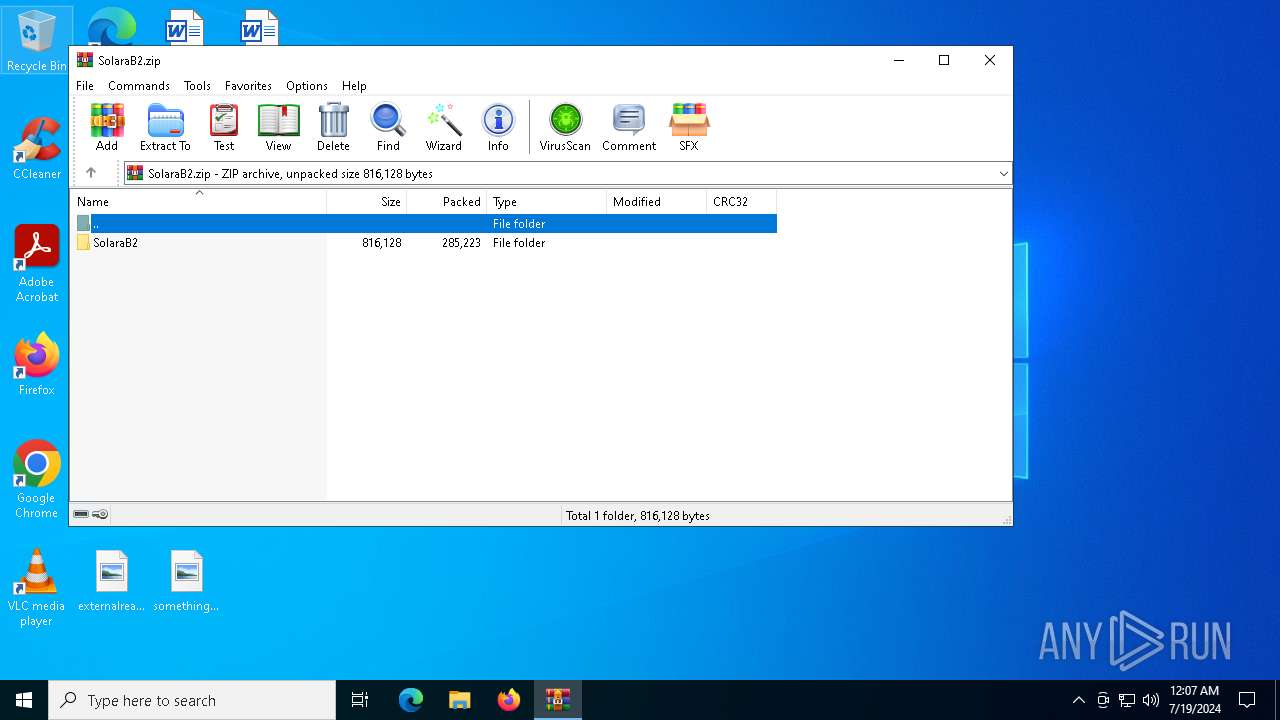
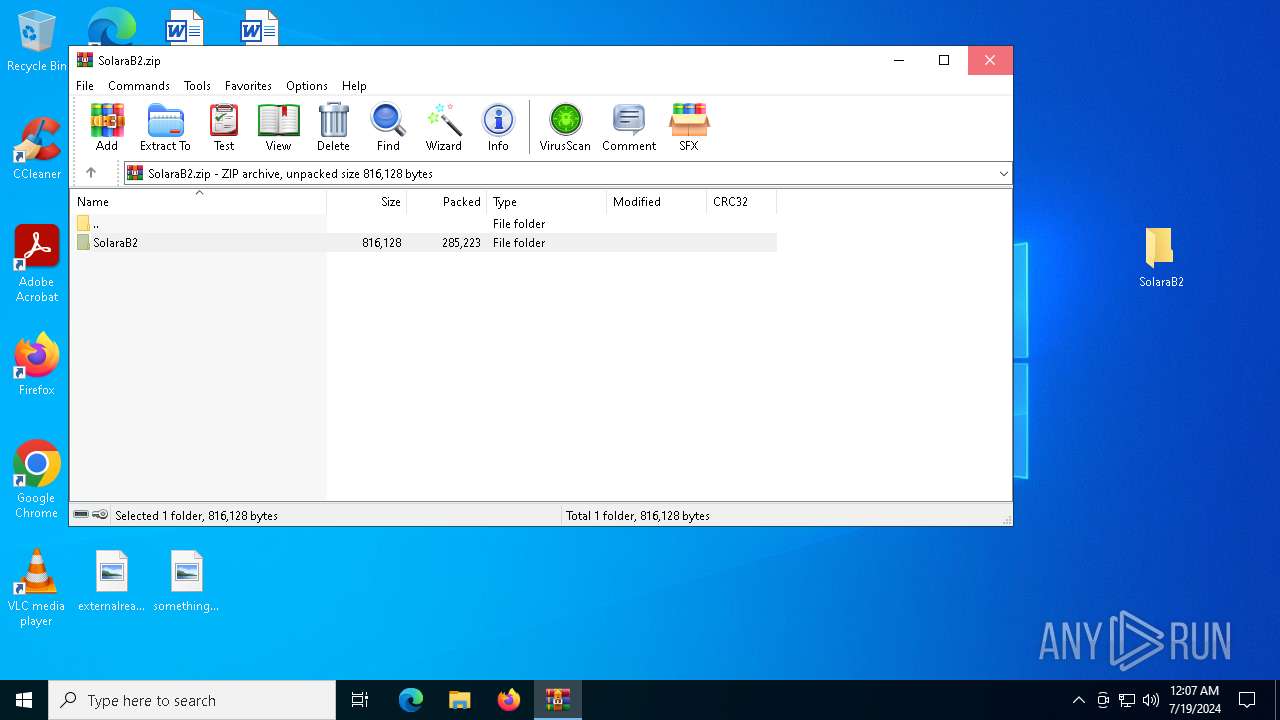
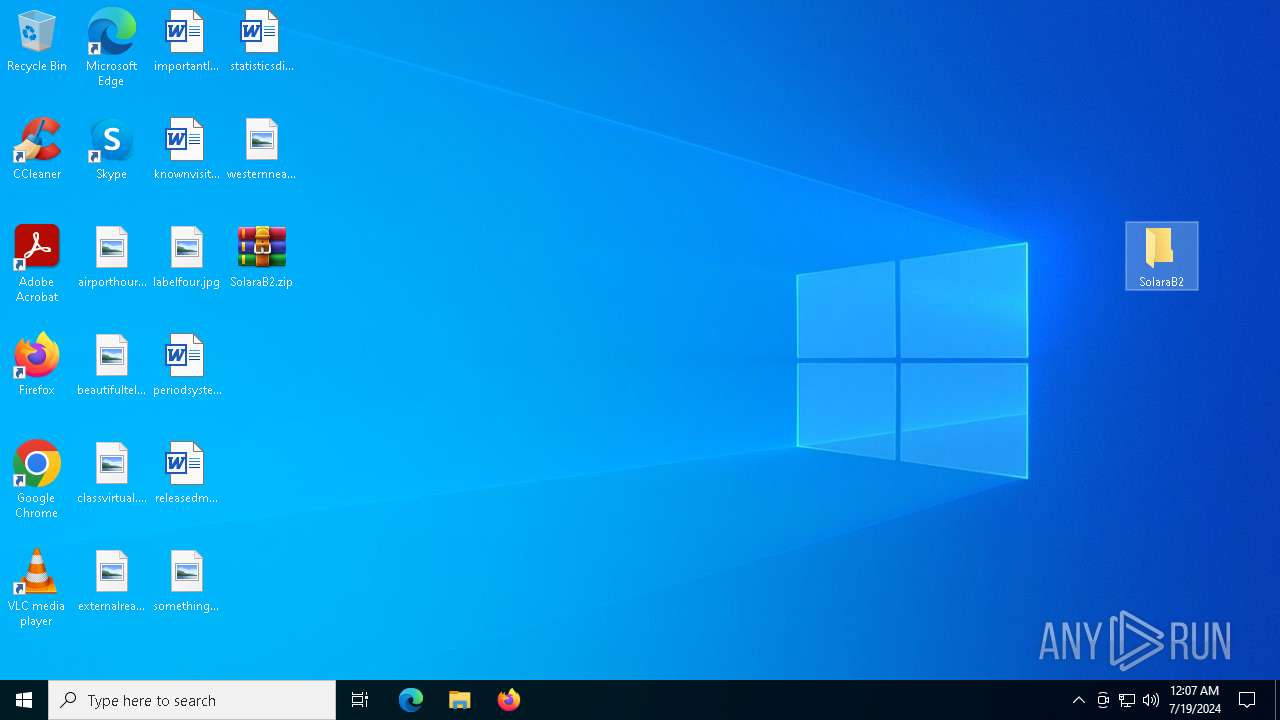
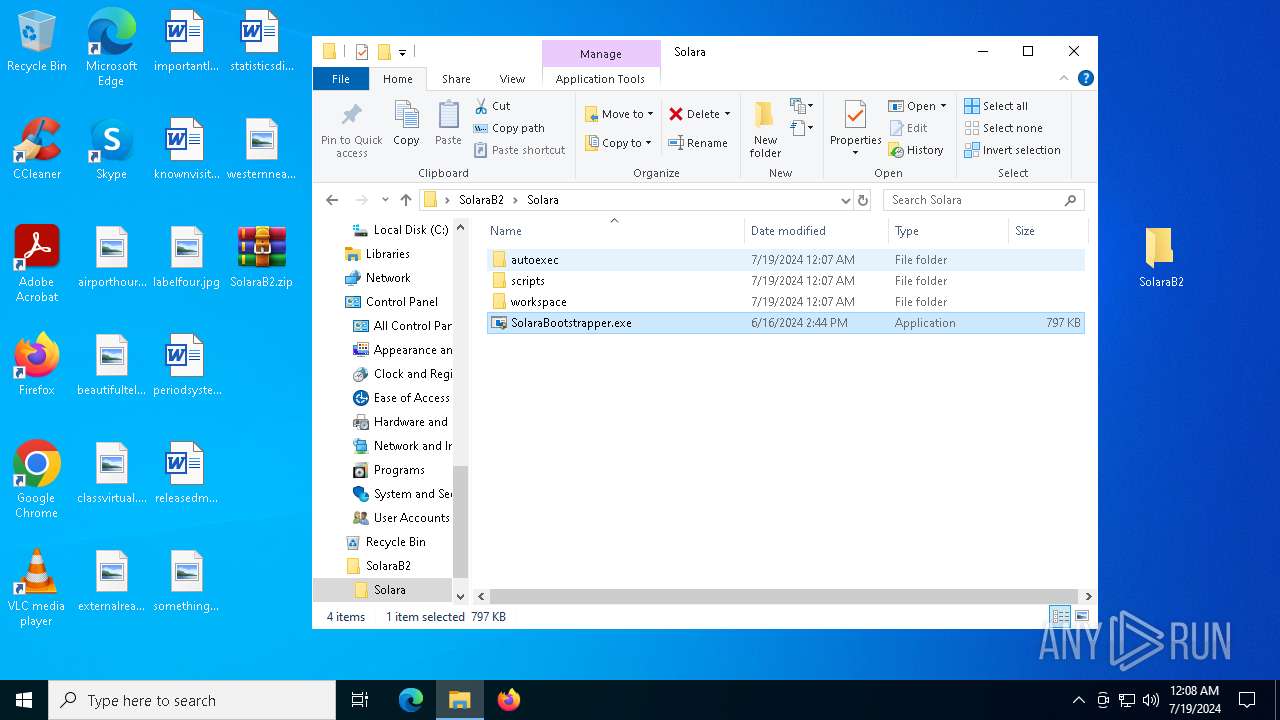
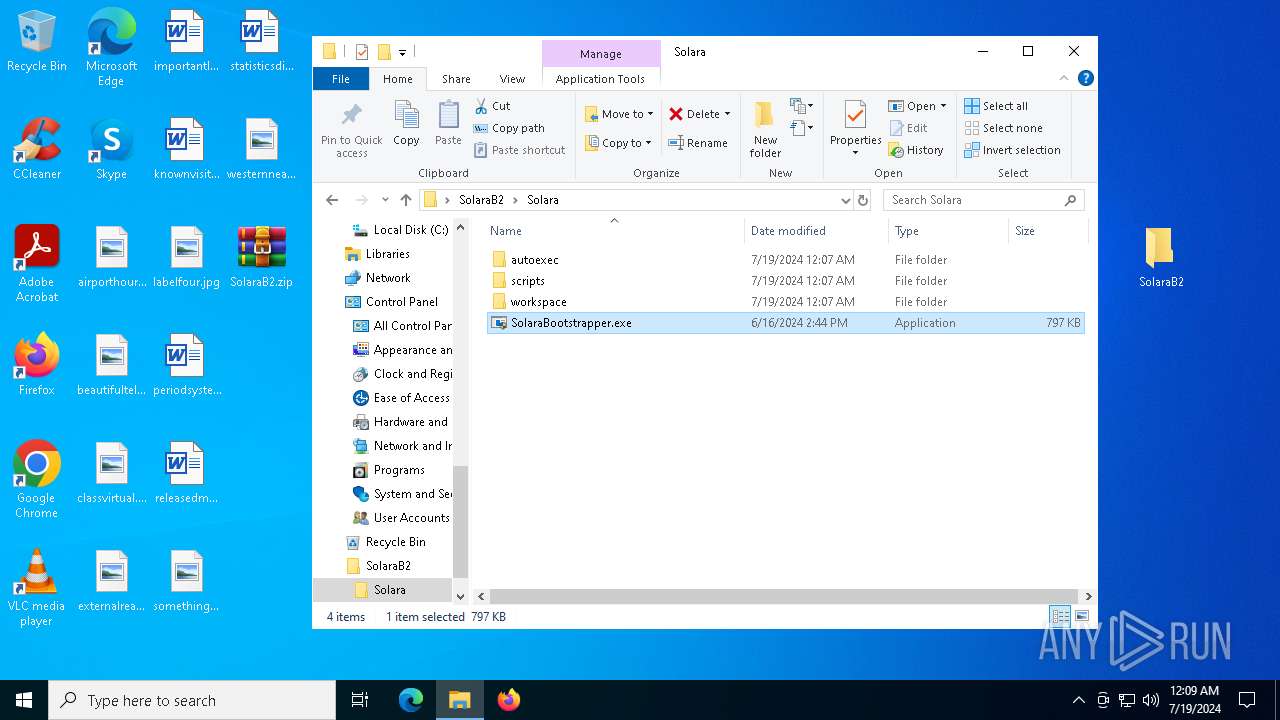
| File name: | SolaraB2.zip |
| Full analysis: | https://app.any.run/tasks/77c3698c-6f02-4ec0-b665-7c8c8e917b7b |
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2024, 00:07:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | EA418B261E24A56105A6D328B60E9CC7 |
| SHA1: | 4F89568A40FFF23B381EB1009A764CC7EAF6580C |
| SHA256: | DA9098D4713D46C44B95758BDF17E3D2FA1633B3130C7BE47B7111132DC051FF |
| SSDEEP: | 6144:/tRudIww5pmYY6XcHQGeWwYg17lPS3otHCsJZgTxHoJNrgnHwbqhYB2N:lRudIJ5K6XcHbKPXHCsJWsN8nQbqR |
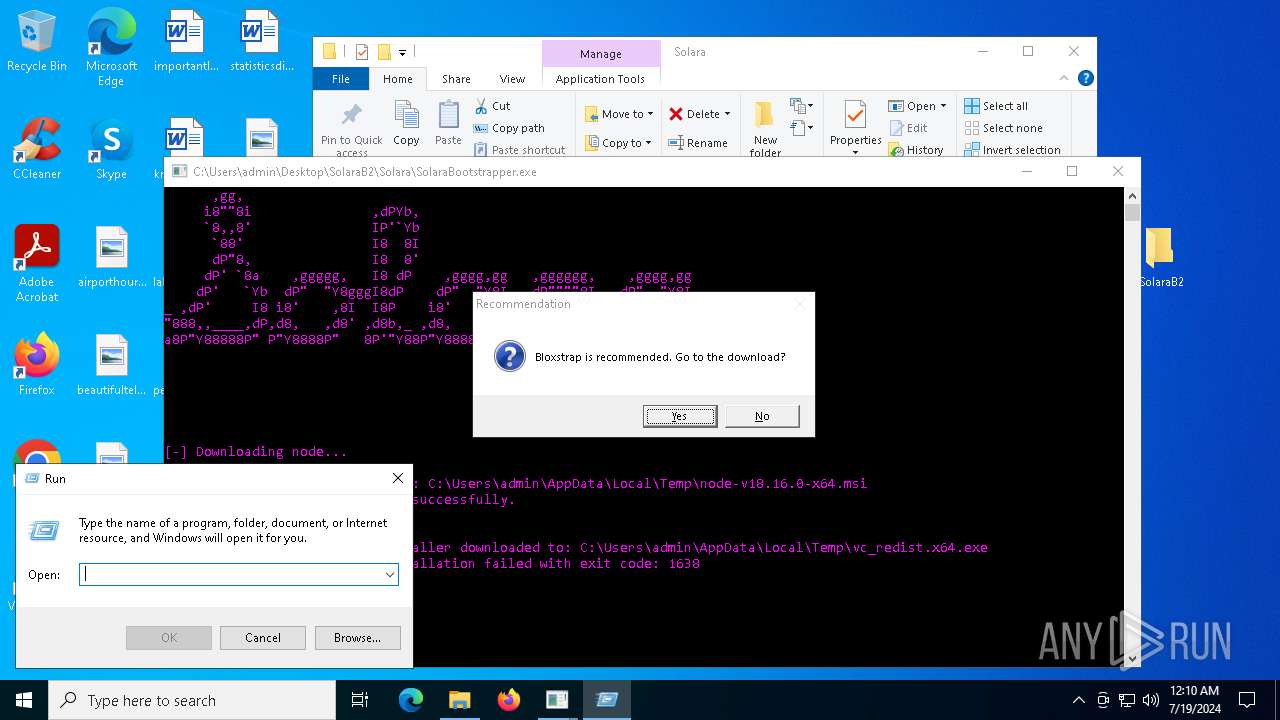
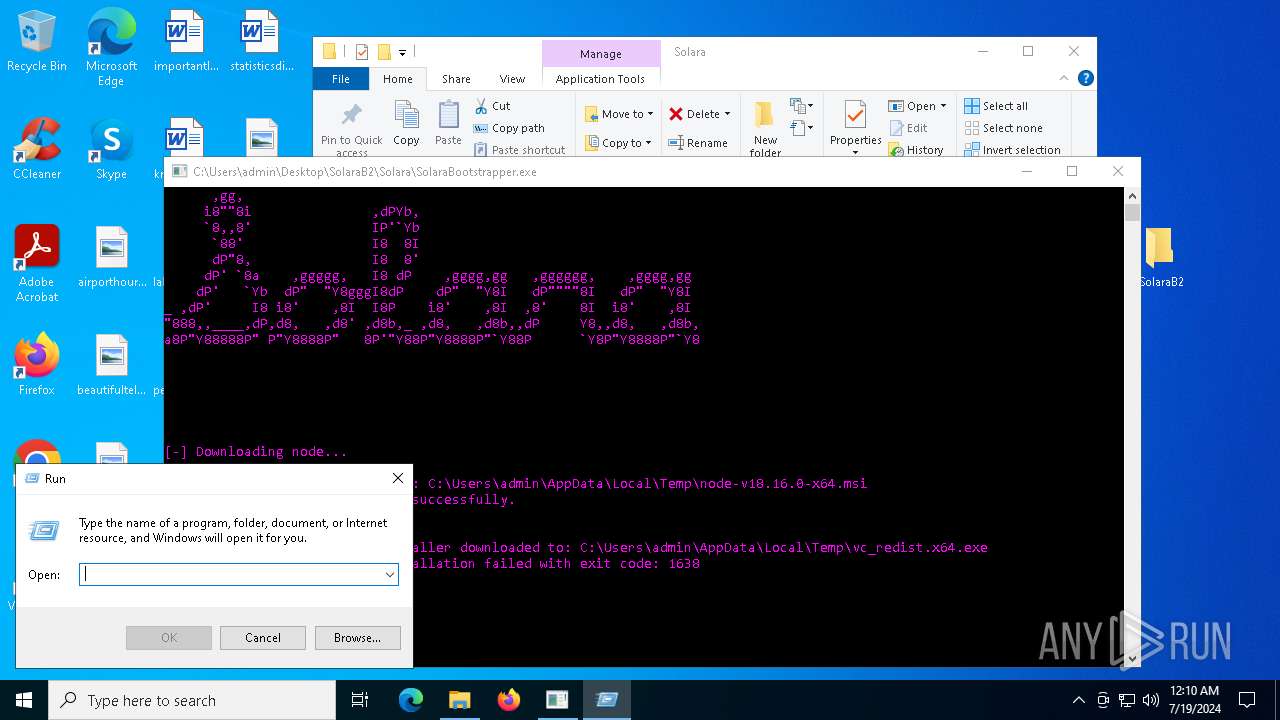
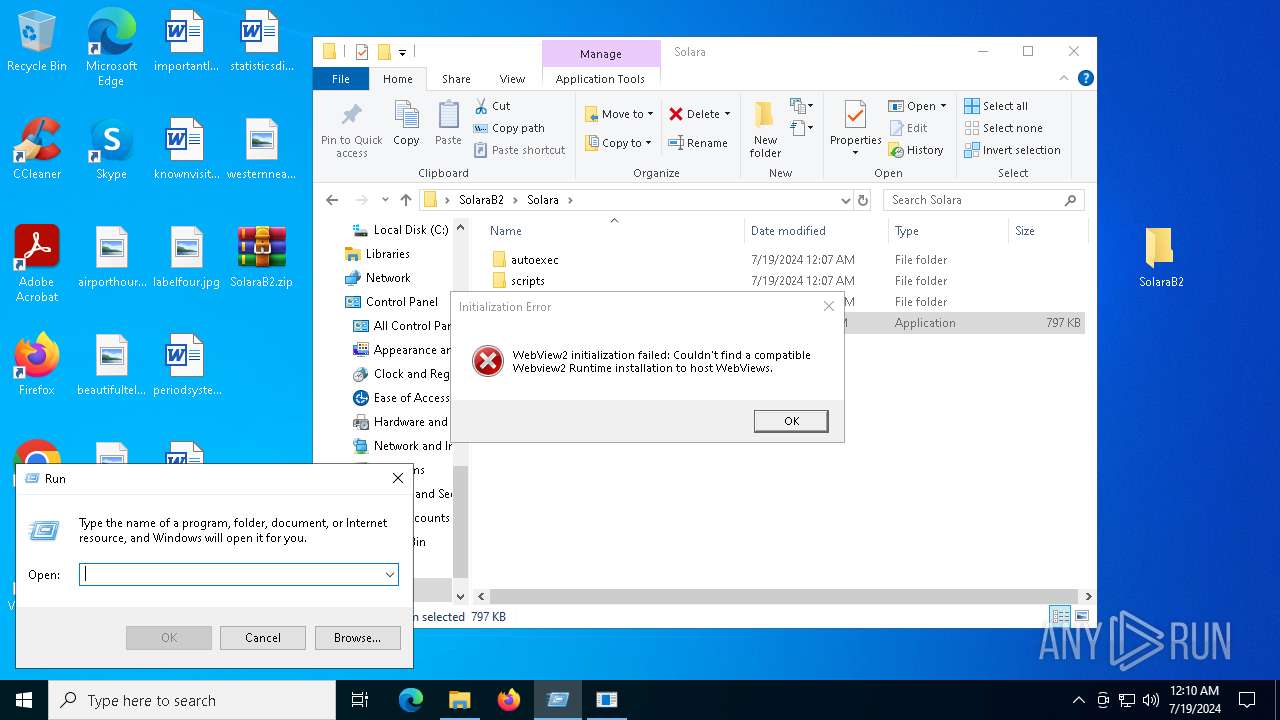
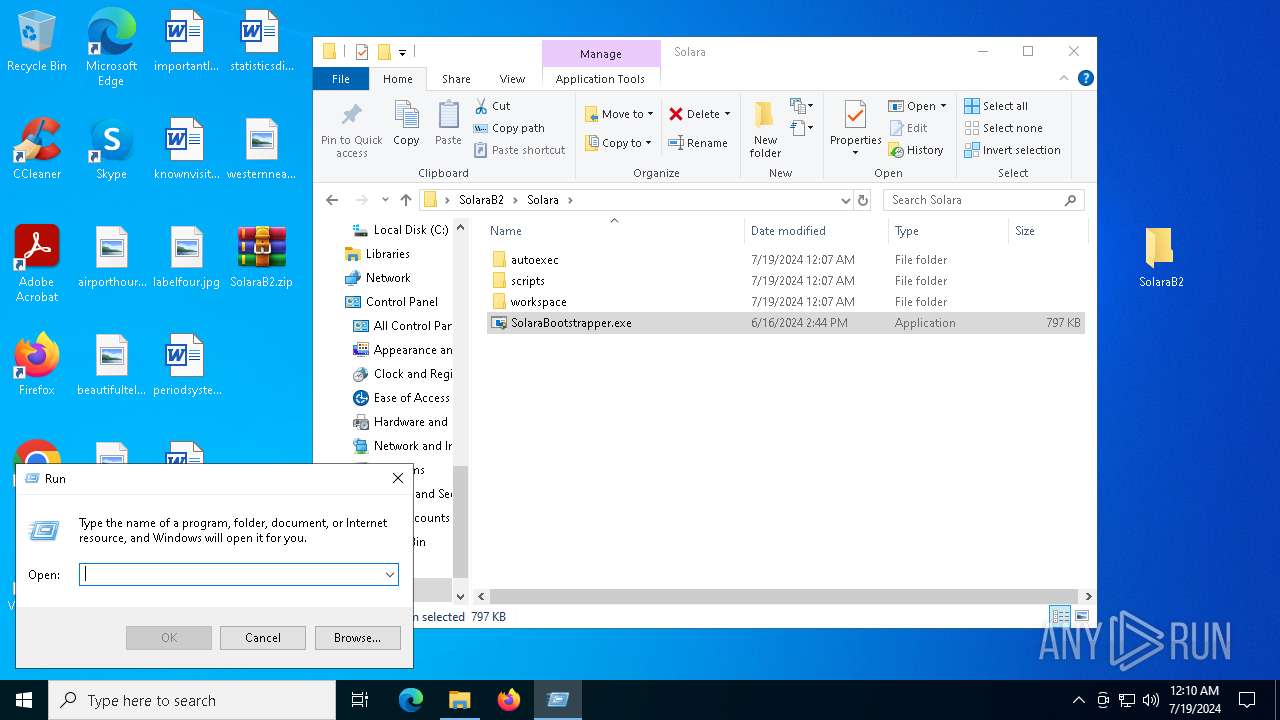
MALICIOUS
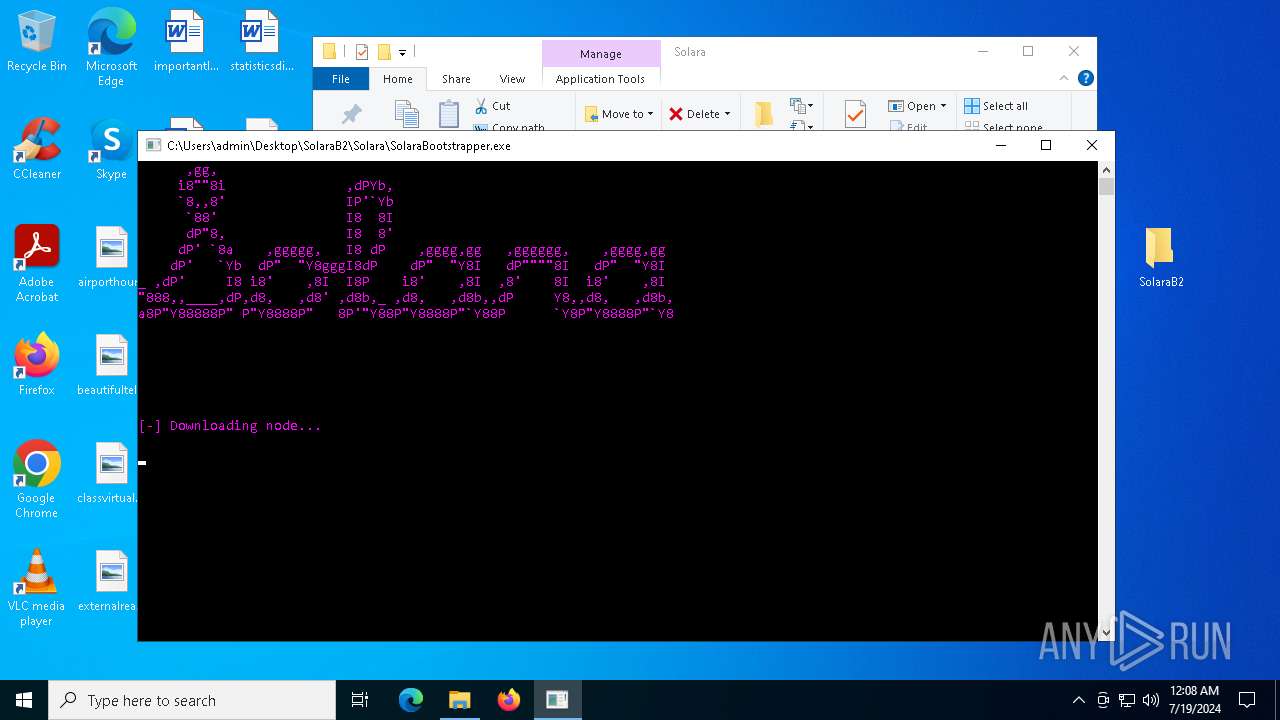
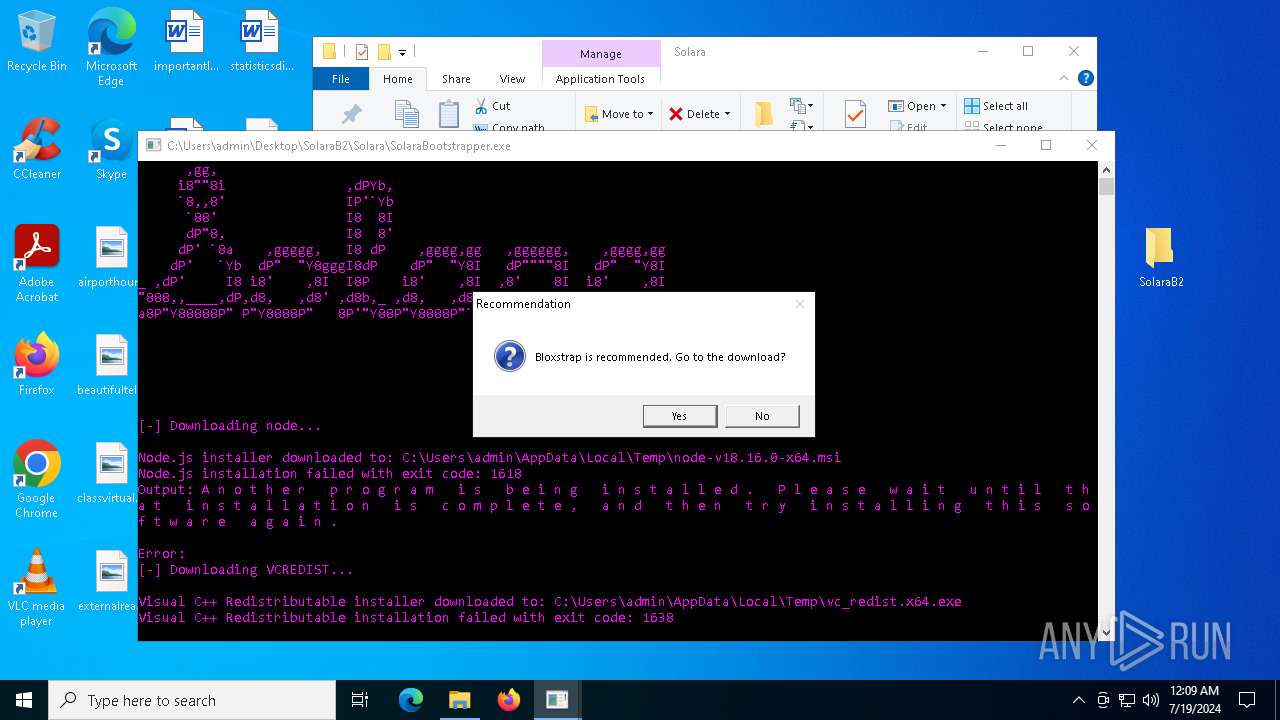
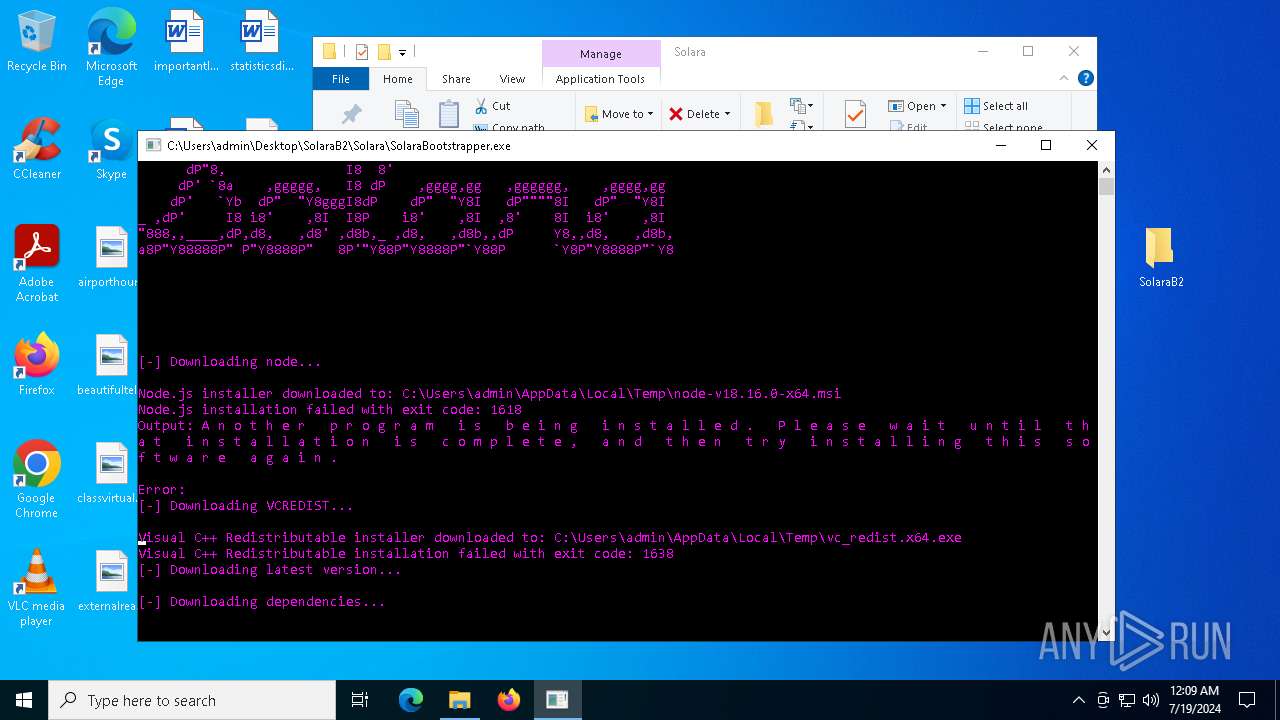
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7044)
- msiexec.exe (PID: 6348)
- vc_redist.x64.exe (PID: 7212)
- vc_redist.x64.exe (PID: 6988)
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 4900)
- vc_redist.x64.exe (PID: 7500)
SUSPICIOUS
Checks Windows Trust Settings
