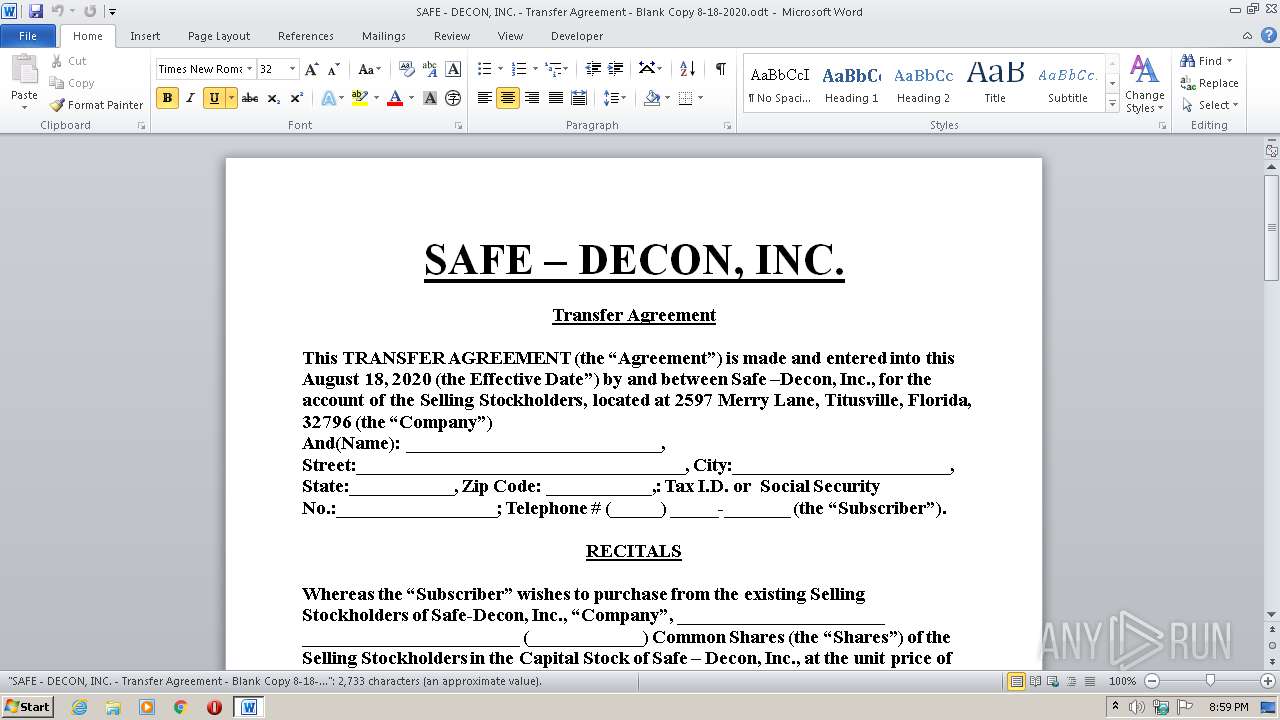
| File name: | SAFE - DECON, INC. - Transfer Agreement - Blank Copy 8-18-2020.odt |
| Full analysis: | https://app.any.run/tasks/4f10d40e-5ec9-49d5-a655-fb0bebf418a5 |
| Verdict: | No threats detected |
| Analysis date: | August 18, 2020, 19:59:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/vnd.oasis.opendocument.text |
| File info: | OpenDocument Text |
| MD5: | B844412A50EC9FBFCBE767C55A13F7F9 |
| SHA1: | 6521BD25575812F1B8FA1075E7F3B27983937195 |
| SHA256: | DA6CBD343F8A6C58684F2284378993A65F8CF8DC87D704BBB9343FA73F999667 |
| SSDEEP: | 192:XzAWUmk/+uKJgYeH3qNGxvqya+yfIWG3QHU8E3+9mI+su:rzuKqT6UFC+yfIt3V8jmnL |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2280)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .odt | | | OpenDocument Text document (86.7) |
|---|---|---|
| .zip | | | ZIP compressed archive (6.6) |
EXIF
XMP
| Generator: | MicrosoftOffice/15.0 MicrosoftWord |
|---|---|
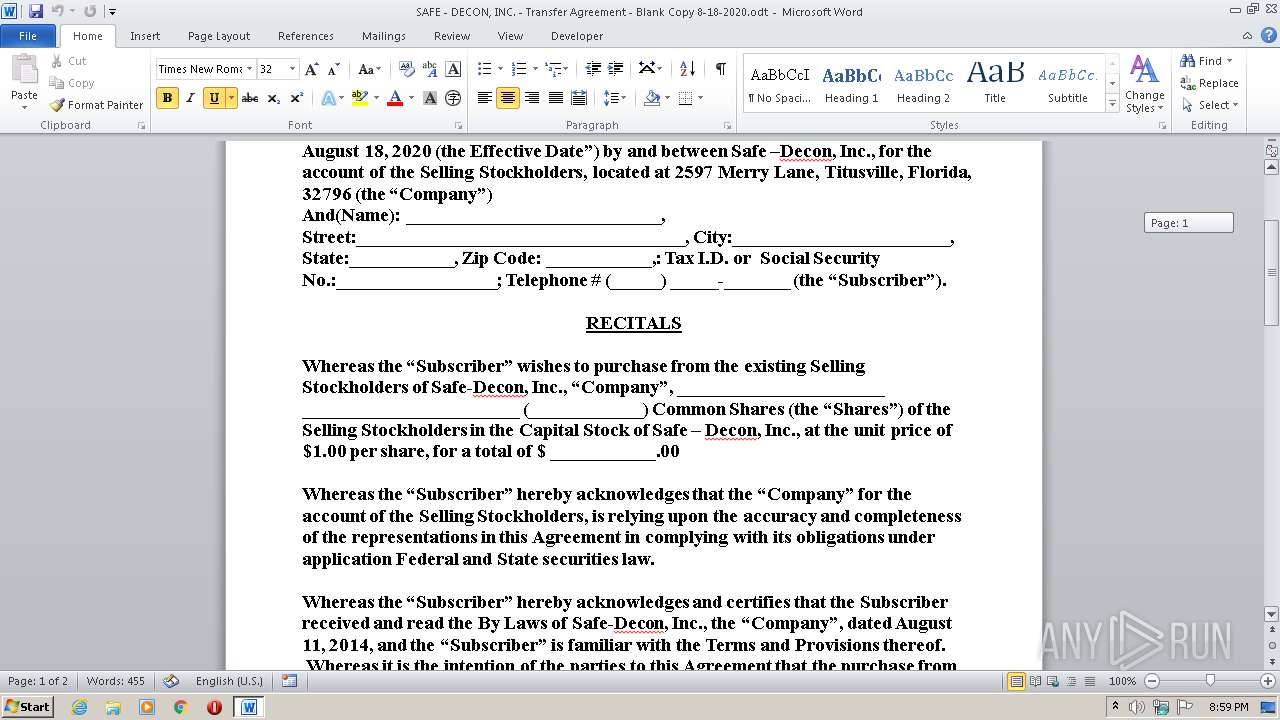
| Initial-creator: | Paul Rondeau |
| Creator: | Paul Rondeau |
| Creation-date: | 2020:08:18 19:25:00Z |
| Date: | 2020:08:18 19:30:00Z |
| Print-date: | 2019:09:22 17:00:00Z |
| TemplateHref: | Normal |
| TemplateType: | simple |
| Editing-cycles: | 3 |
| Editing-duration: | PT360S |
| Document-statisticPage-count: | 2 |
| Document-statisticParagraph-count: | 6 |
| Document-statisticWord-count: | 494 |
| Document-statisticCharacter-count: | 3309 |
| Document-statisticRow-count: | 23 |
| Document-statisticNon-whitespace-character-count: | 2821 |
Total processes
38
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2280 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SAFE - DECON, INC. - Transfer Agreement - Blank Copy 8-18-2020.odt" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 305
Read events
1 019
Write events
154
Delete events
132
Modification events
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )d6 |
Value: 29643600E8080000010000000000000000000000 | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR829.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6FB75E0E-F66A-44CA-957D-71C4F874BEF9}.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{983CB438-5602-49C8-A2A3-A4B2A6691CFF}.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{1FBCD046-03E5-4A39-95C9-C2D598653BC6}.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$FE - DECON, INC. - Transfer Agreement - Blank Copy 8-18-2020.odt | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report