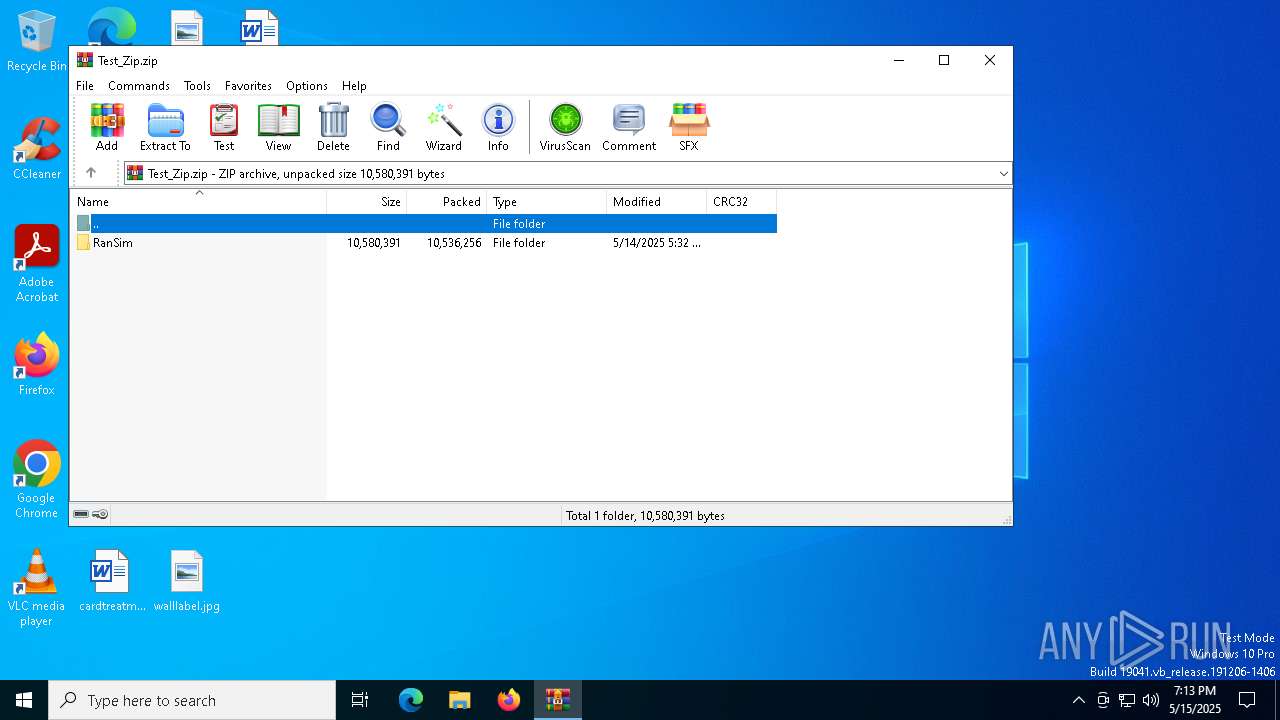
| File name: | Test_Zip.zip |
| Full analysis: | https://app.any.run/tasks/b6ffd437-5ff4-491f-ac66-bfafb778cfe0 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 19:12:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 6003AA93756E09271D6EADB36F68D82C |
| SHA1: | CC44C8D6F4E813CE839009DEB87D64E6230FC22D |
| SHA256: | DA4F037F510BE37B95F9A467EA6B75FE95CA7BDD2637CA3ED98A74B29EDE187C |
| SSDEEP: | 98304:6fxe+FUYtb9g3v0+ZG0SKgH3TTwmXrJTMQ9vkj5L4PhpbsYkinxBXbgR/QRlKZ86:r3mxuJrzinZatamqeB78Yus/ |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7312)
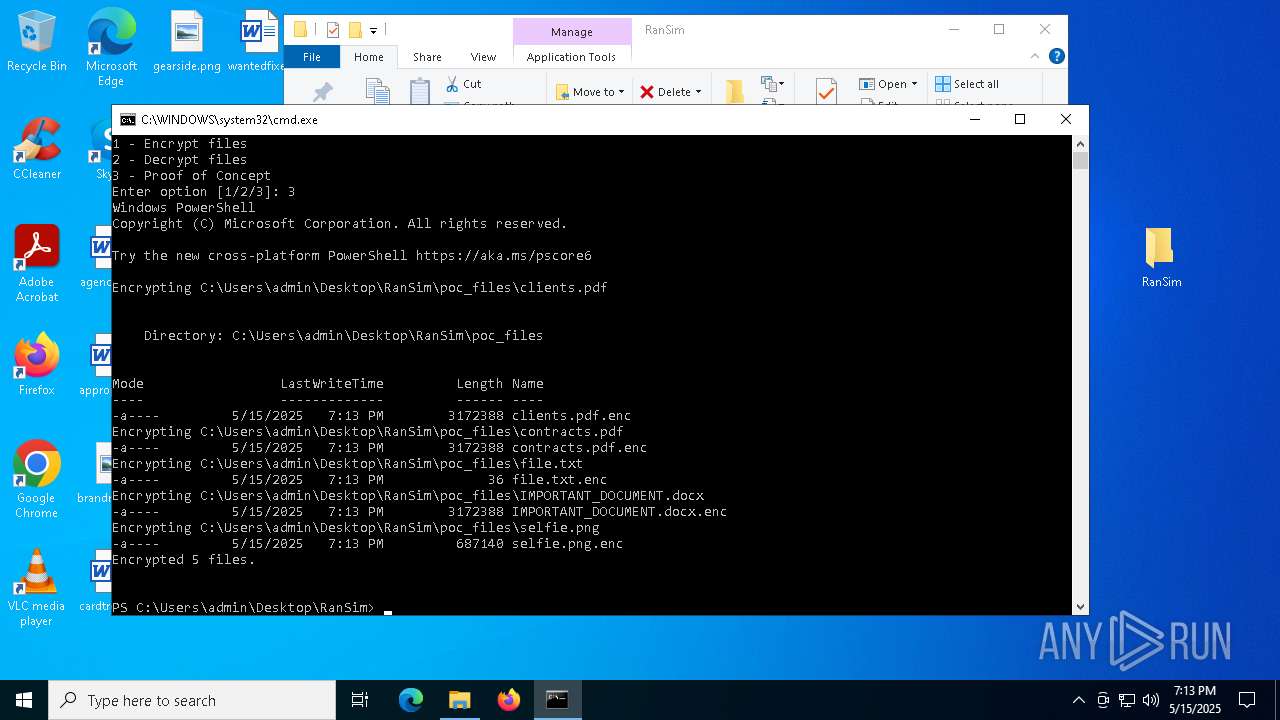
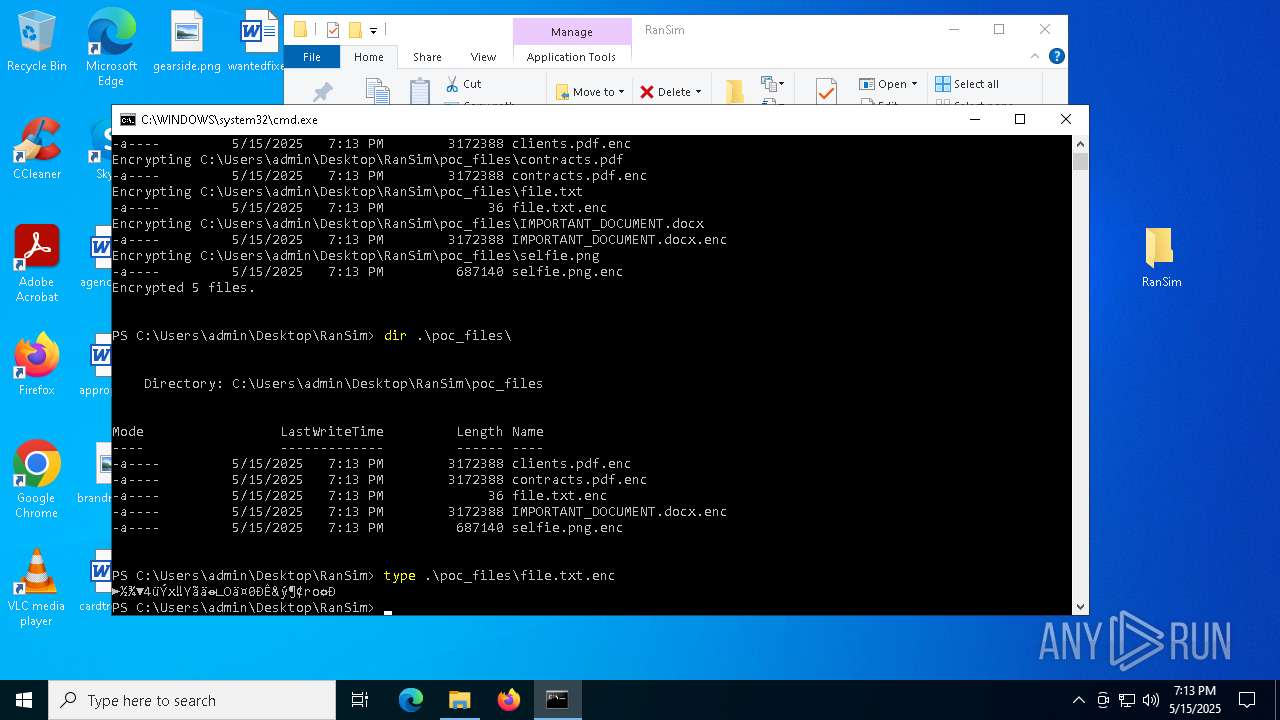
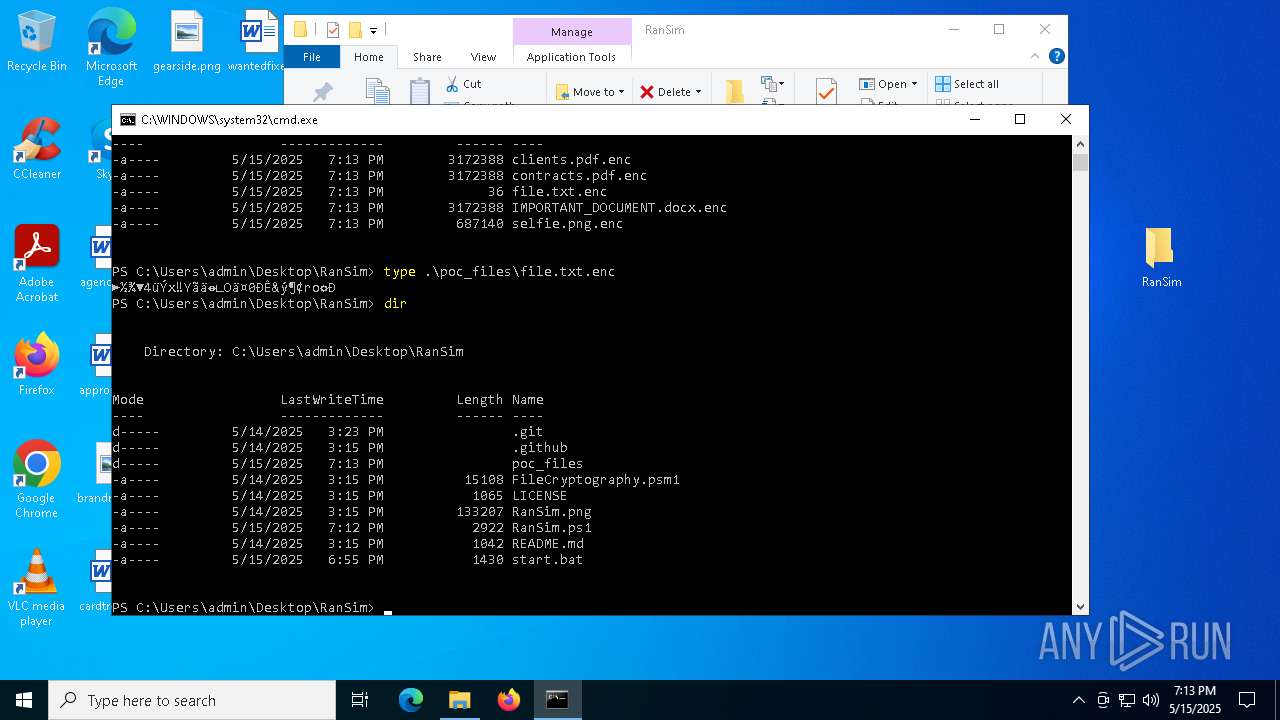
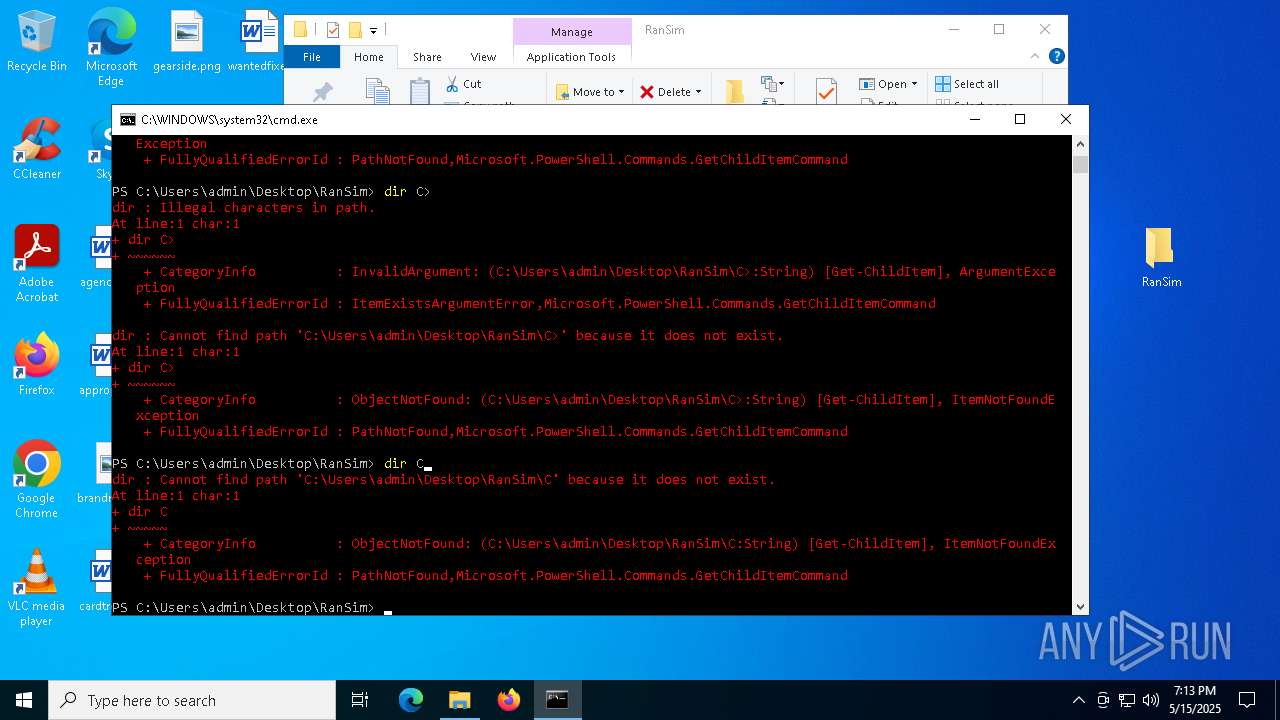
Bypass execution policy to execute commands
- powershell.exe (PID: 7912)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7836)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7912)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7912)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7912)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7836)
The process executes Powershell scripts
- cmd.exe (PID: 7836)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7912)
INFO
Gets data length (POWERSHELL)
- powershell.exe (PID: 7912)
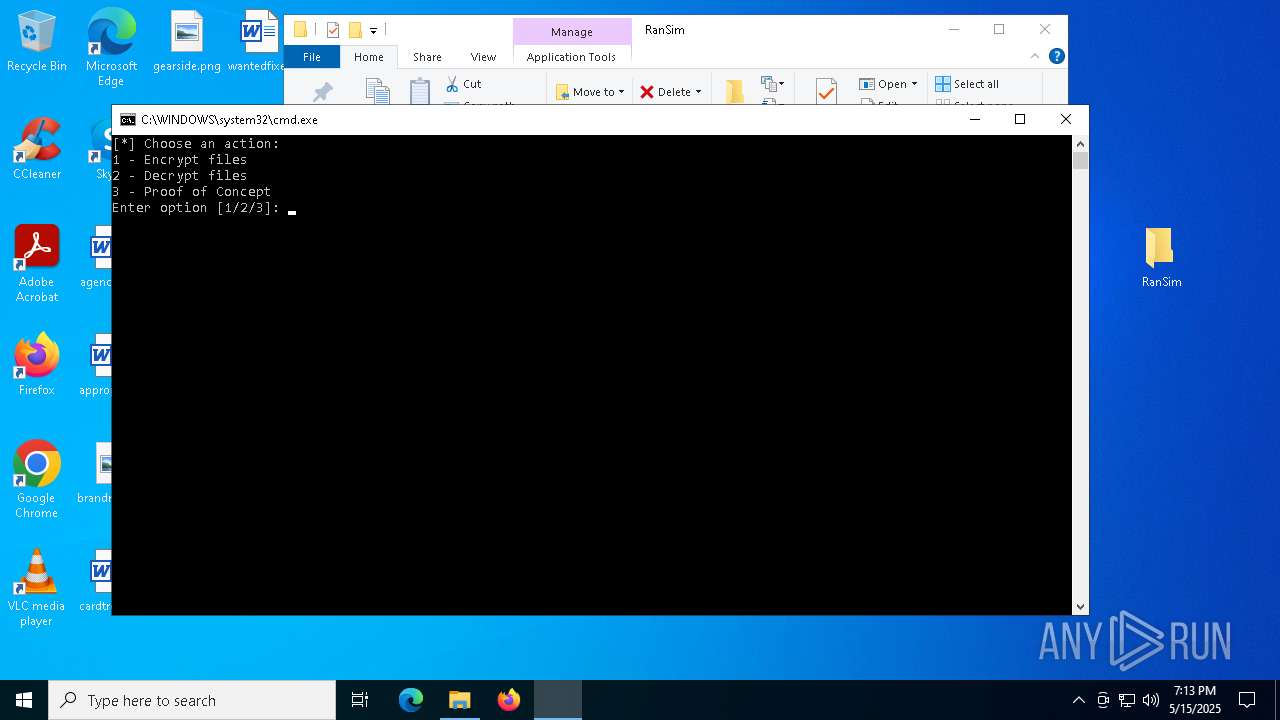
Manual execution by a user
- cmd.exe (PID: 7836)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7912)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7912)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7912)
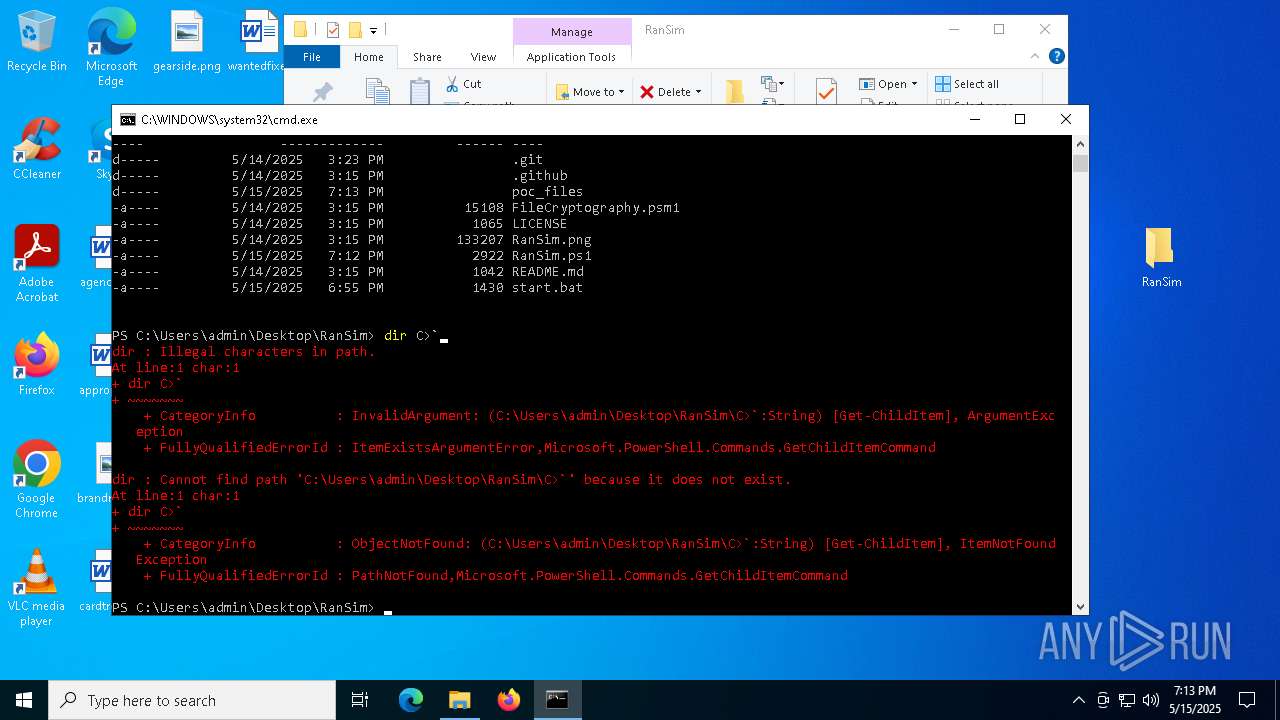
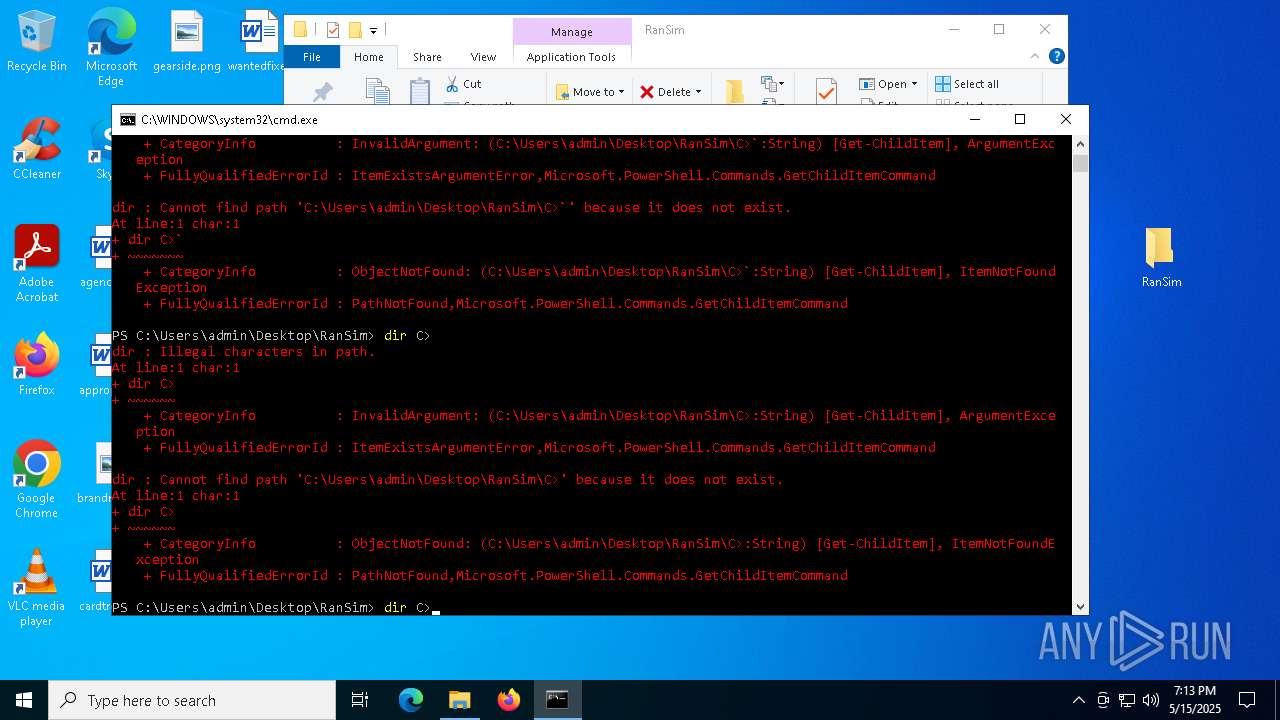
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7912)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:14 18:32:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
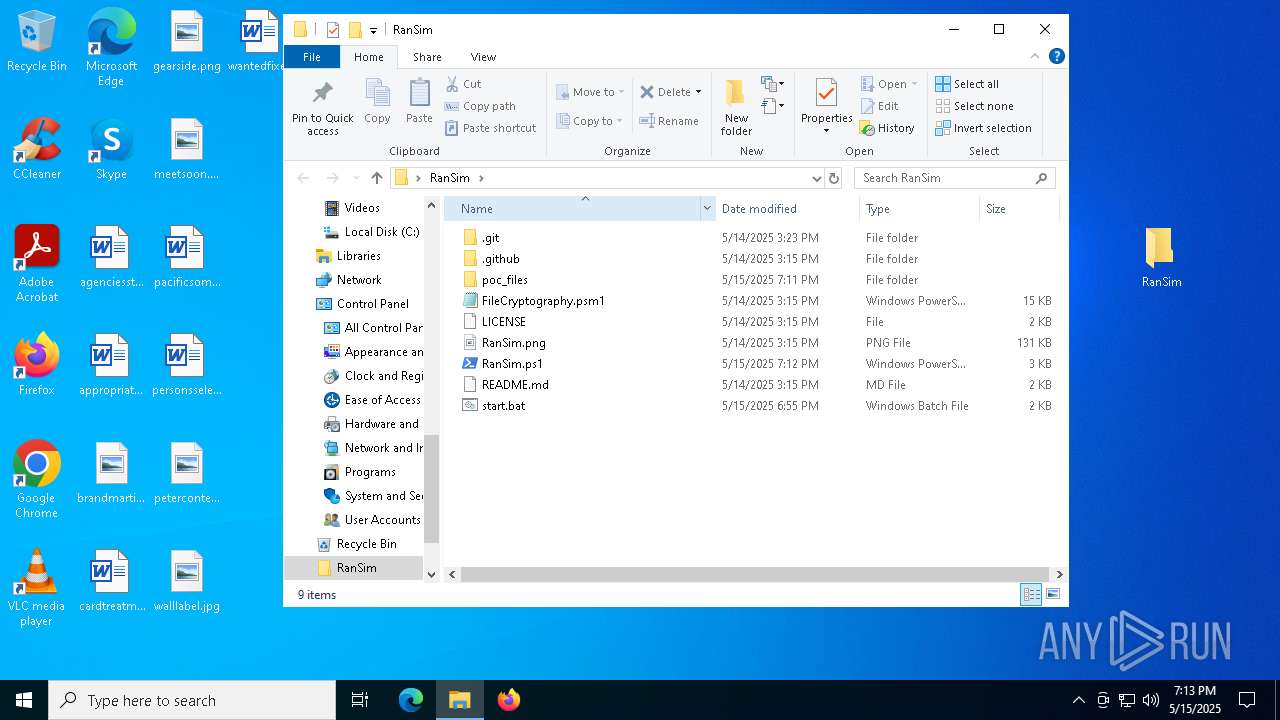
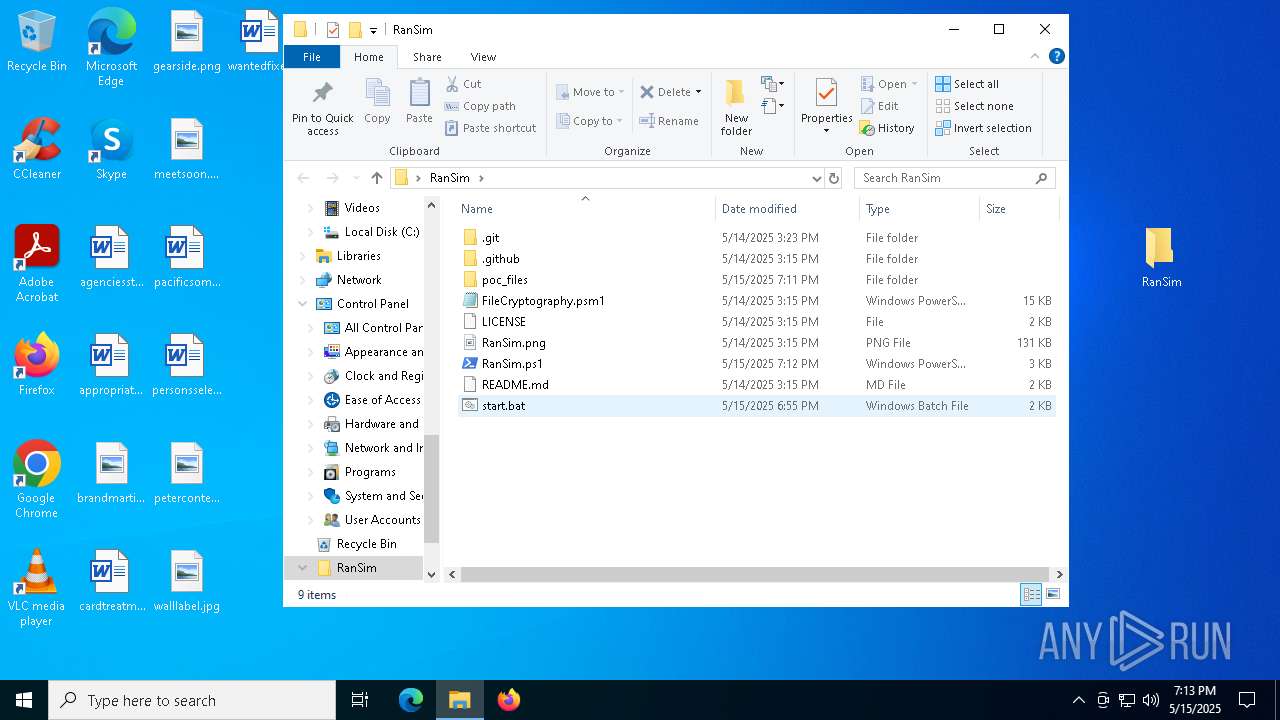
| ZipFileName: | RanSim/ |
Total processes
135
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7204 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
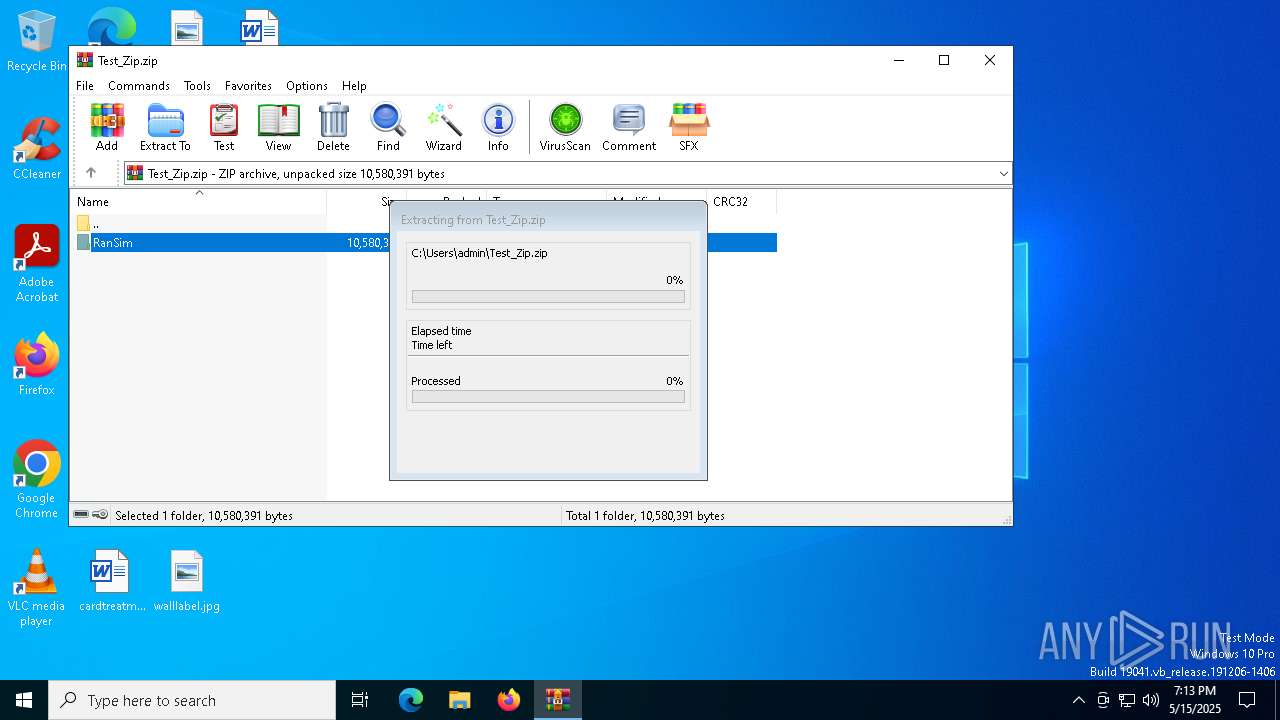
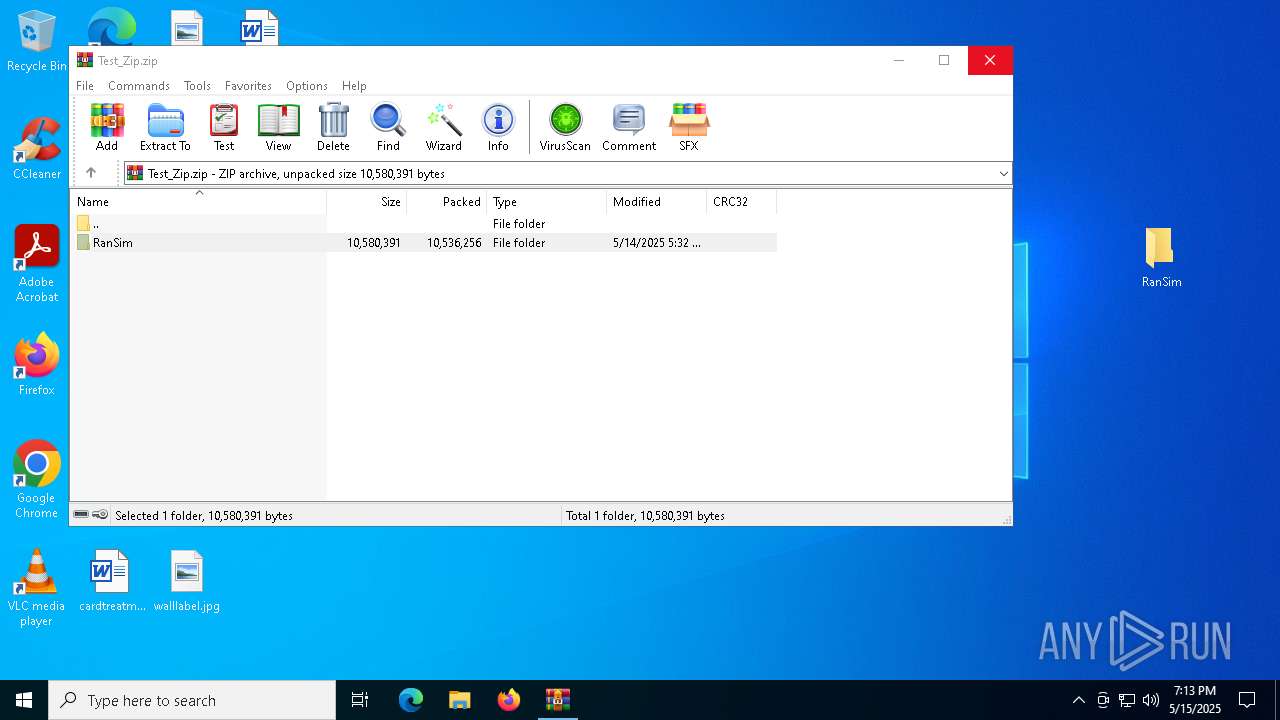
| 7312 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Test_Zip.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7776 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7836 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\RanSim\start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7844 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
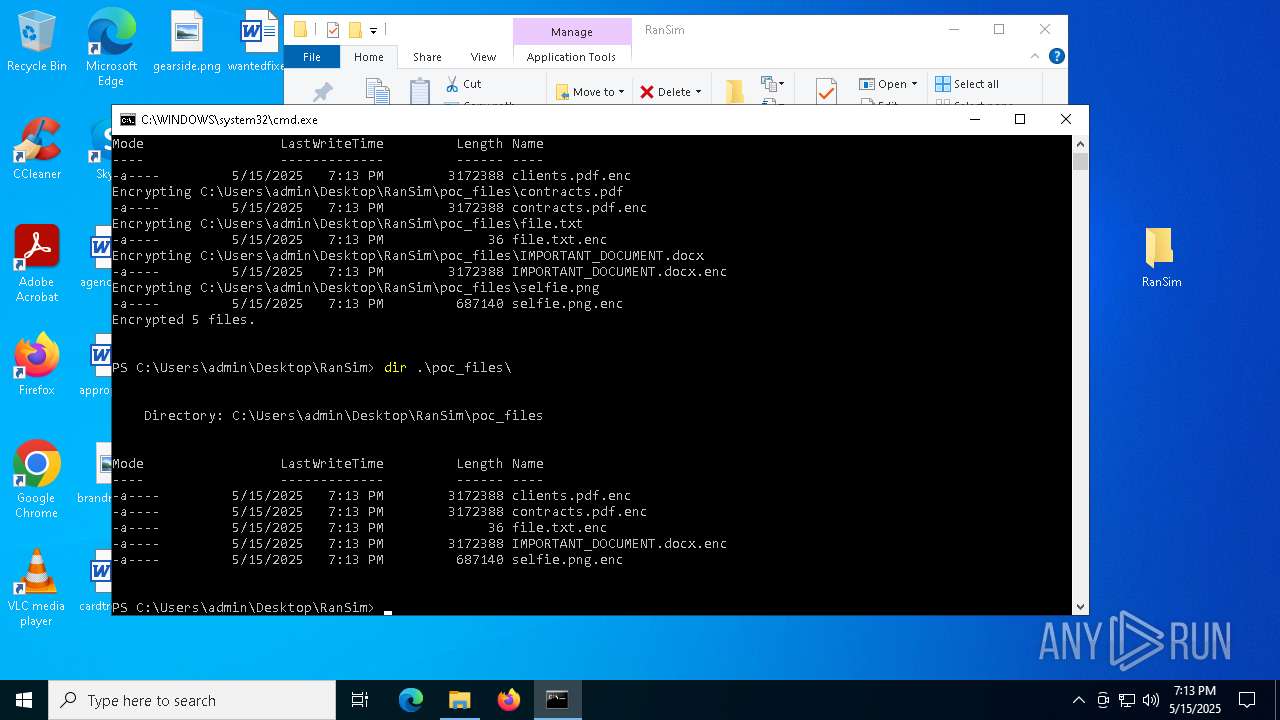
| 7912 | powershell -ExecutionPolicy Bypass -NoExit -File RanSim.ps1 -Mode encrypt -Extension ".enc" -Key "Q5KyUru6wn82hlY9k8xUjJOPIC9da41jgRkpt21jo2L=" -TargetPath ".\poc_files" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 083
Read events
7 065
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Test_Zip.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
14
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\refs\heads\main | text | |
MD5:9BE5355F7AB7E048F73CC415D4EF114E | SHA256:9D4F770D31EABD9D8D461ECD856404E6C9A7365ED003156E87F8B802CE097BF4 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\update.sample | text | |
MD5:647AE13C682F7827C22F5FC08A03674E | SHA256:8D5F2FA83E103CF08B57EAA67521DF9194F45CBDBCB37DA52AD586097A14D106 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\packed-refs | text | |
MD5:944E41CEAF16C74F7B2437C406C00EEC | SHA256:4F93537CE77DFC23BCEDDE1927B125DEF55545C87BF789E13FA9C13752A7EFBE | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\LICENSE | text | |
MD5:7325E58BFC93561A31A5EC2775AB87AC | SHA256:C5232EF7D0F1DDC721E26817DC27A09F8DACA68CF45D7A82EE4F4C1E60FE040B | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\applypatch-msg.sample | text | |
MD5:CE562E08D8098926A3862FC6E7905199 | SHA256:0223497A0B8B033AA58A3A521B8629869386CF7AB0E2F101963D328AA62193F7 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\info\exclude | text | |
MD5:036208B4A1AB4A235D75C181E685E5A3 | SHA256:6671FE83B7A07C8932EE89164D1F2793B2318058EB8B98DC5C06EE0A5A3B0EC1 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\pre-merge-commit.sample | text | |
MD5:39CB268E2A85D436B9EB6F47614C3CBC | SHA256:D3825A70337940EBBD0A5C072984E13245920CDF8898BD225C8D27A6DFC9CB53 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\sendemail-validate.sample | text | |
MD5:4D67DF3A8D5C98CB8565C07E42BE0B04 | SHA256:44EBFC923DC5466BC009602F0ECF067B9C65459ABFE8868DDC49B78E6CED7A92 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\pre-applypatch.sample | text | |
MD5:054F9FFB8BFE04A599751CC757226DDA | SHA256:E15C5B469EA3E0A695BEA6F2C82BCF8E62821074939DDD85B77E0007FF165475 | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7312.19513\RanSim\.git\hooks\push-to-checkout.sample | text | |
MD5:C7AB00C7784EFEADAD3AE9B228D4B4DB | SHA256:A53D0741798B287C6DD7AFA64AEE473F305E65D3F49463BB9D7408EC3B12BF5F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5324 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |