| File name: | KMSPico.exe |
| Full analysis: | https://app.any.run/tasks/5b340c66-ead9-4693-9350-01128b7fbe6c |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2024, 03:21:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FB4FDEFE65C7B05021C2EF1D64B182CA |
| SHA1: | D11112050743E37B2D2FA1D51EAACDACA817B580 |
| SHA256: | DAB49C11D4F14E2643A5FFBB93C86D45B53D6129154253AB5B94680EFBB7FE4B |
| SSDEEP: | 98304:Erq3BdwQnppTYtlExWP5rU7az9zy0Lg5BJItCfDjWlDiPwOA+M5kStlUI2TzPTK8:gCmLKCEnckUvYcM5 |
MALICIOUS
Changes image file execution options
- KMSELDI.exe (PID: 460)
SUSPICIOUS
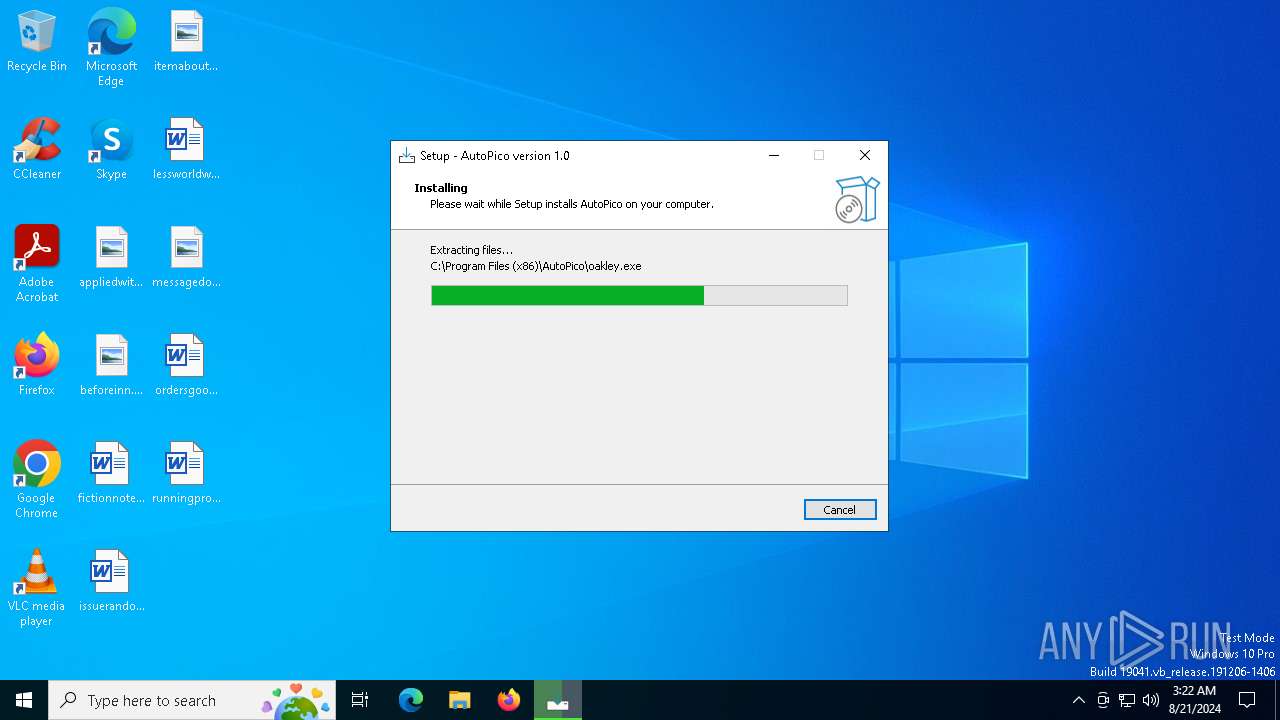
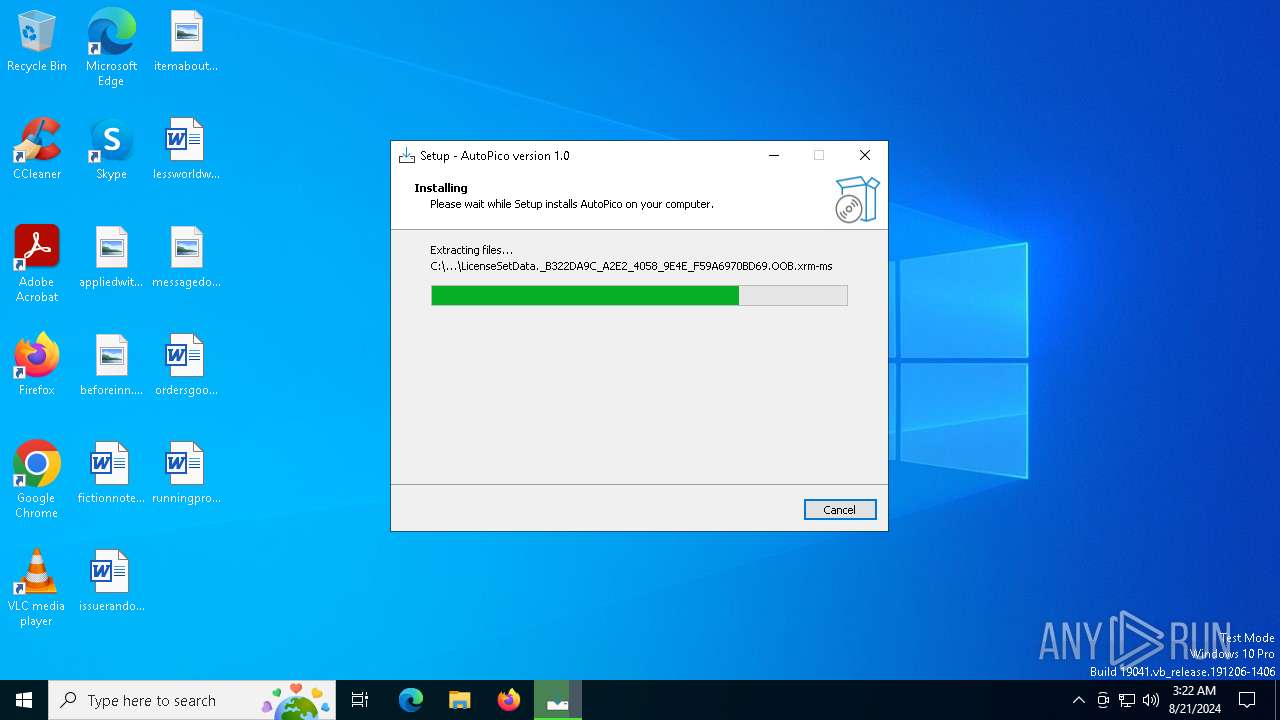
Drops the executable file immediately after the start
- KMSPico.exe (PID: 6668)
- KMSPico.tmp (PID: 6700)
- KMSELDI.exe (PID: 460)
Executable content was dropped or overwritten
- KMSPico.exe (PID: 6668)
- KMSPico.tmp (PID: 6700)
- KMSELDI.exe (PID: 460)
Reads the Windows owner or organization settings
- KMSPico.tmp (PID: 6700)
INFO
Create files in a temporary directory
- KMSPico.exe (PID: 6668)
- KMSPico.tmp (PID: 6700)
Reads Environment values
- KMSPico.exe (PID: 6668)
- KMSPico.tmp (PID: 6700)
- KMSELDI.exe (PID: 460)
Checks supported languages
- KMSPico.tmp (PID: 6700)
- KMSELDI.exe (PID: 460)
- KMSPico.exe (PID: 6668)
- oakley.exe (PID: 3028)
Reads the computer name
- KMSPico.exe (PID: 6668)
- KMSPico.tmp (PID: 6700)
- oakley.exe (PID: 3028)
- KMSELDI.exe (PID: 460)
Creates a software uninstall entry
- KMSPico.tmp (PID: 6700)
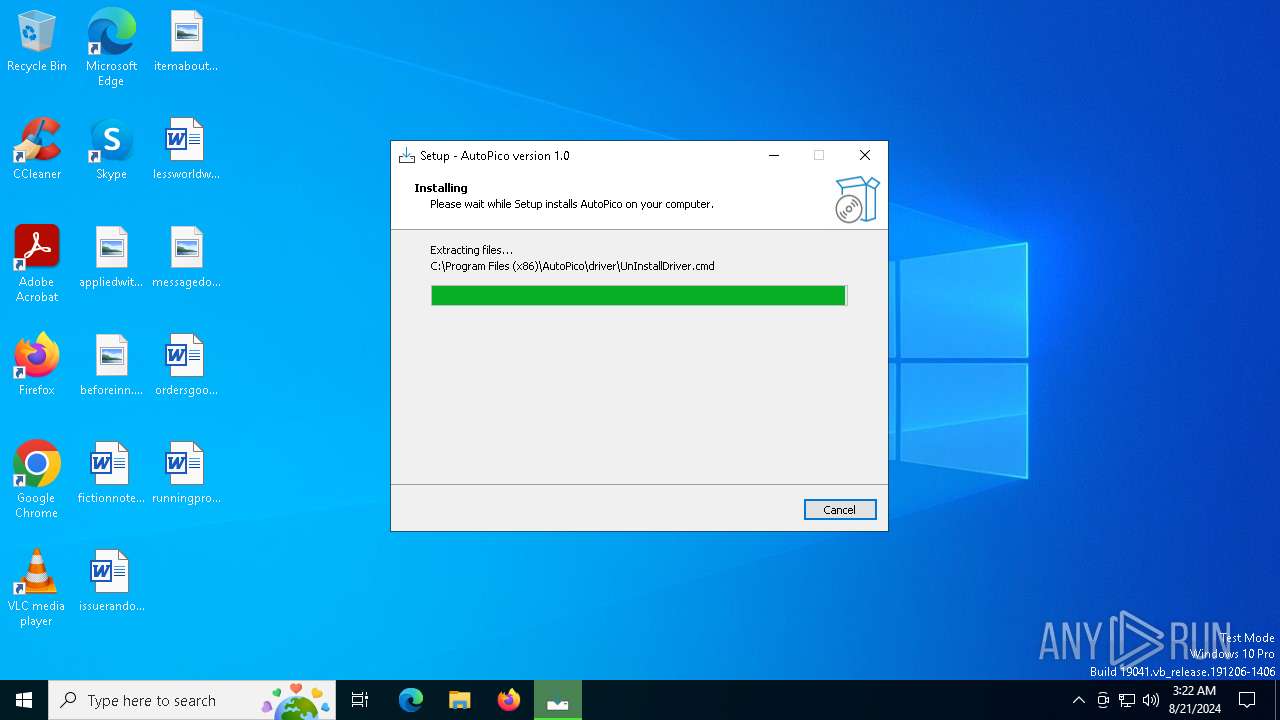
Creates files in the program directory
- KMSPico.tmp (PID: 6700)
- KMSELDI.exe (PID: 460)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 460)
- oakley.exe (PID: 3028)
Reads product name
- KMSELDI.exe (PID: 460)
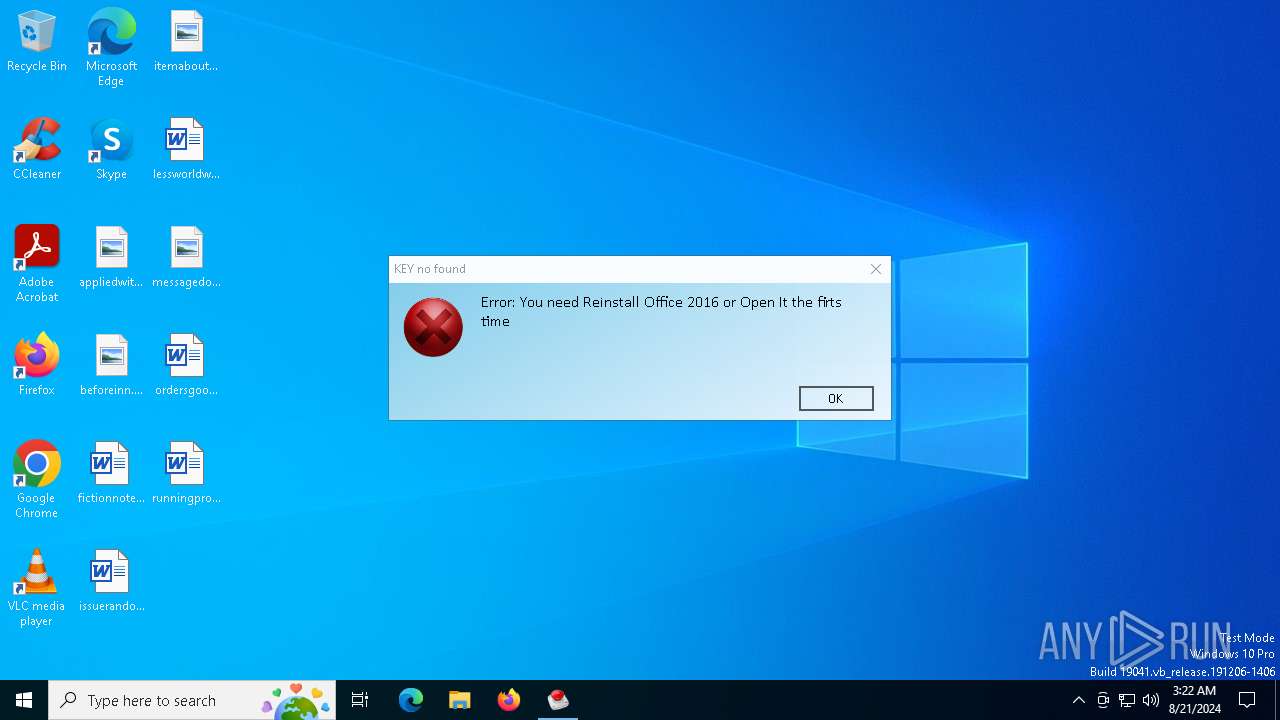
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:12 07:26:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 685056 |
| InitializedDataSize: | 159744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa83bc |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
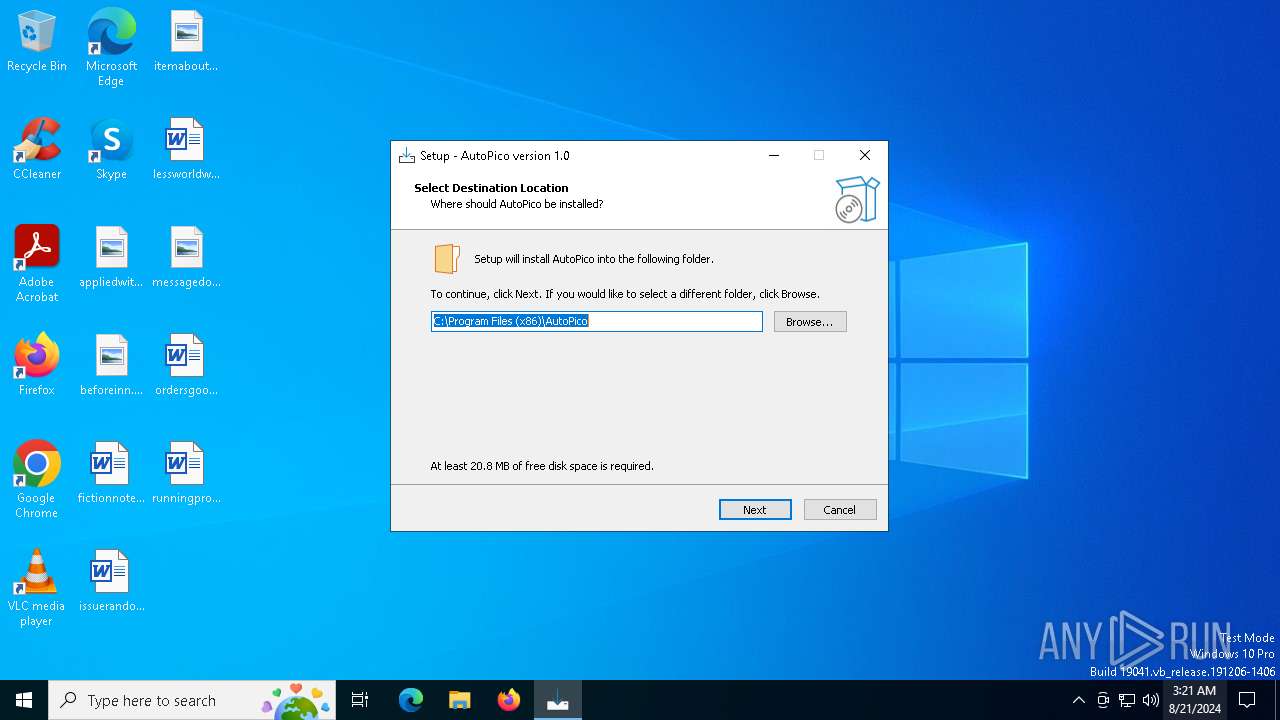
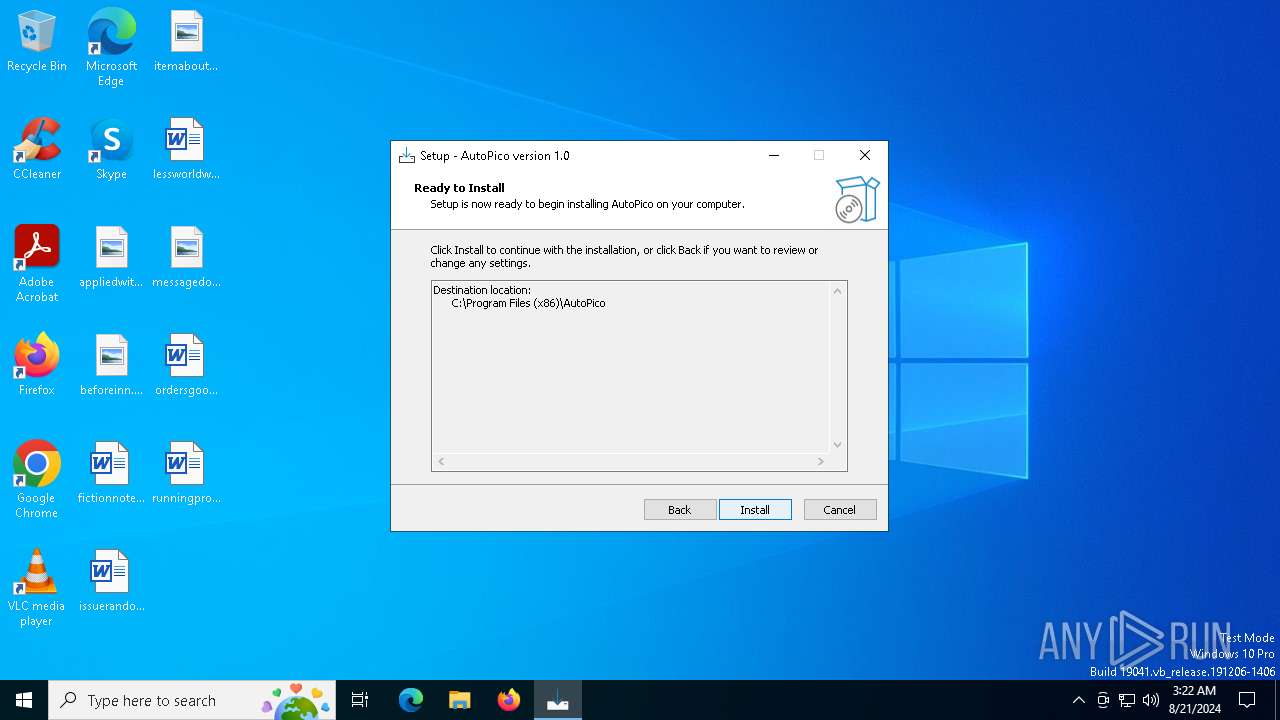
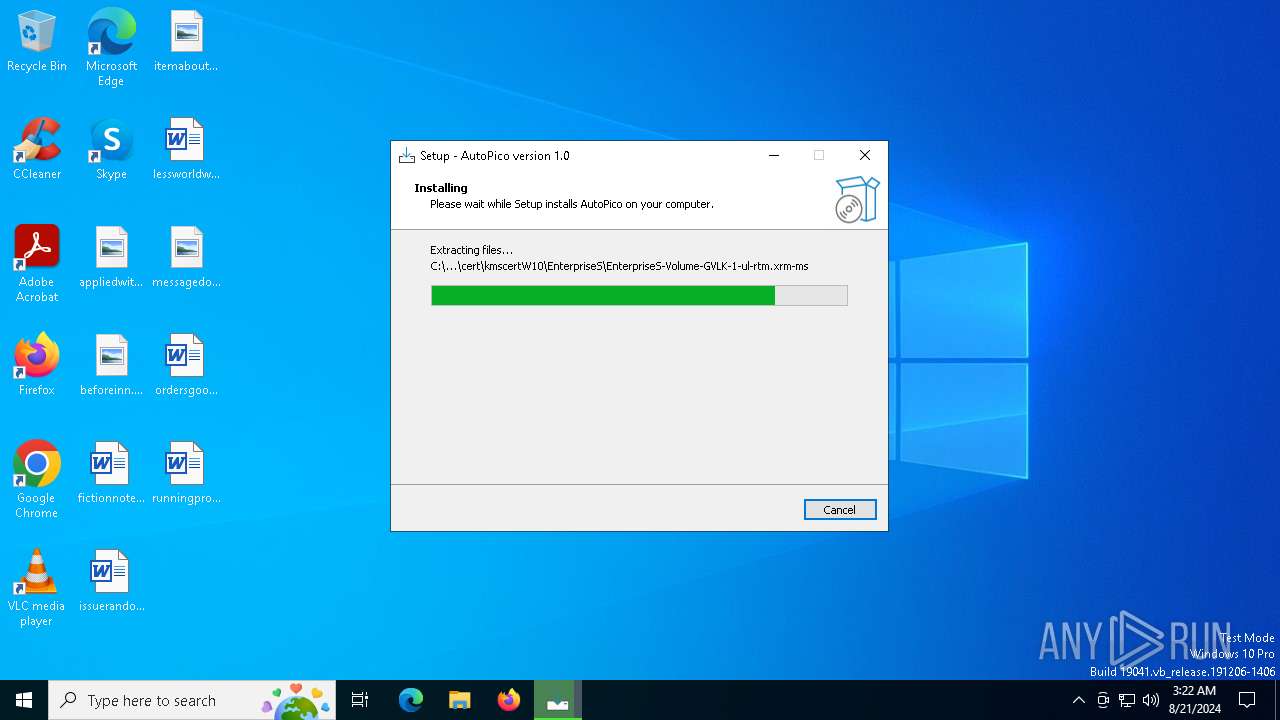
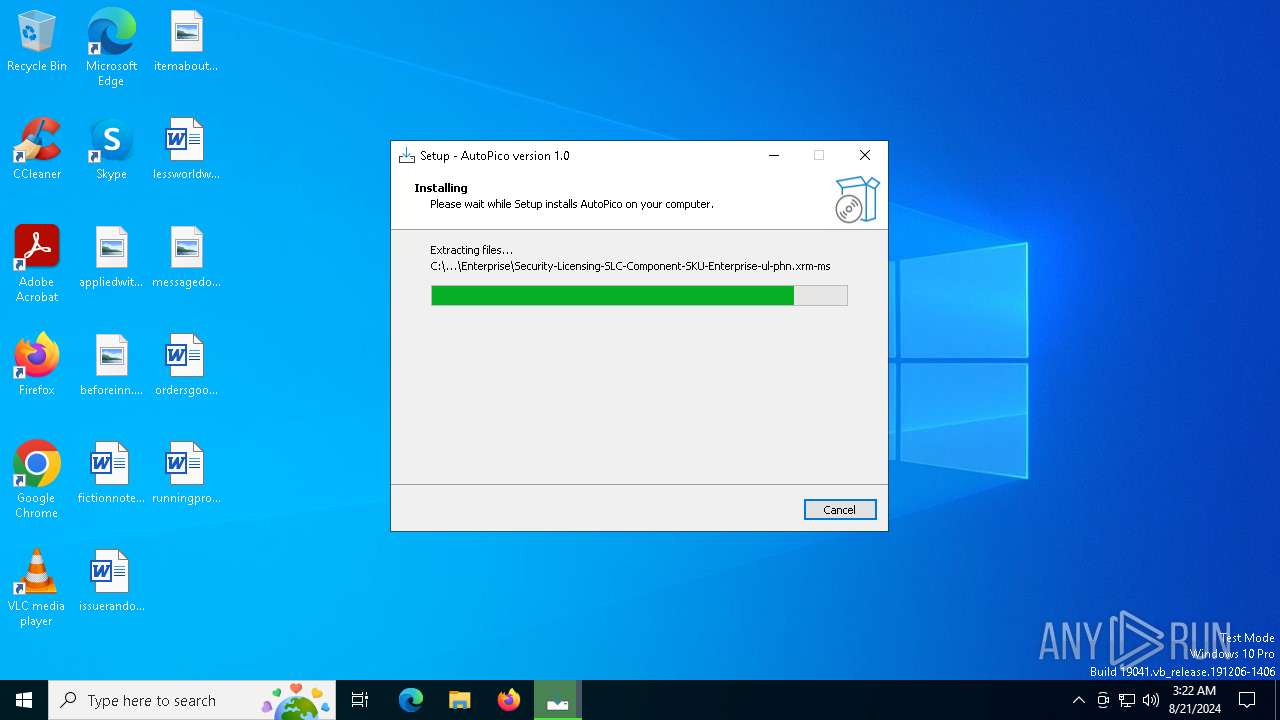
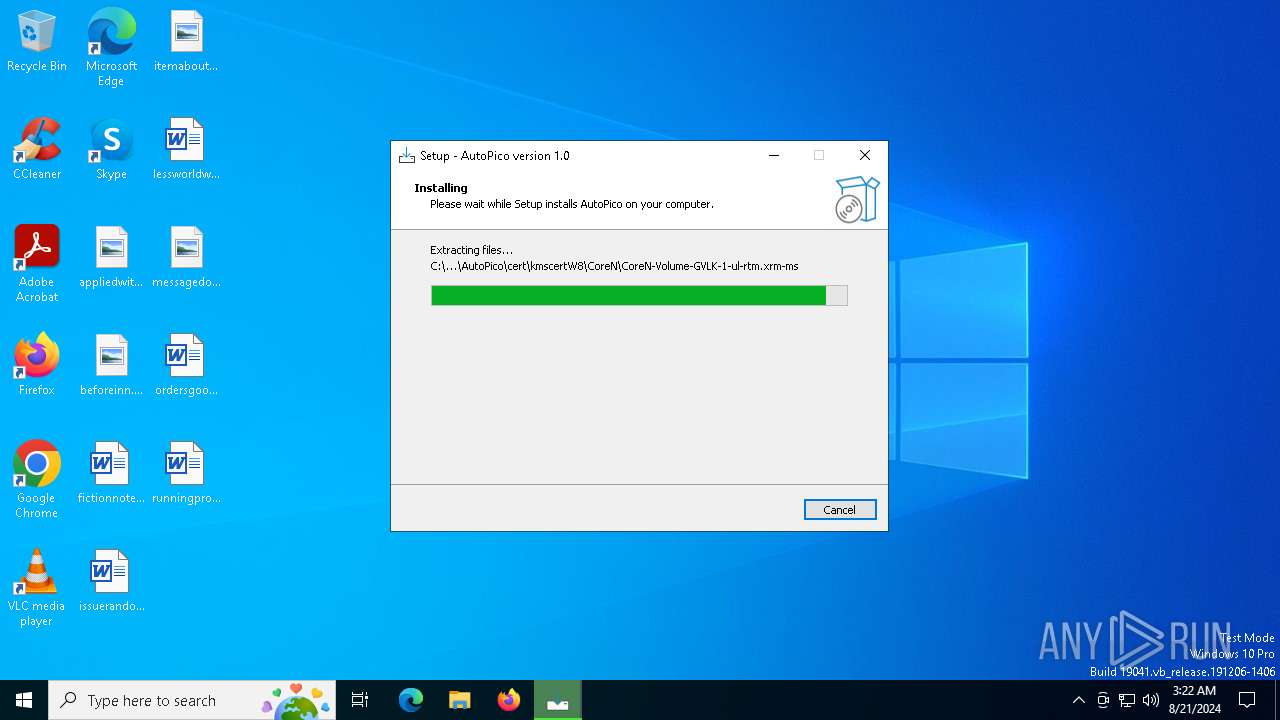
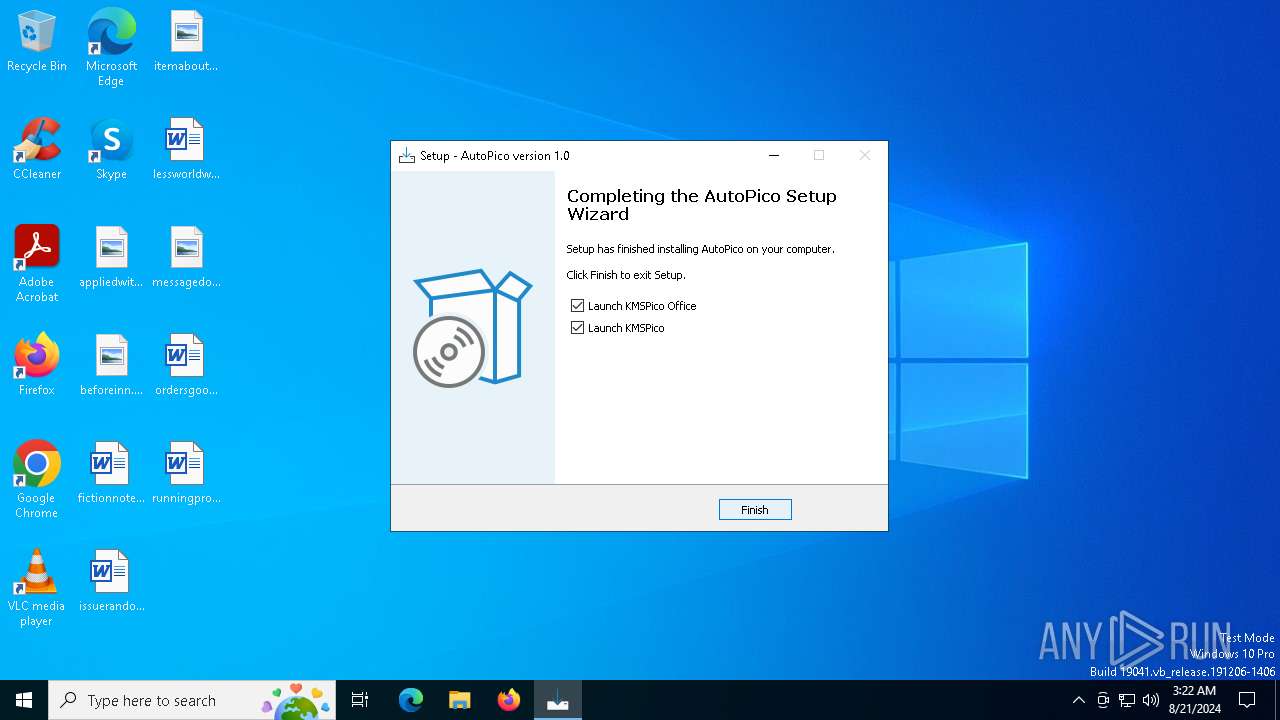
| CompanyName: | AutoPico |
| FileDescription: | AutoPico Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | AutoPico |
| ProductVersion: | 1.0 |
Total processes
139
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 460 | "C:\Program Files (x86)\AutoPico\KMSELDI.exe" | C:\Program Files (x86)\AutoPico\KMSELDI.exe | KMSPico.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Version: 37.1.0.0 Modules
| |||||||||||||||