- msiexec.exe (PID: 6348)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7228)
- SolaraBootstrapper.exe (PID: 236)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
- msiexec.exe (PID: 4636)
- msiexec.exe (PID: 5788)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Executable content was dropped or overwritten
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 6988)
- vc_redist.x64.exe (PID: 7212)
- vc_redist.x64.exe (PID: 7500)
- vc_redist.x64.exe (PID: 4900)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 6988)
- vc_redist.x64.exe (PID: 7212)
- vc_redist.x64.exe (PID: 7500)
- vc_redist.x64.exe (PID: 4900)
Process drops legitimate windows executable
- vc_redist.x64.exe (PID: 6988)
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 7500)
Reads the date of Windows installation
- SolaraBootstrapper.exe (PID: 236)
- SolaraBootstrapper.exe (PID: 1568)
Searches for installed software
- vc_redist.x64.exe (PID: 7212)
- vc_redist.x64.exe (PID: 4900)
The process drops C-runtime libraries
- SolaraBootstrapper.exe (PID: 236)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6348)
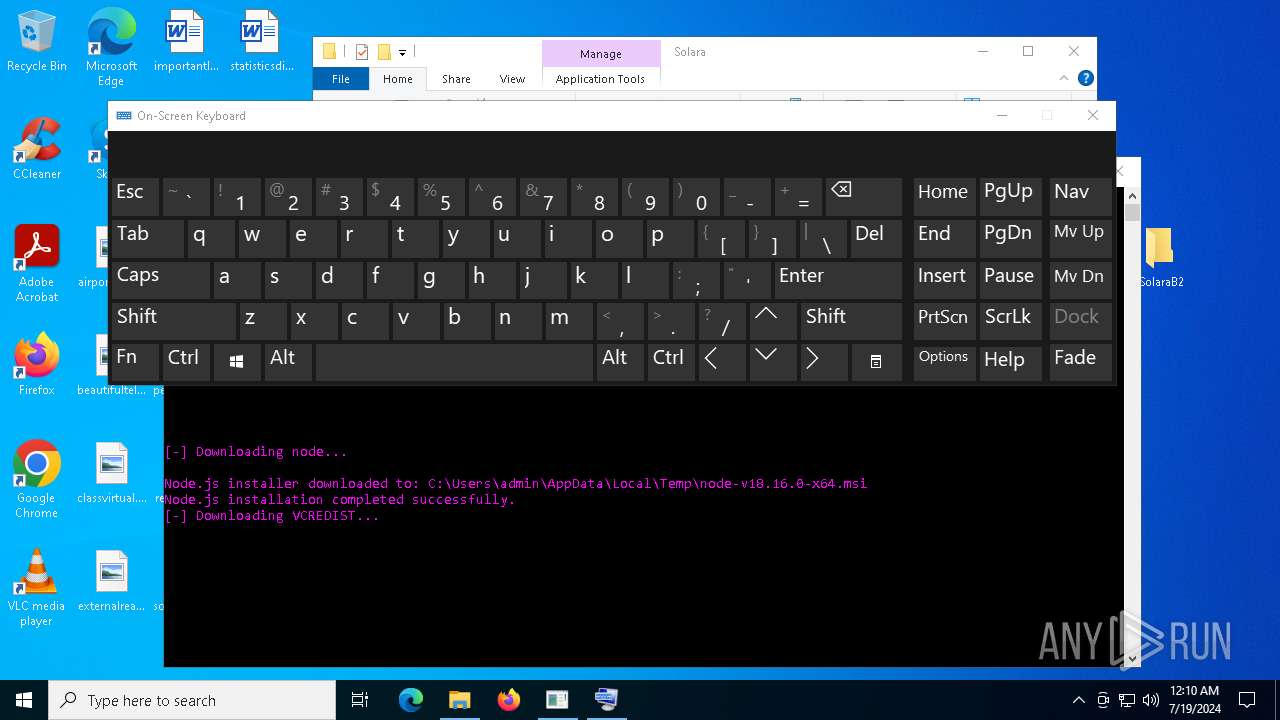
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 4636)
- wevtutil.exe (PID: 2268)
Reads the BIOS version
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7044)
- msiexec.exe (PID: 6348)
Checks supported languages
- SolaraBootstrapper.exe (PID: 6380)
- msiexec.exe (PID: 6348)
- msiexec.exe (PID: 7084)
- msiexec.exe (PID: 7228)
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 7212)
- vc_redist.x64.exe (PID: 6988)
- SolaraBootstrapper.exe (PID: 1568)
- msiexec.exe (PID: 4636)
- msiexec.exe (PID: 6696)
- msiexec.exe (PID: 5788)
- msiexec.exe (PID: 1148)
- vc_redist.x64.exe (PID: 7500)
- vc_redist.x64.exe (PID: 4900)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
Reads Environment values
- SolaraBootstrapper.exe (PID: 6380)
- SolaraBootstrapper.exe (PID: 236)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
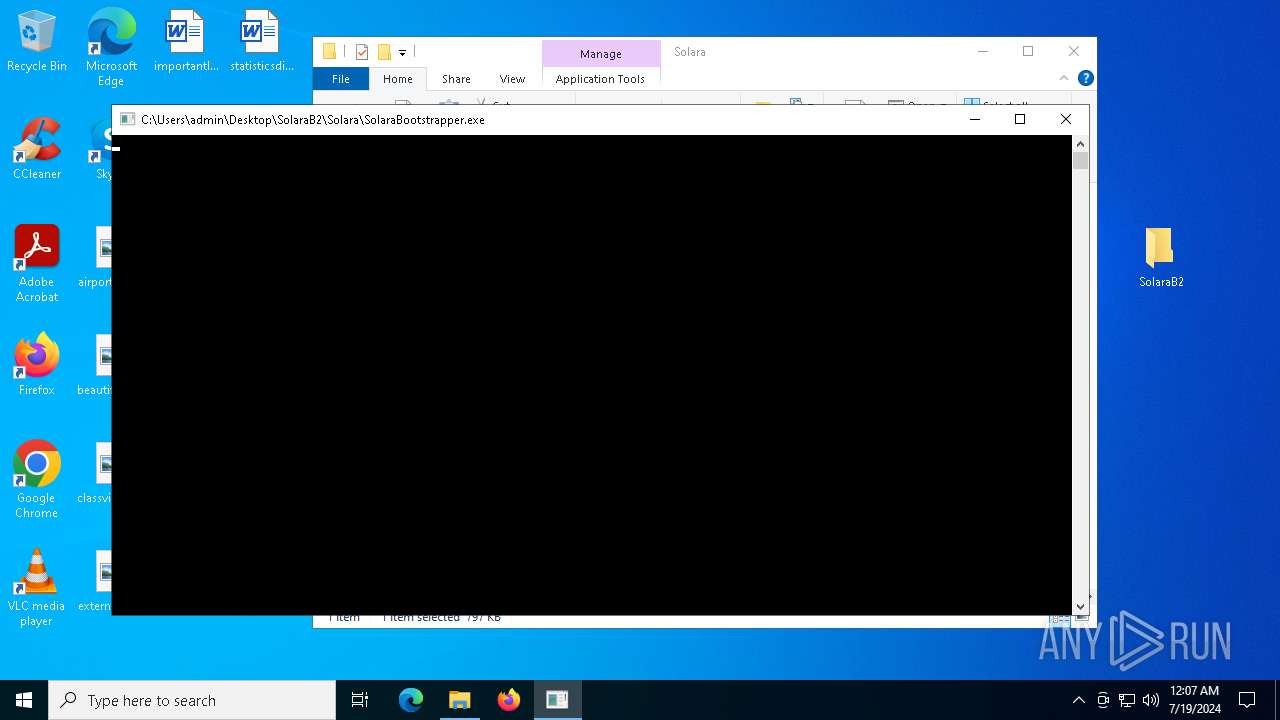
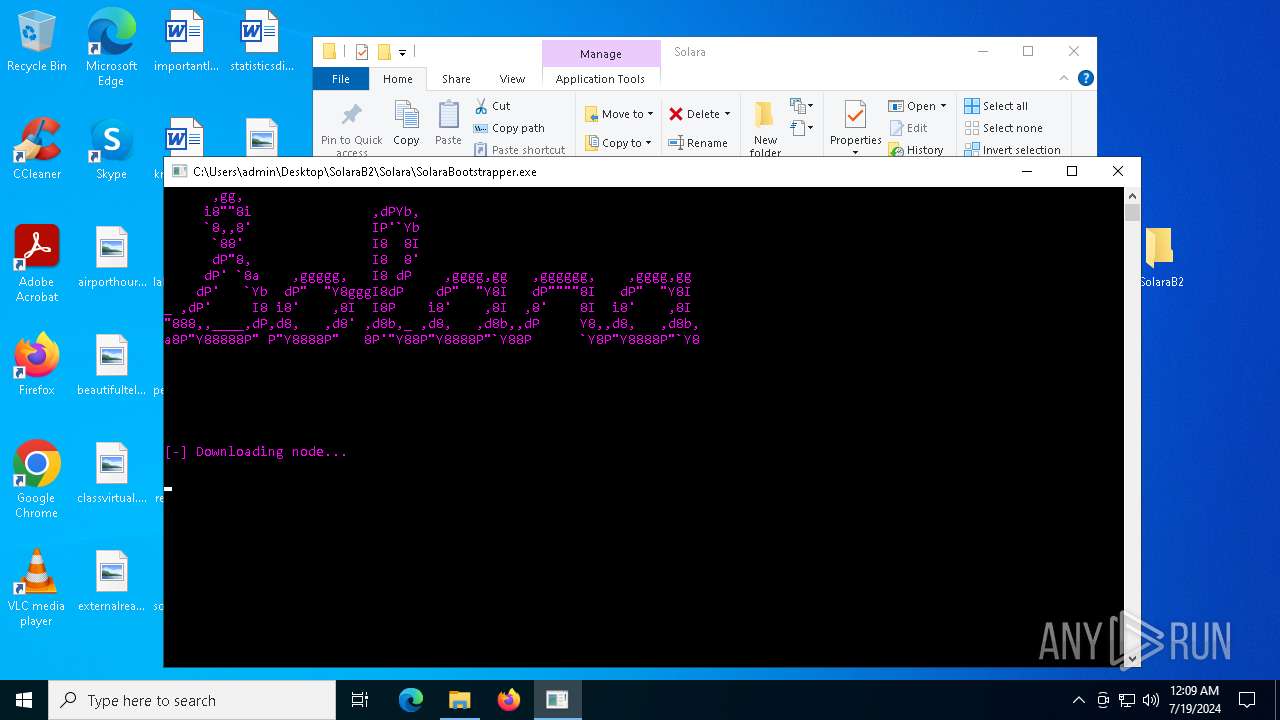
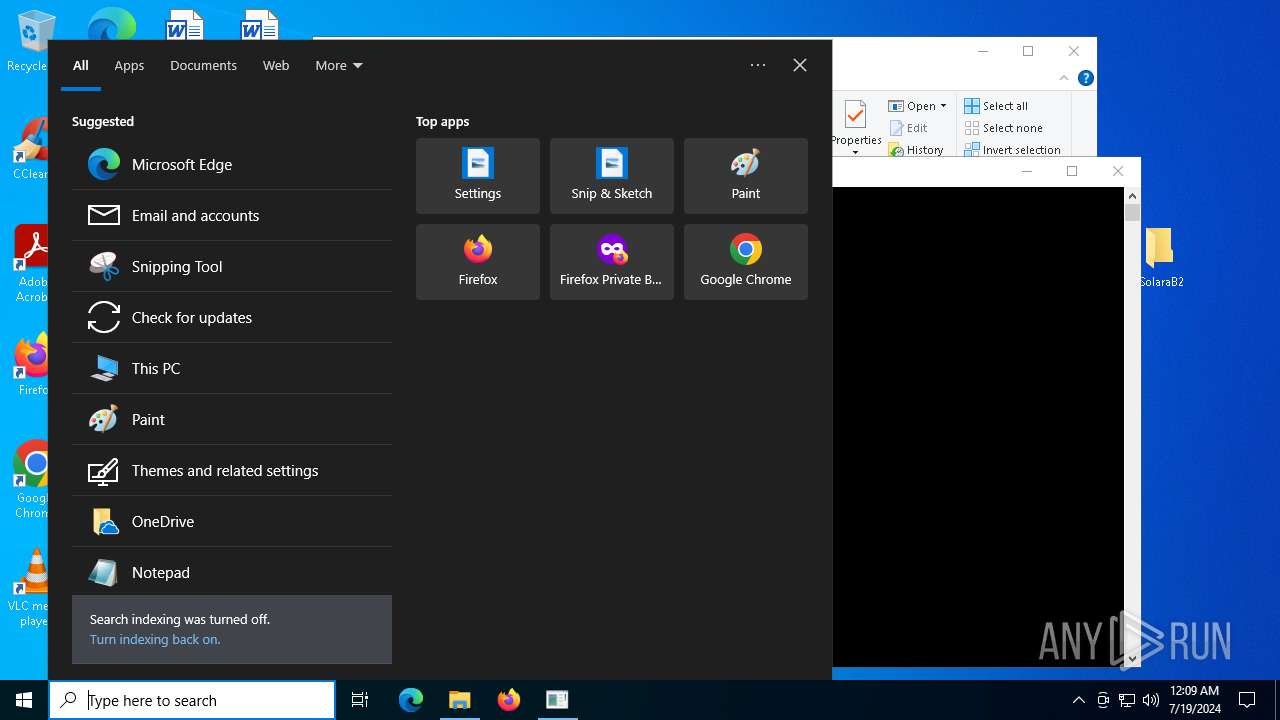
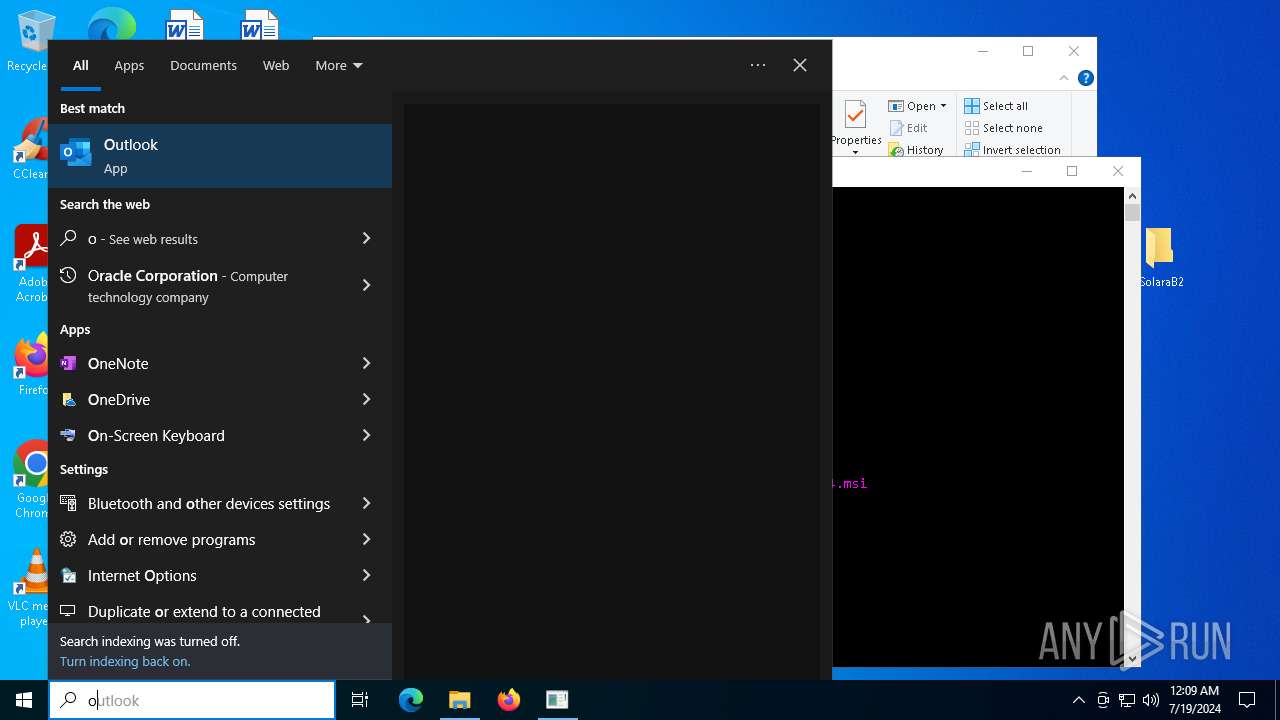
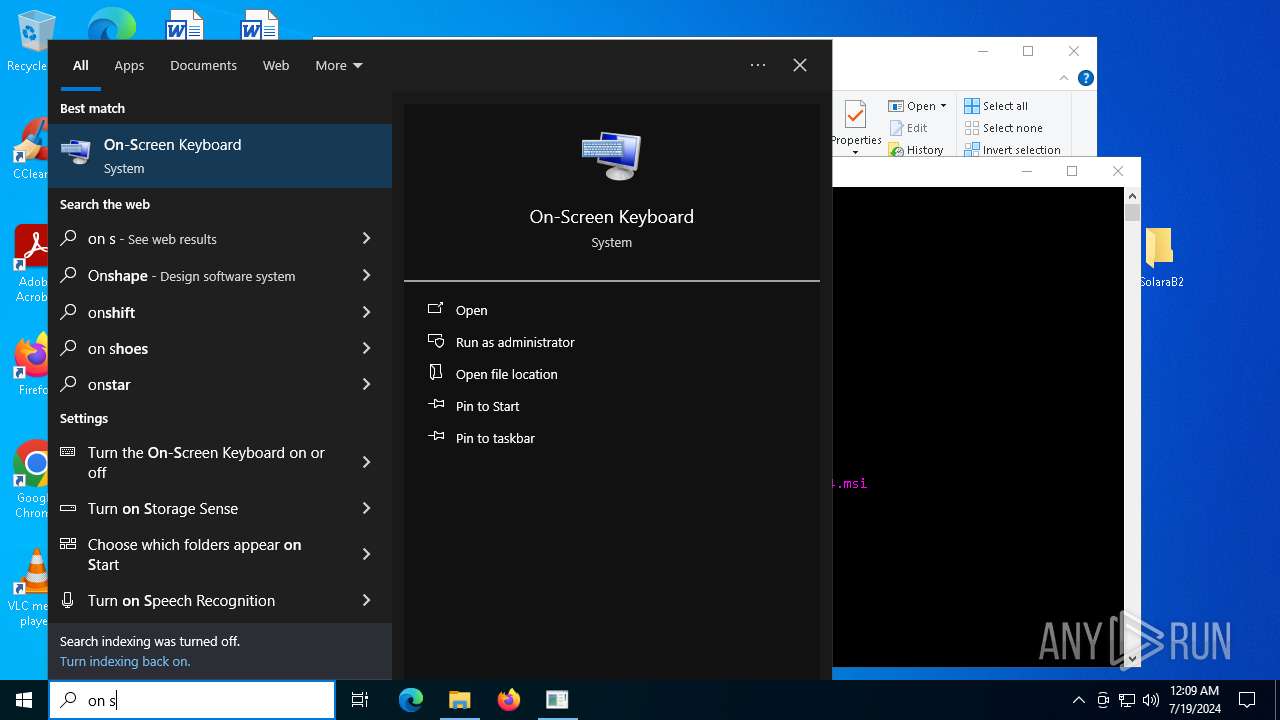
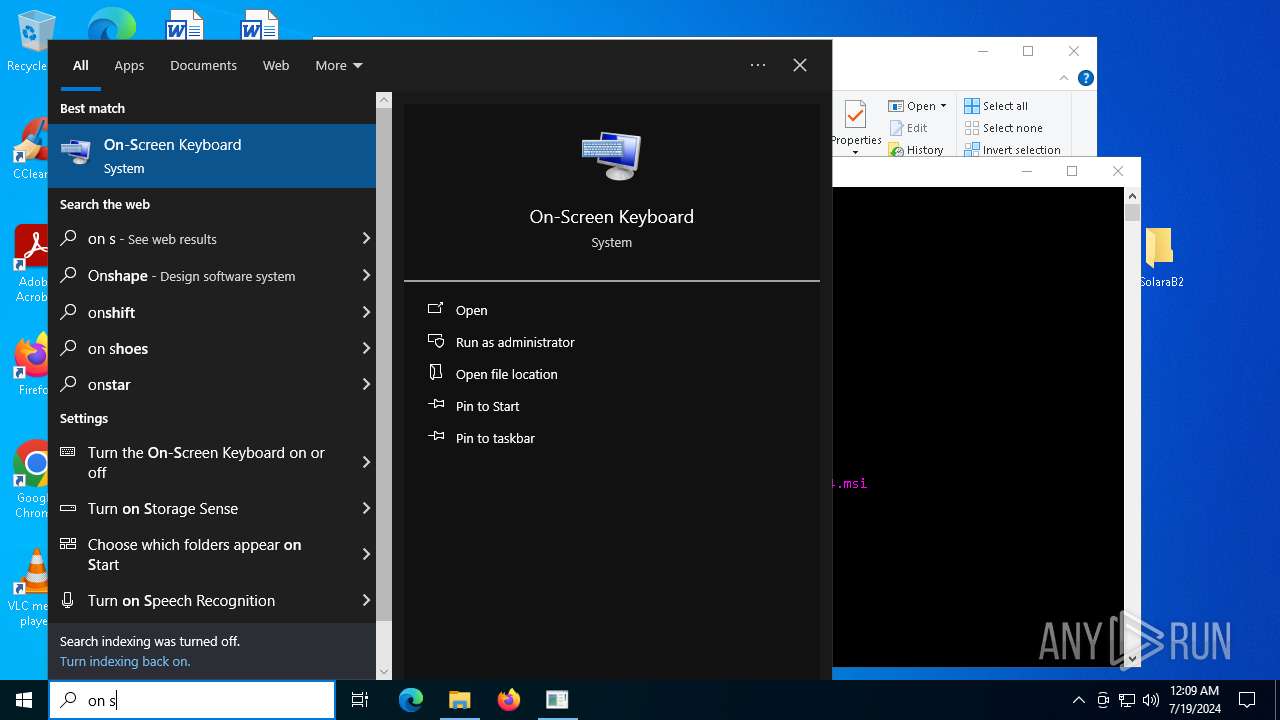
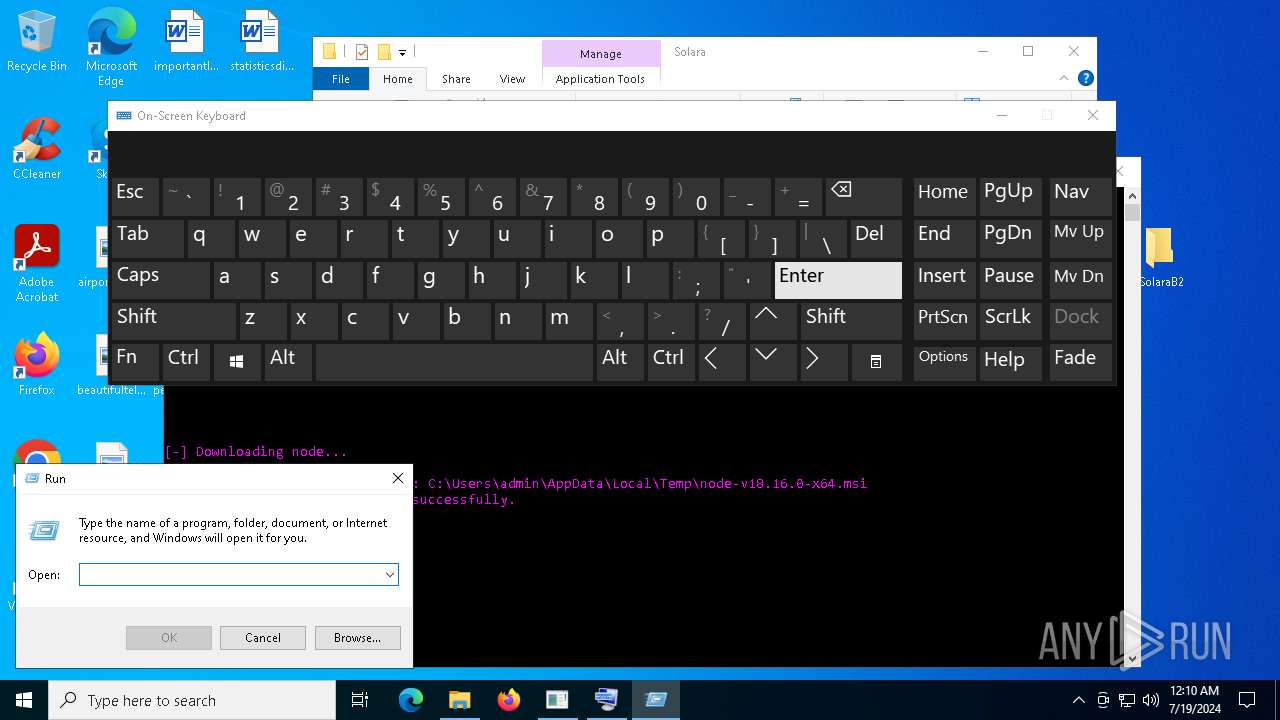
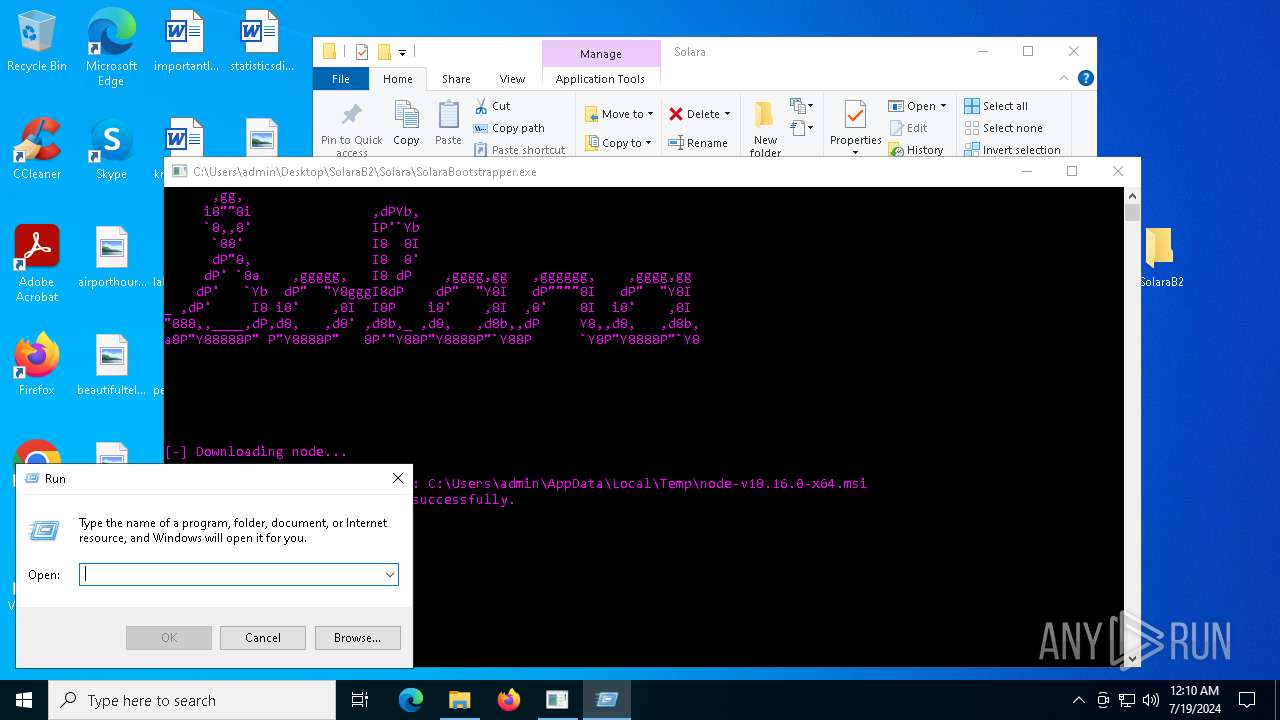
Manual execution by a user
- SolaraBootstrapper.exe (PID: 6380)
- SolaraBootstrapper.exe (PID: 7468)
- SolaraBootstrapper.exe (PID: 236)
- SolaraBootstrapper.exe (PID: 5392)
- SolaraBootstrapper.exe (PID: 1568)
- SolaraBootstrapper.exe (PID: 4168)
- osk.exe (PID: 7028)
- osk.exe (PID: 2624)
Reads the computer name
- SolaraBootstrapper.exe (PID: 6380)
- msiexec.exe (PID: 6348)
- msiexec.exe (PID: 7228)
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 7212)
- SolaraBootstrapper.exe (PID: 1568)
- msiexec.exe (PID: 4636)
- msiexec.exe (PID: 6696)
- msiexec.exe (PID: 5788)
- msiexec.exe (PID: 7084)
- msiexec.exe (PID: 1148)
- vc_redist.x64.exe (PID: 4900)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
Reads the software policy settings
- SolaraBootstrapper.exe (PID: 6380)
- msiexec.exe (PID: 6348)
- SolaraBootstrapper.exe (PID: 236)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Create files in a temporary directory
- SolaraBootstrapper.exe (PID: 6380)
- SolaraBootstrapper.exe (PID: 236)
- vc_redist.x64.exe (PID: 7212)
- SolaraBootstrapper.exe (PID: 1568)
- vc_redist.x64.exe (PID: 4900)
Reads the machine GUID from the registry
- SolaraBootstrapper.exe (PID: 6380)
- msiexec.exe (PID: 6348)
- SolaraBootstrapper.exe (PID: 236)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
Disables trace logs
- SolaraBootstrapper.exe (PID: 6380)
- SolaraBootstrapper.exe (PID: 236)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Checks proxy server information
- SolaraBootstrapper.exe (PID: 6380)
- SolaraBootstrapper.exe (PID: 236)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 5452)
- SolaraBootstrapper.exe (PID: 1568)
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Creates files or folders in the user directory
- msiexec.exe (PID: 6348)
Application launched itself
- msiexec.exe (PID: 6348)
Process checks computer location settings
- SolaraBootstrapper.exe (PID: 236)
- SolaraBootstrapper.exe (PID: 1568)
Dropped object may contain TOR URL's
- SolaraBootstrapper.exe (PID: 236)
Creates a software uninstall entry
- msiexec.exe (PID: 6348)
Process checks whether UAC notifications are on
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Themida protector has been detected
- cd57e4c171d6e8f5ea8b8f824a6a7316.exe (PID: 7588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
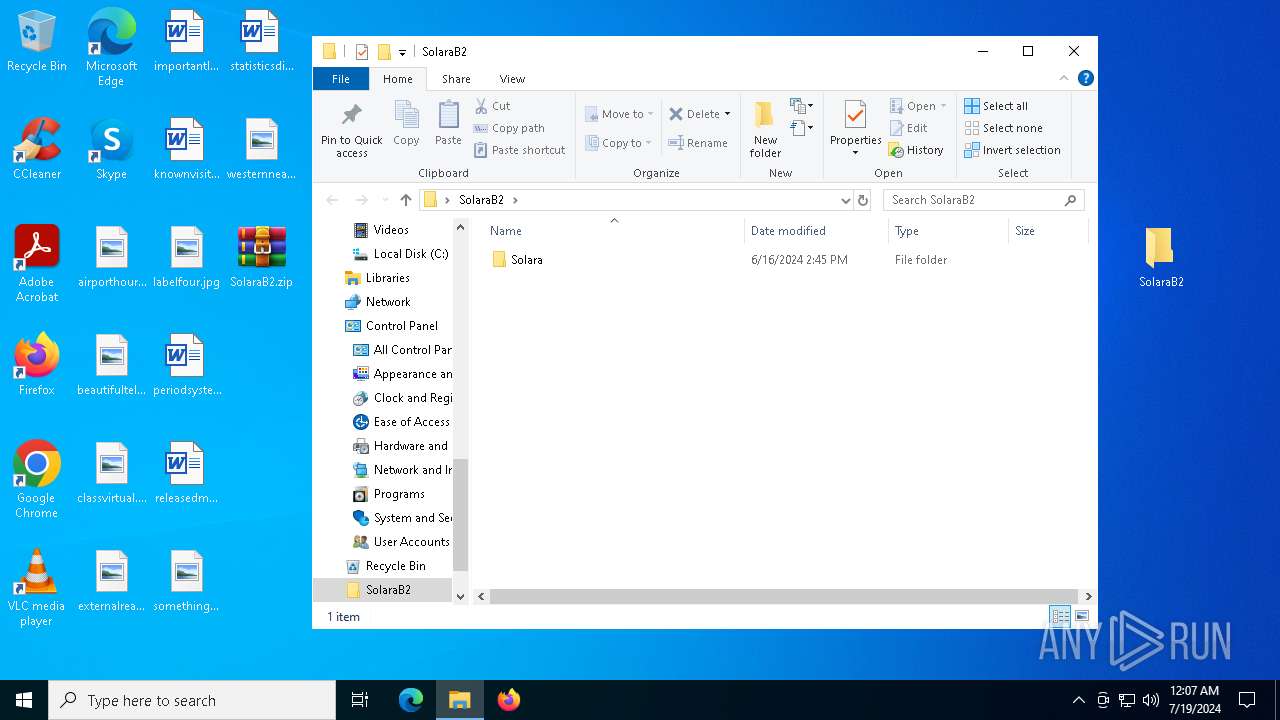
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:06:16 14:45:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | SolaraB2/Solara/ |
Total processes
161
Monitored processes
33
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
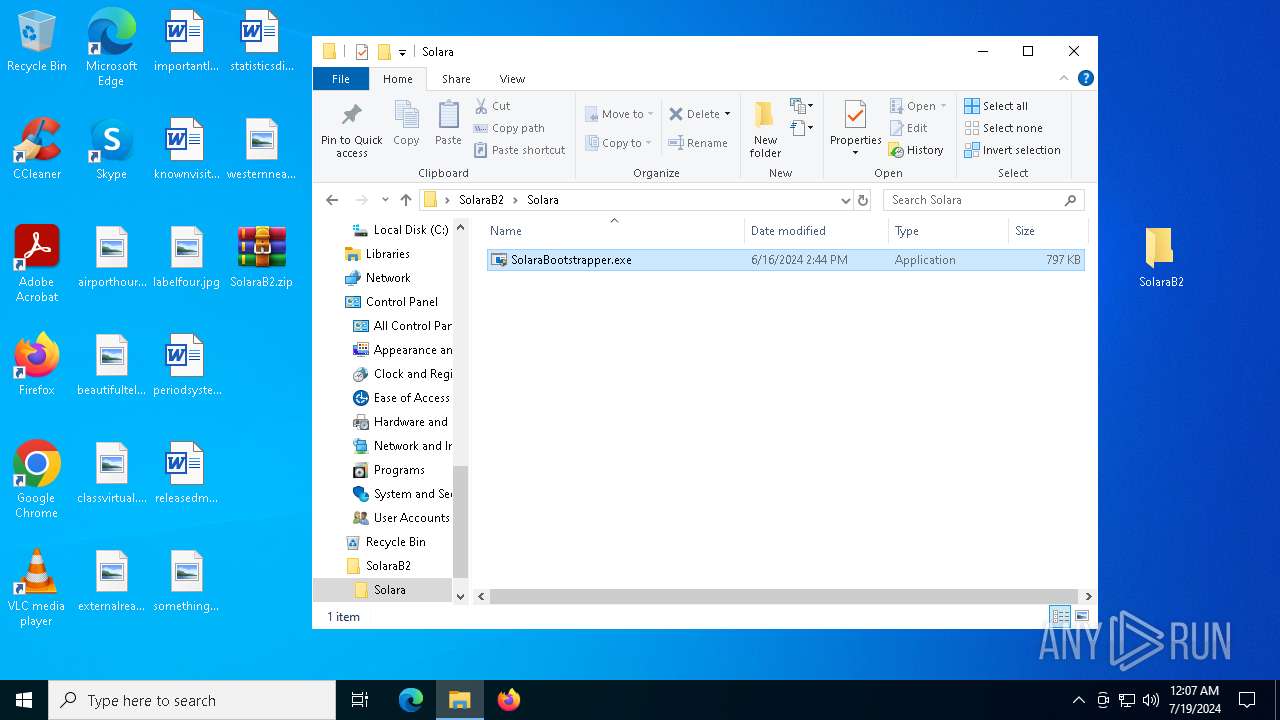
| 236 | "C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe" | C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SolaraBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | C:\Windows\syswow64\MsiExec.exe -Embedding C09E205D2E4728C2F676320FE59018C6 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe" | C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
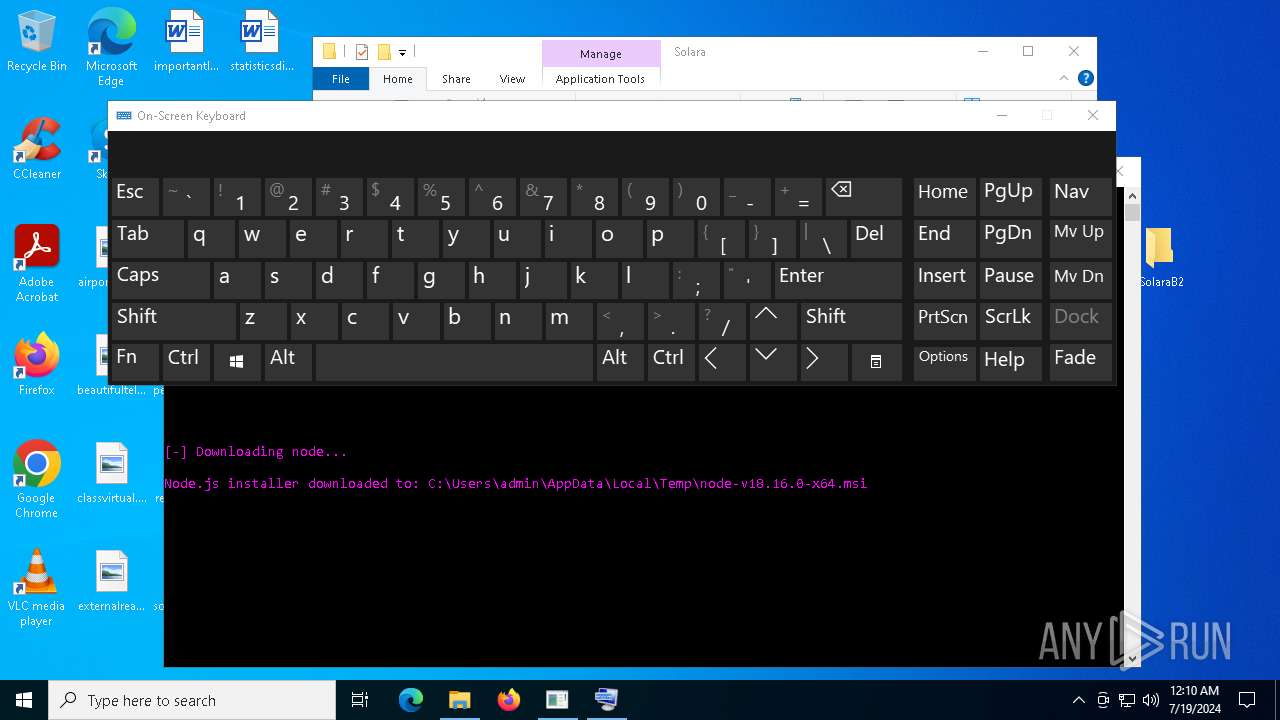
| 2116 | "msiexec" /i "C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi" /qn | C:\Windows\SysWOW64\msiexec.exe | — | SolaraBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "wevtutil.exe" im "C:\Program Files\nodejs\node_etw_provider.man" | C:\Windows\SysWOW64\wevtutil.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2624 | "C:\WINDOWS\system32\osk.exe" | C:\Windows\System32\osk.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Accessibility On-Screen Keyboard Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3772 | "msiexec" /i "C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi" /qn | C:\Windows\SysWOW64\msiexec.exe | — | SolaraBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1618 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4168 | "C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe" | C:\Users\admin\Desktop\SolaraB2\Solara\SolaraBootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
38 782
Read events
35 672
Write events
3 087
Delete events
23
Modification events
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SolaraB2.zip | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
46
Suspicious files
957
Text files
1 585
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6380 | SolaraBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi | — | |
MD5:— | SHA256:— | |||
| 6348 | msiexec.exe | C:\WINDOWS\Installer\4320a1.msi | — | |
MD5:— | SHA256:— | |||
| 6348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\42B9A473B4DAF01285A36B4D3C7B1662_178C086B699FD6C56B804AF3EF759CB5 | binary | |
MD5:A0412B65905A25FAD4FB326838D32184 | SHA256:F41B8519601D4ECF05AA03AC3A3C12631CE558C508BCE8BB3703A52F0F0FE35E | |||
| 6348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:78767BD2DBE814D4FDBBF4BB4D9A62D2 | SHA256:E8655A3F19C049DA58E758F99F20B6E4508FC6BD23621BFB7FA6F3972853121C | |||
| 6348 | msiexec.exe | C:\WINDOWS\Installer\MSI327A.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 6348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:A4EAD96694DDE1AAC979F4F9B7AA2381 | SHA256:17B75F5482B7F423B94A9330976D0162BC7984FF019661282DC4D0FACB4E7743 | |||
| 7044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7044.45190\SolaraB2\Solara\SolaraBootstrapper.exe | executable | |
MD5:36B62BA7D1B5E149A2C297F11E0417EE | SHA256:8353C5ACE62FDA6ABA330FB3396E4AAB11D7E0476F815666BD96A978724B9E0C | |||
| 6348 | msiexec.exe | C:\WINDOWS\Installer\MSI23B0.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 6348 | msiexec.exe | C:\WINDOWS\Installer\inprogressinstallinfo.ipi | binary | |
MD5:F83CC66068D6E6A45B059F4709A314CE | SHA256:E230640EDED166B826A4F1F81EC48BBD51E0A2ABCBA83CEAF1B9E5551E256580 | |||
| 6348 | msiexec.exe | C:\WINDOWS\TEMP\~DF1D63CCAB5AEF8CD8.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
40
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
5628 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7552 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4716 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
7856 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7552 | backgroundTaskHost.exe | 20.199.58.43:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3404 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6380 | SolaraBootstrapper.exe | 104.20.22.46:443 | www.nodejs.org | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arc.msn.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.nodejs.org |
| whitelisted |
www.bing.com |
| whitelisted |
nodejs.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
aka.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |