| File name: | inst.exe |
| Full analysis: | https://app.any.run/tasks/5bd0c32f-6ceb-4c95-a303-6af39d56bc20 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2020, 05:48:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3828310B20CE363137CBB37F19E146A2 |
| SHA1: | 450F7682A836755CE7552F9247999549AA022F63 |
| SHA256: | DA53B27B6C6AD79A209E31DDD9B0BEC02AB53211A0D35BD4BF684D854274AC63 |
| SSDEEP: | 98304:6VOpDTdOVl804FL8VIavYtmvWNs4lqMi0S2v7VDfHrai1Pwm:vBROn4yVI4HL/2vhDfLaS |
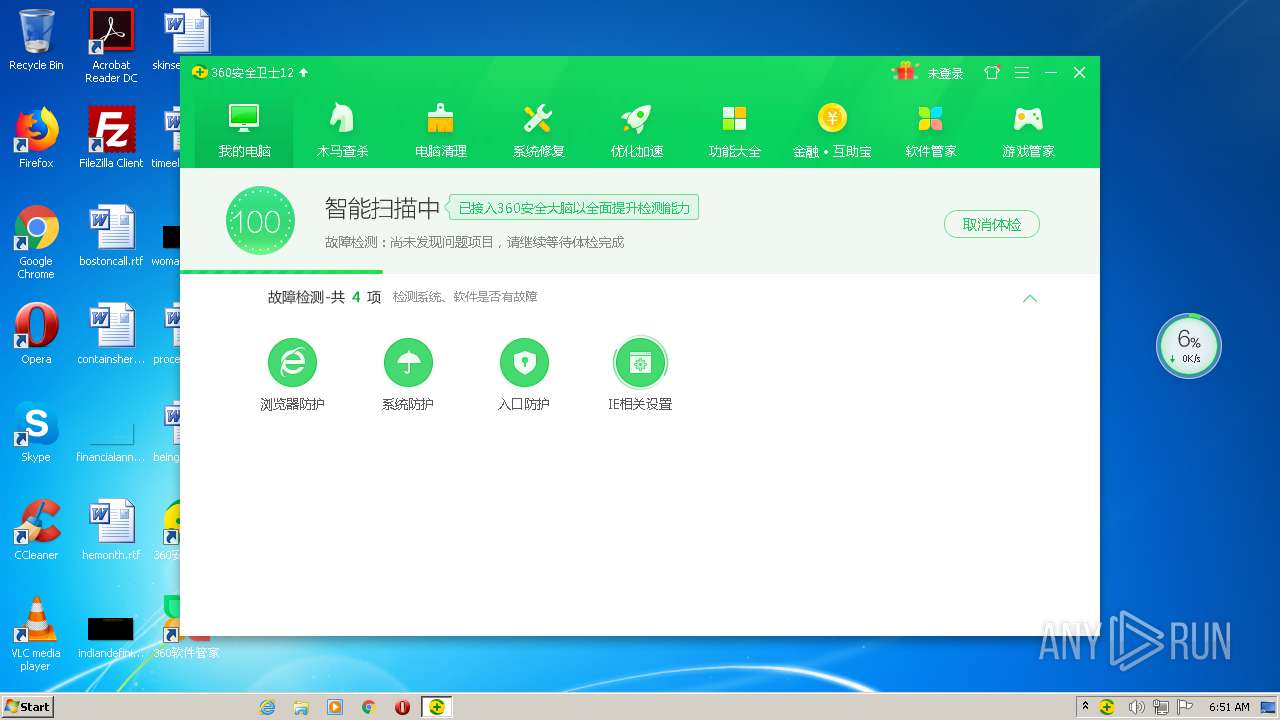
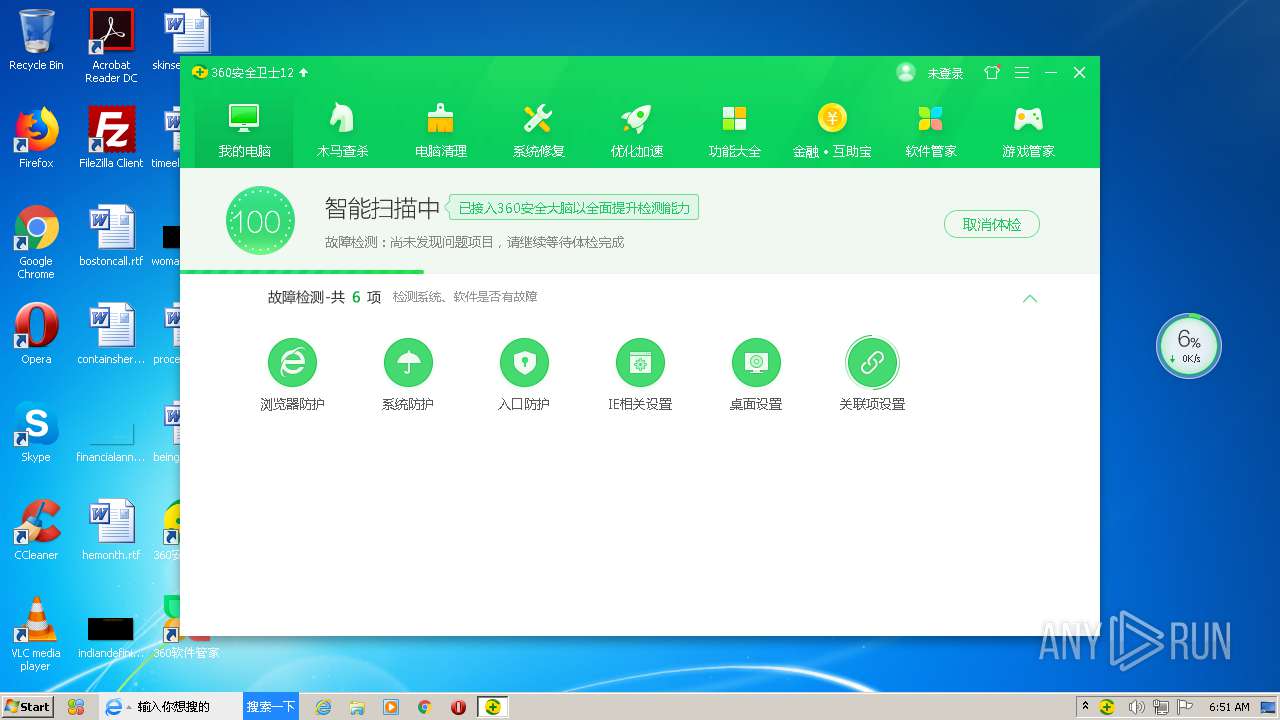
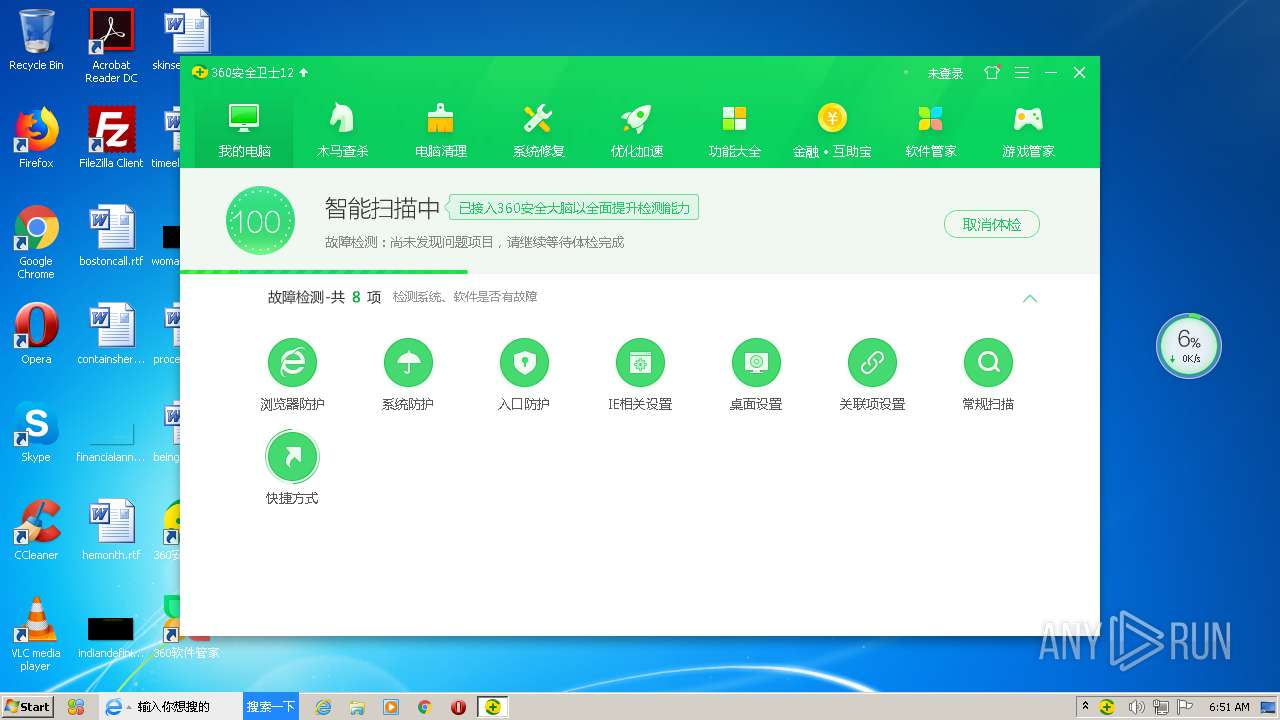
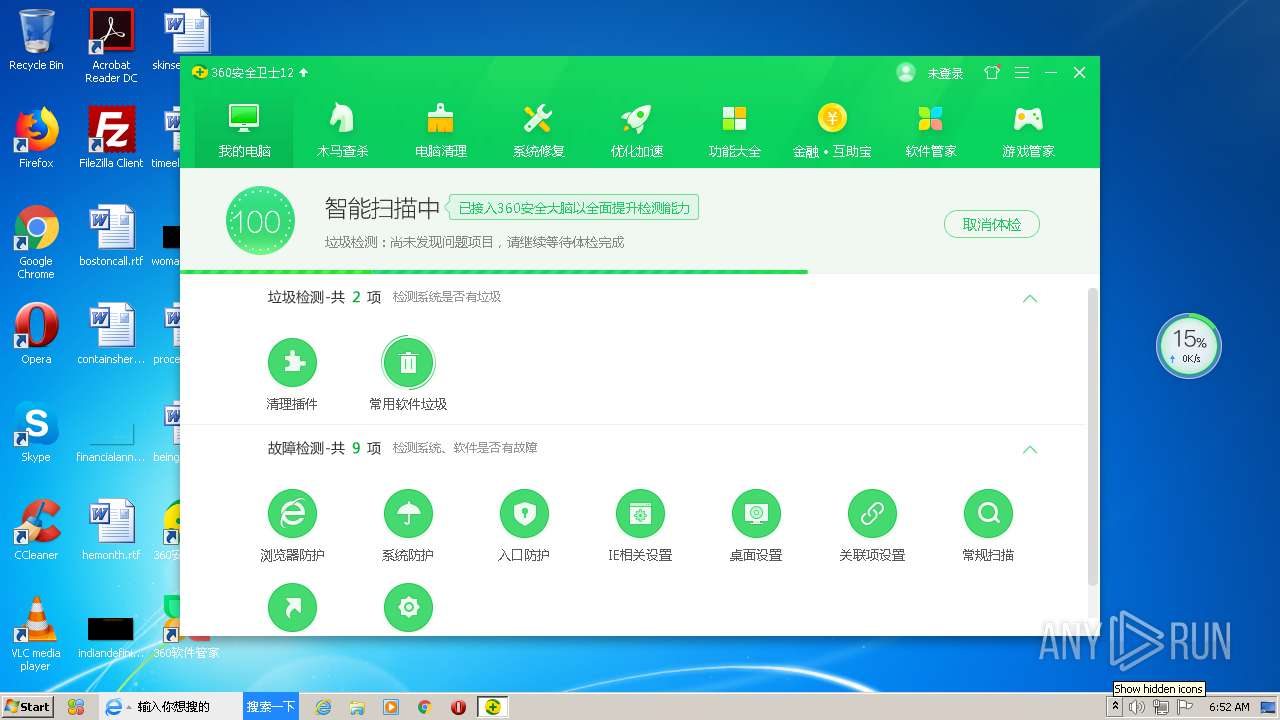
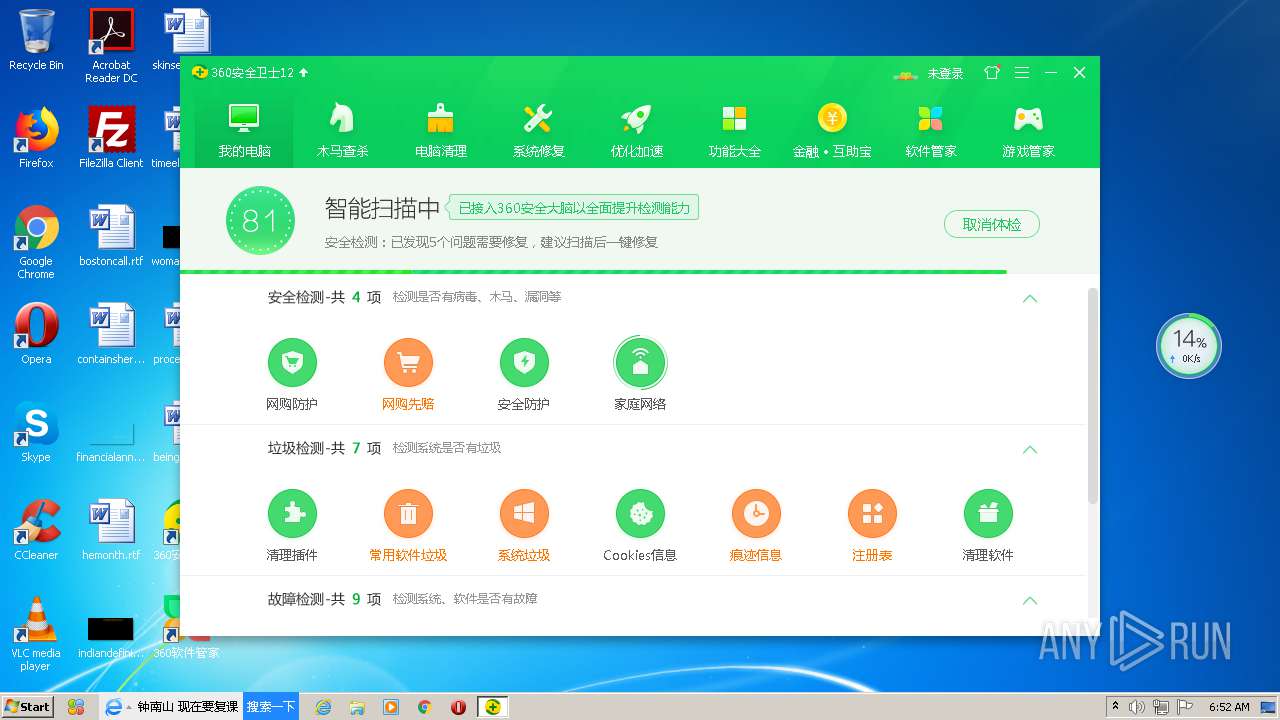
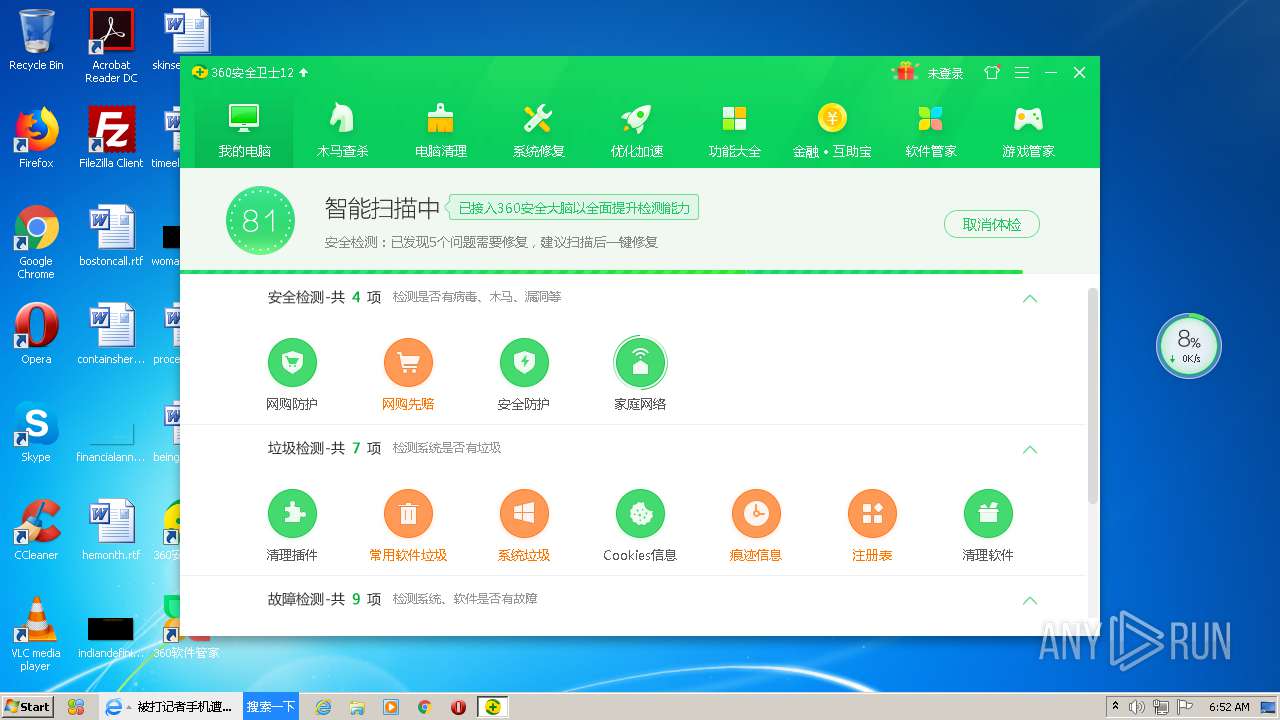
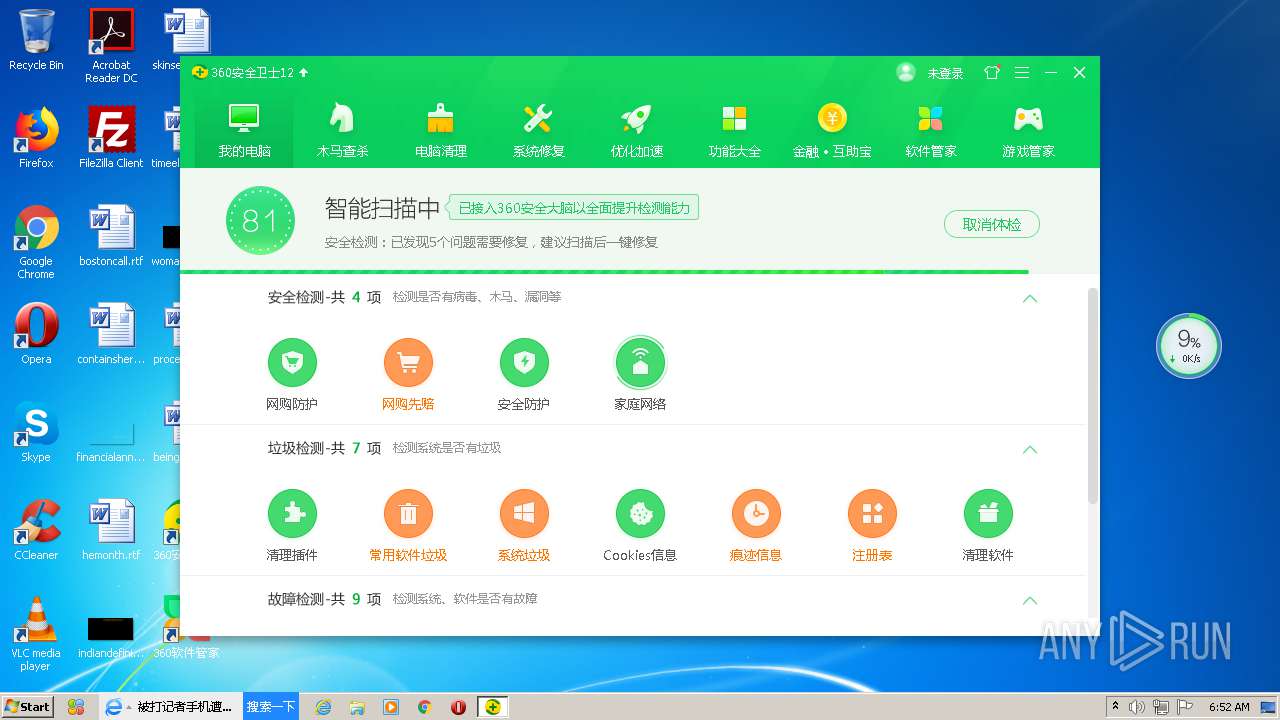
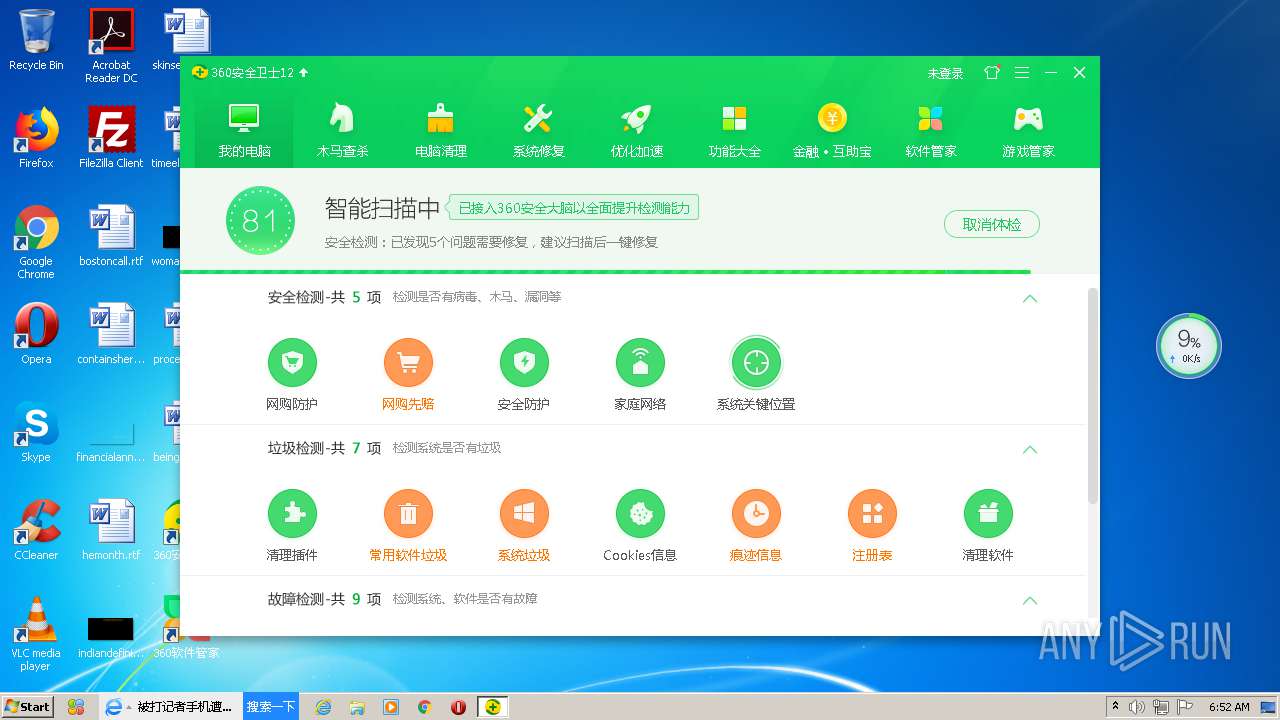
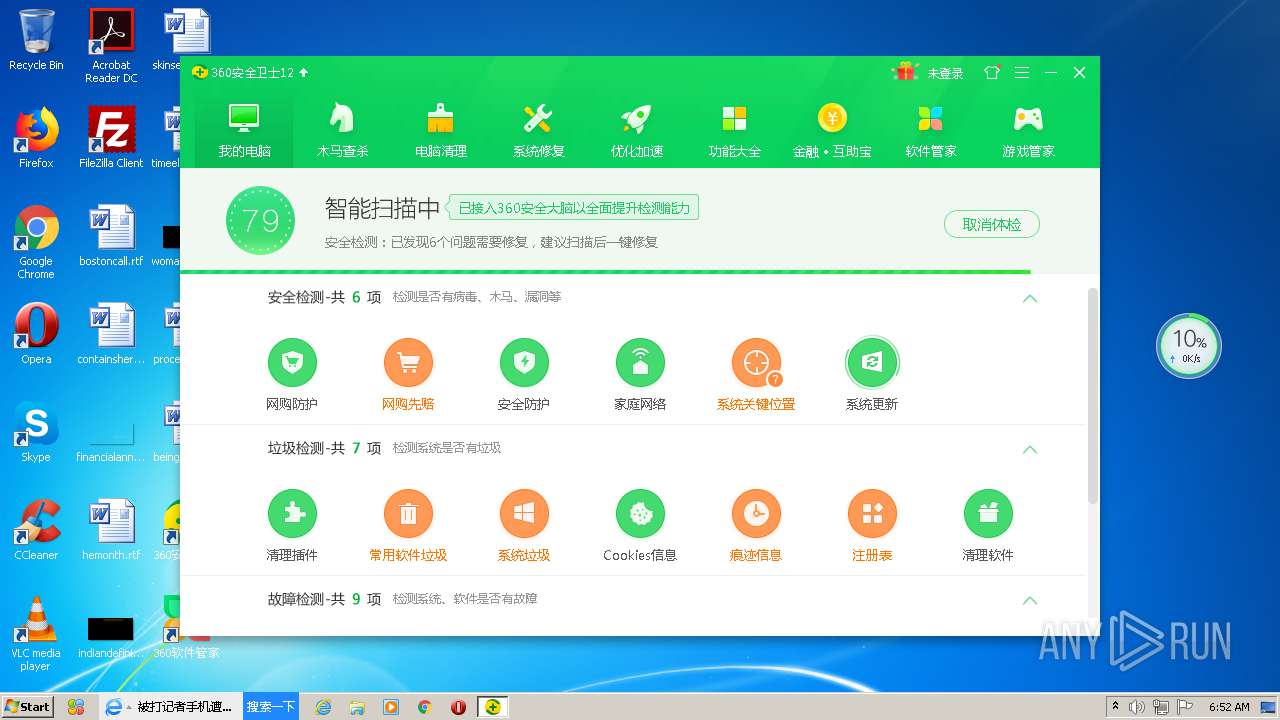
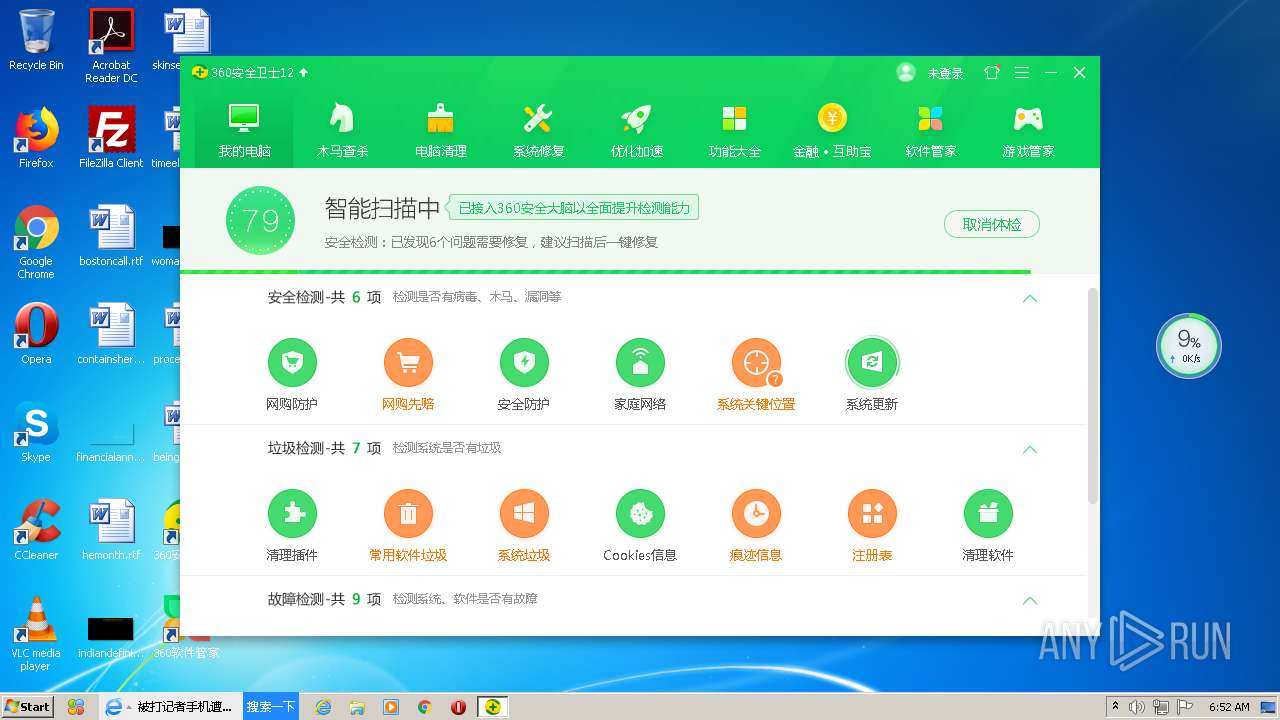
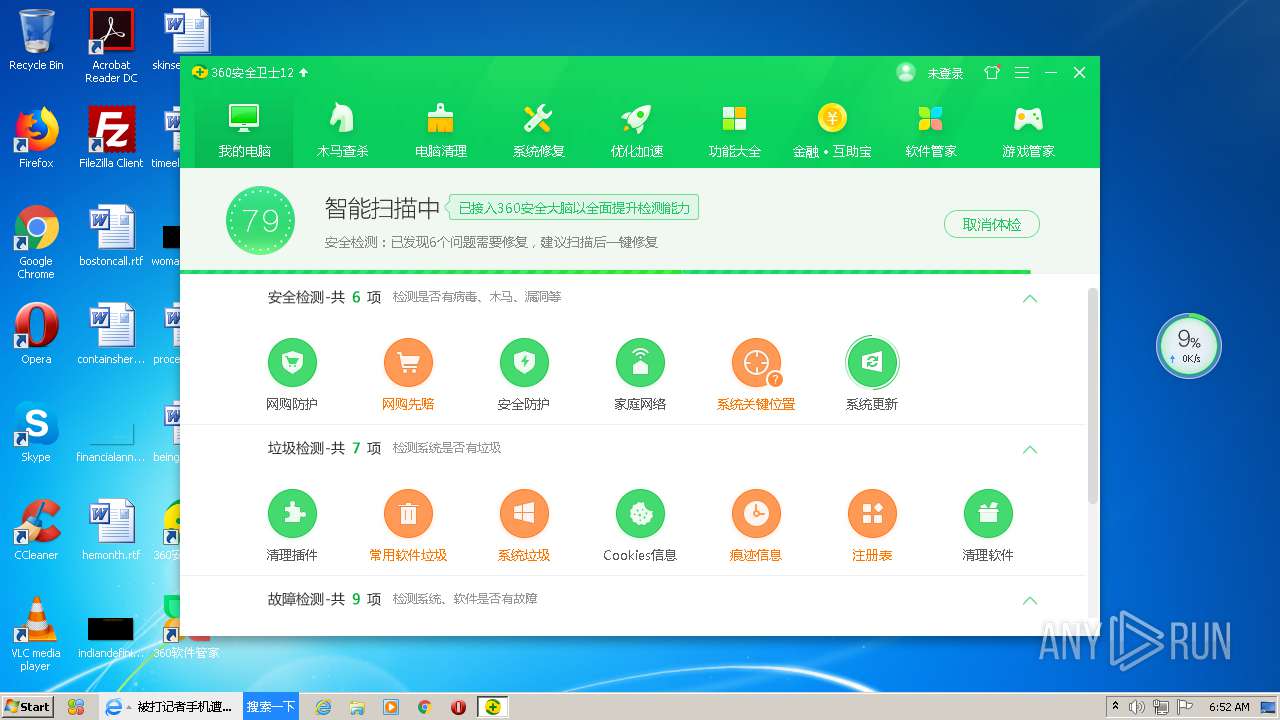
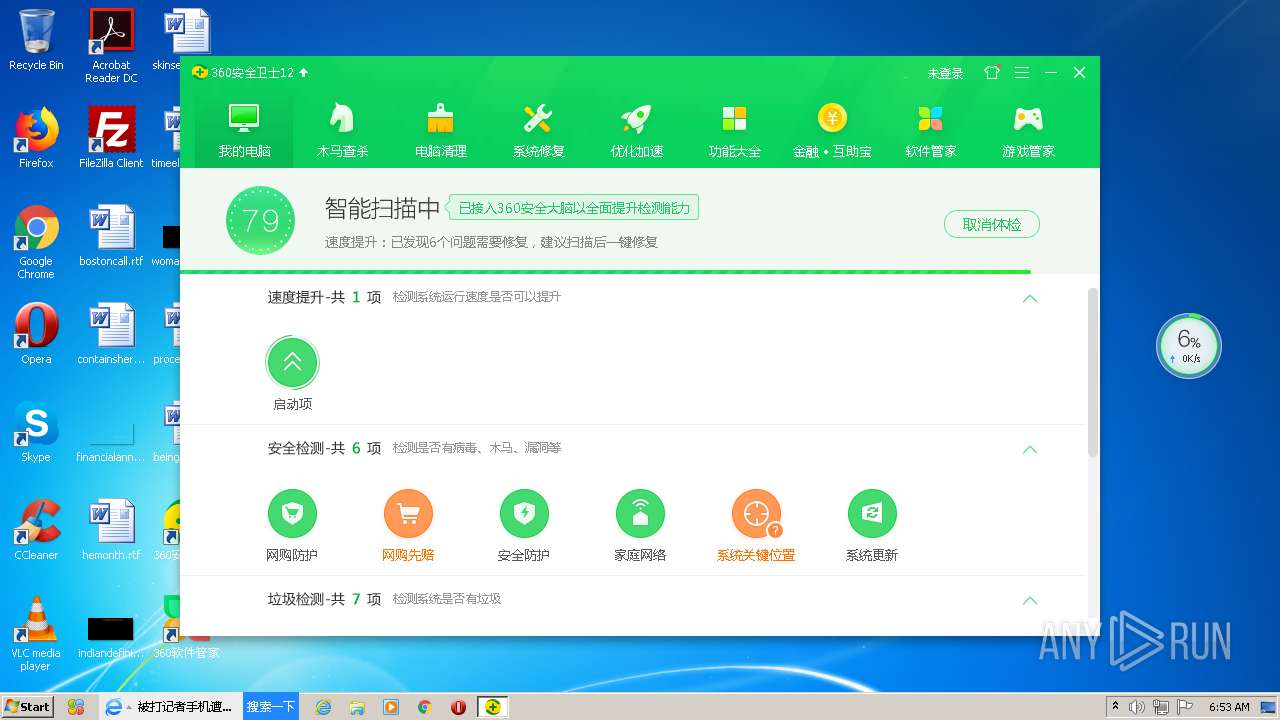
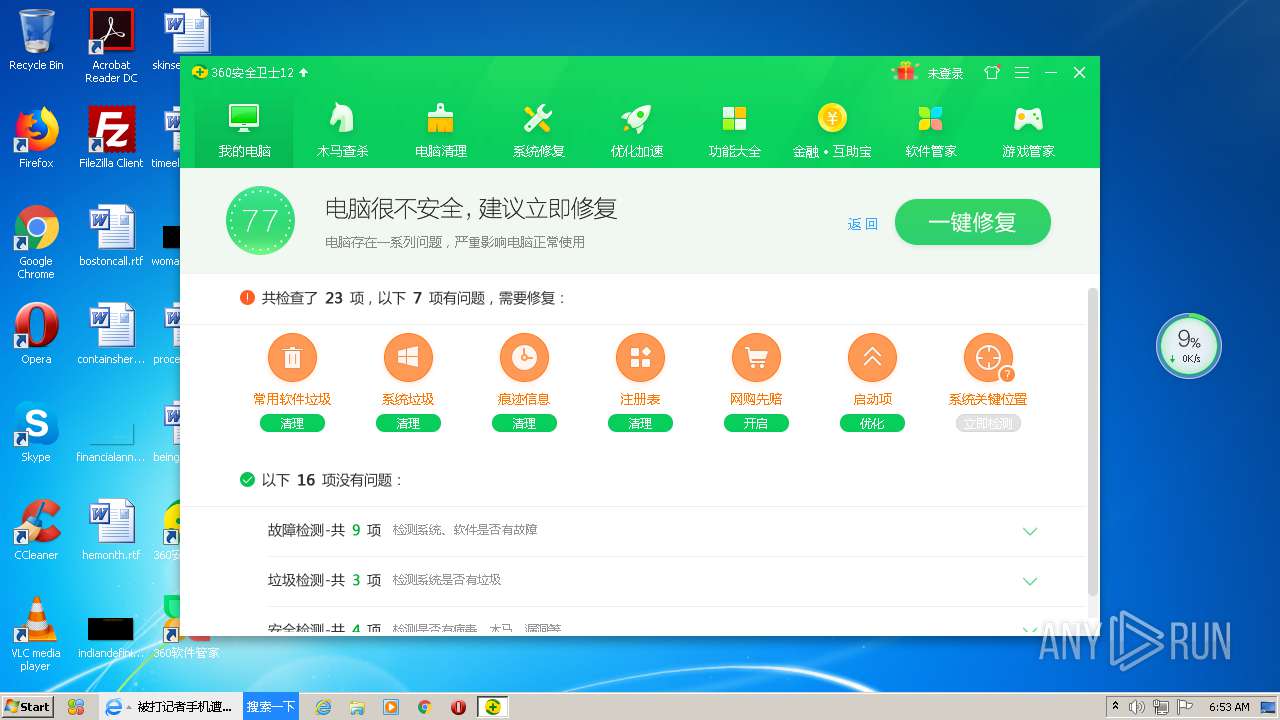
MALICIOUS
Actions looks like stealing of personal data
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- explorer.exe (PID: 468)
- 360tray.exe (PID: 3712)
- 360safe.exe (PID: 3644)
- SoftMgrLite.exe (PID: 3244)
Loads dropped or rewritten executable
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360safe.exe (PID: 3644)
- 360entcall.exe (PID: 4092)
- 360tray.exe (PID: 3712)
- 360UHelper.exe (PID: 3580)
- 360leakfixer.exe (PID: 3048)
- zhudongfangyu.exe (PID: 2920)
- explorer.exe (PID: 468)
- LiveUpdate360.exe (PID: 3960)
- PowerSaver.exe (PID: 2060)
- SoftupNotify.exe (PID: 3180)
- 360SecLogonHelper.exe (PID: 3768)
- zhudongfangyu.exe (PID: 3172)
- PopWndTracker.exe (PID: 3892)
- zhudongfangyu.exe (PID: 2856)
- 360IA.exe (PID: 3276)
- SoftMgrLite.exe (PID: 3244)
- regsvr32.exe (PID: 2156)
- regsvr32.exe (PID: 2572)
- services.exe (PID: 480)
- 360DeskAna.exe (PID: 3696)
- svchost.exe (PID: 868)
- 360DeskAna.exe (PID: 3132)
- 360DayPop.exe (PID: 2692)
- 360IA.exe (PID: 3916)
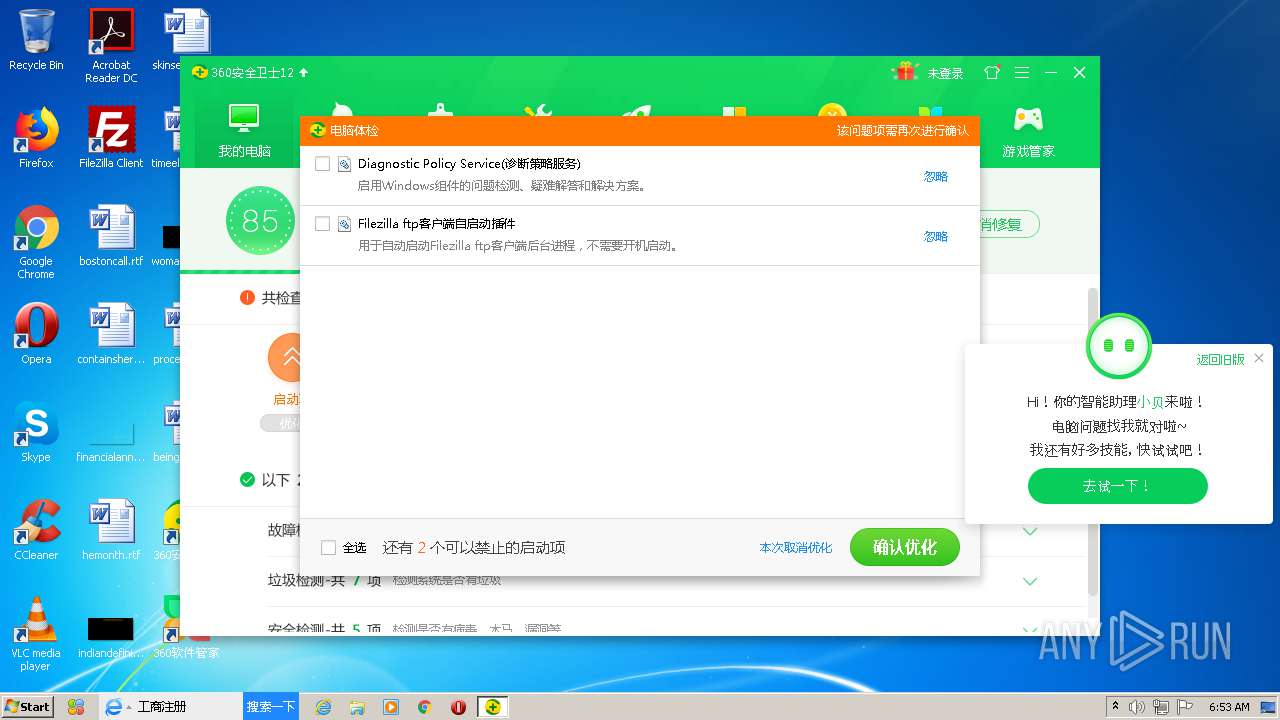
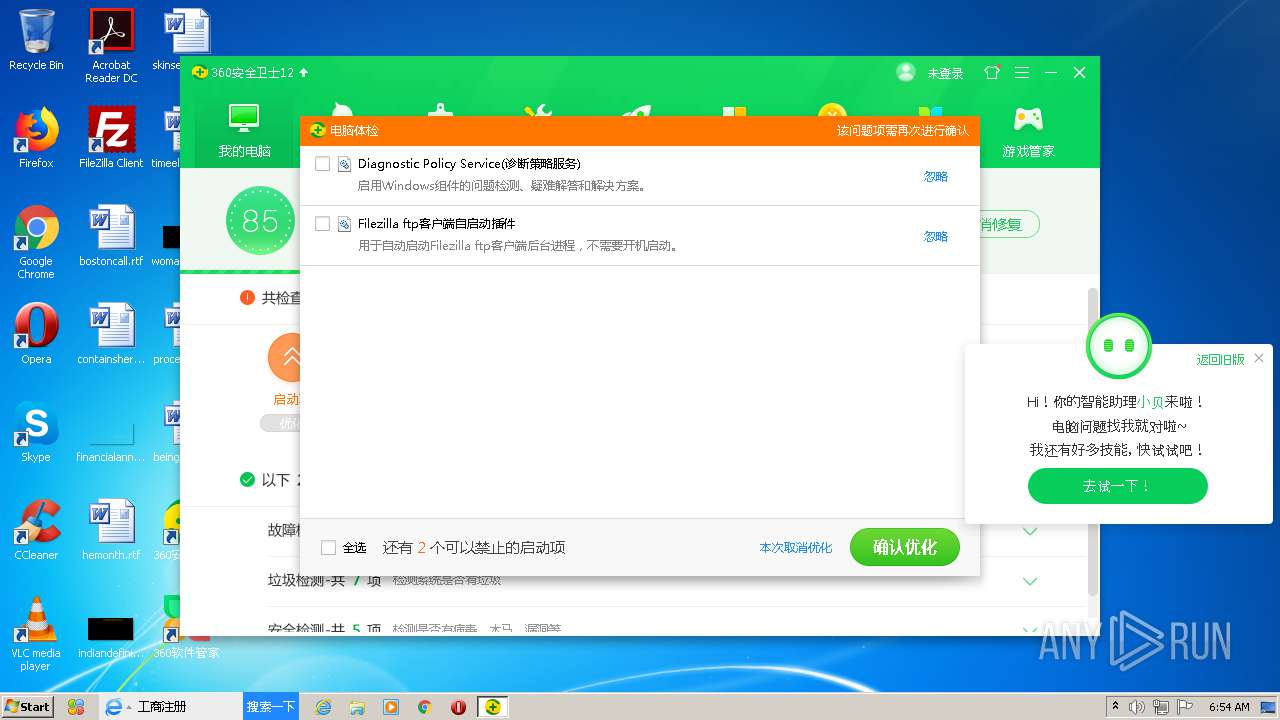
Changes the autorun value in the registry
- setup_12.0.0.2002y.exe (PID: 3424)
Changes settings of System certificates
- PowerSaver.exe (PID: 2060)
