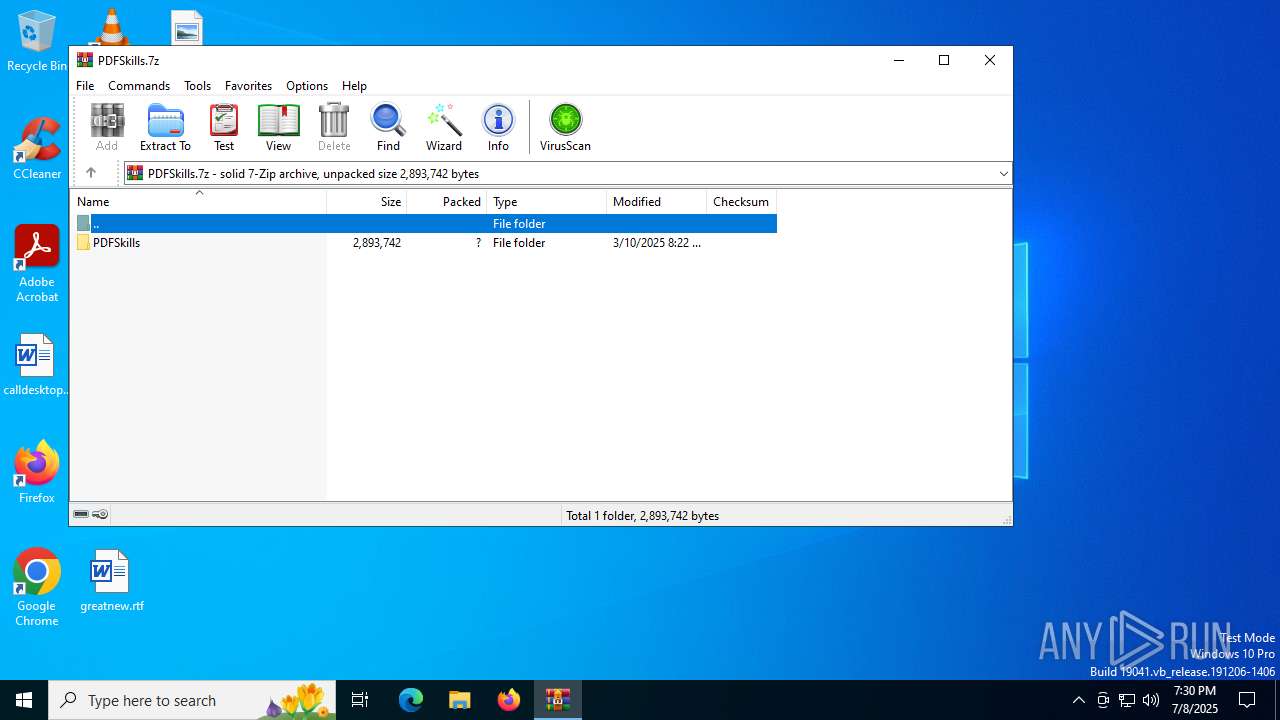
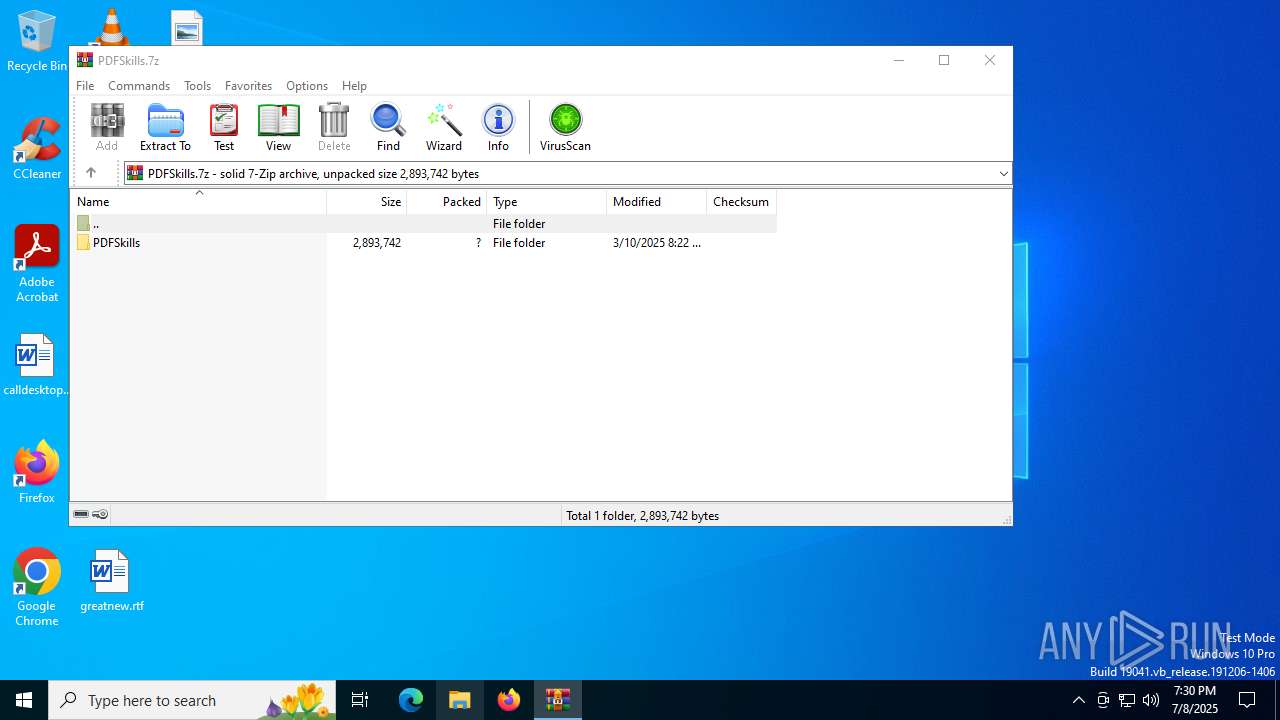
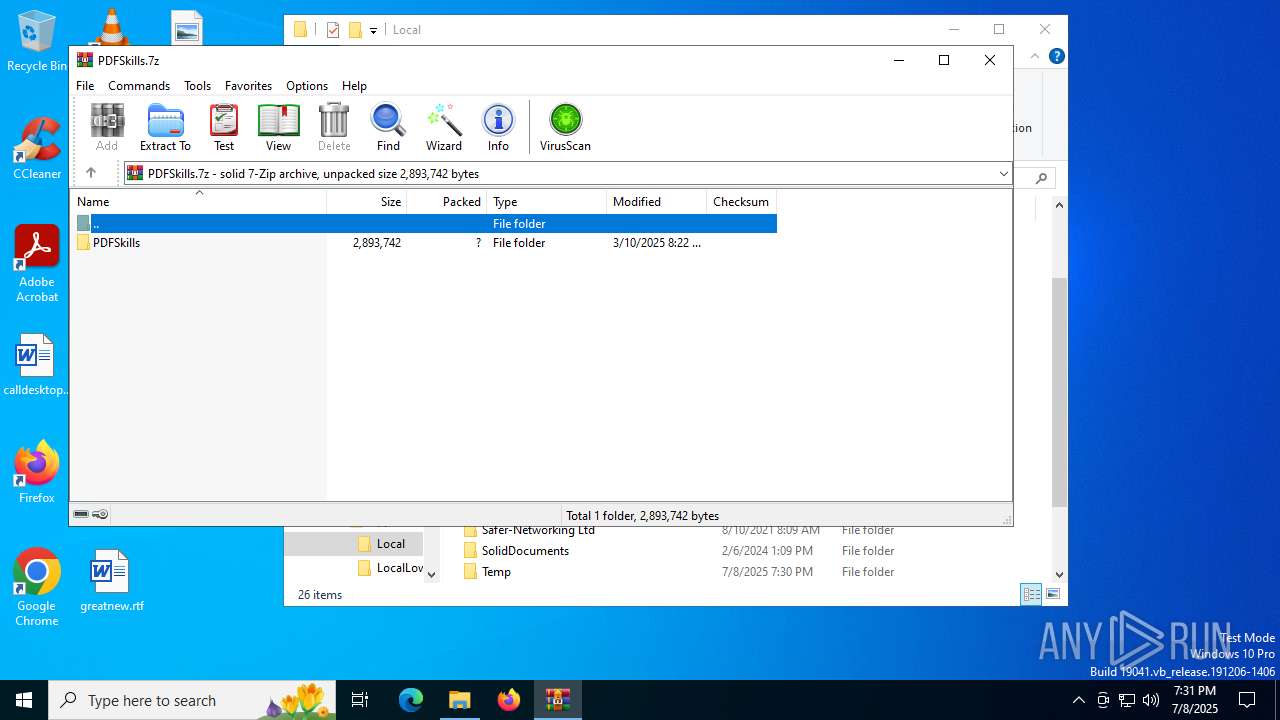
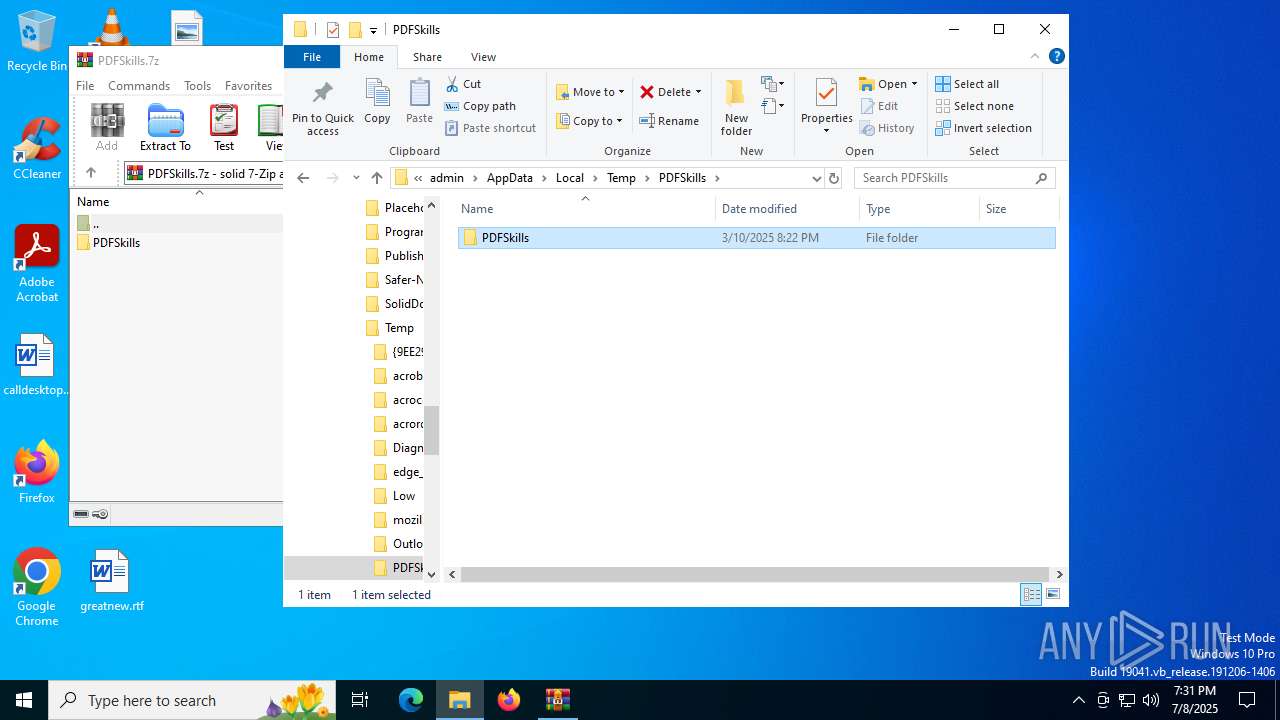
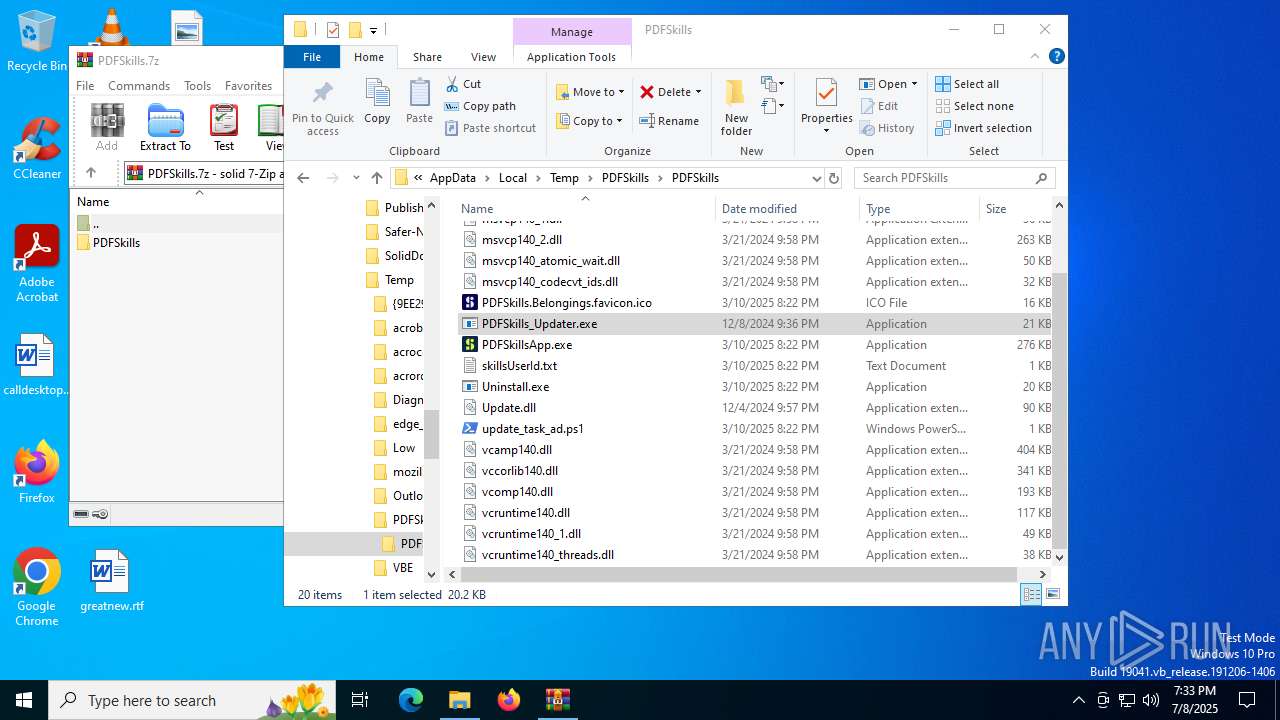
| File name: | PDFSkills.7z |
| Full analysis: | https://app.any.run/tasks/73bdeb8b-5866-4188-9a0b-4bbaf10acd8c |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 19:30:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/x-7z-compressed |
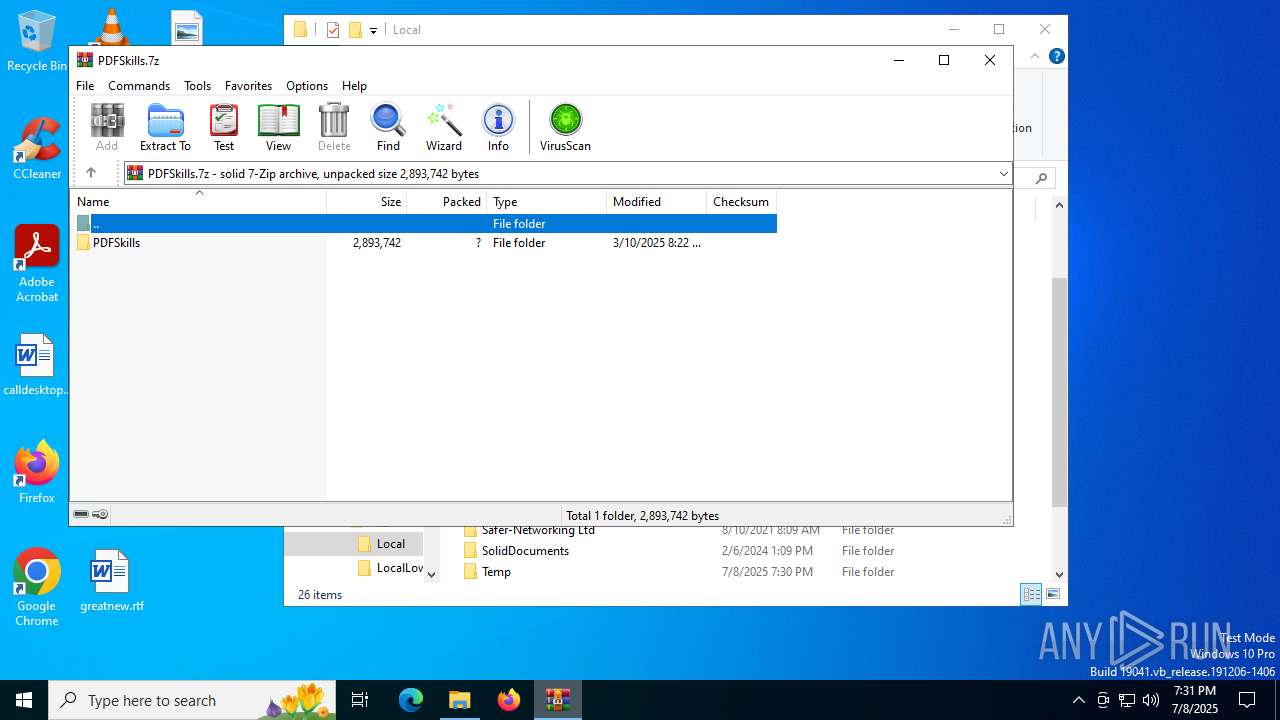
| File info: | 7-zip archive data, version 0.3 |
| MD5: | D57447AABFE1CD7039EEB16B1B21ED79 |
| SHA1: | 864363F109405CC9D4F8AA4D621BD33F616358B1 |
| SHA256: | DAE89726CAC255345704BFB908FD5FF44BC3E592977B7596C13591981EEA293E |
| SSDEEP: | 24576:oUHDYI0GtV49K0sln0dce5ylg3SZLs2+NBzkheF9w150BMp4QVaM00HY1vg+:oUHDYI0GtV49K0sln0dce5ylg3SZLsnJ |
MALICIOUS
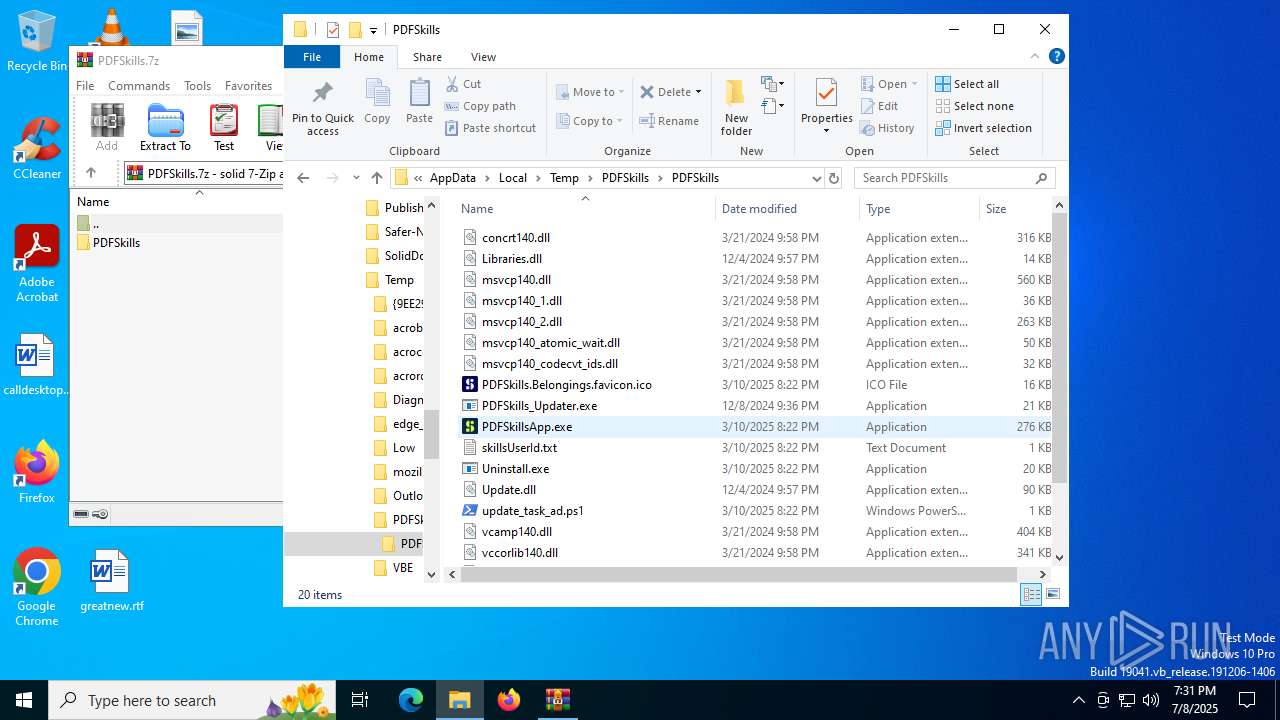
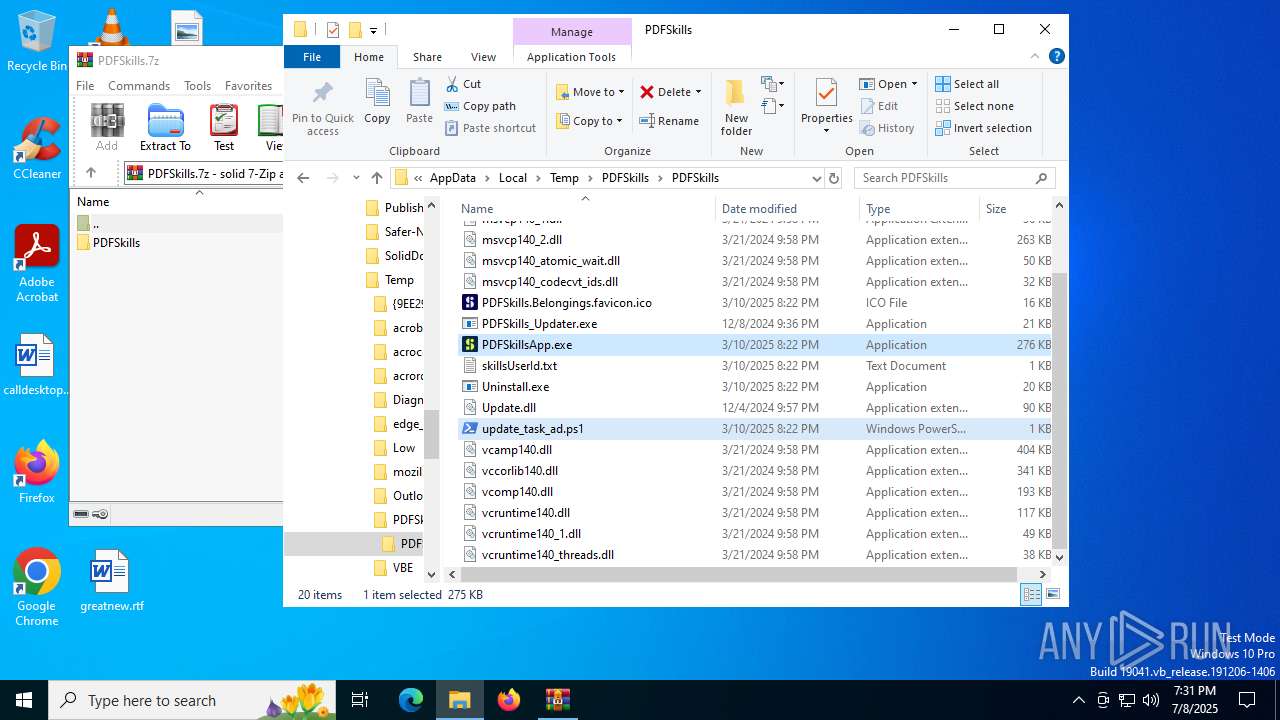
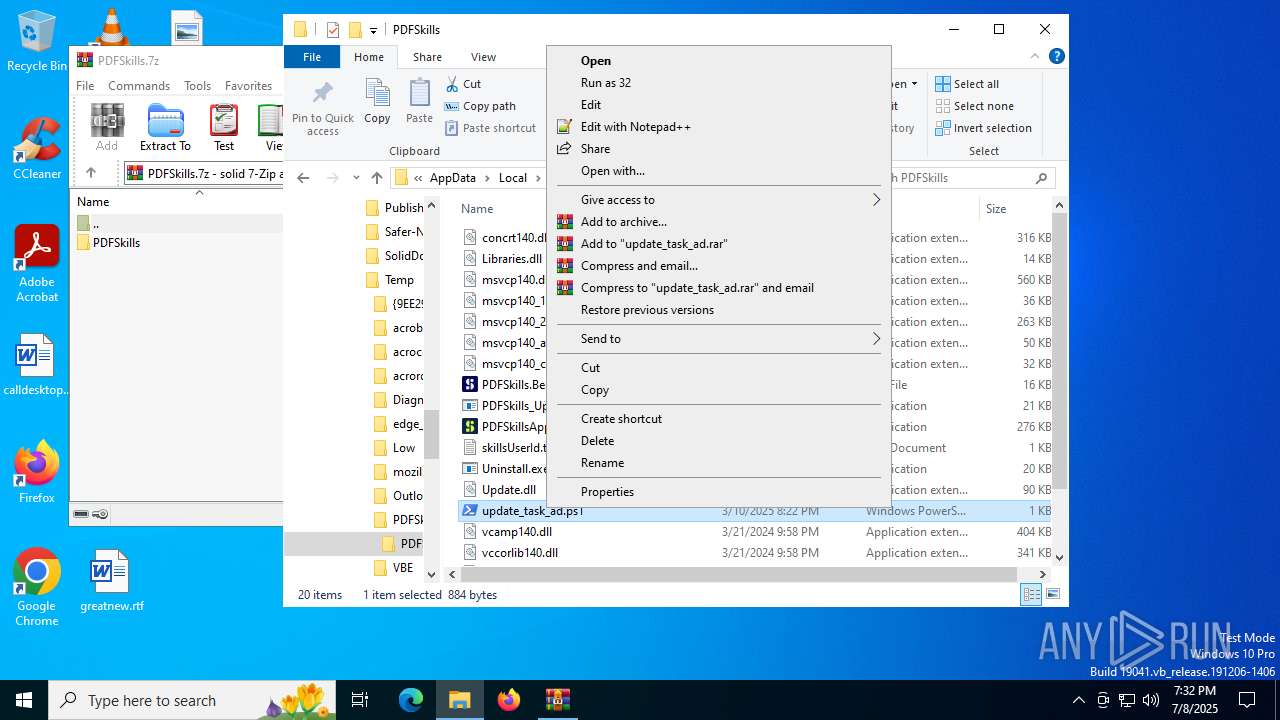
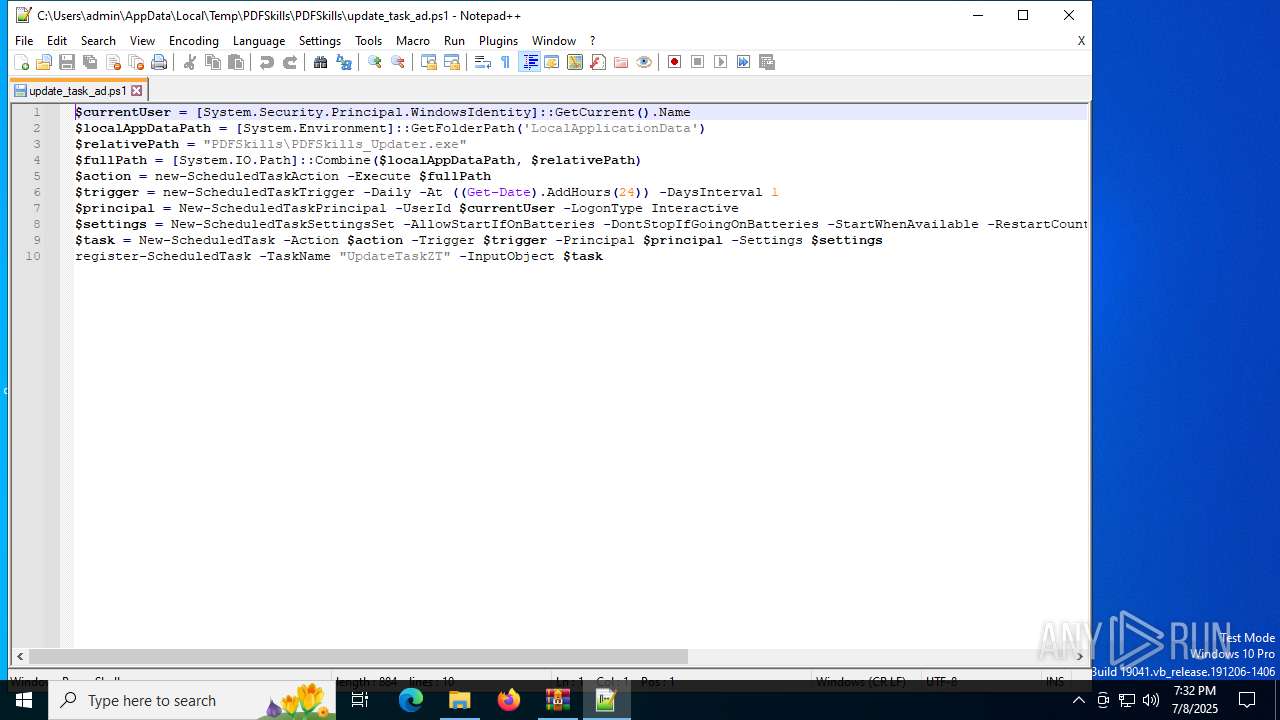
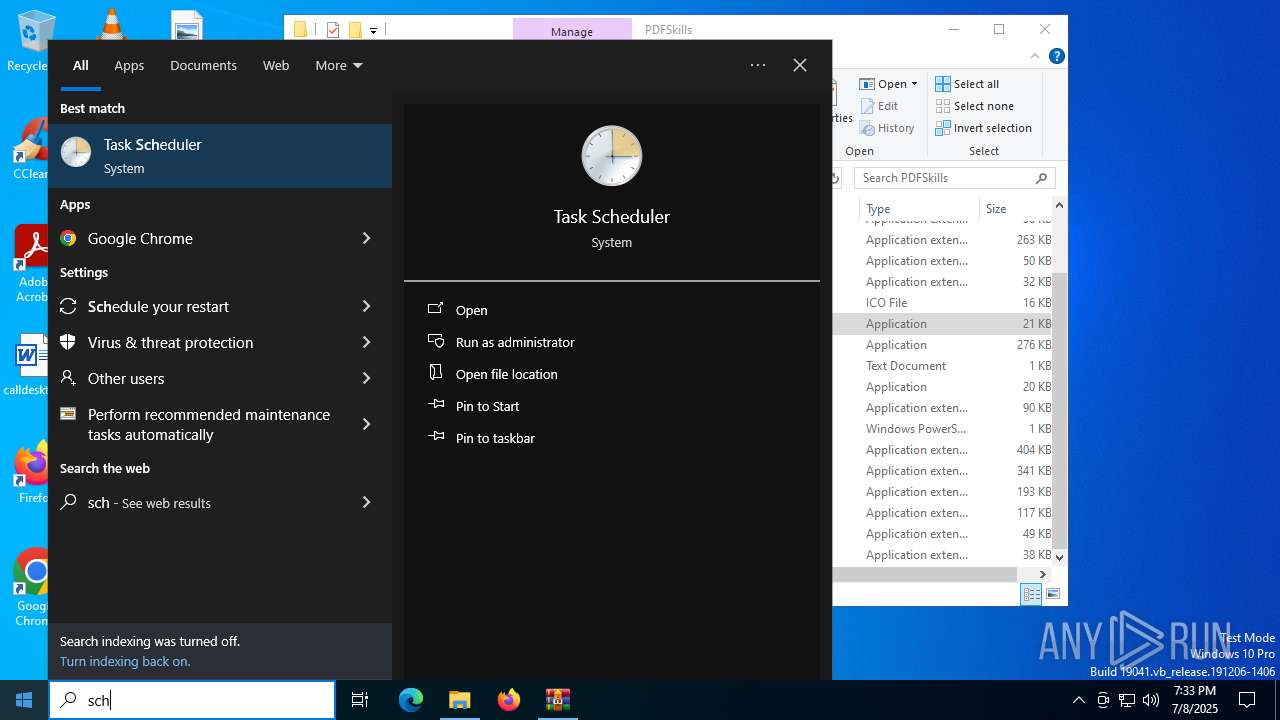
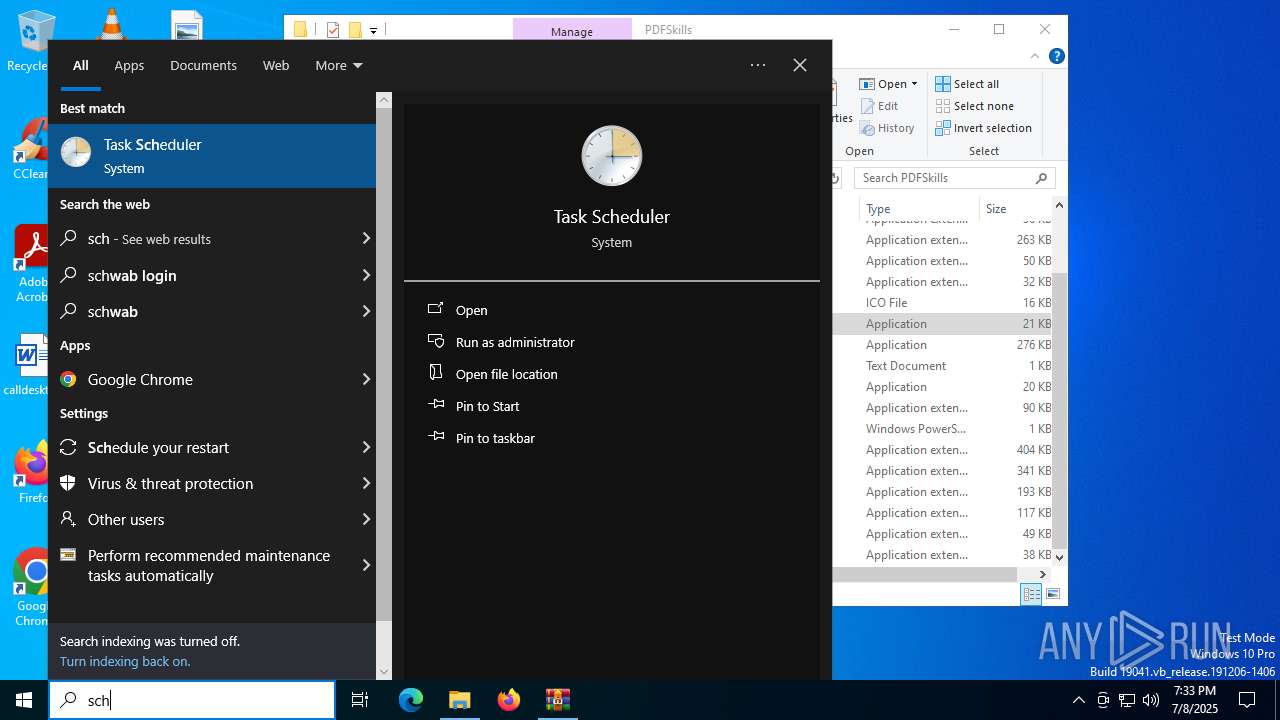
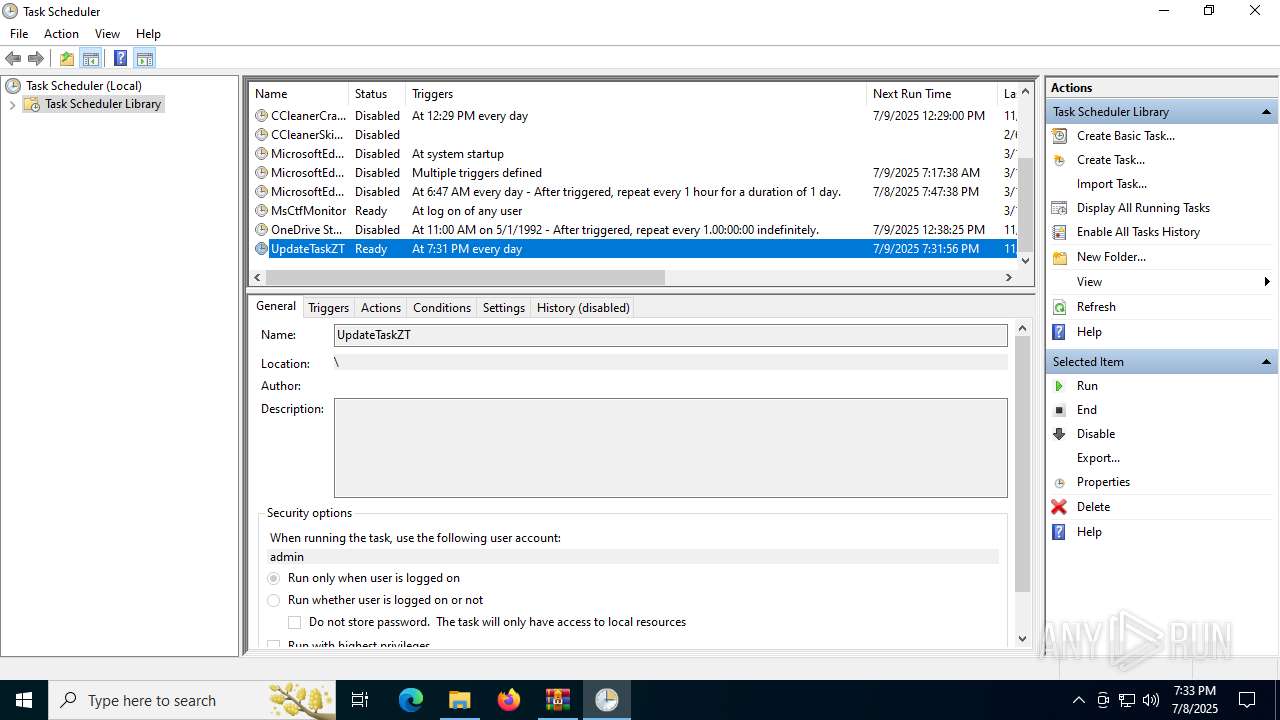
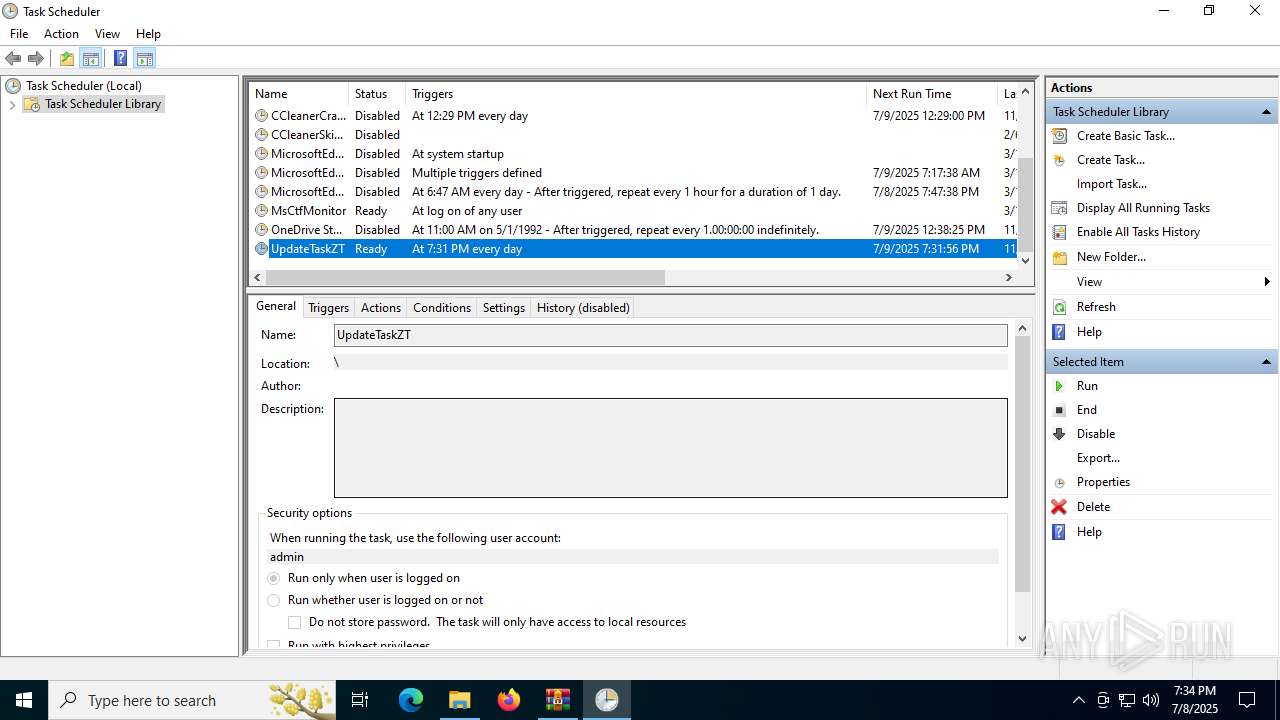
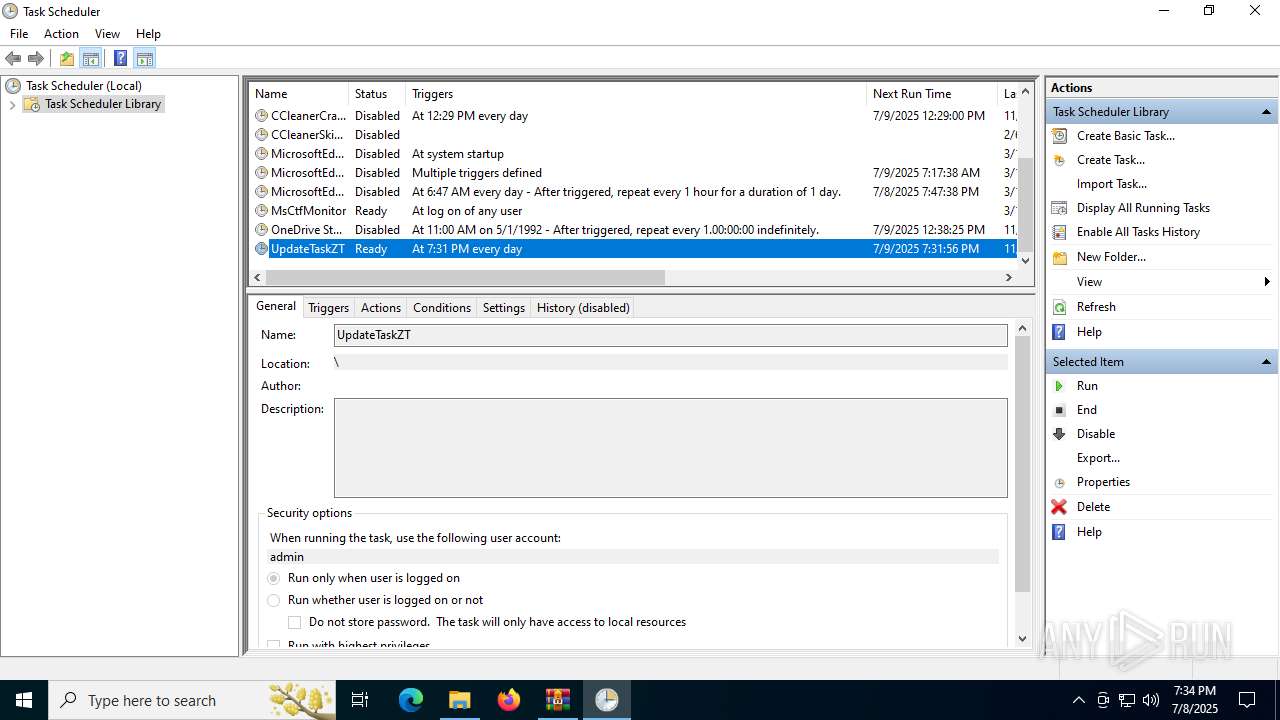
Bypass execution policy to execute commands
- powershell.exe (PID: 1356)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3820)
The process drops C-runtime libraries
- WinRAR.exe (PID: 3820)
Reads security settings of Internet Explorer
- PDFSkillsApp.exe (PID: 1512)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 1356)
INFO
Reads the machine GUID from the registry
- PDFSkillsApp.exe (PID: 1512)
- PDFSkills_Updater.exe (PID: 5724)
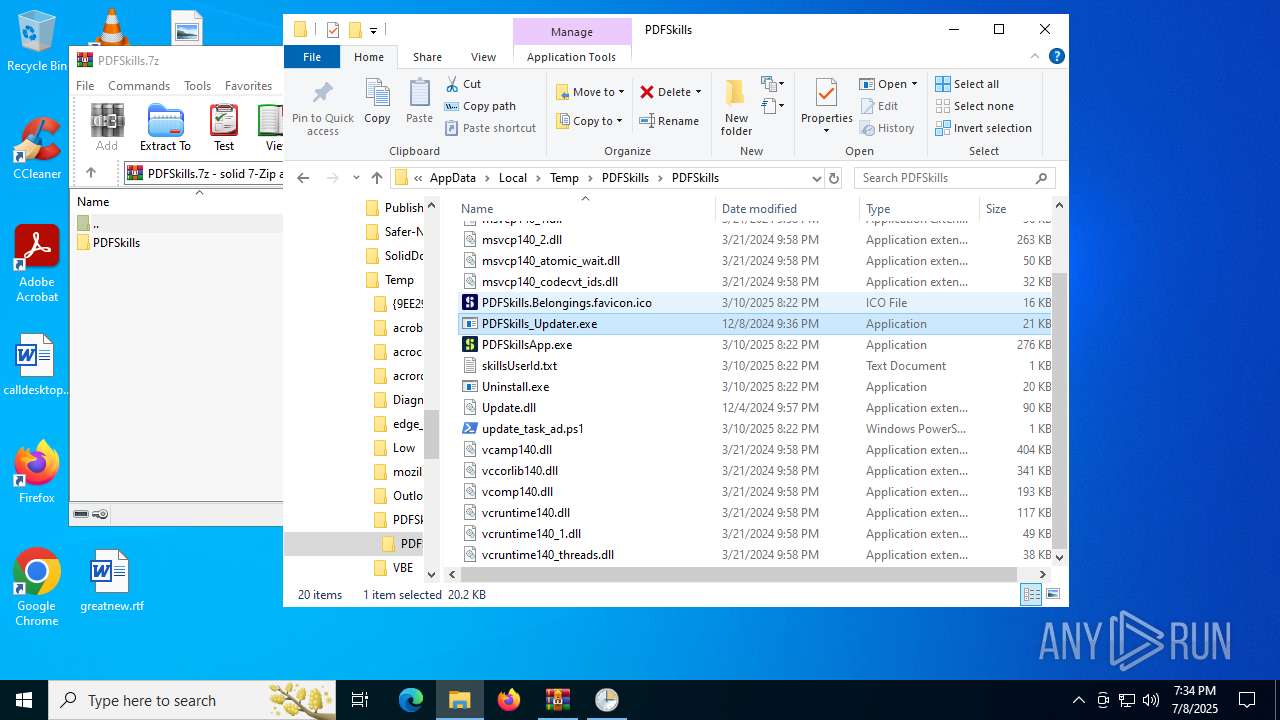
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3820)
The sample compiled with english language support
- WinRAR.exe (PID: 3820)
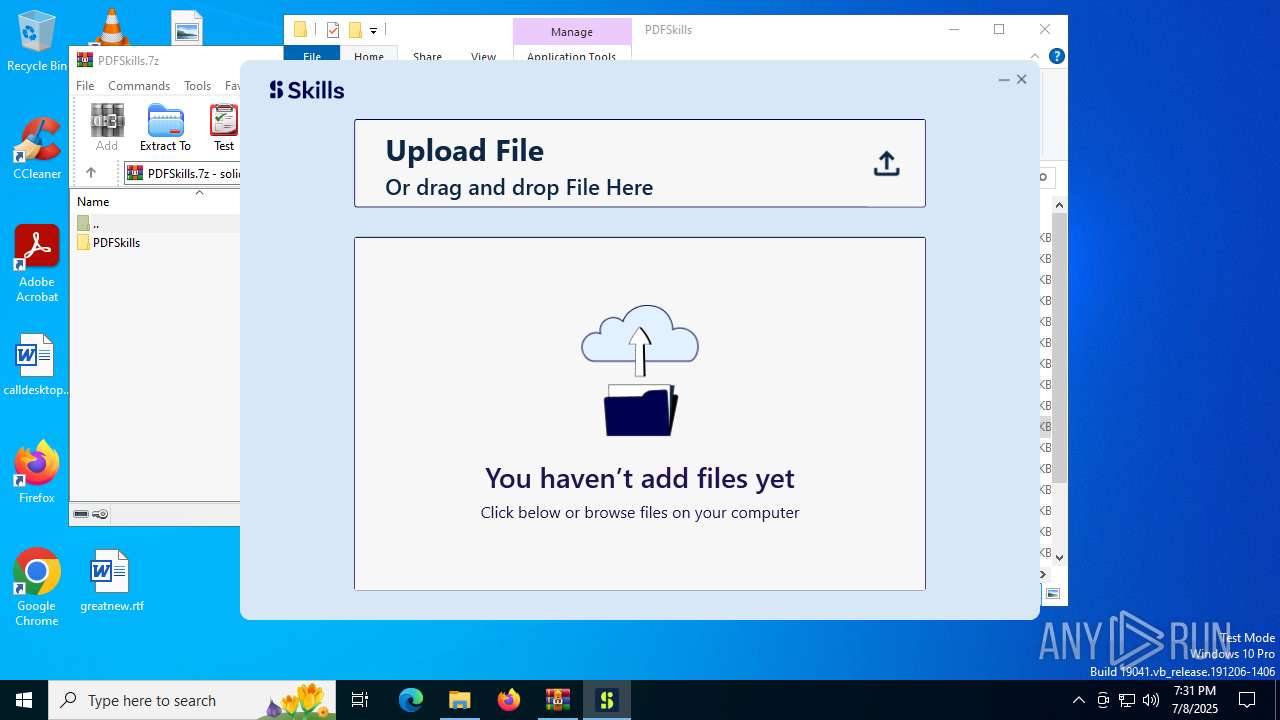
Manual execution by a user
- PDFSkillsApp.exe (PID: 1512)
- powershell.exe (PID: 1356)
- notepad++.exe (PID: 3716)
- PDFSkills_Updater.exe (PID: 5724)
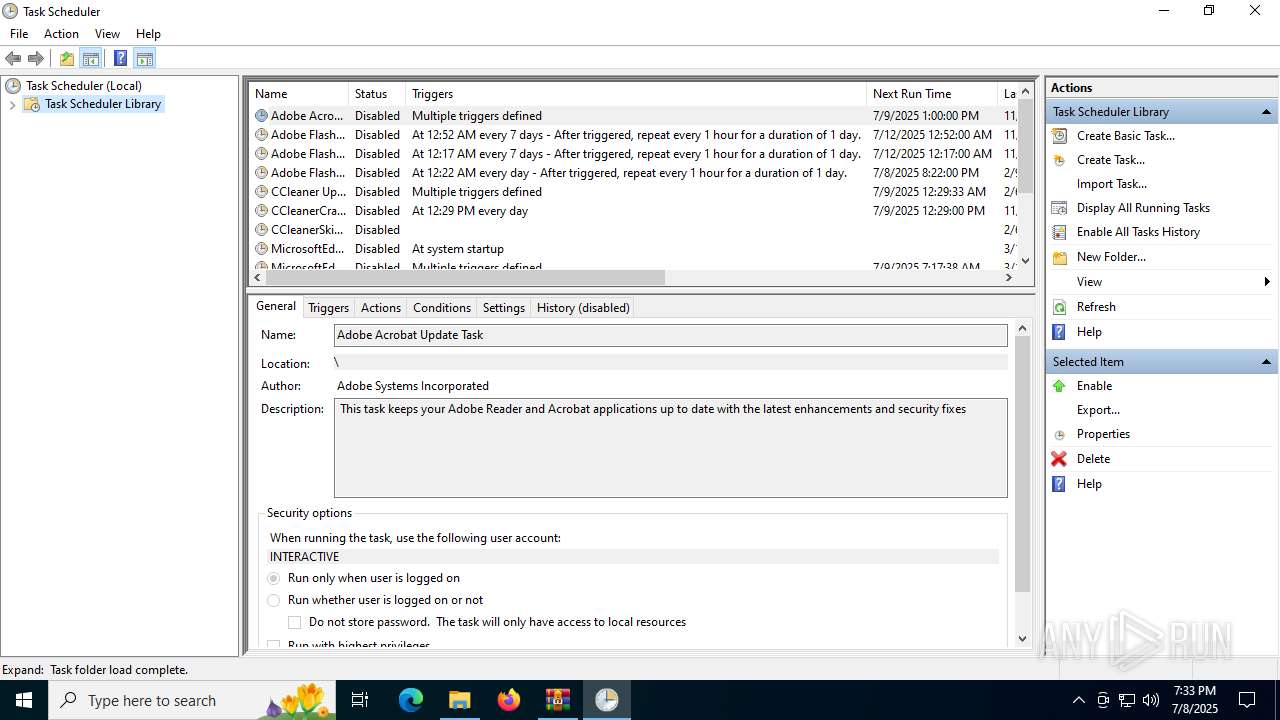
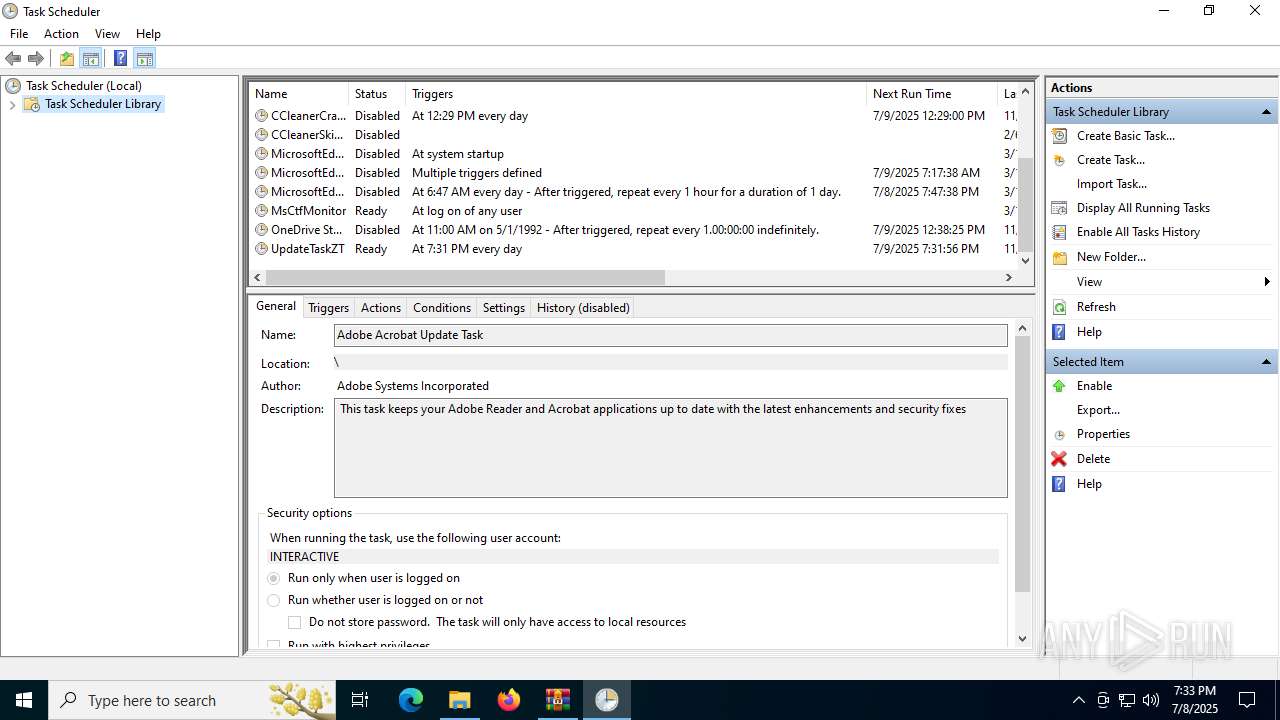
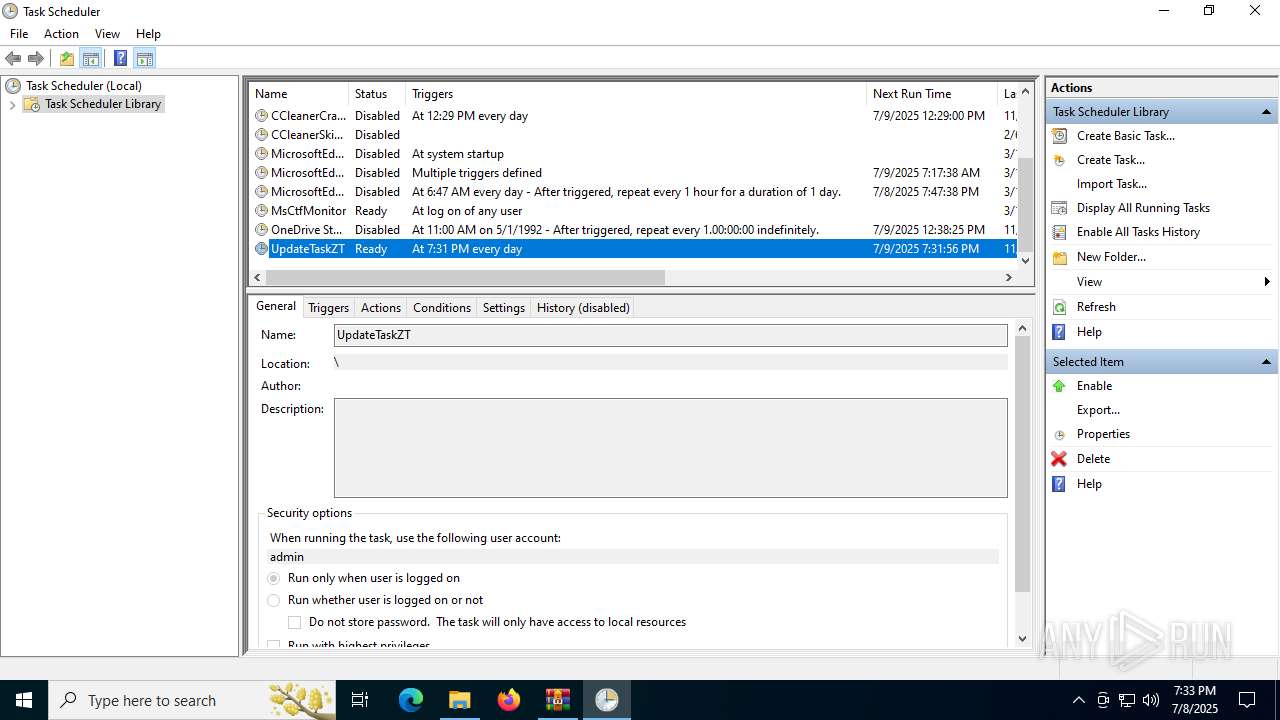
- mmc.exe (PID: 2804)
- mmc.exe (PID: 7040)
Checks supported languages
- PDFSkillsApp.exe (PID: 1512)
- PDFSkills_Updater.exe (PID: 5724)
Reads the computer name
- PDFSkillsApp.exe (PID: 1512)
- PDFSkills_Updater.exe (PID: 5724)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1356)
Checks proxy server information
- slui.exe (PID: 1028)
- PDFSkills_Updater.exe (PID: 5724)
Reads the software policy settings
- slui.exe (PID: 1028)
- PDFSkills_Updater.exe (PID: 5724)
Reads Environment values
- PDFSkills_Updater.exe (PID: 5724)
Disables trace logs
- PDFSkills_Updater.exe (PID: 5724)
Reads security settings of Internet Explorer
- mmc.exe (PID: 7040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
EXIF
ZIP
| FileVersion: | 7z v0.03 |
|---|---|
| ModifyDate: | 2024:03:21 21:58:24+00:00 |
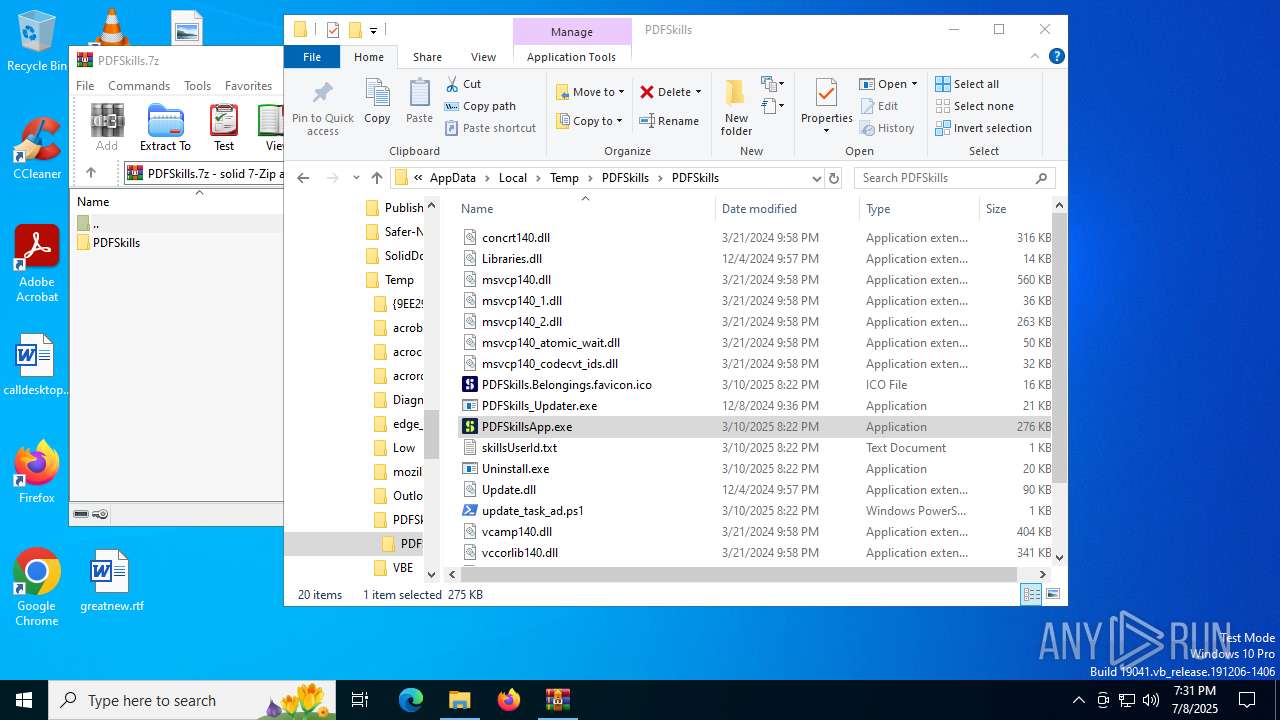
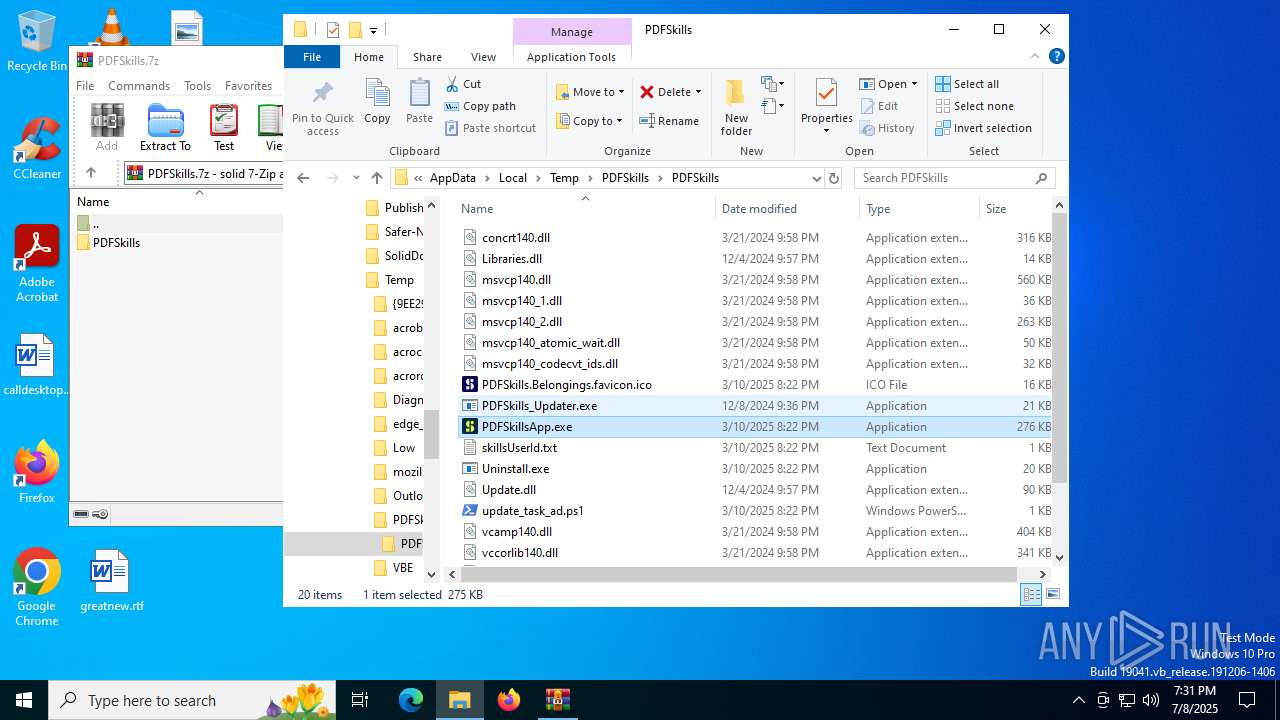
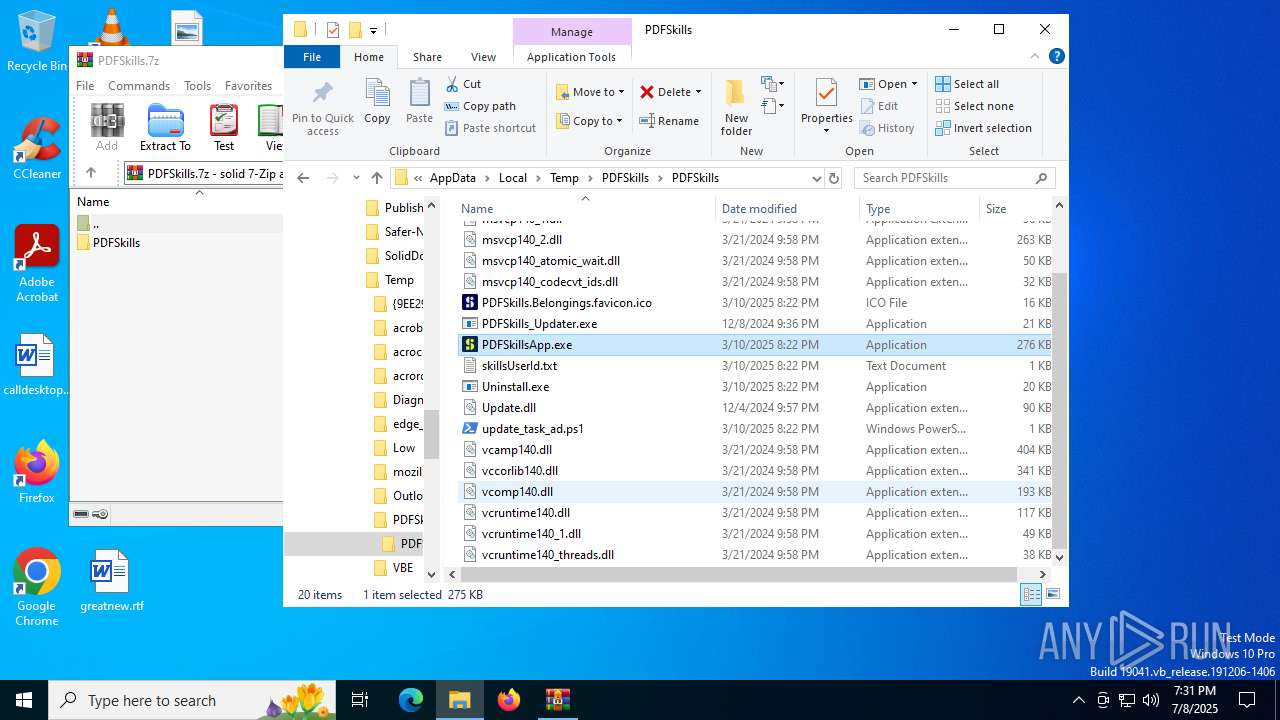
| ArchivedFileName: | PDFSkills/concrt140.dll |
Total processes
149
Monitored processes
10
Malicious processes
1
Suspicious processes
0
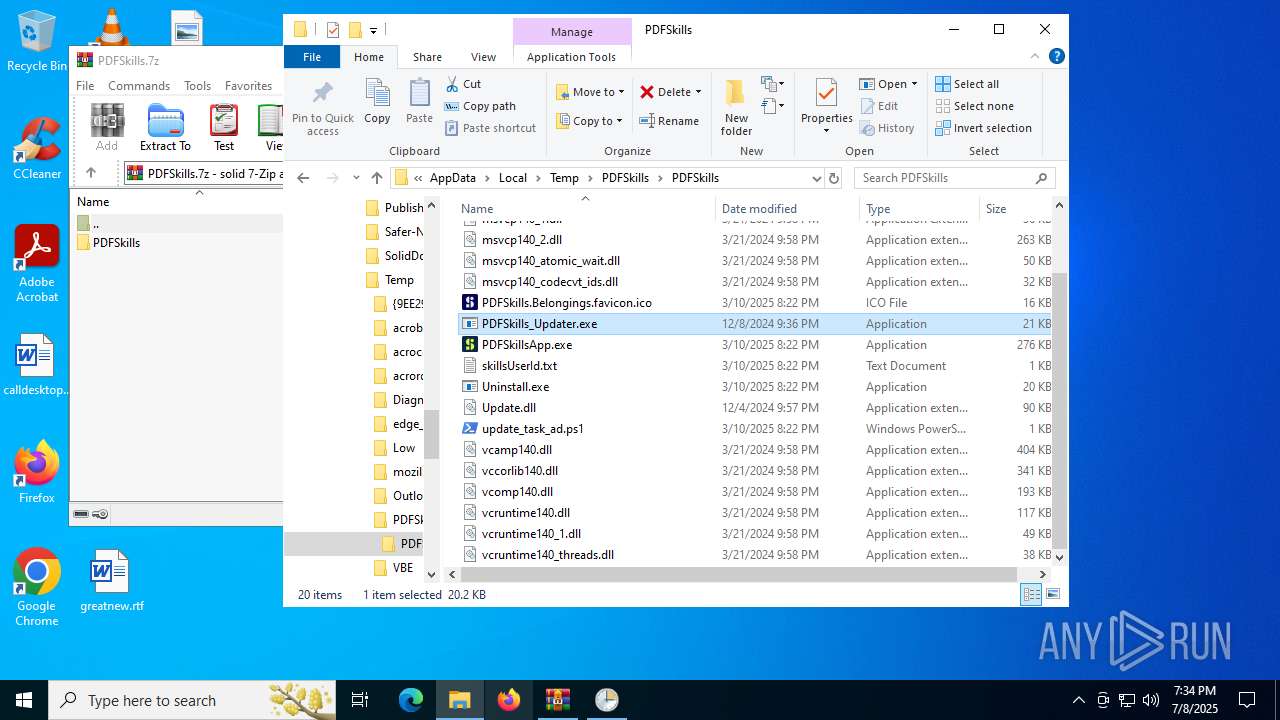
Behavior graph
Click at the process to see the details
Process information
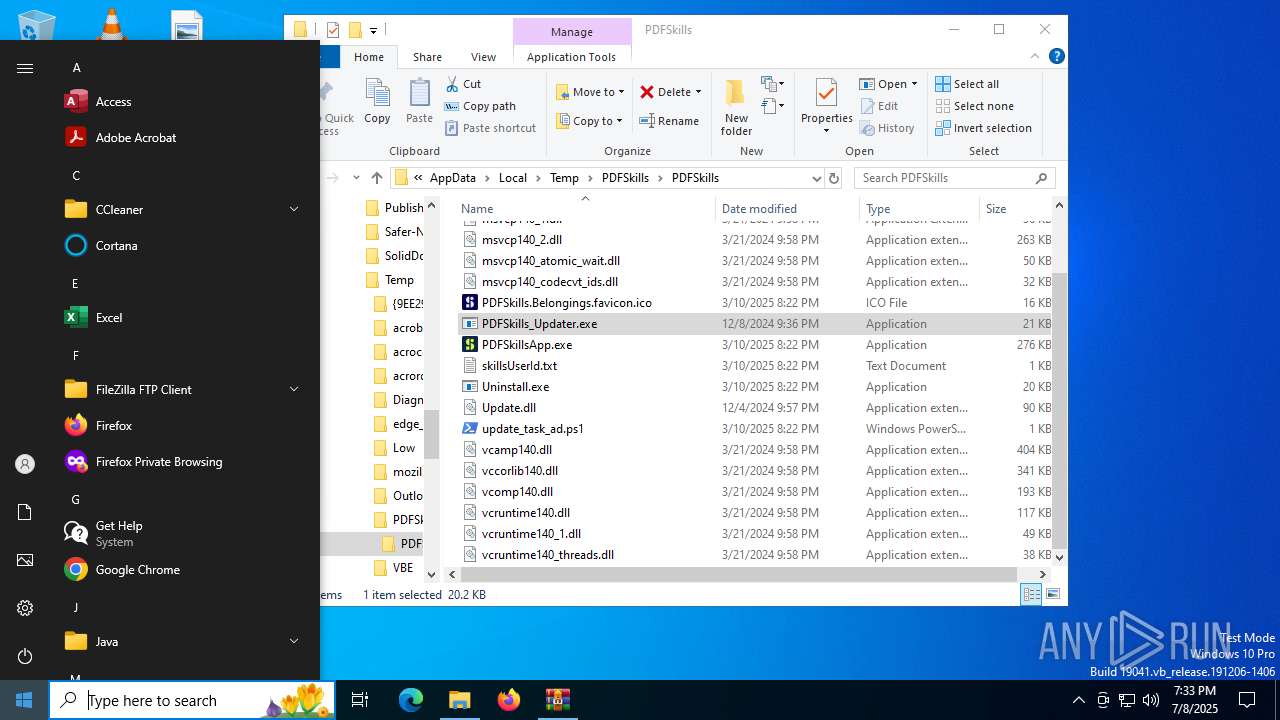
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
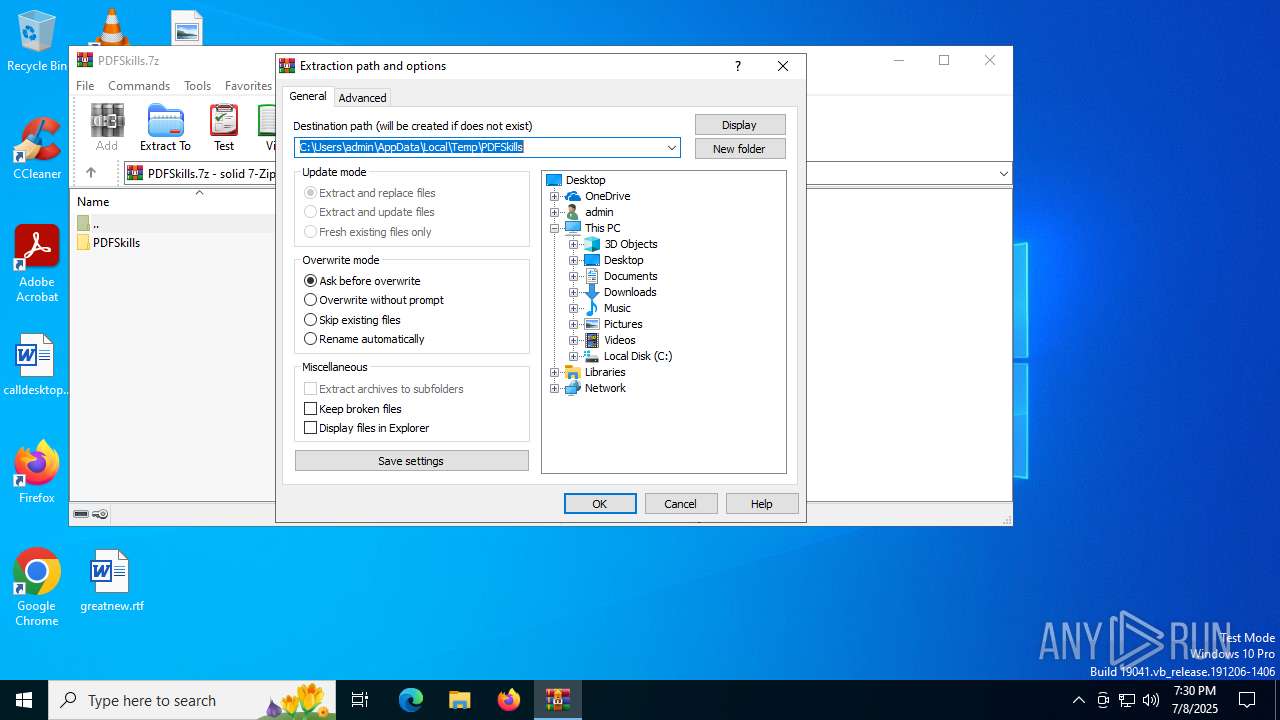
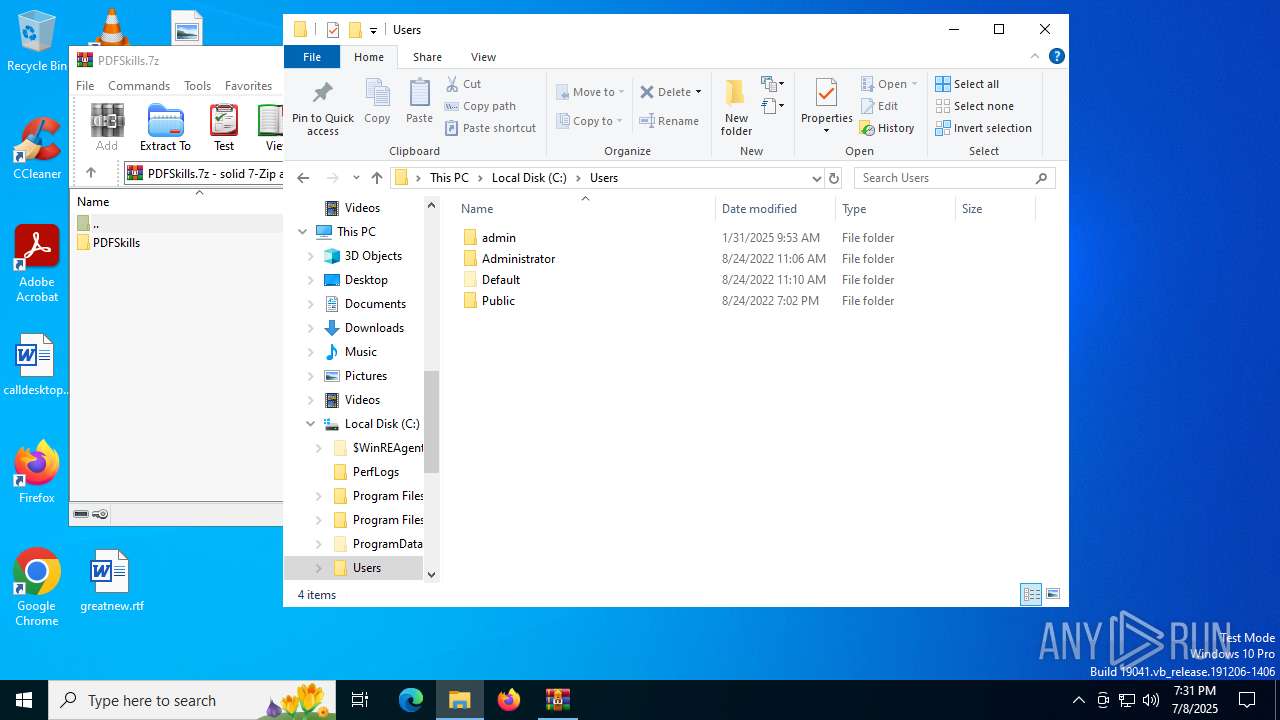
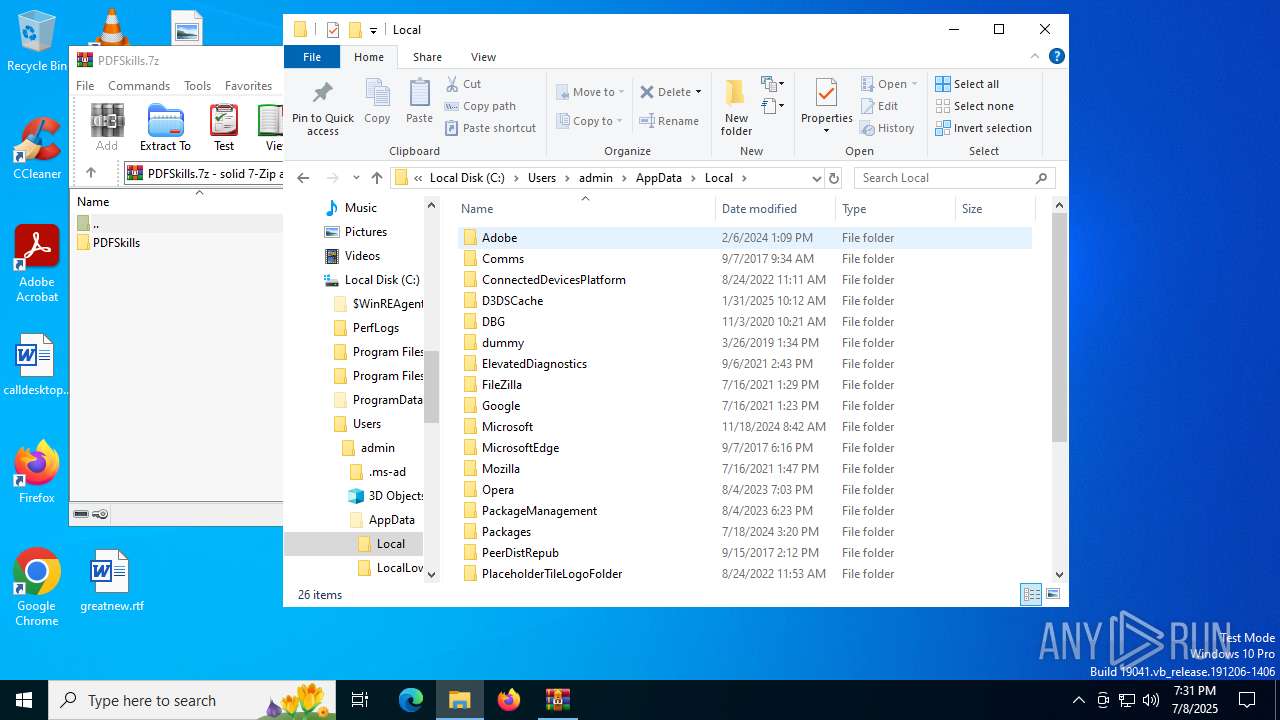
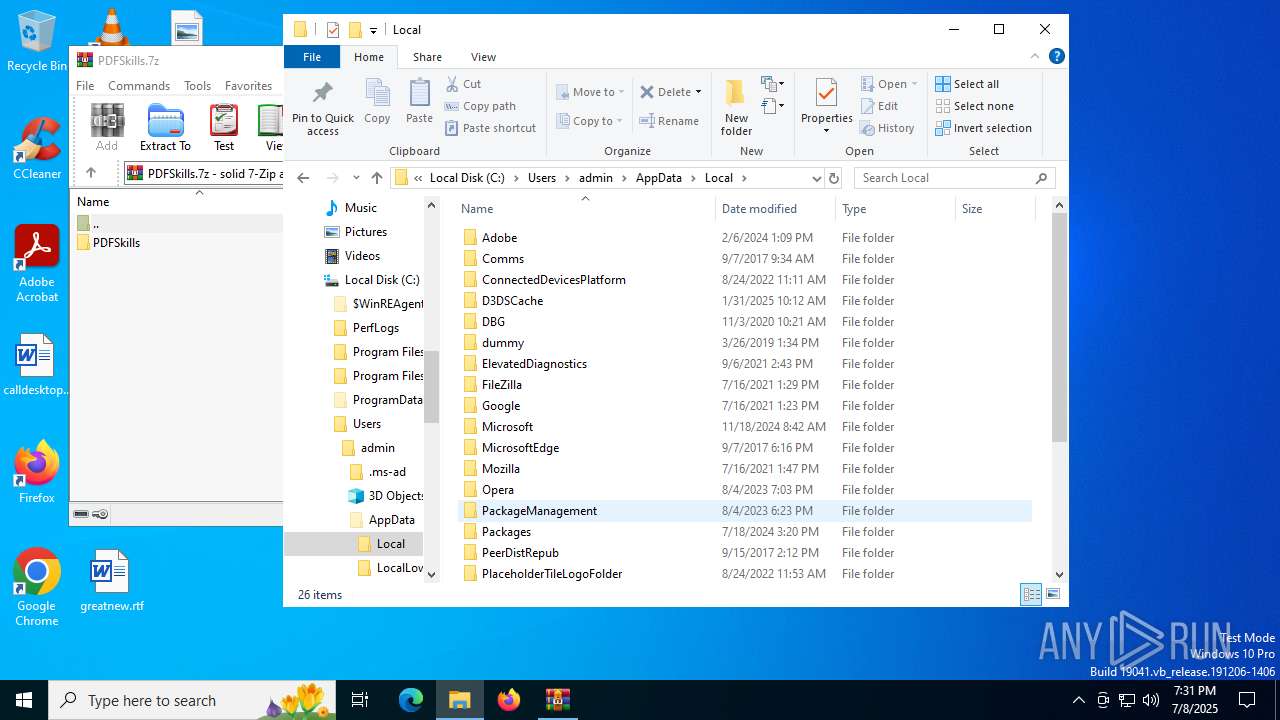
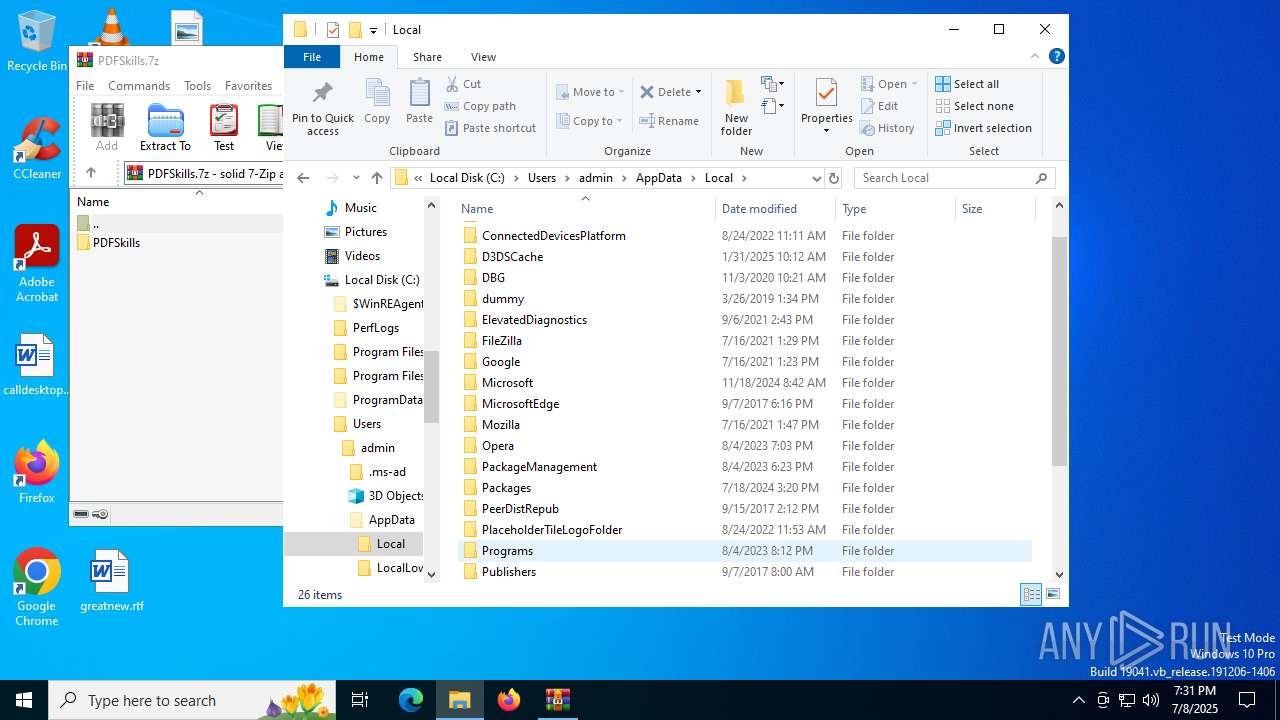
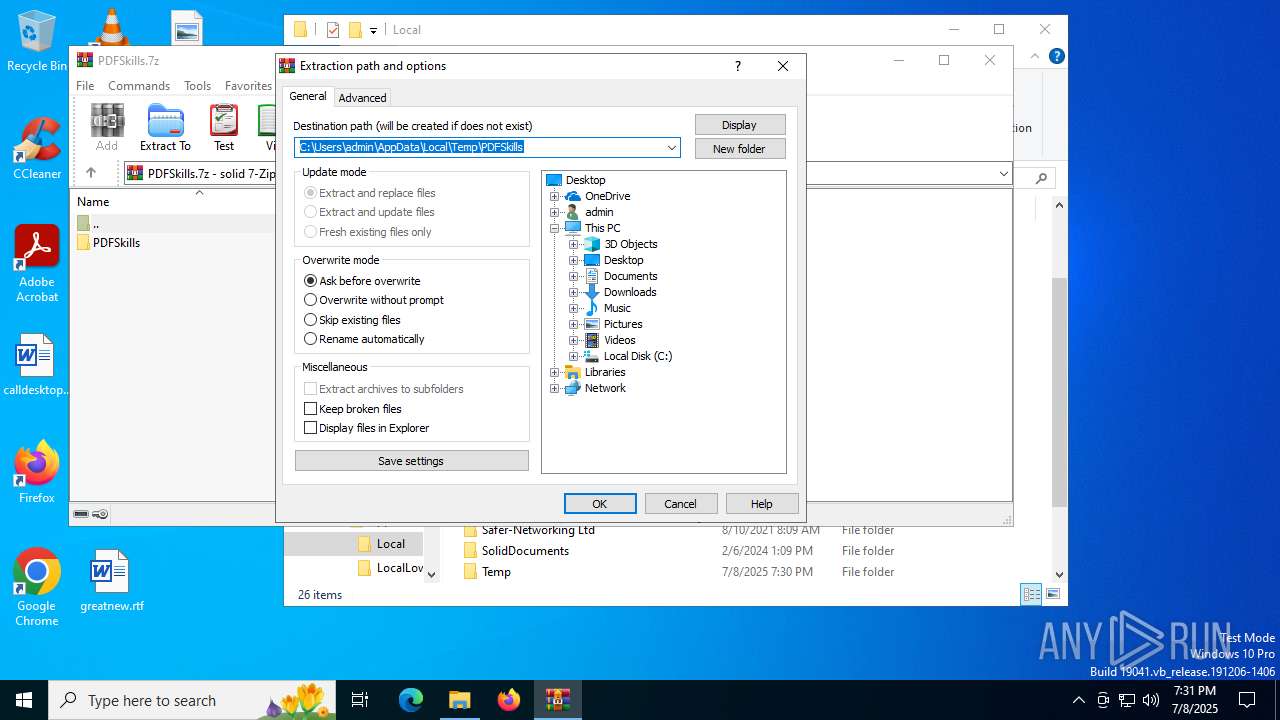
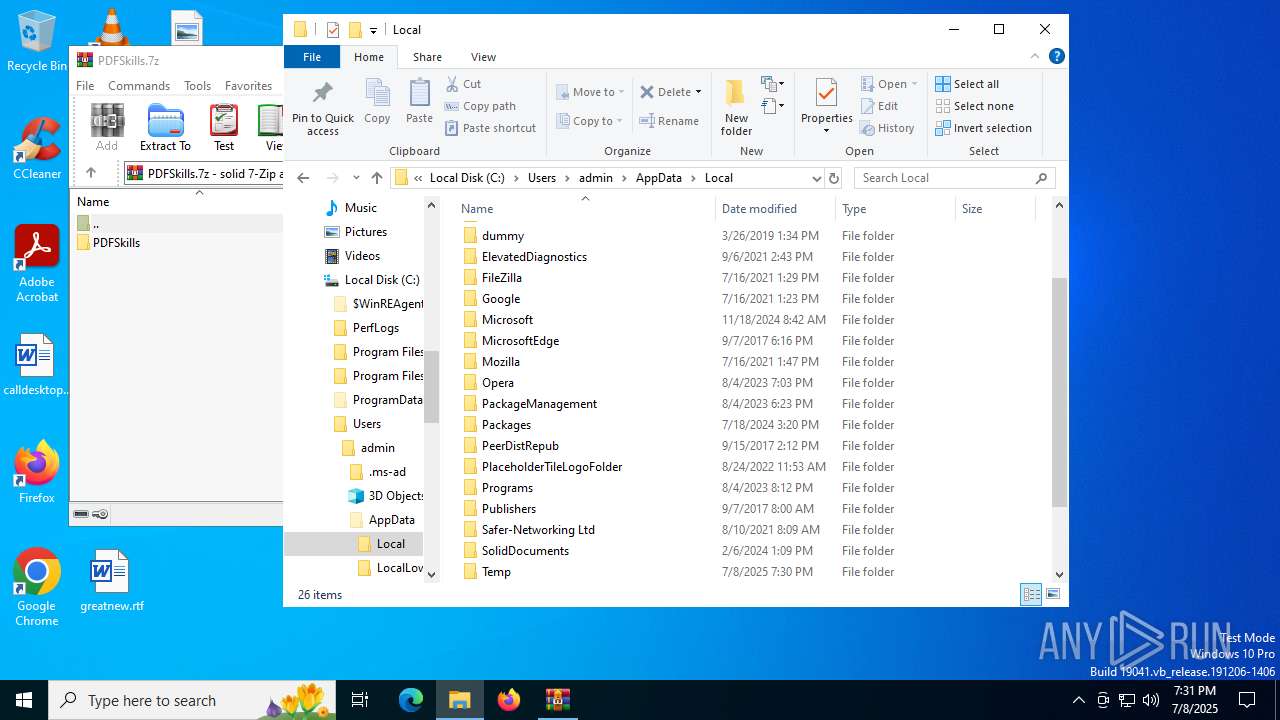
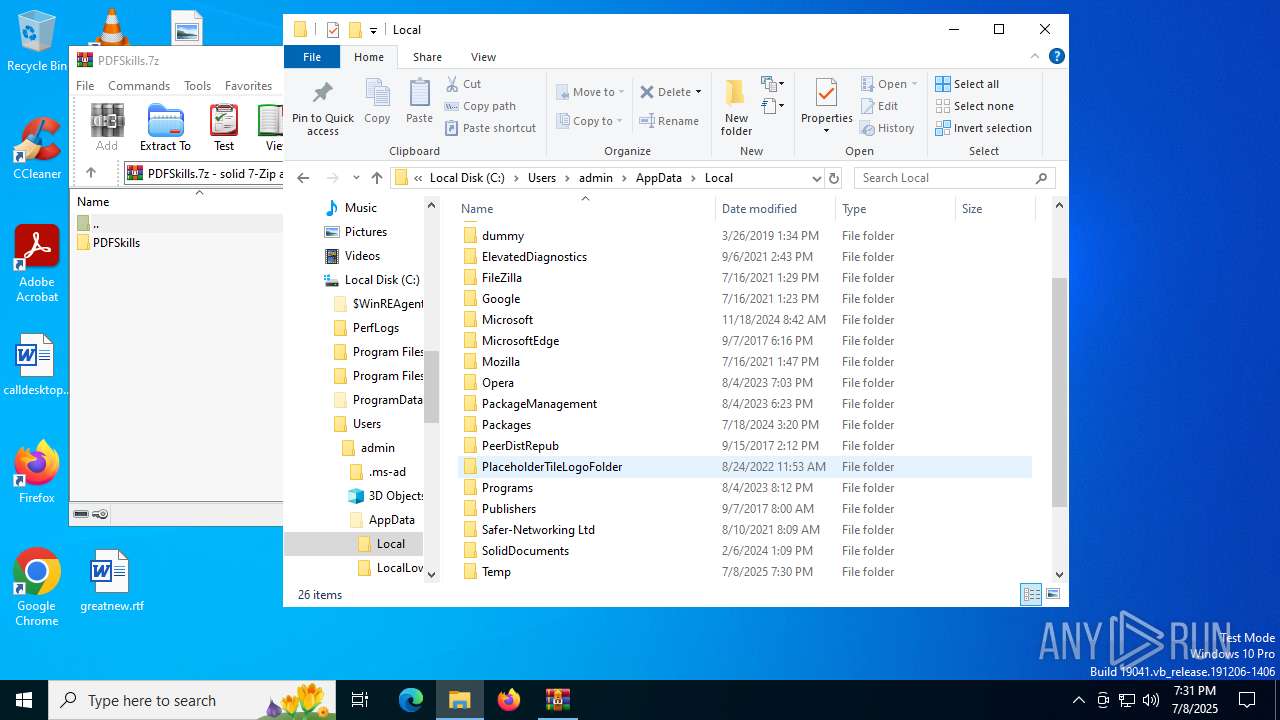
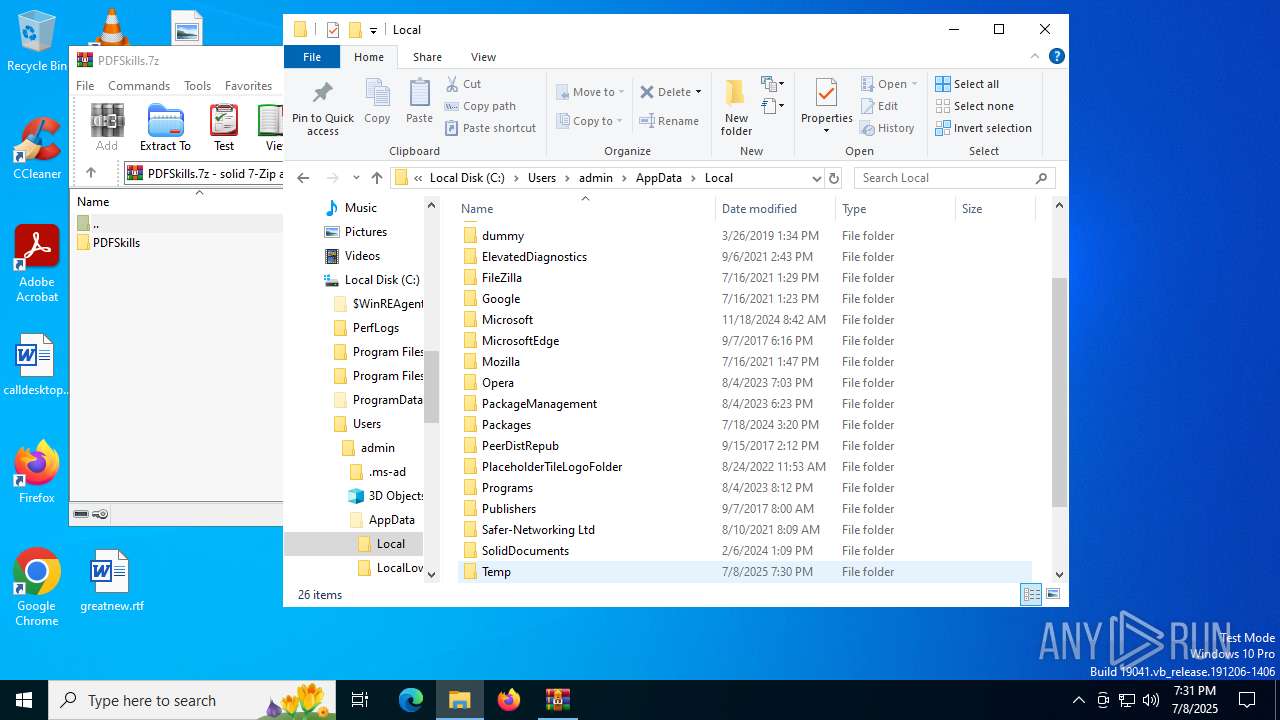
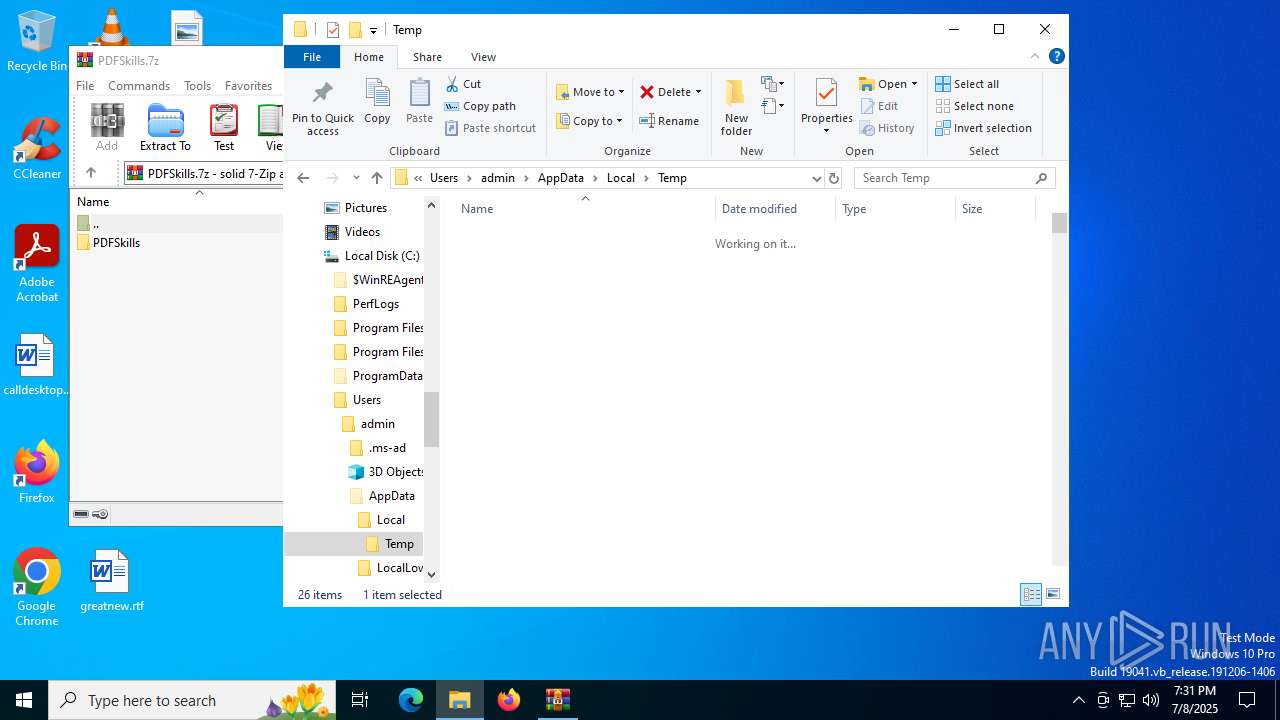
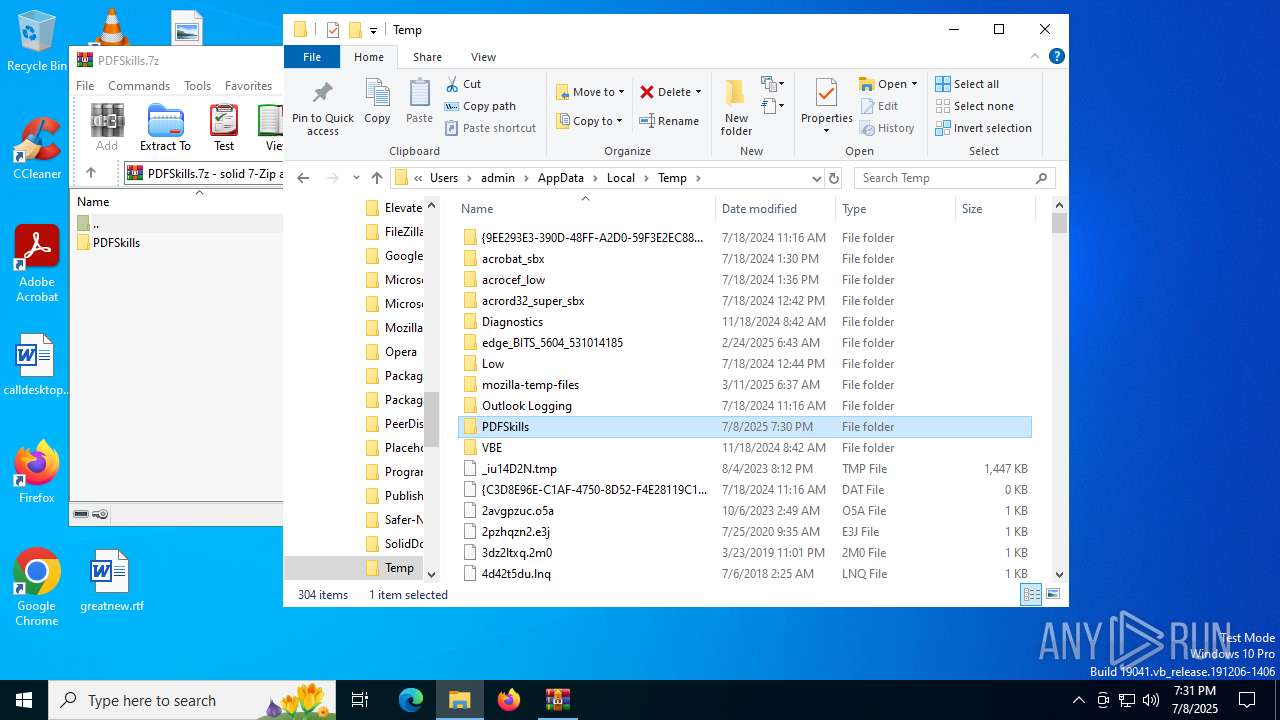
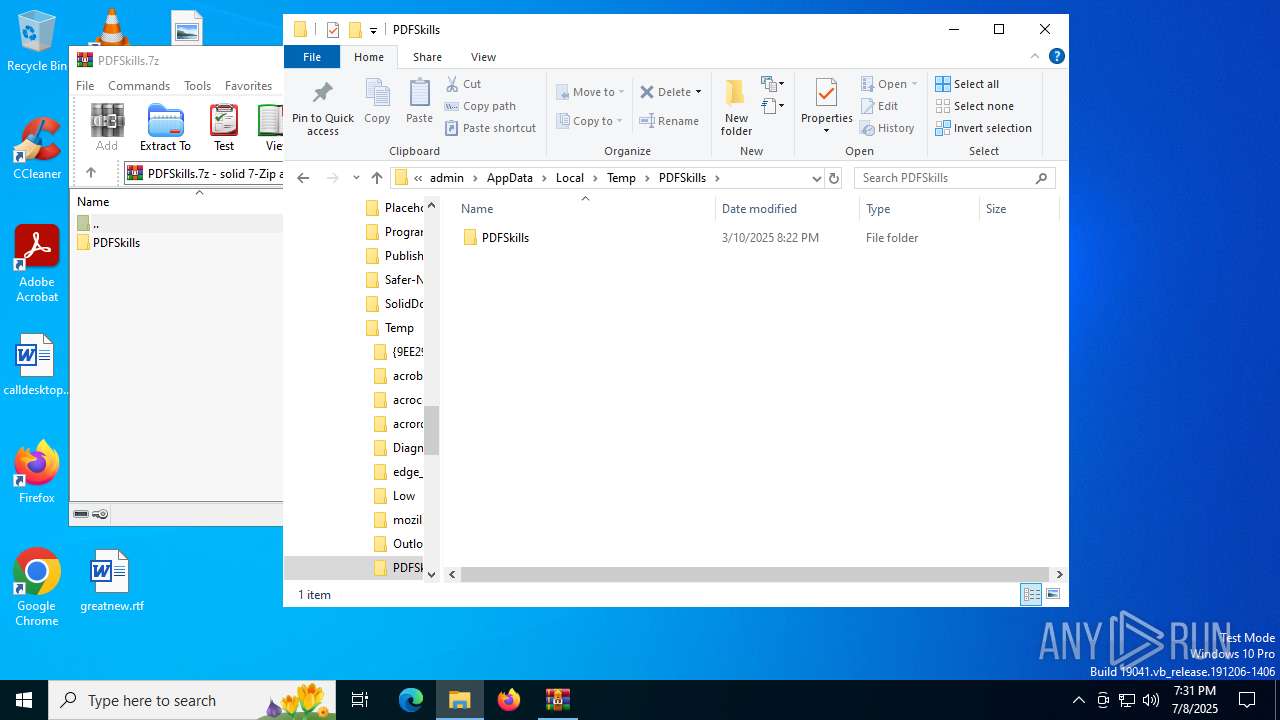
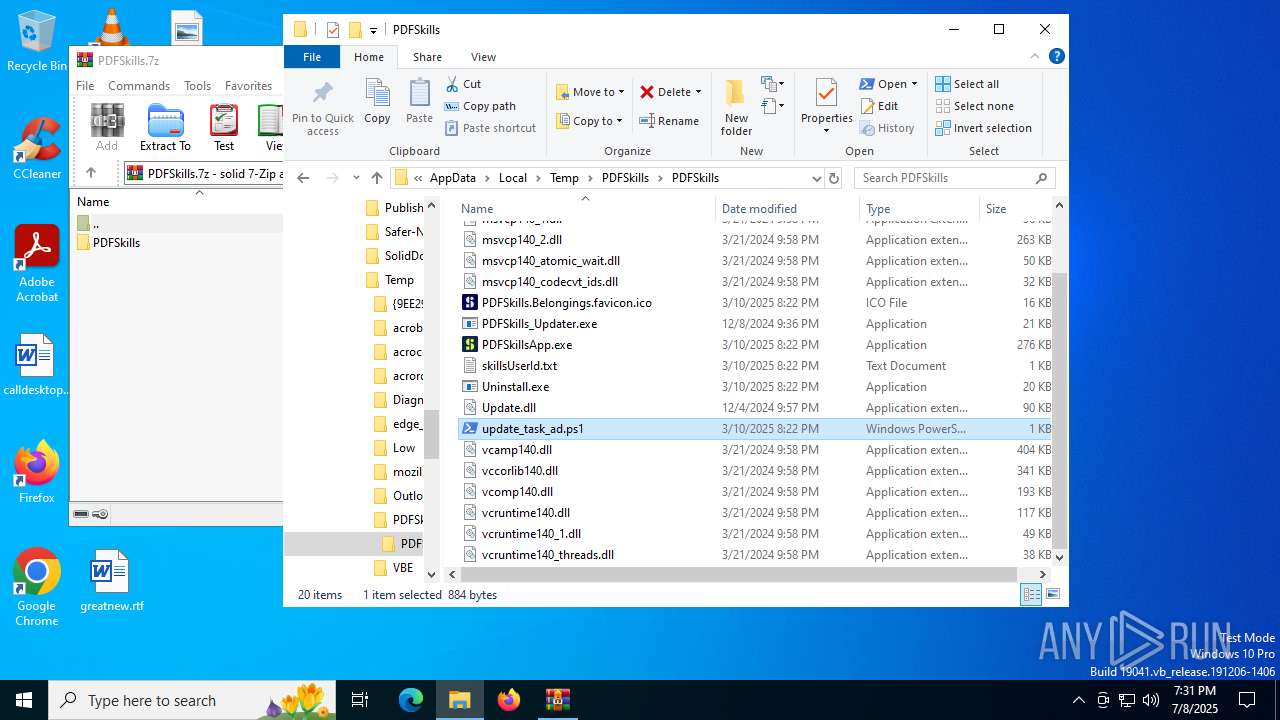
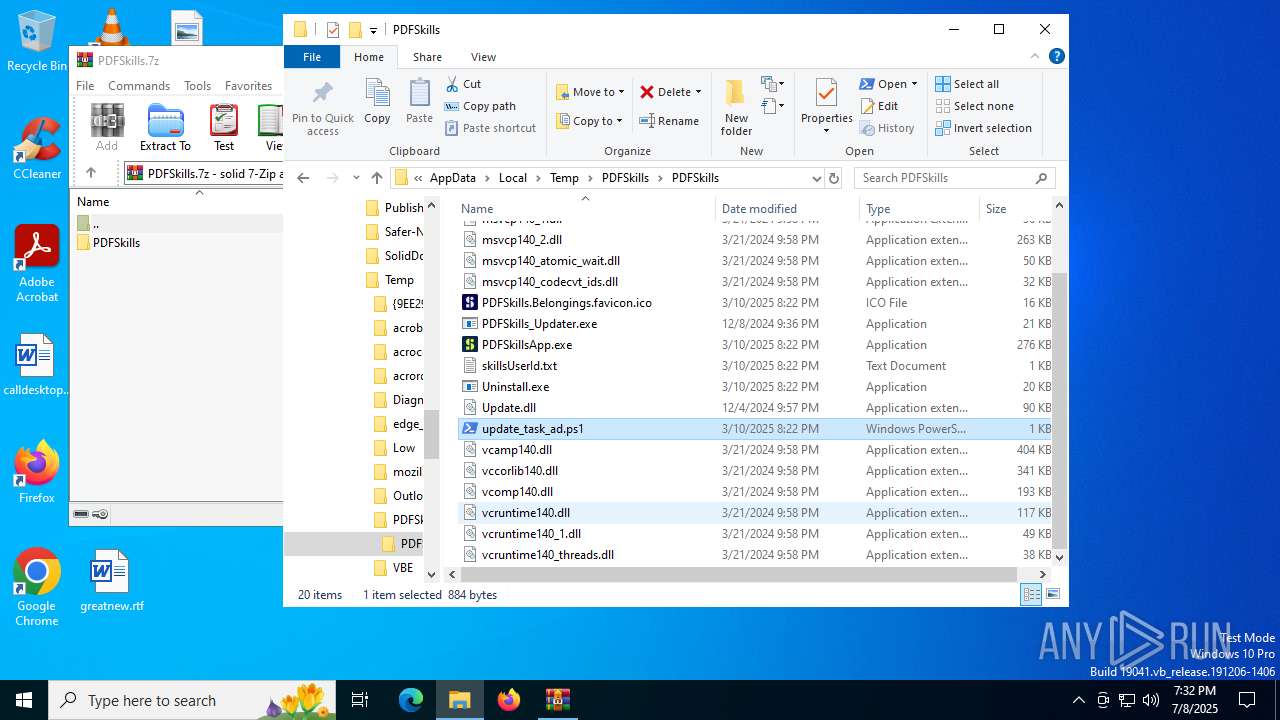
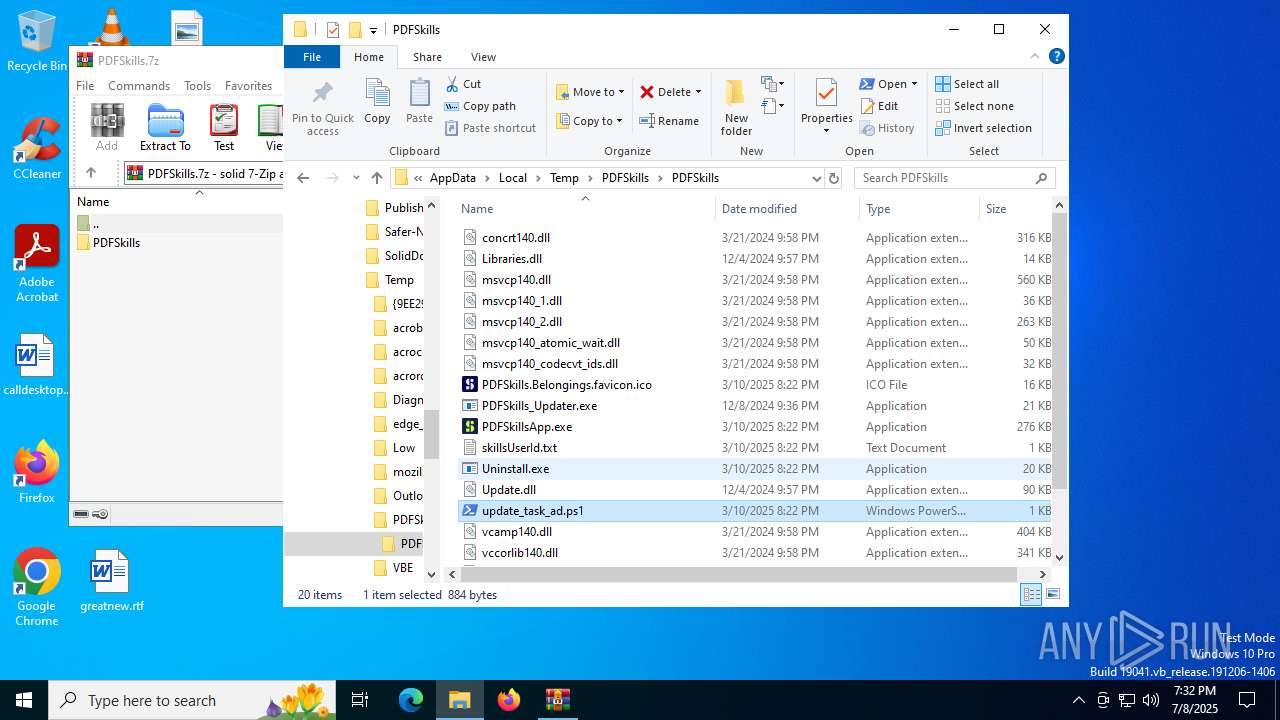
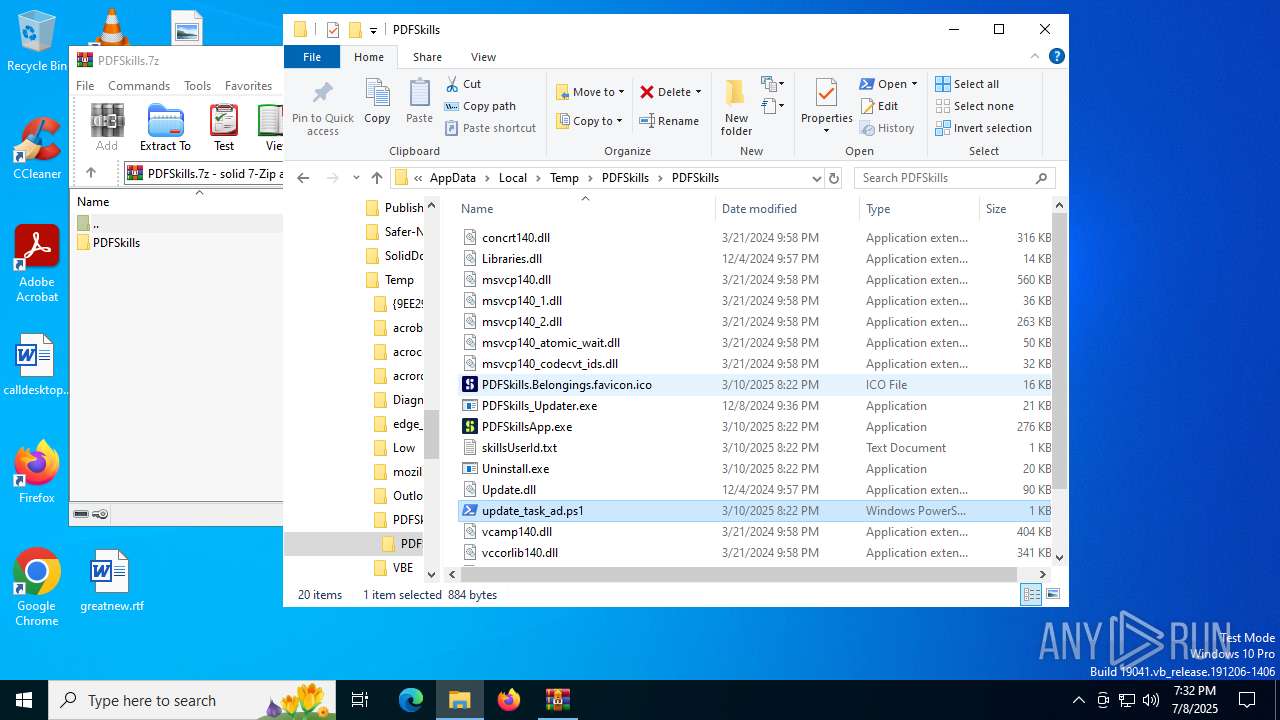
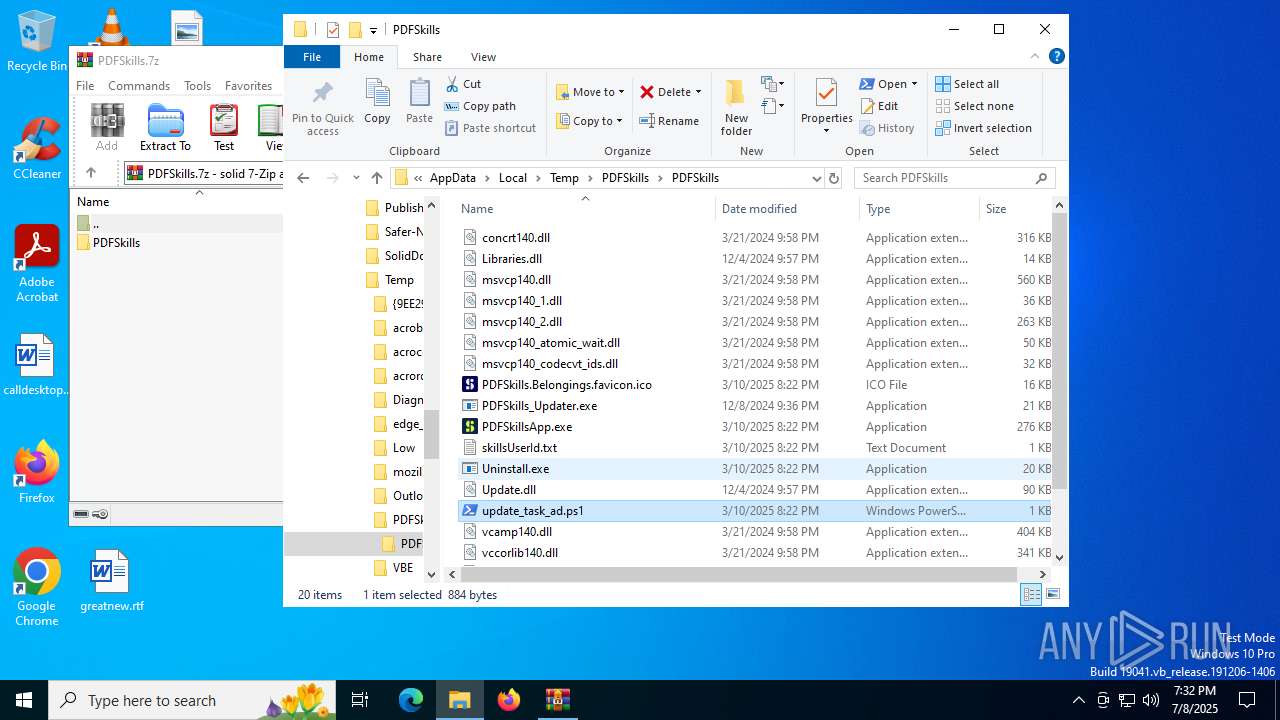
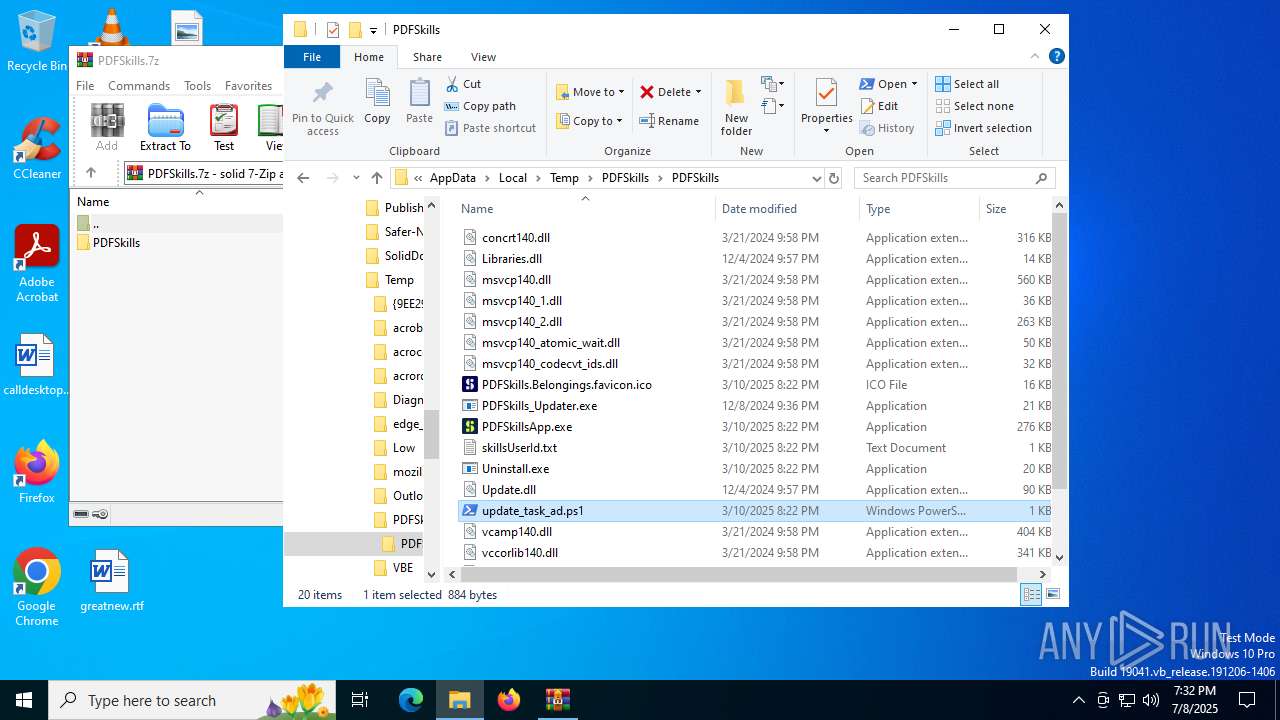
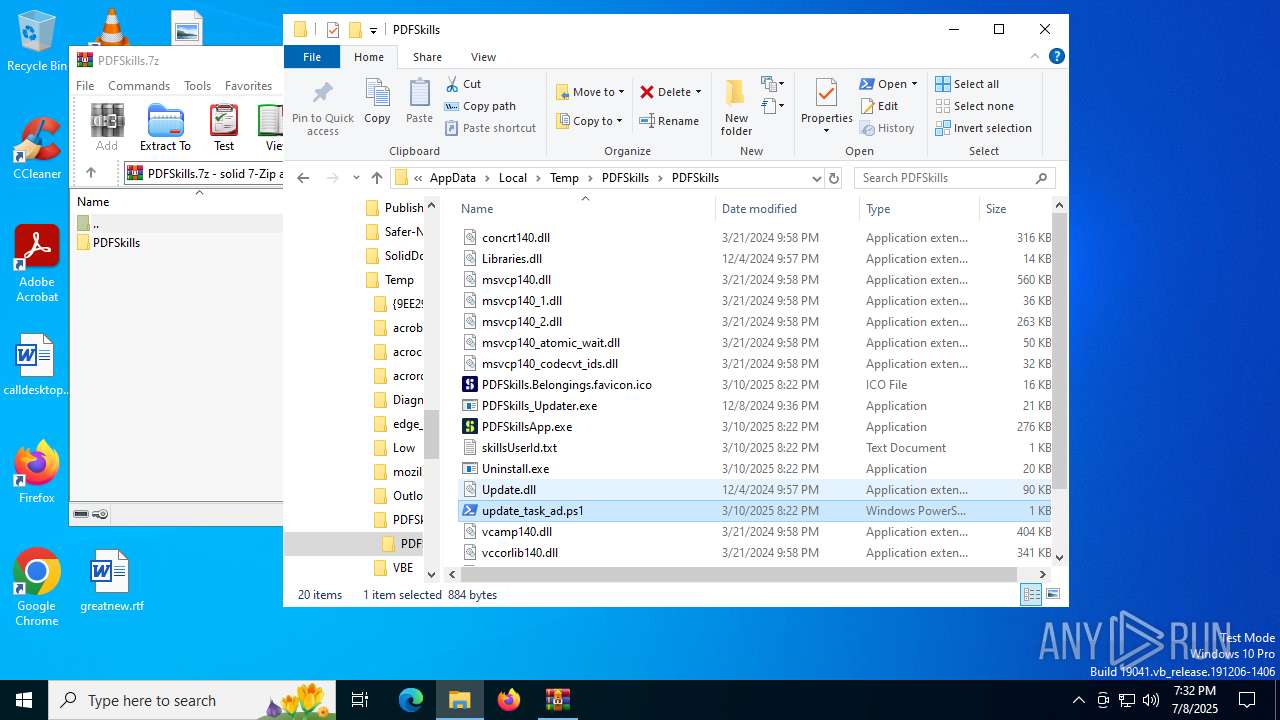
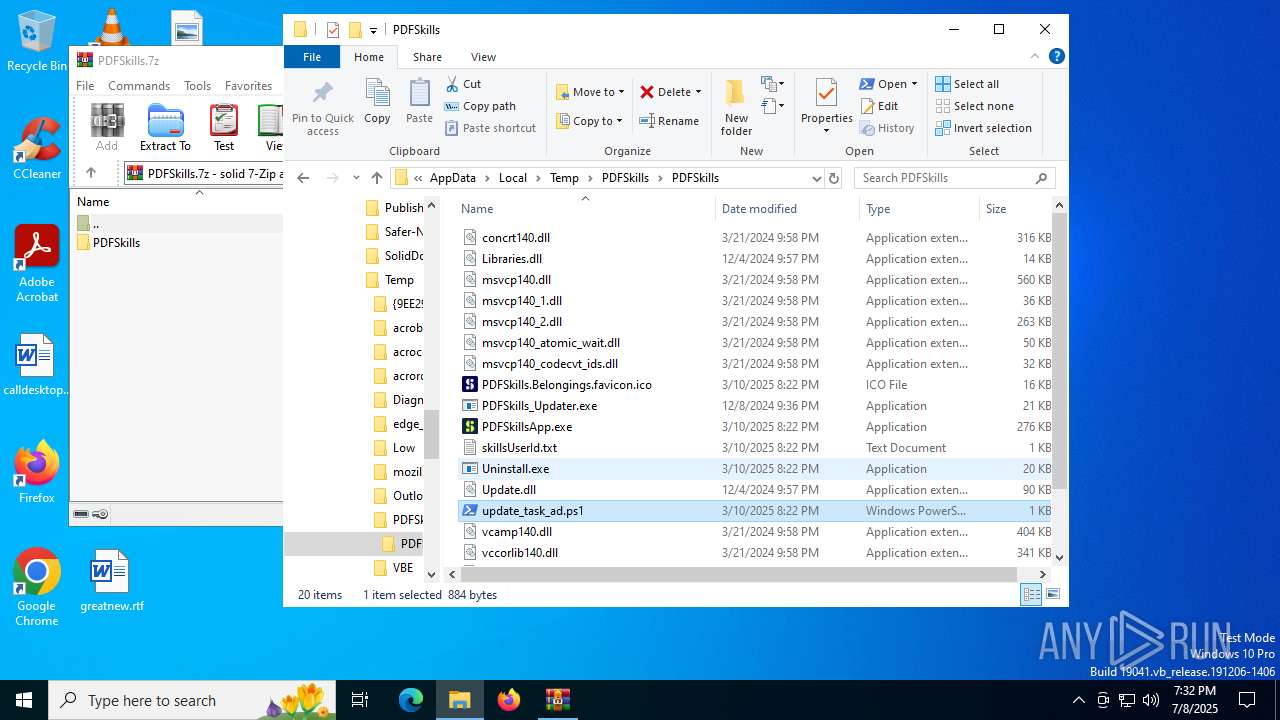
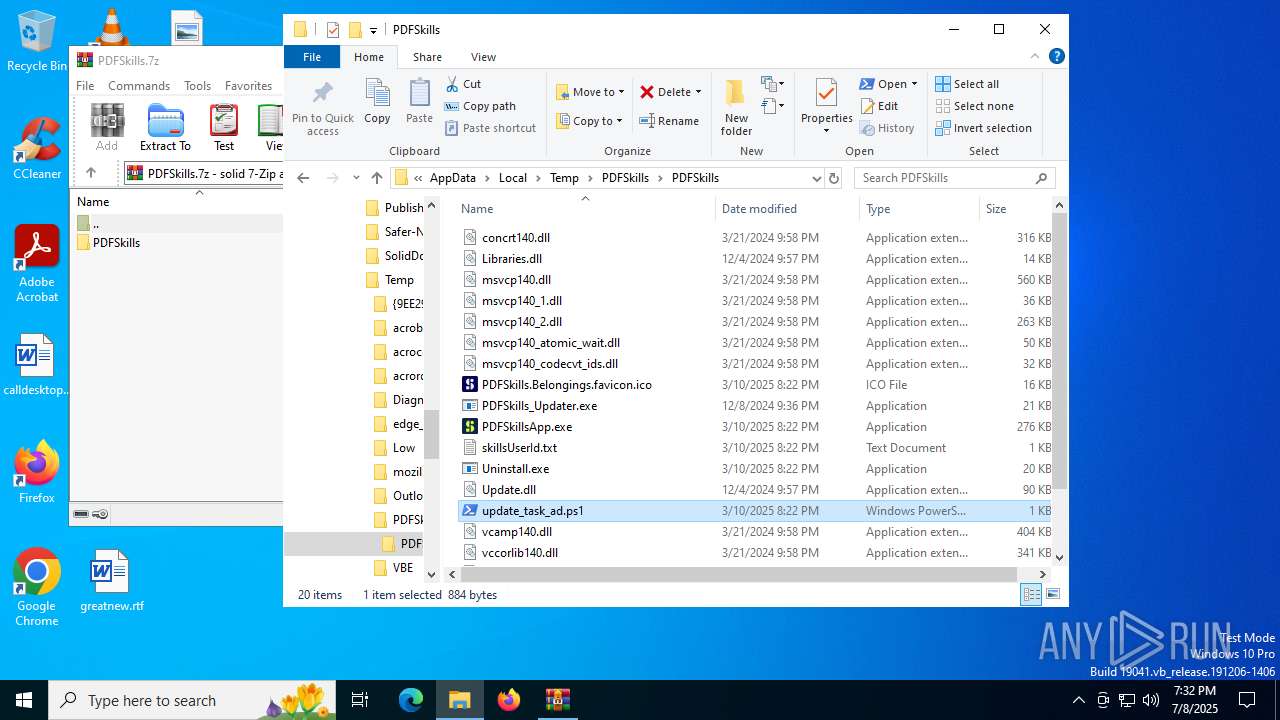
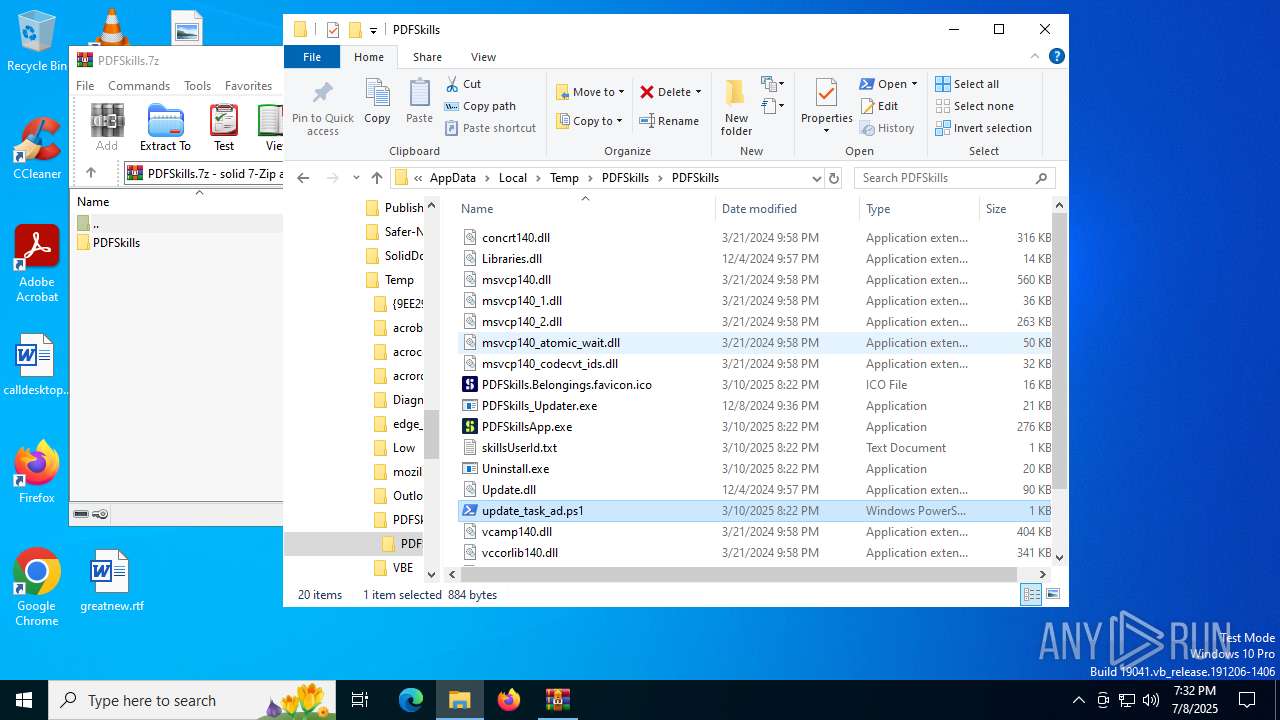
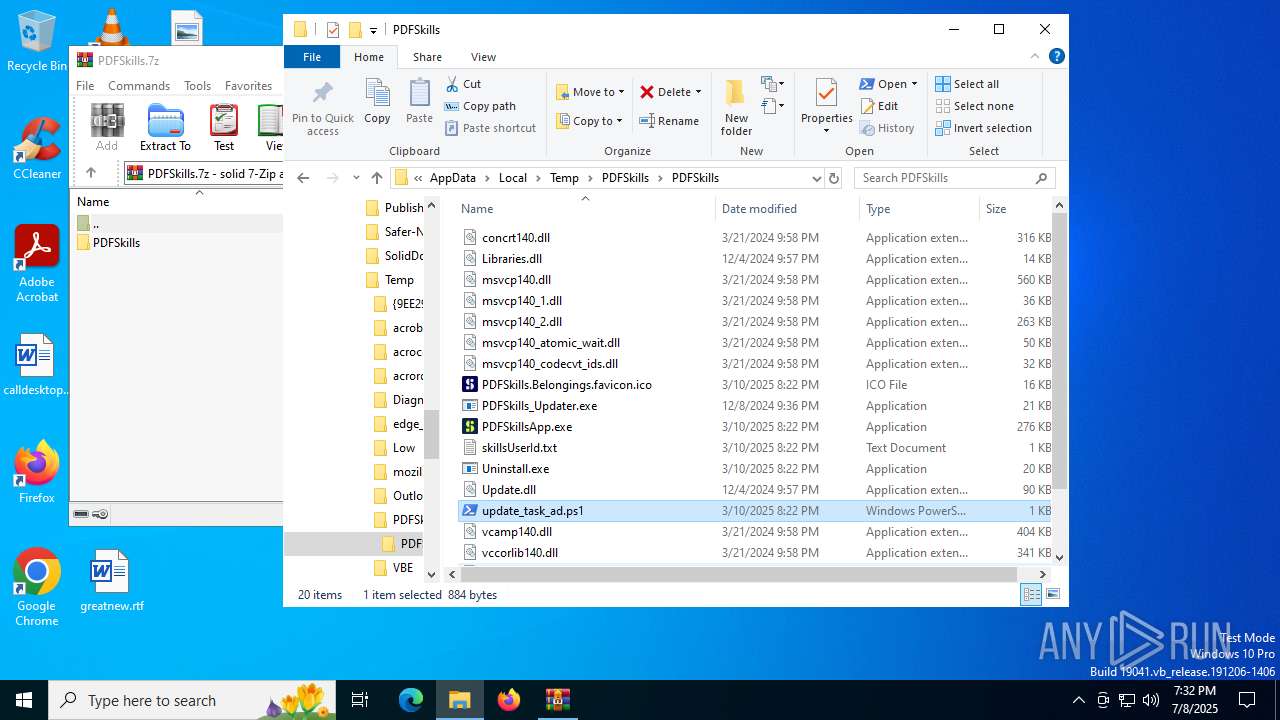
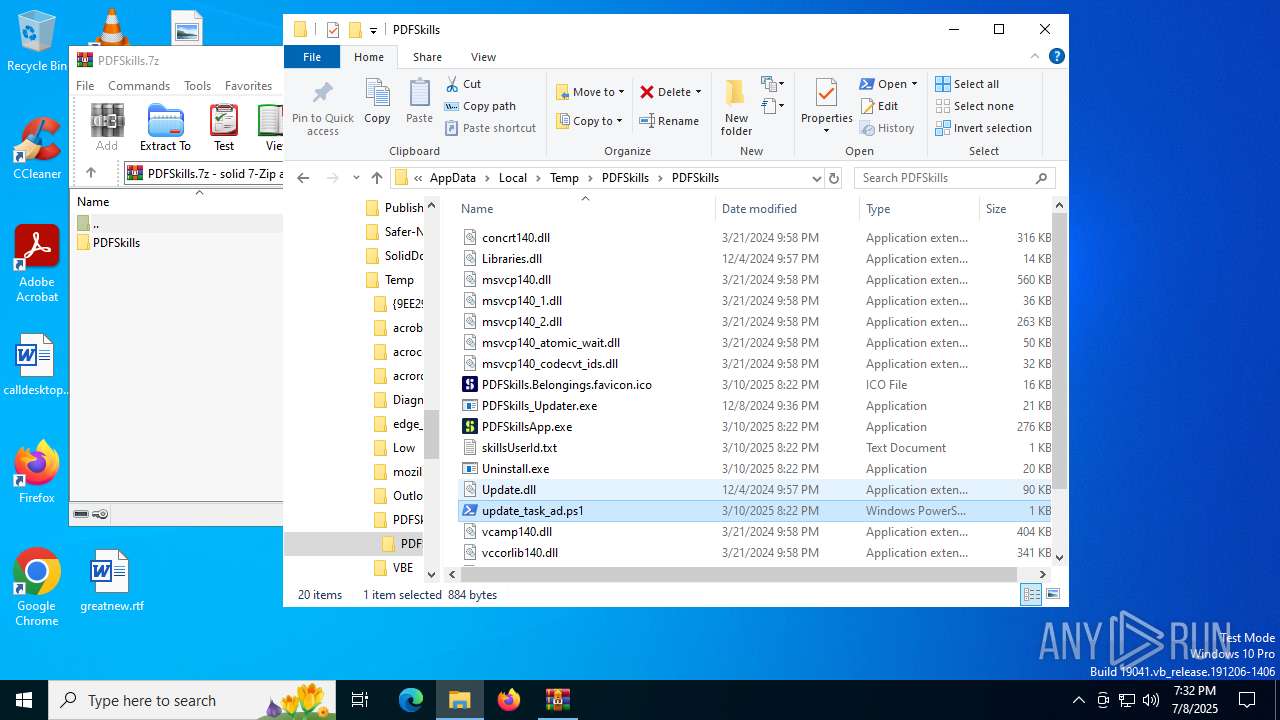
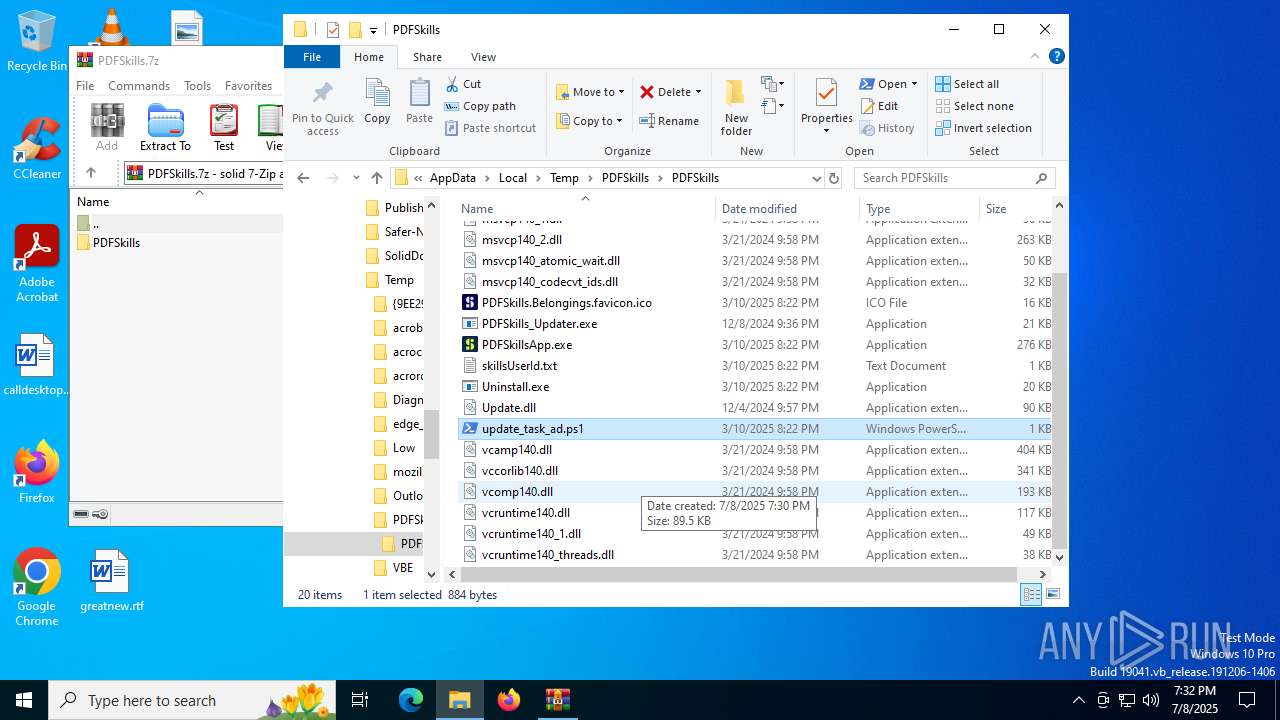
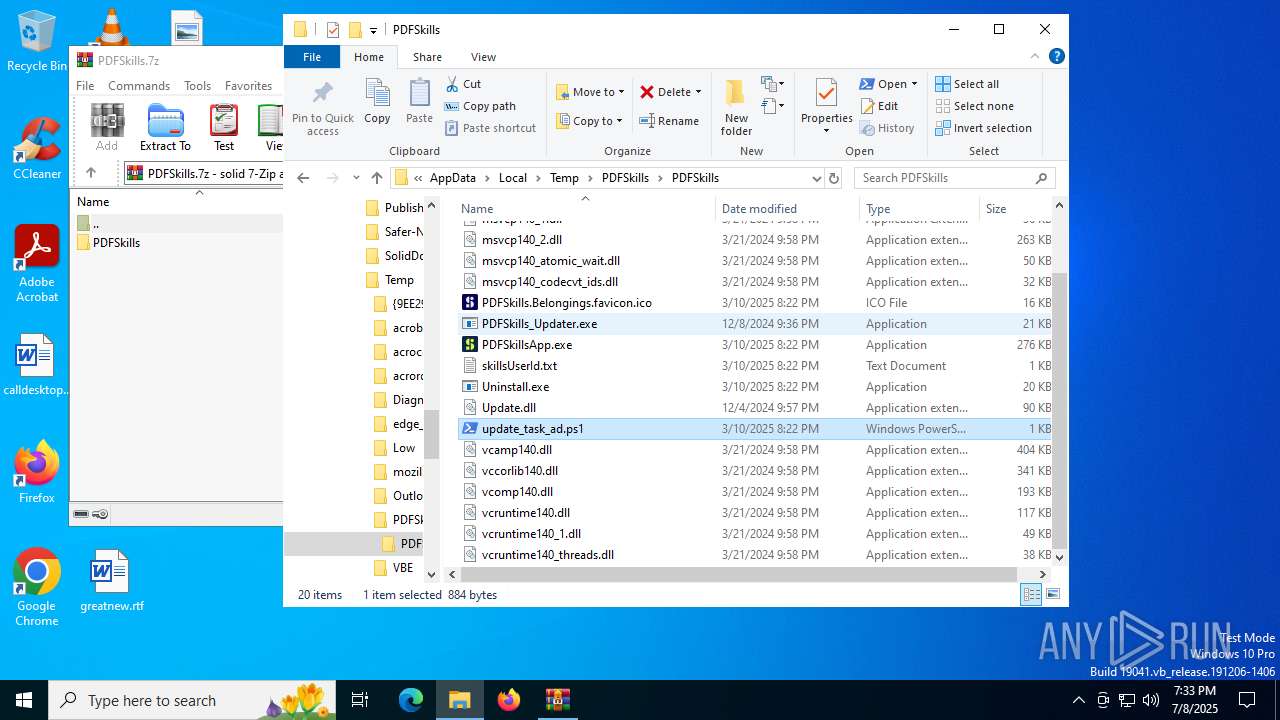
| 1356 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\update_task_ad.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkillsApp.exe" | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkillsApp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: NativeTemplate Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 2356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
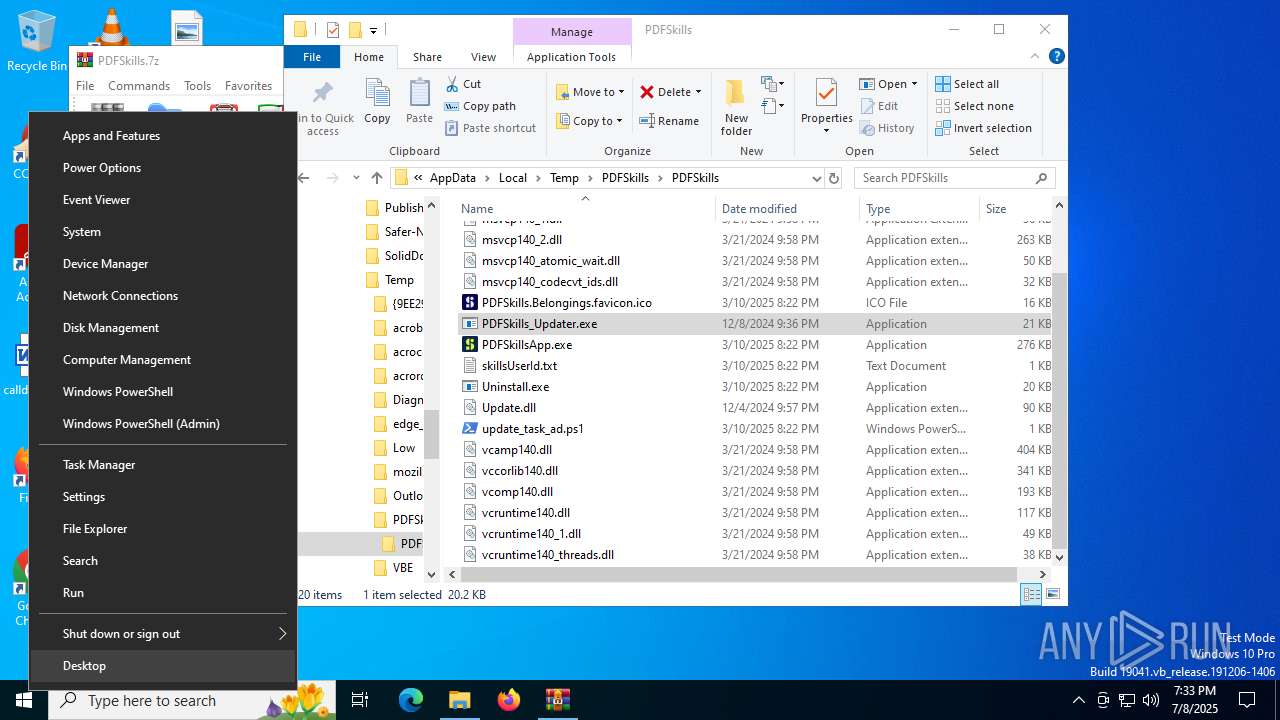
| 2804 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3480 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\update_task_ad.ps1" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
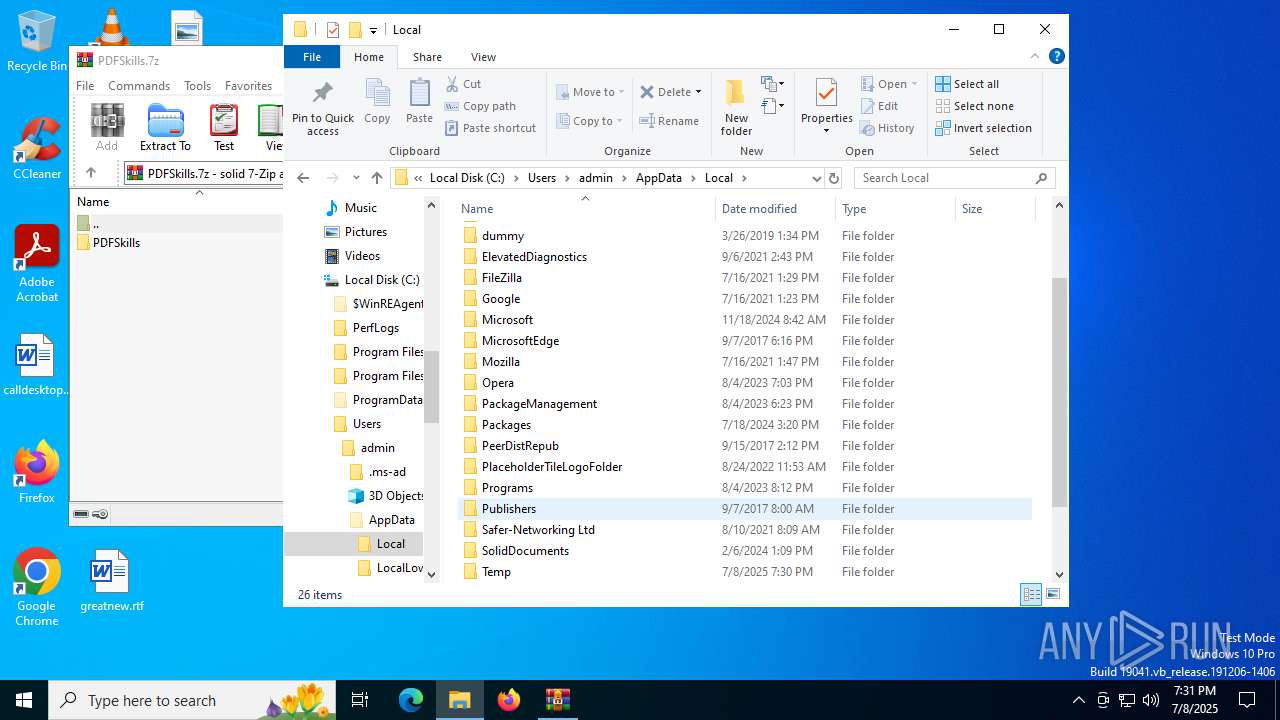
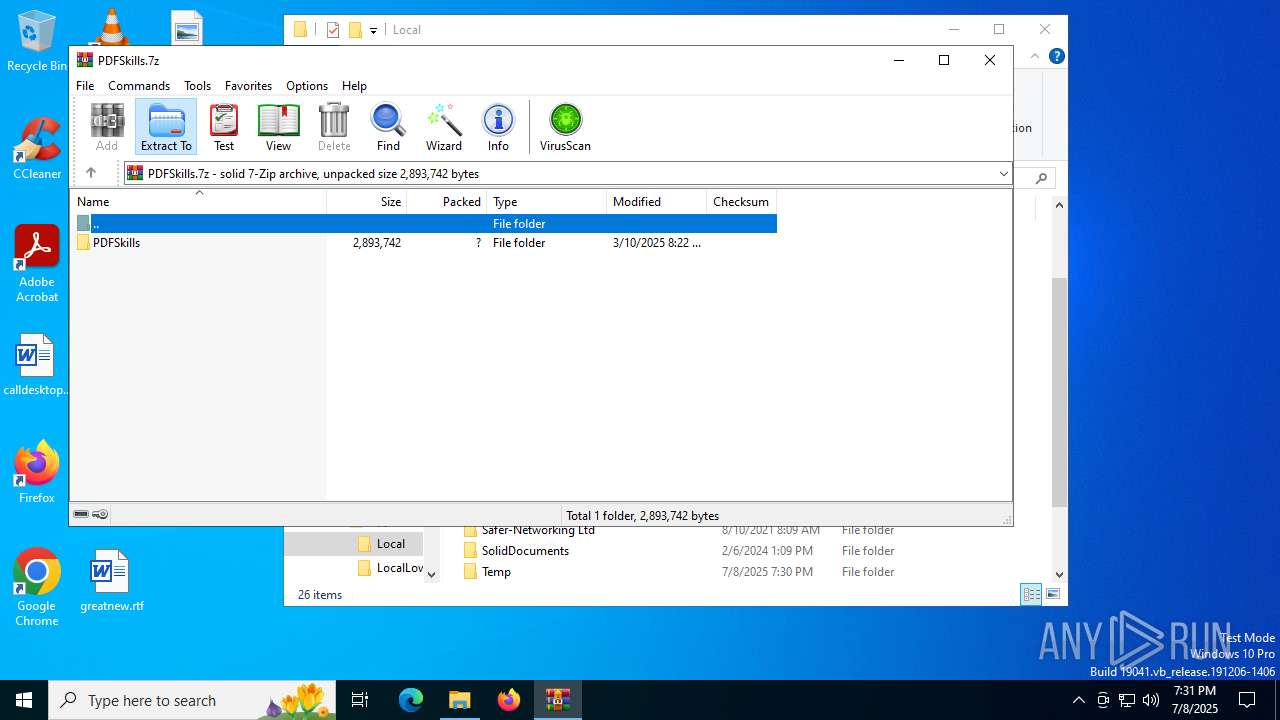
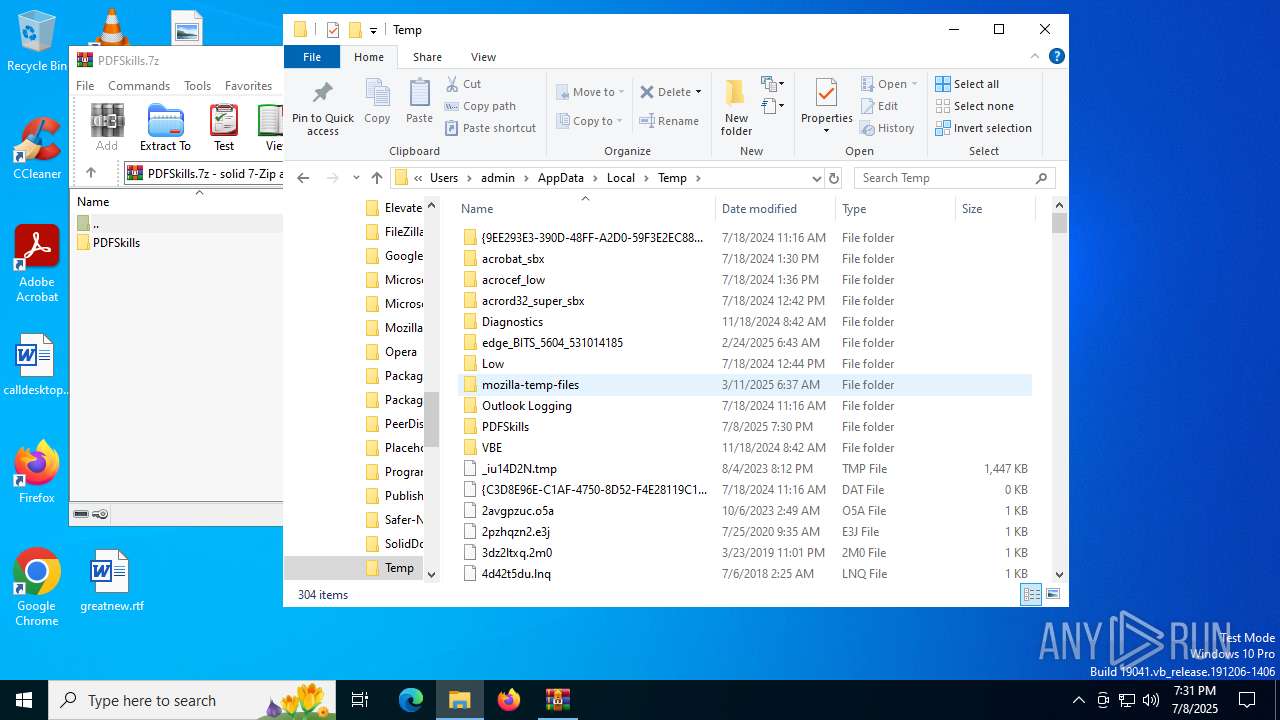
| 3820 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PDFSkills.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5724 | "C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkills_Updater.exe" | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkills_Updater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PDFSkills_Updater Exit code: 0 Version: 25.0.0.101 Modules
| |||||||||||||||
| 7040 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 402
Read events
11 360
Write events
29
Delete events
13
Modification events
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PDFSkills.7z | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (3820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
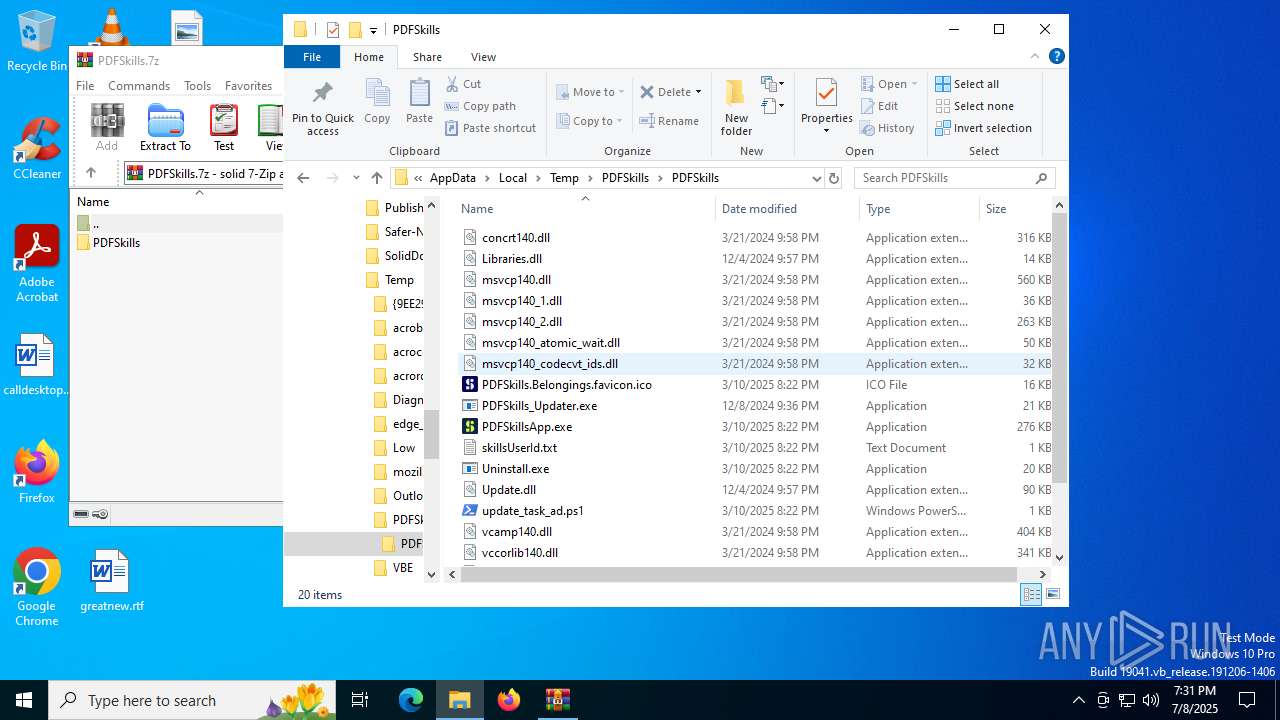
Executable files
17
Suspicious files
4
Text files
11
Unknown types
0
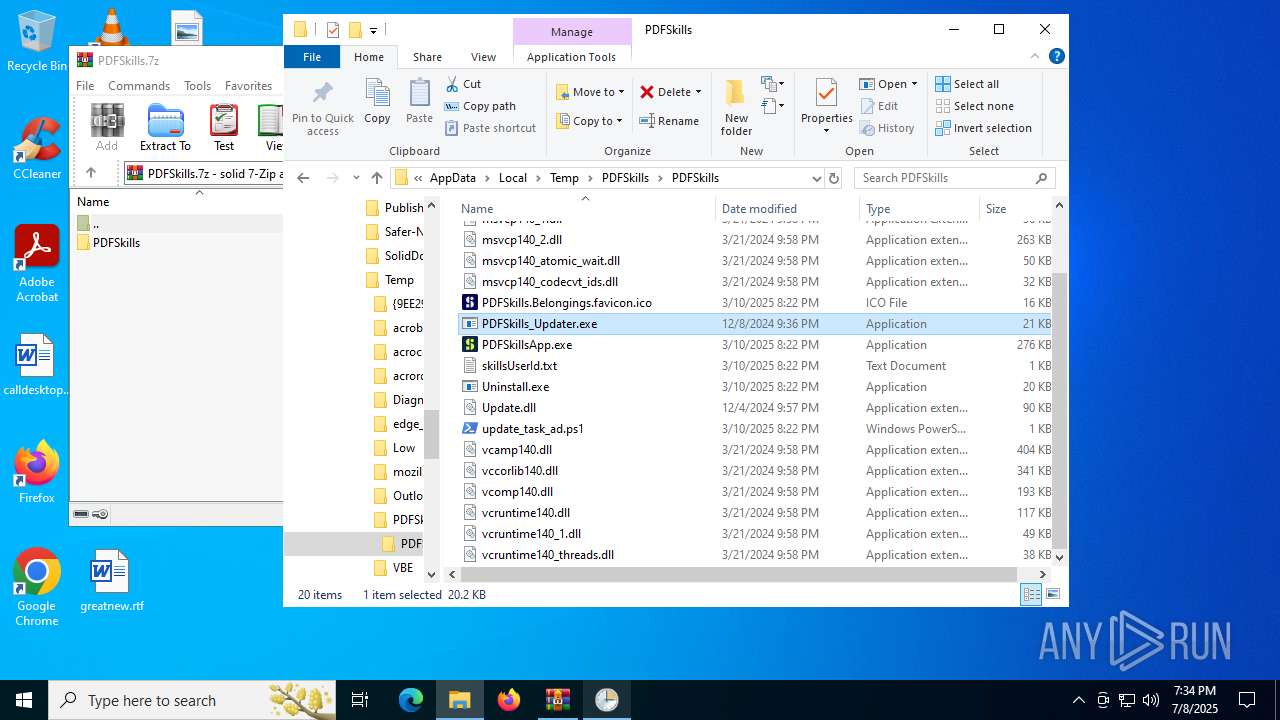
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
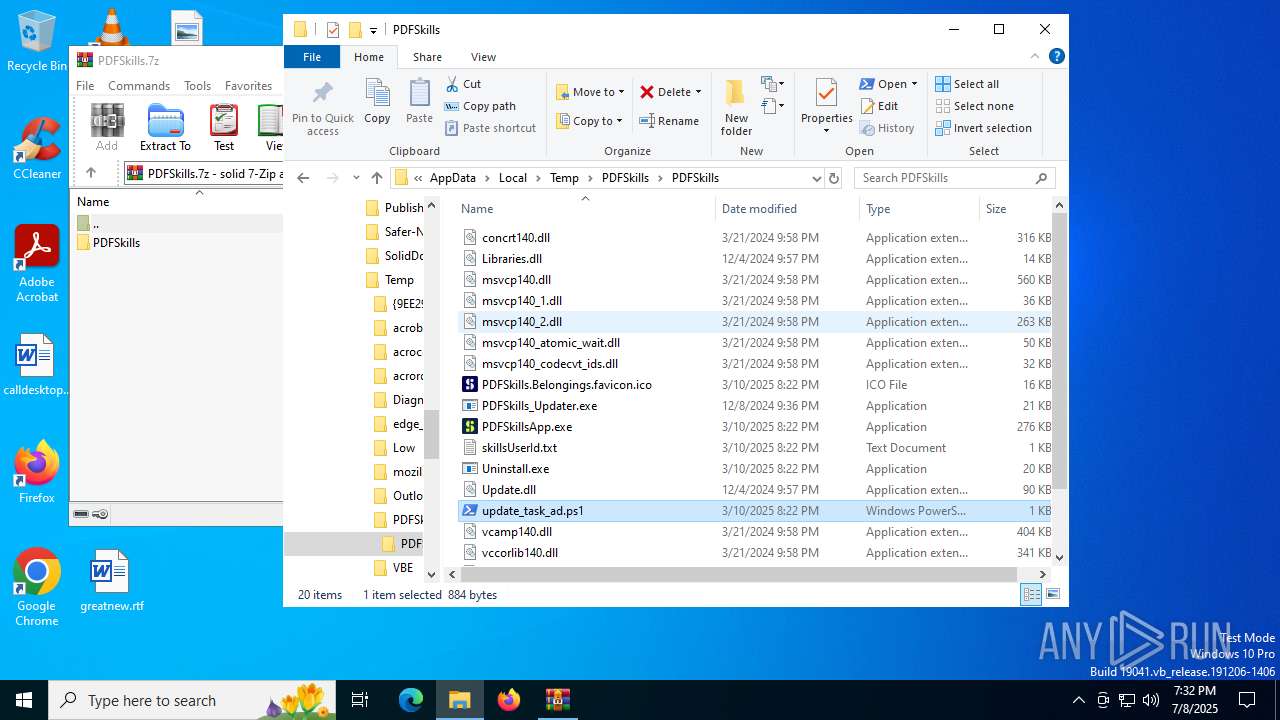
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\msvcp140_2.dll | executable | |
MD5:AA0148E20D34C10E01A4A9E1BAB1D058 | SHA256:583AD842BCF2F77AF57D07B8F00ECA77BB2DF763DF96BB9C50F7E52031B54E42 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\msvcp140_codecvt_ids.dll | executable | |
MD5:165308EE66D0B8F11CA20F3BCD410EA9 | SHA256:08DF3AB1B59D1F7D63F0811838E4FCCC107087FCBC469D94975C0E44477058E7 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\vcamp140.dll | executable | |
MD5:8441A618D2CEF67BDEDCA224FD61AFA2 | SHA256:6CD300E597C477260809C5CA036993D923CD8BE304AE323C9C4D7776115FE62D | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkills.Belongings.favicon.ico | image | |
MD5:FC5F48AAF4694FABB338180E78FCFDCB | SHA256:575233647D440DF001566E8092FD408E1F3C840BC3991A1866408AFDA3DC6F99 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\vcomp140.dll | executable | |
MD5:EF76327FF132A48F3BAC24598C99B373 | SHA256:D49B394DE1154176B39611C37C669EBFF50AA5A818DBD5FF3D2214A299368DDD | |||
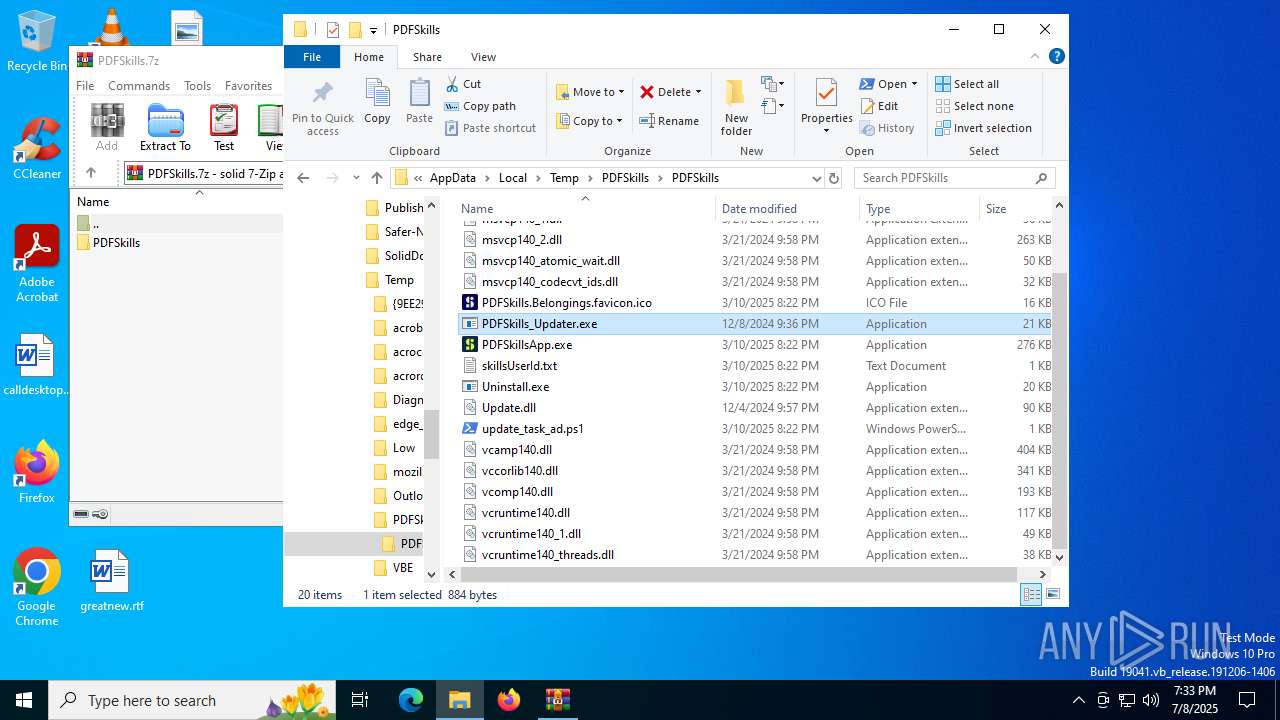
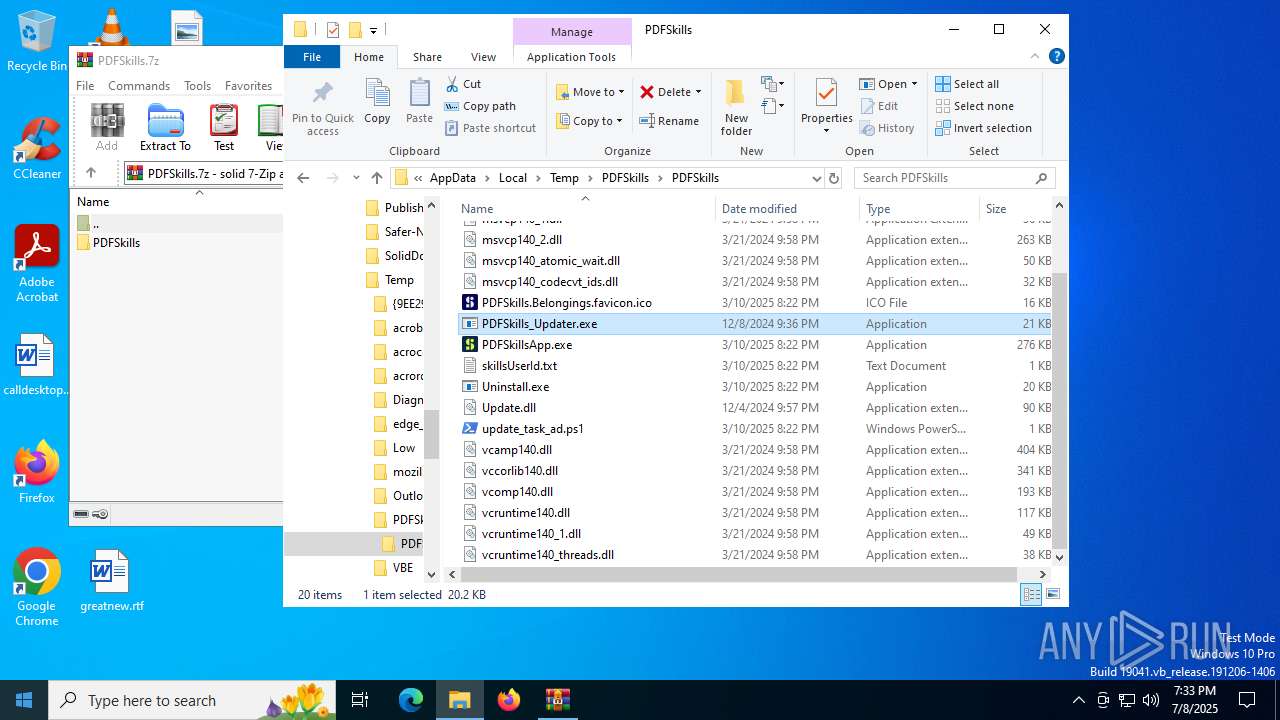
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\PDFSkills_Updater.exe | executable | |
MD5:BFC168A01A2B0F3CD11BF4BCCD5E84A1 | SHA256:186AA2C281CA7BB699CE0B48240B7559A9AC5B0BA260FB78B81EC53249548F62 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\msvcp140_atomic_wait.dll | executable | |
MD5:6722344B74084D0AF629283060716BAE | SHA256:C9FD25862B1B8B2977BF188A4E0C4460DADE43C31710283C2B42DBD3B15B4317 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\Update.dll | executable | |
MD5:887A8EE2C57EFDE7512F221E53B853BD | SHA256:C4C29485DC0FFD7DBB2D0226854F42434931307EE307CE72FE2FDEDB35794BB7 | |||
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\vcruntime140.dll | executable | |
MD5:E9B690FBE5C4B96871214379659DD928 | SHA256:A06C9EA4F815DAC75D2C99684D433FBFC782010FAE887837A03F085A29A217E8 | |||
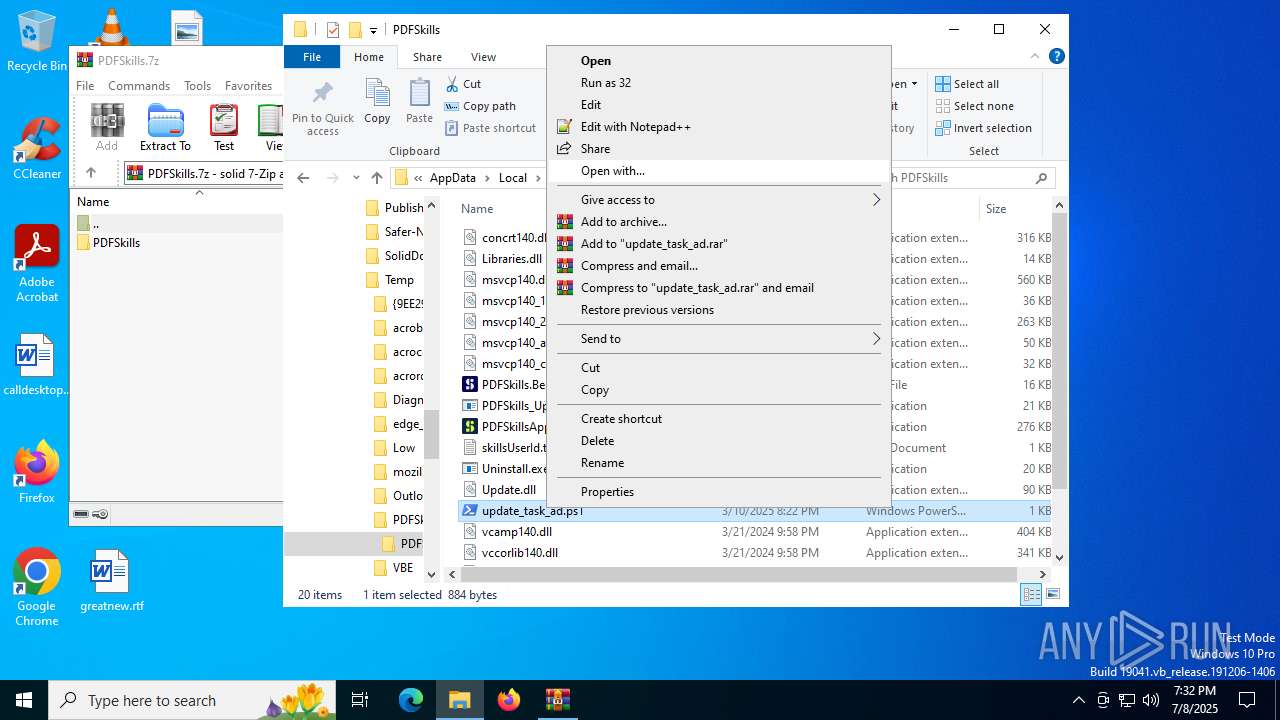
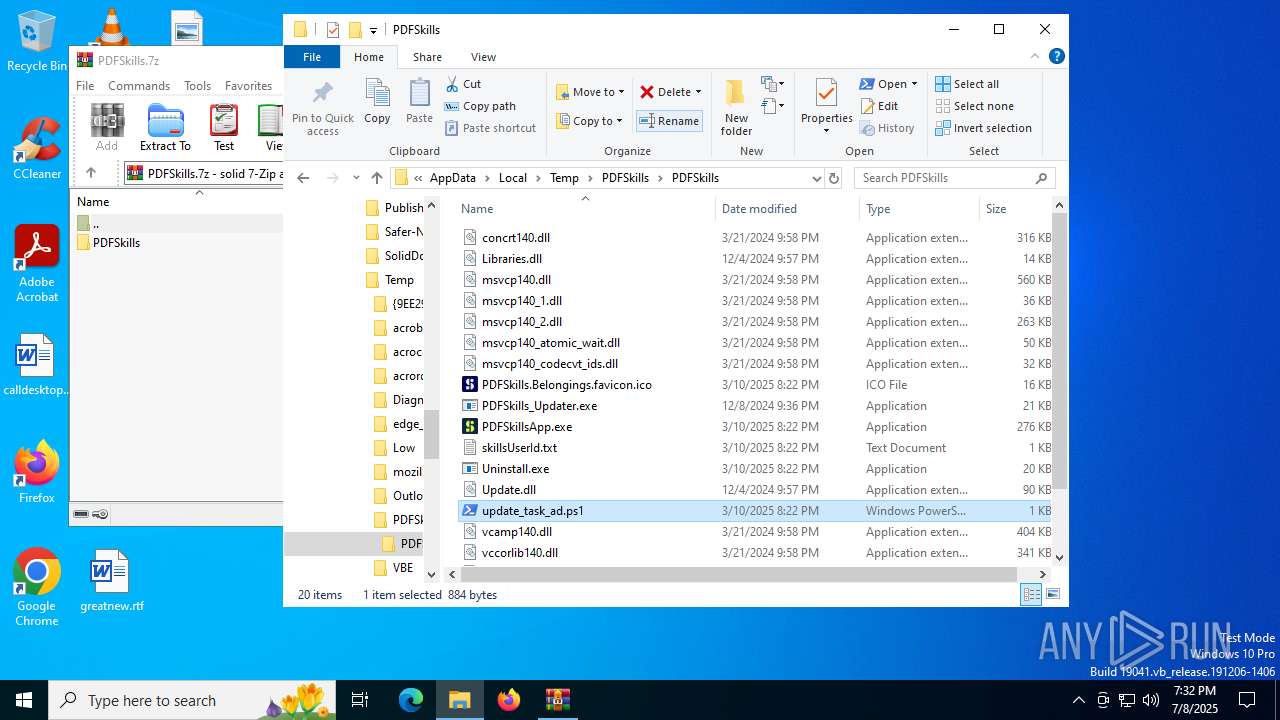
| 3820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\PDFSkills\PDFSkills\update_task_ad.ps1 | text | |
MD5:303E2E6AD62BDBC4AB32F6041FEA897A | SHA256:5FDF76A78556E479E41422D577F6FC7B672CBC9C131721B725FEA765E288EED9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
41
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1336 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.16.252.233:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4868 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4080 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|