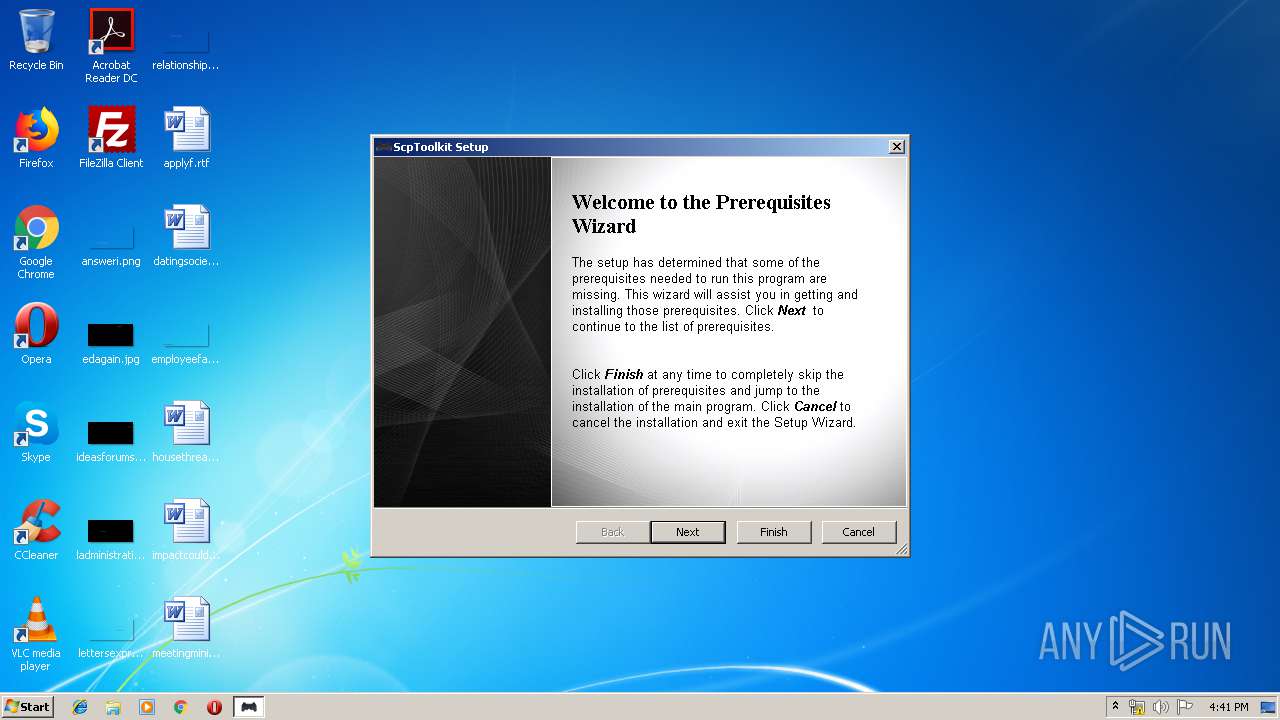
| download: | ScpToolkit_Setup.exe |
| Full analysis: | https://app.any.run/tasks/5862fca1-d38a-4f97-a5d7-3d7ddf92e72d |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2019, 15:40:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5B96F9B8B77AB460C72A52C53CD06D4E |
| SHA1: | A6430AE1EBC3AE34178980E8ED29F00C8B557CCC |
| SHA256: | DA7B1AAB547CAC97047F705381D244BB53A8BAC45581E0A897AB965CCCECF538 |
| SSDEEP: | 393216:b3AxZ6YSb7bweK0/IU+Bc6R7k+hjwewggk4GN+FGVa6VwTFdr9scIjeJEni3Mv+t:UP6nbQ8IU4k/6FAFGdVwT1scIxi3xMG |
MALICIOUS
Changes settings of System certificates
- ScpToolkit_Setup.exe (PID: 1000)
Loads the Task Scheduler DLL interface
- MsiExec.exe (PID: 3436)
Writes to a start menu file
- msiexec.exe (PID: 4024)
Loads the Task Scheduler COM API
- ngen.exe (PID: 2476)
SUSPICIOUS
Creates files in the user directory
- ScpToolkit_Setup.exe (PID: 3772)
Executed as Windows Service
- vssvc.exe (PID: 2608)
Executed via COM
- DrvInst.exe (PID: 764)
Adds / modifies Windows certificates
- ScpToolkit_Setup.exe (PID: 1000)
Creates files in the Windows directory
- MsiExec.exe (PID: 3436)
- ngen.exe (PID: 2476)
Executable content was dropped or overwritten
- ScpToolkit_Setup.exe (PID: 3772)
- msiexec.exe (PID: 4024)
Application launched itself
- ScpToolkit_Setup.exe (PID: 3772)
Executes PowerShell scripts
- MsiExec.exe (PID: 3984)
Reads Environment values
- MsiExec.exe (PID: 3984)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2532)
- MsiExec.exe (PID: 3984)
- MsiExec.exe (PID: 3436)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2608)
Application launched itself
- msiexec.exe (PID: 4024)
Searches for installed software
- msiexec.exe (PID: 4024)
Creates files in the program directory
- msiexec.exe (PID: 4024)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 4024)
Creates a software uninstall entry
- msiexec.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:23 10:36:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1132032 |
| InitializedDataSize: | 671744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd2ba3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.277.16103 |
| ProductVersionNumber: | 1.7.277.16103 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Nefarius Software Solutions |
| FileDescription: | ScpToolkit Setup |
| FileVersion: | 1.7.277.16103 |
| InternalName: | ScpToolkit_Setup |
| LegalCopyright: | Copyright (C) 2016 Nefarius Software Solutions |
| OriginalFileName: | ScpToolkit_Setup.exe |
| ProductName: | ScpToolkit |
| ProductVersion: | 1.7.277.16103 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Mar-2016 09:36:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Nefarius Software Solutions |
| FileDescription: | ScpToolkit Setup |
| FileVersion: | 1.7.277.16103 |
| InternalName: | ScpToolkit_Setup |
| LegalCopyright: | Copyright (C) 2016 Nefarius Software Solutions |
| OriginalFileName: | ScpToolkit_Setup.exe |
| ProductName: | ScpToolkit |
| ProductVersion: | 1.7.277.16103 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 23-Mar-2016 09:36:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001144A0 | 0x00114600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63578 |
.rdata | 0x00116000 | 0x0004E26A | 0x0004E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42801 |
.data | 0x00165000 | 0x000075EC | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.14531 |
.gfids | 0x0016D000 | 0x000003E8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.91254 |
.tls | 0x0016E000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0016F000 | 0x0003B780 | 0x0003B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.13052 |
.reloc | 0x001AB000 | 0x00014758 | 0x00014800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60442 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.82586 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.52771 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.84181 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.59841 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.98012 | 48439 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.48207 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.72244 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
49
Monitored processes
10
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005A8" "000003C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\AppData\Local\Temp\ScpToolkit_Setup.exe" /i "C:\Users\admin\AppData\Roaming\Nefarius Software Solutions\ScpToolkit 1.7.277.16103\install\ScpToolkit_Setup.msi" CLIENTPROCESSID="3772" AI_MORE_CMD_LINE=1 | C:\Users\admin\AppData\Local\Temp\ScpToolkit_Setup.exe | ScpToolkit_Setup.exe | ||||||||||||
User: admin Company: Nefarius Software Solutions Integrity Level: HIGH Description: ScpToolkit Setup Exit code: 0 Version: 1.7.277.16103 Modules
| |||||||||||||||
| 2476 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "C:\Program Files\Nefarius Software Solutions\ScpToolkit\ScpService.exe" /queue:1 /AppBase:"C:\Program Files\Nefarius Software Solutions\ScpToolkit\\" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2532 | C:\Windows\system32\MsiExec.exe -Embedding AA3CB15E531781C4F81CDD8ECFDCC05E C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | -NoProfile -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssF3FF.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | C:\Windows\system32\MsiExec.exe -Embedding D9490CB65C0547DCB77999B776F886A3 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\Temp\ScpToolkit_Setup.exe" | C:\Users\admin\AppData\Local\Temp\ScpToolkit_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Nefarius Software Solutions Integrity Level: MEDIUM Description: ScpToolkit Setup Exit code: 0 Version: 1.7.277.16103 Modules
| |||||||||||||||
| 3984 | C:\Windows\system32\MsiExec.exe -Embedding 814BC02E8122D90FC103859A15F19F29 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 378
Read events
965
Write events
406
Delete events
7
Modification events
| (PID) Process: | (3772) ScpToolkit_Setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3772) ScpToolkit_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3772) ScpToolkit_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1000) ScpToolkit_Setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1000) ScpToolkit_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\07E032E020B72C3F192F0628A2593A19A70F069E |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000A8569CCD21EF9CC5737C7A12DF608C2CBC545DF153000000010000006500000030633021060B2A84680186F6770205010130123010060A2B0601040182373C0101030200C03021060B2A84680186F6770205010730123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B0000000100000034000000430065007200740075006D002000540072007500730074006500640020004E006500740077006F0072006B0020004300410000006200000001000000200000005C58468D55F58E497E743982D2B50010B6D165374ACF83A7D4A32DB768C4408E1400000001000000140000000876CDCB07FF24F6C5CDEDBB90BCE284374675F71D0000000100000010000000E3F9AF952C6DF2AAA41706A77A44C20303000000010000001400000007E032E020B72C3F192F0628A2593A19A70F069E2000000001000000BF030000308203BB308202A3A00302010202030444C0300D06092A864886F70D0101050500307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B204341301E170D3038313032323132303733375A170D3239313233313132303733375A307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B20434130820122300D06092A864886F70D01010105000382010F003082010A0282010100E3FB7DA372BAC2F0C91487F56B014EE16E4007BA6D275D7FF75B2DB35AC7515FABA432A66187B66E0F86D2300297F8D76957A118395D6A6479C60159AC3C314A387CD204D24B28E8205F3B07A2CC4D73DBF3AE4FC756D55AA79689FAF3AB68D423865927CF0927BCAC6E72831C3072DFE0A2E9D2E1747519BD2A9E7B1554041BD74339AD5528C5E21ABBF4C0E4AE384933CC76859F3945D2A49EF2128C51F87CE42D7FF5AC5FEB169FB12DD1BACC9142774C25C990386FDBF0CCFB8E1E97593ED5604EE60528ED4979134BBA48DB2FF972D339CAFE1FD83472F5B440CF3101C3ECDE112D175D1FB850D15E19A769DE073328CA5095F9A754CB54865045A9F9490203010001A3423040300F0603551D130101FF040530030101FF301D0603551D0E041604140876CDCB07FF24F6C5CDEDBB90BCE284374675F7300E0603551D0F0101FF040403020106300D06092A864886F70D01010505000382010100A6A8AD22CE013DA6A3FF62D0489D8B5E72B07844E3DC1CAF09FD2348FABD2AC4B95504B510A38D27DE0B8263D0EEDE0C3779415B22B2B09A415CA670E0D4D077CB23D300E06C562FE1690D0DD9AABF218150D906A5A8FF9537D0AAFEE2B3F5992D45848AE54209D774022FF789D899E9BC27D4478DBA0D461C77CF14A41CB9A431C49C28740334FF331926A5E90D74B73E97C676E82796A366DDE1AEF2415BCA9856837370E4861AD23141BA2FBE2D135A766F4EE84E810E3F5B0322A012BE6658114ACB03C4B42A2A2D9617E03954BC48D376279D9A2D06A6C9EC39D2ABDB9F9A0B27023529B14095E7F9E89C55881946D6B734F57ECE399AD938F151F74F2C | |||
| (PID) Process: | (1000) ScpToolkit_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\07E032E020B72C3F192F0628A2593A19A70F069E |
| Operation: | write | Name: | Blob |
Value: 1900000001000000100000001F7E750B566B128AC0B8D6576D2A70A503000000010000001400000007E032E020B72C3F192F0628A2593A19A70F069E1D0000000100000010000000E3F9AF952C6DF2AAA41706A77A44C2031400000001000000140000000876CDCB07FF24F6C5CDEDBB90BCE284374675F76200000001000000200000005C58468D55F58E497E743982D2B50010B6D165374ACF83A7D4A32DB768C4408E0B0000000100000034000000430065007200740075006D002000540072007500730074006500640020004E006500740077006F0072006B002000430041000000090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308060A2B0601040182370A030406082B0601050507030606082B0601050507030753000000010000006500000030633021060B2A84680186F6770205010130123010060A2B0601040182373C0101030200C03021060B2A84680186F6770205010730123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00F0000000100000014000000A8569CCD21EF9CC5737C7A12DF608C2CBC545DF12000000001000000BF030000308203BB308202A3A00302010202030444C0300D06092A864886F70D0101050500307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B204341301E170D3038313032323132303733375A170D3239313233313132303733375A307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B20434130820122300D06092A864886F70D01010105000382010F003082010A0282010100E3FB7DA372BAC2F0C91487F56B014EE16E4007BA6D275D7FF75B2DB35AC7515FABA432A66187B66E0F86D2300297F8D76957A118395D6A6479C60159AC3C314A387CD204D24B28E8205F3B07A2CC4D73DBF3AE4FC756D55AA79689FAF3AB68D423865927CF0927BCAC6E72831C3072DFE0A2E9D2E1747519BD2A9E7B1554041BD74339AD5528C5E21ABBF4C0E4AE384933CC76859F3945D2A49EF2128C51F87CE42D7FF5AC5FEB169FB12DD1BACC9142774C25C990386FDBF0CCFB8E1E97593ED5604EE60528ED4979134BBA48DB2FF972D339CAFE1FD83472F5B440CF3101C3ECDE112D175D1FB850D15E19A769DE073328CA5095F9A754CB54865045A9F9490203010001A3423040300F0603551D130101FF040530030101FF301D0603551D0E041604140876CDCB07FF24F6C5CDEDBB90BCE284374675F7300E0603551D0F0101FF040403020106300D06092A864886F70D01010505000382010100A6A8AD22CE013DA6A3FF62D0489D8B5E72B07844E3DC1CAF09FD2348FABD2AC4B95504B510A38D27DE0B8263D0EEDE0C3779415B22B2B09A415CA670E0D4D077CB23D300E06C562FE1690D0DD9AABF218150D906A5A8FF9537D0AAFEE2B3F5992D45848AE54209D774022FF789D899E9BC27D4478DBA0D461C77CF14A41CB9A431C49C28740334FF331926A5E90D74B73E97C676E82796A366DDE1AEF2415BCA9856837370E4861AD23141BA2FBE2D135A766F4EE84E810E3F5B0322A012BE6658114ACB03C4B42A2A2D9617E03954BC48D376279D9A2D06A6C9EC39D2ABDB9F9A0B27023529B14095E7F9E89C55881946D6B734F57ECE399AD938F151F74F2C | |||
| (PID) Process: | (1000) ScpToolkit_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\07E032E020B72C3F192F0628A2593A19A70F069E |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D5E98140C51869FC462C8975620FAA780F0000000100000014000000A8569CCD21EF9CC5737C7A12DF608C2CBC545DF153000000010000006500000030633021060B2A84680186F6770205010130123010060A2B0601040182373C0101030200C03021060B2A84680186F6770205010730123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B0000000100000034000000430065007200740075006D002000540072007500730074006500640020004E006500740077006F0072006B0020004300410000006200000001000000200000005C58468D55F58E497E743982D2B50010B6D165374ACF83A7D4A32DB768C4408E1400000001000000140000000876CDCB07FF24F6C5CDEDBB90BCE284374675F71D0000000100000010000000E3F9AF952C6DF2AAA41706A77A44C20303000000010000001400000007E032E020B72C3F192F0628A2593A19A70F069E1900000001000000100000001F7E750B566B128AC0B8D6576D2A70A52000000001000000BF030000308203BB308202A3A00302010202030444C0300D06092A864886F70D0101050500307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B204341301E170D3038313032323132303733375A170D3239313233313132303733375A307E310B300906035504061302504C31223020060355040A1319556E697A65746F20546563686E6F6C6F6769657320532E412E31273025060355040B131E43657274756D2043657274696669636174696F6E20417574686F72697479312230200603550403131943657274756D2054727573746564204E6574776F726B20434130820122300D06092A864886F70D01010105000382010F003082010A0282010100E3FB7DA372BAC2F0C91487F56B014EE16E4007BA6D275D7FF75B2DB35AC7515FABA432A66187B66E0F86D2300297F8D76957A118395D6A6479C60159AC3C314A387CD204D24B28E8205F3B07A2CC4D73DBF3AE4FC756D55AA79689FAF3AB68D423865927CF0927BCAC6E72831C3072DFE0A2E9D2E1747519BD2A9E7B1554041BD74339AD5528C5E21ABBF4C0E4AE384933CC76859F3945D2A49EF2128C51F87CE42D7FF5AC5FEB169FB12DD1BACC9142774C25C990386FDBF0CCFB8E1E97593ED5604EE60528ED4979134BBA48DB2FF972D339CAFE1FD83472F5B440CF3101C3ECDE112D175D1FB850D15E19A769DE073328CA5095F9A754CB54865045A9F9490203010001A3423040300F0603551D130101FF040530030101FF301D0603551D0E041604140876CDCB07FF24F6C5CDEDBB90BCE284374675F7300E0603551D0F0101FF040403020106300D06092A864886F70D01010505000382010100A6A8AD22CE013DA6A3FF62D0489D8B5E72B07844E3DC1CAF09FD2348FABD2AC4B95504B510A38D27DE0B8263D0EEDE0C3779415B22B2B09A415CA670E0D4D077CB23D300E06C562FE1690D0DD9AABF218150D906A5A8FF9537D0AAFEE2B3F5992D45848AE54209D774022FF789D899E9BC27D4478DBA0D461C77CF14A41CB9A431C49C28740334FF331926A5E90D74B73E97C676E82796A366DDE1AEF2415BCA9856837370E4861AD23141BA2FBE2D135A766F4EE84E810E3F5B0322A012BE6658114ACB03C4B42A2A2D9617E03954BC48D376279D9A2D06A6C9EC39D2ABDB9F9A0B27023529B14095E7F9E89C55881946D6B734F57ECE399AD938F151F74F2C | |||
| (PID) Process: | (4024) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000030BE149D101ED501B80F0000440C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000030BE149D101ED501B80F0000440C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
Executable files
71
Suspicious files
15
Text files
196
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Roaming\Nefarius Software Solutions\ScpToolkit 1.7.277.16103\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Cab42BE.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Tar42BF.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Cab42DF.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Tar42E0.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Cab436E.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\Tar436F.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI4768.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI4789.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | ScpToolkit_Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI47B9.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3772 | ScpToolkit_Setup.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3772 | ScpToolkit_Setup.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3772 | ScpToolkit_Setup.exe | 23.111.11.204:80 | repository.certum.pl | netDNA | US | unknown |
3772 | ScpToolkit_Setup.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
repository.certum.pl |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |