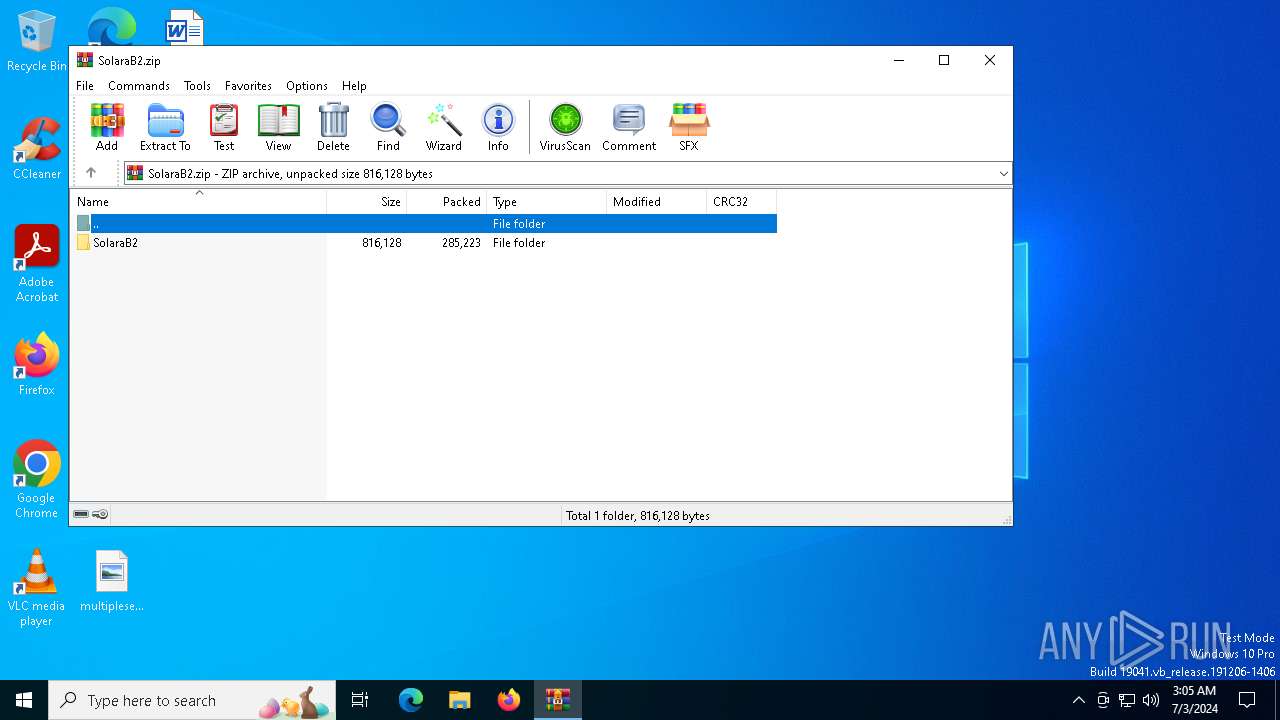
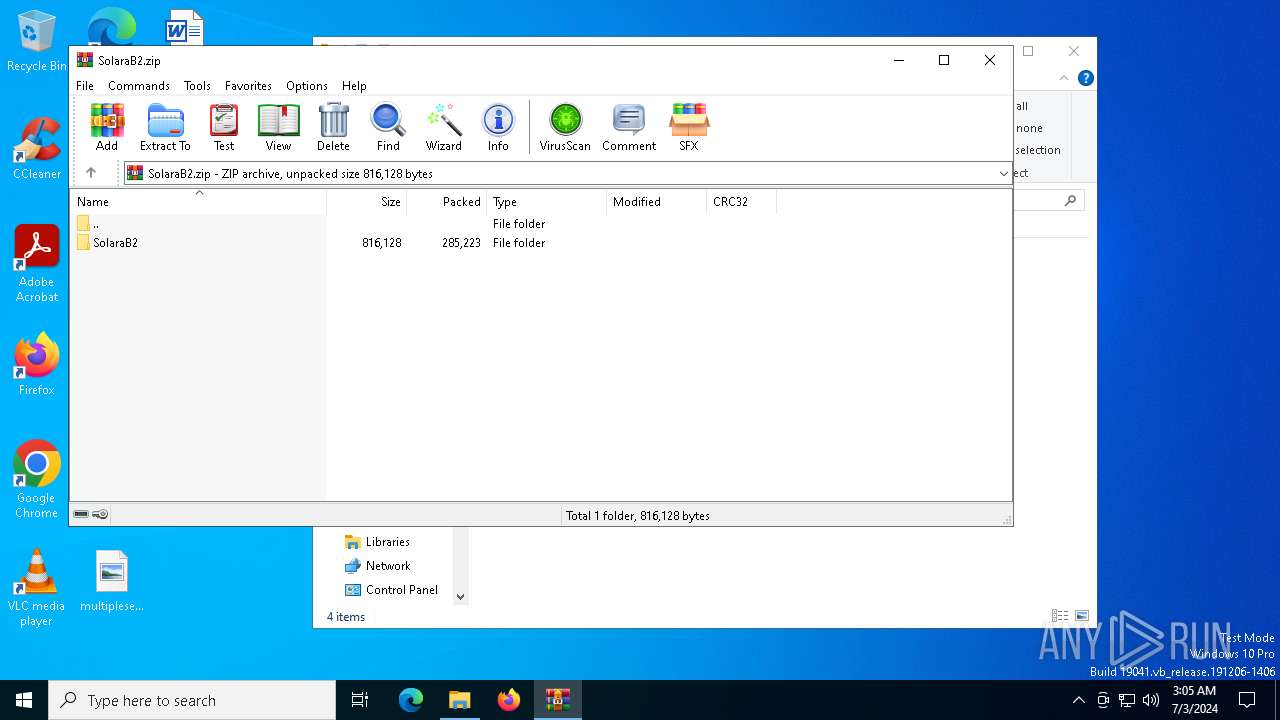
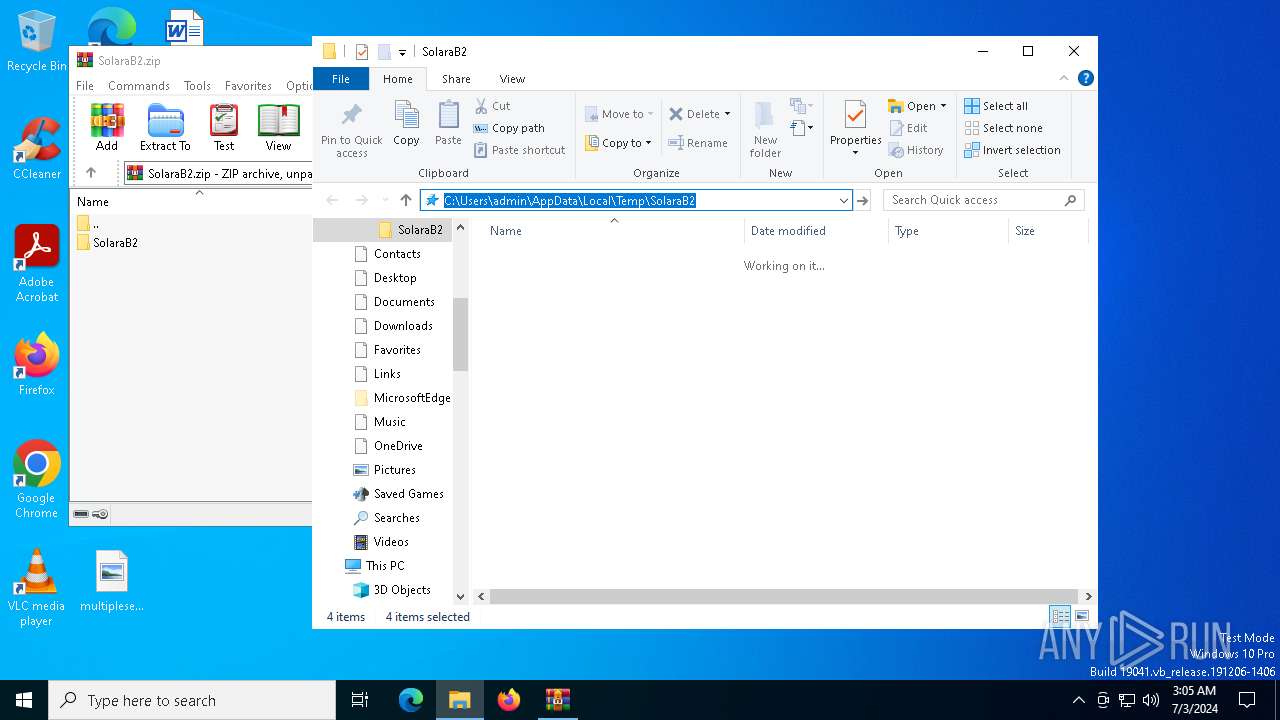
| File name: | SolaraB2.zip |
| Full analysis: | https://app.any.run/tasks/bc11f5a5-753b-448e-a9ab-3233798451de |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2024, 03:05:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | EA418B261E24A56105A6D328B60E9CC7 |
| SHA1: | 4F89568A40FFF23B381EB1009A764CC7EAF6580C |
| SHA256: | DA9098D4713D46C44B95758BDF17E3D2FA1633B3130C7BE47B7111132DC051FF |
| SSDEEP: | 6144:/tRudIww5pmYY6XcHQGeWwYg17lPS3otHCsJZgTxHoJNrgnHwbqhYB2N:lRudIJ5K6XcHbKPXHCsJWsN8nQbqR |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 436)
- msiexec.exe (PID: 3908)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3908)
Checks Windows Trust Settings
- msiexec.exe (PID: 3908)
INFO
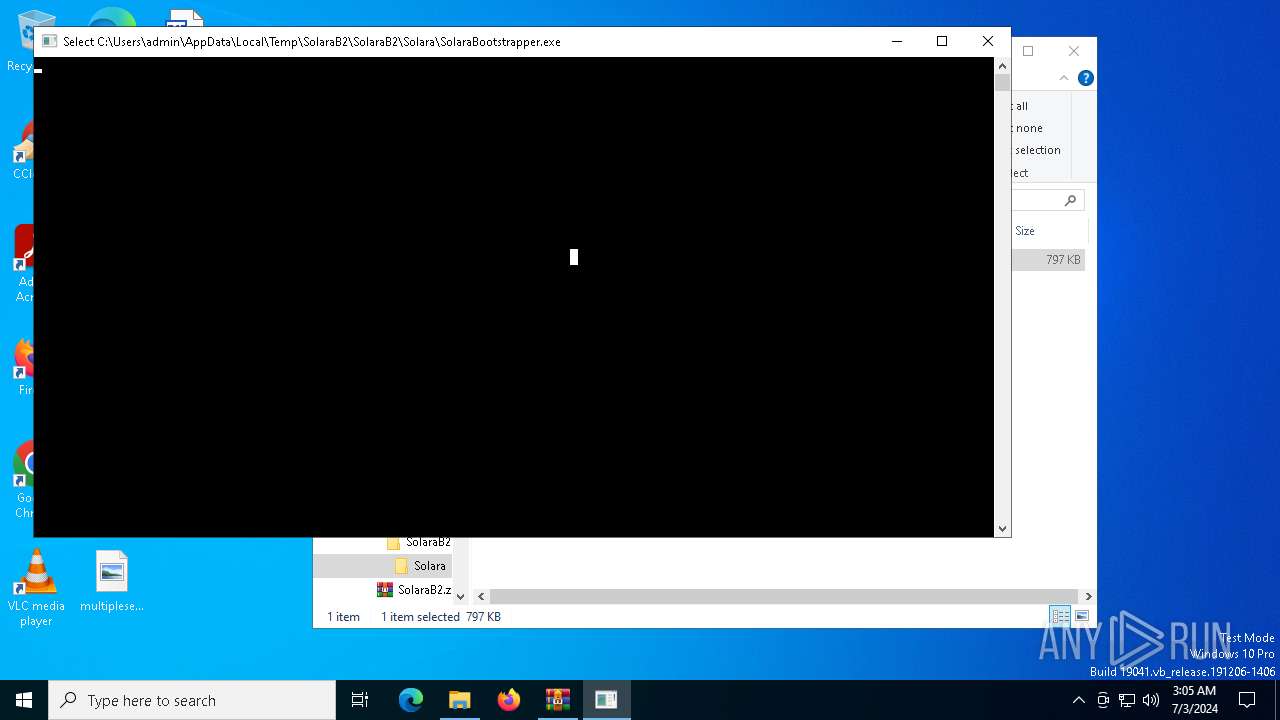
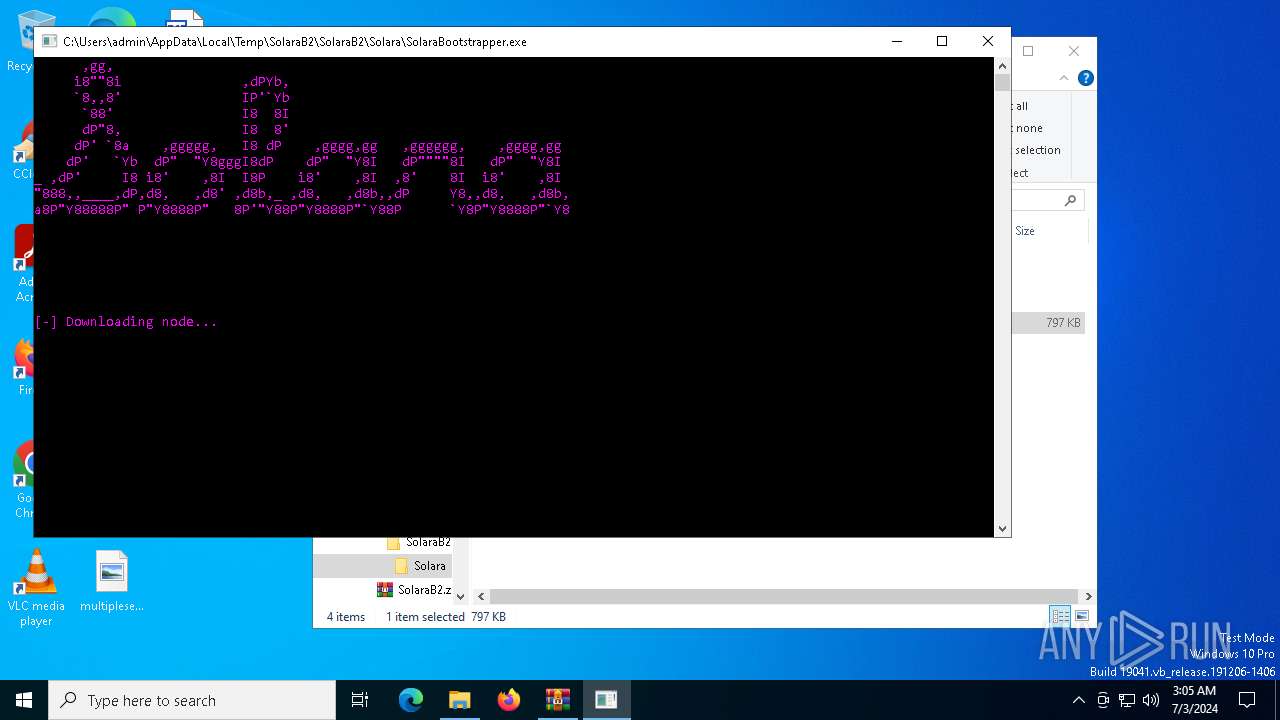
Manual execution by a user
- SolaraBootstrapper.exe (PID: 5432)
- SolaraBootstrapper.exe (PID: 3716)
Checks supported languages
- SolaraBootstrapper.exe (PID: 3716)
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 524)
- msiexec.exe (PID: 1588)
Reads the computer name
- SolaraBootstrapper.exe (PID: 3716)
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1588)
- msiexec.exe (PID: 524)
Reads the machine GUID from the registry
- SolaraBootstrapper.exe (PID: 3716)
- msiexec.exe (PID: 3908)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 436)
- msiexec.exe (PID: 3908)
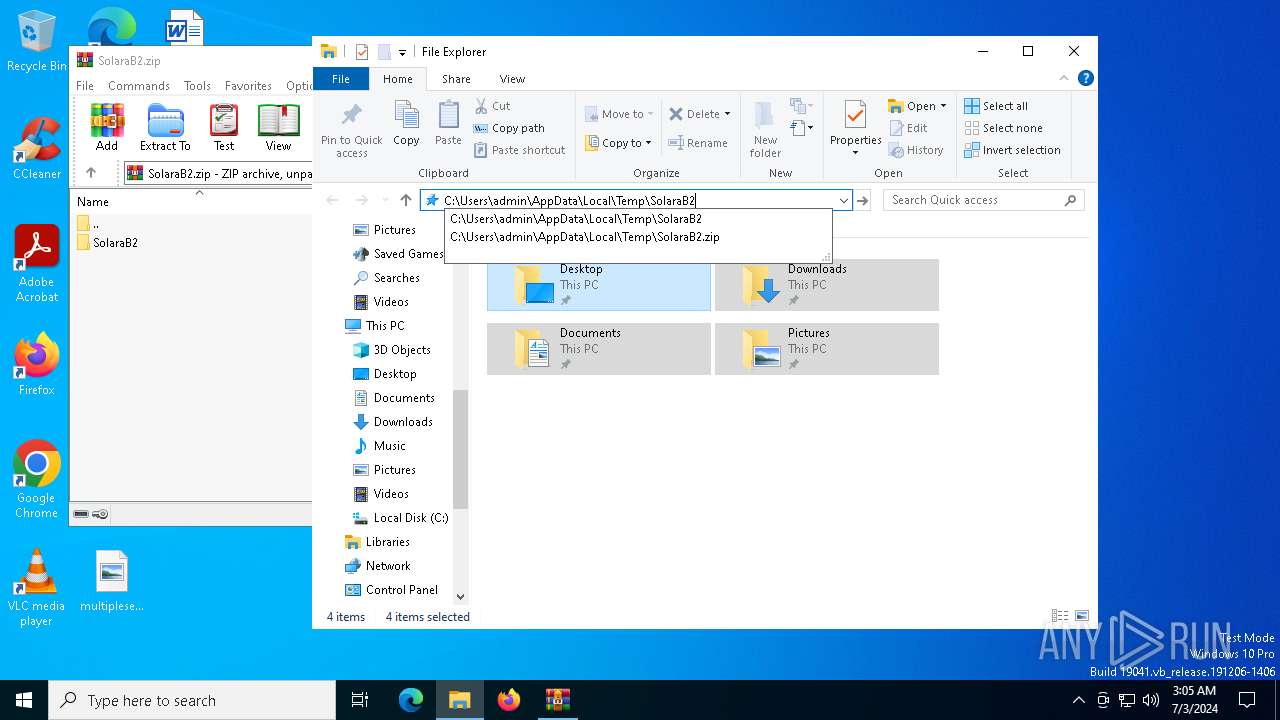
Create files in a temporary directory
- SolaraBootstrapper.exe (PID: 3716)
Disables trace logs
- SolaraBootstrapper.exe (PID: 3716)
Checks proxy server information
- SolaraBootstrapper.exe (PID: 3716)
Reads the software policy settings
- SolaraBootstrapper.exe (PID: 3716)
- msiexec.exe (PID: 3908)
Reads Environment values
- SolaraBootstrapper.exe (PID: 3716)
Creates files or folders in the user directory
- msiexec.exe (PID: 3908)
Application launched itself
- msiexec.exe (PID: 3908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:06:16 14:45:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | SolaraB2/Solara/ |
Total processes
134
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
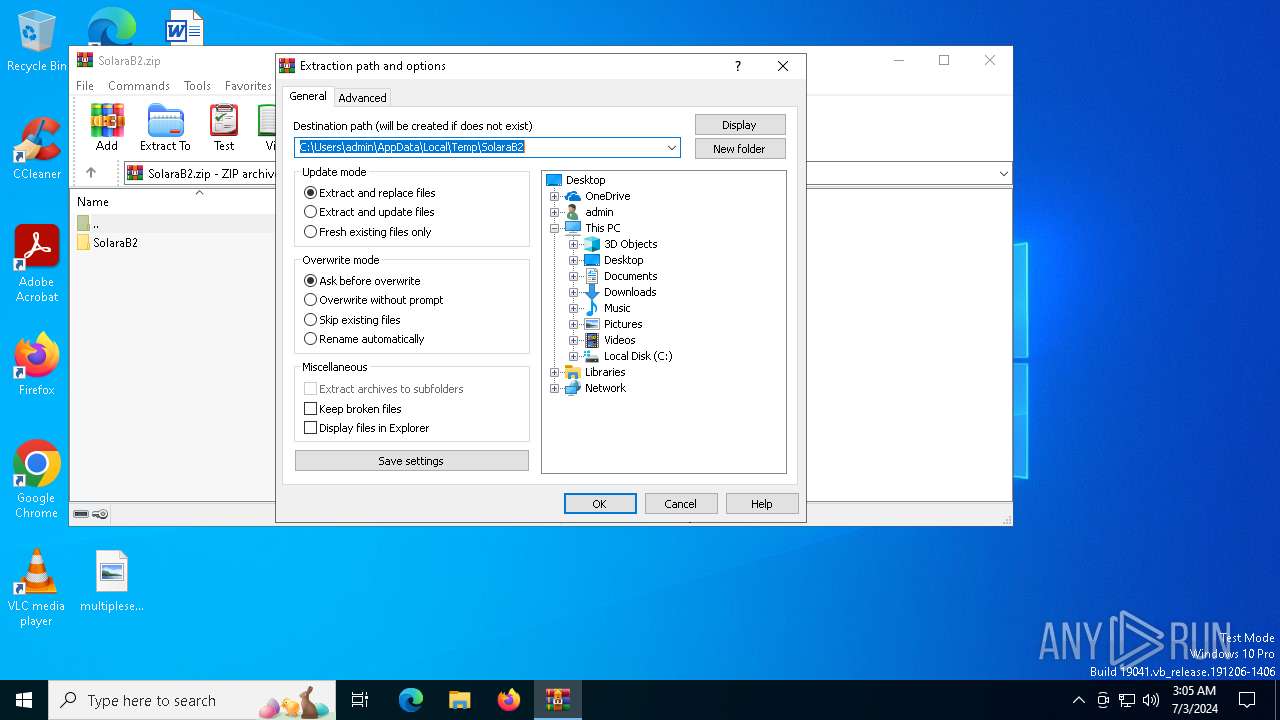
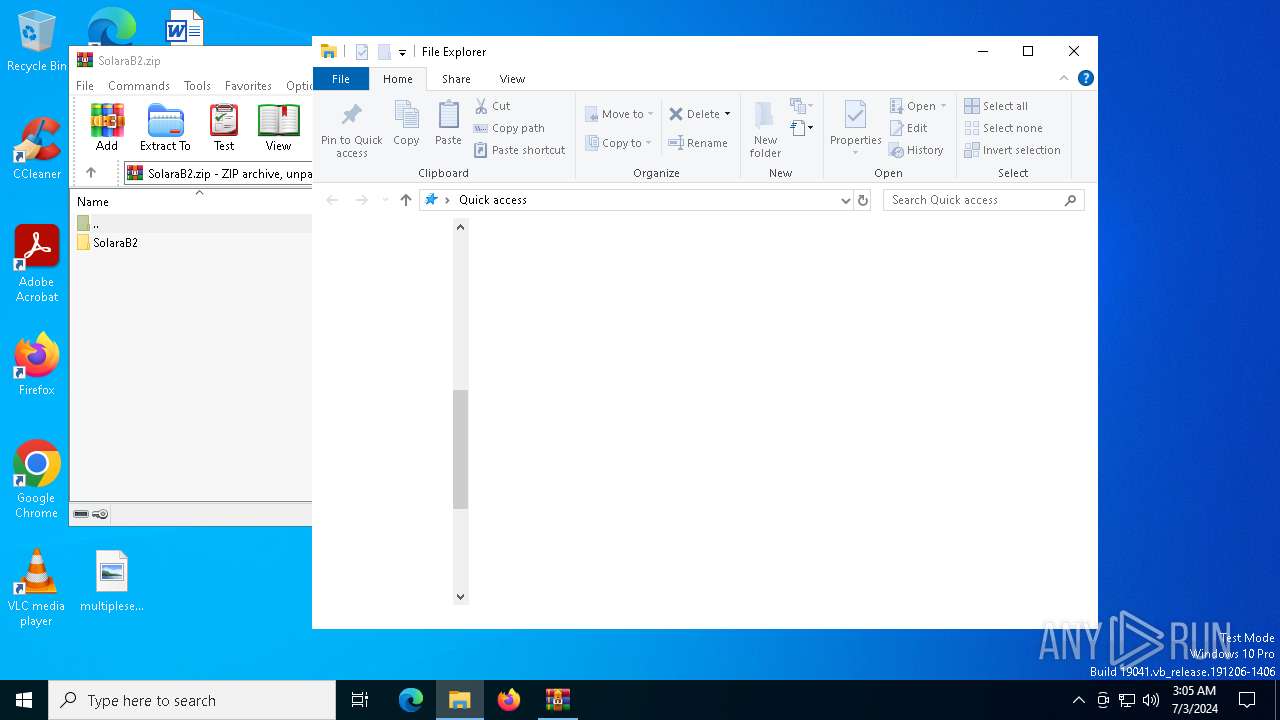
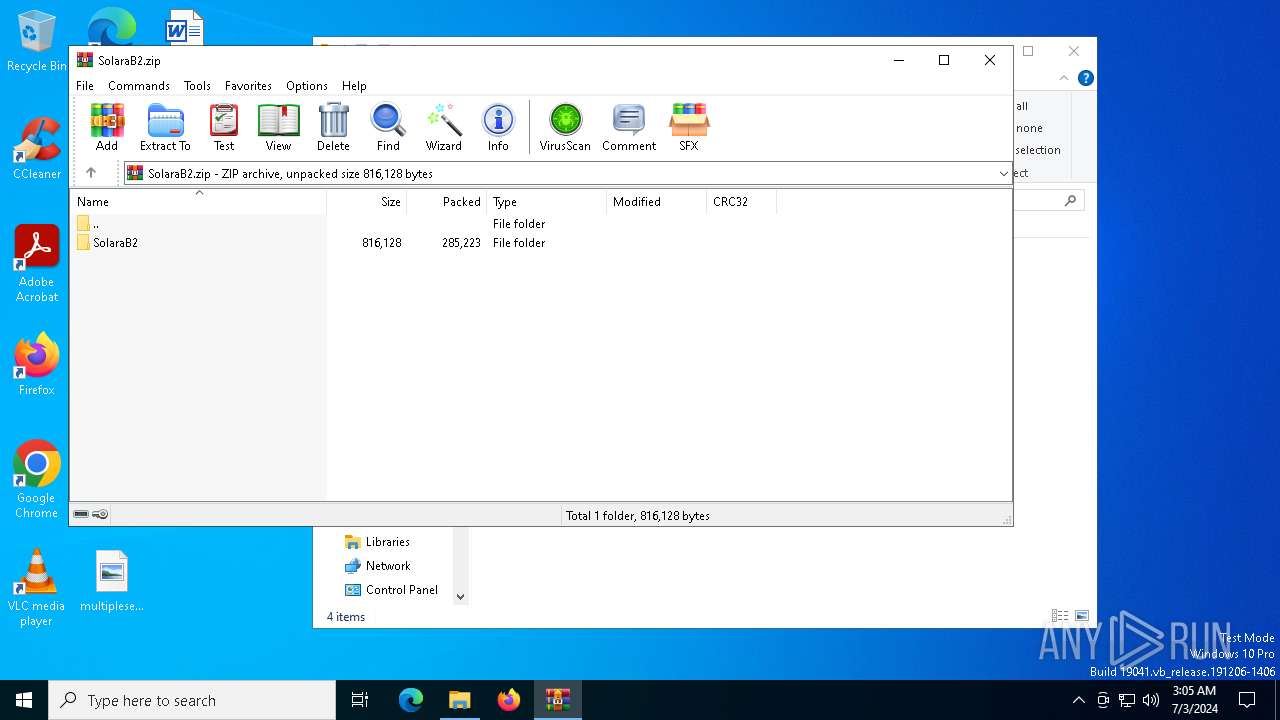
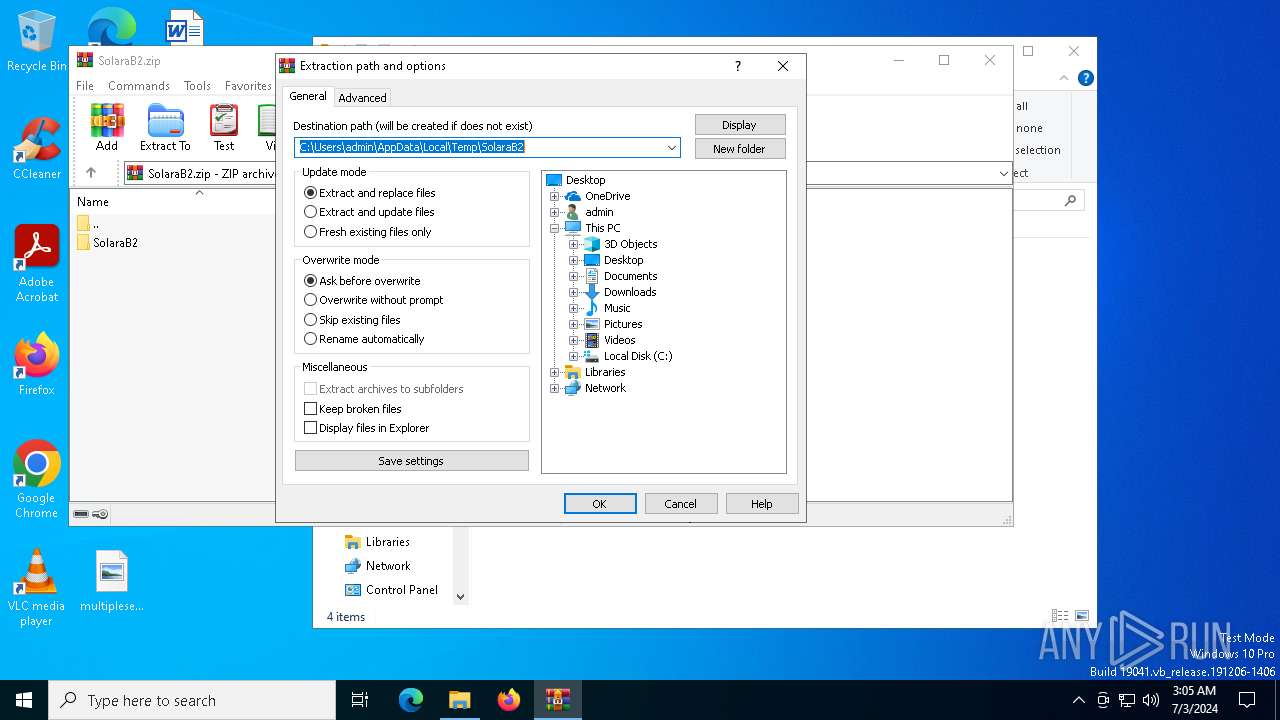
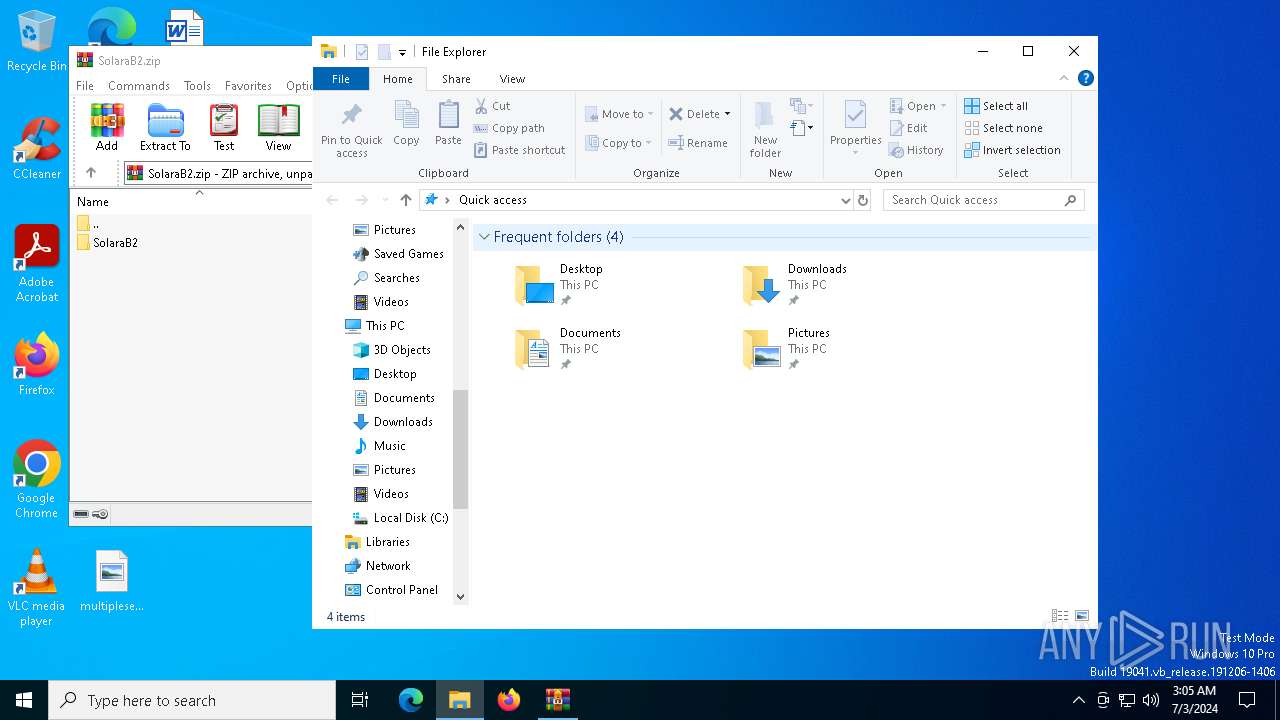
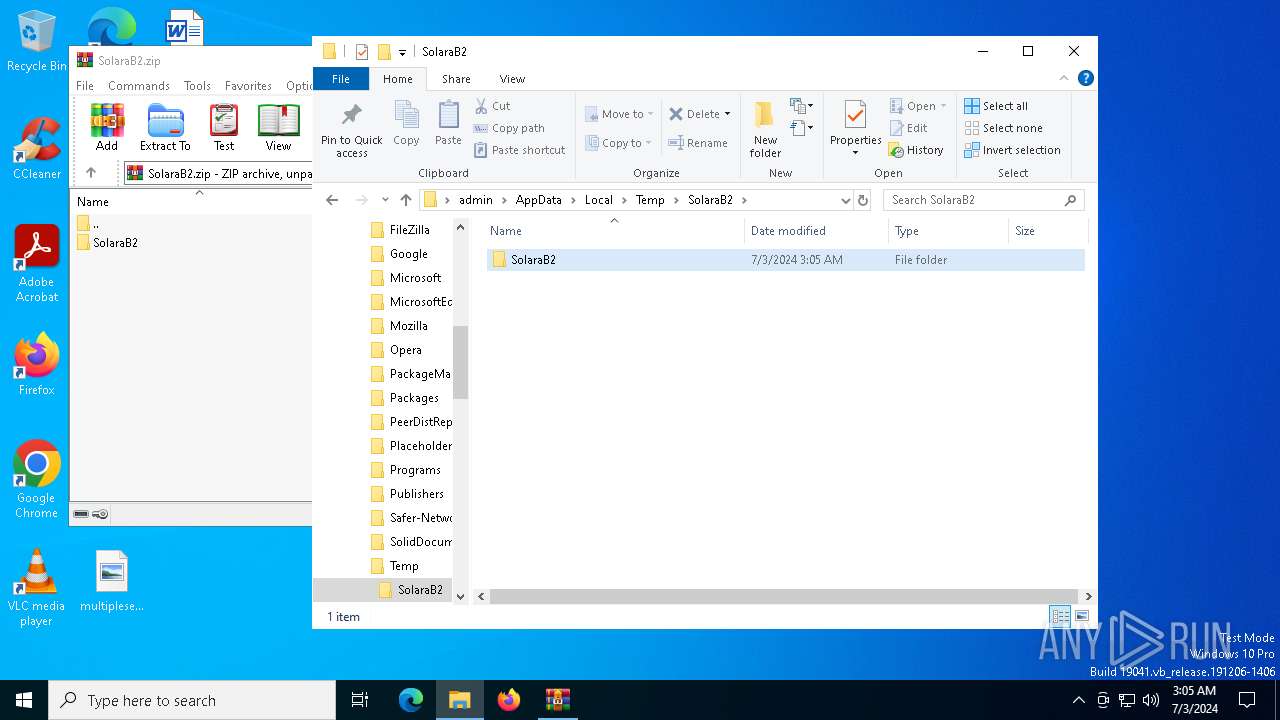
| 436 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SolaraB2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 524 | C:\Windows\System32\MsiExec.exe -Embedding 5A34A355E0A7925C43EBF0E686D0DC37 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1588 | C:\Windows\syswow64\MsiExec.exe -Embedding CABFB00BDB99E8B5996212CEC0C95530 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1736 | "msiexec" /i "C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi" /qn | C:\Windows\SysWOW64\msiexec.exe | — | SolaraBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SolaraBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
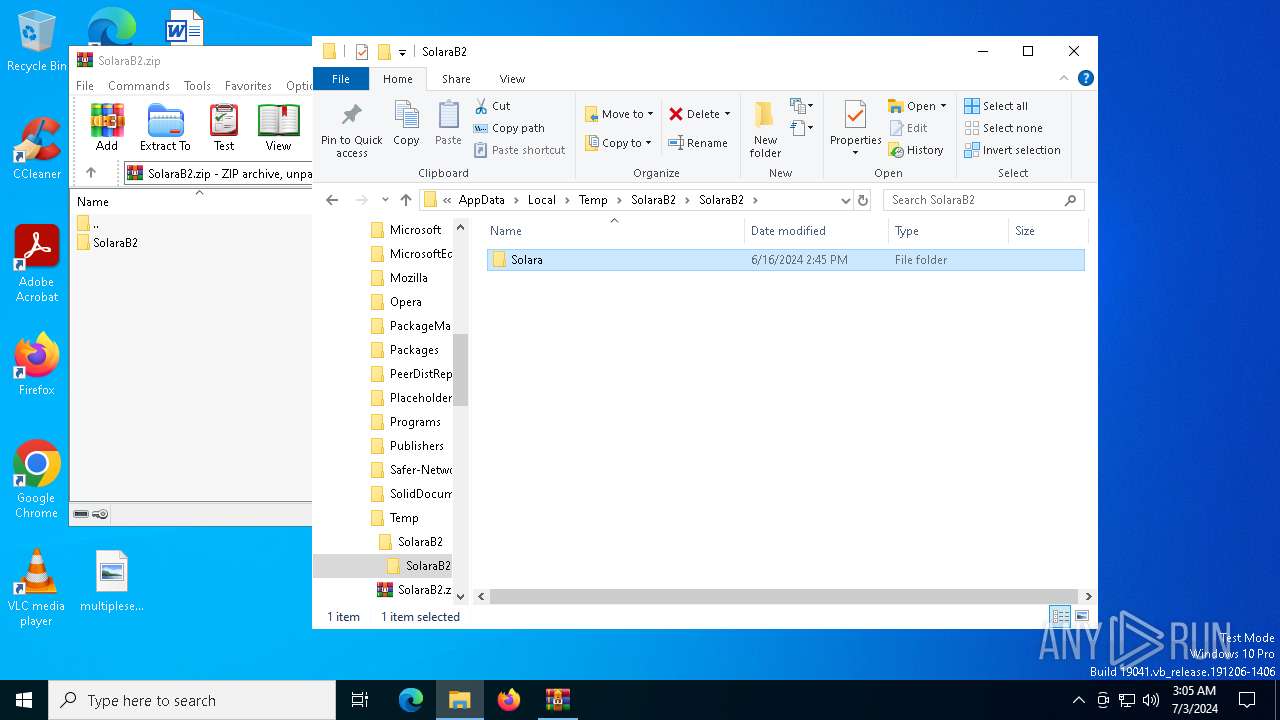
| 3716 | "C:\Users\admin\AppData\Local\Temp\SolaraB2\SolaraB2\Solara\SolaraBootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\SolaraB2\SolaraB2\Solara\SolaraBootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Version: 1.0.0.0 Modules
| |||||||||||||||
| 3908 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5432 | "C:\Users\admin\AppData\Local\Temp\SolaraB2\SolaraB2\Solara\SolaraBootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\SolaraB2\SolaraB2\Solara\SolaraBootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
12 082
Read events
12 055
Write events
27
Delete events
0
Modification events
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SolaraB2.zip | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SolaraB2 | |||
| (PID) Process: | (3716) SolaraBootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
8
Suspicious files
8
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | SolaraBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi | — | |
MD5:— | SHA256:— | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\1ba768.msi | — | |
MD5:— | SHA256:— | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\MSIA9FA.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\MSIB9BD.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 3908 | msiexec.exe | C:\WINDOWS\TEMP\~DFEABE018D01DA61F8.TMP | binary | |
MD5:976E4E95FA288EEB72B6E1B9E54814B9 | SHA256:A67B6DF5DCA905A0EB9EBC265552D3045C520BDA7FA37892DF6659831421ABFC | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\MSIAEAE.tmp | binary | |
MD5:5AA1BCCD8CA9DA4677EB0FE3F923C9AF | SHA256:01197FE89F128E86973E3B8A1626863F4314C16A69FFC6B56CA89FB0923BC403 | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\MSIB19E.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\inprogressinstallinfo.ipi | binary | |
MD5:976E4E95FA288EEB72B6E1B9E54814B9 | SHA256:A67B6DF5DCA905A0EB9EBC265552D3045C520BDA7FA37892DF6659831421ABFC | |||
| 3908 | msiexec.exe | C:\WINDOWS\Installer\MSIA9AA.tmp | executable | |
MD5:9FE9B0ECAEA0324AD99036A91DB03EBB | SHA256:E2CCE64916E405976A1D0C522B44527D12B1CBA19DE25DA62121CF5F41D184C9 | |||
| 436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\SolaraB2\SolaraB2\Solara\SolaraBootstrapper.exe | executable | |
MD5:36B62BA7D1B5E149A2C297F11E0417EE | SHA256:8353C5ACE62FDA6ABA330FB3396E4AAB11D7E0476F815666BD96A978724B9E0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
53
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
2204 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
1672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3068 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
1672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
3908 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | unknown | — | — | unknown |
3908 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2212 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4656 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1544 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4656 | SearchApp.exe | 104.126.37.178:443 | r.bing.com | Akamai International B.V. | DE | unknown |
1060 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
r.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |