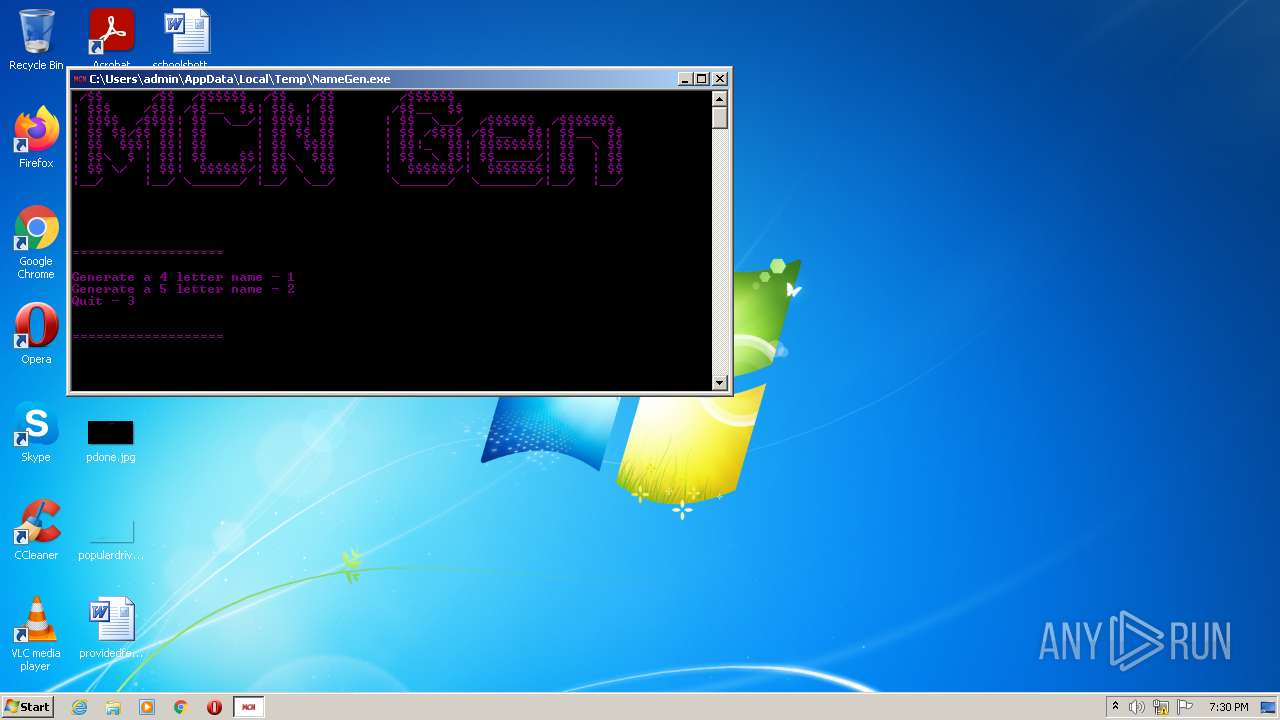
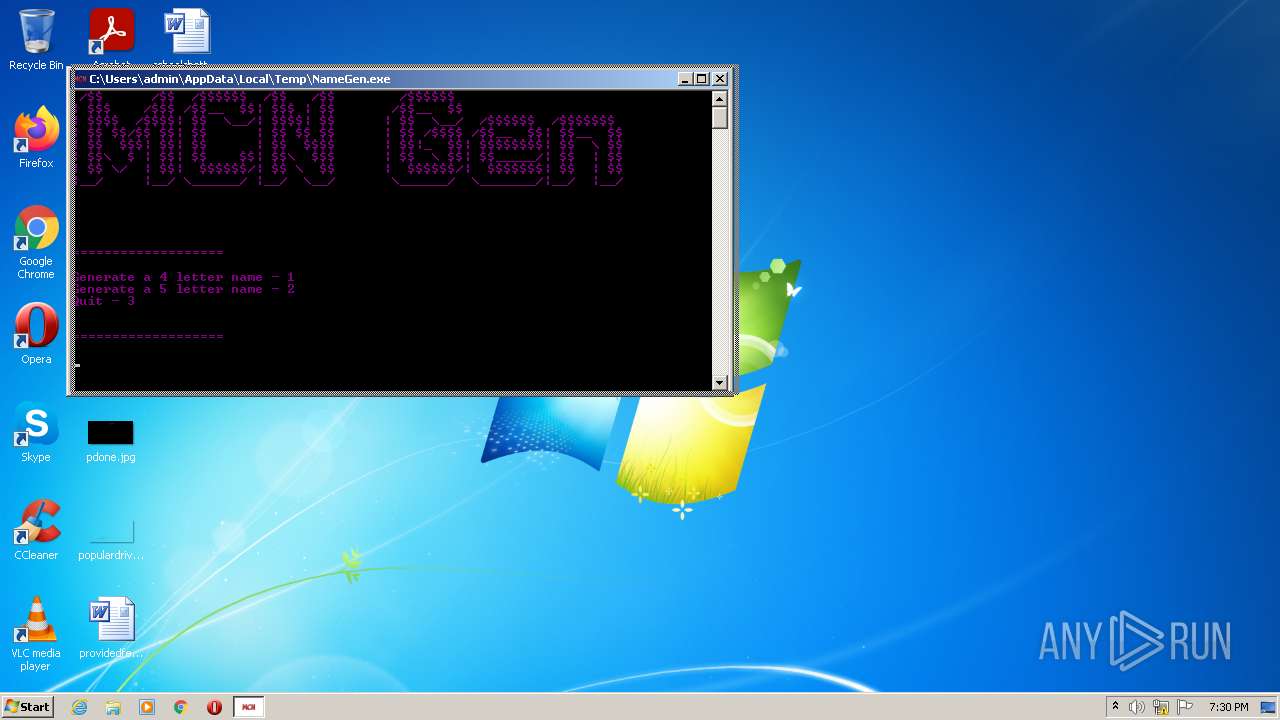
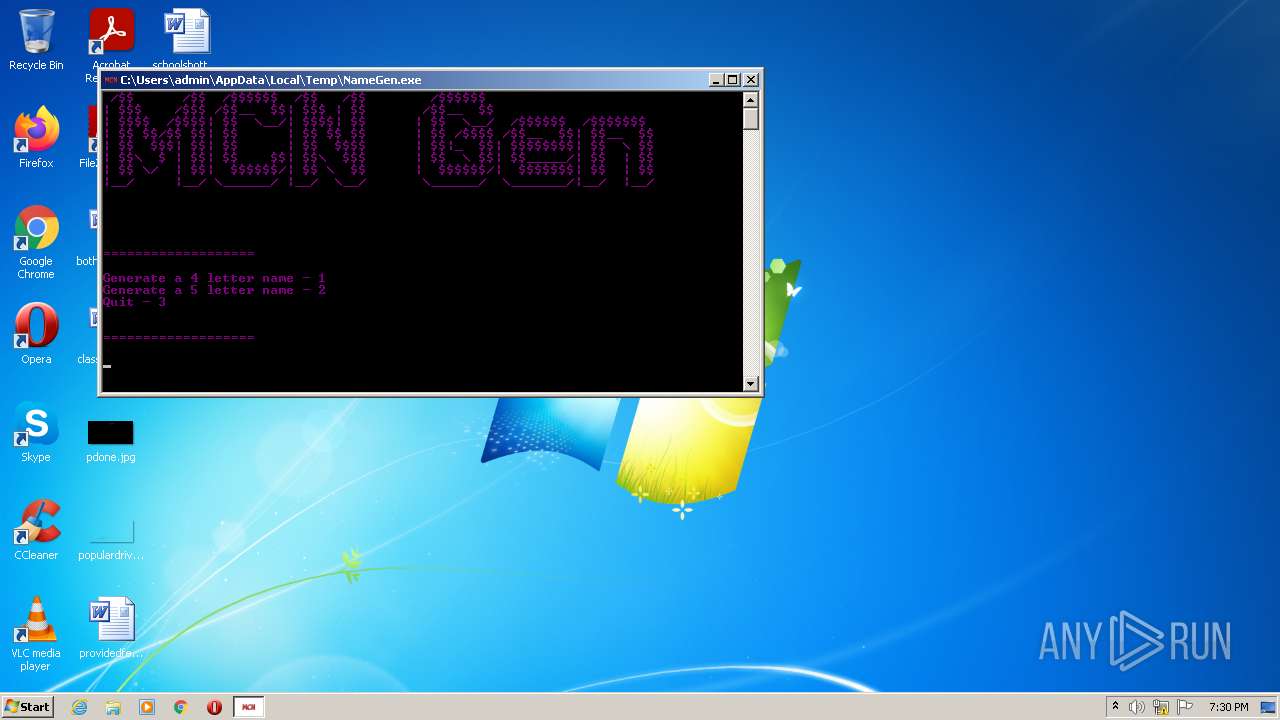
| File name: | NameGen.exe |
| Full analysis: | https://app.any.run/tasks/b87620d1-ab2e-4fc5-b27b-3a07bdcd4709 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 19:30:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A73CD19C3D082F97B31082D00309CB8E |
| SHA1: | CC2F193C59E9D260B7A70348EDA52B5850D07474 |
| SHA256: | DAEF2013621E8CA3B49D02DF215838CC8AF1659D612621FDA9F37DF6E99D89C1 |
| SSDEEP: | 768:Cm/RIdqaO7QnSUi9Wdu2Q5igyc6yuFRulOTDySxip9yVmODi:h/UiUolucM/SADI3ywei |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- NameGen.exe (PID: 1988)
Reads the computer name
- NameGen.exe (PID: 1988)
Reads Environment values
- NameGen.exe (PID: 1988)
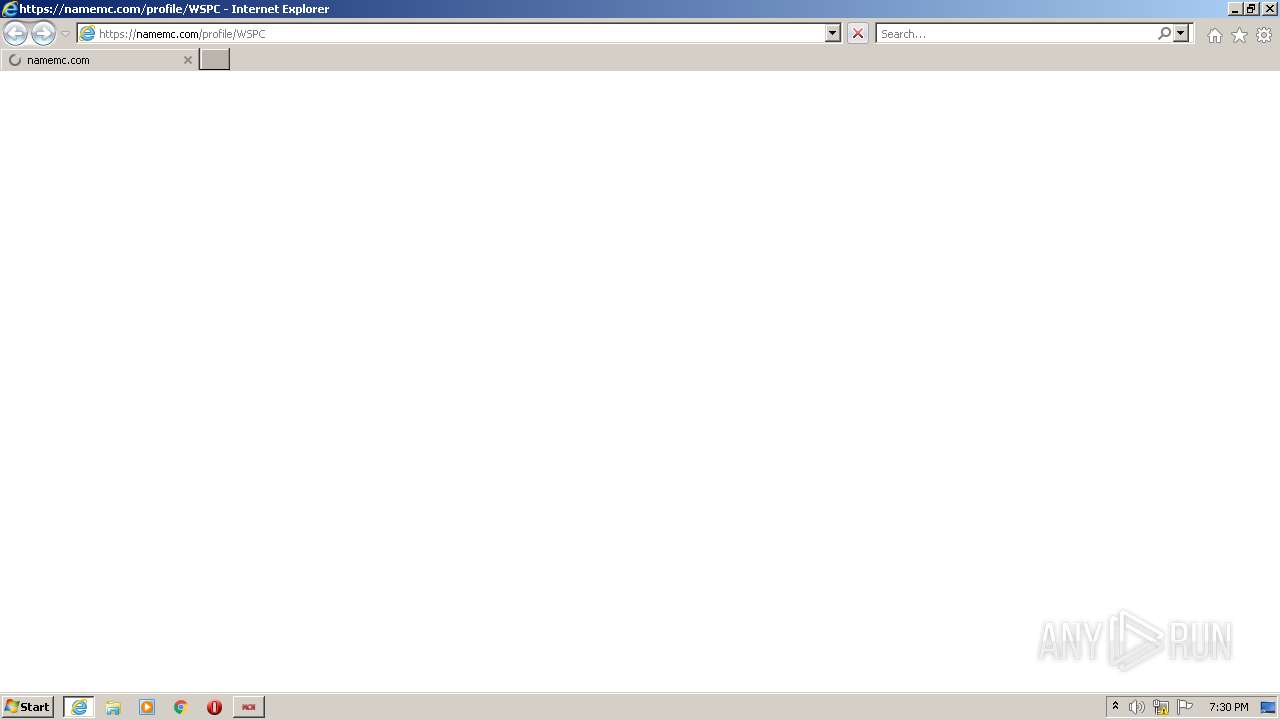
Starts Internet Explorer
- NameGen.exe (PID: 1988)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 272)
INFO
Checks supported languages
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 272)
Changes internet zones settings
- iexplore.exe (PID: 736)
Reads settings of System Certificates
- NameGen.exe (PID: 1988)
- iexplore.exe (PID: 272)
- iexplore.exe (PID: 736)
Reads the computer name
- iexplore.exe (PID: 272)
- iexplore.exe (PID: 736)
Checks Windows Trust Settings
- iexplore.exe (PID: 272)
- iexplore.exe (PID: 736)
Application launched itself
- iexplore.exe (PID: 736)
Reads internet explorer settings
- iexplore.exe (PID: 272)
Creates files in the user directory
- iexplore.exe (PID: 272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | MCN |
| OriginalFileName: | NameGen.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | NameGen.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Minecraft Name Generator |
| CompanyName: | - |
| Comments: | A generator for minecraft |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x33aa |
| UninitializedDataSize: | - |
| InitializedDataSize: | 120832 |
| CodeSize: | 5120 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2056:10:07 09:22:07+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Sep-1920 00:53:51 |
| Comments: | A generator for minecraft |
| CompanyName: | - |
| FileDescription: | Minecraft Name Generator |
| FileVersion: | 1.0.0.0 |
| InternalName: | NameGen.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | NameGen.exe |
| ProductName: | MCN |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Sep-1920 00:53:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000013B0 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.52244 |
.rsrc | 0x00004000 | 0x0001D528 | 0x0001D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.45992 |
.reloc | 0x00022000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.02988 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.26646 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.48337 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.74631 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.05226 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:736 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
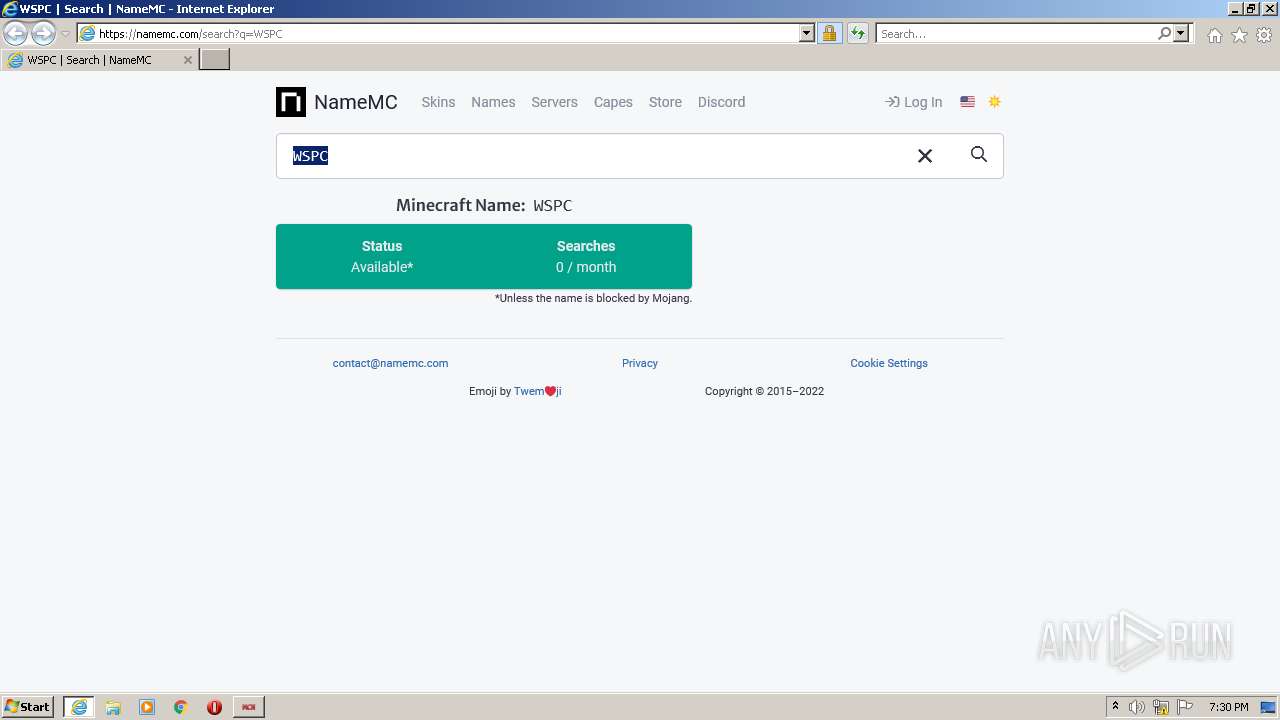
| 736 | "C:\Program Files\Internet Explorer\iexplore.exe" https://namemc.com/profile/WSPC | C:\Program Files\Internet Explorer\iexplore.exe | NameGen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Local\Temp\NameGen.exe" | C:\Users\admin\AppData\Local\Temp\NameGen.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Minecraft Name Generator Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
18 247
Read events
18 100
Write events
147
Delete events
0
Modification events
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1988) NameGen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\NameGen_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
0
Suspicious files
22
Text files
73
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\search[1].htm | html | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U7BG3JKN.txt | text | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\script[1].js | text | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\dark[1].css | text | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\adcde[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
55
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
272 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
272 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
272 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEH4wYrandiOsCgAAAAErgCs%3D | US | der | 471 b | whitelisted |
272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
272 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEFKxQHtEPcBCgAAAAErfHU%3D | US | der | 471 b | whitelisted |
272 | iexplore.exe | GET | 200 | 23.32.238.67:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNW6oVC%2FmCya3bi5RCuFbxCTA%3D%3D | US | der | 503 b | shared |
736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
272 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?924966bb39fbaa83 | ZA | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1988 | NameGen.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
272 | iexplore.exe | 104.27.18.114:443 | namemc.com | Cloudflare Inc | US | unknown |
272 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
272 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
272 | iexplore.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
272 | iexplore.exe | 142.250.185.226:443 | securepubads.g.doubleclick.net | Google Inc. | US | suspicious |
272 | iexplore.exe | 104.26.12.10:443 | z.namemc-static.com | Cloudflare Inc | US | unknown |
272 | iexplore.exe | 142.250.185.232:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
272 | iexplore.exe | 138.199.37.226:443 | kumo.network-n.com | — | — | malicious |
272 | iexplore.exe | 65.9.49.114:443 | d322cqt584bo4o.cloudfront.net | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
namemc.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
tags.bkrtx.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
kumo.network-n.com |
| malicious |
z.namemc-static.com |
| unknown |
www.googletagmanager.com |
| whitelisted |