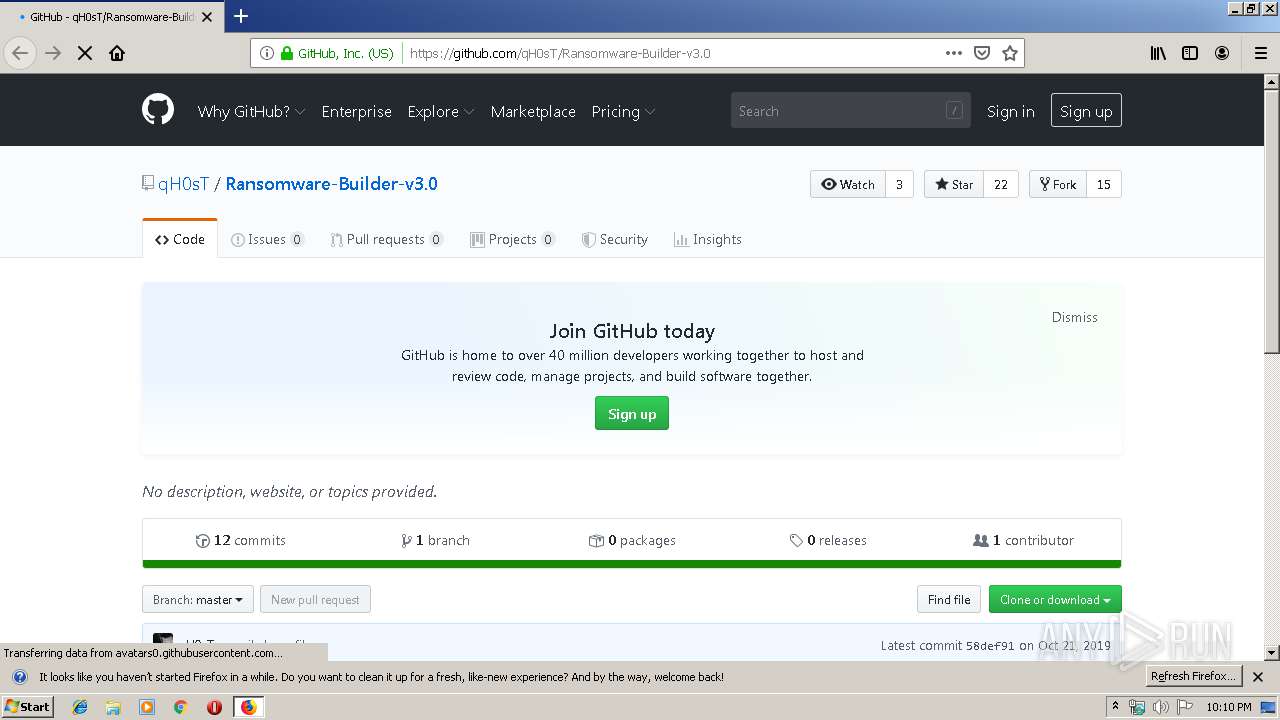
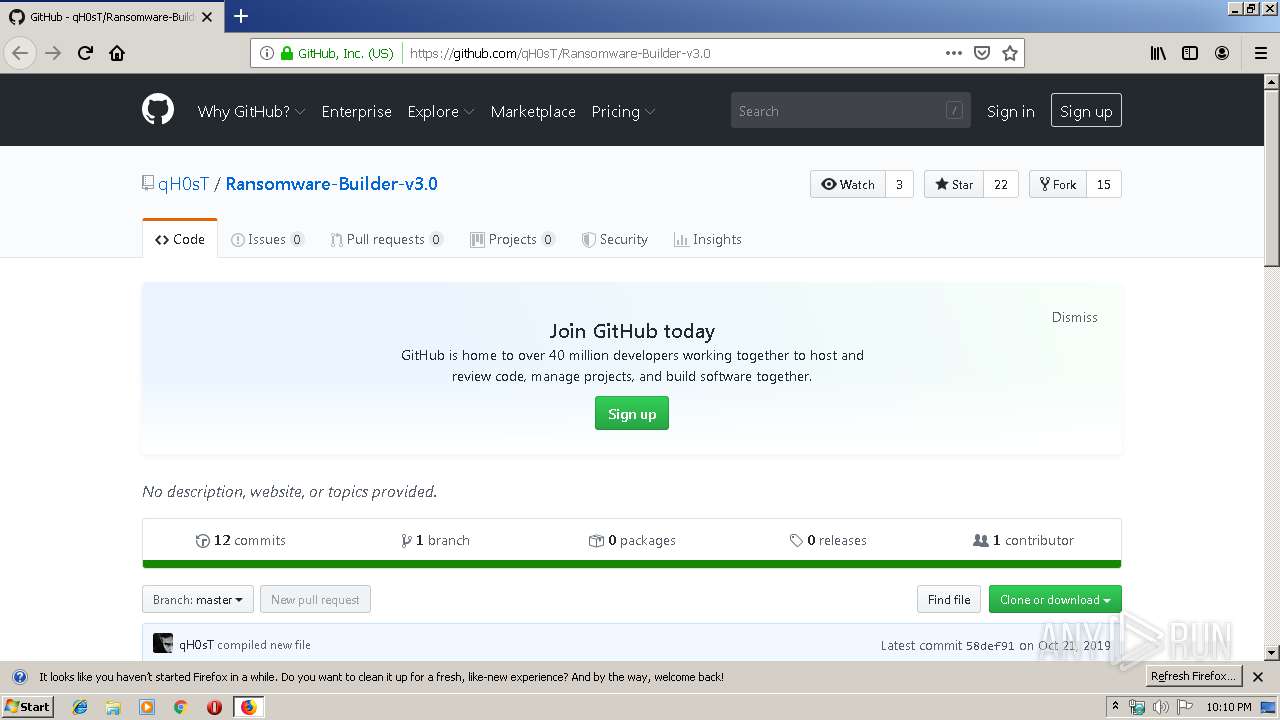
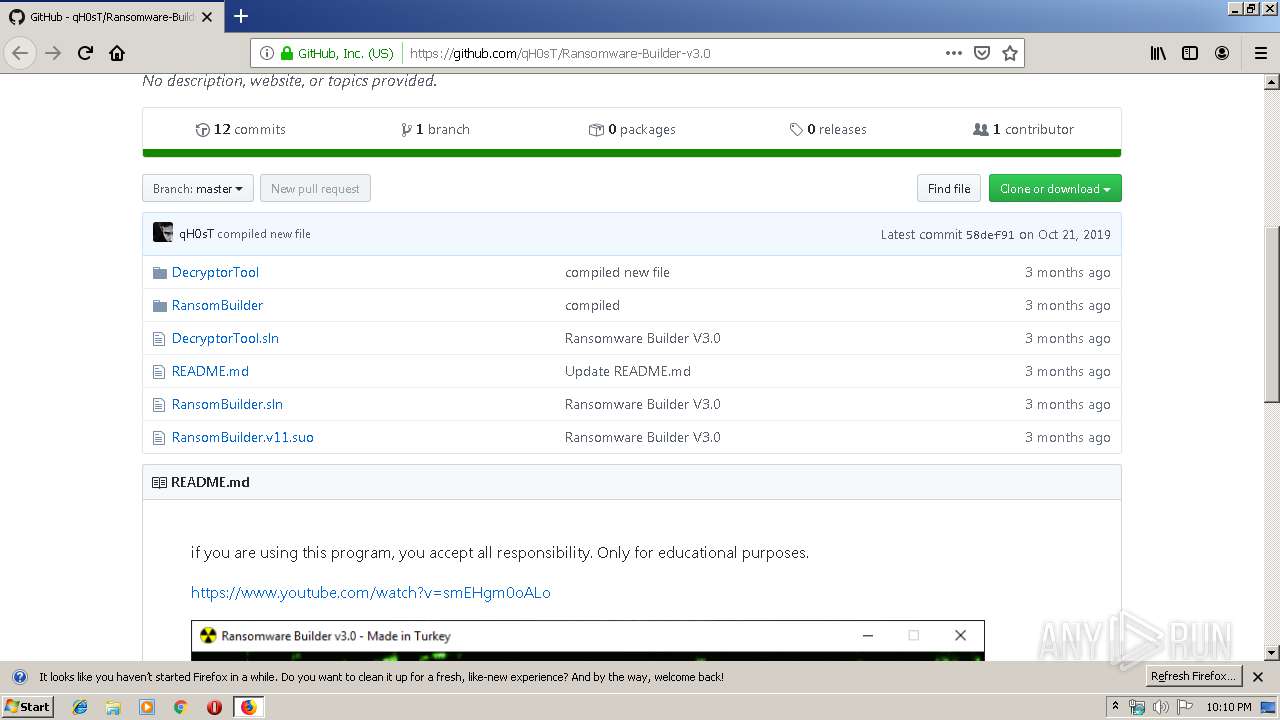
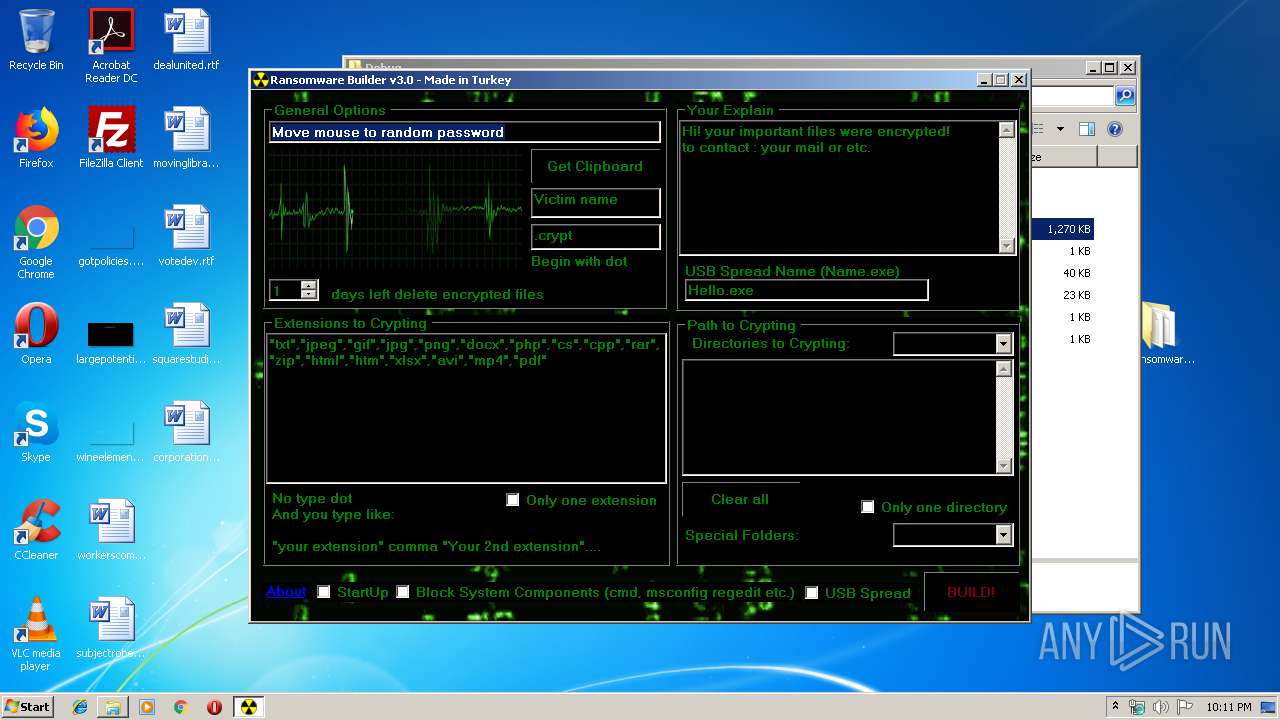
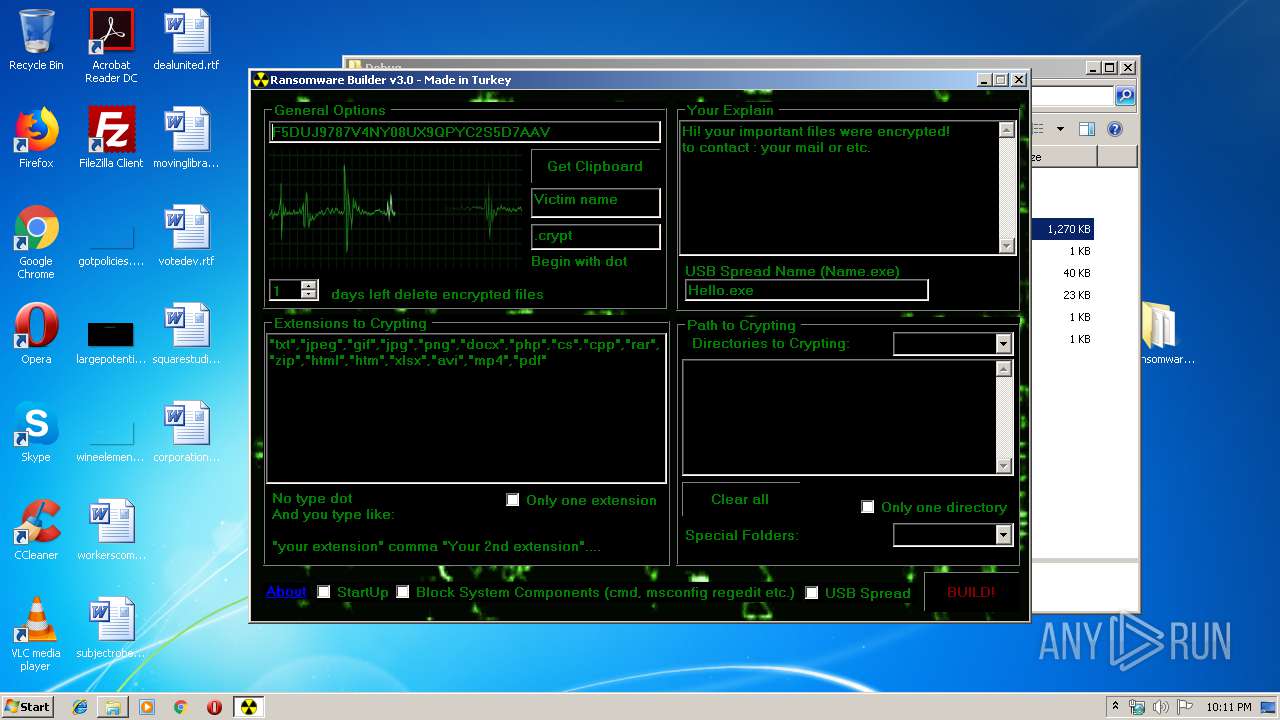
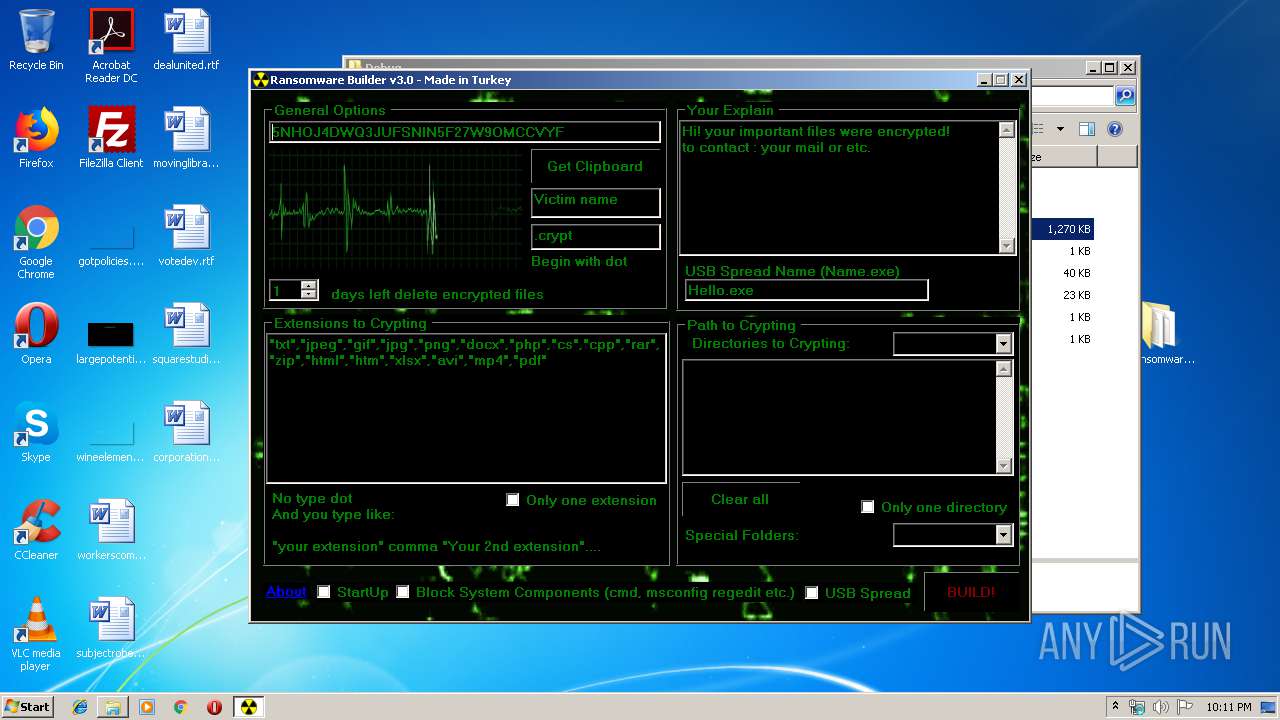
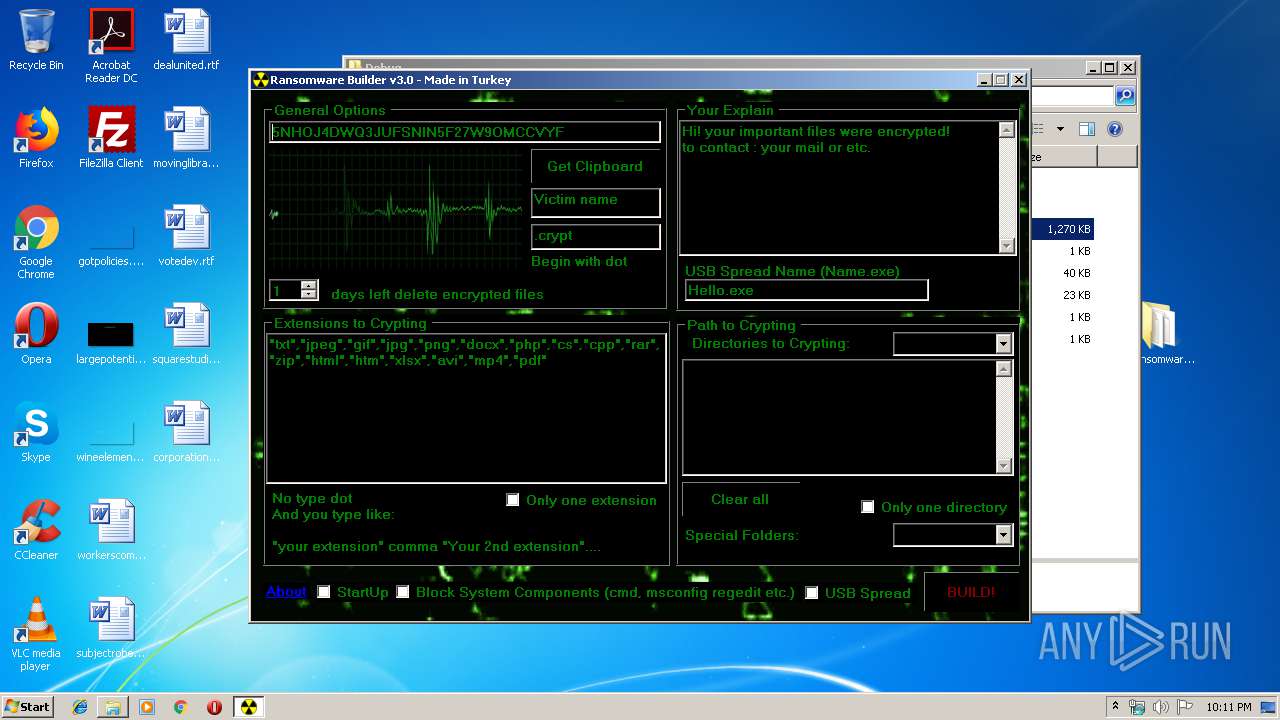
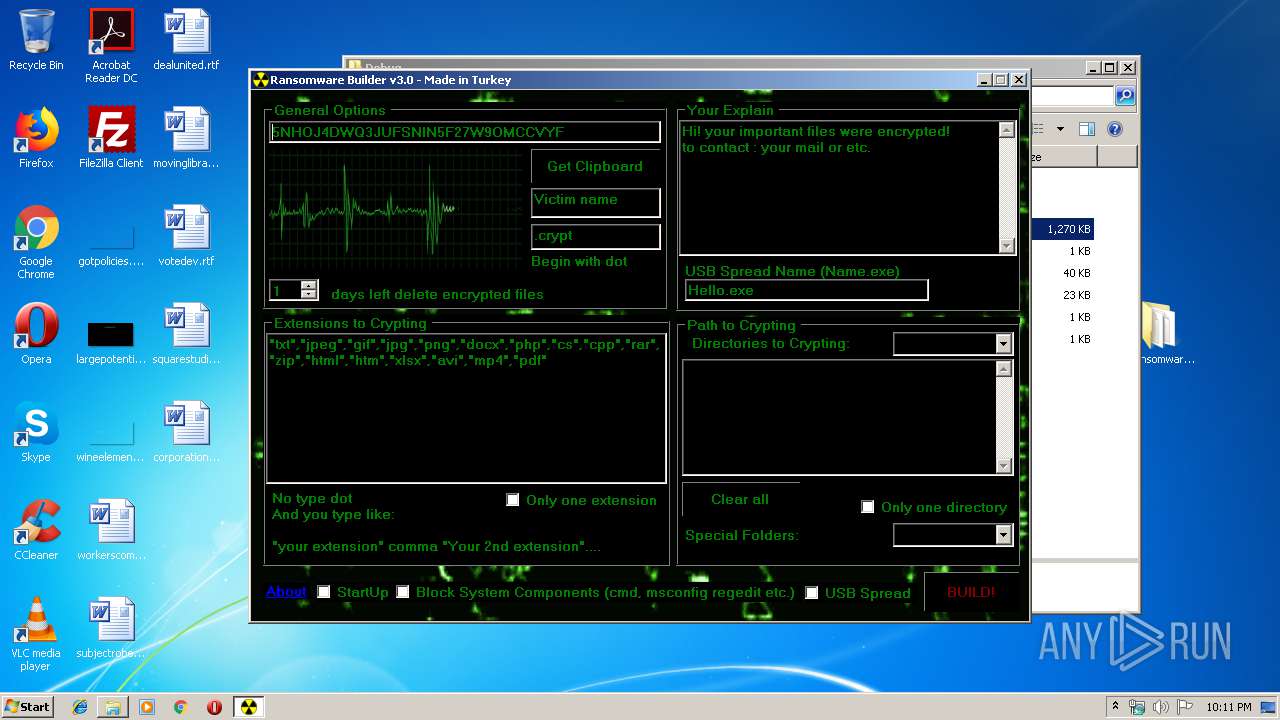
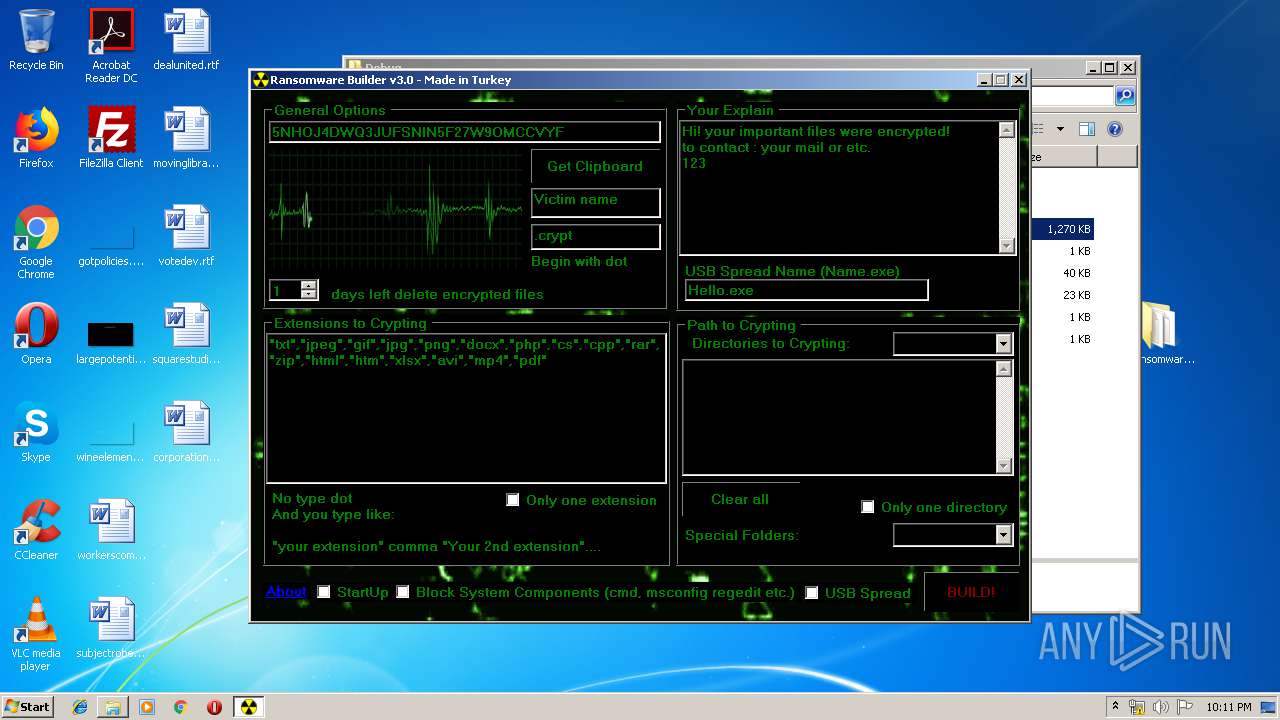
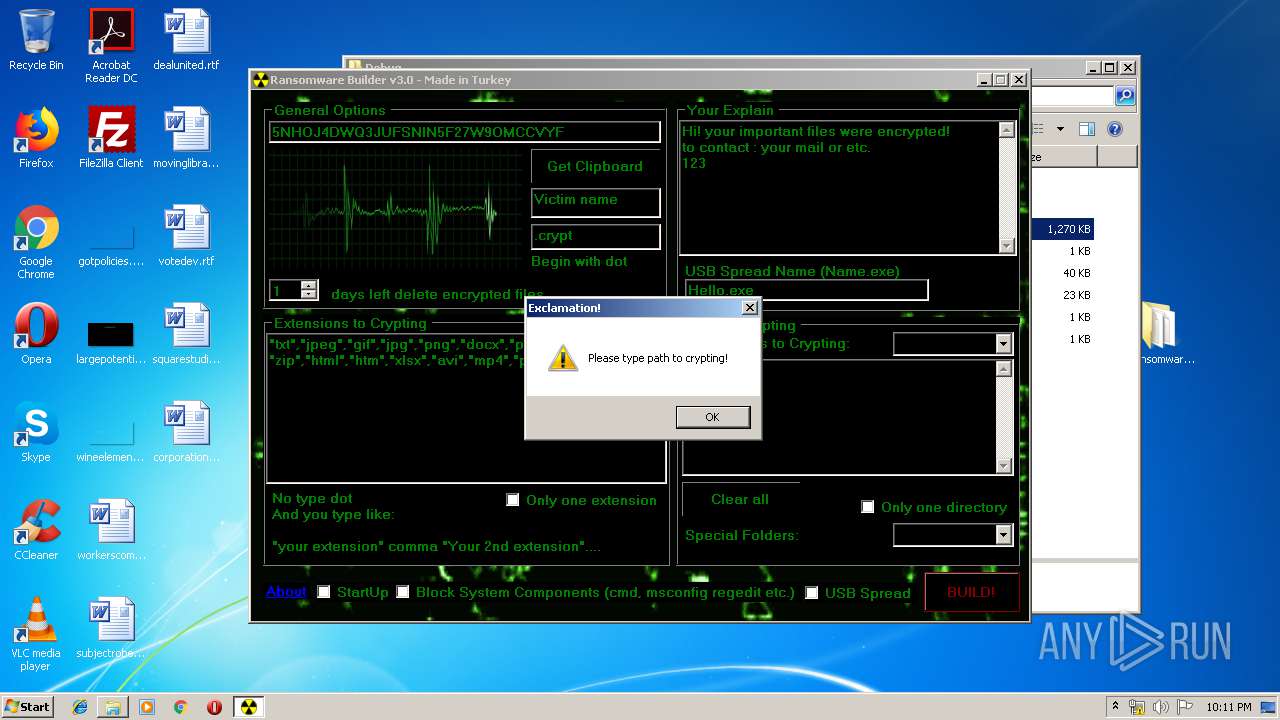
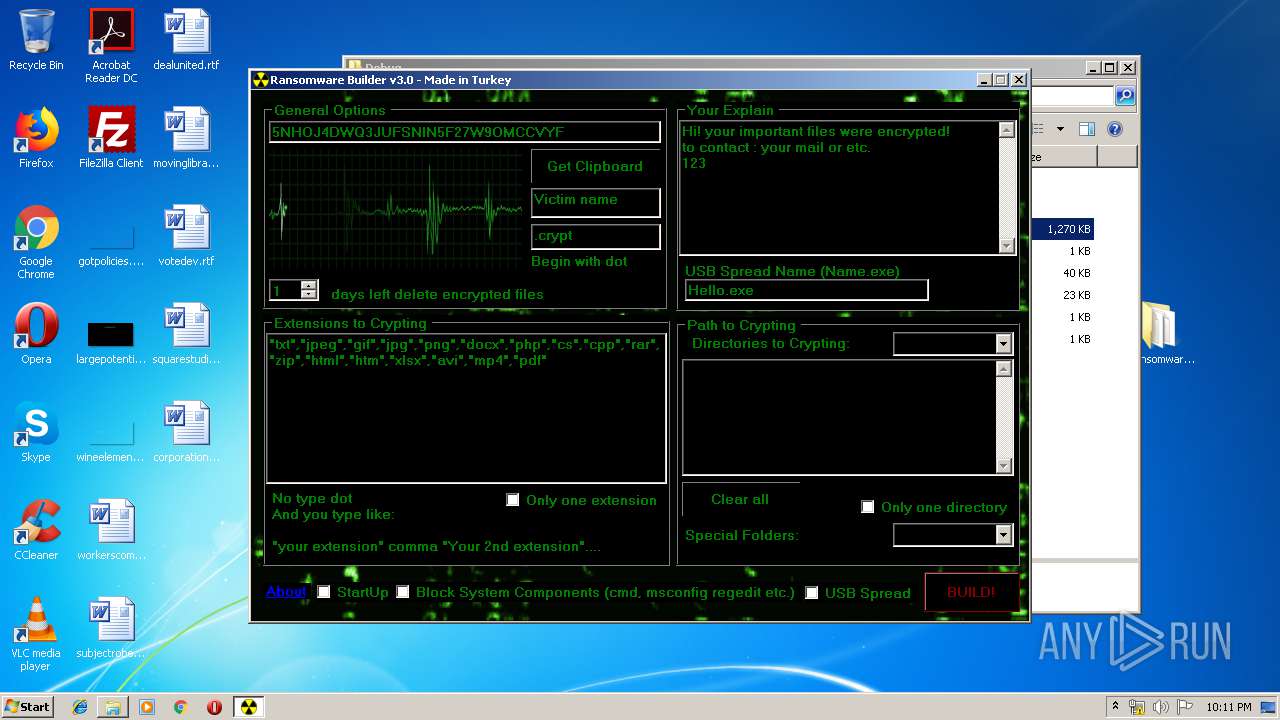
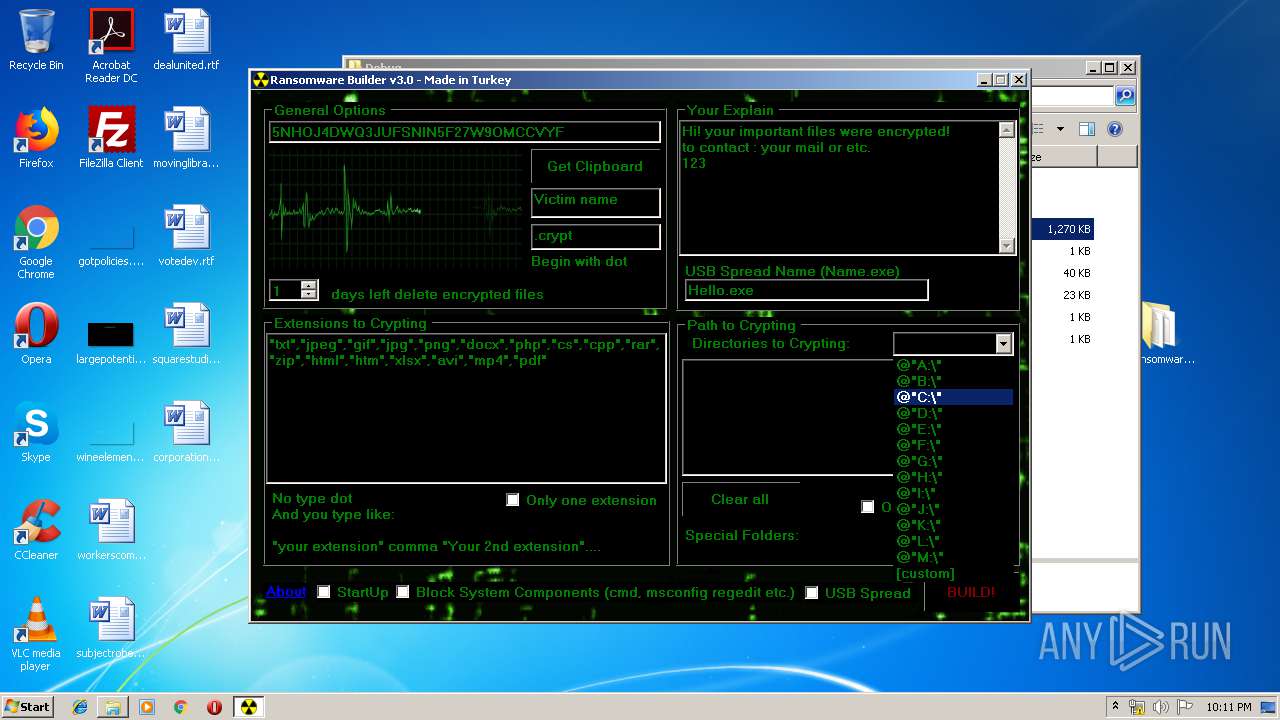
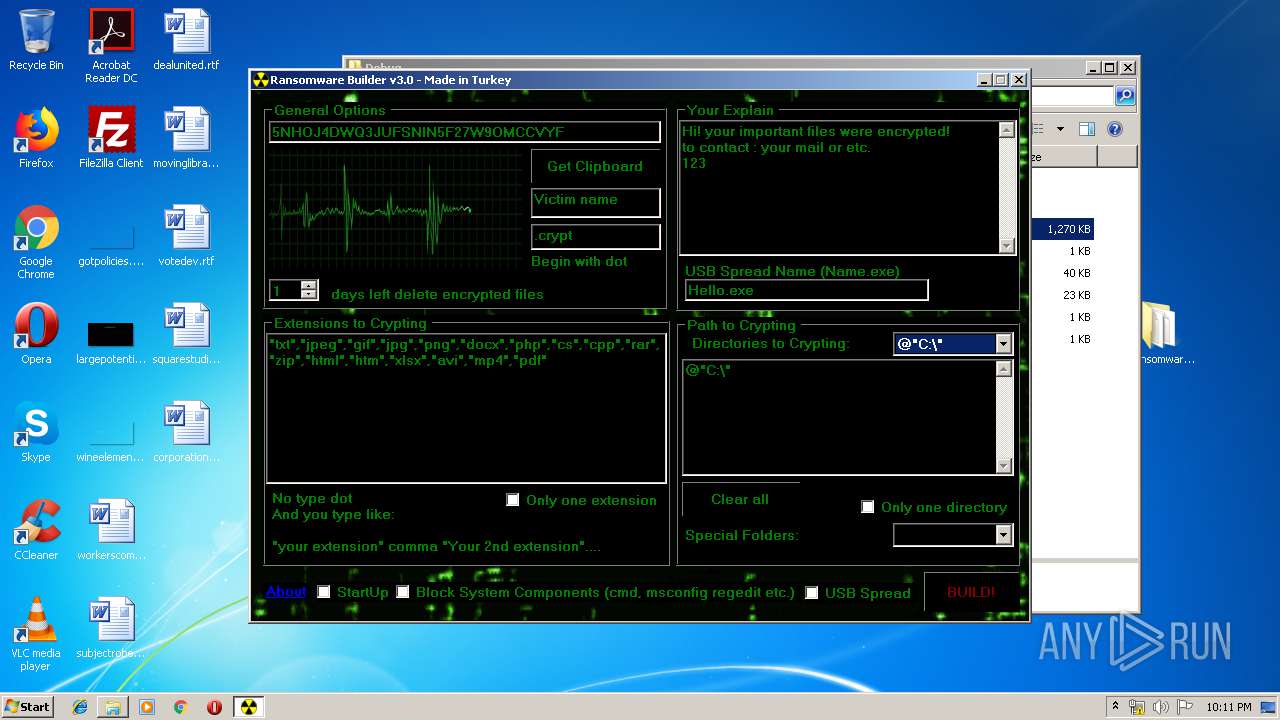
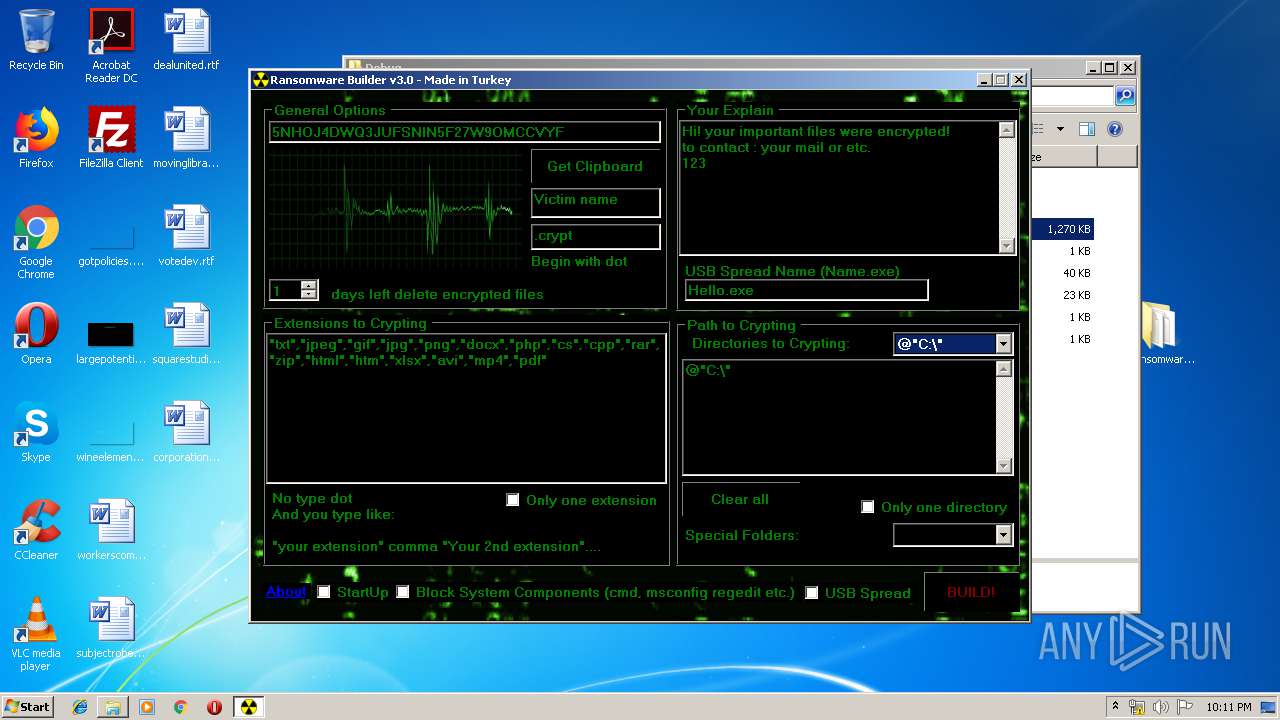
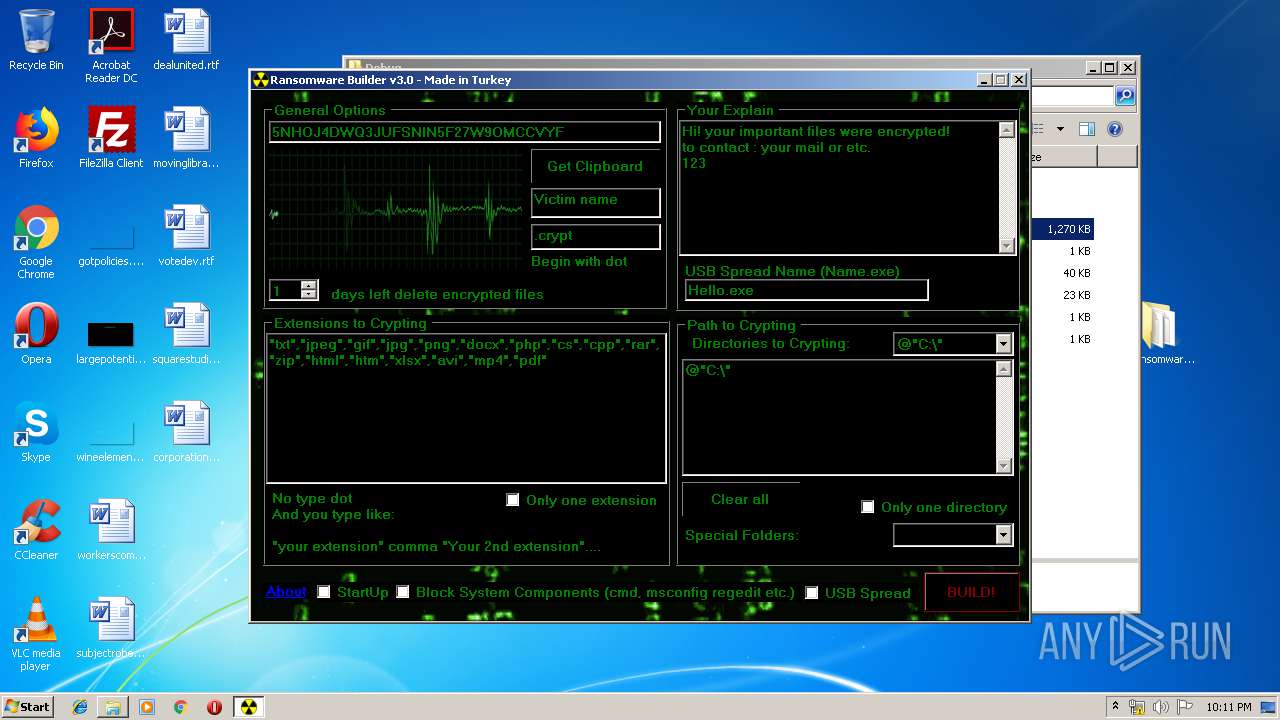
| URL: | https://github.com/qH0sT/Ransomware-Builder-v3.0 |
| Full analysis: | https://app.any.run/tasks/564ba010-31a5-47b7-be07-e8f9ff743c2f |
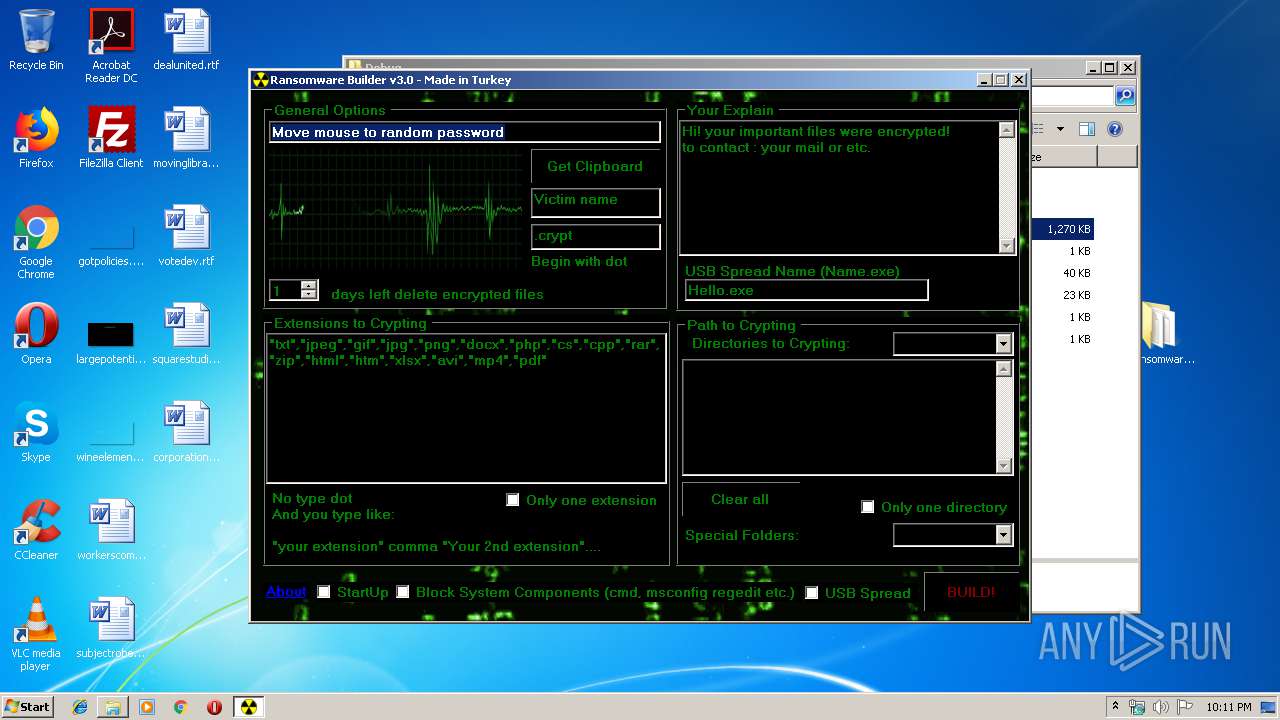
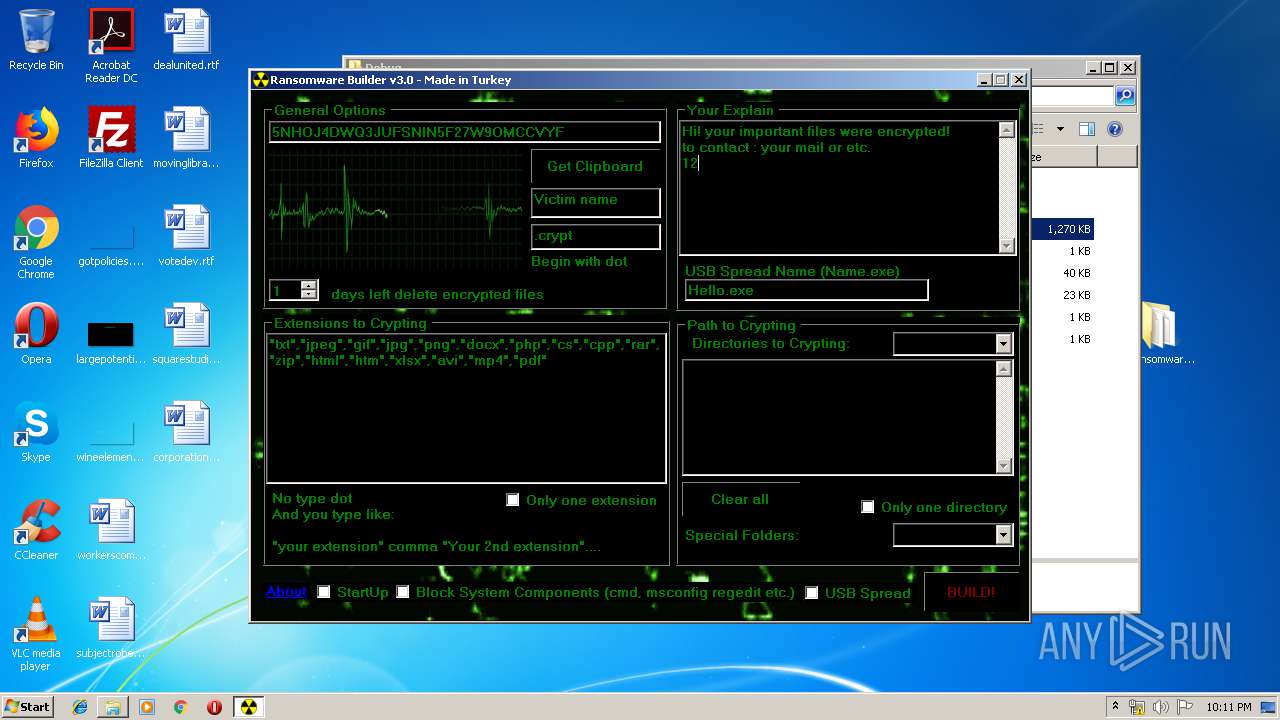
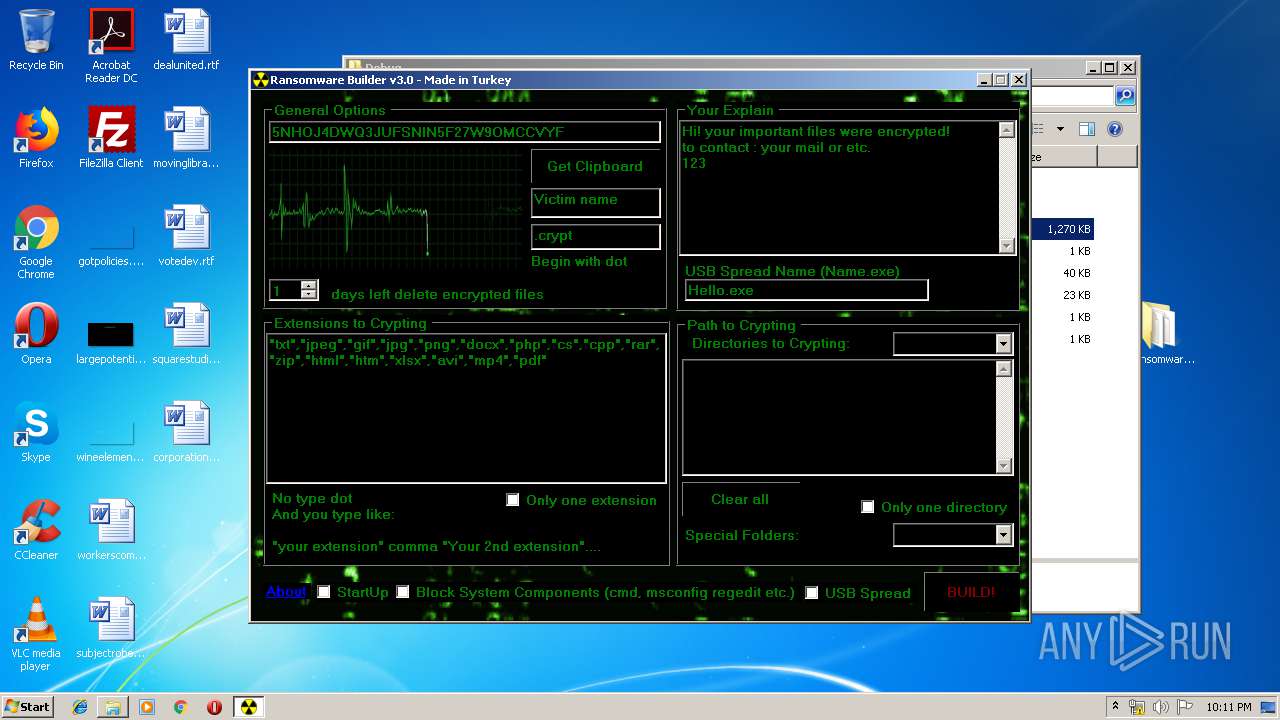
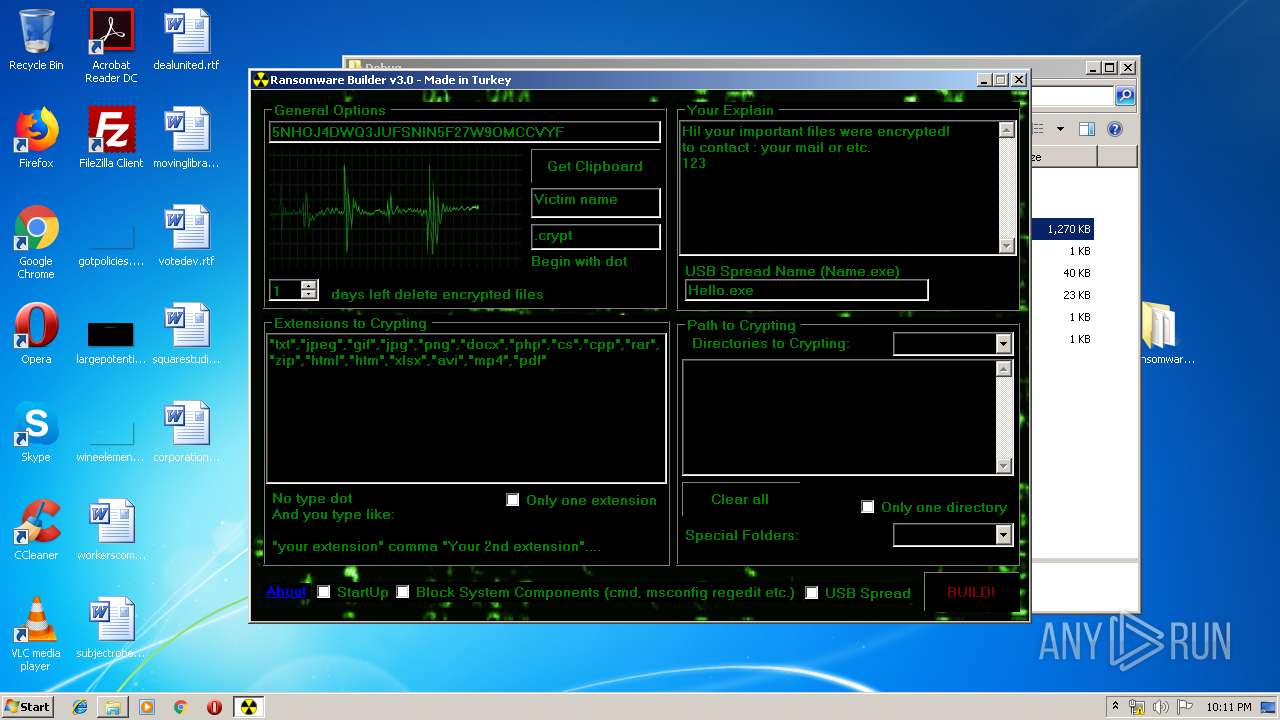
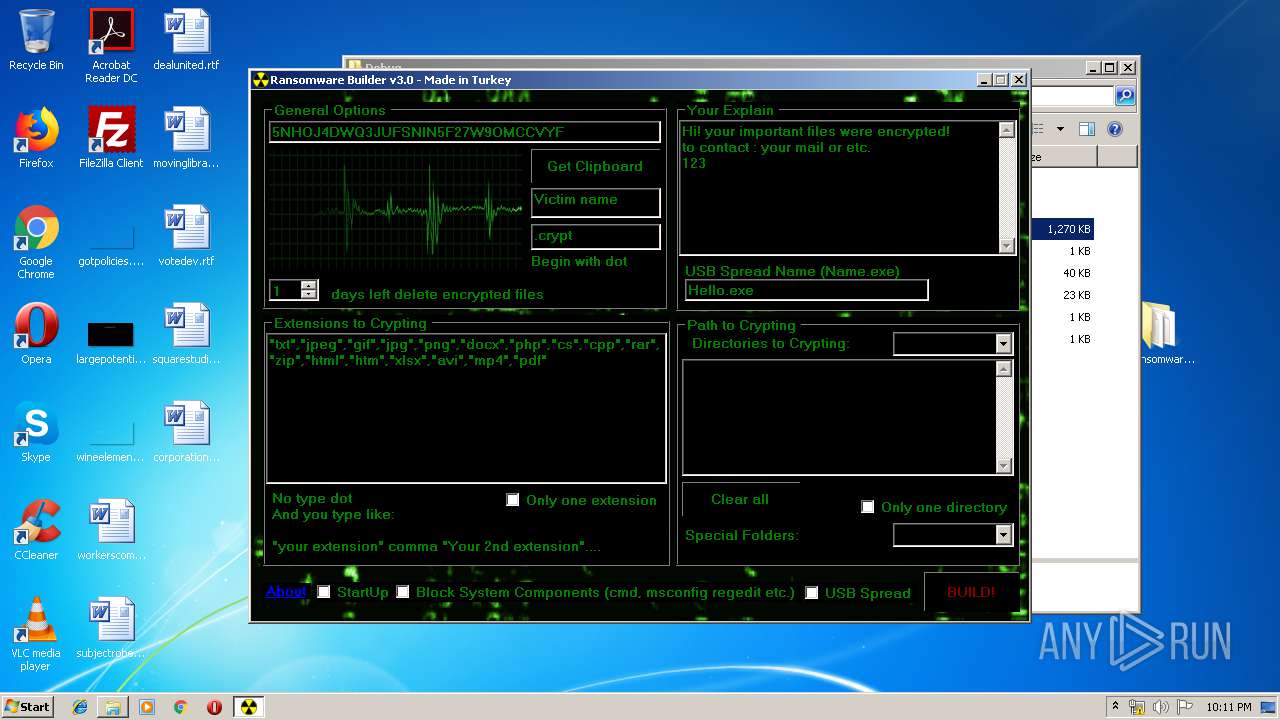
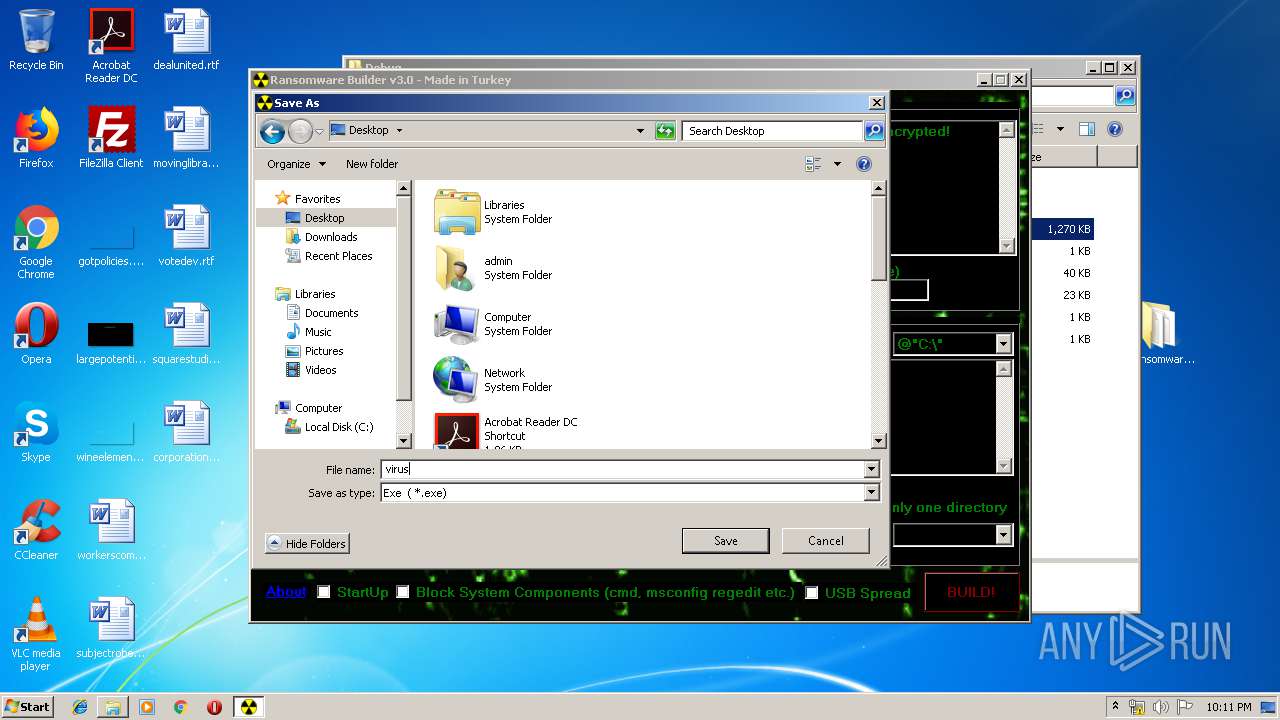
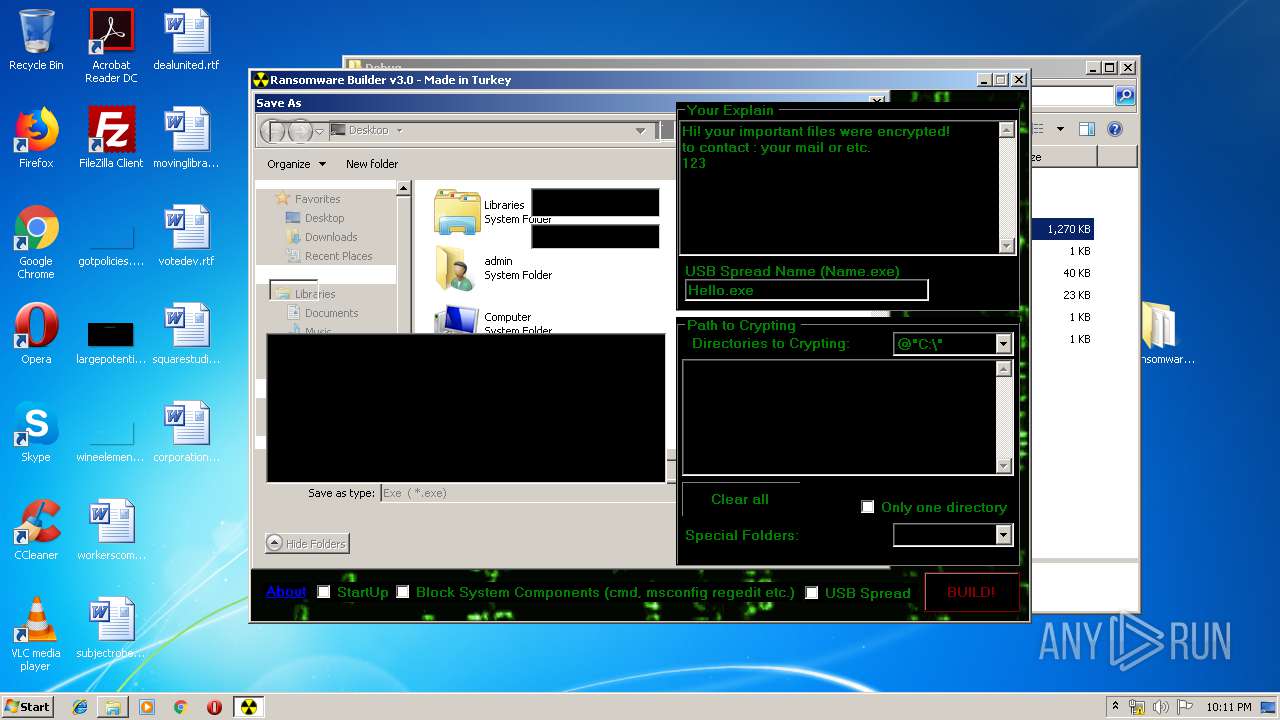
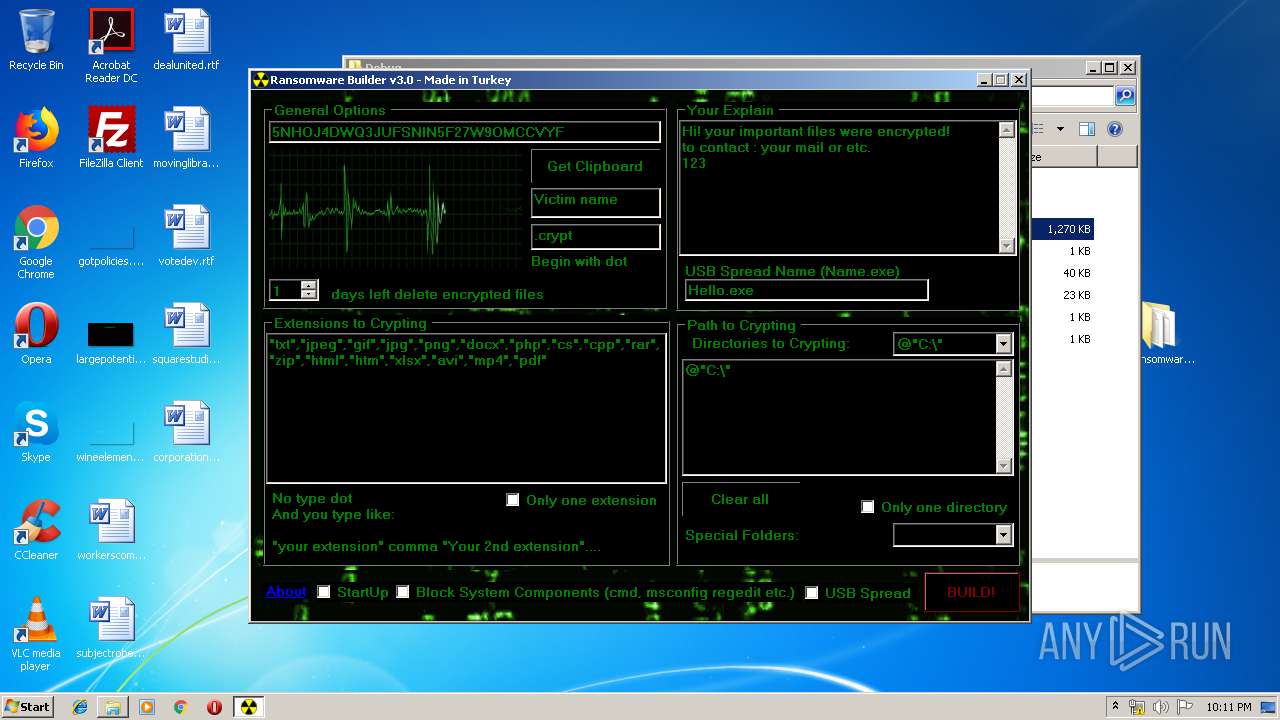
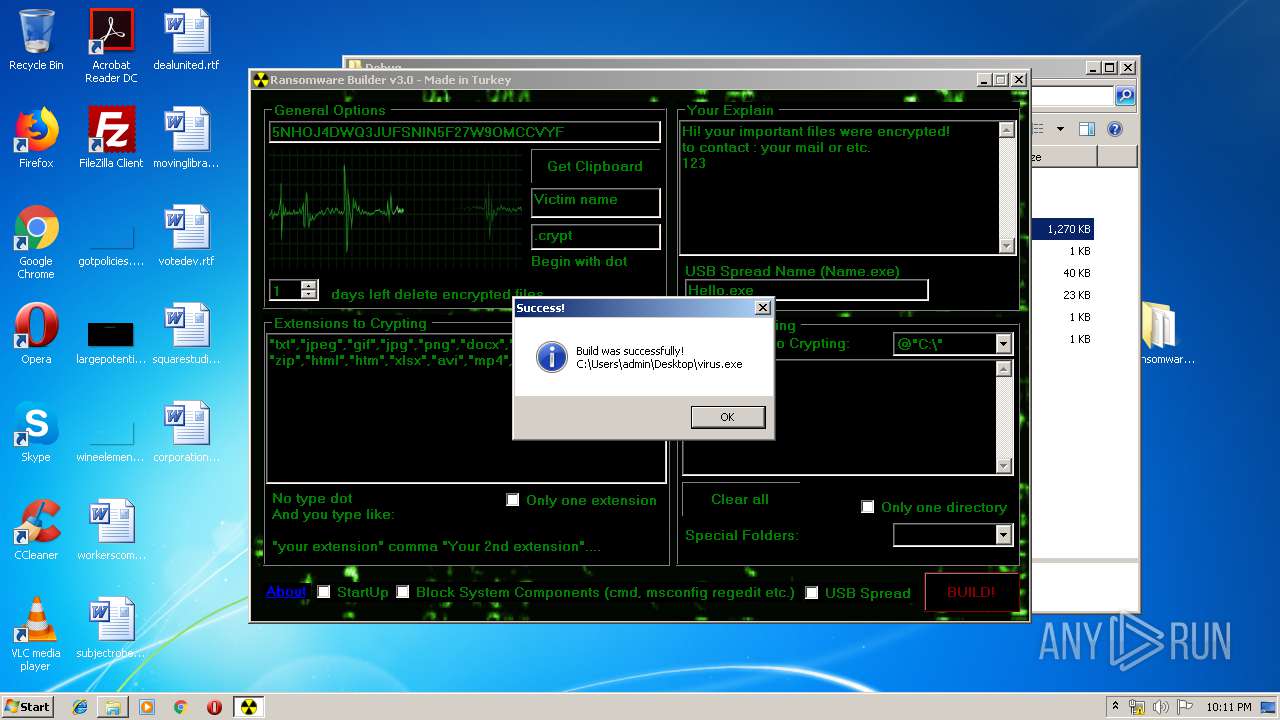
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 22:10:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 385A47F9130843A3EC53D6280F1CC592 |
| SHA1: | 5DEE4C5FFDD13D197C94E9B12505DEFA20E176DC |
| SHA256: | DA533529AAF326C257A5004F19DE91EB655D7A37E0D8A9726244D678BD487BF3 |
| SSDEEP: | 3:N8tEdktP3i8nJBAYah:2uyta8nuh |
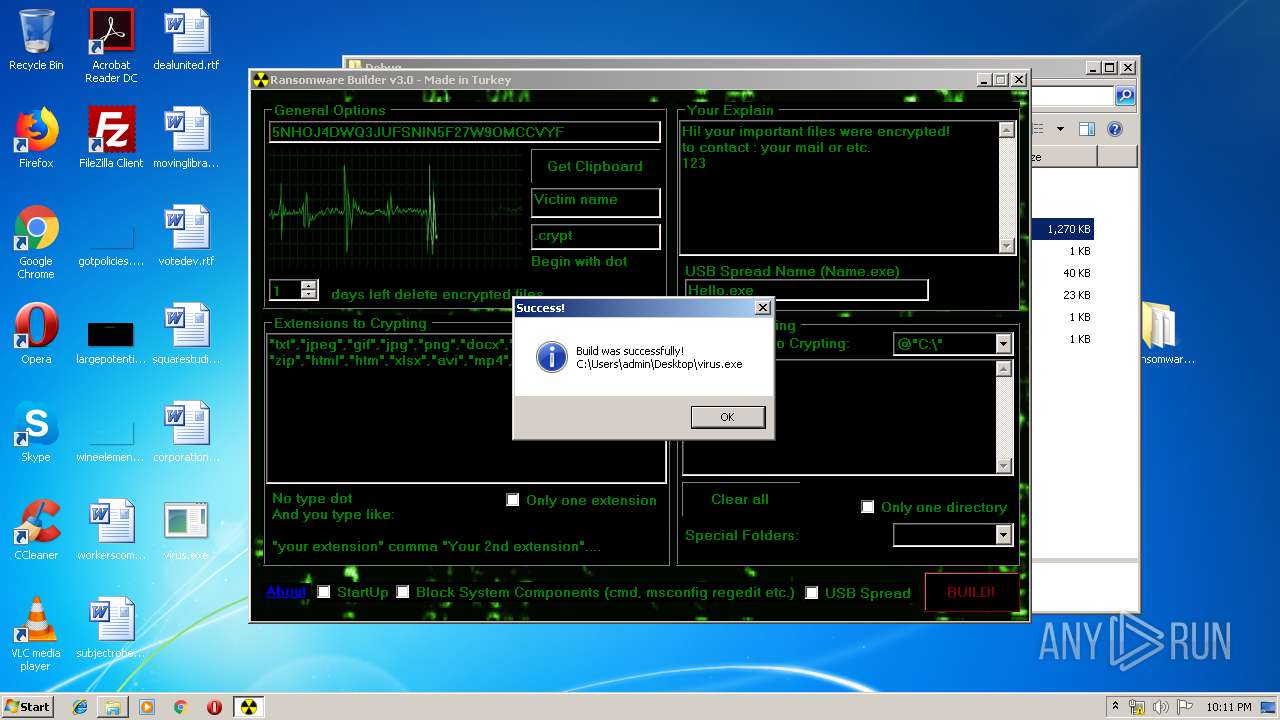
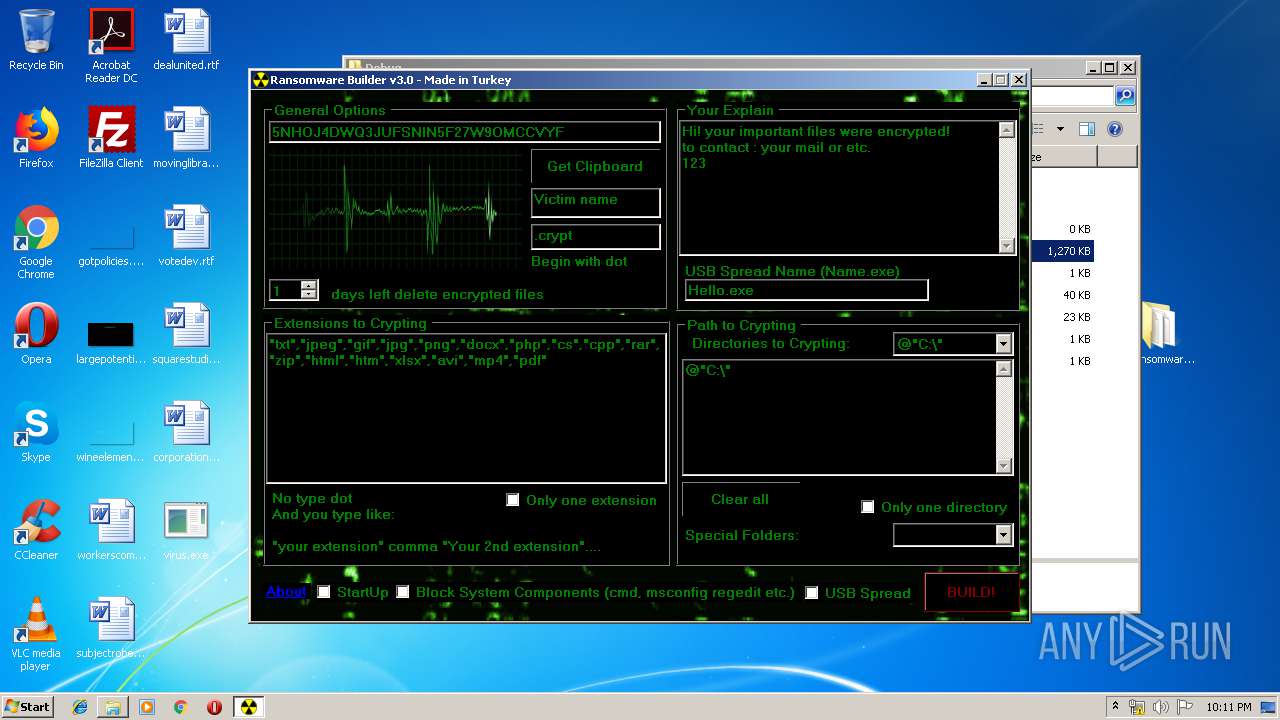
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3544)
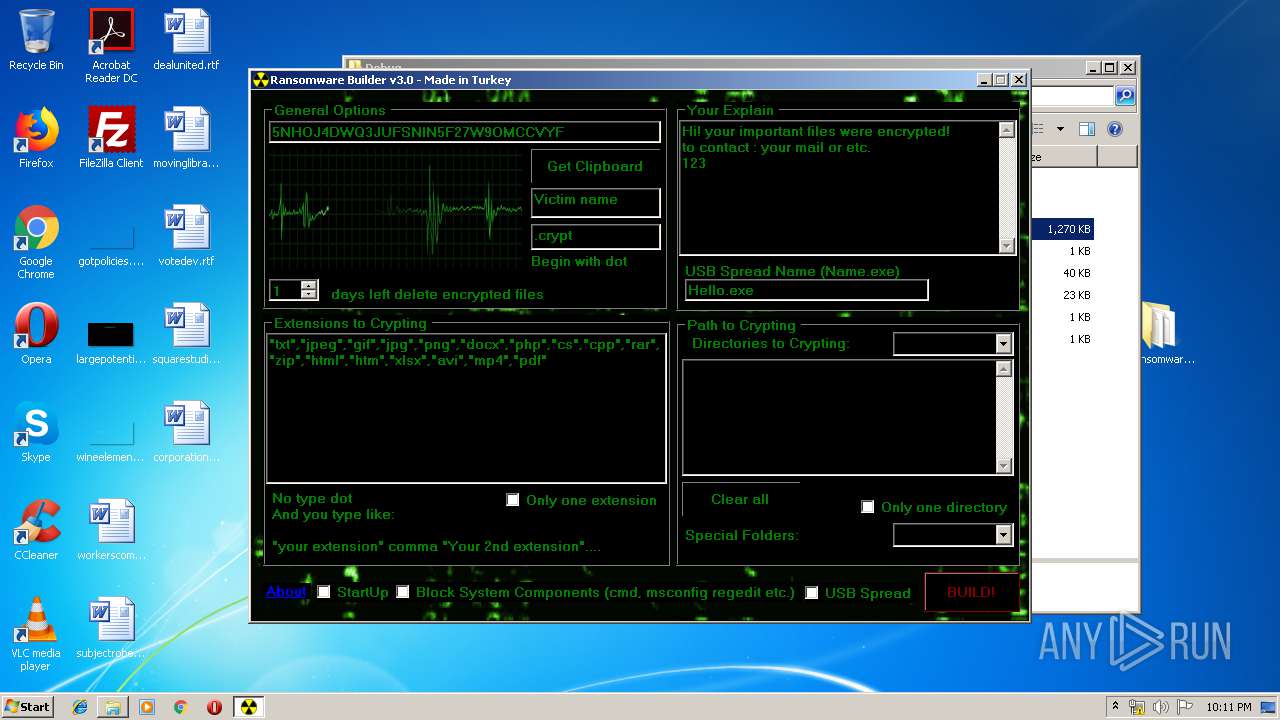
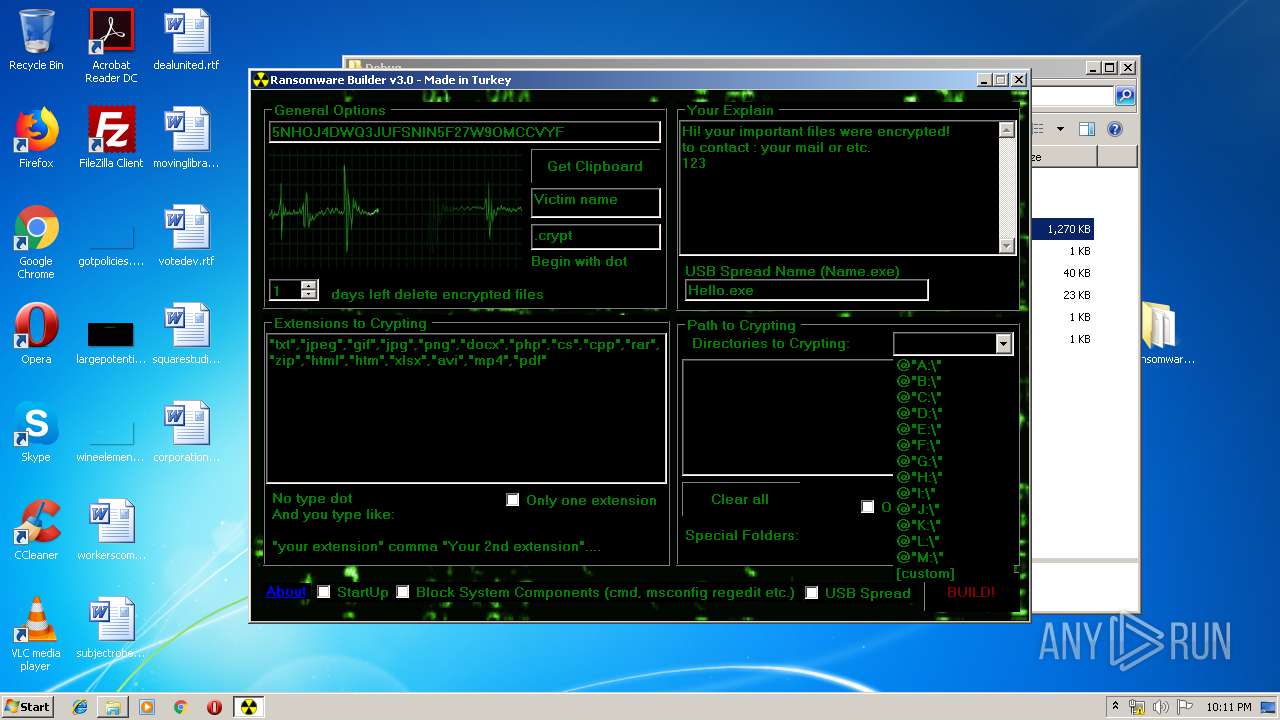
Starts Visual C# compiler
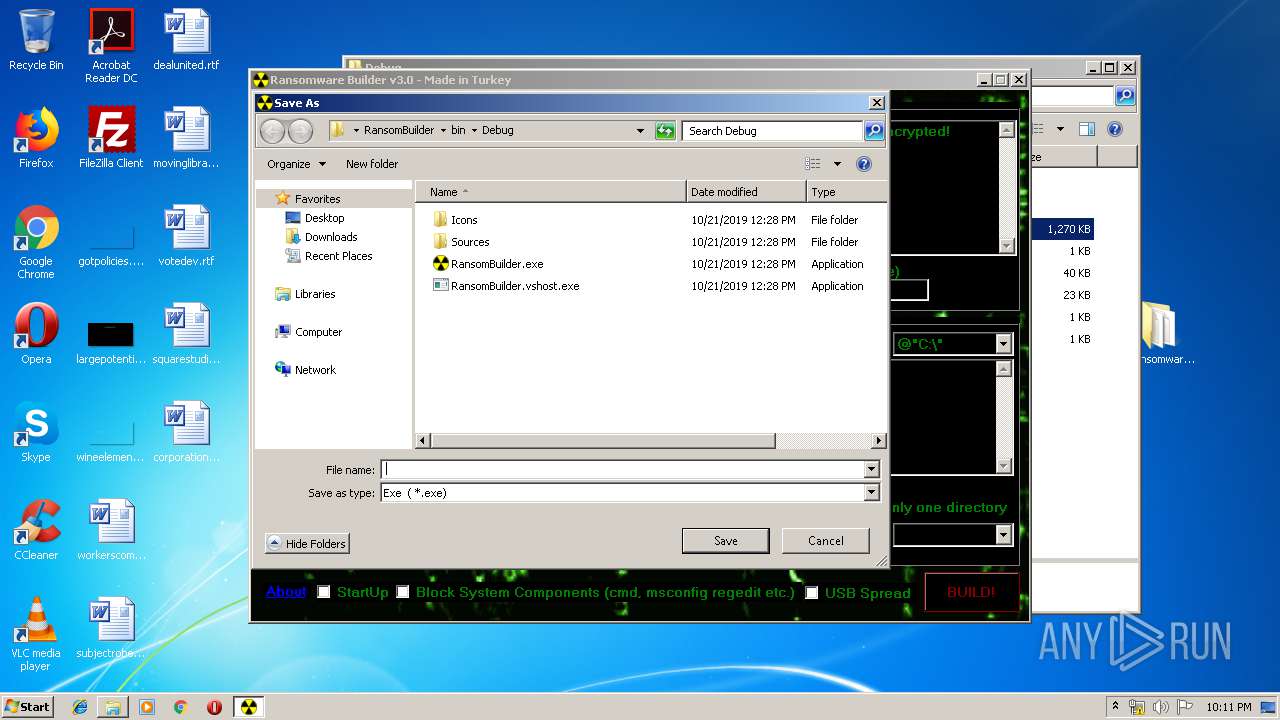
- RansomBuilder.exe (PID: 2420)
Application was dropped or rewritten from another process
- RansomBuilder.exe (PID: 2420)
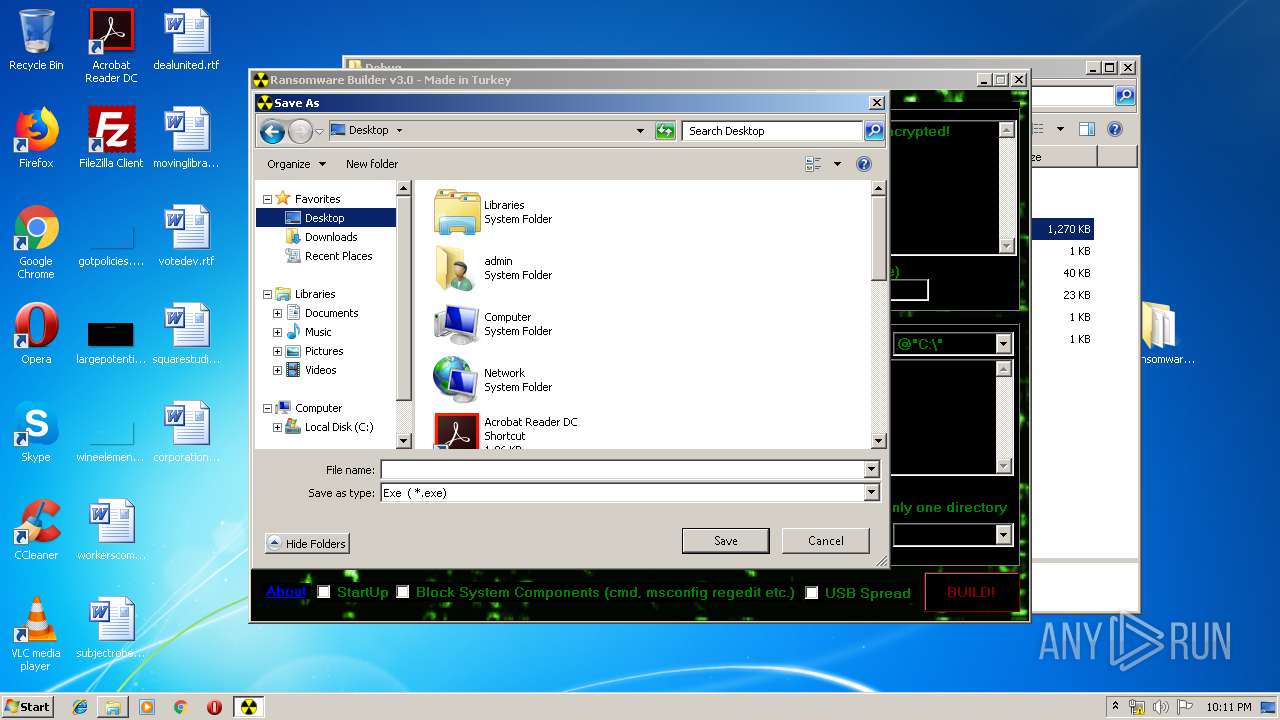
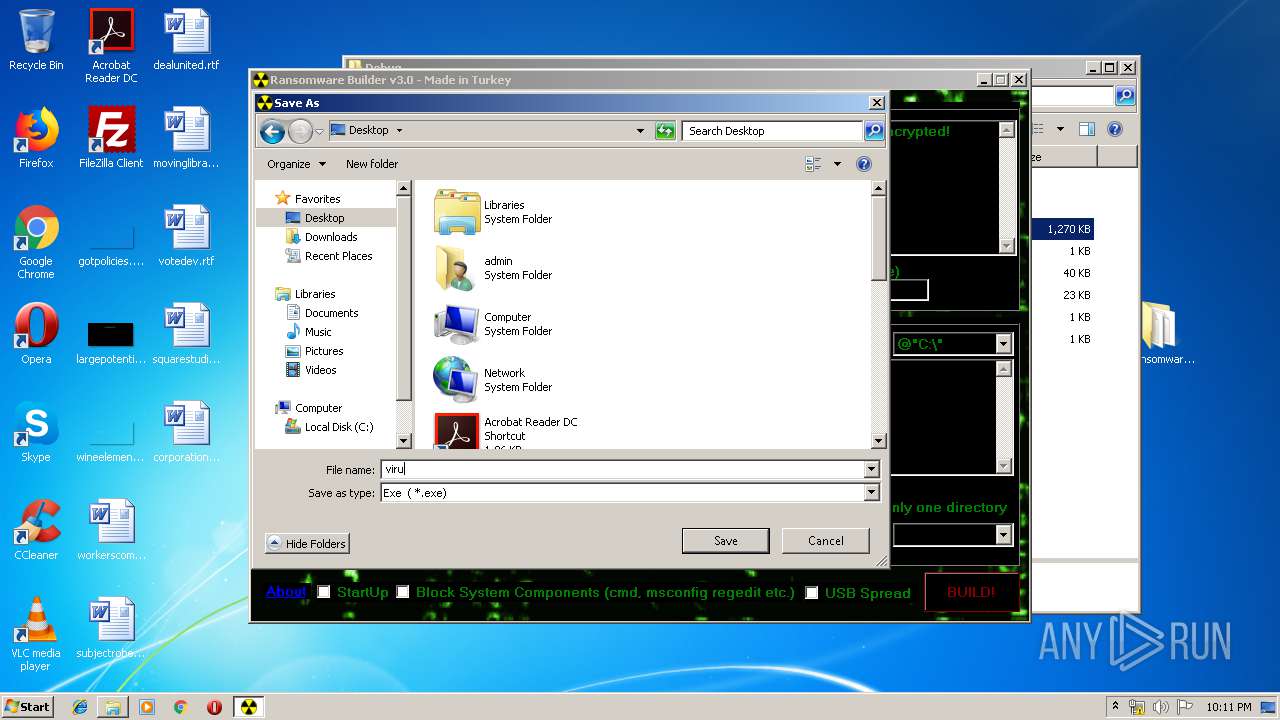
- virus.exe (PID: 2068)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 960)
Creates files in the user directory
- virus.exe (PID: 2068)
Executable content was dropped or overwritten
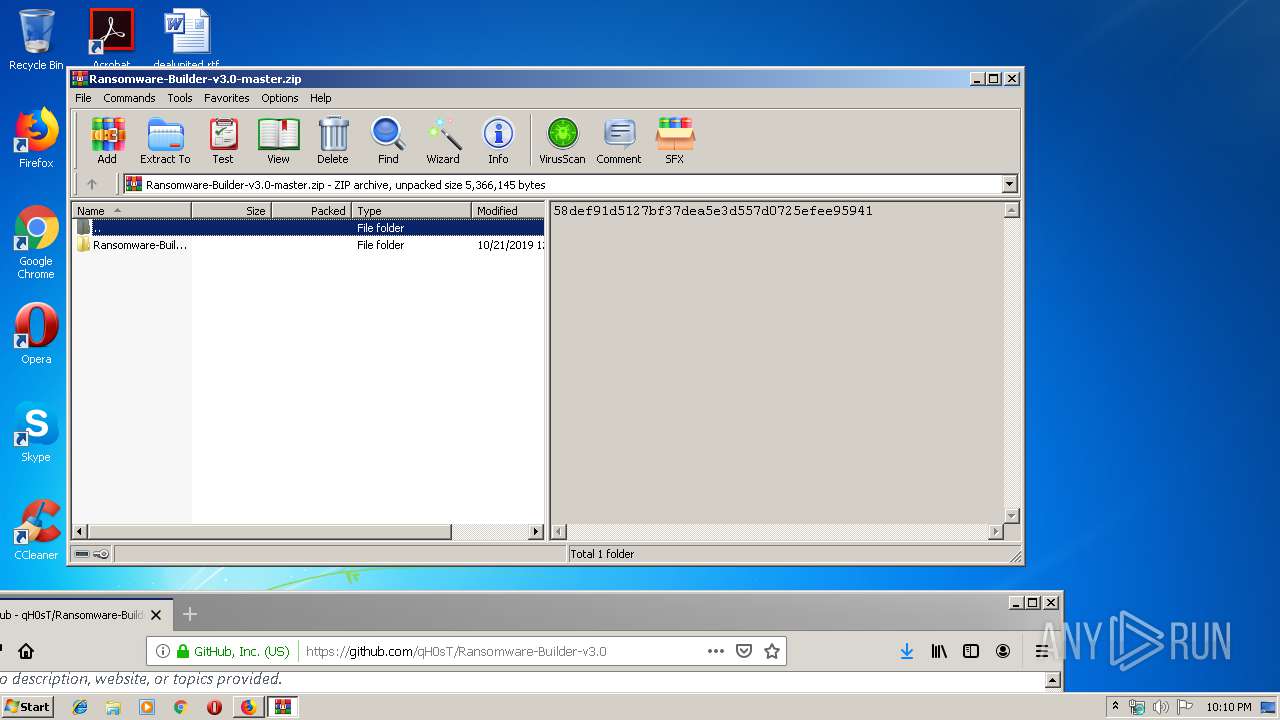
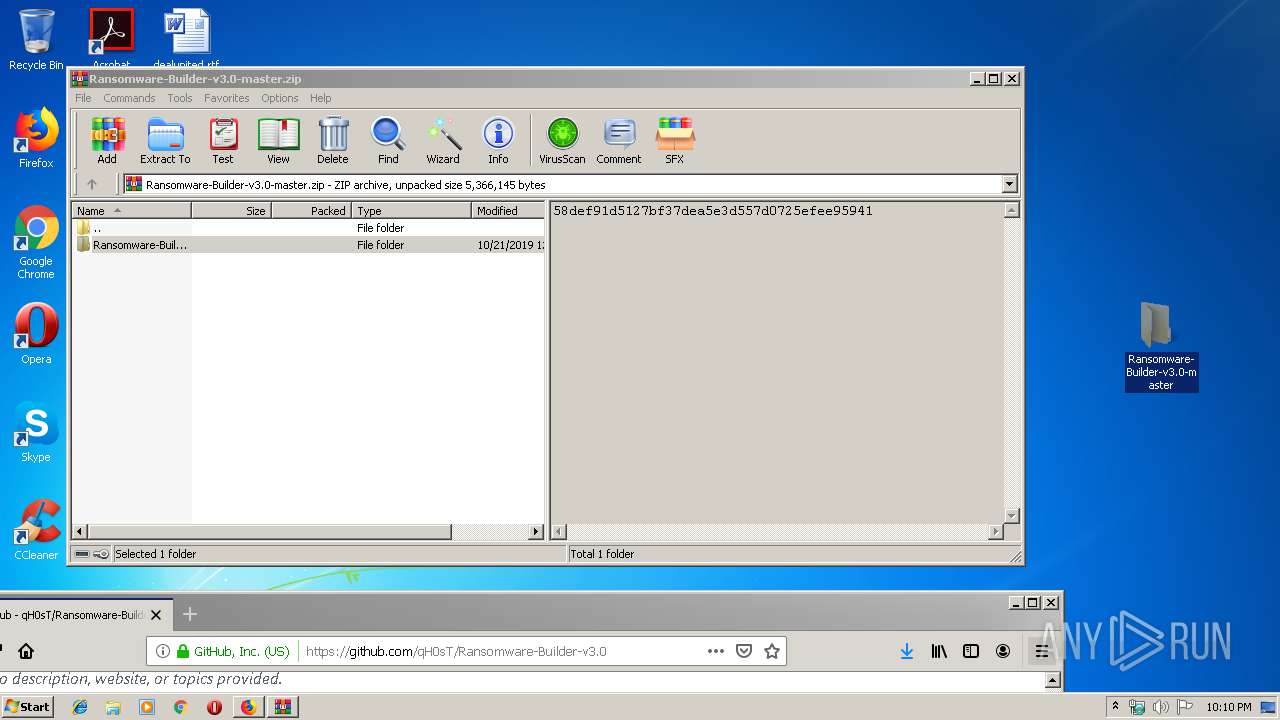
- WinRAR.exe (PID: 1748)
- csc.exe (PID: 2352)
INFO
Application launched itself
- firefox.exe (PID: 2512)
- firefox.exe (PID: 960)
Creates files in the user directory
- firefox.exe (PID: 960)
Reads CPU info
- firefox.exe (PID: 960)
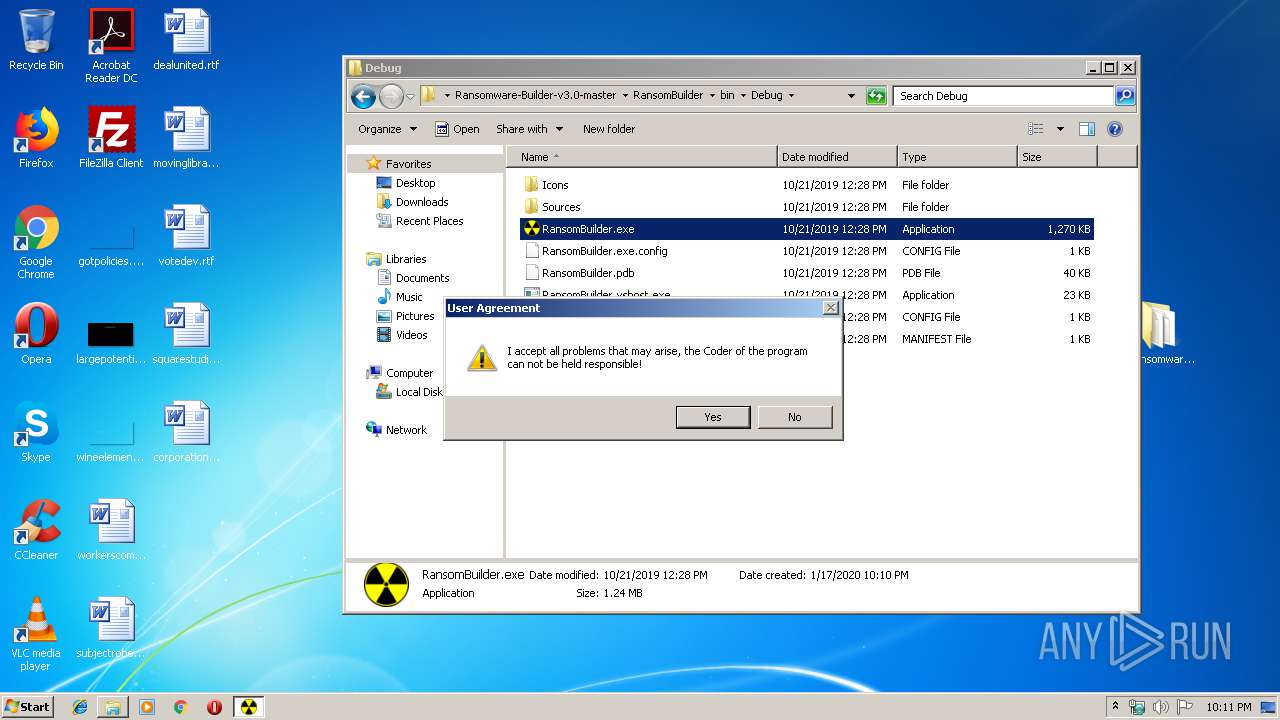
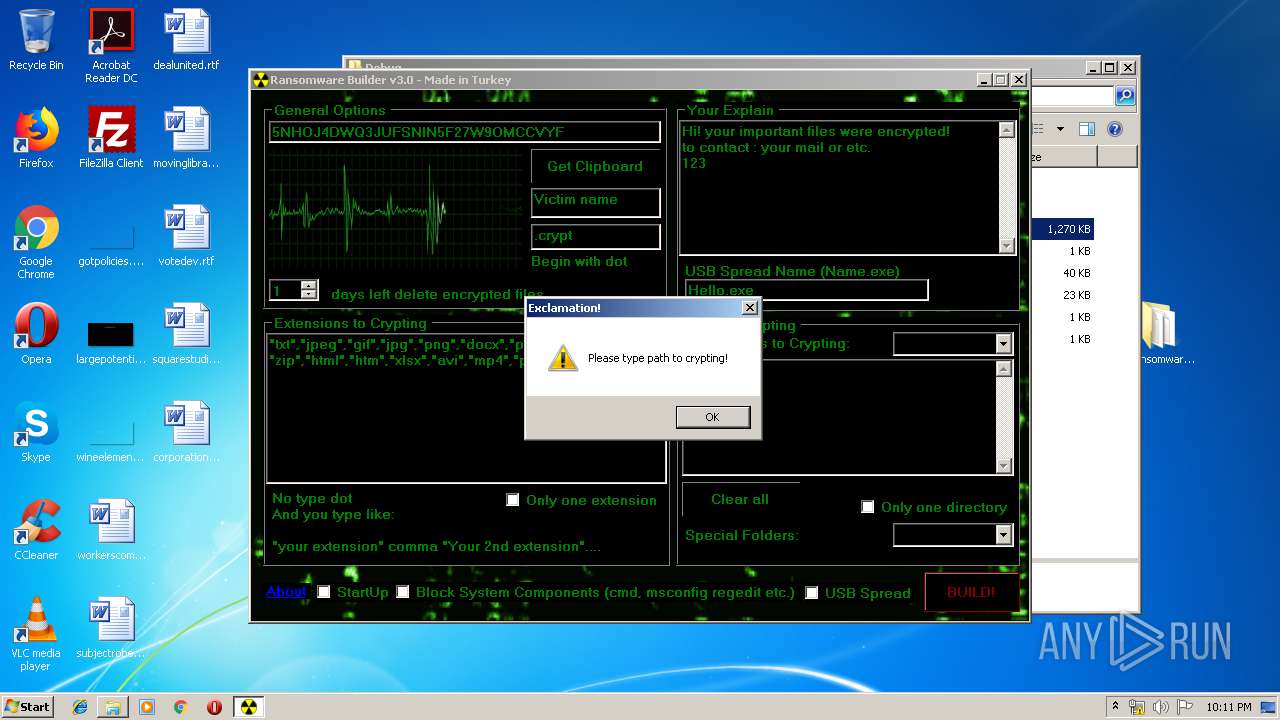
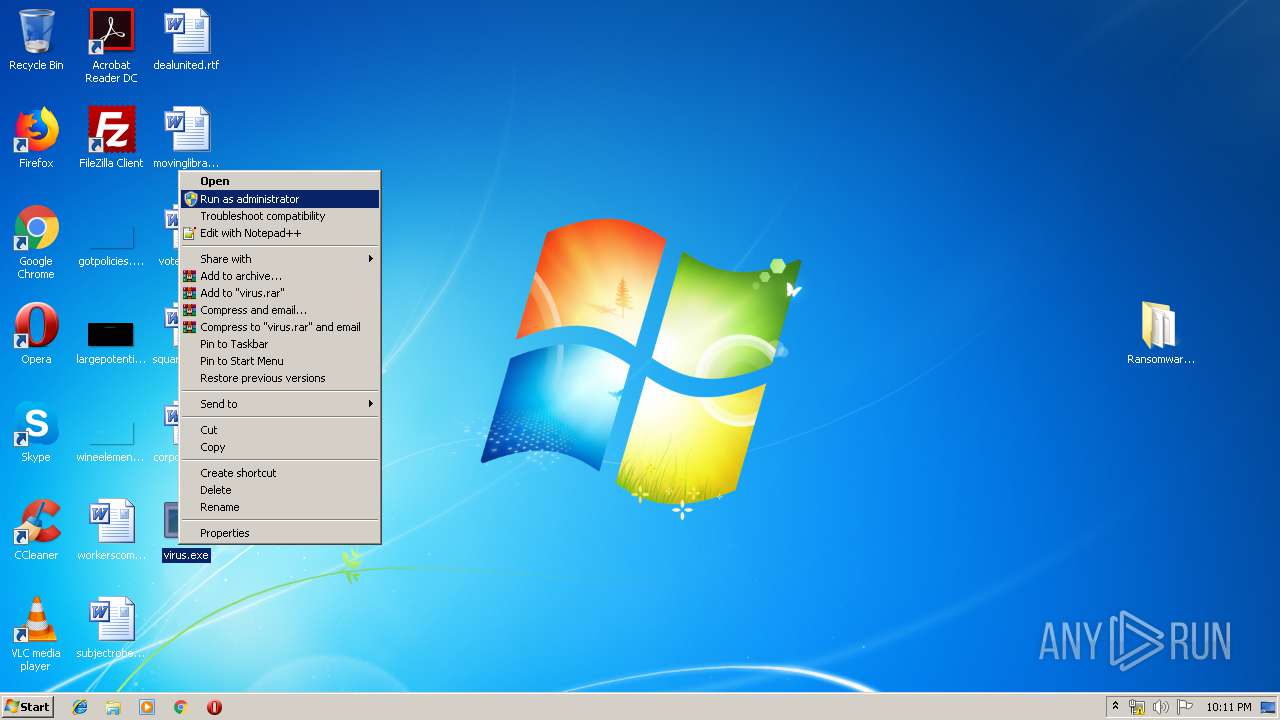
Manual execution by user
- RansomBuilder.exe (PID: 2420)
- virus.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
14
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
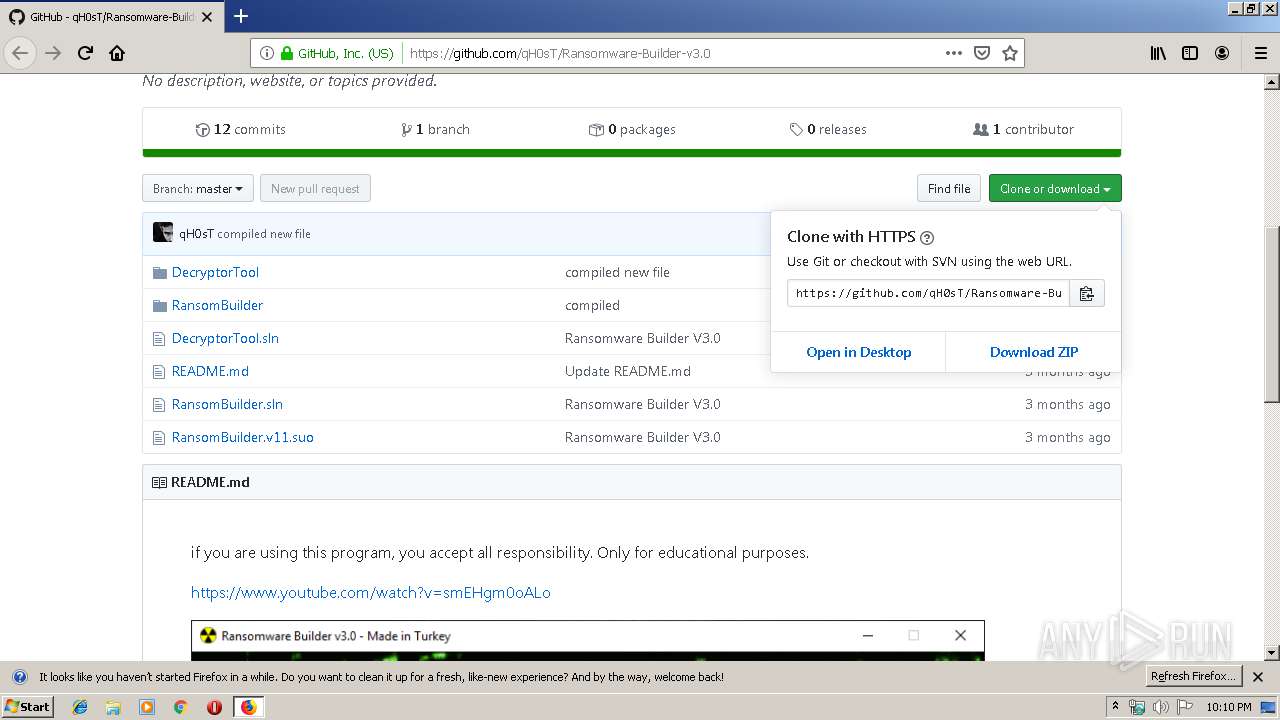
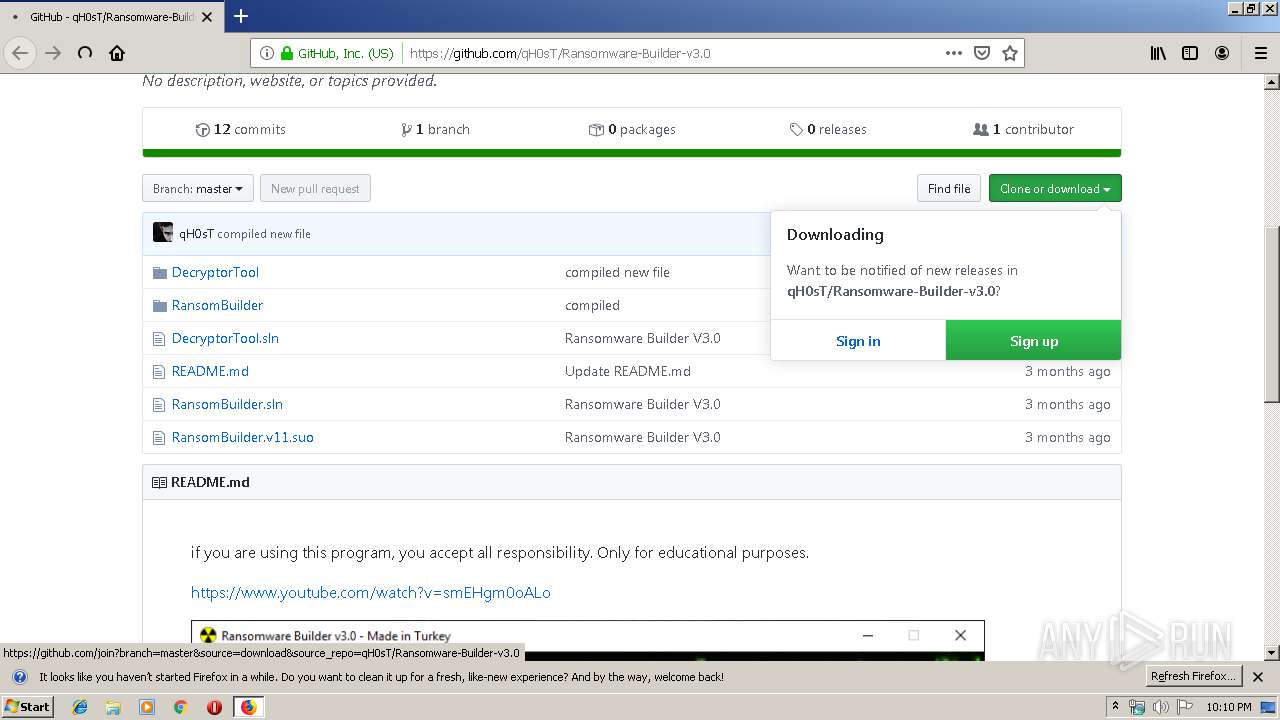
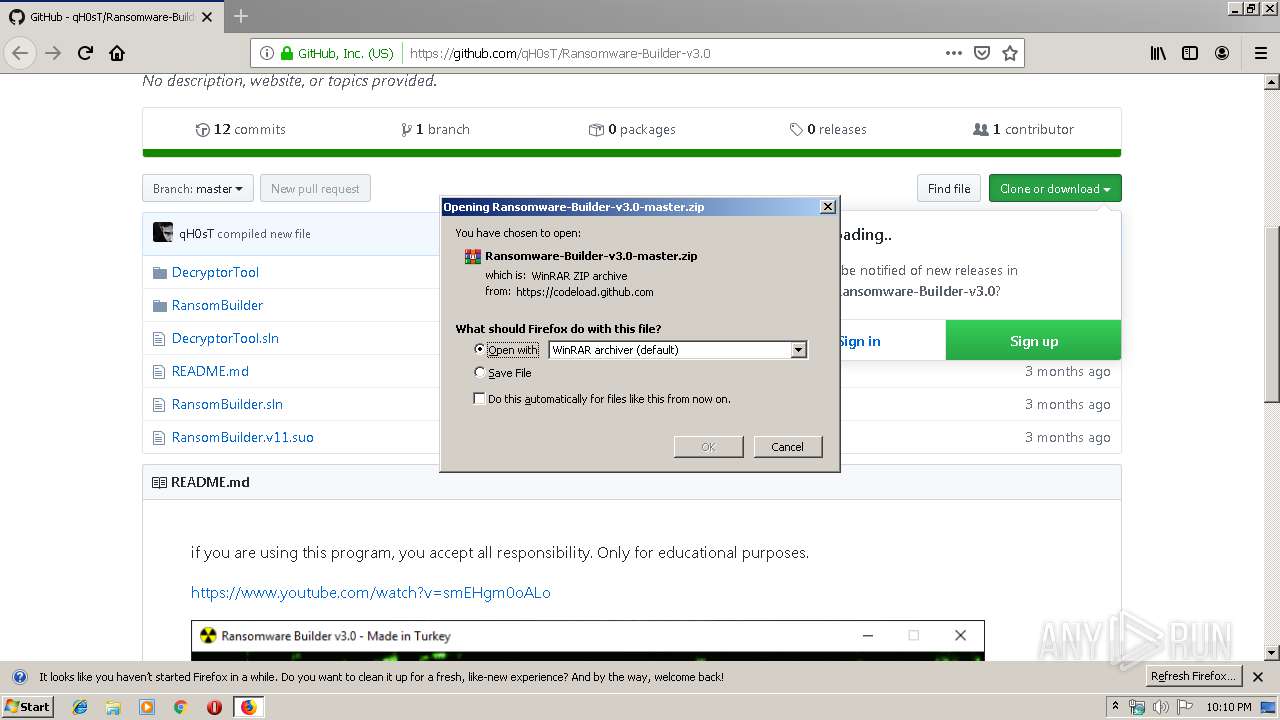
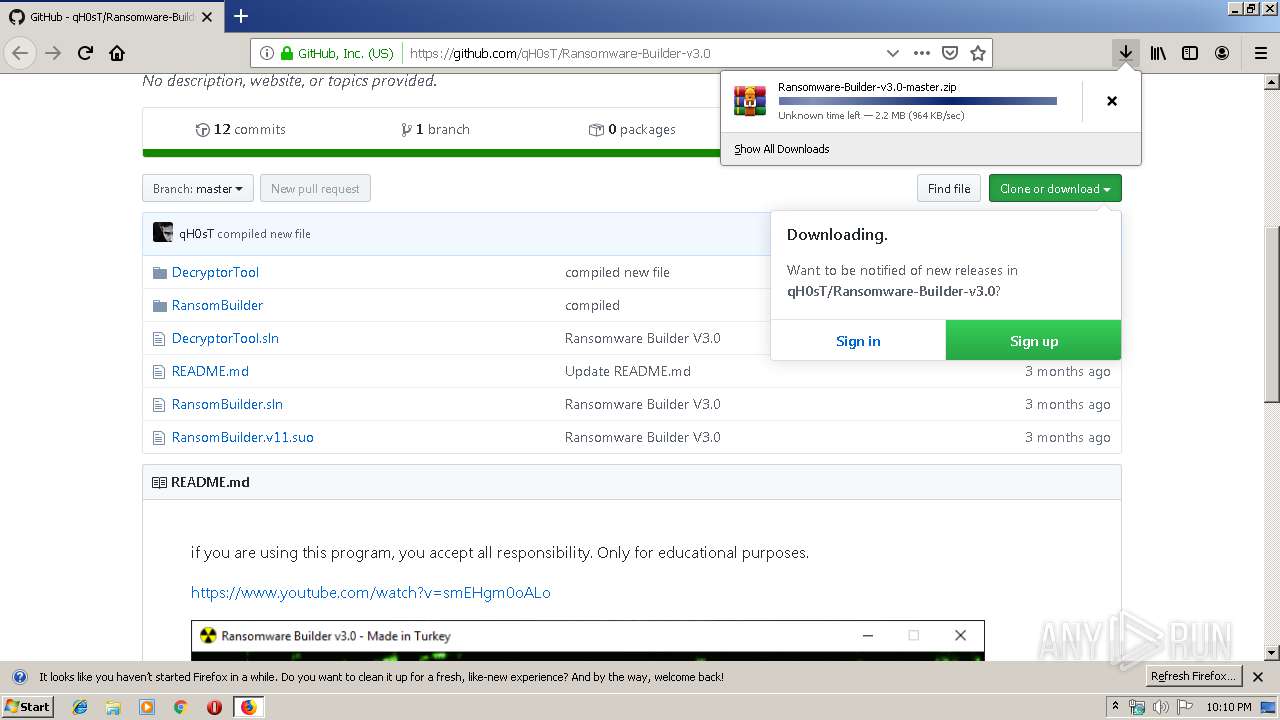
| 960 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/qH0sT/Ransomware-Builder-v3.0 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
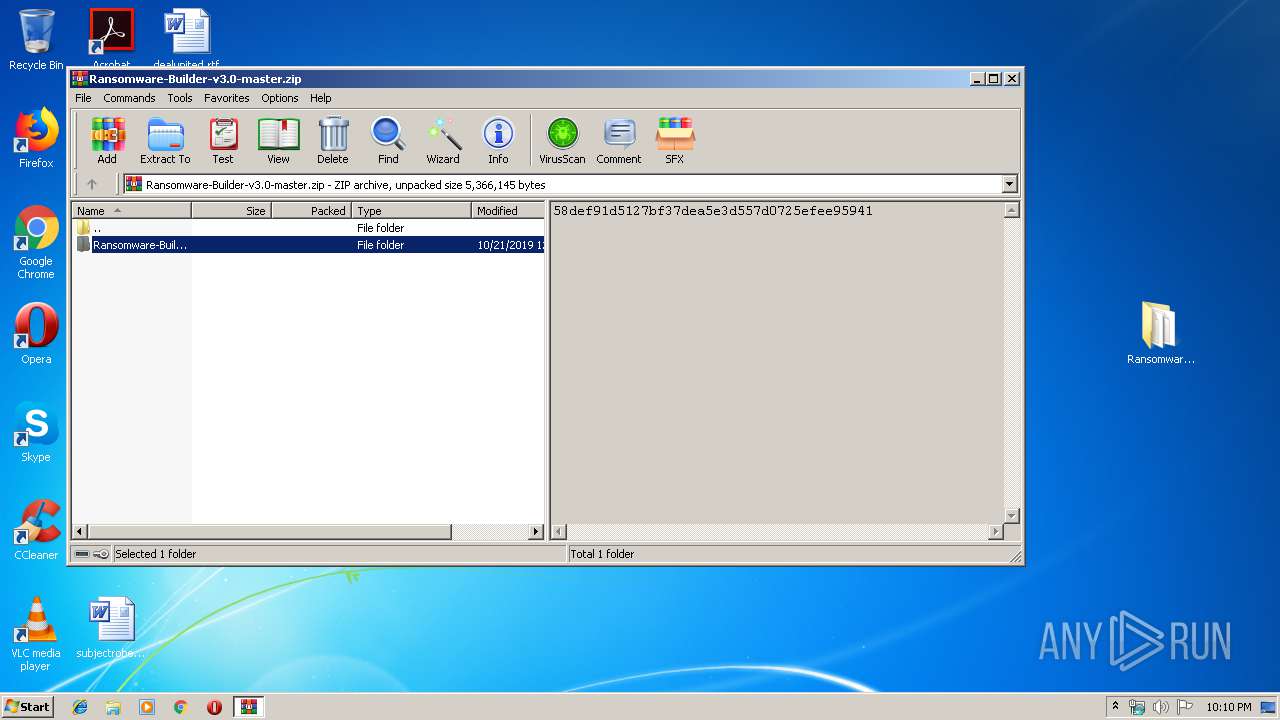
| 1748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ransomware-Builder-v3.0-master.zip" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="960.0.43858104\646726711" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 960 "\\.\pipe\gecko-crash-server-pipe.960" 1168 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
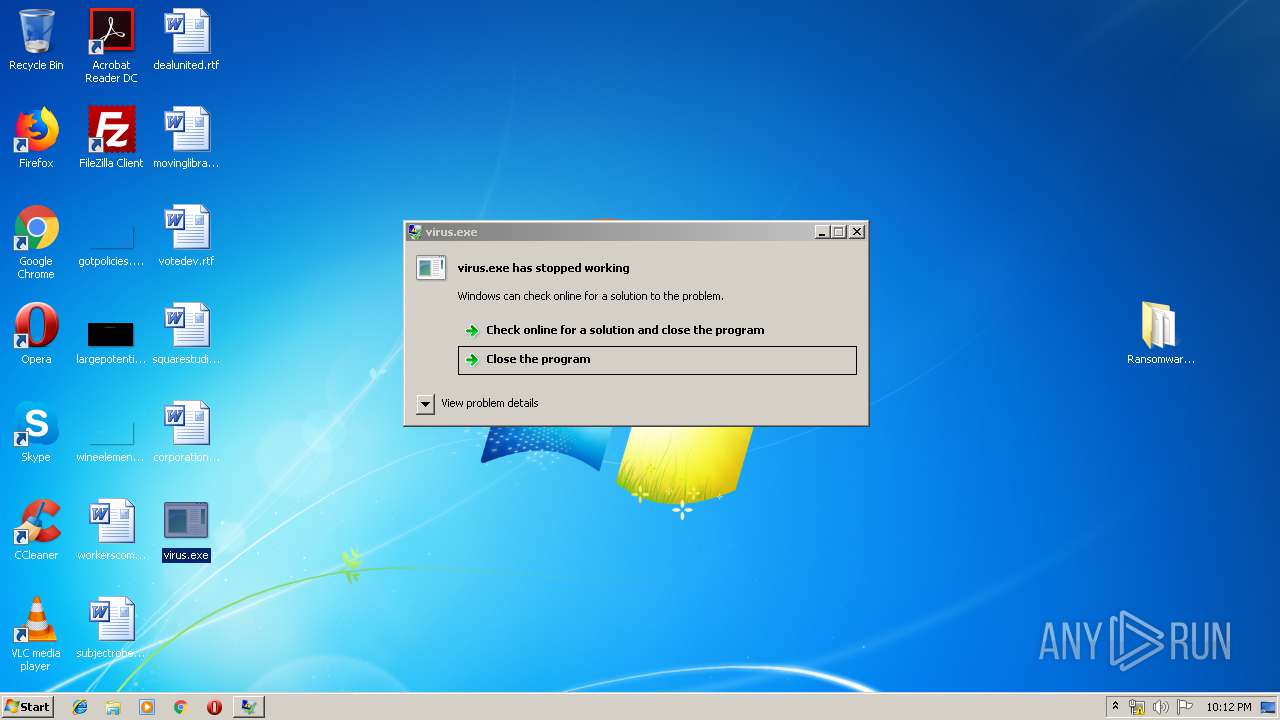
| 2068 | "C:\Users\admin\Desktop\virus.exe" | C:\Users\admin\Desktop\virus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 3762504530 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2096 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES243.tmp" "c:\Users\admin\Desktop\CSCE36096249EB44A99A6E5D7247125B683.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52519.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="960.13.1389795052\815133544" -childID 2 -isForBrowser -prefsHandle 2840 -prefMapHandle 2844 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 960 "\\.\pipe\gecko-crash-server-pipe.960" 2856 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
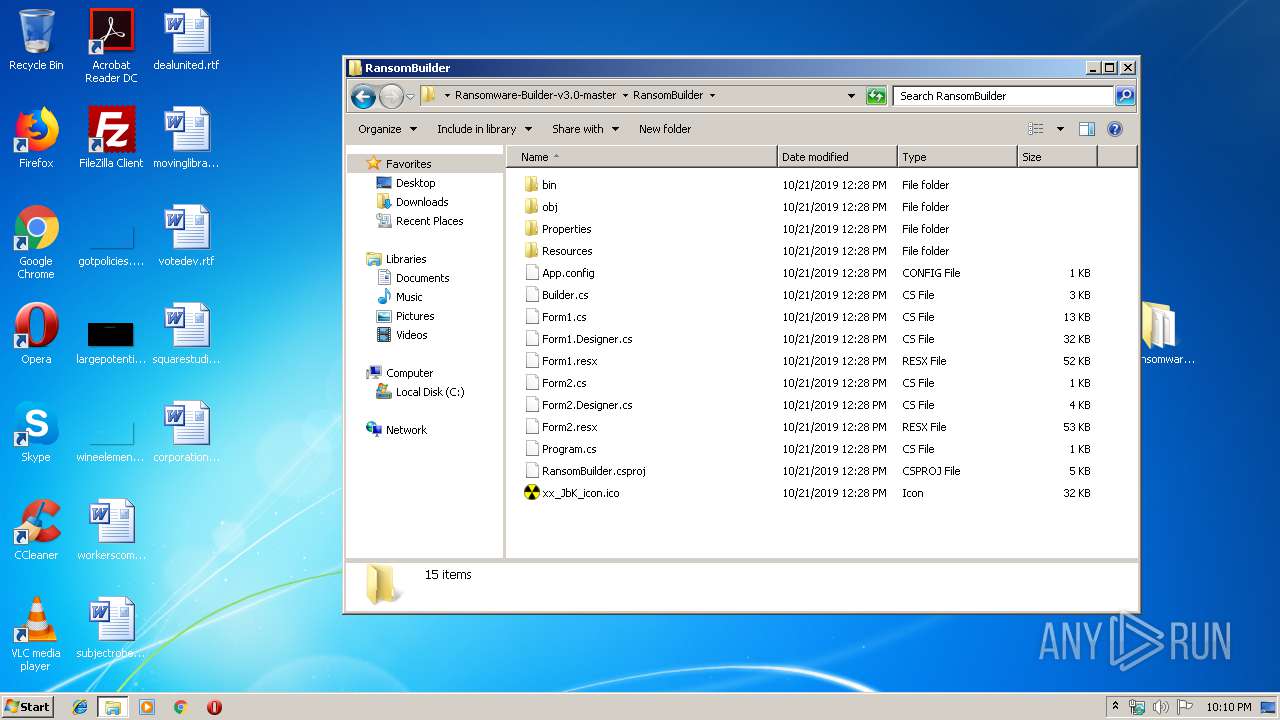
| 2352 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\nn5lrm1w.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | RansomBuilder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/02cbc227-ab2b-4904-9d52-b9a08a3a17f8/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\02cbc227-ab2b-4904-9d52-b9a08a3a17f8 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
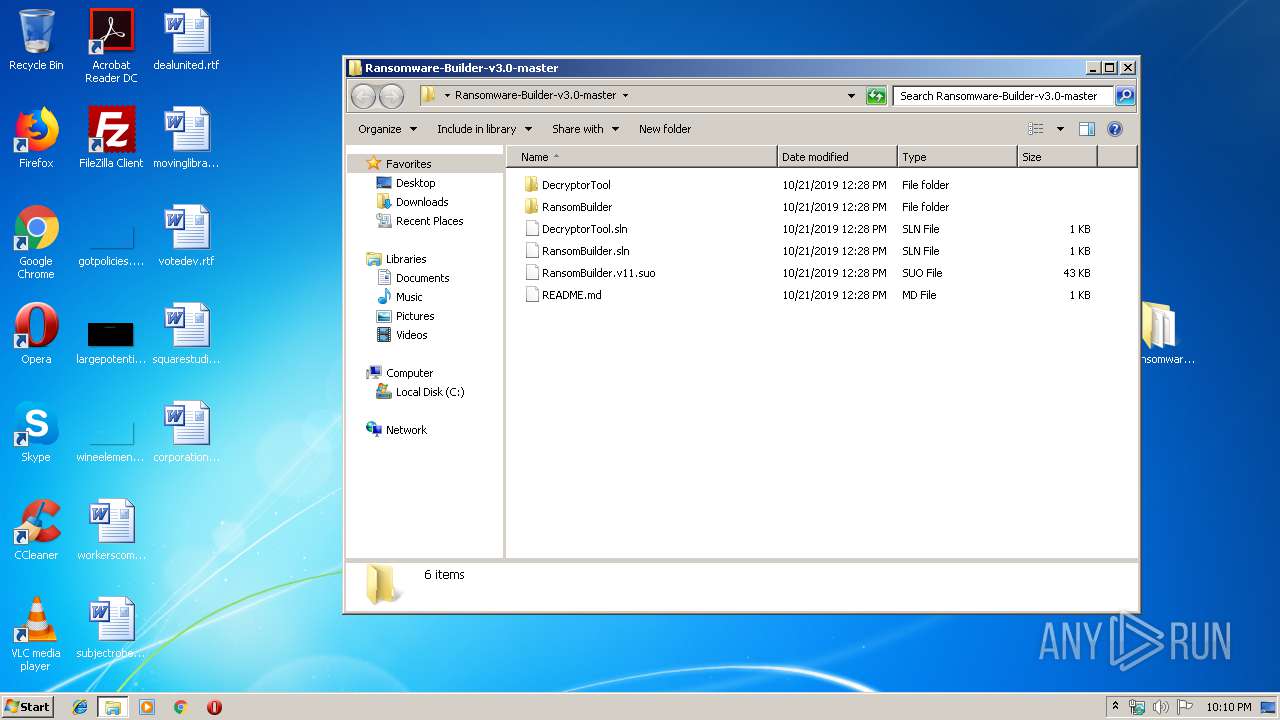
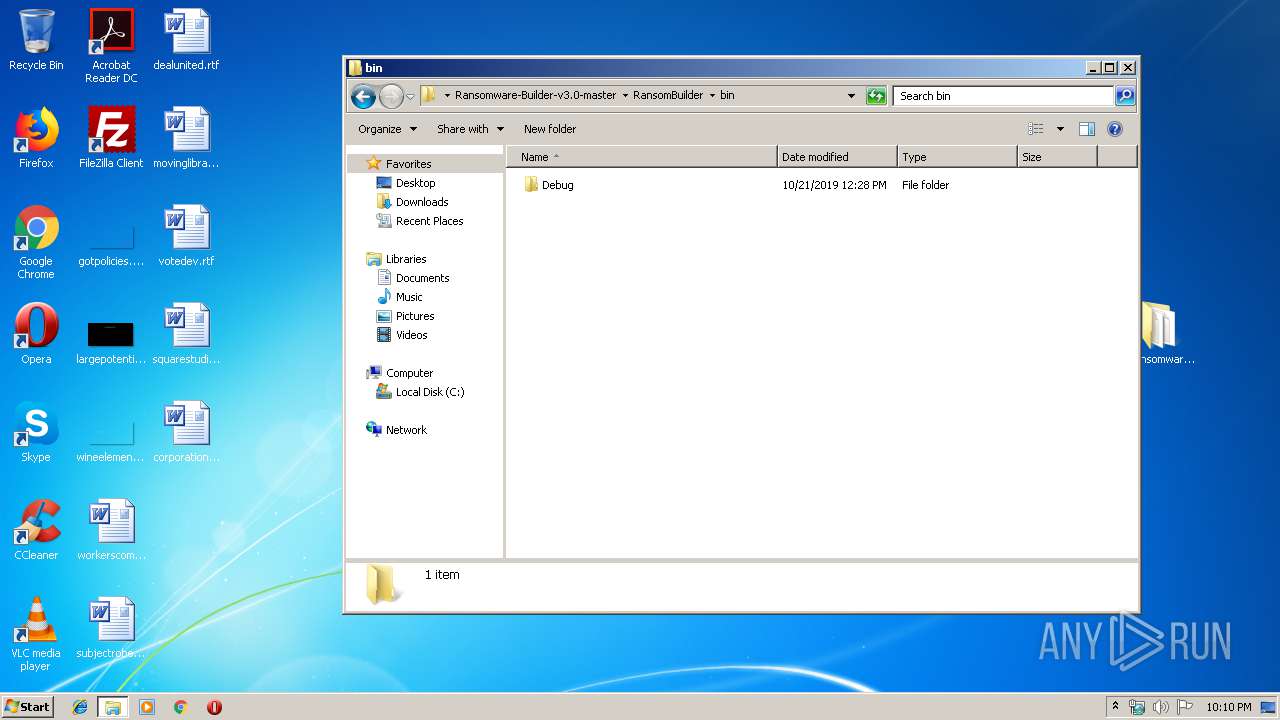
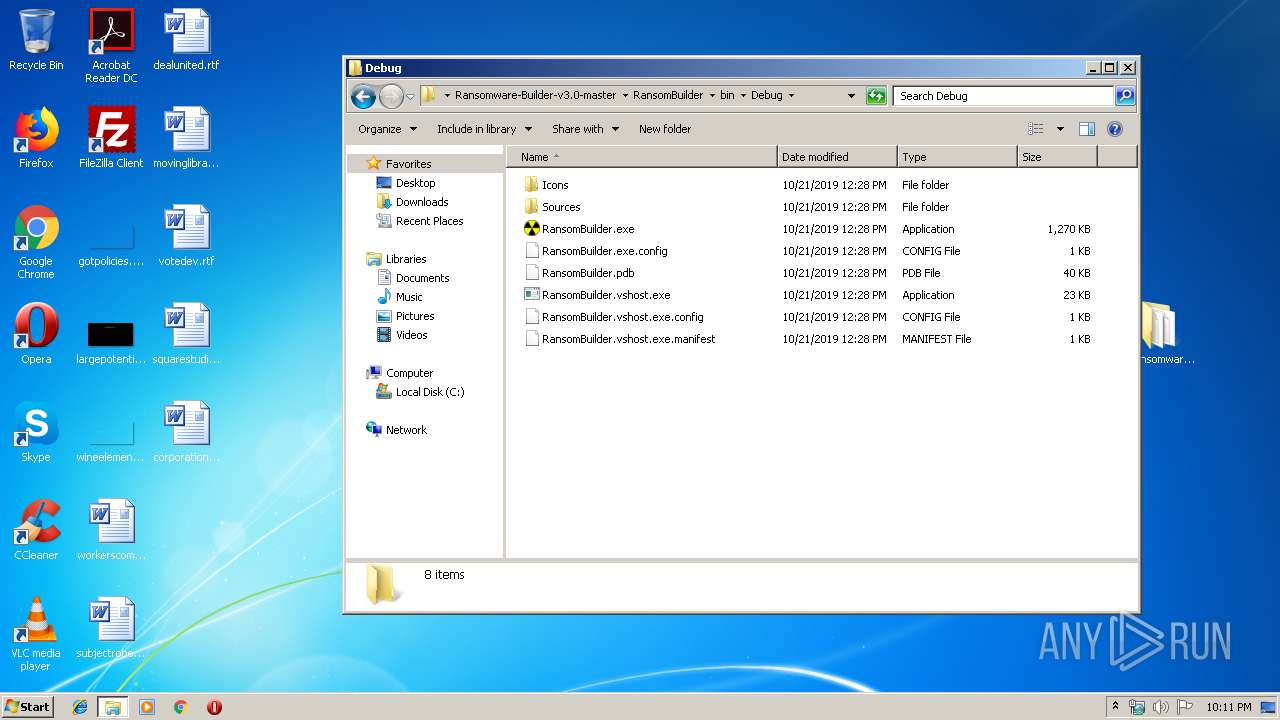
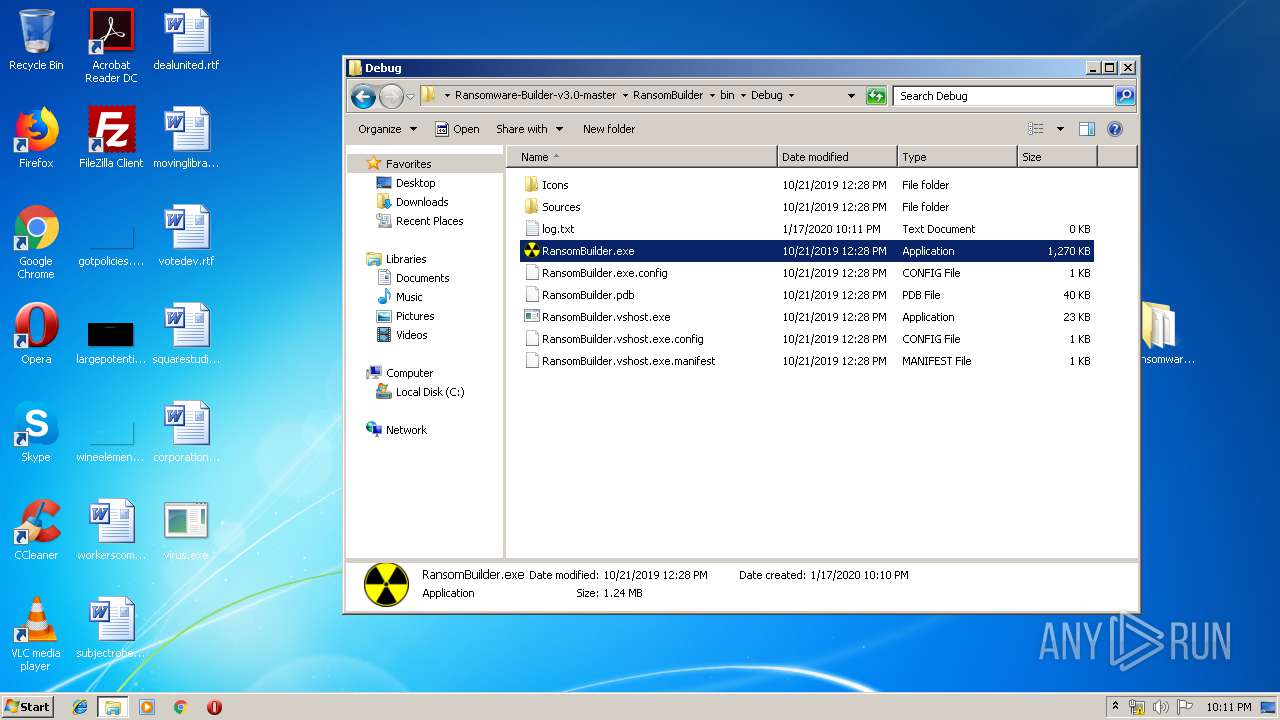
| 2420 | "C:\Users\admin\Desktop\Ransomware-Builder-v3.0-master\RansomBuilder\bin\Debug\RansomBuilder.exe" | C:\Users\admin\Desktop\Ransomware-Builder-v3.0-master\RansomBuilder\bin\Debug\RansomBuilder.exe | — | explorer.exe | |||||||||||
User: admin Company: FeelFreeSoft(R) Integrity Level: MEDIUM Description: Ransom Builder v3.0 Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/qH0sT/Ransomware-Builder-v3.0" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
2 571
Read events
2 449
Write events
119
Delete events
3
Modification events
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 1380441803000000 | |||
| (PID) Process: | (2512) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 8892411803000000 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (960) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
9
Suspicious files
93
Text files
95
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_vIVLrhWoQf7lcgb | — | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 960 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\DAAFD30E140BED4D35630A07BAABA650D0019475 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
37
DNS requests
81
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
960 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
960 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
960 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
960 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
960 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
960 | firefox.exe | 54.186.106.198:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
960 | firefox.exe | 52.35.182.58:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
960 | firefox.exe | 140.82.118.4:443 | github.com | — | US | malicious |
960 | firefox.exe | 13.35.253.14:443 | snippets.cdn.mozilla.net | — | US | unknown |
960 | firefox.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
960 | firefox.exe | 151.101.0.133:443 | avatars0.githubusercontent.com | Fastly | US | malicious |
960 | firefox.exe | 54.148.67.145:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
960 | firefox.exe | 143.204.101.24:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
960 | firefox.exe | 13.35.253.78:443 | content-signature-2.cdn.mozilla.net | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |