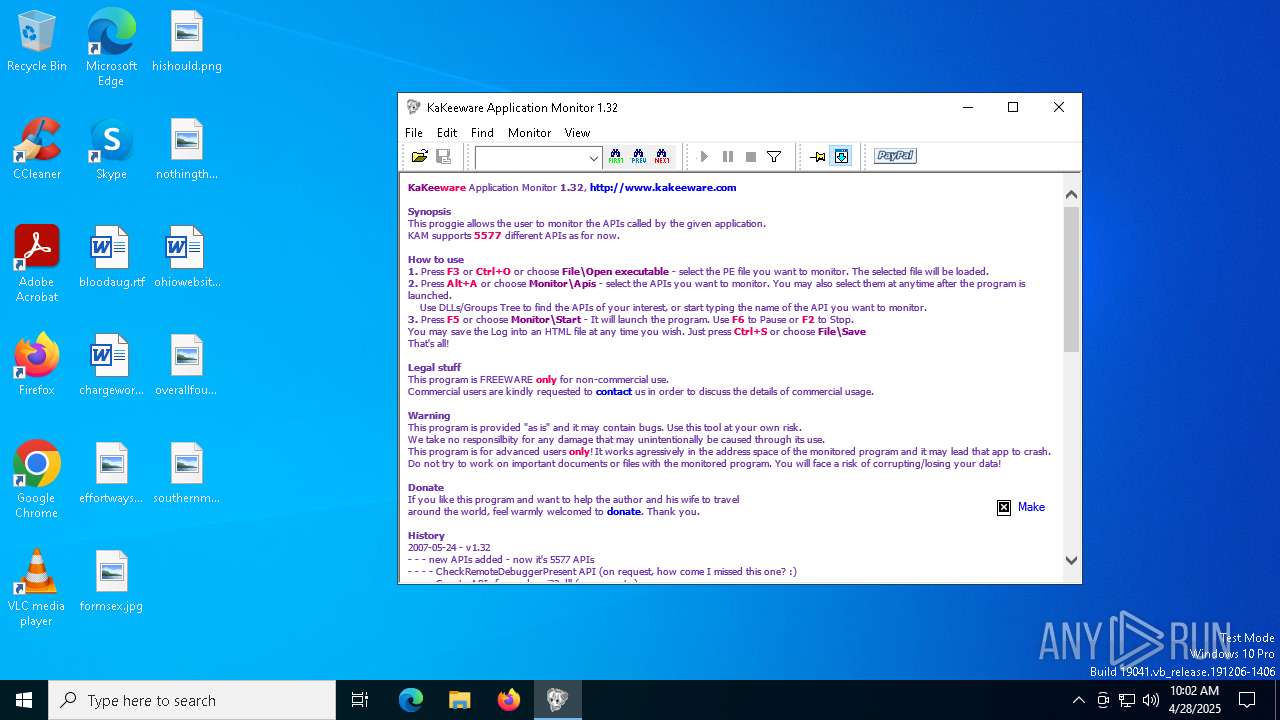
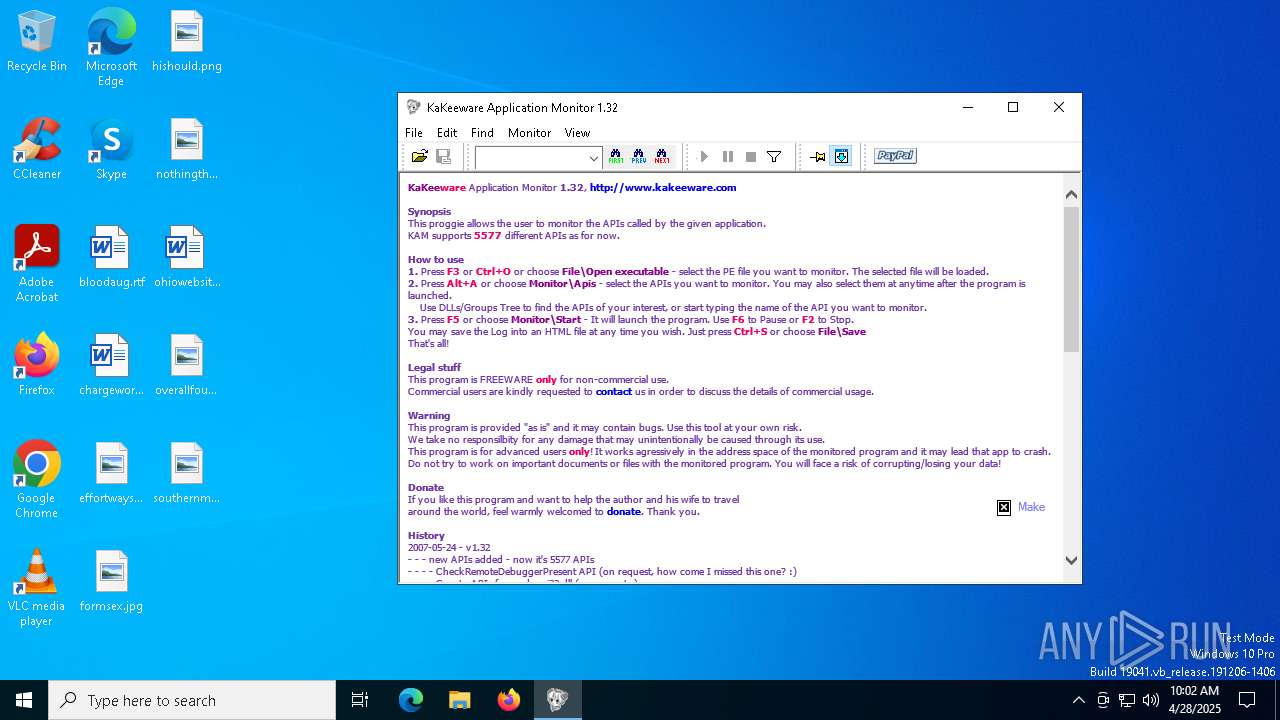
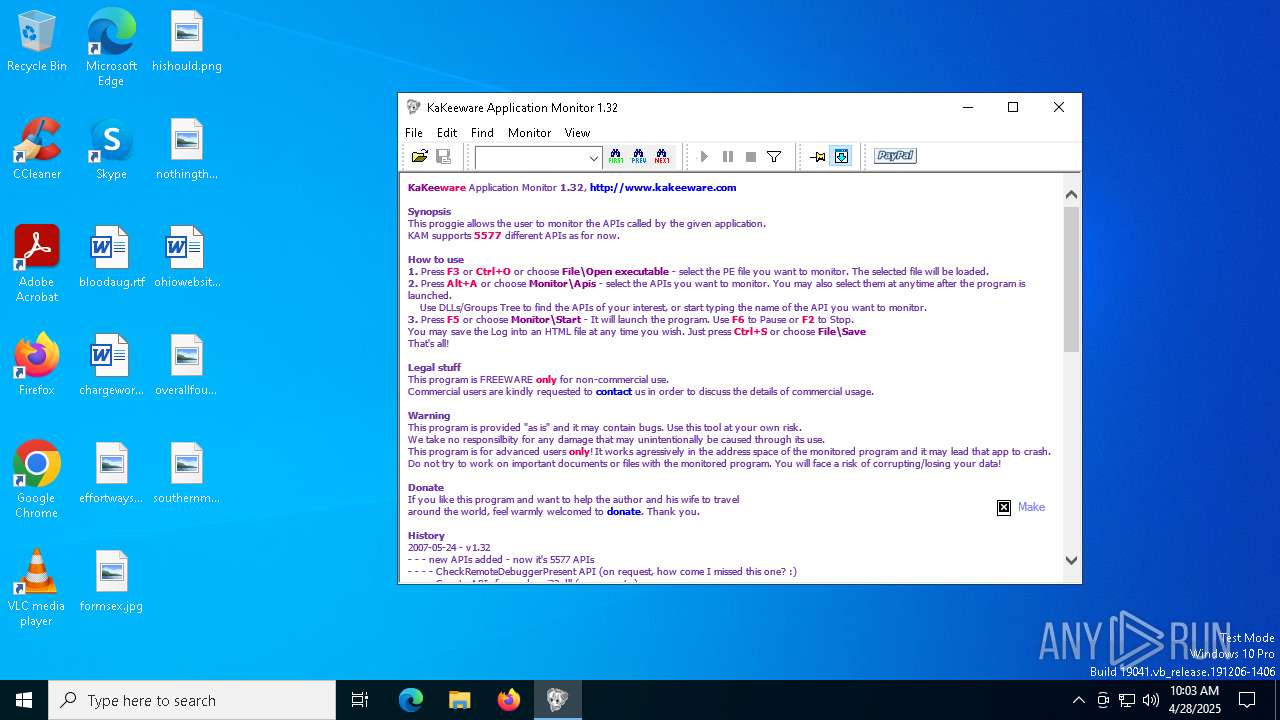
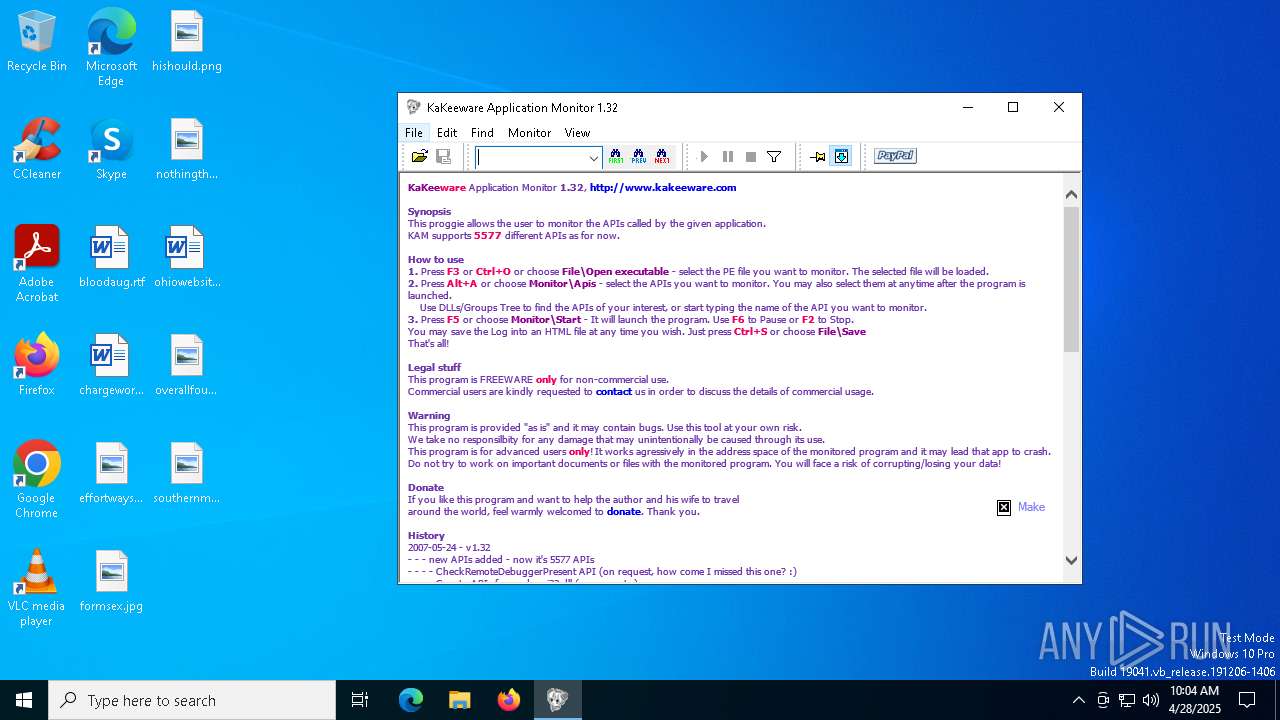
| File name: | KaKeeware Application Monitor 1.32.exe |
| Full analysis: | https://app.any.run/tasks/4d734827-8607-4fdd-a769-d8312a3cfb63 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 10:01:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4FAFBED39BCF3758105F356F0F27841B |
| SHA1: | 0208E639A6DD67A5937379D171B3C7298EE166DC |
| SHA256: | DA6C5A0A3AD4E32C87C2E032472BBD6F605007AE0F4ABB7A77BB8DE5C5A985E4 |
| SSDEEP: | 3072:uGBHRysXRrYuFyi98K03AEmIPYkN7CDfXTq01lQO+oFqM:ZBv9l9a3XYq4/TT1NdFqM |
MALICIOUS
No malicious indicators.SUSPICIOUS
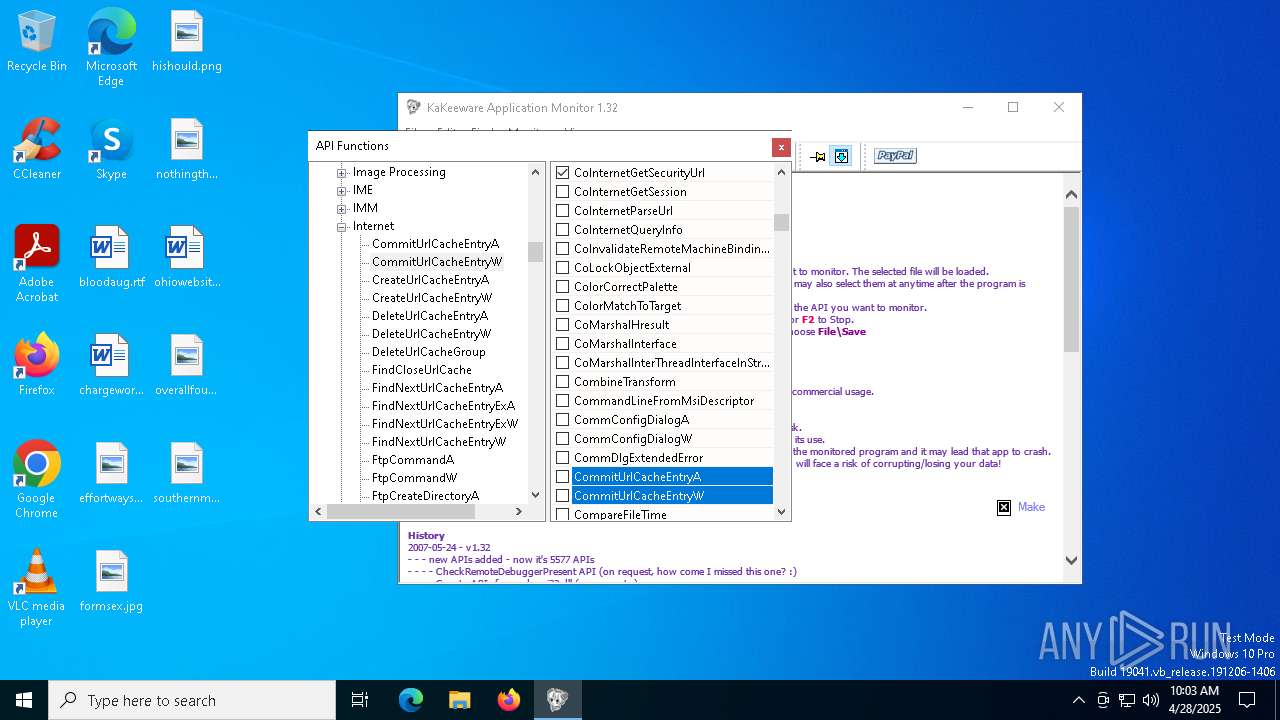
Reads Microsoft Outlook installation path
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
Reads Internet Explorer settings
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
There is functionality for communication over UDP network (YARA)
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
Reads security settings of Internet Explorer
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
There is functionality for taking screenshot (YARA)
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
INFO
Checks supported languages
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
- ielowutil.exe (PID: 7152)
Create files in a temporary directory
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
Checks proxy server information
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
- slui.exe (PID: 6268)
Reads the machine GUID from the registry
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
Reads the computer name
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
- ielowutil.exe (PID: 7152)
Reads the software policy settings
- slui.exe (PID: 5008)
- slui.exe (PID: 6268)
Local mutex for internet shortcut management
- iexplore.exe (PID: 3888)
Process checks whether UAC notifications are on
- KaKeeware Application Monitor 1.32.exe (PID: 6800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:01:23 23:39:42+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 76.111 |
| CodeSize: | 1766614113 |
| InitializedDataSize: | 1918988898 |
| UninitializedDataSize: | 16761 |
| EntryPoint: | 0x1018 |
| OSVersion: | 4 |
| ImageVersion: | 0.57 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
136
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2284 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
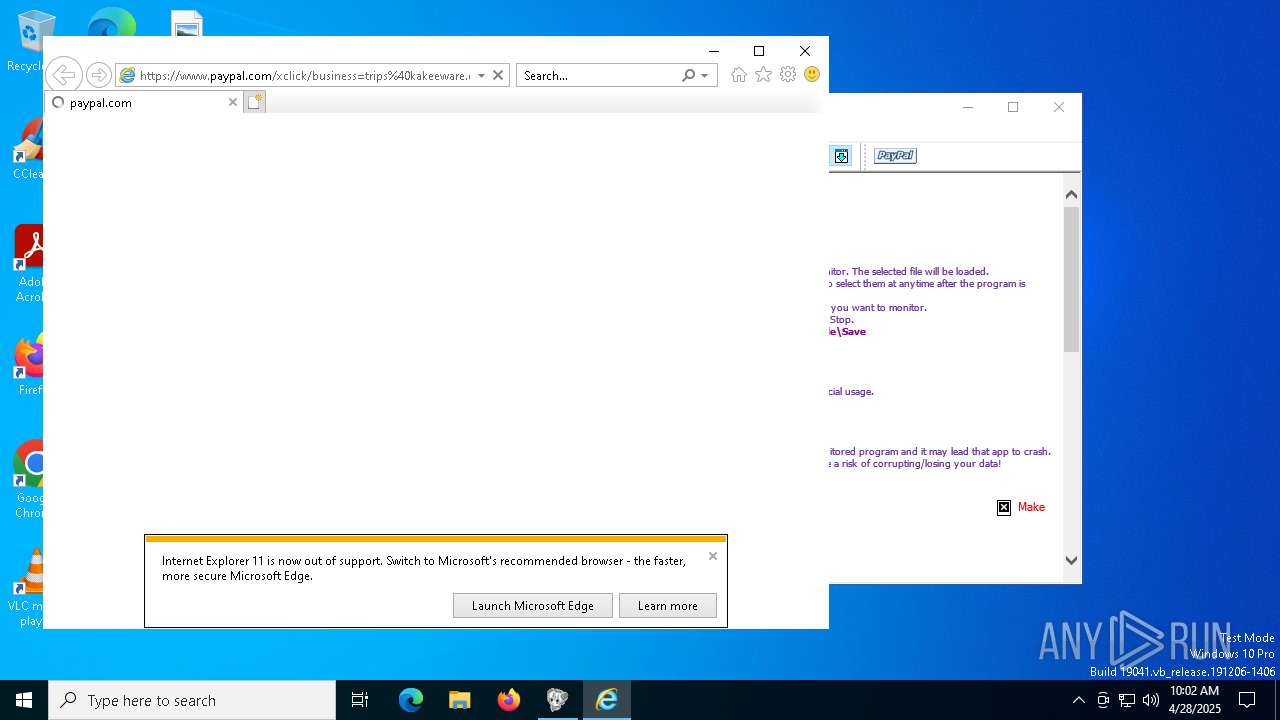
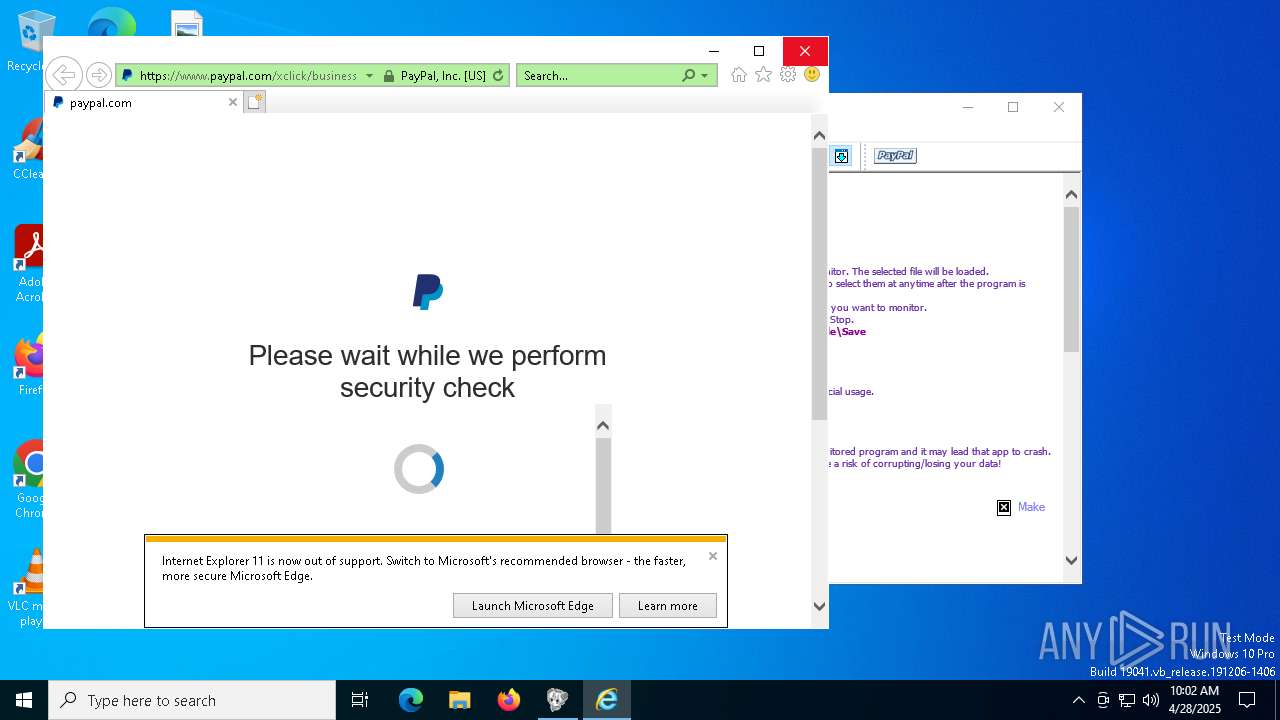
| 3888 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3888 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6676 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3888 CREDAT:595220 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6800 | "C:\Users\admin\AppData\Local\Temp\KaKeeware Application Monitor 1.32.exe" | C:\Users\admin\AppData\Local\Temp\KaKeeware Application Monitor 1.32.exe | — | explorer.exe | |||||||||||
User: admin Company: KaKeeware Integrity Level: MEDIUM Description: The witchiest Application Monitor in the world! Exit code: 0 Version: 1,32,0,0 Modules
| |||||||||||||||
| 7152 | "C:\Program Files (x86)\Internet Explorer\ielowutil.exe" -CLSID:{0002DF01-0000-0000-C000-000000000046} -Embedding | C:\Program Files (x86)\Internet Explorer\ielowutil.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Low-Mic Utility Tool Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 629
Read events
6 557
Write events
64
Delete events
8
Modification events
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | X |
Value: 50 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | Y |
Value: 50 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | W |
Value: 700 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | H |
Value: 500 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | XA |
Value: 300 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | YA |
Value: 130 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | WA |
Value: 500 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | HA |
Value: 400 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | A |
Value: 0 | |||
| (PID) Process: | (6800) KaKeeware Application Monitor 1.32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\KaKeeware\KAM |
| Operation: | write | Name: | B |
Value: 1 | |||
Executable files
0
Suspicious files
46
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6800 | KaKeeware Application Monitor 1.32.exe | C:\Users\admin\AppData\Local\Temp\KaKeeware Application Monitor 1.32.ini | — | |
MD5:— | SHA256:— | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4D1ED785E3365DE6C966A82E99CCE8EA_4FF033DDC375ECDD914F61B03DEEDB1E | binary | |
MD5:0F14BEF8FE264F5FCA6B9510134023FD | SHA256:E8A9B5D02947E06BDE2C53CDBF479007322A00F3532F3545040A1F17FE98B68A | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\pa[1].js | binary | |
MD5:4AA49E9AE86585D68F3E28B3F1C5A9F5 | SHA256:3DFAE0A1223147DEF22534F4B97B5B75A373276A263B6D16545A0646010CCAF3 | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C31B2498754E340573F1336DE607D619 | binary | |
MD5:97C2C7D759D993FD22E876EC8E473361 | SHA256:23CA9B604B9EBDECBF9B1F8F025214389006992CD81F9DF7023FB3E18580E90A | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\business=trips@kakeeware[1].htm | html | |
MD5:A0DA2E3B56ECB65AFB749EDFE675C402 | SHA256:10DCAF34534CC4834BDFA9E9E2021BE8C68E3F1E387C0D26E7A594B1ED728C72 | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\0CBLTDI3\mktconf[1].js | binary | |
MD5:0DF3C3E0809AFCDEAEB222F94DC1E198 | SHA256:96F4F9A32EE8FDCC11A282F48A9DEA472F1C855B225FF8541FD3AF46A5562E06 | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\SG5UMOCJ\mktgtagmanager[1].js | binary | |
MD5:8D00DCCCE823EF1ABAF337DF3E76CB93 | SHA256:5AE47299A5BABA803FF17AF3566300D591920B3584D98062A8CAC5C7B1317748 | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\authchallenge[1].js | binary | |
MD5:D23BAE32FF68D9C2A3B8EB8B6C727723 | SHA256:E2D105873ADDCCE454007B6DCCB05C7B66FF505F989249AA044A89596587BD1D | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\modernizr-2.6.1[1].js | binary | |
MD5:E0463BDE74EF42034671E53BCA8462E9 | SHA256:A58147AEB14487FEF56E141EA0659AC604D61F5E682CFE95C05189BE17DF9F27 | |||
| 5544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\8SFCICQF\app[1].css | text | |
MD5:56DB1D34250E7CE789E59F168620D6A1 | SHA256:A35733F9D6F939DE23693E567722A9942F471B2EE21E6B6CFD9F08473964D31C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
44
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | iexplore.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3888 | iexplore.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5544 | iexplore.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5544 | iexplore.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEA31vlAZBeB5LQ9S94Ivjno%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.paypal.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
t.paypal.com |
| whitelisted |