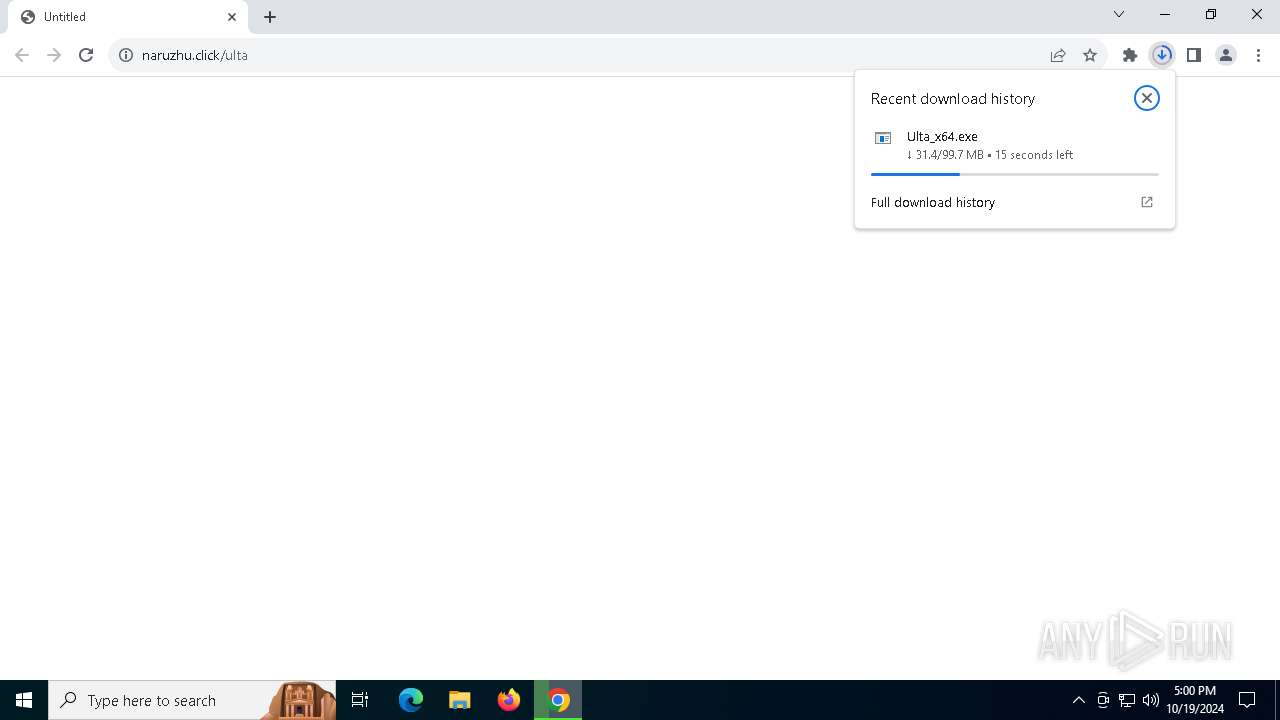
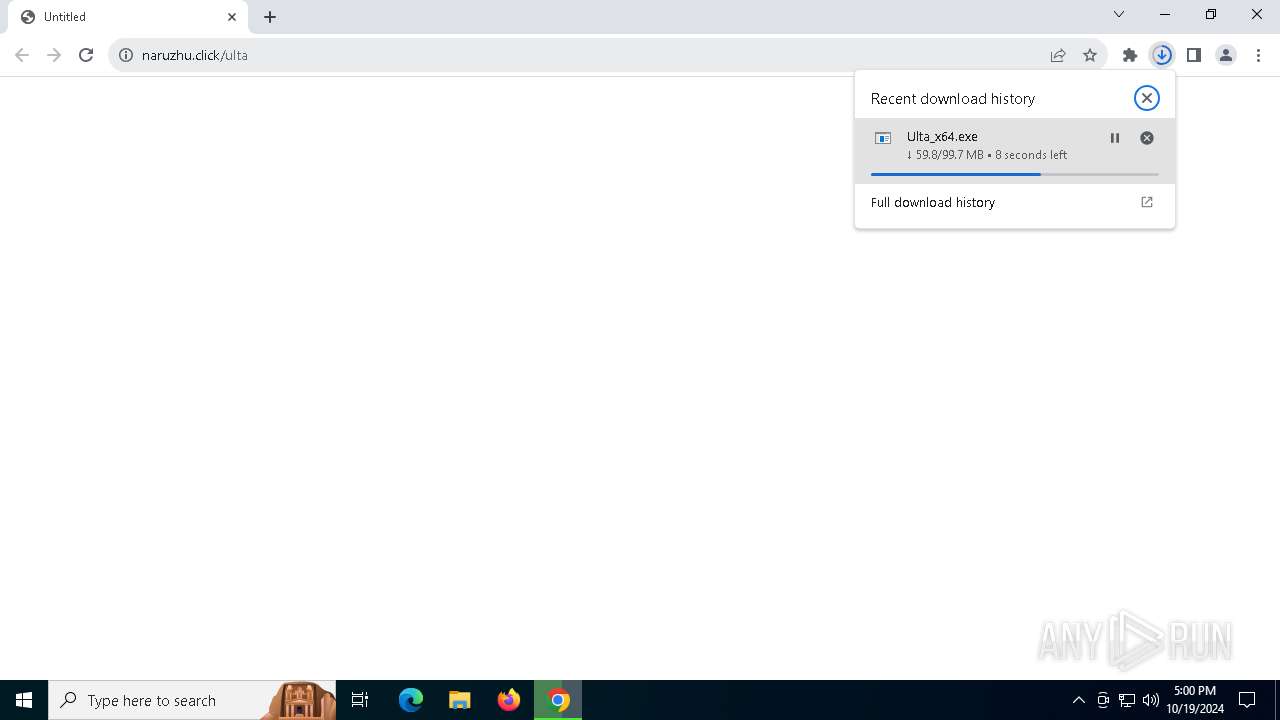
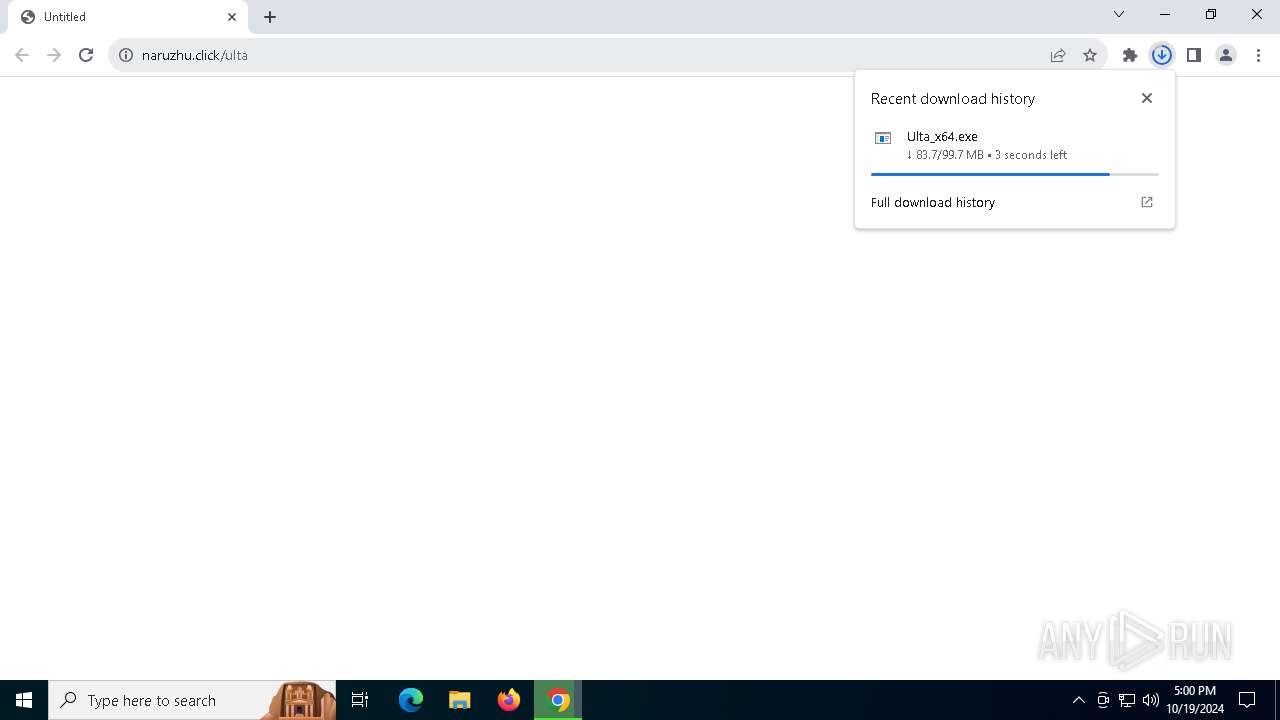
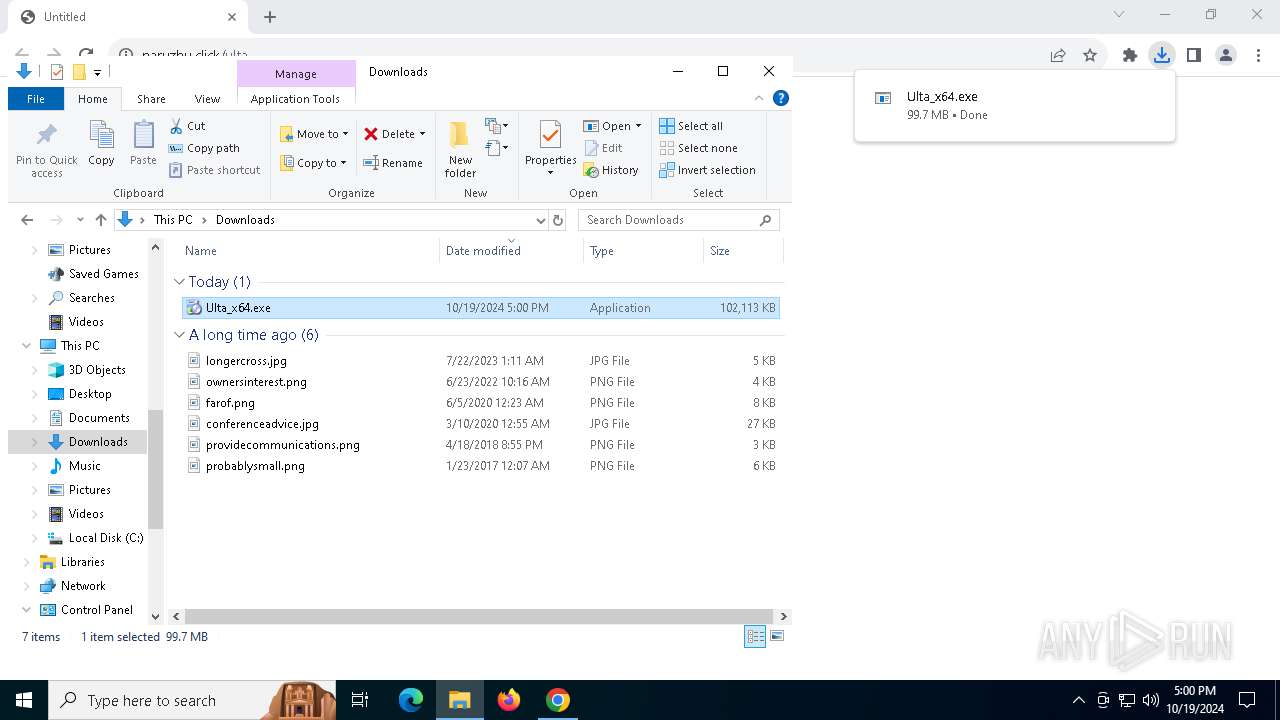
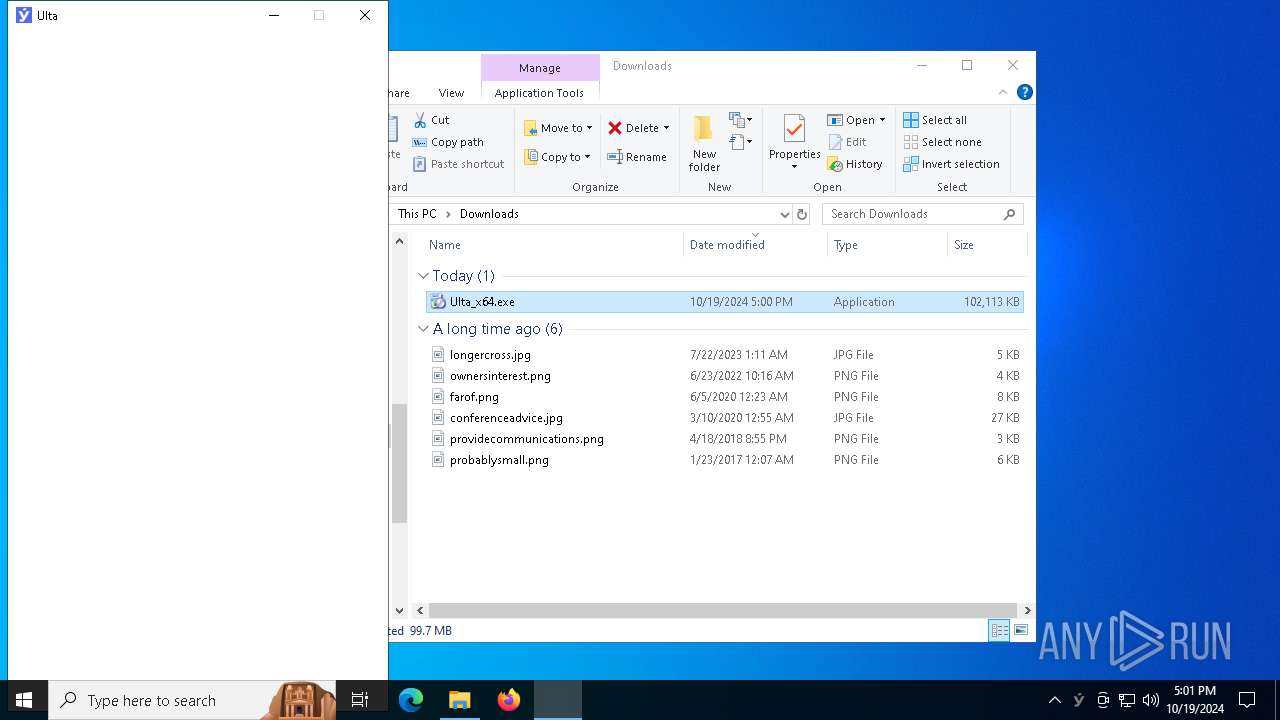
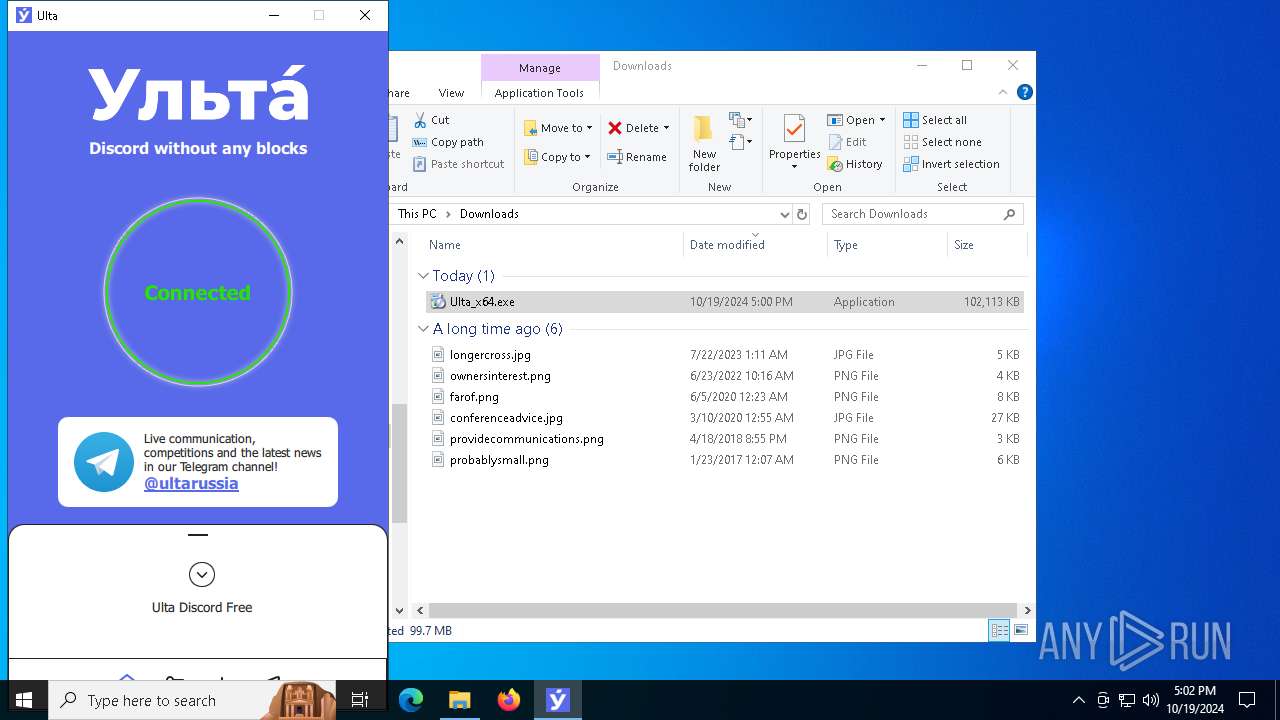
| URL: | https://naruzhu.click/ulta |
| Full analysis: | https://app.any.run/tasks/81f8f957-fd1c-46fb-a7bf-e632569826d1 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2024, 16:59:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 126DE06C19A27F0829D745E70E810ECD |
| SHA1: | B786420B3FDEE2DC1495F9D515CE70407650855A |
| SHA256: | DAA2A21E45BBD0DC47B12A2AF8E6519C28D48D6DBF8E488C26A591DC7C4AFA5C |
| SSDEEP: | 3:N8tKC:2YC |
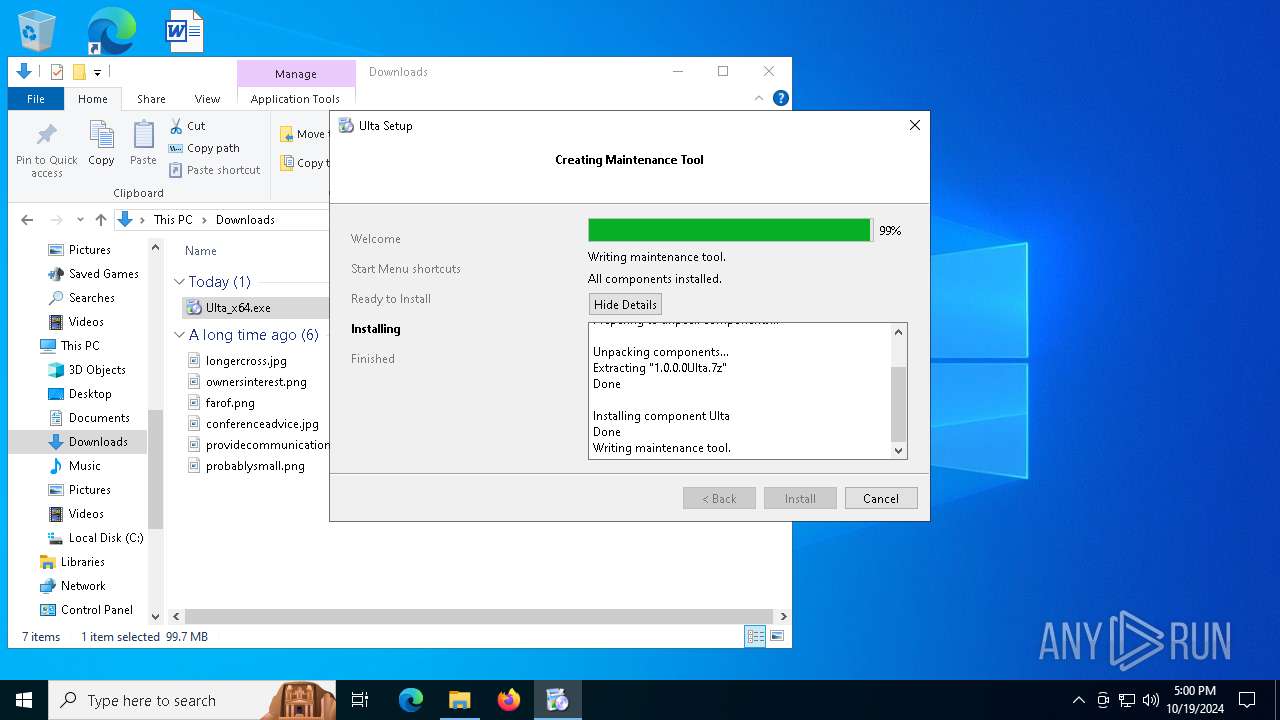
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 7536)
- Ulta_x64.exe (PID: 7252)
SUSPICIOUS
Get information on the list of running processes
- Ulta_x64.exe (PID: 8088)
Reads security settings of Internet Explorer
- Ulta_x64.exe (PID: 8088)
Reads the date of Windows installation
- Ulta_x64.exe (PID: 8088)
Application launched itself
- Ulta_x64.exe (PID: 8088)
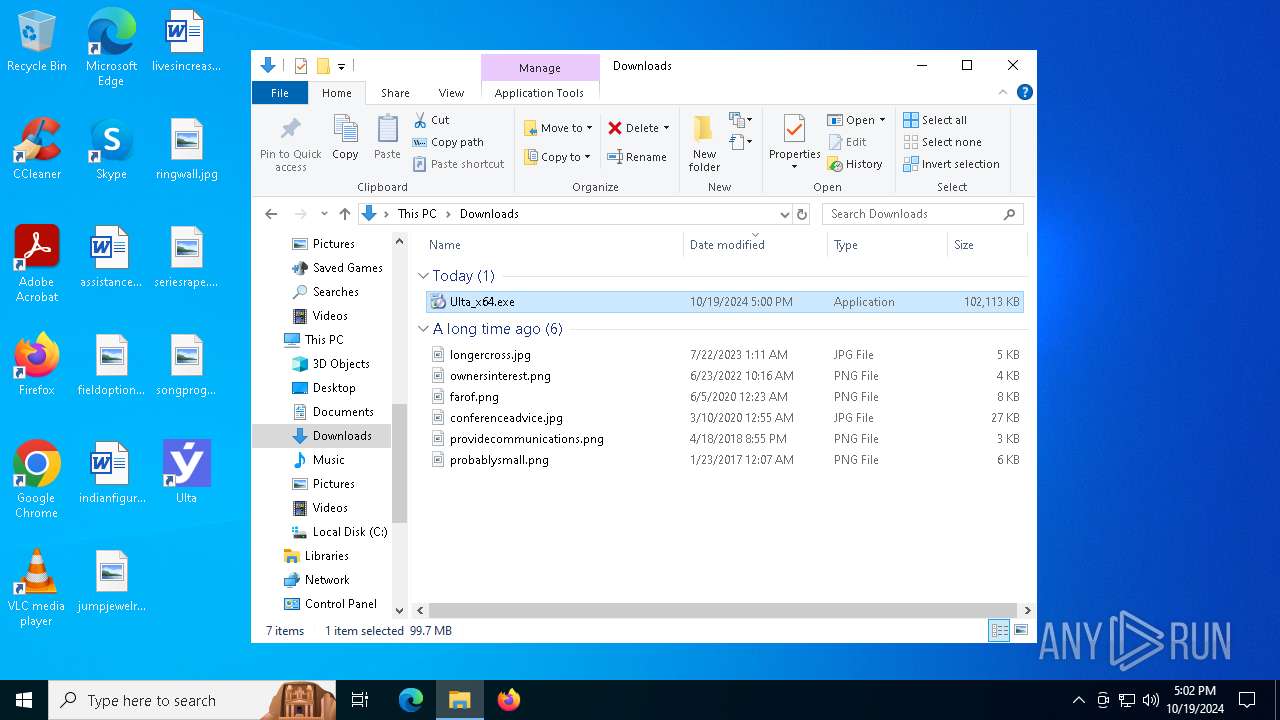
Process drops legitimate windows executable
- Ulta_x64.exe (PID: 7252)
Executing commands from ".cmd" file
- Ulta_x64.exe (PID: 7252)
Executable content was dropped or overwritten
- Ulta_x64.exe (PID: 7252)
- Ulta-service.exe (PID: 6460)
- drvinst.exe (PID: 6724)
Starts SC.EXE for service management
- Ulta_x64.exe (PID: 7252)
- cmd.exe (PID: 2432)
Starts CMD.EXE for commands execution
- Ulta_x64.exe (PID: 7252)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2432)
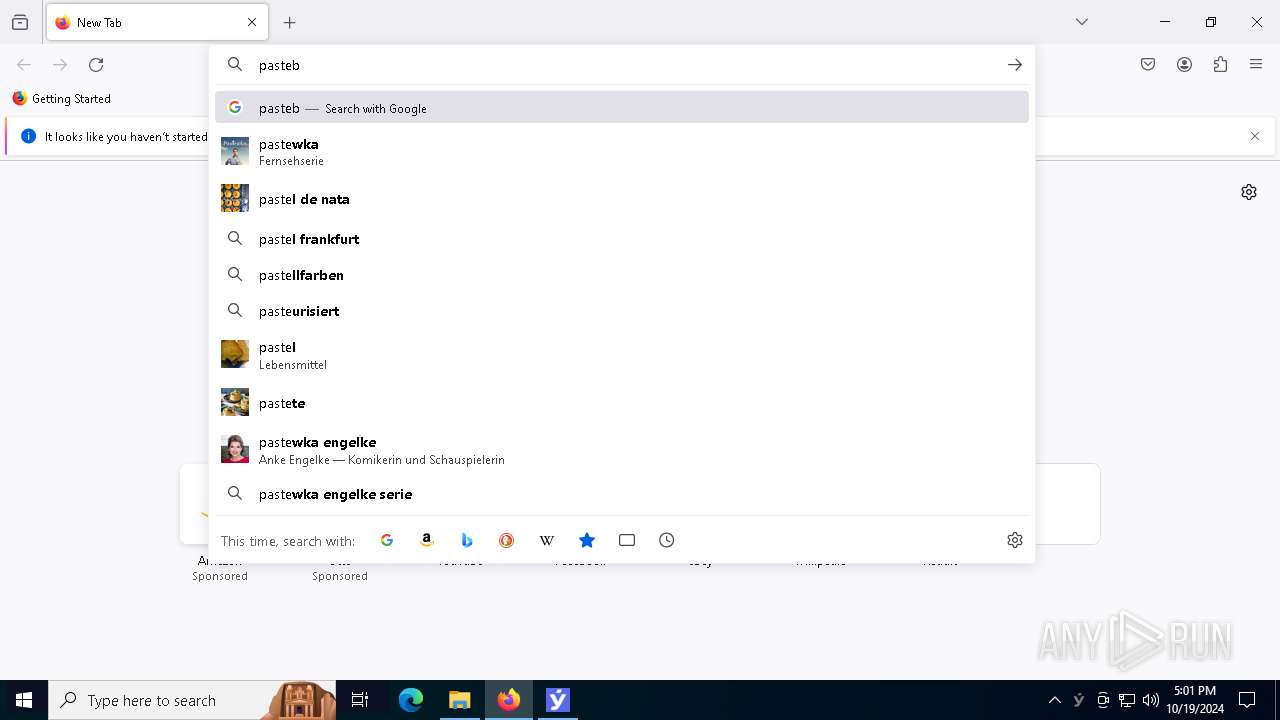
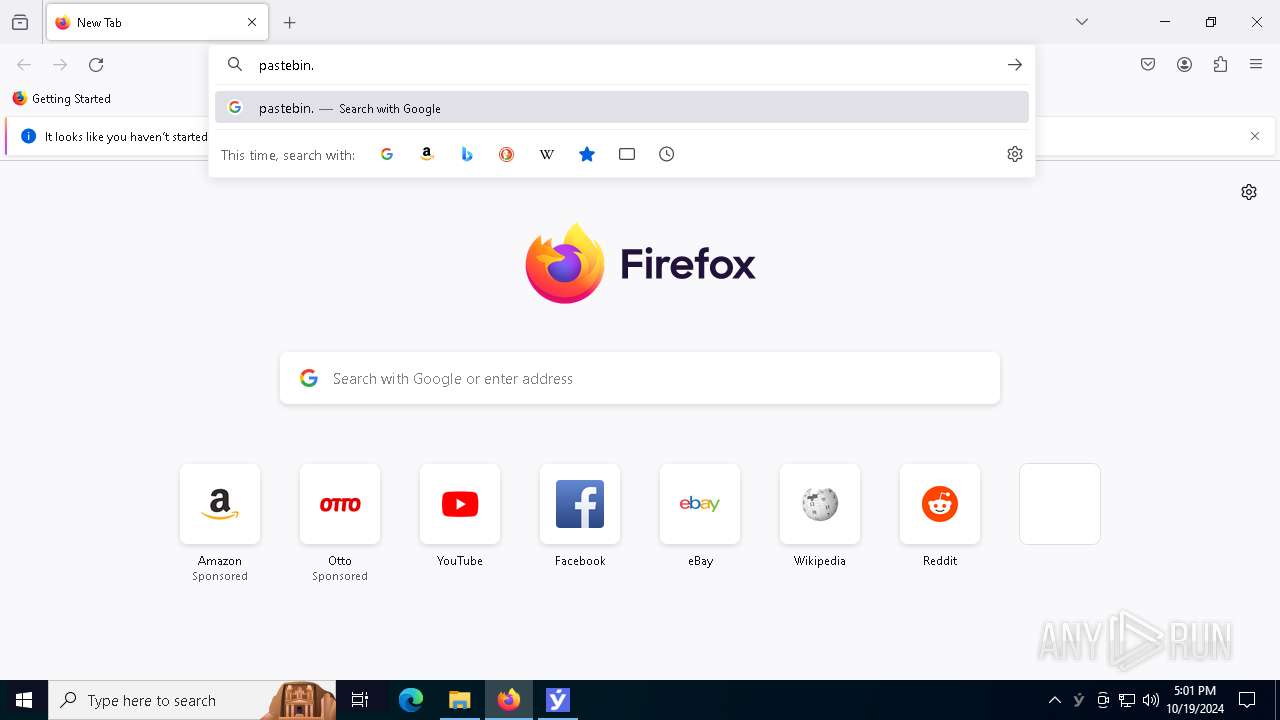
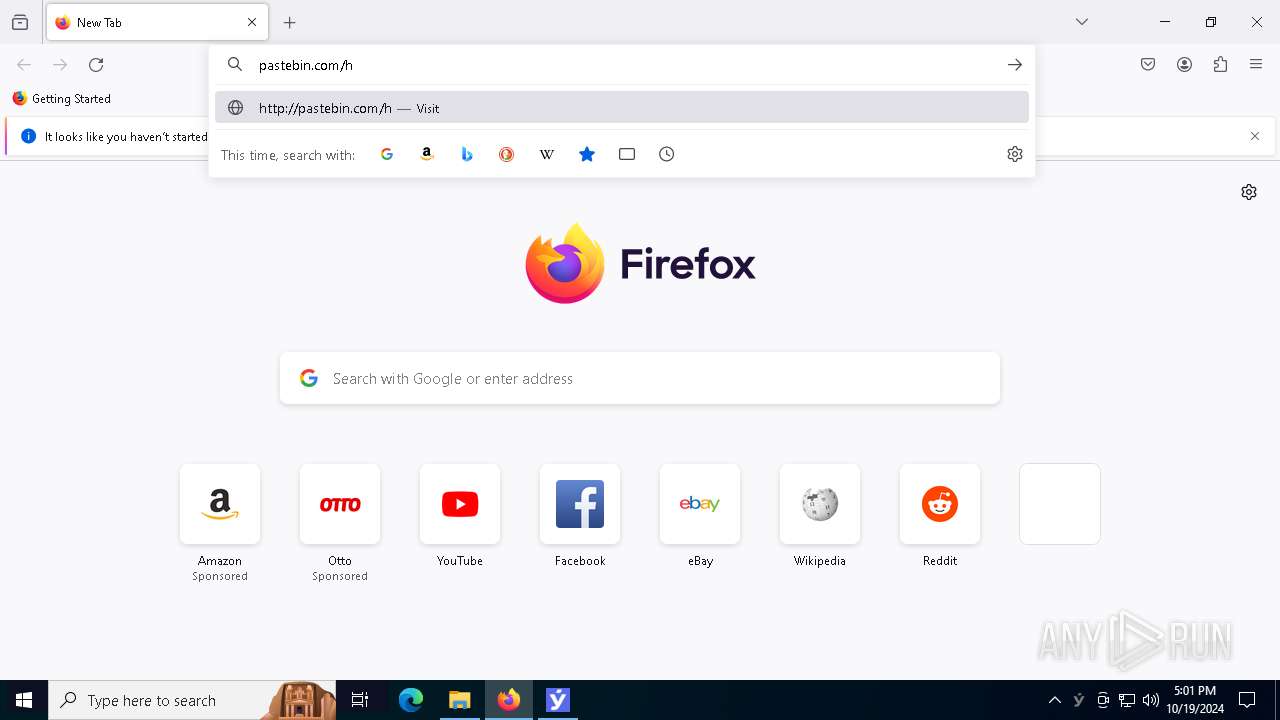
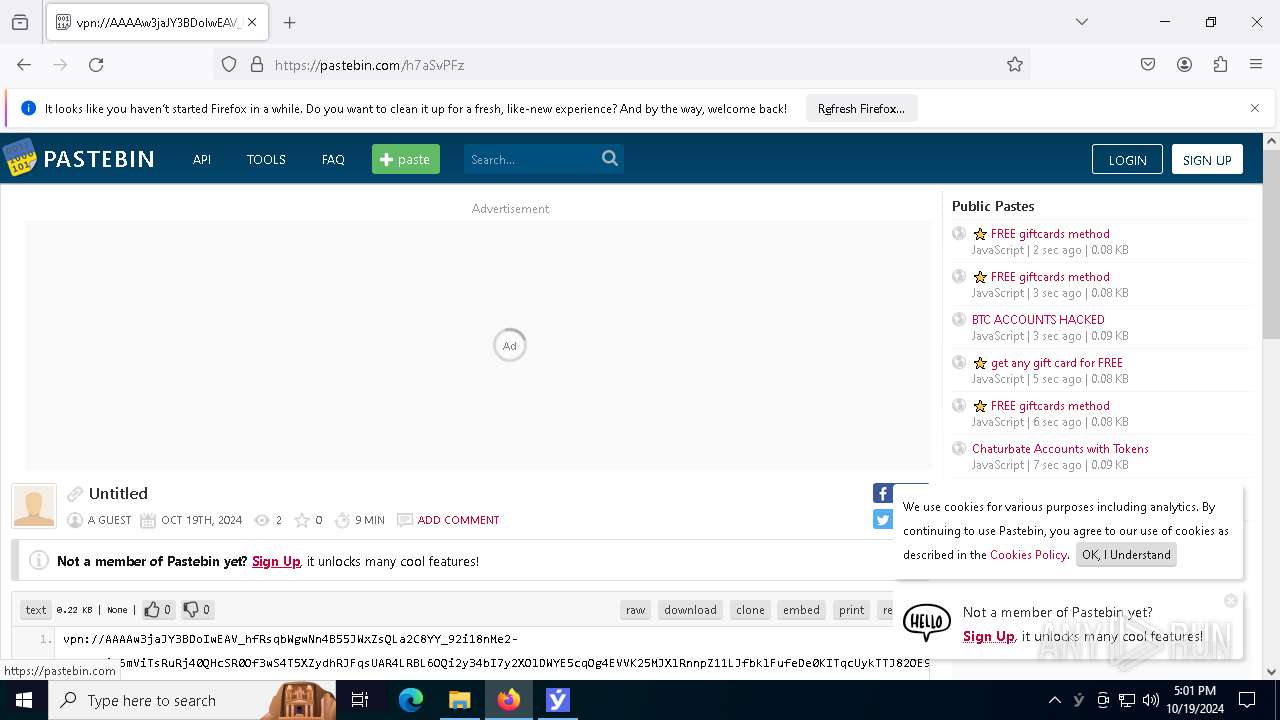
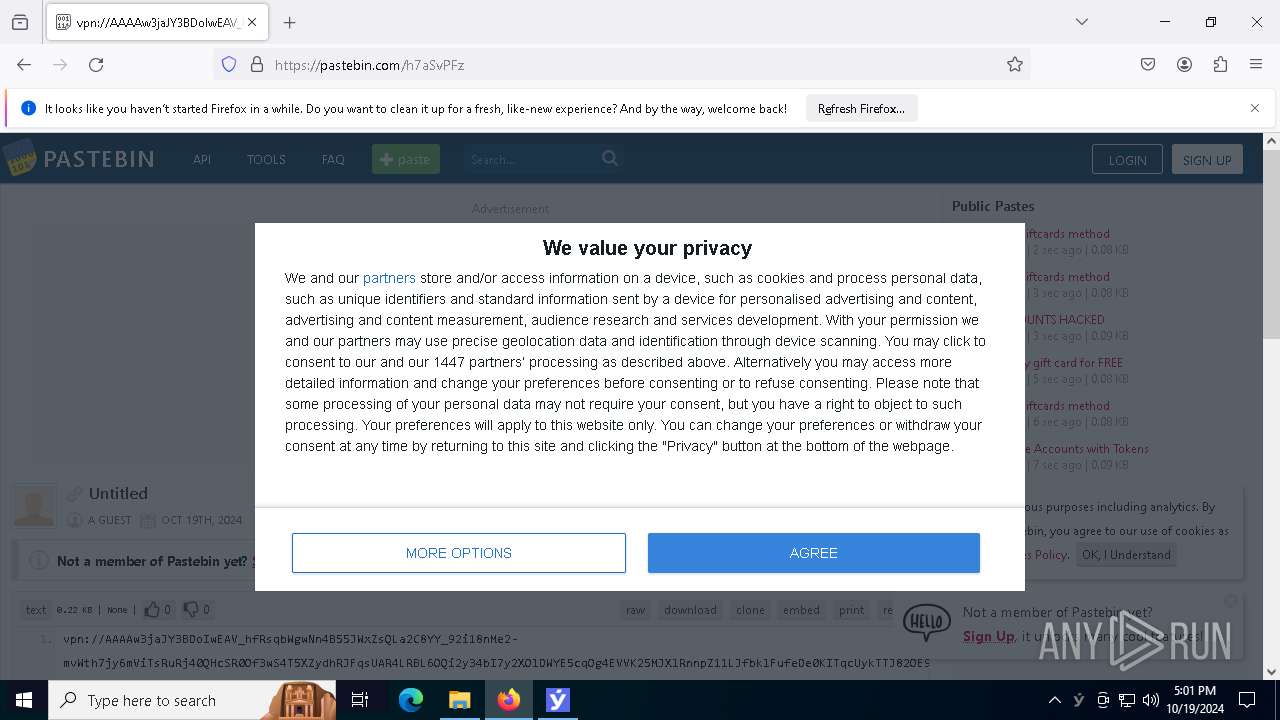
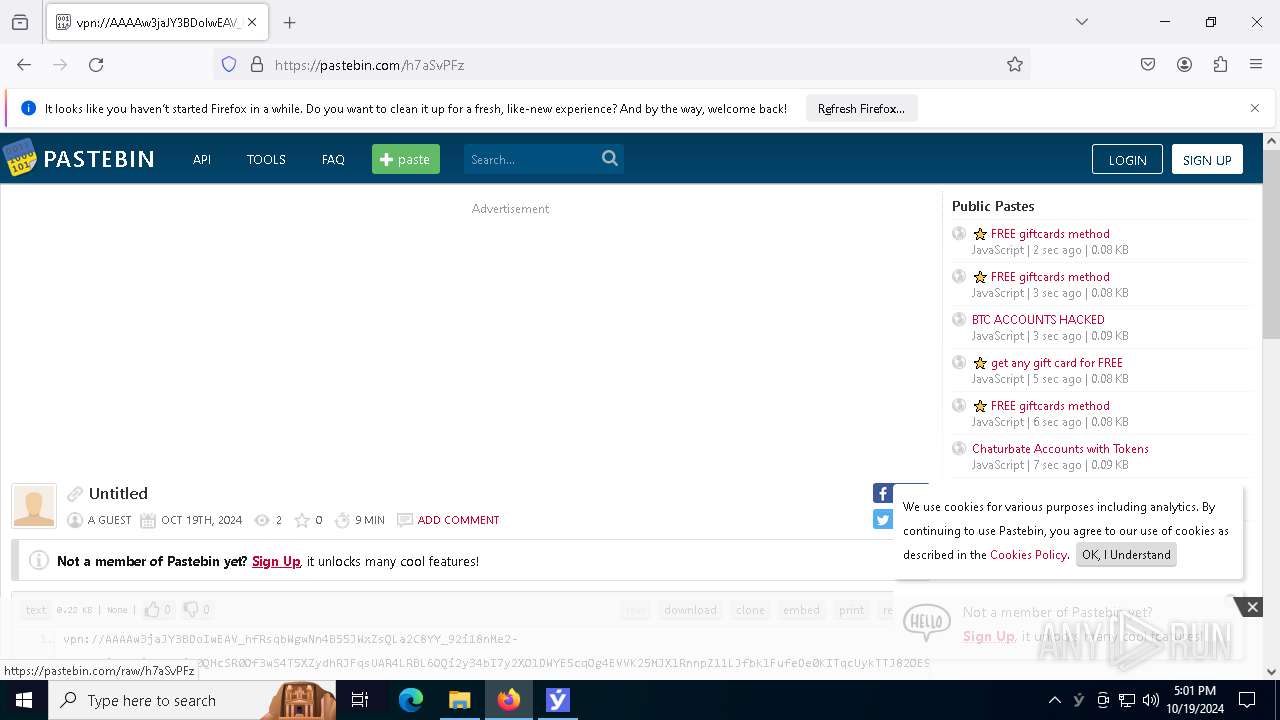
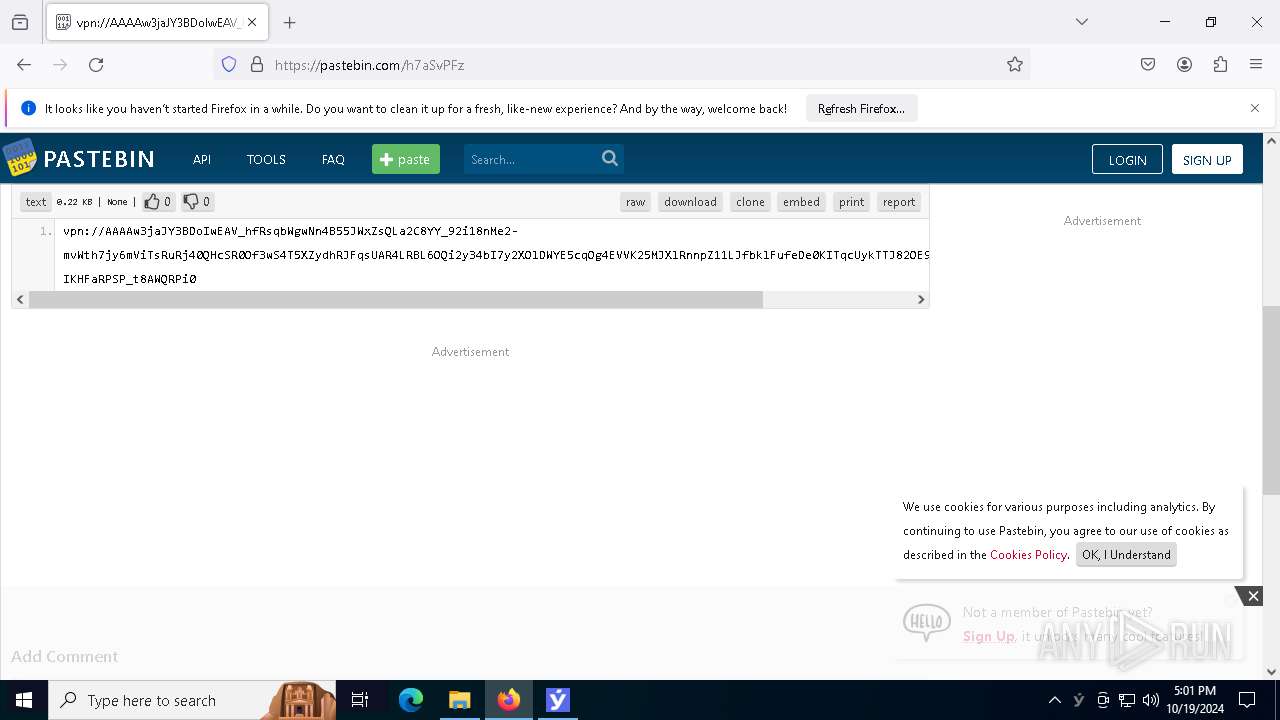
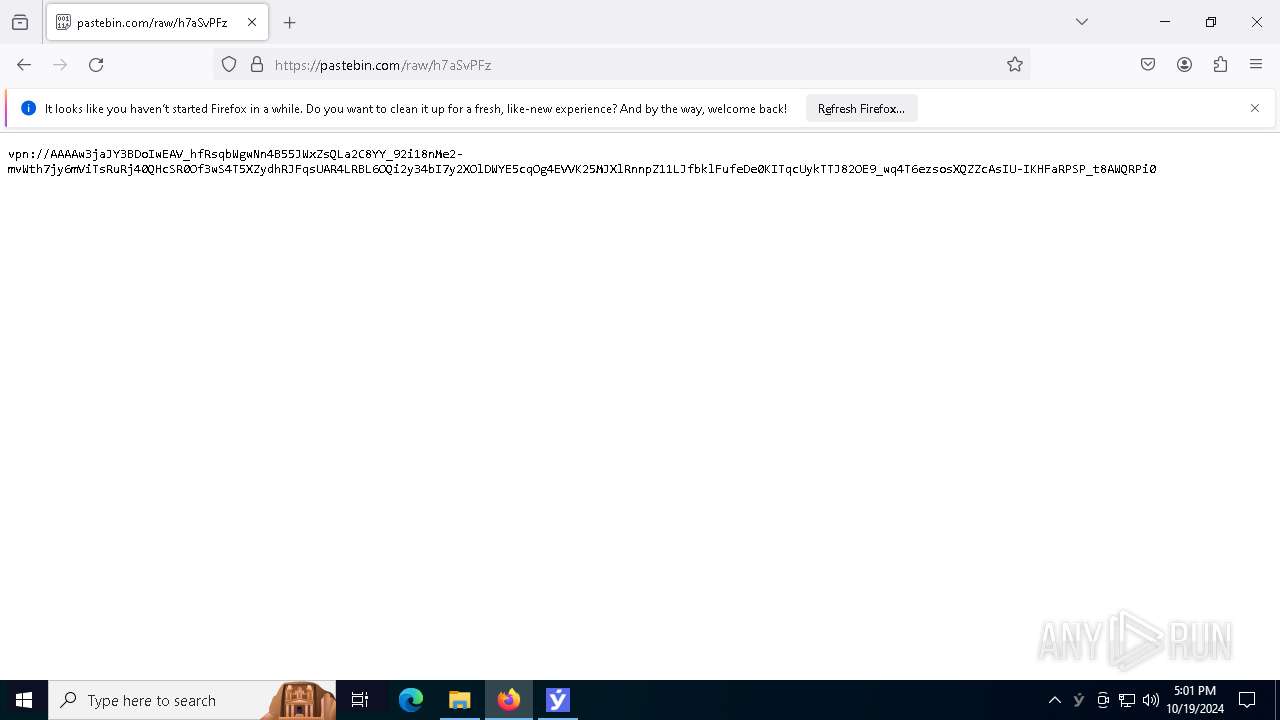
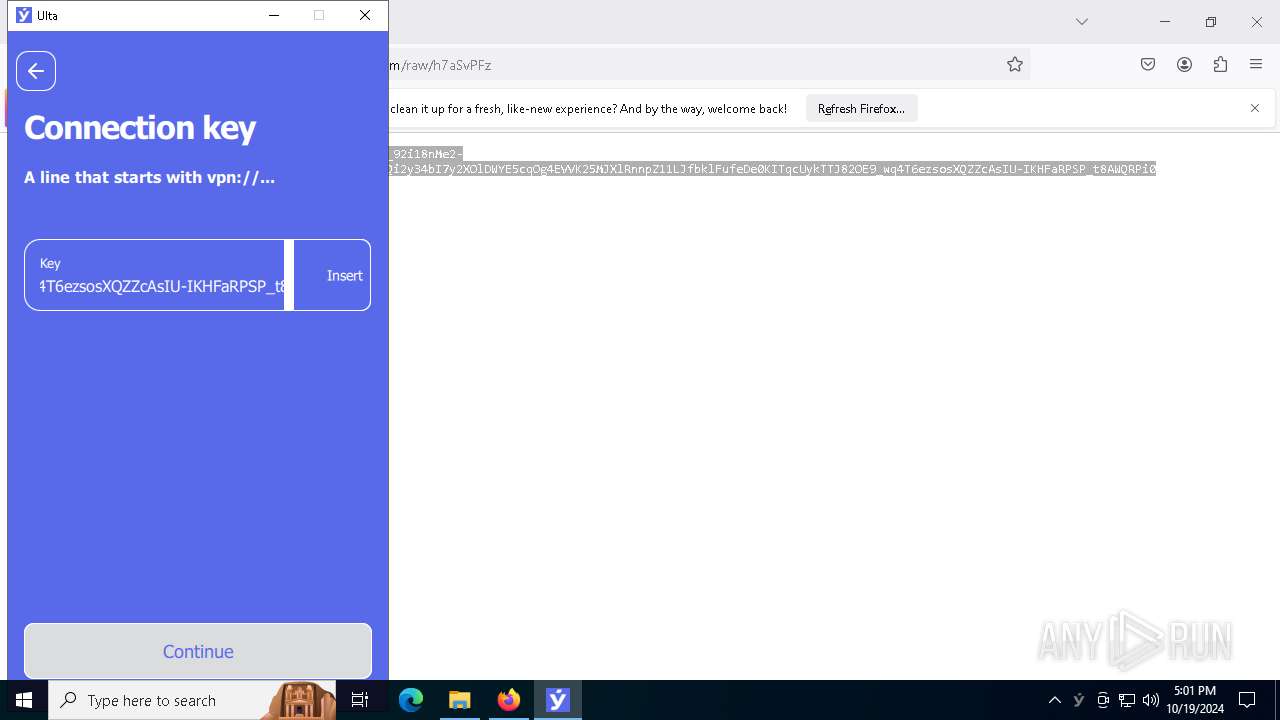
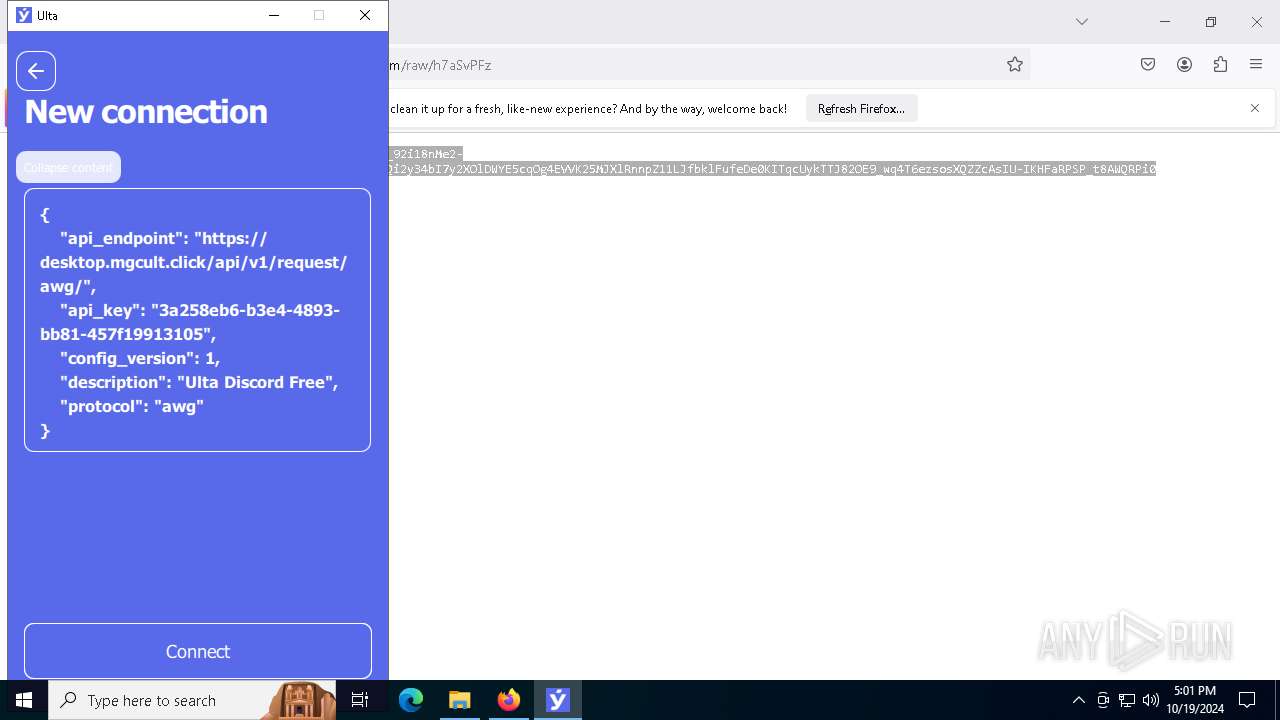
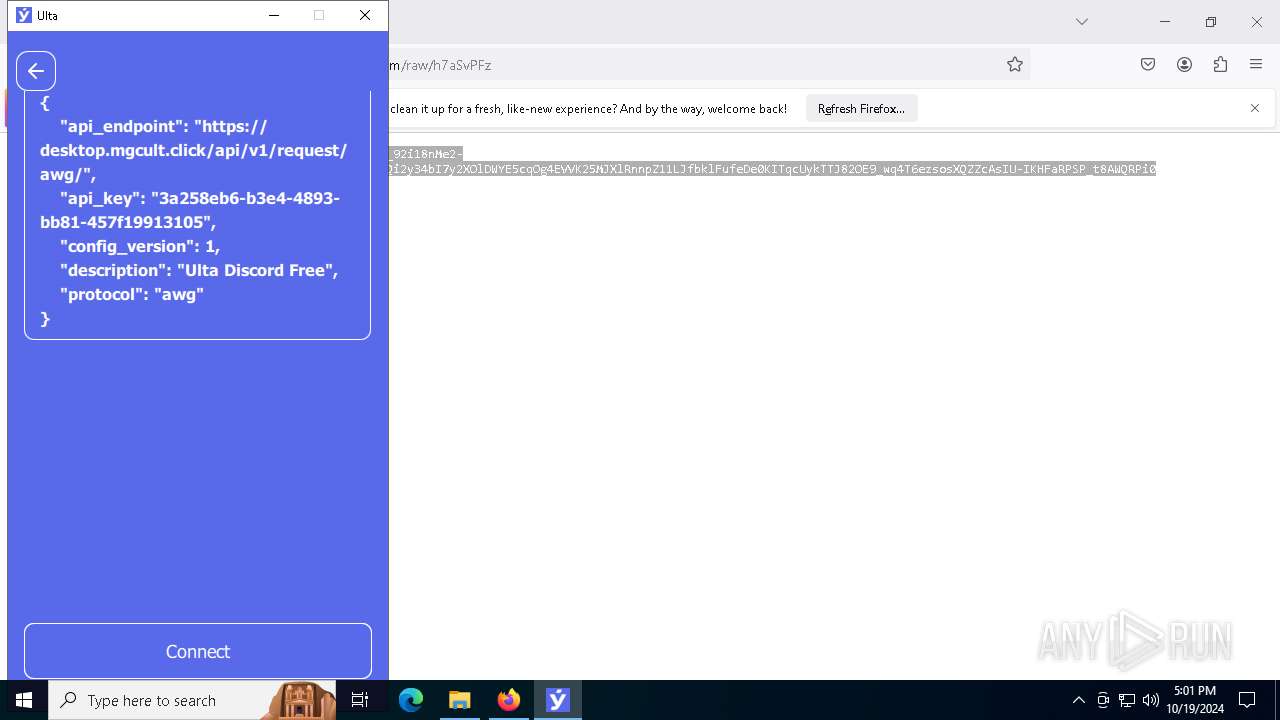
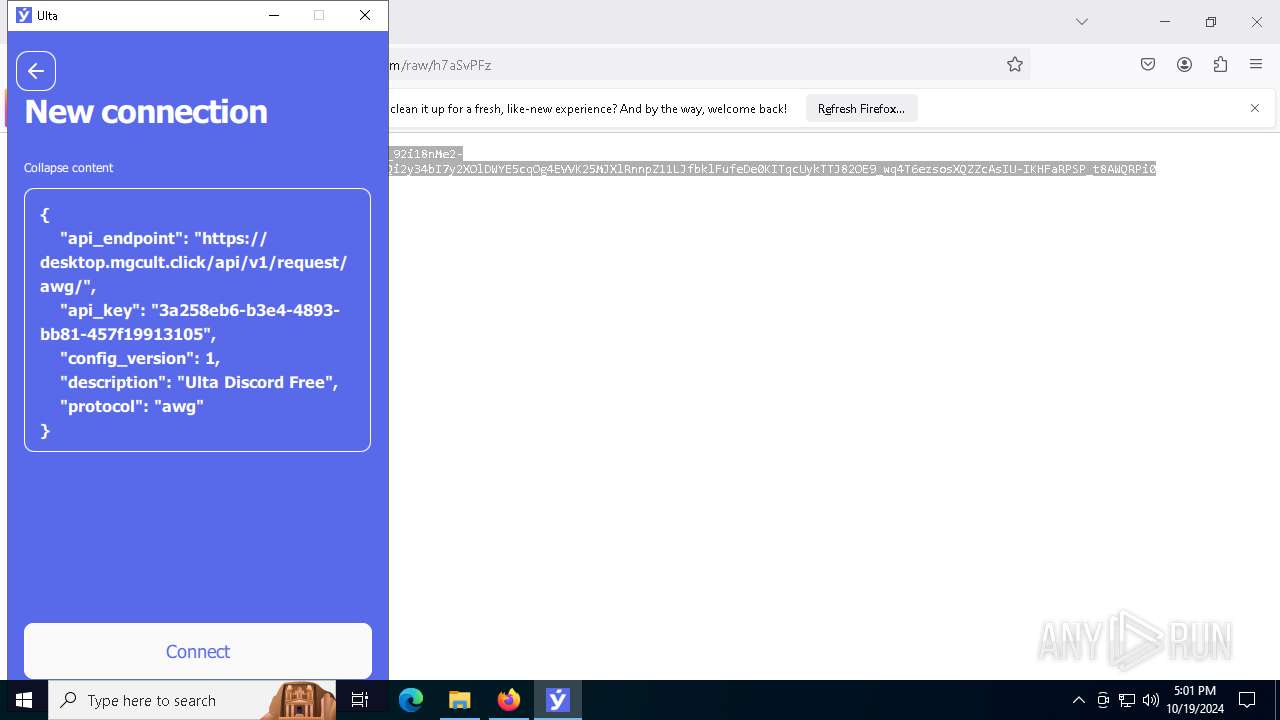
Requests information from PasteBin
- firefox.exe (PID: 3864)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 6724)
- Ulta-service.exe (PID: 6460)
- Ulta_x64.exe (PID: 7252)
Executes as Windows Service
- Ulta-service.exe (PID: 6460)
- Ulta-service.exe (PID: 5232)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1064)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 1156)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4616)
Creates files or folders in the user directory
- explorer.exe (PID: 4616)
- Ulta_x64.exe (PID: 8088)
Application launched itself
- chrome.exe (PID: 1156)
- firefox.exe (PID: 7928)
- firefox.exe (PID: 3864)
Reads the software policy settings
- explorer.exe (PID: 4616)
Checks supported languages
- Ulta_x64.exe (PID: 8088)
Checks proxy server information
- explorer.exe (PID: 4616)
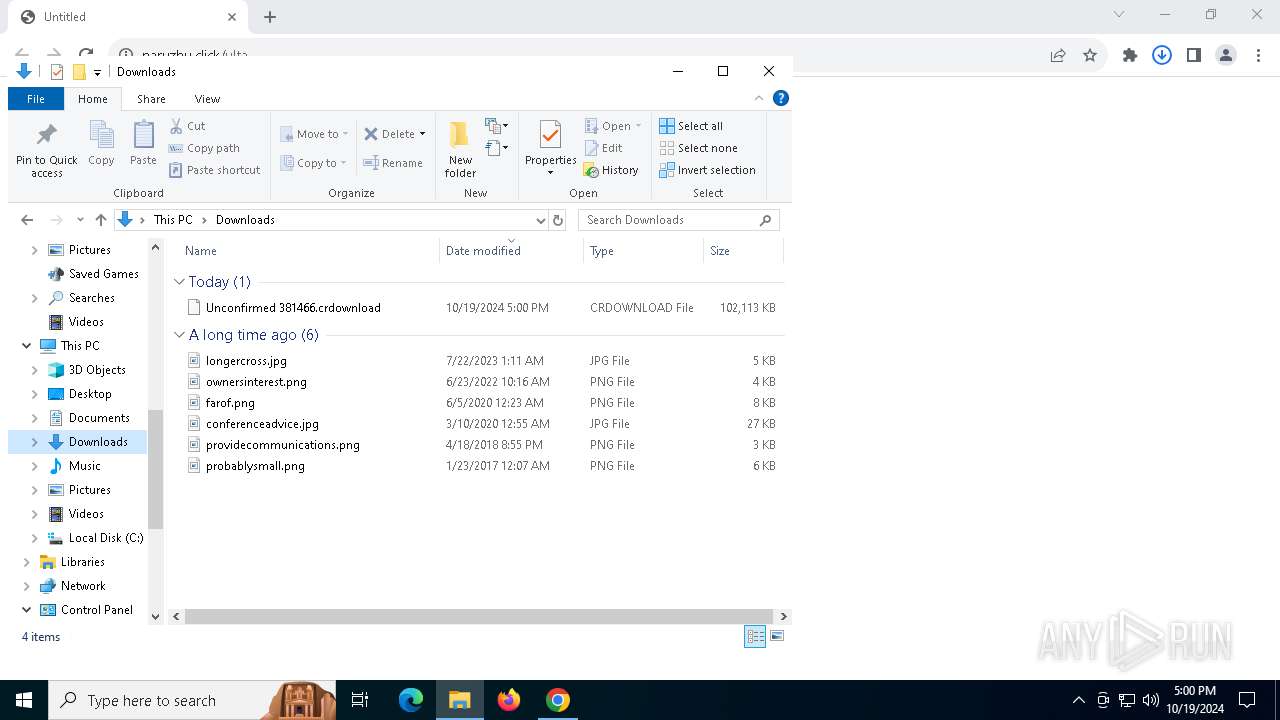
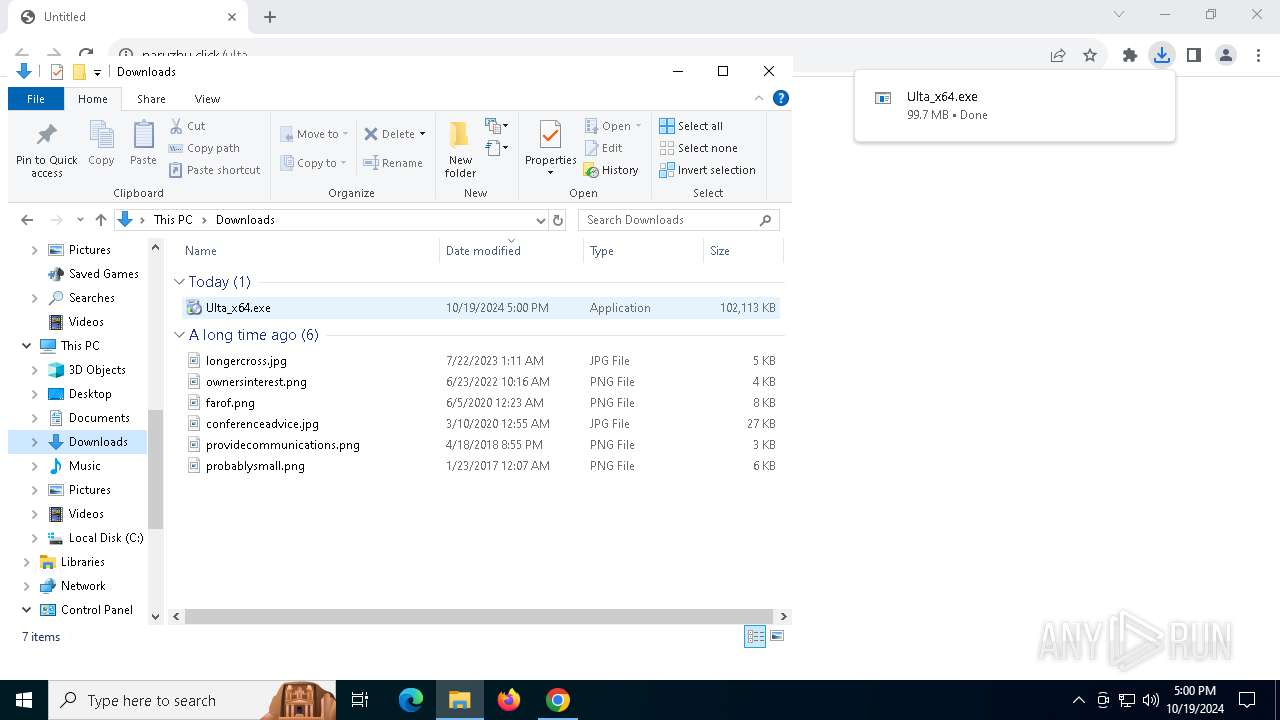
The process uses the downloaded file
- chrome.exe (PID: 7808)
- explorer.exe (PID: 4616)
- Ulta_x64.exe (PID: 8088)
Reads the computer name
- Ulta_x64.exe (PID: 8088)
Reads the machine GUID from the registry
- Ulta_x64.exe (PID: 8088)
Create files in a temporary directory
- Ulta_x64.exe (PID: 8088)
Process checks whether UAC notifications are on
- Ulta_x64.exe (PID: 8088)
Process checks computer location settings
- Ulta_x64.exe (PID: 8088)
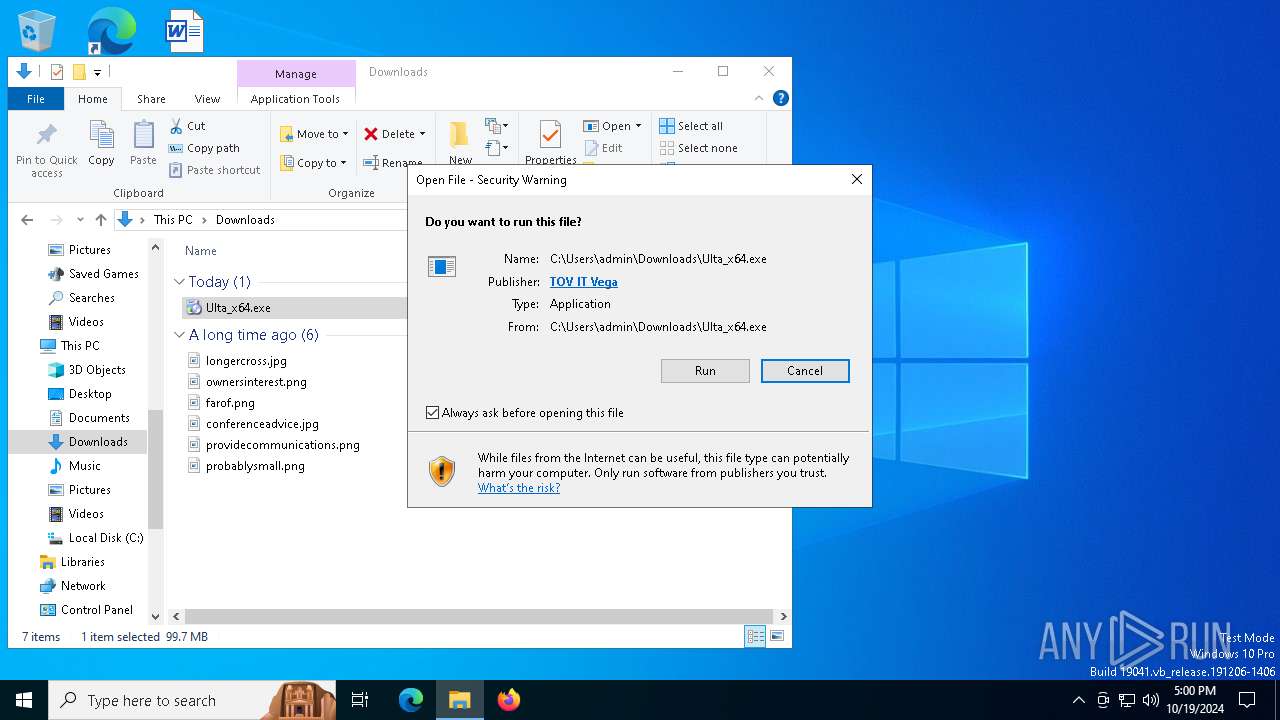
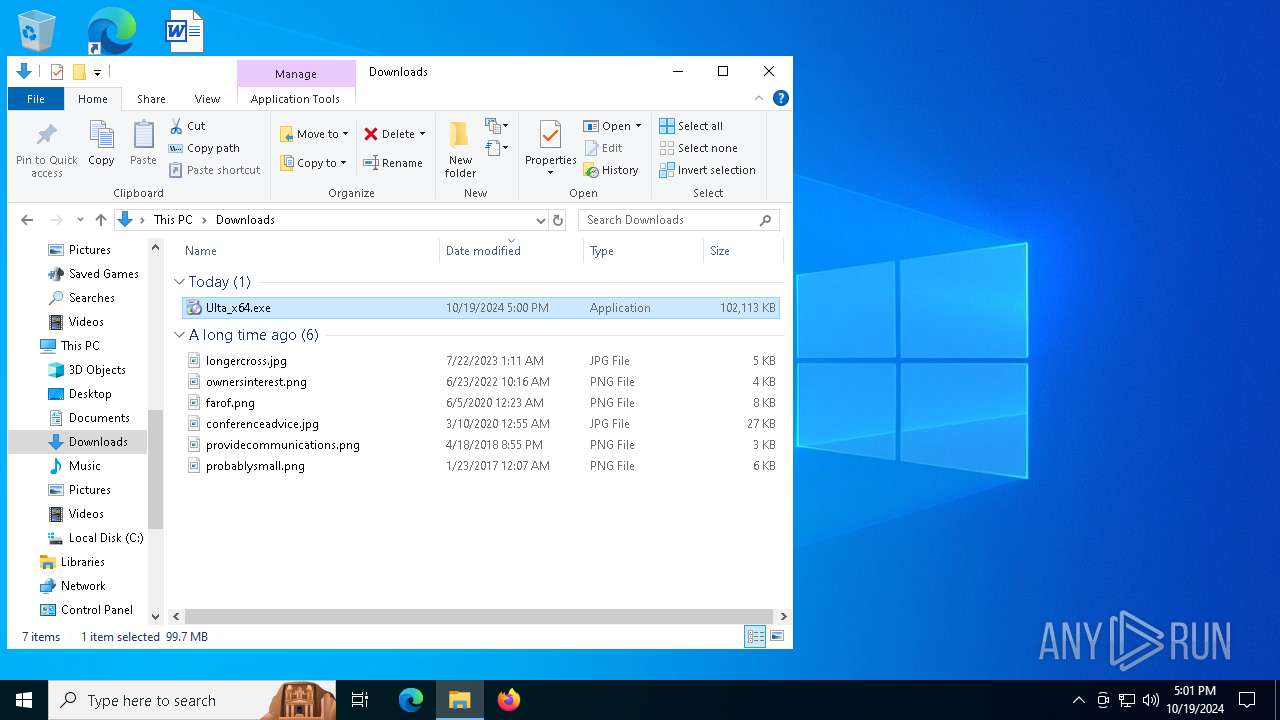
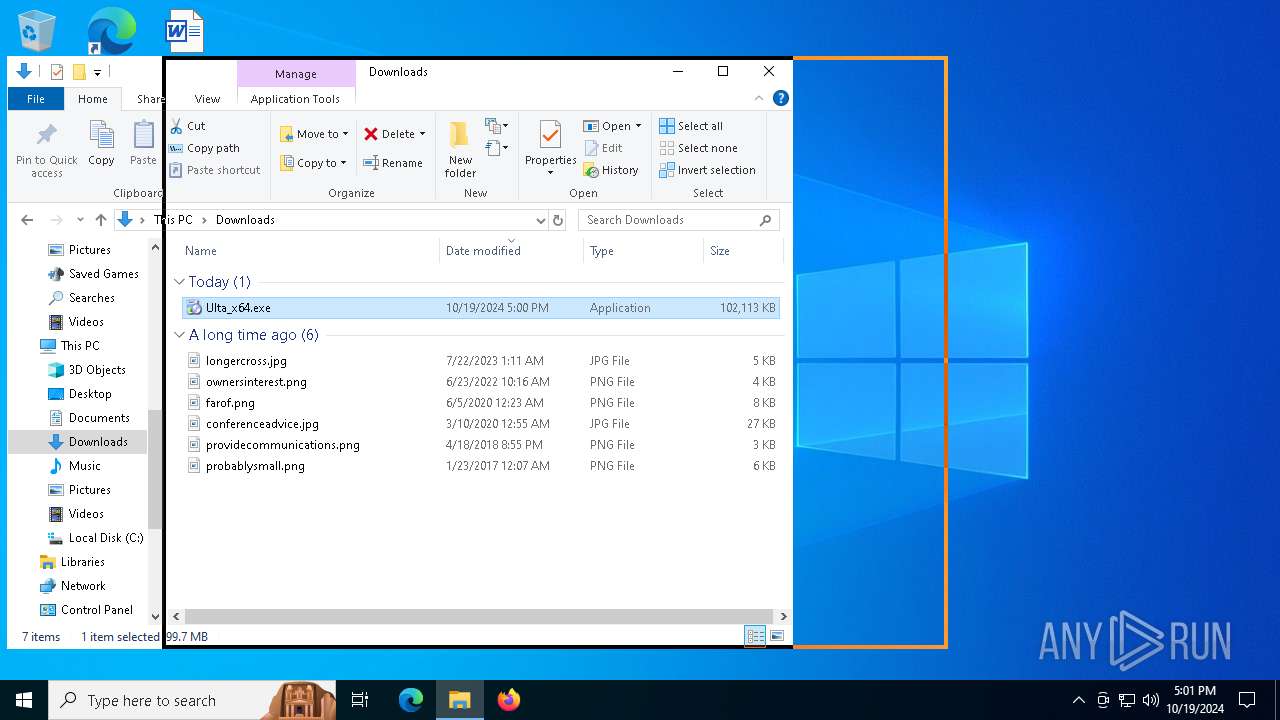
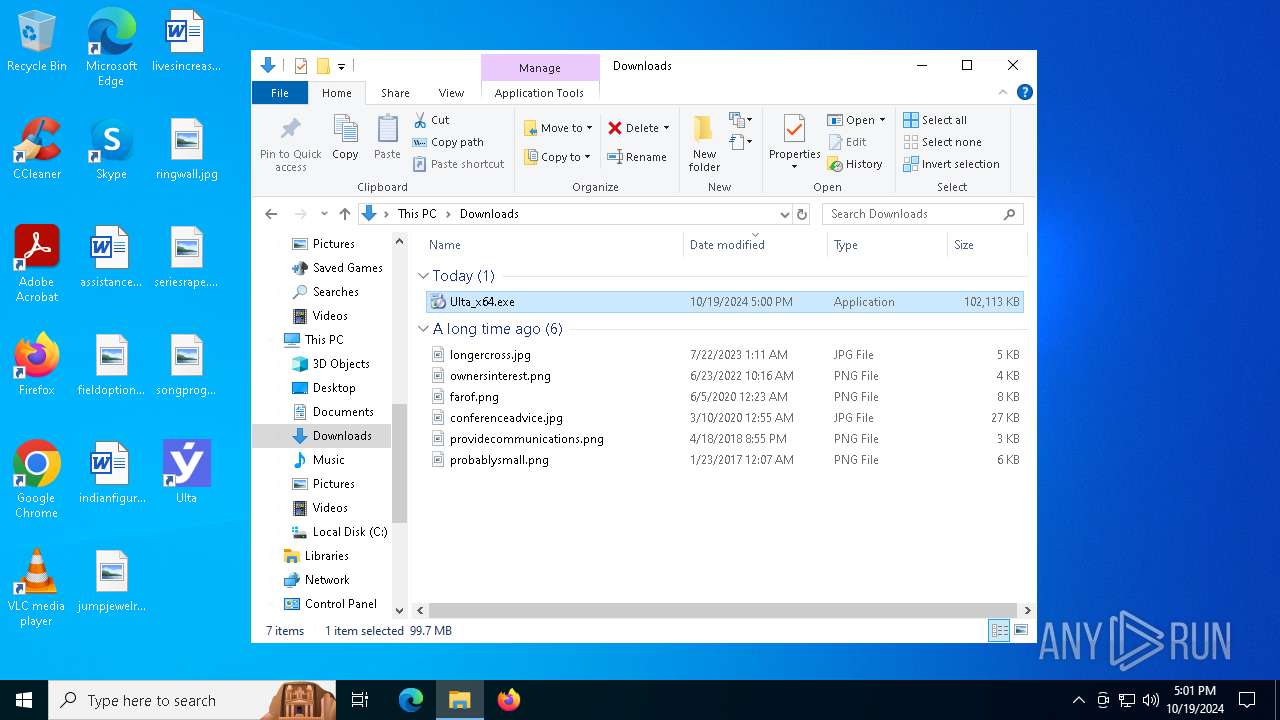
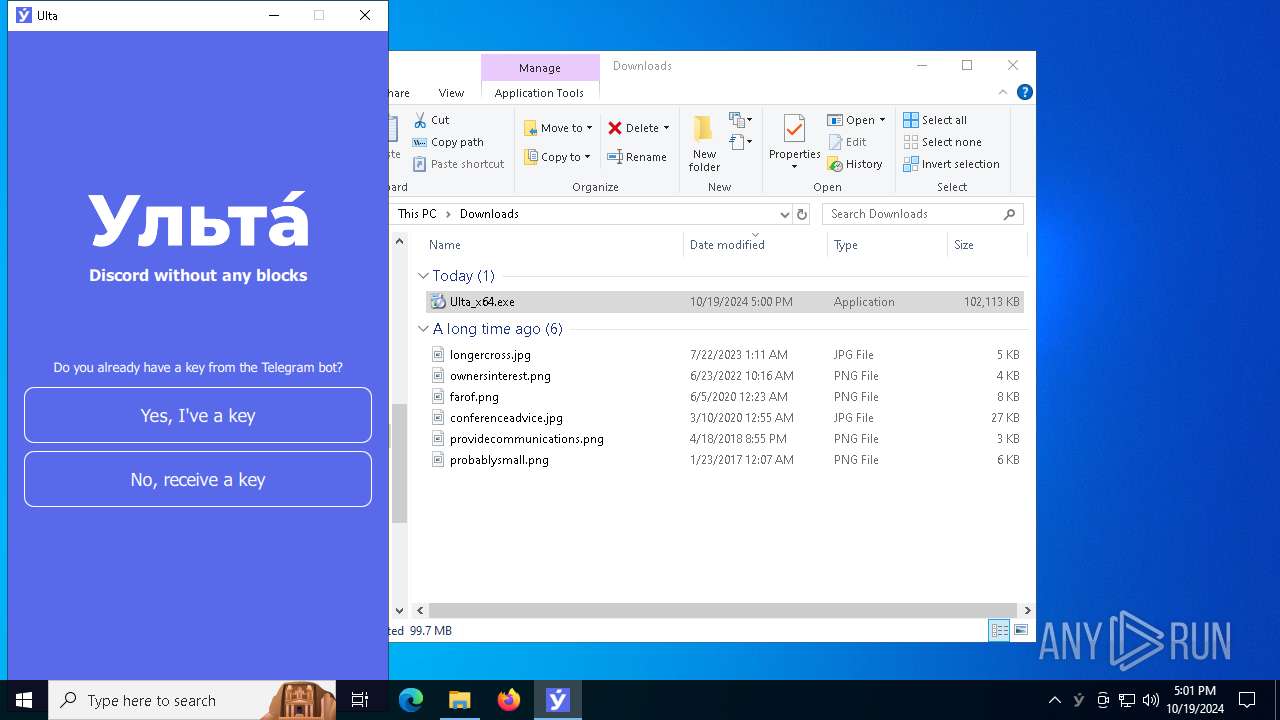
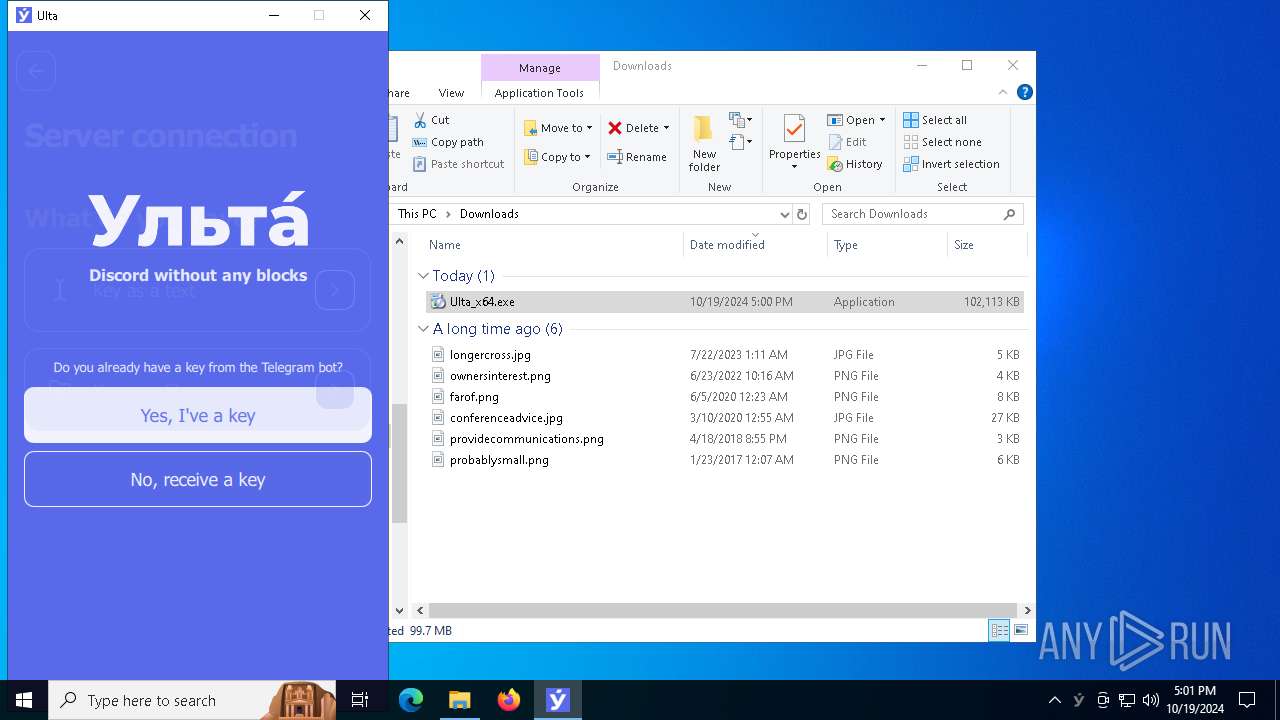
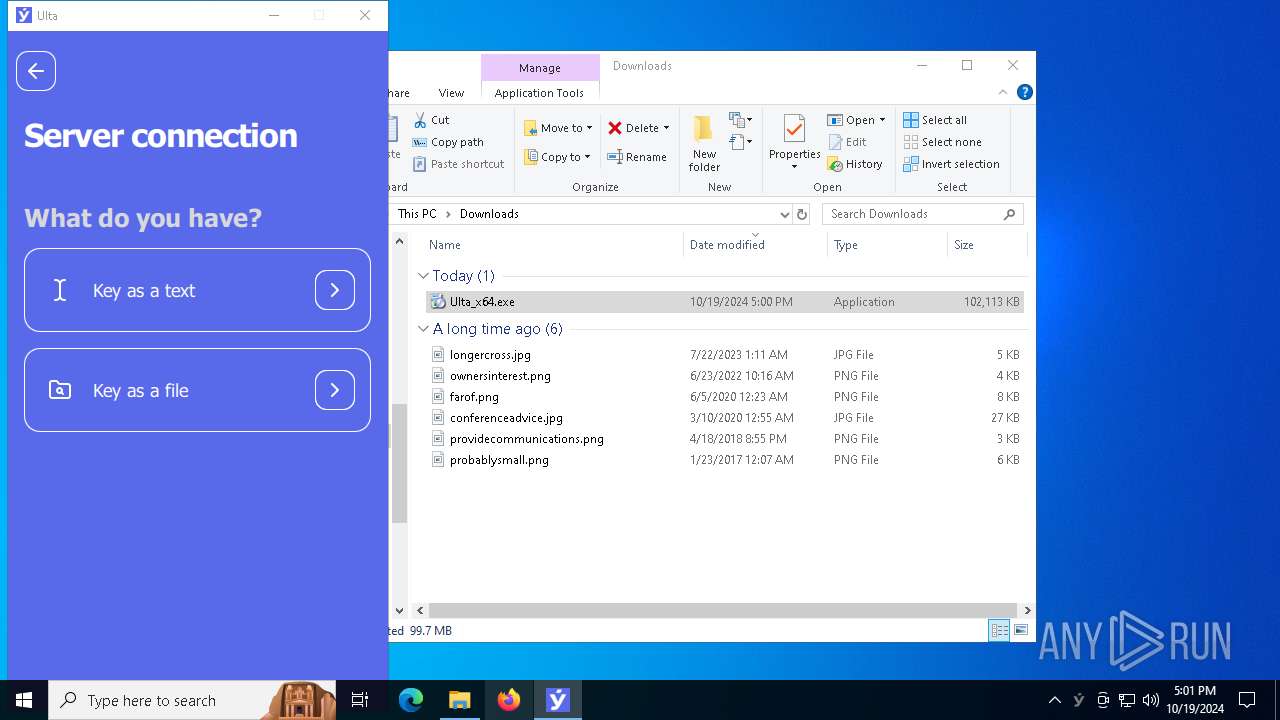
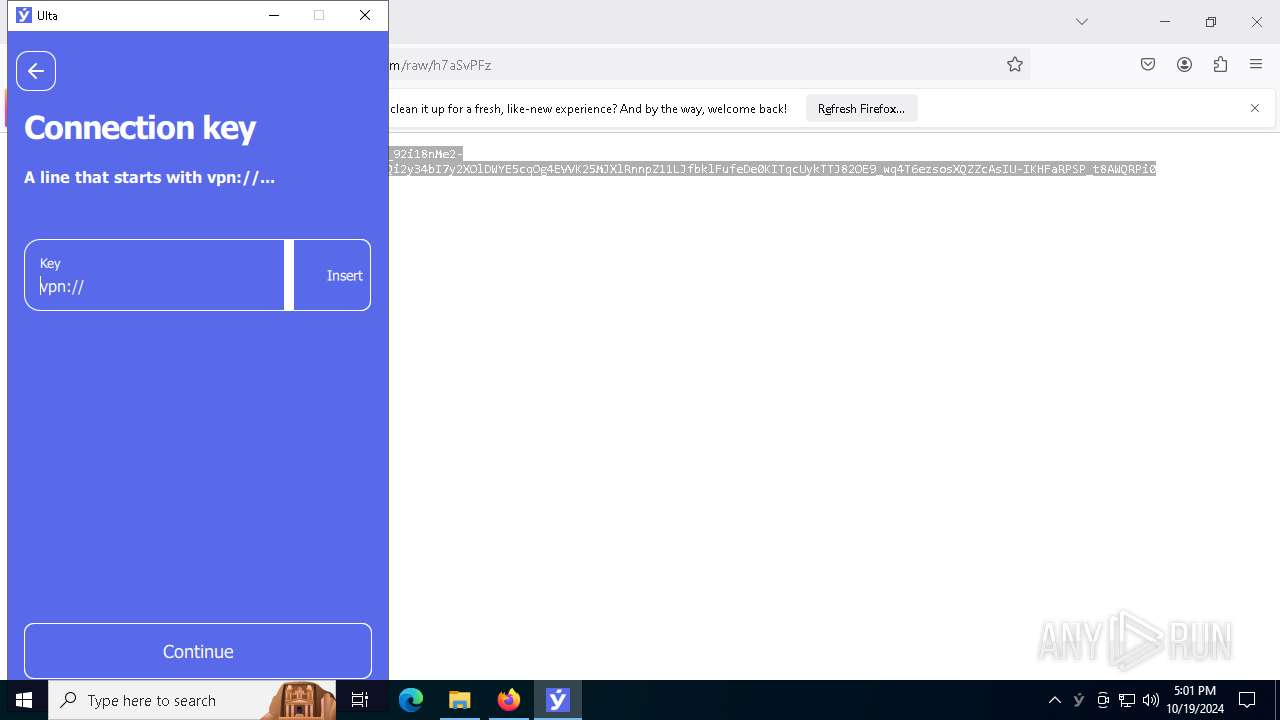
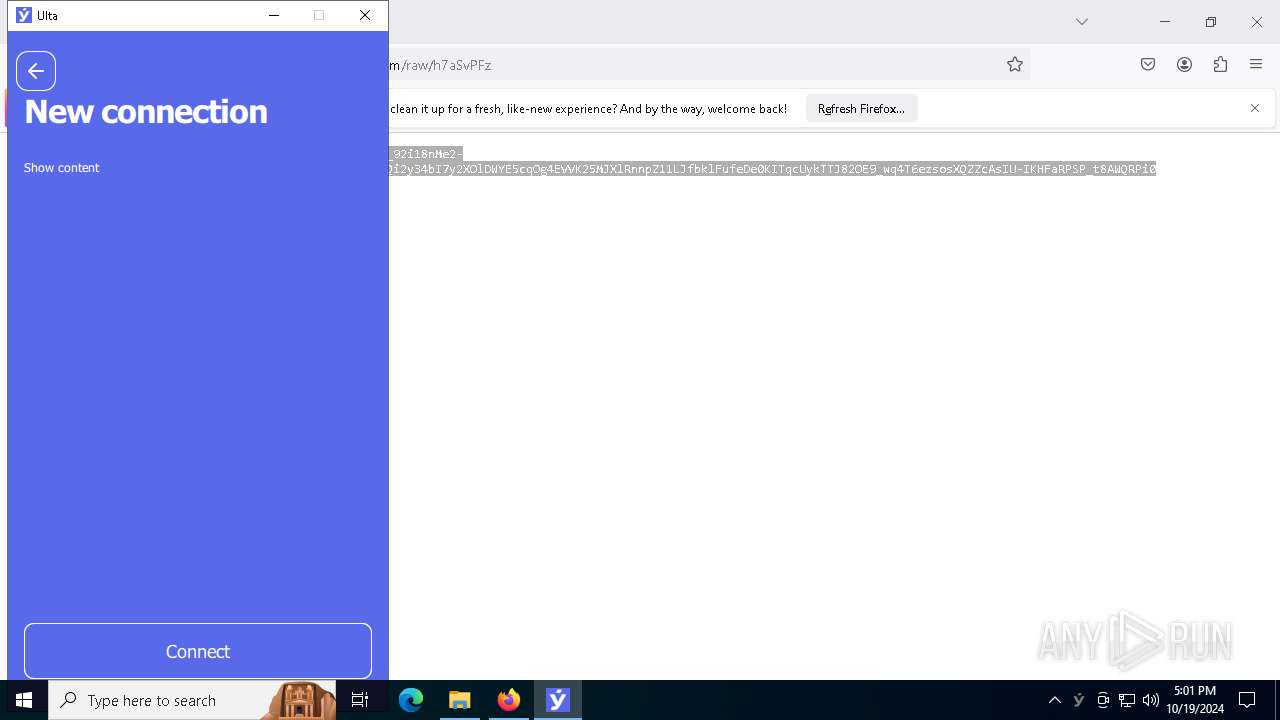
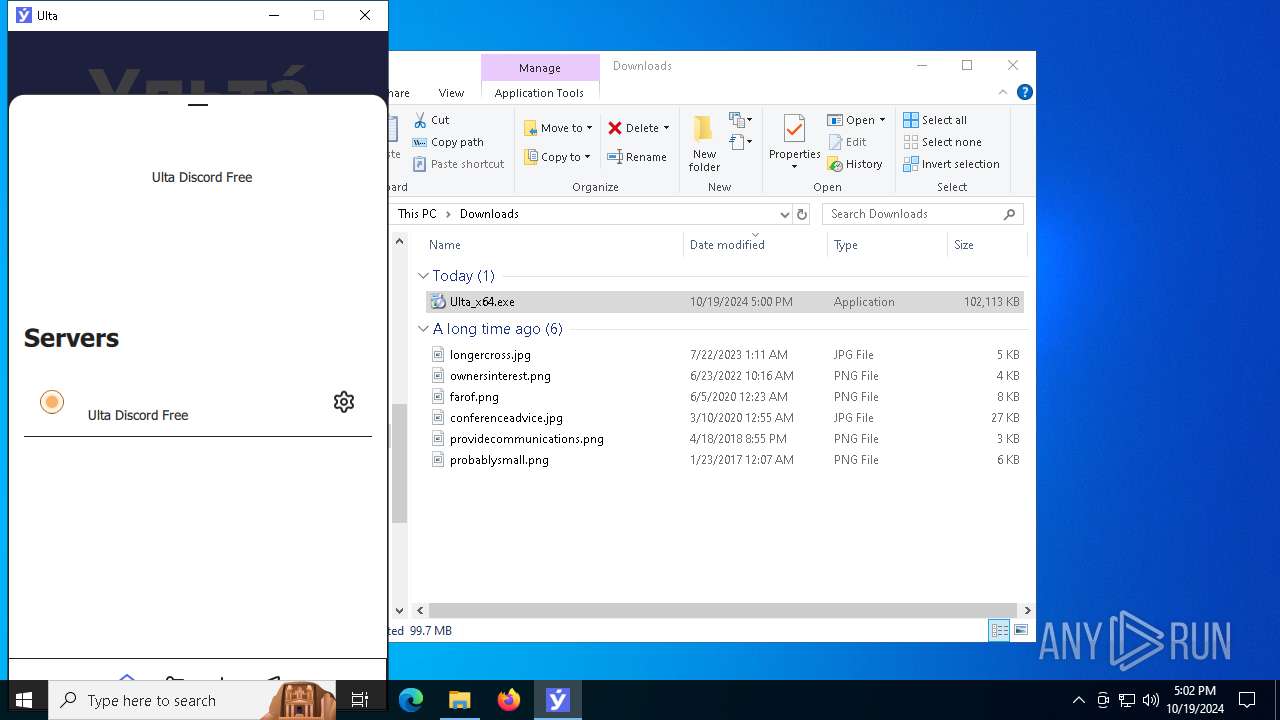
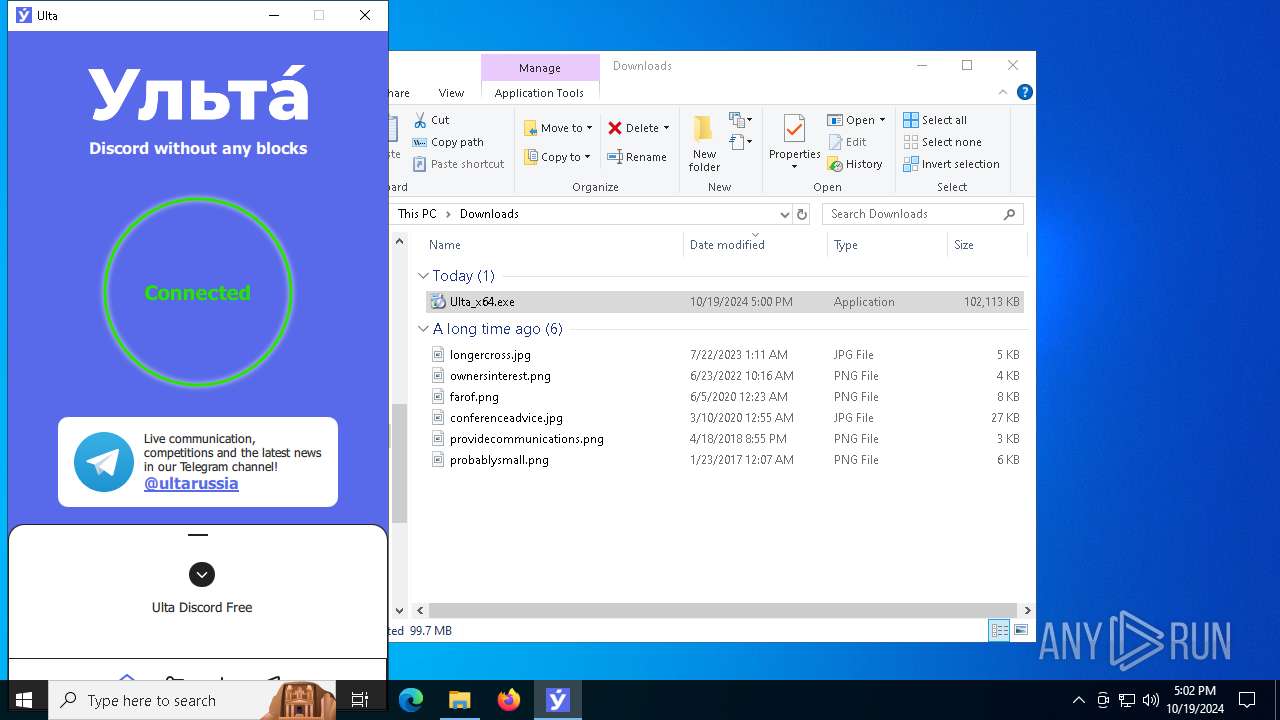
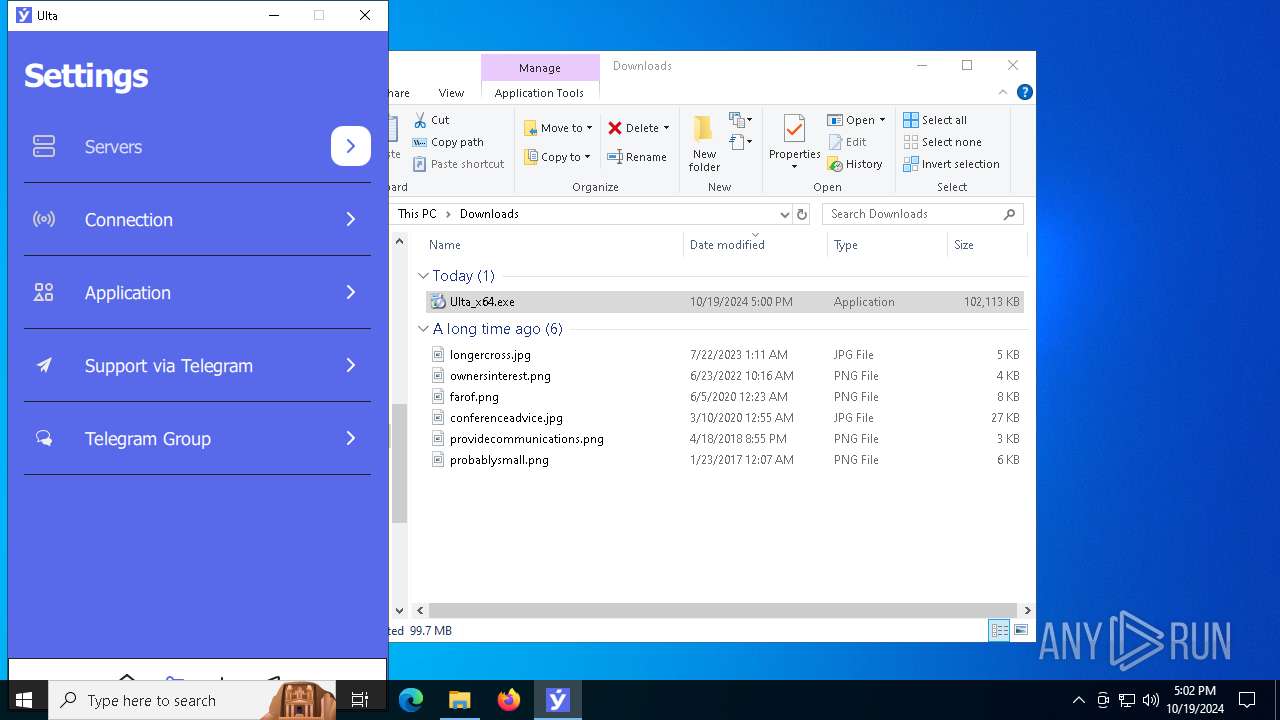
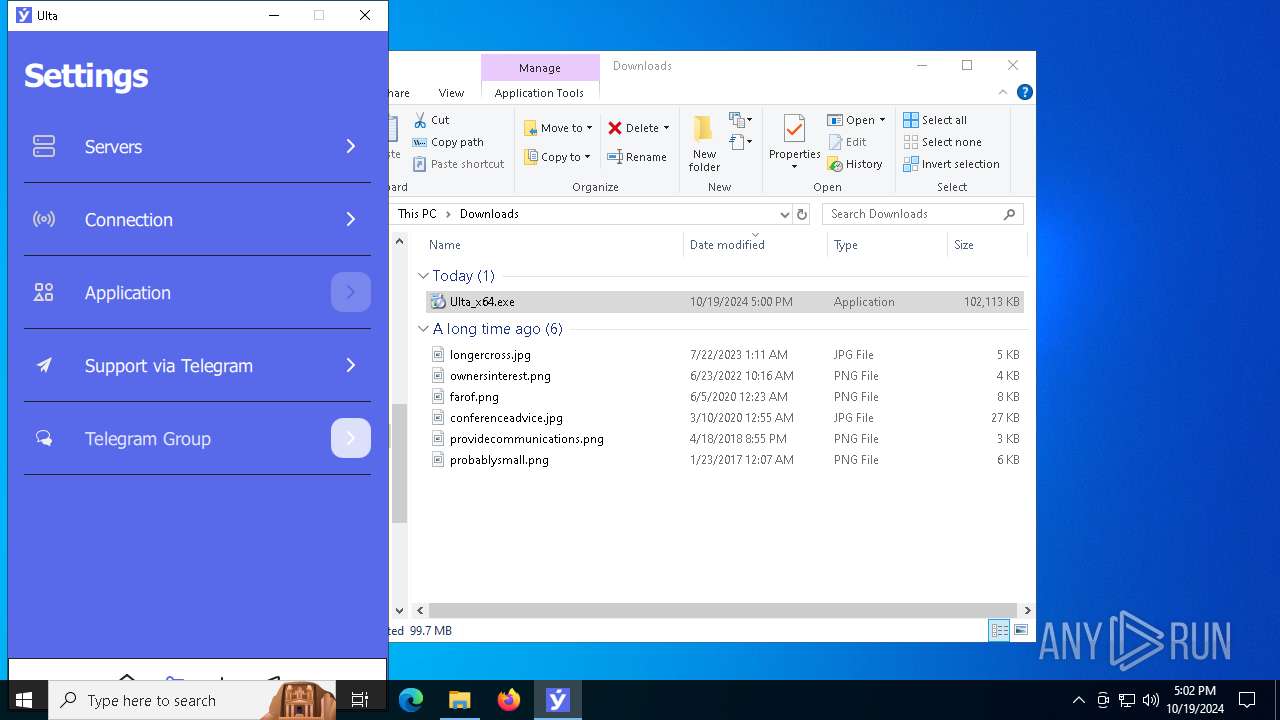
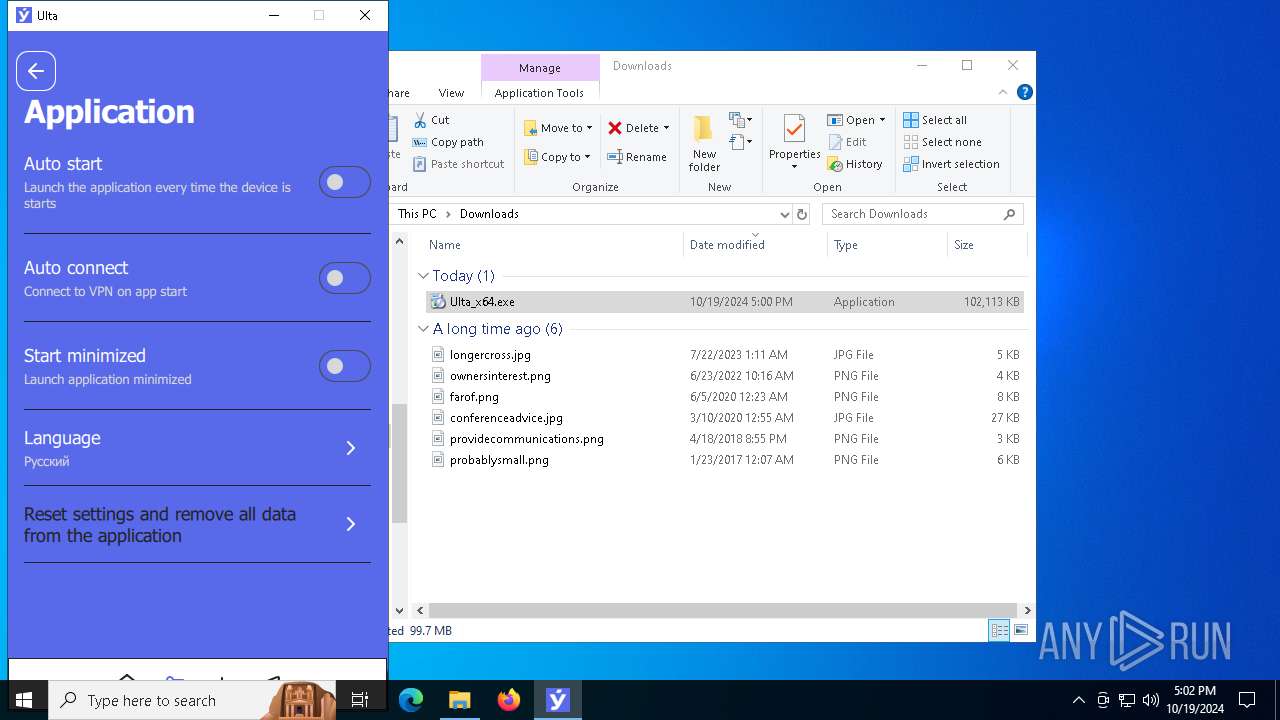
Manual execution by a user
- Ulta.exe (PID: 5144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
326
Monitored processes
52
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2280 -parentBuildID 20240213221259 -prefsHandle 2272 -prefMapHandle 2184 -prefsLen 30705 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {924a6864-8bdf-4d07-b147-f41316f4ccc8} 3864 "\\.\pipe\gecko-crash-server-pipe.3864" 21900e80f10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) | |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://naruzhu.click/ulta" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4588 -childID 2 -isForBrowser -prefsHandle 4576 -prefMapHandle 4580 -prefsLen 36339 -prefMapSize 244343 -jsInitHandle 1452 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c9594058-b439-4365-a718-856071eb791c} 3864 "\\.\pipe\gecko-crash-server-pipe.3864" 21913f23690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2432 | cmd /c "C:\\Program Files\Ulta\post_install.cmd" | C:\Windows\System32\cmd.exe | — | Ulta_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5720 -childID 3 -isForBrowser -prefsHandle 5692 -prefMapHandle 5724 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1452 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0be85c22-c3f2-43df-bef8-cf617b23780b} 3864 "\\.\pipe\gecko-crash-server-pipe.3864" 219189d5850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2968 -childID 1 -isForBrowser -prefsHandle 2960 -prefMapHandle 2956 -prefsLen 31121 -prefMapSize 244343 -jsInitHandle 1452 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f301e270-9151-4a2f-9728-82ef9503ee91} 3864 "\\.\pipe\gecko-crash-server-pipe.3864" 21913152150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4616 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1073807364 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5144 | "C:\Program Files\Ulta\Ulta.exe" | C:\Program Files\Ulta\Ulta.exe | — | explorer.exe | |||||||||||
User: admin Company: Ulta Integrity Level: MEDIUM Description: Ulta Version: 1.0.0.0 | |||||||||||||||
Total events
48 396
Read events
48 198
Write events
180
Delete events
18
Modification events
| (PID) Process: | (4616) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050240 |
| Operation: | write | Name: | VirtualDesktop |
Value: 100000003030445671D90A7D3588864C9F3CEA9EBAB7B4A7 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4616) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppLaunch |
| Operation: | write | Name: | Microsoft.Windows.Explorer |
Value: 49 | |||
| (PID) Process: | (4616) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: A7E5136700000000 | |||
| (PID) Process: | (4616) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4616) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0300000000000000040000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
127
Suspicious files
396
Text files
552
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
285
DNS requests
320
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
7728 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
7728 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
4616 | explorer.exe | GET | 200 | 23.53.43.50:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEBu1jyUq3yMASSjJrj1%2B7Sc%3D | DE | binary | 1.52 Kb | whitelisted |
4616 | explorer.exe | GET | 200 | 23.53.43.50:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEBu1jyUq3yMASSjJrj1%2B7Sc%3D | DE | binary | 1.52 Kb | whitelisted |
4616 | explorer.exe | GET | 200 | 23.53.43.48:80 | http://crl.certum.pl/ctnca.crl | DE | binary | 770 b | whitelisted |
4616 | explorer.exe | GET | 200 | 23.53.43.50:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQCZo4AKJlU7ZavcboSms%2Bo5 | DE | binary | 1.80 Kb | whitelisted |
3864 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
4616 | explorer.exe | GET | 200 | 23.53.43.50:80 | http://ccsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRxypYNH69rICCzQBIRXN0YAFa3AAQU3XRdTADbe5%2BgdMqxbvc8wDLAcM0CEH9cUGOTVmB1svQAnfpkX5E%3D | DE | binary | 2.25 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5700 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1156 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5744 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5744 | chrome.exe | 67.199.248.13:443 | naruzhu.click | GOOGLE-CLOUD-PLATFORM | US | shared |
5744 | chrome.exe | 51.89.24.164:443 | l.vpnn.io | OVH SAS | GB | unknown |
4360 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
naruzhu.click |
| unknown |
accounts.google.com |
| whitelisted |
l.vpnn.io |
| unknown |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
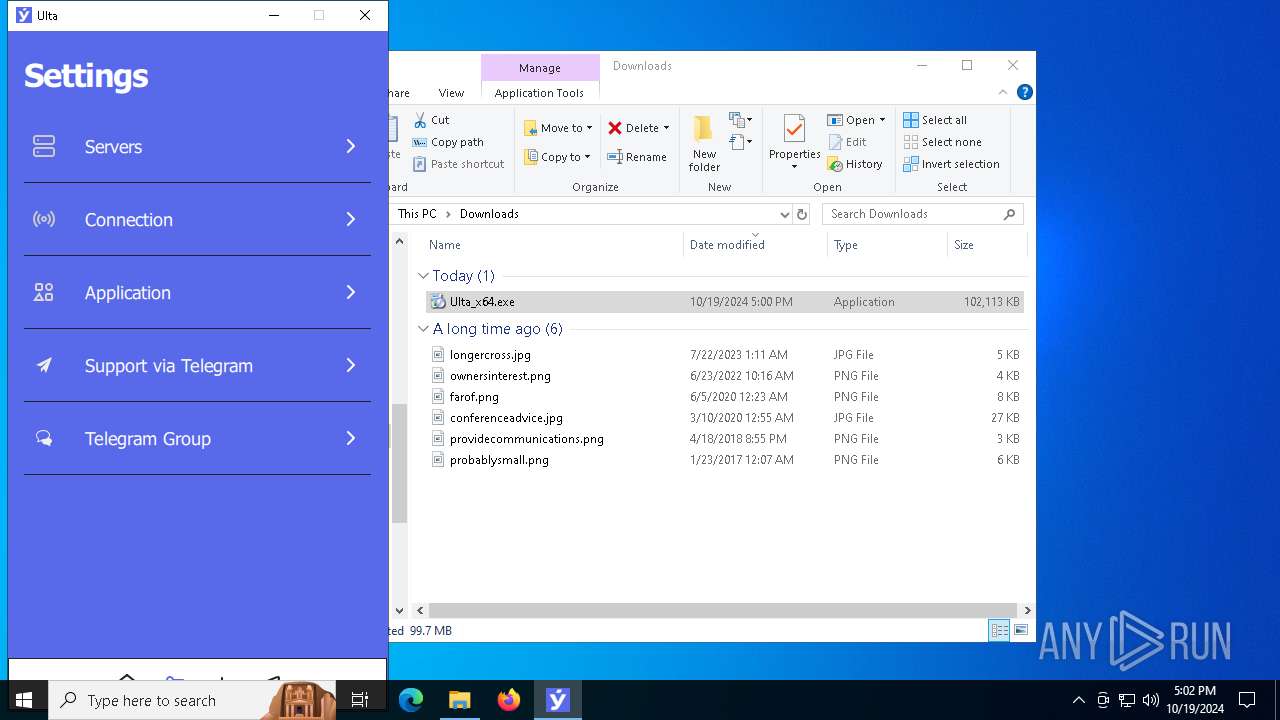
Process | Message |
|---|---|
Ulta-service.exe | Started as system service
|
Ulta-service.exe | Amnezia "Daemon" "Daemon created"
|
Ulta-service.exe | Amnezia "WindowsSplitTunnel" "No Split-Tunnel Conflict detected, continue."
|
Ulta-service.exe | Amnezia "WindowsSplitTunnel" "Driver is not Installed, doing so"
|
Ulta-service.exe | Amnezia "WindowsSplitTunnel" "Driver installed"
|
Ulta-service.exe | Amnezia "WindowsSplitTunnel" "No Split-Tunnel Conflict detected, continue."
|
Ulta-service.exe | Amnezia "WindowsSplitTunnel" "Try to open Split Tunnel Driver"
|
Ulta-service.exe | Amnezia "WindowsUtils" "Failed to open Driver: - The system cannot find the file specified."
|
Ulta-service.exe | Amnezia "WindowsServiceManager" "OpenSCManager access given - 0"
|
Ulta-service.exe | Amnezia "WindowsServiceManager" "Opening Service - UltaSplitTunnel"
|