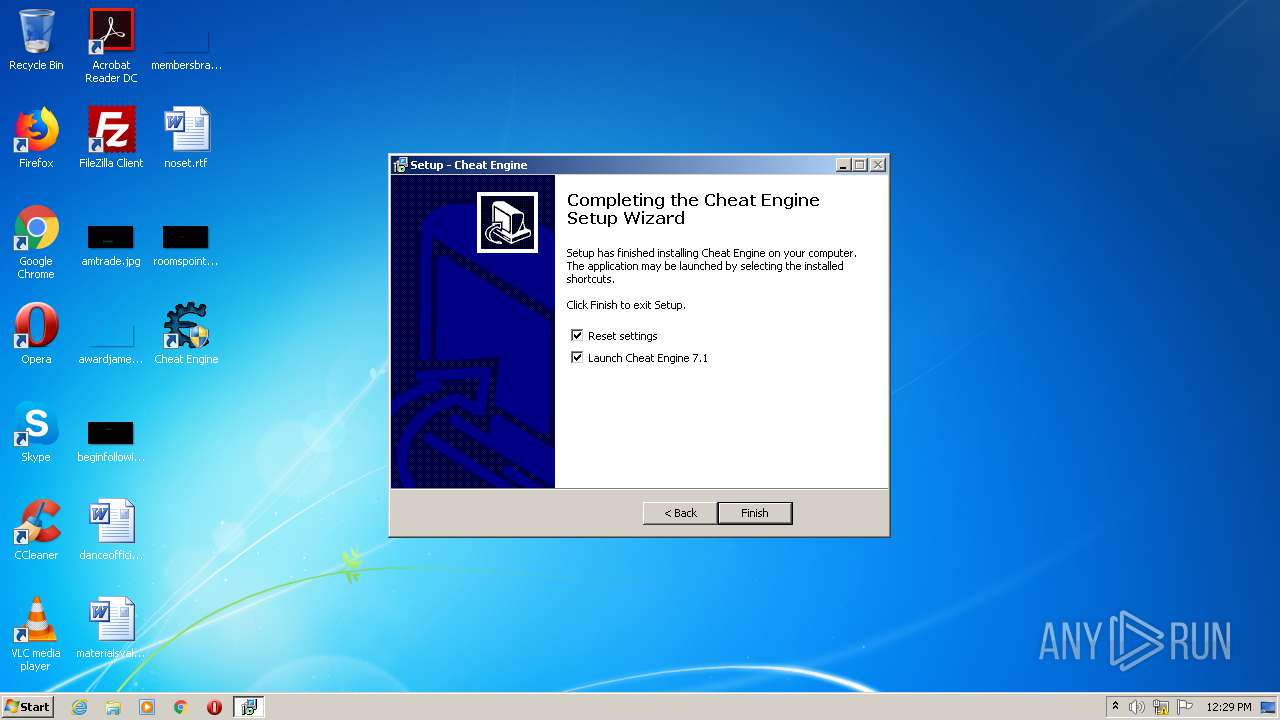
| download: | CheatEngine71.exe |
| Full analysis: | https://app.any.run/tasks/414a1194-9729-4017-ac07-f8c903950e16 |
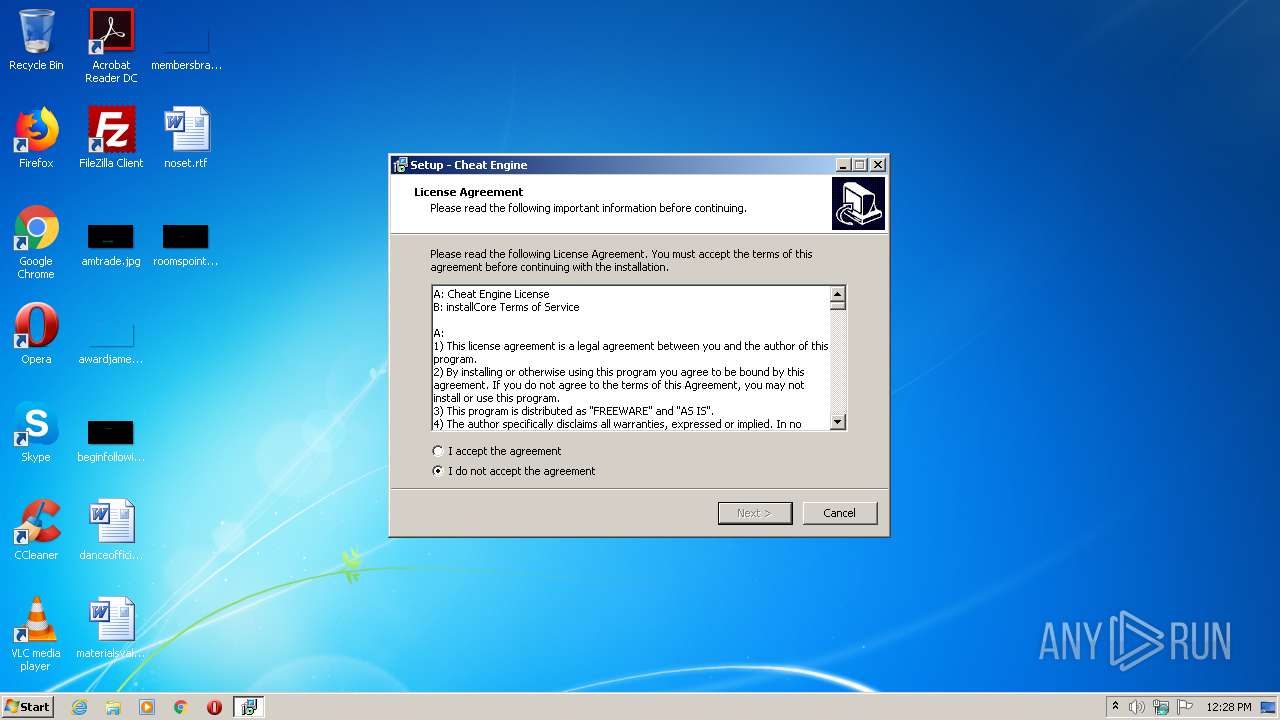
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2020, 11:28:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 786A3BF82B79CA605B2E23887047D1C5 |
| SHA1: | DFA2E77A7ED79BD64CF4EA1D65D8645D3A1D701B |
| SHA256: | DAB8B0C4850115E3EE09168656739A693C0024D9924C90D27D12463A60237D1F |
| SSDEEP: | 393216:olzt8vWDkHk+hotioyhE/u9Ho7H/mGaXjYr/l6BPCpf7M8Dh5D3TOTJdWSlKZN+:ChgHkAEFu9IzYjG/oaxMm5DDOTJISls0 |
MALICIOUS
Actions looks like stealing of personal data
- CheatEngine71.tmp (PID: 3936)
Application was dropped or rewritten from another process
- windowsrepair.exe (PID: 1804)
- Kernelmoduleunloader.exe (PID: 2108)
SUSPICIOUS
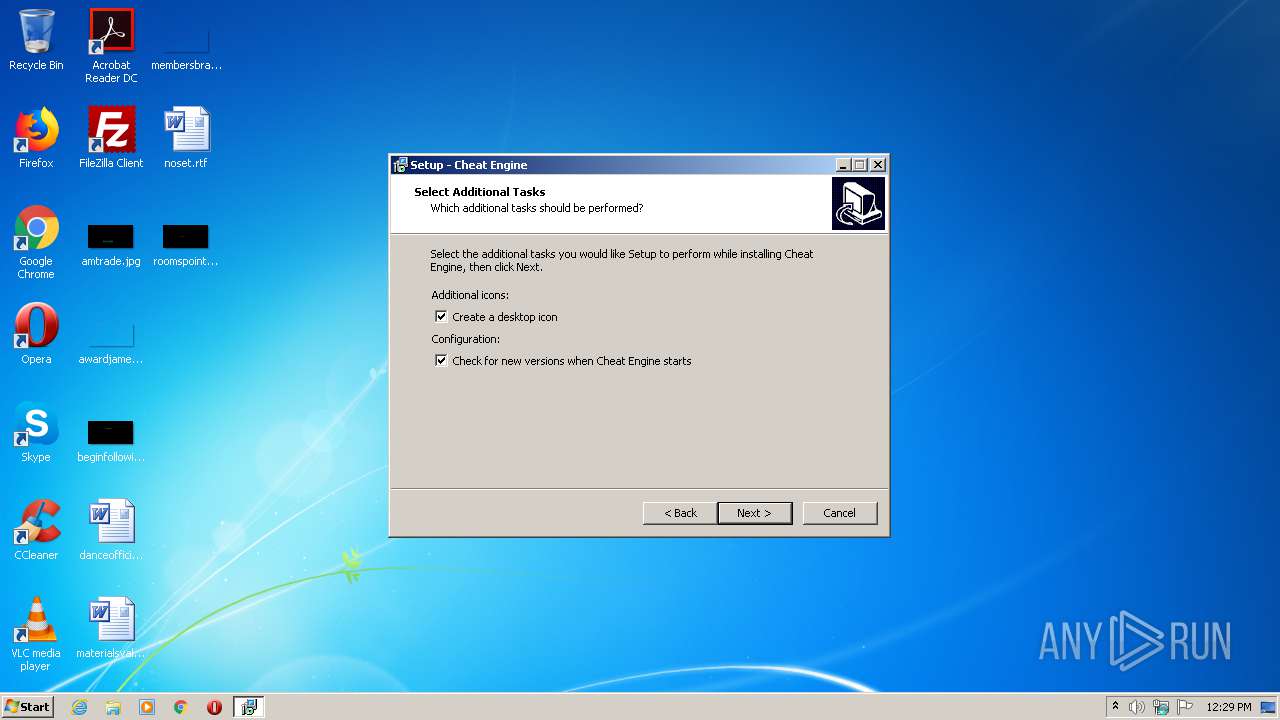
Executable content was dropped or overwritten
- CheatEngine71.exe (PID: 2624)
- CheatEngine71.exe (PID: 3028)
- CheatEngine71.tmp (PID: 3936)
Reads Environment values
- CheatEngine71.tmp (PID: 3936)
Reads Internet Cache Settings
- CheatEngine71.tmp (PID: 3936)
Reads the Windows organization settings
- CheatEngine71.tmp (PID: 3936)
Reads Windows owner or organization settings
- CheatEngine71.tmp (PID: 3936)
Reads internet explorer settings
- CheatEngine71.tmp (PID: 3936)
Modifies the open verb of a shell class
- CheatEngine71.tmp (PID: 3936)
Uses ICACLS.EXE to modify access control list
- CheatEngine71.tmp (PID: 3936)
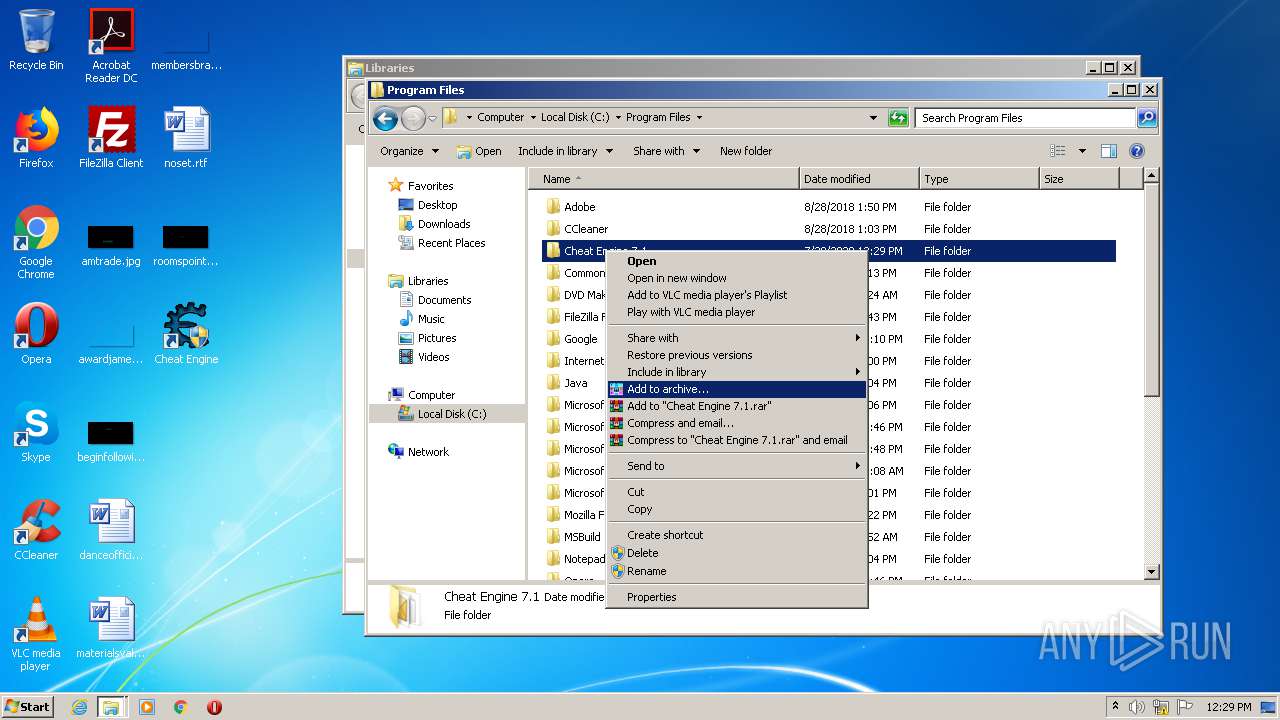
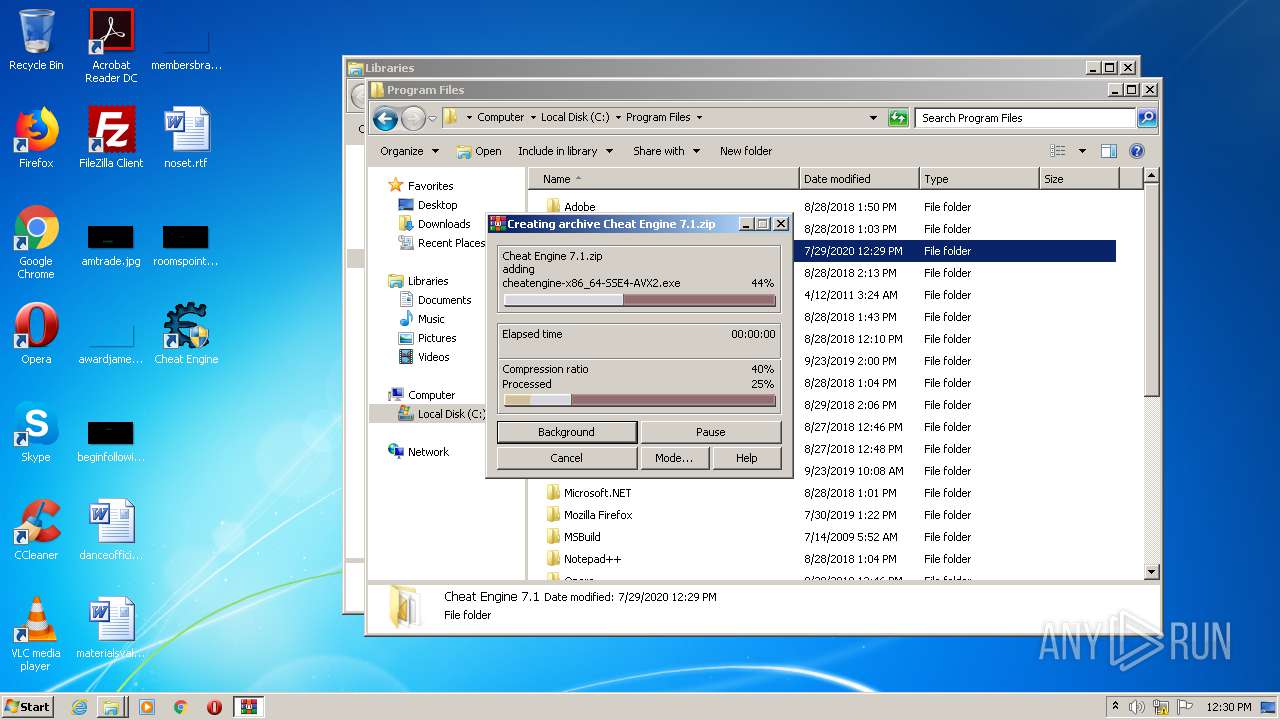
Application launched itself
- WinRAR.exe (PID: 900)
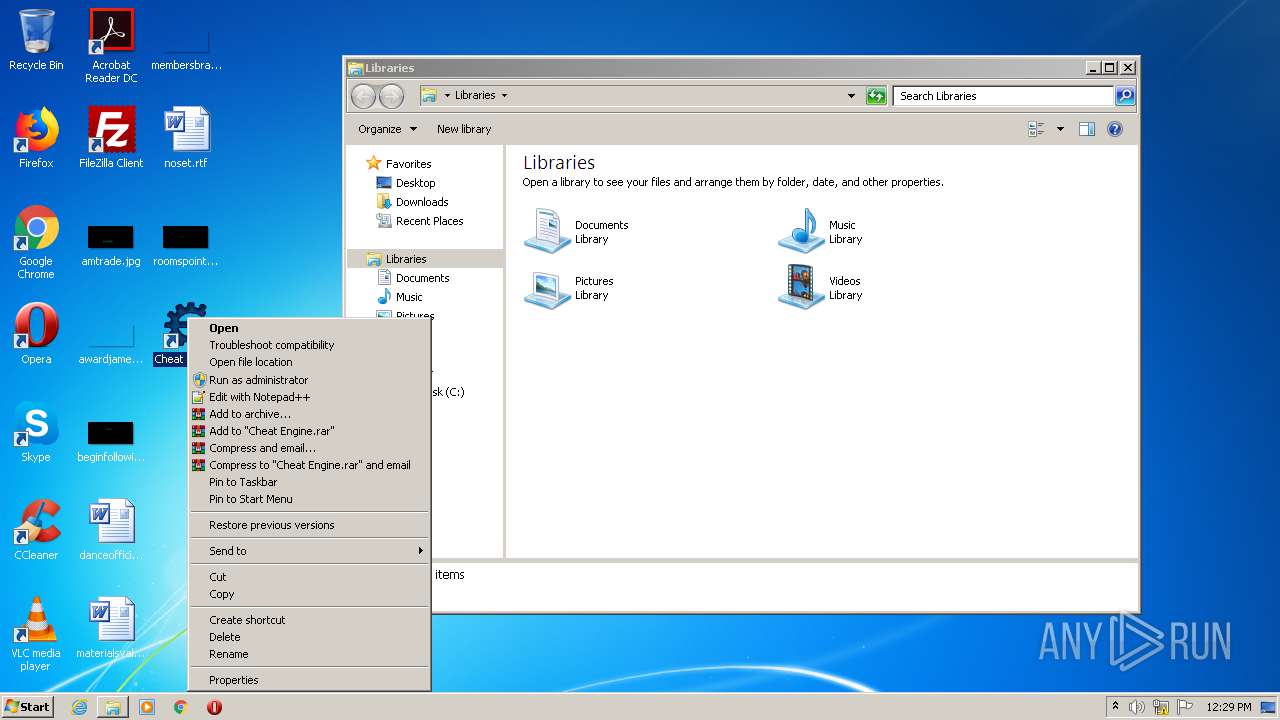
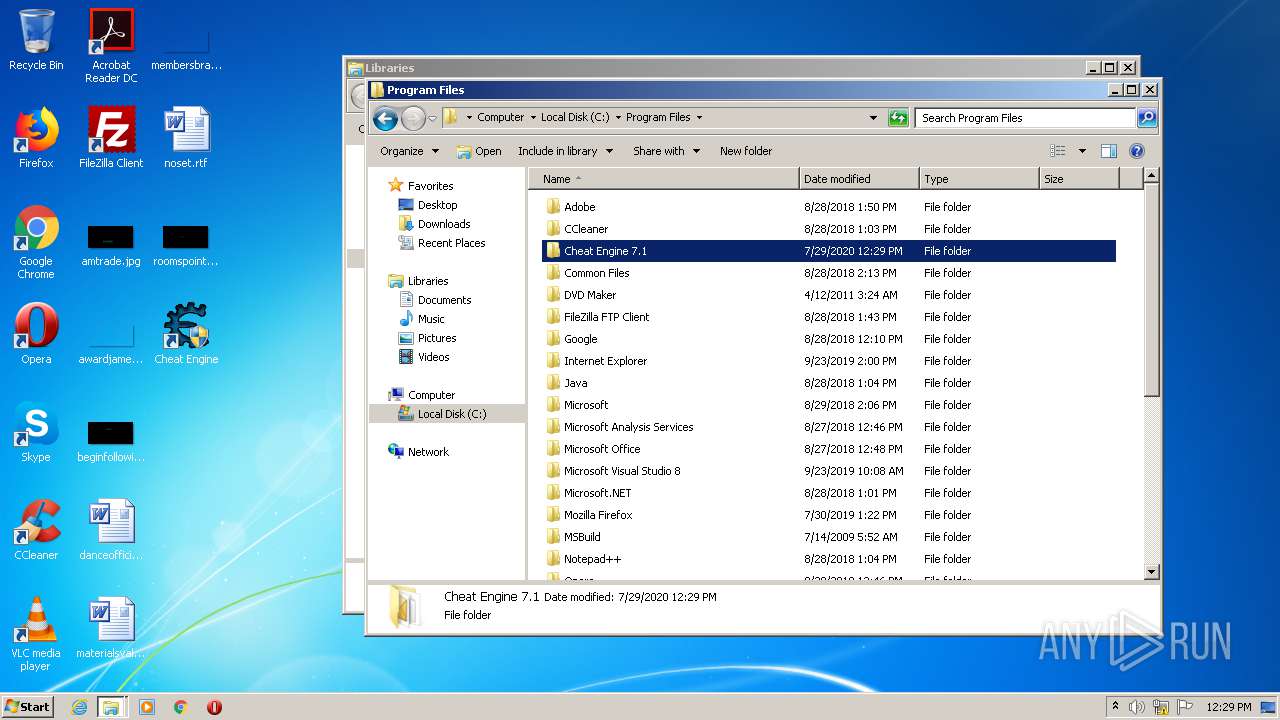
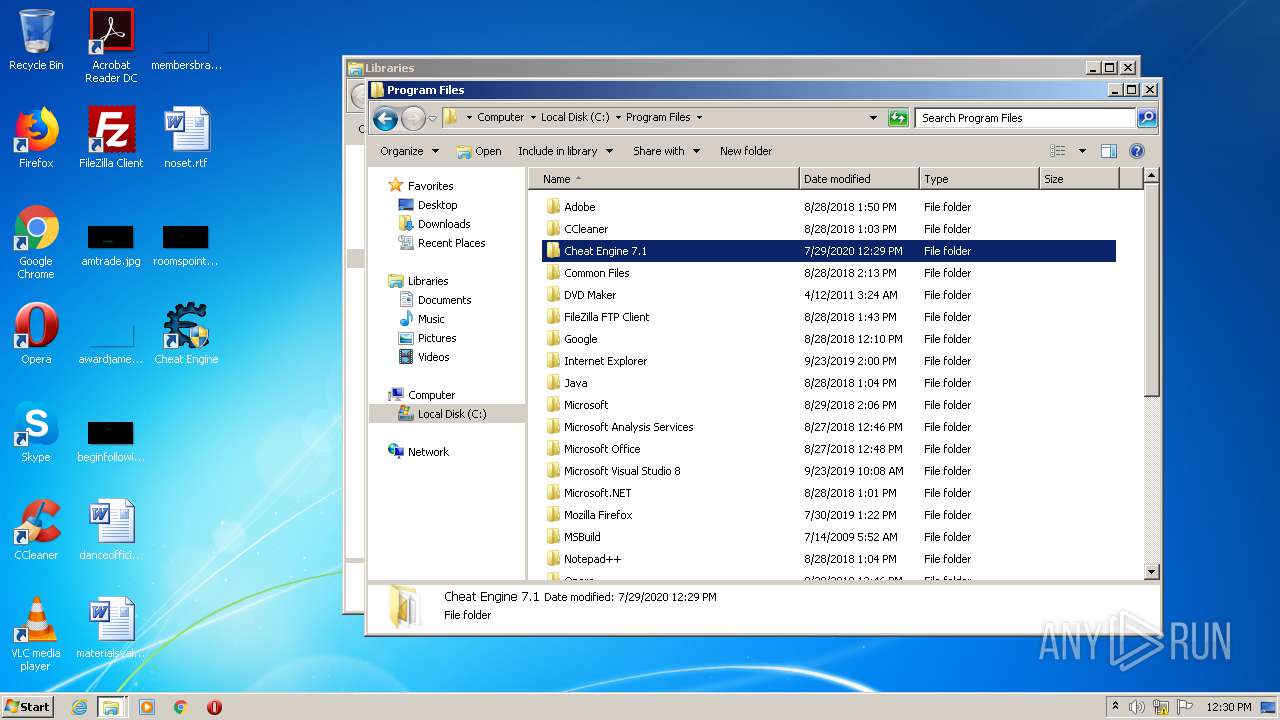
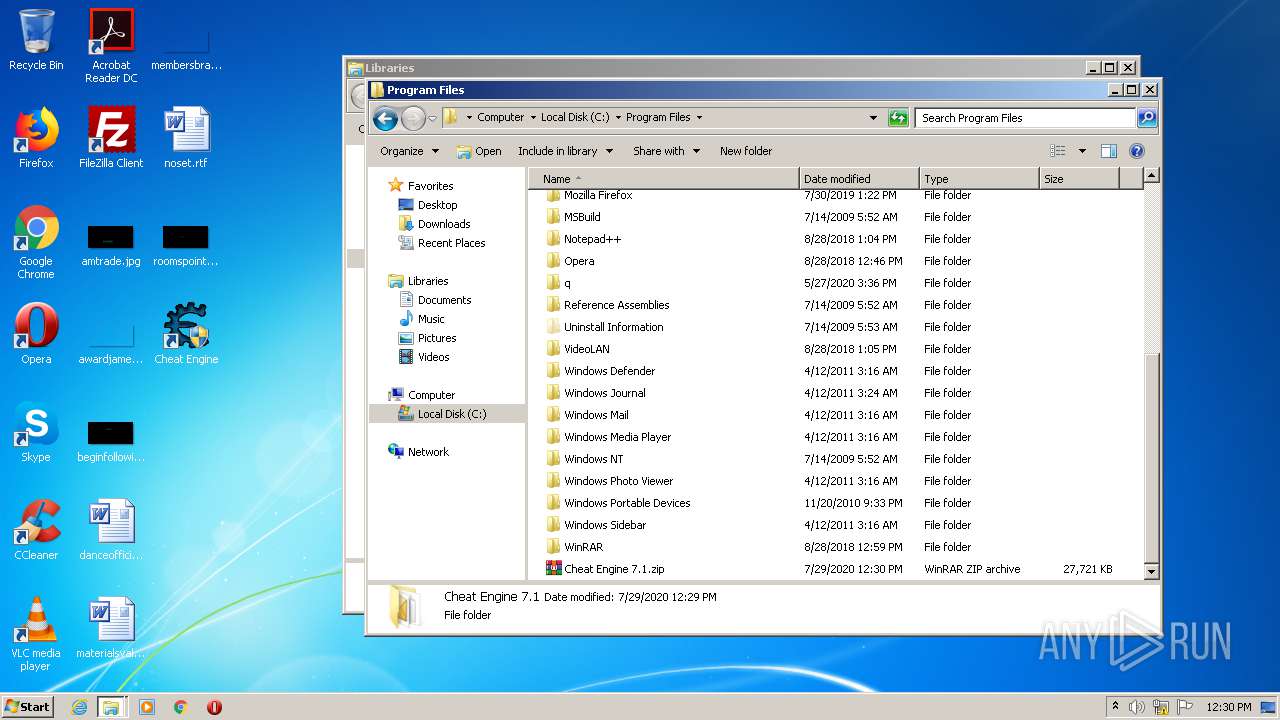
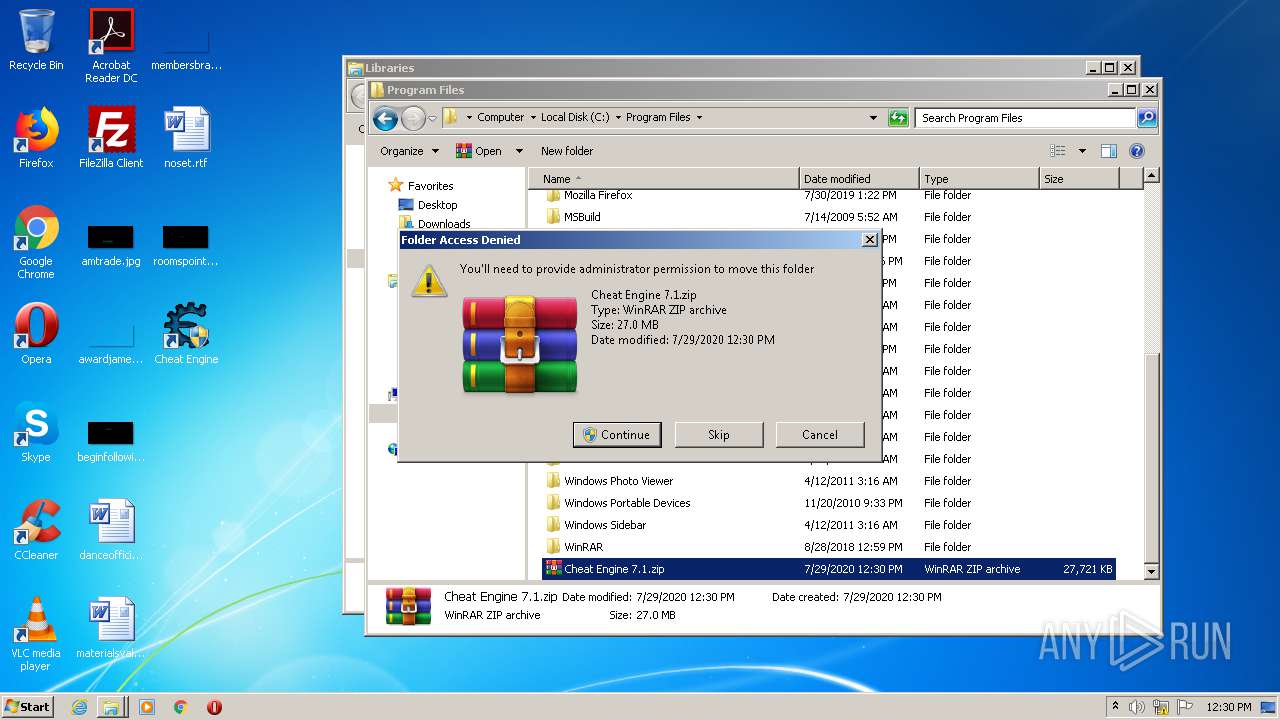
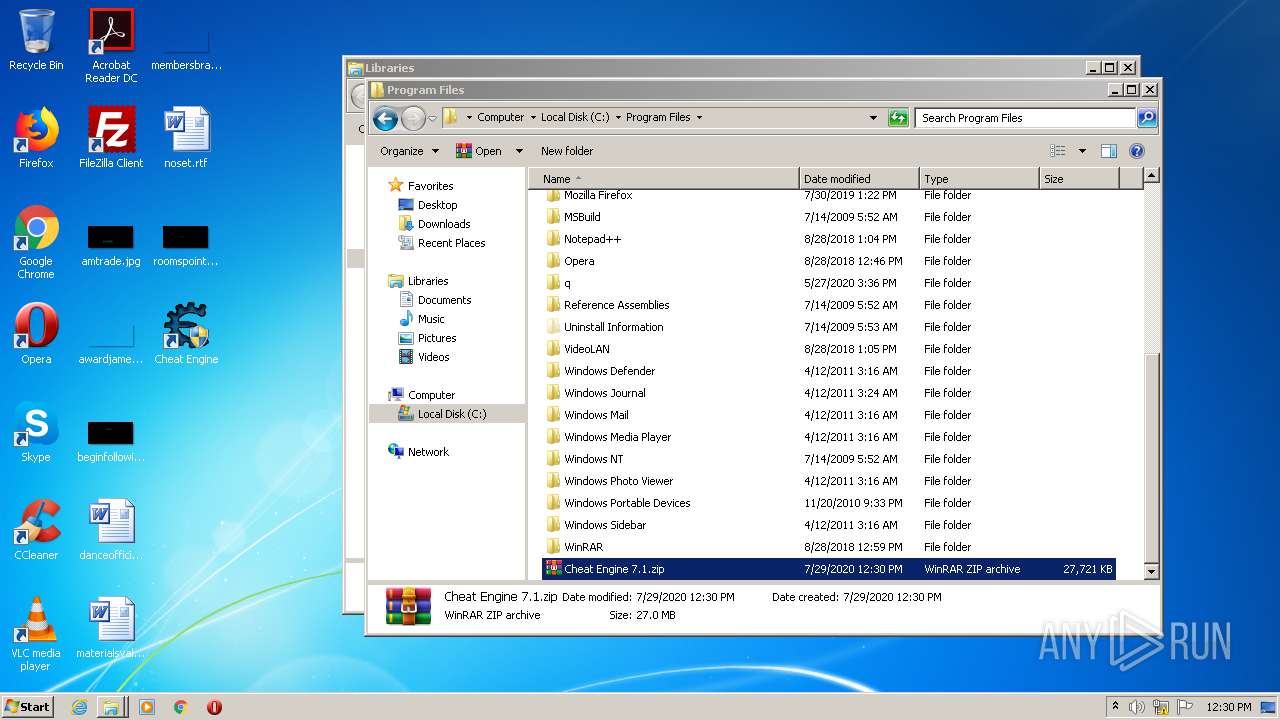
Creates files in the program directory
- WinRAR.exe (PID: 2308)
Executed via COM
- DllHost.exe (PID: 2600)
INFO
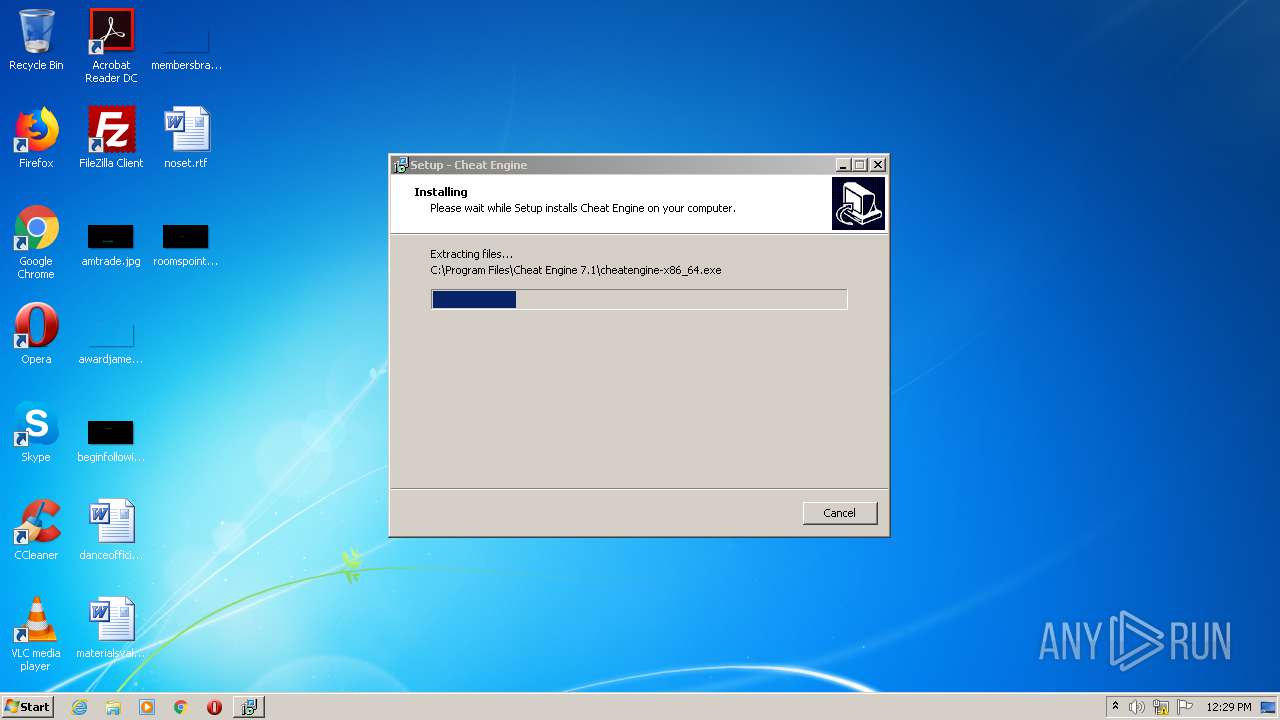
Application was dropped or rewritten from another process
- CheatEngine71.tmp (PID: 3692)
- CheatEngine71.tmp (PID: 3936)
Loads dropped or rewritten executable
- CheatEngine71.tmp (PID: 3936)
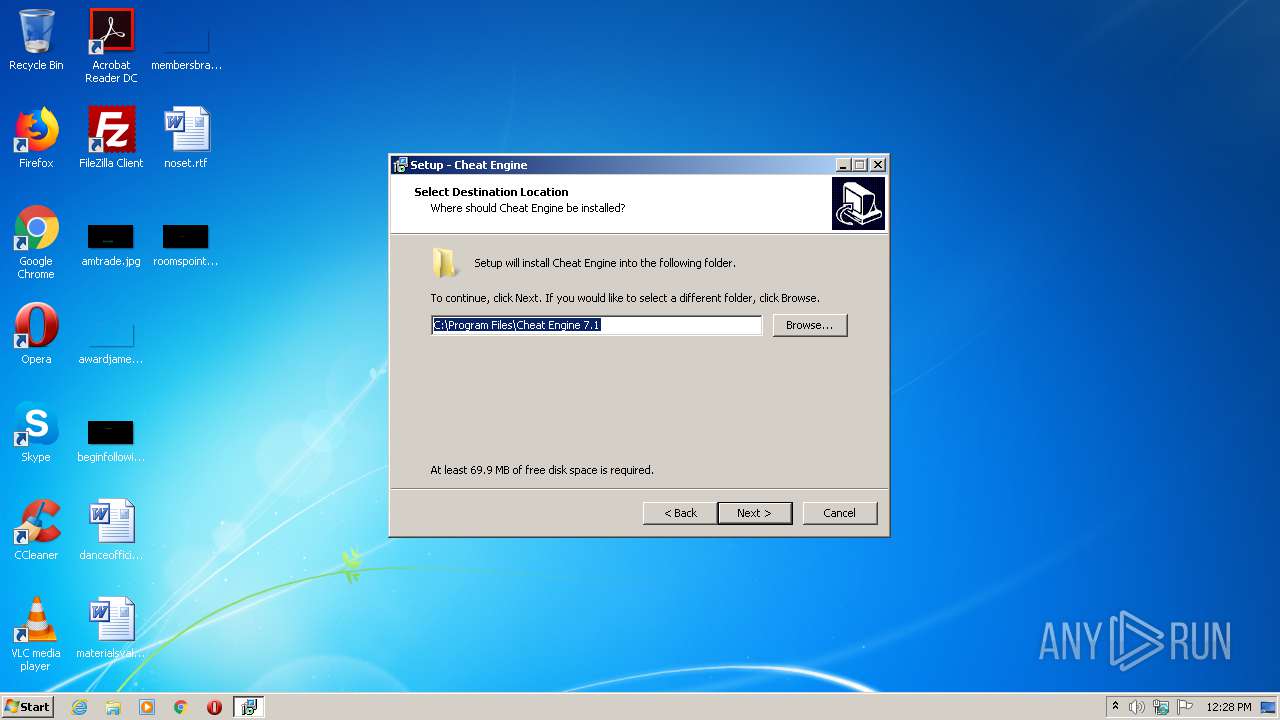
Creates a software uninstall entry
- CheatEngine71.tmp (PID: 3936)
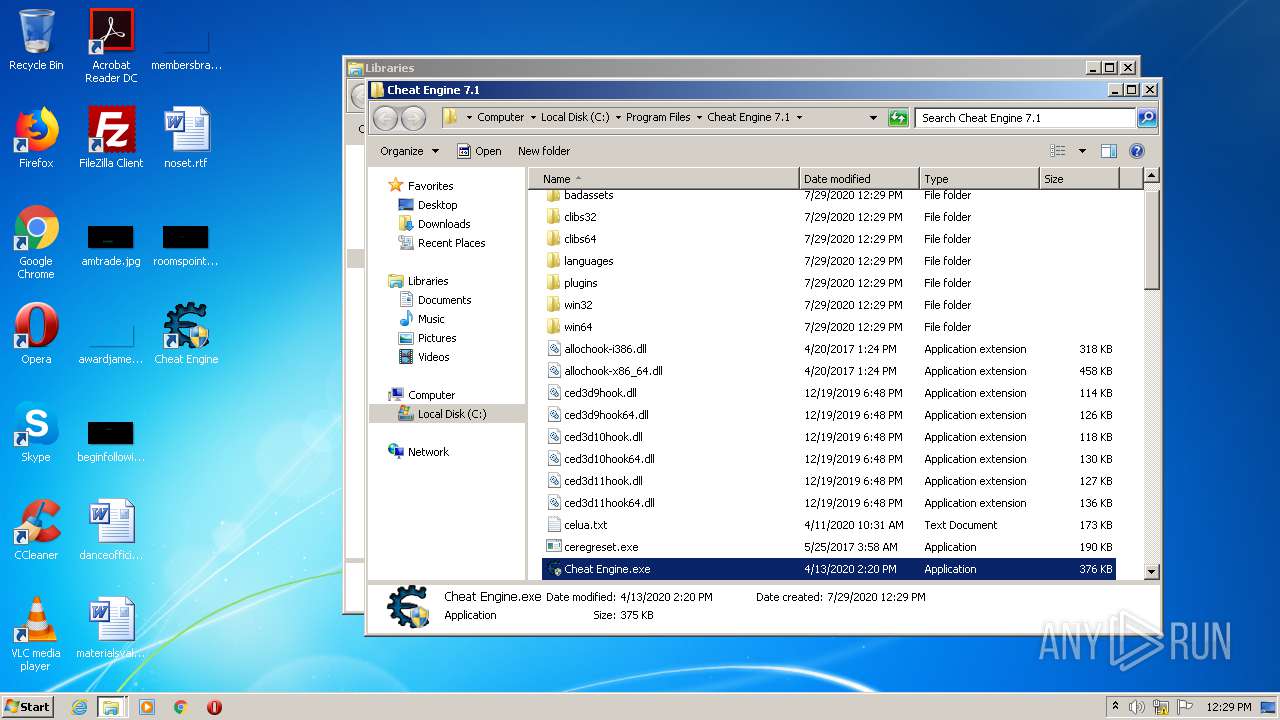
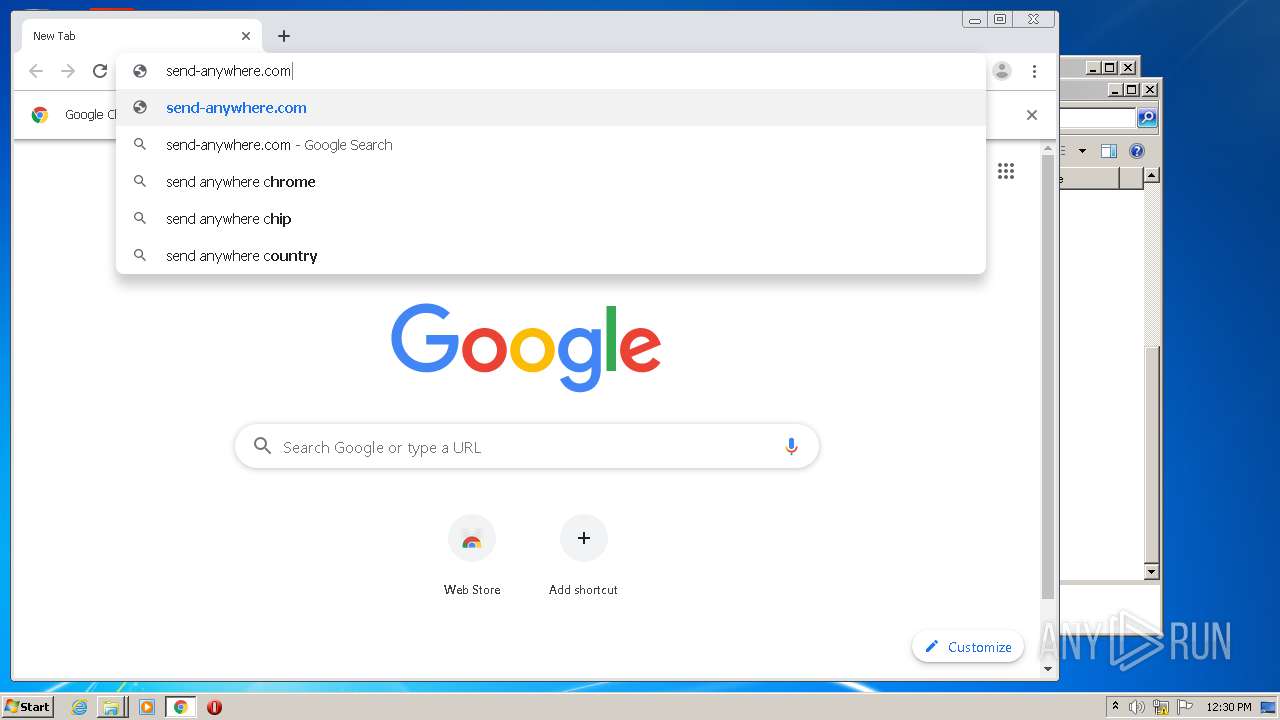
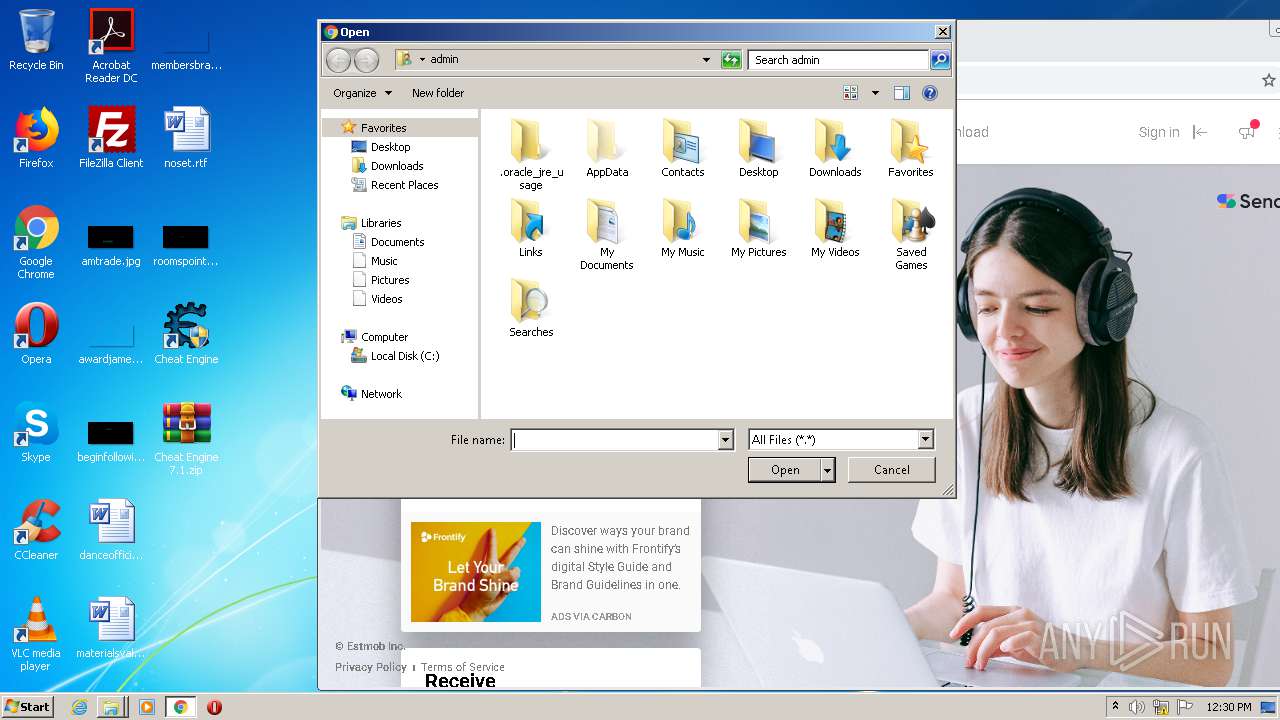
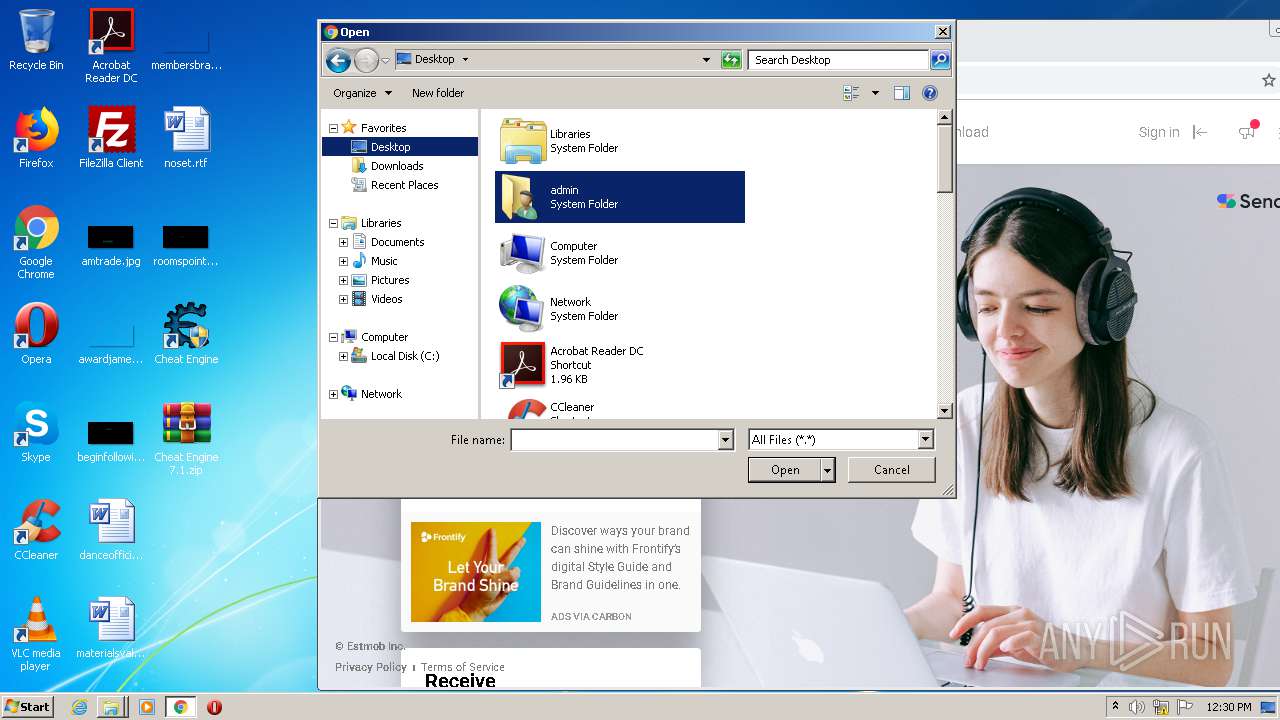
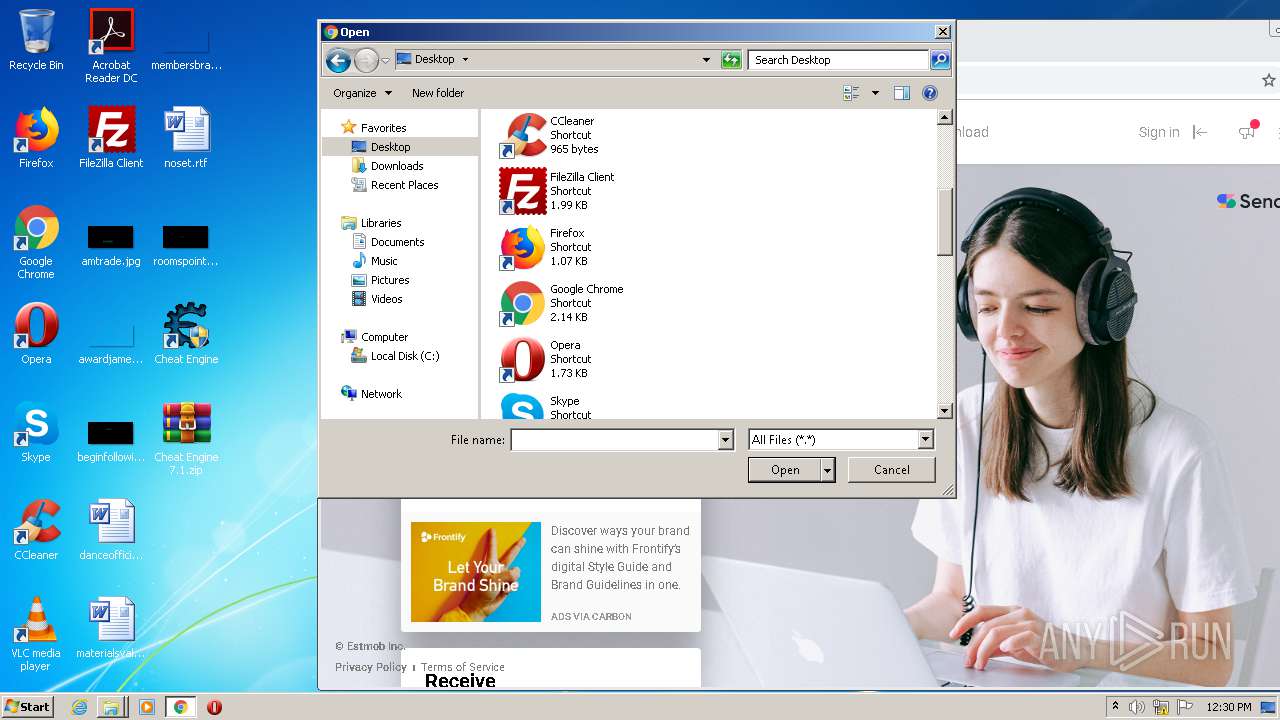
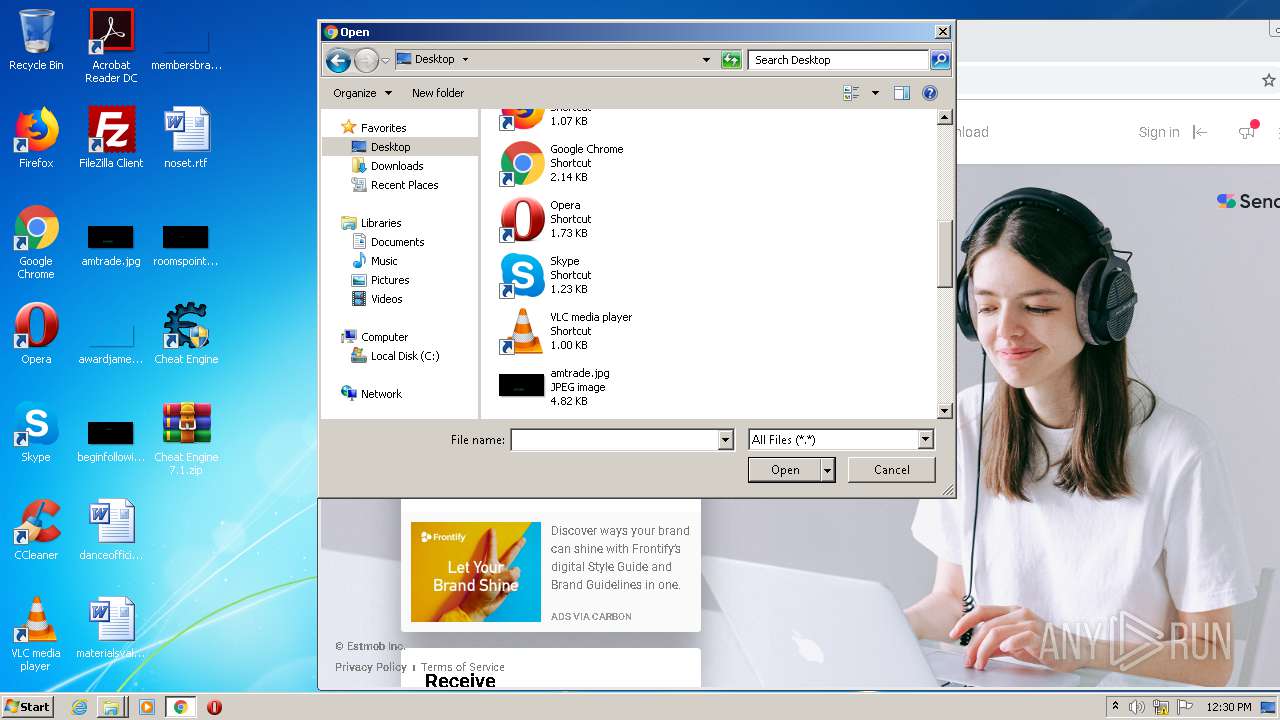
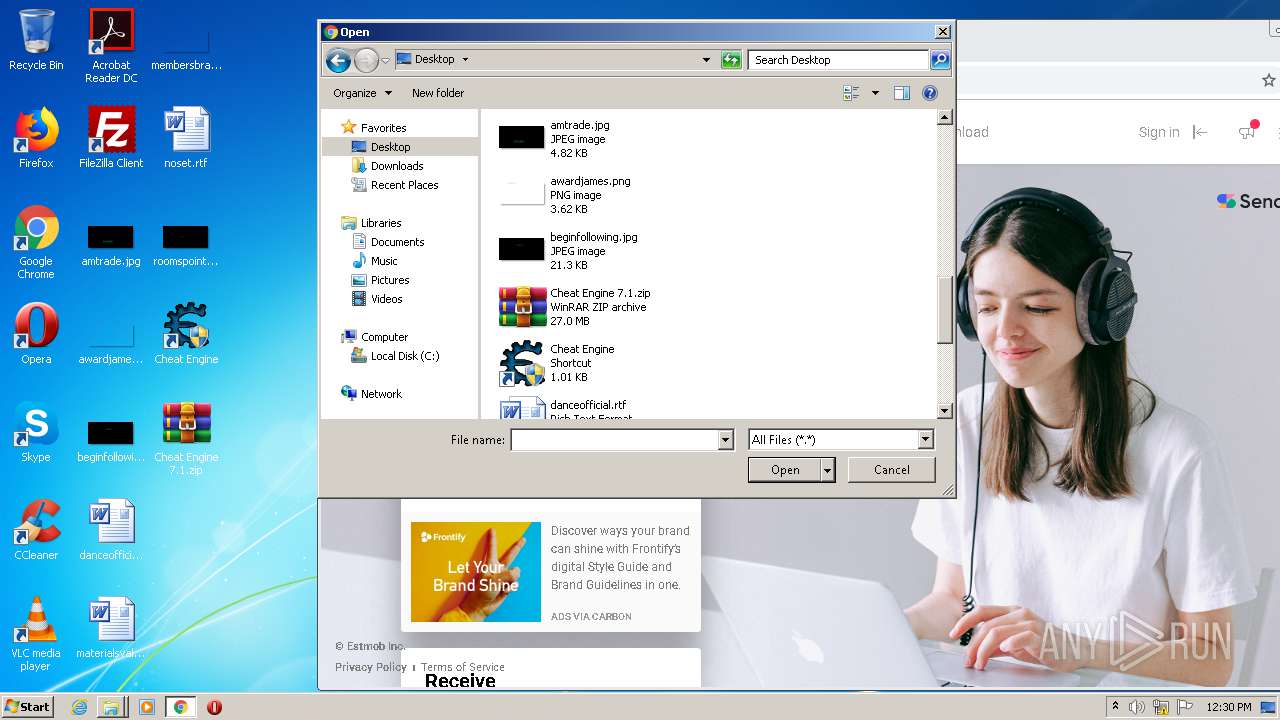
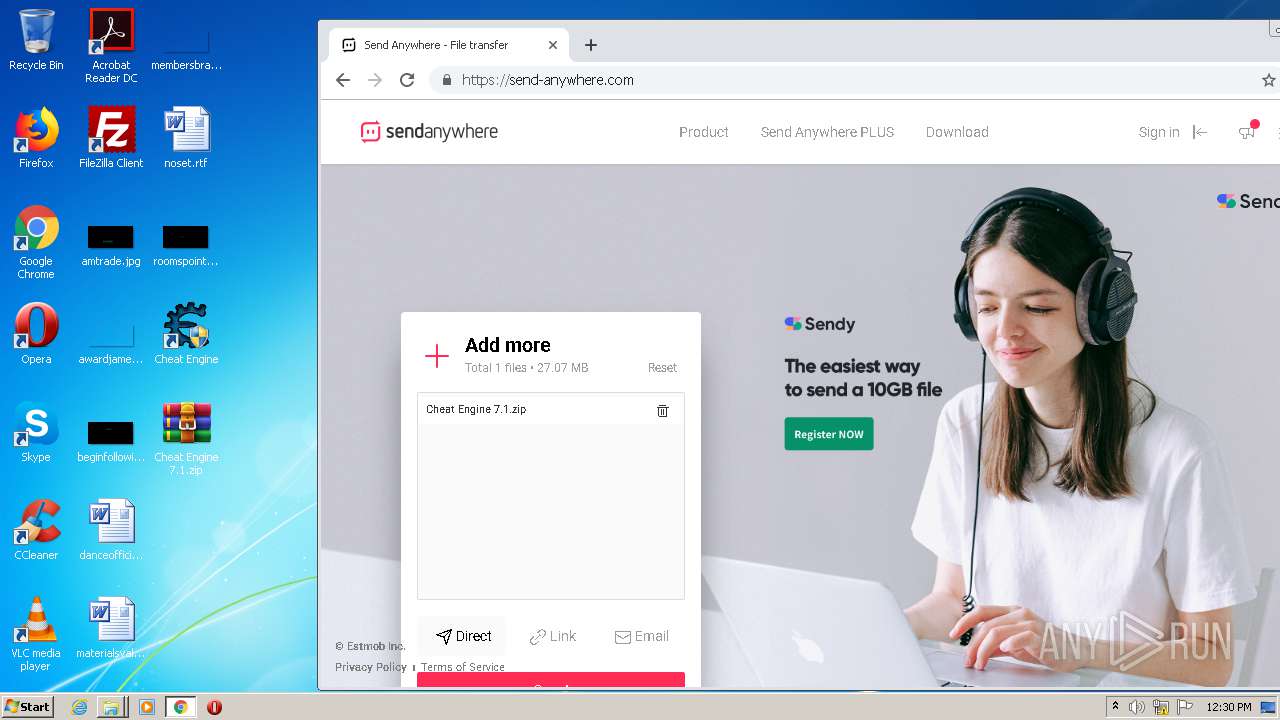
Manual execution by user
- explorer.exe (PID: 1832)
- WinRAR.exe (PID: 900)
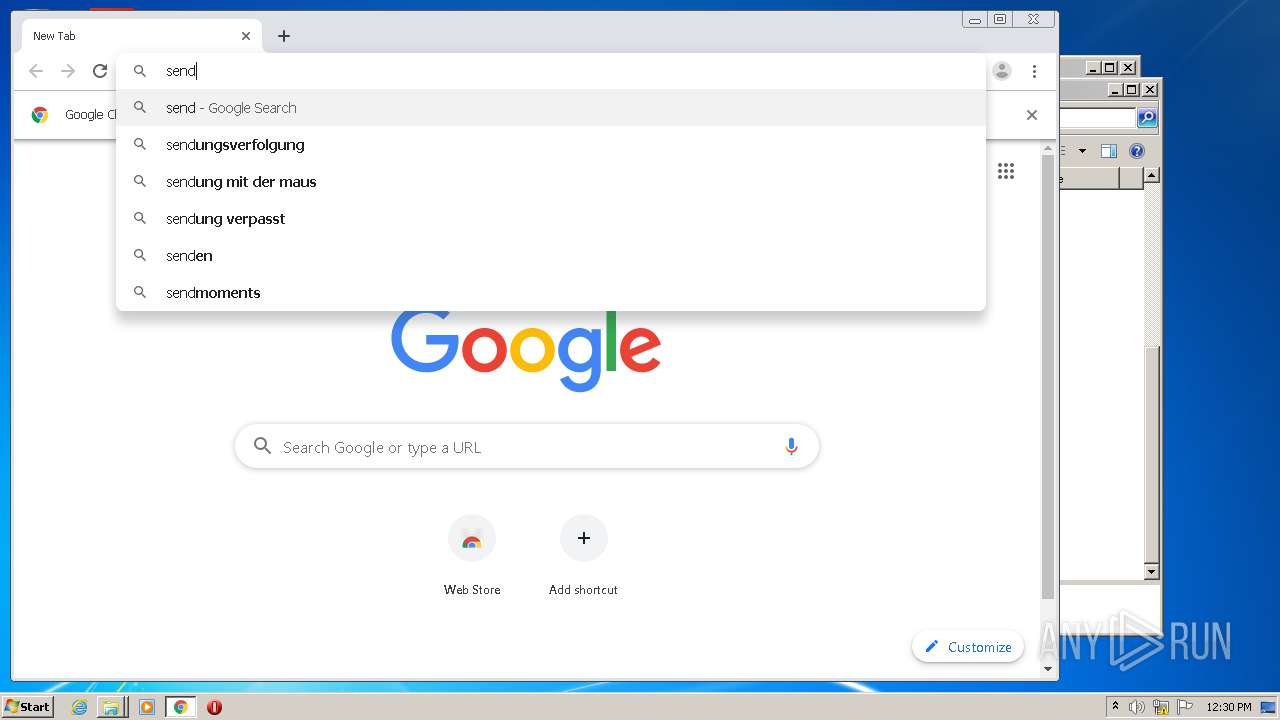
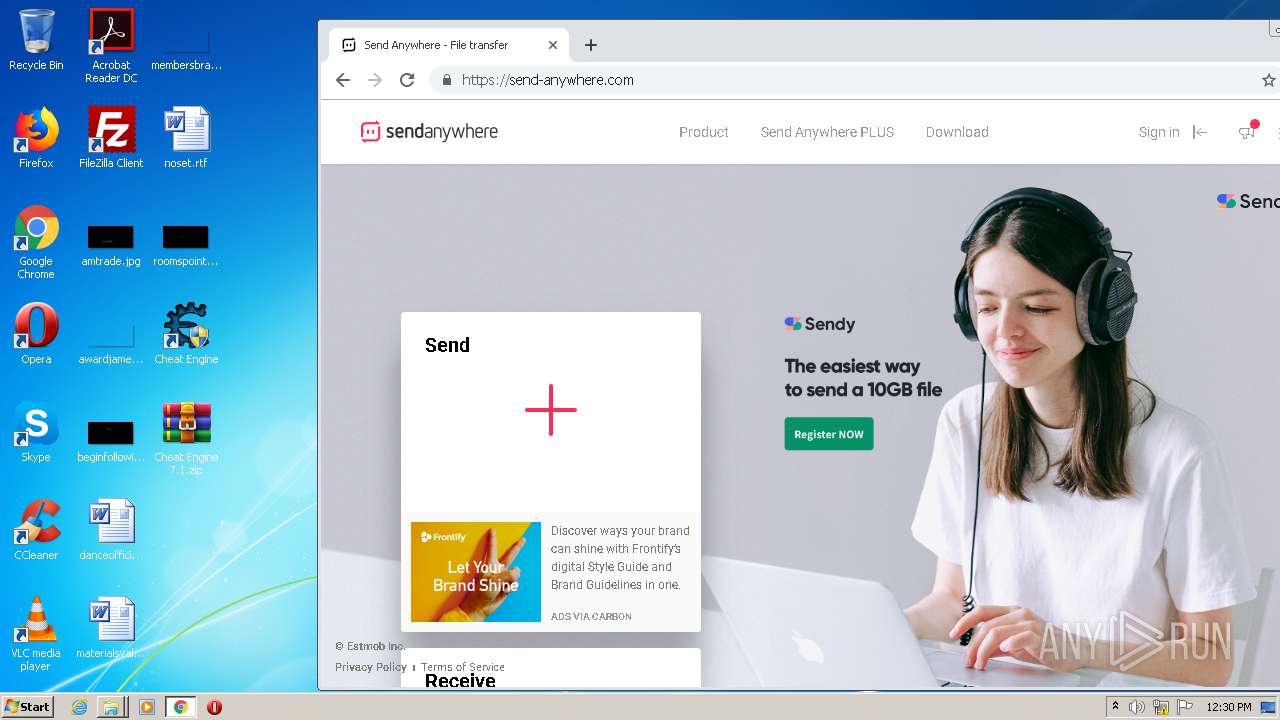
- chrome.exe (PID: 1856)
Application launched itself
- chrome.exe (PID: 1856)
Reads the hosts file
- chrome.exe (PID: 1856)
- chrome.exe (PID: 1384)
Reads settings of System Certificates
- chrome.exe (PID: 1384)
Creates files in the program directory
- CheatEngine71.tmp (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.1.0.10 |
| ProductVersionNumber: | 7.1.0.10 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
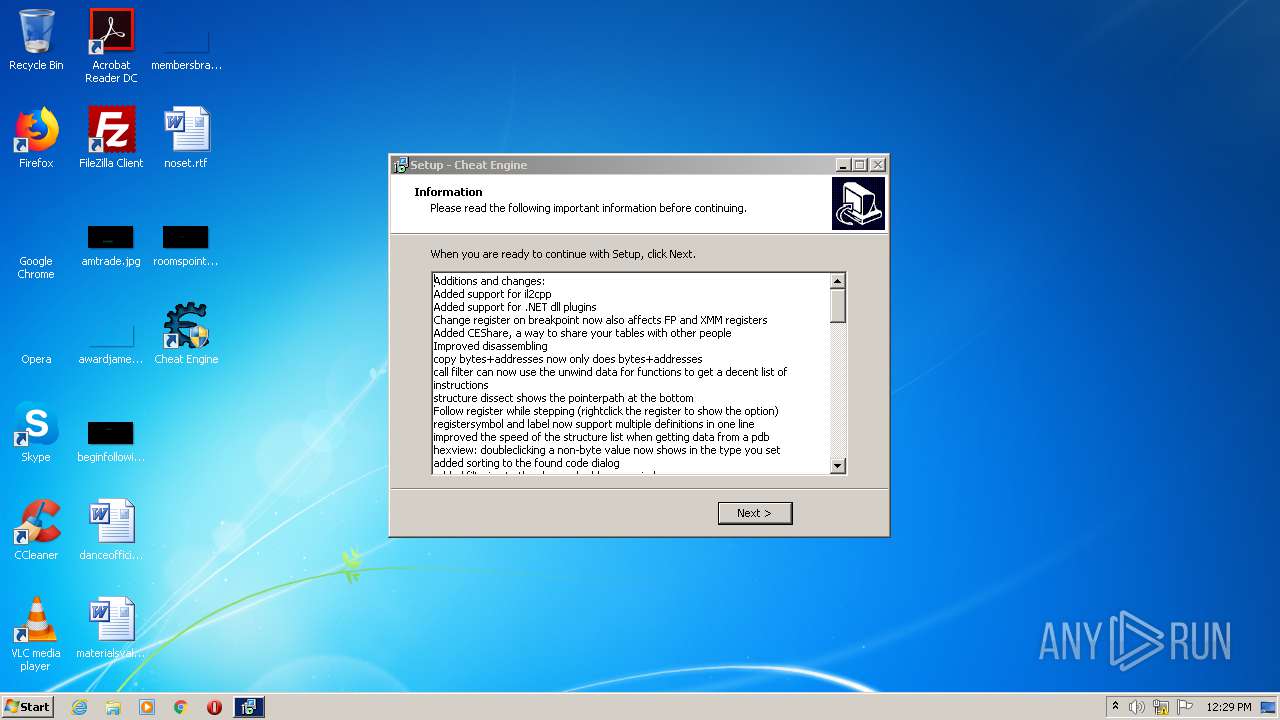
| CompanyName: | Cheat Engine |
| FileDescription: | Cheat Engine Setup |
| FileVersion: | 7.1.0.10 |
| LegalCopyright: | Cheat Engine |
| ProductName: | Cheat Engine |
| ProductVersion: | 7.1.0.10 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Cheat Engine |
| FileDescription: | Cheat Engine Setup |
| FileVersion: | 7.1.0.10 |
| LegalCopyright: | Cheat Engine |
| ProductName: | Cheat Engine |
| ProductVersion: | 7.1.0.10 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14445 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
87
Monitored processes
37
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13528915418529147622 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12311893138563876769 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11131298272892801098 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13512056484952542168 --mojo-platform-channel-handle=1300 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\WinRAR\WinRAR.exe" a -ep1 -scul -r0 -iext -- . "C:\Program Files\Cheat Engine 7.1" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17052202591355002041 --mojo-platform-channel-handle=2996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11418448486303827636 --mojo-platform-channel-handle=2616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1724 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15403302743646631863 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11060860665106066358,18137325191255028974,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17059029295845262468 --mojo-platform-channel-handle=3588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 447
Read events
2 201
Write events
234
Delete events
12
Modification events
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 600F000092D3966B9B65D601 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A511FF3ABFC957F4A2CBA3F52C31119BCCF895B0451617A15820D0CC801E14D5 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3936) CheatEngine71.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
61
Suspicious files
81
Text files
301
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\000D9EE0.log | — | |
MD5:— | SHA256:— | |||
| 3028 | CheatEngine71.exe | C:\Users\admin\AppData\Local\Temp\is-C7GIS.tmp\CheatEngine71.tmp | executable | |
MD5:— | SHA256:— | |||
| 2624 | CheatEngine71.exe | C:\Users\admin\AppData\Local\Temp\is-60H19.tmp\CheatEngine71.tmp | executable | |
MD5:— | SHA256:— | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\is-LCV56.tmp\gvkyvdmf.dll | executable | |
MD5:— | SHA256:— | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\sdk-ui\button.css | text | |
MD5:37E1FF96E084EC201F0D95FEEF4D5E94 | SHA256:8E806F5B94FC294E918503C8053EF1284E4F4B1E02C7DA4F4635E33EC33E0534 | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\ie6_main.css | text | |
MD5:74F08D5A243AE79F1DE64DFFDAF846CB | SHA256:15590060BFD227F656E569031113A080E0D45621A5C944DFC352F869EADAFEF2 | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\sdk-ui\progress-bar.css | text | |
MD5:5335F1C12201B5F7CF5F8B4F5692E3D1 | SHA256:974CD89E64BDAA85BF36ED2A50AF266D245D781A8139F5B45D7C55A0B0841DDA | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\main.css | text | |
MD5:9B27E2A266FE15A3AABFE635C29E8923 | SHA256:166AA42BC5216C5791388847AE114EC0671A0D97B9952D14F29419B8BE3FB23F | |||
| 3936 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\nsd89264038463\css\sdk-ui\images\button-bg.png | image | |
MD5:98B1DE48DFA64DC2AA1E52FACFBEE3B0 | SHA256:2693930C474FE640E2FE8D6EF98ABE2ECD303D2392C3D8B2E006E8942BA8F534 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
61
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
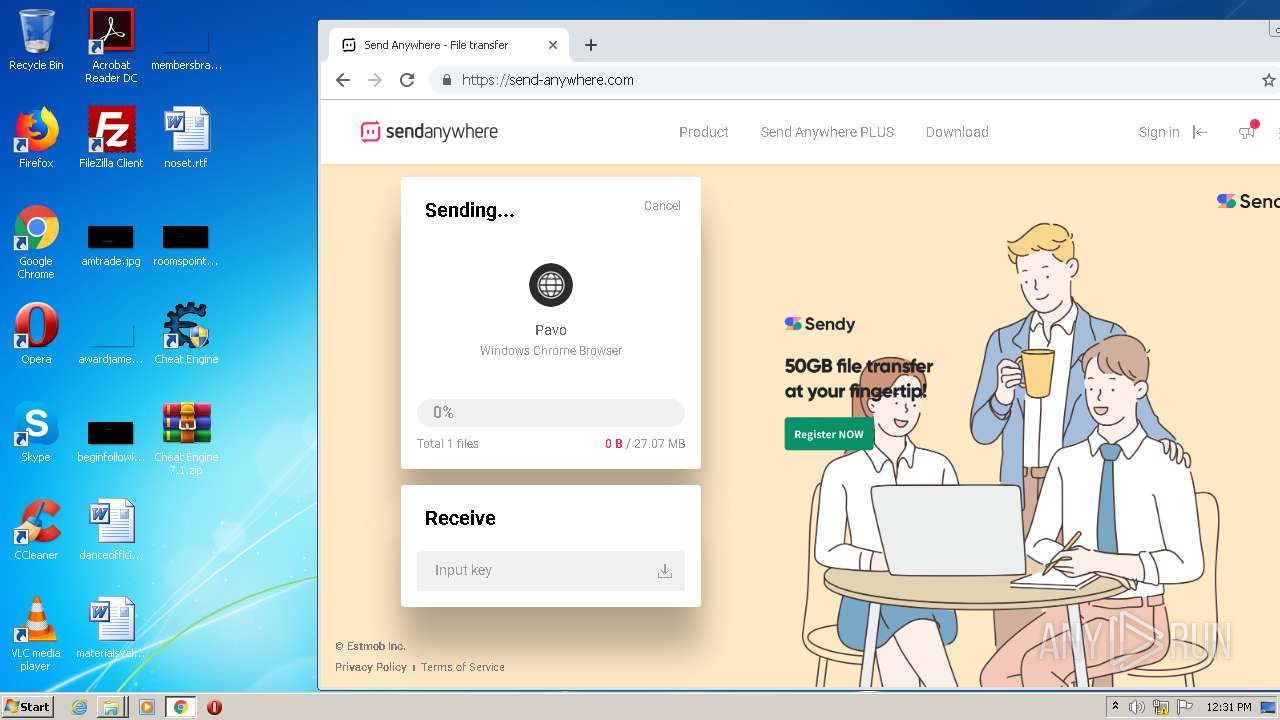
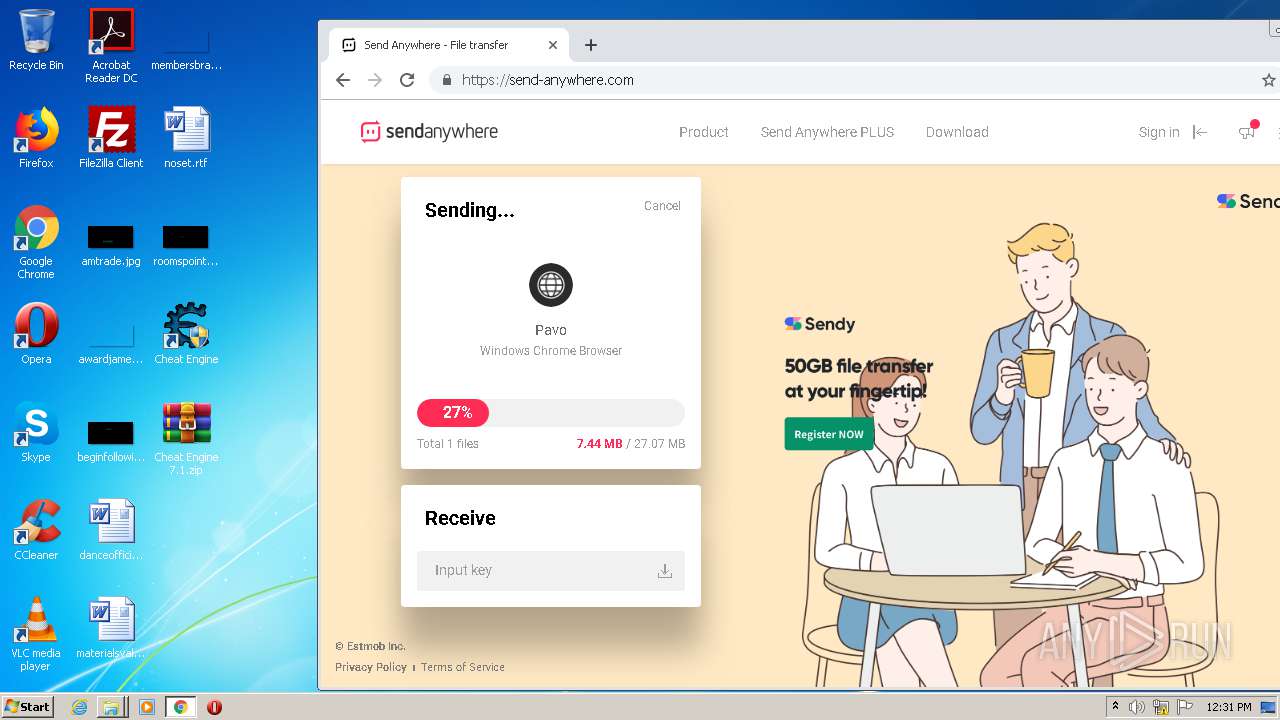
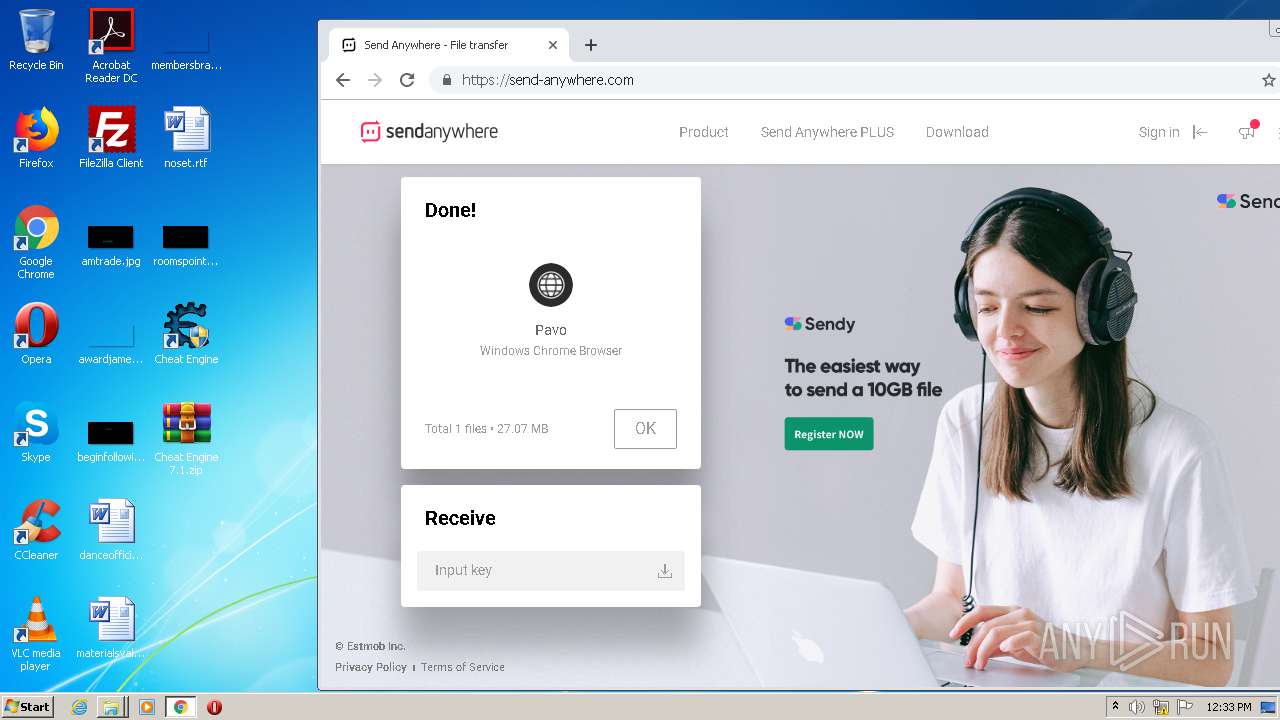
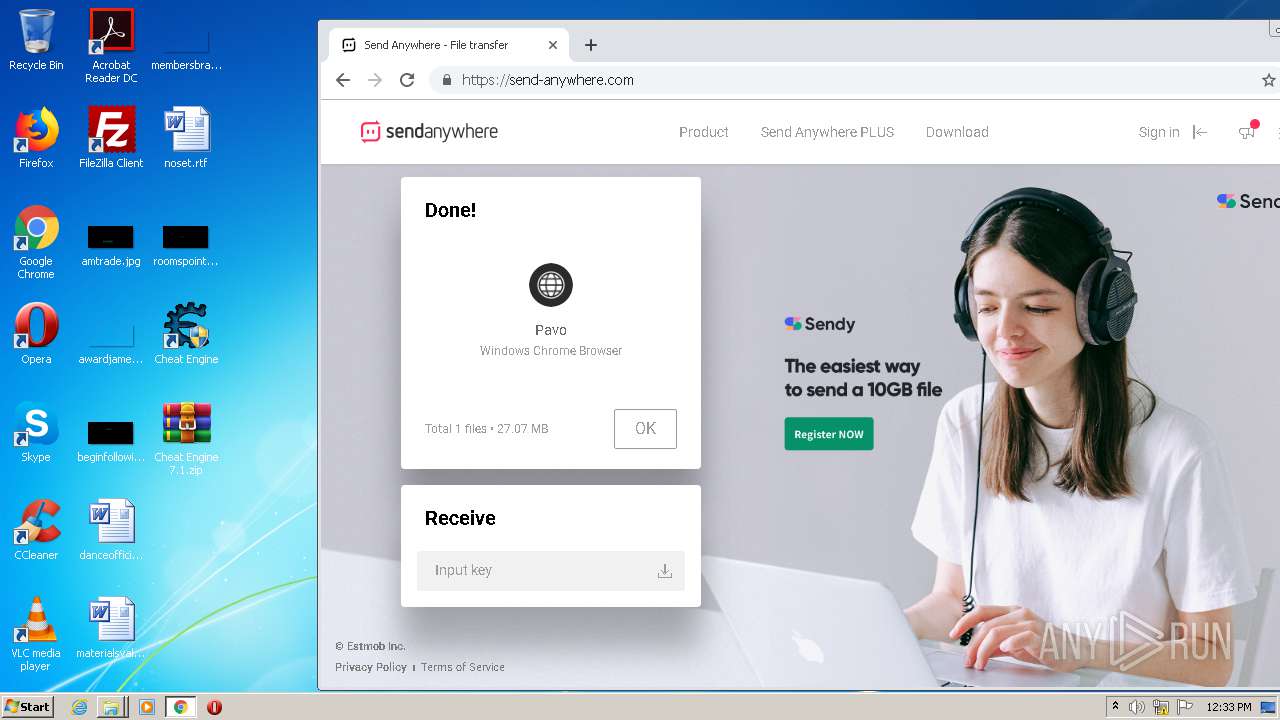
3936 | CheatEngine71.tmp | POST | 200 | 143.204.202.51:80 | http://apps.wayirrsscafece.com/ | US | — | — | malicious |
3936 | CheatEngine71.tmp | POST | 200 | 143.204.202.47:80 | http://live.wayirrsscafece.com/ | US | binary | 915 Kb | malicious |
1384 | chrome.exe | GET | 200 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
1384 | chrome.exe | GET | 304 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
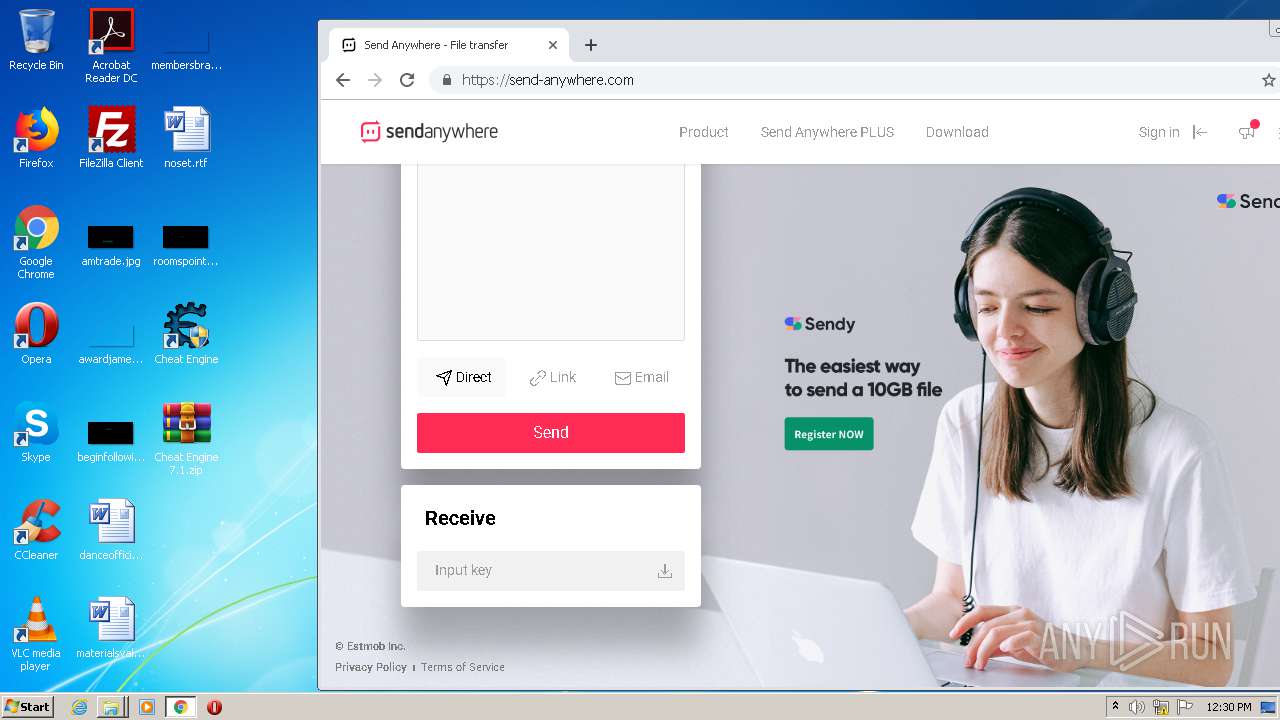
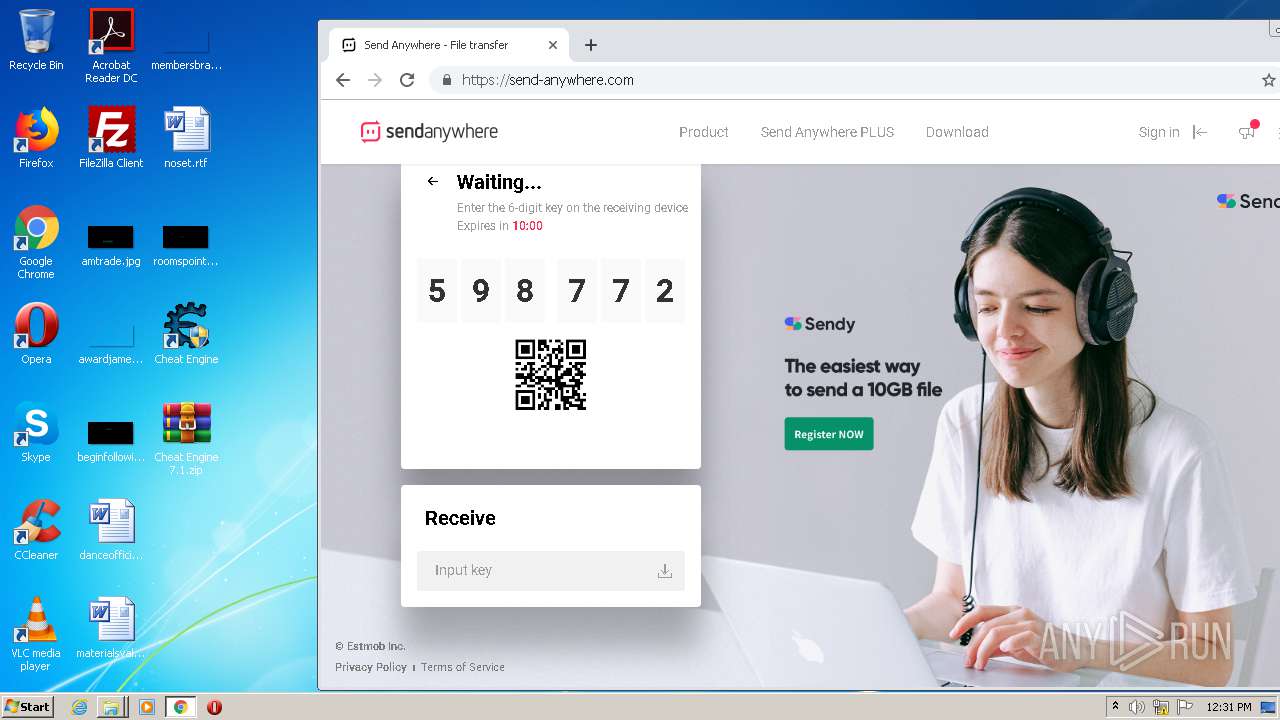
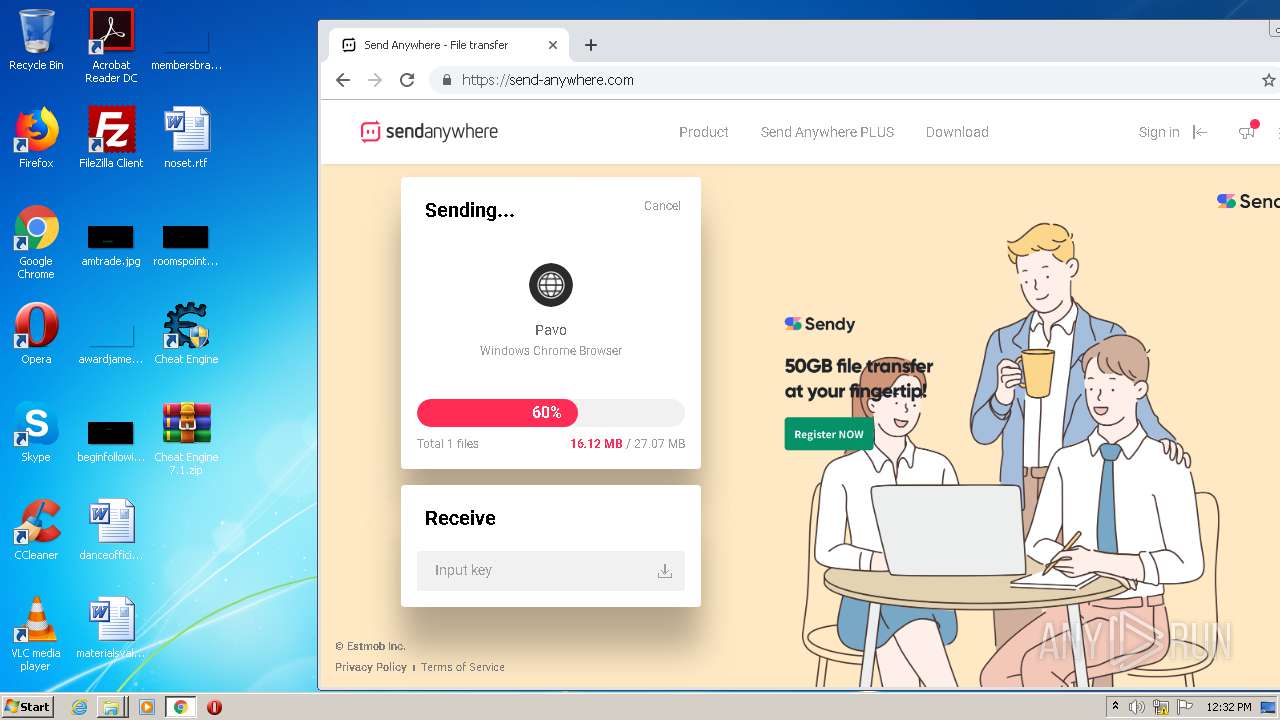
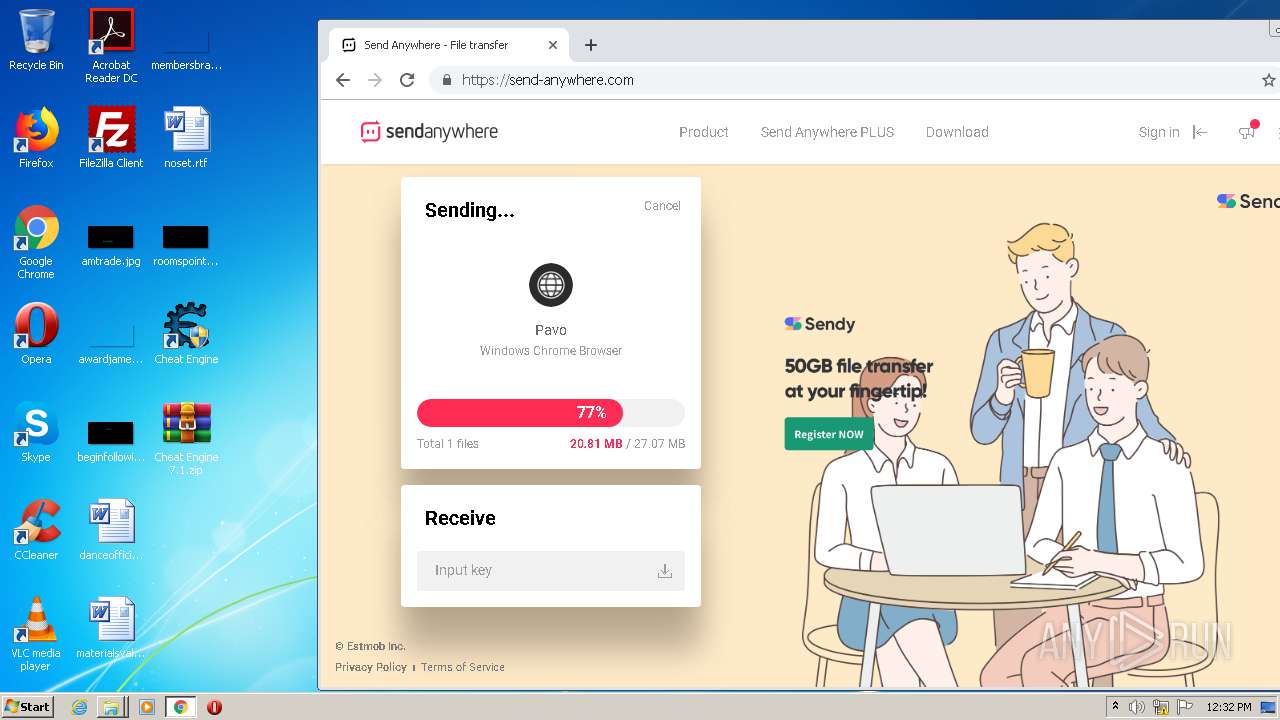
1384 | chrome.exe | GET | 301 | 143.204.202.80:80 | http://send-anywhere.com/ | US | html | 183 b | whitelisted |
1384 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1384 | chrome.exe | GET | 304 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3936 | CheatEngine71.tmp | 143.204.202.34:80 | apps.wayirrsscafece.com | — | US | malicious |
3936 | CheatEngine71.tmp | 143.204.202.51:80 | apps.wayirrsscafece.com | — | US | suspicious |
3936 | CheatEngine71.tmp | 143.204.202.47:80 | live.wayirrsscafece.com | — | US | suspicious |
1384 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 172.217.23.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1384 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
apps.wayirrsscafece.com |
| malicious |
live.wayirrsscafece.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Kernelmoduleunloader.exe | Setup. So do not show messages |
Kernelmoduleunloader.exe | setup=true |
Kernelmoduleunloader.exe | Kernelmodule unloader |
Kernelmoduleunloader.exe | SCManager opened |
Kernelmoduleunloader.exe | setup=true |
Kernelmoduleunloader.exe | attempting to unload |