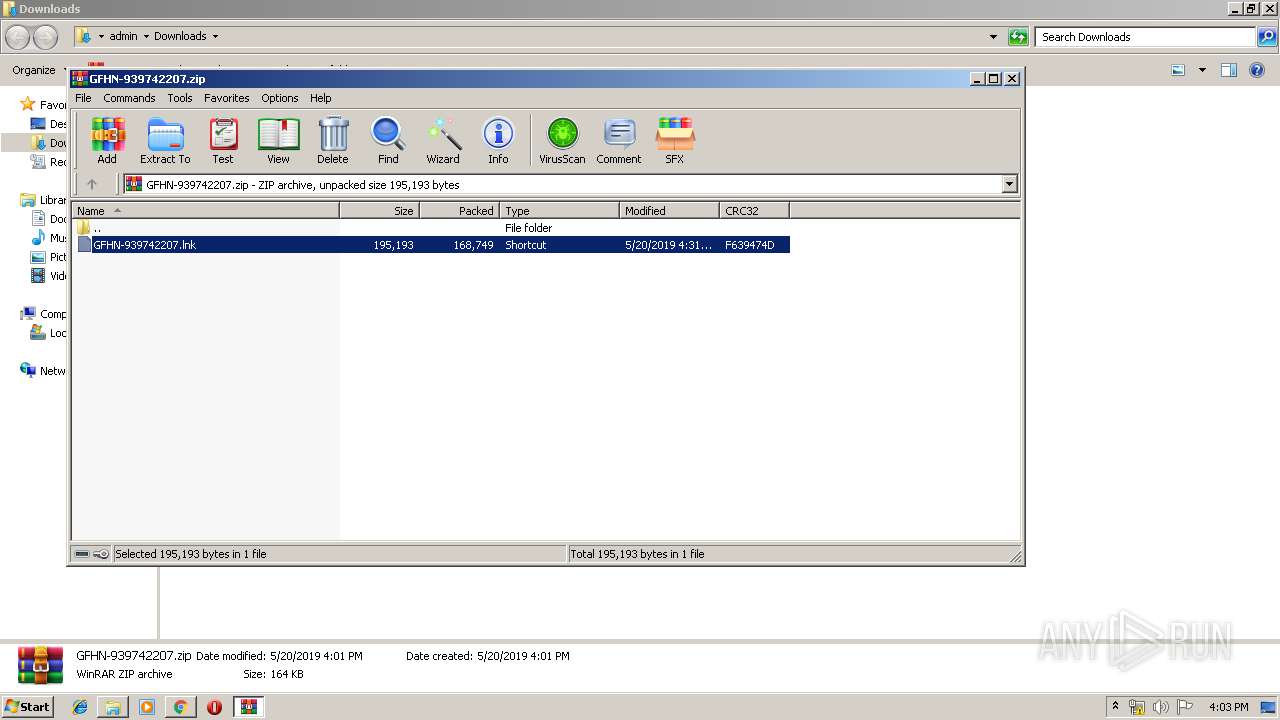
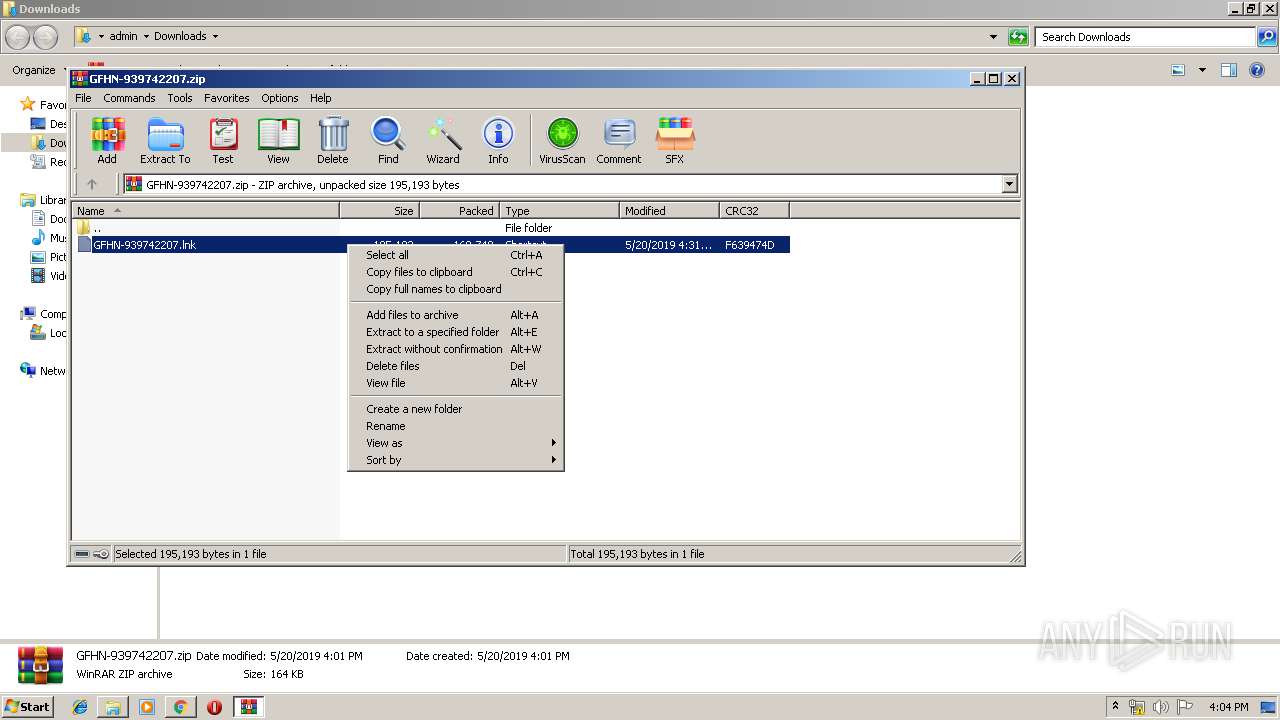
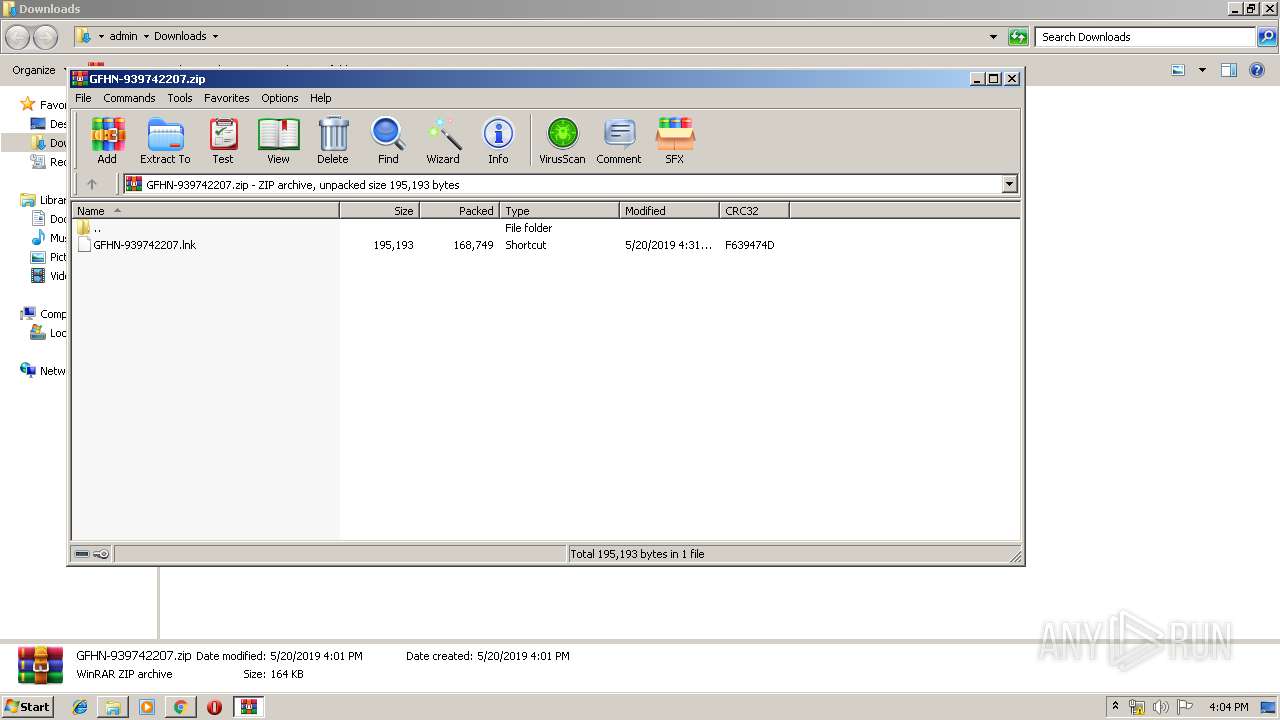
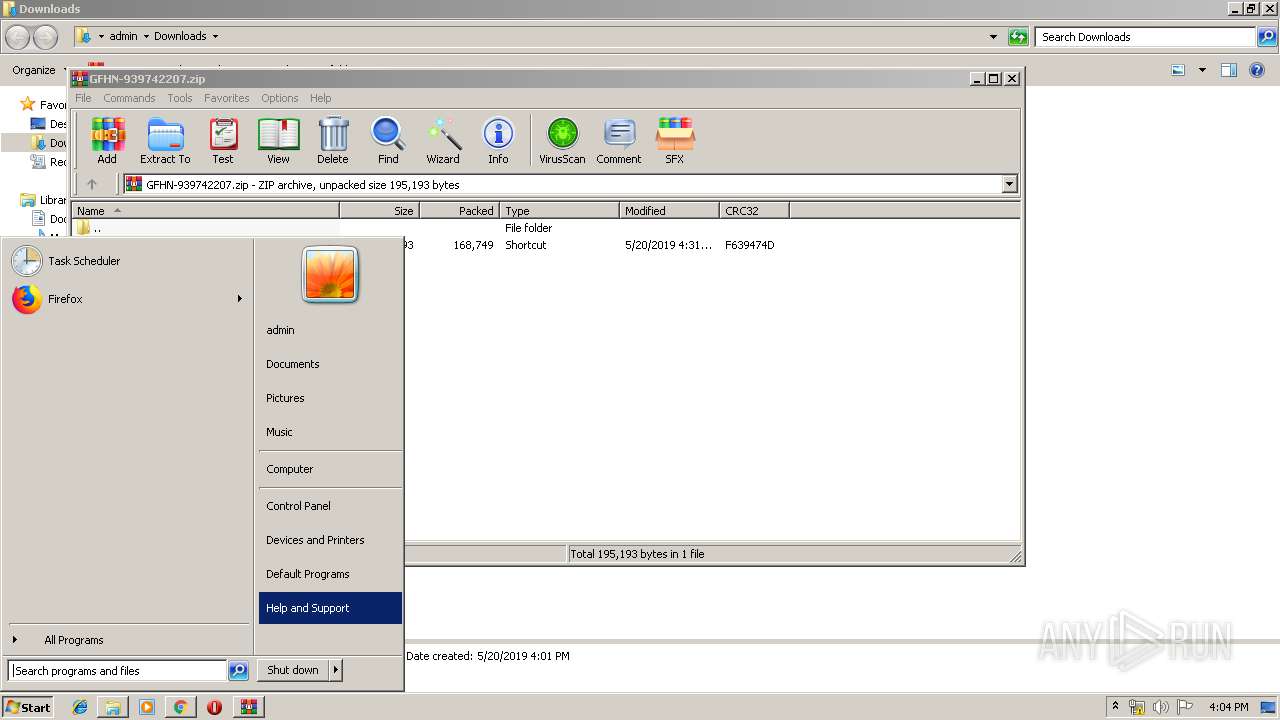
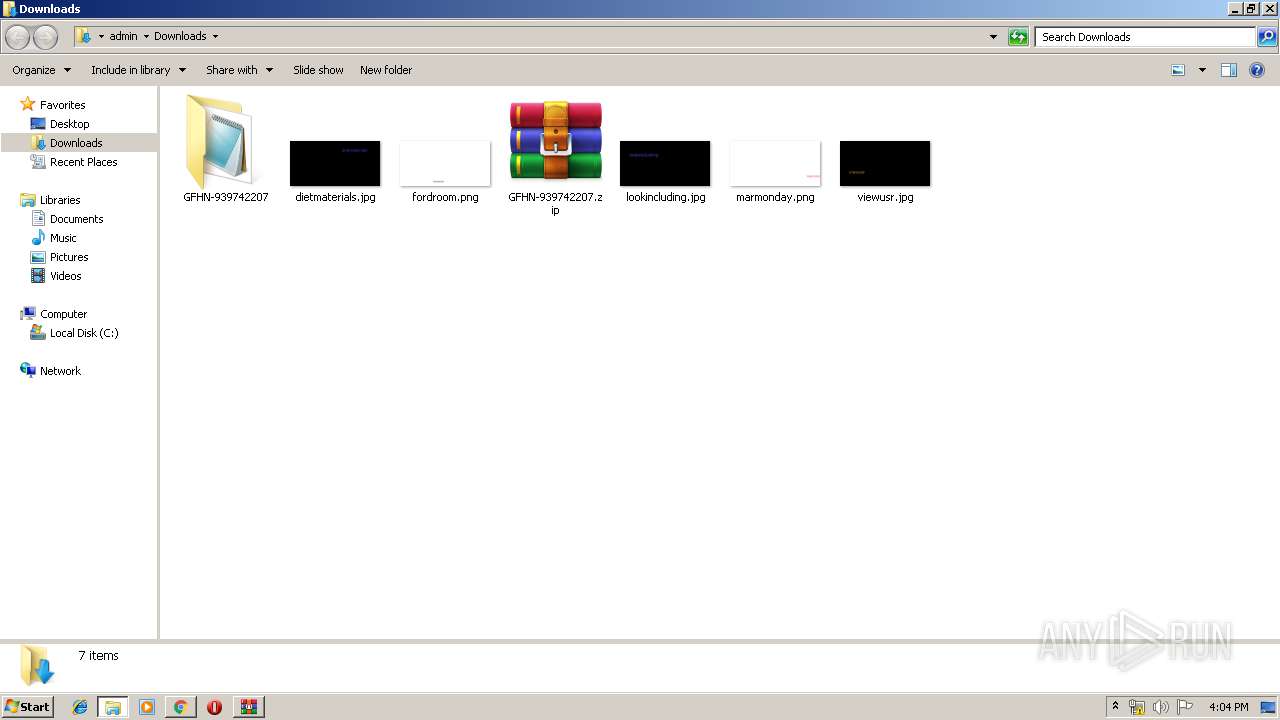
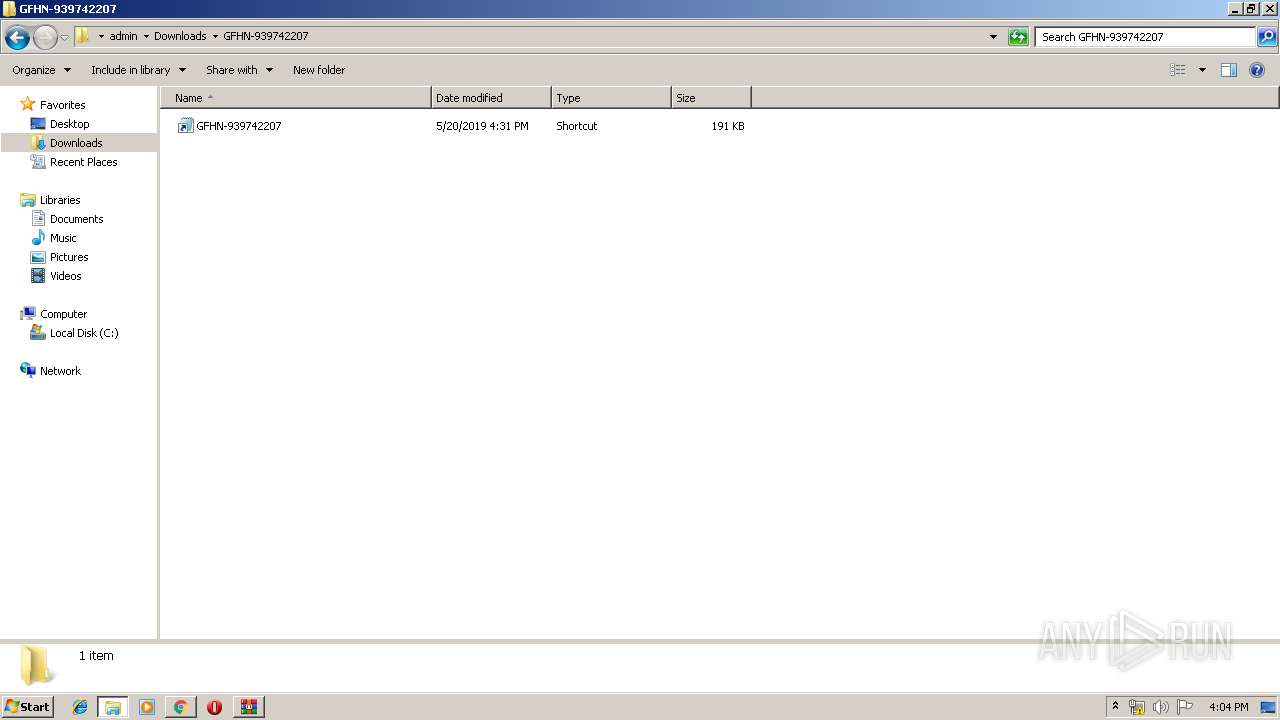
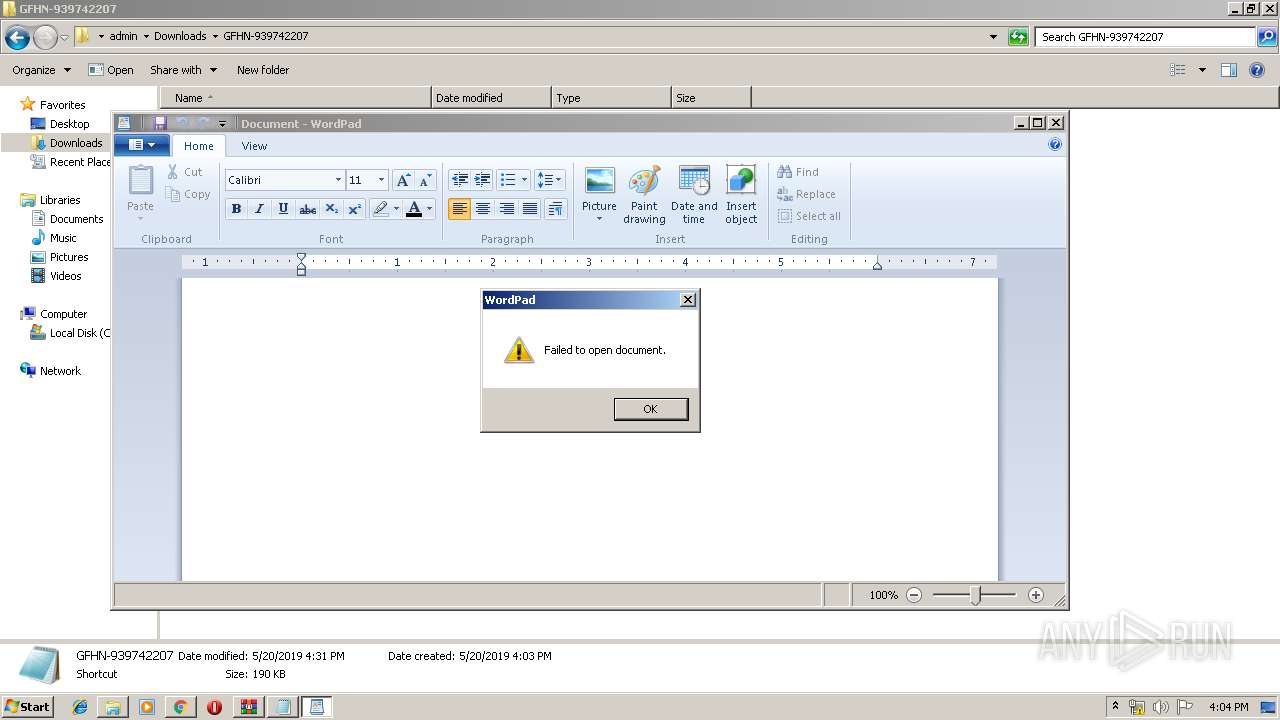
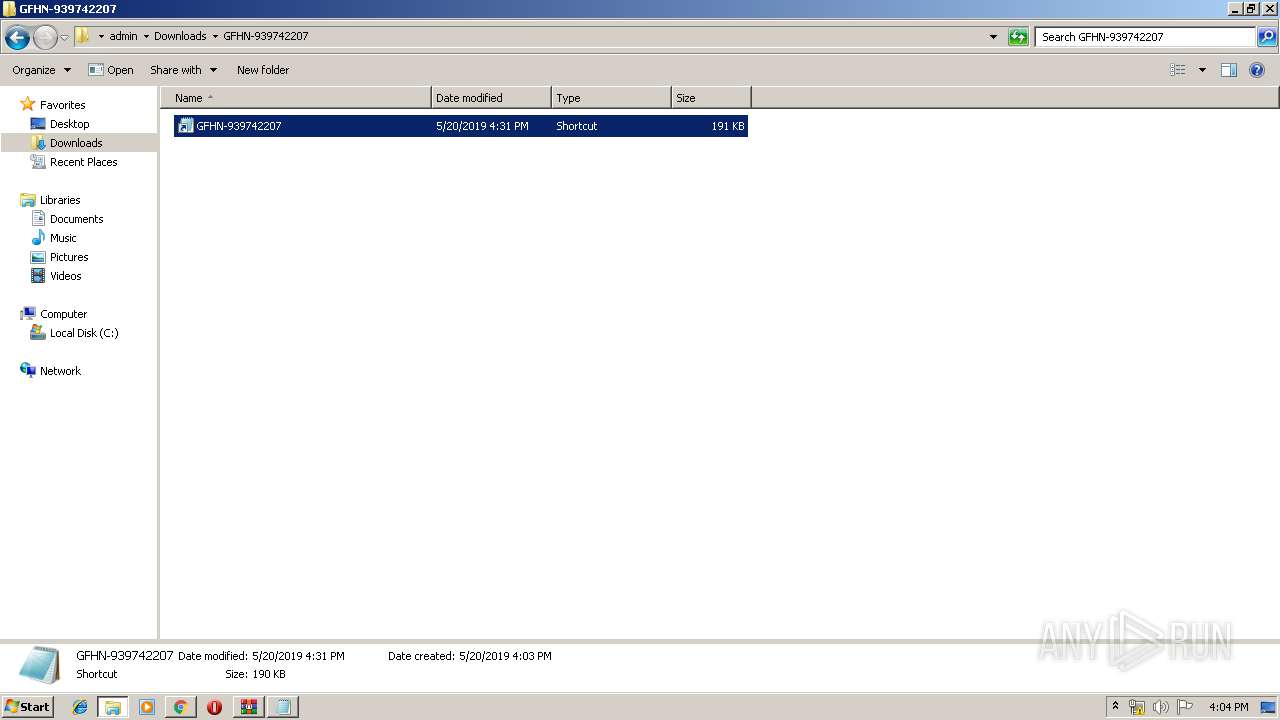
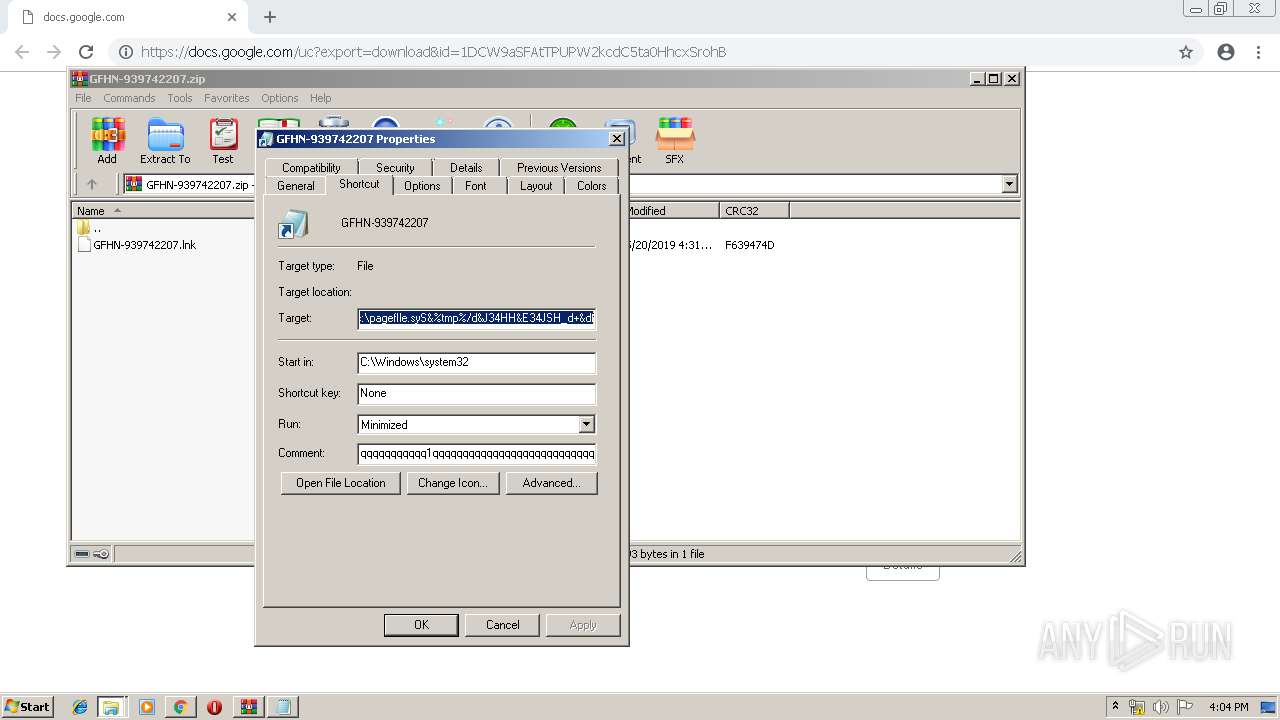
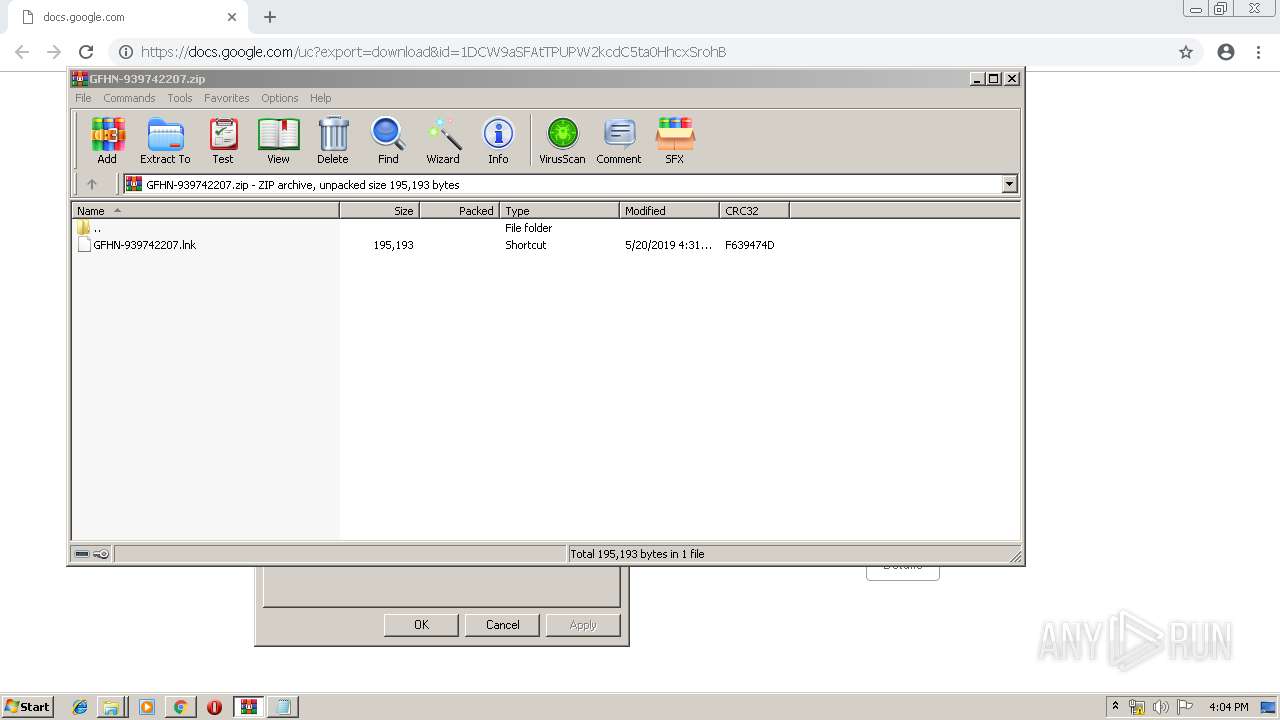
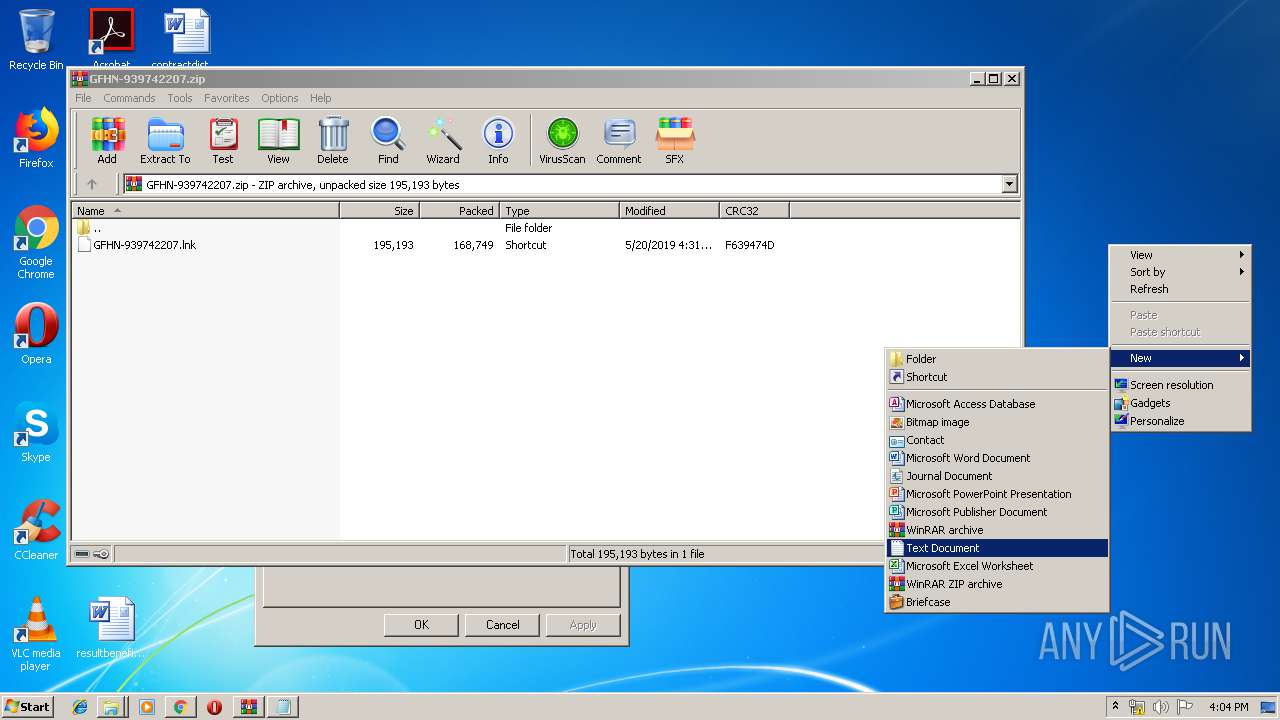
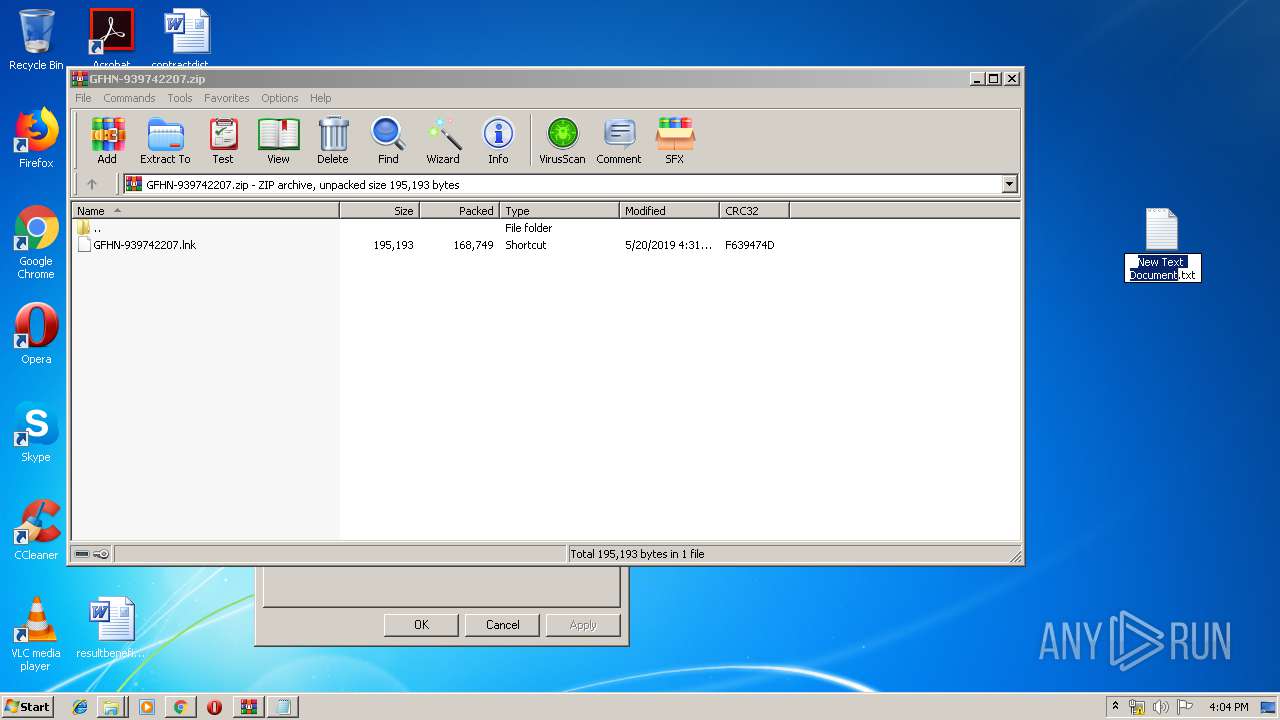
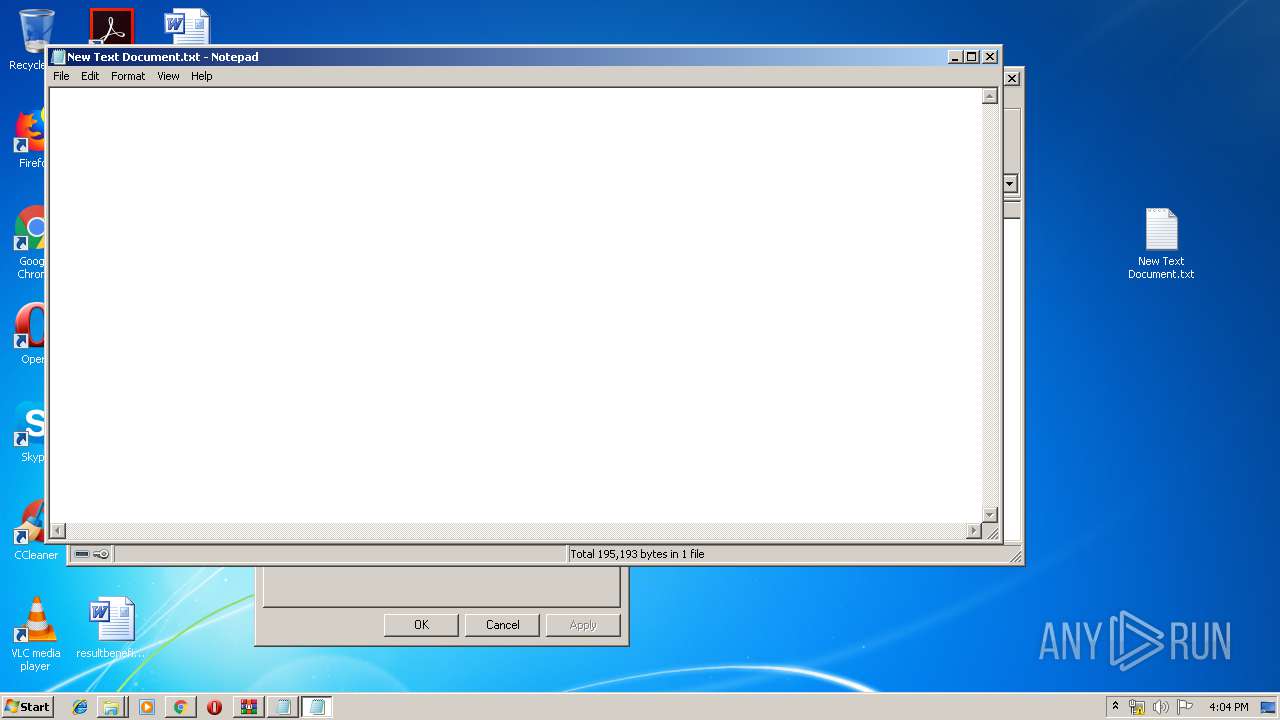
Manual execution by user
- WinRAR.exe (PID: 3332)
- cmd.exe (PID: 1180)
- NOTEPAD.EXE (PID: 1864)
Reads settings of System Certificates
- powershell.exe (PID: 1732)
Reads Internet Cache Settings
- chrome.exe (PID: 1812)
Application launched itself
- chrome.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
63
Malicious processes
8
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,14973688077423212947,618400570326057128,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4074878187917365201 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,14973688077423212947,618400570326057128,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8787023601751233970 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8787023601751233970 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 596 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,14973688077423212947,618400570326057128,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18370553747238486967 --mojo-platform-channel-handle=4380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 860 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,14973688077423212947,618400570326057128,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3682872938328037244 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3682872938328037244 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1004 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,14973688077423212947,618400570326057128,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15971879968407267291 --mojo-platform-channel-handle=3852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 590
Read events
3 103
Write events
482
Delete events
5
Modification events
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1812-13202838085373625 |
Value: 259 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
38
Text files
191
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\88fb521b-a63f-4a08-855b-114bd0a83229.tmp | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
23
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1812 | chrome.exe | GET | 204 | 172.217.18.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1812 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
1812 | chrome.exe | GET | 200 | 173.194.183.201:80 | http://r4---sn-aigl6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1558364227&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1812 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 216.58.207.78:443 | docs.google.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 172.217.18.99:80 | www.gstatic.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 173.194.183.201:80 | r4---sn-aigl6nl7.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1732 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
docs.google.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
doc-10-5o-docs.googleusercontent.com |
| shared |
redirector.gvt1.com |
| whitelisted |