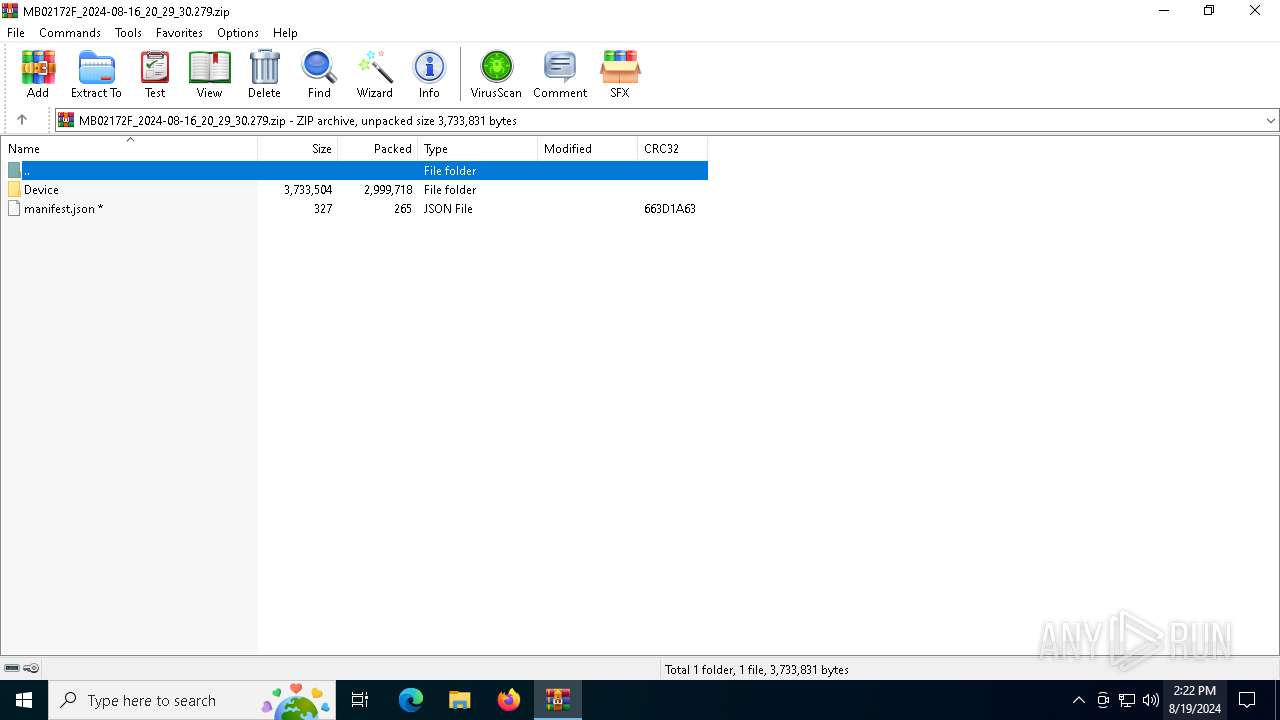
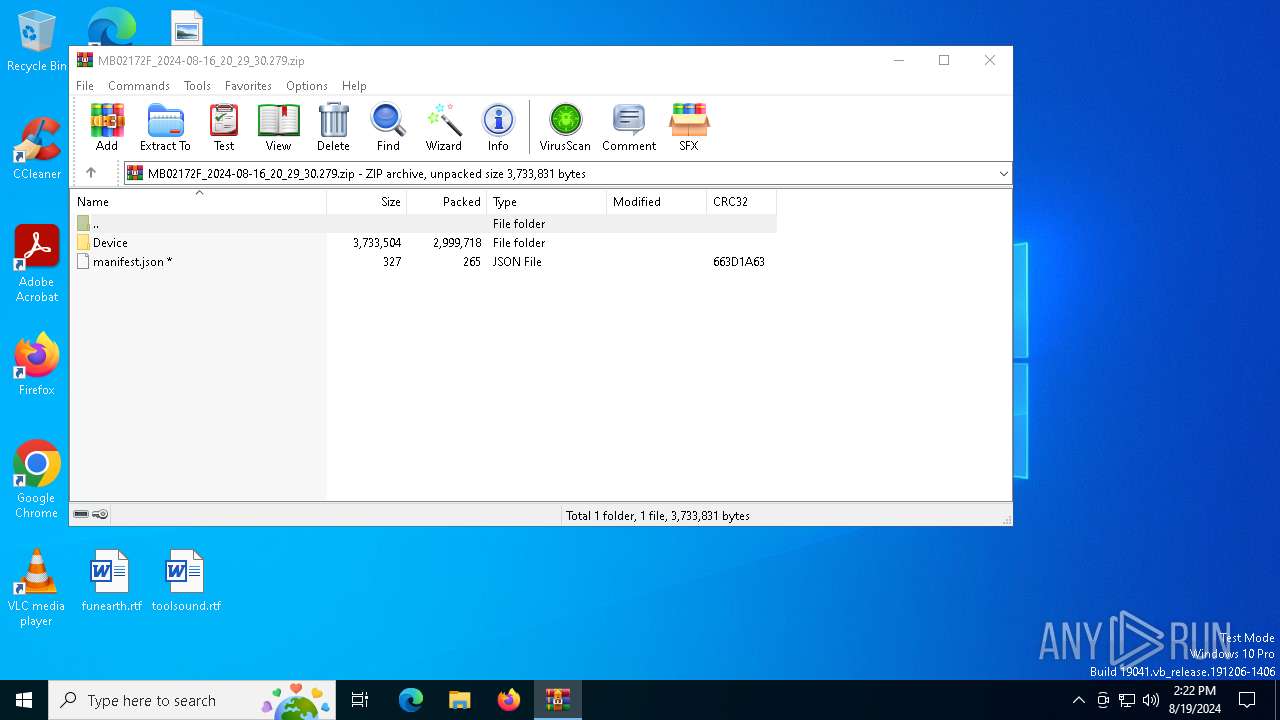
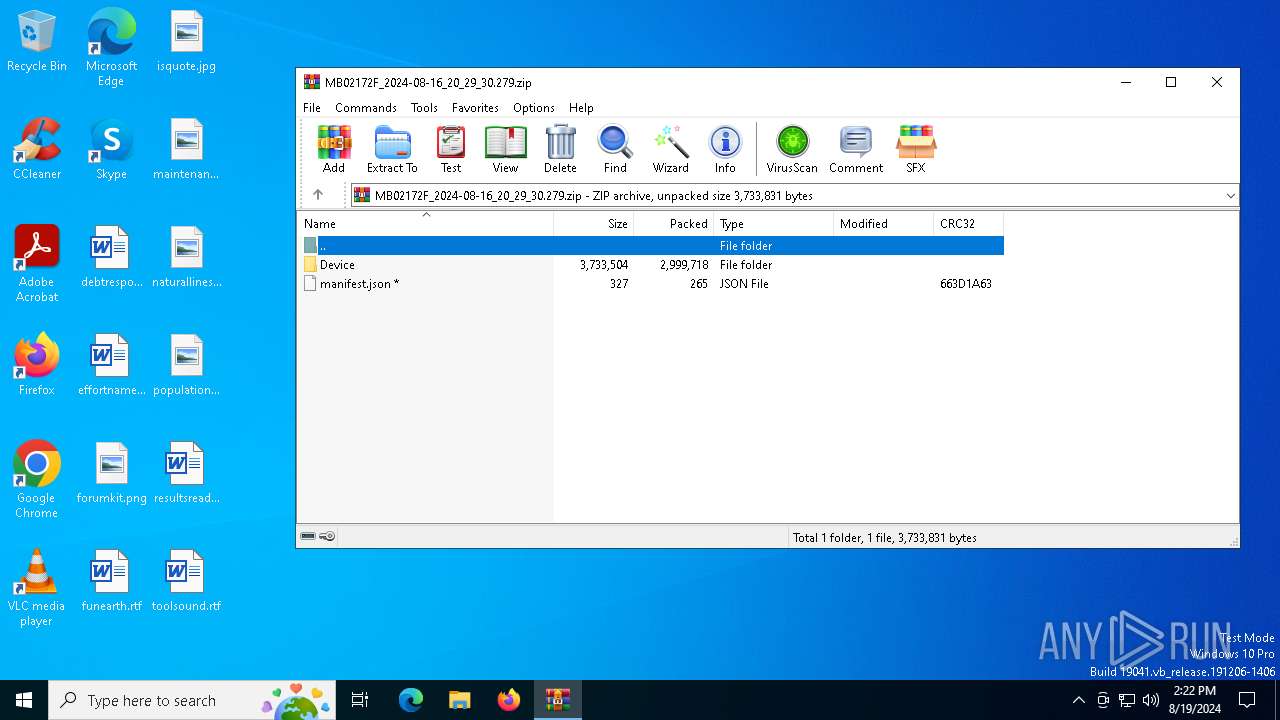
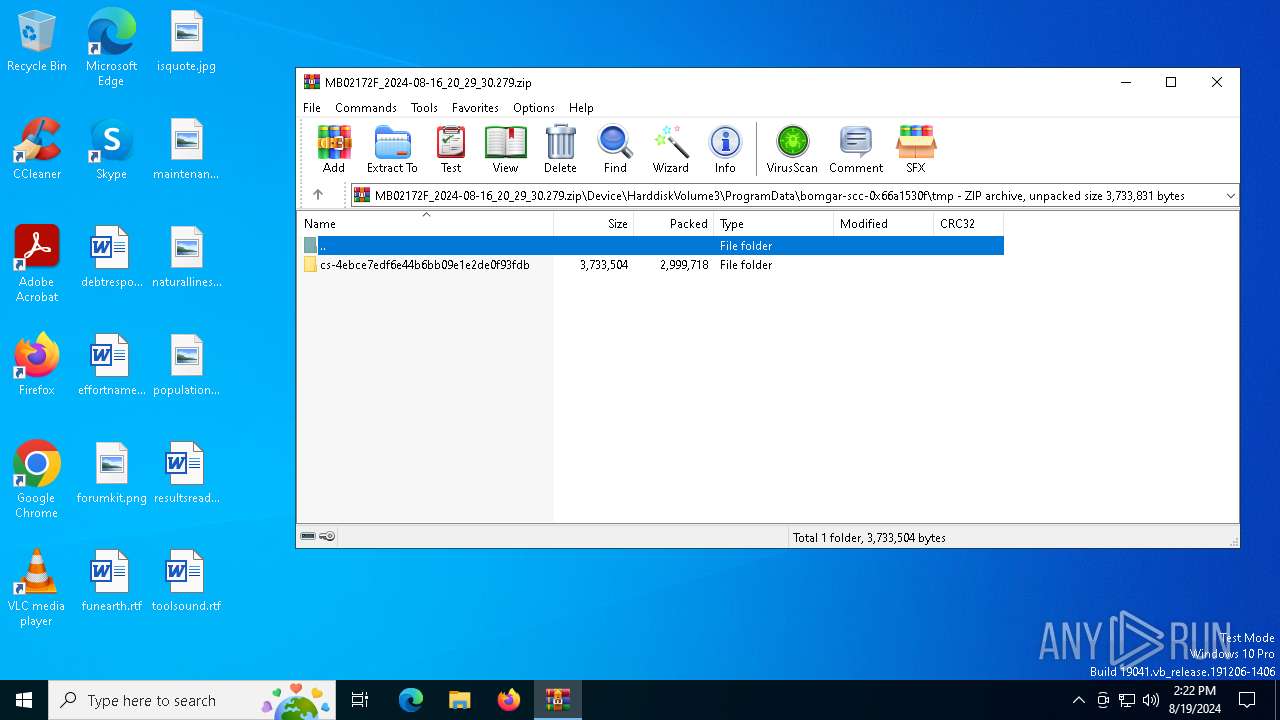
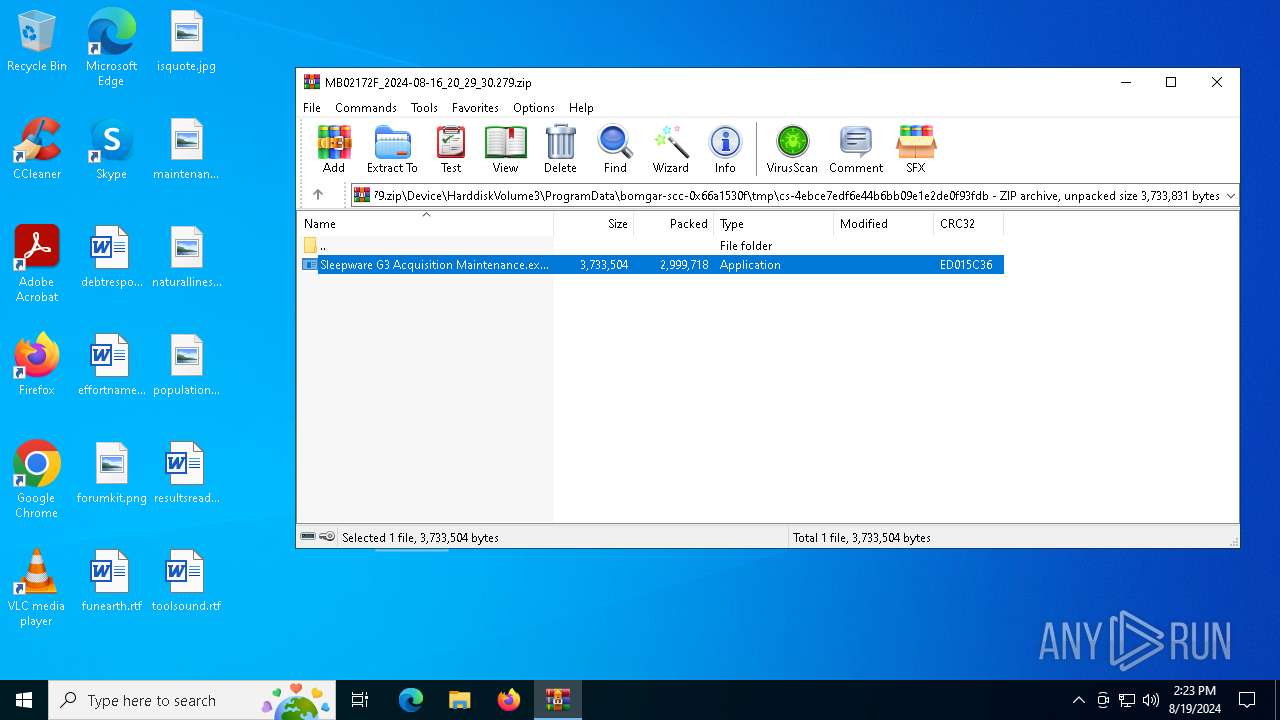
| File name: | MB02172F_2024-08-16_20_29_30.279.zip |
| Full analysis: | https://app.any.run/tasks/f6ec838e-ba17-44ca-9bcd-03be95422c0d |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2024, 14:22:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 4A5B750EF845F8BCFE9E77549F06F4BC |
| SHA1: | D3B6C6E852AEE4B0792F8B5391A99EA4FB9D42F1 |
| SHA256: | DA6B93147D9C4B3AC66D5938FFDECD309840E1AADEFE44452A675C58362F885F |
| SSDEEP: | 98304:NnBe7pPIngCNeiXVDsWkyv9Rbcdg6qXYSReJKhha5D4Um+Cm/mT+EBdyWKvRiX0T:Vbi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Checks Windows Trust Settings
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Detected use of alternative data streams (AltDS)
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Starts CMD.EXE for commands execution
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6684)
Executing commands from a ".bat" file
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
INFO
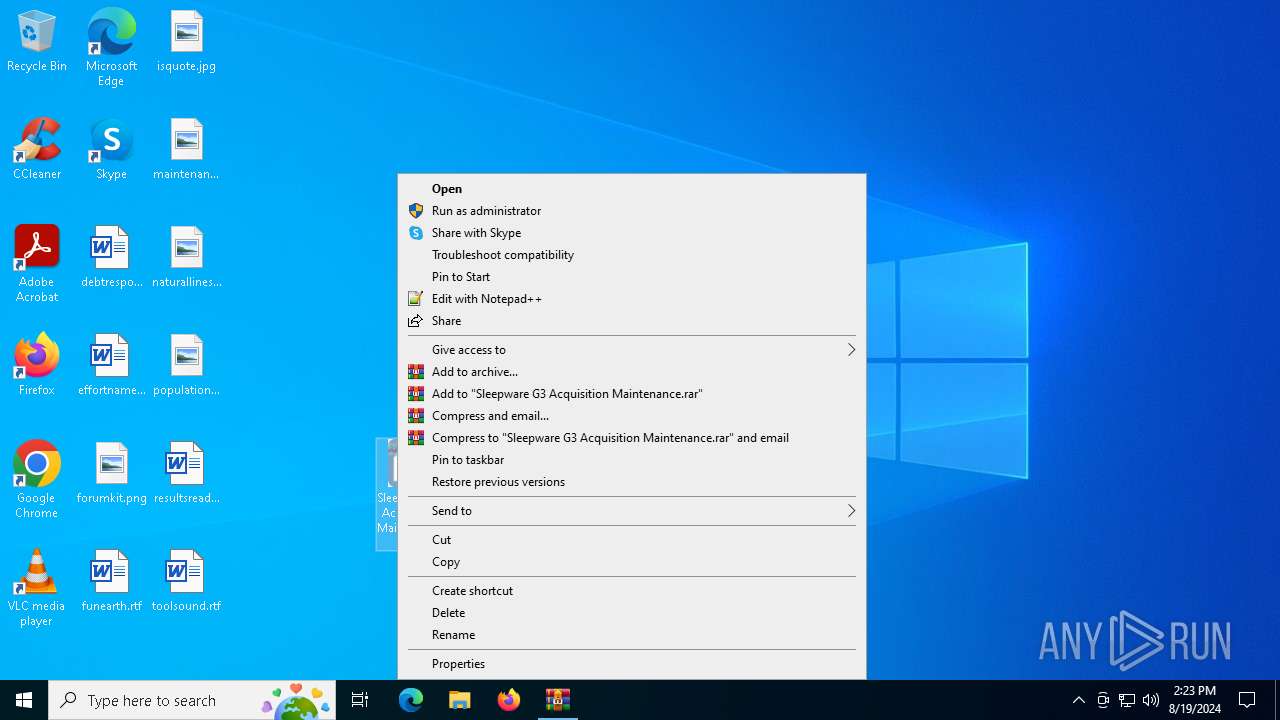
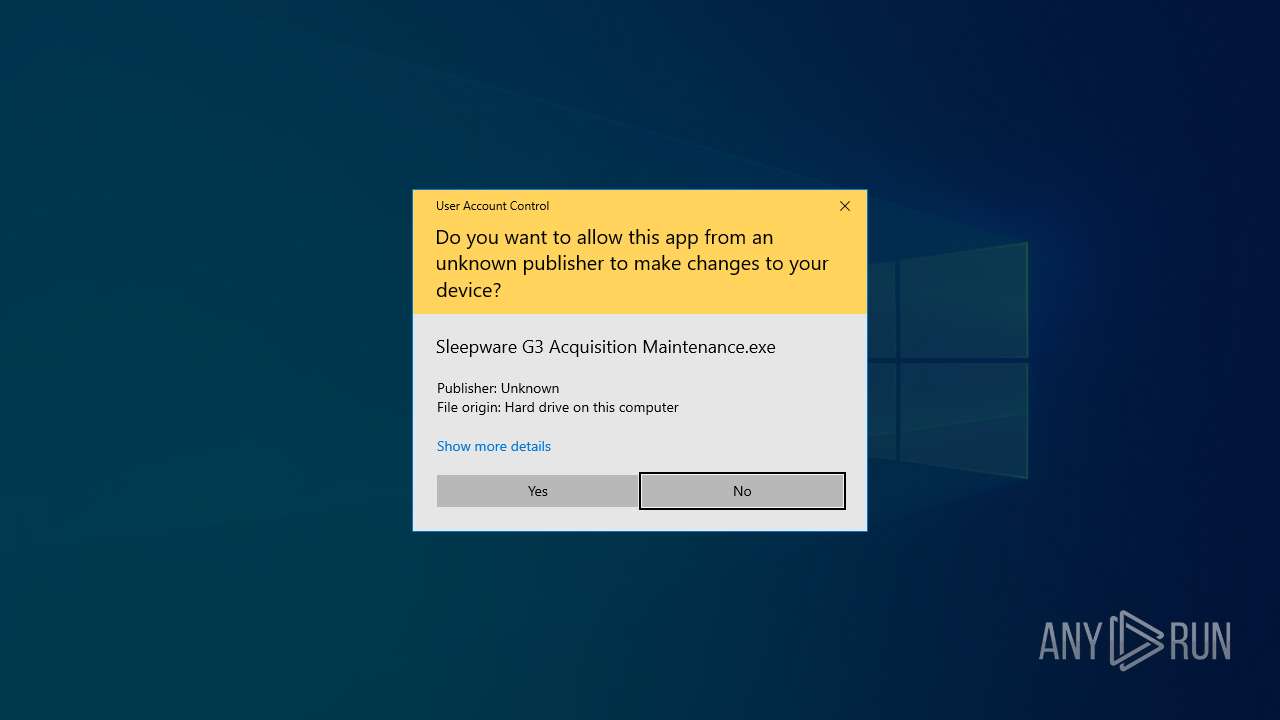
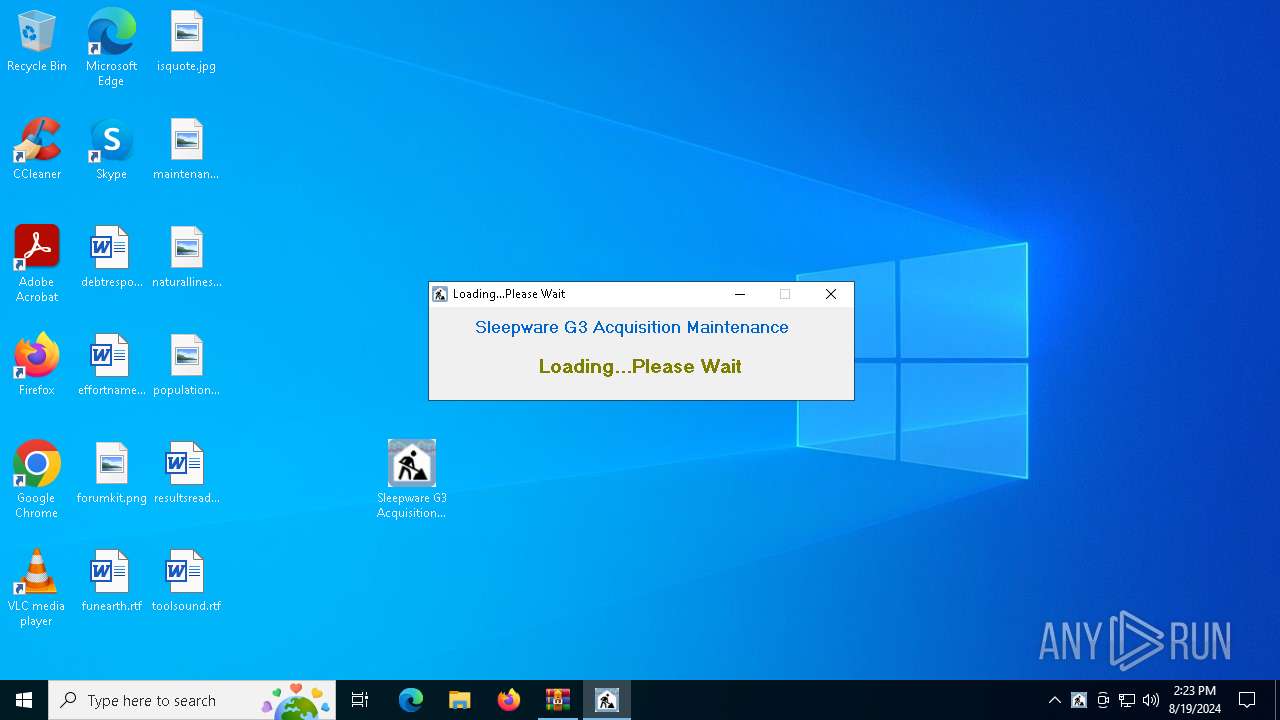
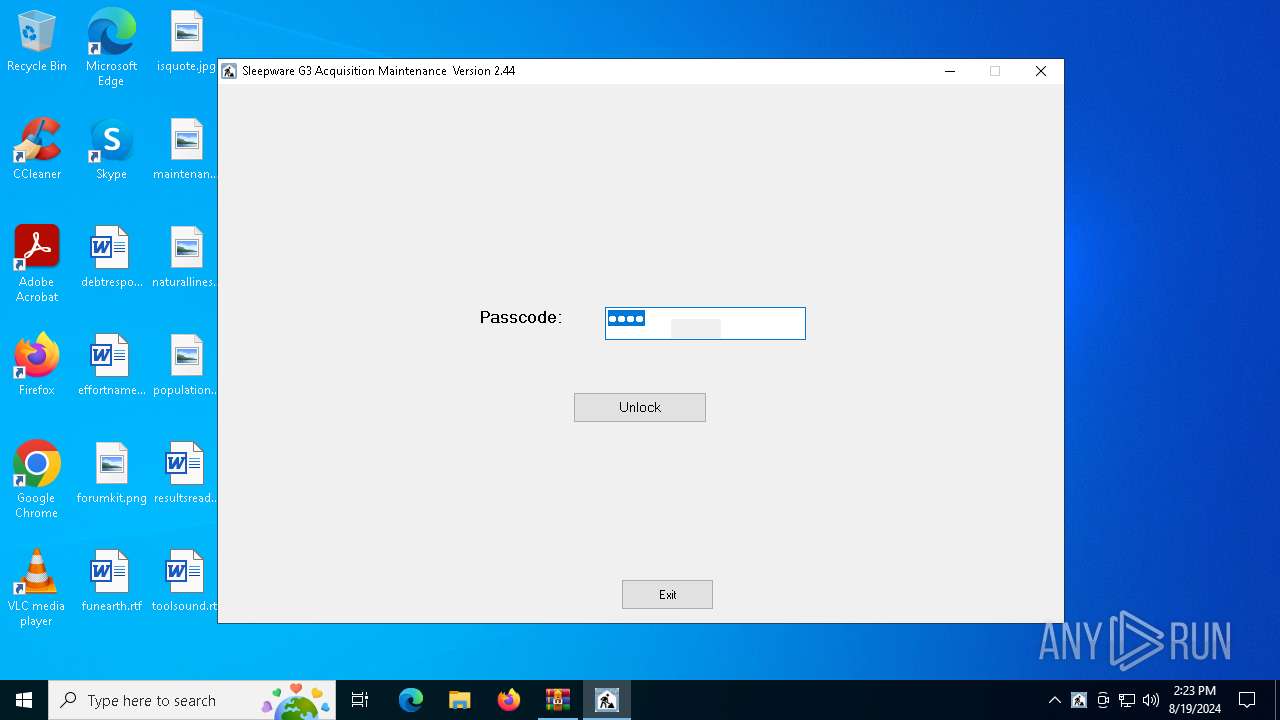
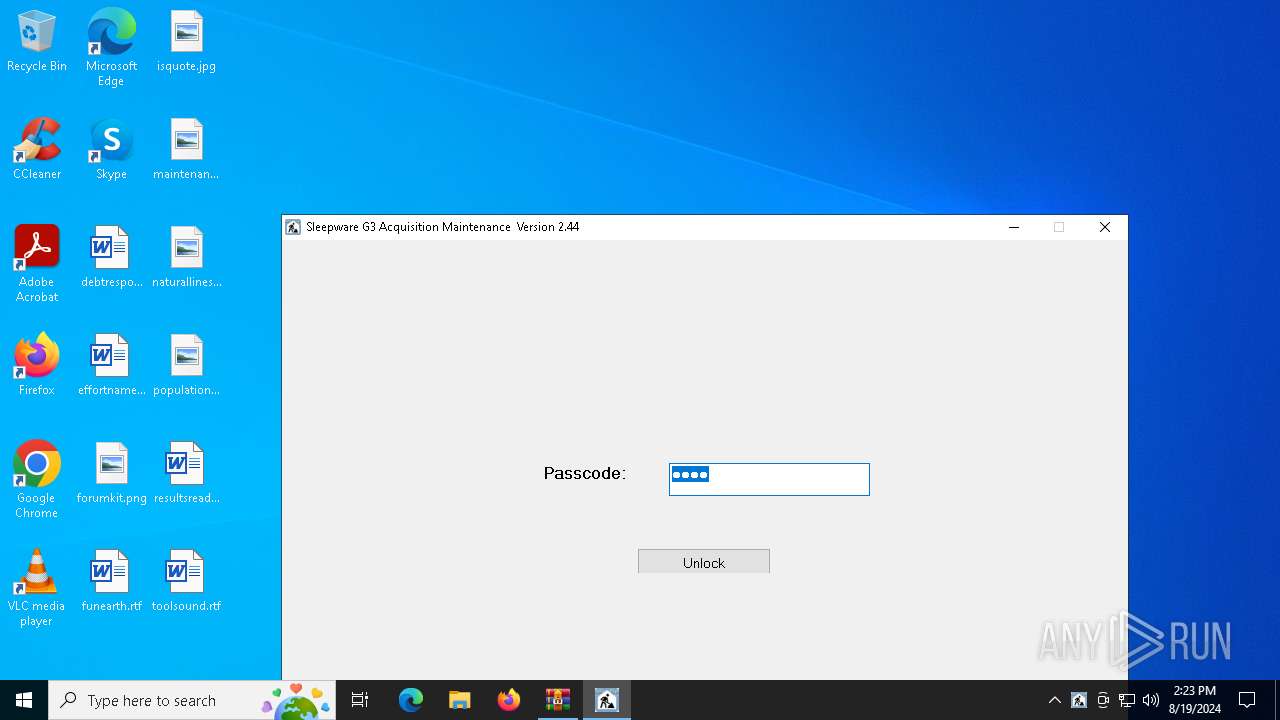
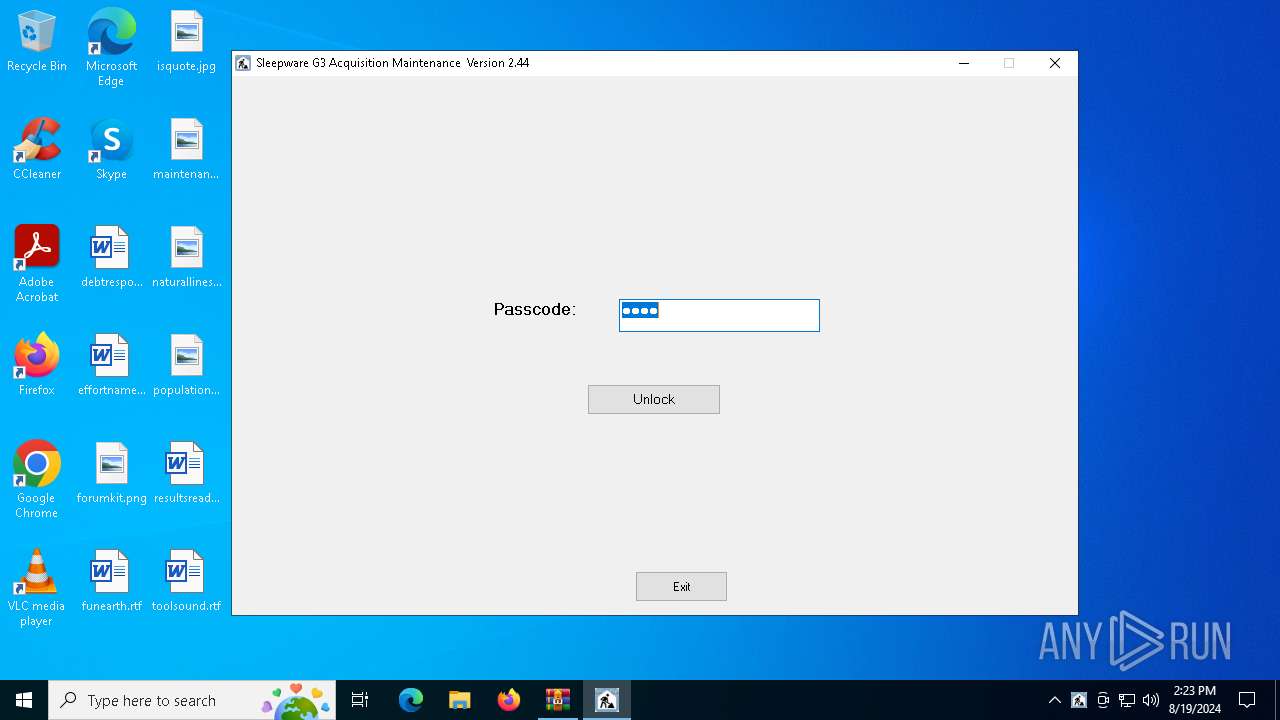
Manual execution by a user
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
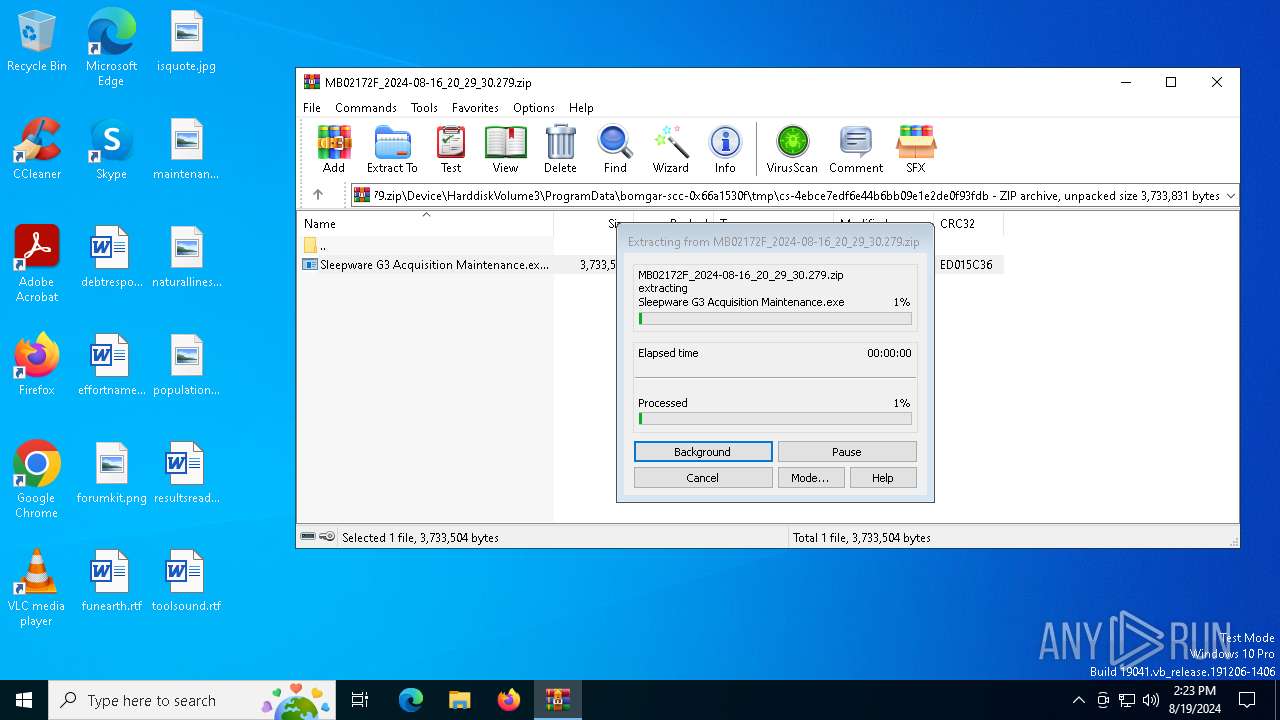
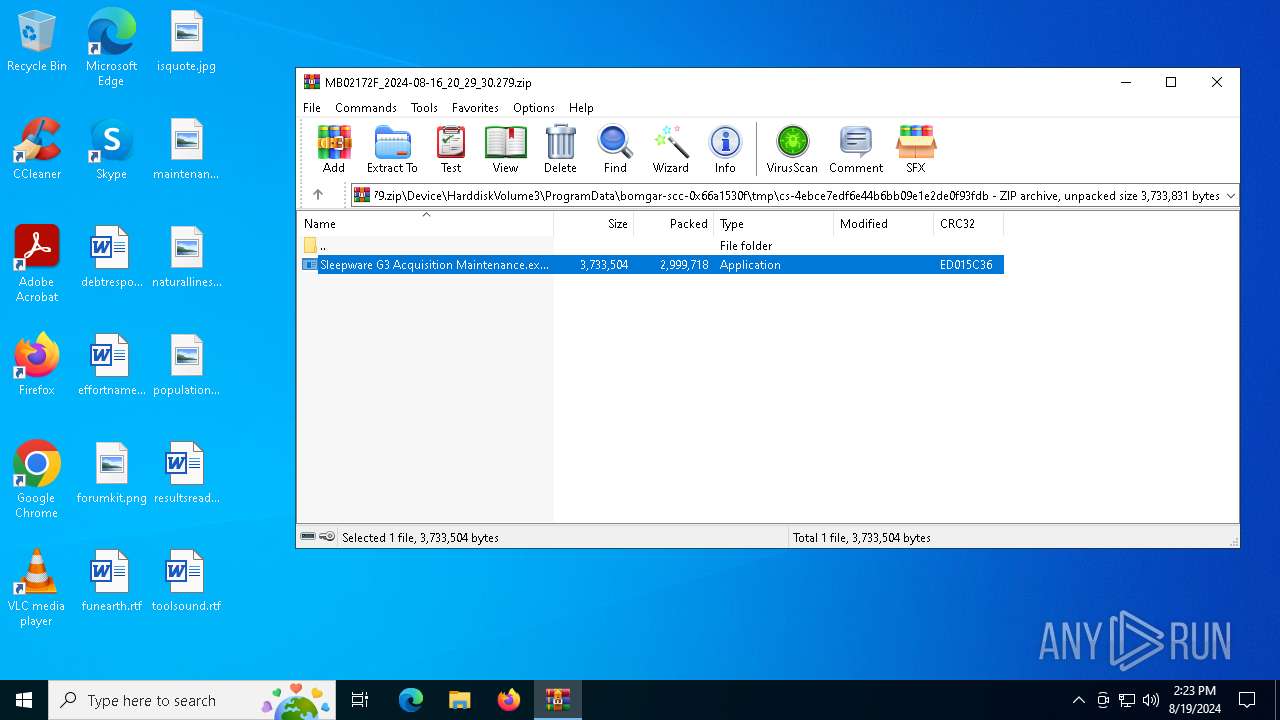
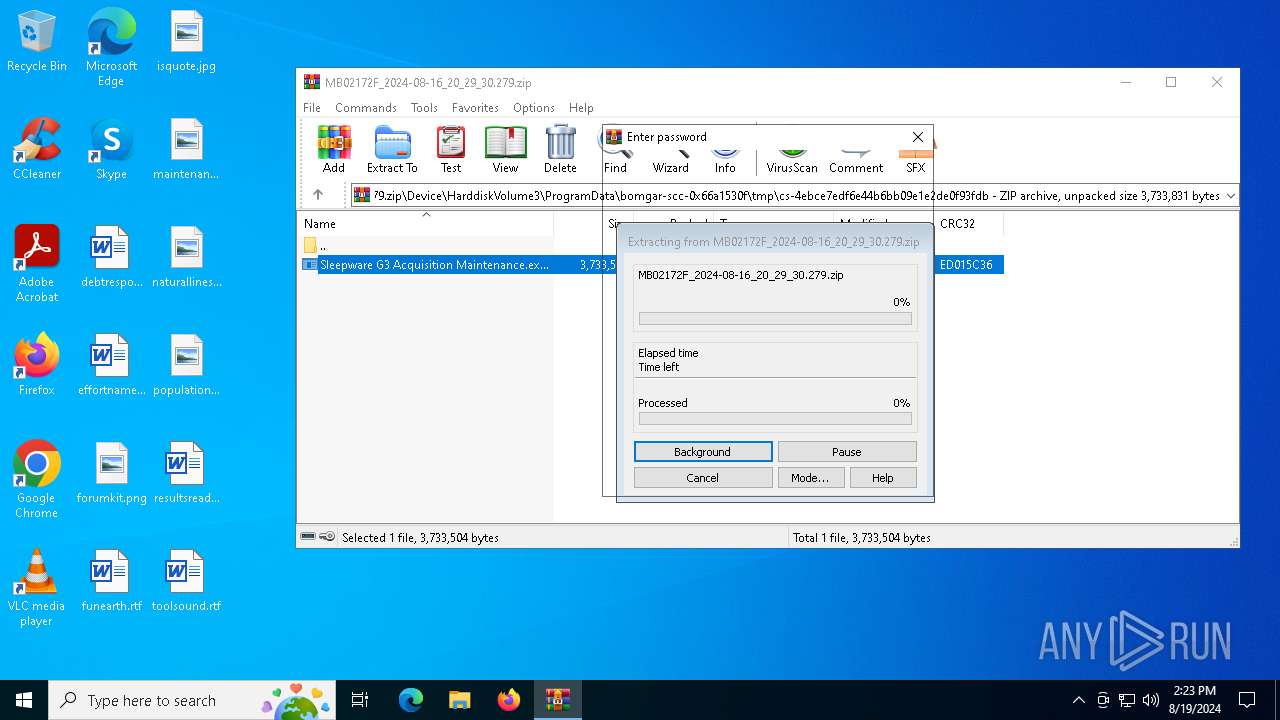
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6756)
Reads mouse settings
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Checks supported languages
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Checks proxy server information
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Reads the machine GUID from the registry
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Reads the computer name
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Reads the software policy settings
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Creates files or folders in the user directory
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Creates files in the program directory
- Sleepware G3 Acquisition Maintenance.exe (PID: 6752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xed015c36 |
| ZipCompressedSize: | 2999718 |
| ZipUncompressedSize: | 3733504 |
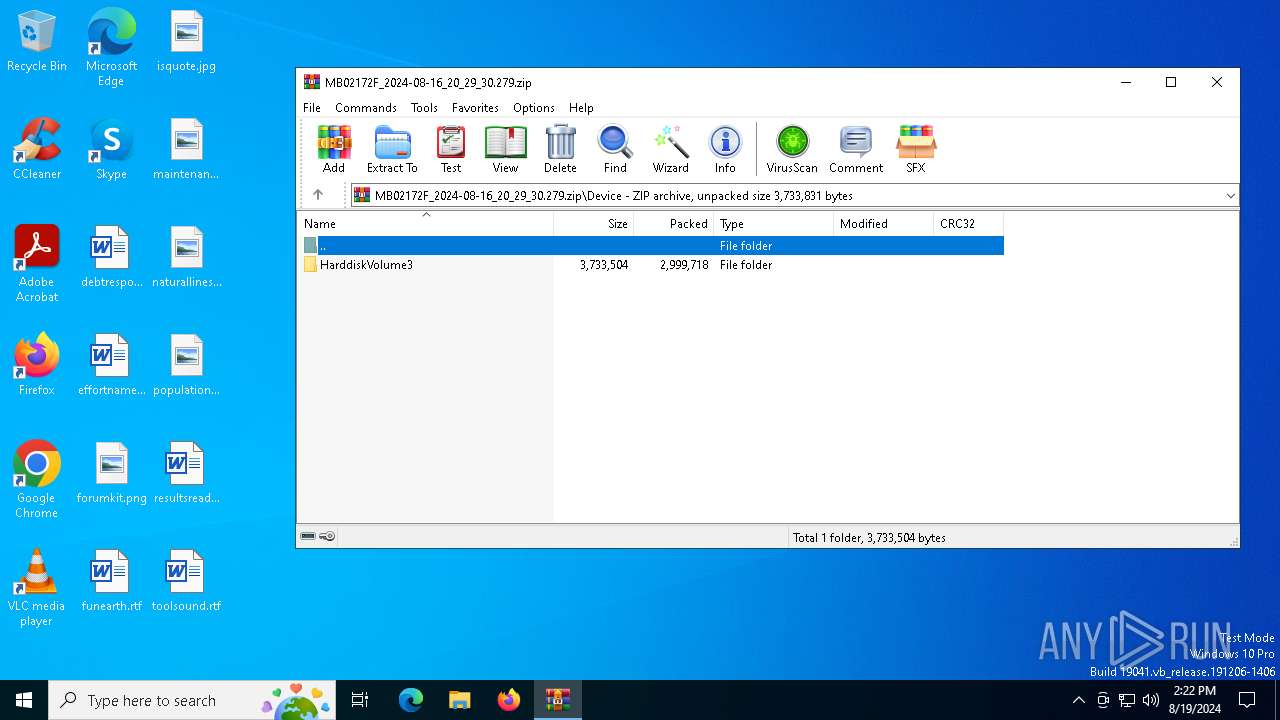
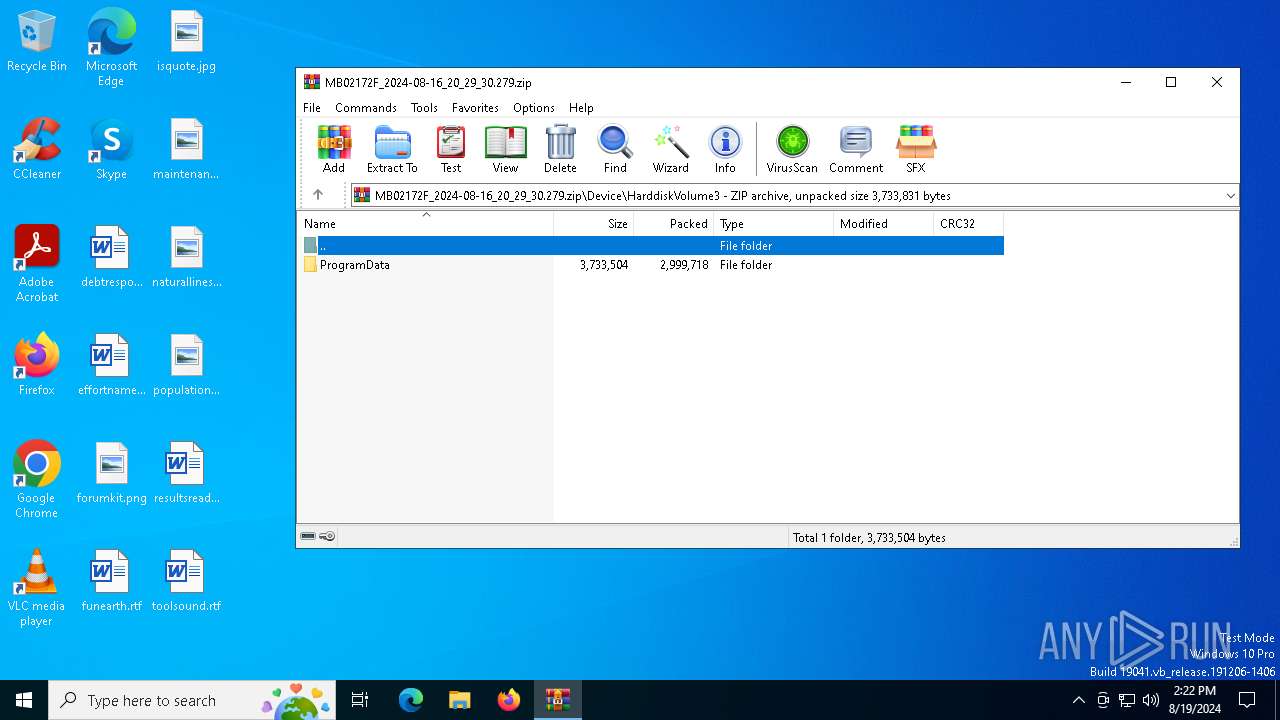
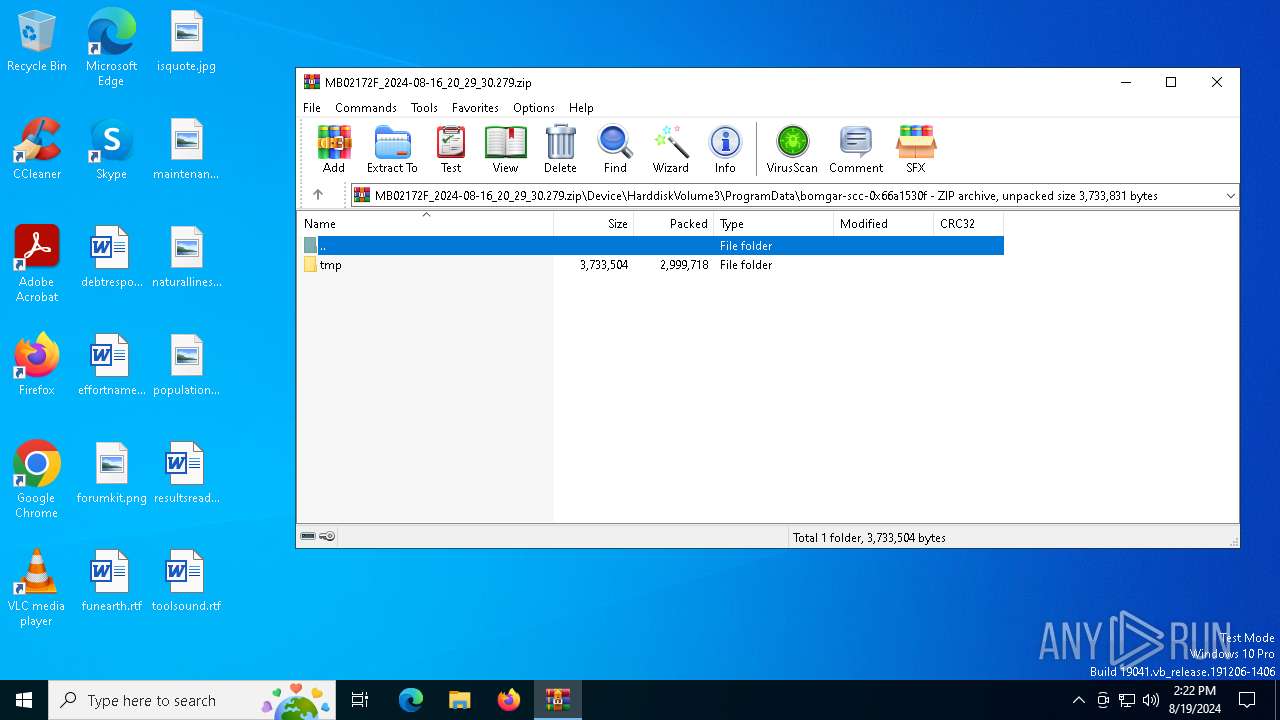
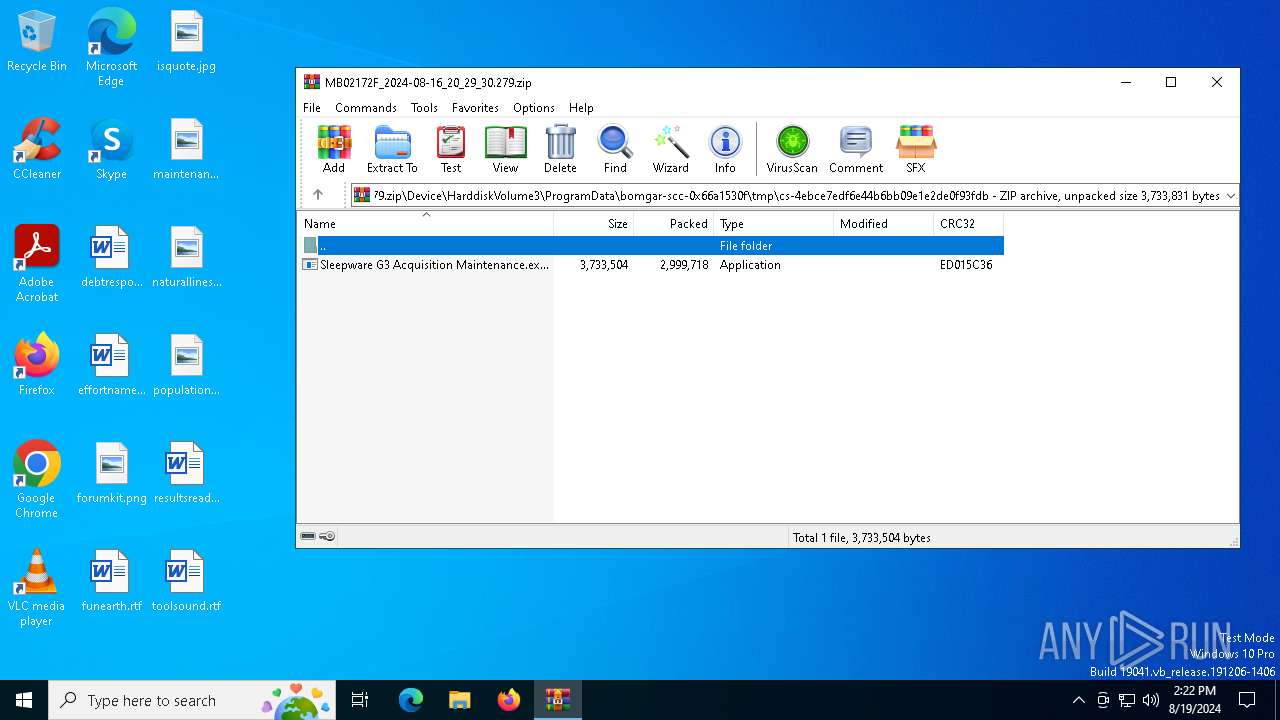
| ZipFileName: | Device/HarddiskVolume3/ProgramData/bomgar-scc-0x66a1530f/tmp/cs-4ebce7edf6e44b6bb09e1e2de0f93fdb/Sleepware G3 Acquisition Maintenance.exe |
Total processes
134
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6684 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Tempscratch.bat | C:\Windows\SysWOW64\cmd.exe | — | Sleepware G3 Acquisition Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6720 | ping -n 0 127.0.0.1 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | "C:\Users\admin\Desktop\Sleepware G3 Acquisition Maintenance.exe" | C:\Users\admin\Desktop\Sleepware G3 Acquisition Maintenance.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
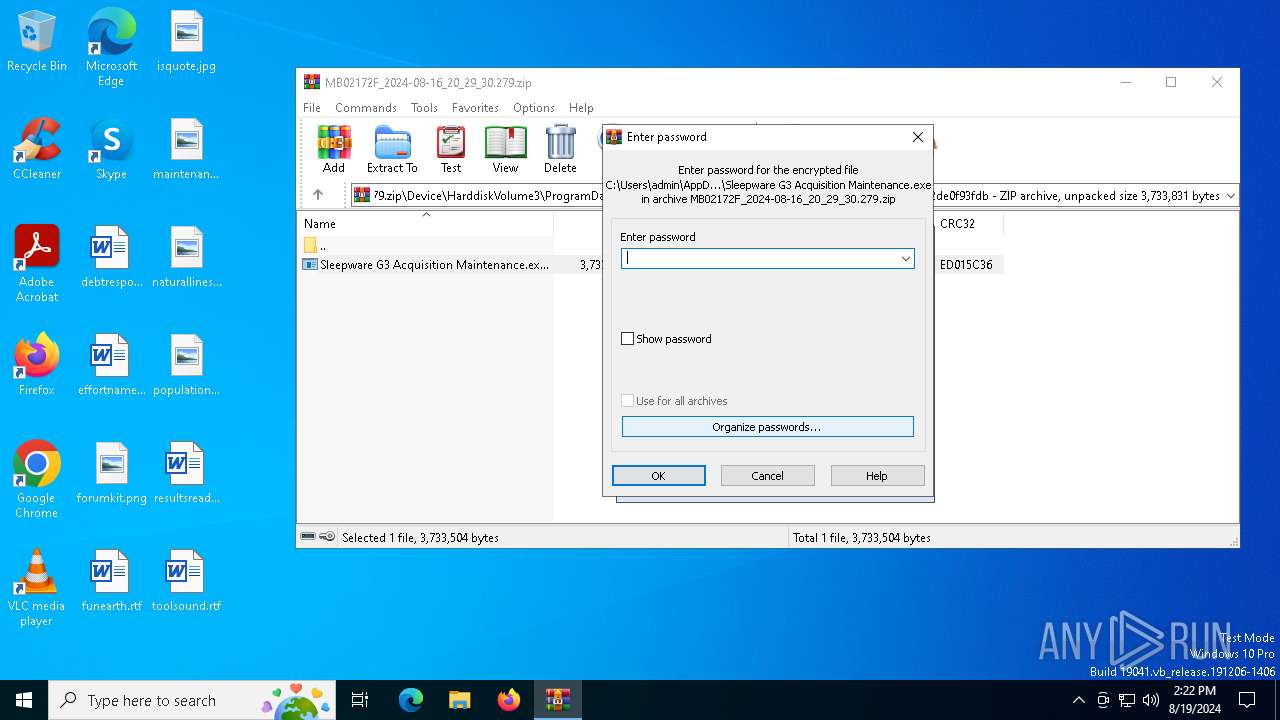
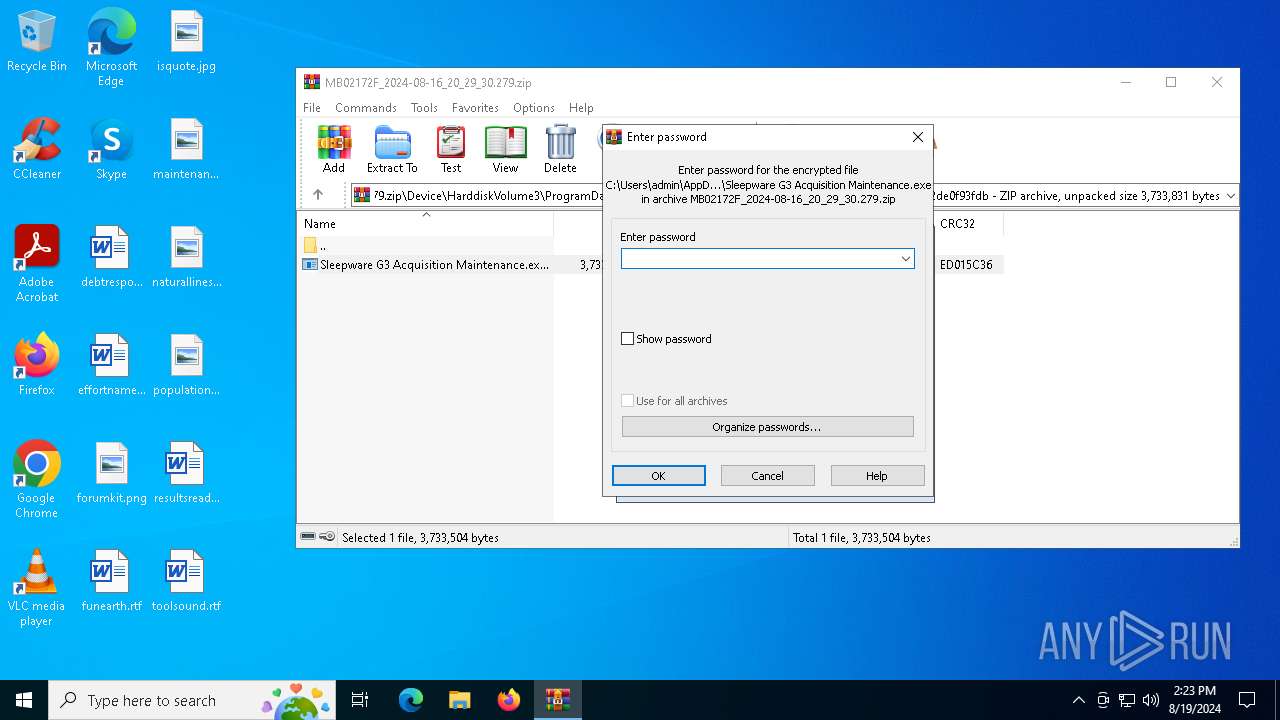
| 6756 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\MB02172F_2024-08-16_20_29_30.279.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
7 693
Read events
7 672
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MB02172F_2024-08-16_20_29_30.279.zip | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6756) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6752) Sleepware G3 Acquisition Maintenance.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6756 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6756.18646\Device\HarddiskVolume3\ProgramData\bomgar-scc-0x66a1530f\tmp\cs-4ebce7edf6e44b6bb09e1e2de0f93fdb\Sleepware G3 Acquisition Maintenance.exe | executable | |
MD5:A9AFC3E1CD5B83D44623FD4BF4DAFAD1 | SHA256:A3E8E05E2935E5F689285610E3CFCAFFC40206FA5DFF4AF5D1F04A6CFF919802 | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:0A8A642712AB815D5FEC03E4EB81B4AD | SHA256:291AB8BA2C7BCB2AE19C64FED2079A3BBDA727B20FDBFBDE6A008E22DC88A4C1 | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\59D76868C250B3240414CE3EFBB12518_630168765158DC6FC24EB9C3201C9C4F | binary | |
MD5:2E754C1603E7DB1E15A4258AF920B0A5 | SHA256:2CAE1B012B65CAB8579A2C78AE39C1AAB8C5BDC9A093FCA65E931FA805D8BCDB | |||
| 6756 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6756.22696\Device\HarddiskVolume3\ProgramData\bomgar-scc-0x66a1530f\tmp\cs-4ebce7edf6e44b6bb09e1e2de0f93fdb\Sleepware G3 Acquisition Maintenance.exe | executable | |
MD5:A9AFC3E1CD5B83D44623FD4BF4DAFAD1 | SHA256:A3E8E05E2935E5F689285610E3CFCAFFC40206FA5DFF4AF5D1F04A6CFF919802 | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\59D76868C250B3240414CE3EFBB12518_630168765158DC6FC24EB9C3201C9C4F | binary | |
MD5:4E0C1A6BDB495D7C6B18959EB234D4BC | SHA256:9C90E099874D381559BE5B09F3CD1DF871A4F693870772C20DC665B01547D463 | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | der | |
MD5:29D09E7393544D920237159477947802 | SHA256:345359FCEB27B419F3877A6739636E9D248899281F3DC46445FB2DDE6201CDDF | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\ProgramData\Philips Respironics\Sleepware G3\Online\Status\status.txt | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 6752 | Sleepware G3 Acquisition Maintenance.exe | C:\Users\admin\AppData\Local\Tempscratch.bat | text | |
MD5:F68C20C10041F270195CF46A2B35CBD7 | SHA256:3529D2E2CDDC302FFA10BDC1003AF090000A88E58ECF4A56B448EA88F185D978 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
30
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6248 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6972 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6752 | Sleepware G3 Acquisition Maintenance.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAIkRbIrCMlD39wCKGczXAA%3D | unknown | — | — | whitelisted |
6752 | Sleepware G3 Acquisition Maintenance.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3308 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3308 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3028 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3028 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
support.respironics.com |
| unknown |