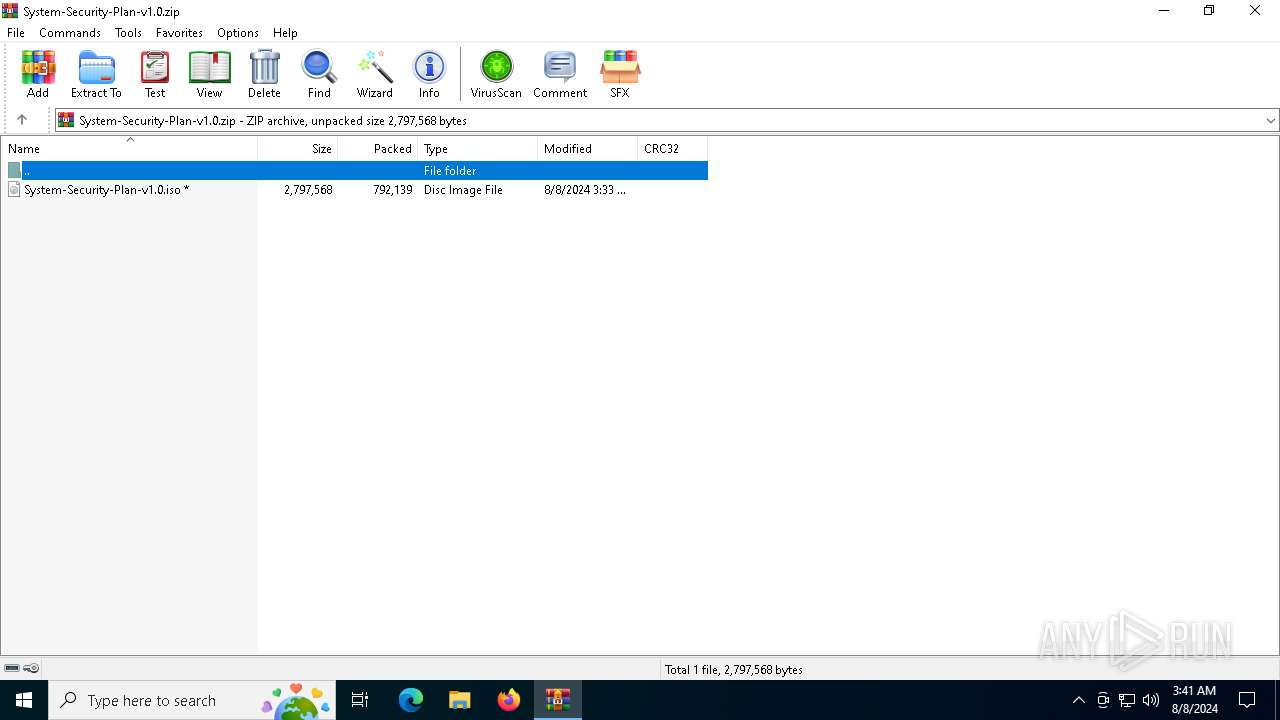
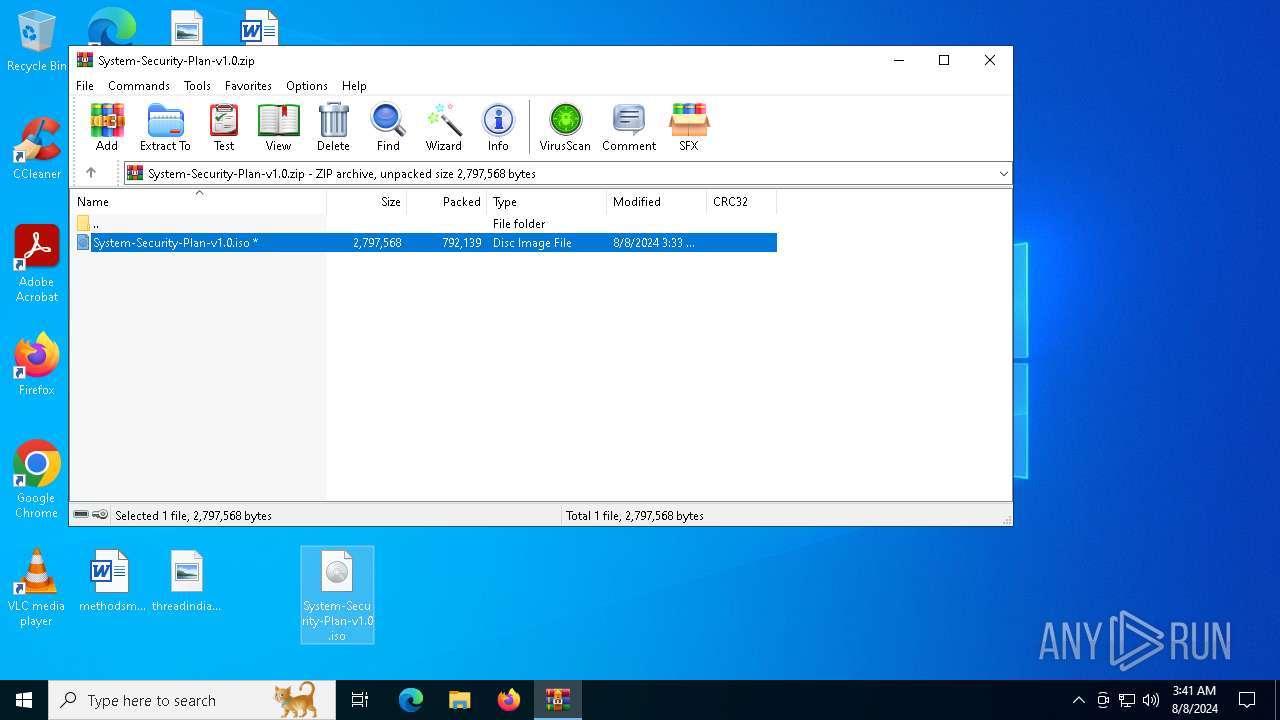
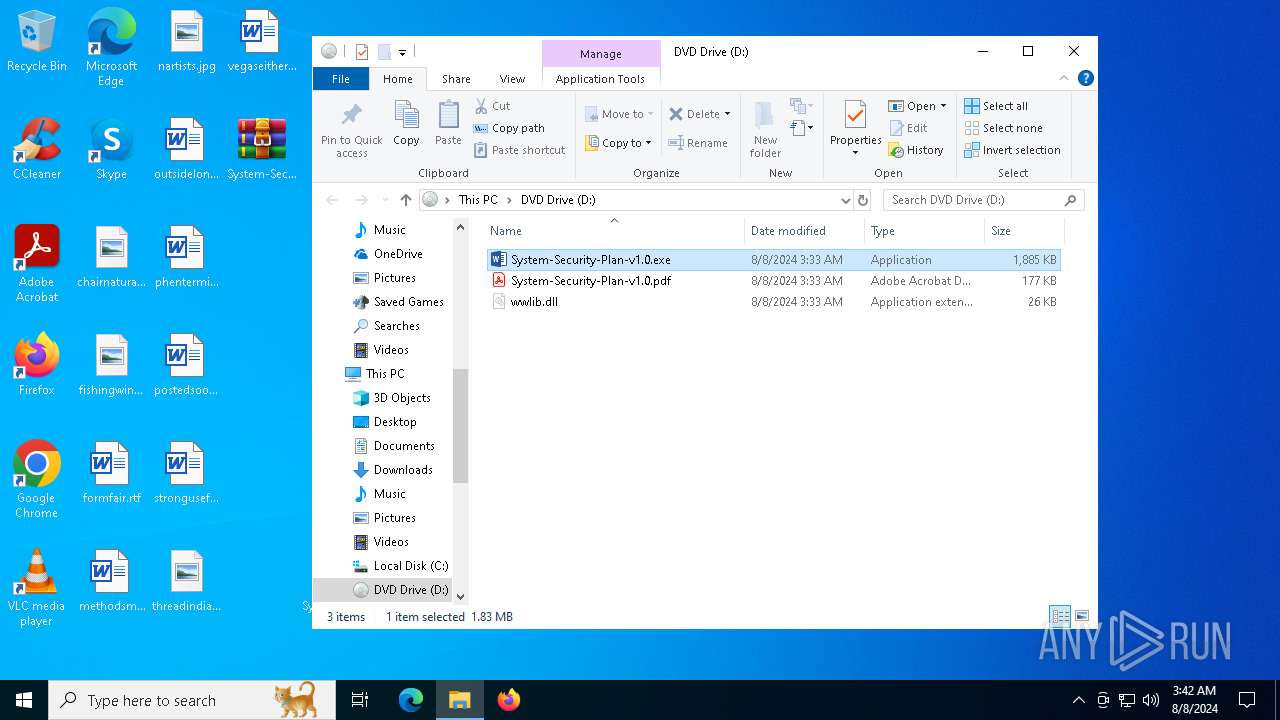
| File name: | System-Security-Plan-v1.0.zip |
| Full analysis: | https://app.any.run/tasks/448aab94-4698-411a-95e8-9ba5c2c2cc6a |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2024, 03:41:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
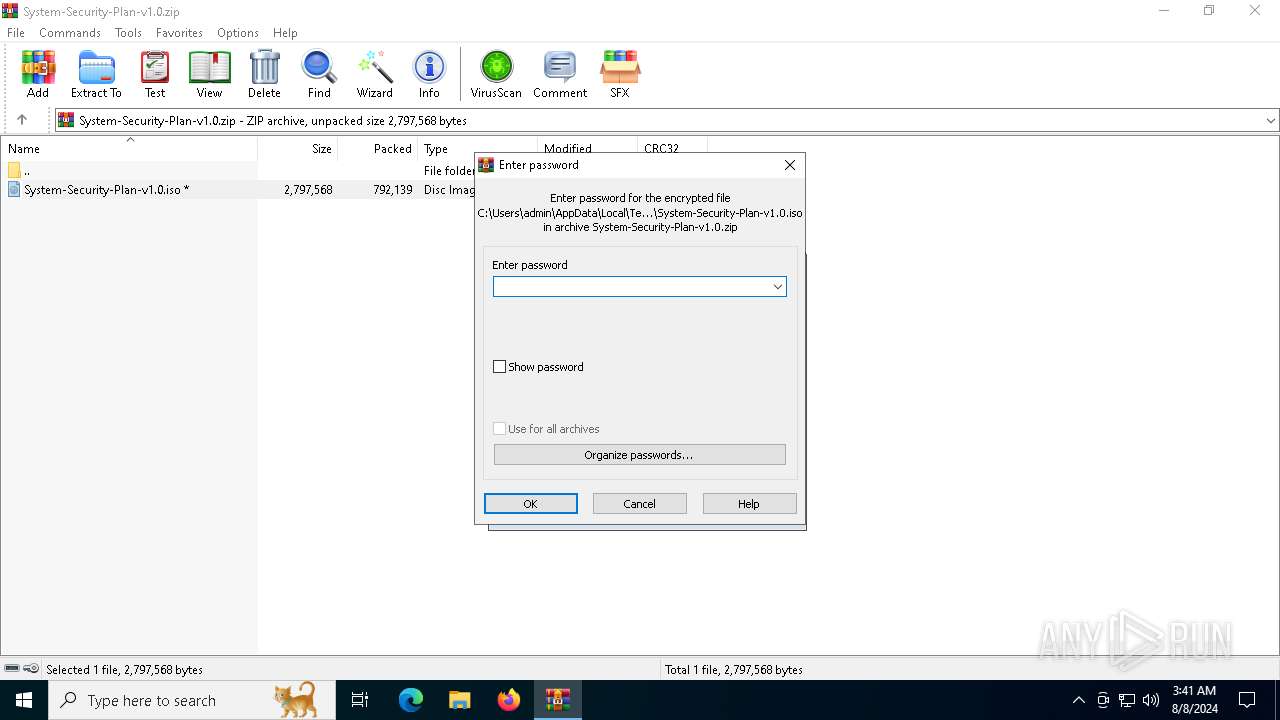
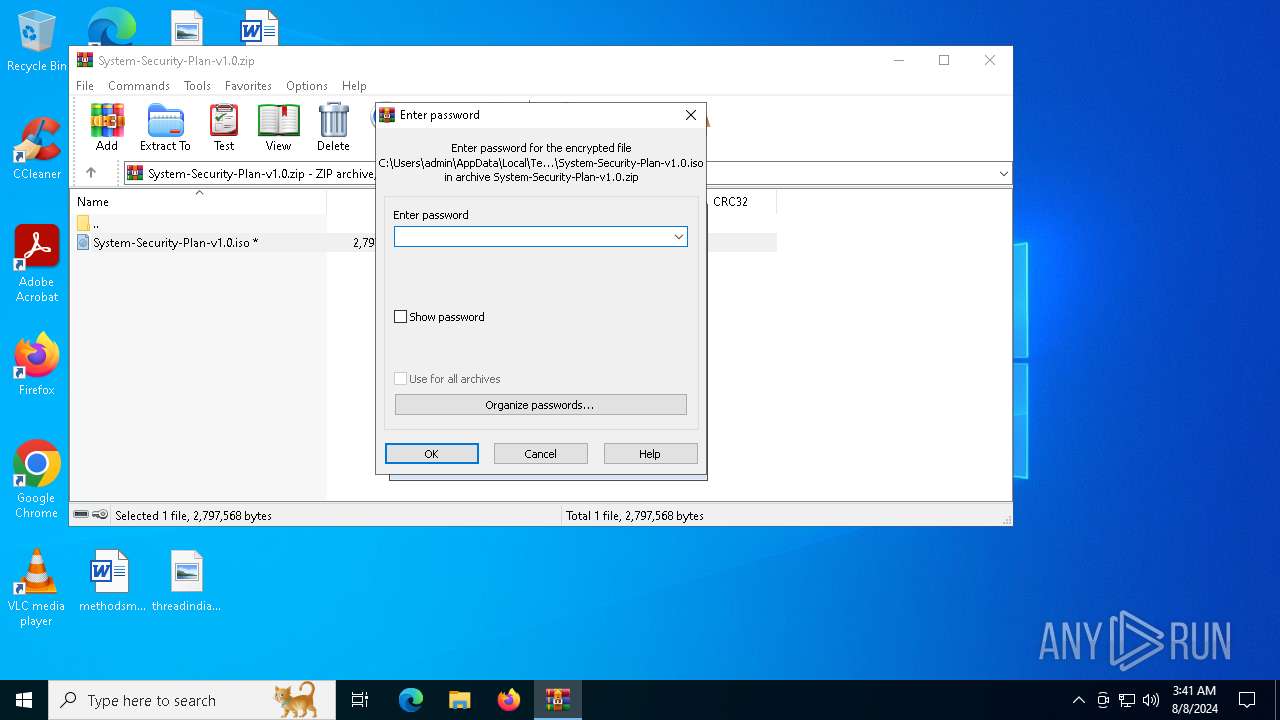
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 980C7E06EE8C7F57633BC76D831C4767 |
| SHA1: | 216D938F5254EF04EEF68777F5FE1477773E96D2 |
| SHA256: | DAD8BDC887E868981F874578A81936562FF6228C2D924FA37FECA7660CB93EF1 |
| SSDEEP: | 24576:ldu39W1/2OLYQXXIGVFHEBgAxYMlrme35pSfDwKfELhDaK0+OrbNUNmGoEW2Zy3H:ldu39W1/2OLYQXXIoFHEBgUYMlrme352 |
MALICIOUS
Changes the login/logoff helper path in the registry
- System-Security-Plan-v1.0.exe (PID: 3720)
Uses Task Scheduler to run other applications
- System-Security-Plan-v1.0.exe (PID: 3720)
SUSPICIOUS
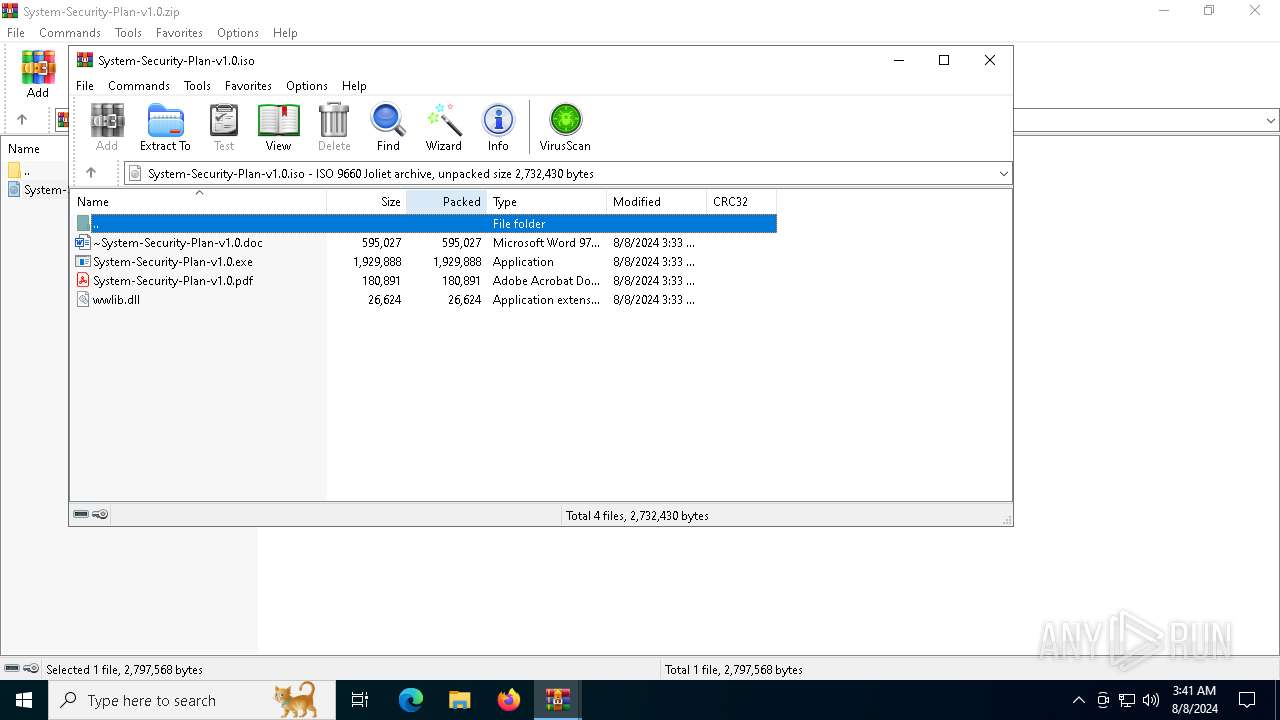
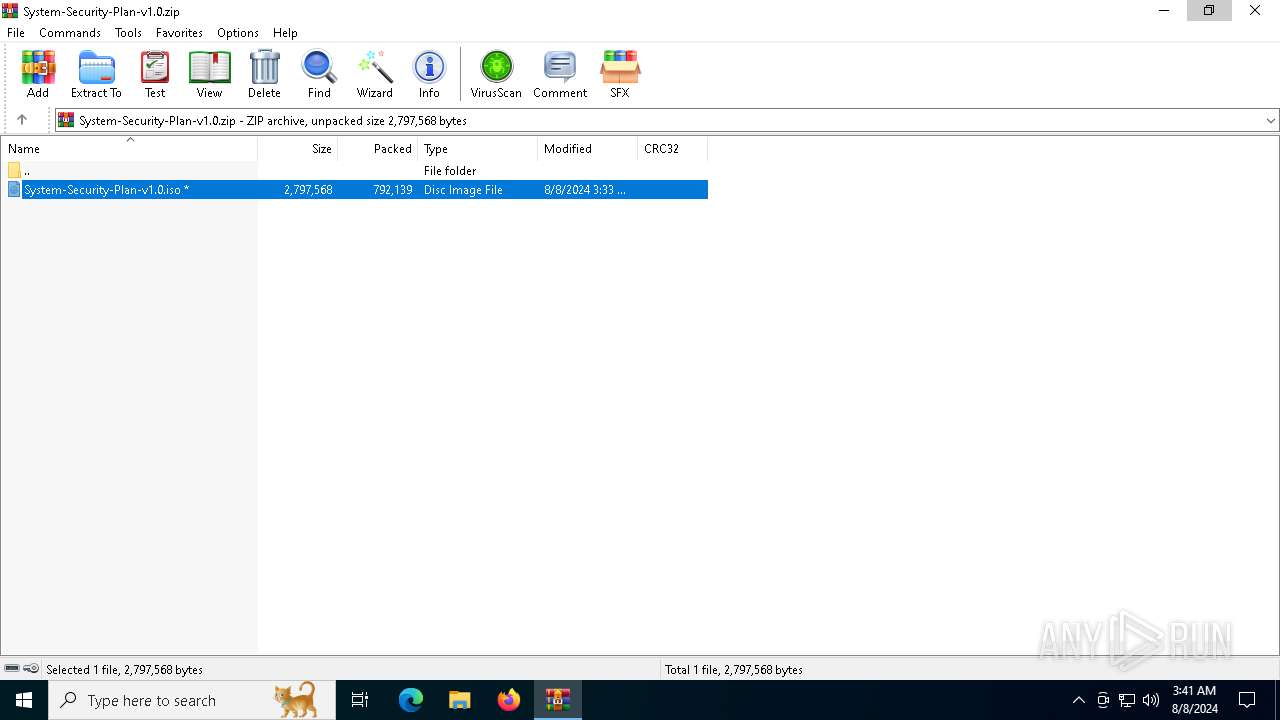
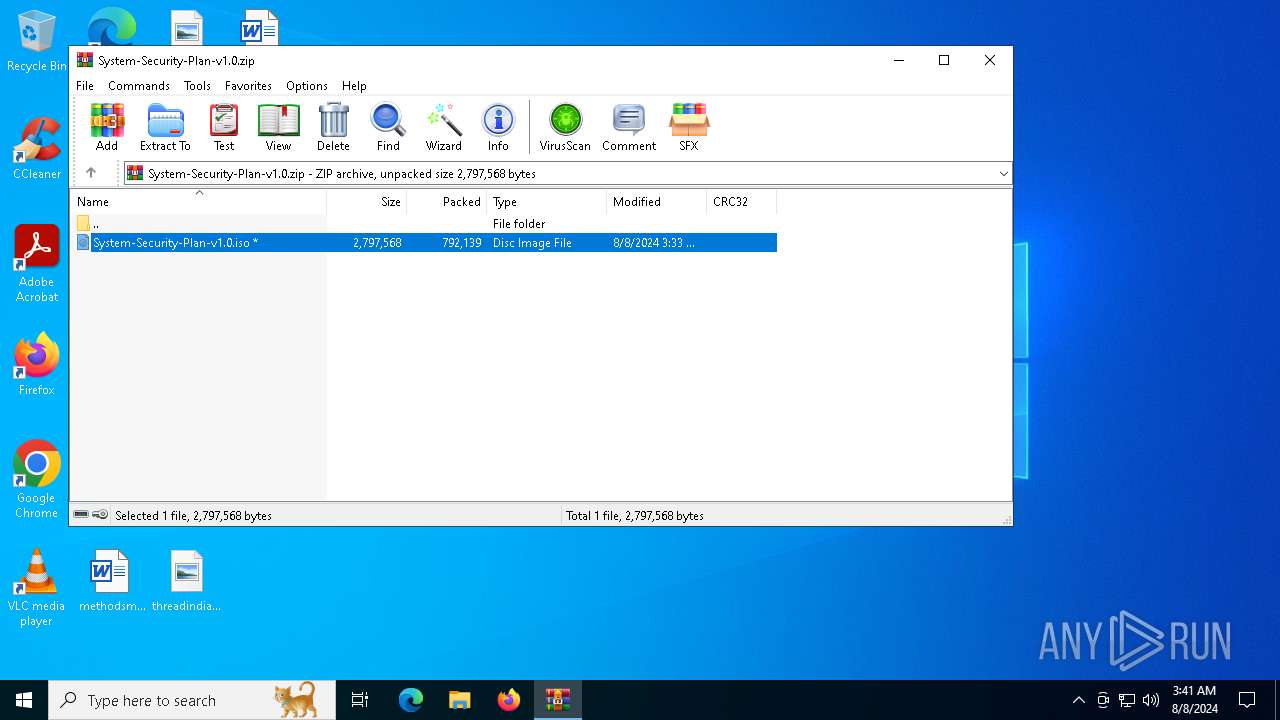
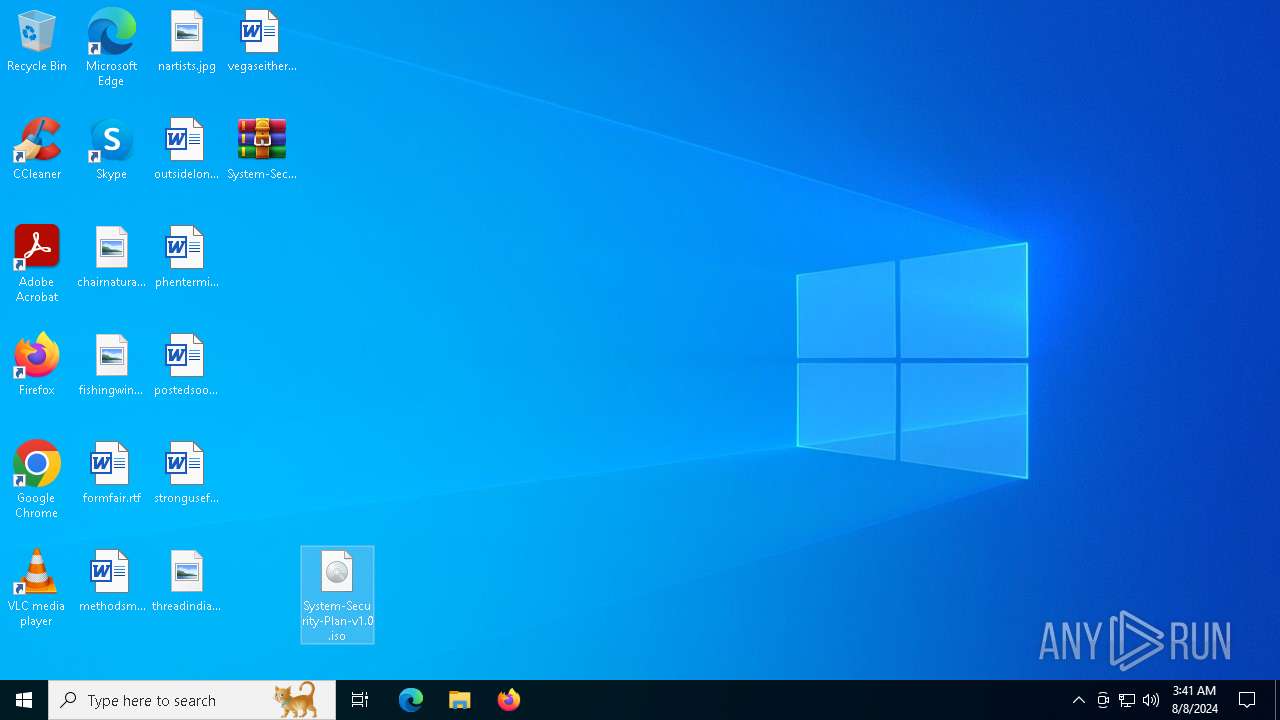
Image mount has been detect
- explorer.exe (PID: 4552)
Application launched itself
- WinRAR.exe (PID: 6380)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6380)
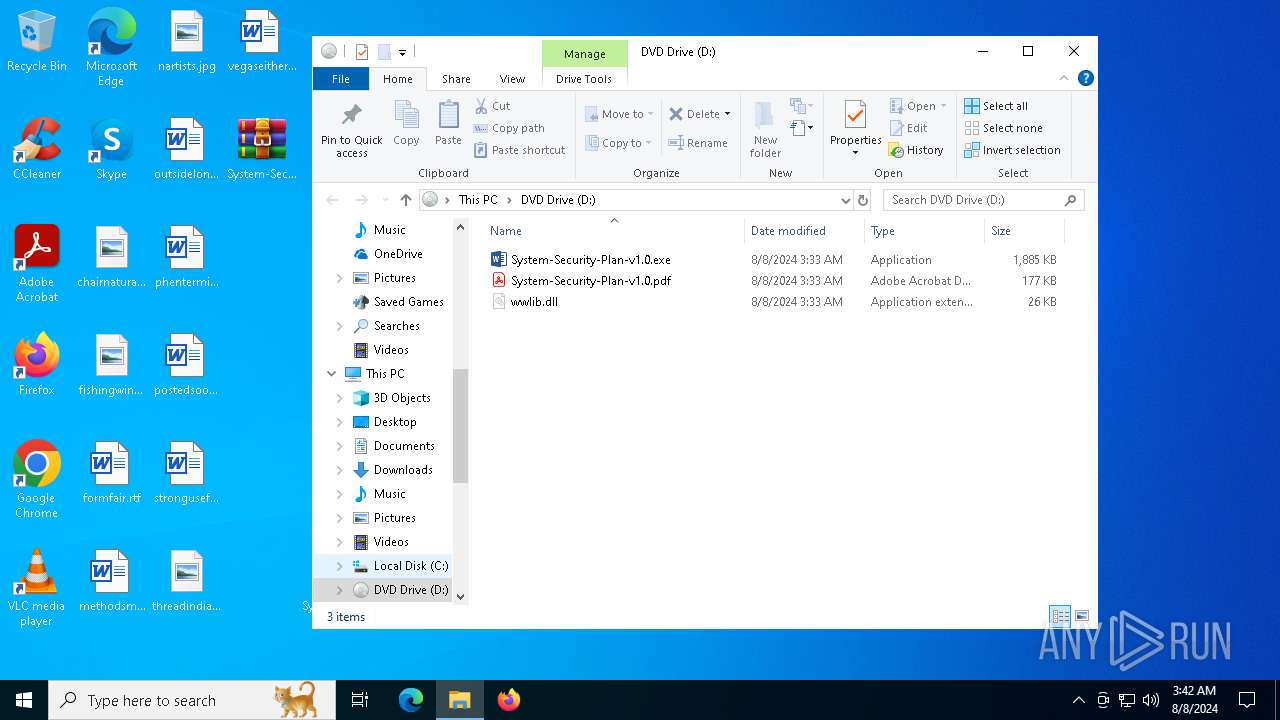
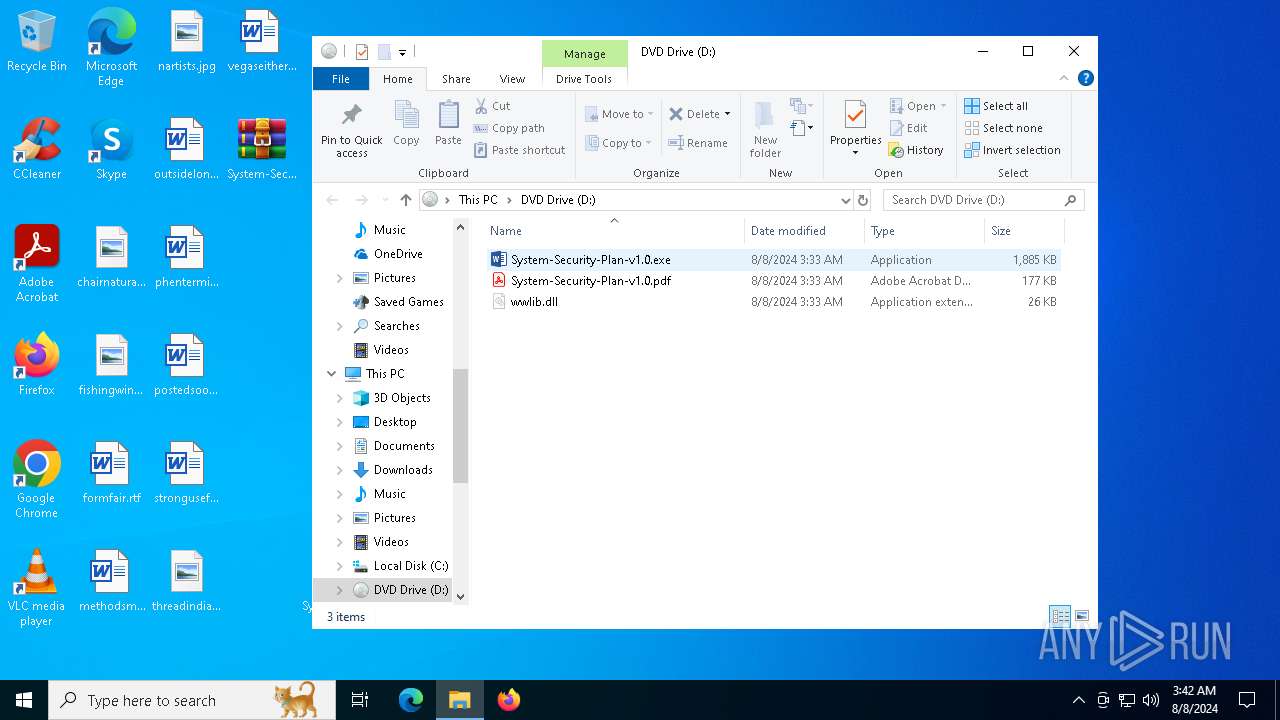
Loading modules from mounted disk drive
- System-Security-Plan-v1.0.exe (PID: 3720)
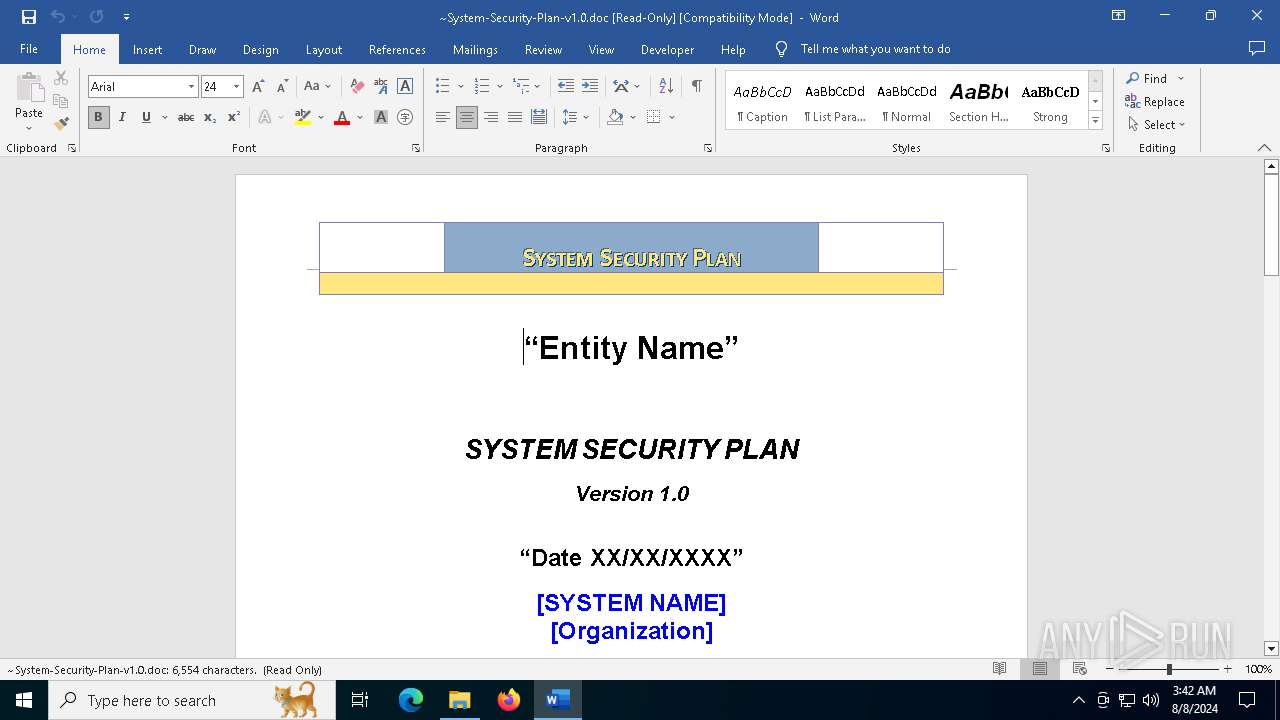
Suspicious WINWORD start
- WINWORD.EXE (PID: 7128)
Starts CMD.EXE for commands execution
- System-Security-Plan-v1.0.exe (PID: 3720)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
Create files in a temporary directory
- System-Security-Plan-v1.0.exe (PID: 3720)
Reads Microsoft Office registry keys
- System-Security-Plan-v1.0.exe (PID: 3720)
Checks supported languages
- System-Security-Plan-v1.0.exe (PID: 3720)
- TextInputHost.exe (PID: 6372)
Reads the computer name
- TextInputHost.exe (PID: 6372)
Manual execution by a user
- System-Security-Plan-v1.0.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:08:08 10:33:52 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 792139 |
| ZipUncompressedSize: | 2797568 |
| ZipFileName: | System-Security-Plan-v1.0.iso |
Total processes
143
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2272 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "6FDAF2FE-E68F-44AB-92DF-C9F0D48EE699" "BC9F0ECA-9841-42D9-812F-E4A16B5D3D0C" "7128" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 2468 | cmd /c """"C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Word.lnk" "~System-Security-Plan-v1.0.doc"""" | C:\Windows\System32\cmd.exe | — | System-Security-Plan-v1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3720 | "D:\System-Security-Plan-v1.0.exe" | D:\System-Security-Plan-v1.0.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.4266.1001 Modules
| |||||||||||||||
| 4552 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | SCHTASKS /CREATE /f /TN "ChromeSoftwareUpdateTask" /TR "shutdown /l /f" /SC WEEKLY /d MON,THU /ST 01:23 | C:\Windows\System32\schtasks.exe | — | System-Security-Plan-v1.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6380 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\System-Security-Plan-v1.0.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6632 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb6380.31602\System-Security-Plan-v1.0.iso | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
40 414
Read events
39 896
Write events
488
Delete events
30
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010014000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C0000001400000000000000630068006100690072006E00610074007500720061006C002E006A00700067003E002000200000001300000000000000660069007300680069006E006700770069006E0065002E006A00700067003E00200020000000100000000000000066006F0072006D0066006100690072002E007200740066003E0020002000000014000000000000006D006500740068006F00640073006D0065006400690061002E007200740066003E0020002000000010000000000000006E0061007200740069007300740073002E006A00700067003E0020002000000015000000000000006F007500740073006900640065006C006F006E0064006F006E002E007200740066003E002000200000001B000000000000007000680065006E007400650072006D0069006E00650066006F006F007400620061006C006C002E007200740066003E00200020000000120000000000000070006F00730074006500640073006F006F006E002E007200740066003E0020002000000014000000000000007300740072006F006E006700750073006500660075006C002E007200740066003E00200020000000140000000000000074006800720065006100640069006E006400690061006E002E006A00700067003E002000200000001300000000000000760065006700610073006500690074006800650072002E007200740066003E002000200000002100000000000000530079007300740065006D002D00530065006300750072006900740079002D0050006C0061006E002D00760031002E0030002E007A00690070003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001400000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000080410000A0401300 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010014000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C0000001400000000000000630068006100690072006E00610074007500720061006C002E006A00700067003E002000200000001300000000000000660069007300680069006E006700770069006E0065002E006A00700067003E00200020000000100000000000000066006F0072006D0066006100690072002E007200740066003E0020002000000014000000000000006D006500740068006F00640073006D0065006400690061002E007200740066003E0020002000000010000000000000006E0061007200740069007300740073002E006A00700067003E0020002000000015000000000000006F007500740073006900640065006C006F006E0064006F006E002E007200740066003E002000200000001B000000000000007000680065006E007400650072006D0069006E00650066006F006F007400620061006C006C002E007200740066003E00200020000000120000000000000070006F00730074006500640073006F006F006E002E007200740066003E0020002000000014000000000000007300740072006F006E006700750073006500660075006C002E007200740066003E00200020000000140000000000000074006800720065006100640069006E006400690061006E002E006A00700067003E002000200000001300000000000000760065006700610073006500690074006800650072002E007200740066003E002000200000002100000000000000530079007300740065006D002D00530065006300750072006900740079002D0050006C0061006E002D00760031002E0030002E007A00690070003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001400000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000040400000803F1300 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 653EB46600000000 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\System-Security-Plan-v1.0.zip | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
128
Text files
49
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb6380.31602\System-Security-Plan-v1.0.iso | compressed | |
MD5:A84103CBF9187EF4432573AA549166DB | SHA256:1A1FE9E5B024EBAB4A1E412BB8FA43E13FA15D32620B88D824B0013F46E0969C | |||
| 3720 | System-Security-Plan-v1.0.exe | C:\Users\admin\AppData\Local\Temp\wctA91F.tmp | text | |
MD5:10EEE23908391C559F2C5DEE45E63628 | SHA256:A03579698D3A47CD12CE6BF98B0CE39316486DD5D76A9C71A28957A7B0E3CE10 | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:83CD56136942C145023B69B54C7F89F6 | SHA256:121559F2286F6A1D633543378BD9108A0401BB6D5B17BA56BFDA41BBD6F2F972 | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:B3A418EAFEE8B7DC6932AB0A1FE23E00 | SHA256:911EE85BED29EB588C0AE7D749D1A991BB8935A81BDE8B66FF082BFB50D6D0B4 | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:51EFF429CC01C6ECBF3C0EE1A07E6630 | SHA256:0FED9DC482110CE0F301795969FA68E11BACAAF326C255C5AD7723A38E84BE1C | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 4552 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\~System-Security-Plan-v1.0.doc.LNK | binary | |
MD5:F993CFFAD3FB24DCFDAF95B009672BA5 | SHA256:BF1BFA2B1258B7E05553775A255B341C36819CE356E08187BAEF7D33E49BF4CD | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\PreviewFont\flat_officeFontsPreview_4_40.ttf | binary | |
MD5:4296A064B917926682E7EED650D4A745 | SHA256:E04E41C74D6C78213BA1588BACEE64B42C0EDECE85224C474A714F39960D8083 | |||
| 7128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:76B7179B1464F41B371ABAAA5B8160E5 | SHA256:5E13B7C964C1646C9CC8FD8F46311566583CE9E169901D19C07B177A41ECEEAC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
105
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3160 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3160 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6696 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7128 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6752 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7128 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7128 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7128 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7128 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5796 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4084 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4084 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 95.100.146.34:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3160 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|