- 360UHelper.exe (PID: 3580)
- inst.exe (PID: 4060)
- 360safe.exe (PID: 3644)
- 360tray.exe (PID: 3712)
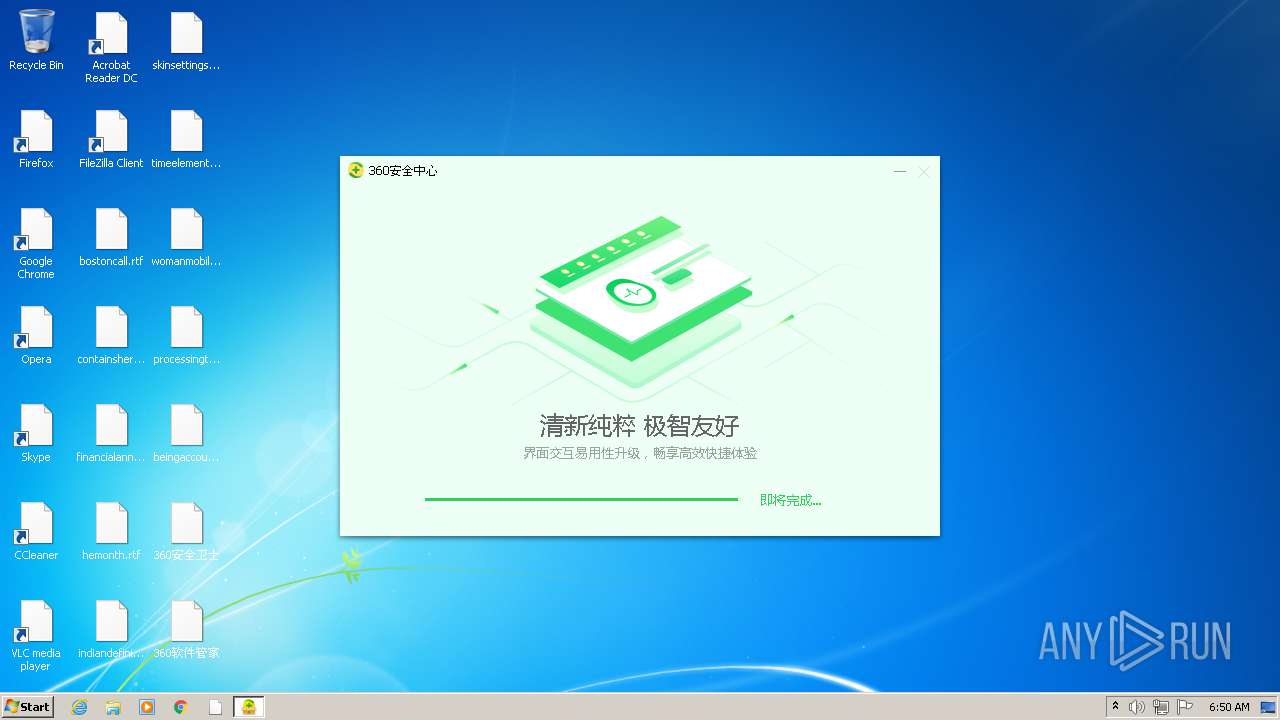
Application was dropped or rewritten from another process
- 360tray.exe (PID: 3712)
- 360safe.exe (PID: 3644)
- 360entcall.exe (PID: 4092)
- SoftupNotify.exe (PID: 3180)
- 360SecLogonHelper.exe (PID: 3768)
- 360UHelper.exe (PID: 3580)
- 360leakfixer.exe (PID: 3048)
- PowerSaver.exe (PID: 2060)
- PopWndTracker.exe (PID: 3892)
- PowerSaver.exe (PID: 2436)
- LiveUpdate360.exe (PID: 3960)
- zhudongfangyu.exe (PID: 2856)
- zhudongfangyu.exe (PID: 3172)
- zhudongfangyu.exe (PID: 2920)
- 360IA.exe (PID: 3276)
- SoftMgrLite.exe (PID: 3244)
- WscReg.exe (PID: 2296)
- 360DeskAna.exe (PID: 3696)
- svchost.exe (PID: 868)
- 360DeskAna.exe (PID: 3132)
- 360DayPop.exe (PID: 2692)
- 360PatchMgr.exe (PID: 3640)
- 360PatchMgr.exe (PID: 2452)
- 360PatchMgr.exe (PID: 1480)
- 360PatchMgr.exe (PID: 2812)
- svchost.exe (PID: 3600)
- 360IA.exe (PID: 3916)
- SimpleIME.exe (PID: 4040)
Runs injected code in another process
- SoftupNotify.exe (PID: 3180)
Application was injected by another process
- explorer.exe (PID: 468)
Registers / Runs the DLL via REGSVR32.EXE
- SoftupNotify.exe (PID: 3180)
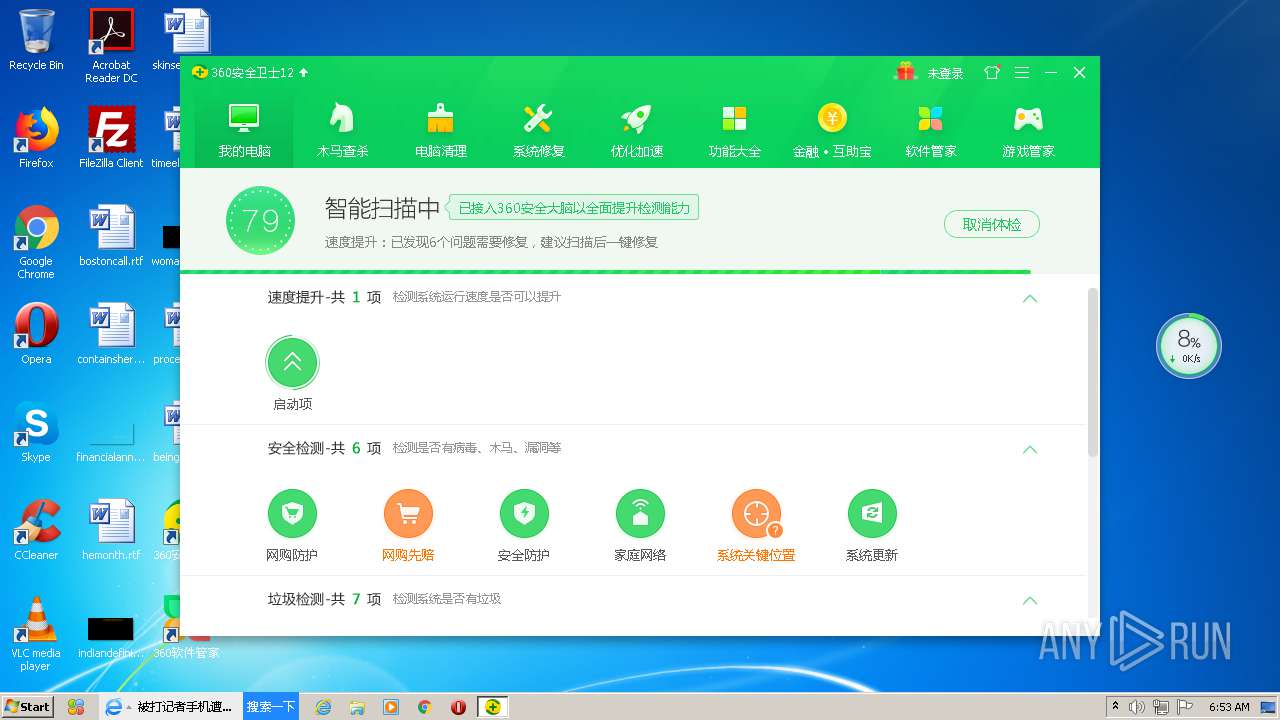
Changes Windows auto-update feature
- 360safe.exe (PID: 3644)
Disables Windows Defender
- 360safe.exe (PID: 3644)
Loads the Task Scheduler COM API
- 360safe.exe (PID: 3644)
Loads the Task Scheduler DLL interface
- 360safe.exe (PID: 3644)
SUSPICIOUS
Low-level read access rights to disk partition
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360SecLogonHelper.exe (PID: 3768)
- 360tray.exe (PID: 3712)
- 360safe.exe (PID: 3644)
- 360leakfixer.exe (PID: 3048)
- SoftMgrLite.exe (PID: 3244)
- 360IA.exe (PID: 3916)
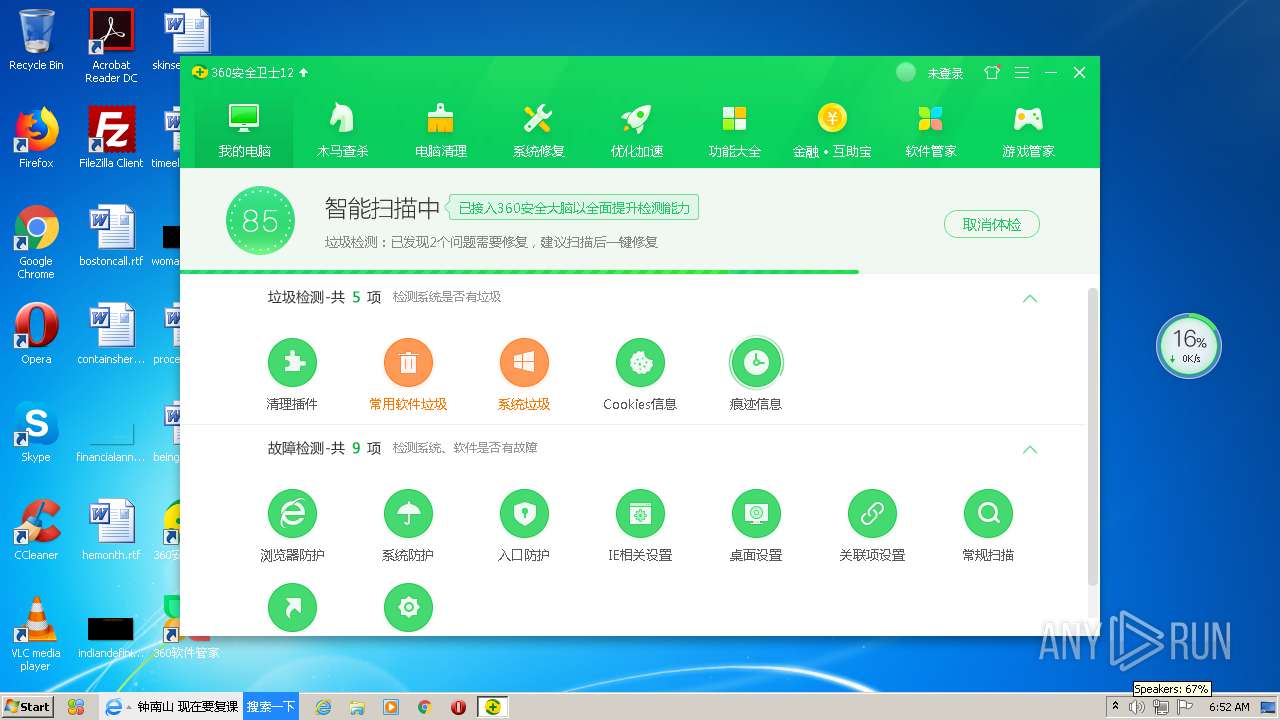
Reads Internet Cache Settings
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360safe.exe (PID: 3644)
- 360tray.exe (PID: 3712)
Executable content was dropped or overwritten
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360safe.exe (PID: 3644)
- 360tray.exe (PID: 3712)
Creates files in the program directory
- inst.exe (PID: 4060)
- PopWndTracker.exe (PID: 3892)
- 360entcall.exe (PID: 4092)
- zhudongfangyu.exe (PID: 2920)
- SoftupNotify.exe (PID: 3180)
- LiveUpdate360.exe (PID: 3960)
- 360safe.exe (PID: 3644)
- 360UHelper.exe (PID: 3580)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
- SoftMgrLite.exe (PID: 3244)
Creates files in the user directory
- setup_12.0.0.2002y.exe (PID: 3424)
- 360safe.exe (PID: 3644)
- explorer.exe (PID: 468)
- LiveUpdate360.exe (PID: 3960)
- SoftupNotify.exe (PID: 3180)
- 360tray.exe (PID: 3712)
- SoftMgrLite.exe (PID: 3244)
- SimpleIME.exe (PID: 4040)
Writes to a desktop.ini file (may be used to cloak folders)
- setup_12.0.0.2002y.exe (PID: 3424)
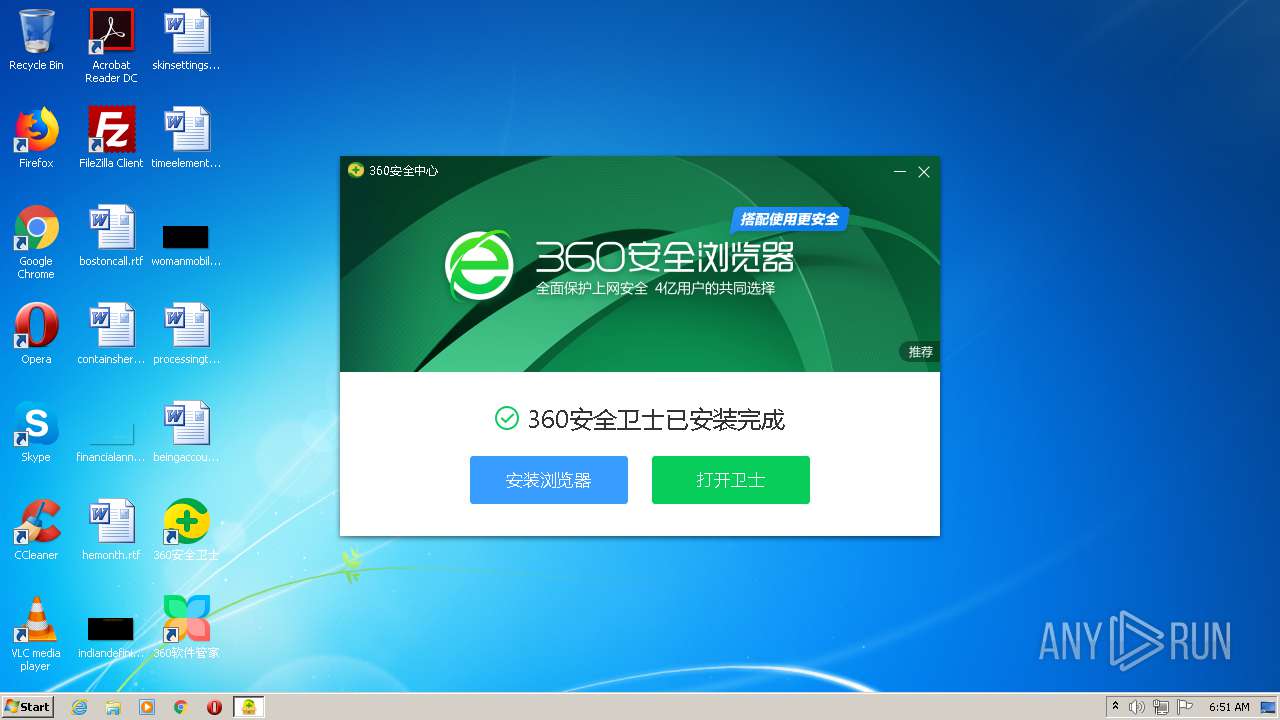
Creates a software uninstall entry
- setup_12.0.0.2002y.exe (PID: 3424)
Creates files in the driver directory
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
Creates files in the Windows directory
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
- TrustedInstaller.exe (PID: 3716)
- 360safe.exe (PID: 3644)
Creates or modifies windows services
- services.exe (PID: 480)
- setup_12.0.0.2002y.exe (PID: 3424)
- zhudongfangyu.exe (PID: 3172)
- zhudongfangyu.exe (PID: 2920)
- 360tray.exe (PID: 3712)
Creates COM task schedule object
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
- regsvr32.exe (PID: 2572)
- regsvr32.exe (PID: 2156)
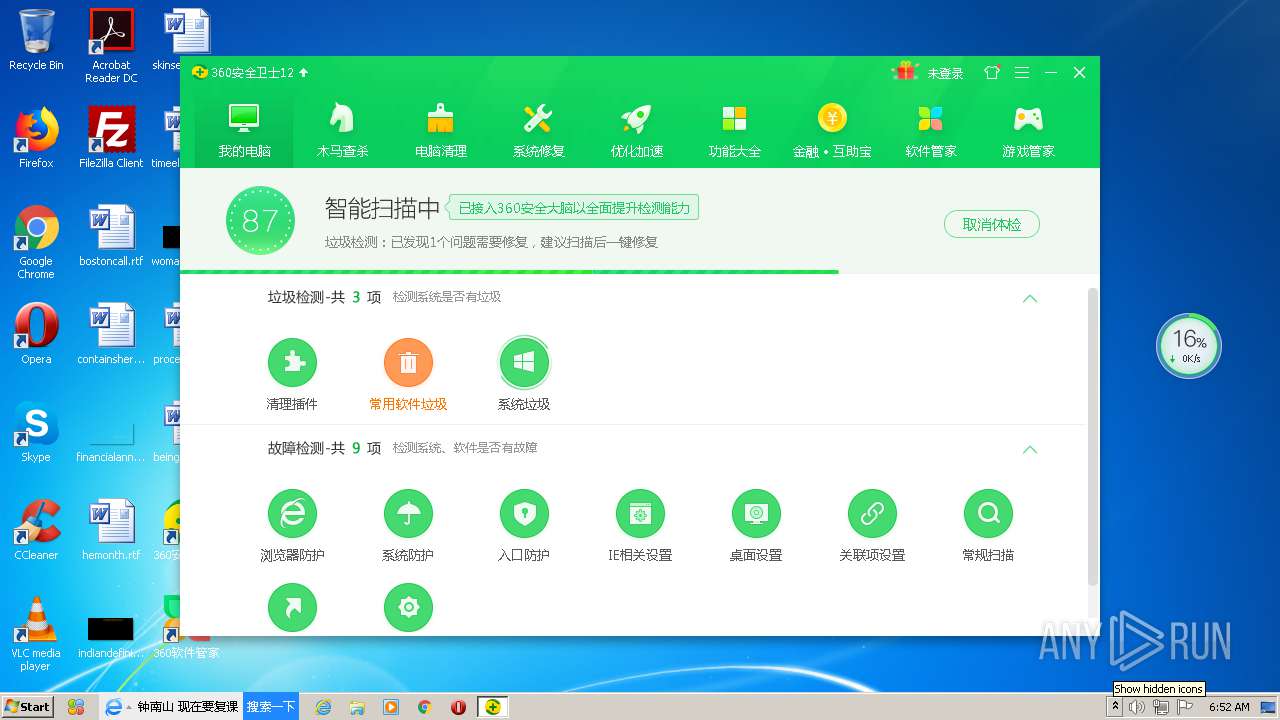
Reads the cookies of Google Chrome
- setup_12.0.0.2002y.exe (PID: 3424)
- 360safe.exe (PID: 3644)
Executed as Windows Service
- zhudongfangyu.exe (PID: 2920)
Modifies the open verb of a shell class
- setup_12.0.0.2002y.exe (PID: 3424)
- SoftupNotify.exe (PID: 3180)
Adds / modifies Windows certificates
- 360UHelper.exe (PID: 3580)
- inst.exe (PID: 4060)
- 360safe.exe (PID: 3644)
- 360tray.exe (PID: 3712)
Reads the BIOS version
- 360tray.exe (PID: 3712)
Searches for installed software
- 360tray.exe (PID: 3712)
- 360safe.exe (PID: 3644)
Removes files from Windows directory
- 360safe.exe (PID: 3644)
INFO
Reads settings of System Certificates
- inst.exe (PID: 4060)
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
Dropped object may contain TOR URL's
- setup_12.0.0.2002y.exe (PID: 3424)
Dropped object may contain Bitcoin addresses
- setup_12.0.0.2002y.exe (PID: 3424)
- 360tray.exe (PID: 3712)
- 360safe.exe (PID: 3644)
Reads the hosts file
- 360safe.exe (PID: 3644)
Reads Microsoft Office registry keys
- 360safe.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:26 10:58:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 734720 |
| InitializedDataSize: | 4542464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x87154 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.0.0.1131 |
| ProductVersionNumber: | 12.0.0.1131 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Neutral 2 |
| CharacterSet: | Unicode |
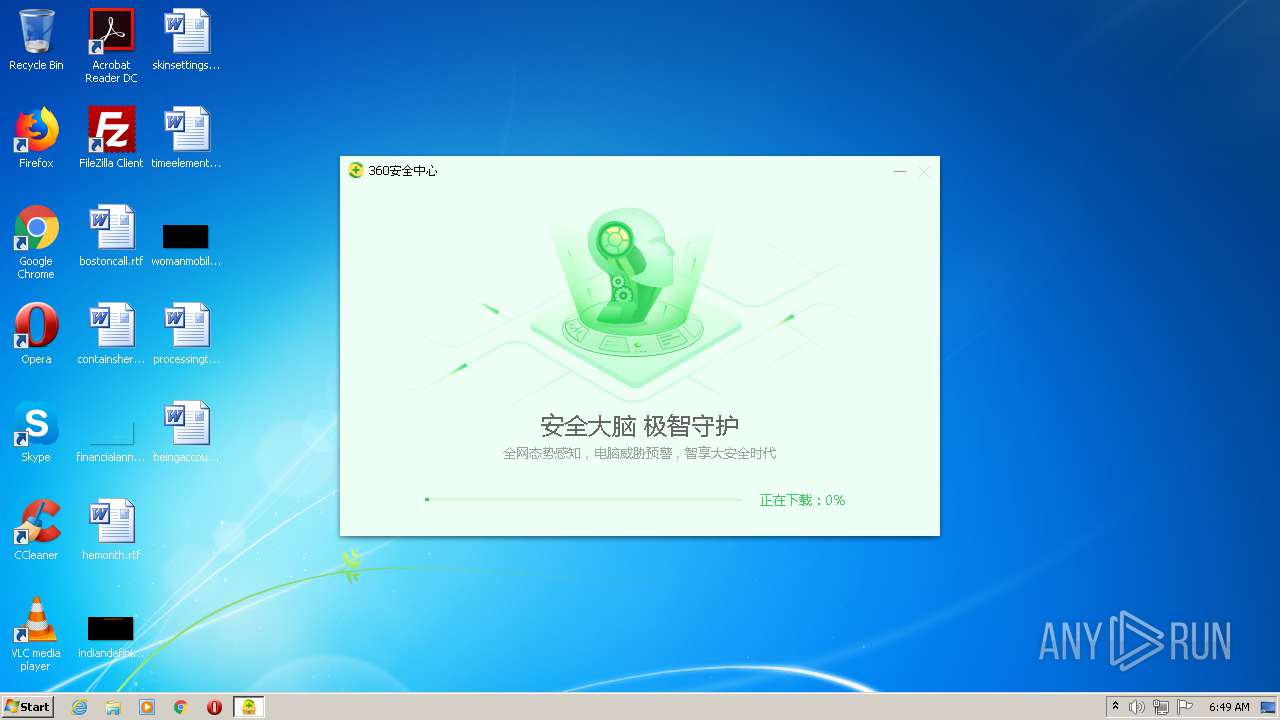
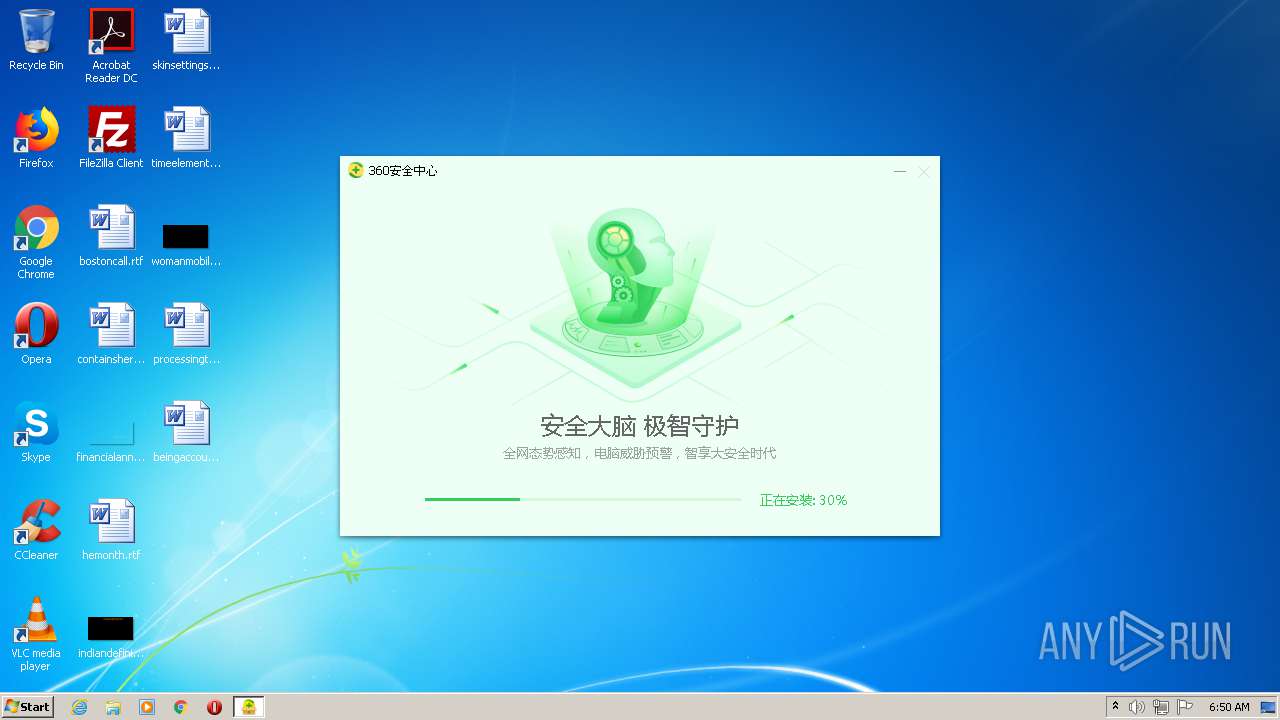
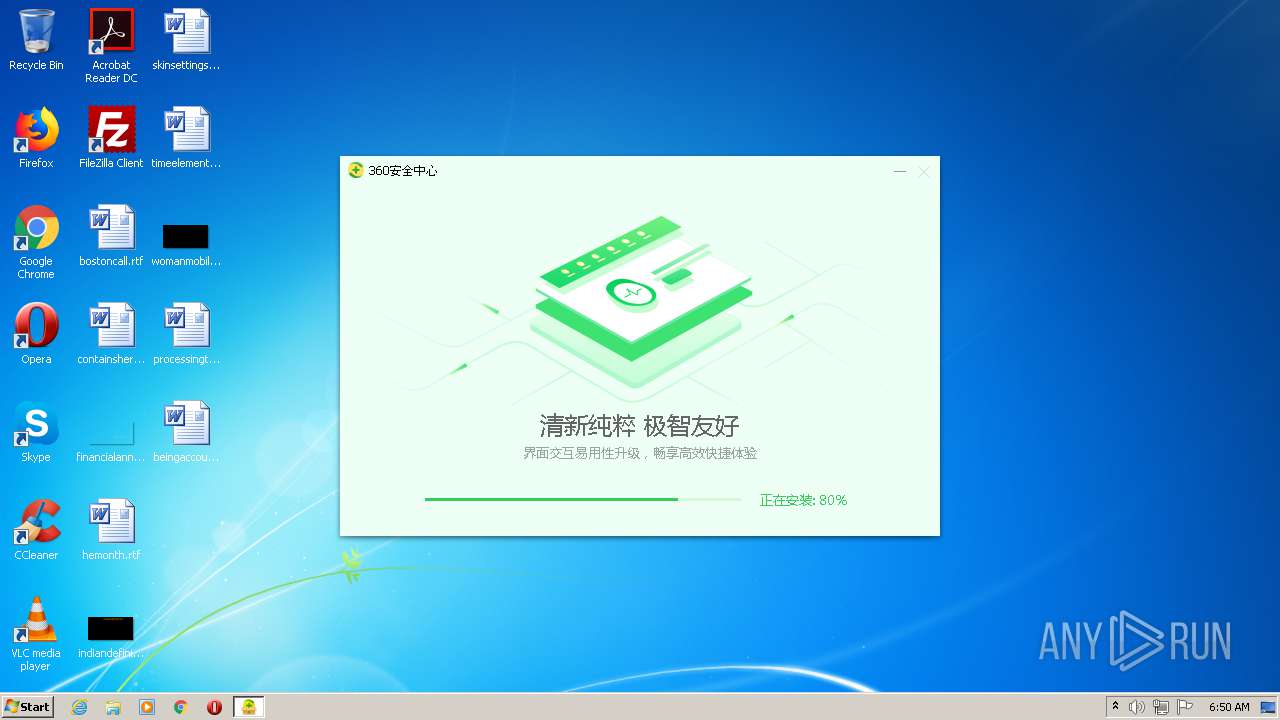
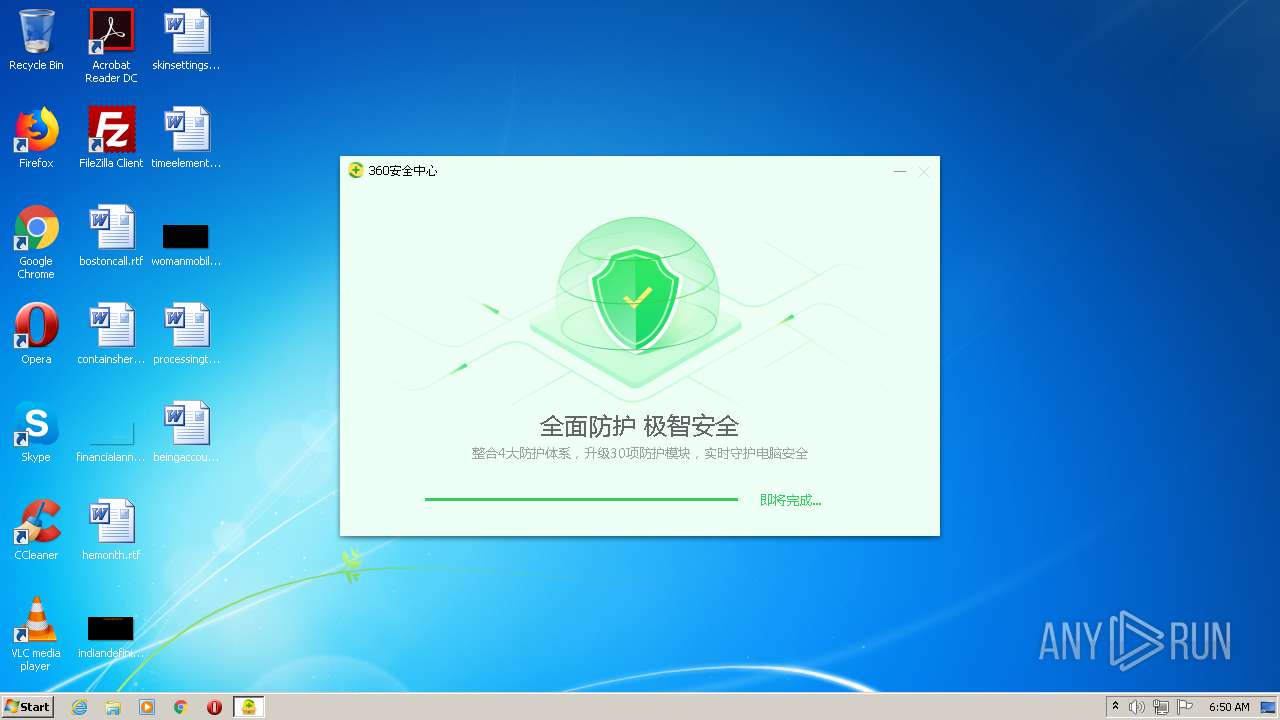
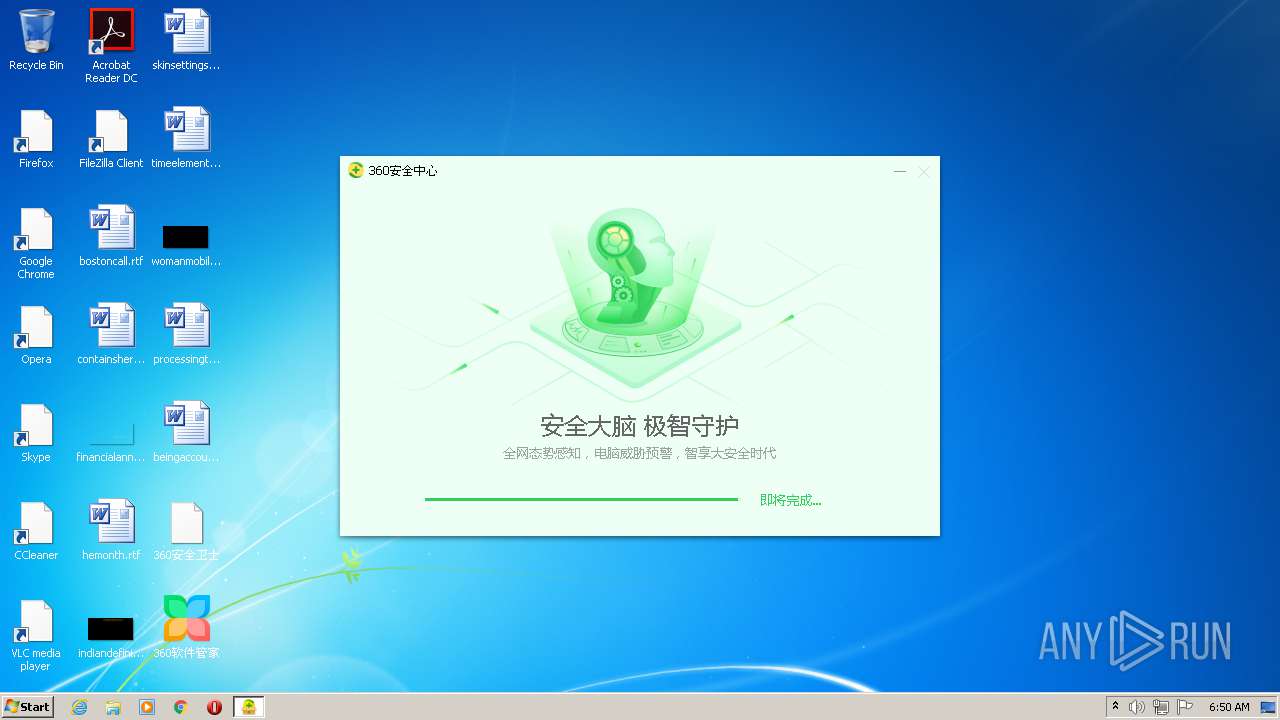
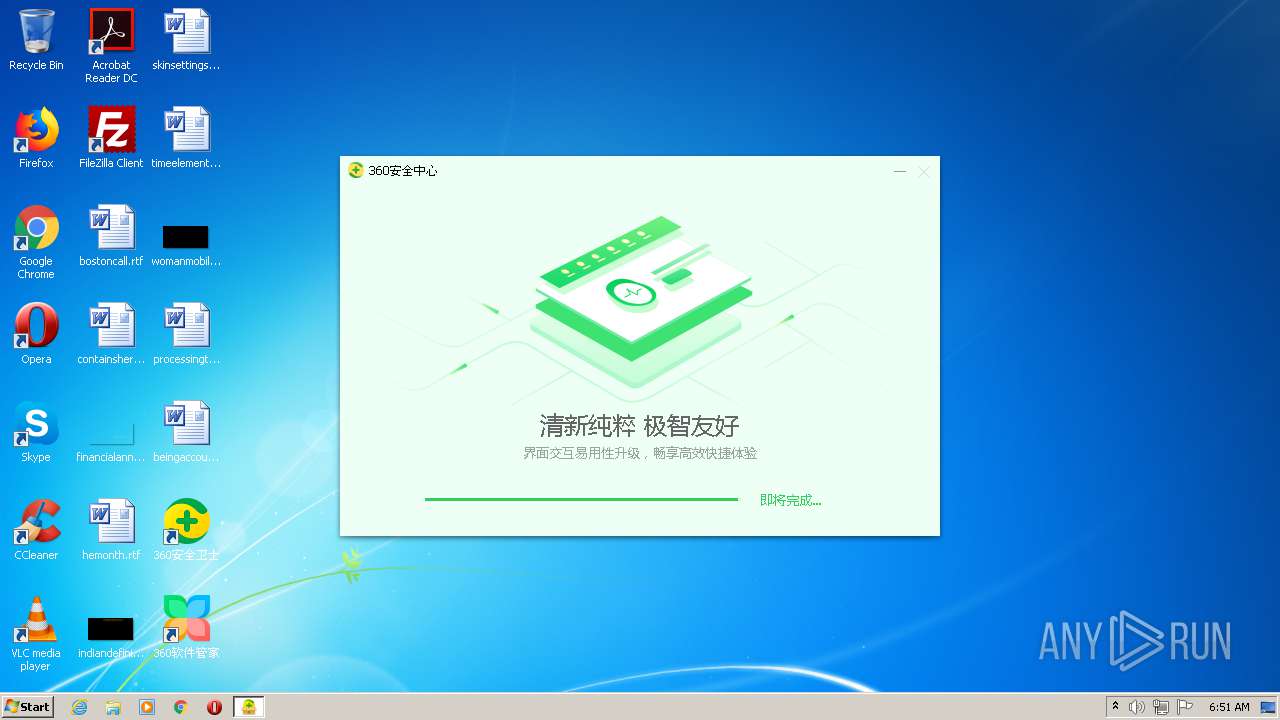
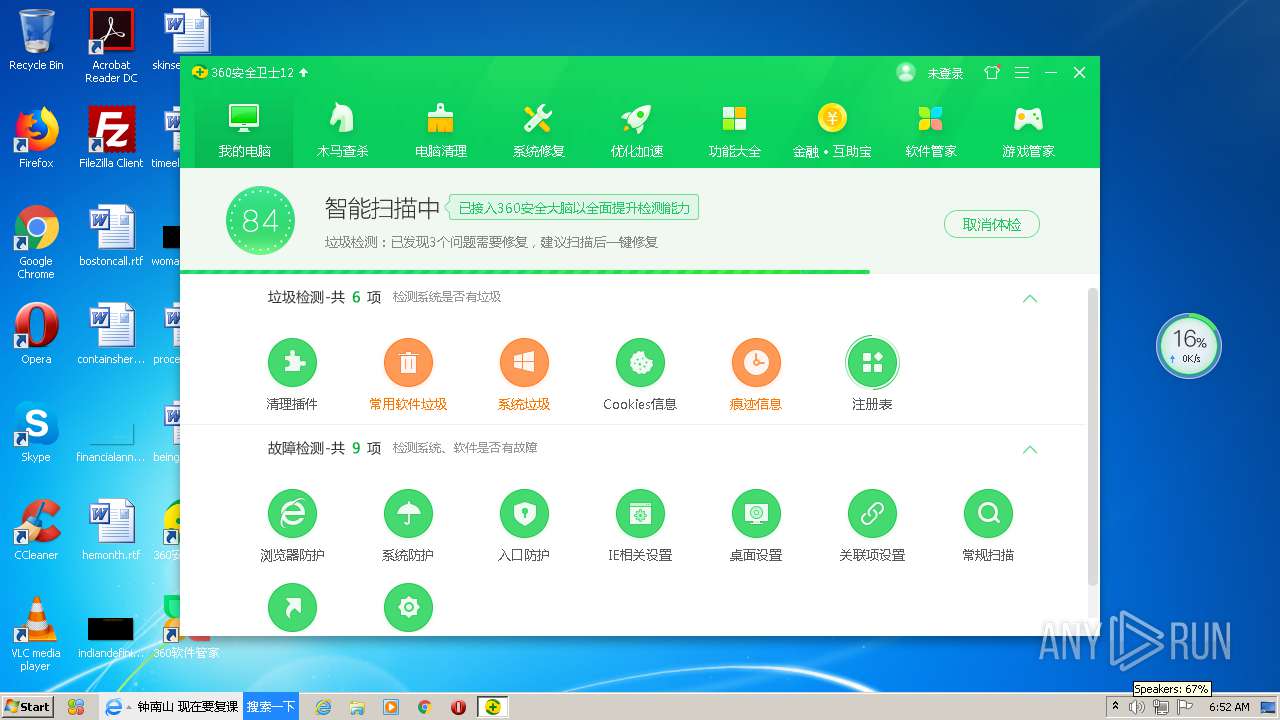
| CompanyName: | 360.cn |
| FileDescription: | 360 安全卫士在线安装程序 |
| FileVersion: | 12, 0, 0, 1131 |
| InternalName: | 360 Installer |
| LegalCopyright: | Copyright 2012 |
| OriginalFileName: | 360Installer.exe |
| ProductName: | 360 安全卫士在线安装程序 |
| ProductVersion: | 12, 0, 0, 1131 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Feb-2020 09:58:54 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | 360.cn |
| FileDescription: | 360 安全卫士在线安装程序 |
| FileVersion: | 12, 0, 0, 1131 |
| InternalName: | 360 Installer |
| LegalCopyright: | Copyright 2012 |
| OriginalFilename: | 360Installer.exe |
| ProductName: | 360 安全卫士在线安装程序 |
| ProductVersion: | 12, 0, 0, 1131 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Feb-2020 09:58:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B3485 | 0x000B3600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64805 |
.rdata | 0x000B5000 | 0x0002142E | 0x00021600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.72352 |
.data | 0x000D7000 | 0x0000CD6C | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29476 |
.rsrc | 0x000E4000 | 0x0041E520 | 0x0041E604 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94873 |
.reloc | 0x00503000 | 0x0000C19C | 0x0000C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.7953 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26275 | 1064 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.56733 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.60391 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.16294 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.70608 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 5.80041 | 512 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.80669 | 656 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
11 | 5.86822 | 558 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
12 | 6.37095 | 658 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
13 | 6.15143 | 578 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SETUPAPI.dll |
SHELL32.dll |
Total processes
73
Monitored processes
36
Malicious processes
19
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | "C:\Program Files\360\360Safe\modules\360PatchMgr.exe" /IsBusy | C:\Program Files\360\360Safe\modules\360PatchMgr.exe | — | 360safe.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士 漏洞补丁安装模块 Exit code: 0 Version: 1.0.0.1270 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\360\360Safe\Utils\PowerSaver.exe" /flightsigning | C:\Program Files\360\360Safe\Utils\PowerSaver.exe | — | setup_12.0.0.2002y.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士卸载清理模块 Exit code: 0 Version: 11.0.0.1081 Modules
| |||||||||||||||
| 2156 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\360\360Safe\SoftMgr\SMWebProxy.dll" | C:\Windows\system32\regsvr32.exe | — | SoftupNotify.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\360\360Safe\safemon\WscReg.exe" /install | C:\Program Files\360\360Safe\safemon\WscReg.exe | — | 360tray.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士 安全中心接口 Exit code: 0 Version: 10, 0, 0, 8091 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\360\360Safe\Utils\PowerSaver.exe" /HImmu | C:\Program Files\360\360Safe\Utils\PowerSaver.exe | — | setup_12.0.0.2002y.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士卸载清理模块 Exit code: 0 Version: 11.0.0.1081 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\360\360Safe\modules\360PatchMgr.exe" -Embedding5 Global\WusEvent_e3c_2763699d-f5fa-4e4e-9837-0ba1d25f722a E3C "C:\Program Files\360\360Safe\libleak2.dat" | C:\Program Files\360\360Safe\modules\360PatchMgr.exe | — | 360safe.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士 漏洞补丁安装模块 Exit code: 2147942402 Version: 1.0.0.1270 Modules
| |||||||||||||||
| 2572 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\360\360Safe\SoftMgr\SoftMgrExt.dll" | C:\Windows\system32\regsvr32.exe | SoftupNotify.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 635
Read events
7 060
Write events
10 092
Delete events
483
Modification events
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\Liveup |
| Operation: | write | Name: | mid |
Value: cfe1ce9b8f5123cc37f394accff90c49e593c1ef62585eeea14b615c6b4efcbe | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\{06726E98-A6E0-4d36-9215-211EB96C7DC1}.tmp\360P2SP.dll | |||
| (PID) Process: | (4060) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\LiveUpdate360 |
| Operation: | write | Name: | proxytype |
Value: 1 | |||
Executable files
1 018
Suspicious files
1 279
Text files
1 619
Unknown types
128
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\{6135DCA1-731E-45c4-ABC4-3C5FCCD7C901}.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\{599CB543-F764-4c53-8175-11BB30183D0B}.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Program Files\360\360Safe\{113E3DAD-1CF8-47c5-AF5C-E1D3E947366A}.tf | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\{A44B7723-4283-41b8-B9C0-6B1983C61382}.tmp\themes\NewInstallAir\NewInstallAir.ui | compressed | |
MD5:94E390B6ED7BAD362FA1E0416AB856E7 | SHA256:6CEA90E144A6D30823ACEB210D740E5C17372EC94F50C33F70B04E6C06030AF0 | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\Cab1BC5.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\Tar1BC6.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\{EEA394B2-7B9F-4c98-A650-CAE72A551D34}.tmp | image | |
MD5:5A11C0D0FF95E7A8810B87571EE552D6 | SHA256:8E1E9F7615039D166F777449ACE1B9752F5376F9CDDD589AD29E6DC5A58B38F5 | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tFAED.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tFAED.tmp.dir\setup.ini | — | |
MD5:— | SHA256:— | |||
| 4060 | inst.exe | C:\Users\admin\AppData\Local\Temp\setup_12.0.0.2002y.exe.P2P | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
116
TCP/UDP connections
78
DNS requests
23
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | inst.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEAXtiNgIjRHr3dYjljy67UI%3D | US | der | 1.62 Kb | whitelisted |
4060 | inst.exe | GET | 200 | 151.139.236.246:80 | http://wotrus-ovca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROB68uPCabixs381BzpJxWVlED2AQUasBJGVKf6gFeRQyx8A9%2BoF9tj%2BUCEFMH%2F07n%2FYI5jPITy5bv%2Fds%3D | US | der | 1.47 Kb | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=425&status=6&mid=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&ver=12.0.0.1131&vv=10&appkey=&usetime=0&downrate=0&downlen=0 | CN | — | — | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=425&status=14&mid=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&ver=12.0.0.1131&vv=10&appkey=&usetime=0&downrate=0&downlen=0 | CN | — | — | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=10&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=12.0.0.1131 | CN | — | — | whitelisted |
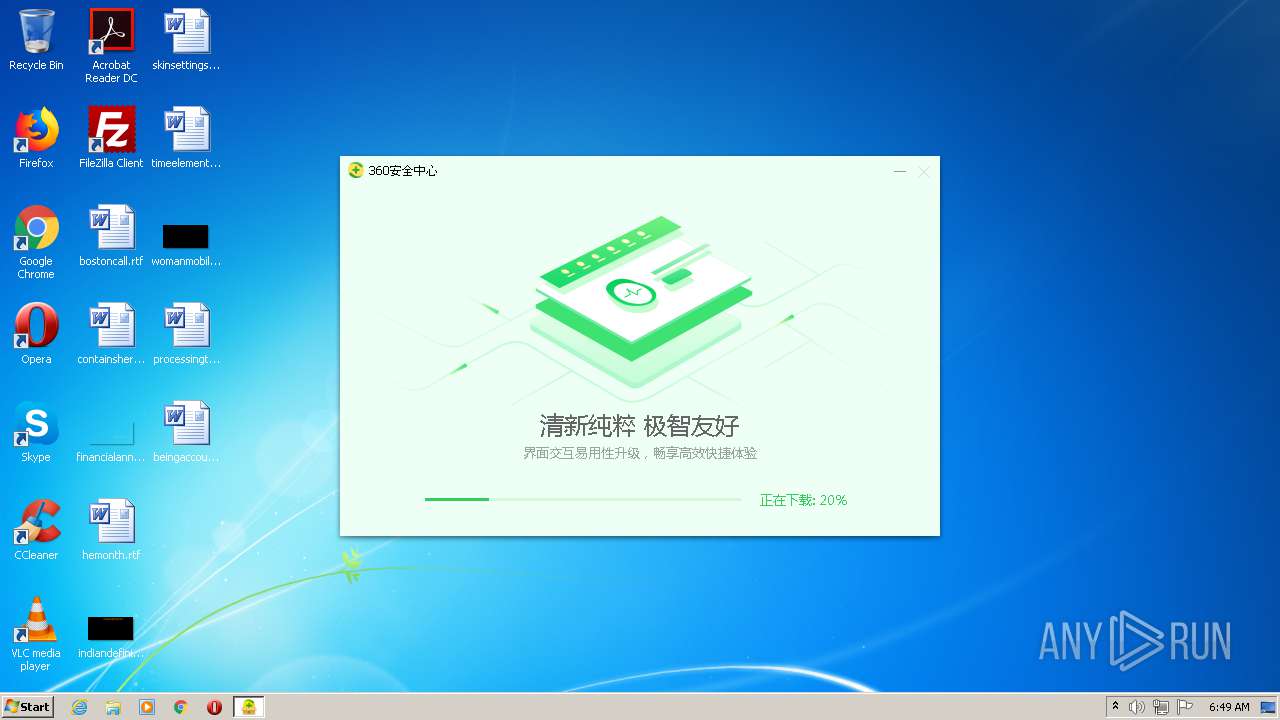
4060 | inst.exe | GET | — | 104.192.108.18:80 | http://dl.360safe.com/setup_12.0.0.2002y.exe | US | — | — | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=129&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&installed=0&ver=12.0.0.1131 | CN | — | — | whitelisted |
4060 | inst.exe | GET | — | 104.192.108.17:80 | http://dl.360safe.com/setup_12.0.0.2002y.exe | US | — | — | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=127&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&installed=0&parent=explorer.exe&ver=12.0.0.1131 | CN | — | — | whitelisted |
4060 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=1&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=12.0.0.1131 | CN | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4060 | inst.exe | 171.8.167.89:80 | s.360.cn | No.31,Jin-rong Street | CN | suspicious |
4060 | inst.exe | 1.192.136.136:3478 | st.p.360.cn | No.31,Jin-rong Street | CN | unknown |
— | — | 1.192.136.137:3478 | — | No.31,Jin-rong Street | CN | unknown |
— | — | 185.212.170.83:29895 | — | M247 Ltd | CH | unknown |
4060 | inst.exe | 1.192.136.132:80 | tr.p.360.cn | No.31,Jin-rong Street | CN | unknown |
4060 | inst.exe | 36.110.211.219:443 | pinst.360.cn | IDC, China Telecommunications Corporation | CN | unknown |
4060 | inst.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
4060 | inst.exe | 104.192.108.18:80 | dl.360safe.com | Beijing Qihu Technology Company Limited | US | suspicious |
4060 | inst.exe | 104.192.108.17:80 | dl.360safe.com | Beijing Qihu Technology Company Limited | US | malicious |
— | — | 106.87.14.106:10004 | — | No.31,Jin-rong Street | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
st.p.360.cn |
| whitelisted |
s.360.cn |
| whitelisted |
tr.p.360.cn |
| suspicious |
agt.p.360.cn |
| whitelisted |
pinst.360.cn |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
wotrus-ovca.ocsp-certum.com |
| whitelisted |
agd.p.360.cn |
| whitelisted |
dl.360safe.com |
| whitelisted |
sd.p.360.cn |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4060 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4060 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
4060 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
— | — | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
— | — | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4060 | inst.exe | Misc activity | ET INFO Packed Executable Download |
4060 | inst.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3712 | 360tray.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 8 through 15 set |
3712 | 360tray.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Reserved Bit Set |
4 | System | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 6 or 7 set |
Process | Message |
|---|---|
SoftupNotify.exe | /install |
regsvr32.exe | 360softmgr.shellext.SafeExistThread |
regsvr32.exe | 360softmgr.shellext.SafeExistThread leave |
explorer.exe | 360softmgr.shellext.CommandMonitor loop, InterlockedCompareExchange(&lThreadExitFlag_CommandMonitor, 1, 1) -> 0 |
explorer.exe | startmenuUnpin |
explorer.exe | open Global\360SoftMgr.ShellExt.Share |
explorer.exe | mapview Global\360SoftMgr.ShellExt.Share |
explorer.exe | C:\Program Files\360\360Safe\SoftMgr\??????????.lnk |
explorer.exe | 360softmgr.shellext.CommandMonitor loop, InterlockedCompareExchange(&lThreadExitFlag_CommandMonitor, 1, 1) -> 0 |
explorer.exe | softmgrext_share_valid_path:C:\Program Files\360\360Safe\SoftMgr\??????????.lnk, C:\Program Files\360\360Safe\SoftMgr\??????????.lnk, verb:startmenuUnpin, icmp:1 |