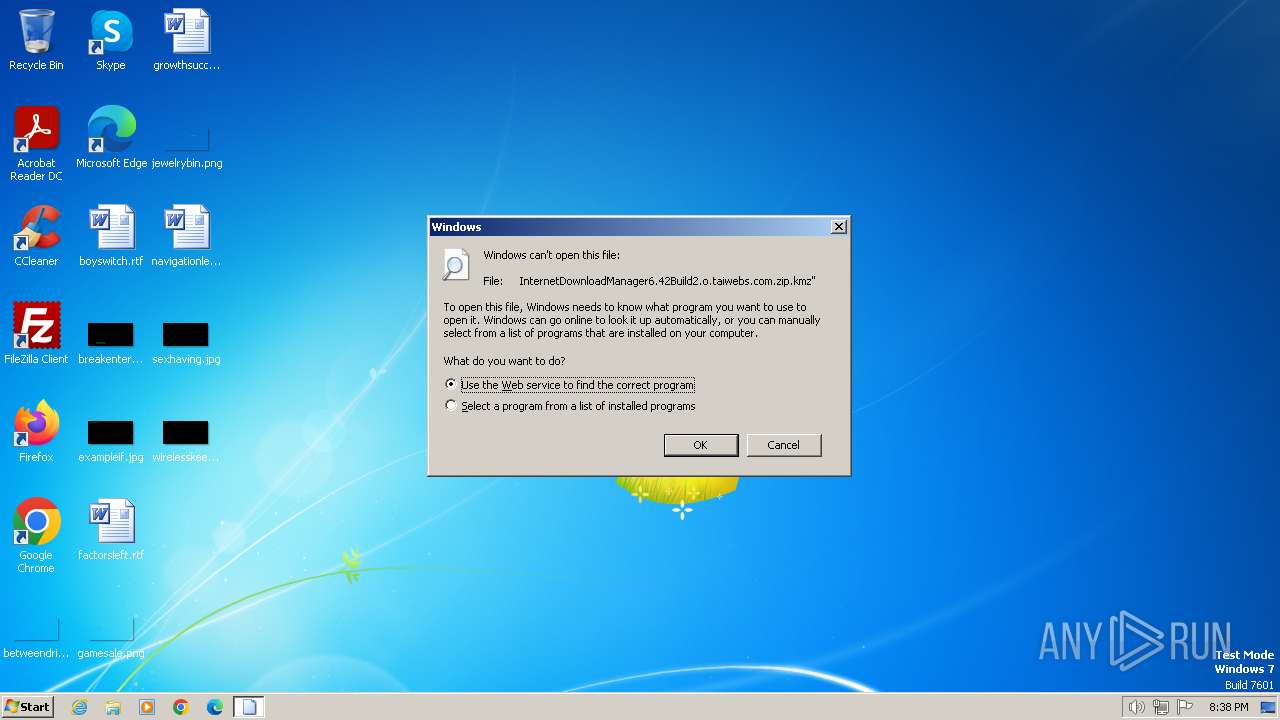
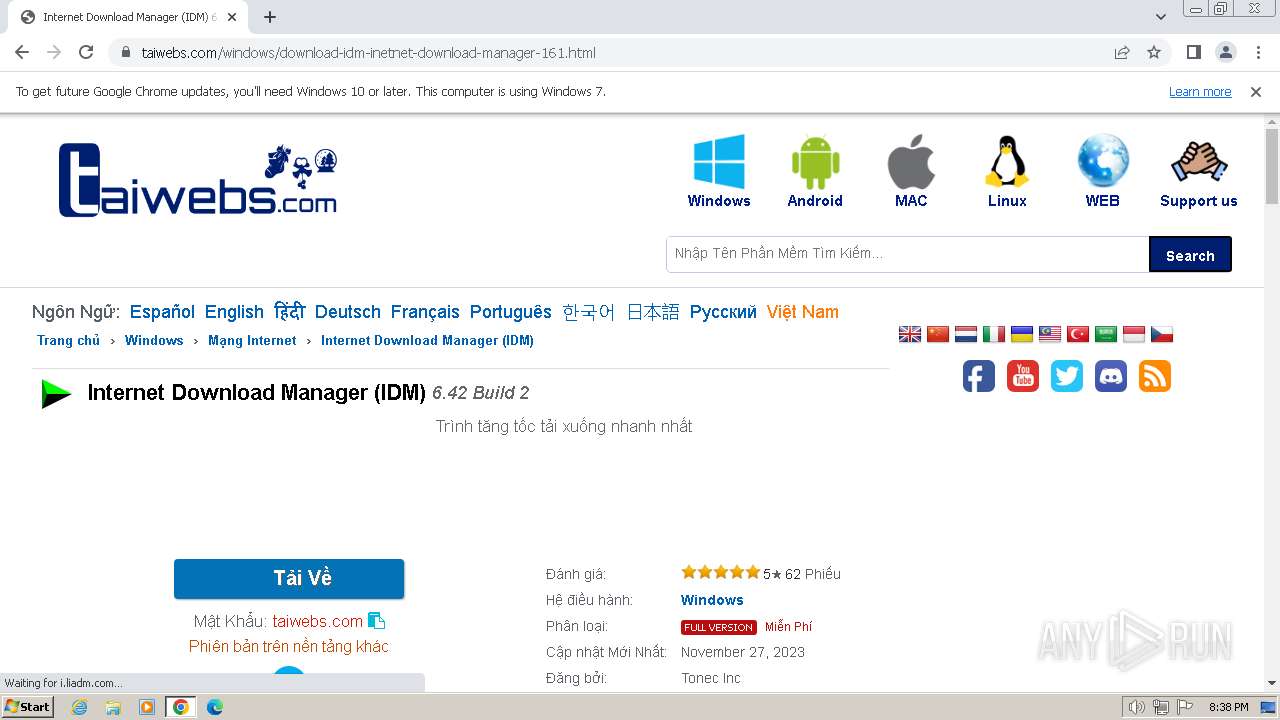
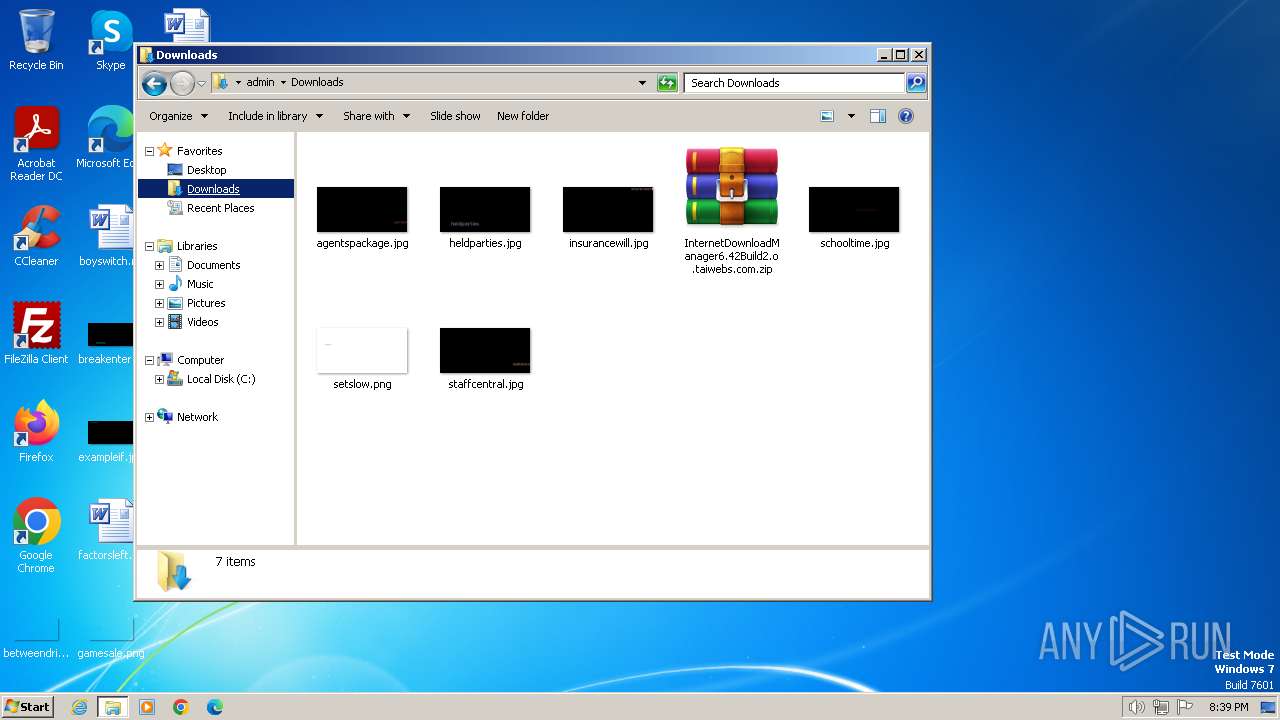
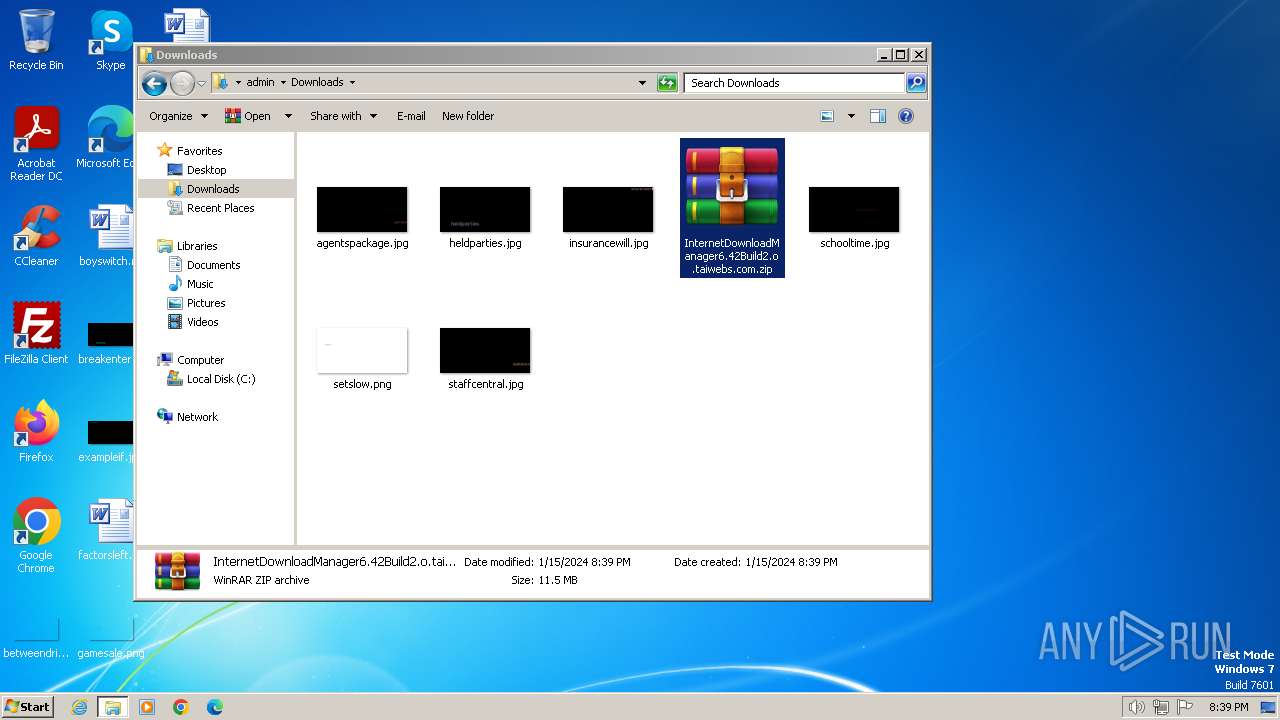
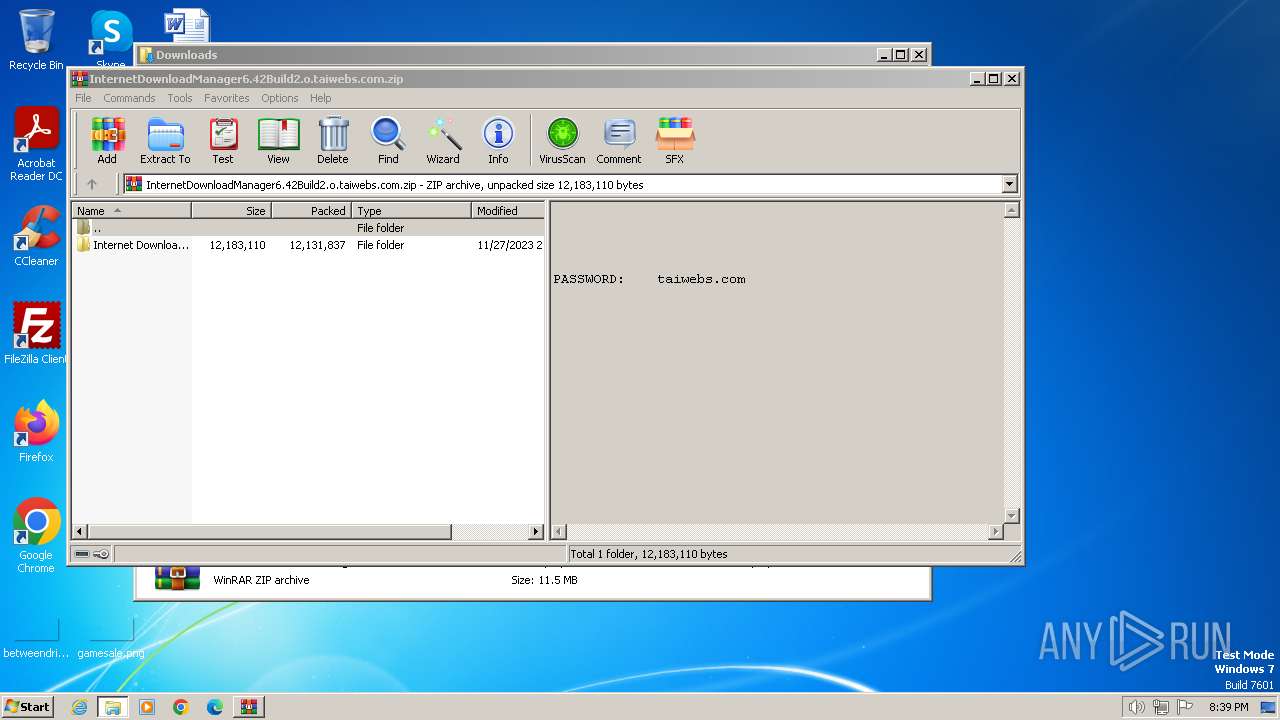
| File name: | InternetDownloadManager6.42Build2.o.taiwebs.com.zip |
| Full analysis: | https://app.any.run/tasks/29db69bb-bf6d-4832-af62-a5f6f1386431 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2024, 20:37:50 |
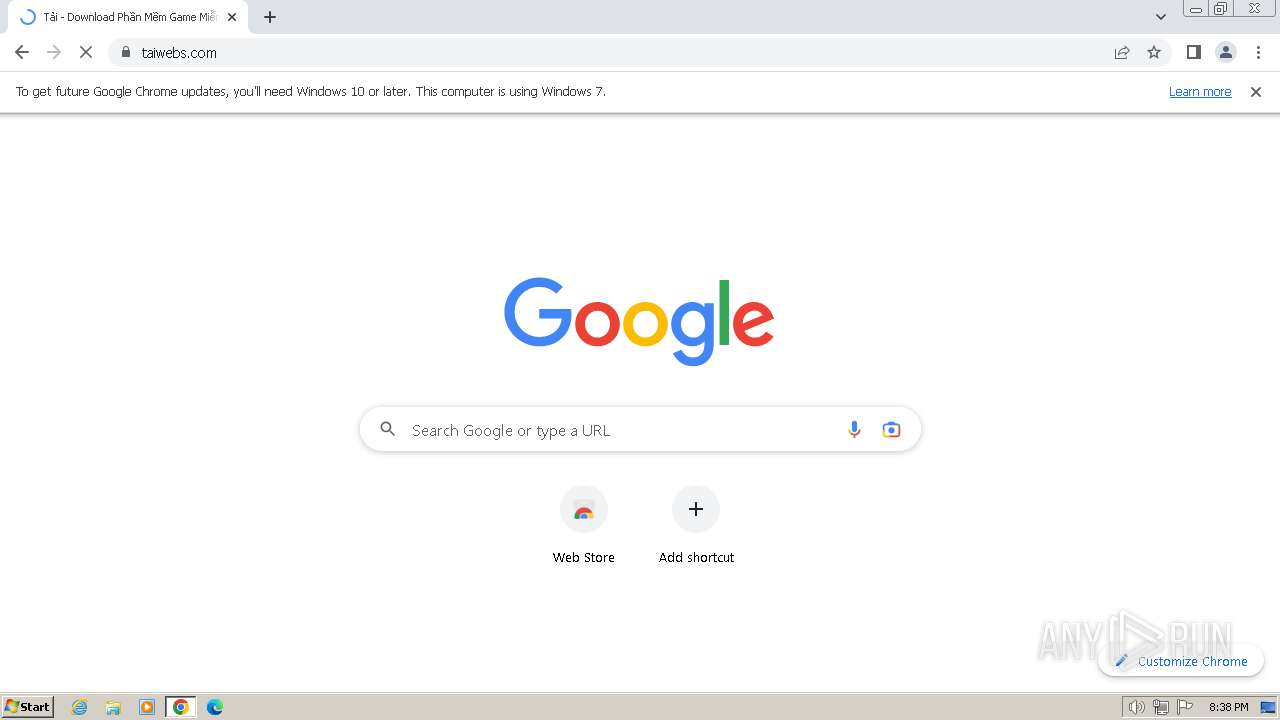
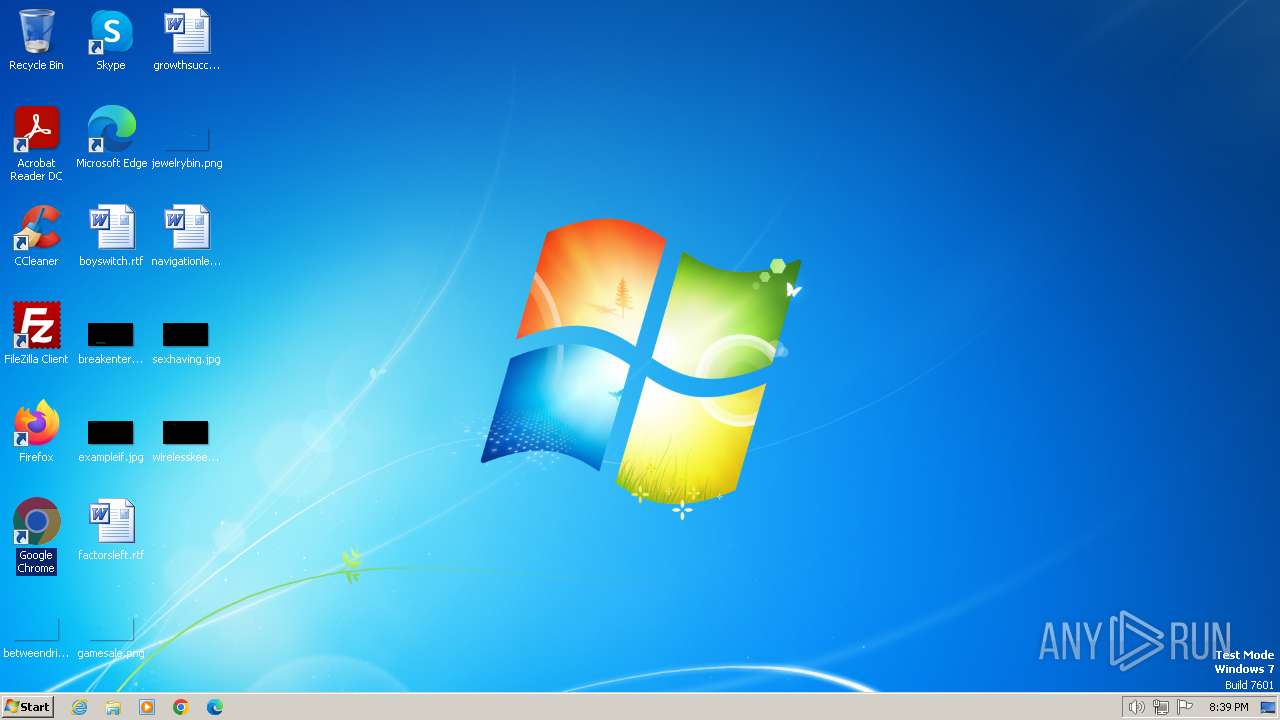
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | CFA9AB40161CD529FB13B9F59A67454E |
| SHA1: | 1C38506FFB0A7E36DF4AC8F2C6828CF13F5EE81A |
| SHA256: | DA57FC395104B9D3D3796E0AECDDCC6F6C6528C8C724EB242232CC11A2D38E6F |
| SSDEEP: | 98304:Rs9bwoPNBWptXE2VgQ1R9dvjd/zd2CJ5vil6TMEbXq/Xoo1IclcR4G5zXxwnrU6Z:S5IdNbShYbq6qujG9FrChm |
MALICIOUS
Drops the executable file immediately after the start
- IDMan.exe (PID: 2636)
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
- wscript.exe (PID: 2544)
Creates a writable file in the system directory
- rundll32.exe (PID: 2676)
Starts NET.EXE for service management
- Uninstall.exe (PID: 1600)
- net.exe (PID: 2668)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 2544)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2544)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2544)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2544)
SUSPICIOUS
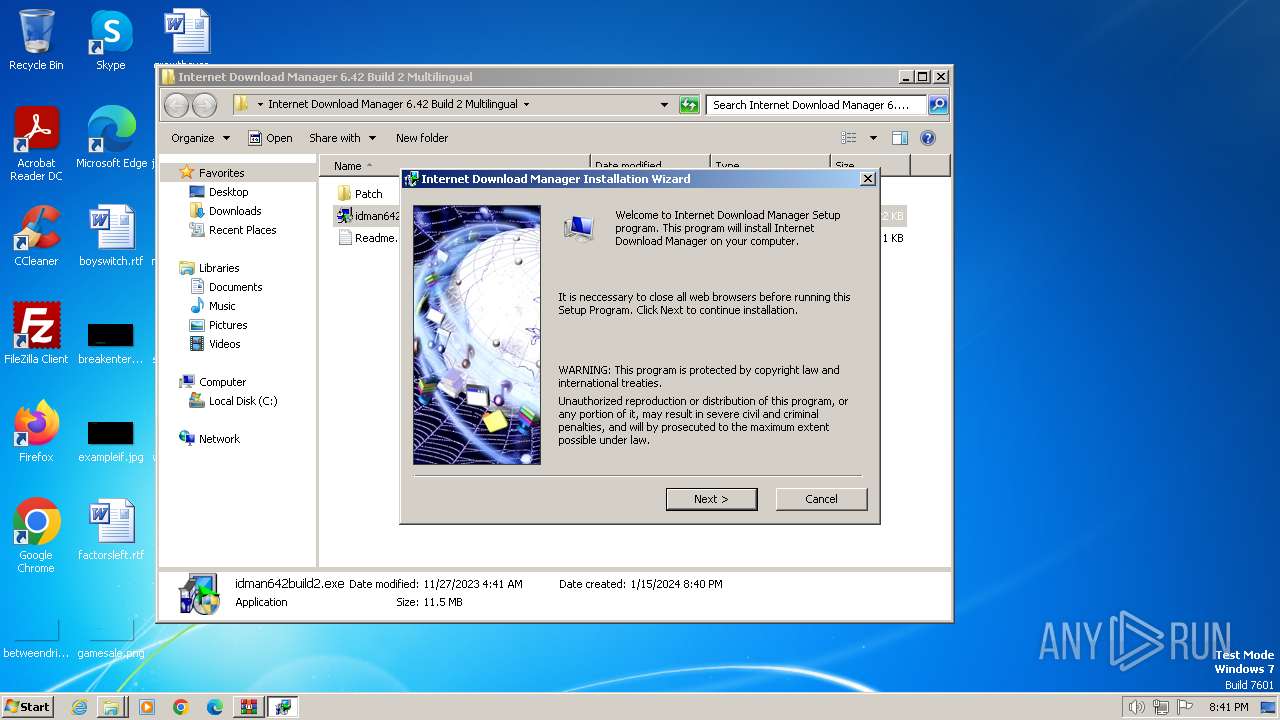
Starts application with an unusual extension
- idman642build2.exe (PID: 2528)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 2960)
Reads the Internet Settings
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- Uninstall.exe (PID: 1600)
- runonce.exe (PID: 3432)
- IDMan.exe (PID: 900)
Checks Windows Trust Settings
- IDMan.exe (PID: 2636)
- IDMan.exe (PID: 900)
Reads security settings of Internet Explorer
- IDMan.exe (PID: 2636)
- IDMan.exe (PID: 900)
Reads settings of System Certificates
- IDMan.exe (PID: 2636)
- IDMan.exe (PID: 900)
Creates/Modifies COM task schedule object
- IDMan.exe (PID: 2636)
- Uninstall.exe (PID: 1600)
Executable content was dropped or overwritten
- IDMan.exe (PID: 2636)
- rundll32.exe (PID: 2676)
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
- wscript.exe (PID: 2544)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 1600)
Creates or modifies Windows services
- Uninstall.exe (PID: 1600)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 2676)
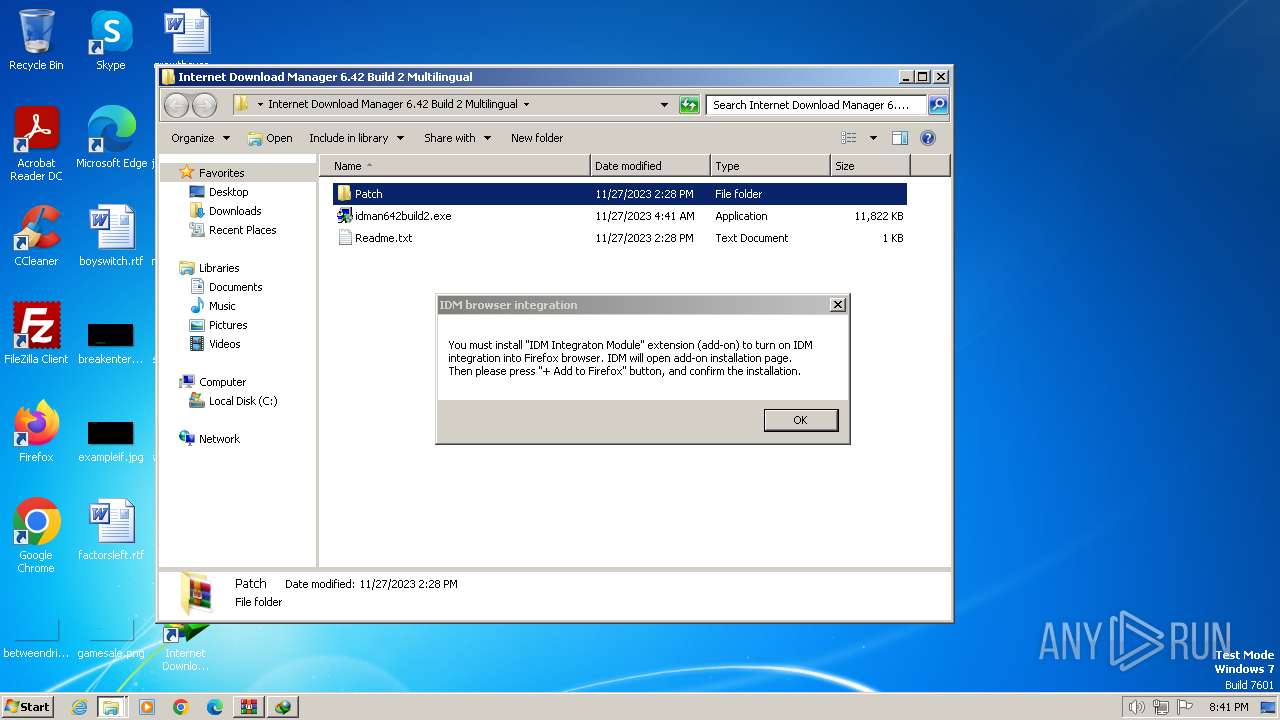
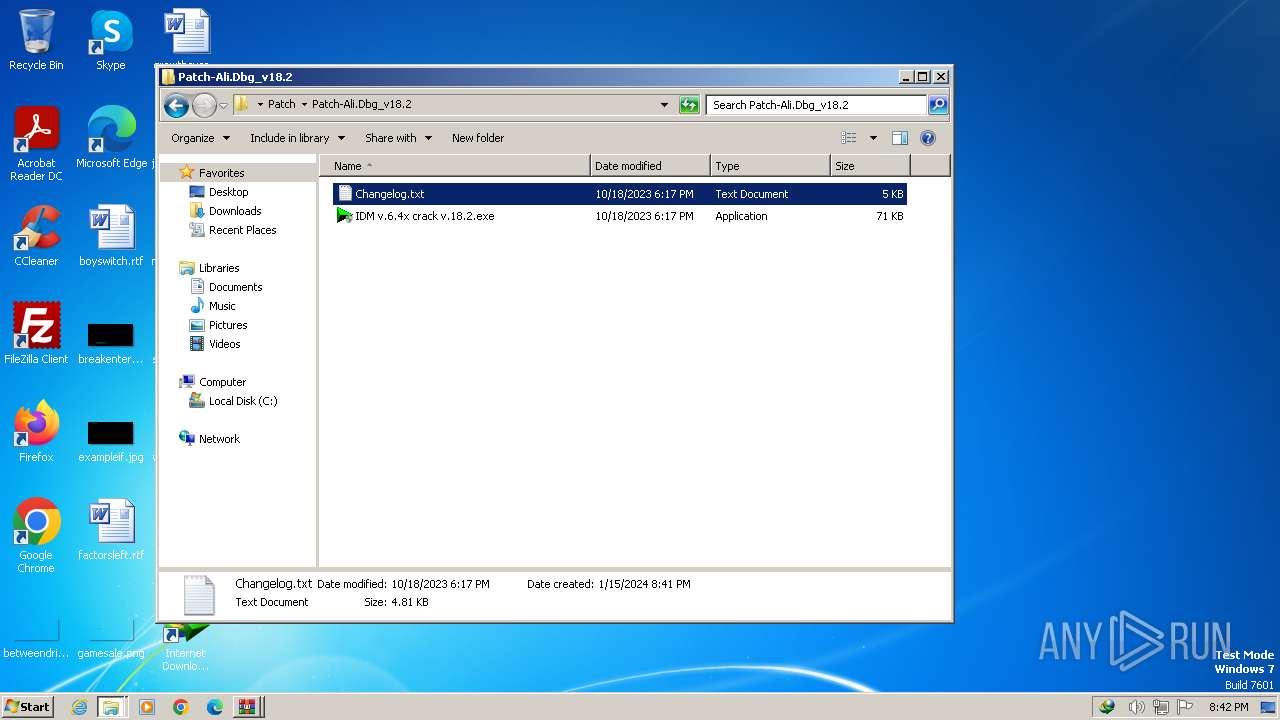
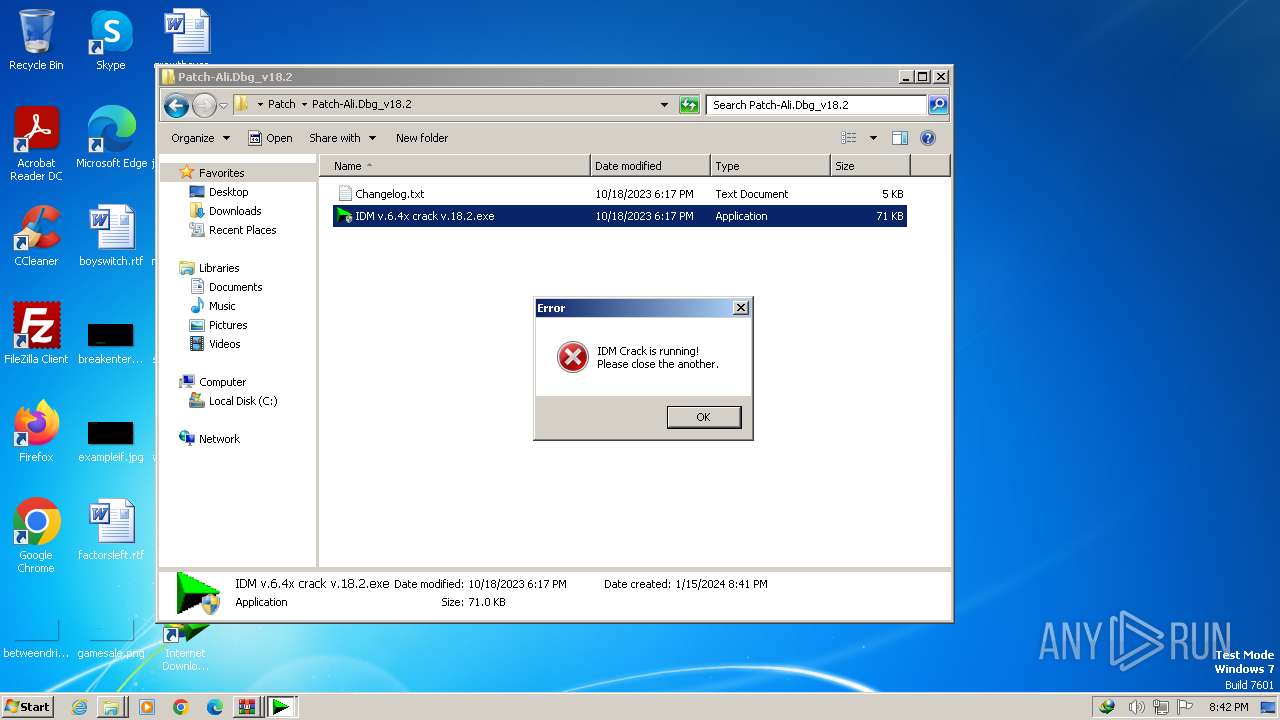
Searches for installed software
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
The process executes VB scripts
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2544)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2544)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2544)
INFO
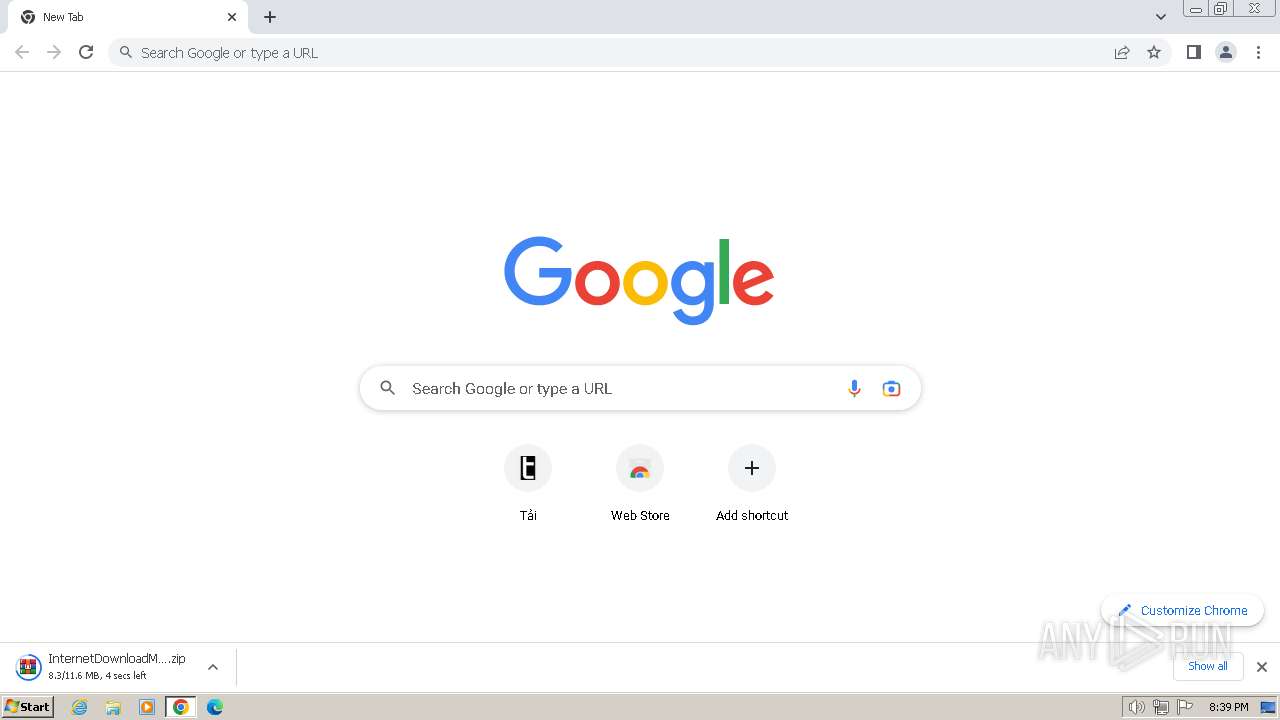
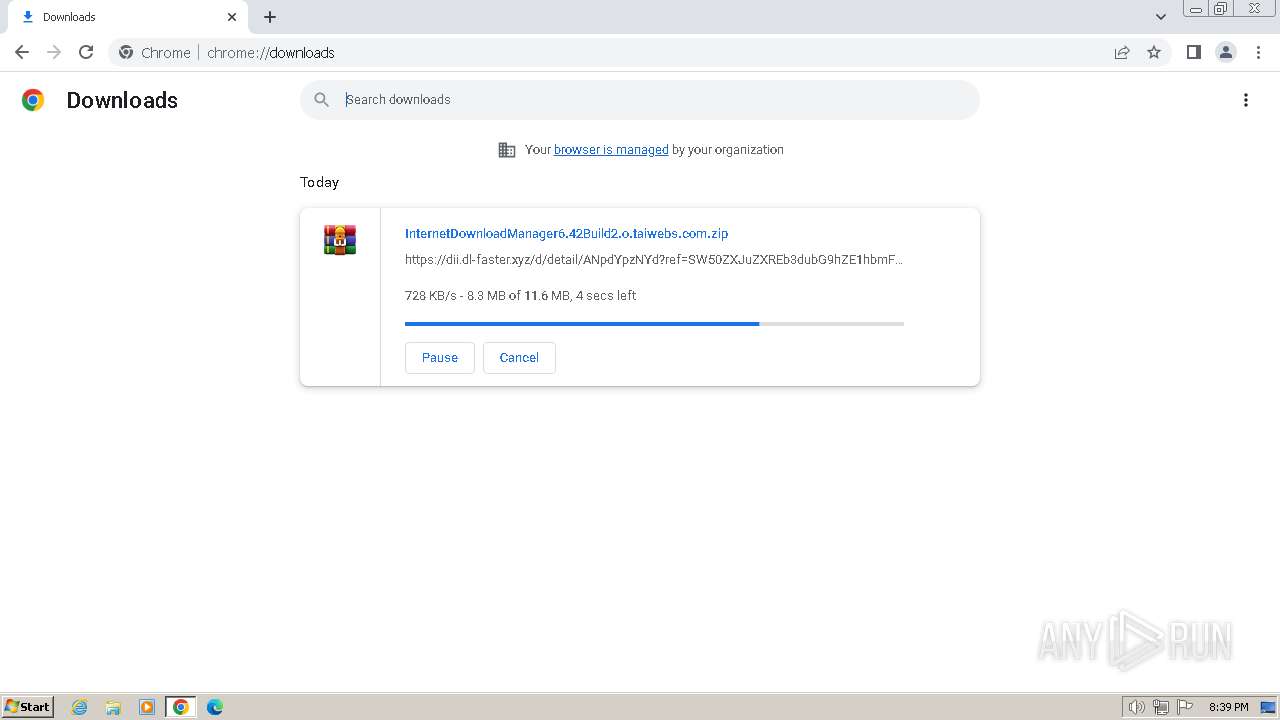
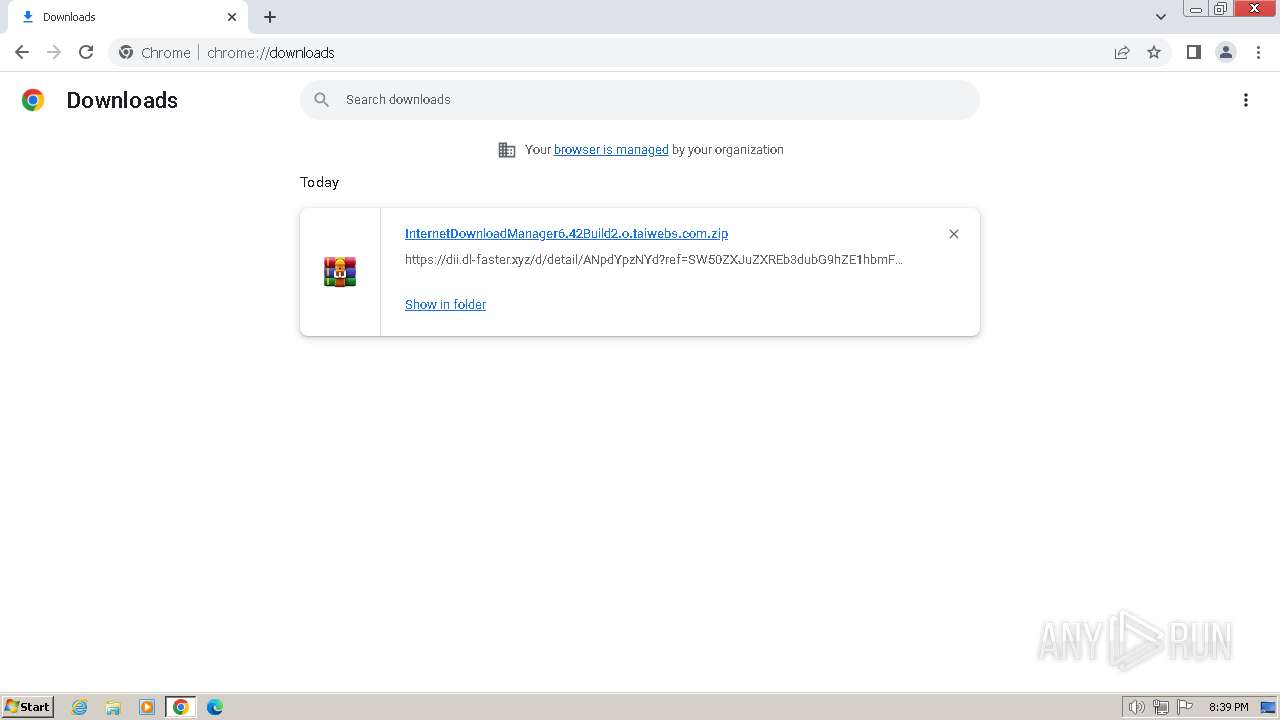
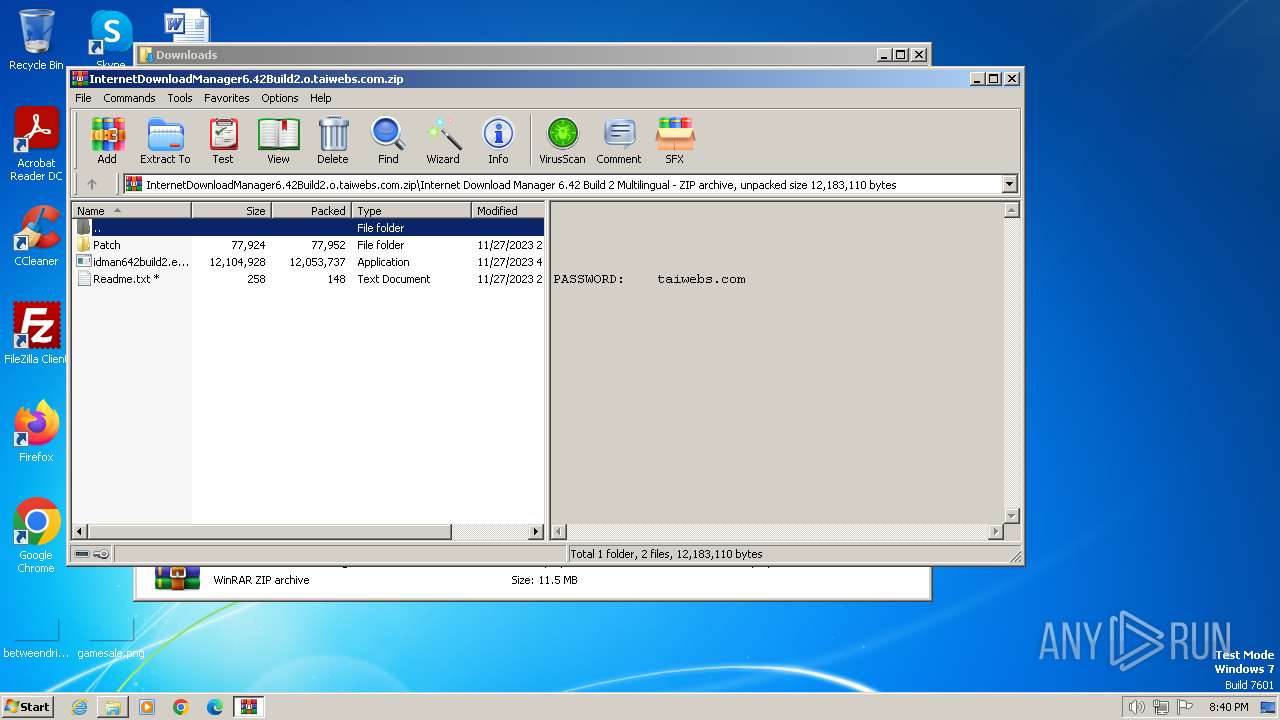
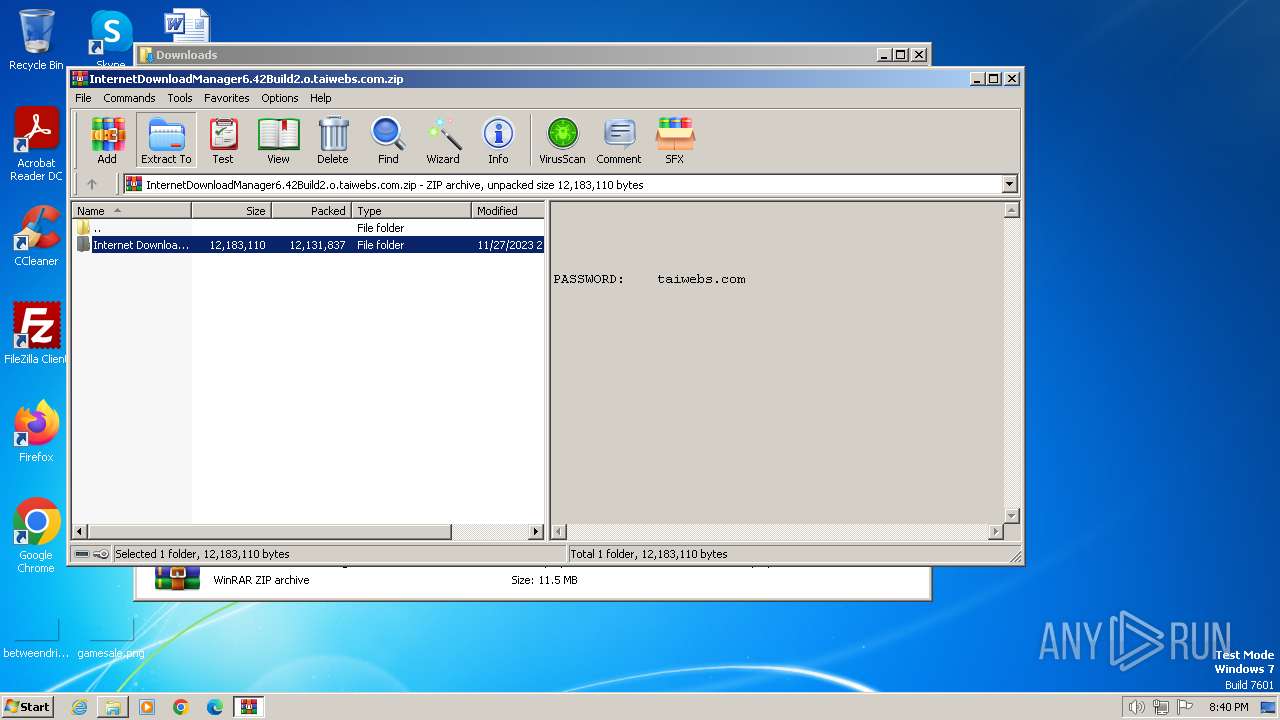
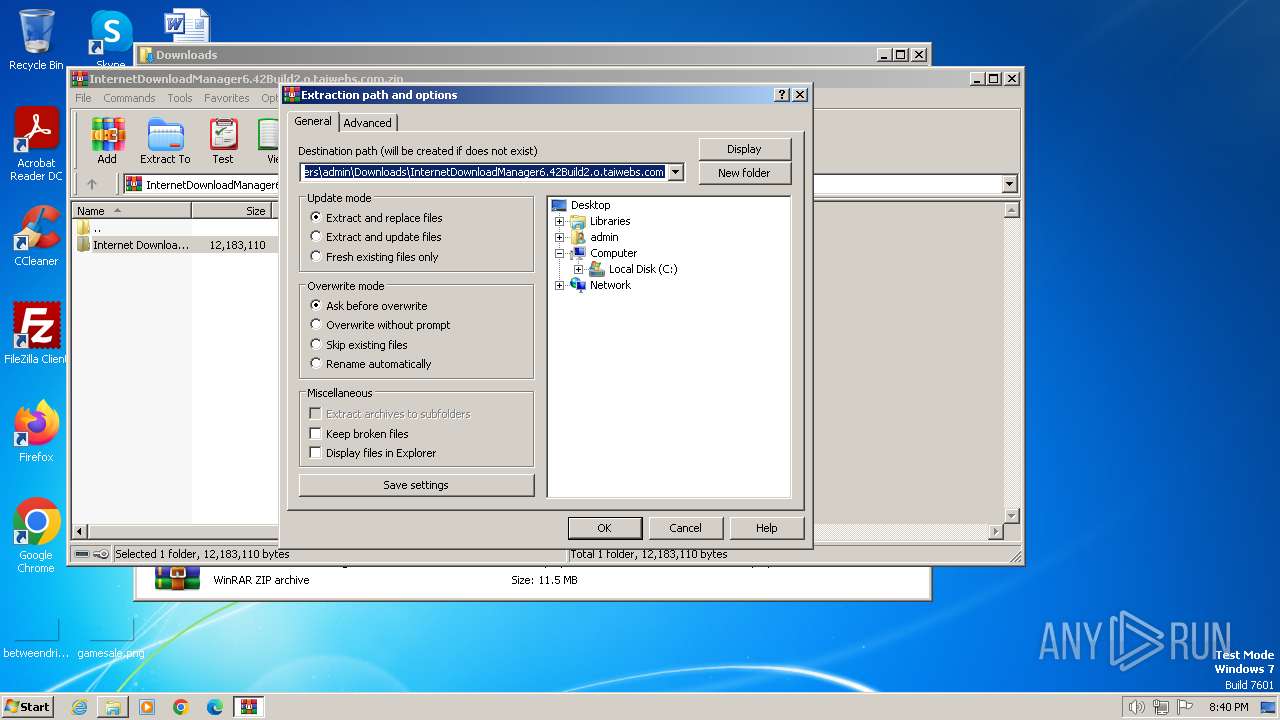
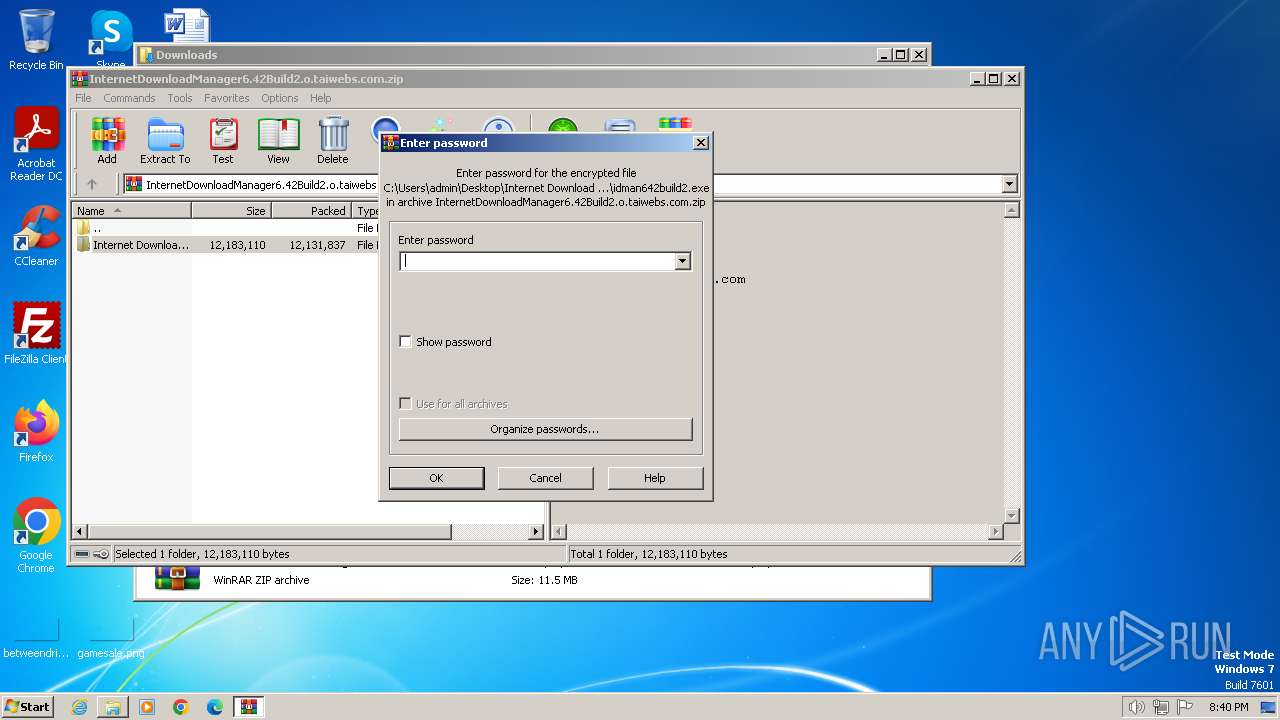
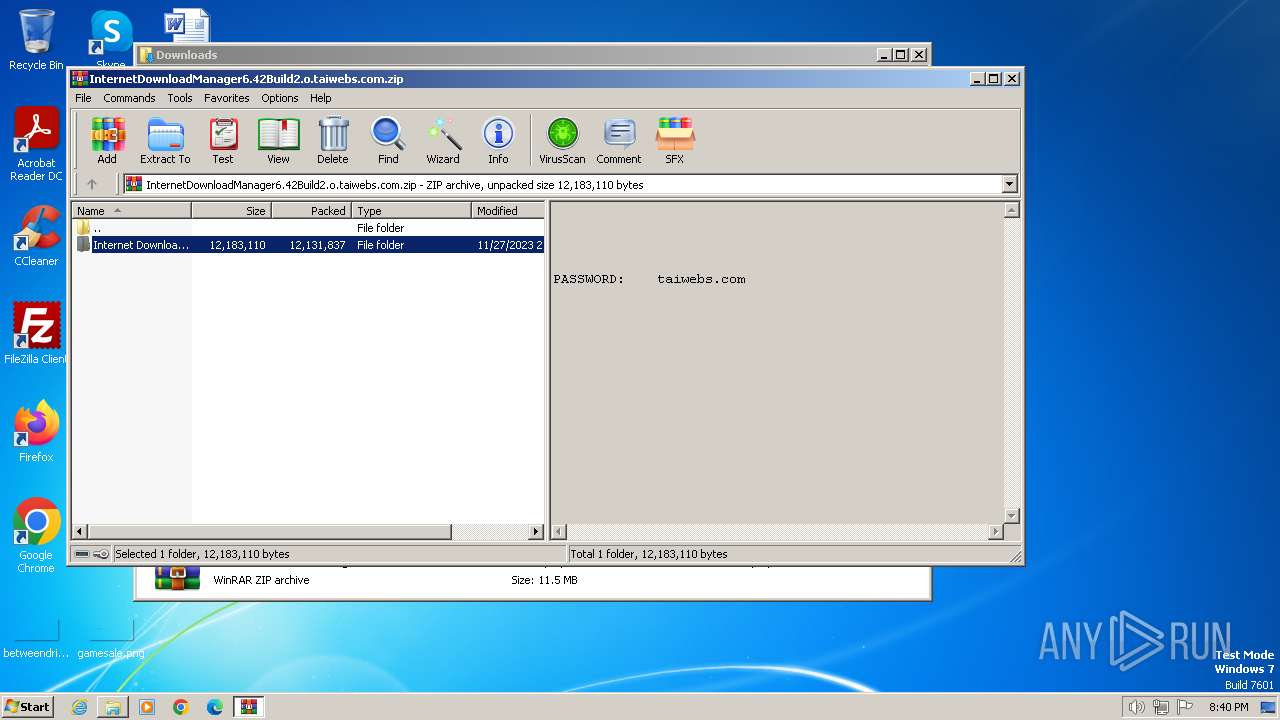
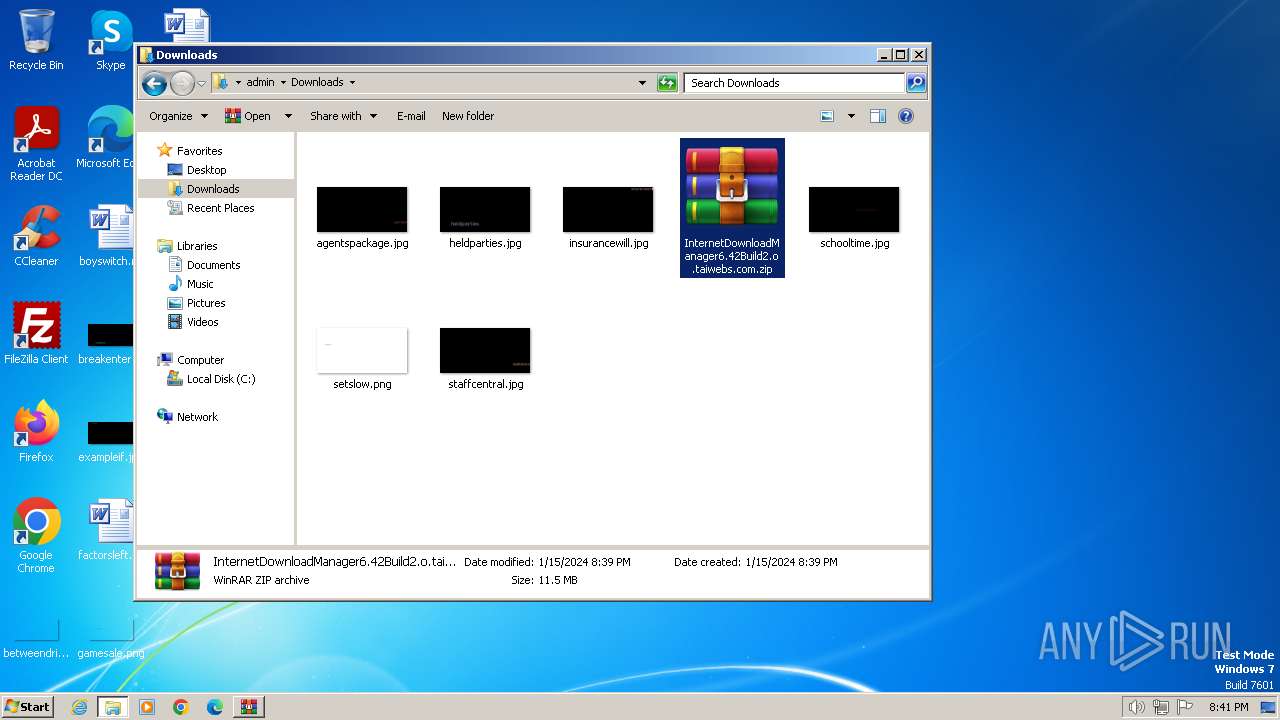
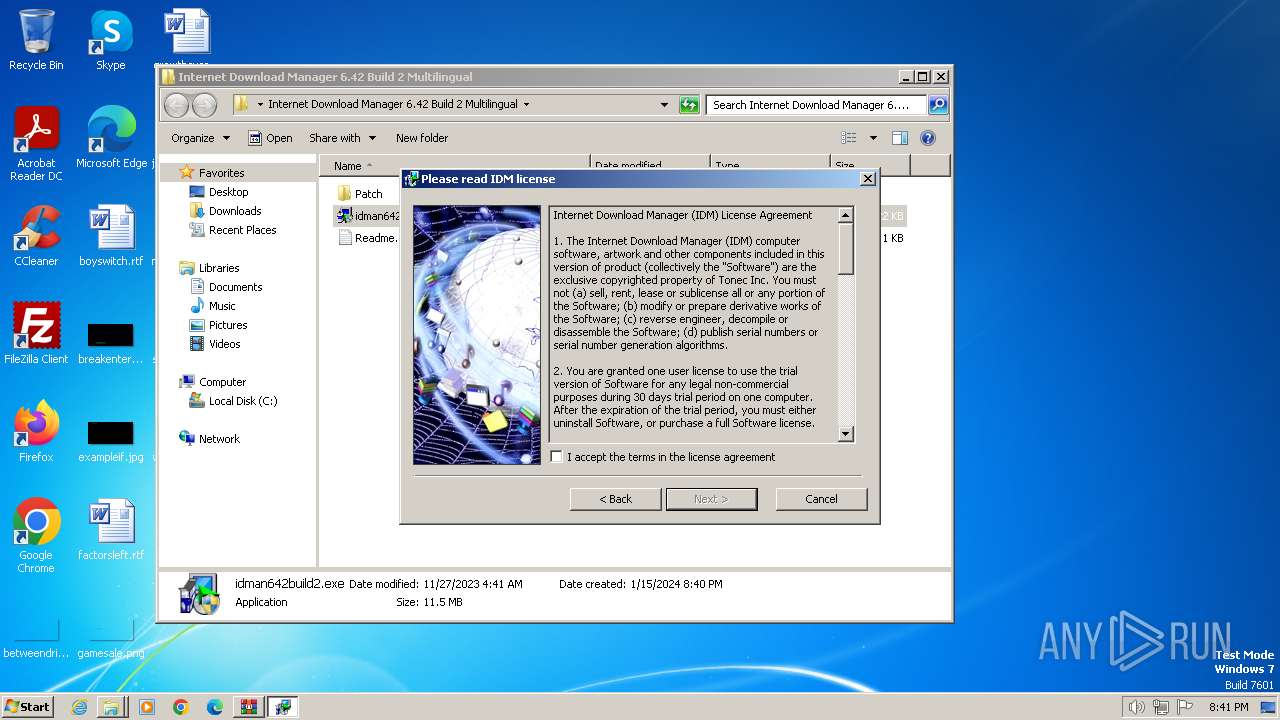
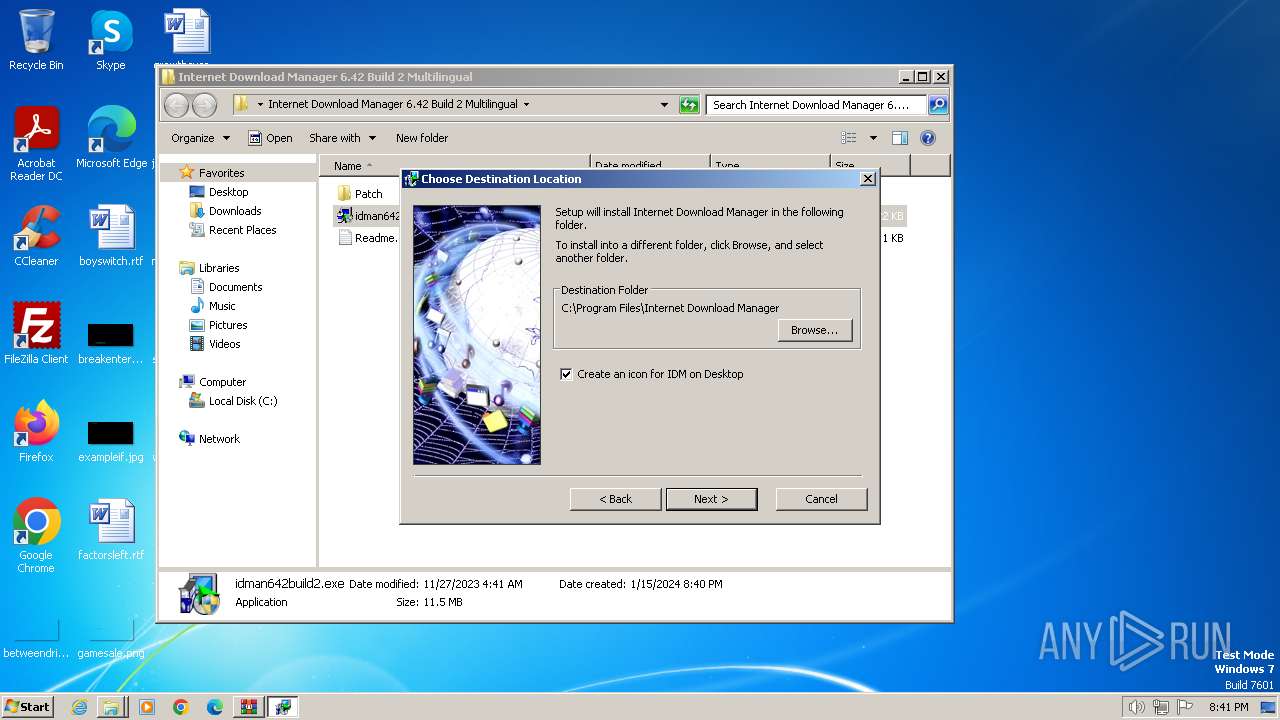
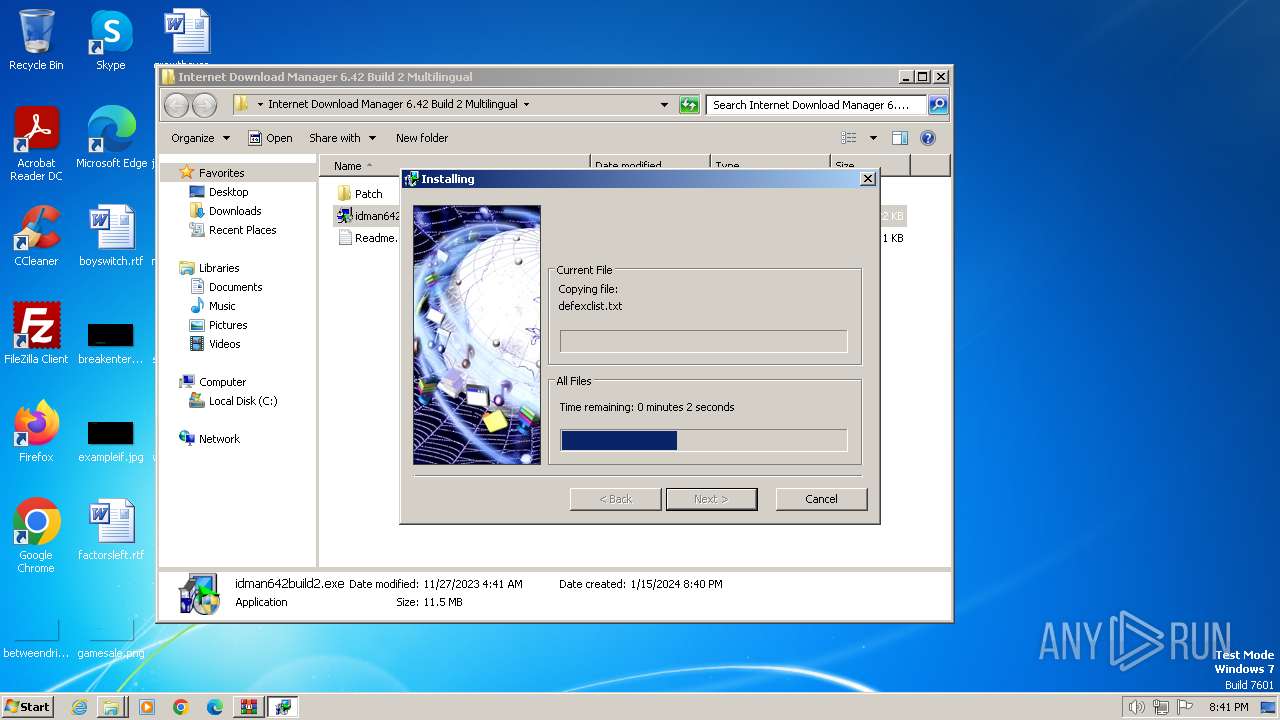
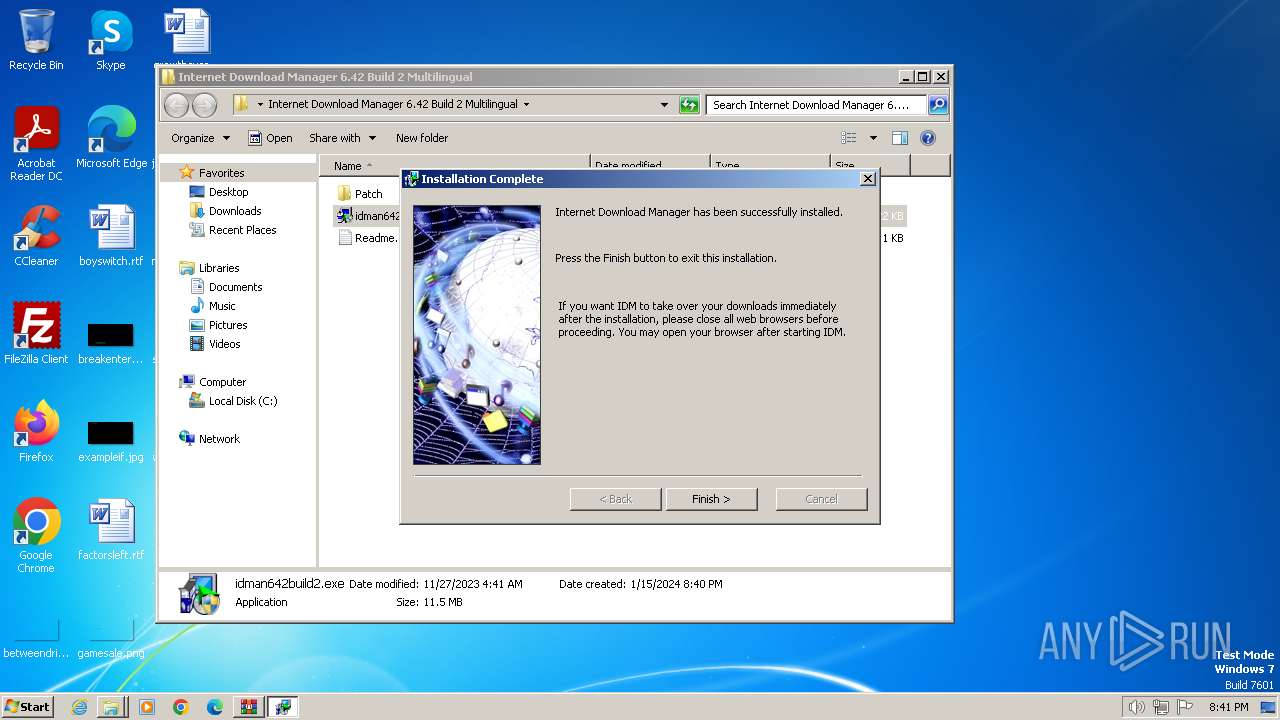
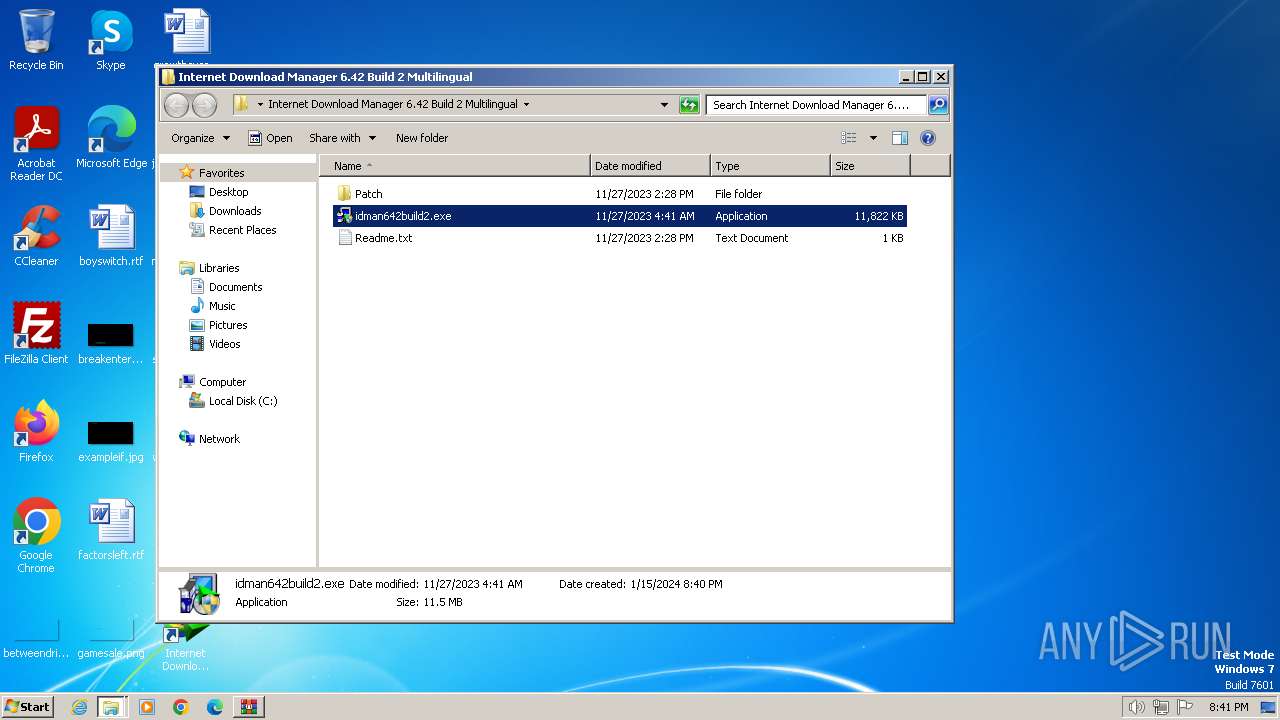
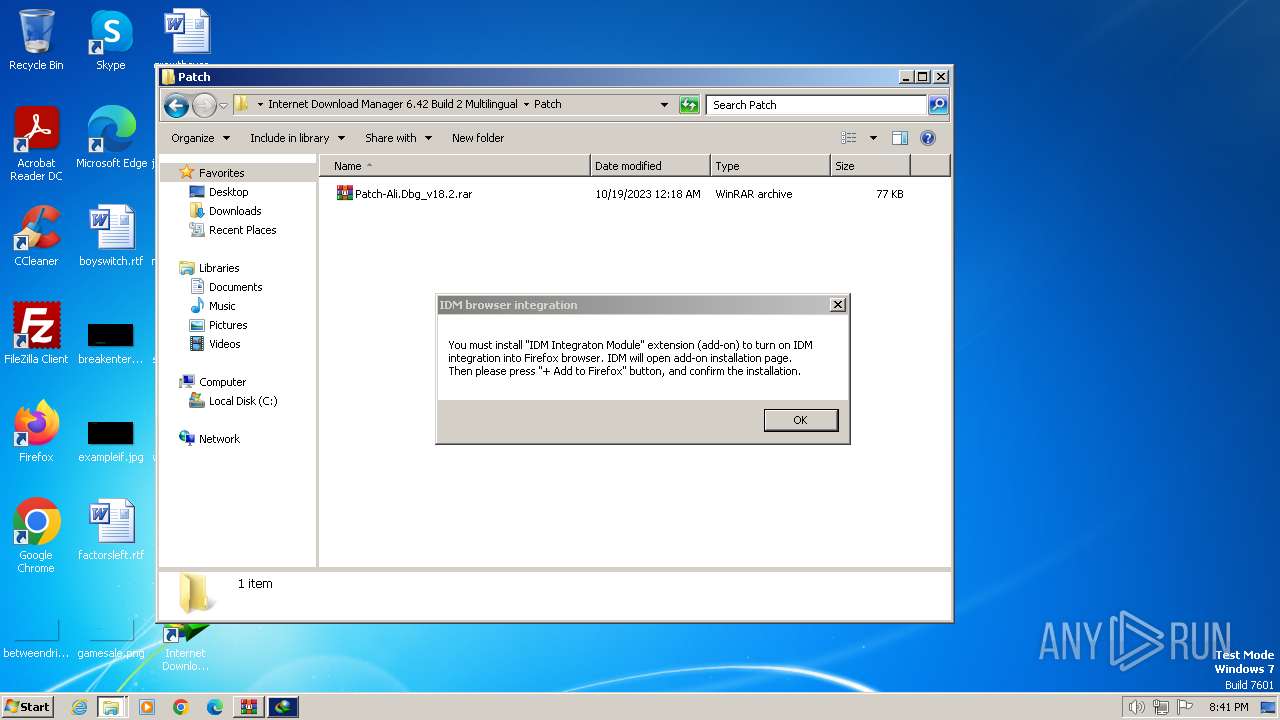
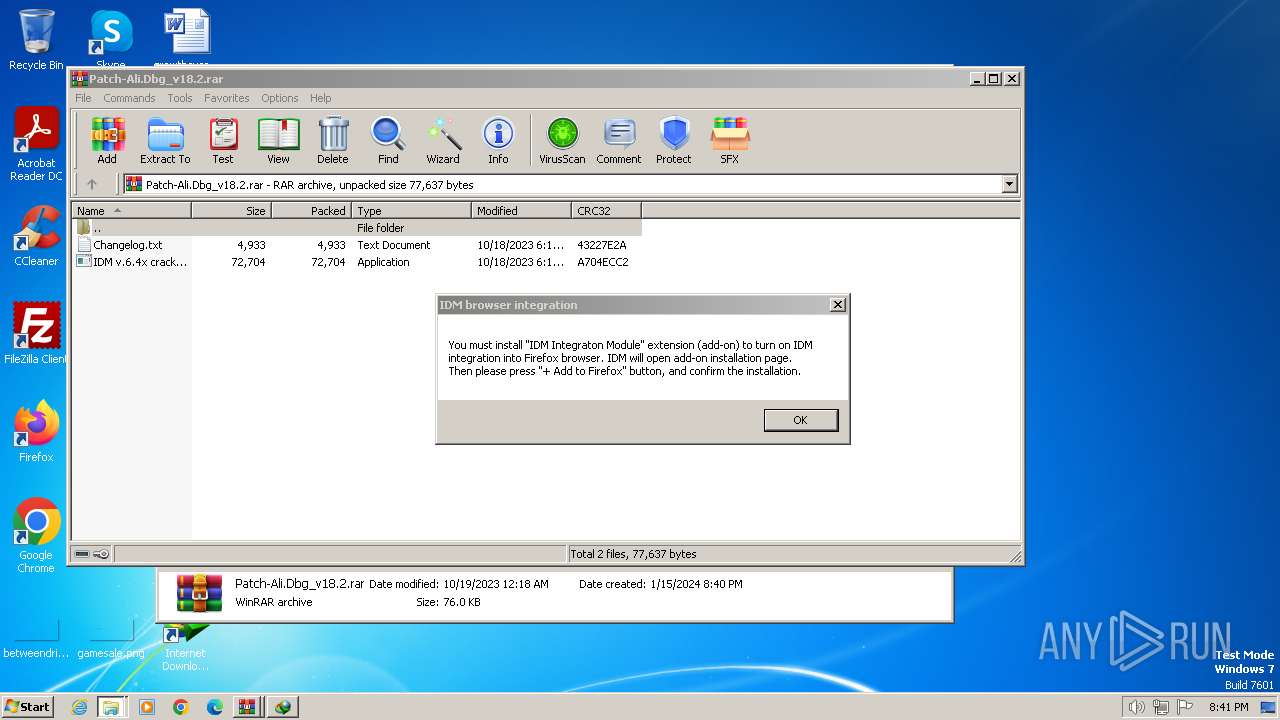
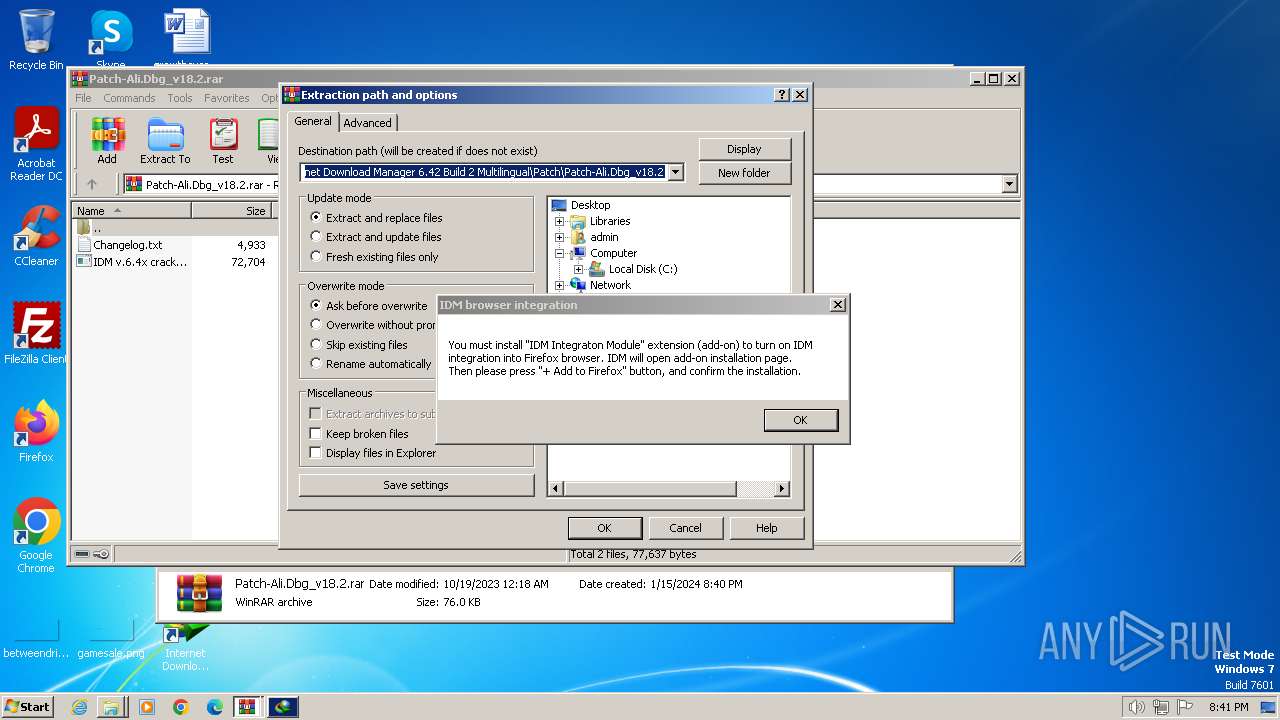
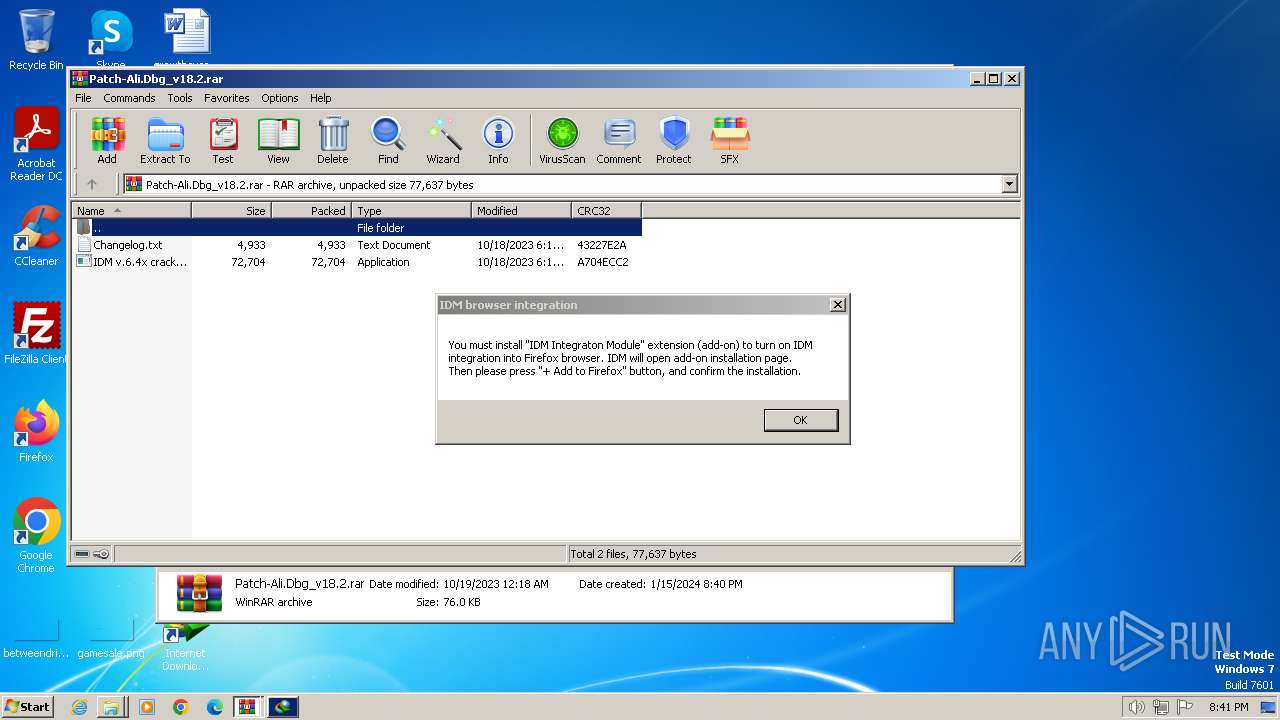
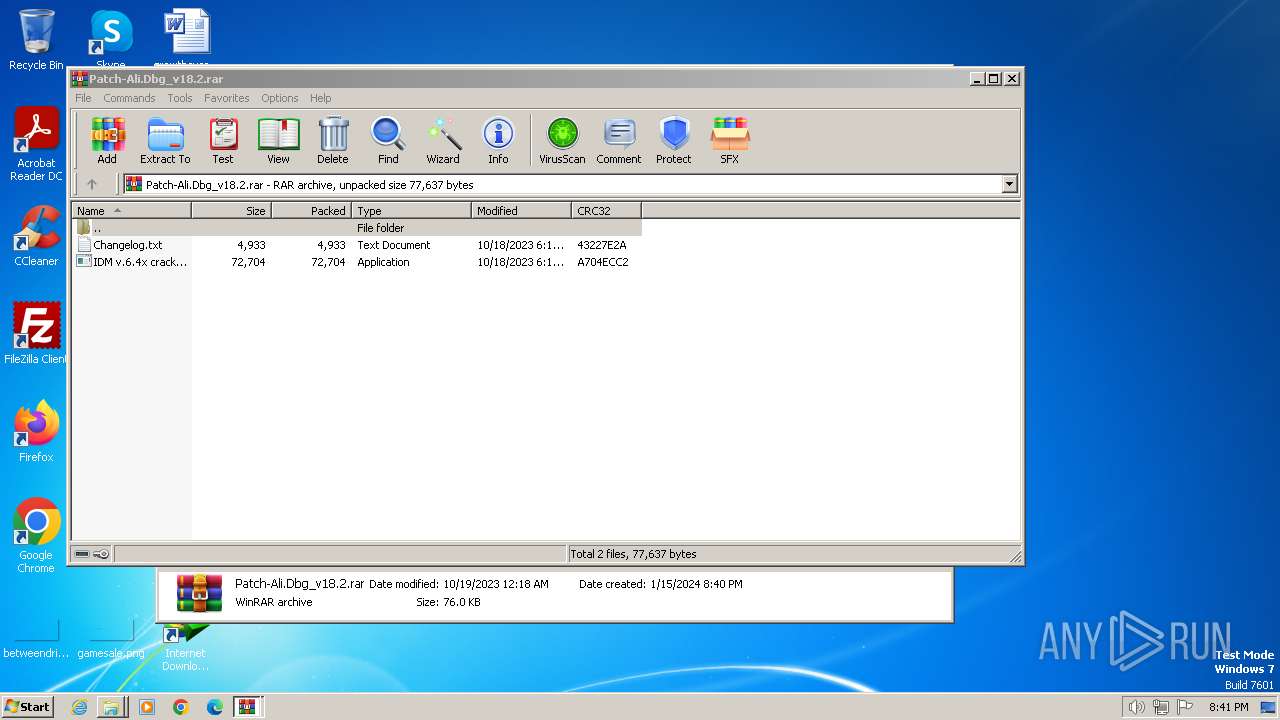
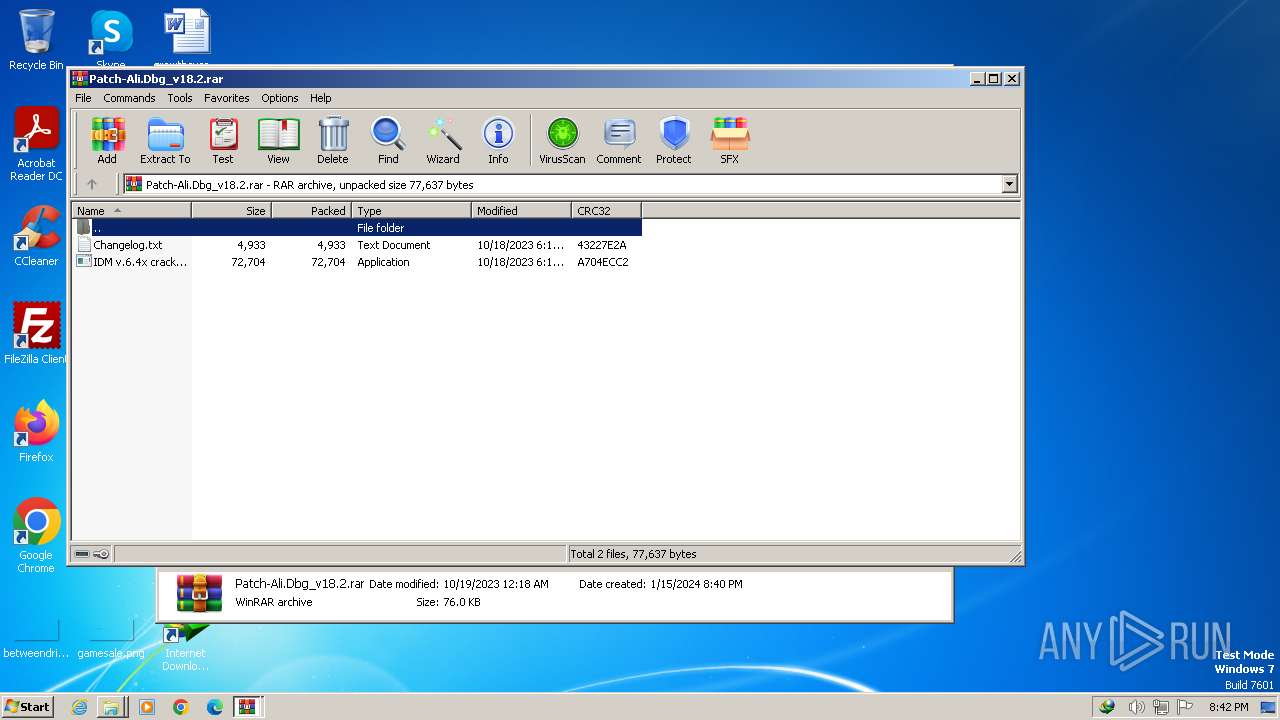
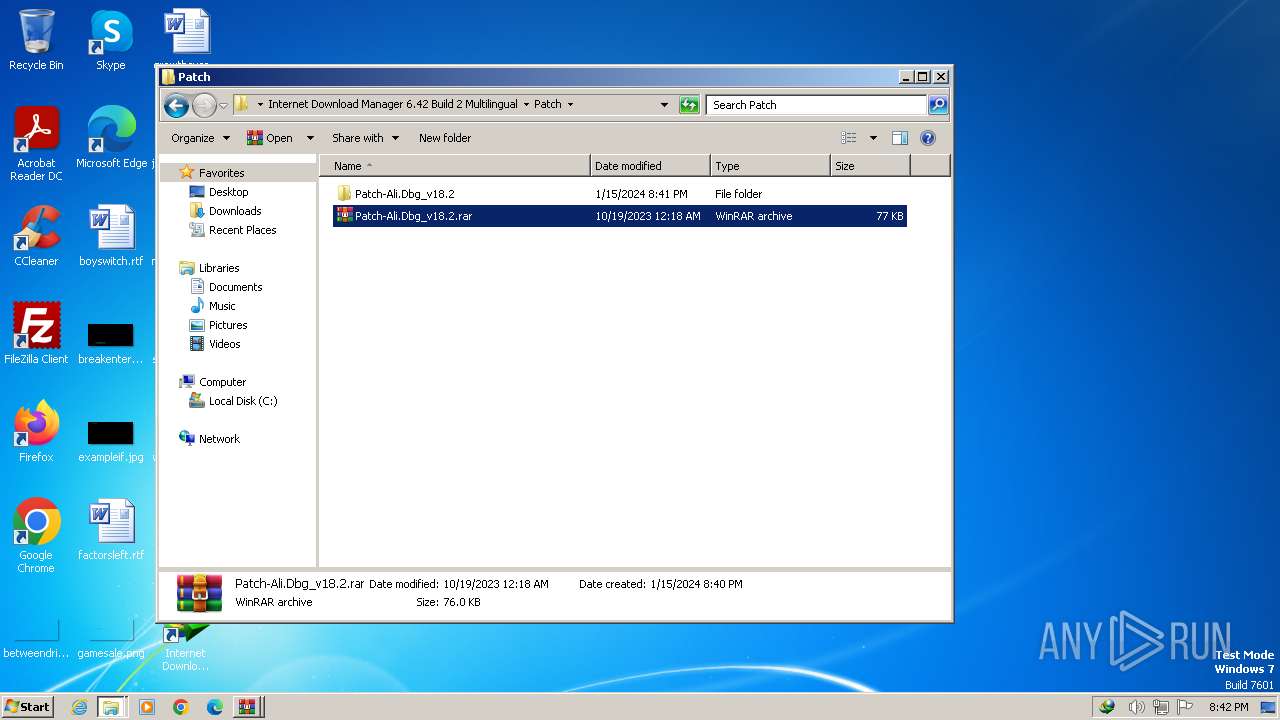
Manual execution by a user
- explorer.exe (PID: 3360)
- chrome.exe (PID: 1404)
- WinRAR.exe (PID: 3632)
- idman642build2.exe (PID: 2356)
- idman642build2.exe (PID: 2528)
- WinRAR.exe (PID: 1956)
- firefox.exe (PID: 3744)
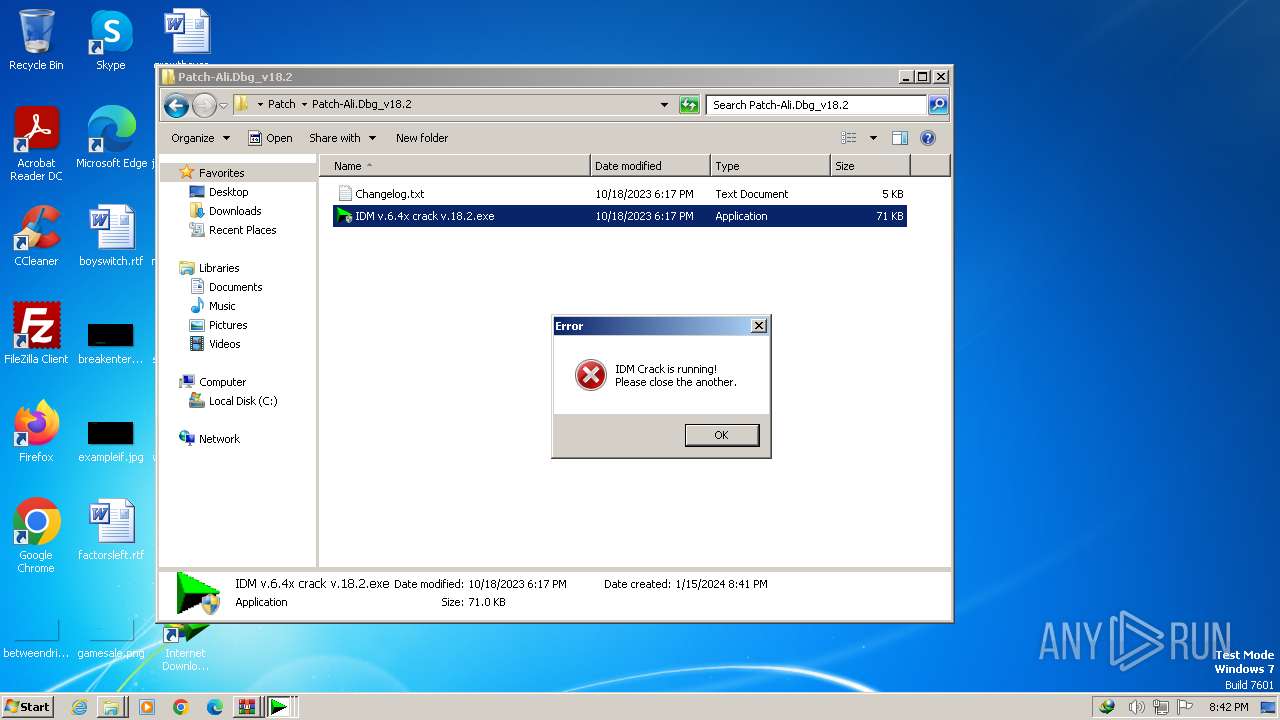
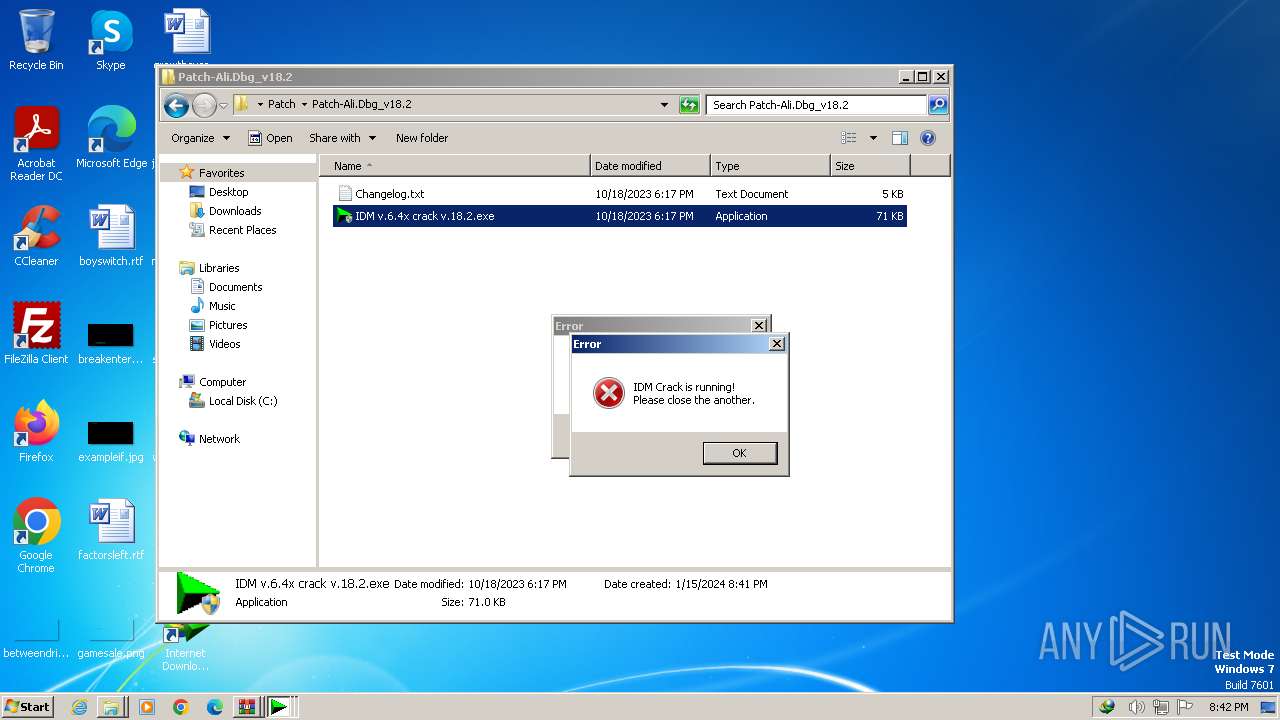
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
- IDM v.6.4x crack v.18.2.exe (PID: 4036)
- IDM v.6.4x crack v.18.2.exe (PID: 292)
- IDM v.6.4x crack v.18.2.exe (PID: 2168)
- IDM v.6.4x crack v.18.2.exe (PID: 1628)
- IDM v.6.4x crack v.18.2.exe (PID: 2760)
- IDM v.6.4x crack v.18.2.exe (PID: 1900)
- IDM v.6.4x crack v.18.2.exe (PID: 3416)
- IDM v.6.4x crack v.18.2.exe (PID: 1652)
- IDM v.6.4x crack v.18.2.exe (PID: 1492)
The process uses the downloaded file
- chrome.exe (PID: 3100)
- WinRAR.exe (PID: 3632)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3632)
- WinRAR.exe (PID: 1956)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3632)
- WinRAR.exe (PID: 1956)
- rundll32.exe (PID: 2676)
Application launched itself
- chrome.exe (PID: 1404)
- firefox.exe (PID: 3744)
- firefox.exe (PID: 1020)
Checks supported languages
- idman642build2.exe (PID: 2528)
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- idmBroker.exe (PID: 2828)
- Uninstall.exe (PID: 1600)
- MediumILStart.exe (PID: 1104)
- IDMan.exe (PID: 900)
- IEMonitor.exe (PID: 1772)
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
- IDM v.6.4x crack v.18.2.exe (PID: 2760)
- IDM v.6.4x crack v.18.2.exe (PID: 292)
- IDM v.6.4x crack v.18.2.exe (PID: 1900)
- IDM v.6.4x crack v.18.2.exe (PID: 1492)
Create files in a temporary directory
- idman642build2.exe (PID: 2528)
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- IDMan.exe (PID: 900)
- IDM v.6.4x crack v.18.2.exe (PID: 3064)
Reads the machine GUID from the registry
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- MediumILStart.exe (PID: 1104)
- IDMan.exe (PID: 900)
Creates files in the program directory
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- wscript.exe (PID: 2544)
Creates files or folders in the user directory
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- IDMan.exe (PID: 900)
Reads the computer name
- IDM1.tmp (PID: 2960)
- IDMan.exe (PID: 2636)
- Uninstall.exe (PID: 1600)
- MediumILStart.exe (PID: 1104)
- IDMan.exe (PID: 900)
- IEMonitor.exe (PID: 1772)
Creates files in the driver directory
- rundll32.exe (PID: 2676)
Reads the time zone
- runonce.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:11:27 14:28:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
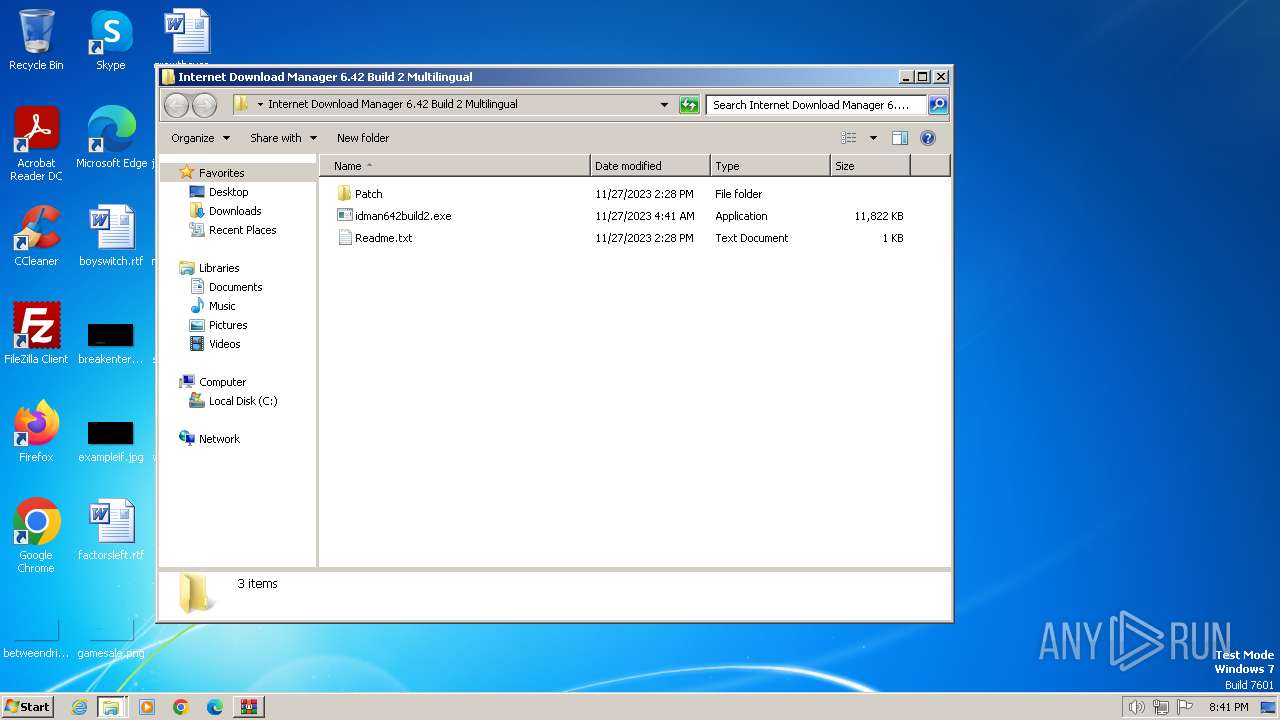
| ZipFileName: | Internet Download Manager 6.42 Build 2 Multilingual/ |
Total processes
152
Monitored processes
97
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\AppData\Local\Temp\InternetDownloadManager6.42Build2.o.taiwebs.com.zip.kmz" | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1020.4.1829987287\179134695" -childID 3 -isForBrowser -prefsHandle 3580 -prefMapHandle 3568 -prefsLen 34225 -prefMapSize 244195 -jsInitHandle 912 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {63aa8748-a6ca-459e-8615-6c341e027dc4} 1020 "\\.\pipe\gecko-crash-server-pipe.1020" 3592 18515840 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 292 | "C:\Users\admin\Desktop\Internet Download Manager 6.42 Build 2 Multilingual\Patch\Patch-Ali.Dbg_v18.2\IDM v.6.4x crack v.18.2.exe" | C:\Users\admin\Desktop\Internet Download Manager 6.42 Build 2 Multilingual\Patch\Patch-Ali.Dbg_v18.2\IDM v.6.4x crack v.18.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=5656 --field-trial-handle=1124,i,20426745360273577,7177951566619045359,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3472 --field-trial-handle=1124,i,20426745360273577,7177951566619045359,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1452 --field-trial-handle=1124,i,20426745360273577,7177951566619045359,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2176 --field-trial-handle=1124,i,20426745360273577,7177951566619045359,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=2368 --field-trial-handle=1124,i,20426745360273577,7177951566619045359,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Internet Download Manager\IDMan.exe" -Embedding | C:\Program Files\Internet Download Manager\IDMan.exe | svchost.exe | ||||||||||||
User: admin Company: Tonec Inc. Integrity Level: MEDIUM Description: Internet Download Manager (IDM) Exit code: 0 Version: 6, 42, 2, 2 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1020.8.653319672\973725364" -childID 7 -isForBrowser -prefsHandle 2216 -prefMapHandle 2092 -prefsLen 29313 -prefMapSize 244195 -jsInitHandle 912 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {314beb4e-07b4-458b-b6ef-7c7d8909c3b4} 1020 "\\.\pipe\gecko-crash-server-pipe.1020" 2360 1a4fb110 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
Total events
30 457
Read events
30 026
Write events
344
Delete events
87
Modification events
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
22
Suspicious files
458
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe49f5.TMP | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe4a14.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe4d12.TMP | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe49f5.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
464
DNS requests
661
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 5.84 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 9.61 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 8.90 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 9.87 Kb | unknown |
1020 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | unknown |
2636 | IDMan.exe | GET | 200 | 173.222.108.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f1efbd474219b04a | CH | compressed | 65.2 Kb | unknown |
1020 | firefox.exe | POST | 200 | 95.101.54.216:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
1020 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | unknown |
1020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
584 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1404 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
584 | chrome.exe | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | unknown |
584 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
584 | chrome.exe | 142.250.185.110:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
584 | chrome.exe | 216.58.206.35:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1404 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
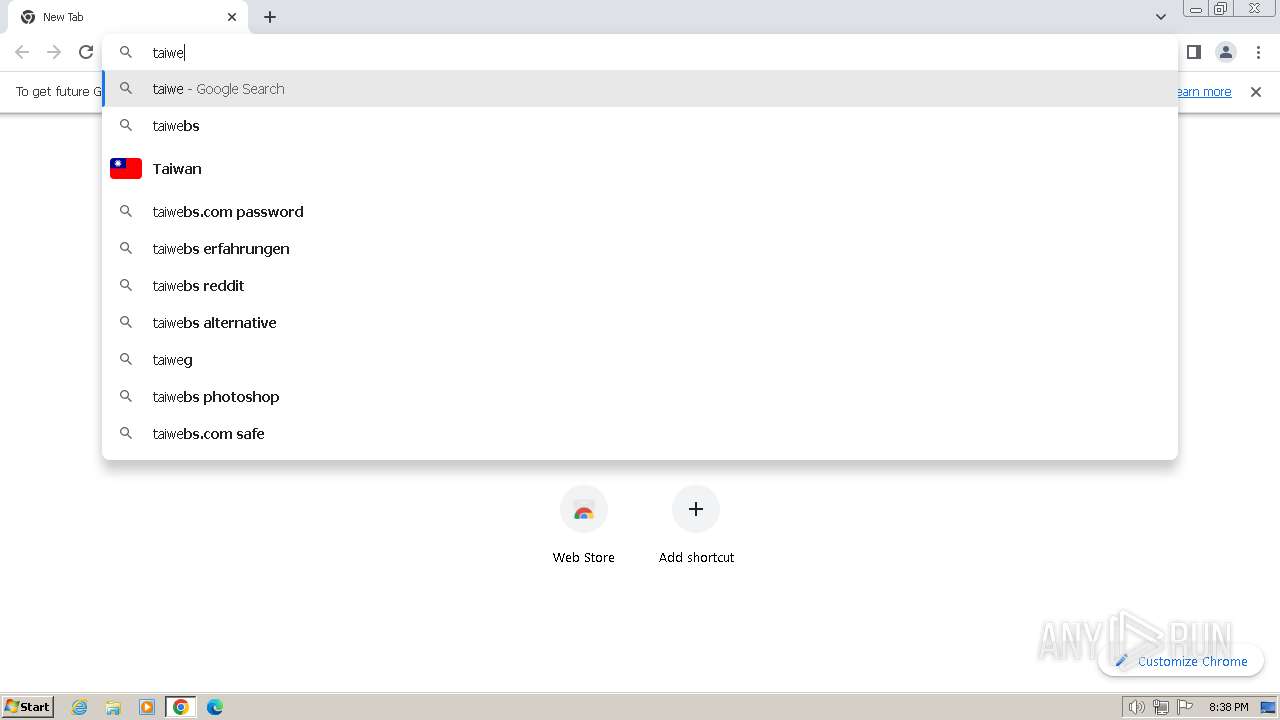
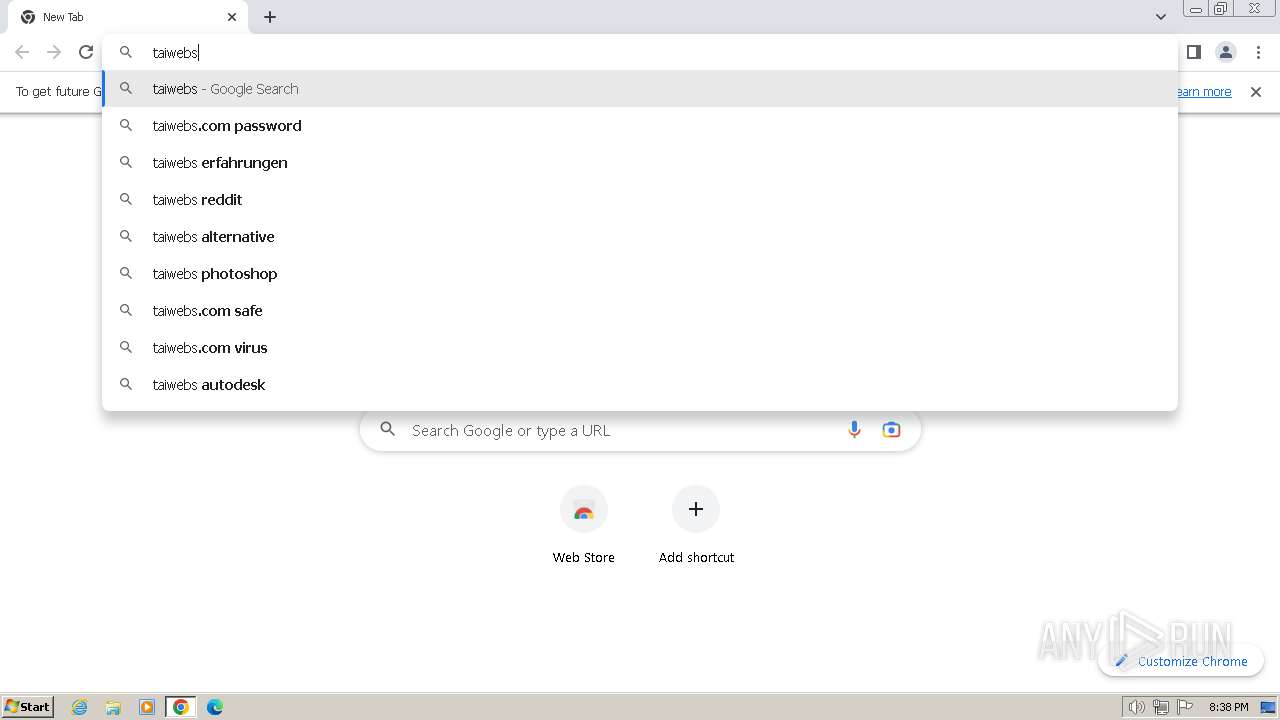
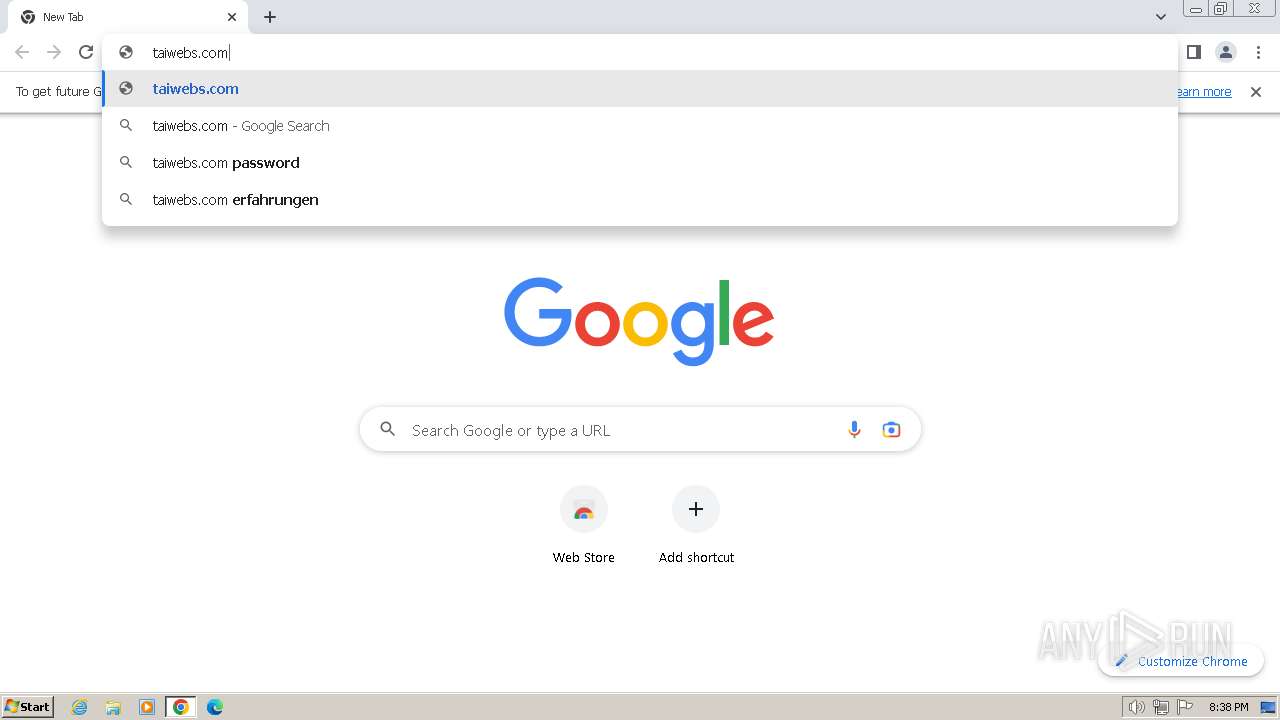
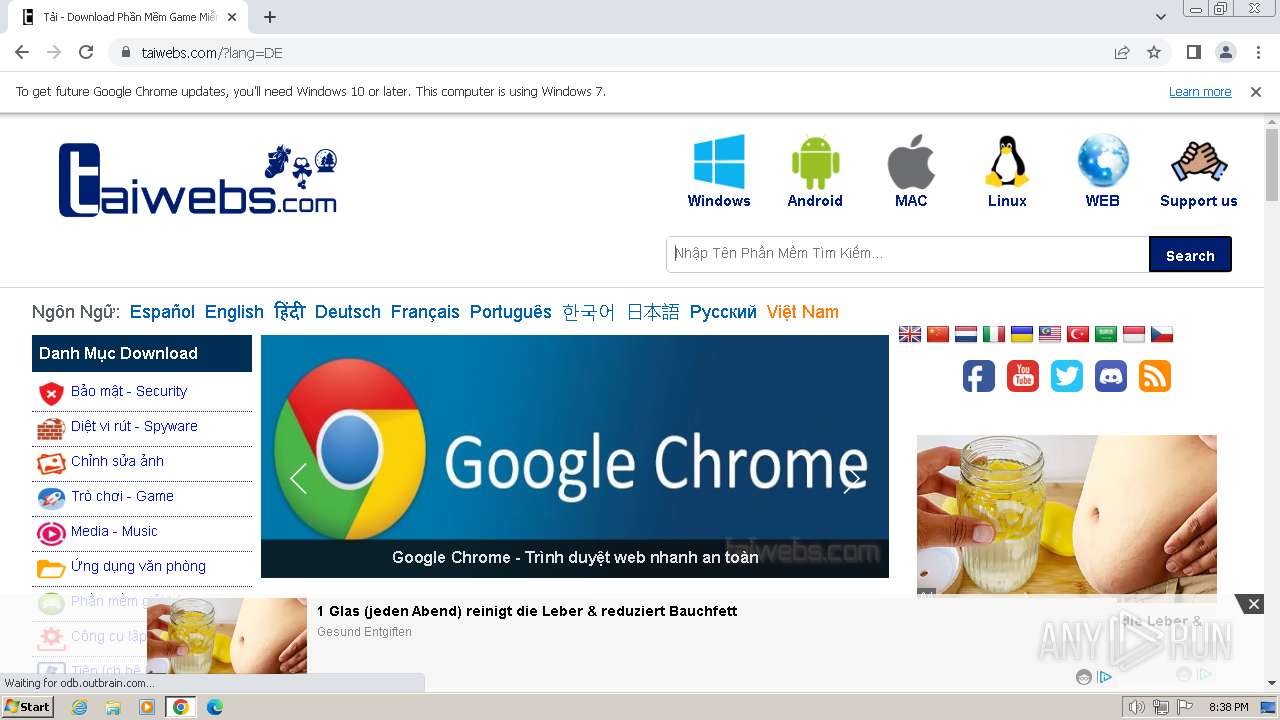
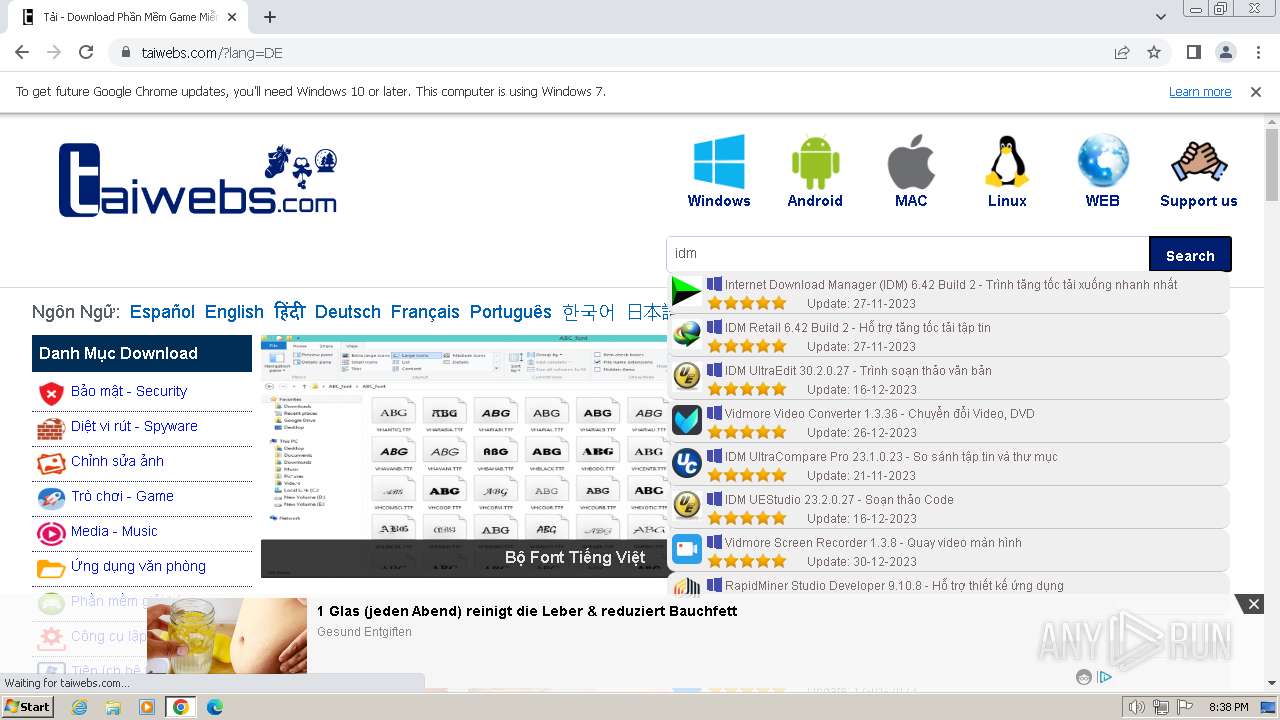
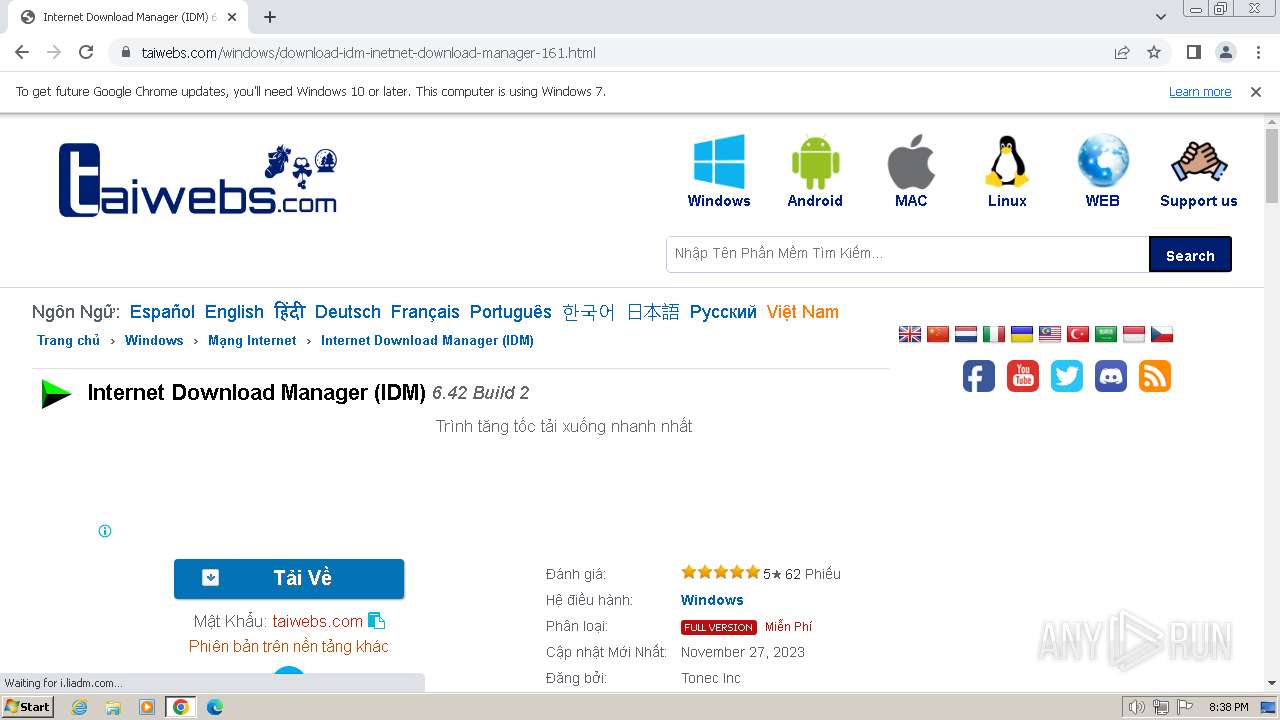
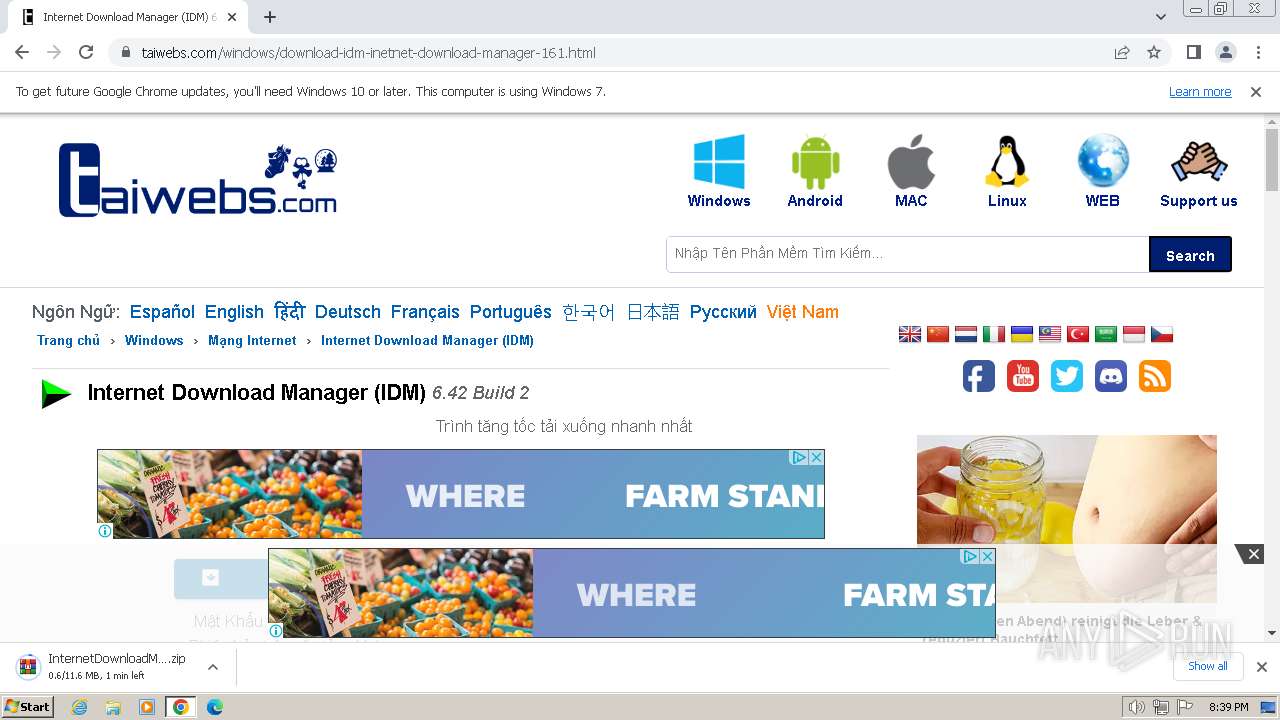
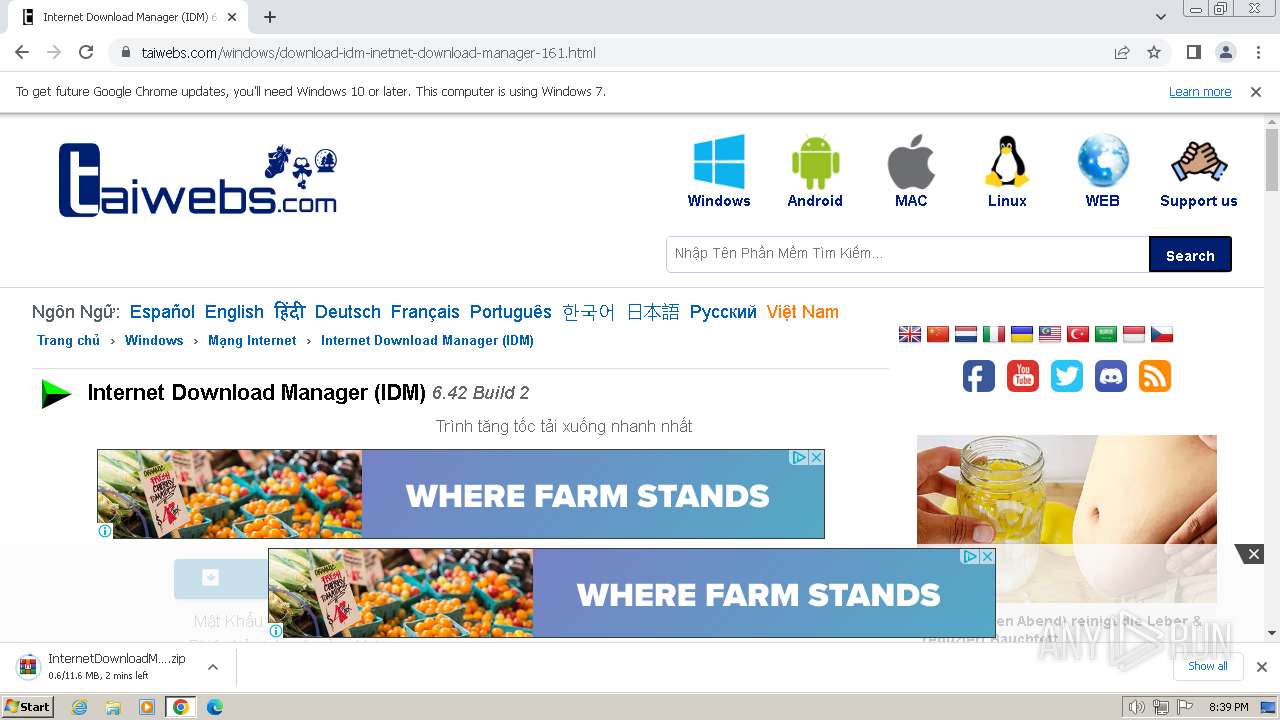
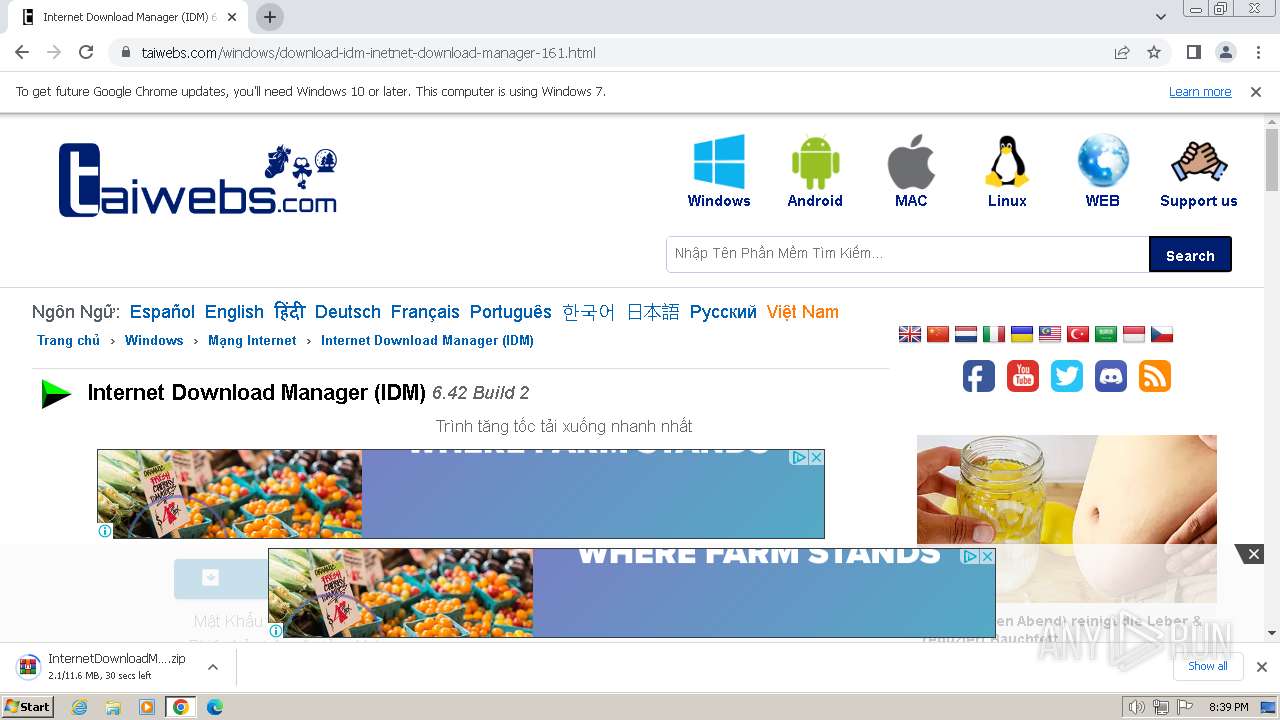
taiwebs.com |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
translate.google.com |
| whitelisted |
services.vlitag.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
584 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
584 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
584 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
584 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
584 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |