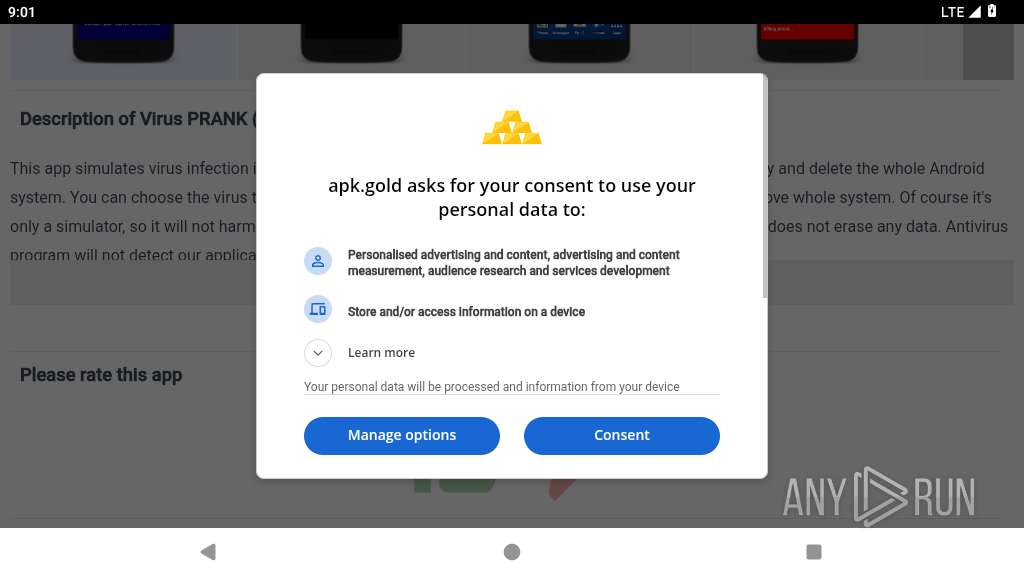
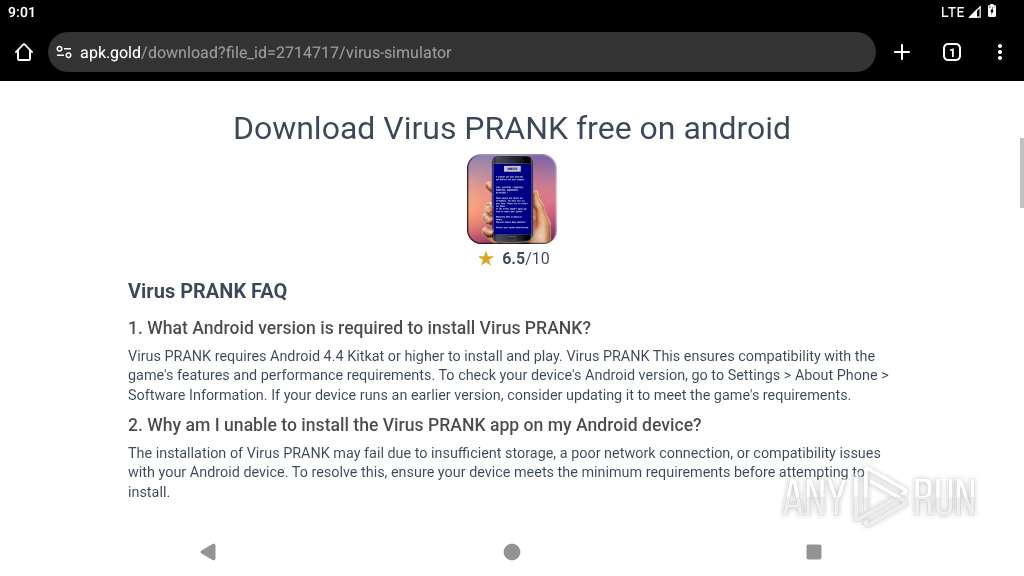
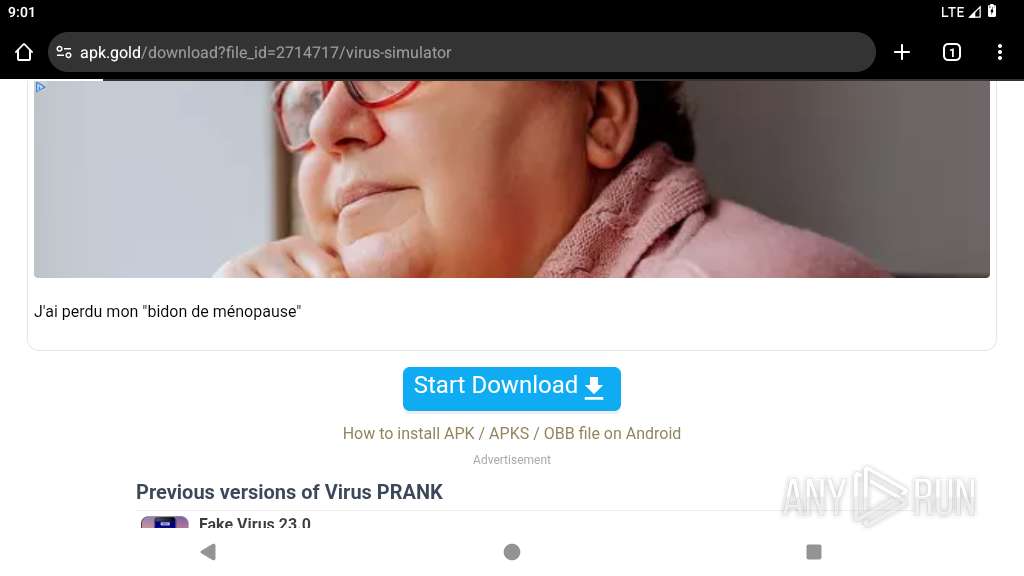
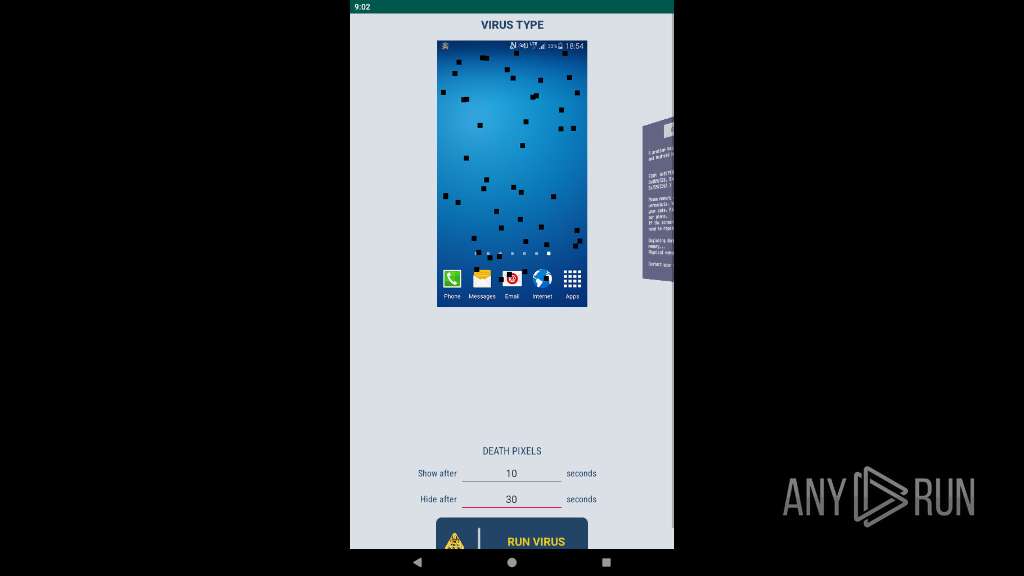
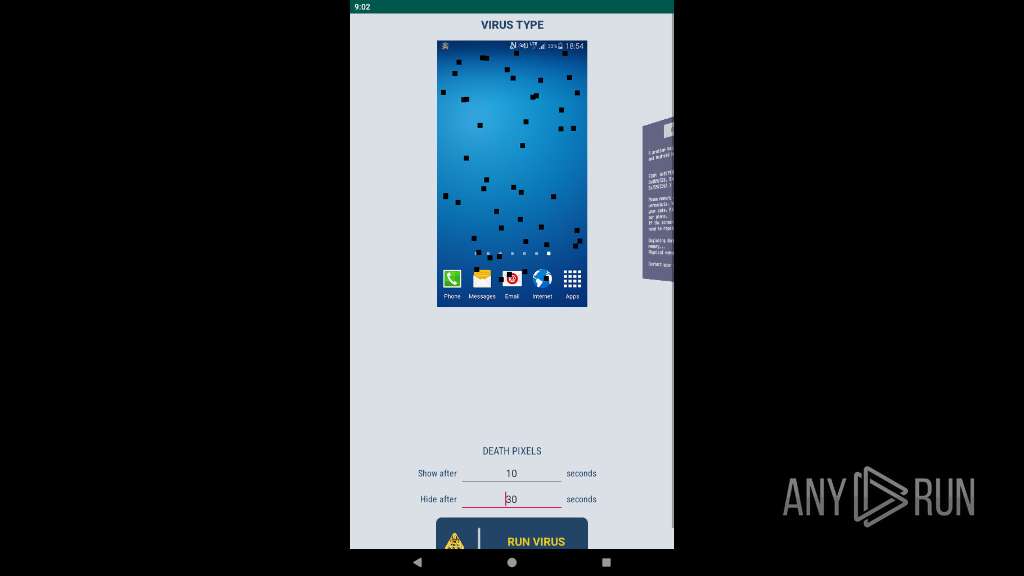
| URL: | https://virus-simulator.apk.gold |
| Full analysis: | https://app.any.run/tasks/5c699d5b-3600-4c00-ba85-a2d4fa8295dd |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2025, 21:00:54 |
| OS: | Android 14 |
| Indicators: | |
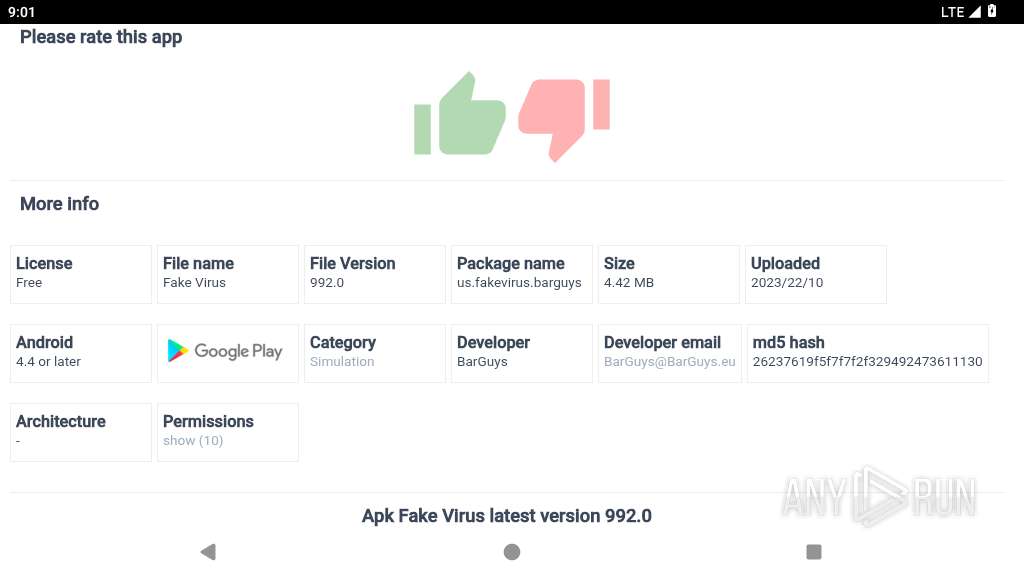
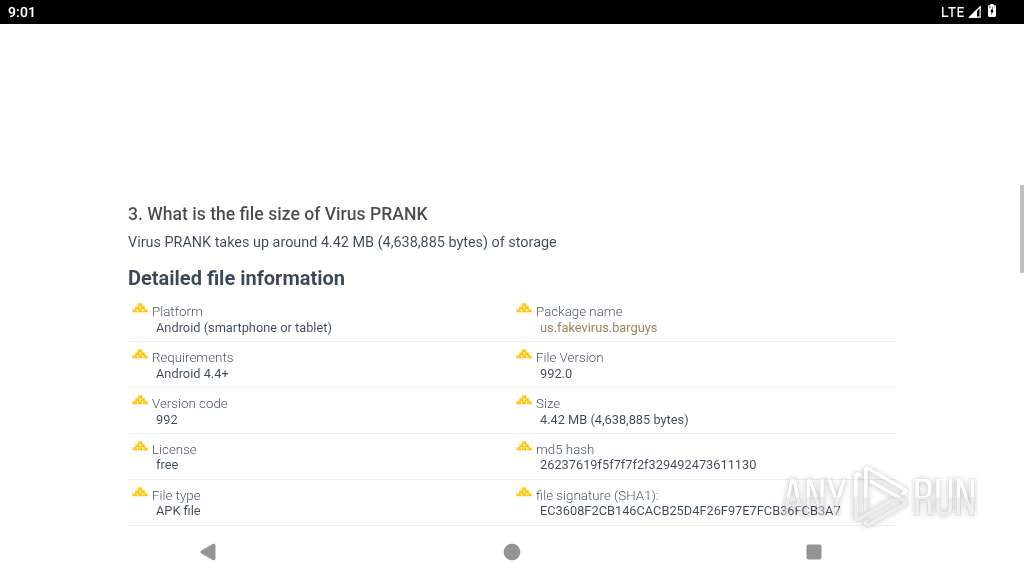
| MD5: | 1E2F8A8B94AD95C8D68B9836F2EF46B6 |
| SHA1: | 3992B4CDFEE41432701D99E8C4551565CDA7A6B1 |
| SHA256: | DAF68CE4B6353D89875ADC56EDE4DB81CF2EF51043B47E9D74454D8CE1EBF2A4 |
| SSDEEP: | 3:N8Y0IQKML7B:2Z0MvB |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 2724)
SUSPICIOUS
Retrieves installed applications on device
- app_process64 (PID: 2724)
Detects presence of QEMU emulator
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
- app_process64 (PID: 3084)
Checks if ADB is enabled
- app_process64 (PID: 2724)
- app_process64 (PID: 3084)
- app_process64 (PID: 3193)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
Retrieves a list of running application processes
- app_process64 (PID: 2724)
- app_process64 (PID: 3084)
- app_process64 (PID: 3193)
Establishing a connection
- app_process64 (PID: 2724)
Accesses system-level resources
- app_process64 (PID: 2724)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2724)
- app_process64 (PID: 3084)
- app_process64 (PID: 3193)
Retrieves a list of running services
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
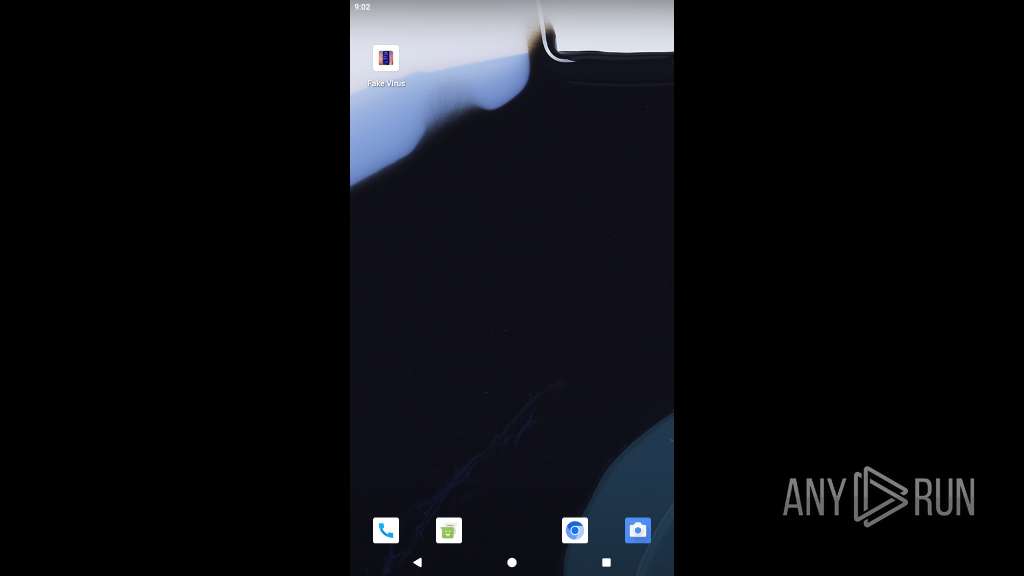
Launches a new activity
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
Starts a service
- app_process64 (PID: 2724)
Abuses foreground service for persistence
- app_process64 (PID: 3084)
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
- app_process64 (PID: 3444)
INFO
Stores data using SQLite database
- app_process64 (PID: 2724)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2724)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2724)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2724)
- app_process64 (PID: 3084)
- app_process64 (PID: 3193)
Returns elapsed time since boot
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
- app_process64 (PID: 3084)
- app_process64 (PID: 3444)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2724)
- app_process64 (PID: 3193)
- app_process64 (PID: 3084)
Dynamically loads a class in Java
- app_process64 (PID: 2724)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2724)
Detects device power status
- app_process64 (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
126
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2197 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2218 | com.android.settings | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2257 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2271 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2307 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 6 | ||||
| 2328 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2381 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 2410 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2431 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2459 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
380
Text files
165
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2481 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.TRcSNI/list.pb | binary | |
MD5:— | SHA256:— | |||
| 2481 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.TRcSNI/manifest.json | binary | |
MD5:— | SHA256:— | |||
| 2481 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.TRcSNI/LICENSE | text | |
MD5:— | SHA256:— | |||
| 2481 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.TRcSNI/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 2481 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/cab4d1f0a6a2a1afecae808a520f6690dd2b9d58bf54762877f2dc9715d55461 | binary | |
MD5:— | SHA256:— | |||
| 2500 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.XH9mJm/privacy-sandbox-attestations.dat | binary | |
MD5:— | SHA256:— | |||
| 2500 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.XH9mJm/manifest.json | binary | |
MD5:— | SHA256:— | |||
| 2500 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.XH9mJm/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 2500 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/38c89b12bb20a8f2751c9c7cd2e31c173a47af08c115e1ecccc2f5151a2cf2c6 | binary | |
MD5:— | SHA256:— | |||
| 2544 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.78dngl/LICENSE.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
167
DNS requests
256
Threats
121
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.184.195:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2197 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | unknown | — | — | whitelisted |
2197 | app_process64 | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/obedbbhbpmojnkanicioggnmelmoomoc/4add6d01f60003b23f83b4d88899b7c648d41ce3c061a88262671b53880a068c | unknown | — | — | whitelisted |
2197 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
2197 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
2197 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jnzdct7t5tv5pkowbndx6dbquu_520/lmelglejhemejginpboagddgdfbepgmp_520_all_ZZ_admnatqefx4m3hvunawmx6gjx4ya.crx3 | unknown | — | — | whitelisted |
2197 | app_process64 | GET | 200 | 142.250.185.142:80 | http://clients2.google.com/time/1/current?cup2key=9:2wm3eWL0DQI6NlyCdna1NdwCHqp10KC1jCSGUfqm_uc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
451 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.8:123 | time.android.com | — | — | whitelisted |
— | — | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.195:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1755 | app_process64 | 142.250.110.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2197 | app_process64 | 142.250.185.142:80 | clients2.google.com | GOOGLE | US | whitelisted |
2197 | app_process64 | 193.42.111.112:443 | virus-simulator.apk.gold | 3W Infra B.V. | NL | whitelisted |
2197 | app_process64 | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2197 | app_process64 | 142.250.181.228:443 | www.google.com | — | — | whitelisted |
2197 | app_process64 | 172.217.16.194:443 | pagead2.googlesyndication.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
virus-simulator.apk.gold |
| whitelisted |
accounts.google.com |
| whitelisted |
apk.gold |
| whitelisted |
google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2197 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |