| File name: | WIN_DA_INSTALL_4.0.2.1.exe |
| Full analysis: | https://app.any.run/tasks/ca868e7b-e972-4adc-bdc7-dc2f5bd20bda |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2021, 19:39:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 704D05871E51A3609C381AAB6A40D3B7 |
| SHA1: | DA74D6ED70593E832C509E6BE7B96C9AA56C01A1 |
| SHA256: | DA6DE0B9942733A46FFC5A5E96C6F5CB2FC4FC89C6B3ED6A7AFEEA212D880EF5 |
| SSDEEP: | 393216:Y4jualIsDJMvSVyOOL6NNwmQV1Uhxv2I0:UalxtGZL6AmQzGxv2I0 |
MALICIOUS
Changes the autorun value in the registry
- WIN_DA_INSTALL_4.0.2.1.exe (PID: 2512)
Drops executable file immediately after starts
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- rdmappweb-4.6.0-ms-windows-x86.exe (PID: 820)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 3820)
- Setup.exe (PID: 1204)
- rdmappweb-4.6.0-ms-windows-x86.exe (PID: 820)
- CertMgr.exe (PID: 980)
- certutil.exe (PID: 1848)
- rdmappman.exe (PID: 3816)
- rdmappman.exe (PID: 2068)
- RDMDAService.exe (PID: 2516)
- rdmappman.exe (PID: 3796)
- RDMAppweb.exe (PID: 1012)
- RDMDAService.exe (PID: 1920)
- rdmappman.exe (PID: 2708)
- RDMDAService.exe (PID: 3848)
- rdmappman.exe (PID: 2640)
- rdmappman.exe (PID: 792)
- RDMAppweb.exe (PID: 1008)
Actions looks like stealing of personal data
- vcredist_x86.exe (PID: 3820)
Changes settings of System certificates
- Setup.exe (PID: 1204)
- CertMgr.exe (PID: 980)
Loads dropped or rewritten executable
- Setup.exe (PID: 1204)
- certutil.exe (PID: 1848)
- rdmappman.exe (PID: 3816)
- rdmappman.exe (PID: 2068)
- rdmappman.exe (PID: 2708)
- rdmappman.exe (PID: 3796)
- RDMAppweb.exe (PID: 1012)
- rdmappman.exe (PID: 792)
- RDMAppweb.exe (PID: 1008)
- rdmappman.exe (PID: 2640)
Starts NET.EXE for service management
- MsiExec.exe (PID: 1972)
SUSPICIOUS
Drops a file with too old compile date
- rdmappweb-4.6.0-ms-windows-x86.exe (PID: 820)
- WIN_DA_INSTALL_4.0.2.1.exe (PID: 2512)
- vcredist_x86.exe (PID: 3820)
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- MsiExec.exe (PID: 1972)
Creates a directory in Program Files
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
Executable content was dropped or overwritten
- WIN_DA_INSTALL_4.0.2.1.exe (PID: 2512)
- rdmappweb-4.6.0-ms-windows-x86.exe (PID: 820)
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- vcredist_x86.exe (PID: 3820)
- MsiExec.exe (PID: 1972)
Drops a file that was compiled in debug mode
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- vcredist_x86.exe (PID: 3820)
- MsiExec.exe (PID: 1972)
Adds / modifies Windows certificates
- Setup.exe (PID: 1204)
Application launched itself
- cmd.exe (PID: 3452)
Starts CMD.EXE for commands execution
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- cmd.exe (PID: 3452)
Creates files in the user directory
- certutil.exe (PID: 1848)
Creates or modifies windows services
- rdmappman.exe (PID: 2068)
Executed as Windows Service
- rdmappman.exe (PID: 3796)
- rdmappman.exe (PID: 792)
- RDMDAService.exe (PID: 3848)
Starts Microsoft Installer
- WIN_DA_INSTALL_4.0.2.1.exe (PID: 2512)
Creates files in the program directory
- RDMAppweb.exe (PID: 1012)
- RDMAppweb.exe (PID: 1008)
Creates/Modifies COM task schedule object
- MsiExec.exe (PID: 3564)
Creates files in the Windows directory
- RDMAppweb.exe (PID: 1008)
INFO
Dropped object may contain Bitcoin addresses
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
Creates files in the program directory
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
Creates a software uninstall entry
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
Application was dropped or rewritten from another process
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
Reads settings of System Certificates
- Setup.exe (PID: 1204)
Loads dropped or rewritten executable
- rdmappweb-4.6.0-ms-windows-x86.tmp (PID: 2672)
- MsiExec.exe (PID: 1972)
- MsiExec.exe (PID: 3564)
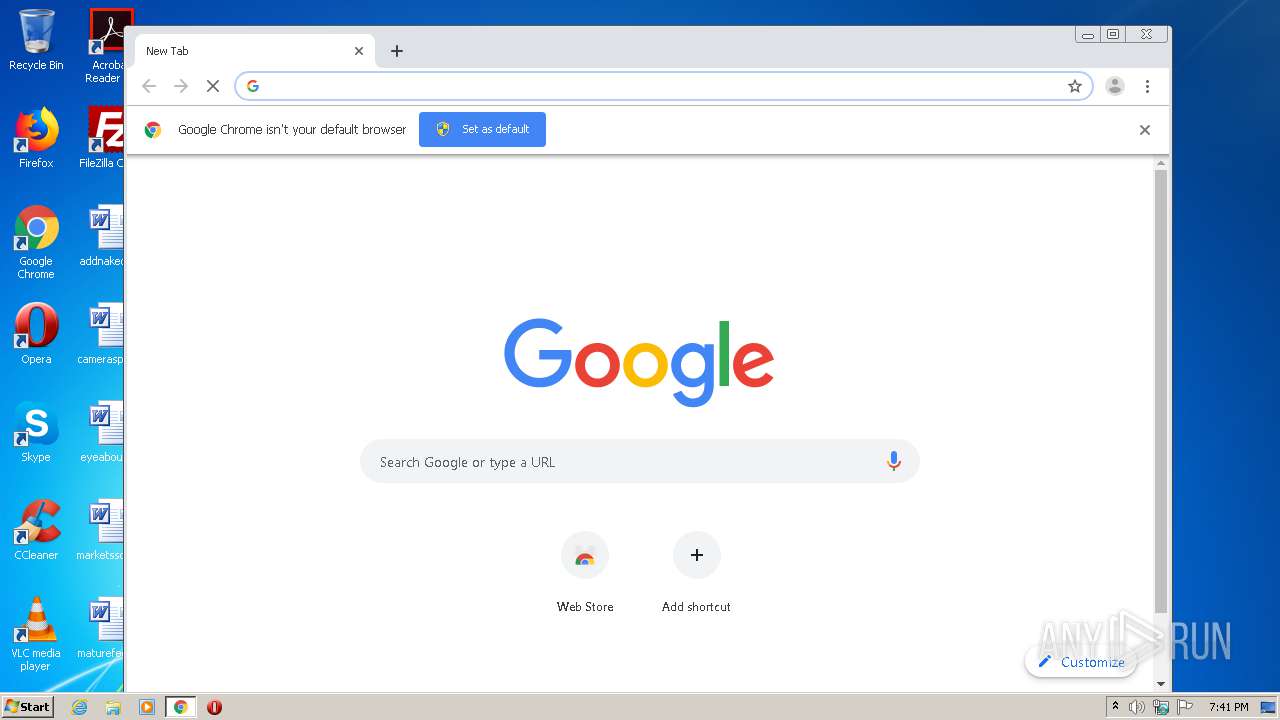
Reads the hosts file
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2164)
Application launched itself
- chrome.exe (PID: 3548)
Manual execution by user
- chrome.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (38.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.3) |
| .scr | | | Windows screen saver (16.2) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:09:11 07:56:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 499712 |
| InitializedDataSize: | 204800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x47ac7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.2.1 |
| ProductVersionNumber: | 4.0.2.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | RDM Corporation |
| FileDescription: | Setup Launcher |
| FileVersion: | 4.0.2.1 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2008 Acresso Software Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFileName: | Setup.exe |
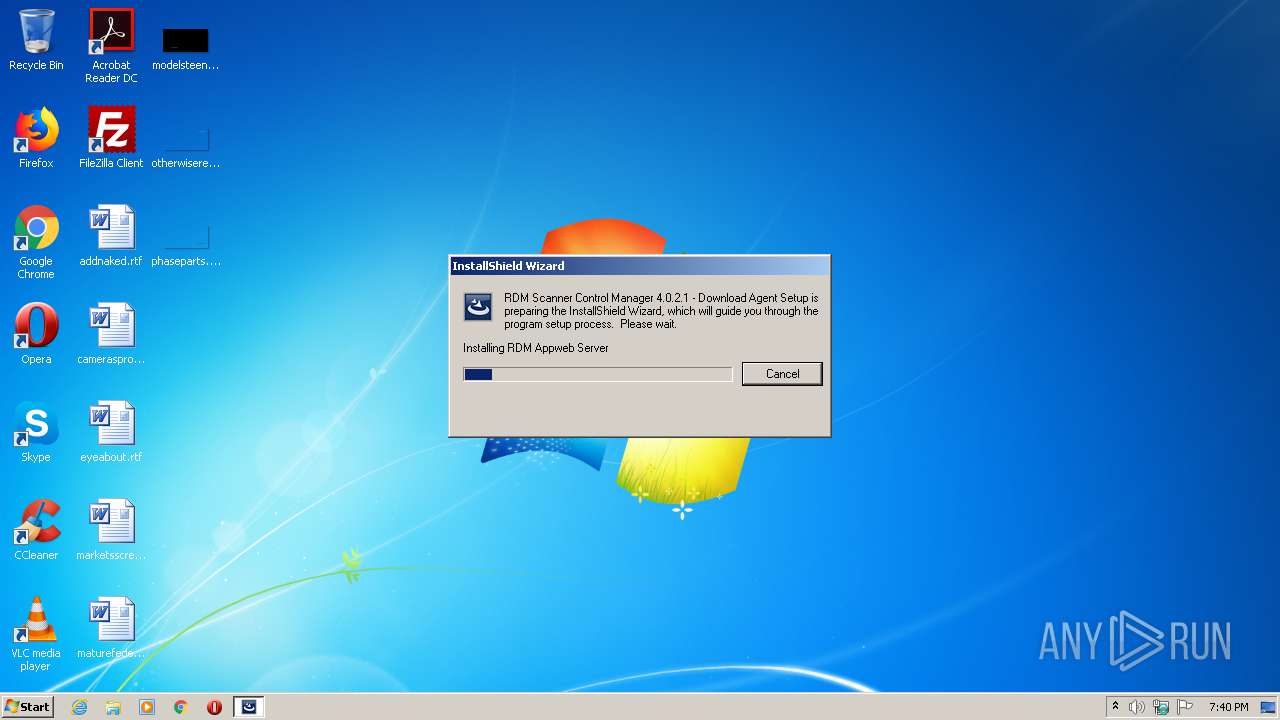
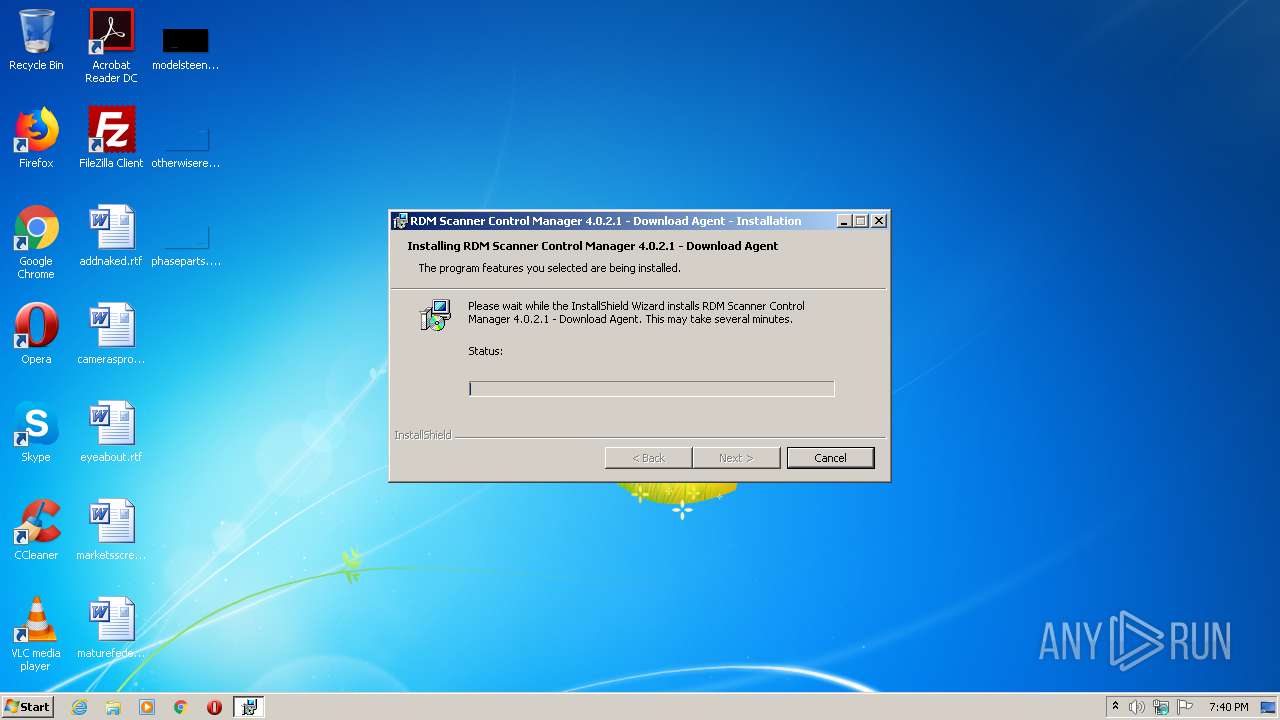
| ProductName: | RDM Scanner Control Manager 4.0.2.1 - Download Agent |
| ProductVersion: | 4.0.2.1 |
| InternalBuildNumber: | 82160 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Sep-2008 05:56:15 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RDM Corporation |
| FileDescription: | Setup Launcher |
| FileVersion: | 4.0.2.1 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2008 Acresso Software Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFilename: | Setup.exe |
| ProductName: | RDM Scanner Control Manager 4.0.2.1 - Download Agent |
| ProductVersion: | 4.0.2.1 |
| Internal Build Number: | 82160 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 11-Sep-2008 05:56:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00079EE0 | 0x0007A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63186 |
.rdata | 0x0007B000 | 0x0001398E | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00464 |
.data | 0x0008F000 | 0x0000E08C | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.81238 |
.rsrc | 0x0009E000 | 0x00013C40 | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.43023 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02144 | 899 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.835 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.35696 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.57777 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.81004 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.48972 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
90
Monitored processes
42
Malicious processes
14
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,7134950604210657671,11865251633862907723,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6126459601855780860 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\RDM Corporation\RDM Appweb\bin\rdmappman.exe" | C:\Program Files\RDM Corporation\RDM Appweb\bin\rdmappman.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\AppData\Local\Temp\{53A1175C-EDC0-4D8F-81F9-DC5342259211}\{FDC4977B-2C56-470A-A713-3C7C7D4D9FC3}\rdmappweb-4.6.0-ms-windows-x86.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\{53A1175C-EDC0-4D8F-81F9-DC5342259211}\{FDC4977B-2C56-470A-A713-3C7C7D4D9FC3}\rdmappweb-4.6.0-ms-windows-x86.exe | WIN_DA_INSTALL_4.0.2.1.exe | ||||||||||||
User: admin Company: RDM Corporation Integrity Level: HIGH Description: RDM Appweb Setup Exit code: 0 Version: 4.6.0.8 Modules
| |||||||||||||||
| 980 | "C:\Program Files\RDM Corporation\RDM Appweb/CertMgr.exe" -add -all -c rdmroot.pem -s -r localmachine Root | C:\Program Files\RDM Corporation\RDM Appweb\CertMgr.exe | — | rdmappweb-4.6.0-ms-windows-x86.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7134950604210657671,11865251633862907723,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15242018159986552517 --mojo-platform-channel-handle=3624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\RDM Corporation\RDM Appweb\bin\RDMAppweb.exe" | C:\Program Files\RDM Corporation\RDM Appweb\bin\RDMAppweb.exe | rdmappman.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\RDM Corporation\RDM Appweb\bin\RDMAppweb.exe" | C:\Program Files\RDM Corporation\RDM Appweb\bin\RDMAppweb.exe | — | rdmappman.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1204 | c:\07a598a54cbf4d2ed1e4ad26b3067b80\Setup.exe /q /norestart | c:\07a598a54cbf4d2ed1e4ad26b3067b80\Setup.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 10.0.40219.1 built by: SP1Rel Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7134950604210657671,11865251633862907723,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11727341561738274831 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | Net stop "RdmAppWeb" | C:\Windows\system32\Net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 058
Read events
850
Write events
169
Delete events
39
Modification events
| (PID) Process: | (2512) WIN_DA_INSTALL_4.0.2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | %IS_PREREQ%-RDM Scanner Control Manager 4.0.2.1 - Download Agent |
Value: 0 | |||
| (PID) Process: | (2512) WIN_DA_INSTALL_4.0.2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | ISSetupPrerequisistes |
Value: "C:\Users\admin\AppData\Local\Temp\WIN_DA_INSTALL_4.0.2.1.exe" | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 700A000026912F32531FD701 | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 474AD21D1286B9D2FF639C29AE9C7F03BCE1572A6C024470C54E8F2C6F4CA35C | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\RDM Corporation\RDM Appweb\redist\vcredist_x86.exe | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 95C7172D2F72B7E9C4A3F8F748AD5FF4EF9BABFA30FDE261C48C7A86C3E8DFC0 | |||
| (PID) Process: | (2512) WIN_DA_INSTALL_4.0.2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2512) WIN_DA_INSTALL_4.0.2.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2672) rdmappweb-4.6.0-ms-windows-x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RDM Appweb_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
Executable files
61
Suspicious files
36
Text files
195
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\_is9461.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\_is9462.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\_is9473.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\~9472.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\_is9494.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | WIN_DA_INSTALL_4.0.2.1.exe | C:\Users\admin\AppData\Local\Temp\_is94C3.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | rdmappweb-4.6.0-ms-windows-x86.tmp | C:\Program Files\RDM Corporation\RDM Appweb\is-SAQK5.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | rdmappweb-4.6.0-ms-windows-x86.tmp | C:\Program Files\RDM Corporation\RDM Appweb\redist\is-AFS7L.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | rdmappweb-4.6.0-ms-windows-x86.tmp | C:\Program Files\RDM Corporation\RDM Appweb\is-FJ4TF.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | rdmappweb-4.6.0-ms-windows-x86.tmp | C:\Program Files\RDM Corporation\RDM Appweb\is-PHRFO.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2164 | chrome.exe | GET | — | 142.250.34.2:80 | http://edgedl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2164 | chrome.exe | 172.217.19.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.16.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.20.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.20.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.19.110:443 | ogs.google.ae | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.ae |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|
RDMAppweb.exe | RDMDA(604):
RDMDA instance has been loaded. Instance count = 0
|
RDMDAService.exe | (2600)RDMDASVC: Assertion failed at line 200 of ErrorUtils.cpp, rc=0x80040154
|
RDMDAService.exe | (2600)RDMDASVC: InitializeSecurity() returns 0
|
RDMDAService.exe | (2600)RDMDASVC: Executing C:\Program Files\RDM Corporation\RDM Appweb\bin\rdmappman.exe
|
RDMAppweb.exe | RDMDA(604): LoadServiceInterface() succeeded.
|
RDMAppweb.exe | RDMDA(604): Released service interface.
|
RDMAppweb.exe | RDMDA(604): get_InstallationStatus() (from RDMDAService) returns Success
|
RDMAppweb.exe | RDMDA(604): Firing event <scanresp status="Exception"><exception id="Progress"><deviceId>default</deviceId><summary>Event</summary><recoveryid>0</recoveryid><description>Download progress update</description><DownloadProgress>100</DownloadProgress><OverallProgress>100</OverallProgress></exception></scanresp>
|
RDMAppweb.exe | RDMDA(604): Firing event <scanresp status="Exception"><exception id="NoMoreItems"><deviceId>default</deviceId><summary>Event</summary><recoveryid>0</recoveryid><scannererrorcode>1</scannererrorcode><description>Installation completed successfully</description></exception></scanresp>
|