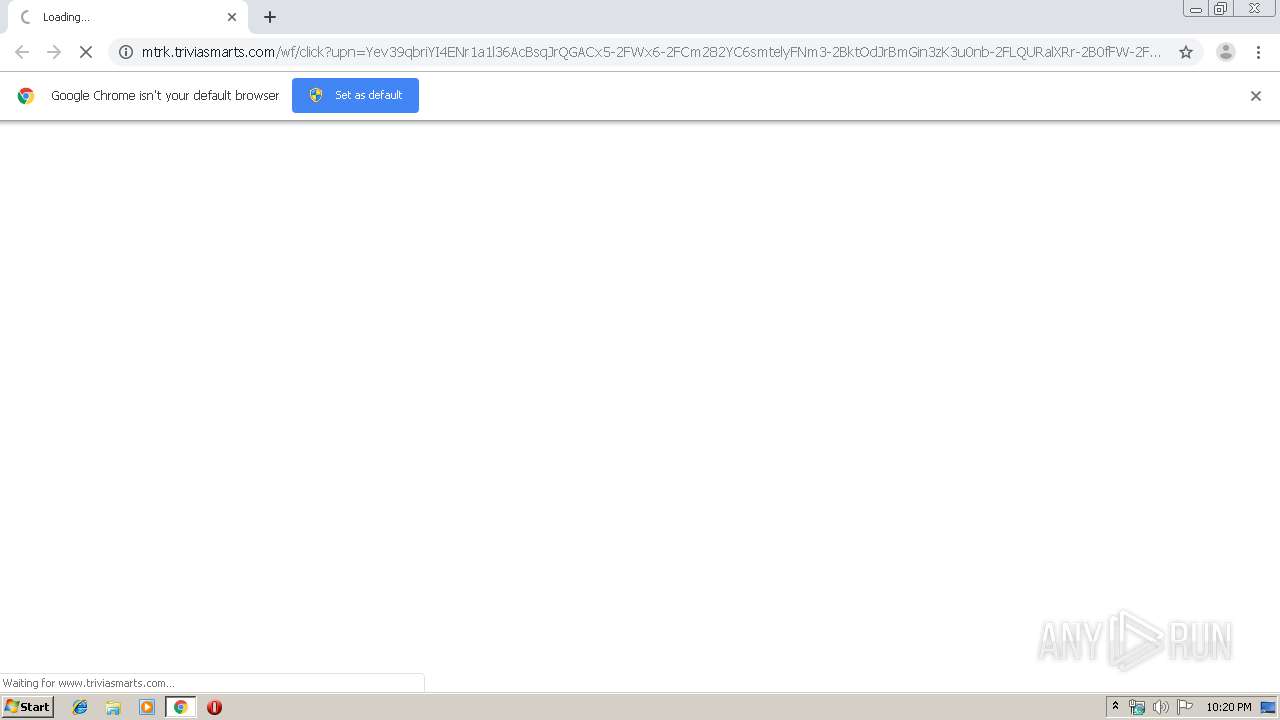
| URL: | http://mtrk.triviasmarts.com/wf/click?upn=Yev39qbriYI4ENr1a1l36AcBsqJrQGACx5-2FWx6-2FCm282YC6smtelyFNm3-2BktOdJrBmGin3zK3u0nb-2FLQURalXRr-2B0fFW-2FcOU-2FqScB2LLuat-2Bdv-2BBoez3Fs7-2F8l0f-2BOto1IeRn2-2FESu5r-2BIbl7i0hgkSJDeFzQk7zqKlujvnLNxe4UOvv7uudNPLesn7DieN8Om67If18x19o-2BZZLvwmH-2F61faSAcuZpBO-2BWRrUJMFqwcDPuT3bnzkRw7cLee7OT4RprkuAZ6v6K45uymh96jCcej21WEe05uTOel1UCM7O58hGjWO9TWHbiajKgdra-2BkIAGPmBZX9ClSYzwL2gUgdUM8MQ-2F2pgKJlcdtteJps5l1ewlHsJa7RiWq7C3Ma7YdDWXutcEi-2BMqstJgV2JxdERrS0H-2FIO7mGHpYL3qTUVj4MkJZKDKPv0ZrC5qDspwaV2BacENNsSka62UpwU51c8WYhuwtGEDfBRIromagGuh896lkqq0GeiwMVQ33DW0V0EhUFfM-2Fj9PV30S1V5MopUSJPn0UTbNzLIS1CYpiSgDzUJ5pyVoRGJ4i5Y-2FoIydXSWmjOjRAnk-2FLgK1-2Fd1vFJMTPoD1Z9q6D-2B0zRxS-2BKPMmQIqZaAGNTAoD-2FDPK3mOAhEAKUzS6yLRBkEtRPcVnRa0w-3D-3D_Hcomczv99Nu1BylQX0x6o-2FoSiNHeRdMFGYxDaVhfOjEAk-2BUc3ck39aJBWDpYYndjT50pzzSFZoaxtO1a59SRNgv7fHggtJn13unIVkyDt1FJmUPbCuk7ZSmqMewxB0EsVx33qLR-2BTKWhNEEr3VA15WgTp2c6De-2FuqWTOpdcJ7ue4XptZpgPArEAPcczMdSsnuXtpCOutKCko3EFPsifQZzUPwdJuNkA-2BFZ1grRW7sVBzqdM83IoS0aMJStSNzgYN4lJzUUEUiLX0JBwSc5XG2rzIc-2BLCNV2nlhyGI8mfZJuYR0CpsSqsQ3m-2BvtPZEThG |
| Full analysis: | https://app.any.run/tasks/03ede781-7358-4656-a3c9-97ca8e1b7ebf |
| Verdict: | No threats detected |
| Analysis date: | July 17, 2019, 21:20:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D0AC61814C790F63FA2335CB7F62BB48 |
| SHA1: | 38CC4630762DCF5D8E7672FA8E6C33B09ED8B6AA |
| SHA256: | DACCAF19C51F46DF90C593D2FB19BBC6E082C5467B208DF69FB79437CE9FABB1 |
| SSDEEP: | 24:rlXuGXhiDiKYX4kJsmIuqs2QfxdzG4VJUAErrSw7lC1jycfk2hQ:50eKe48Tqs2cdzG4VKxewmy+pm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2888)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2928)
Application launched itself
- chrome.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12205809161745236046 --mojo-platform-channel-handle=3992 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17521171314340976427 --mojo-platform-channel-handle=4652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7946087309262024392 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14231592630457660342 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15503573893082268219 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6189835783040447038 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16986905022840809712 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12227190216120076520 --mojo-platform-channel-handle=4420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12249894933670467369 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7261105415448768823,4268591893537900462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3928611937006873148 --mojo-platform-channel-handle=4128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
615
Read events
523
Write events
87
Delete events
5
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2888-13207872019730750 |
Value: 259 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
79
Text files
211
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d80e573c-02d0-4de2-94d7-19846ecce494.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10dc68.TMP | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10dc58.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
54
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
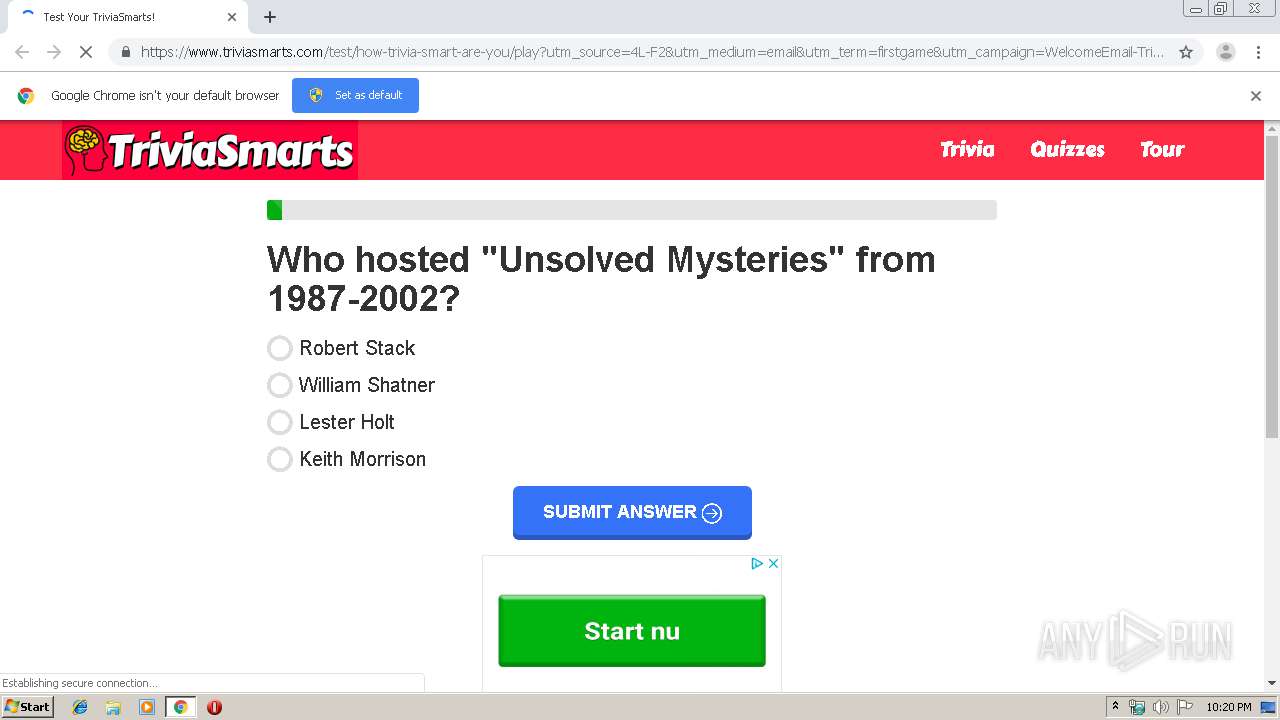
2928 | chrome.exe | GET | 302 | 3.94.176.246:80 | http://ogtrk.triviasmarts.com/?xtl=xl1zpf5j69oqg7cs8no6tmrymxid339k67cq35jt7s71gn2pkf27gyph8tqfkhhjw994fennu5tvwxk52uokp6vk7q6c1a75x783qtd2jpww41k93ei3hs6be4d43s4fcxneryalzd3cuc7nhf2lszpt6xe8yx246s5dz52bw8bru8gtmy5fnui9i43hg53vnl3sxs9wjhw5iwn9rsznsxvrzej0shuk5yf6vhnwi390lmrrds18ogq8mmg4tl9nzm68vb0lukrfva73jx58fwz6tt7l9daq7jnqccv7udg8j12lgvmzyljl2ag4ojiaib3mf0j5a2a4t1n31xkgn2l34a5pesrhi0m2spxxkxn&eih=4dog94gtvojnjh2j664mfh2mhdi1vo72nzsd4g9j&email=john.langendorf@swgas.com&source=4L-F2 | US | — | — | whitelisted |
2928 | chrome.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.3 Kb | whitelisted |
2928 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
2928 | chrome.exe | GET | 200 | 173.194.182.70:80 | http://r1---sn-4g5e6ns7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=5.79.79.103&mm=28&mn=sn-4g5e6ns7&ms=nvh&mt=1563397840&mv=u&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2928 | chrome.exe | GET | 200 | 13.225.84.136:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2928 | chrome.exe | GET | 302 | 167.89.118.52:80 | http://mtrk.triviasmarts.com/wf/click?upn=Yev39qbriYI4ENr1a1l36AcBsqJrQGACx5-2FWx6-2FCm282YC6smtelyFNm3-2BktOdJrBmGin3zK3u0nb-2FLQURalXRr-2B0fFW-2FcOU-2FqScB2LLuat-2Bdv-2BBoez3Fs7-2F8l0f-2BOto1IeRn2-2FESu5r-2BIbl7i0hgkSJDeFzQk7zqKlujvnLNxe4UOvv7uudNPLesn7DieN8Om67If18x19o-2BZZLvwmH-2F61faSAcuZpBO-2BWRrUJMFqwcDPuT3bnzkRw7cLee7OT4RprkuAZ6v6K45uymh96jCcej21WEe05uTOel1UCM7O58hGjWO9TWHbiajKgdra-2BkIAGPmBZX9ClSYzwL2gUgdUM8MQ-2F2pgKJlcdtteJps5l1ewlHsJa7RiWq7C3Ma7YdDWXutcEi-2BMqstJgV2JxdERrS0H-2FIO7mGHpYL3qTUVj4MkJZKDKPv0ZrC5qDspwaV2BacENNsSka62UpwU51c8WYhuwtGEDfBRIromagGuh896lkqq0GeiwMVQ33DW0V0EhUFfM-2Fj9PV30S1V5MopUSJPn0UTbNzLIS1CYpiSgDzUJ5pyVoRGJ4i5Y-2FoIydXSWmjOjRAnk-2FLgK1-2Fd1vFJMTPoD1Z9q6D-2B0zRxS-2BKPMmQIqZaAGNTAoD-2FDPK3mOAhEAKUzS6yLRBkEtRPcVnRa0w-3D-3D_Hcomczv99Nu1BylQX0x6o-2FoSiNHeRdMFGYxDaVhfOjEAk-2BUc3ck39aJBWDpYYndjT50pzzSFZoaxtO1a59SRNgv7fHggtJn13unIVkyDt1FJmUPbCuk7ZSmqMewxB0EsVx33qLR-2BTKWhNEEr3VA15WgTp2c6De-2FuqWTOpdcJ7ue4XptZpgPArEAPcczMdSsnuXtpCOutKCko3EFPsifQZzUPwdJuNkA-2BFZ1grRW7sVBzqdM83IoS0aMJStSNzgYN4lJzUUEUiLX0JBwSc5XG2rzIc-2BLCNV2nlhyGI8mfZJuYR0CpsSqsQ3m-2BvtPZEThG | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2928 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2928 | chrome.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2928 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2928 | chrome.exe | 172.217.21.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2928 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2928 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 167.89.118.52:80 | mtrk.triviasmarts.com | SendGrid, Inc. | US | suspicious |
2928 | chrome.exe | 167.89.118.52:80 | mtrk.triviasmarts.com | SendGrid, Inc. | US | suspicious |
2928 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2928 | chrome.exe | 216.58.207.66:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mtrk.triviasmarts.com |
| suspicious |
accounts.google.com |
| shared |
ogtrk.triviasmarts.com |
| unknown |
www.triviasmarts.com |
| unknown |
cdn.onesignal.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |