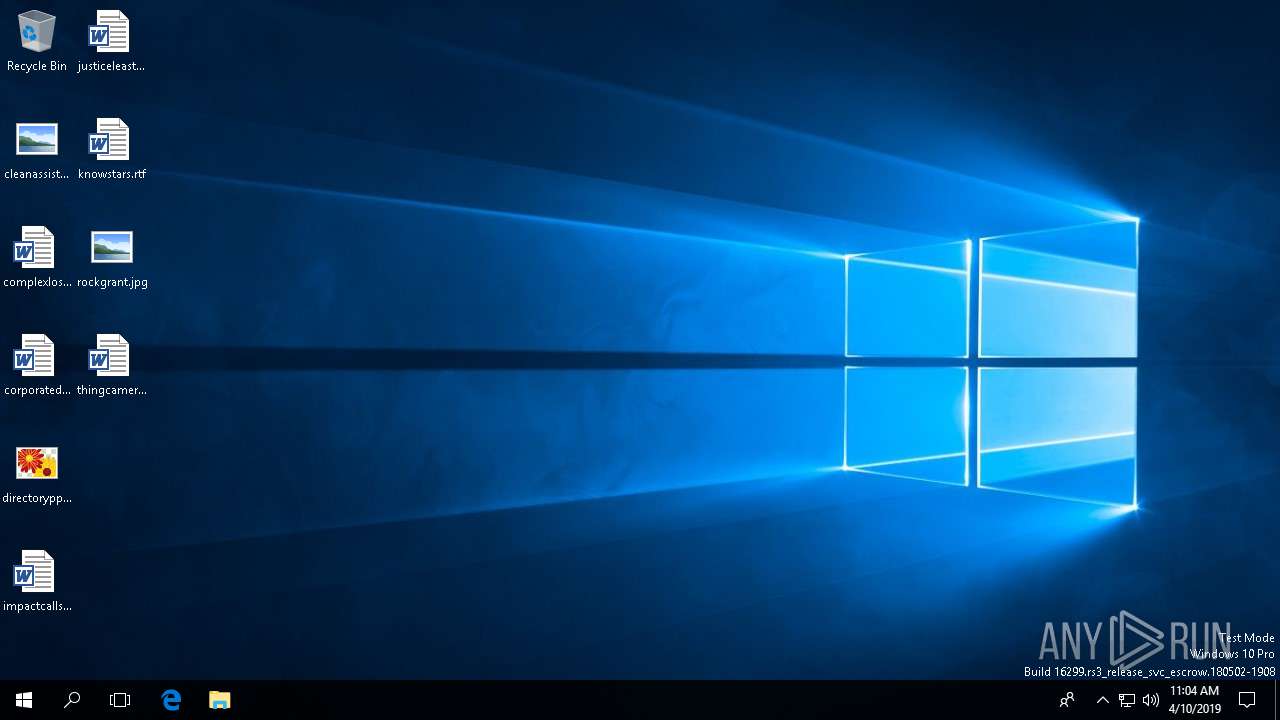
| File name: | b9a67ffb81420e68f9e5607cc200604a.docx |
| Full analysis: | https://app.any.run/tasks/48bc8aeb-fb07-40de-b988-ca05ebcb7d4b |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2019, 11:04:06 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | B9A67FFB81420E68F9E5607CC200604A |
| SHA1: | 248214CC3011A70BB473DC12B0C07CB730AA04B2 |
| SHA256: | DAB2CD3DDFE29A89B3D80830C6A4950952A44B6C97A664F1E9C182318AE5F4DA |
| SSDEEP: | 6144:EY0QYQ+rwD1vkTkCJ6AjC6w9NZsK0cabUOAZ9AJEJ:ErrOkF6Z79DUU7J |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2472)
Changes the autorun value in the registry
- EXCEL.EXE (PID: 5956)
SUSPICIOUS
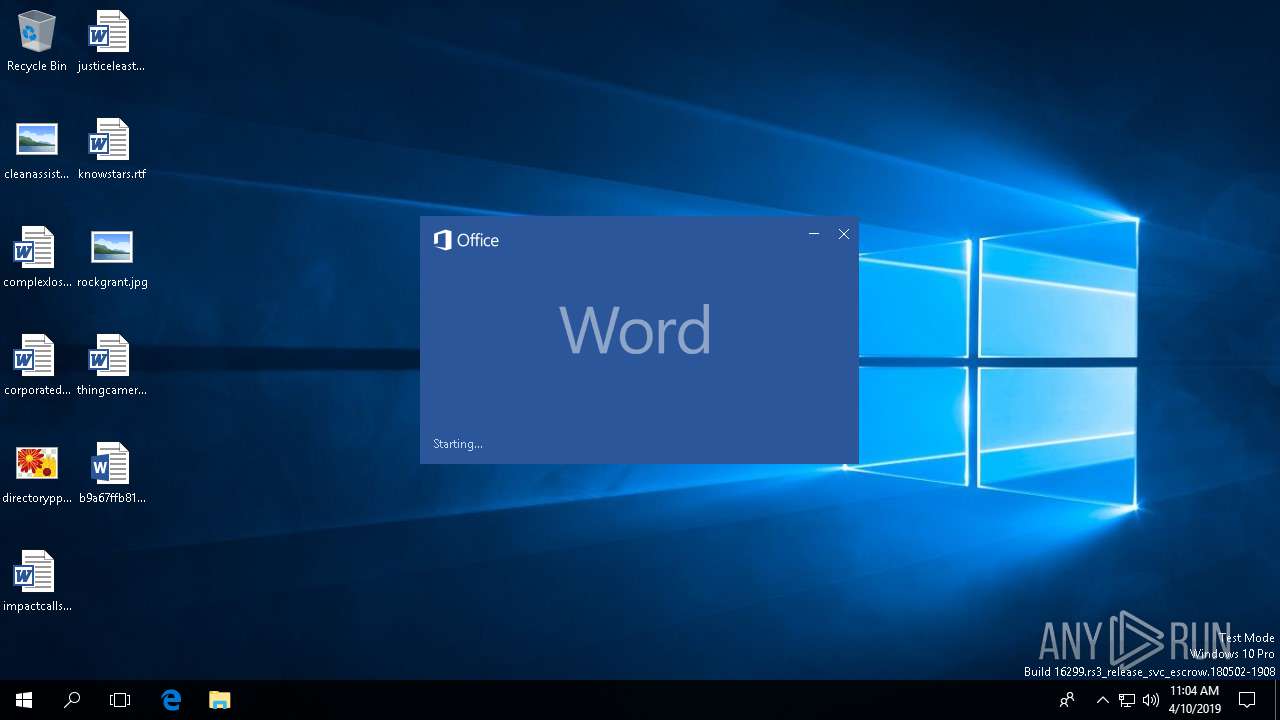
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2472)
Reads the machine GUID from the registry
- MsoSync.exe (PID: 5364)
- MsoSync.exe (PID: 5980)
Creates files in the Windows directory
- EXCEL.EXE (PID: 5956)
INFO
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2472)
- EXCEL.EXE (PID: 5956)
Reads settings of System Certificates
- MsoSync.exe (PID: 5364)
- MsoSync.exe (PID: 5980)
- EXCEL.EXE (PID: 5956)
- WINWORD.EXE (PID: 2472)
Reads the software policy settings
- MsoSync.exe (PID: 5980)
- EXCEL.EXE (PID: 5956)
- WINWORD.EXE (PID: 2472)
- MsoSync.exe (PID: 5364)
Creates files in the user directory
- WINWORD.EXE (PID: 2472)
Reads Microsoft Office registry keys
- MsoSync.exe (PID: 5980)
- EXCEL.EXE (PID: 5956)
- MsoSync.exe (PID: 5364)
- WINWORD.EXE (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xbc2b2aaa |
| ZipCompressedSize: | 392 |
| ZipUncompressedSize: | 1553 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | I'm Negan |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | I'm Negan |
| RevisionNumber: | 2 |
| CreateDate: | 2019:04:07 18:10:00Z |
| ModifyDate: | 2019:04:07 19:21:00Z |
| Template: | README.txt |
| TotalEditTime: | 1.1 hours |
| Pages: | 1 |
| Words: | 31 |
| Characters: | 183 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 213 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
92
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2472 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\b9a67ffb81420e68f9e5607cc200604a.docx" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.6741.2048 Modules
| |||||||||||||||
| 5364 | "C:\Program Files\Microsoft Office\Root\Office16\MsoSync.exe" | C:\Program Files\Microsoft Office\Root\Office16\MsoSync.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Document Cache Exit code: 0 Version: 16.0.6741.2048 Modules
| |||||||||||||||
| 5956 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" /automation -Embedding | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.6741.2048 Modules
| |||||||||||||||
| 5980 | "C:\Program Files\Microsoft Office\Root\Office16\MsoSync.exe" | C:\Program Files\Microsoft Office\Root\Office16\MsoSync.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Document Cache Exit code: 0 Version: 16.0.6741.2048 Modules
| |||||||||||||||
Total events
3 821
Read events
3 116
Write events
511
Delete events
194
Modification events
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 1 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u2" |
Value: 75322200A8090000010000000000000051C35A358DEFD40100000000 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %3" |
Value: 25332200A809000000000440010000008C275D358DEFD4013A000000D271FABBACBC994C9B567E61E525EBF08C275D358DEFD40100000000000010000008551A00000000030000006C00000002000000000000000000 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %3" |
Value: 25332200A809000000000440010000008C275D358DEFD4013C000000D271FABBACBC994C9B567E61E525EBF08C275D358DEFD40100000000000010000008551A000000000300000007000000040000000000000000000000 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\winword.exe\ETWMonitor\{02FD33DF-F746-4A10-93A0-2BC6273BC8E4} |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
23
Text files
24
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\A62EBDB9-6D5D-4653-AD94-8CF2FEE1ED55 | xml | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\OfficeFileCache\CentralTable.accdb | accdb | |
MD5:— | SHA256:— | |||
| 5980 | MsoSync.exe | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\msosync.exe_Rules.xml | xml | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\350527D7.txt | document | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\WLJYL64M\README[1].txt | document | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\Desktop\~$a67ffb81420e68f9e5607cc200604a.docx | pgc | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\README.txt.url | text | |
MD5:— | SHA256:— | |||
| 5364 | MsoSync.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\{AB96E3B6-7691-41BC-B4B3-3FDEF70431B1} (0) - 5364 - msosync.exe - OTele.dat | pgc | |
MD5:— | SHA256:— | |||
| 5364 | MsoSync.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\{AB96E3B6-7691-41BC-B4B3-3FDEF70431B1} (0) - 5364 - msosync.exe - OTeleMediumCost.dat | pgc | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\b9a67ffb81420e68f9e5607cc200604a.docx.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
45
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2472 | WINWORD.EXE | OPTIONS | — | 23.111.134.163:80 | http://tfu.ae/ | US | — | — | suspicious |
2472 | WINWORD.EXE | OPTIONS | — | 23.111.134.163:80 | http://tfu.ae/ | US | — | — | suspicious |
2472 | WINWORD.EXE | HEAD | 200 | 23.111.134.163:80 | http://tfu.ae/README.txt | US | — | — | suspicious |
2472 | WINWORD.EXE | GET | 200 | 52.109.32.27:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.6701&crev=3 | GB | xml | 98.9 Kb | whitelisted |
2472 | WINWORD.EXE | GET | 200 | 13.107.5.88:443 | https://ocos-office365-s2s.msedge.net/ab?&clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d | US | text | 15 b | whitelisted |
— | — | POST | 200 | 65.54.187.132:443 | https://login.live.com/RST2.srf | US | xml | 11.2 Kb | whitelisted |
2472 | WINWORD.EXE | POST | 201 | 52.109.12.24:443 | https://nexus.officeapps.live.com/nexus/upload/%7bACB1E0F0-9F62-4C9F-9990-7A019B382668%7d | US | — | — | whitelisted |
5980 | MsoSync.exe | GET | 200 | 52.109.8.21:443 | https://nexusrules.officeapps.live.com/nexus/rules?Application=msosync.exe&Version=16.0.6741.2048&ClientId=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&OSEnvironment=10&MsoAppId=16&AudienceName=Unknown&AudienceGroup=Unknown&AppVersion=16.0.6741.2048& | US | xml | 90.9 Kb | whitelisted |
5364 | MsoSync.exe | GET | 200 | 52.109.8.21:443 | https://nexusrules.officeapps.live.com/nexus/rules?Application=msosync.exe&Version=16.0.6741.2048&ClientId=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&OSEnvironment=10&MsoAppId=16&AudienceName=Unknown&AudienceGroup=Unknown&AppVersion=16.0.6741.2048& | US | xml | 90.9 Kb | whitelisted |
— | — | POST | 200 | 65.54.187.132:443 | https://login.live.com/RST2.srf | US | xml | 10.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2868 | svchost.exe | 40.67.251.132:443 | client.wns.windows.com | Microsoft Corporation | IE | whitelisted |
2472 | WINWORD.EXE | 13.107.5.88:443 | ocos-office365-s2s.msedge.net | Microsoft Corporation | US | whitelisted |
— | — | 52.109.32.27:443 | officeclient.microsoft.com | Microsoft Corporation | GB | whitelisted |
2472 | WINWORD.EXE | 52.109.32.23:443 | roaming.officeapps.live.com | Microsoft Corporation | GB | whitelisted |
2472 | WINWORD.EXE | 23.111.134.163:80 | tfu.ae | HIVELOCITY VENTURES CORP | US | suspicious |
2472 | WINWORD.EXE | 52.109.12.24:443 | nexus.officeapps.live.com | Microsoft Corporation | US | whitelisted |
5364 | MsoSync.exe | 13.107.5.88:443 | ocos-office365-s2s.msedge.net | Microsoft Corporation | US | whitelisted |
5364 | MsoSync.exe | 52.109.8.21:443 | nexusrules.officeapps.live.com | Microsoft Corporation | US | whitelisted |
5980 | MsoSync.exe | 52.109.8.21:443 | nexusrules.officeapps.live.com | Microsoft Corporation | US | whitelisted |
5980 | MsoSync.exe | 13.107.5.88:443 | ocos-office365-s2s.msedge.net | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocos-office365-s2s.msedge.net |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
tfu.ae |
| suspicious |
nexus.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
odc.officeapps.live.com |
| whitelisted |
templateservice.office.com |
| whitelisted |
omextemplates.content.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2472 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |