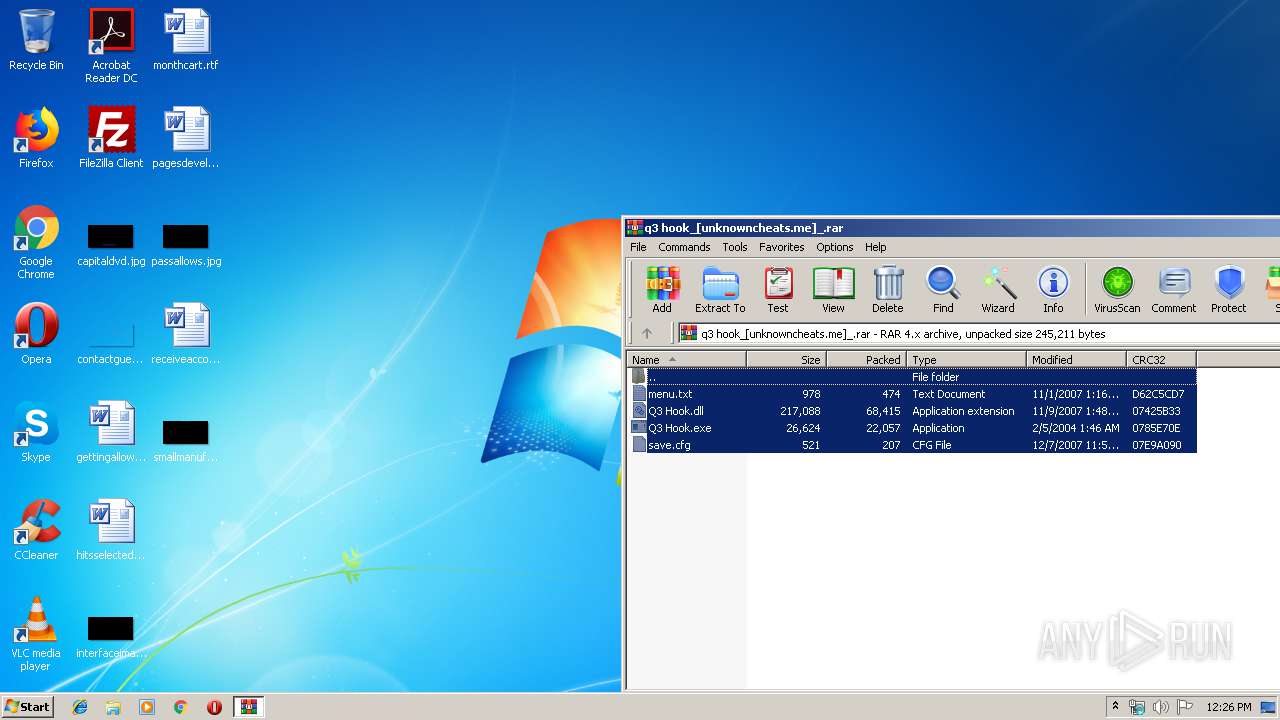
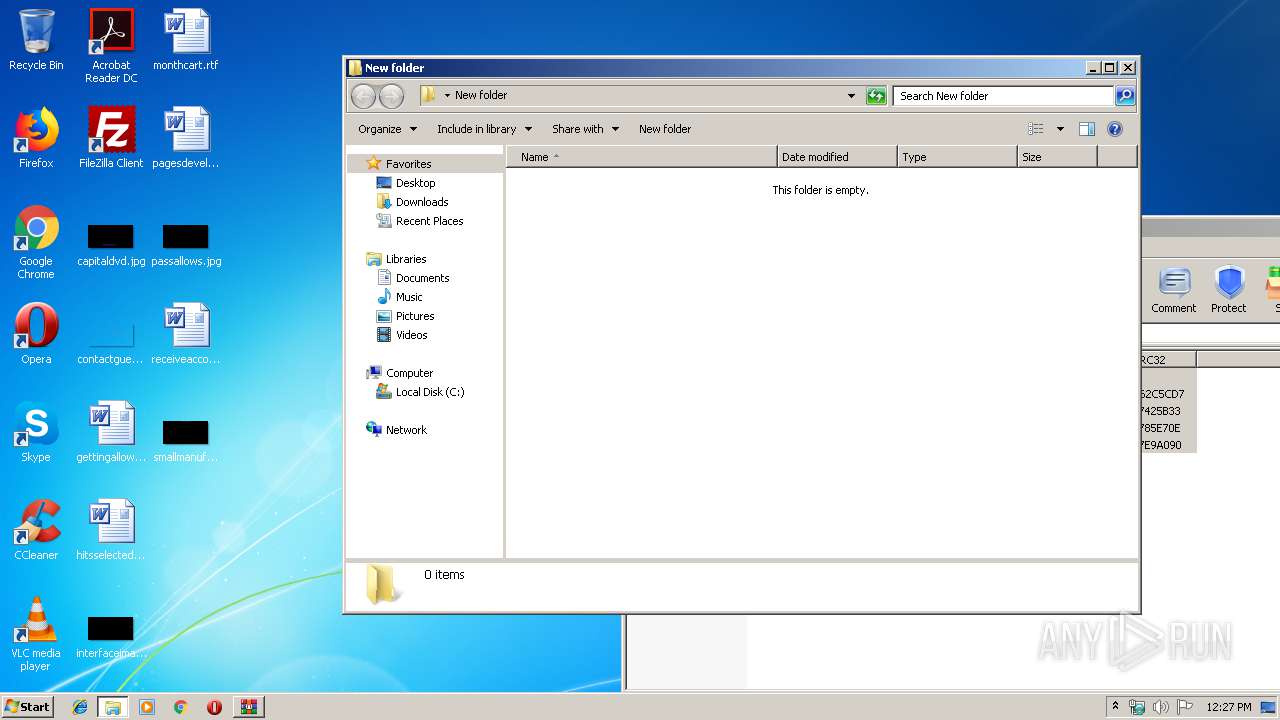
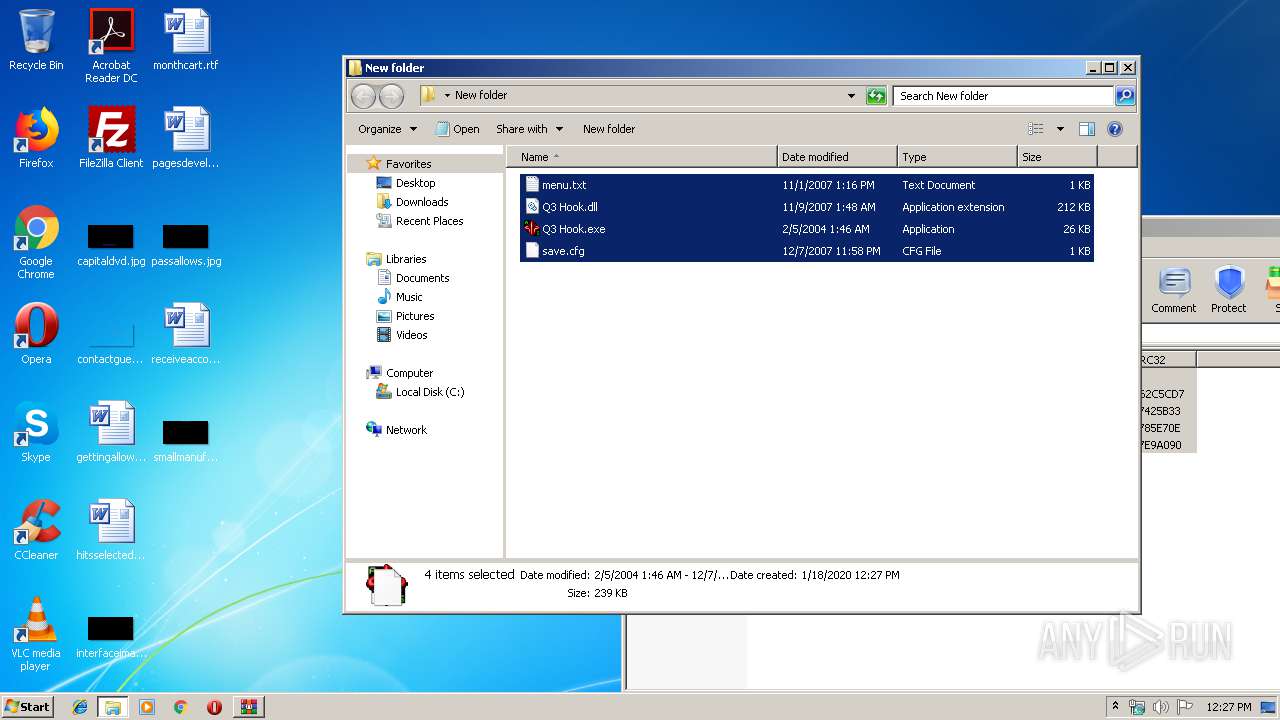
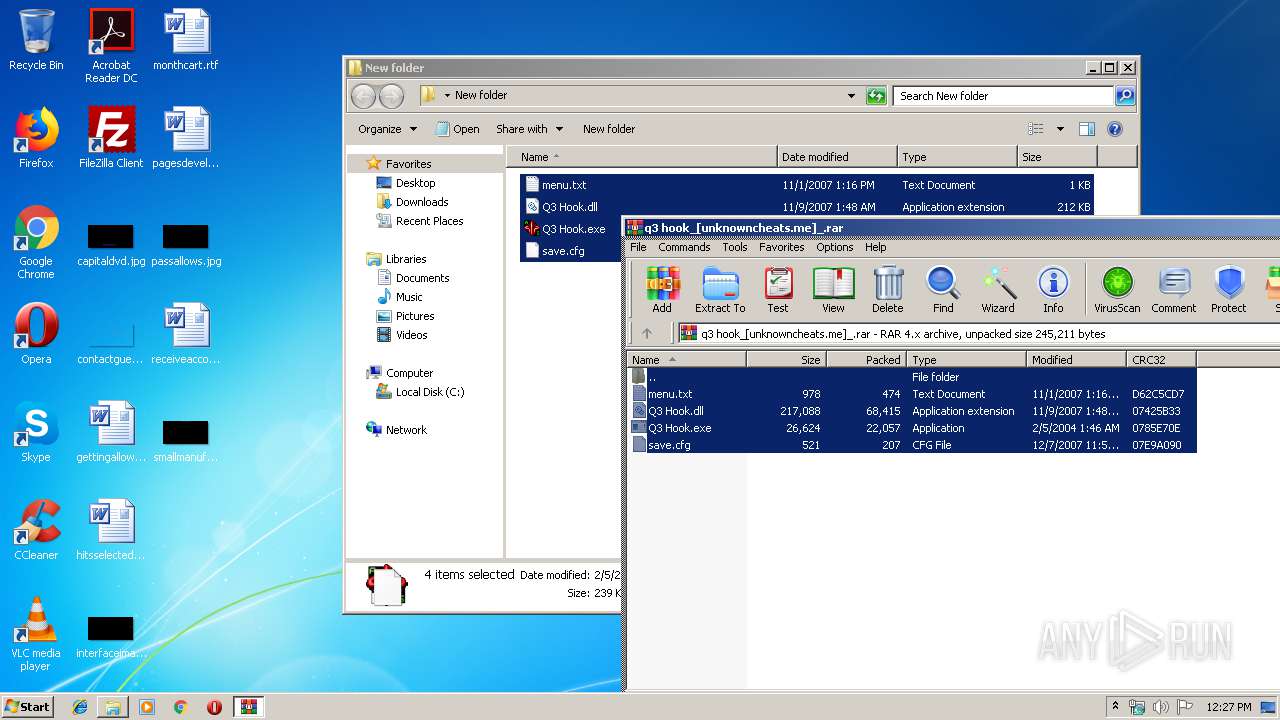
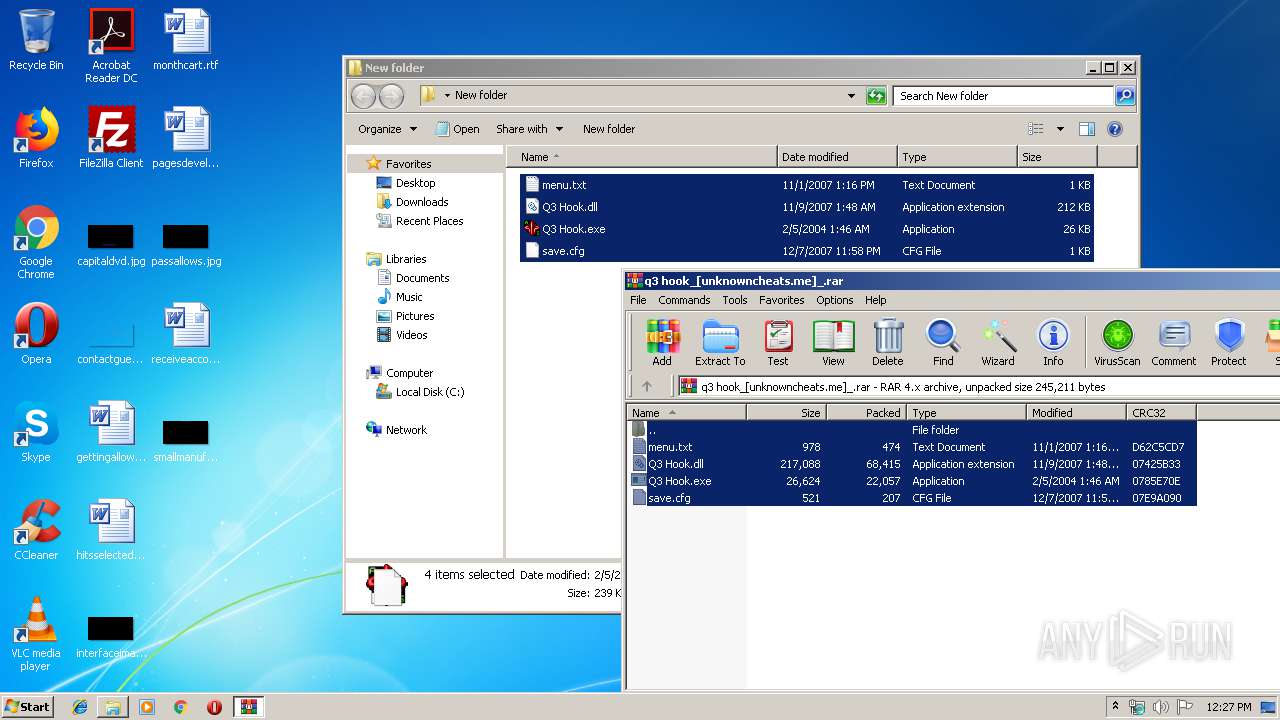
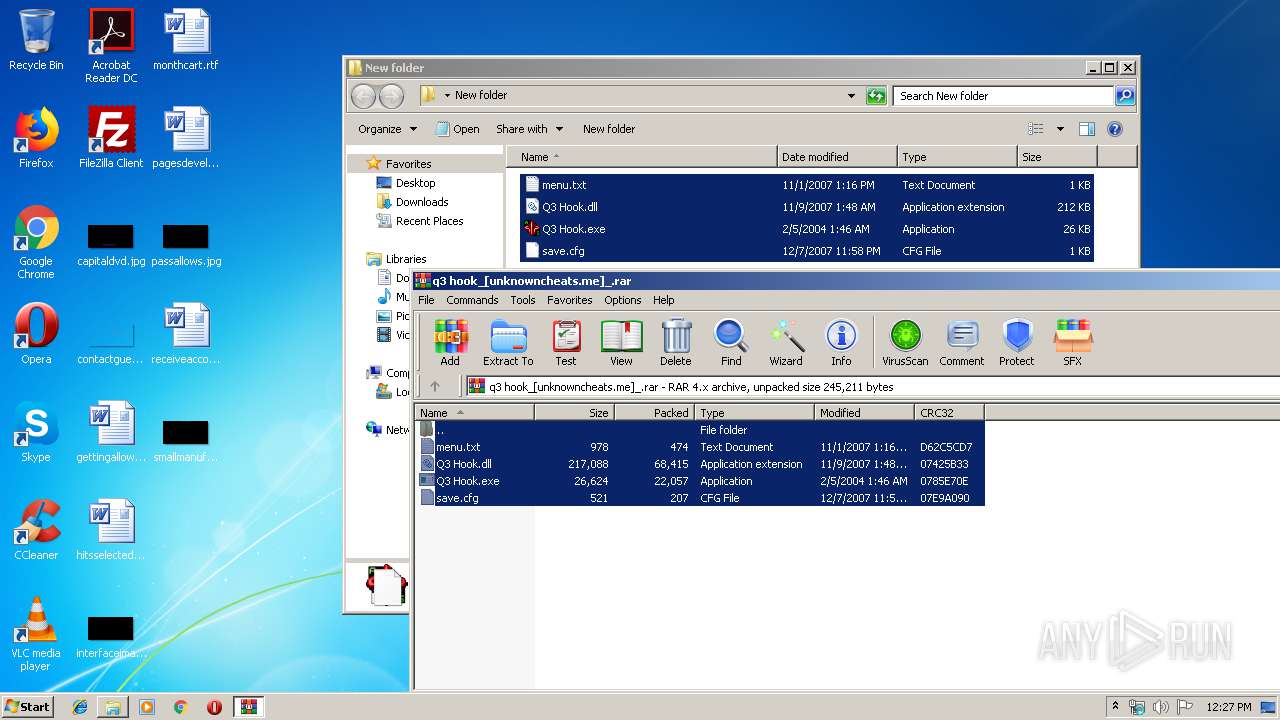
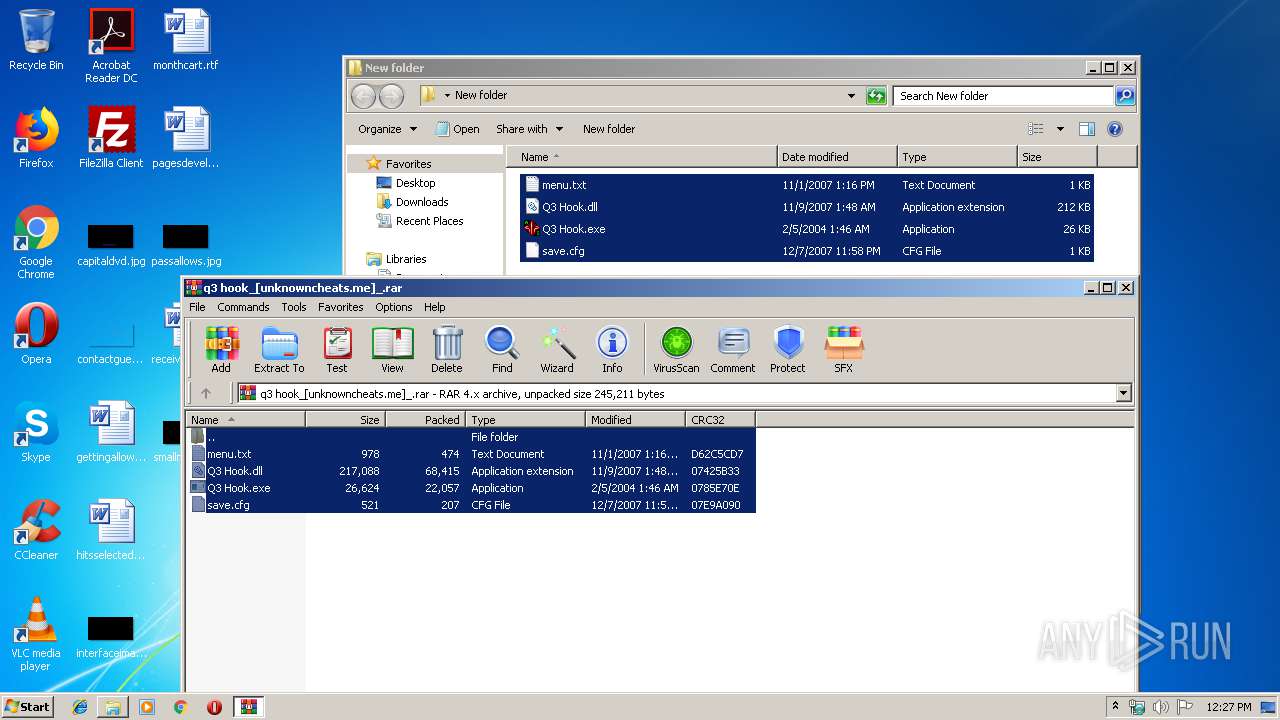
| File name: | q3 hook_[unknowncheats.me]_.rar |
| Full analysis: | https://app.any.run/tasks/54691186-0172-4449-abd2-8de06dcb8a8e |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 12:26:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
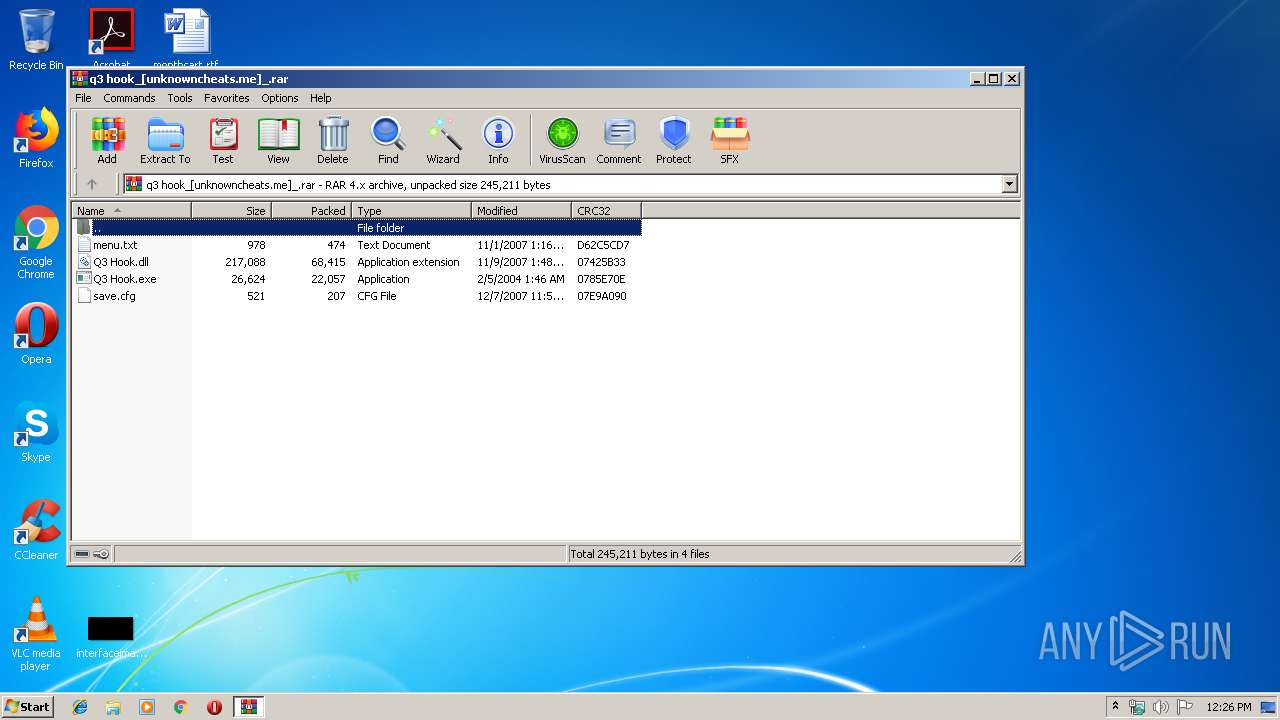
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | E4846958829B6A86B52AF1EB04946A02 |
| SHA1: | A78FE115613226C2CE4E1566B86E40DA4458AA58 |
| SHA256: | DAB215D74D9A89A5AB3E7C862F58FB079396D87C0495A8D39F837CEC41844CAF |
| SSDEEP: | 1536:AT8s5JUG+E/3M2qGW+31zwRq4hX/084bz80ME1ddnkO/4dAWh1gxazYf/oW:Aw8UB882tW+F8RPhPvYoqbnhuvwfAW |
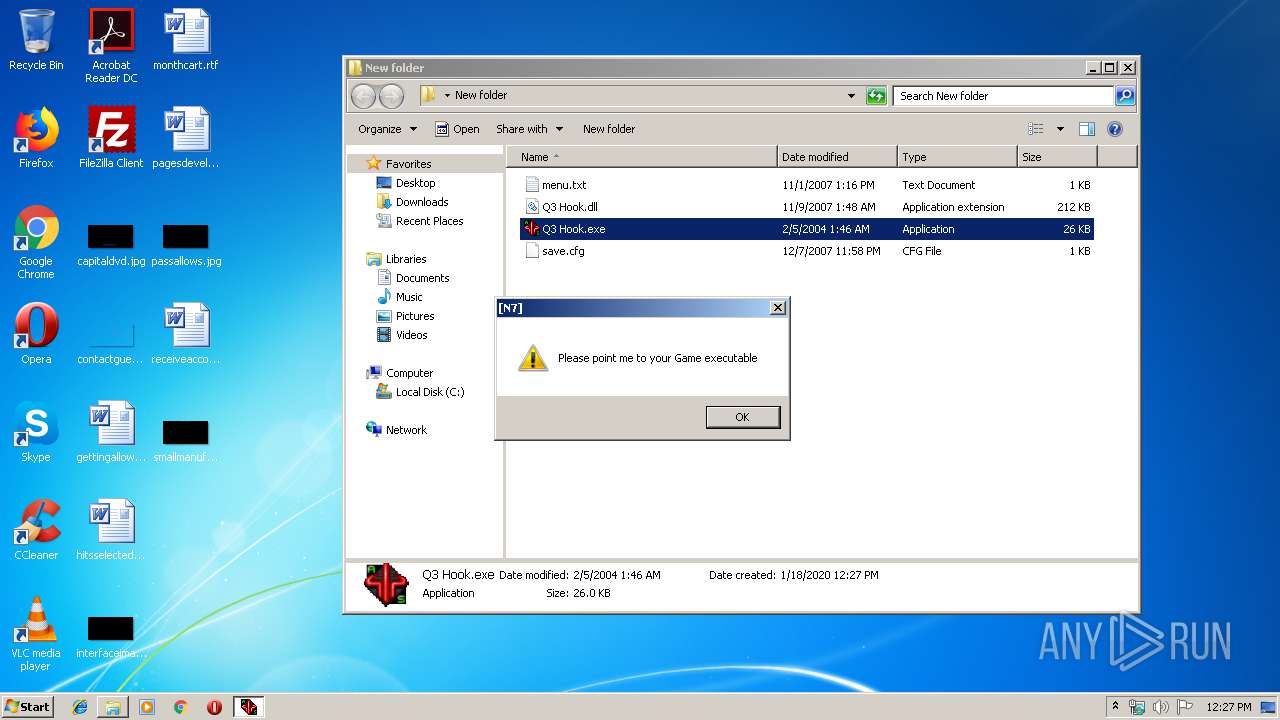
MALICIOUS
Application was dropped or rewritten from another process
- Q3 Hook.exe (PID: 2416)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3476)
- explorer.exe (PID: 352)
- SOUNDMAN.EXE (PID: 436)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- SOUNDMAN.EXE (PID: 436)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
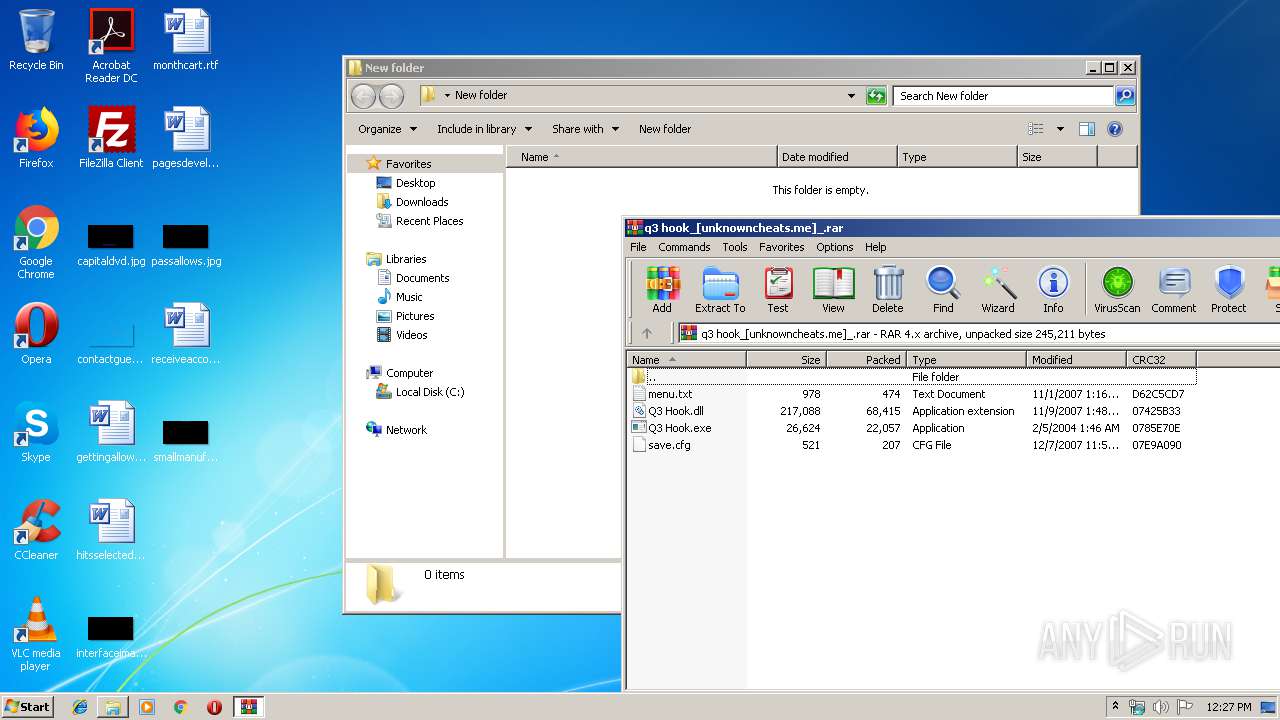
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 22089 |
|---|---|
| UncompressedSize: | 26624 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2004:02:05 01:46:00 |
| PackingMethod: | Normal |
| ArchivedFileName: | Q3 Hook.exe |
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | -game cstrike | C:\Windows\SOUNDMAN.EXE | — | Q3 Hook.exe | |||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: MEDIUM Description: Realtek Sound Manager Exit code: 0 Version: 6, 0, 0, 5 Modules
| |||||||||||||||
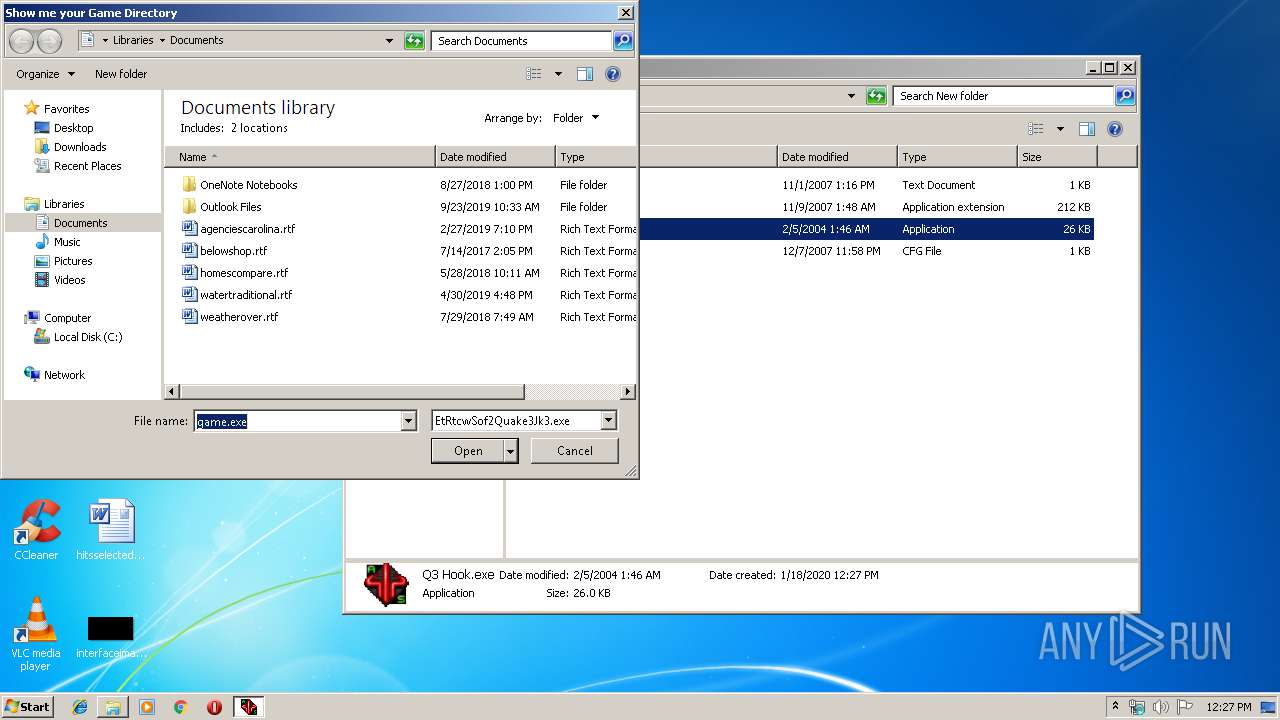
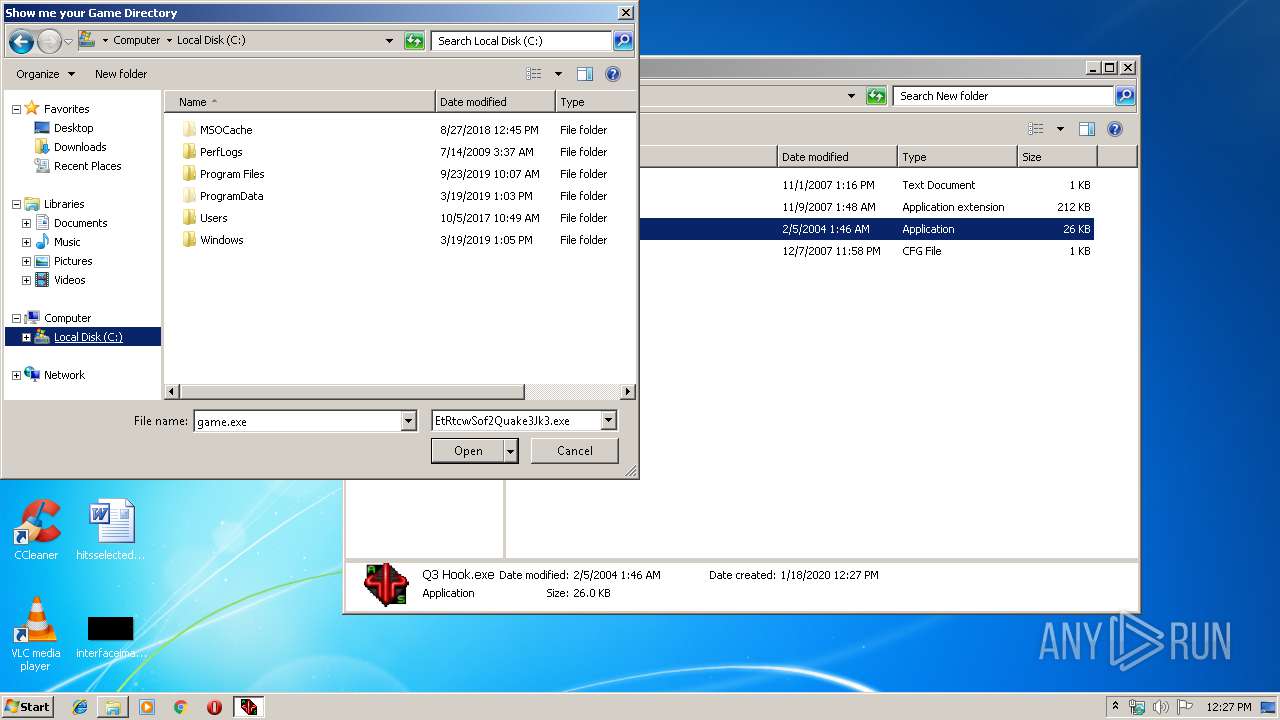
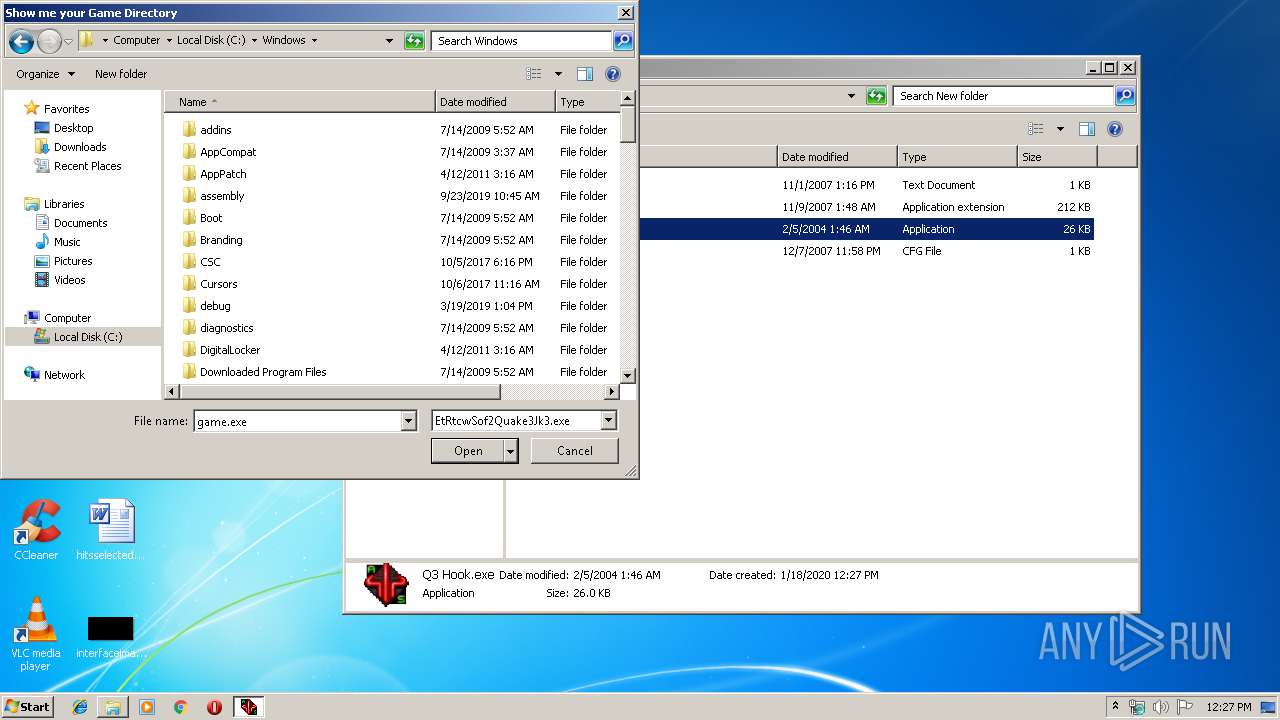
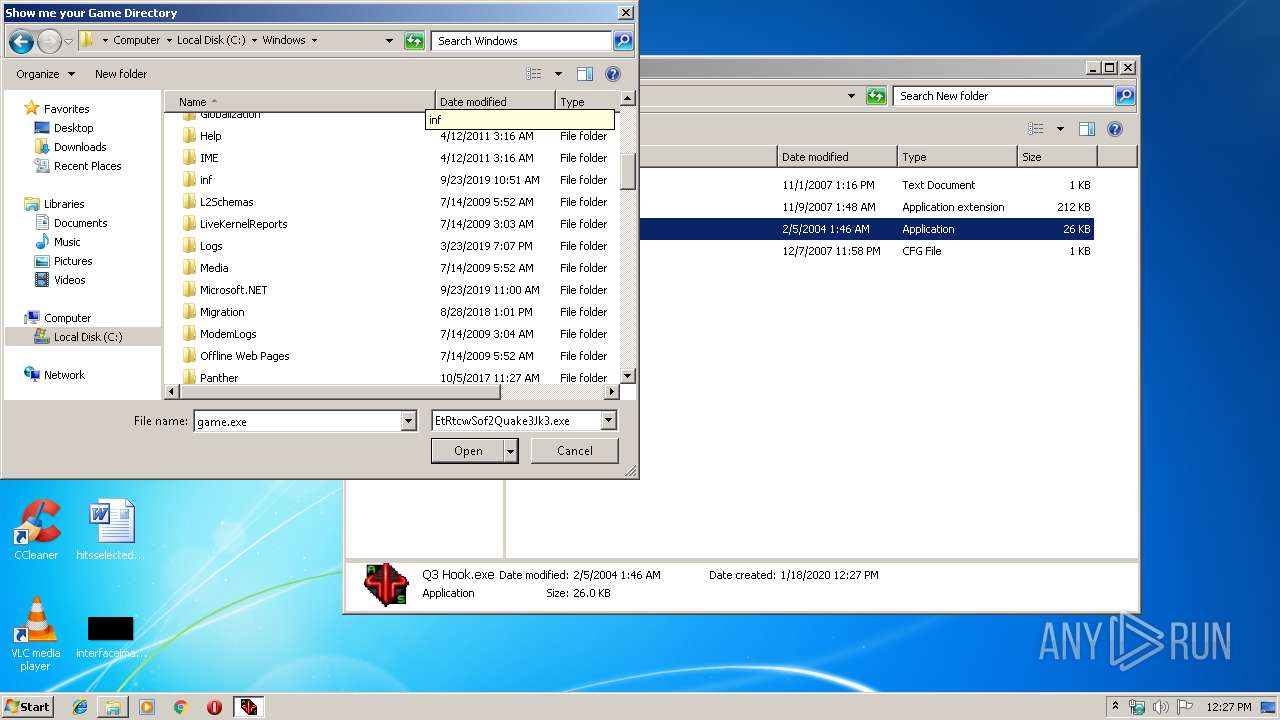
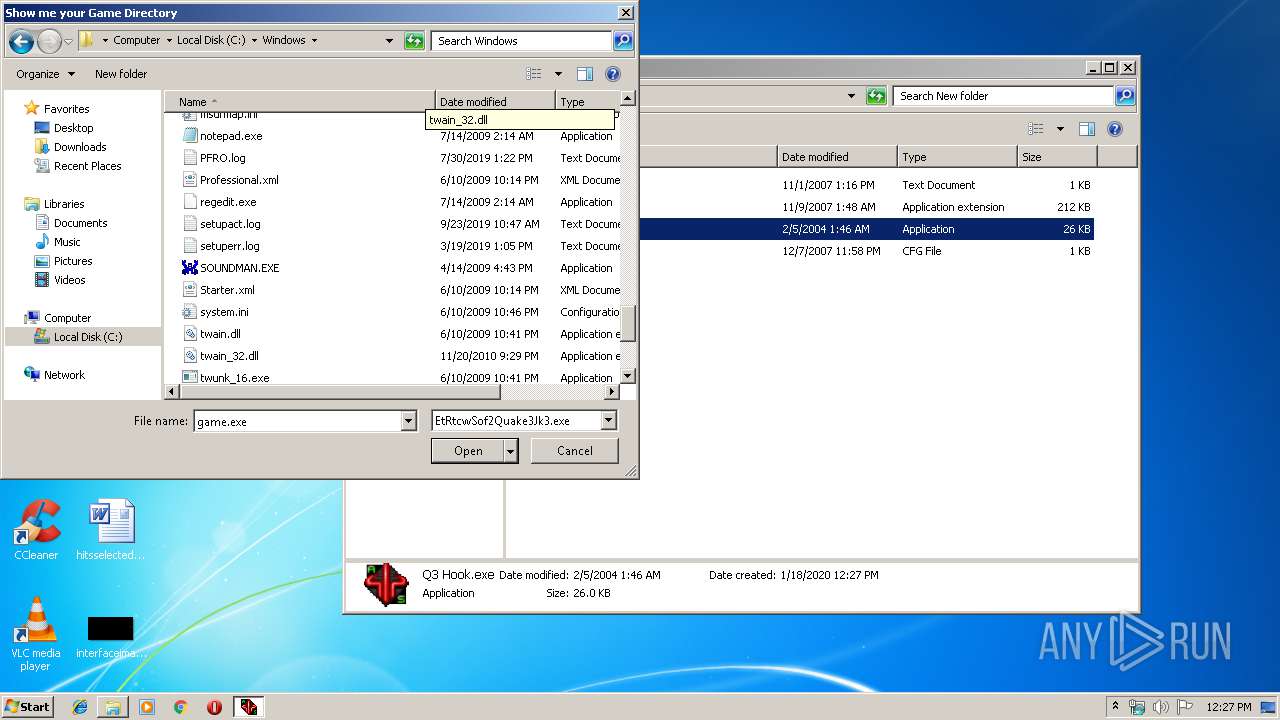
| 2416 | "C:\Users\admin\Desktop\New folder\Q3 Hook.exe" | C:\Users\admin\Desktop\New folder\Q3 Hook.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2456 | rundll32.exe shell32.dll,Control_RunDLL alsndmgr.cpl,,104 | C:\Windows\system32\rundll32.exe | — | SOUNDMAN.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
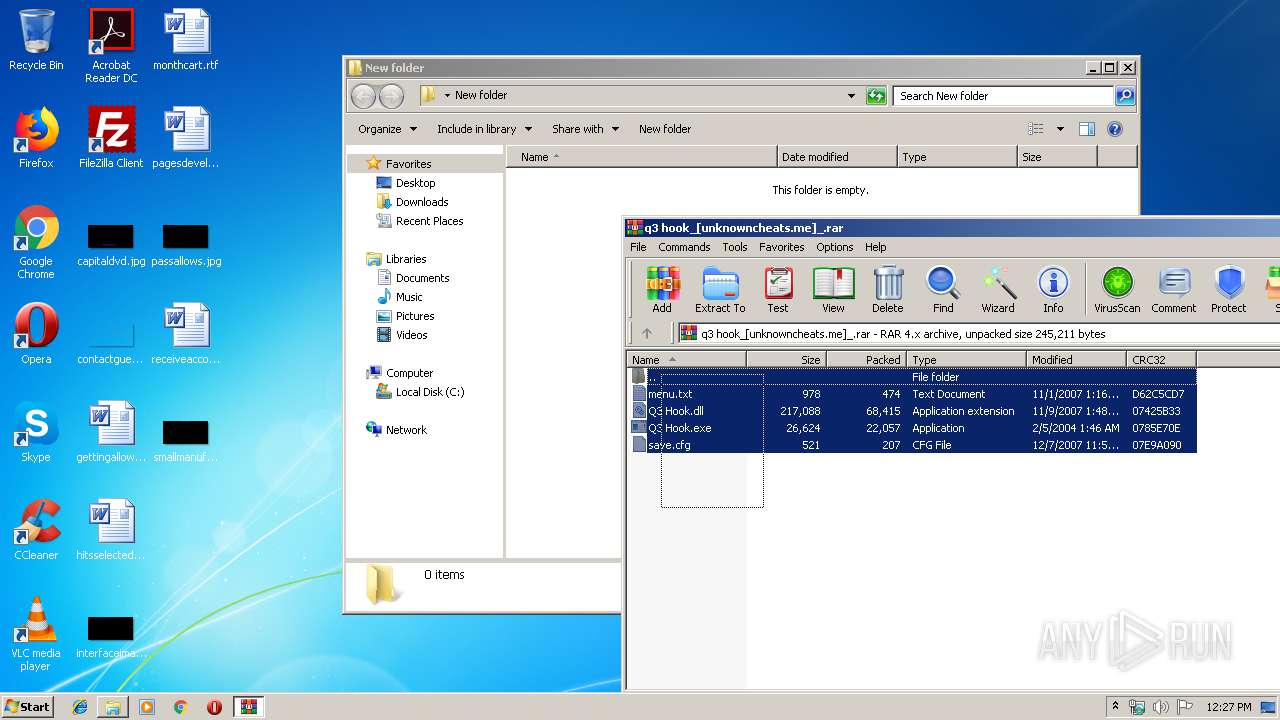
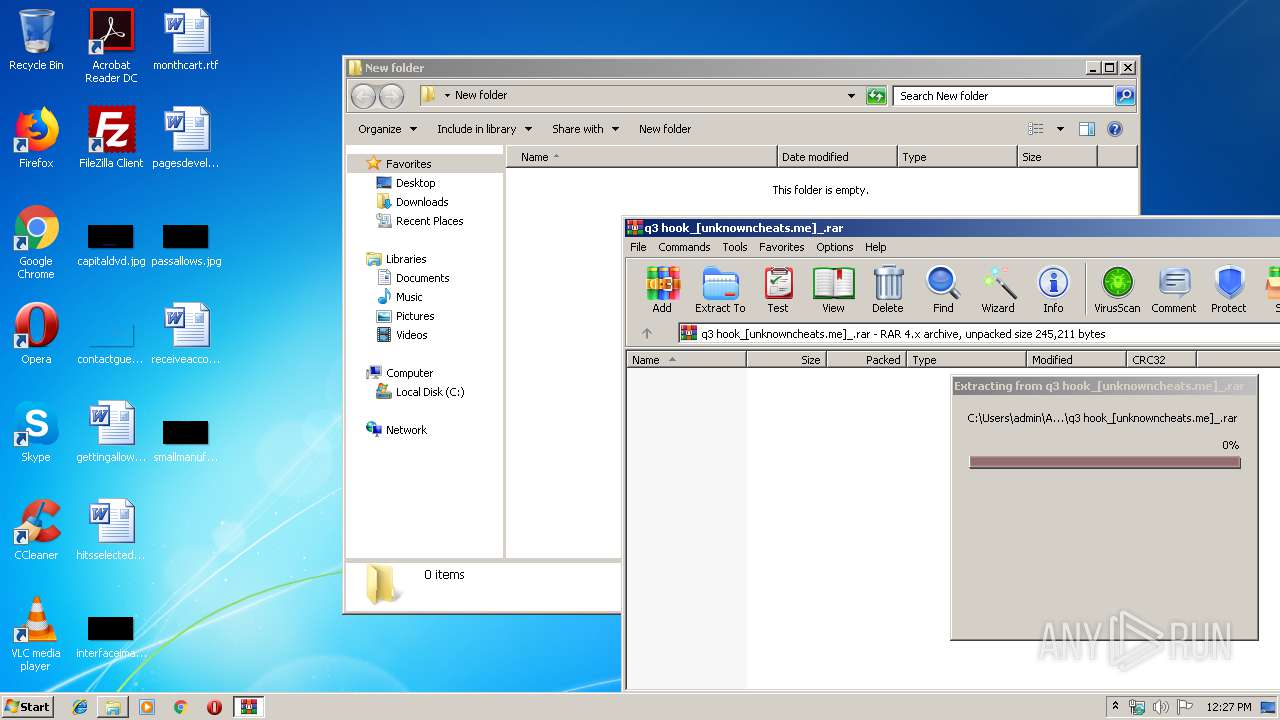
| 2752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\q3 hook_[unknowncheats.me]_.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3476 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 335
Read events
4 109
Write events
224
Delete events
2
Modification events
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\q3 hook_[unknowncheats.me]_.rar | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
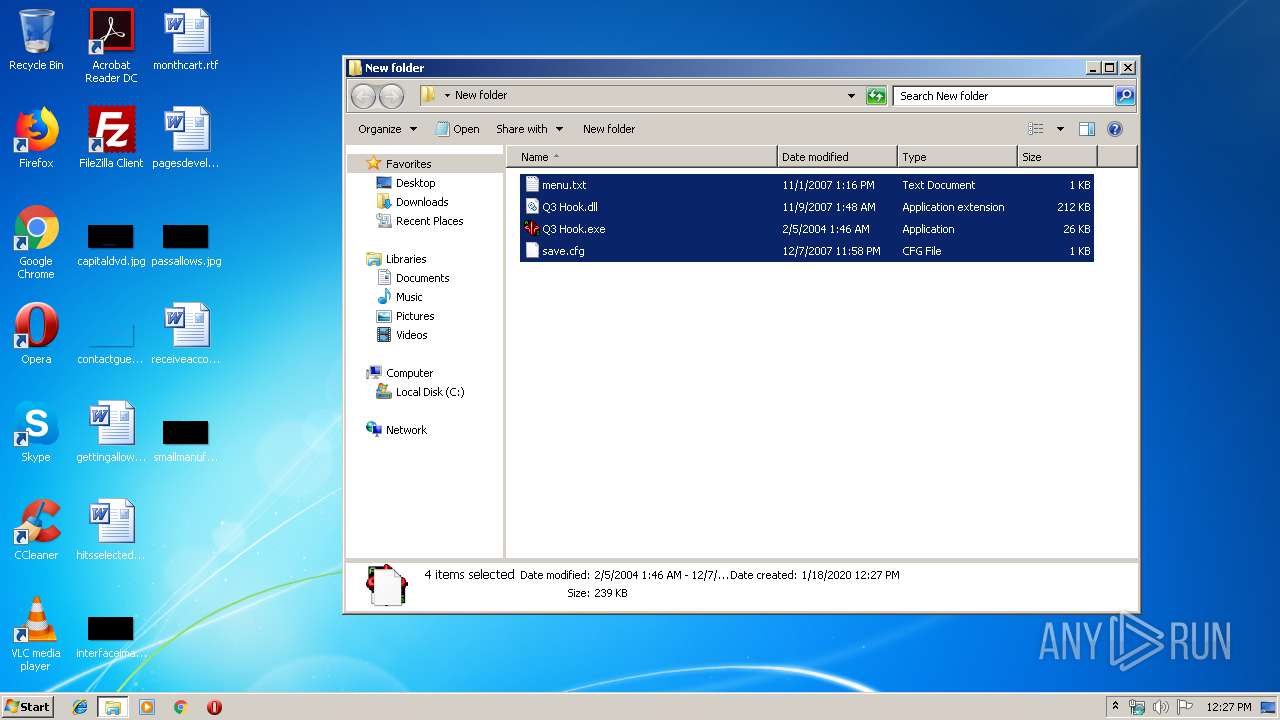
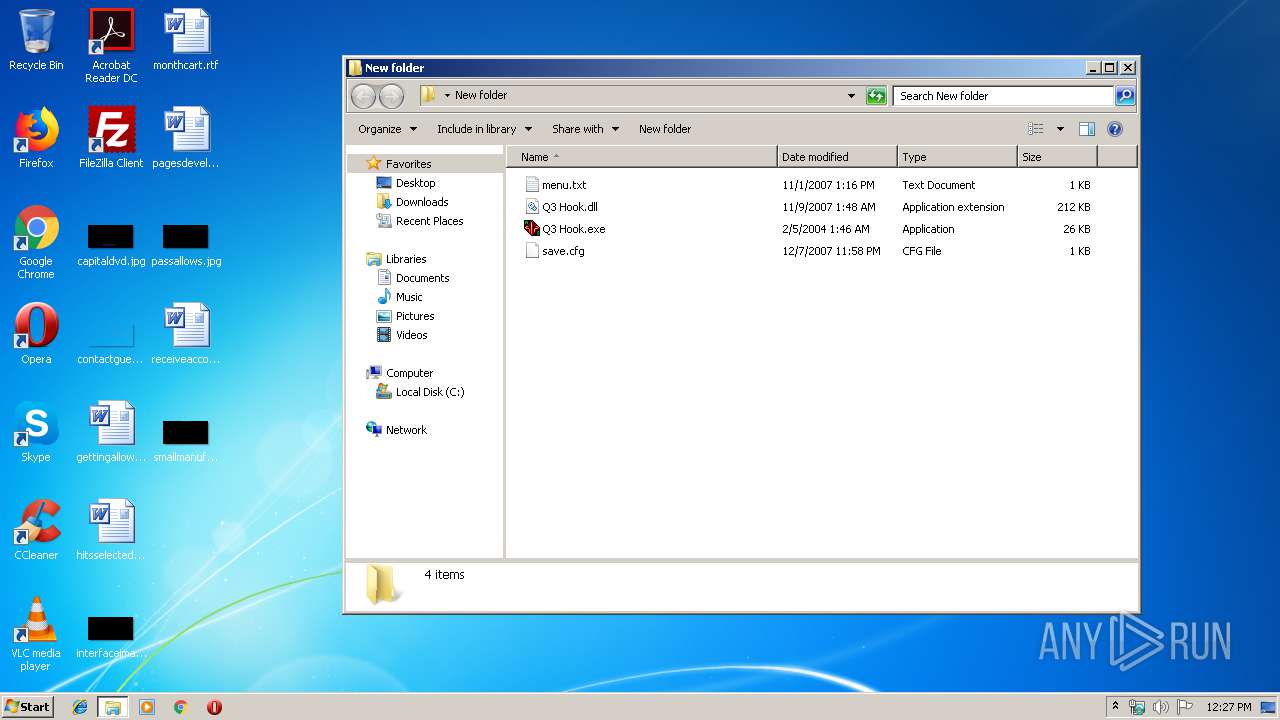
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
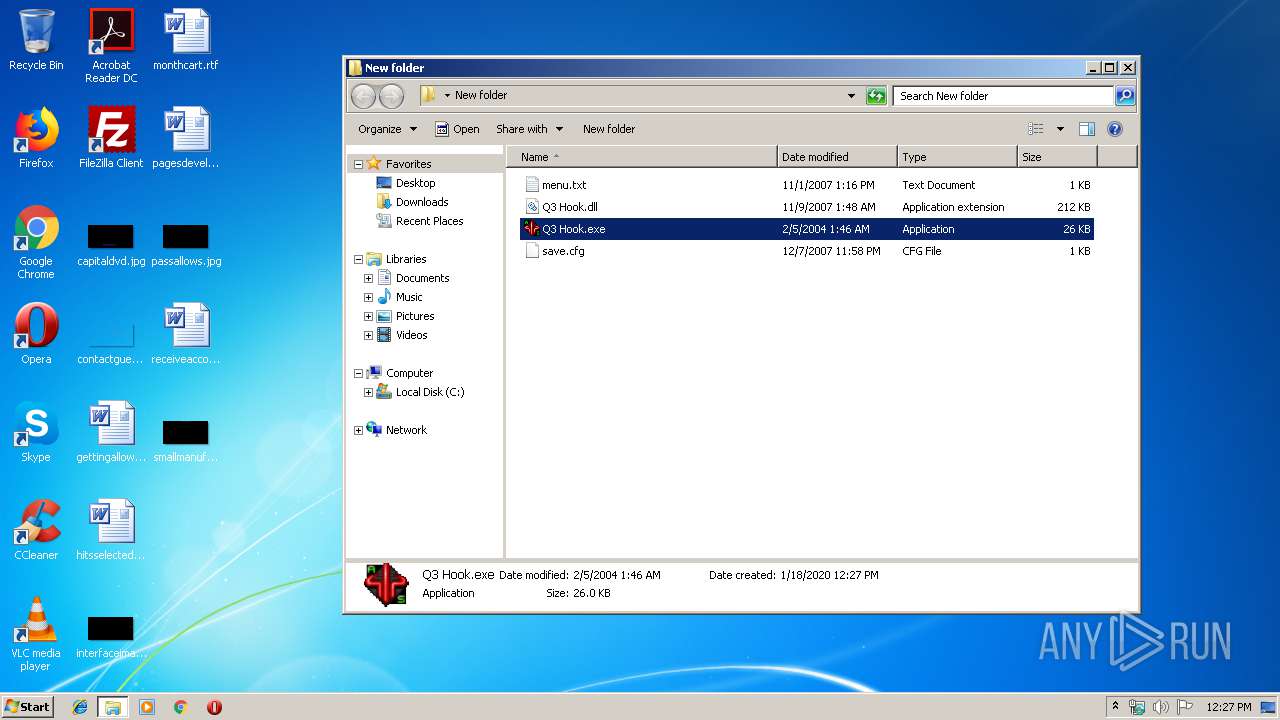
| 2752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2752.42779\Q3 Hook.exe | — | |
MD5:— | SHA256:— | |||
| 2752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2752.42779\Q3 Hook.dll | — | |
MD5:— | SHA256:— | |||
| 2752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2752.42779\save.cfg | — | |
MD5:— | SHA256:— | |||
| 2752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2752.42779\menu.txt | — | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\New folder\Q3 Hook.dll | executable | |
MD5:— | SHA256:— | |||
| 2416 | Q3 Hook.exe | C:\Users\admin\Desktop\New folder\Q3 Hook.ini | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\New folder\menu.txt | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\New folder\save.cfg | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\New folder\Q3 Hook.exe | executable | |
MD5:E0E79DE72893C35758750AD08F66CBEB | SHA256:DE8013614D6C10E360F9F21688307FF4BA39717B4469DD057C48E7142096D679 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report