| 3028 | "C:\Program Files (x86)\AutoPico\oakley.exe" | C:\Program Files (x86)\AutoPico\oakley.exe | — | KMSPico.tmp | |||||||||||
User: admin Company: www.proficad.com Integrity Level: HIGH Description: ProfiCAD - Electrical Software Version: 12.2.3.0 Modules
| |||||||||||||||
| 6572 | "C:\Users\admin\AppData\Local\Temp\KMSPico.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoPico Integrity Level: MEDIUM Description: AutoPico Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 6668 | "C:\Users\admin\AppData\Local\Temp\KMSPico.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico.exe | explorer.exe | ||||||||||||
User: admin Company: AutoPico Integrity Level: HIGH Description: AutoPico Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 6700 | "C:\Users\admin\AppData\Local\Temp\is-FASRV.tmp\KMSPico.tmp" /SL5="$602F2,5347198,845824,C:\Users\admin\AppData\Local\Temp\KMSPico.exe" | C:\Users\admin\AppData\Local\Temp\is-FASRV.tmp\KMSPico.tmp | KMSPico.exe | ||||||||||||
User: admin Company: AutoPico Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
4 667
Read events
4 588
Write events
72
Delete events
7
Modification events
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 2C1A000011AEC14379F3DA01 | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 5BD1114927EC8100D93A03961F98B5C3FF8EB910D05EFAEC7CF673C1E8109786 | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files (x86)\AutoPico\AutoPico.exe | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: A9B34D3799775FAFB6A1EAA61F66DE2445DB487C7ED10D29C0F163E7CC29C11E | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\AutoPico_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.3.3 | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\AutoPico_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\AutoPico | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\AutoPico_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\AutoPico\ | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\AutoPico_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (6700) KMSPico.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\AutoPico_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
18
Suspicious files
25
Text files
689
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\is-GMTQ4.tmp | executable | |
MD5:8E34C5942B6D976A0B6ADE26C07D5FA3 | SHA256:C5AF0E9D4BD80FBA2CFB9B9E22CD055785F2561C3205E2206CE8D37F96923AAC | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\unins000.exe | executable | |
MD5:8E34C5942B6D976A0B6ADE26C07D5FA3 | SHA256:C5AF0E9D4BD80FBA2CFB9B9E22CD055785F2561C3205E2206CE8D37F96923AAC | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\is-V24N0.tmp | executable | |
MD5:CFE1C391464C446099A5EB33276F6D57 | SHA256:4A714D98CE40F5F3577C306A66CB4A6B1FF3FD01047C7F4581F8558F0BCDF5FA | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\DisableSmartScreen.reg | text | |
MD5:98726CF4E77C2A5159801D4E888833DA | SHA256:20AEE3A1B0ECD68E642A5C8FF550D1525DF1C3F2FDA22B7DB51010947153FEBA | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\AutoPico.exe | executable | |
MD5:CFE1C391464C446099A5EB33276F6D57 | SHA256:4A714D98CE40F5F3577C306A66CB4A6B1FF3FD01047C7F4581F8558F0BCDF5FA | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\DevComponents.DotNetBar2.dll | executable | |
MD5:1397B23F30681F97049DF61F94F54D05 | SHA256:FA76151A783250014AC8FA55D4C833100A623FCAD1D6E2DDADCDE259F5709609 | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\is-1SQ1N.tmp | executable | |
MD5:1397B23F30681F97049DF61F94F54D05 | SHA256:FA76151A783250014AC8FA55D4C833100A623FCAD1D6E2DDADCDE259F5709609 | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\is-8HAQH.tmp | text | |
MD5:98726CF4E77C2A5159801D4E888833DA | SHA256:20AEE3A1B0ECD68E642A5C8FF550D1525DF1C3F2FDA22B7DB51010947153FEBA | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\is-FGHLT.tmp | executable | |
MD5:722CE6EF94372C7DF83AA5DF74A60F9C | SHA256:BE7CEAE52902E657D14A987FBF5284B1600811456CCFC6766284600B42673AD5 | |||
| 6700 | KMSPico.tmp | C:\Program Files (x86)\AutoPico\KMSELDI.exe | executable | |
MD5:F0280DE3880EF581BF14F9CC72EC1C16 | SHA256:50EBFA1DD5B147E40244607D5D5BE25709EDF2CC66247A78BEB920C77AC514CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6396 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1048 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2096 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3164 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3164 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
1048 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1048 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6940 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |