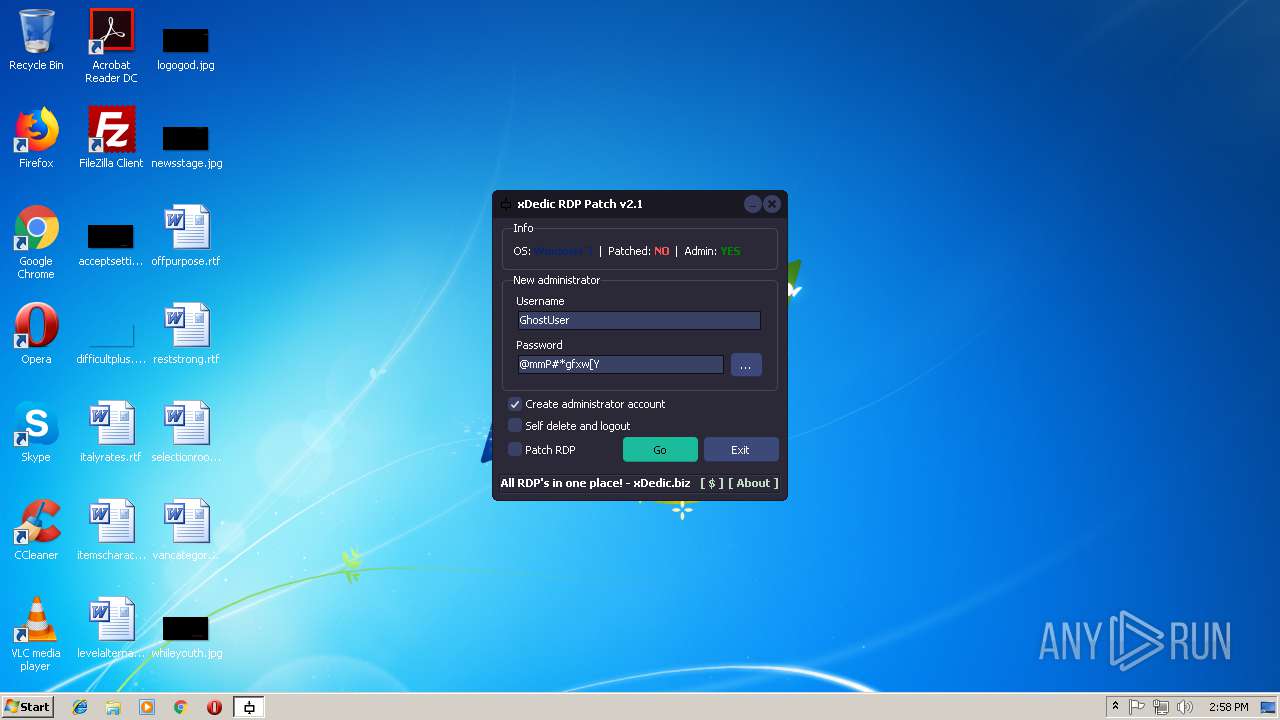
| File name: | xRdp.v2.1.exe |
| Full analysis: | https://app.any.run/tasks/25400e19-5944-4686-8c01-25e5bfb47fd7 |
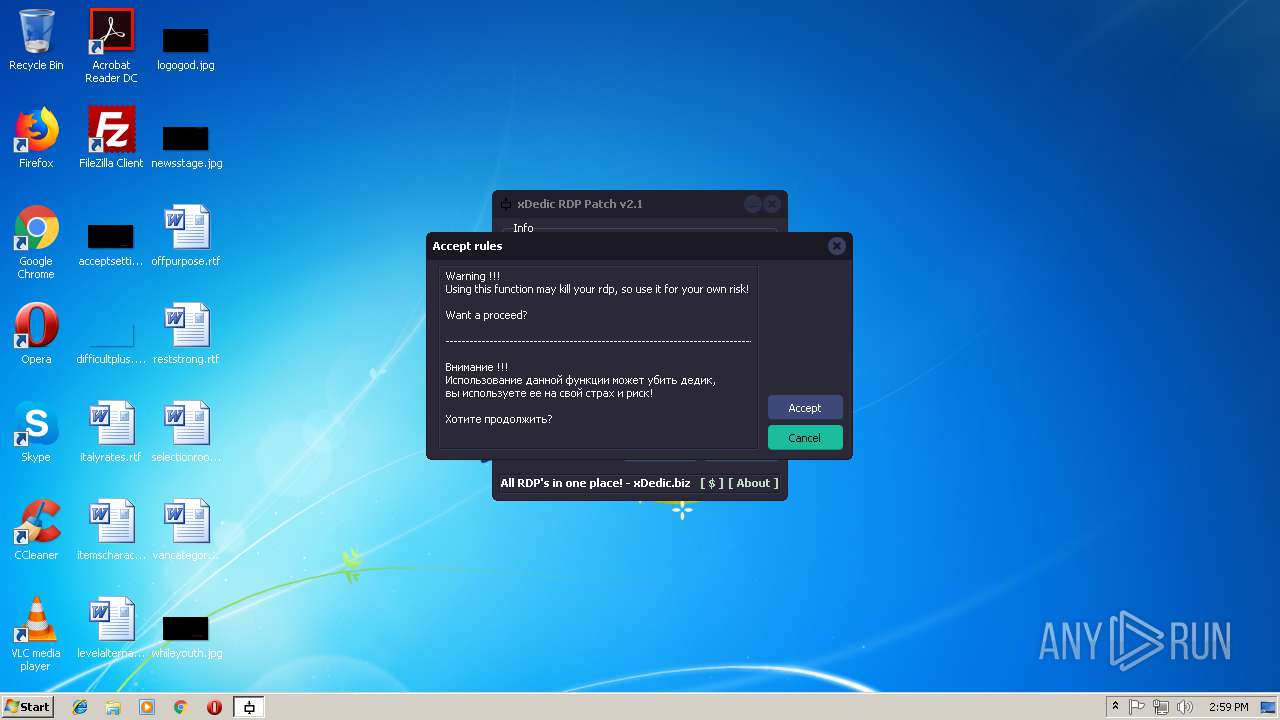
| Verdict: | Suspicious activity |
| Analysis date: | October 20, 2018, 13:58:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F17A6FEB053A24A0B69860C8E1C13F46 |
| SHA1: | 2BE3287FDB63AA42B1CF689CFBD90D3594D48757 |
| SHA256: | DADDC833BFFCADE36B432B21046487B29DCD2A162D91B503334A52CAEE9C1FD2 |
| SSDEEP: | 24576:K17loPTk5SlerAqhJlRWt5vcWkJJa/YvQRttJgWwfQZpNxIiJMox1Wp4+eZ:KRluw5tAq1RmvcWkbaGQRtt/TpNxPx1A |
MALICIOUS
Application was dropped or rewritten from another process
- tch.exe (PID: 2056)
Loads dropped or rewritten executable
- svchost.exe (PID: 3724)
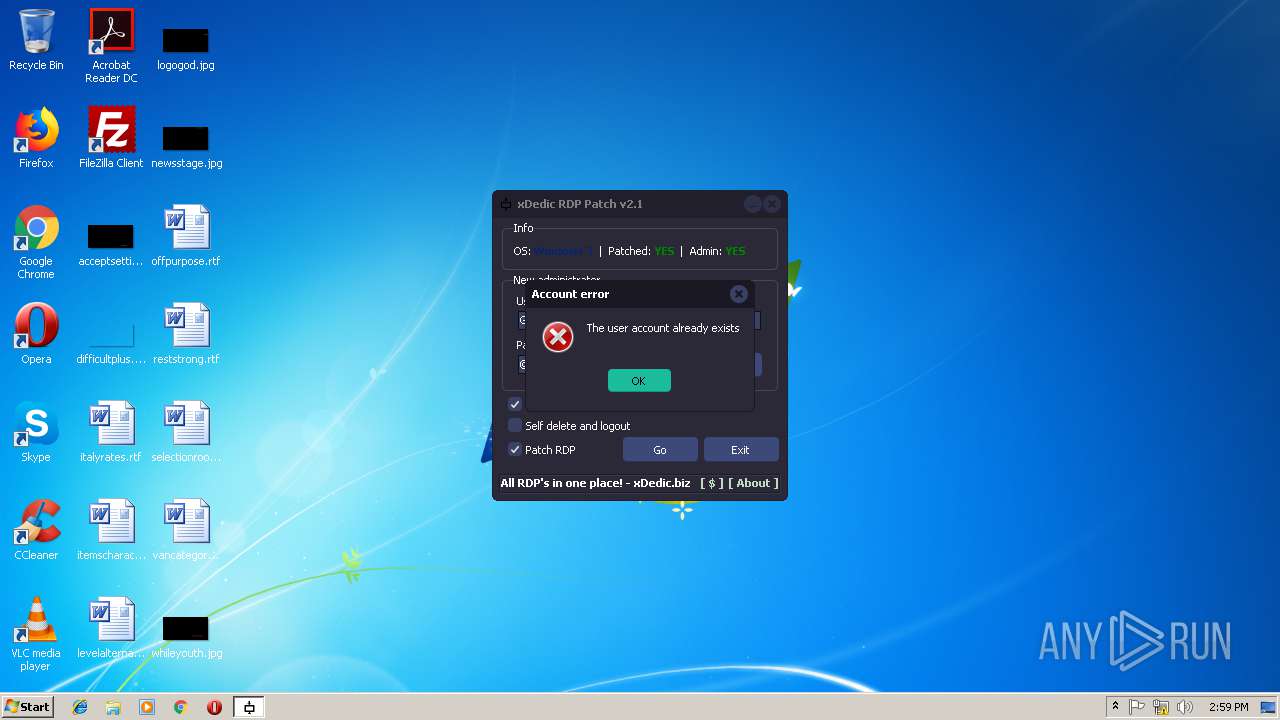
SUSPICIOUS
Starts CMD.EXE for commands execution
- xRdp.v2.1.exe (PID: 1672)
Creates files in the Windows directory
- tch.exe (PID: 2056)
Creates or modifies windows services
- tch.exe (PID: 2056)
- svchost.exe (PID: 3724)
Uses NETSH.EXE for network configuration
- tch.exe (PID: 2056)
Executable content was dropped or overwritten
- xRdp.v2.1.exe (PID: 1672)
- tch.exe (PID: 2056)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:25 23:22:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2535936 |
| InitializedDataSize: | 1176064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x42b001 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.1.11 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | xDedic INC. |
| FileVersion: | 2.1.1.11 |
| InternalName: | xDedicRDPPatch |
| ProductName: | xDedicRDPPatch |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Mar-2016 22:22:33 |
| Detected languages: |
|
| CompanyName: | xDedic INC. |
| FileVersion: | 2.1.1.11 |
| InternalName: | xDedicRDPPatch |
| ProductName: | xDedicRDPPatch |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 13 |
| Time date stamp: | 25-Mar-2016 22:22:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0026A000 | 0x0009E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99965 |
.itext | 0x0026B000 | 0x00002000 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.73423 |
.data | 0x0026D000 | 0x0000A000 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97045 |
.bss | 0x00277000 | 0x0009A724 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00312000 | 0x00004000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.87067 |
.didata | 0x00316000 | 0x00001000 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.22624 |
.edata | 0x00317000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.18844 |
.tls | 0x00318000 | 0x00000050 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00319000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.37365 |
.reloc | 0x0031A000 | 0x00037000 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8618 | 723 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.70679 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 0.65819 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 0.585754 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 0.794341 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 7.32783 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 7.34454 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 7.2749 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4062 | 7.72299 | 636 | UNKNOWN | UNKNOWN | RT_STRING |
4063 | 7.76352 | 964 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x0005E608 |
Total processes
43
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | "C:\Users\admin\AppData\Local\Temp\xRdp.v2.1.exe" | C:\Users\admin\AppData\Local\Temp\xRdp.v2.1.exe | explorer.exe | ||||||||||||
User: admin Company: xDedic INC. Integrity Level: HIGH Exit code: 0 Version: 2.1.1.11 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\tch.exe" -i -s | C:\Users\admin\AppData\Local\Temp\tch.exe | xRdp.v2.1.exe | ||||||||||||
User: admin Company: Stas'M Corp. Integrity Level: HIGH Description: RDP Wrapper Library Installer Exit code: 0 Version: 2.3.0.0 Modules
| |||||||||||||||
| 3092 | hostname | C:\Windows\system32\HOSTNAME.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Hostname APP Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | cmd.exe /c hostname | C:\Windows\system32\cmd.exe | — | xRdp.v2.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3484 | netsh advfirewall firewall add rule name="Remote Desktop" dir=in protocol=tcp localport=3389 profile=any action=allow | C:\Windows\system32\netsh.exe | — | tch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3628 | "C:\Users\admin\AppData\Local\Temp\xRdp.v2.1.exe" | C:\Users\admin\AppData\Local\Temp\xRdp.v2.1.exe | — | explorer.exe | |||||||||||
User: admin Company: xDedic INC. Integrity Level: MEDIUM Exit code: 3221226540 Version: 2.1.1.11 Modules
| |||||||||||||||
| 3724 | C:\Windows\System32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
604
Read events
528
Write events
76
Delete events
0
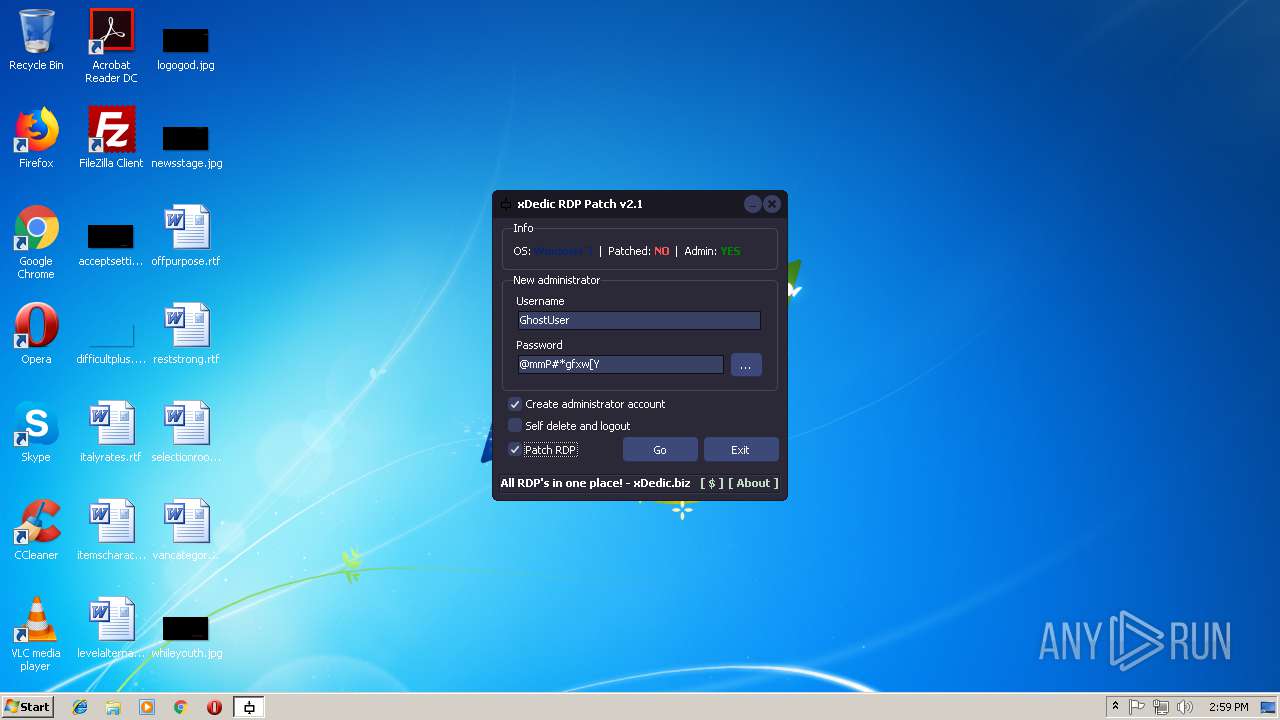
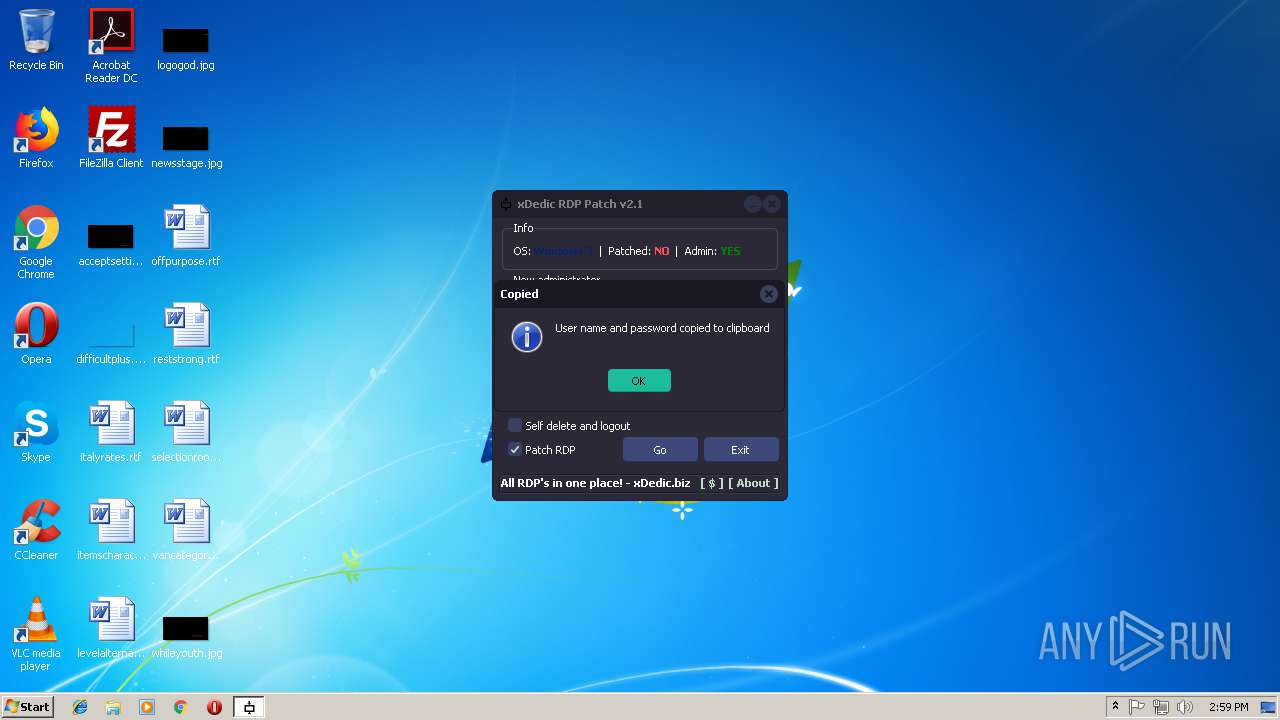
Modification events
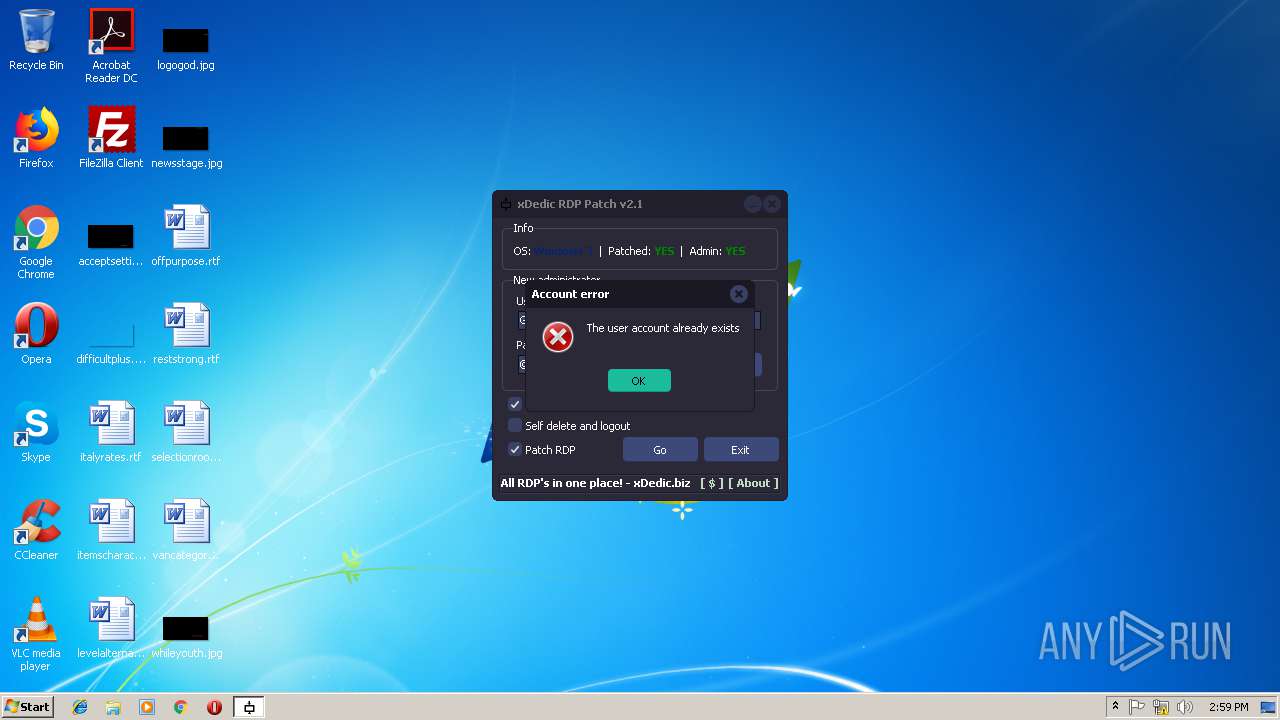
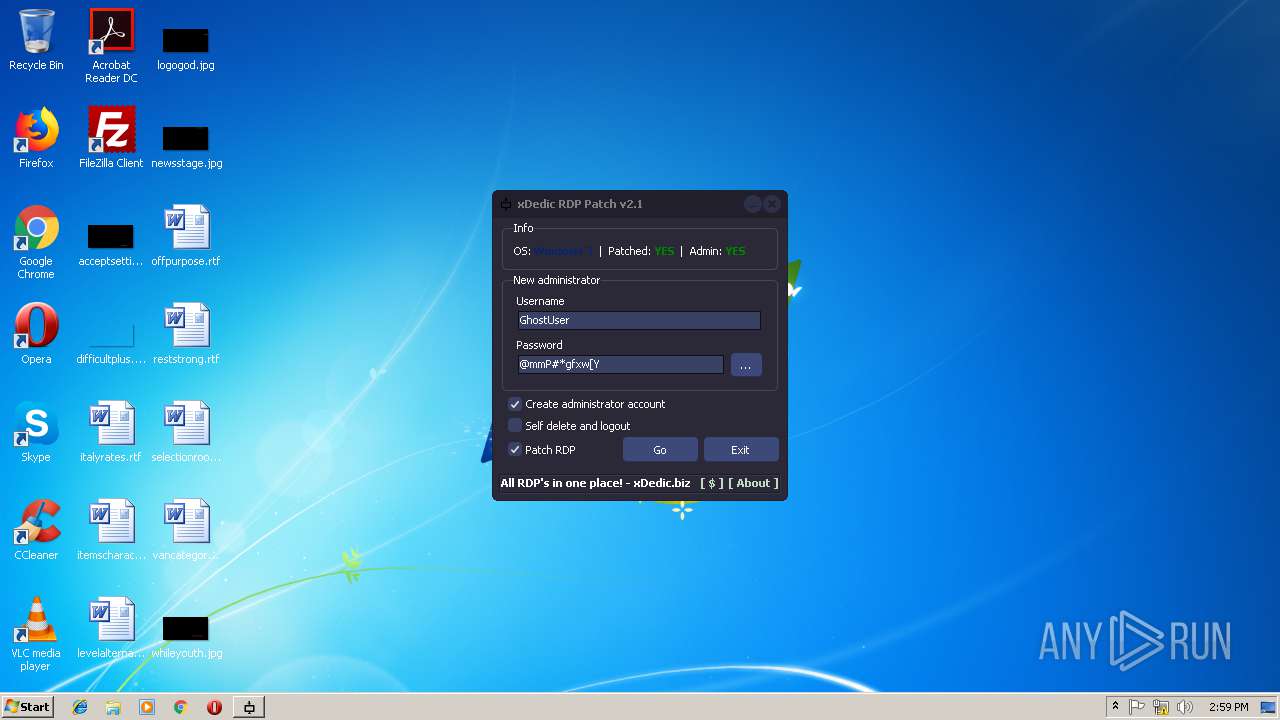
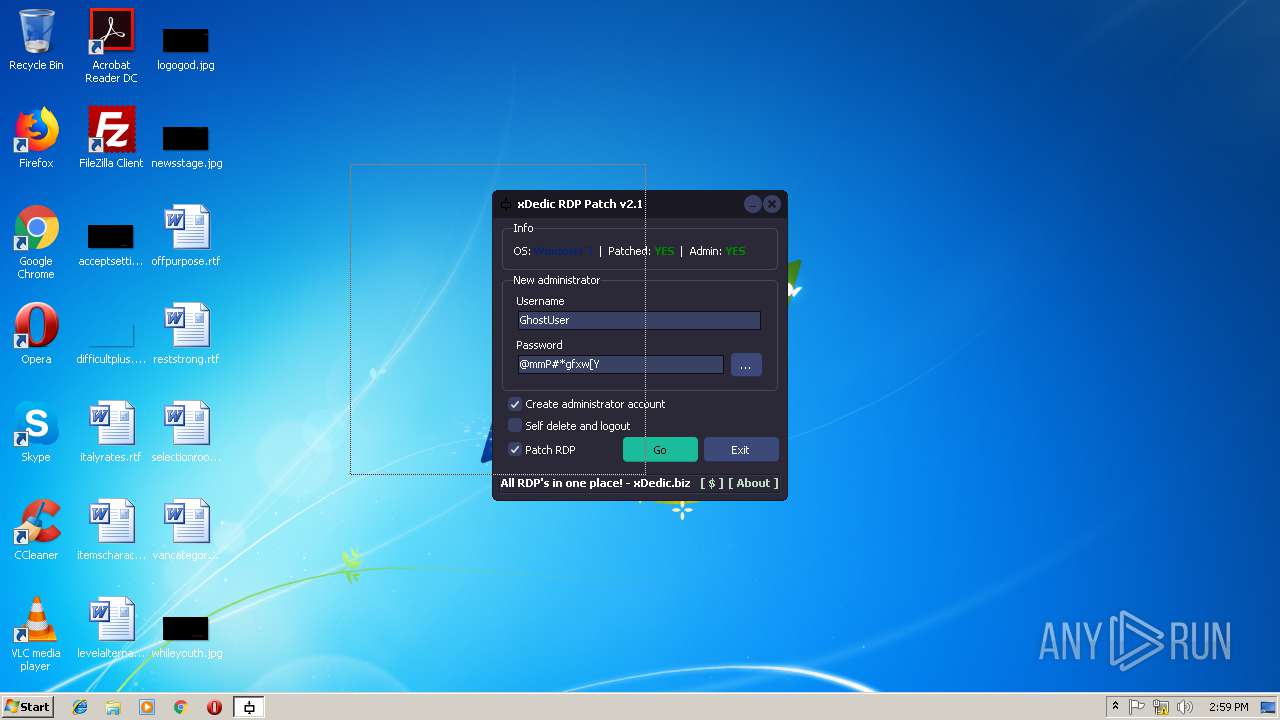
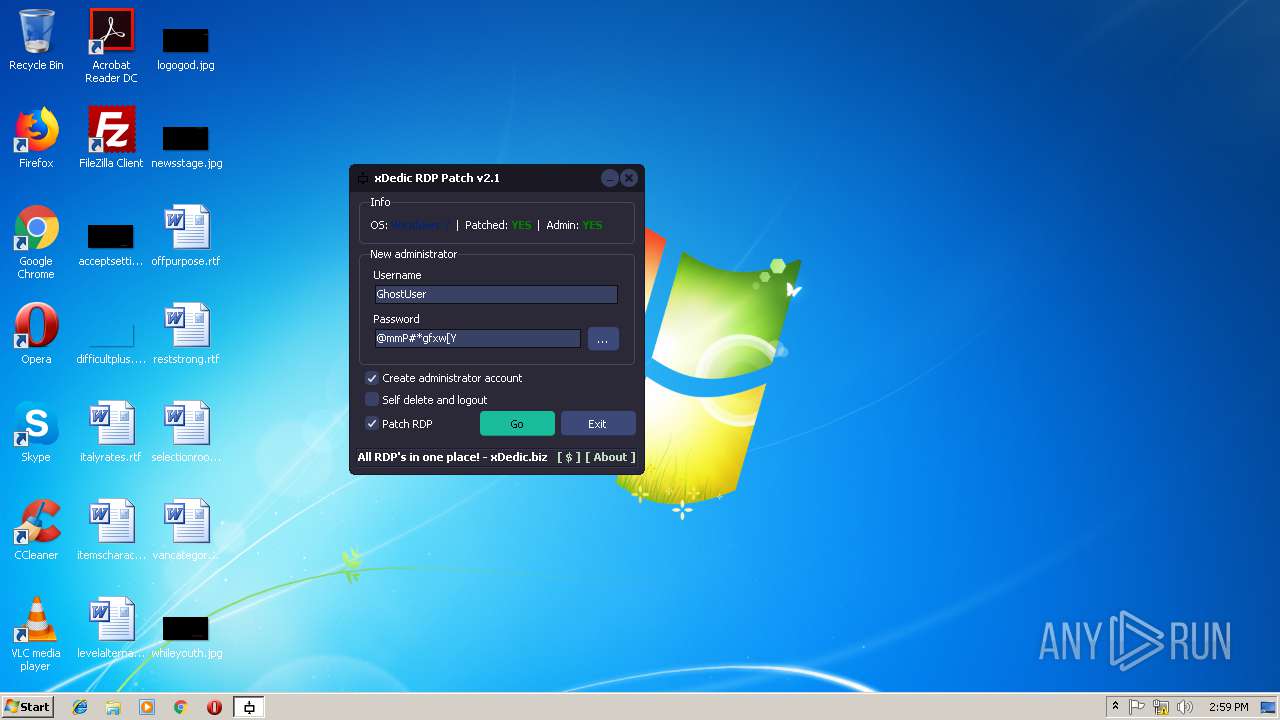
| (PID) Process: | (1672) xRdp.v2.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList |
| Operation: | write | Name: | GhostUser |
Value: 0 | |||
| (PID) Process: | (1672) xRdp.v2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1672) xRdp.v2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1672) xRdp.v2.1.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | UserAuthentication |
Value: 1 | |||
| (PID) Process: | (2056) tch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TermService\Parameters |
| Operation: | write | Name: | ServiceDll |
Value: %SystemRoot%\system32\rdpwrap.dll | |||
| (PID) Process: | (3724) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Dnscache\Parameters\DnsCache |
| Operation: | write | Name: | ShutdownOnIdle |
Value: 0 | |||
| (PID) Process: | (3724) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: 525400363EFF | |||
| (PID) Process: | (3484) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3484) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3484) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
Executable files
2
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | svchost.exe | C:\Windows\system32\CatRoot2\edb.log | — | |
MD5:— | SHA256:— | |||
| 3724 | svchost.exe | C:\Windows\system32\CatRoot2\{127D0A1D-4EF2-11D1-8608-00C04FC295EE}\catdb | — | |
MD5:— | SHA256:— | |||
| 3724 | svchost.exe | C:\Windows\system32\CatRoot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\catdb | — | |
MD5:— | SHA256:— | |||
| 2056 | tch.exe | C:\Windows\system32\rdpwrap.ini | text | |
MD5:398BE25B8F112FFCB06C8FED2CD23CFC | SHA256:DB1D30EC1FCEC8186B0EC01B8A2984244B3393DD7883BE442D983AA4CBF29814 | |||
| 1672 | xRdp.v2.1.exe | C:\Users\admin\AppData\Local\Temp\tch.exe | executable | |
MD5:78D4E9BA8F641970162260273722C887 | SHA256:BA91AB389E3219C307980B903D7ED5ABA8BBF9F4EC7F389DB83D73B7DBAB9209 | |||
| 3724 | svchost.exe | C:\Windows\system32\CatRoot2\edb.chk | binary | |
MD5:C0CC6520604CB4949E5916BBF7A50562 | SHA256:D71E664FC9D753FCDFBA6C8992FE7BC6A0188DC7C417F581733EB42A1A084346 | |||
| 2056 | tch.exe | C:\Windows\system32\rdpwrap.dll | executable | |
MD5:9C6A68742EA7ABF802940E7F1502E20F | SHA256:861AD4BBF682B35AFFDA23FAB92C8DB945F3FA34F78177843C87802D1FD02020 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report